| File name: | aacc8432eda684b179dab3de142286625d9a7322e5d9b3501b9cc711af9b50dc.doc |
| Full analysis: | https://app.any.run/tasks/0160ee25-54b7-40d3-b216-bc864c0435f2 |
| Verdict: | Malicious activity |
| Analysis date: | June 19, 2019, 02:41:43 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.openxmlformats-officedocument.wordprocessingml.document |
| File info: | Microsoft Word 2007+ |
| MD5: | 43B1FEE15096EDB5B3EB18999B84B838 |
| SHA1: | 2777ECB029E986AB2FC281724DF1EDF2C71B429A |
| SHA256: | AACC8432EDA684B179DAB3DE142286625D9A7322E5D9B3501B9CC711AF9B50DC |
| SSDEEP: | 1536:Jnz0vf4iGbX51pae9ziilMtQzRzn+FNWqnalO/Kp:Jz0X49L51MVipx+FNWCCp |
MALICIOUS
Runs PING.EXE for delay simulation
- cmd.exe (PID: 332)
- cmd.exe (PID: 2180)
- cmd.exe (PID: 704)
- cmd.exe (PID: 804)
Starts CMD.EXE for commands execution
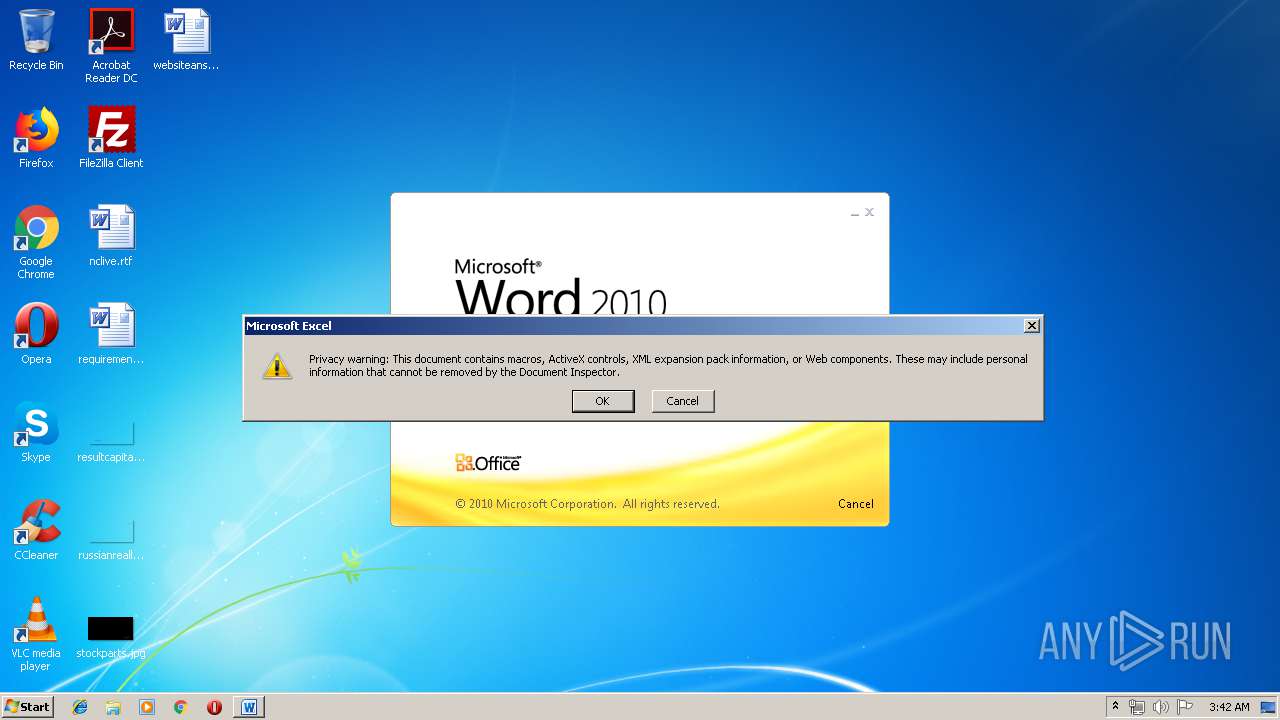
- EXCEL.EXE (PID: 2904)
- EXCEL.EXE (PID: 2212)
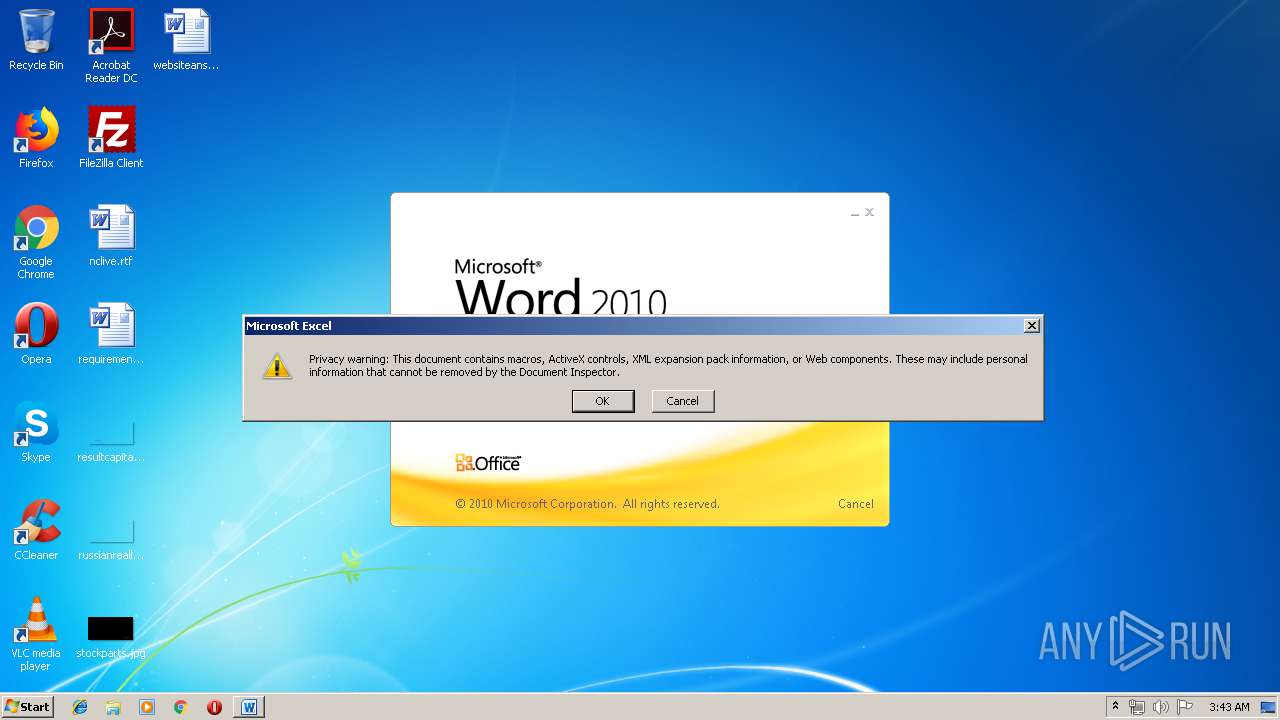
Unusual execution from Microsoft Office
- EXCEL.EXE (PID: 2904)
- EXCEL.EXE (PID: 2212)
Application was dropped or rewritten from another process
- WScript.exe (PID: 3412)
- WScript.exe (PID: 1032)
- amsi.dll (PID: 2432)
- wscript.exe (PID: 3464)
- amsi.dll (PID: 4064)
- WScript.exe (PID: 3612)
- WScript.exe (PID: 872)
- wscript.exe (PID: 3860)
Changes settings of System certificates
- amsi.dll (PID: 2432)
- amsi.dll (PID: 4064)
- WScript.exe (PID: 872)
Loads dropped or rewritten executable
- cmd.exe (PID: 332)
- cmd.exe (PID: 2180)
- WScript.exe (PID: 1032)
- SearchProtocolHost.exe (PID: 2920)
- svchost.exe (PID: 848)
- amsi.dll (PID: 2432)
- wscript.exe (PID: 3464)
- cmd.exe (PID: 804)
- cmd.exe (PID: 704)
Writes to a start menu file
- amsi.dll (PID: 2432)
- amsi.dll (PID: 4064)
- WScript.exe (PID: 872)
Changes the autorun value in the registry
- amsi.dll (PID: 2432)
- WScript.exe (PID: 872)
- amsi.dll (PID: 4064)
SUSPICIOUS
Executed via COM
- EXCEL.EXE (PID: 2904)
- excelcnv.exe (PID: 2460)
- EXCEL.EXE (PID: 2212)
- excelcnv.exe (PID: 4040)
Executes scripts
- cmd.exe (PID: 2180)
- cmd.exe (PID: 332)
- amsi.dll (PID: 2432)
- cmd.exe (PID: 804)
- cmd.exe (PID: 704)
- WScript.exe (PID: 872)
Starts itself from another location
- WScript.exe (PID: 1032)
- amsi.dll (PID: 2432)
- wscript.exe (PID: 3464)
Starts application with an unusual extension
- WScript.exe (PID: 1032)
- wscript.exe (PID: 3464)
Executable content was dropped or overwritten
- WScript.exe (PID: 1032)
Creates files in the user directory
- amsi.dll (PID: 2432)
Adds / modifies Windows certificates
- amsi.dll (PID: 2432)
- amsi.dll (PID: 4064)
- WScript.exe (PID: 872)
Application launched itself
- WScript.exe (PID: 872)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 712)
- EXCEL.EXE (PID: 2904)
Reads Microsoft Office registry keys
- EXCEL.EXE (PID: 2904)
- WINWORD.EXE (PID: 712)
- excelcnv.exe (PID: 2460)
- EXCEL.EXE (PID: 2212)
- excelcnv.exe (PID: 4040)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .docx | | | Word Microsoft Office Open XML Format document (52.2) |
|---|---|---|
| .zip | | | Open Packaging Conventions container (38.8) |
| .zip | | | ZIP compressed archive (8.8) |
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0006 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 1980:01:01 00:00:00 |
| ZipCRC: | 0xf2459e1f |
| ZipCompressedSize: | 392 |
| ZipUncompressedSize: | 1806 |
| ZipFileName: | [Content_Types].xml |
XMP
| Title: | - |
|---|---|
| Subject: | - |
| Creator: | Joselio Bonin |
| Description: | - |
XML
| Keywords: | - |
|---|---|
| LastModifiedBy: | Joselio Bonin |
| RevisionNumber: | 5 |
| CreateDate: | 2019:06:16 00:44:00Z |
| ModifyDate: | 2019:06:17 01:53:00Z |
| Template: | Normal.dotm |
| TotalEditTime: | 17.4 hours |
| Pages: | 1 |
| Words: | 411 |
| Characters: | 2221 |
| Application: | Microsoft Office Word |
| DocSecurity: | None |
| Lines: | 18 |
| Paragraphs: | 5 |
| ScaleCrop: | No |
| HeadingPairs: |
|
| TitlesOfParts: | - |
| Company: | - |
| LinksUpToDate: | No |
| CharactersWithSpaces: | 2627 |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| AppVersion: | 16 |
Total processes
59
Monitored processes
23
Malicious processes
11
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 116 | ping 127.0.0.1 -n 5 | C:\Windows\system32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Ping Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 332 | "C:\Windows\System32\cmd.exe" /c ping 127.0.0.1 -n 3 > nul & start C:\Users\Public\WindowsDefender.vbs | C:\Windows\System32\cmd.exe | — | EXCEL.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 704 | "C:\Windows\System32\cmd.exe" /c ping 127.0.0.1 -n 5 > nul & start C:\Users\Public\atach.vbs | C:\Windows\System32\cmd.exe | — | EXCEL.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 712 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\aacc8432eda684b179dab3de142286625d9a7322e5d9b3501b9cc711af9b50dc.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 804 | "C:\Windows\System32\cmd.exe" /c ping 127.0.0.1 -n 3 > nul & start C:\Users\Public\WindowsDefender.vbs | C:\Windows\System32\cmd.exe | — | EXCEL.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 848 | C:\Windows\system32\svchost.exe -k netsvcs | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 872 | "C:\Windows\System32\WScript.exe" "C:\Users\Public\atach.vbs" | C:\Windows\System32\WScript.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 1032 | "C:\Windows\System32\WScript.exe" "C:\Users\Public\atach.vbs" | C:\Windows\System32\WScript.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 2180 | "C:\Windows\System32\cmd.exe" /c ping 127.0.0.1 -n 5 > nul & start C:\Users\Public\atach.vbs | C:\Windows\System32\cmd.exe | — | EXCEL.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2212 | "C:\Program Files\Microsoft Office\Office14\EXCEL.EXE" -Embedding | C:\Program Files\Microsoft Office\Office14\EXCEL.EXE | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
2 460
Read events
2 026
Write events
400
Delete events
34
Modification events
| (PID) Process: | (712) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | /#: |
Value: 2F233A00C8020000010000000000000000000000 | |||
| (PID) Process: | (712) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (712) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (712) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1322450974 | |||
| (PID) Process: | (712) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1322451088 | |||
| (PID) Process: | (712) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1322451089 | |||
| (PID) Process: | (712) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: C8020000282045914826D50100000000 | |||
| (PID) Process: | (712) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | h$: |
Value: 68243A00C802000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (712) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | h$: |
Value: 68243A00C802000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (712) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
1
Suspicious files
24
Text files
32
Unknown types
9
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 712 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR3F2F.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 712 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\{79F5F166-D795-4C9A-B6CC-19CD88C718B2} | — | |
MD5:— | SHA256:— | |||
| 712 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\{E50BC193-61E3-434A-8D46-E44917757C8E} | — | |
MD5:— | SHA256:— | |||
| 2904 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVRFC45.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 848 | svchost.exe | C:\Windows\appcompat\programs\RecentFileCache.bcf | txt | |
MD5:— | SHA256:— | |||
| 712 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\14.0\OfficeFileCache\FSD-CNRY.FSD | binary | |
MD5:— | SHA256:— | |||
| 2904 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\~DFD85E3DCDDFC85EAA.TMP | — | |
MD5:— | SHA256:— | |||
| 712 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$cc8432eda684b179dab3de142286625d9a7322e5d9b3501b9cc711af9b50dc.doc | pgc | |
MD5:— | SHA256:— | |||
| 2460 | excelcnv.exe | C:\Users\admin\AppData\Local\Temp\CVR18F5.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 712 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
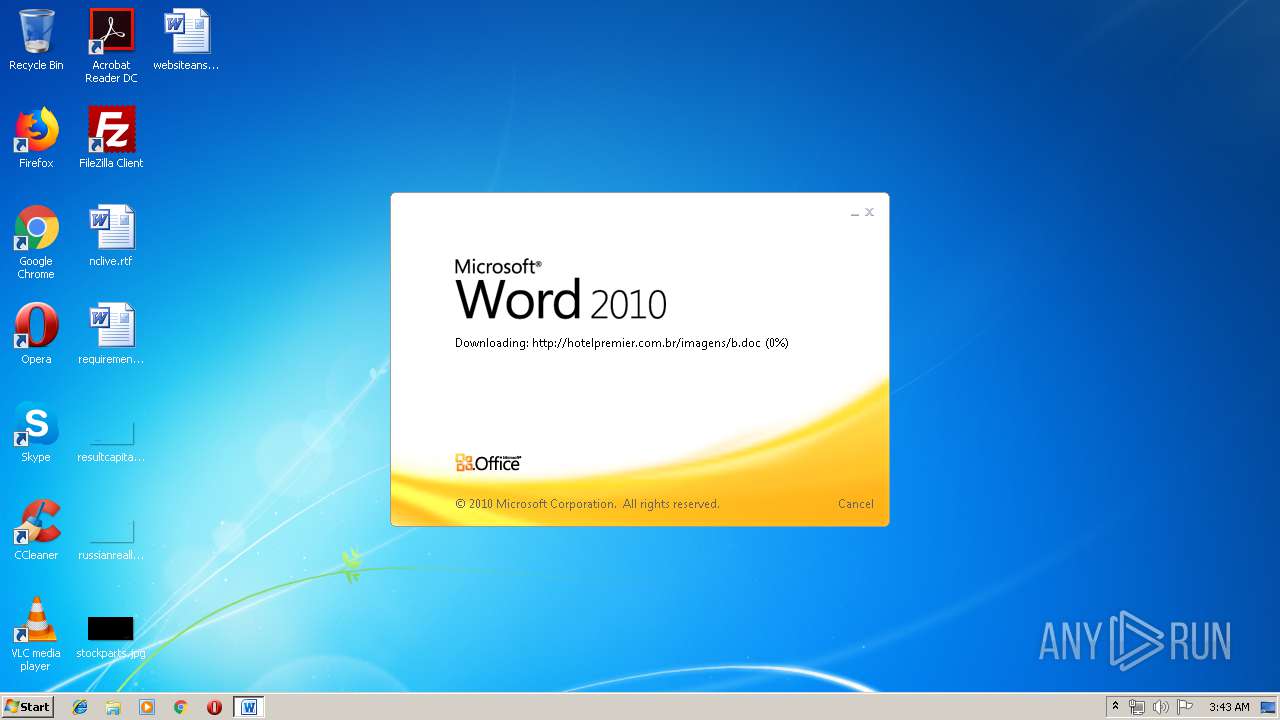
HTTP(S) requests
52
TCP/UDP connections
71
DNS requests
5
Threats
8
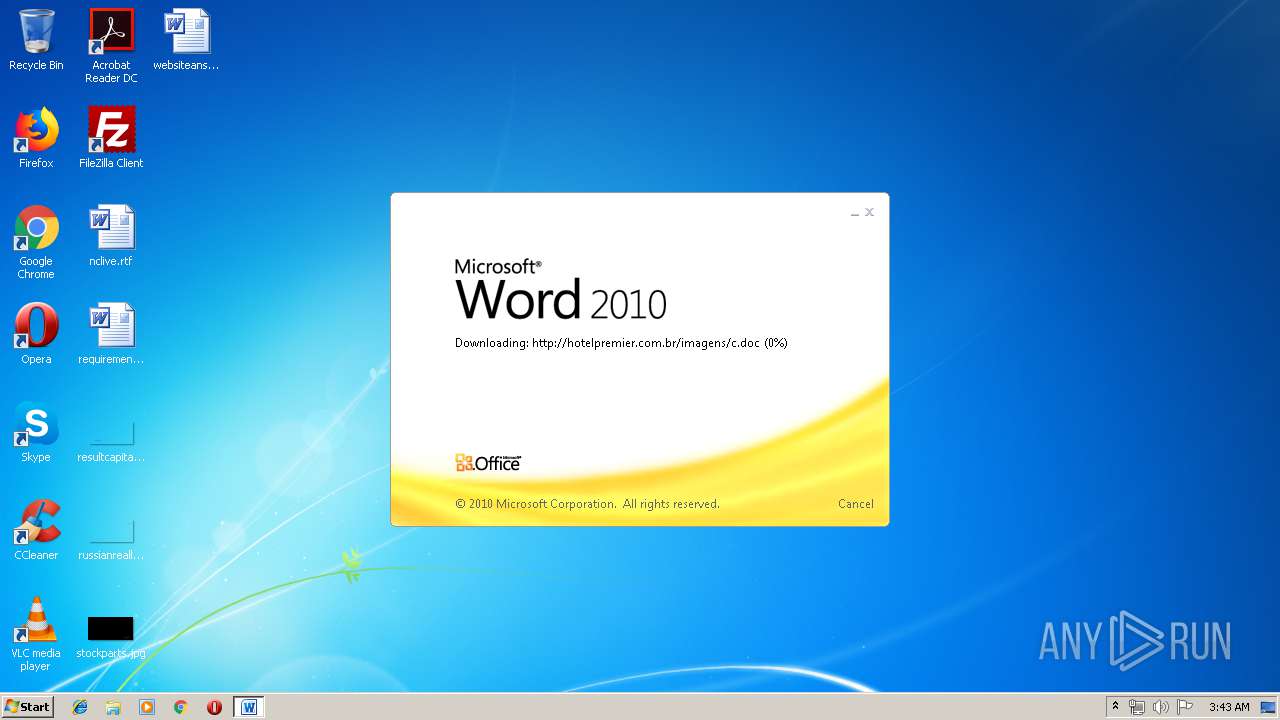
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
712 | WINWORD.EXE | OPTIONS | 200 | 191.252.51.35:80 | http://hotelpremier.com.br/imagens/ | BR | — | — | malicious |
712 | WINWORD.EXE | HEAD | 200 | 191.252.51.35:80 | http://hotelpremier.com.br/imagens/a.doc | BR | — | — | malicious |
712 | WINWORD.EXE | HEAD | 200 | 191.252.51.35:80 | http://hotelpremier.com.br/imagens/a.doc | BR | — | — | malicious |
712 | WINWORD.EXE | HEAD | 200 | 191.252.51.35:80 | http://hotelpremier.com.br/imagens/a.doc | BR | — | — | malicious |
712 | WINWORD.EXE | HEAD | 200 | 191.252.51.35:80 | http://hotelpremier.com.br/imagens/a.doc | BR | — | — | malicious |
712 | WINWORD.EXE | GET | 304 | 191.252.51.35:80 | http://hotelpremier.com.br/imagens/a.doc | BR | — | — | malicious |
712 | WINWORD.EXE | HEAD | 200 | 191.252.51.35:80 | http://hotelpremier.com.br/imagens/a.doc | BR | — | — | malicious |
984 | svchost.exe | PROPFIND | 405 | 191.252.51.35:80 | http://hotelpremier.com.br/imagens/ | BR | xml | 969 b | malicious |
984 | svchost.exe | OPTIONS | 200 | 191.252.51.35:80 | http://hotelpremier.com.br/imagens/ | BR | — | — | malicious |
984 | svchost.exe | PROPFIND | 405 | 191.252.51.35:80 | http://hotelpremier.com.br/imagens/ | BR | xml | 969 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
712 | WINWORD.EXE | 191.252.51.35:80 | hotelpremier.com.br | Locaweb Serviços de Internet S/A | BR | malicious |
984 | svchost.exe | 191.252.51.35:80 | hotelpremier.com.br | Locaweb Serviços de Internet S/A | BR | malicious |
— | — | 191.252.51.35:80 | hotelpremier.com.br | Locaweb Serviços de Internet S/A | BR | malicious |
4064 | amsi.dll | 104.20.209.21:443 | pastebin.com | Cloudflare Inc | US | shared |
4064 | amsi.dll | 168.197.229.117:70 | bylgay.hopto.org | GIGASAT SERVIÇOS DE PROCESSAMENTOS DE DADOS LTDA | BR | malicious |
4064 | amsi.dll | 79.134.225.20:70 | microsoftoutlook.duckdns.org | Andreas Fink trading as Fink Telecom Services | CH | malicious |
2212 | EXCEL.EXE | 104.20.209.21:443 | pastebin.com | Cloudflare Inc | US | shared |
— | — | 168.197.229.117:70 | bylgay.hopto.org | GIGASAT SERVIÇOS DE PROCESSAMENTOS DE DADOS LTDA | BR | malicious |
2904 | EXCEL.EXE | 104.20.209.21:443 | pastebin.com | Cloudflare Inc | US | shared |
2432 | amsi.dll | 104.20.209.21:443 | pastebin.com | Cloudflare Inc | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
hotelpremier.com.br |
| malicious |
pastebin.com |
| malicious |
bylgay.hopto.org |
| malicious |
soucdtevoceumcuzao.duckdns.org |
| malicious |
microsoftoutlook.duckdns.org |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
712 | WINWORD.EXE | A Network Trojan was detected | MALWARE [PTsecurity] RTF CVE-2017-11882 Exploit |
712 | WINWORD.EXE | A Network Trojan was detected | MALWARE [PTsecurity] RTF CVE-2017-11882 Exploit |
712 | WINWORD.EXE | A Network Trojan was detected | MALWARE [PTsecurity] RTF CVE-2017-11882 Exploit |
712 | WINWORD.EXE | A Network Trojan was detected | MALWARE [PTsecurity] RTF CVE-2017-11882 Exploit |
1068 | svchost.exe | Misc activity | ET INFO DYNAMIC_DNS Query to *.duckdns. Domain |
1068 | svchost.exe | Misc activity | ET INFO DYNAMIC_DNS Query to *.duckdns. Domain |
712 | WINWORD.EXE | A Network Trojan was detected | MALWARE [PTsecurity] RTF CVE-2017-11882 Exploit |
712 | WINWORD.EXE | A Network Trojan was detected | MALWARE [PTsecurity] RTF CVE-2017-11882 Exploit |