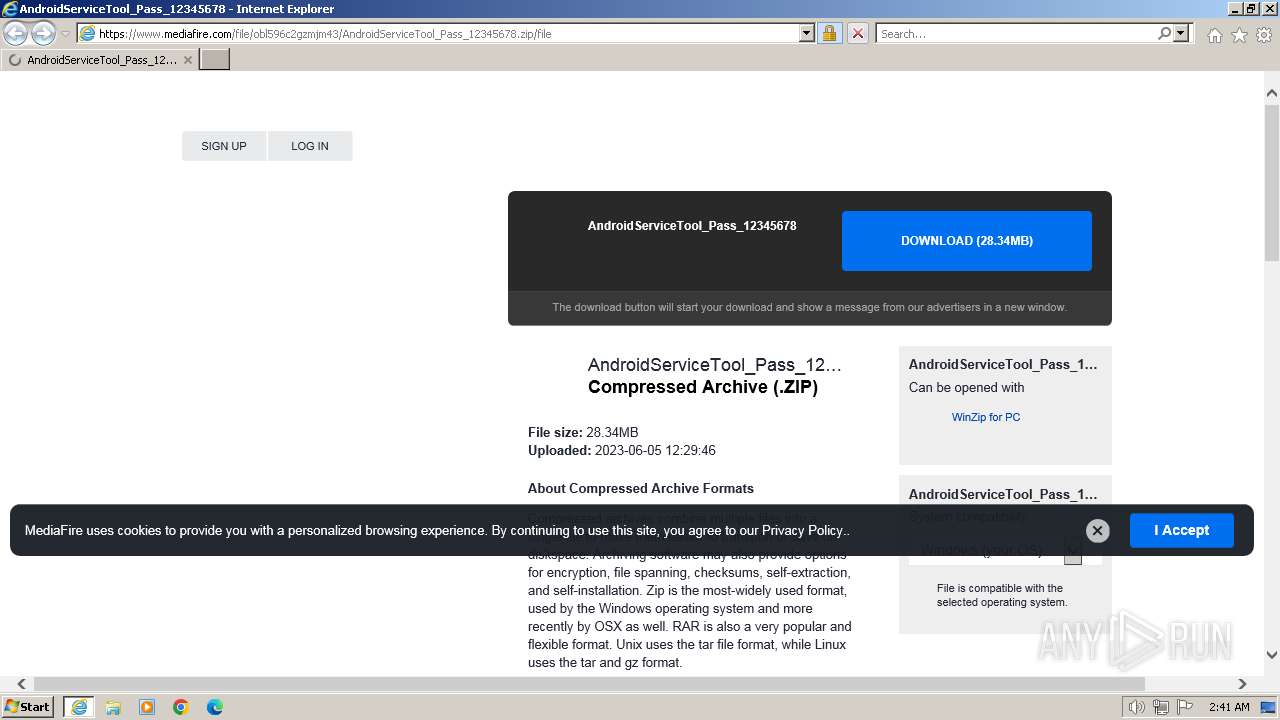
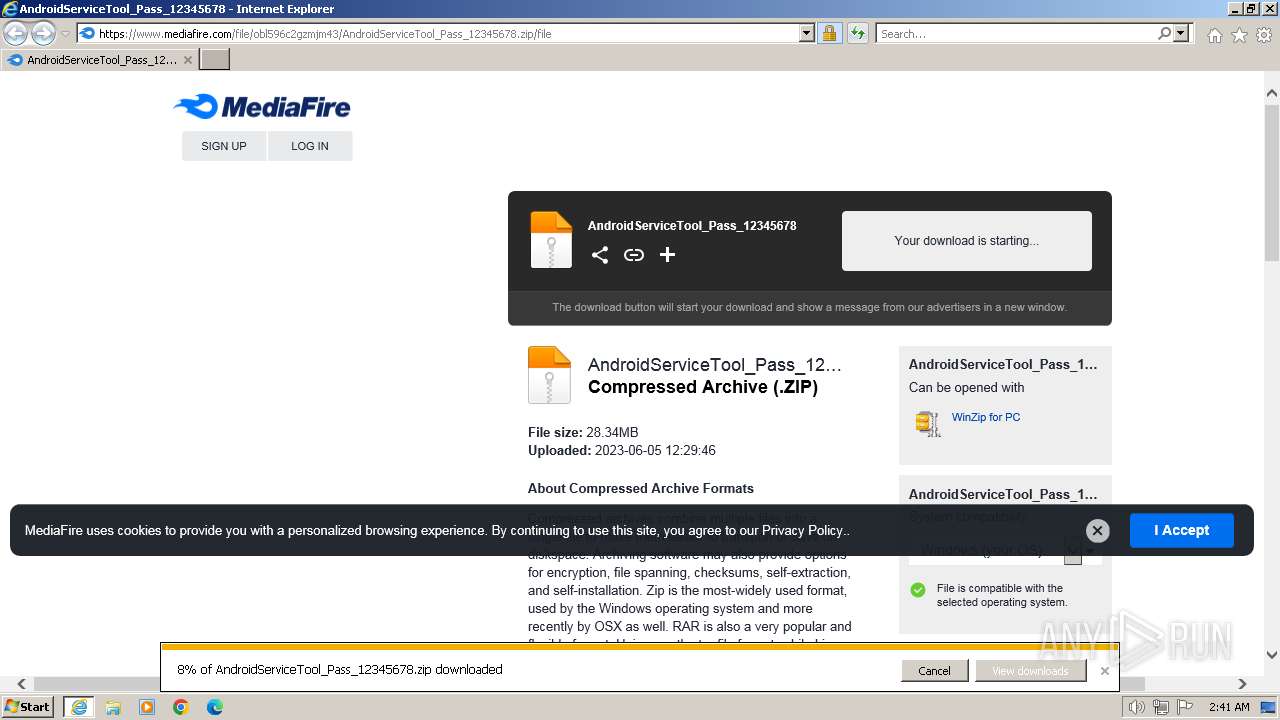
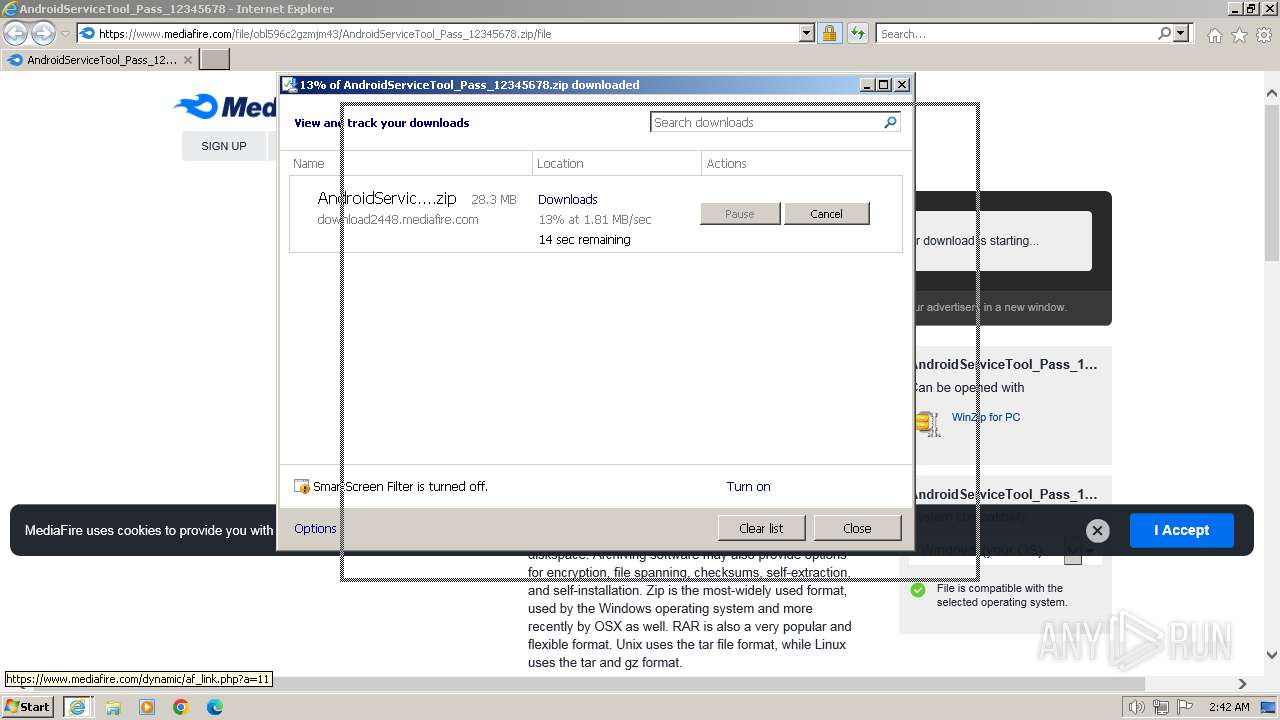
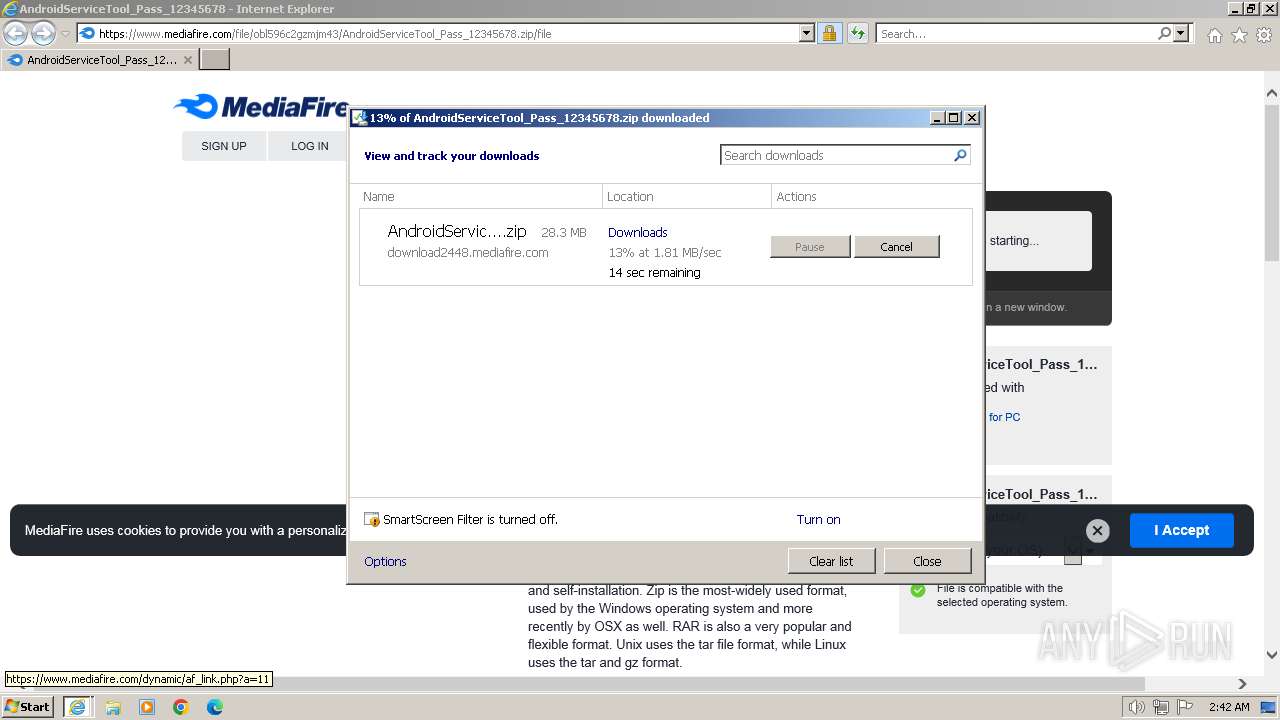
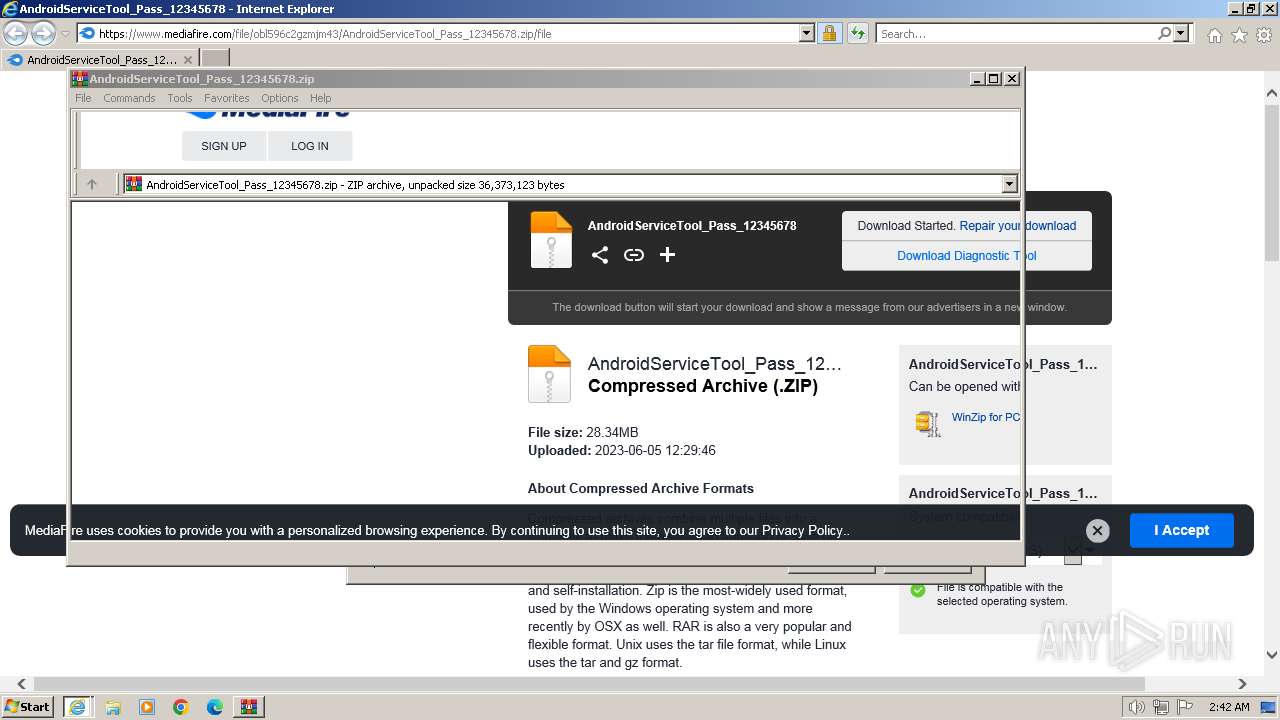
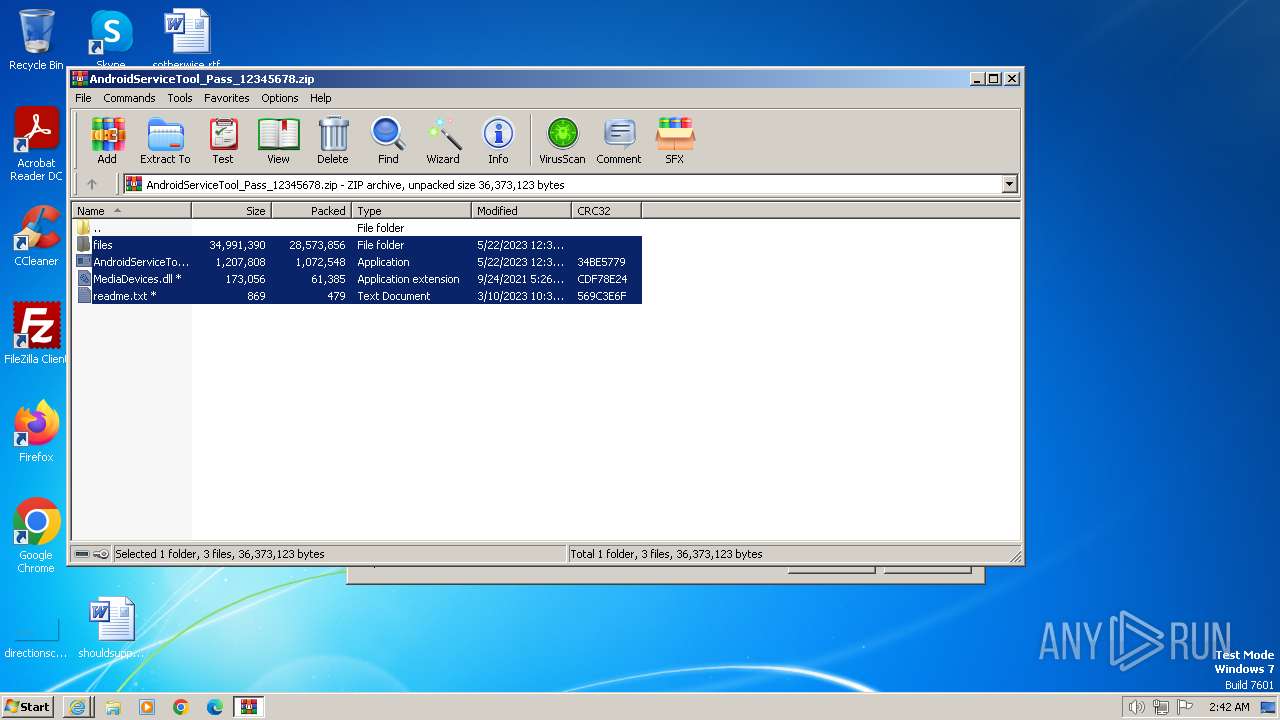
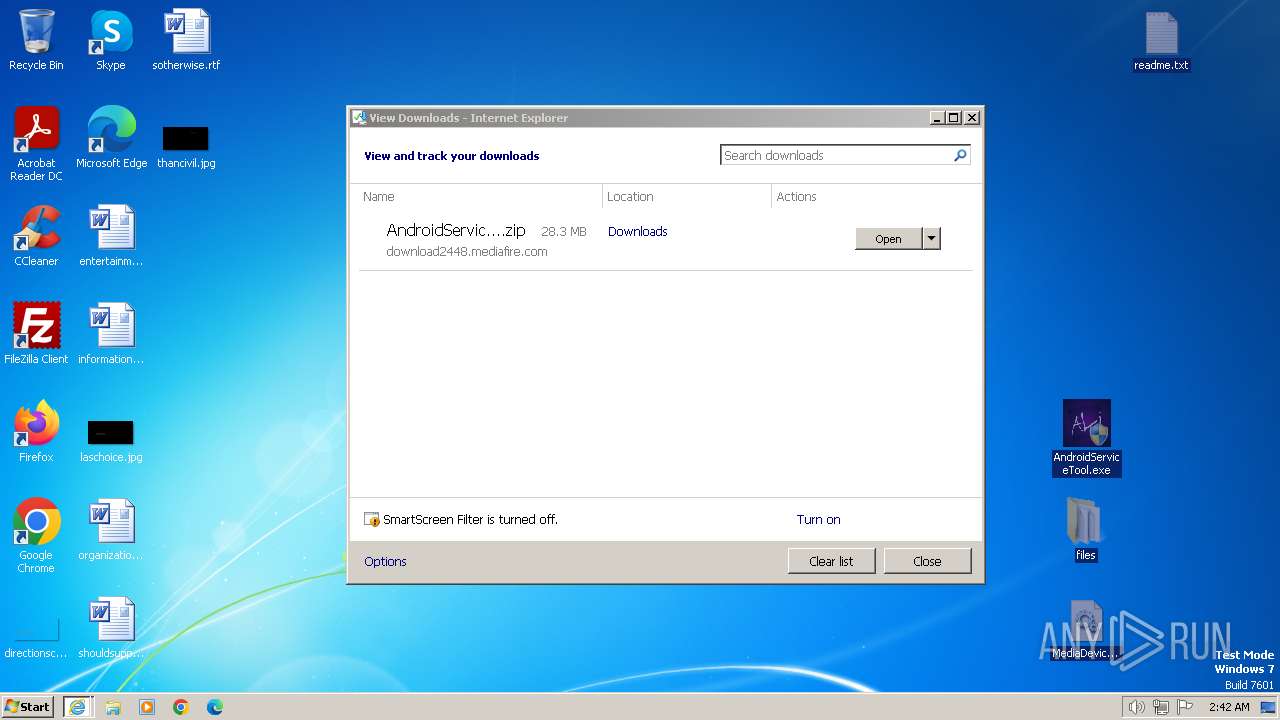
| URL: | https://www.mediafire.com/file/obl596c2gzmjm43/AndroidServiceTool_Pass_12345678.zip/file |
| Full analysis: | https://app.any.run/tasks/3841283a-a139-4b84-a9a1-32f72e460de1 |
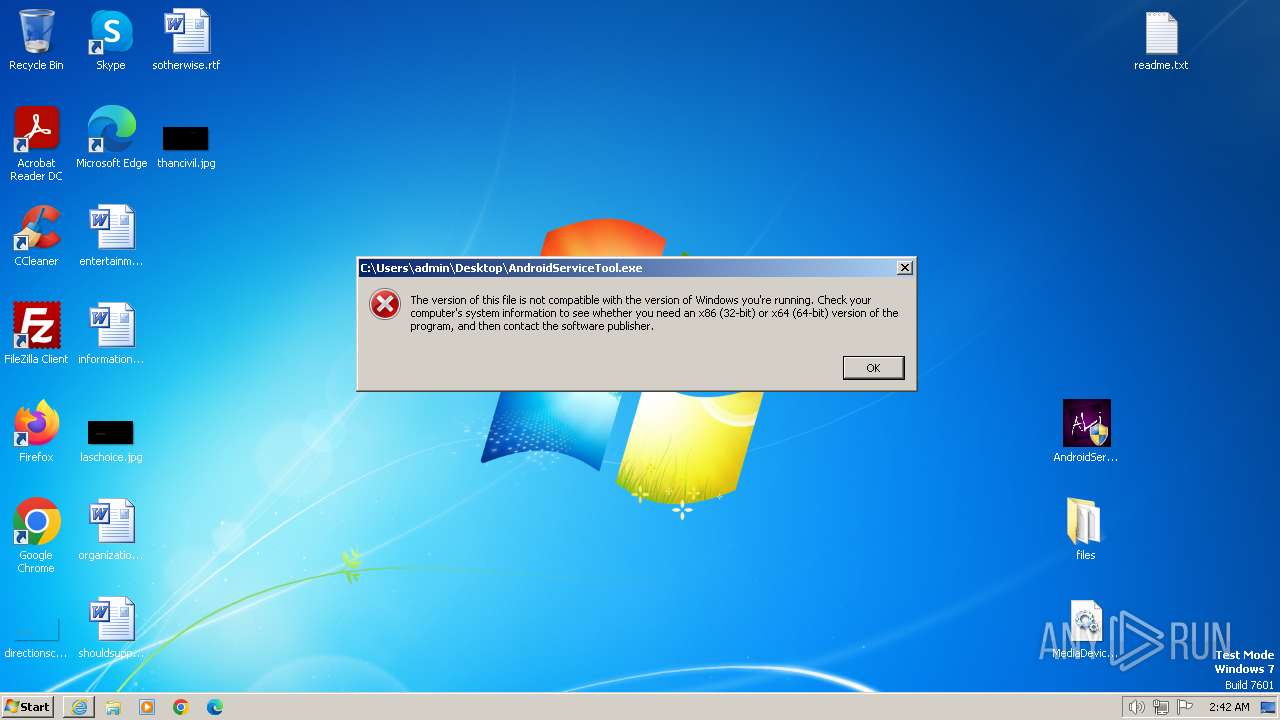
| Verdict: | Malicious activity |
| Analysis date: | February 22, 2024, 02:41:36 |
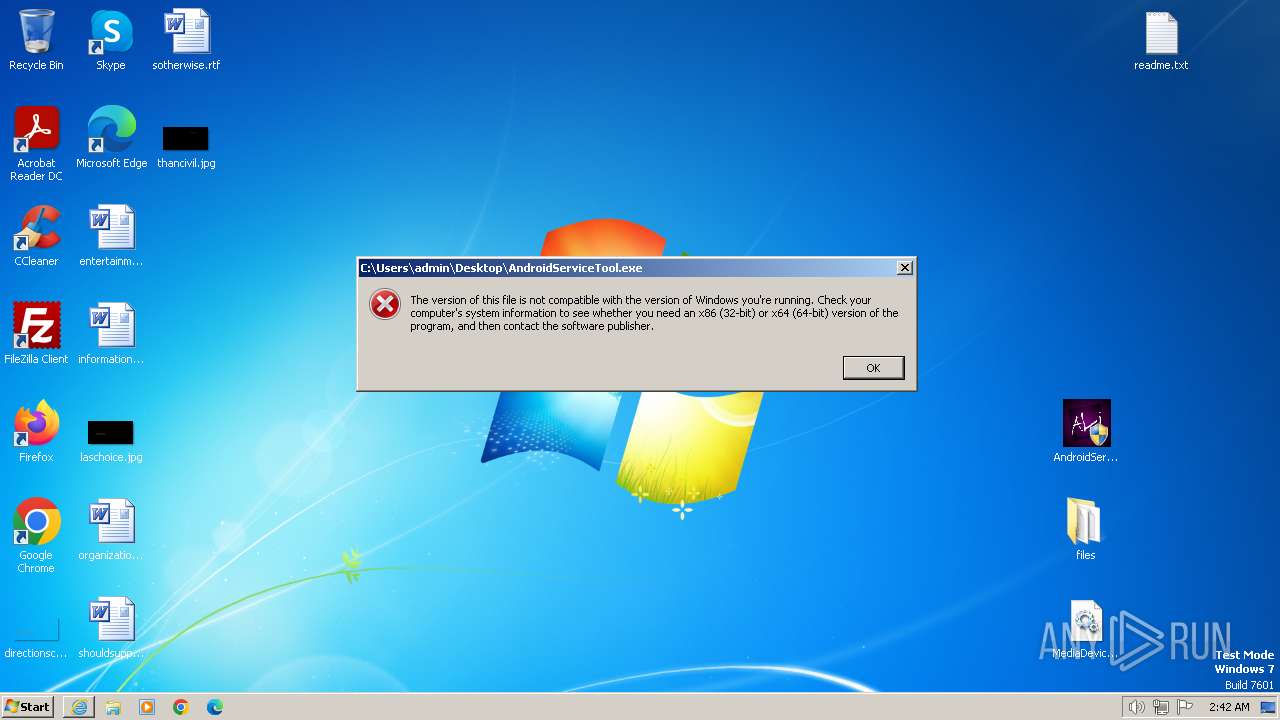
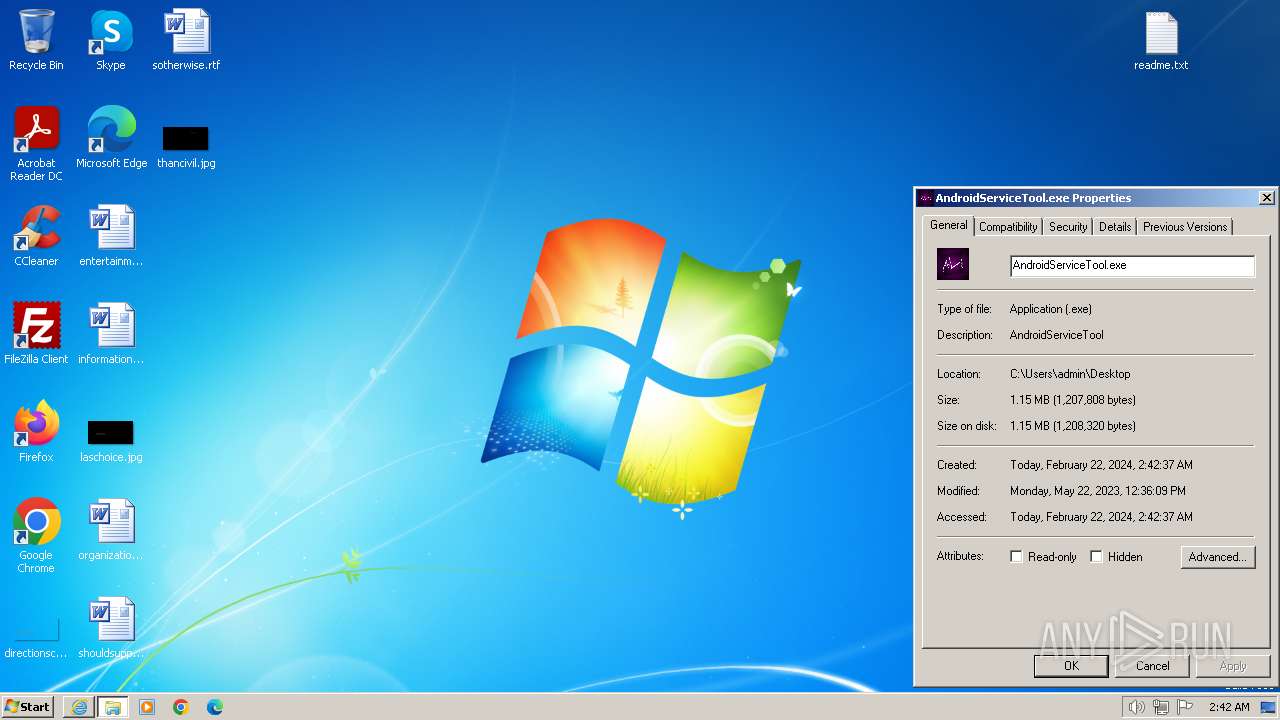
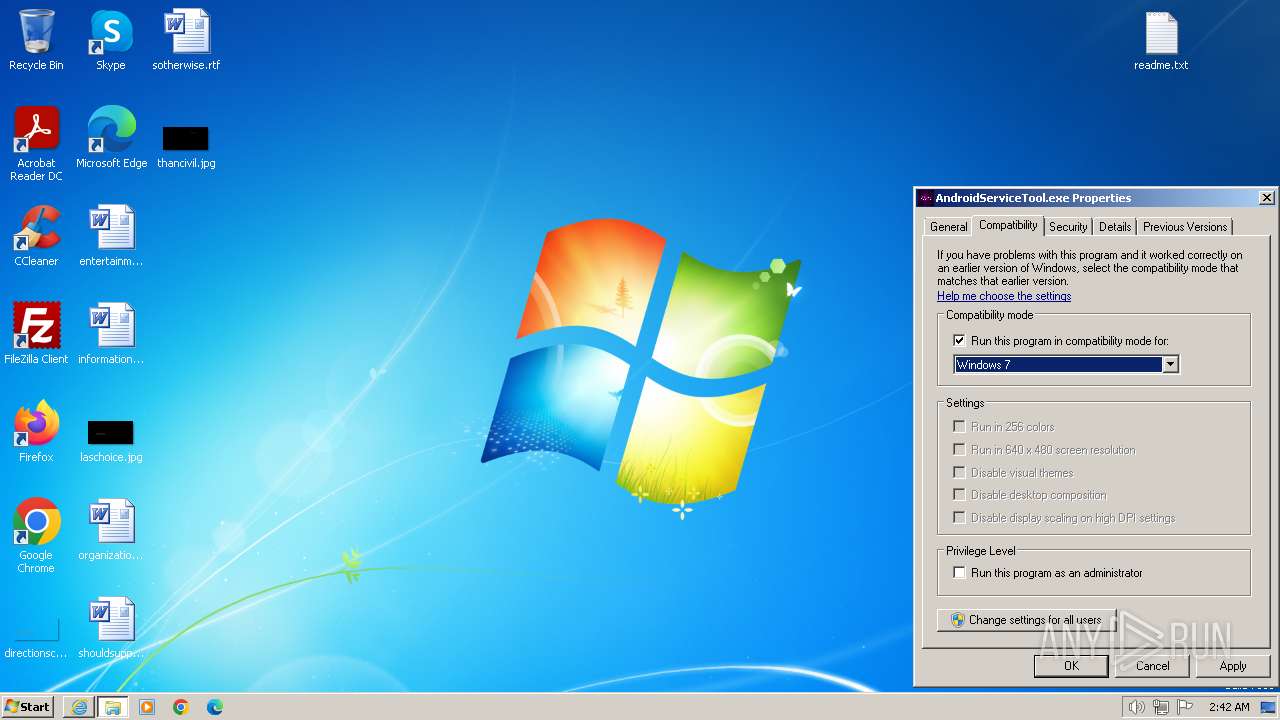
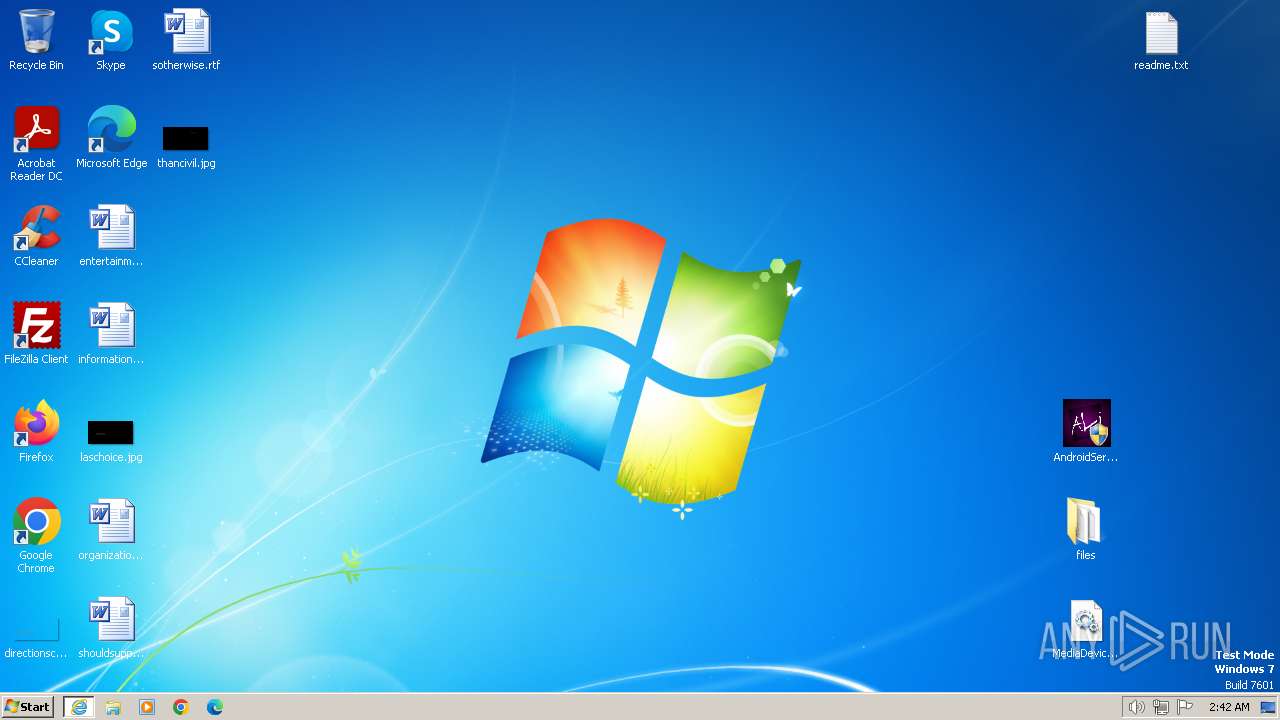
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 13CE3E4C213CEF50484B960D2CD8B815 |
| SHA1: | 319AA483F6B456AFEB63869FE38EF15AEE6E7882 |
| SHA256: | AAAD185C0C23CC8107C59B37766C3EAA7D7D2B83A18FF1F8D726F0CC4997AAC4 |
| SSDEEP: | 3:N8DSLw3eGUodlewDBN9OWr1:2OLw3eGpUwDBNwWR |
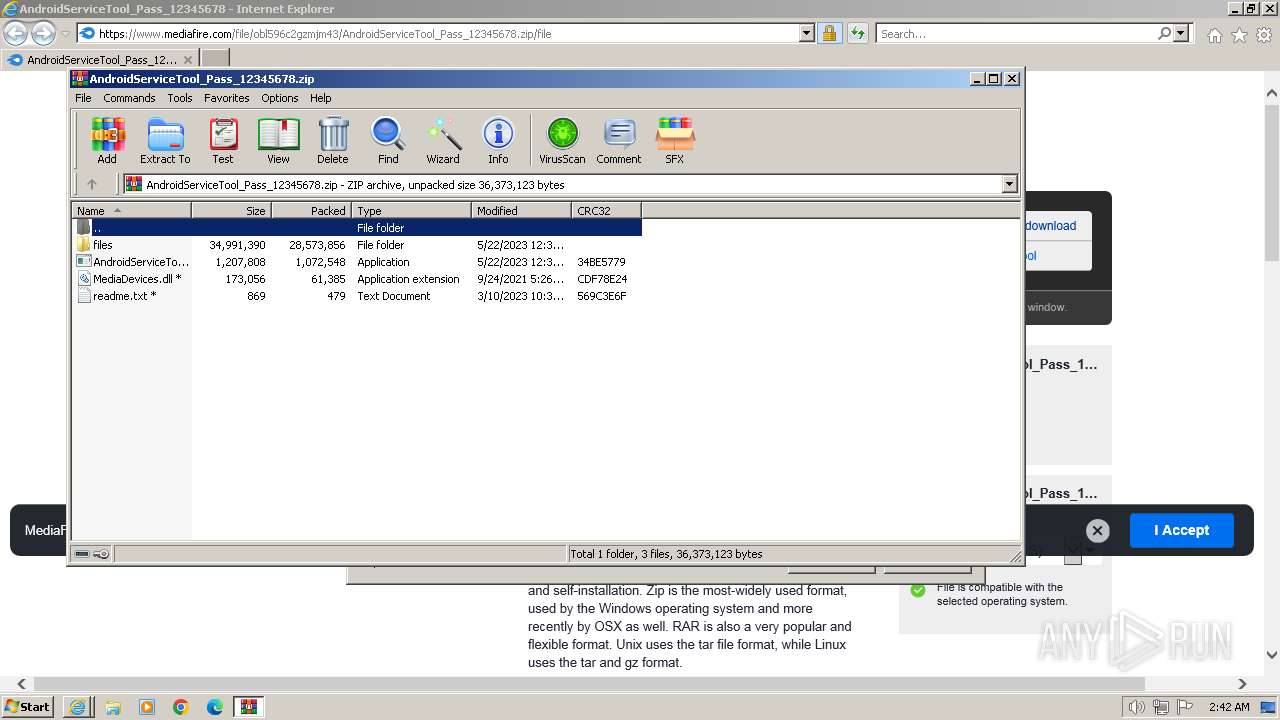
MALICIOUS
Detects Cygwin installation
- WinRAR.exe (PID: 3912)
SUSPICIOUS
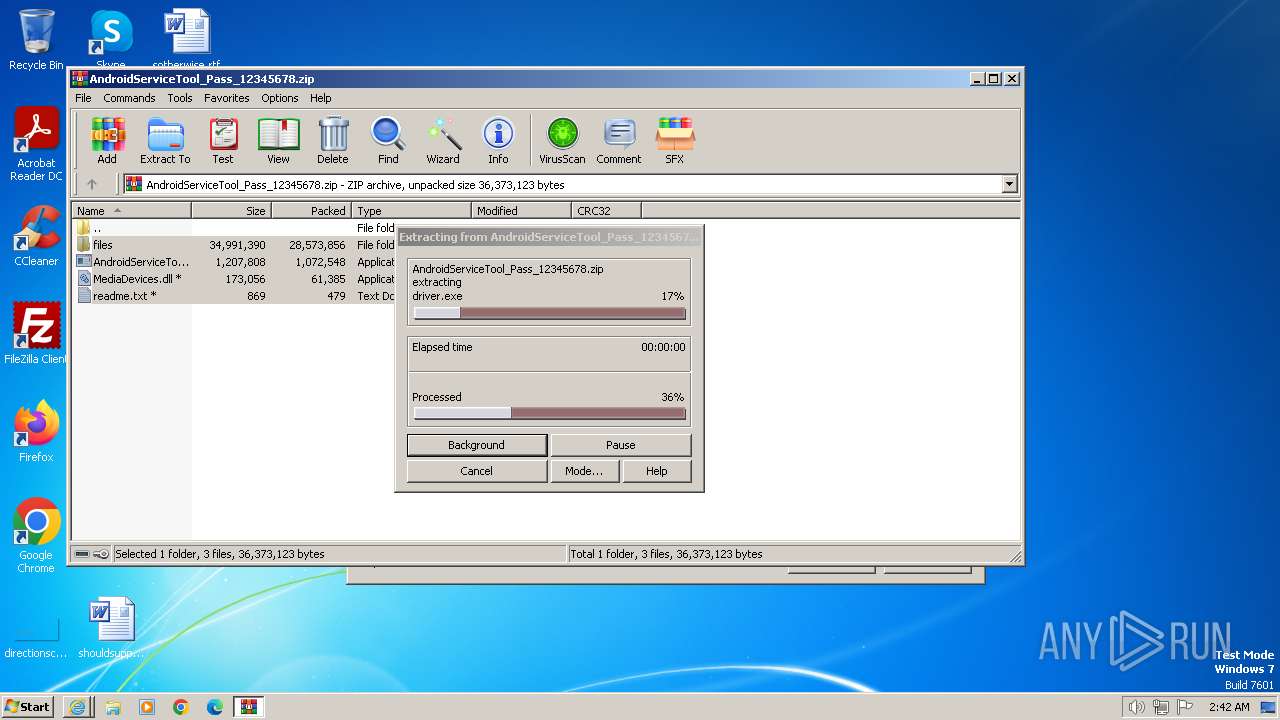
Process drops legitimate windows executable
- WinRAR.exe (PID: 3912)
Drops a system driver (possible attempt to evade defenses)
- WinRAR.exe (PID: 3912)
INFO
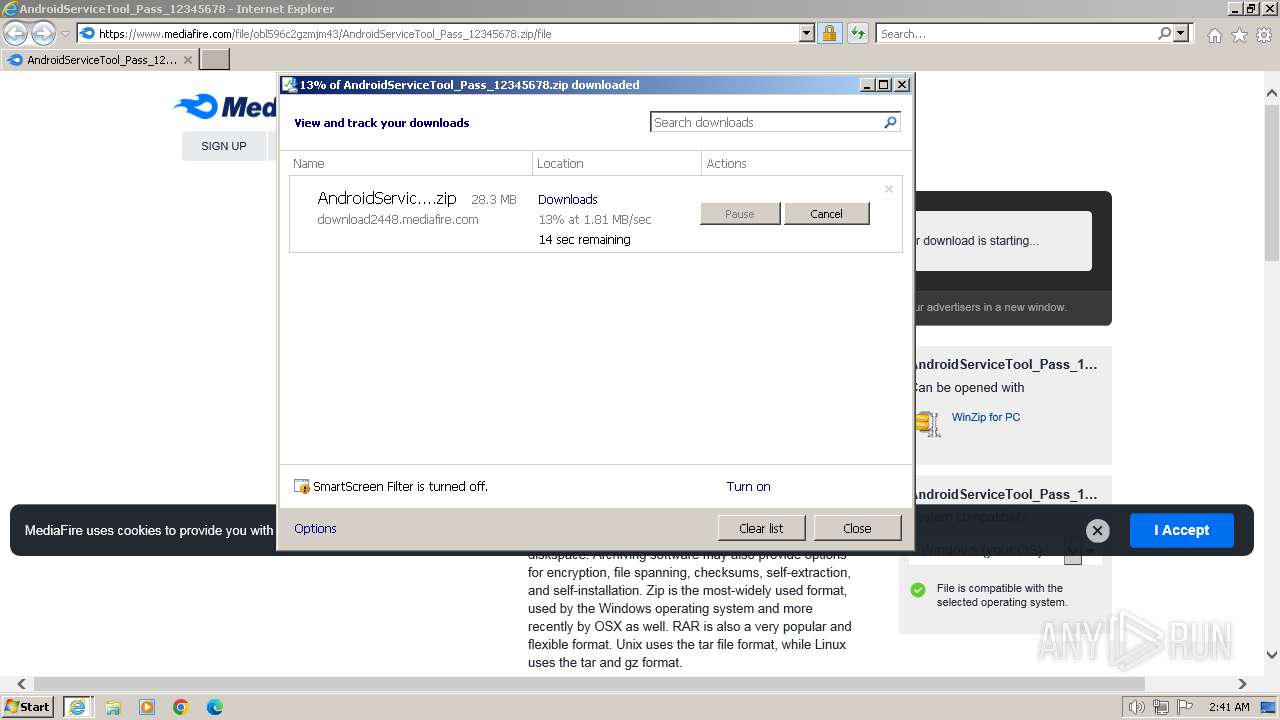
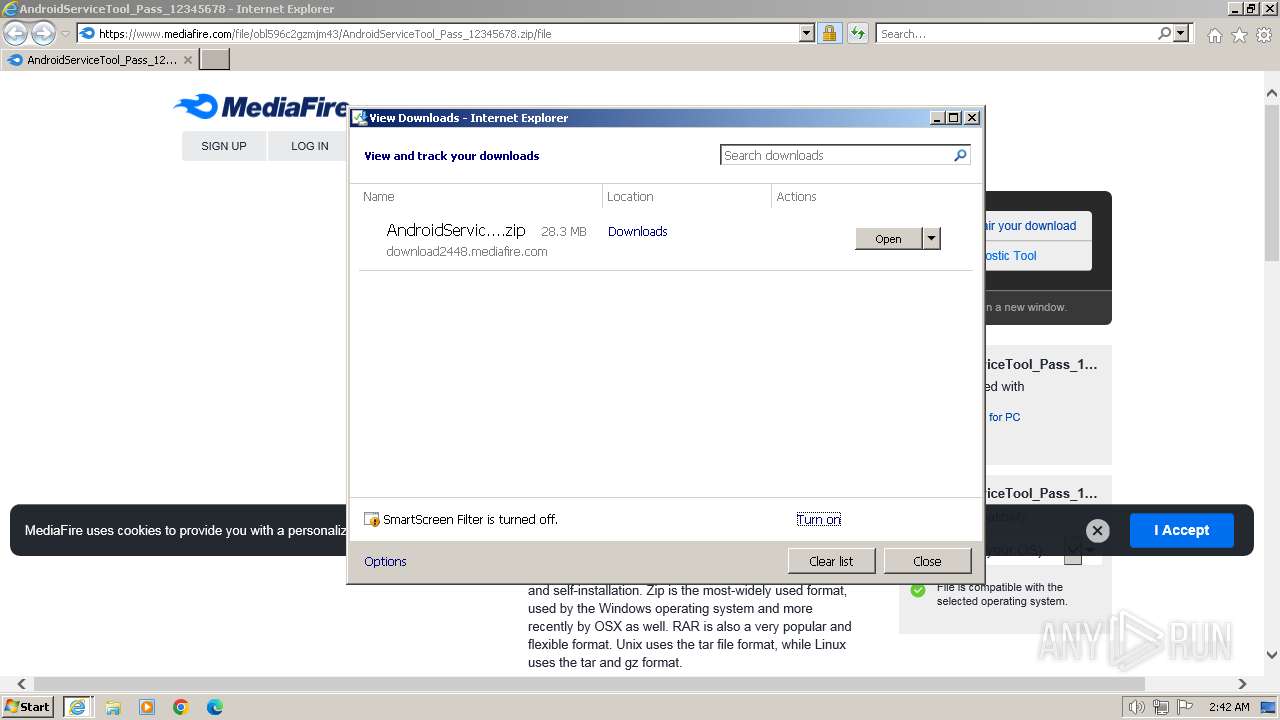
The process uses the downloaded file
- WinRAR.exe (PID: 3912)
- iexplore.exe (PID: 3656)
Modifies the phishing filter of IE
- iexplore.exe (PID: 3656)
Application launched itself
- iexplore.exe (PID: 3656)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3912)
Drops the executable file immediately after the start
- WinRAR.exe (PID: 3912)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
41
Monitored processes
3
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3656 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://www.mediafire.com/file/obl596c2gzmjm43/AndroidServiceTool_Pass_12345678.zip/file" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3720 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3656 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
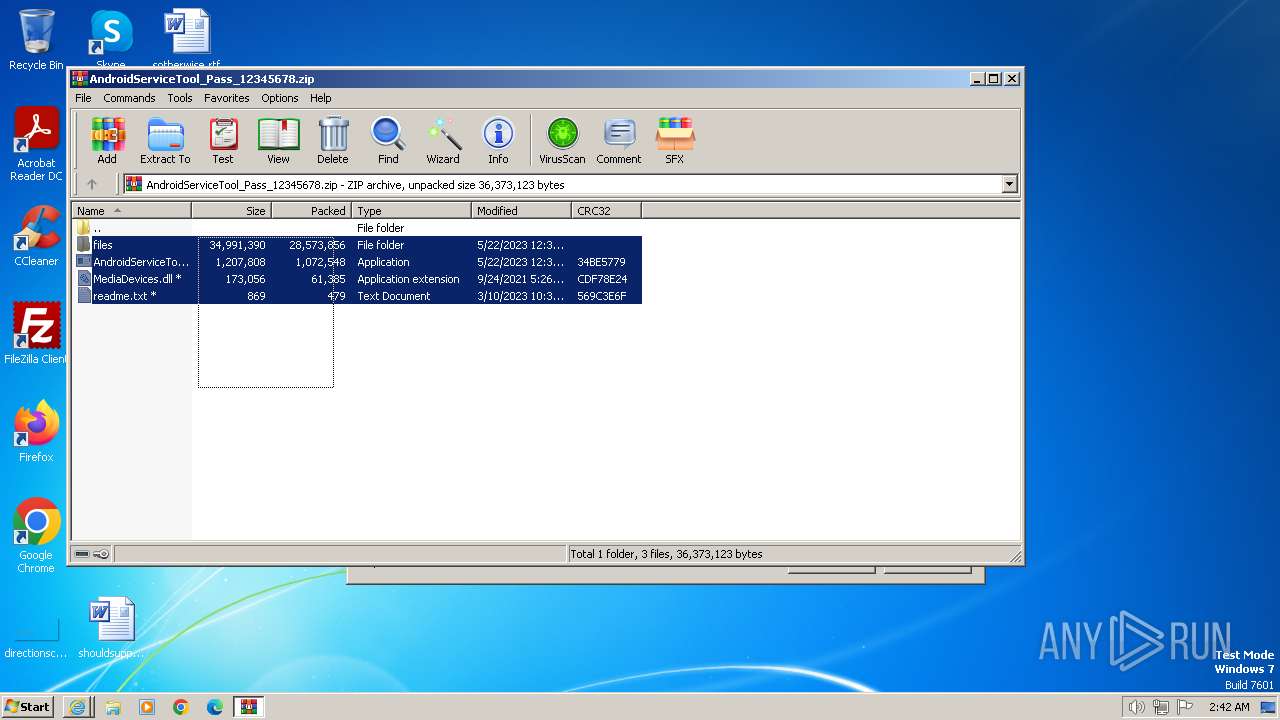
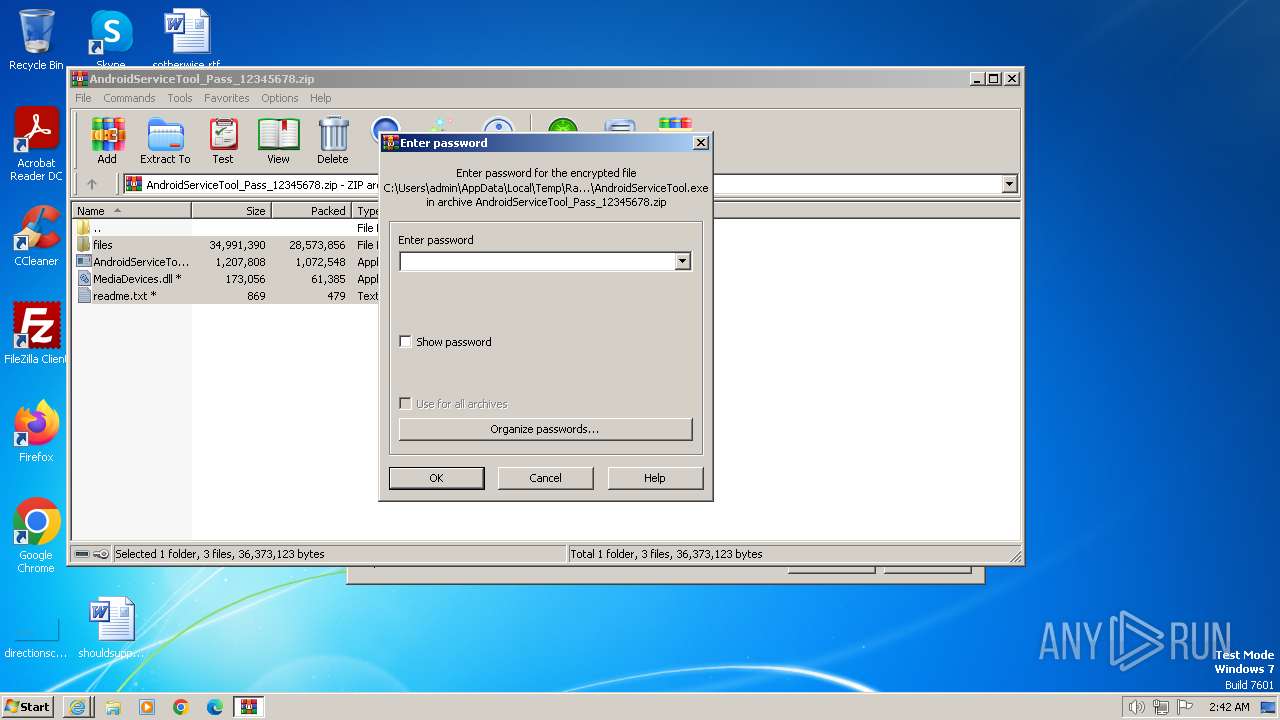
| 3912 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\AndroidServiceTool_Pass_12345678.zip" | C:\Program Files\WinRAR\WinRAR.exe | iexplore.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
Total events
31 814
Read events
31 616
Write events
144
Delete events
54
Modification events
| (PID) Process: | (3656) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (3656) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (3656) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 31089976 | |||
| (PID) Process: | (3656) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (3656) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 31089976 | |||
| (PID) Process: | (3656) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3656) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3656) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3656) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3656) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
29
Suspicious files
45
Text files
90
Unknown types
27
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3720 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\07CEF2F654E3ED6050FFC9B6EB844250_BACC6CD2B29F18349081C9FD2343833B | der | |
MD5:B8A3E9155F3CCE26002FC47B27AADF2D | SHA256:922D6D2E6F88DB3E1C365462302DD6509F95D48A0E28F4C59F496EE82AACF869 | |||
| 3720 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\cmp.min[1].js | text | |
MD5:FBE92038AA9B8D58FC93CFE47E2987AF | SHA256:66F8ECD359CCF9D79AE9C4AD10312DE1A65DB446344B2667E54D604F25D3165B | |||
| 3720 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\tag[1].js | text | |
MD5:9726D2BC333F1A55CE63058032C5D986 | SHA256:FD718DD42E580D653A987F9E848AC8C19F8C3751BA1DBF9AC2FC87922C9561E9 | |||
| 3720 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\v84a3a4012de94ce1a686ba8c167c359c1696973893317[1].js | text | |
MD5:DD1D068FDB5FE90B6C05A5B3940E088C | SHA256:6153D13804862B0FC1C016CF1129F34CB7C6185F2CF4BF1A3A862EECDAB50101 | |||
| 3720 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\BHEU5Y8V.txt | text | |
MD5:985CEB9629A0E881F64155B22D8AAC29 | SHA256:687AD2CDEF23A242F9C8A8B2F1C1114F87673B39E3446756C5FEFC36C6724959 | |||
| 3720 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | binary | |
MD5:CD5B701D6A821A8CCF2A72A794CB4E90 | SHA256:6EAA0B3D3D4117D4D793D53A50A13929B19FC4B669F0CE1C29CC2269B26E8BF2 | |||
| 3720 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\CAF4703619713E3F18D8A9D5D88D6288_F2DAF19C1F776537105D08FC8D978464 | binary | |
MD5:64BD049BEFEB3C23D584D2CE89C0E7C9 | SHA256:D49A3A94D284037E7A3963913CCEA499F5541CBEC45841AB8C6CB87C25DBDE94 | |||
| 3720 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\375RQGMT.txt | text | |
MD5:7A3E38FBF690D5E0F83907FD78162DAA | SHA256:98775841F2F875C45FD07965F52B5BC9A232ED4DF1FE37BF8A5A991A1E016298 | |||
| 3720 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\sa.min[1].js | text | |
MD5:2EA69735400D22316151EE8CAA049D79 | SHA256:A3445310C729D3F95CCAA8B2A90DCD483F5751AB02FC487FDE5137C575142436 | |||
| 3720 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\XTH45033.txt | text | |
MD5:21A9FC8C0DC1099315DDEC4A1D11F55F | SHA256:43FACBA0C9A0797D60AF63D97FAF5B6B2AAE56E71530CF6C6EB0010CC45D3E3A | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
39
TCP/UDP connections
89
DNS requests
45
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3720 | iexplore.exe | GET | 304 | 95.101.54.128:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?a08f35fbea17b647 | DE | — | — | unknown |
3720 | iexplore.exe | GET | 304 | 95.101.54.128:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?545e1839169dd0e6 | DE | — | — | unknown |
3720 | iexplore.exe | GET | 200 | 172.64.149.23:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEDlyRDr5IrdR19NsEN0xNZU%3D | US | binary | 1.42 Kb | unknown |
3720 | iexplore.exe | GET | 200 | 104.18.38.233:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEBN9U5yqfDGppDNwGWiEeo0%3D | unknown | binary | 2.18 Kb | unknown |
3720 | iexplore.exe | GET | 200 | 216.58.212.131:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFCjJ1PwkYAi7fE%3D | US | binary | 724 b | unknown |
3720 | iexplore.exe | GET | 200 | 216.58.212.131:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | US | binary | 1.41 Kb | unknown |
3720 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | binary | 1.47 Kb | unknown |
3720 | iexplore.exe | GET | 200 | 216.58.212.131:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | US | binary | 724 b | unknown |
3720 | iexplore.exe | GET | 200 | 216.58.212.131:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | US | binary | 724 b | unknown |
3720 | iexplore.exe | GET | 200 | 216.58.212.131:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | US | binary | 724 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
3720 | iexplore.exe | 104.16.113.74:443 | www.mediafire.com | CLOUDFLARENET | — | unknown |
3720 | iexplore.exe | 95.101.54.128:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
3720 | iexplore.exe | 172.64.149.23:80 | ocsp.comodoca.com | CLOUDFLARENET | US | unknown |
3720 | iexplore.exe | 104.18.38.233:80 | ocsp.comodoca.com | CLOUDFLARENET | — | shared |
3720 | iexplore.exe | 172.67.199.186:443 | the.gatekeeperconsent.com | CLOUDFLARENET | US | unknown |
3720 | iexplore.exe | 142.250.185.72:443 | www.googletagmanager.com | GOOGLE | US | unknown |
3720 | iexplore.exe | 172.67.41.60:443 | btloader.com | CLOUDFLARENET | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.mediafire.com |
| shared |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.comodoca.com |
| whitelisted |
ocsp.usertrust.com |
| whitelisted |
the.gatekeeperconsent.com |
| unknown |
www.googletagmanager.com |
| whitelisted |
btloader.com |
| whitelisted |
www.ezojs.com |
| unknown |
translate.google.com |
| whitelisted |
static.cloudflareinsights.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1080 | svchost.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
1080 | svchost.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain in DNS Lookup (download .mediafire .com) |