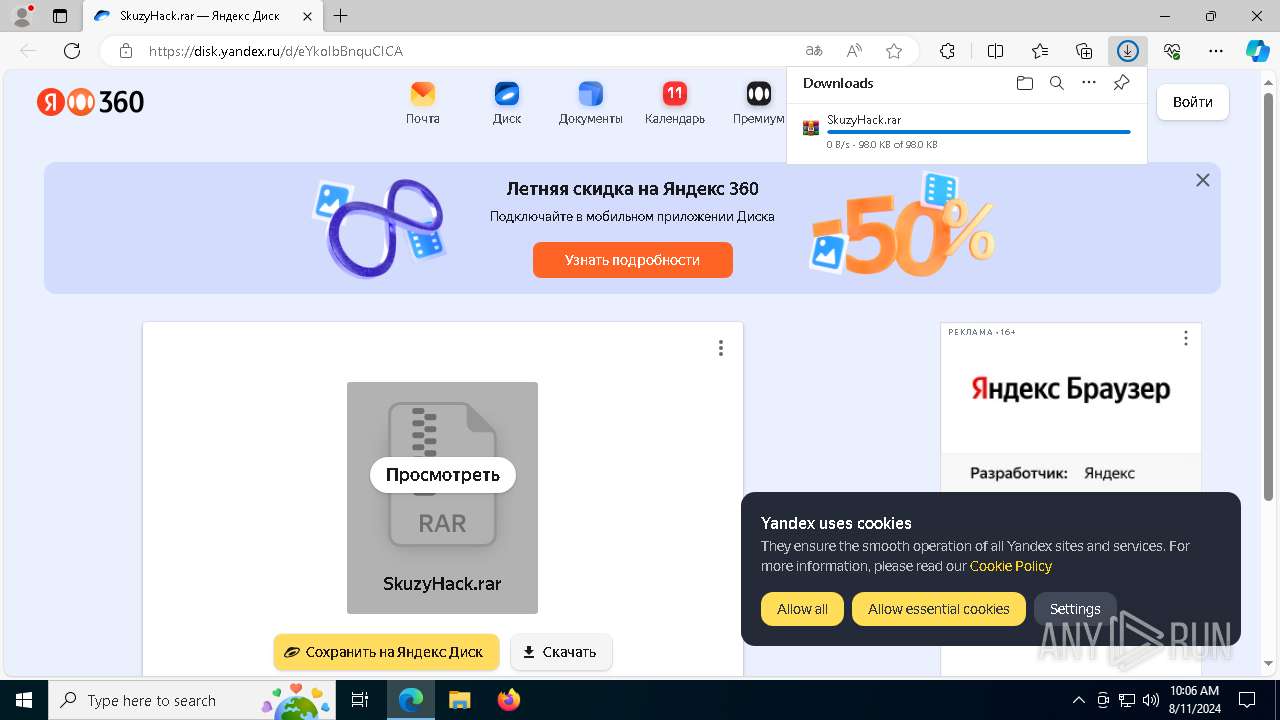
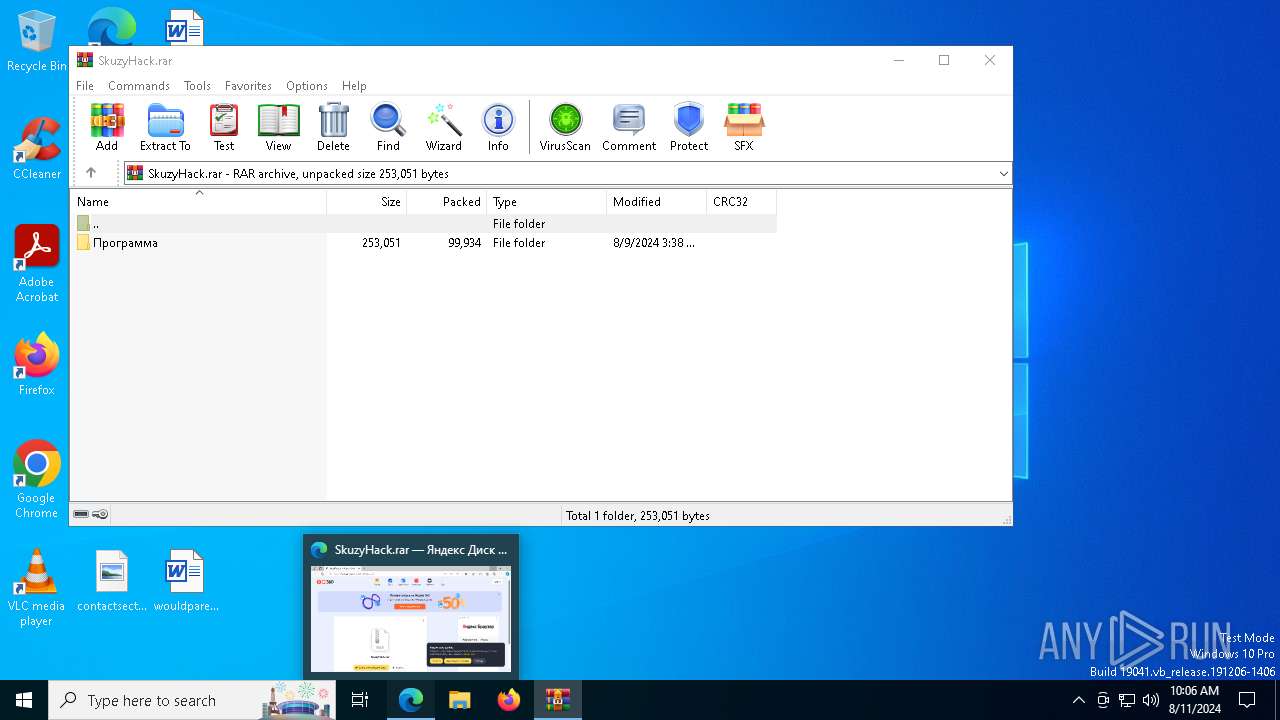
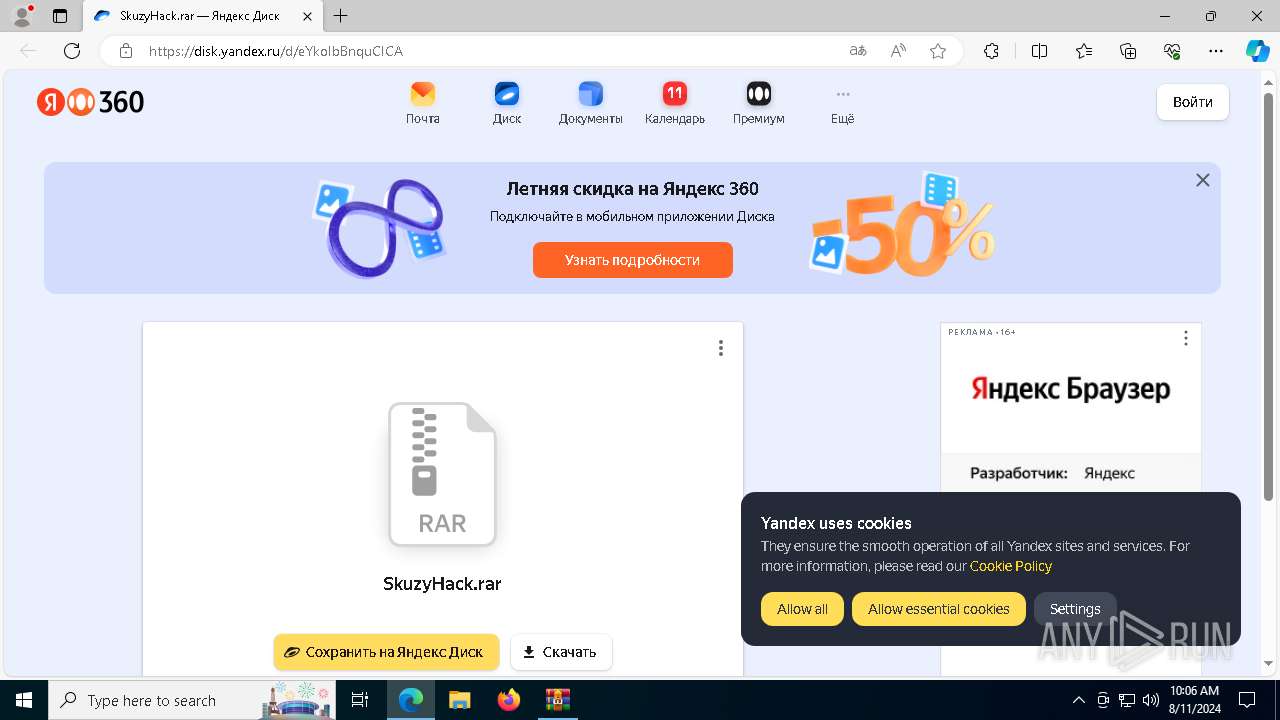
| URL: | https://disk.yandex.ru/d/eYkoIbBnquCICA |
| Full analysis: | https://app.any.run/tasks/fa878a60-75c5-41c5-8db0-0fee1ce42f0f |
| Verdict: | Malicious activity |
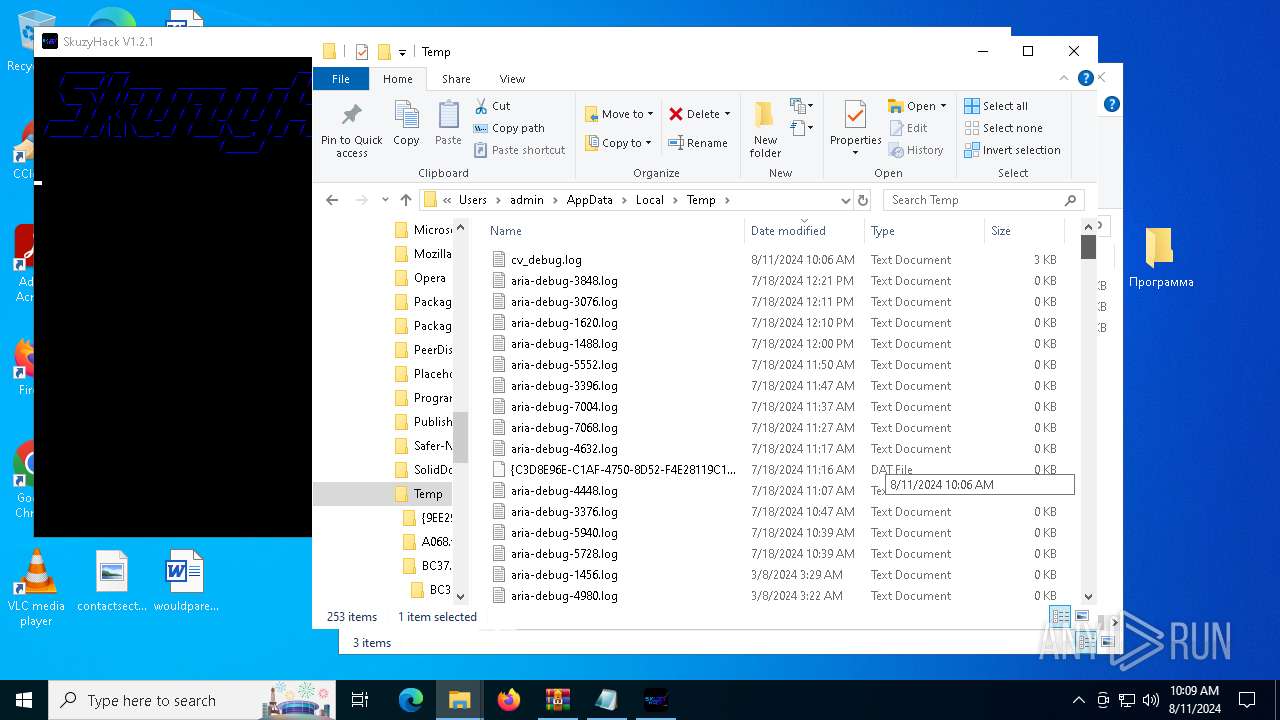
| Analysis date: | August 11, 2024, 10:06:32 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MD5: | BA25E59E131F3C5BA8788089CFD2062C |
| SHA1: | 941738A6FDFB2059CC4D409C93A0E3298BC269F6 |
| SHA256: | AAA8C02FE8D20229E4A0C478C124847408C5551C2EB26C0BBF05C356246EA163 |
| SSDEEP: | 3:N8U2Rf3rUzsmk:2U2RFmk |
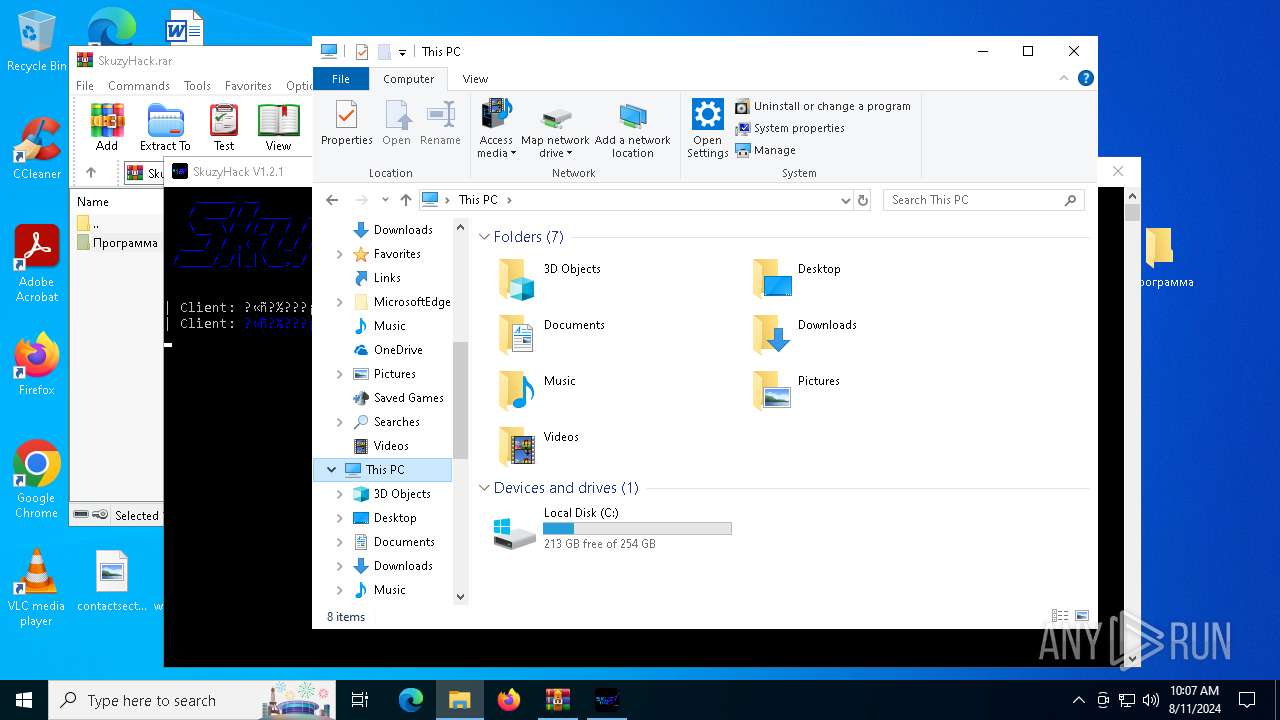
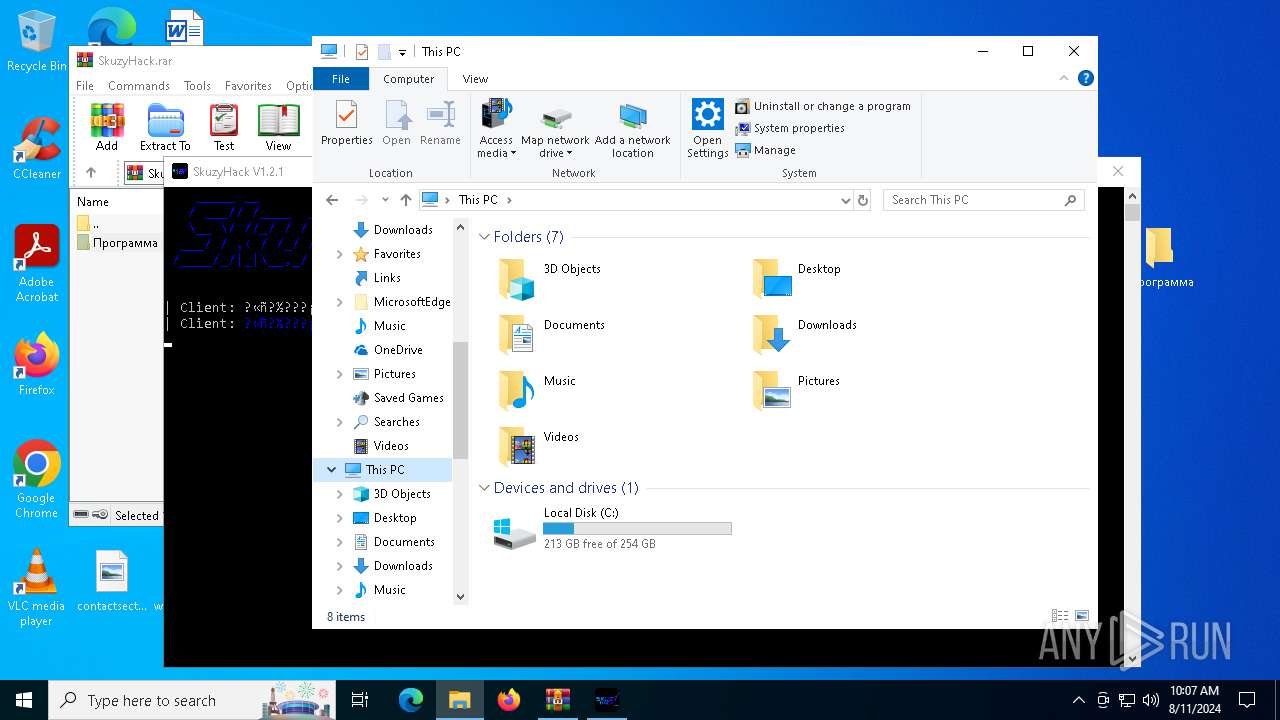
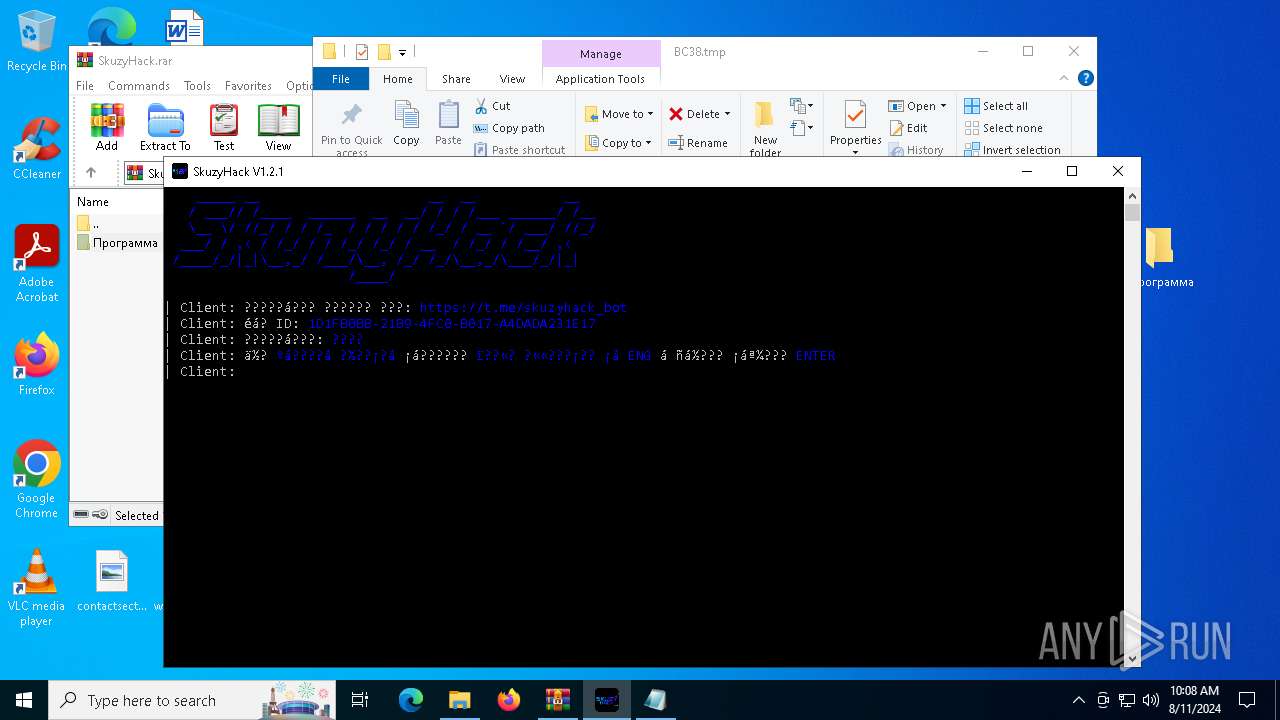
MALICIOUS
No malicious indicators.SUSPICIOUS
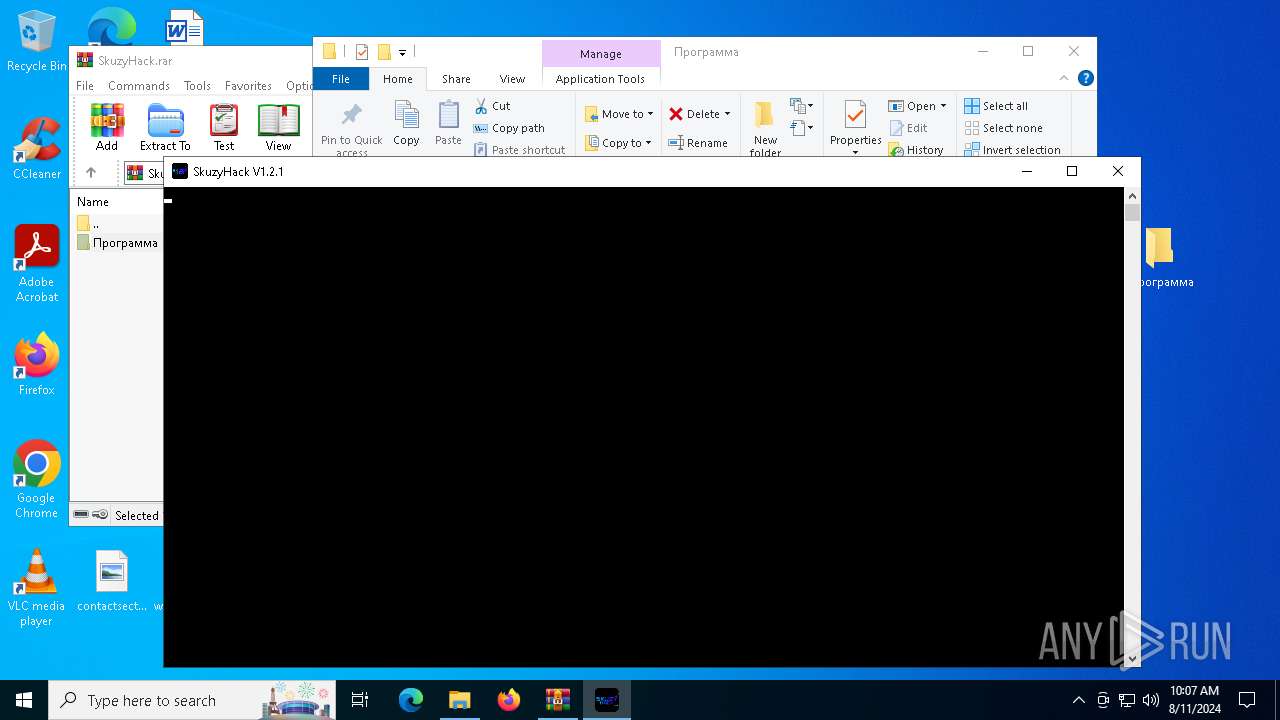
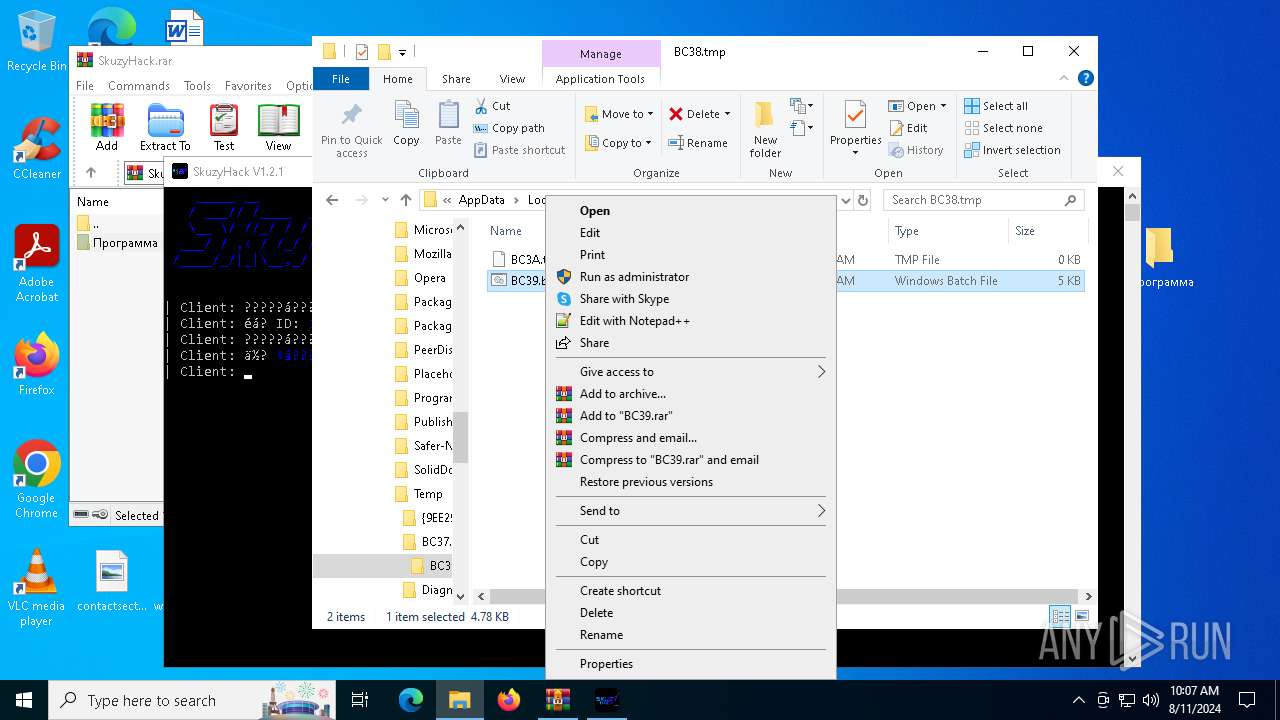
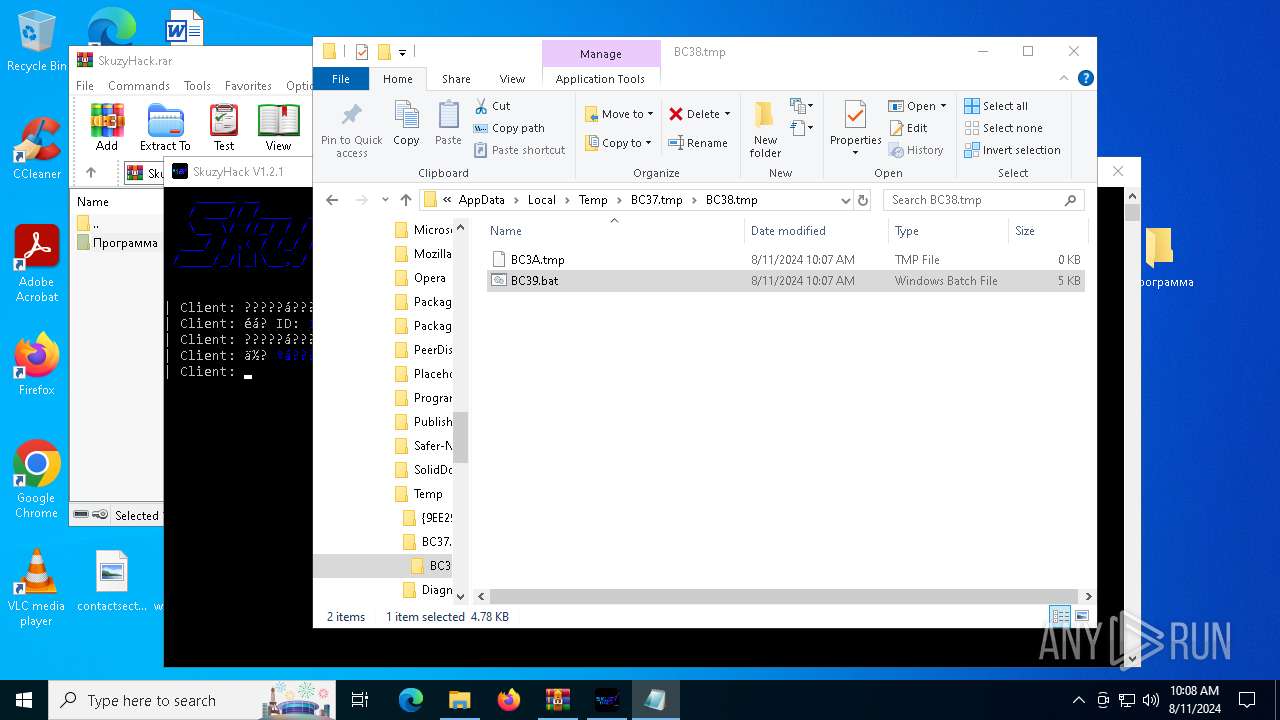
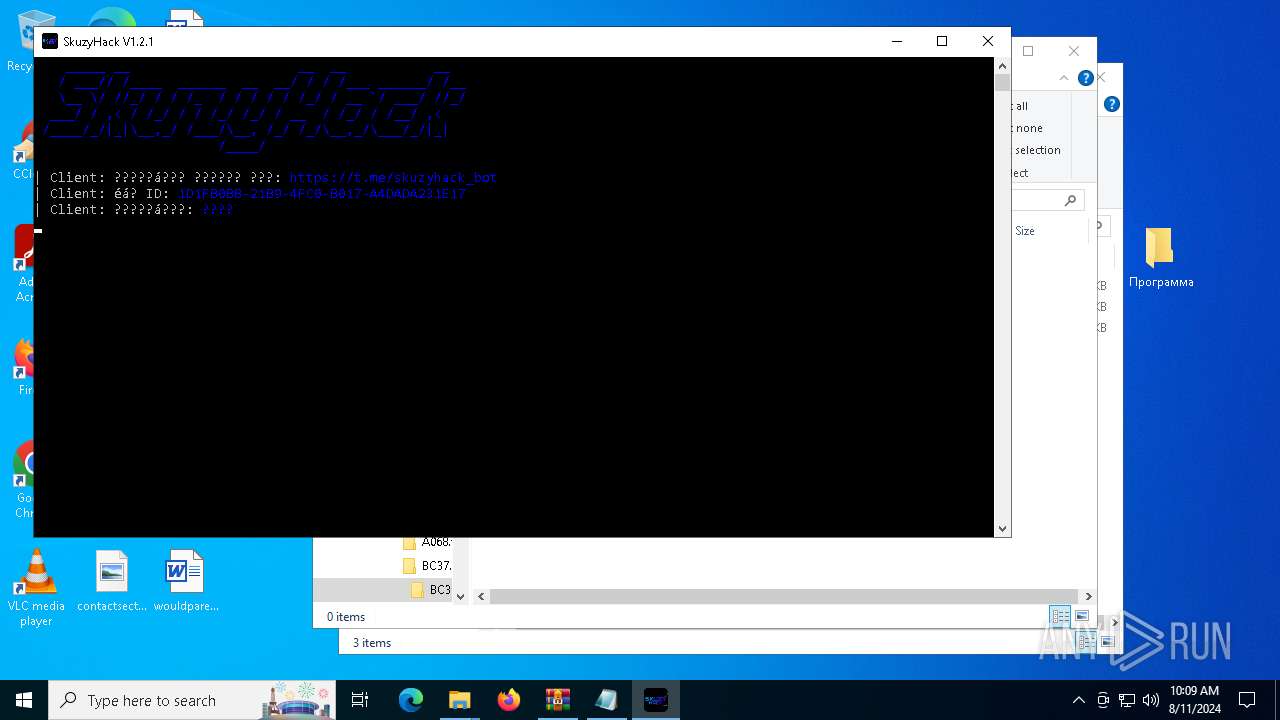
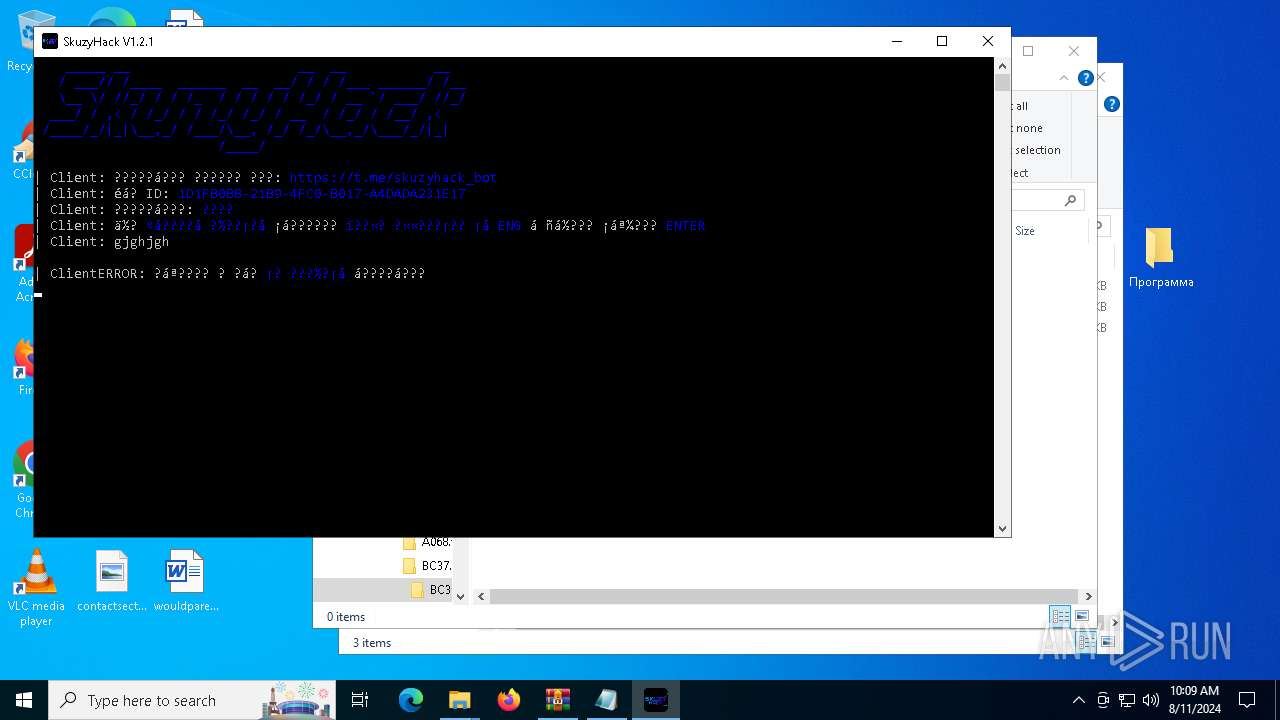
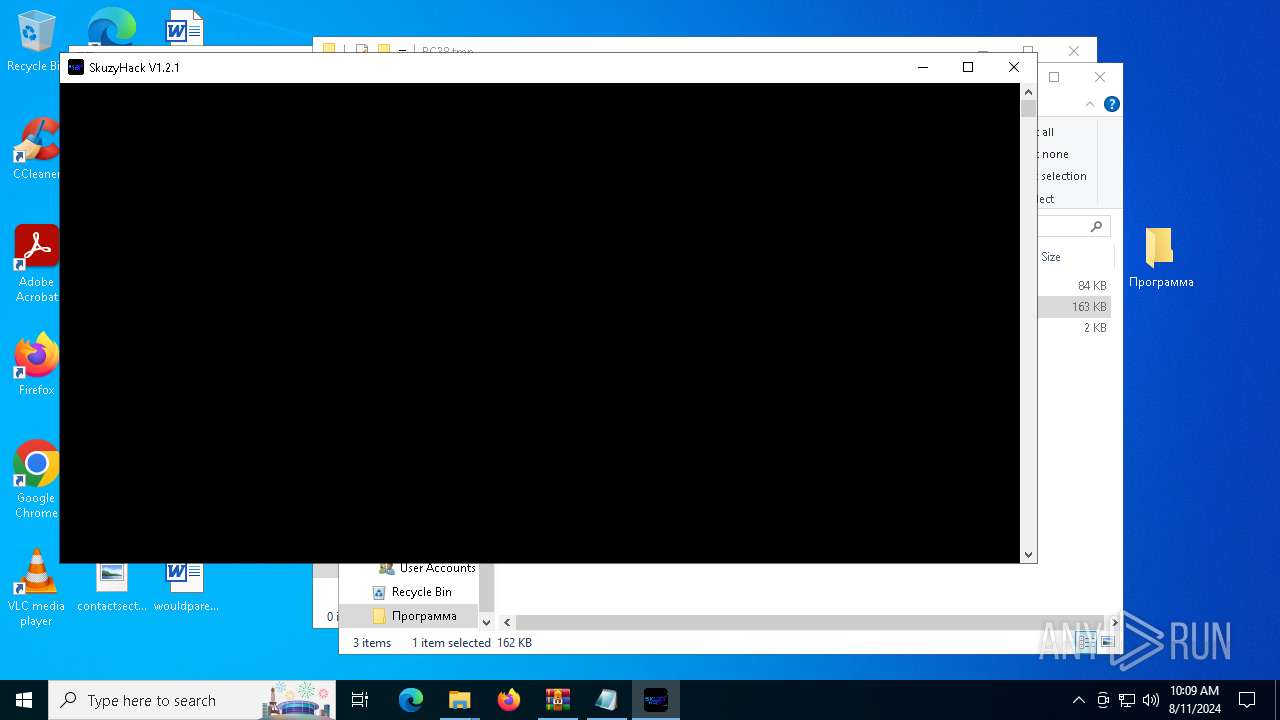
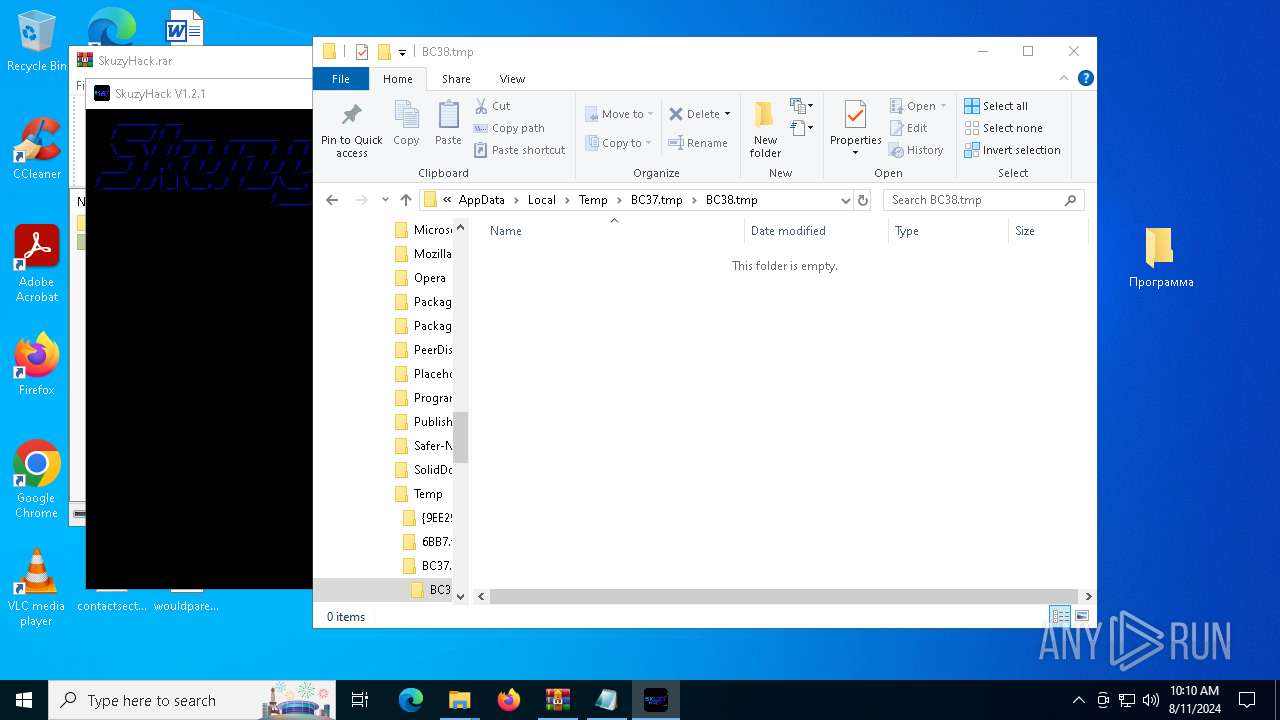
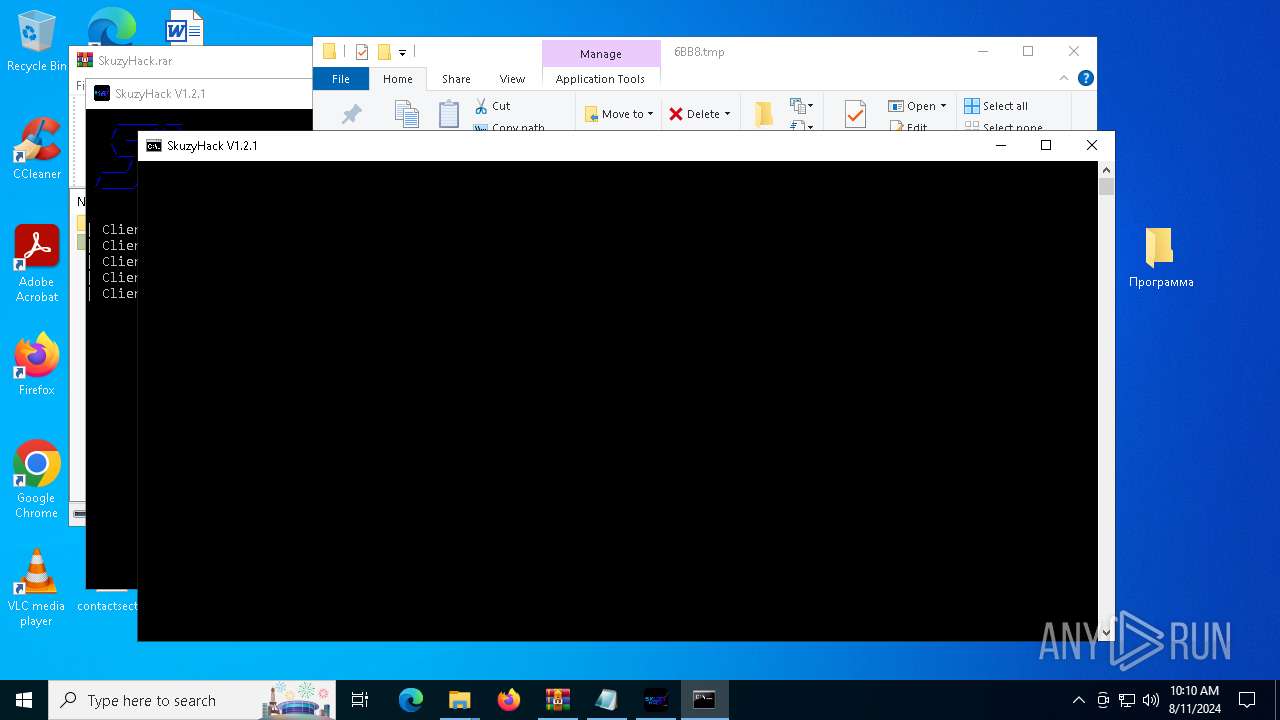
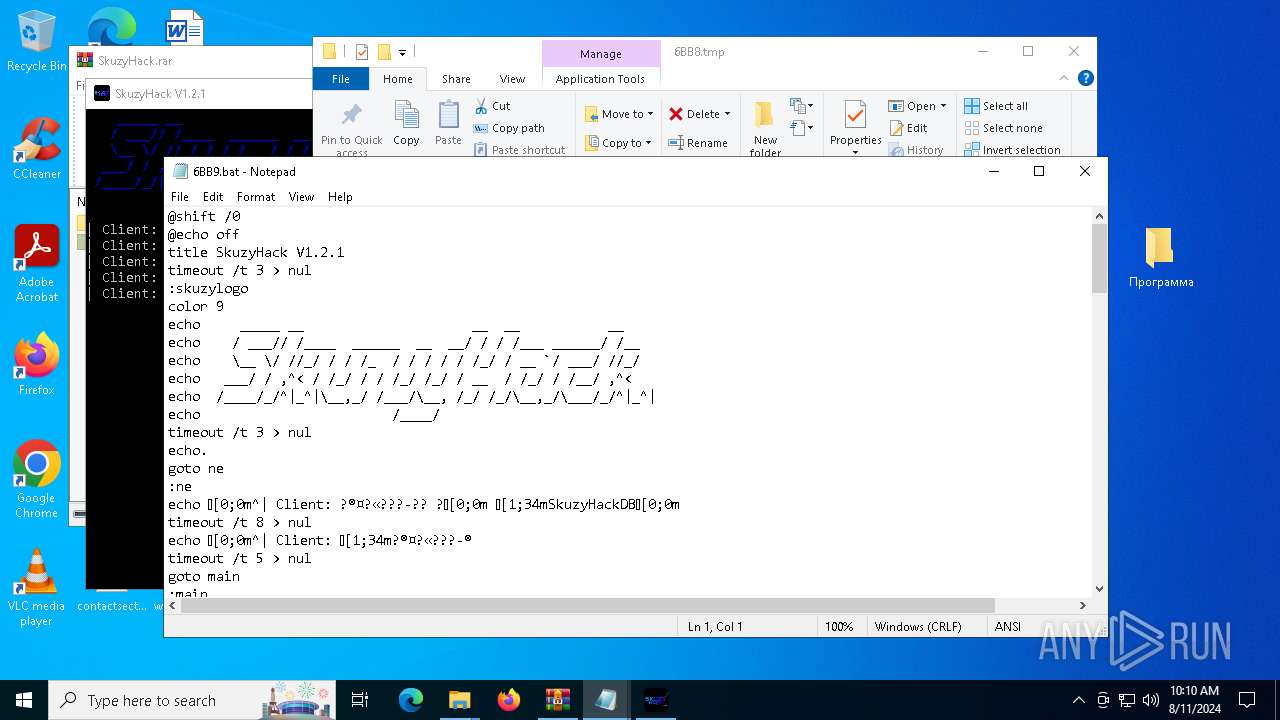
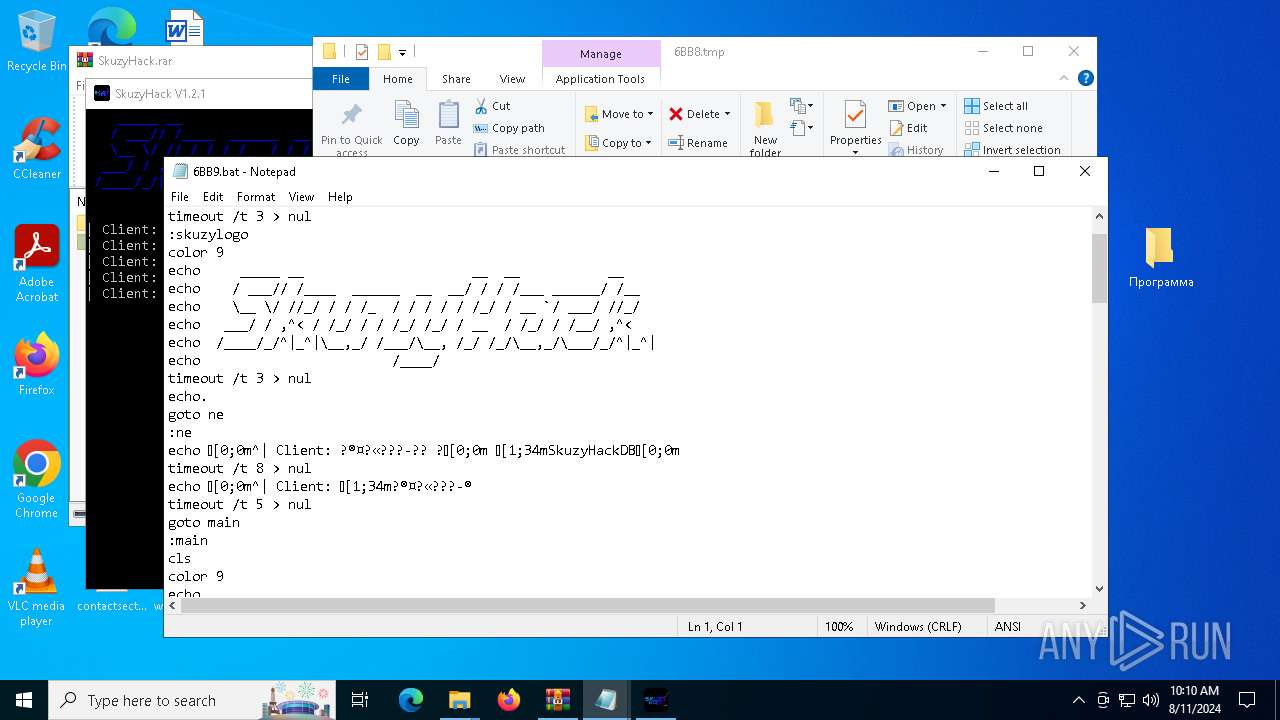
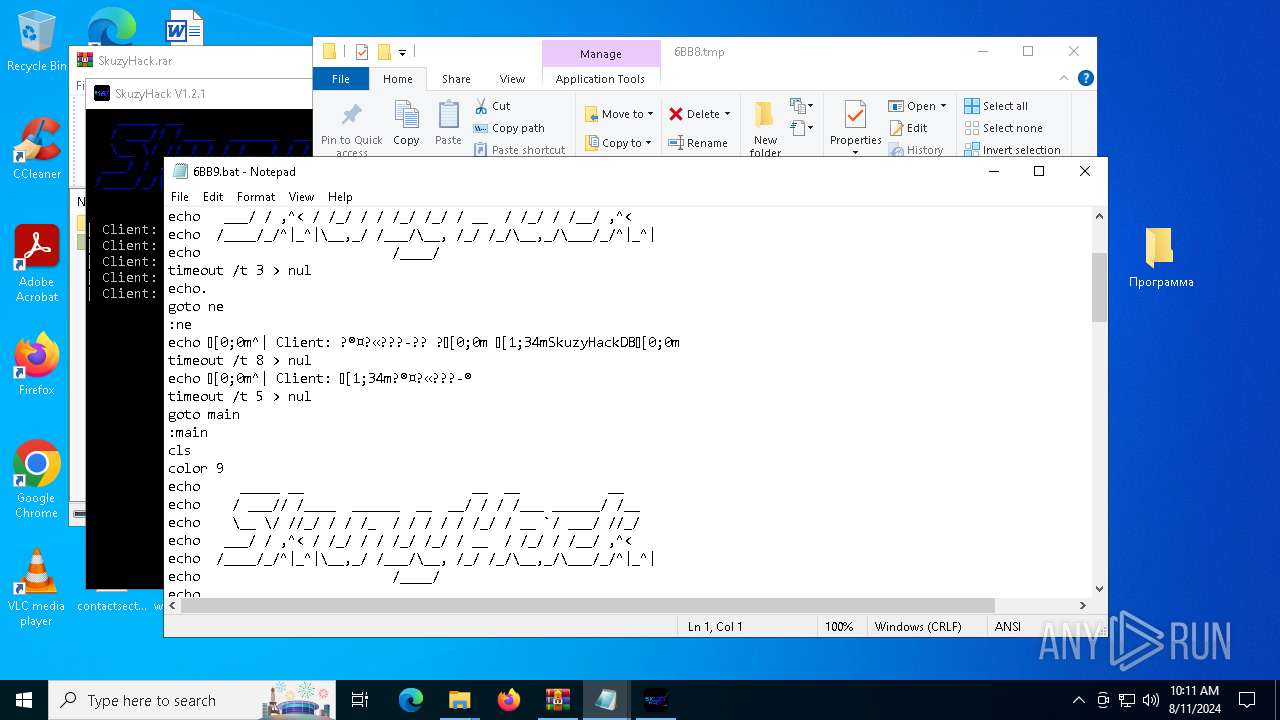
Starts CMD.EXE for commands execution
- SkuzyHack.exe (PID: 2628)
- cmd.exe (PID: 6632)
- SkuzyHack.exe (PID: 6916)
- cmd.exe (PID: 1432)
- SkuzyHack.exe (PID: 7544)
- cmd.exe (PID: 6500)
- SkuzyHack.exe (PID: 6412)
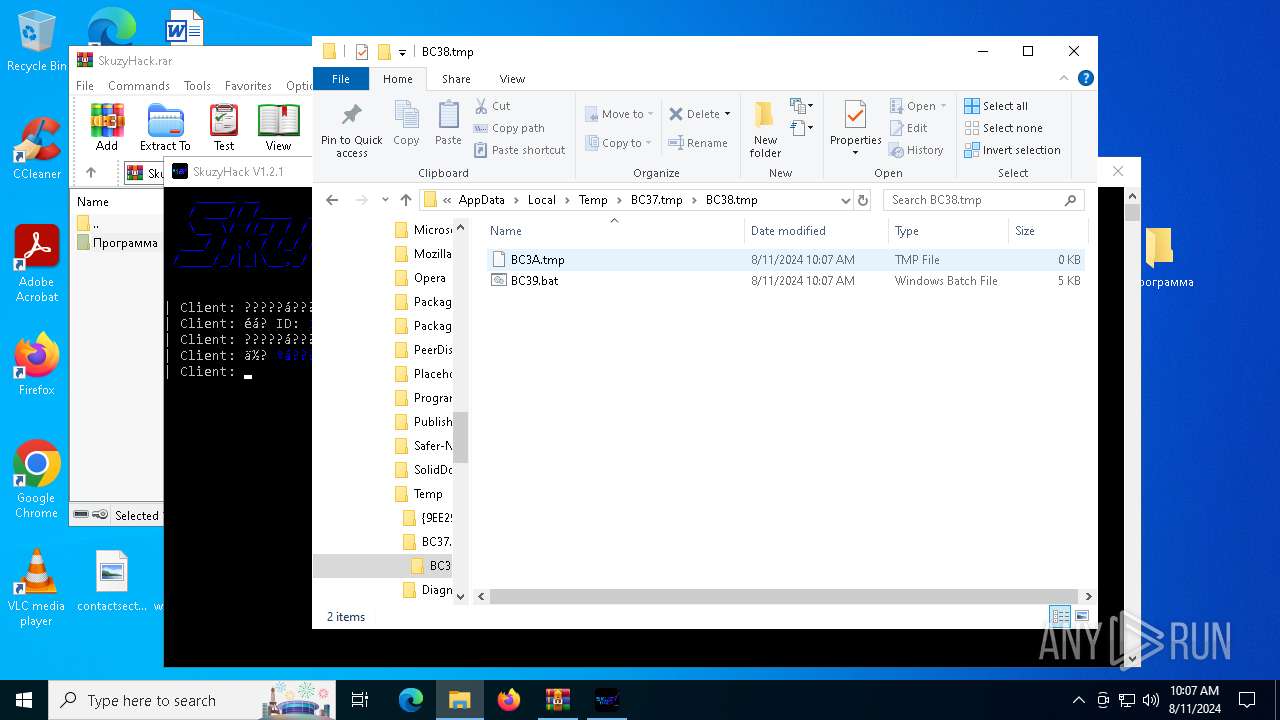
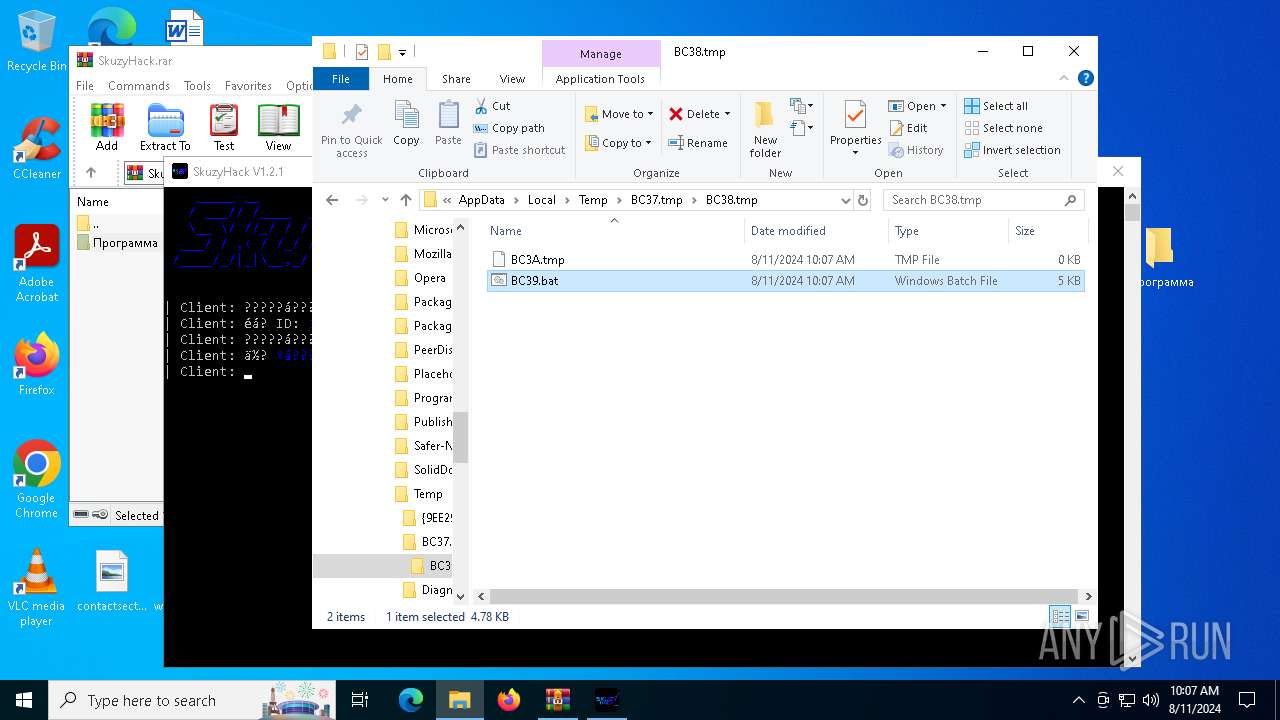
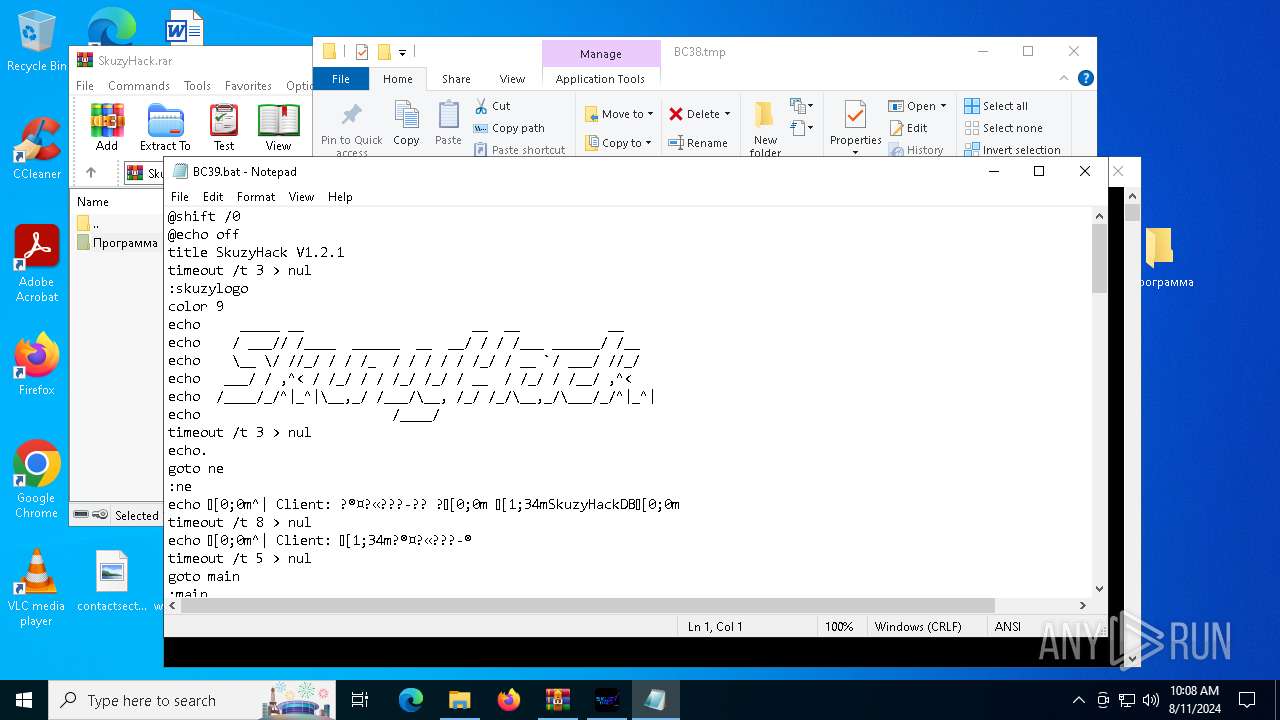
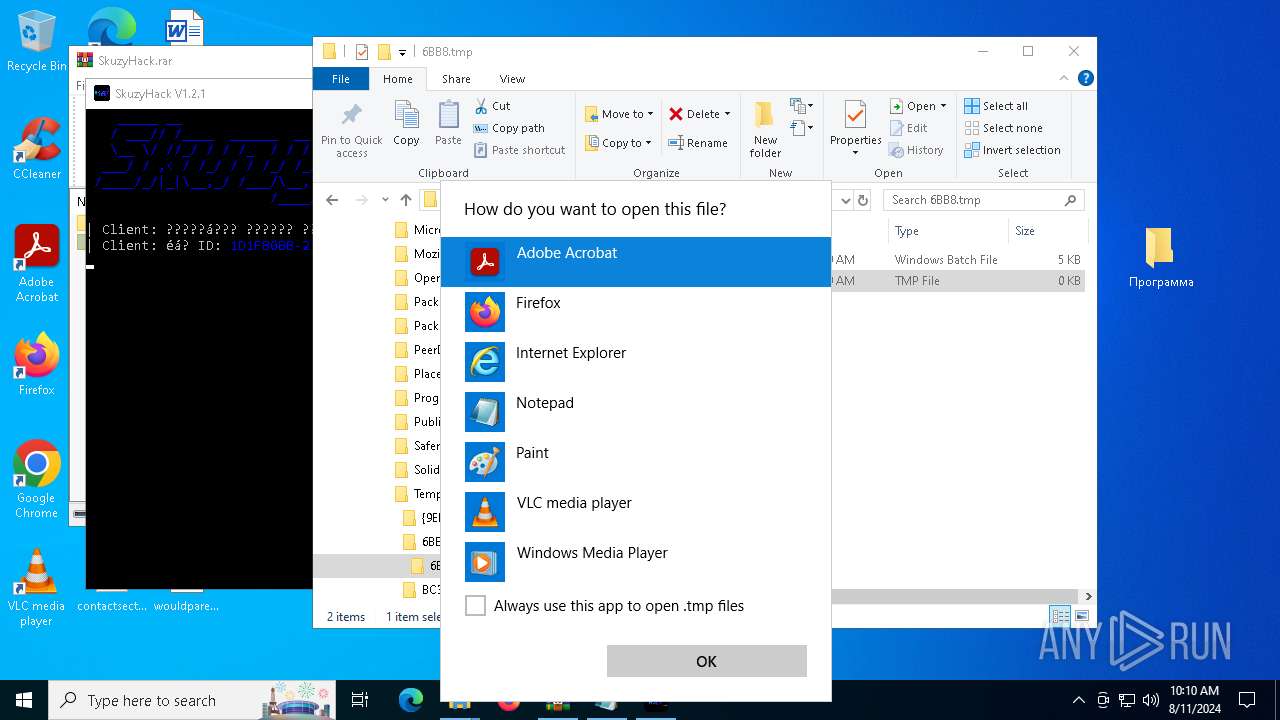
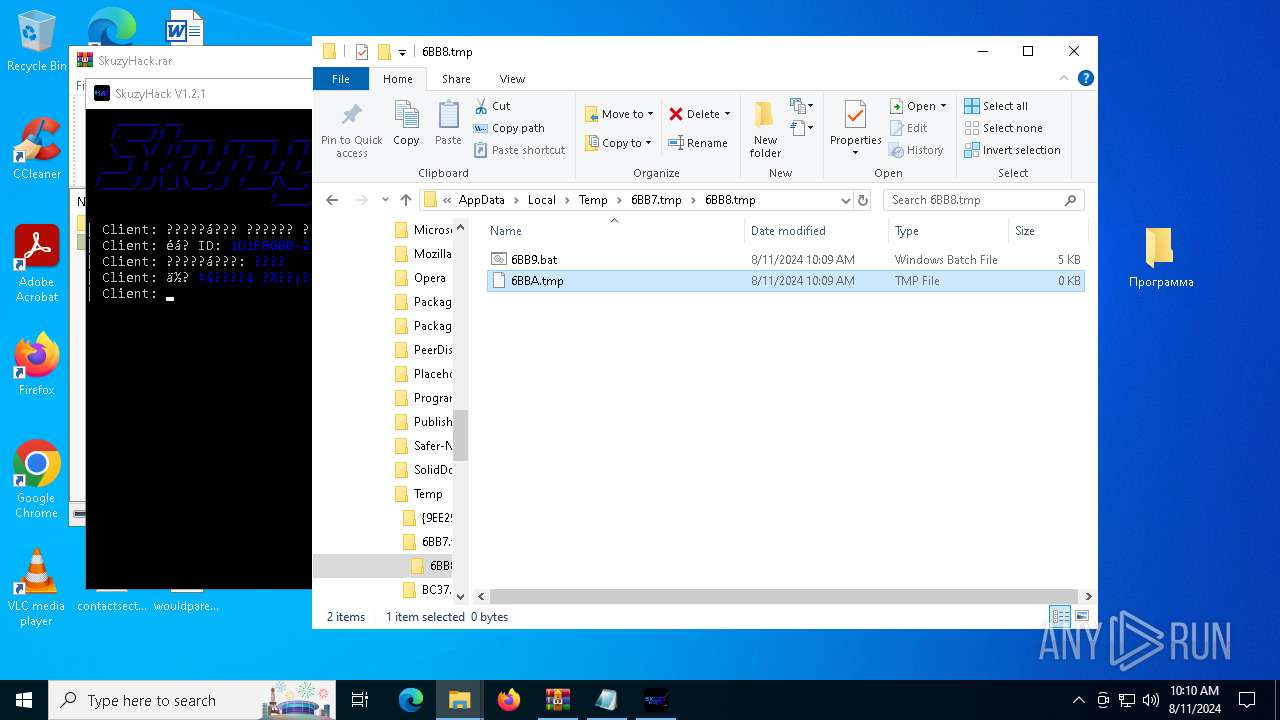
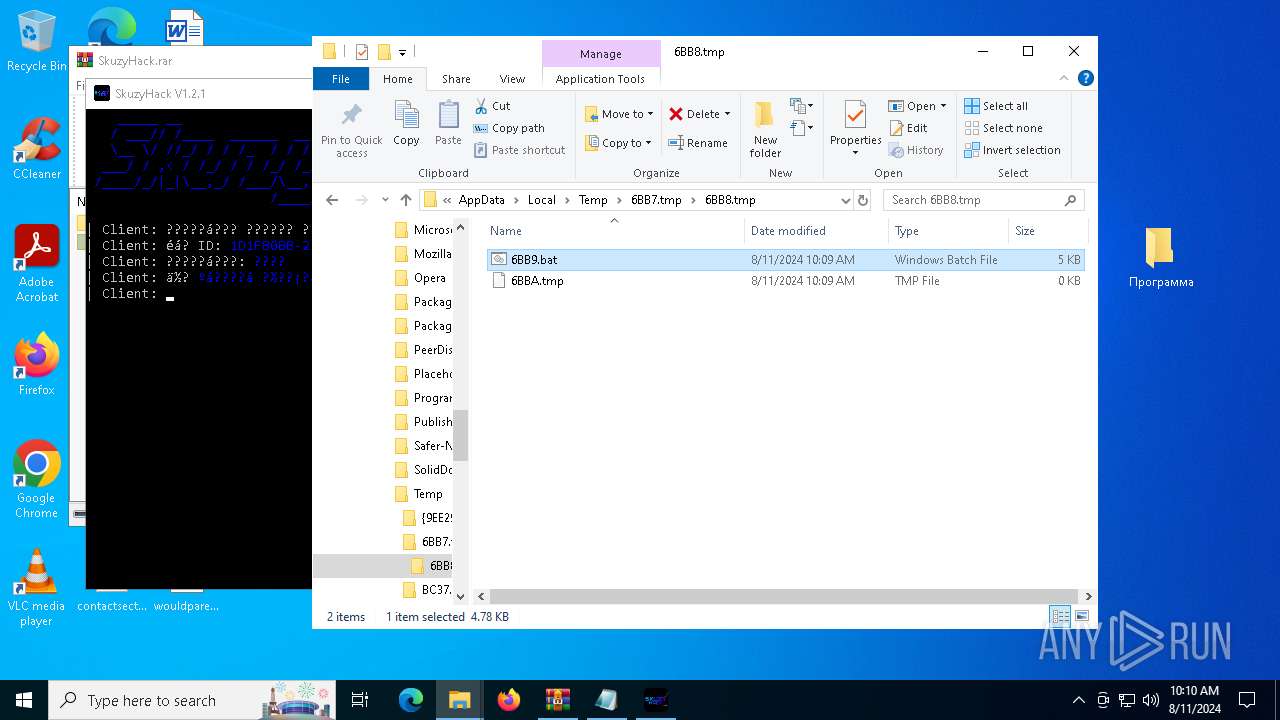
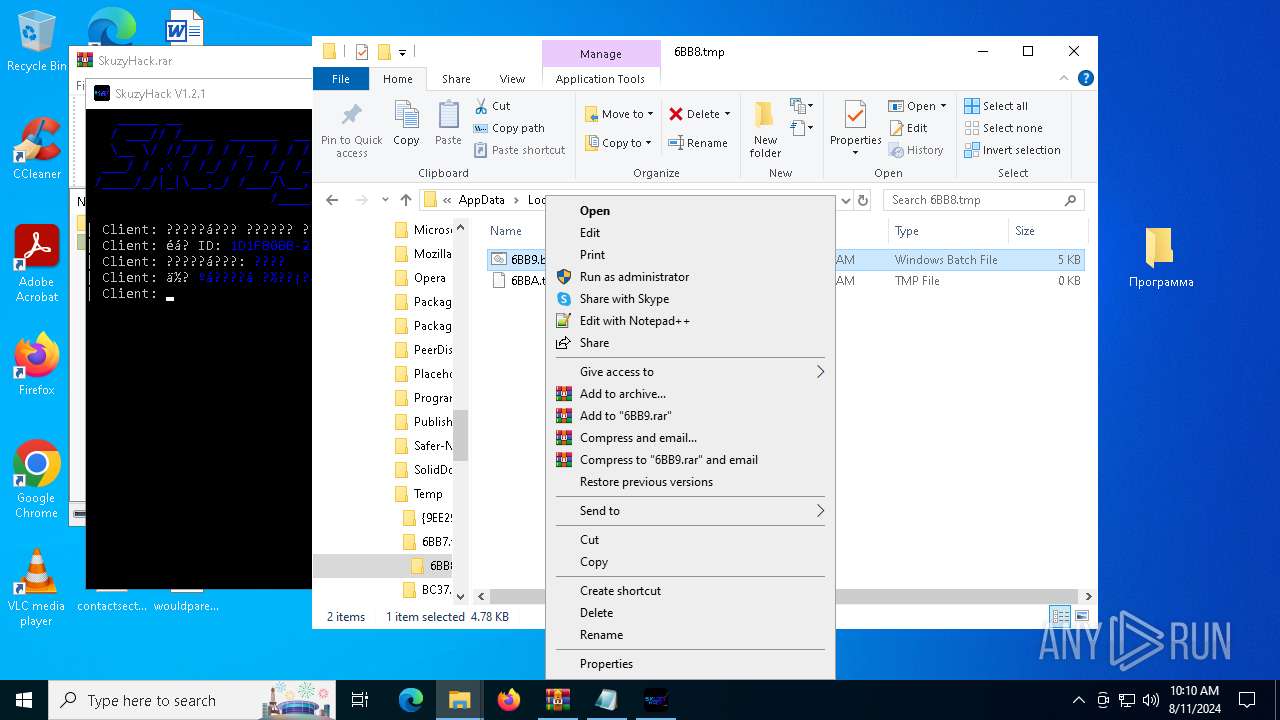
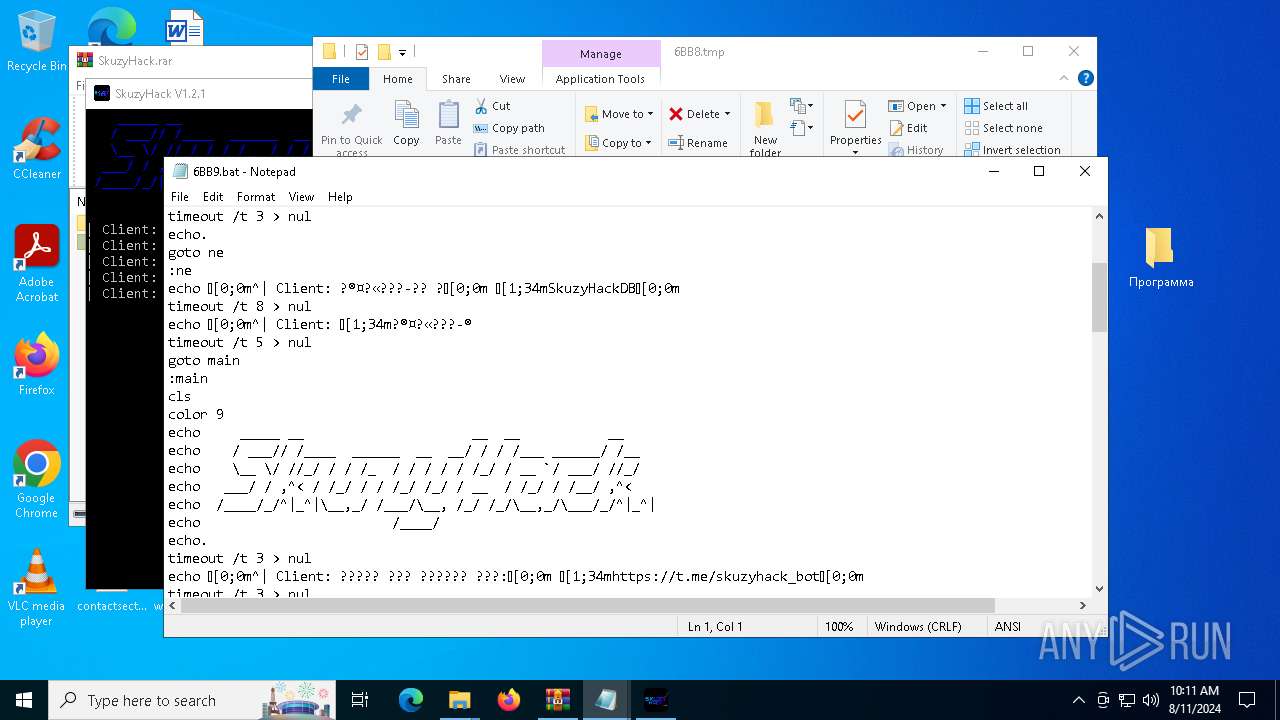
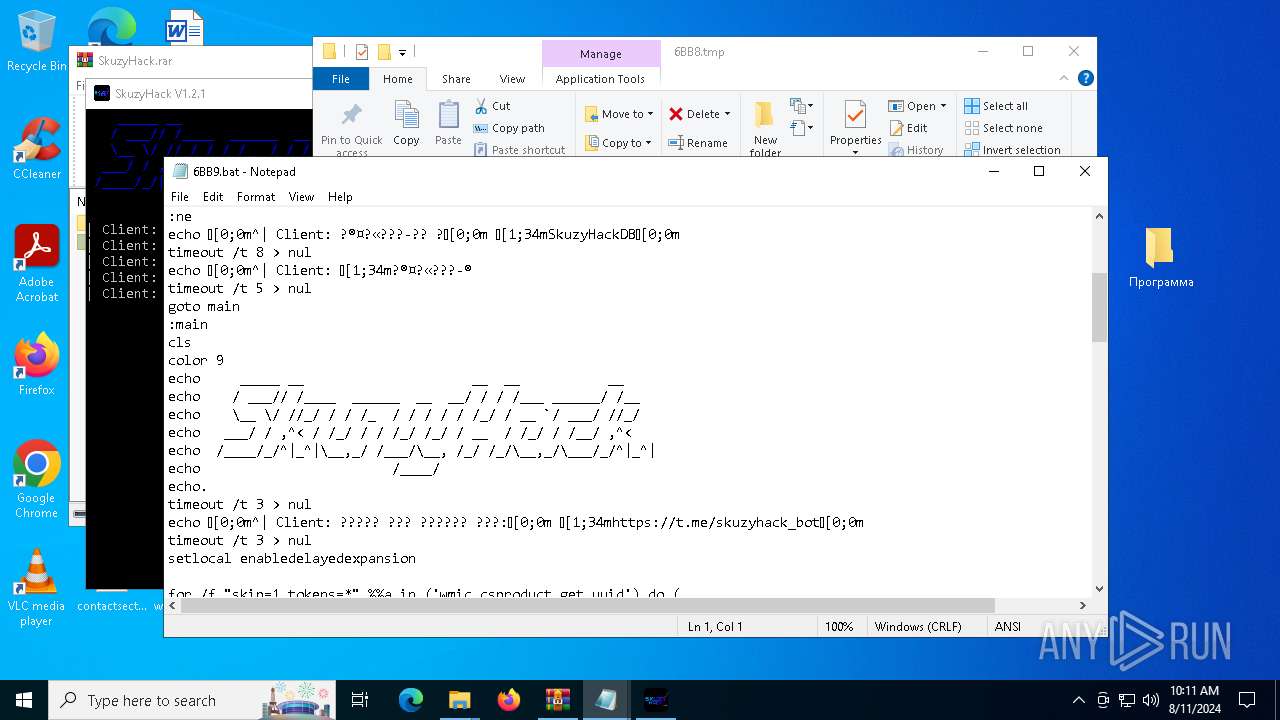
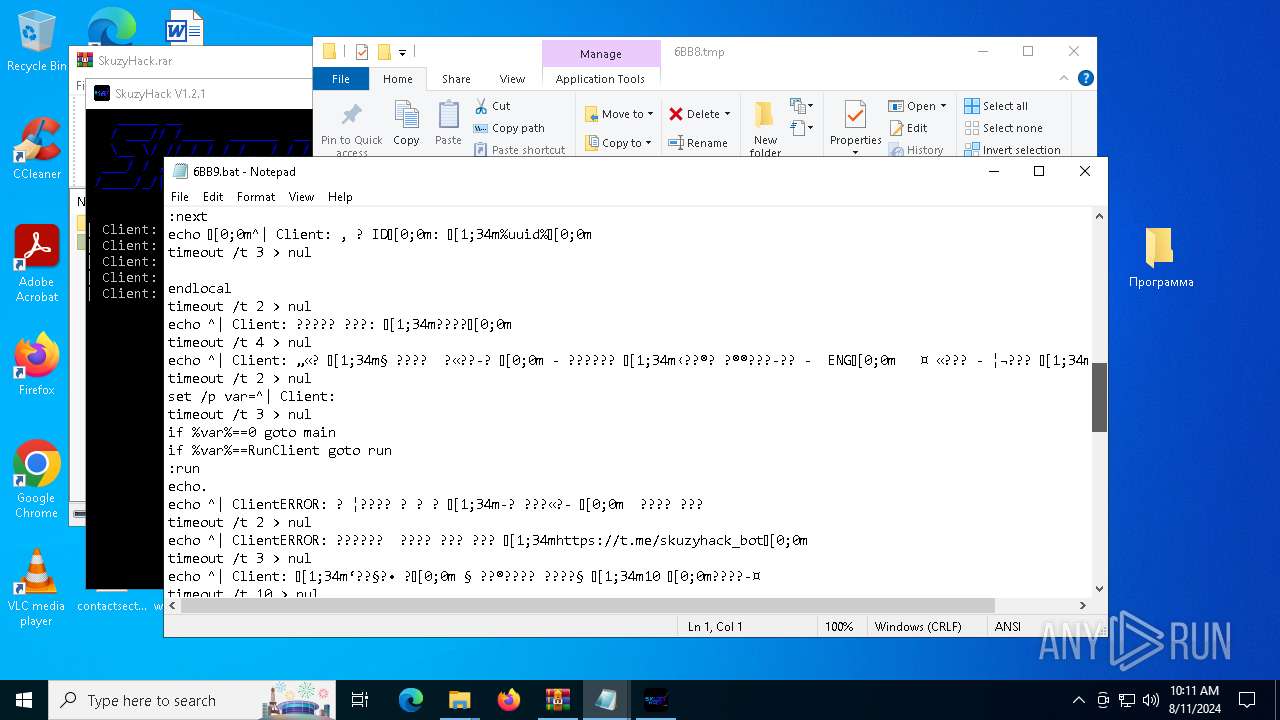
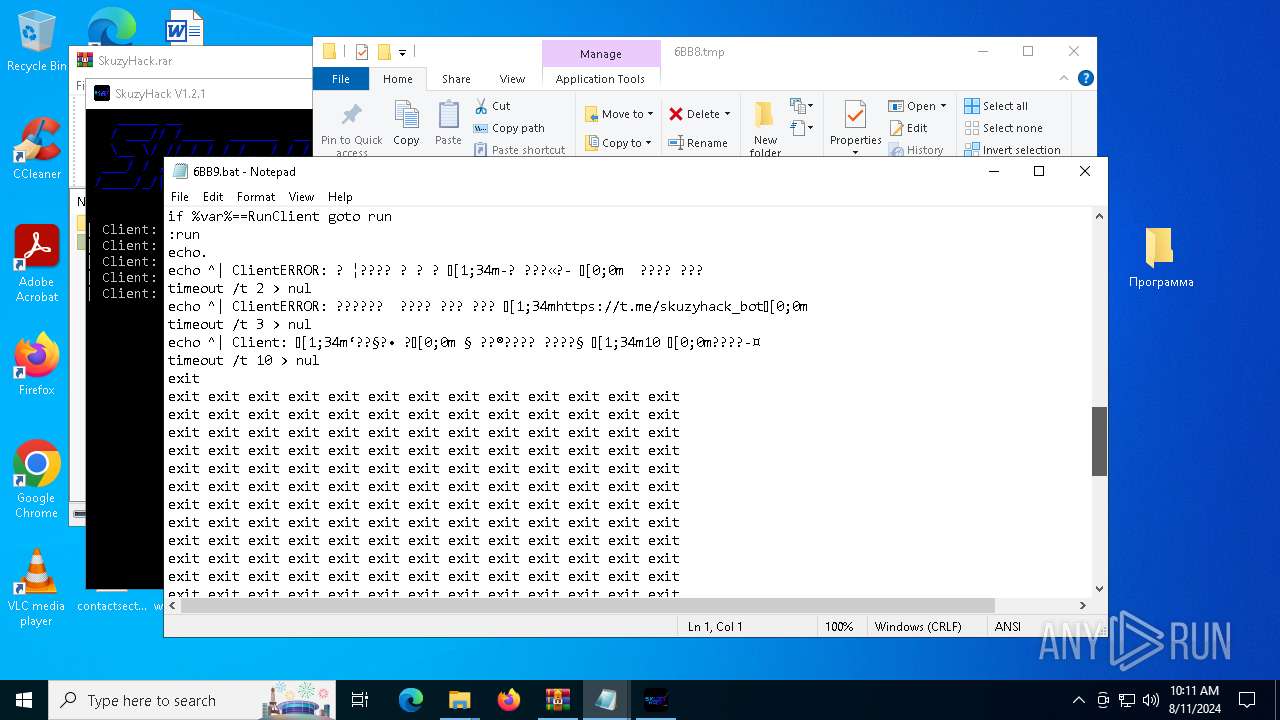
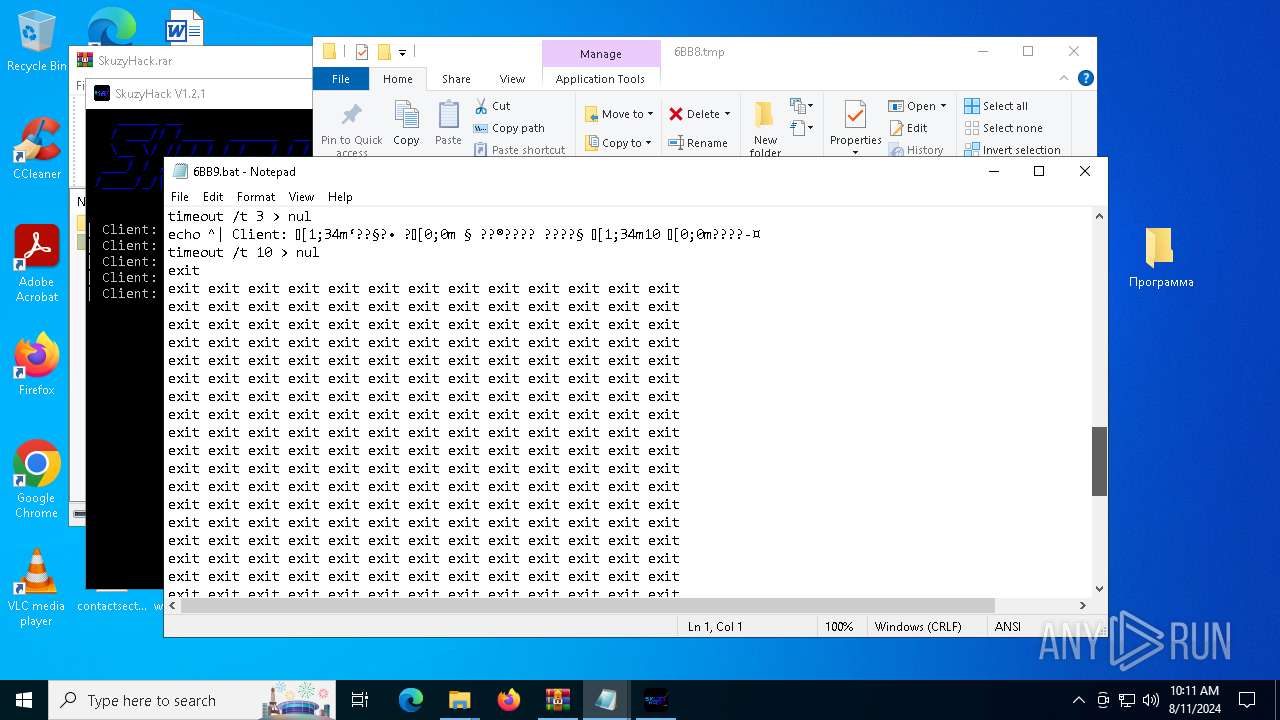
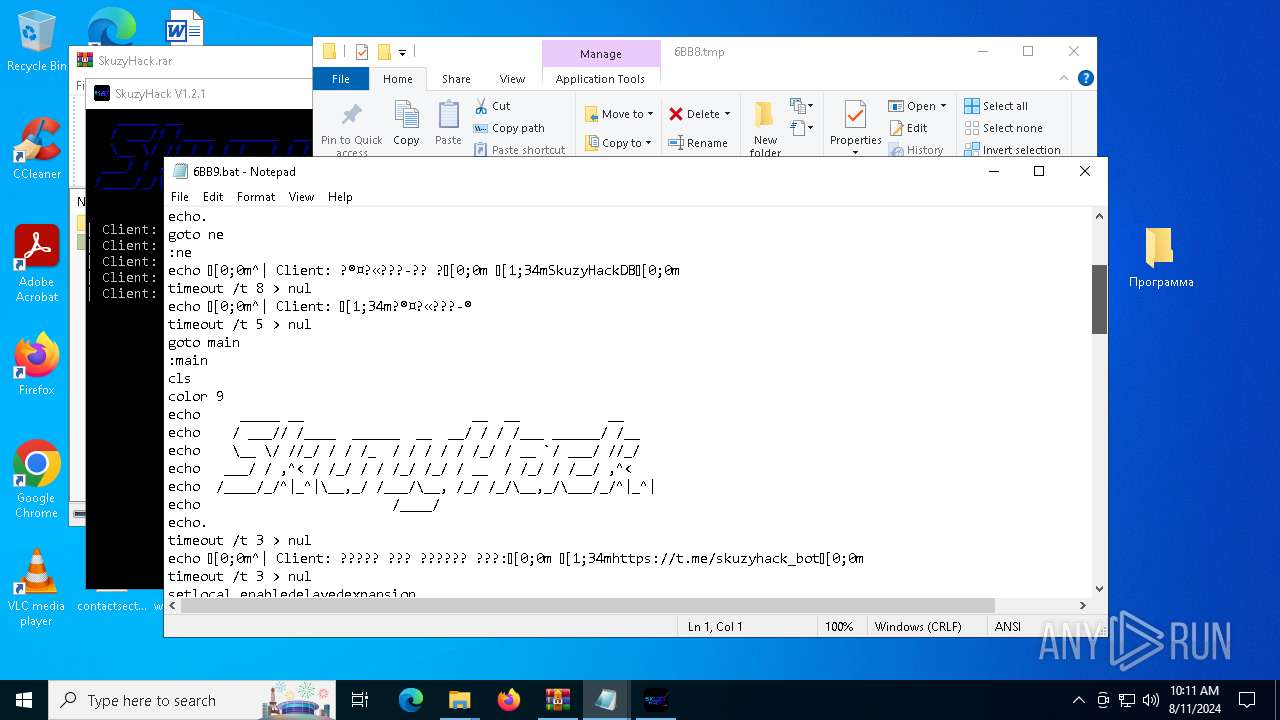
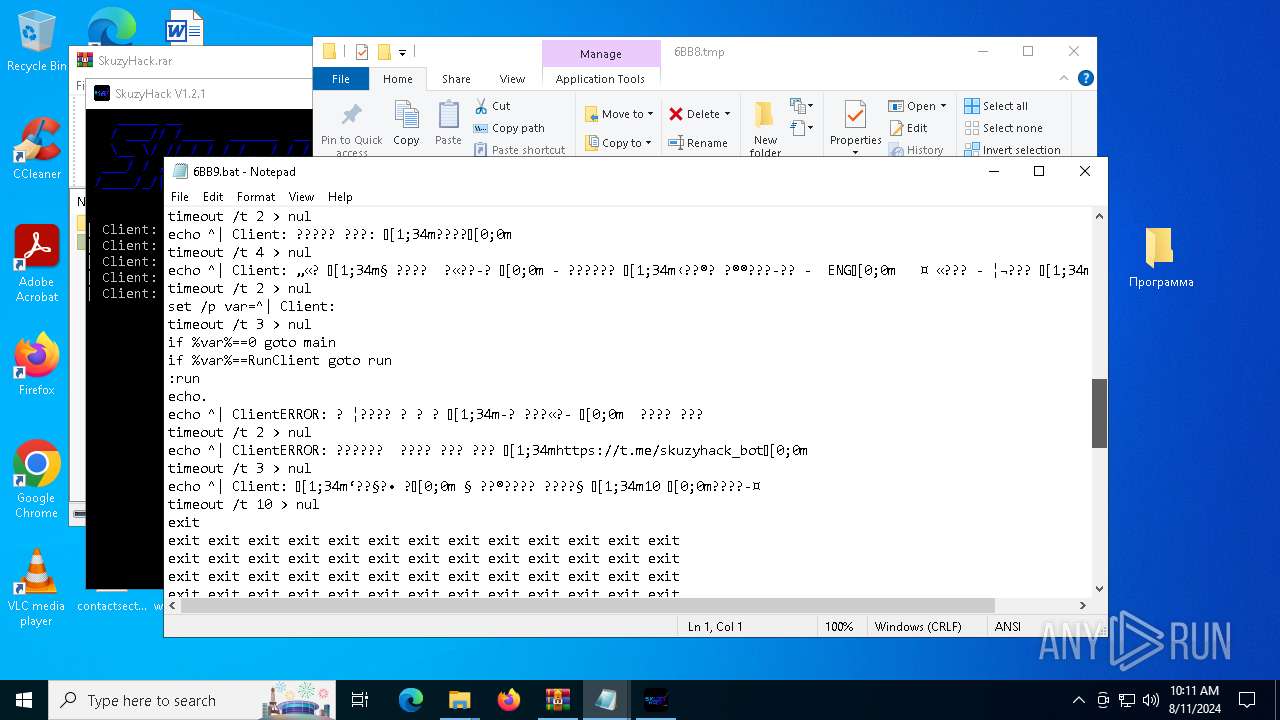
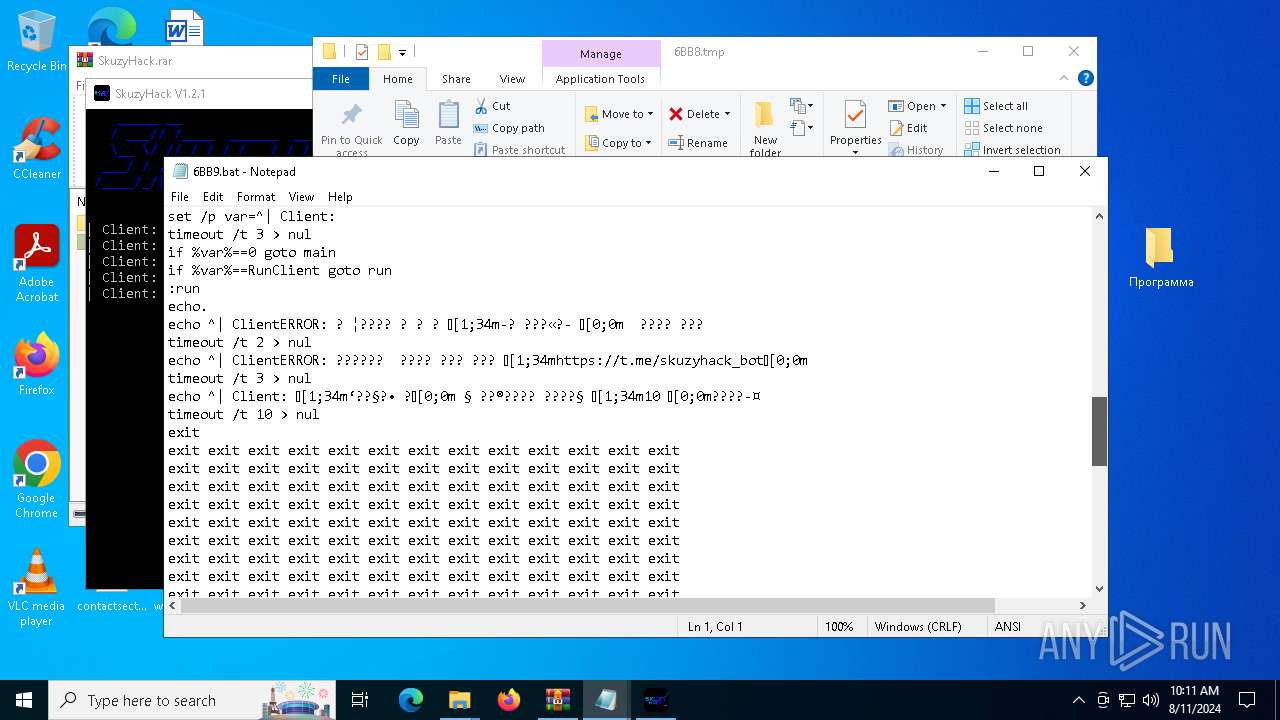
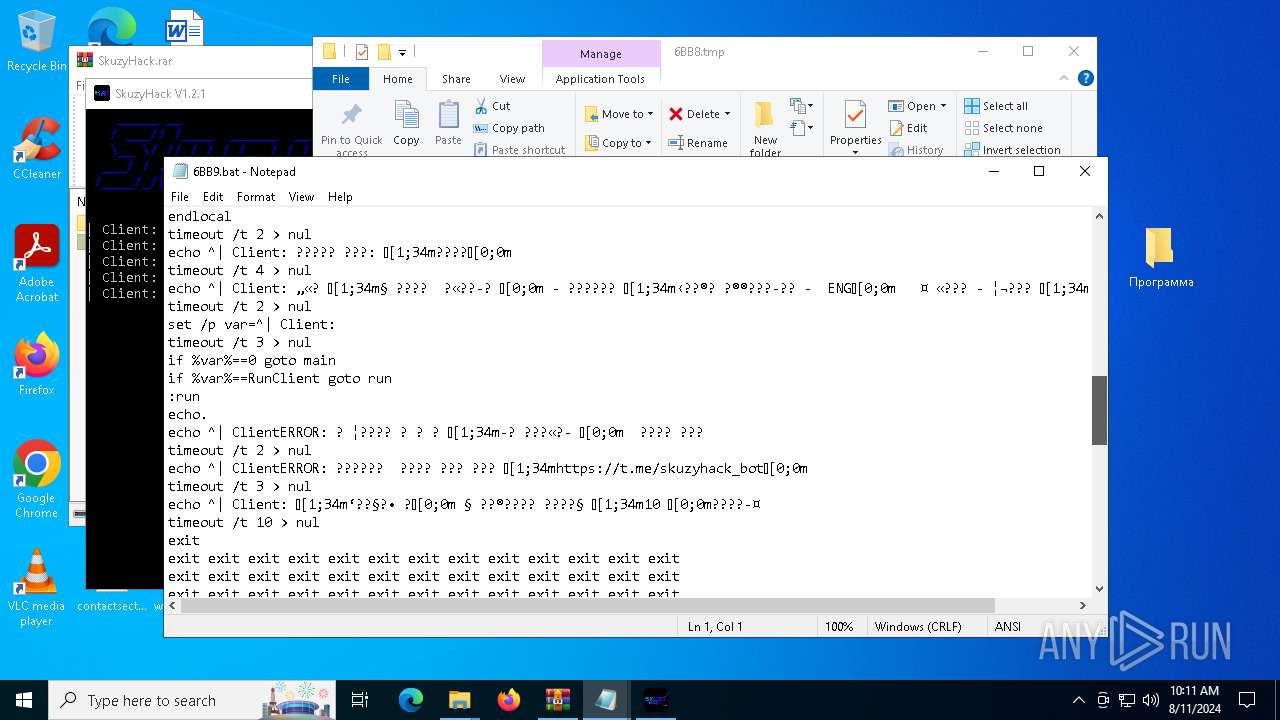
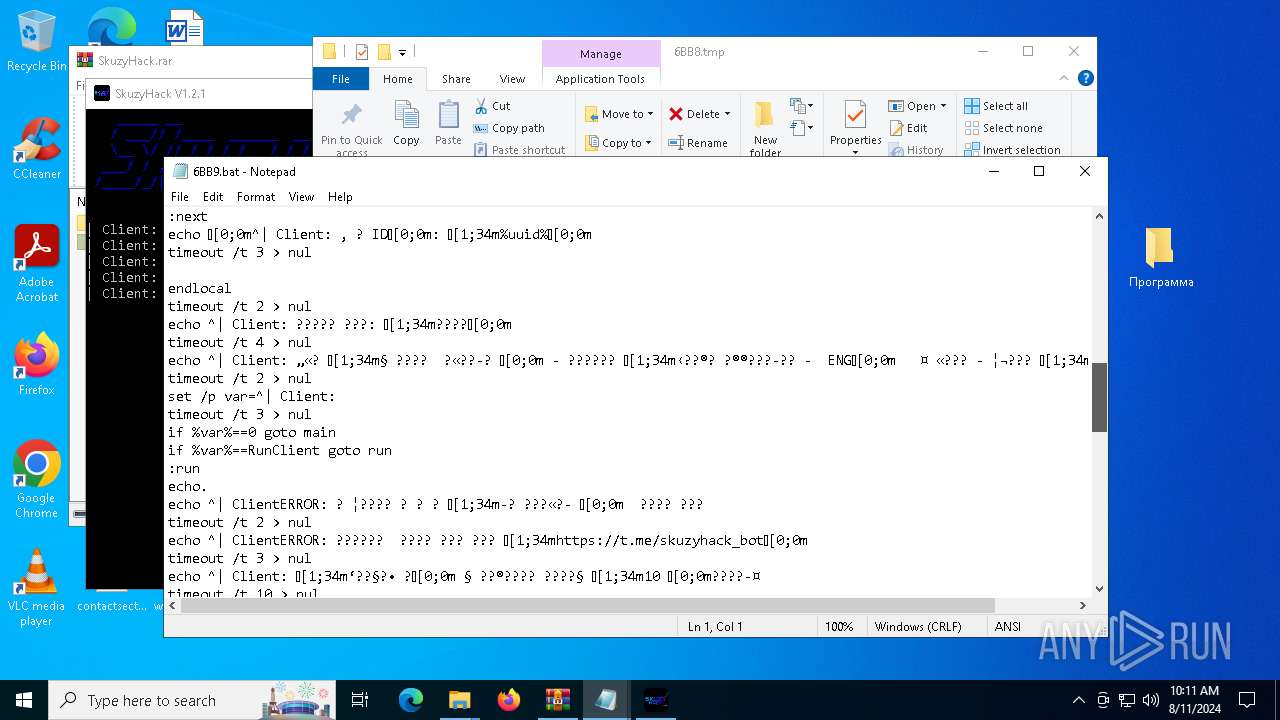
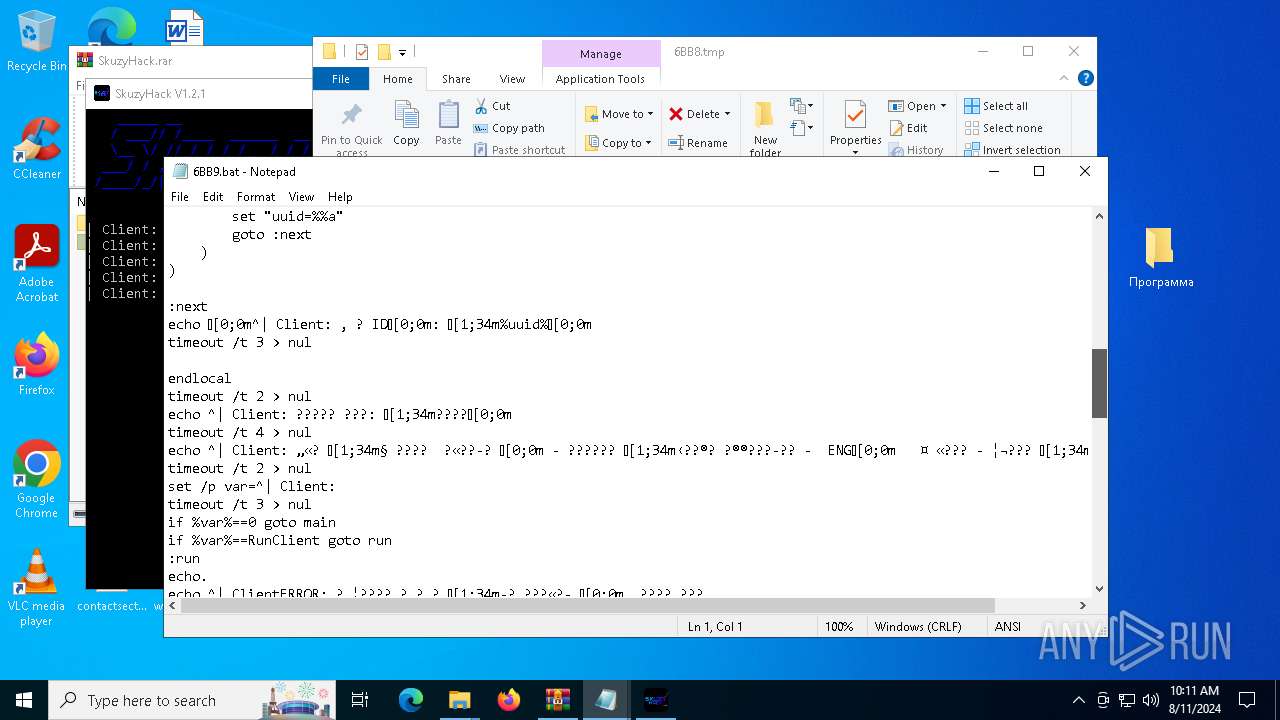
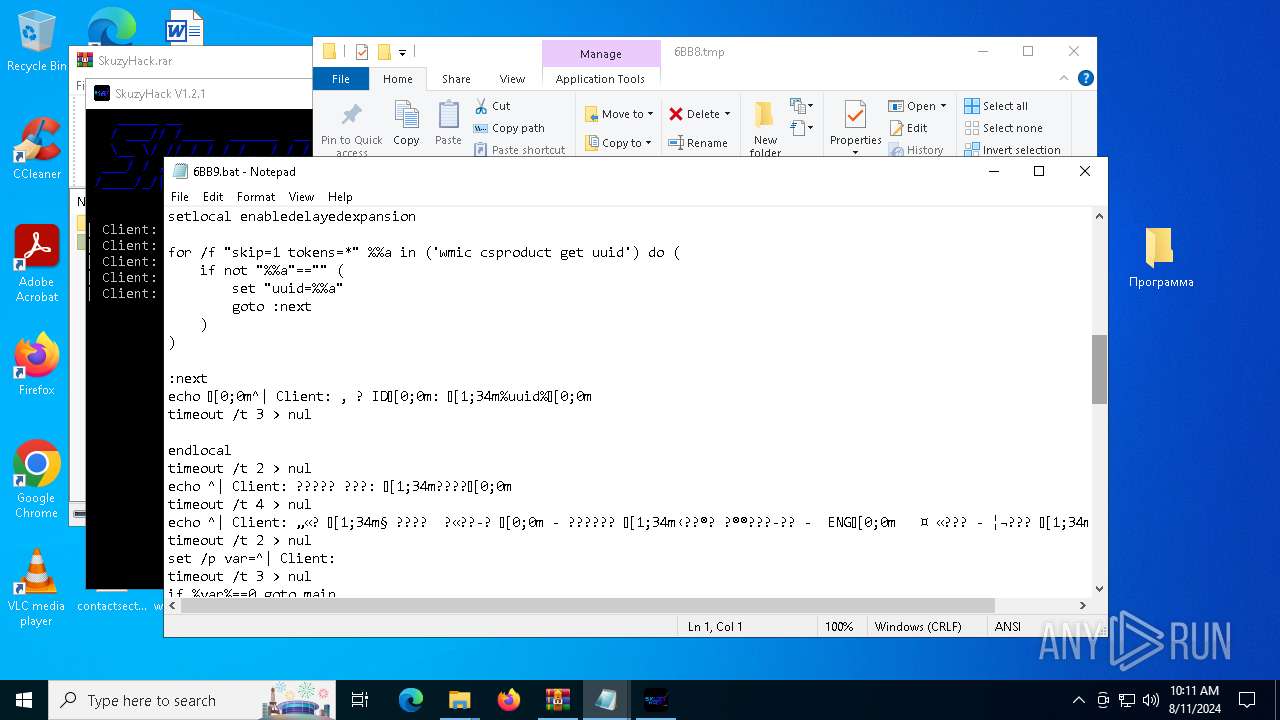
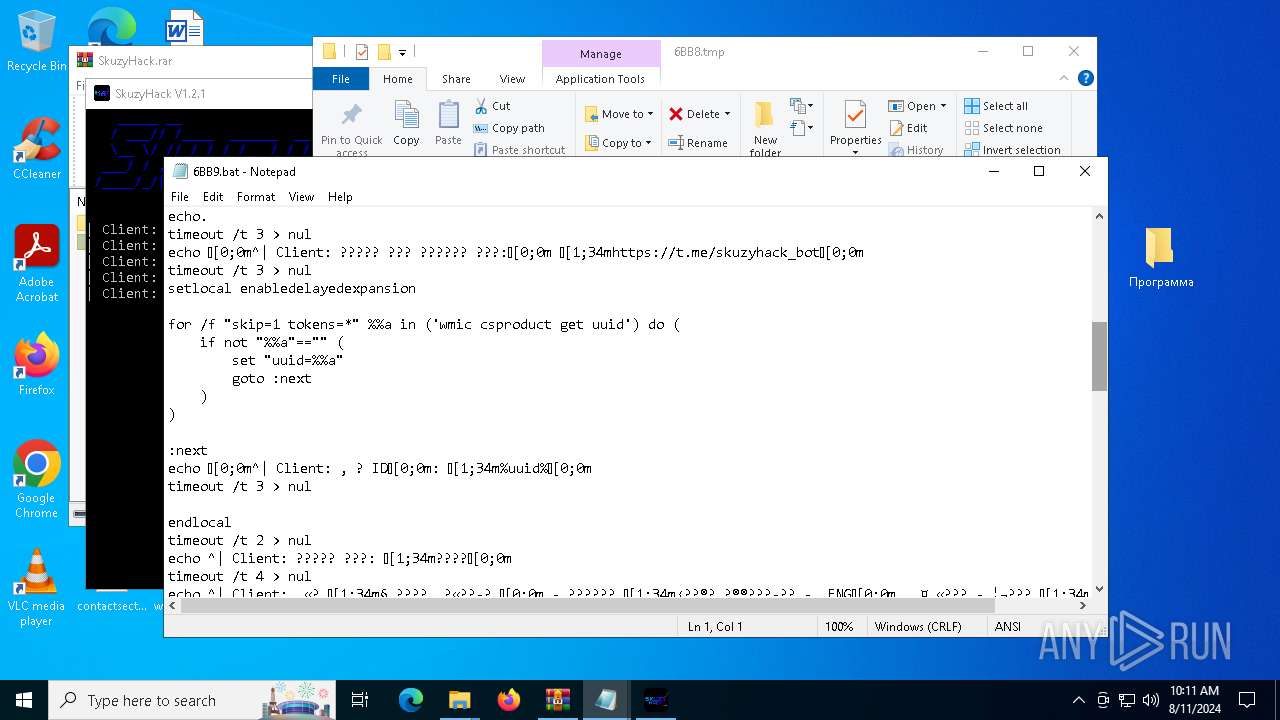
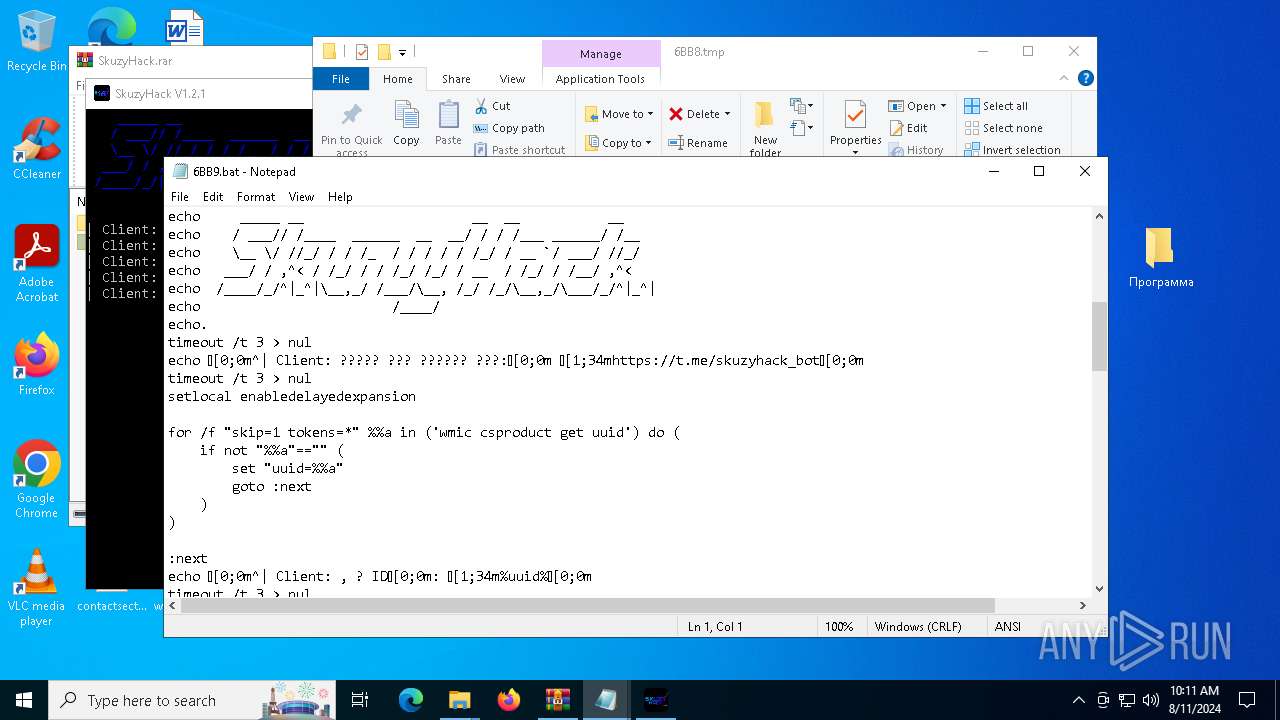
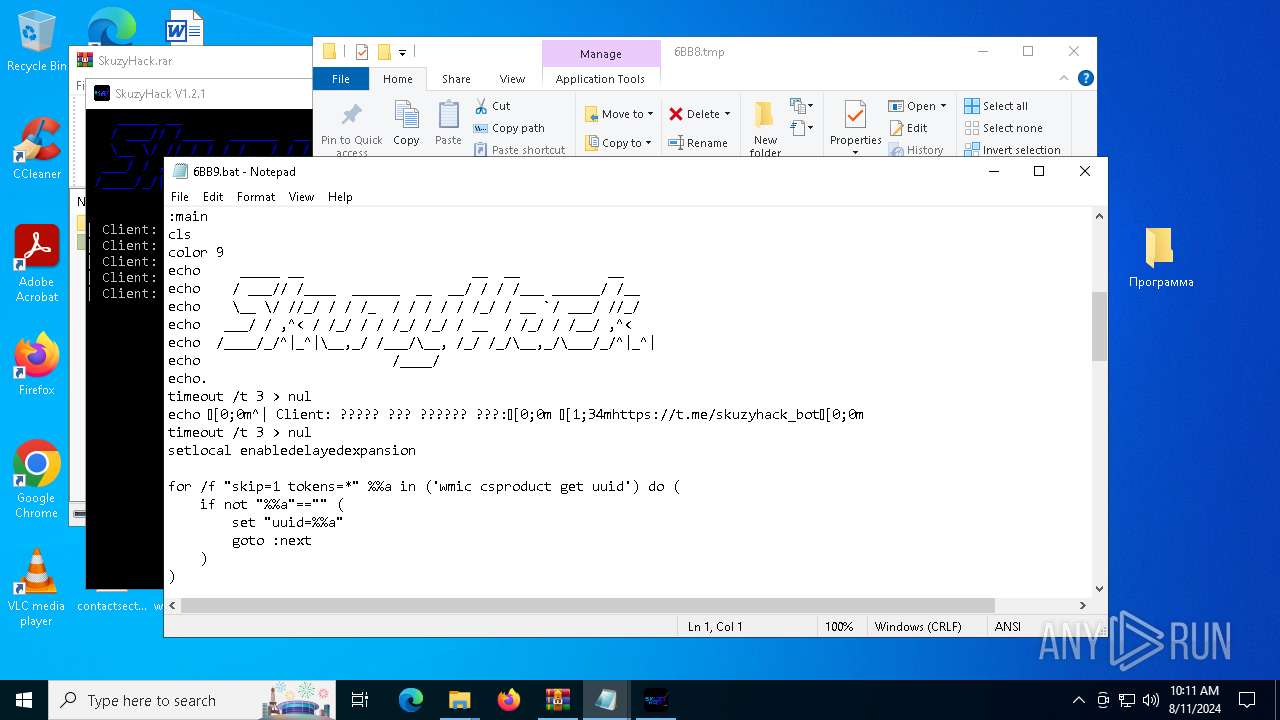
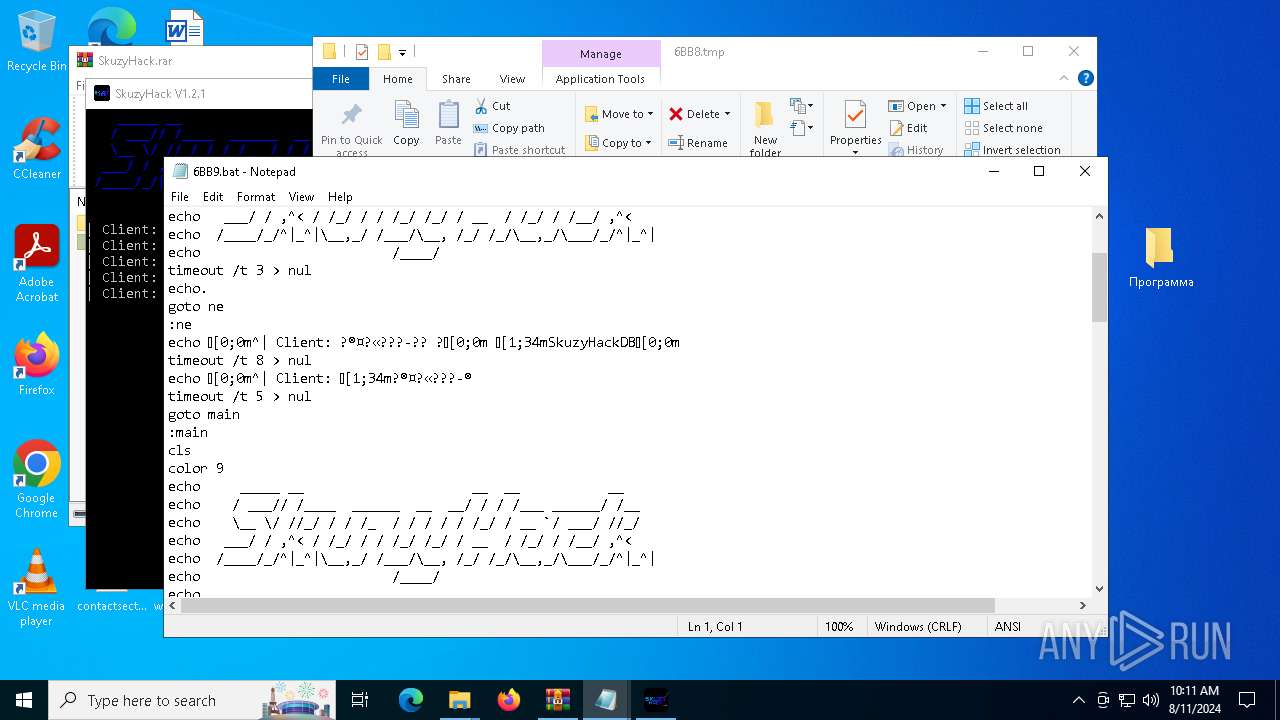
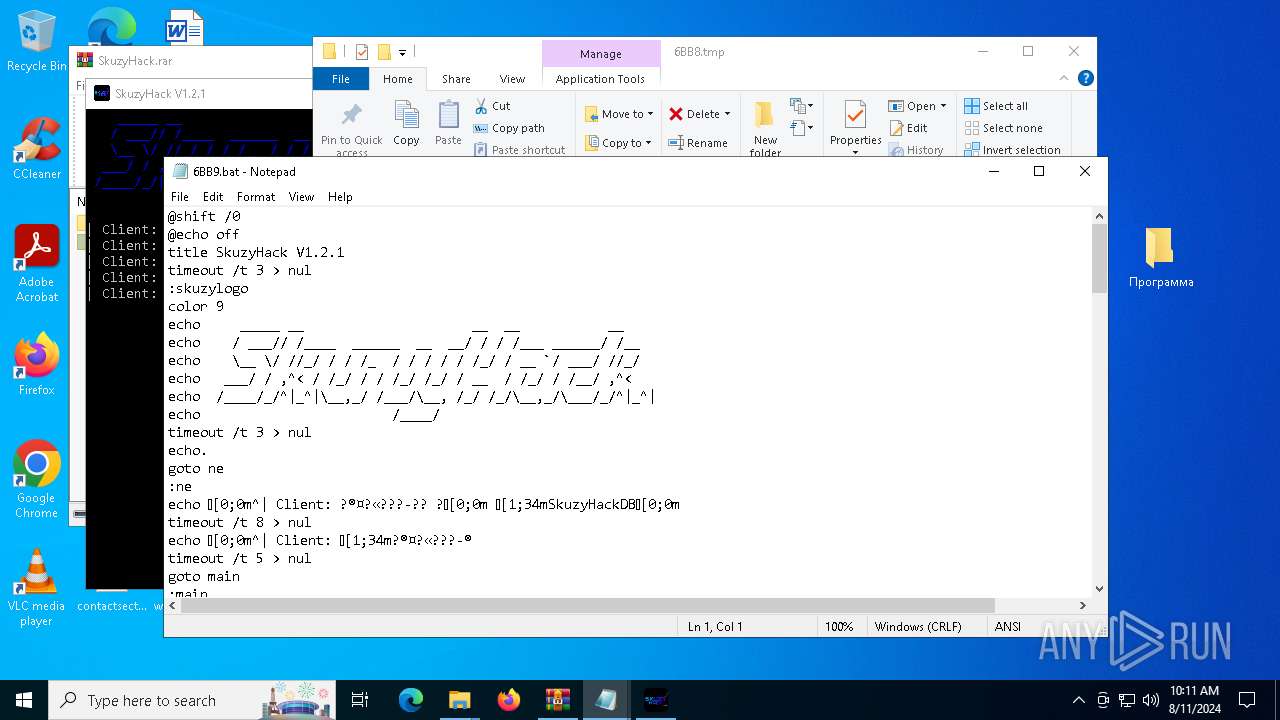
Executing commands from a ".bat" file
- SkuzyHack.exe (PID: 2628)
- SkuzyHack.exe (PID: 6916)
- SkuzyHack.exe (PID: 7544)
- SkuzyHack.exe (PID: 6412)
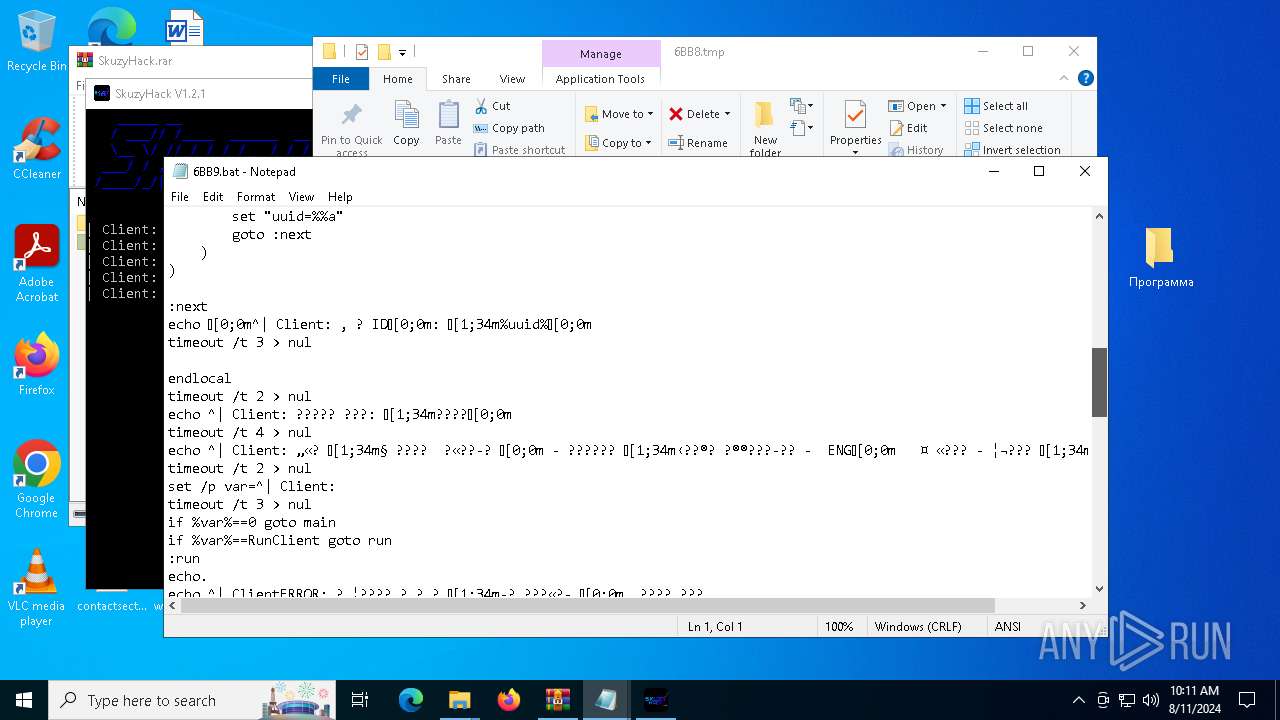
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 6632)
- cmd.exe (PID: 1432)
- cmd.exe (PID: 6172)
- cmd.exe (PID: 6500)
- cmd.exe (PID: 6272)
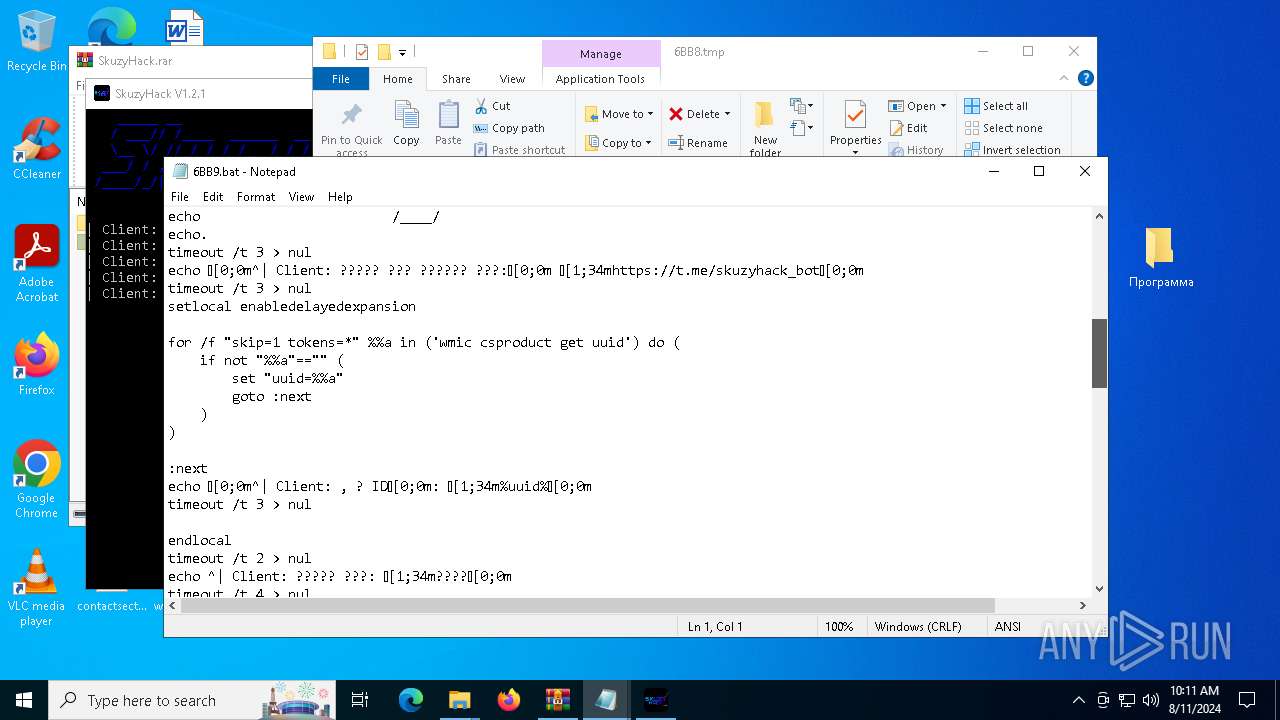
Uses WMIC.EXE to obtain Windows Installer data
- cmd.exe (PID: 6968)
- cmd.exe (PID: 3032)
- cmd.exe (PID: 7424)
Application launched itself
- cmd.exe (PID: 6632)
- cmd.exe (PID: 1432)
- cmd.exe (PID: 6500)
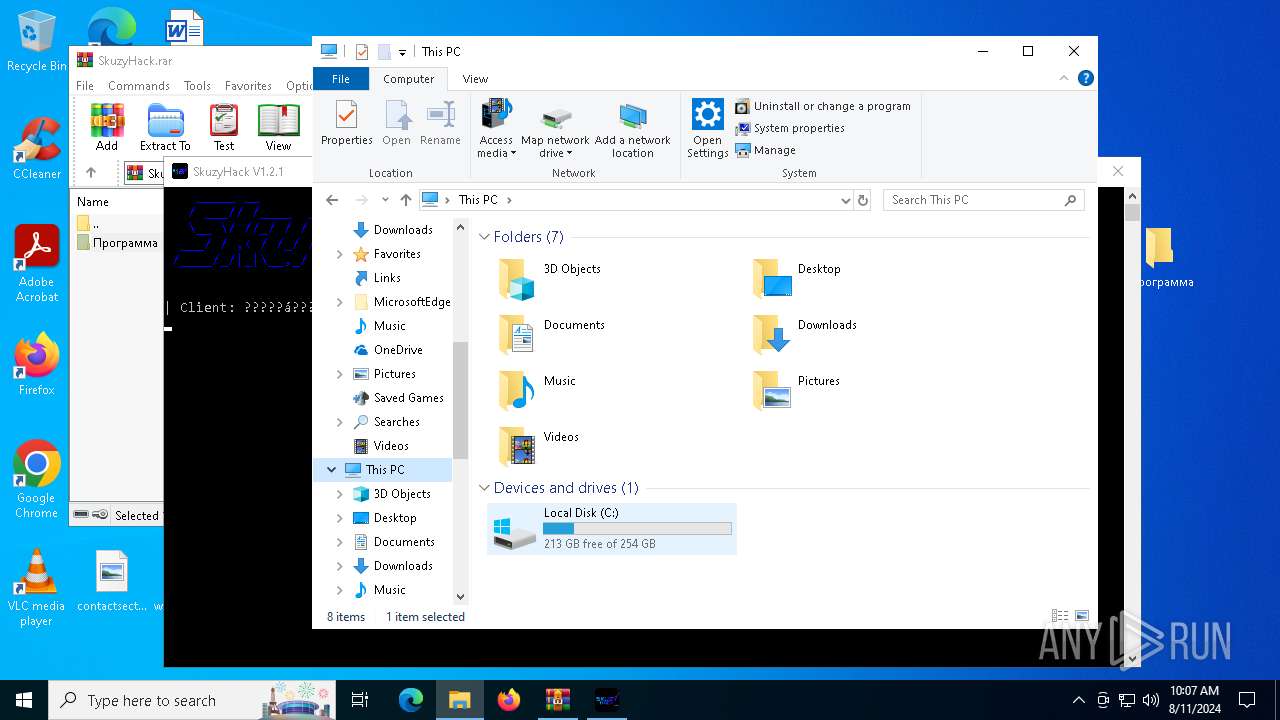
Accesses product unique identifier via WMI (SCRIPT)
- WMIC.exe (PID: 5196)
- WMIC.exe (PID: 4020)
- WMIC.exe (PID: 6548)
INFO
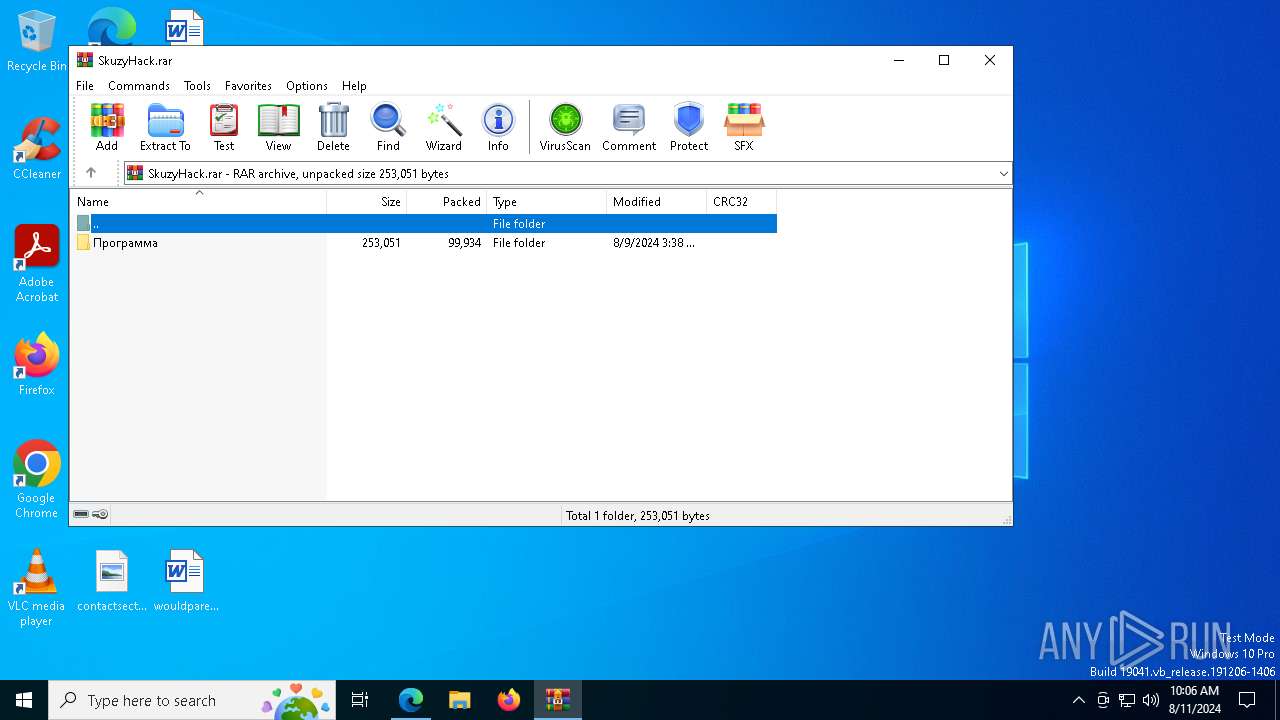
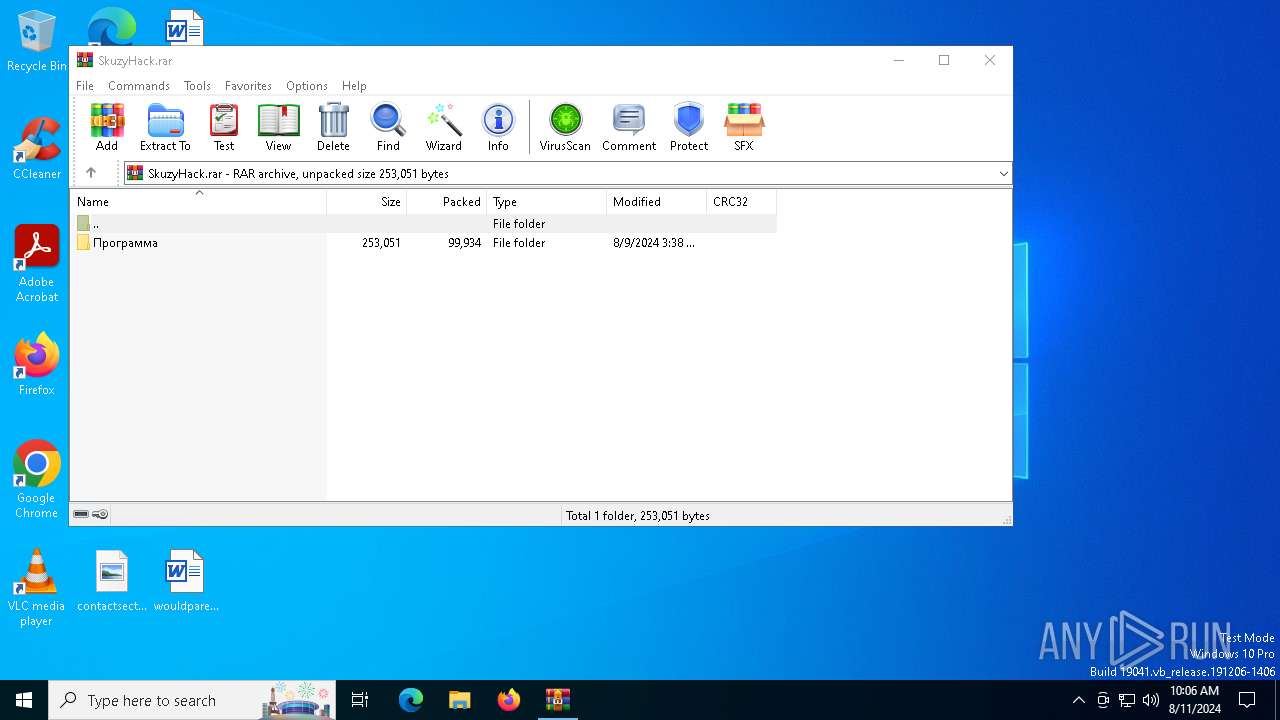
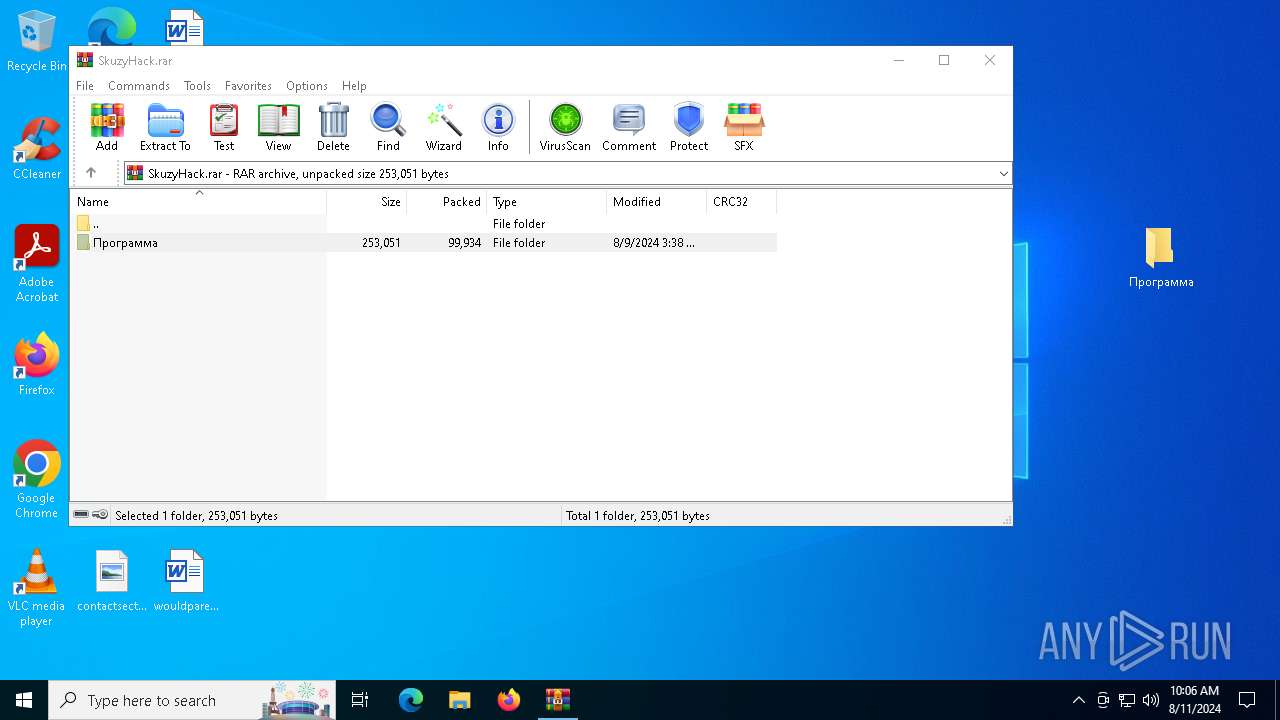
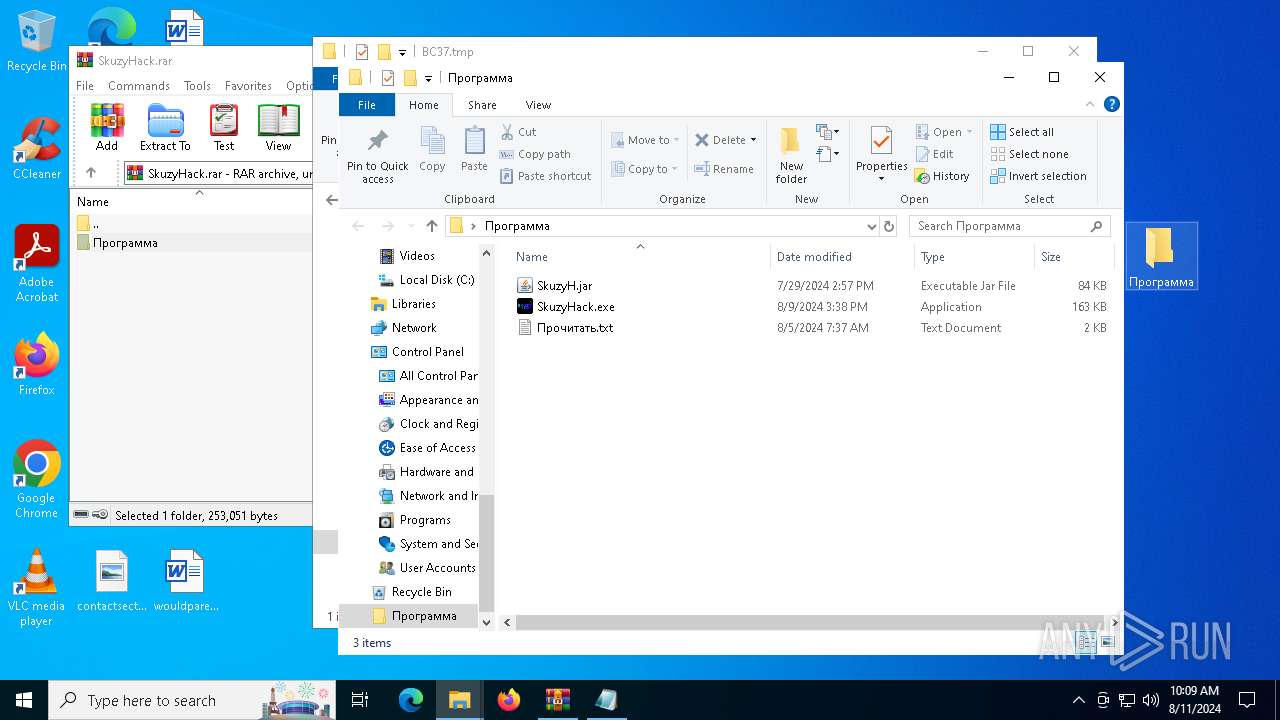
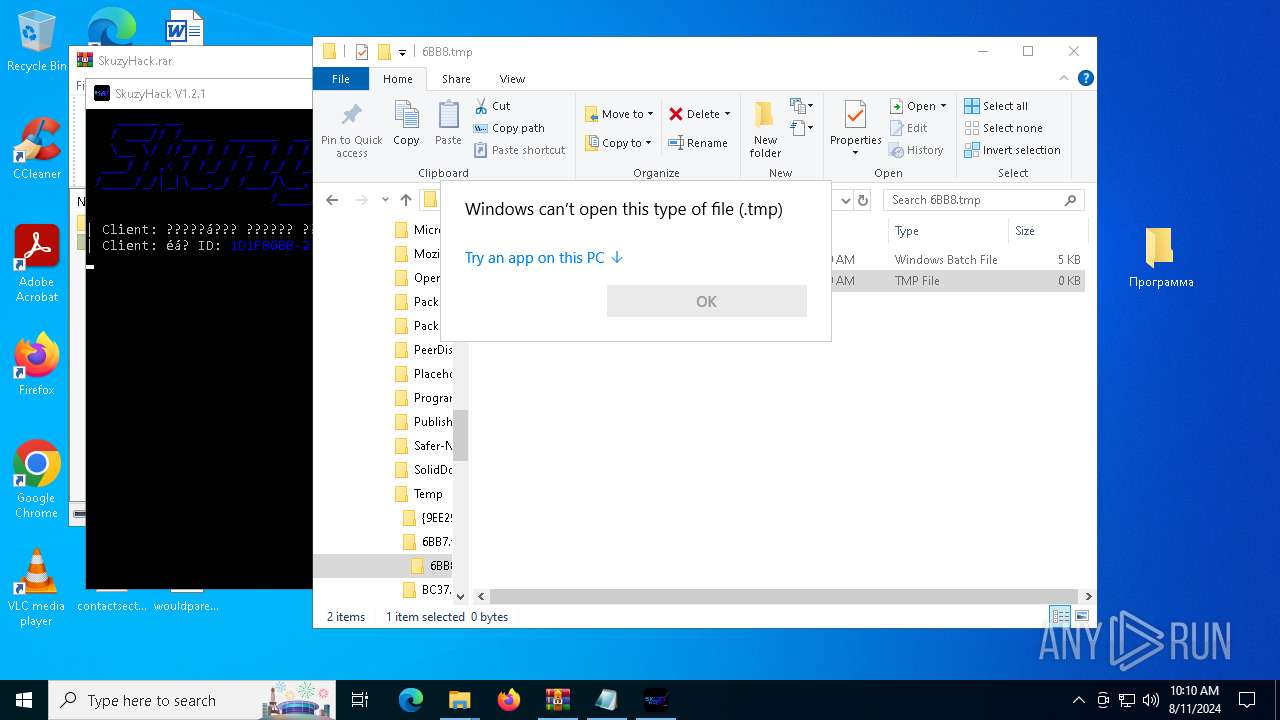
The process uses the downloaded file
- msedge.exe (PID: 5032)
- msedge.exe (PID: 6432)
- WinRAR.exe (PID: 7240)
Reads Microsoft Office registry keys
- msedge.exe (PID: 6432)
- msedge.exe (PID: 4772)
- OpenWith.exe (PID: 6816)
Reads Environment values
- identity_helper.exe (PID: 7360)
- identity_helper.exe (PID: 1492)
Reads the computer name
- identity_helper.exe (PID: 1492)
- identity_helper.exe (PID: 7360)
- TextInputHost.exe (PID: 7172)
Application launched itself
- msedge.exe (PID: 4772)
- msedge.exe (PID: 6432)
Checks supported languages
- identity_helper.exe (PID: 7360)
- SkuzyHack.exe (PID: 2628)
- SkuzyHack.exe (PID: 6916)
- SkuzyHack.exe (PID: 7544)
- SkuzyHack.exe (PID: 6412)
- TextInputHost.exe (PID: 7172)
- identity_helper.exe (PID: 1492)
Reads security settings of Internet Explorer
- WMIC.exe (PID: 5196)
- notepad.exe (PID: 6720)
- WMIC.exe (PID: 4020)
- WMIC.exe (PID: 6548)
- notepad.exe (PID: 7020)
- OpenWith.exe (PID: 6816)
- notepad.exe (PID: 7068)
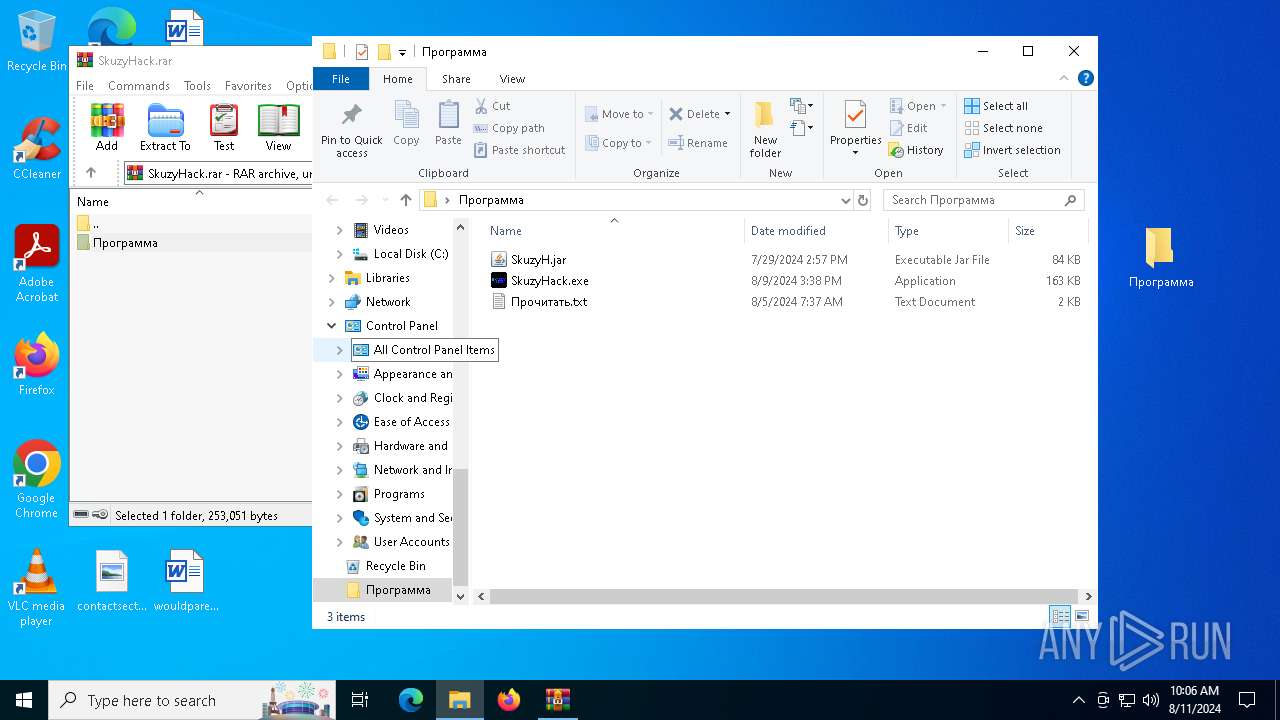
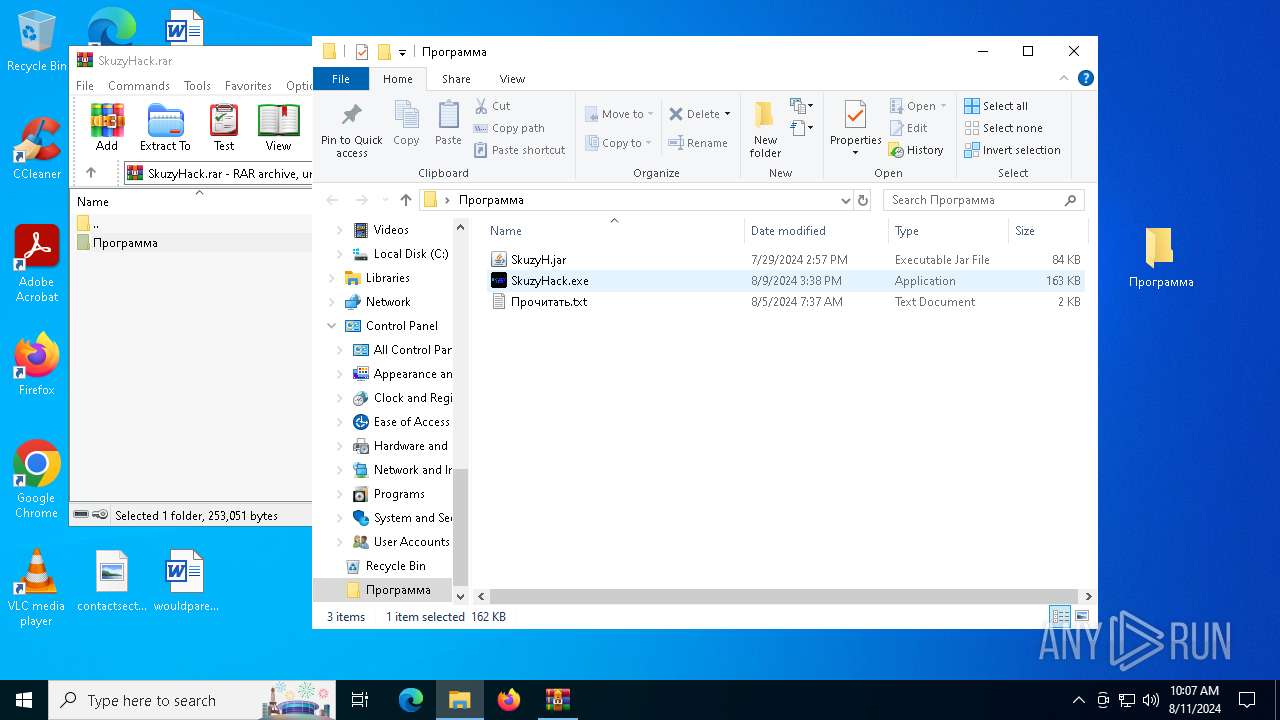
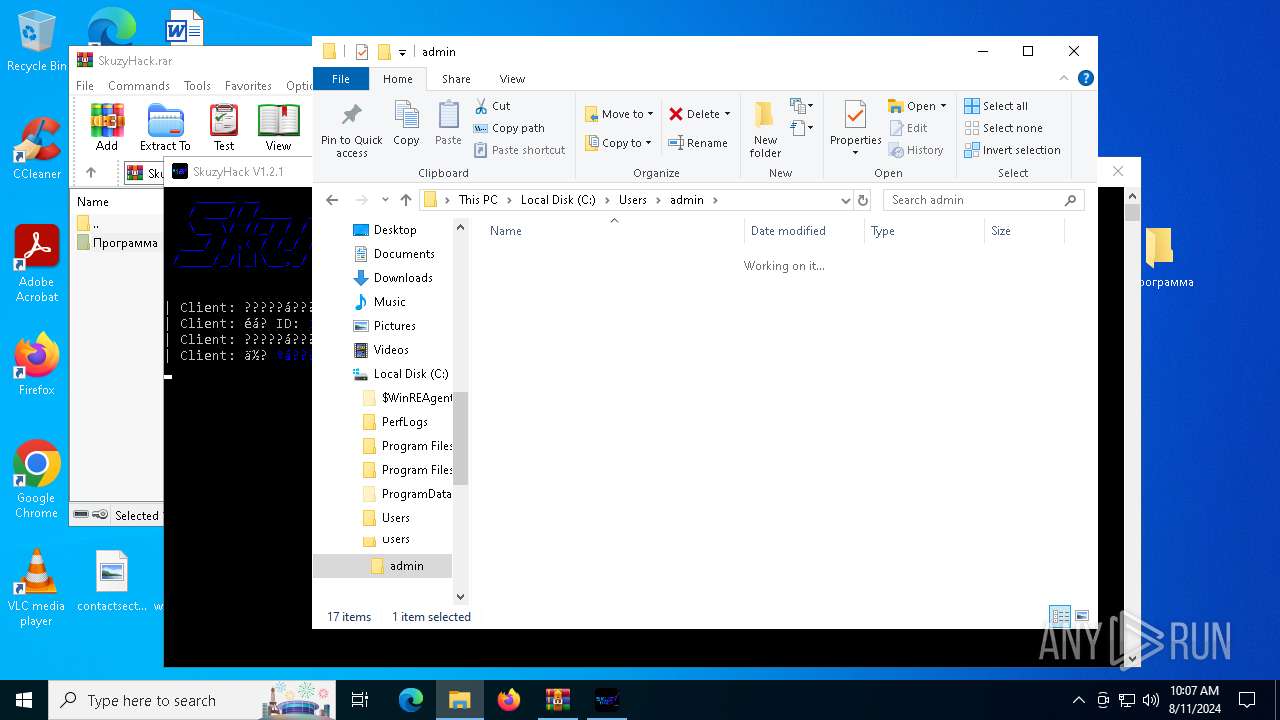
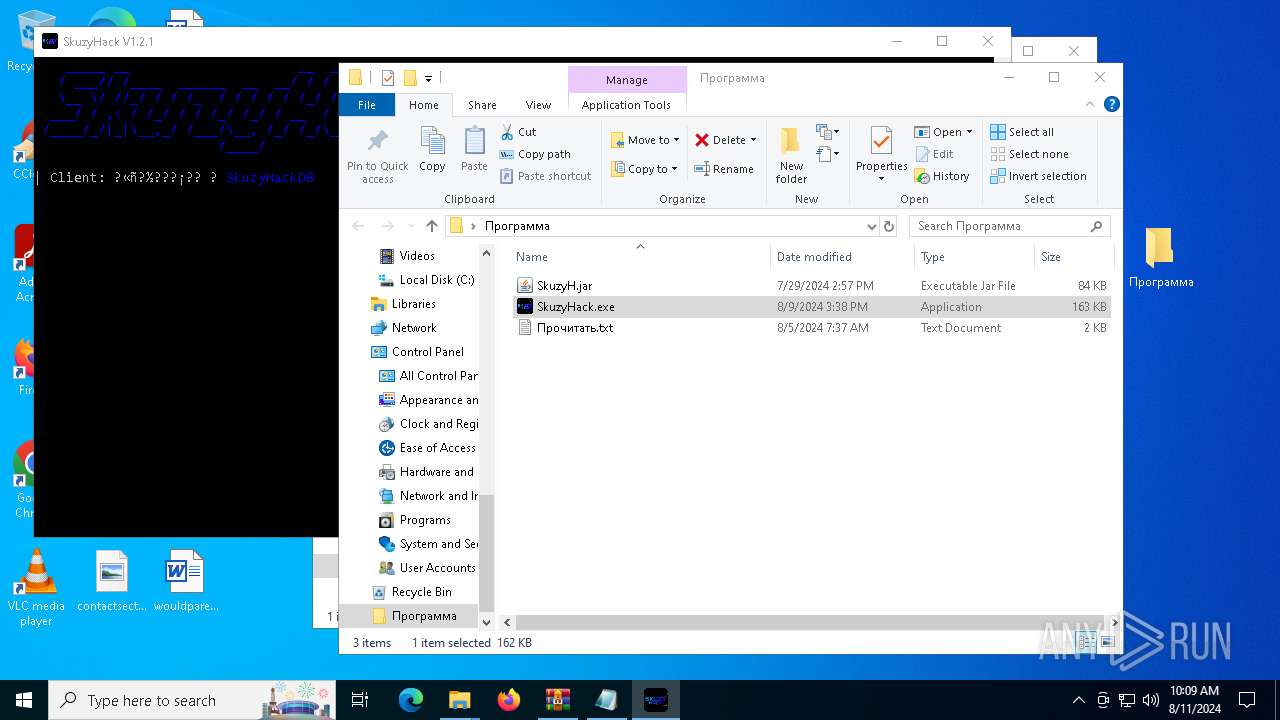
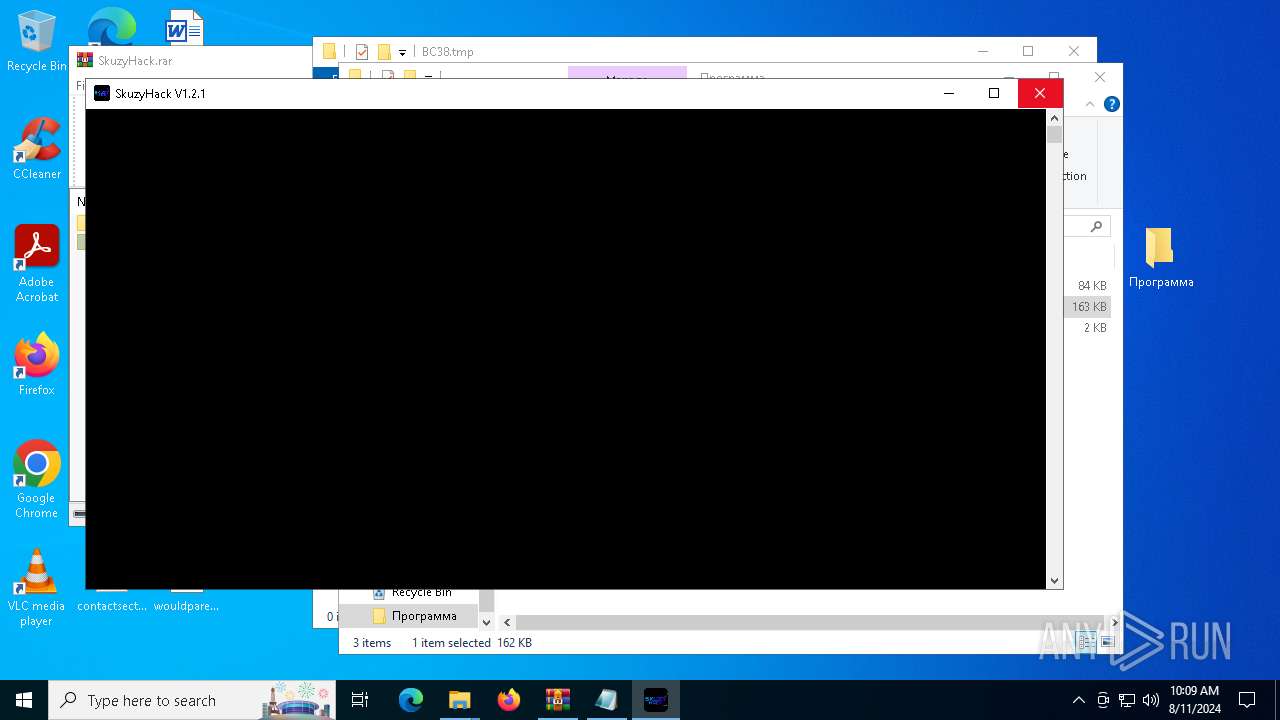
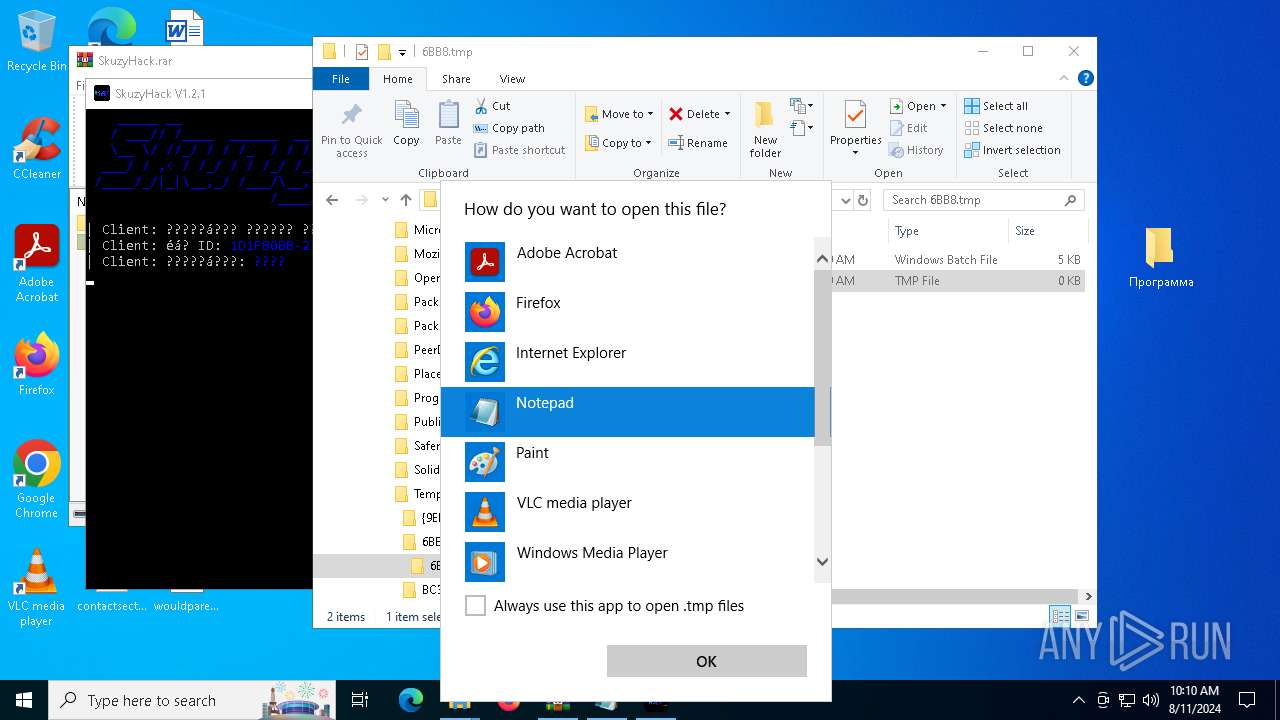
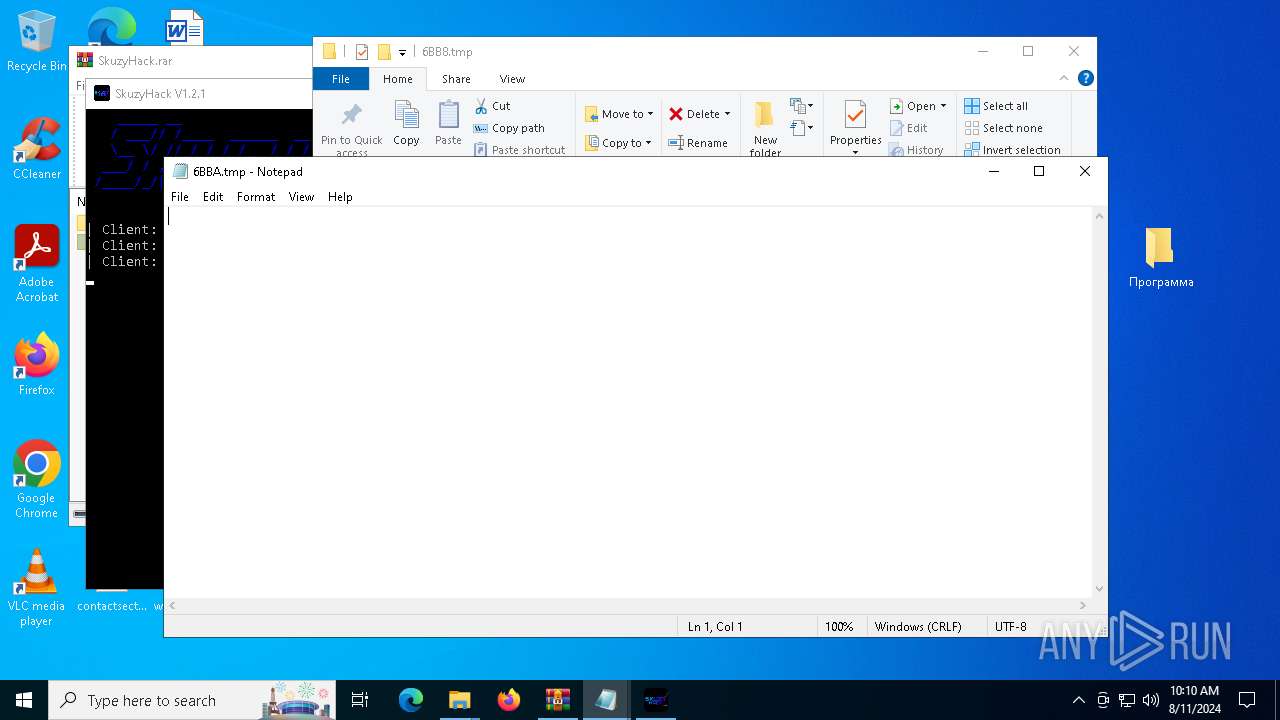
Manual execution by a user
- notepad.exe (PID: 6720)
- SkuzyHack.exe (PID: 6916)
- SkuzyHack.exe (PID: 2628)
- SkuzyHack.exe (PID: 7544)
- SkuzyHack.exe (PID: 6412)
- cmd.exe (PID: 6272)
- notepad.exe (PID: 7068)
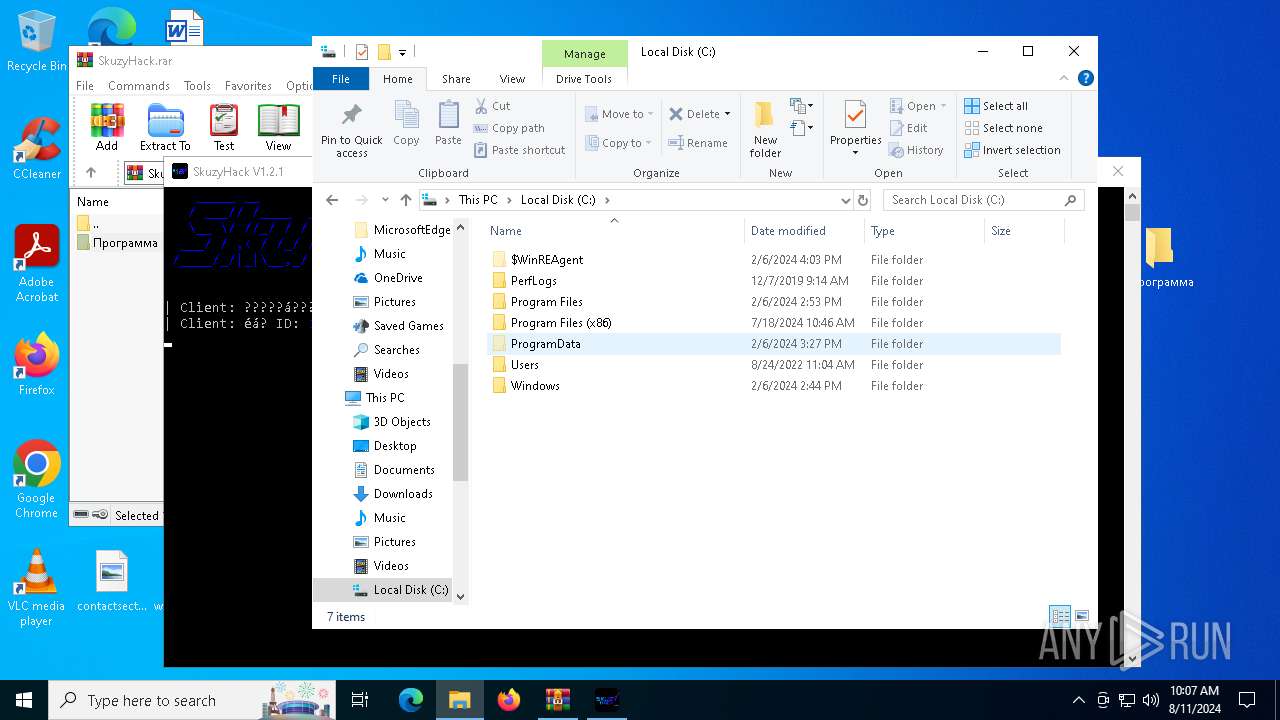
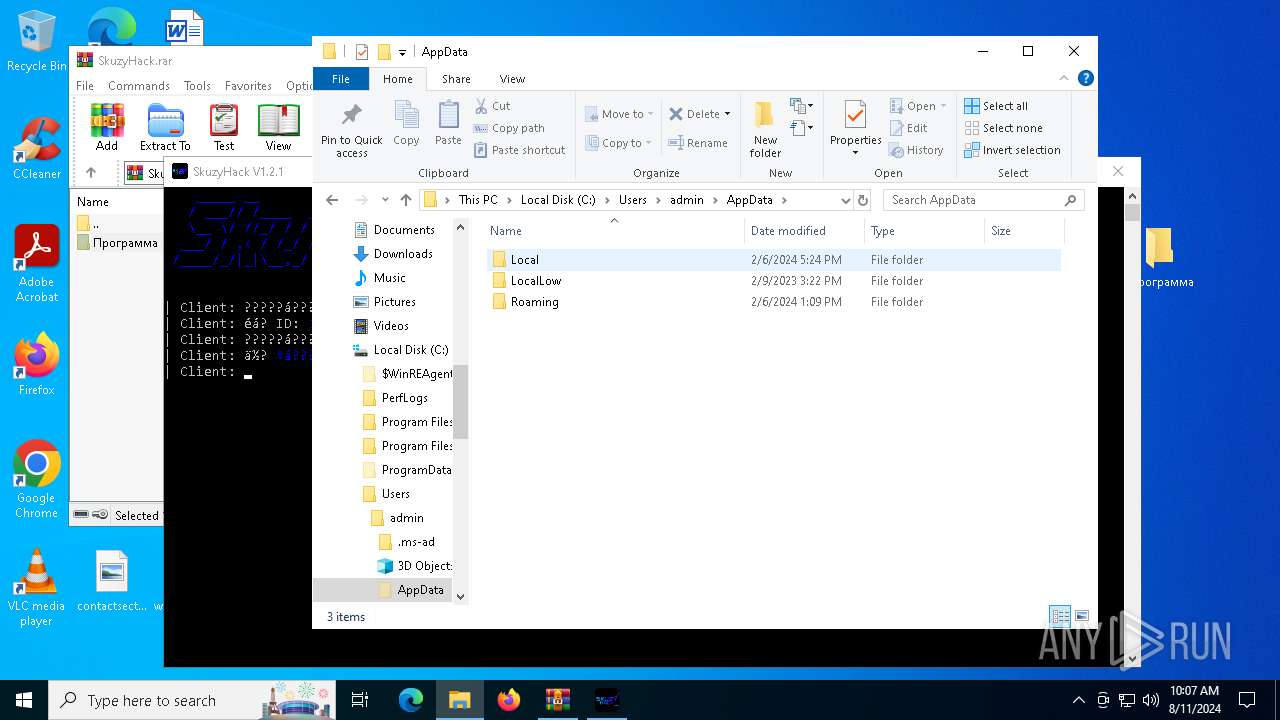
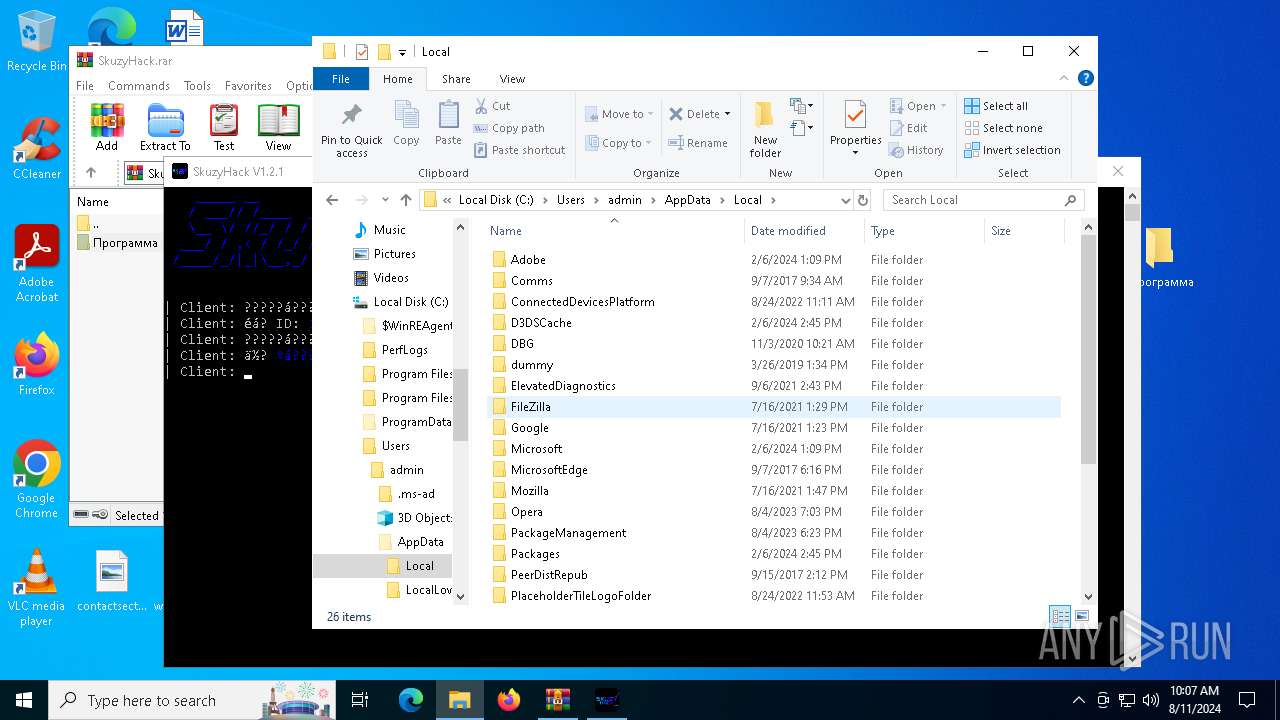
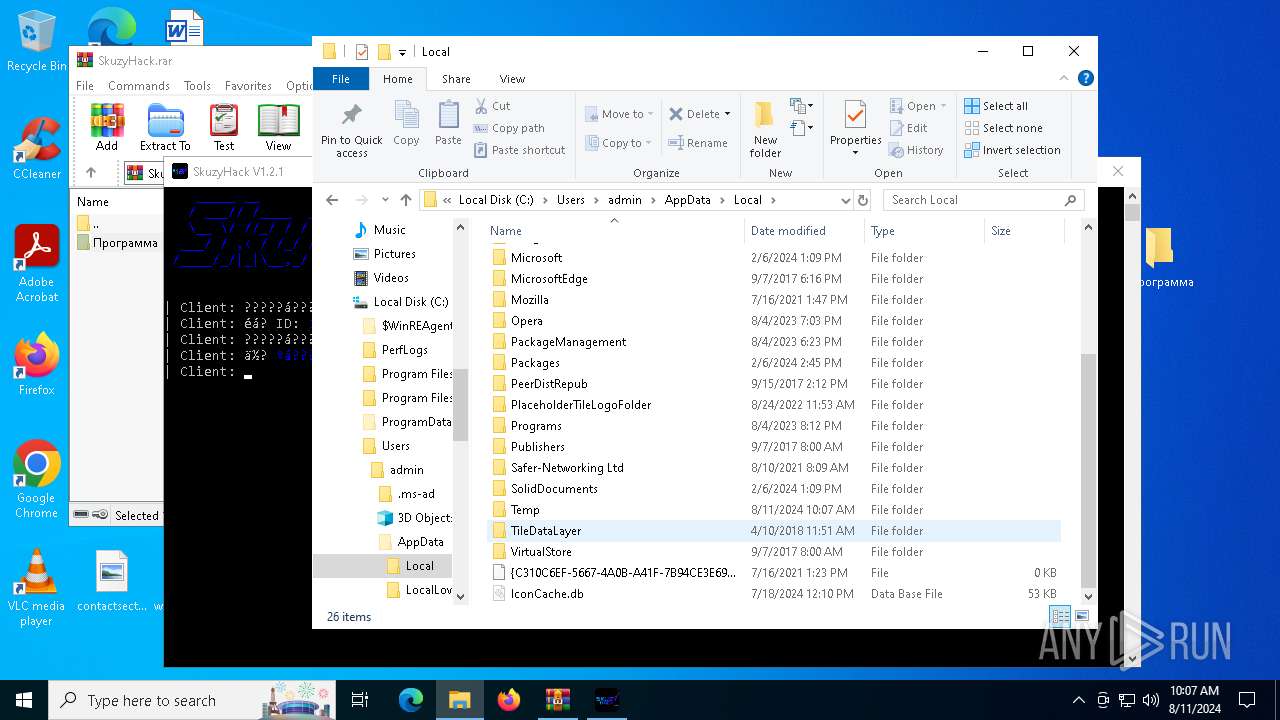
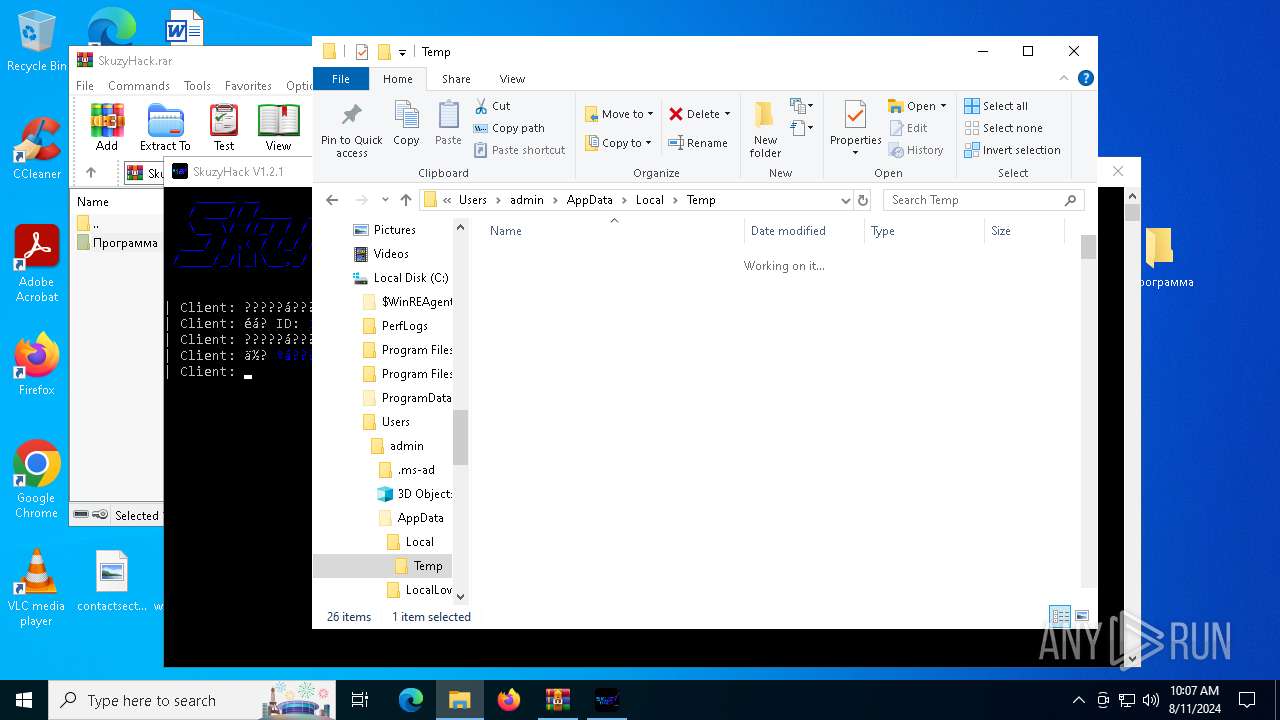
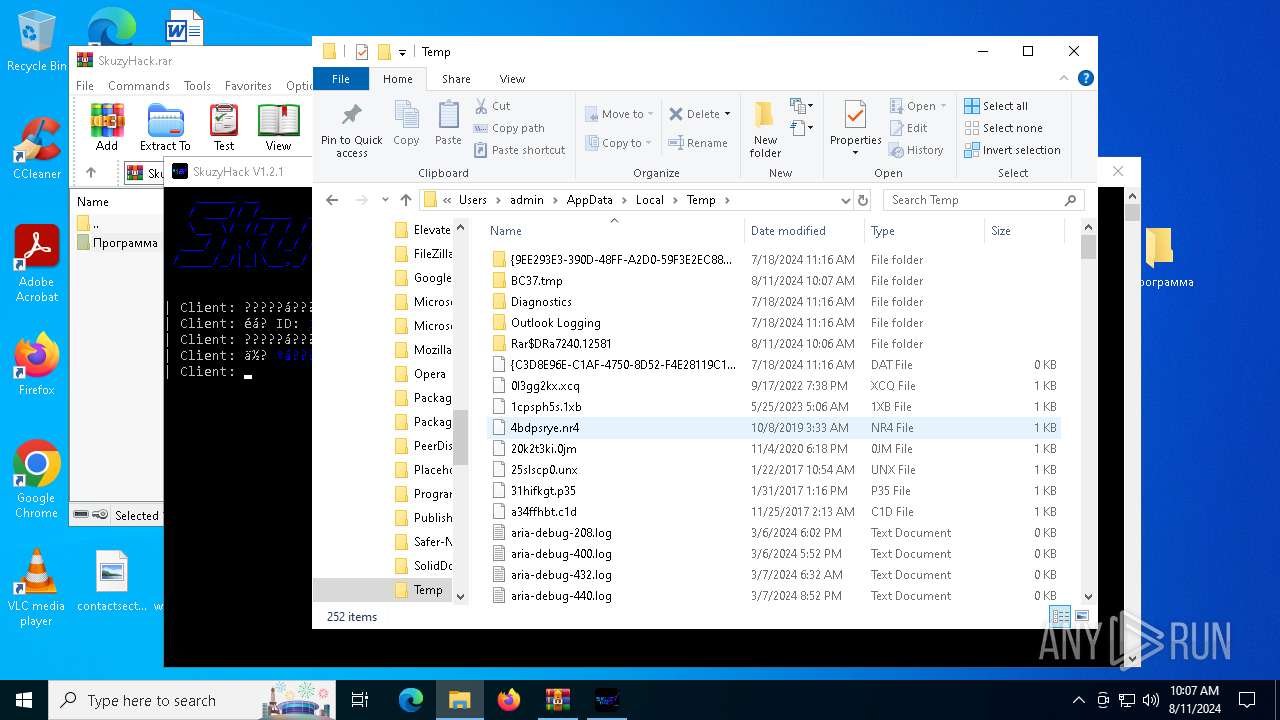
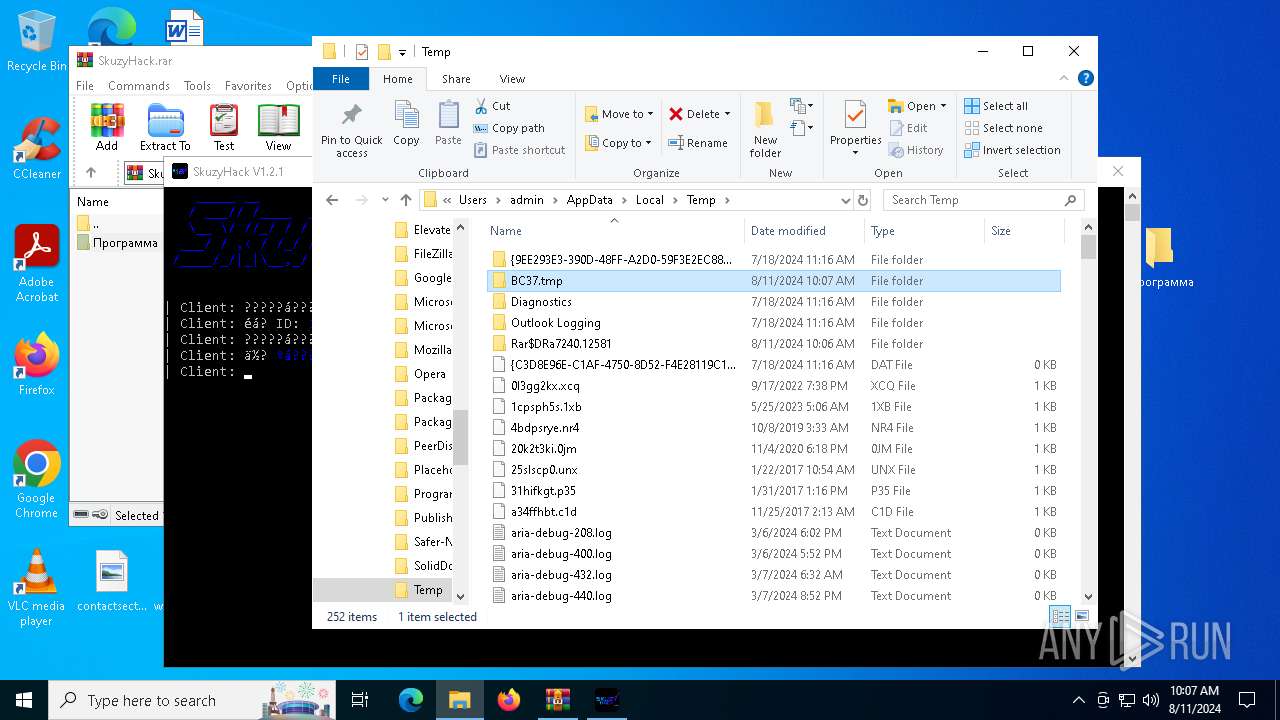
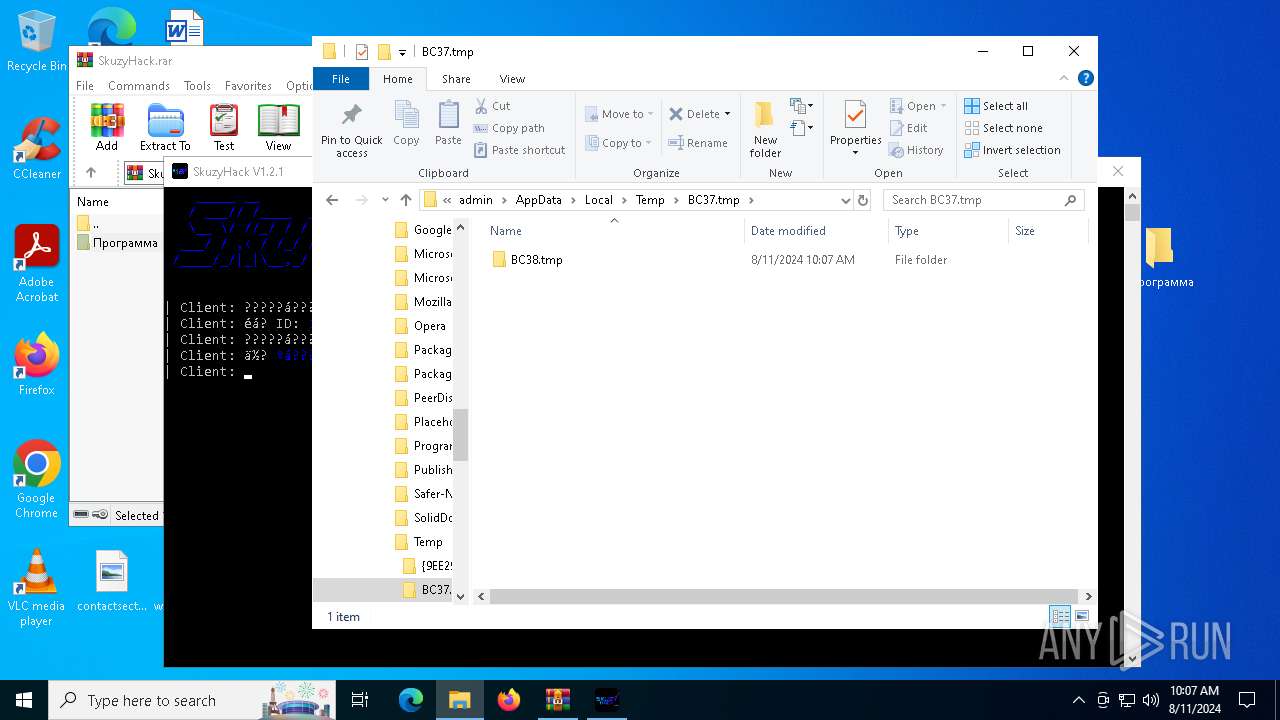
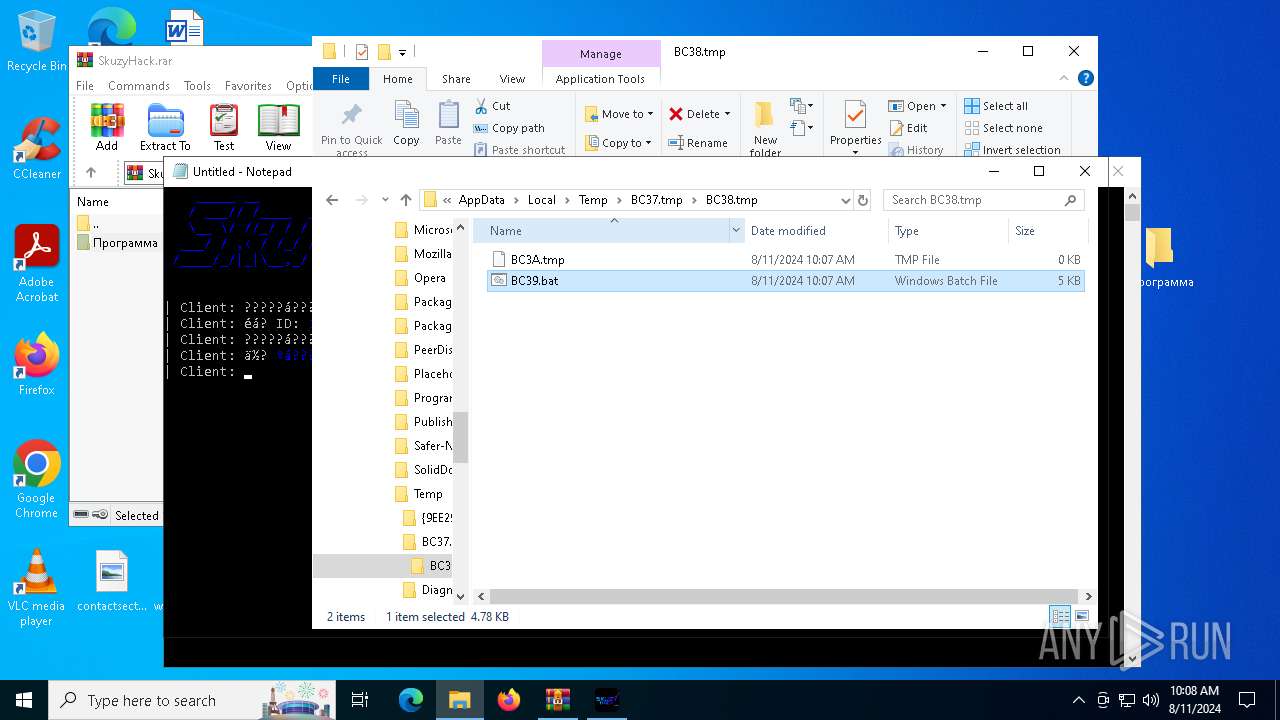
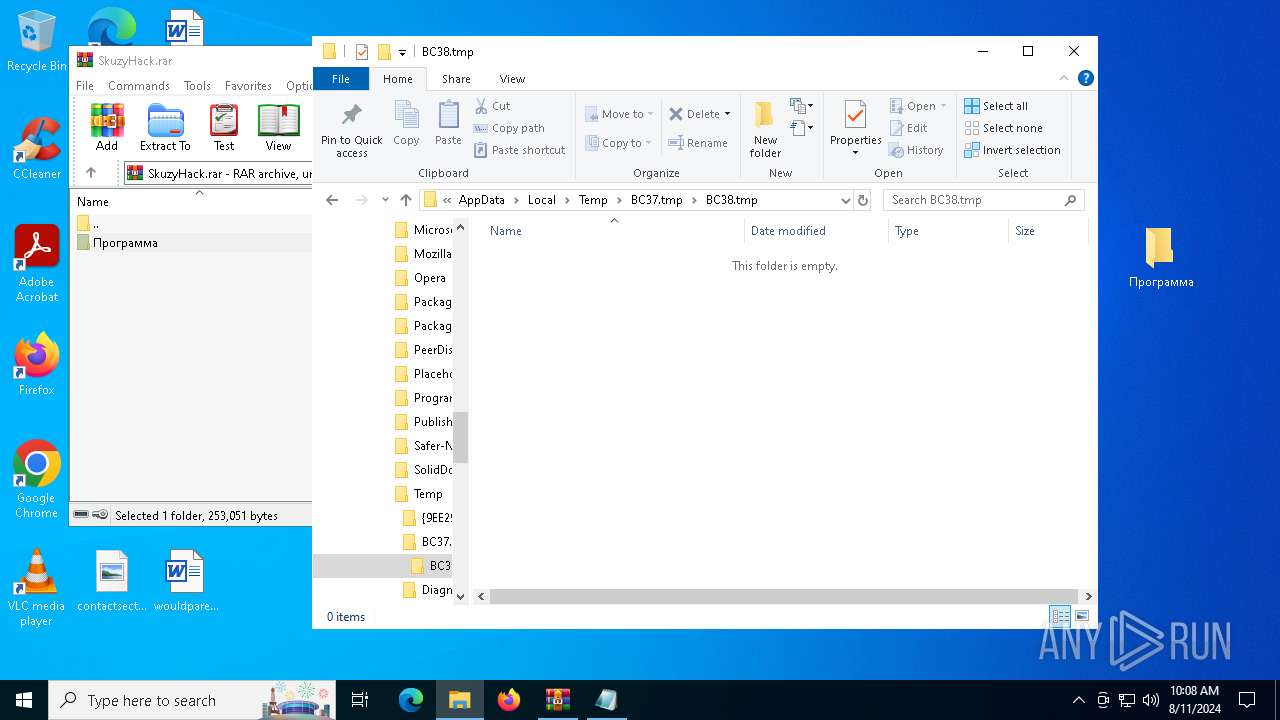
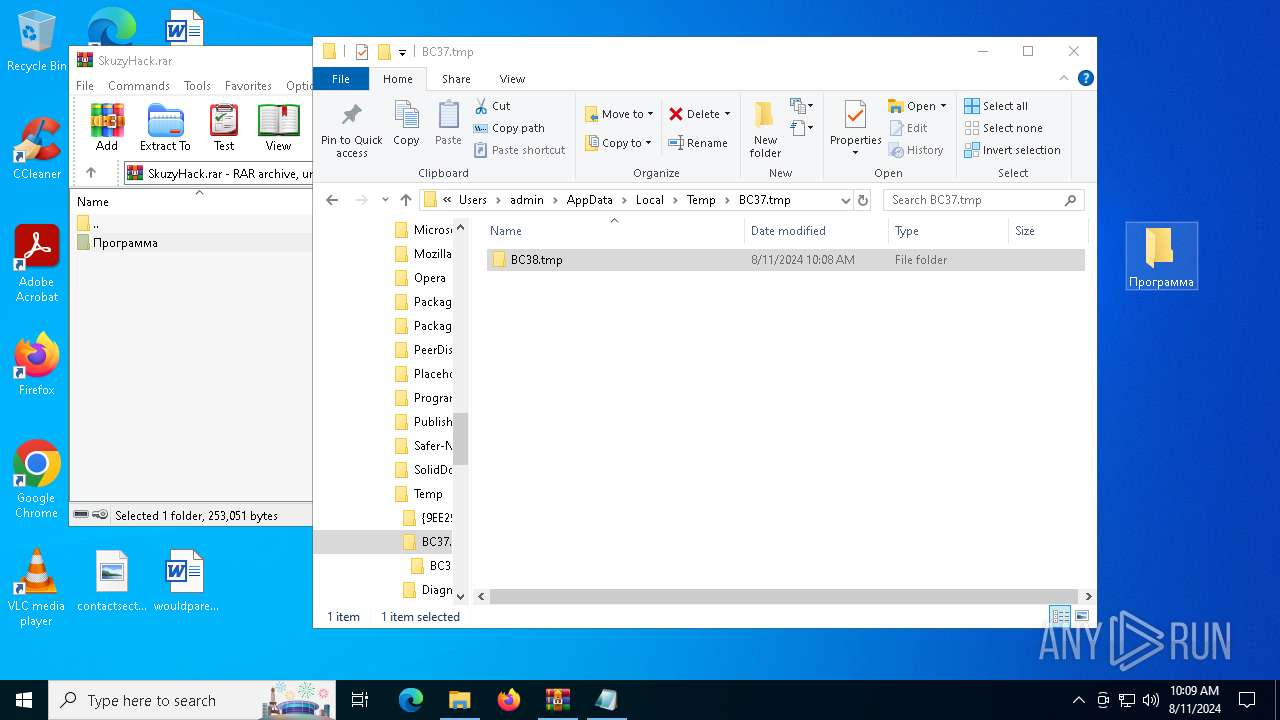
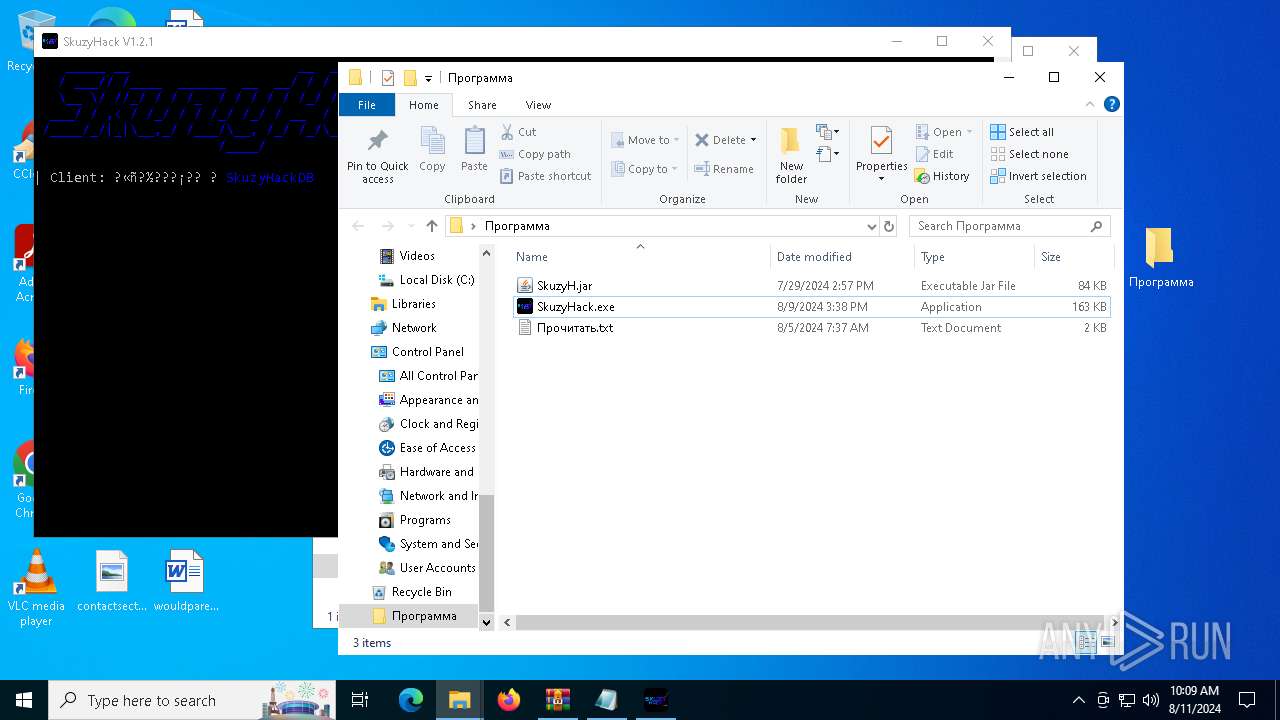
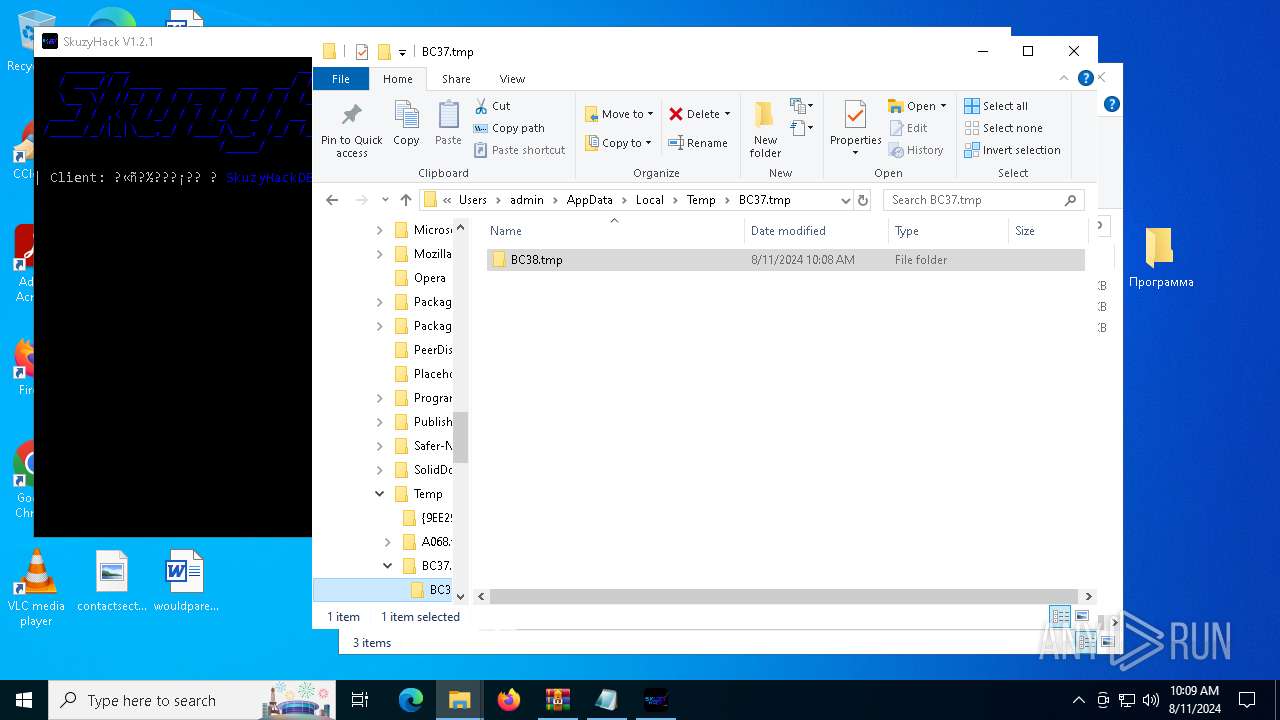
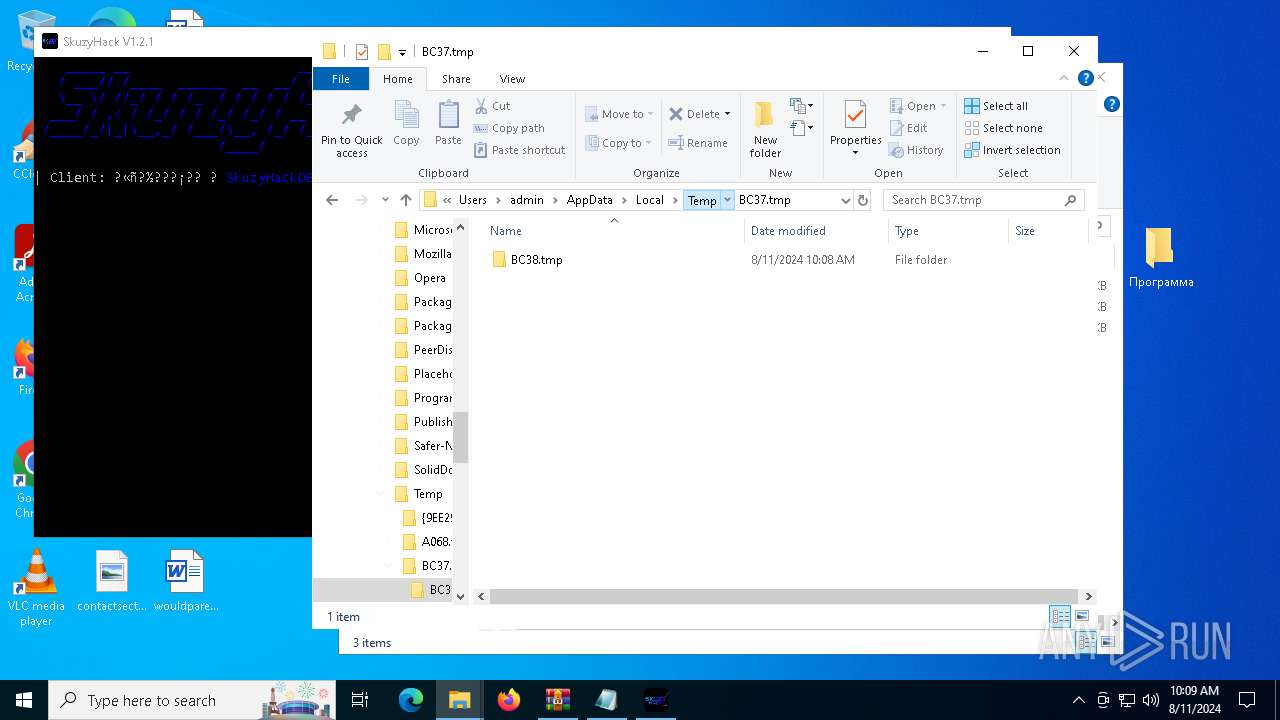
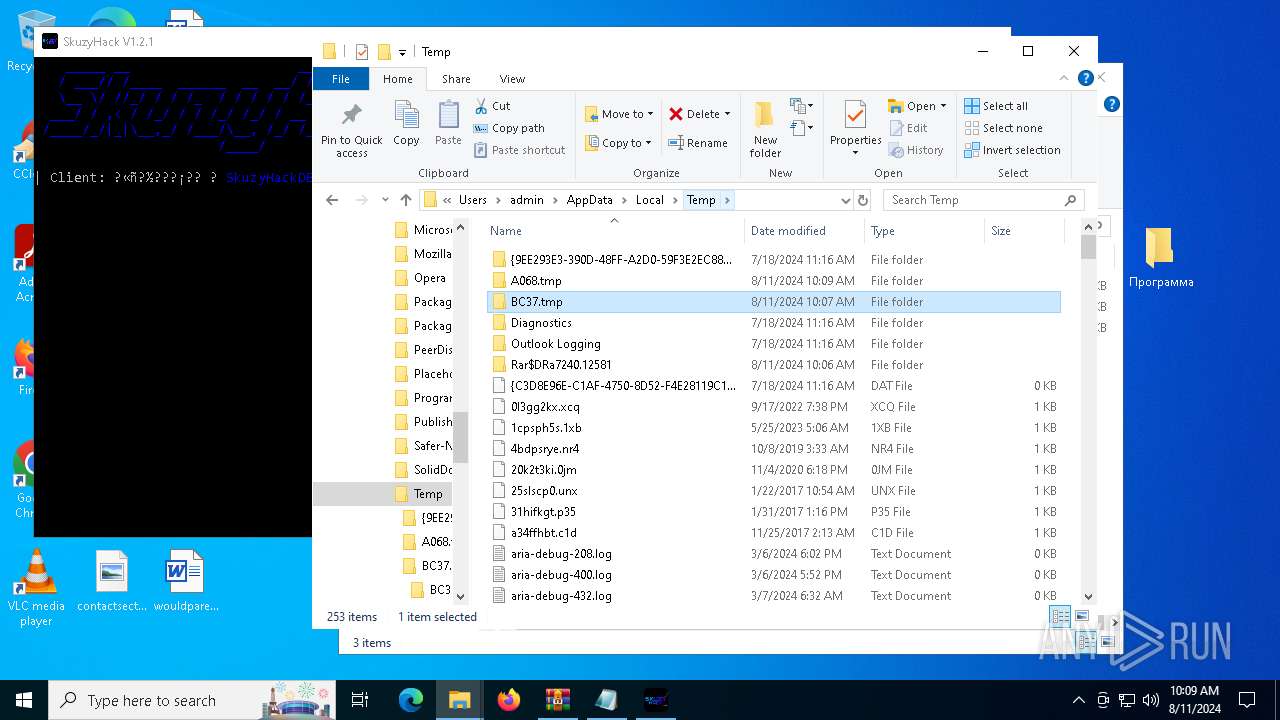
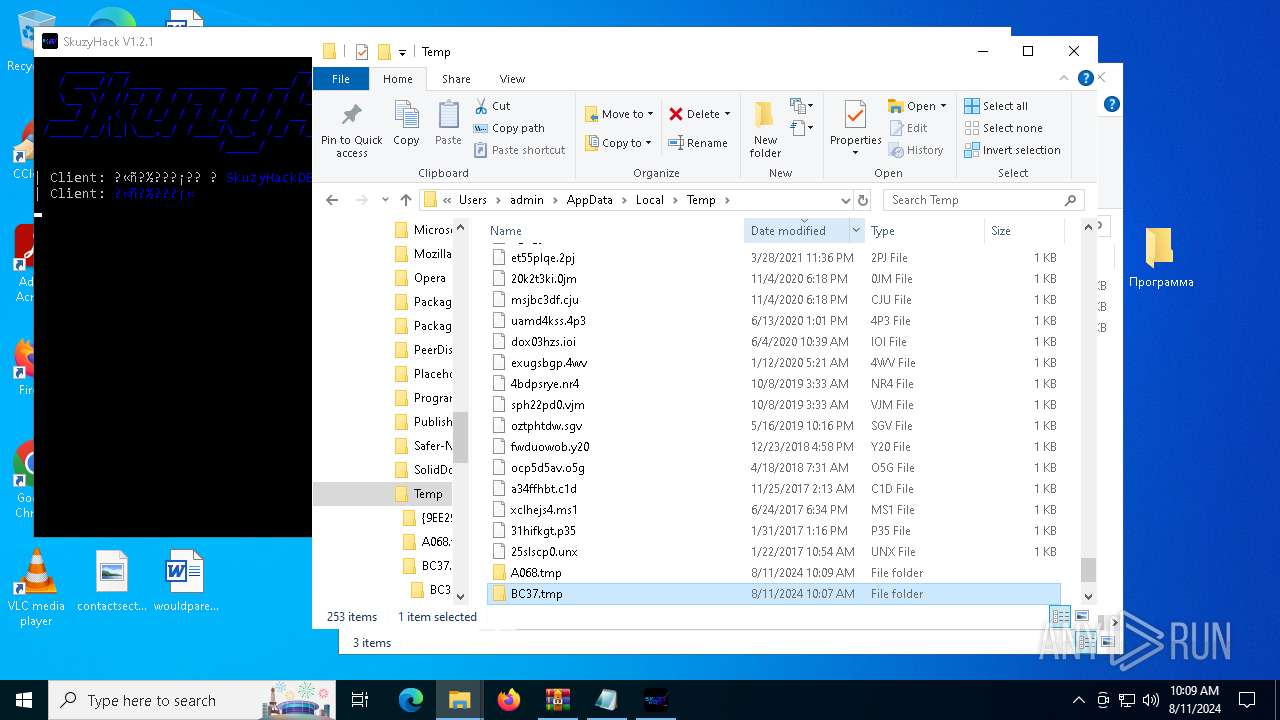
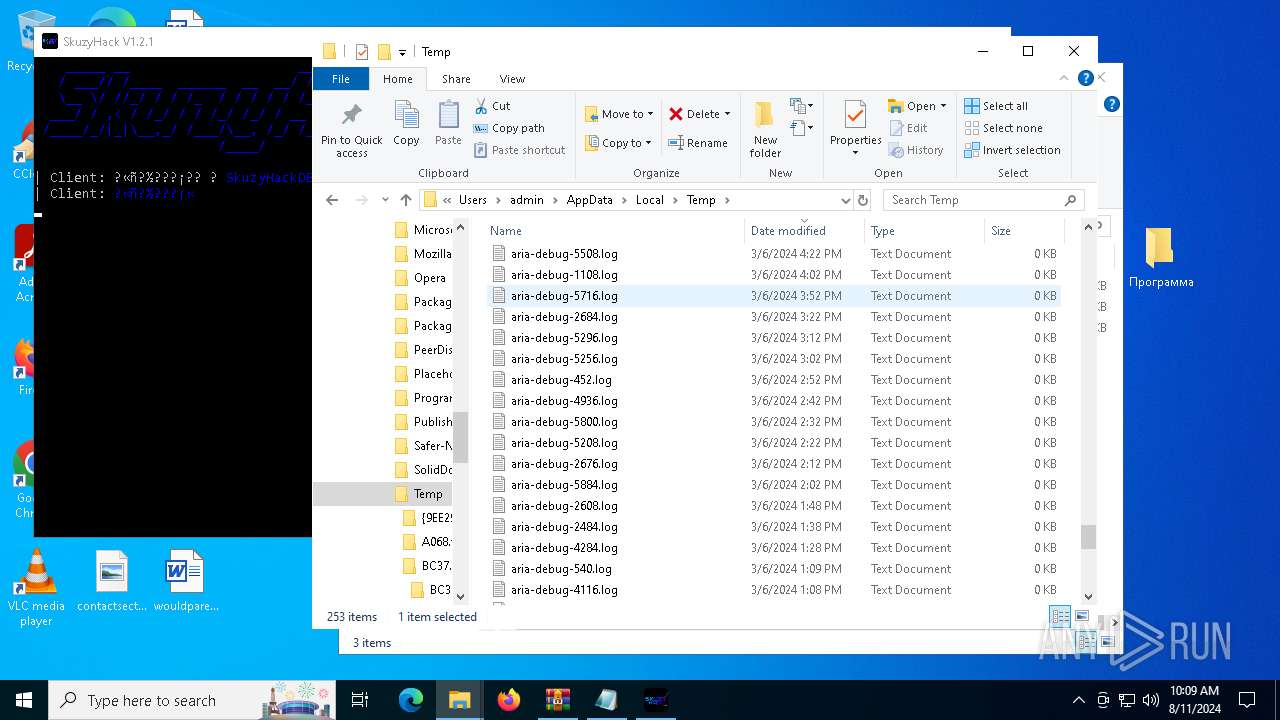
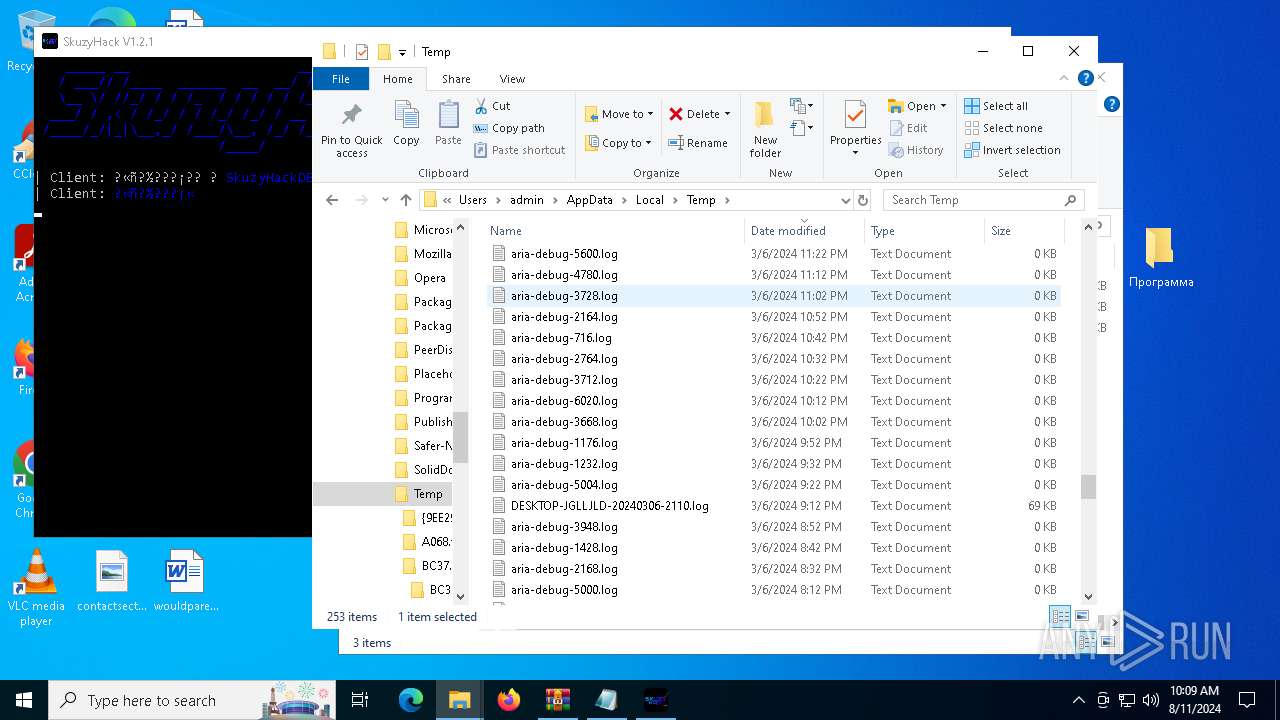
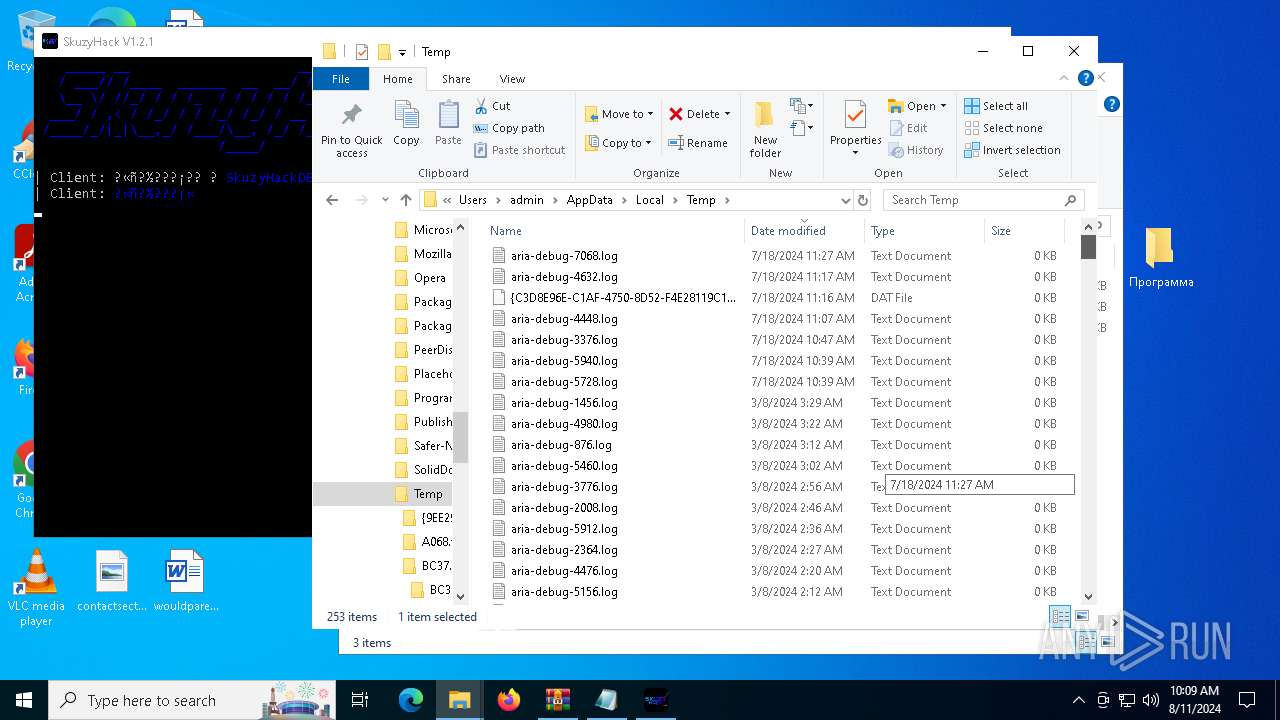
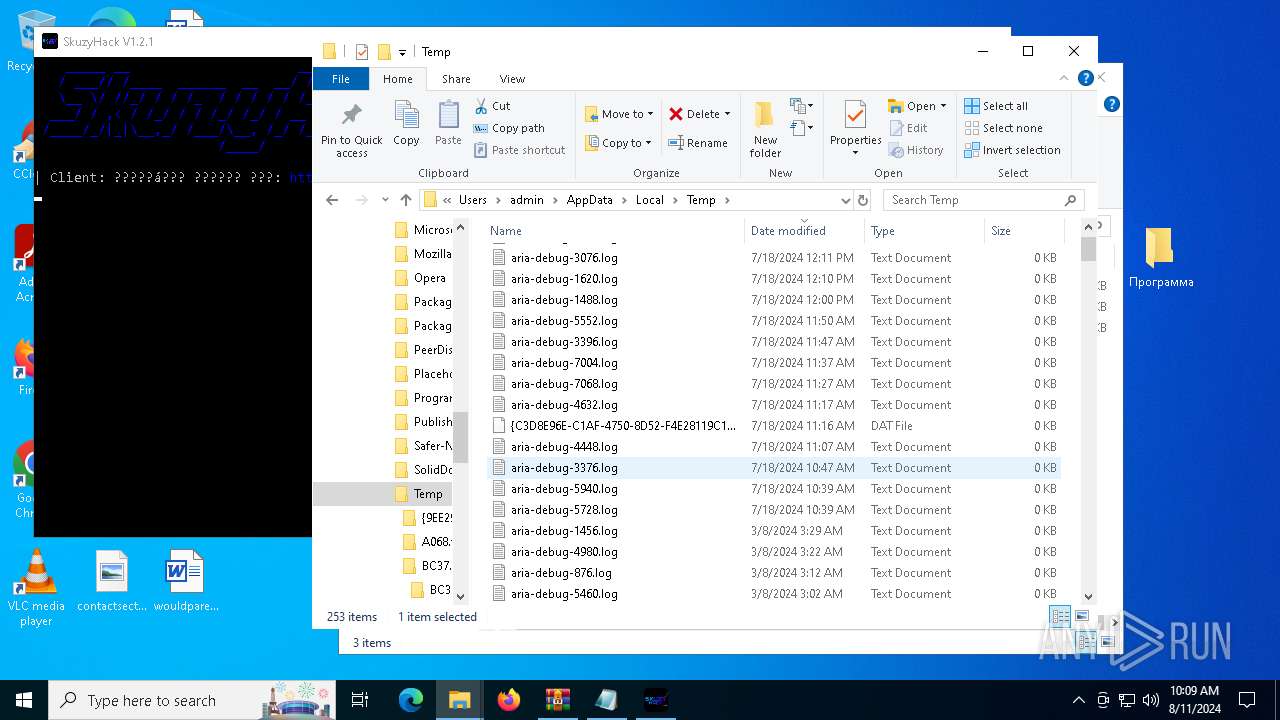
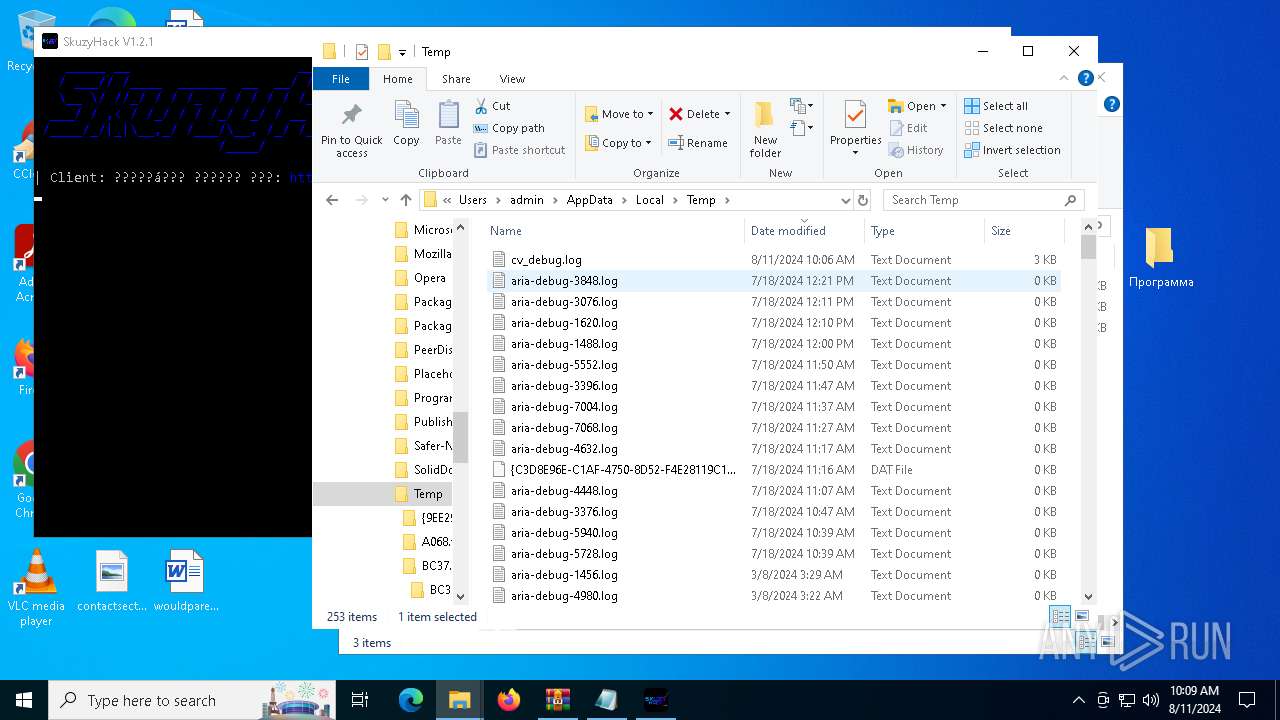
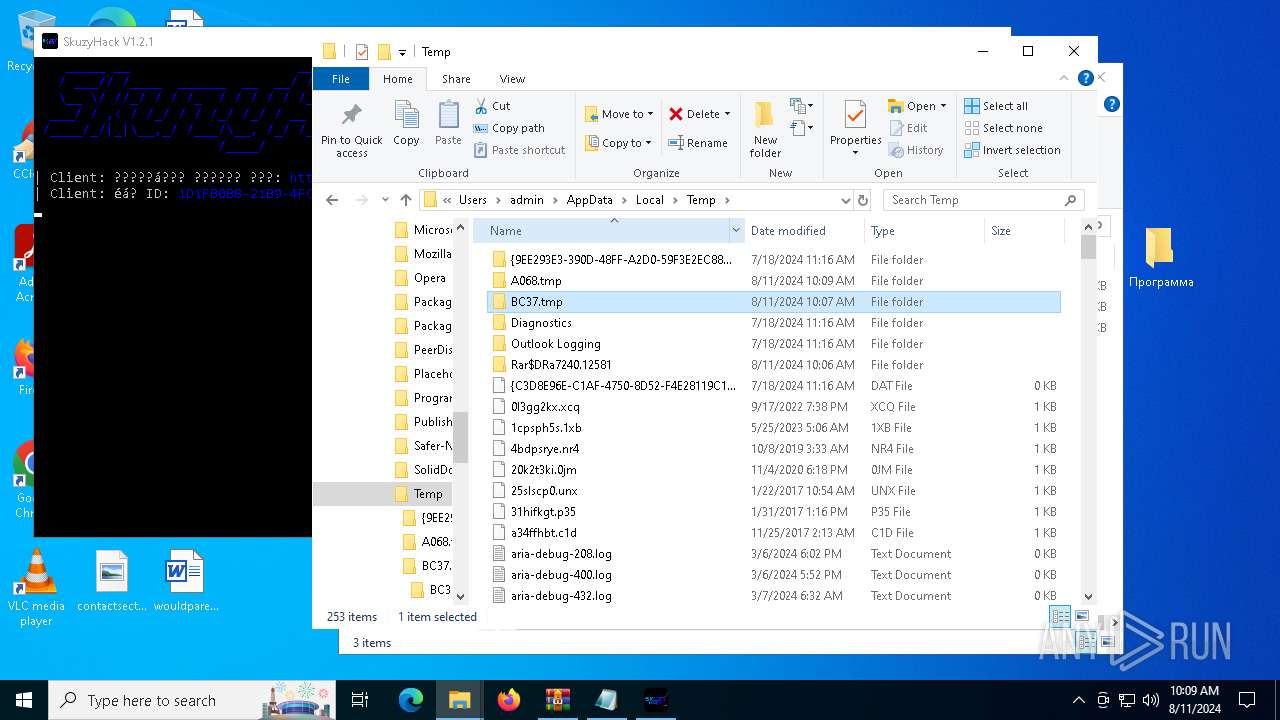
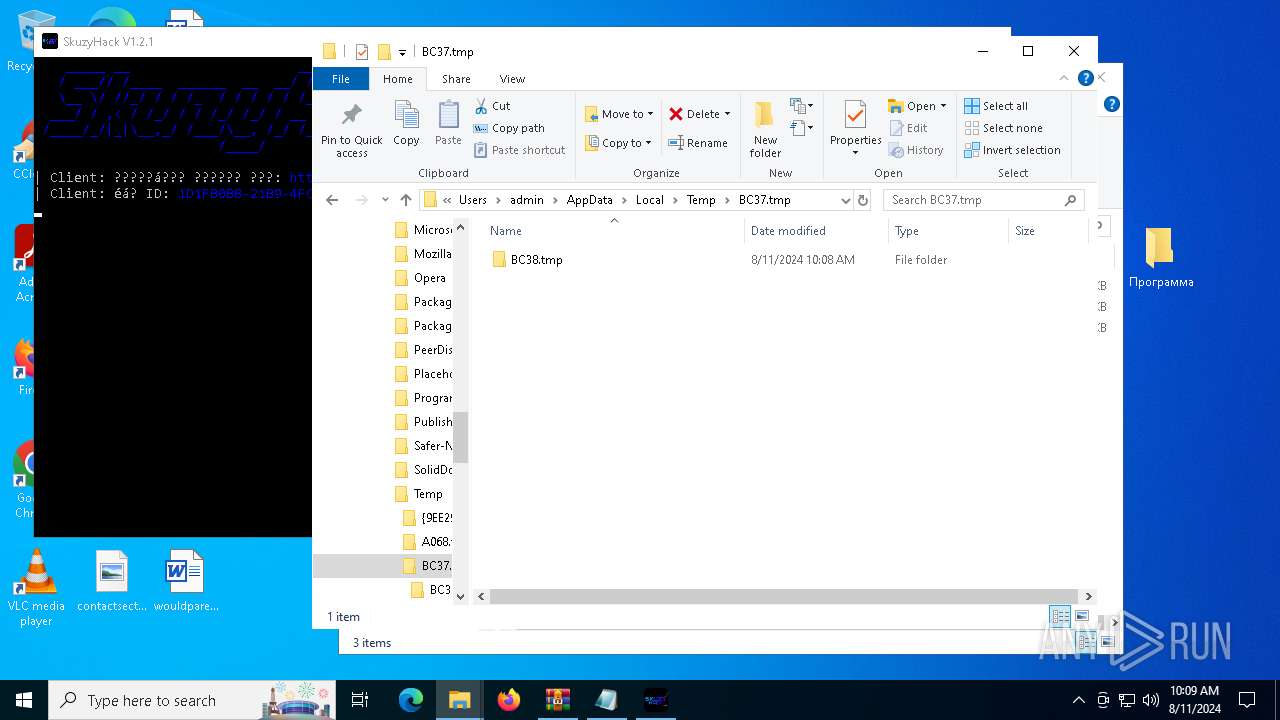
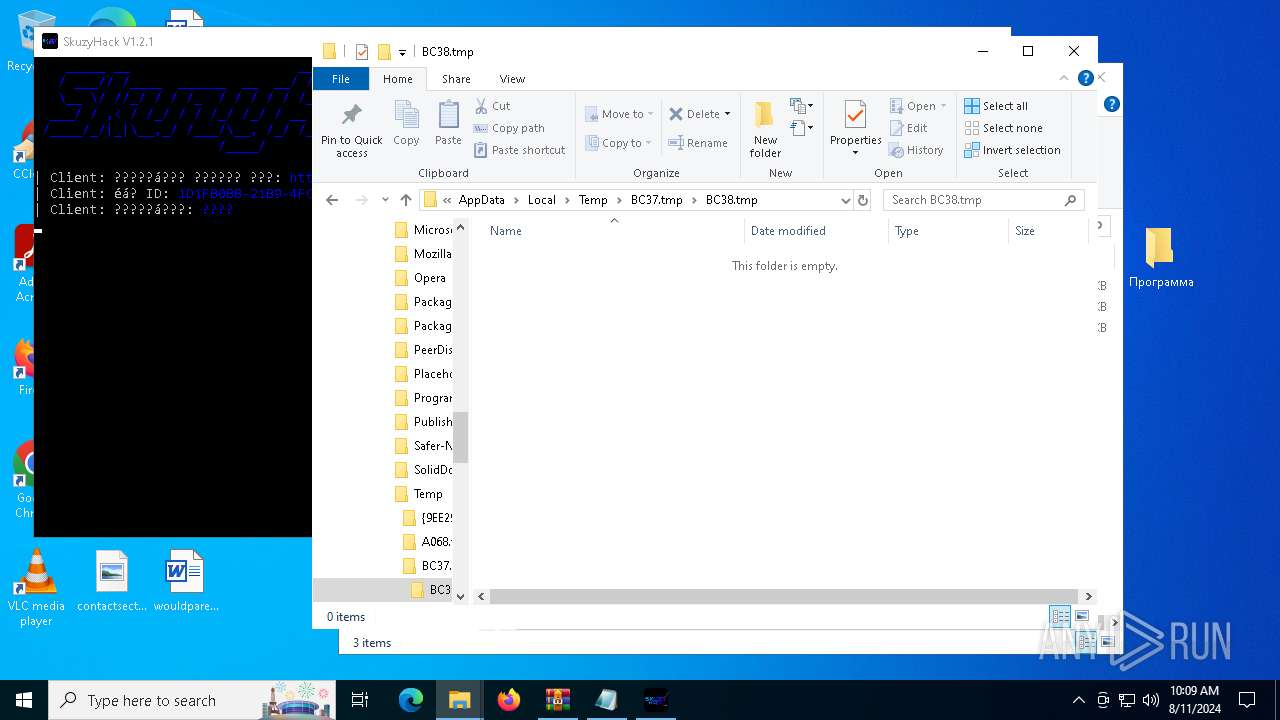
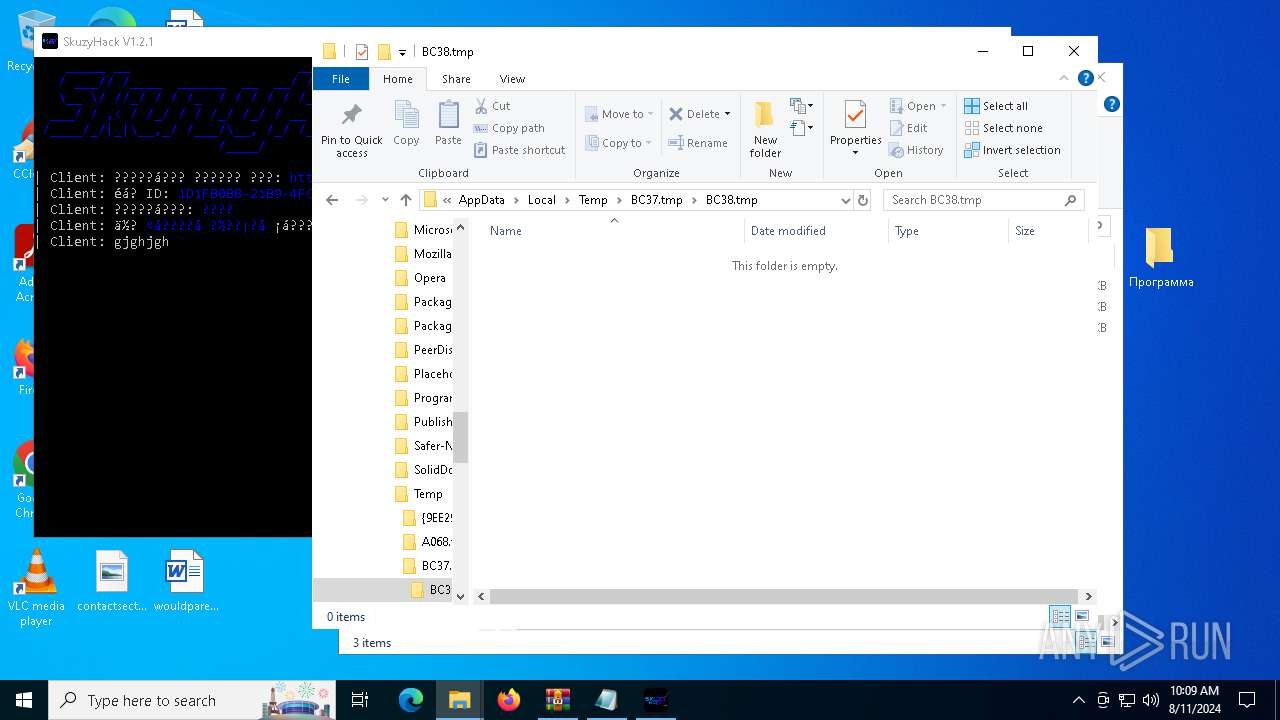
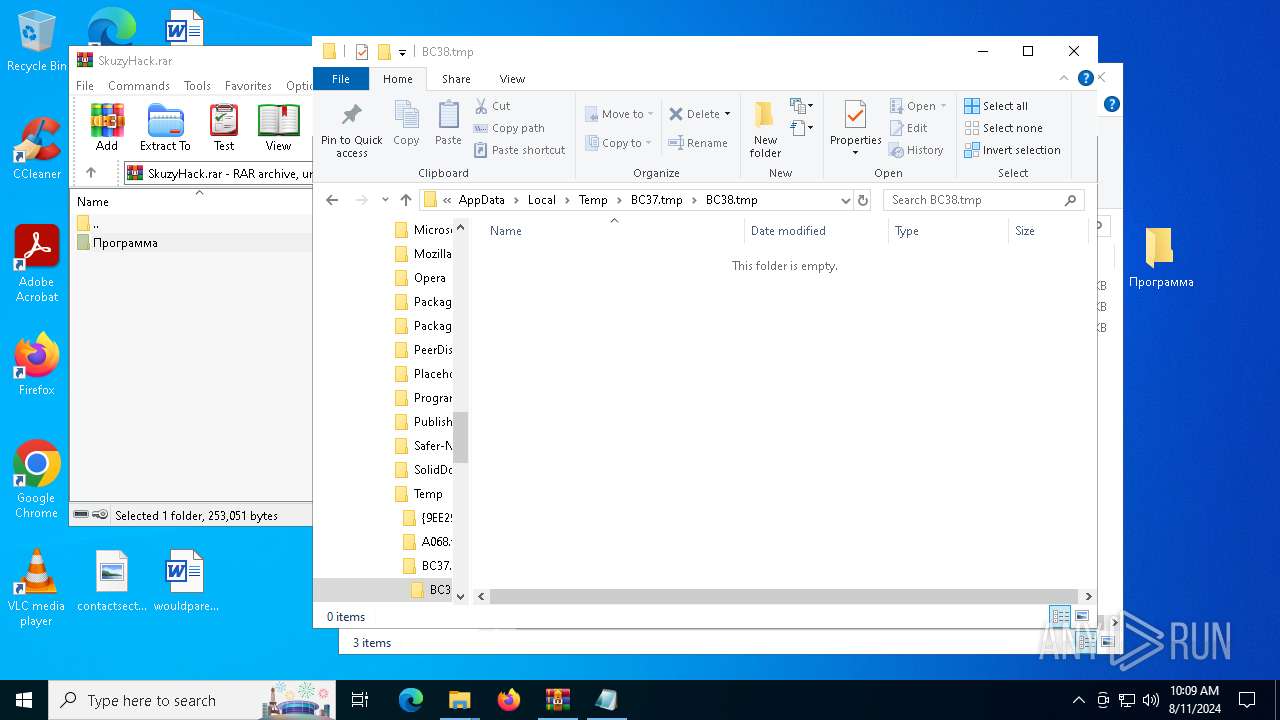
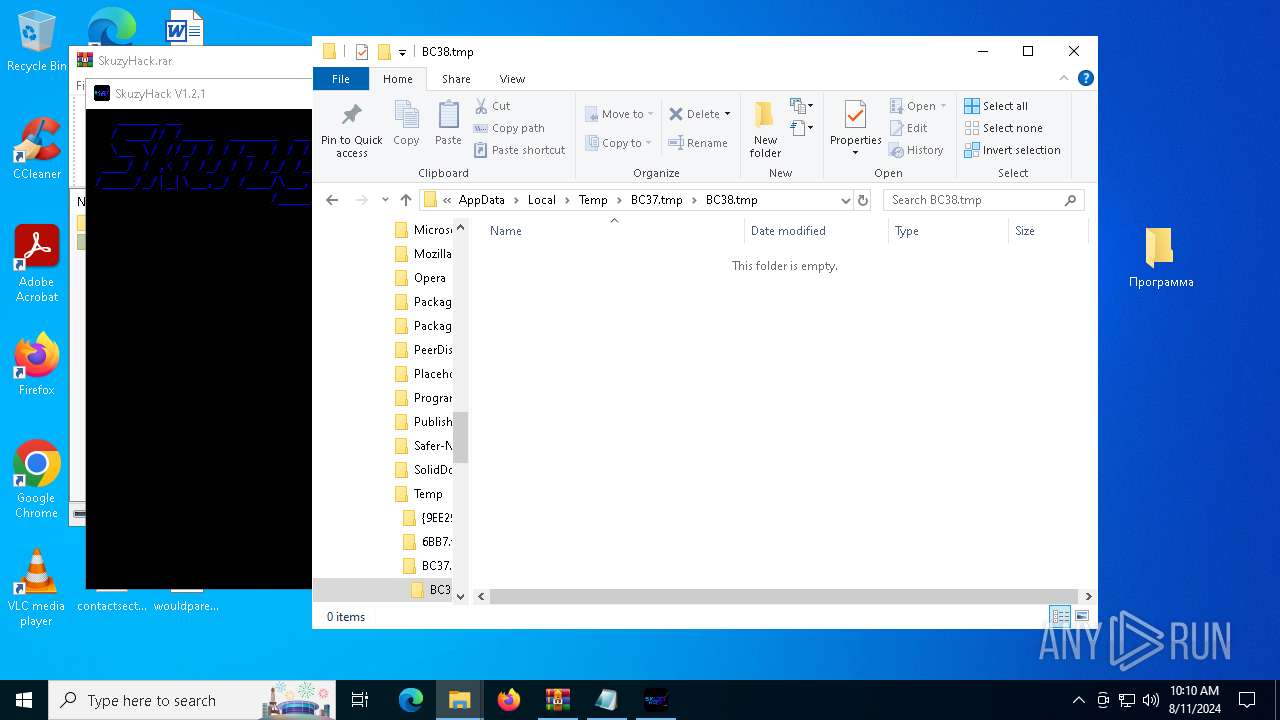
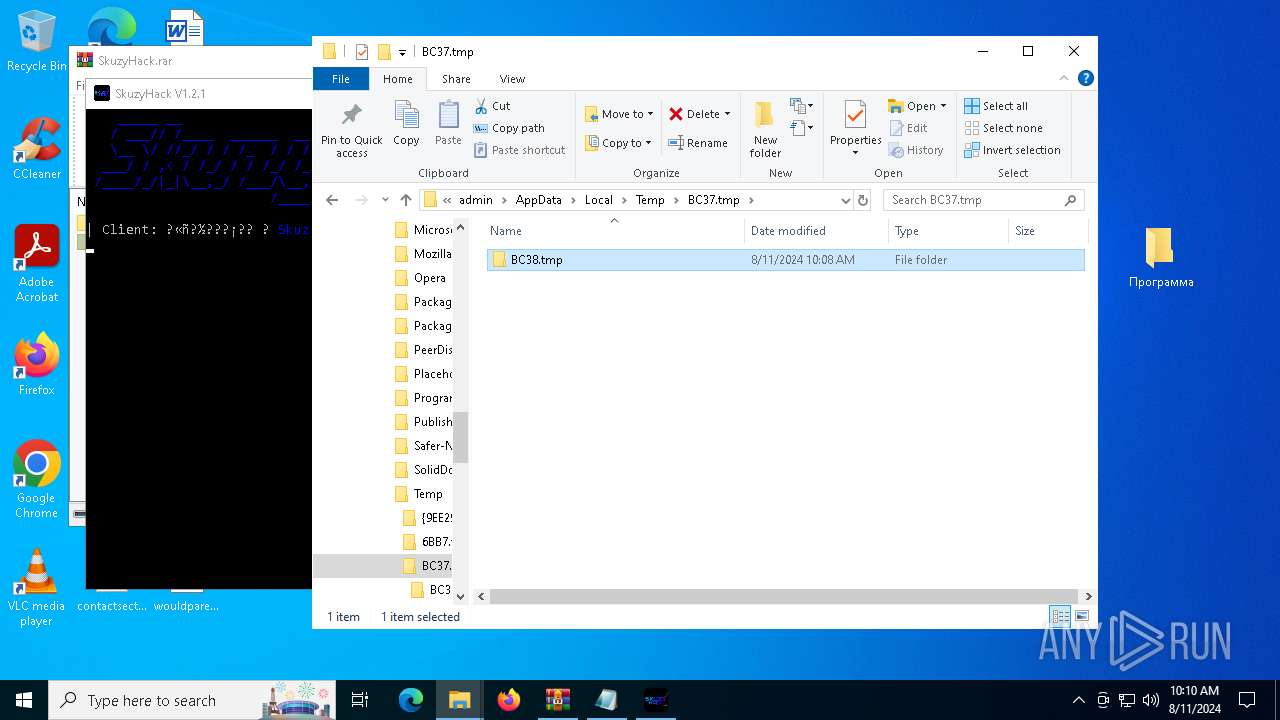
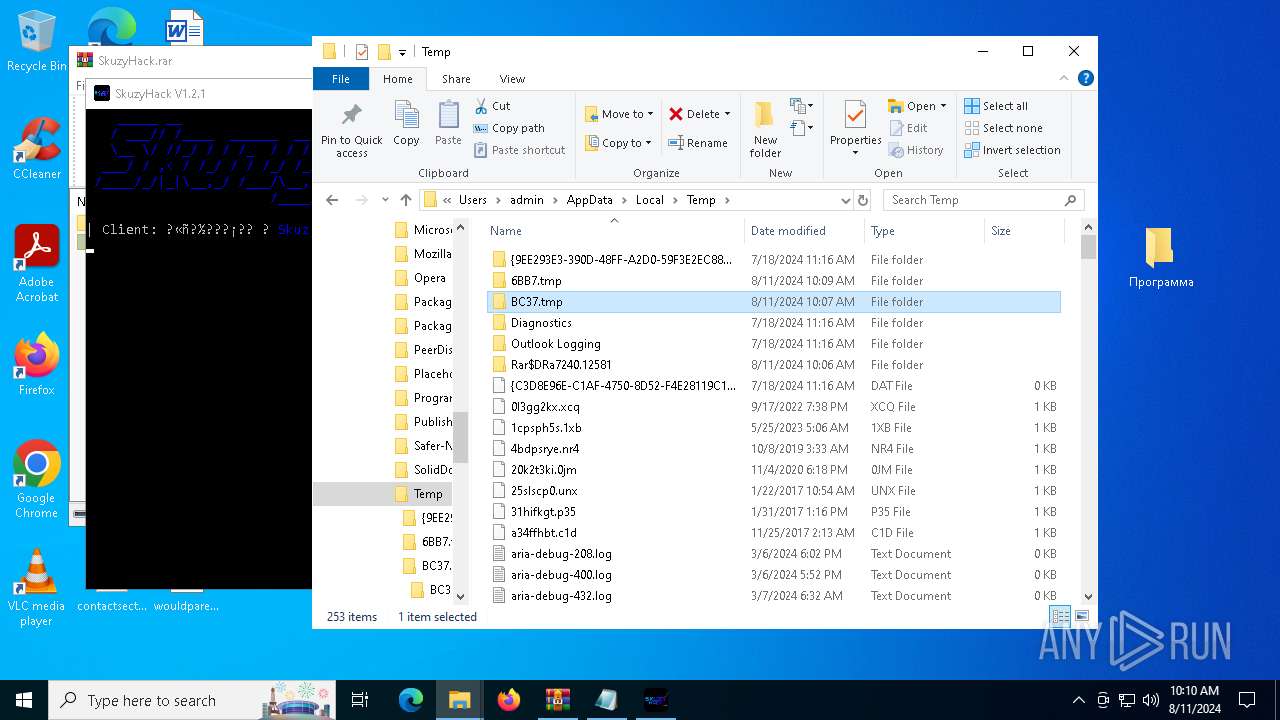
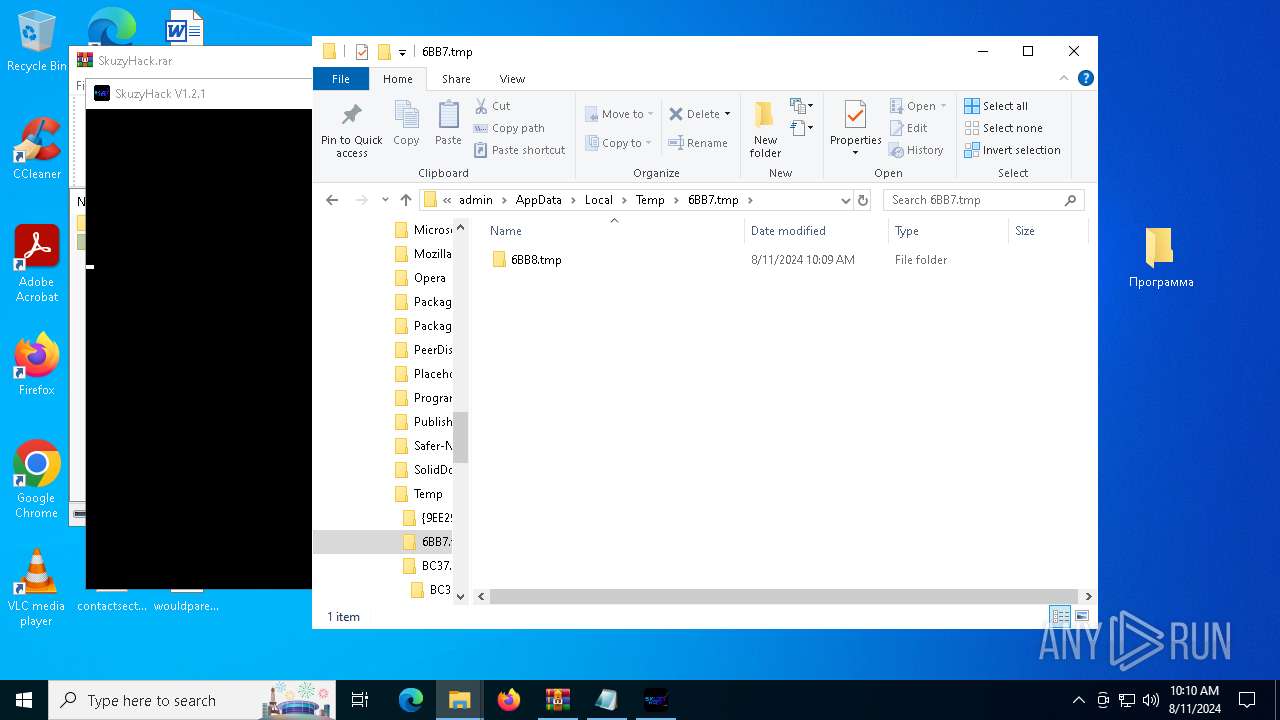
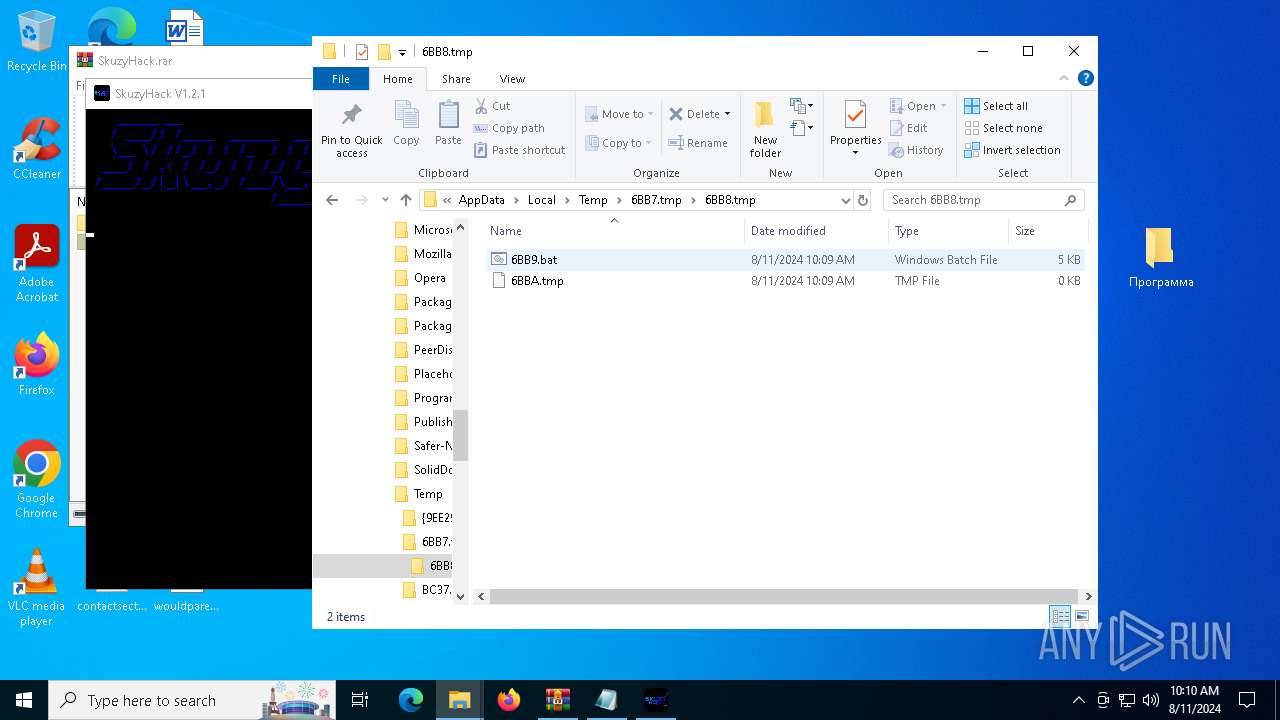
Create files in a temporary directory
- SkuzyHack.exe (PID: 6916)
- SkuzyHack.exe (PID: 2628)
- SkuzyHack.exe (PID: 7544)
- SkuzyHack.exe (PID: 6412)
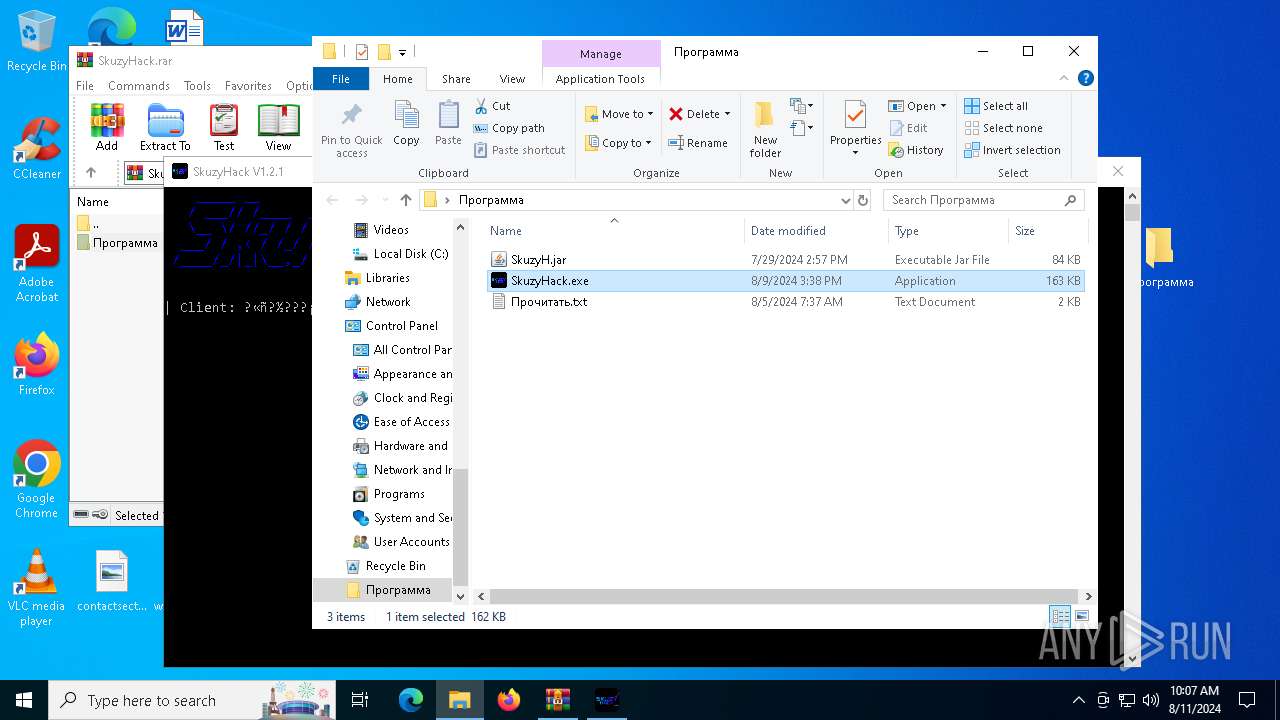
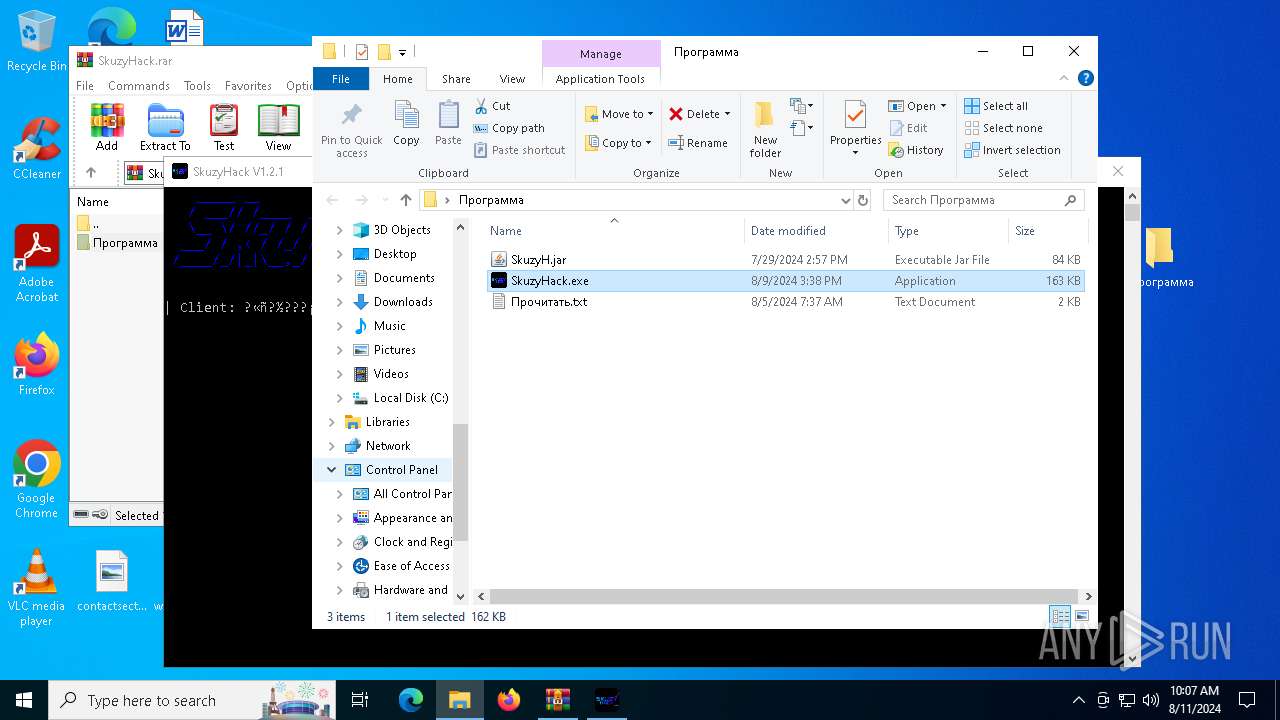
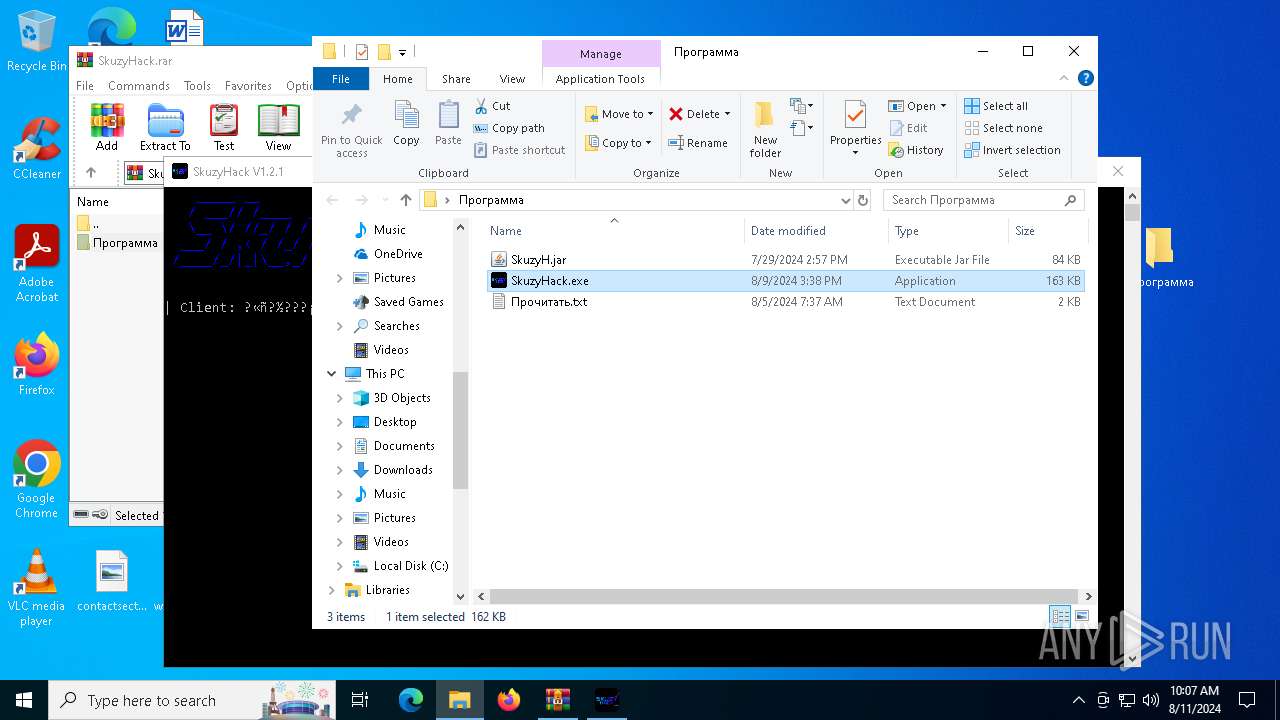
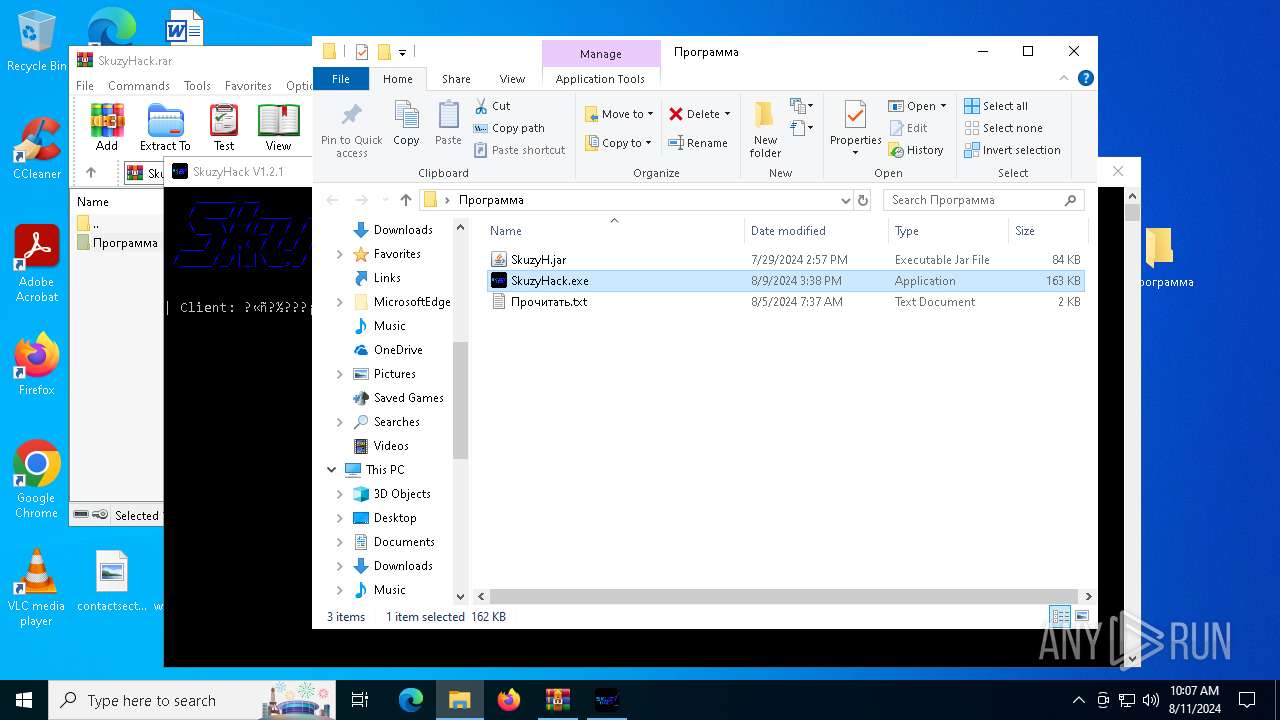
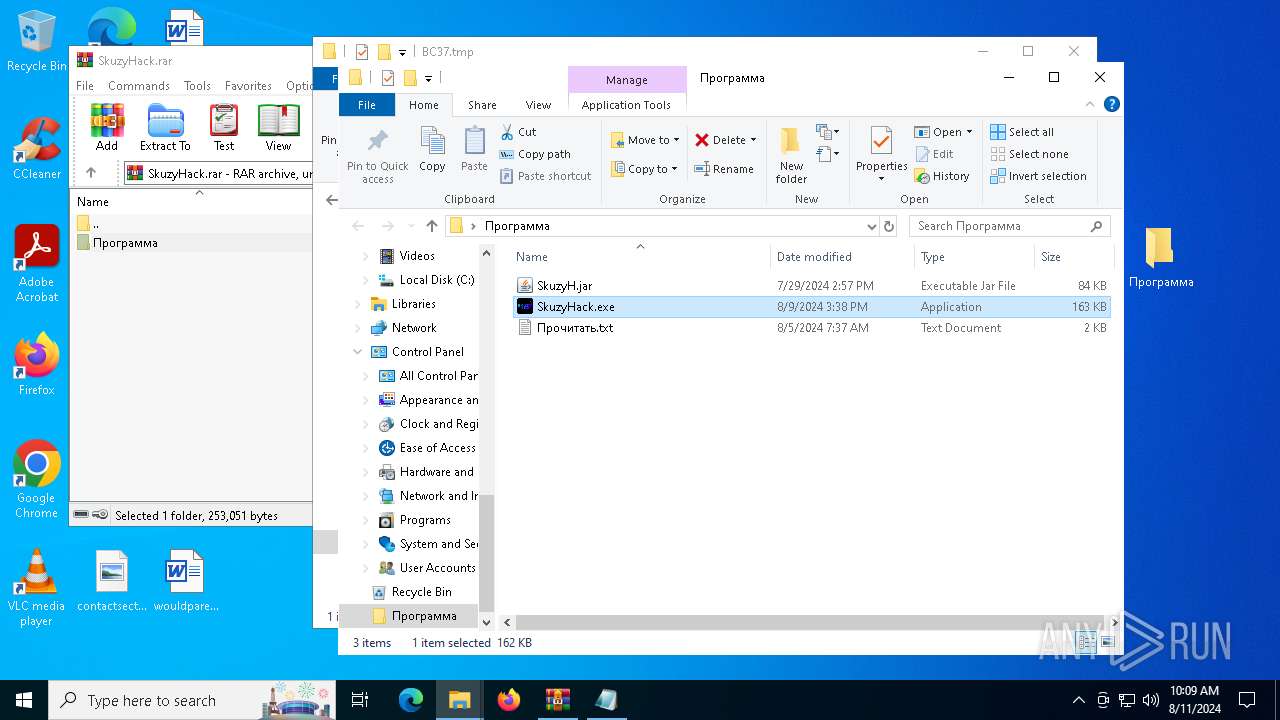
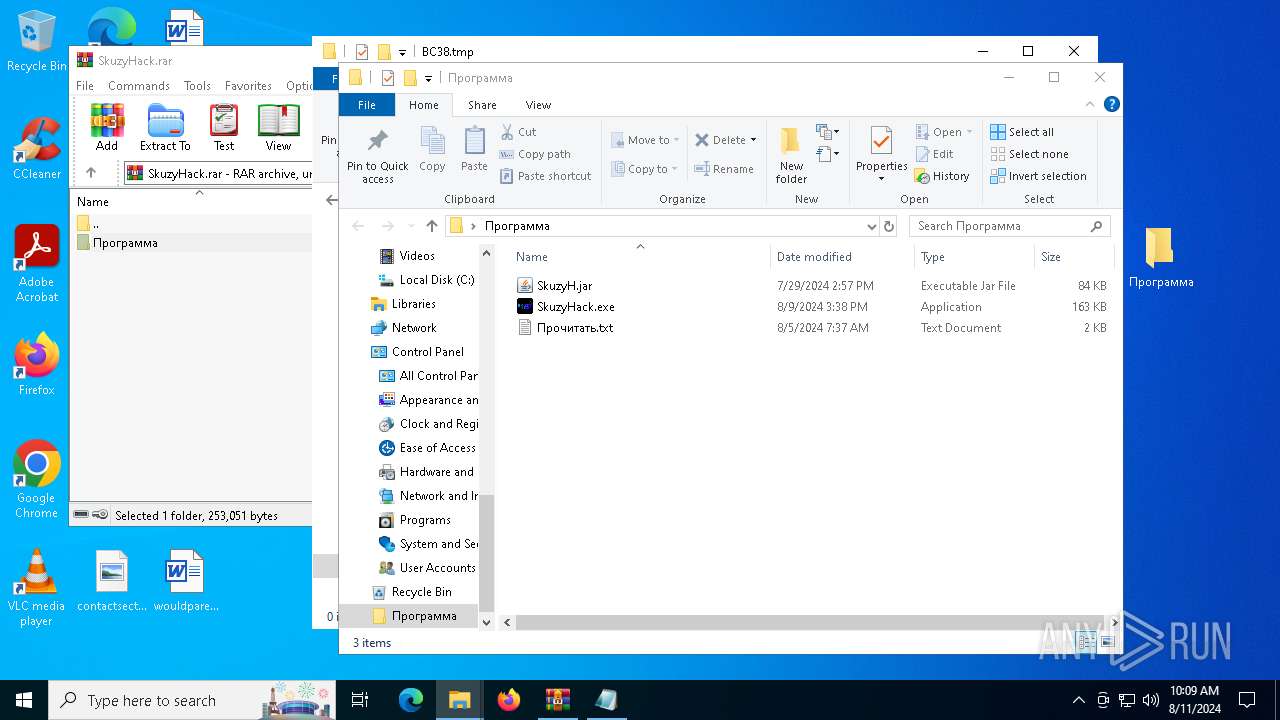
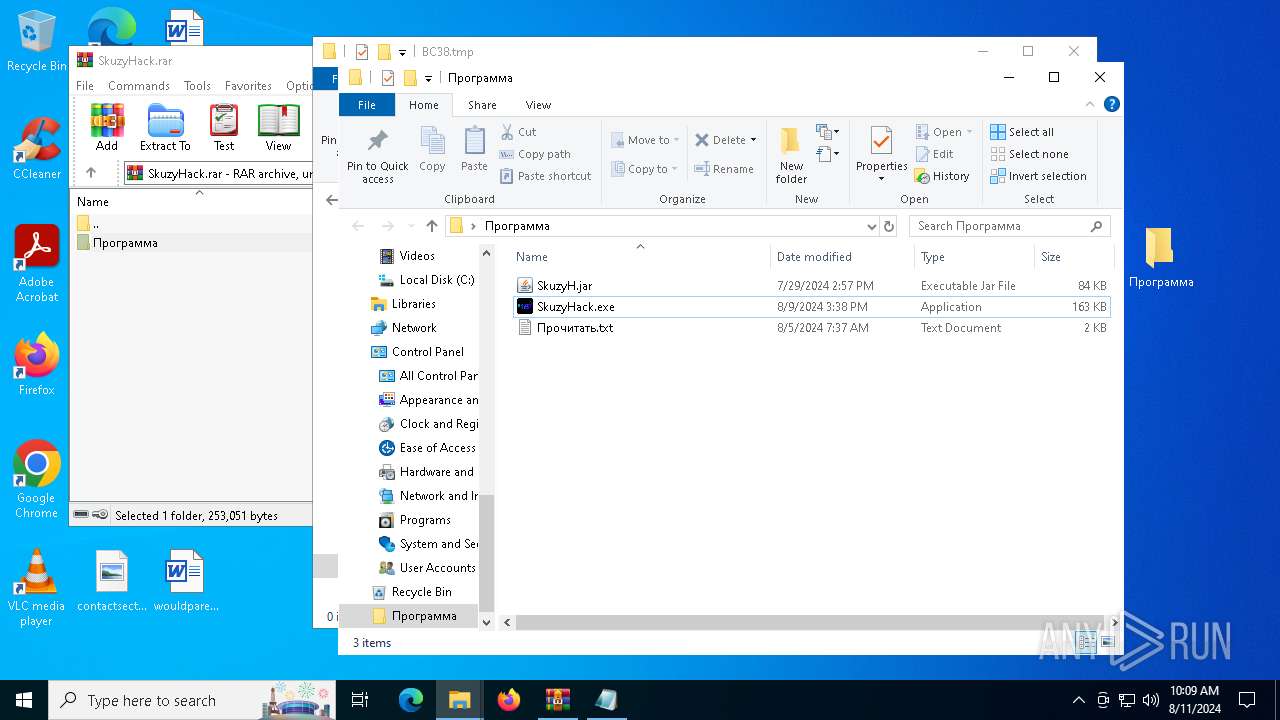
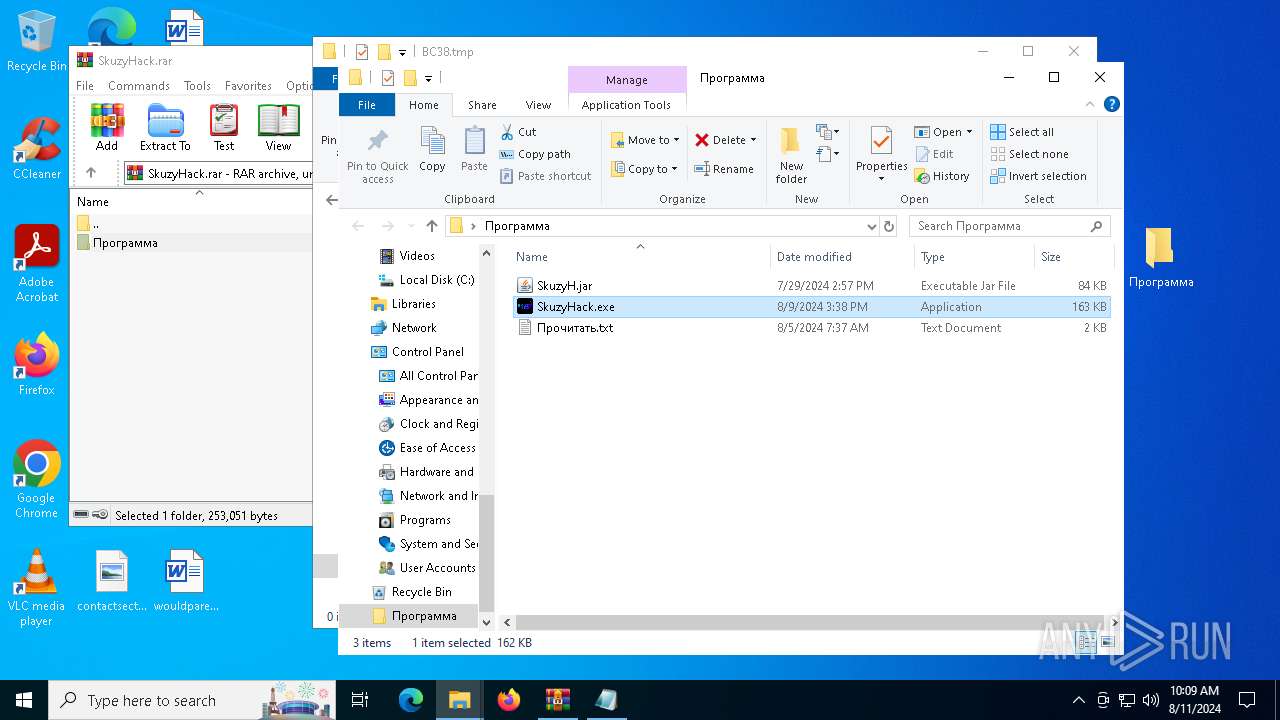
Executable content was dropped or overwritten
- WinRAR.exe (PID: 7240)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
265
Monitored processes
128
Malicious processes
6
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 188 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=17 --mojo-platform-channel-handle=5916 --field-trial-handle=2356,i,16957270481603017942,3898132028380328133,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 188 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=122.0.6261.70 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 "--annotation=prod=Microsoft Edge" --annotation=ver=122.0.2365.59 --initial-client-data=0x290,0x294,0x298,0x288,0x2a0,0x7fffd6675fd8,0x7fffd6675fe4,0x7fffd6675ff0 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 232 | timeout /t 5 | C:\Windows\System32\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: timeout - pauses command processing Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 872 | timeout /t 4 | C:\Windows\System32\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: timeout - pauses command processing Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 876 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=1484 --field-trial-handle=2452,i,17962703844507502421,2169568772300990512,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1432 | "C:\WINDOWS\system32\cmd" /c "C:\Users\admin\AppData\Local\Temp\A068.tmp\A079.tmp\A07A.bat C:\Users\admin\Desktop\Программа\SkuzyHack.exe" | C:\Windows\System32\cmd.exe | — | SkuzyHack.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 3221225786 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1488 | timeout /t 2 | C:\Windows\System32\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: timeout - pauses command processing Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1492 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=7308 --field-trial-handle=2356,i,16957270481603017942,3898132028380328133,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1664 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5496 --field-trial-handle=2452,i,17962703844507502421,2169568772300990512,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1664 | timeout /t 3 | C:\Windows\System32\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: timeout - pauses command processing Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
26 058
Read events
25 900
Write events
154
Delete events
4
Modification events
| (PID) Process: | (6432) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6432) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6432) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (6432) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (6432) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6432) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\EdgeUpdate\ClientState\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (6432) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6432) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge |
| Operation: | write | Name: | UsageStatsInSample |
Value: 1 | |||
| (PID) Process: | (6432) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (6432) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | urlstats |
Value: 0 | |||
Executable files
3
Suspicious files
301
Text files
158
Unknown types
10
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6432 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RFe63b7.TMP | — | |
MD5:— | SHA256:— | |||
| 6432 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RFe63b7.TMP | — | |
MD5:— | SHA256:— | |||
| 6432 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6432 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6432 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RFe63b7.TMP | — | |
MD5:— | SHA256:— | |||
| 6432 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6432 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RFe63f5.TMP | — | |
MD5:— | SHA256:— | |||
| 6432 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6432 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RFe6434.TMP | — | |
MD5:— | SHA256:— | |||
| 6432 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
34
TCP/UDP connections
89
DNS requests
90
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
7580 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
5760 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7624 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
5760 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6216 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/d6dbdc0a-9252-4e2b-941c-28a5425d274d?P1=1723921190&P2=404&P3=2&P4=BEhz94Q8%2bOCgNKv5Qfktb1R2X9VOk%2bMpWRb8OShv8ypg3zqUHL5wjFXItwyH14vj7x%2bkvJz2P%2fCSqceTHENPRA%3d%3d | unknown | — | — | whitelisted |
6216 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/d6dbdc0a-9252-4e2b-941c-28a5425d274d?P1=1723921190&P2=404&P3=2&P4=BEhz94Q8%2bOCgNKv5Qfktb1R2X9VOk%2bMpWRb8OShv8ypg3zqUHL5wjFXItwyH14vj7x%2bkvJz2P%2fCSqceTHENPRA%3d%3d | unknown | — | — | whitelisted |
6216 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/d6dbdc0a-9252-4e2b-941c-28a5425d274d?P1=1723921190&P2=404&P3=2&P4=BEhz94Q8%2bOCgNKv5Qfktb1R2X9VOk%2bMpWRb8OShv8ypg3zqUHL5wjFXItwyH14vj7x%2bkvJz2P%2fCSqceTHENPRA%3d%3d | unknown | — | — | whitelisted |
6216 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/8bc315ba-54e5-49f4-9b75-997d7071eb06?P1=1723476885&P2=404&P3=2&P4=ZLc93pimrHzgpu420HU5qKbMGon239NiQ%2b%2fyz2gjy86p7je%2bAzK7H4inzji0hbkWohq6uUKleDly3L5xzWa%2fPQ%3d%3d | unknown | — | — | whitelisted |
6216 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/d6dbdc0a-9252-4e2b-941c-28a5425d274d?P1=1723921190&P2=404&P3=2&P4=BEhz94Q8%2bOCgNKv5Qfktb1R2X9VOk%2bMpWRb8OShv8ypg3zqUHL5wjFXItwyH14vj7x%2bkvJz2P%2fCSqceTHENPRA%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
6016 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5408 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2120 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6432 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
— | — | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 87.250.250.50:443 | disk.yandex.ru | YANDEX LLC | RU | whitelisted |
— | — | 204.79.197.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
— | — | 13.107.246.60:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
disk.yandex.ru |
| shared |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
business.bing.com |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
www.bing.com |
| whitelisted |
yastatic.net |
| whitelisted |