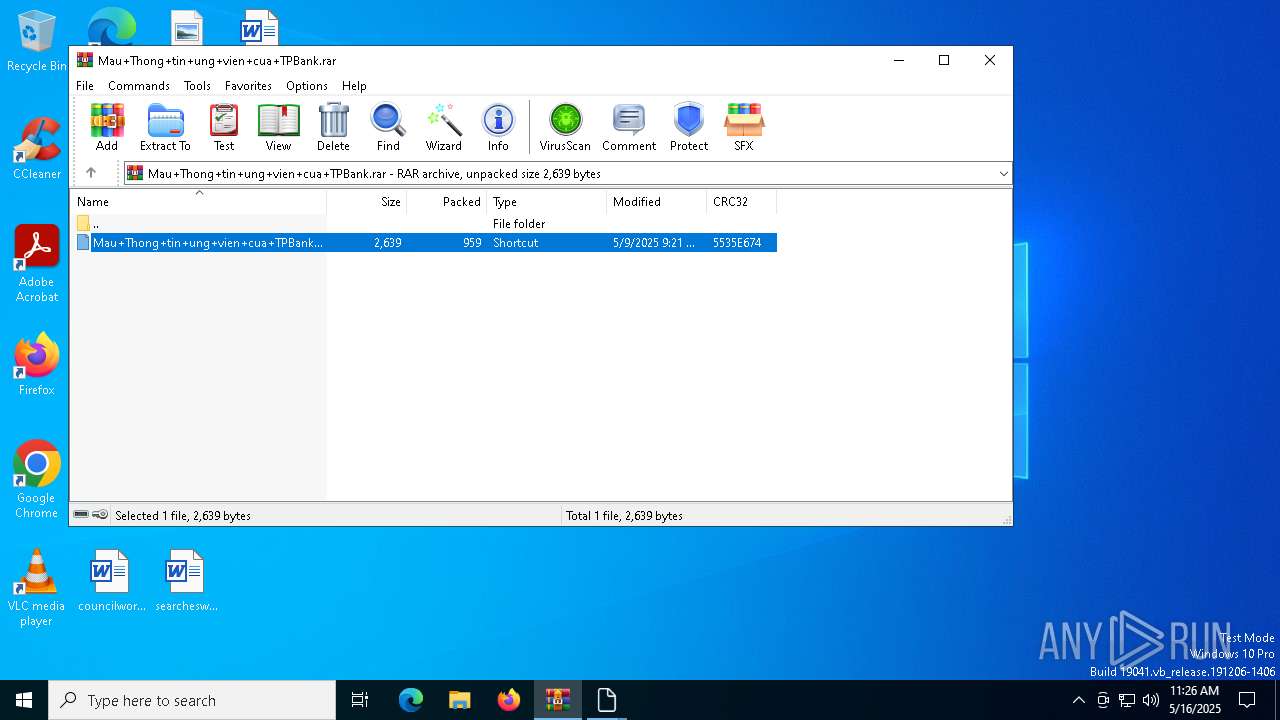
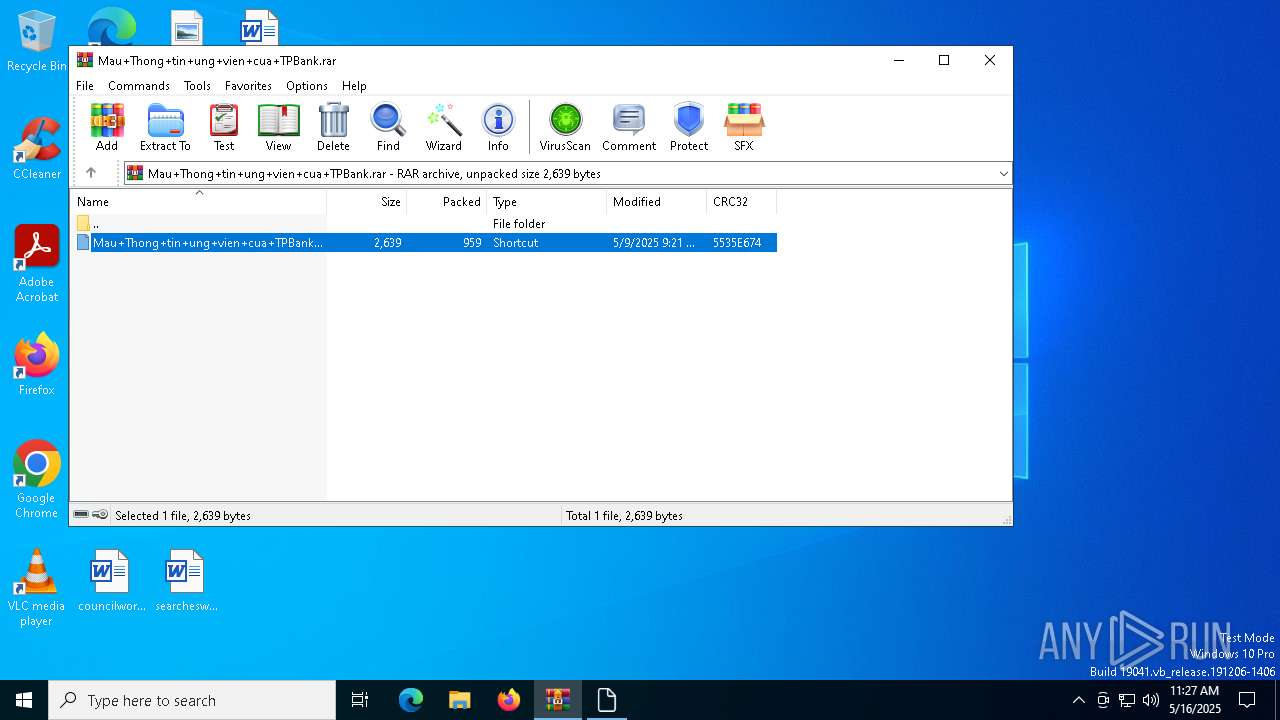
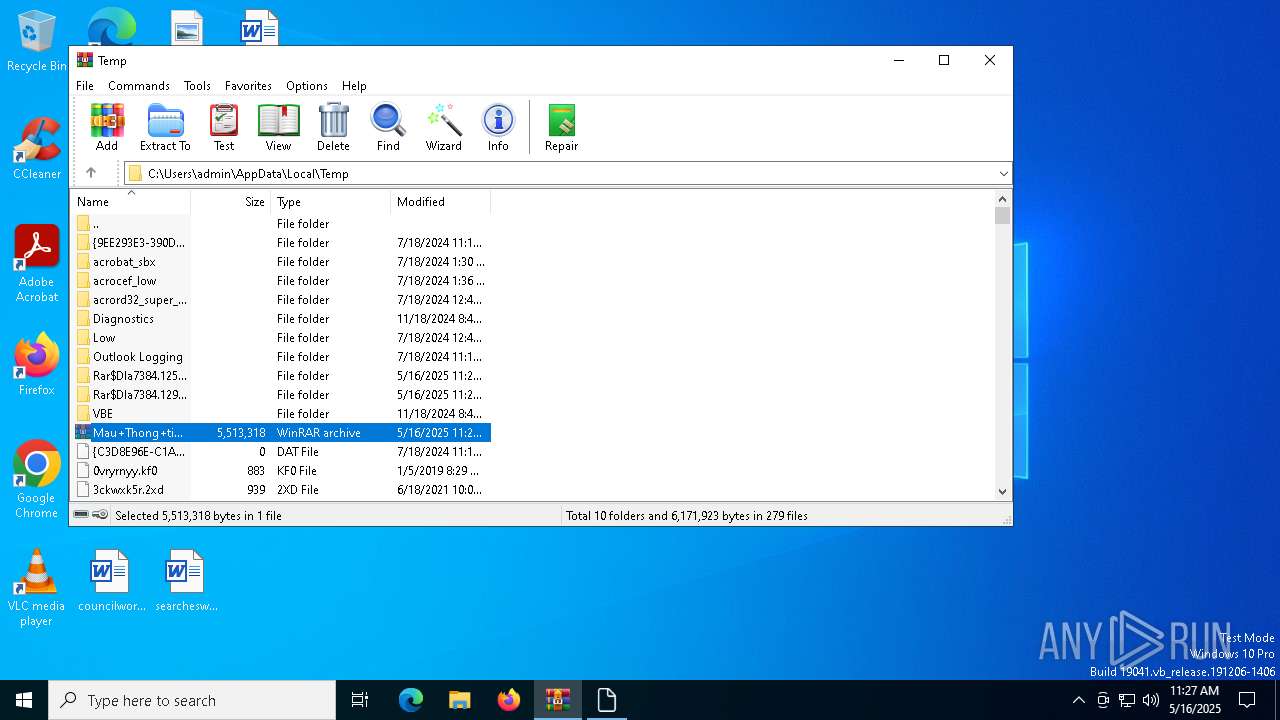
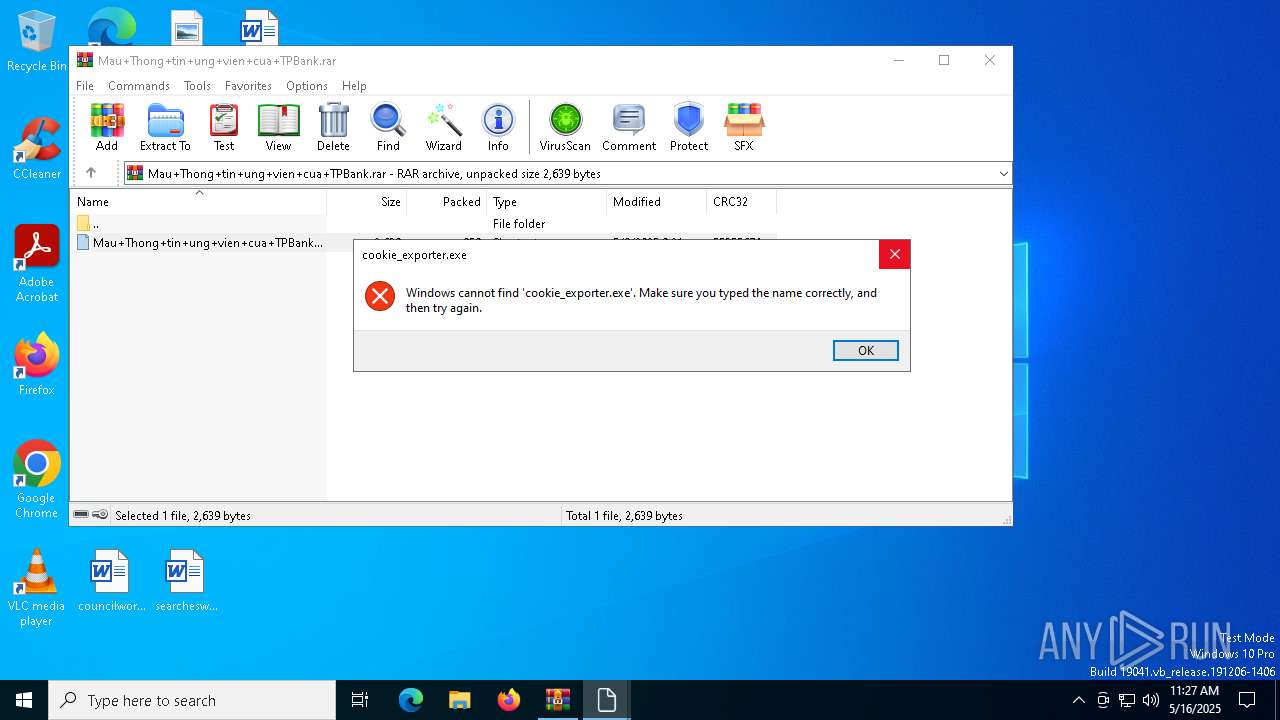
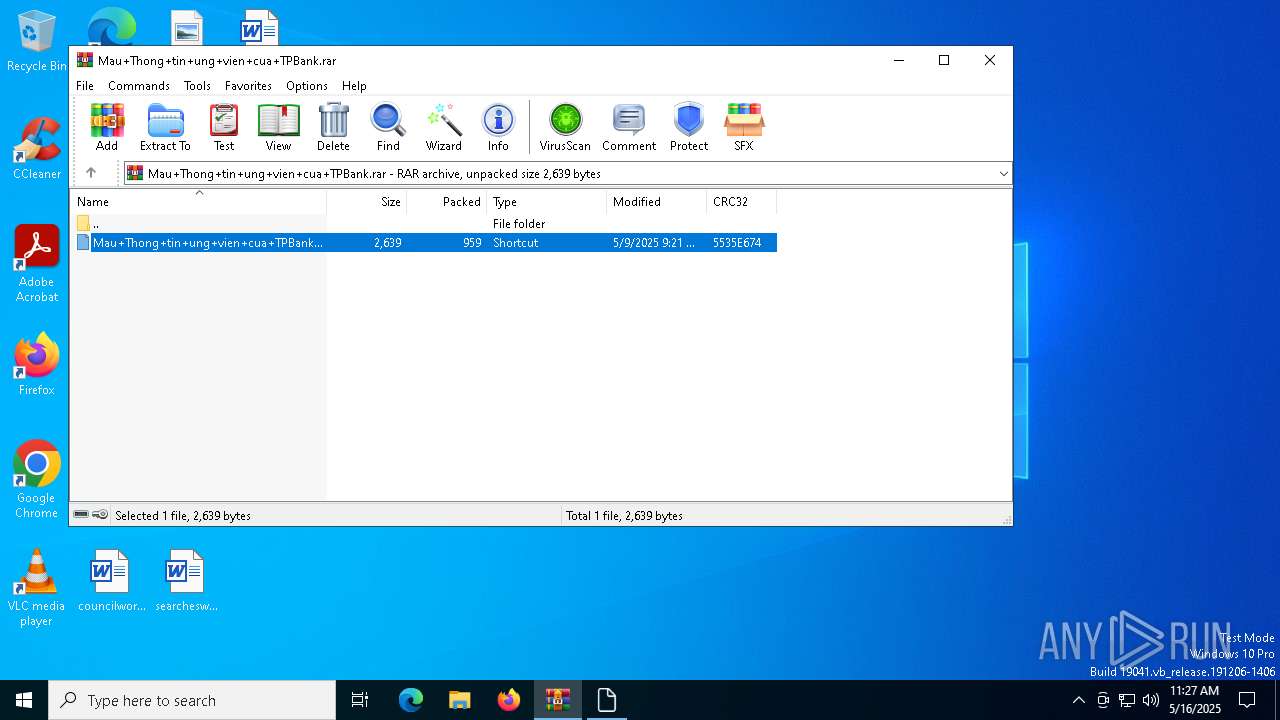
| File name: | Mau+Thong+tin+ung+vien+cua+TPBank.rar |
| Full analysis: | https://app.any.run/tasks/d443bae9-58b2-4dbf-a0b5-5f0b5f320295 |
| Verdict: | Malicious activity |
| Analysis date: | May 16, 2025, 11:26:41 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 499B2EBC09C2BAEE29D09DADF2EC0C5A |
| SHA1: | A066F362BBCDB58B3F8E21050DDF161C86C60CA5 |
| SHA256: | AAA71E8DAF0A6B49386A3A5D7B09730B26800AD9C801484149792468ED7281D1 |
| SSDEEP: | 98304:dXHAP1NHXKD2L5kRhmSQNuIJlWW4YAT7WTlSIJfQFuVn4qtWLRHlroF0126r0VDr:sdZftL8HWjWx53C |
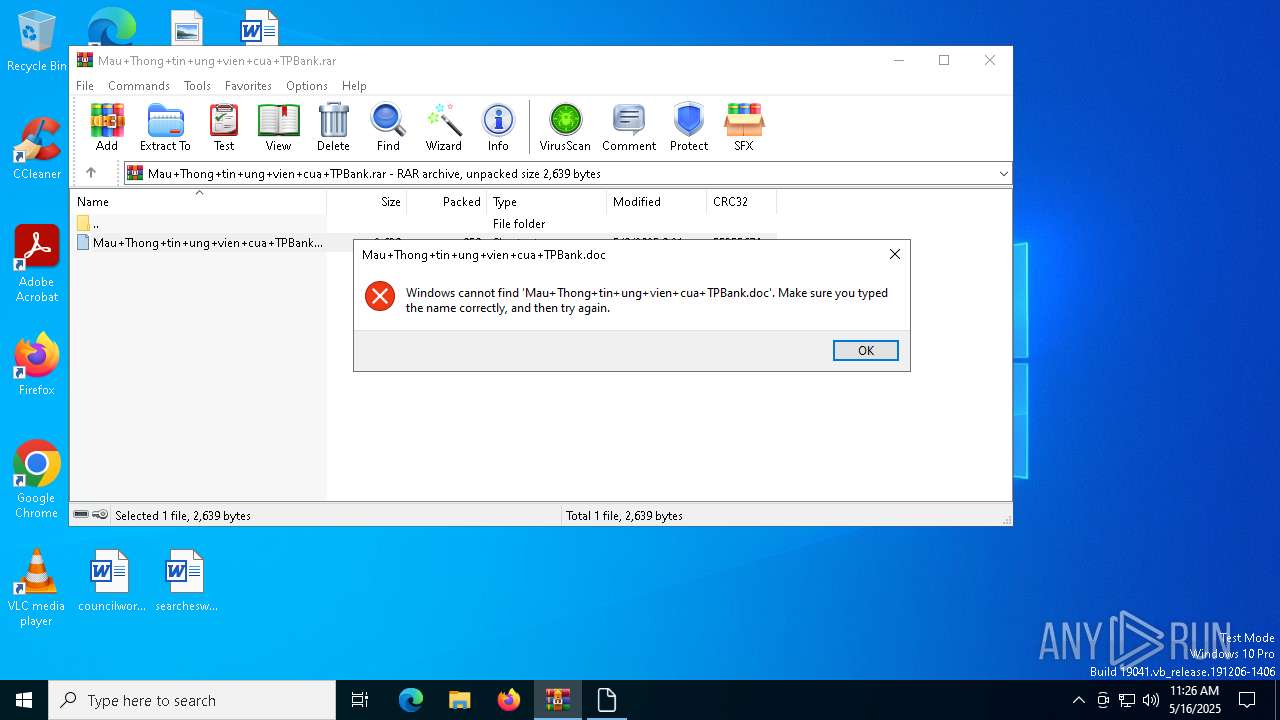
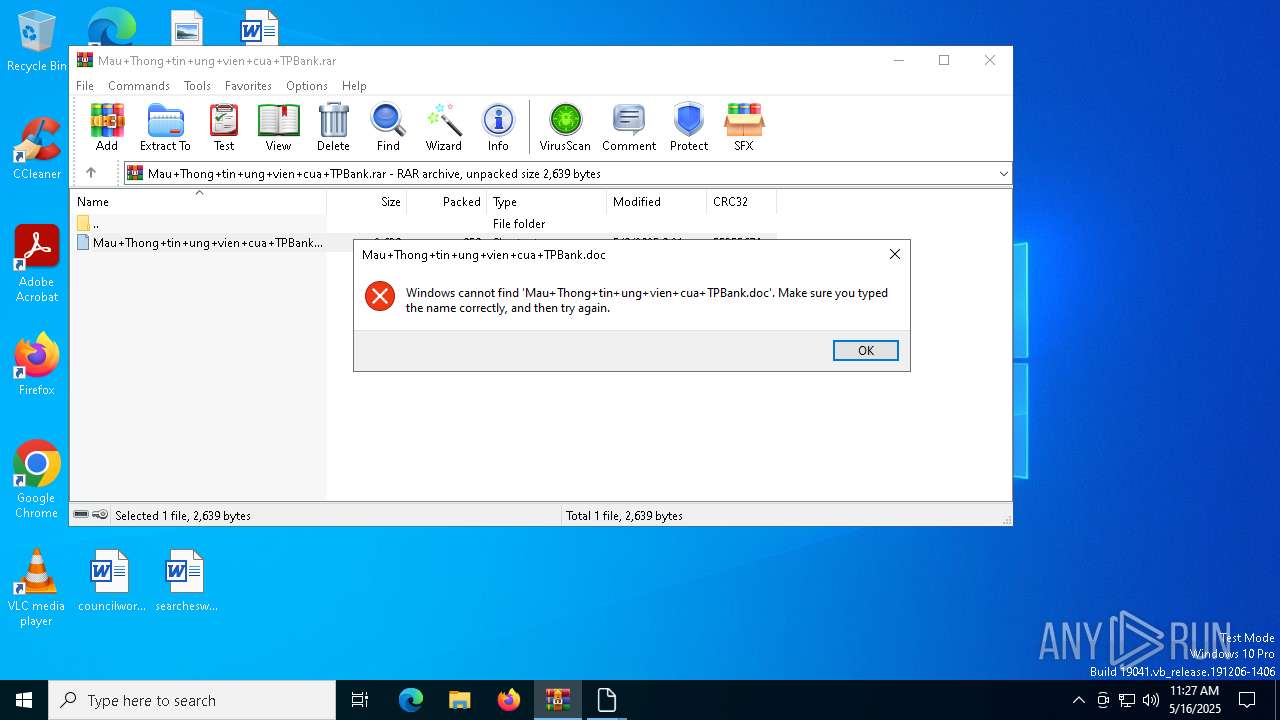
MALICIOUS
Generic archive extractor
- WinRAR.exe (PID: 7384)
SUSPICIOUS
Process drops legitimate windows executable
- WinRAR.exe (PID: 7384)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 7384)
Detected use of alternative data streams (AltDS)
- esentutl.exe (PID: 7720)
- esentutl.exe (PID: 6240)
- esentutl.exe (PID: 7836)
Starts CMD.EXE for commands execution
- WinRAR.exe (PID: 7384)
INFO
Executable content was dropped or overwritten
- WinRAR.exe (PID: 7384)
The sample compiled with english language support
- WinRAR.exe (PID: 7384)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
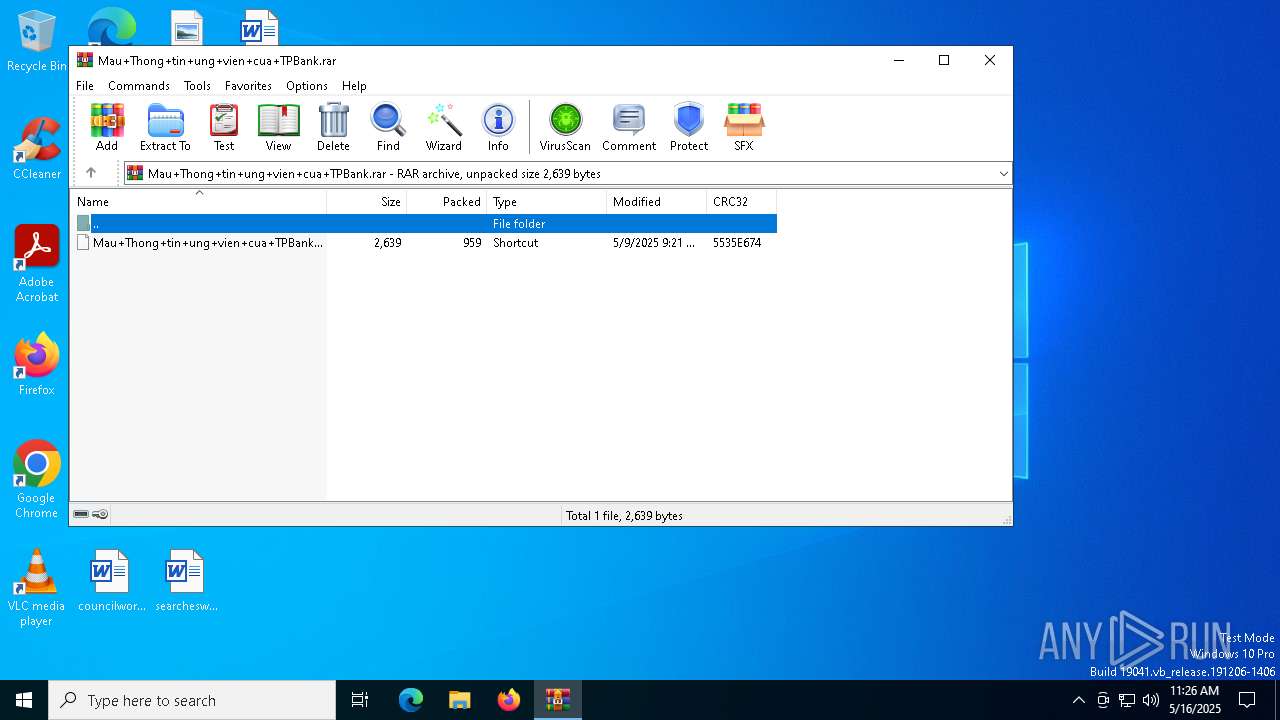
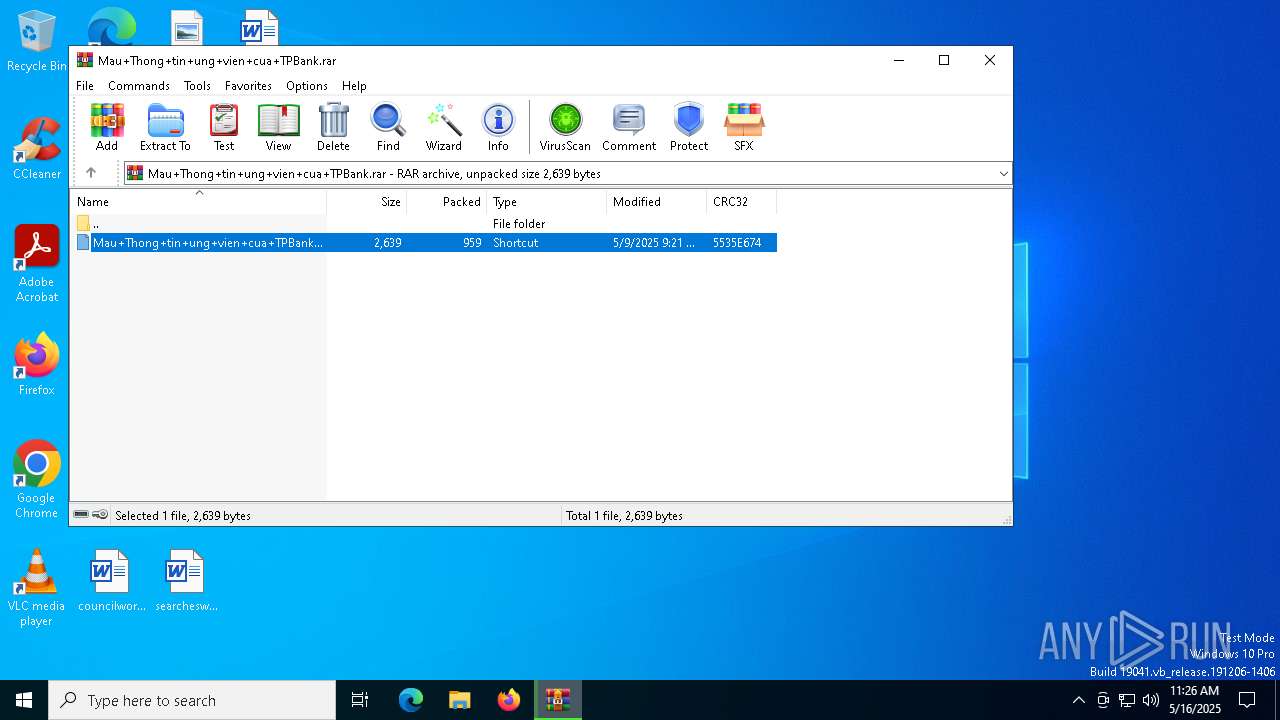
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
EXIF
ZIP
| FileVersion: | RAR v5 |
|---|---|
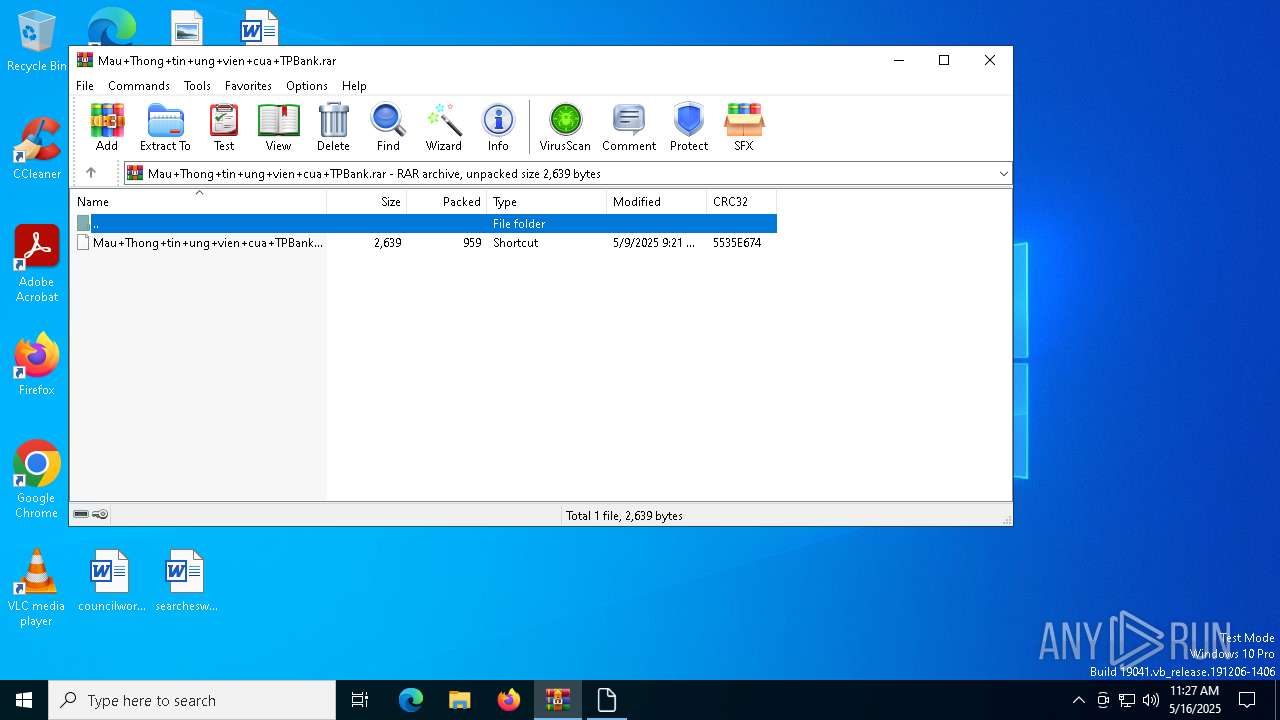
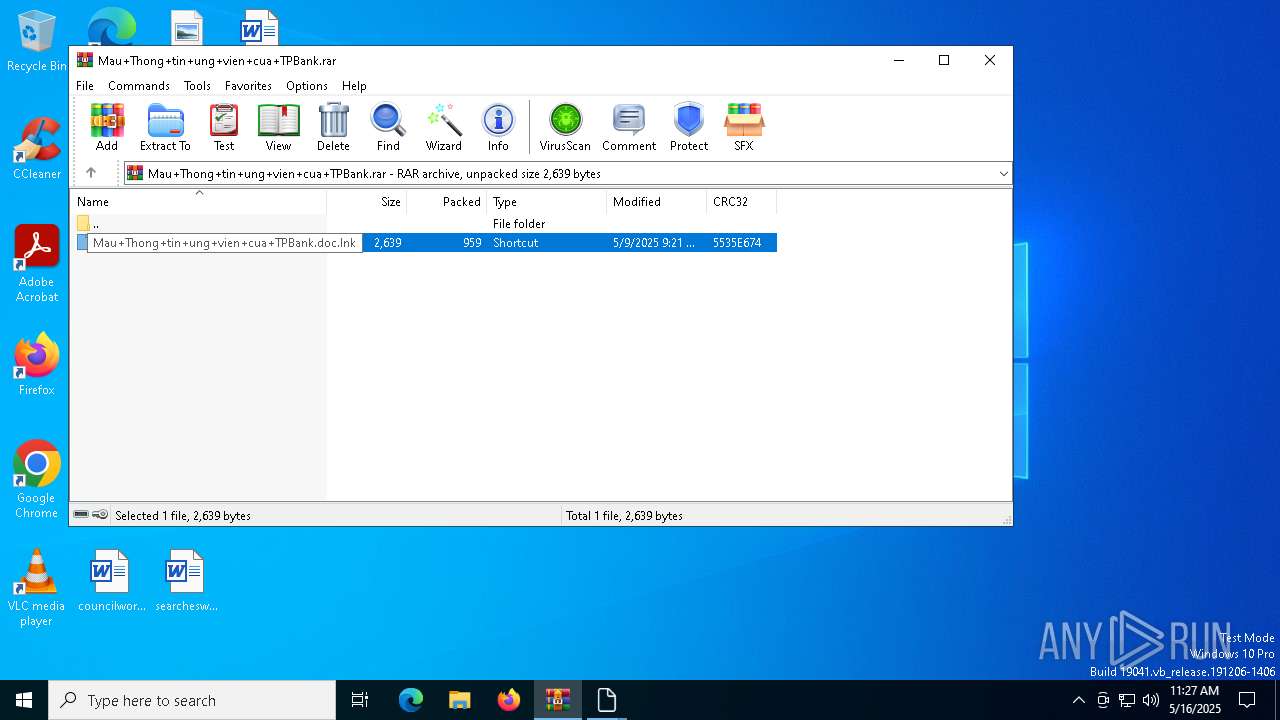
| CompressedSize: | 959 |
| UncompressedSize: | 2639 |
| OperatingSystem: | Win32 |
| ArchivedFileName: | Mau+Thong+tin+ung+vien+cua+TPBank.doc.lnk |
Total processes
138
Monitored processes
12
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 6048 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6240 | esentutl /y Mau+Thong+tin+ung+vien+cua+TPBank.doc.lnk:lib /d ~lib.exe /o | C:\Windows\System32\esentutl.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Extensible Storage Engine Utilities for Microsoft(R) Windows(R) Exit code: 4294967295 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
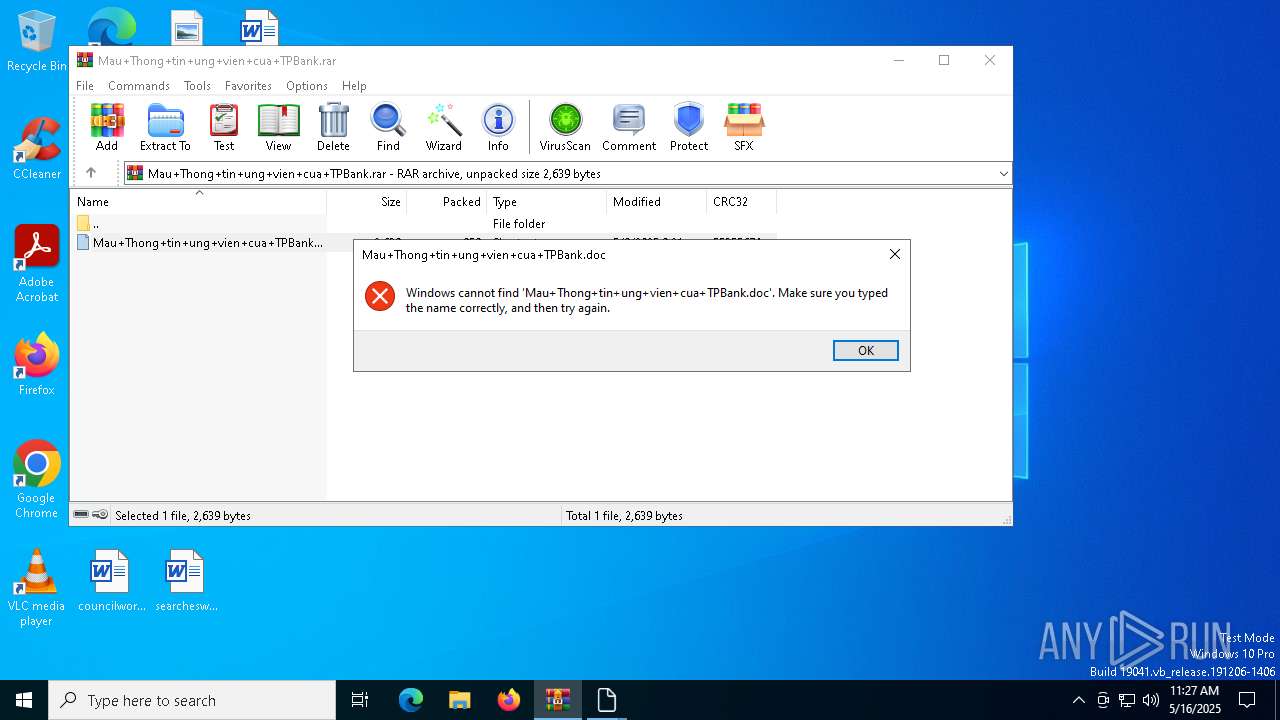
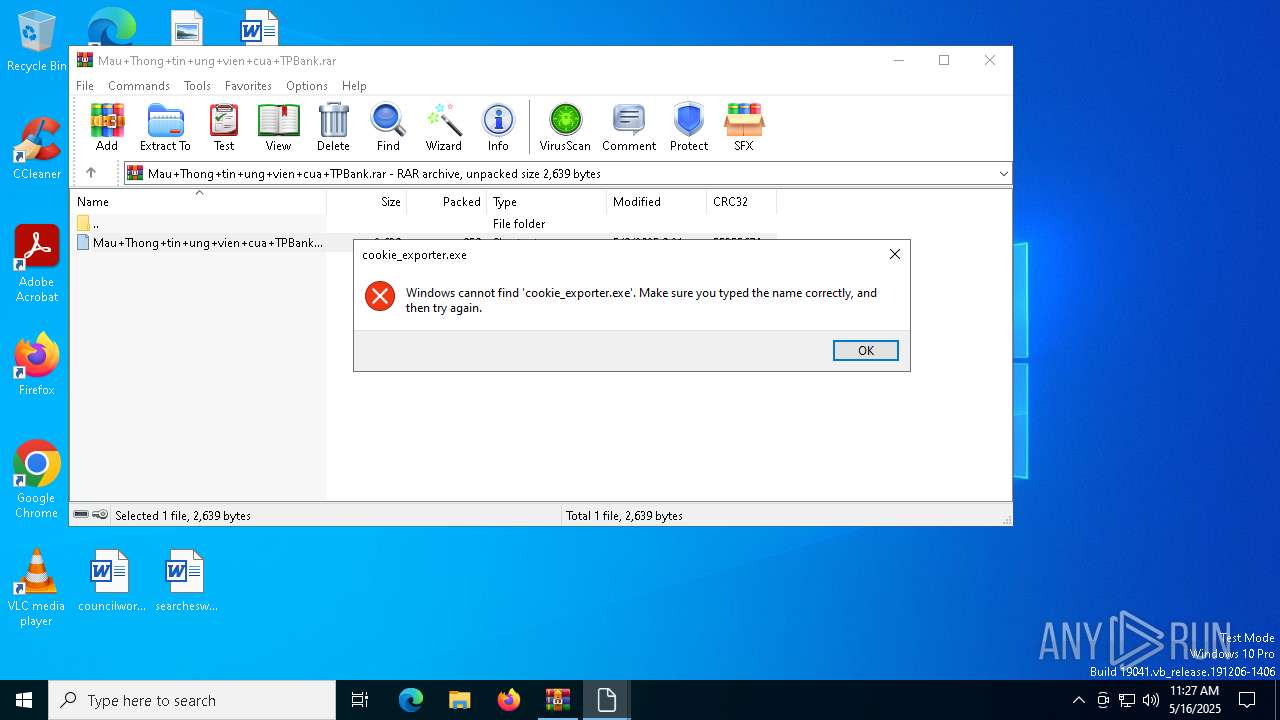
| 7176 | "C:\Windows\System32\cmd.exe" /c "esentutl /y Mau+Thong+tin+ung+vien+cua+TPBank.doc.lnk:lib /d ~lib.exe /o & ~lib.exe Mau+Thong+tin+ung+vien+cua+TPBank.doc.lnk mscore GDHkw & cd /d GDHkw & start """" Mau+Thong+tin+ung+vien+cua+TPBank.doc & start """" cookie_exporter.exe" | C:\Windows\System32\cmd.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7384 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\Mau+Thong+tin+ung+vien+cua+TPBank.rar | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 7524 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7556 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7652 | "C:\Windows\System32\cmd.exe" /c "esentutl /y Mau+Thong+tin+ung+vien+cua+TPBank.doc.lnk:lib /d ~lib.exe /o & ~lib.exe Mau+Thong+tin+ung+vien+cua+TPBank.doc.lnk mscore GDHkw & cd /d GDHkw & start """" Mau+Thong+tin+ung+vien+cua+TPBank.doc & start """" cookie_exporter.exe" | C:\Windows\System32\cmd.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7664 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7720 | esentutl /y Mau+Thong+tin+ung+vien+cua+TPBank.doc.lnk:lib /d ~lib.exe /o | C:\Windows\System32\esentutl.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Extensible Storage Engine Utilities for Microsoft(R) Windows(R) Exit code: 4294967295 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7764 | "C:\Windows\System32\cmd.exe" /c "esentutl /y Mau+Thong+tin+ung+vien+cua+TPBank.doc.lnk:lib /d ~lib.exe /o & ~lib.exe Mau+Thong+tin+ung+vien+cua+TPBank.doc.lnk mscore GDHkw & cd /d GDHkw & start """" Mau+Thong+tin+ung+vien+cua+TPBank.doc & start """" cookie_exporter.exe" | C:\Windows\System32\cmd.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
6 773
Read events
6 752
Write events
21
Delete events
0
Modification events
| (PID) Process: | (7384) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (7384) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (7384) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (7384) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Mau+Thong+tin+ung+vien+cua+TPBank.rar | |||
| (PID) Process: | (7384) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (7384) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (7384) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (7384) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (7384) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | SlowContextMenuEntries |
Value: 6024B221EA3A6910A2DC08002B30309D0A010000BD0E0C47735D584D9CEDE91E22E23282770100000114020000000000C0000000000000468D0000006078A409B011A54DAFA526D86198A780390100009AD298B2EDA6DE11BA8CA68E55D895936E000000 | |||
| (PID) Process: | (7384) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | SlowContextMenuEntries |
Value: 6024B221EA3A6910A2DC08002B30309D0A010000BD0E0C47735D584D9CEDE91E22E23282770100000114020000000000C0000000000000469C0000006078A409B011A54DAFA526D86198A780390100009AD298B2EDA6DE11BA8CA68E55D895936E000000 | |||
Executable files
3
Suspicious files
6
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7384 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIa7384.12559\Mau+Thong+tin+ung+vien+cua+TPBank.doc.lnk:lib | executable | |
MD5:3E5F15A11772C8CD5ABF78A720AB2644 | SHA256:1F22E288F7D22FA0885D4A80DB367F5283B22A69322B9E998A40D6981882A249 | |||
| 7384 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIa7384.12559\Mau+Thong+tin+ung+vien+cua+TPBank.doc.lnk:mscore | compressed | |
MD5:C8A372D1603968D1E73773DB69C2800C | SHA256:7E52ECEB2845DB6013BD78CF13763C7C2A1028E1D098A1EDFEB47C3EEB33248B | |||
| 7384 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIa7384.12917\Mau+Thong+tin+ung+vien+cua+TPBank.doc.lnk | binary | |
MD5:62A507696731F267A211EA66335C5C80 | SHA256:2BC8ACD8911550D3B3314BFC8A735ECE9B0133A37A05E359819FE8774104B912 | |||
| 7384 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIa7384.12917\Mau+Thong+tin+ung+vien+cua+TPBank.doc.lnk:lib | executable | |
MD5:3E5F15A11772C8CD5ABF78A720AB2644 | SHA256:1F22E288F7D22FA0885D4A80DB367F5283B22A69322B9E998A40D6981882A249 | |||
| 7384 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIa7384.15415\Mau+Thong+tin+ung+vien+cua+TPBank.doc.lnk | binary | |
MD5:62A507696731F267A211EA66335C5C80 | SHA256:2BC8ACD8911550D3B3314BFC8A735ECE9B0133A37A05E359819FE8774104B912 | |||
| 7384 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIa7384.15415\Mau+Thong+tin+ung+vien+cua+TPBank.doc.lnk:mscore | compressed | |
MD5:C8A372D1603968D1E73773DB69C2800C | SHA256:7E52ECEB2845DB6013BD78CF13763C7C2A1028E1D098A1EDFEB47C3EEB33248B | |||
| 7384 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIa7384.12917\Mau+Thong+tin+ung+vien+cua+TPBank.doc.lnk:mscore | compressed | |
MD5:C8A372D1603968D1E73773DB69C2800C | SHA256:7E52ECEB2845DB6013BD78CF13763C7C2A1028E1D098A1EDFEB47C3EEB33248B | |||
| 7384 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIa7384.15415\Mau+Thong+tin+ung+vien+cua+TPBank.doc.lnk:lib | executable | |
MD5:3E5F15A11772C8CD5ABF78A720AB2644 | SHA256:1F22E288F7D22FA0885D4A80DB367F5283B22A69322B9E998A40D6981882A249 | |||
| 7384 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIa7384.12559\Mau+Thong+tin+ung+vien+cua+TPBank.doc.lnk | binary | |
MD5:62A507696731F267A211EA66335C5C80 | SHA256:2BC8ACD8911550D3B3314BFC8A735ECE9B0133A37A05E359819FE8774104B912 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
17
DNS requests
10
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.19.11.120:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
8068 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
8068 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
6652 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.19.11.120:80 | crl.microsoft.com | Elisa Oyj | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
— | — | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
2104 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3216 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
8068 | SIHClient.exe | 20.12.23.50:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |