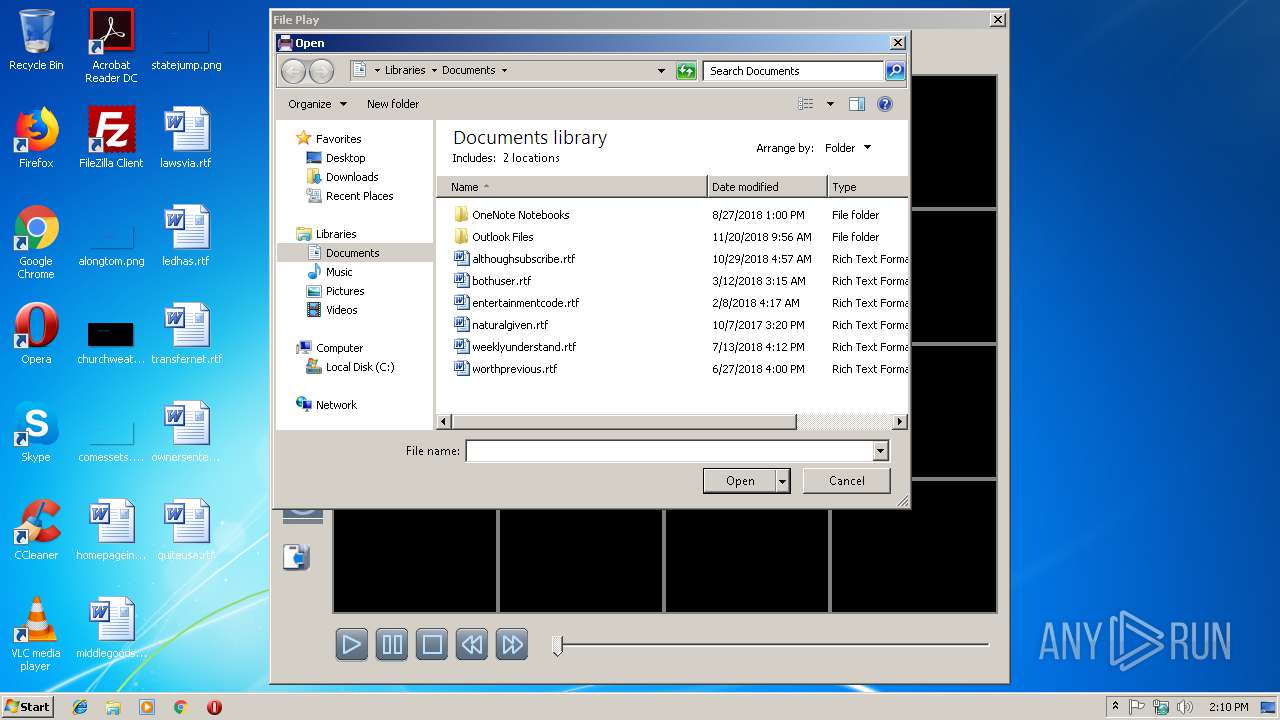
| File name: | ifileplaypack.exe |
| Full analysis: | https://app.any.run/tasks/36b37d00-91b7-40fe-ac1c-c16e4241644a |
| Verdict: | No threats detected |
| Analysis date: | February 10, 2019, 14:09:29 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, RAR self-extracting archive |
| MD5: | FF9469D011F6BE058E8785EF3A189B3B |
| SHA1: | 1B0BCD56628D91D9874654B1102D0EDAF10215AA |
| SHA256: | AA9A8E203E4C72A73488E3A2695D42C520F6E1FF419D99C4E326436BBDD688B0 |
| SSDEEP: | 24576:78HHQkh46KBYyQghs4yaWkhkUsqA9DzxWxDxxX7lj6:78H/bMYyBhsE0ahxxrB6 |
MALICIOUS
Loads dropped or rewritten executable
- ifileplay.exe (PID: 2980)
Application was dropped or rewritten from another process
- ifileplay.exe (PID: 2516)
- ifileplay.exe (PID: 2980)
SUSPICIOUS
Executable content was dropped or overwritten
- ifileplaypack.exe (PID: 3100)
Reads Internet Cache Settings
- ifileplay.exe (PID: 2980)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | WinRAR Self Extracting archive (94.8) |
|---|---|---|
| .scr | | | Windows screen saver (2.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (1.2) |
| .exe | | | Win32 Executable (generic) (0.8) |
| .exe | | | Generic Win/DOS Executable (0.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2007:09:20 14:34:46+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 5 |
| CodeSize: | 81920 |
| InitializedDataSize: | 79872 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1000 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 20-Sep-2007 12:34:46 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000200 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 20-Sep-2007 12:34:46 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00014000 | 0x00013800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.46548 |
.data | 0x00015000 | 0x00007000 | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.90968 |
.idata | 0x0001C000 | 0x00001000 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.12446 |
.rsrc | 0x0001D000 | 0x00011C30 | 0x00011E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.71172 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.06643 | 831 | Latin 1 / Western European | Russian - Russia | RT_MANIFEST |
2 | 7.09544 | 872 | Latin 1 / Western European | Process Default Language | RT_ICON |
3 | 6.64185 | 1128 | Latin 1 / Western European | Process Default Language | RT_ICON |
4 | 5.58189 | 744 | Latin 1 / Western European | Process Default Language | RT_ICON |
5 | 7.11704 | 3240 | Latin 1 / Western European | Process Default Language | RT_ICON |
6 | 6.37162 | 4264 | Latin 1 / Western European | Process Default Language | RT_ICON |
7 | 3.24143 | 556 | Latin 1 / Western European | Russian - Russia | RT_STRING |
8 | 3.28574 | 946 | Latin 1 / Western European | Russian - Russia | RT_STRING |
9 | 3.04375 | 530 | Latin 1 / Western European | Russian - Russia | RT_STRING |
10 | 3.15563 | 638 | Latin 1 / Western European | Russian - Russia | RT_STRING |
Imports
ADVAPI32.DLL |
COMCTL32.DLL |
COMDLG32.DLL |
GDI32.DLL |
KERNEL32.DLL |
OLE32.DLL |
SHELL32.DLL |
USER32.DLL |
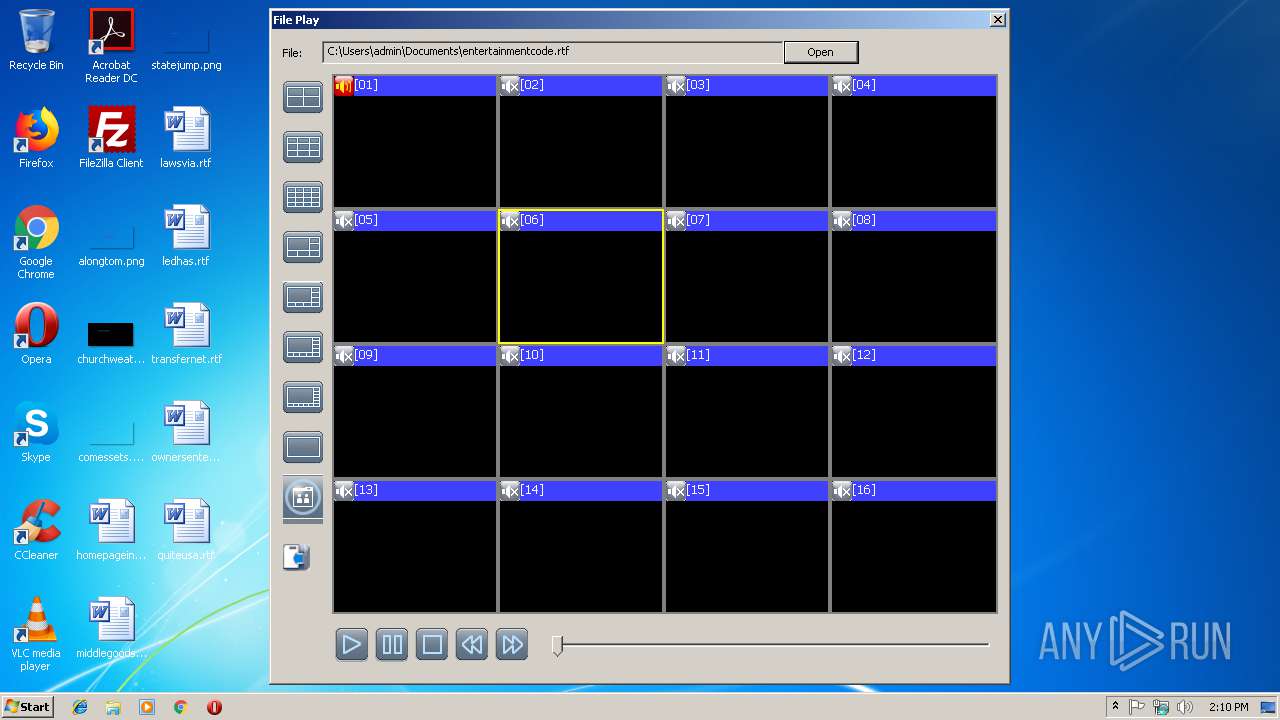
Total processes
36
Monitored processes
3
Malicious processes
0
Suspicious processes
0
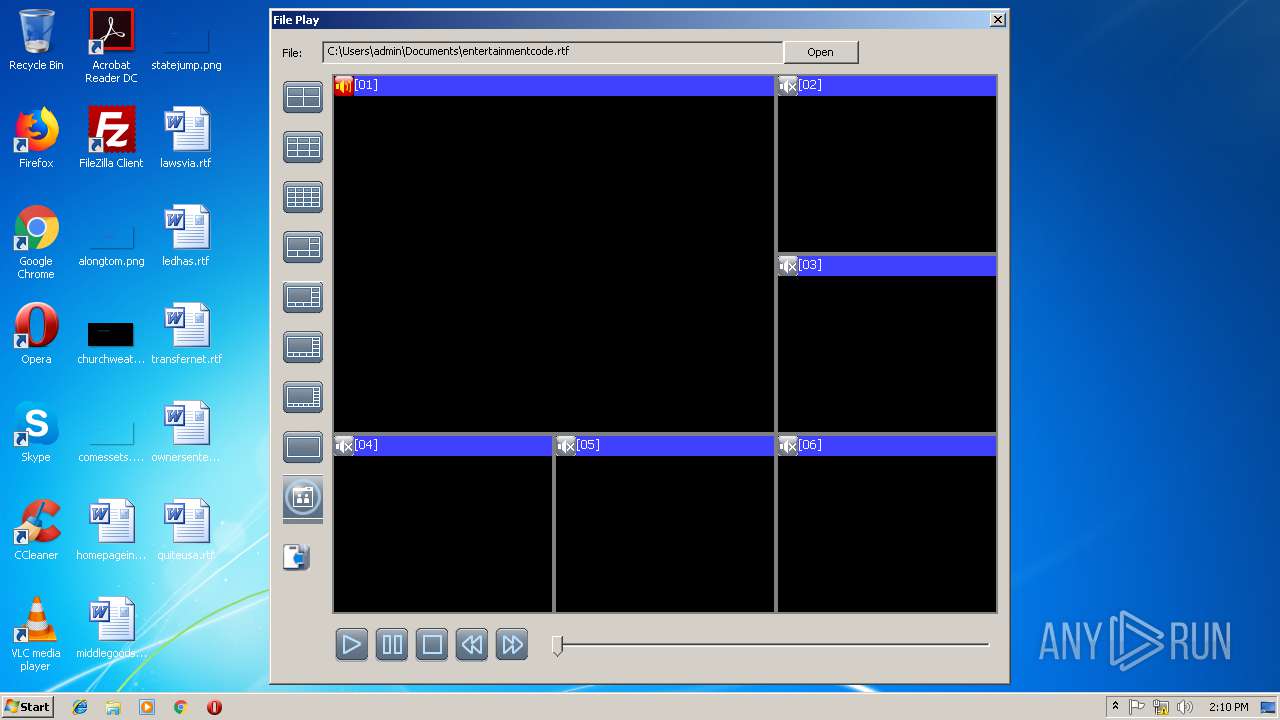
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2516 | "C:\Users\admin\AppData\Local\Temp\RarSFX0\ifileplay.exe" | C:\Users\admin\AppData\Local\Temp\RarSFX0\ifileplay.exe | — | ifileplaypack.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Version: 5, 0, 2, 0 Modules
| |||||||||||||||
| 2980 | "C:\Users\admin\AppData\Local\Temp\RarSFX0\ifileplay.exe" | C:\Users\admin\AppData\Local\Temp\RarSFX0\ifileplay.exe | ifileplaypack.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 5, 0, 2, 0 Modules
| |||||||||||||||
| 3100 | "C:\Users\admin\AppData\Local\Temp\ifileplaypack.exe" | C:\Users\admin\AppData\Local\Temp\ifileplaypack.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
1 082
Read events
862
Write events
219
Delete events
1
Modification events
| (PID) Process: | (3100) ifileplaypack.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3100) ifileplaypack.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2980) ifileplay.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: ifileplay.exe | |||
| (PID) Process: | (2980) ifileplay.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\MediaResources\DirectSound\Speaker Configuration |
| Operation: | write | Name: | Speaker Configuration |
Value: 4 | |||
| (PID) Process: | (2980) ifileplay.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 02020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (2980) ifileplay.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 0200000000000000010000000700000006000000030000000500000004000000FFFFFFFF | |||
| (PID) Process: | (2980) ifileplay.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\50\ComDlg |
| Operation: | write | Name: | TV_FolderType |
Value: {FBB3477E-C9E4-4B3B-A2BA-D3F5D3CD46F9} | |||
| (PID) Process: | (2980) ifileplay.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\50\ComDlg |
| Operation: | write | Name: | TV_TopViewID |
Value: {82BA0782-5B7A-4569-B5D7-EC83085F08CC} | |||
| (PID) Process: | (2980) ifileplay.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\50\ComDlg |
| Operation: | write | Name: | TV_TopViewVersion |
Value: 0 | |||
| (PID) Process: | (2980) ifileplay.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
2
Suspicious files
1
Text files
17
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3100 | ifileplaypack.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\SDVRJR.ocx | executable | |
MD5:— | SHA256:— | |||
| 3100 | ifileplaypack.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\Images\3-1.png | image | |
MD5:F61336396333F9A91E8599BAFC35F175 | SHA256:43D4FF9F0928638CDD4F1EF15FFD19F3DF6EE7E0313E7FD591DA679D41ED2294 | |||
| 3100 | ifileplaypack.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\Images\3-2.png | image | |
MD5:ED6C52B86C1671D49F1E0688F09CDCF7 | SHA256:185E5F1CBAF673BED15F46CF22A60AF45583C74184424013DF812D66D937215B | |||
| 3100 | ifileplaypack.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\Images\3-10.png | image | |
MD5:78E1429AF1A5CBFB3703D4FBD7176191 | SHA256:4D2F84024D27E559CDD7F706ED7FB7A78C2021377440981BF533B4EBB5F51E04 | |||
| 3100 | ifileplaypack.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\Images\Thumbs.db | binary | |
MD5:— | SHA256:— | |||
| 3100 | ifileplaypack.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\Images\3-9.png | image | |
MD5:BA48401AEEB61D4F38728D6797818DC7 | SHA256:59E499CB7E9AA77AF18B749EA117DC28605010CBEF148EABFF47215413FBE36E | |||
| 3100 | ifileplaypack.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\Images\3-8.png | image | |
MD5:10F2A7CBBAB6FF97FA4B3DBA03547572 | SHA256:DA7B64BB12BF0B5F36126DD2C24E1FEDAF9E71A9C989591096E9F4ABB34AF179 | |||
| 3100 | ifileplaypack.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\Images\3-3.png | image | |
MD5:A3A4C5CCEC76E28A8C5A392DECDE6CD3 | SHA256:6E23C2B9855428C2C9200266DAD6F2EB52853694E53C6DE8FB1A18D152BCF8F7 | |||
| 3100 | ifileplaypack.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\Images\catch.png | image | |
MD5:237D7543A969A3750A9EAB594C499671 | SHA256:FAA5E72B84602218EB081E9E253CBF9D852D0F0B8E44CBF9791DD9F62B5EB389 | |||
| 3100 | ifileplaypack.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\Images\3-7.png | image | |
MD5:9D22BA24E41378784755C53093630080 | SHA256:A8577A44AD2E211CAAE029177F24AA9E693E536A0F4148585E68E7F6C6942E06 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report