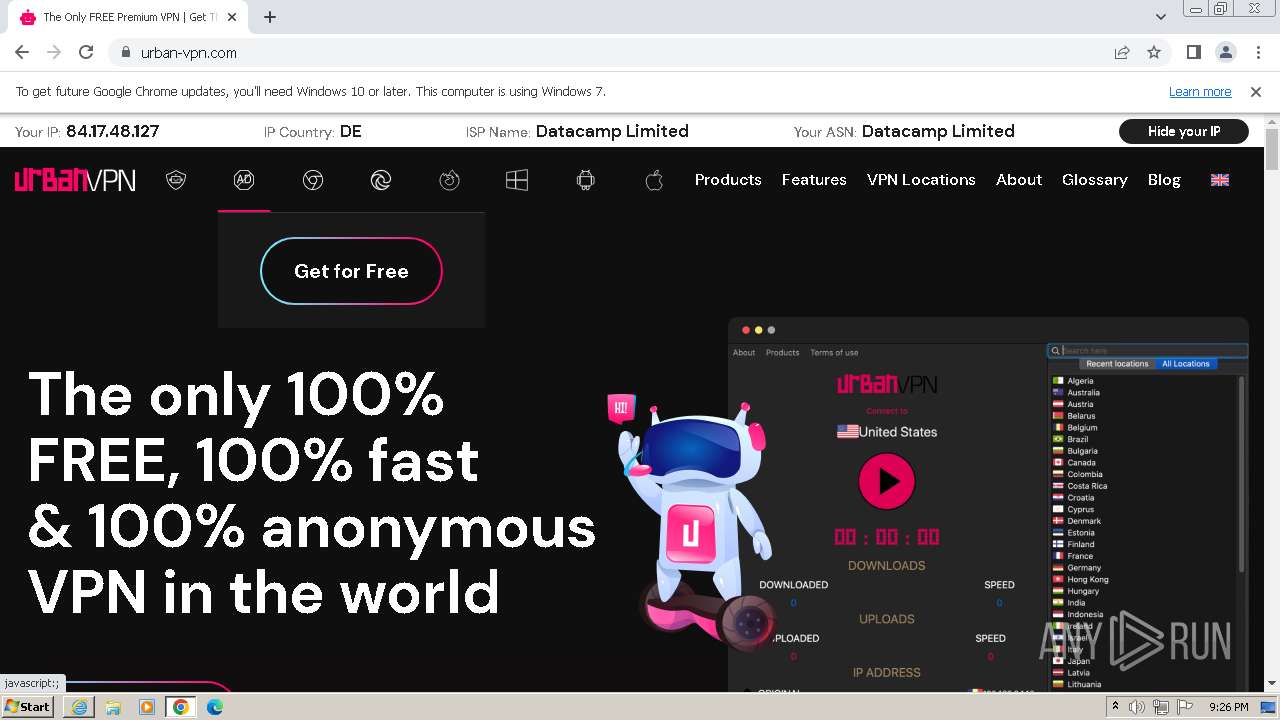
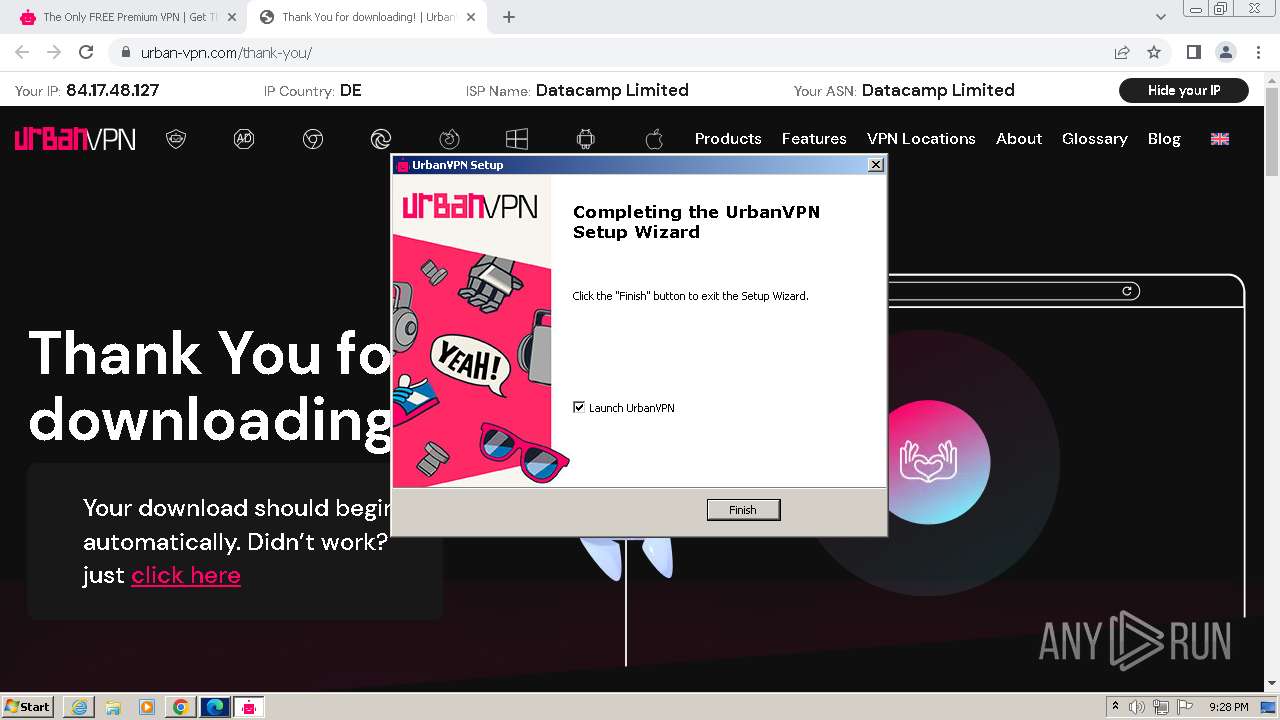
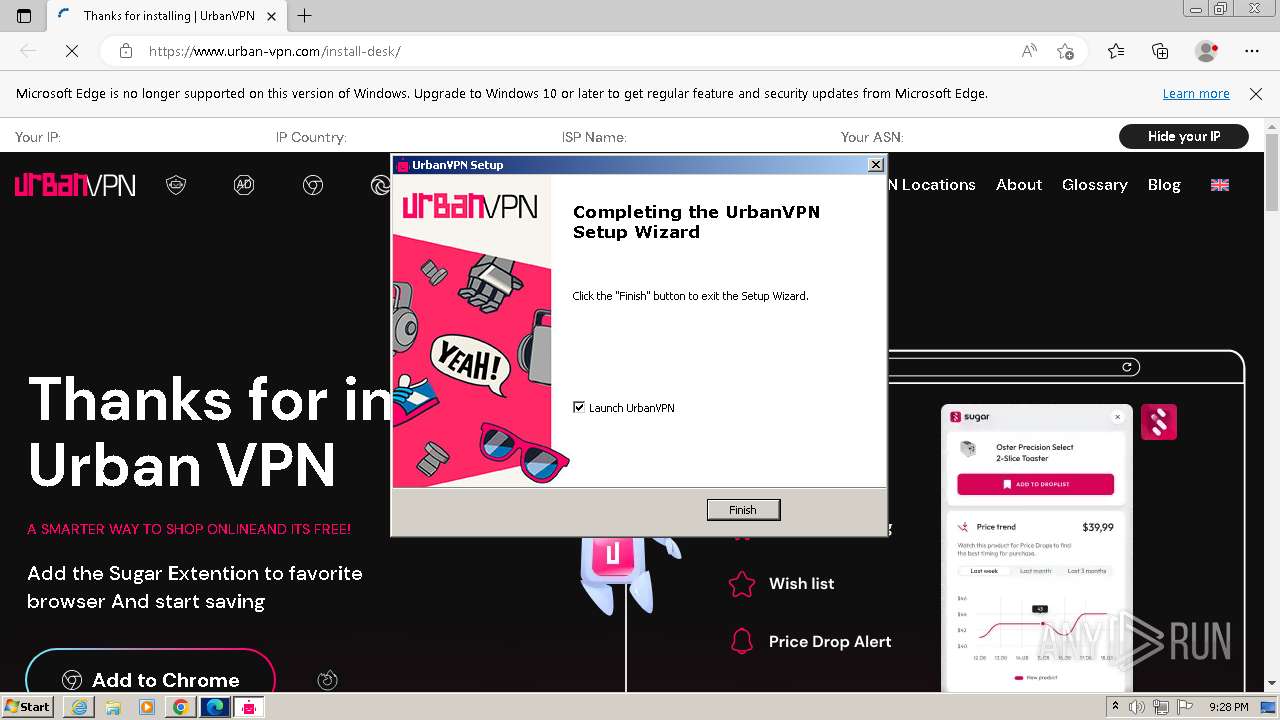
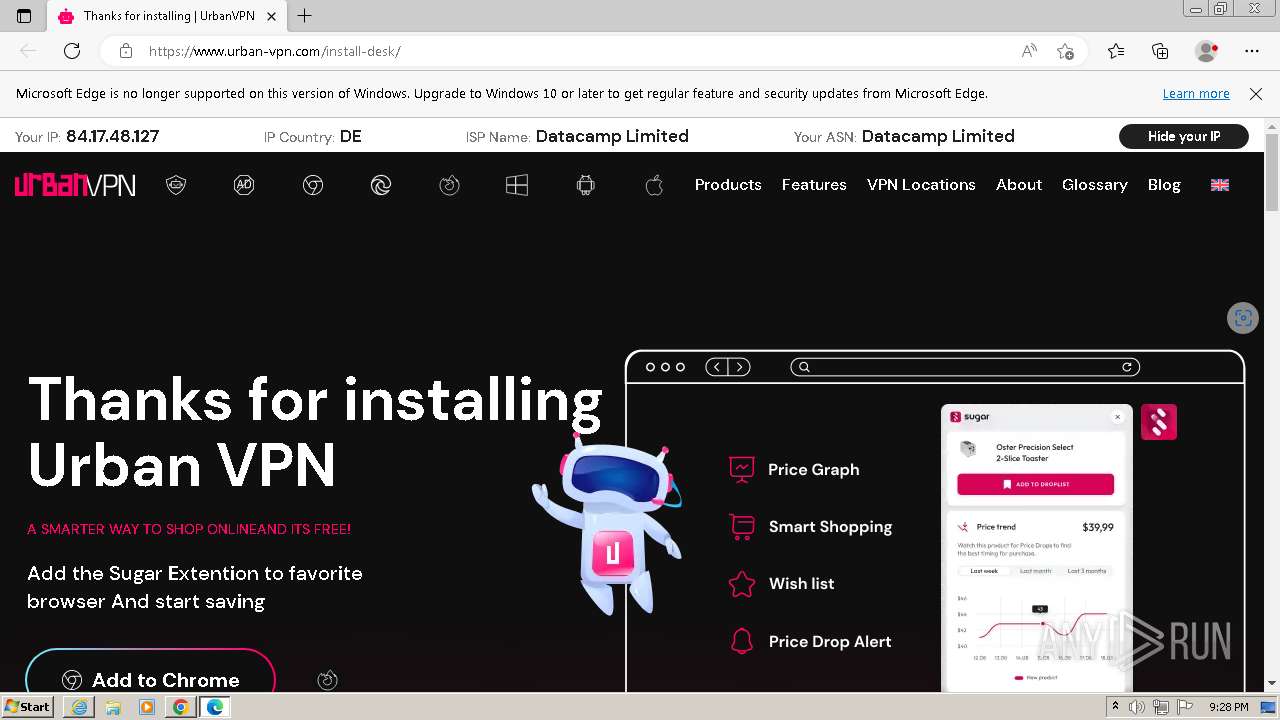
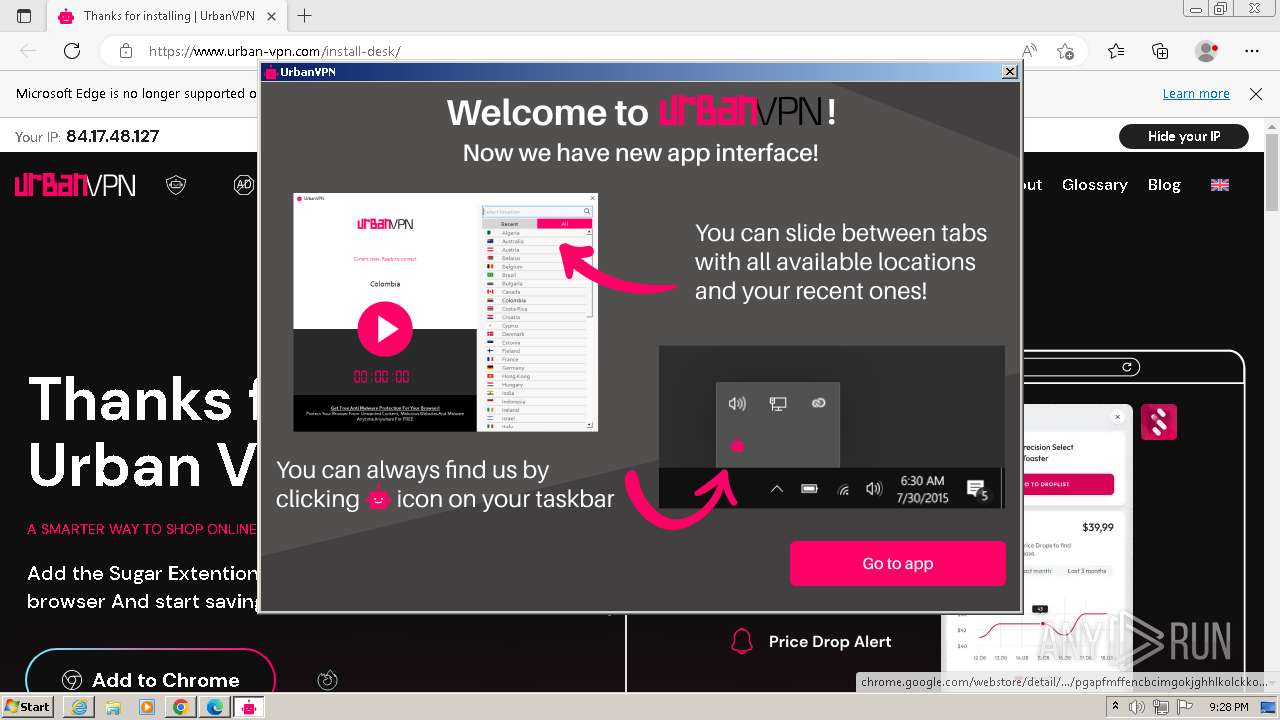
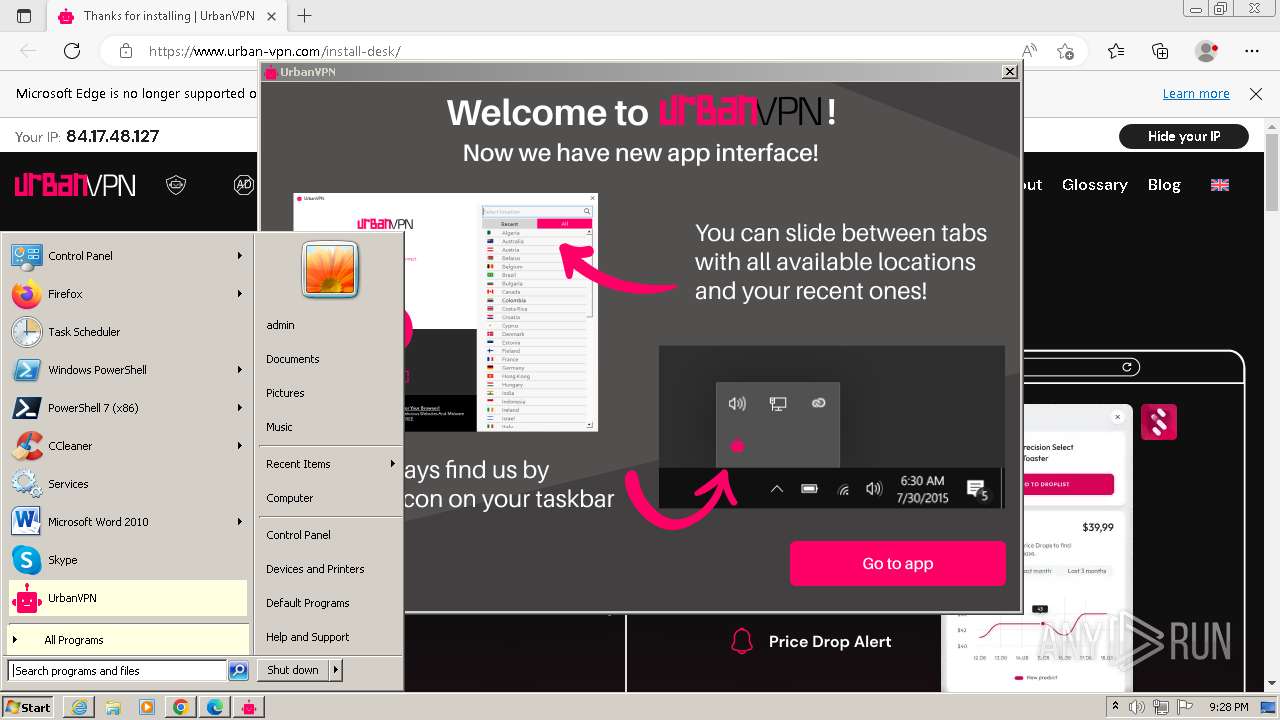
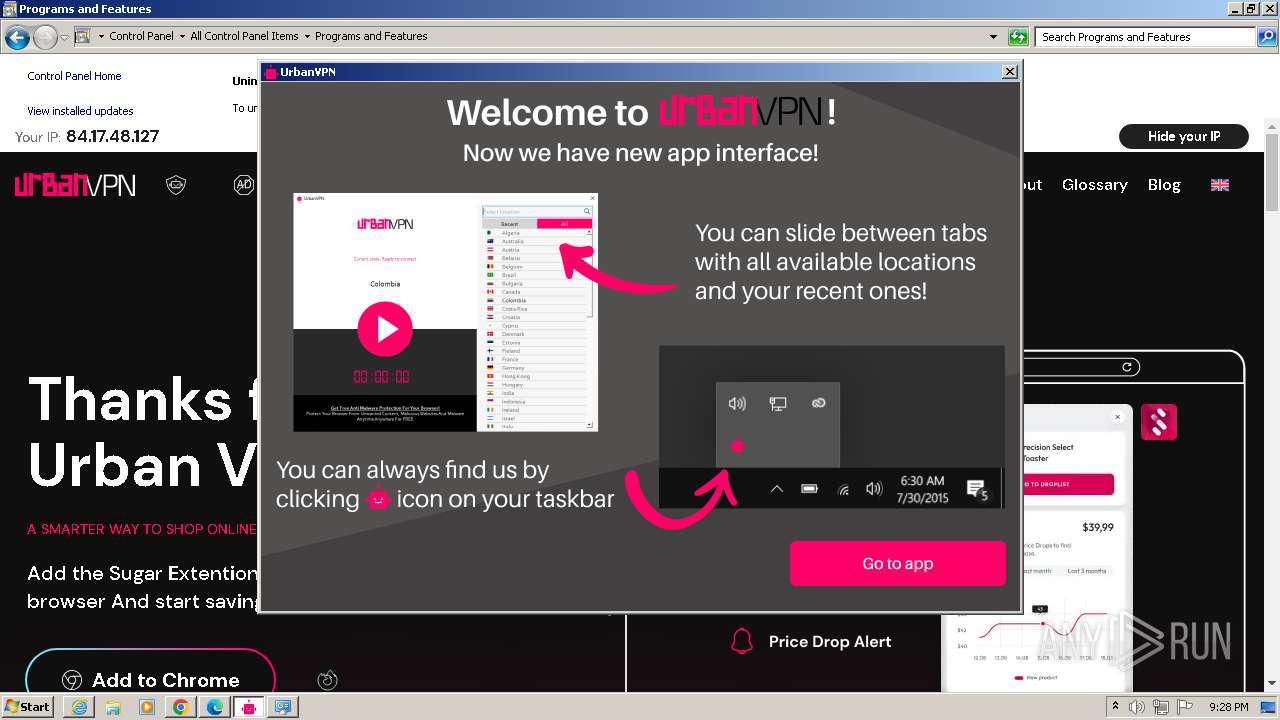
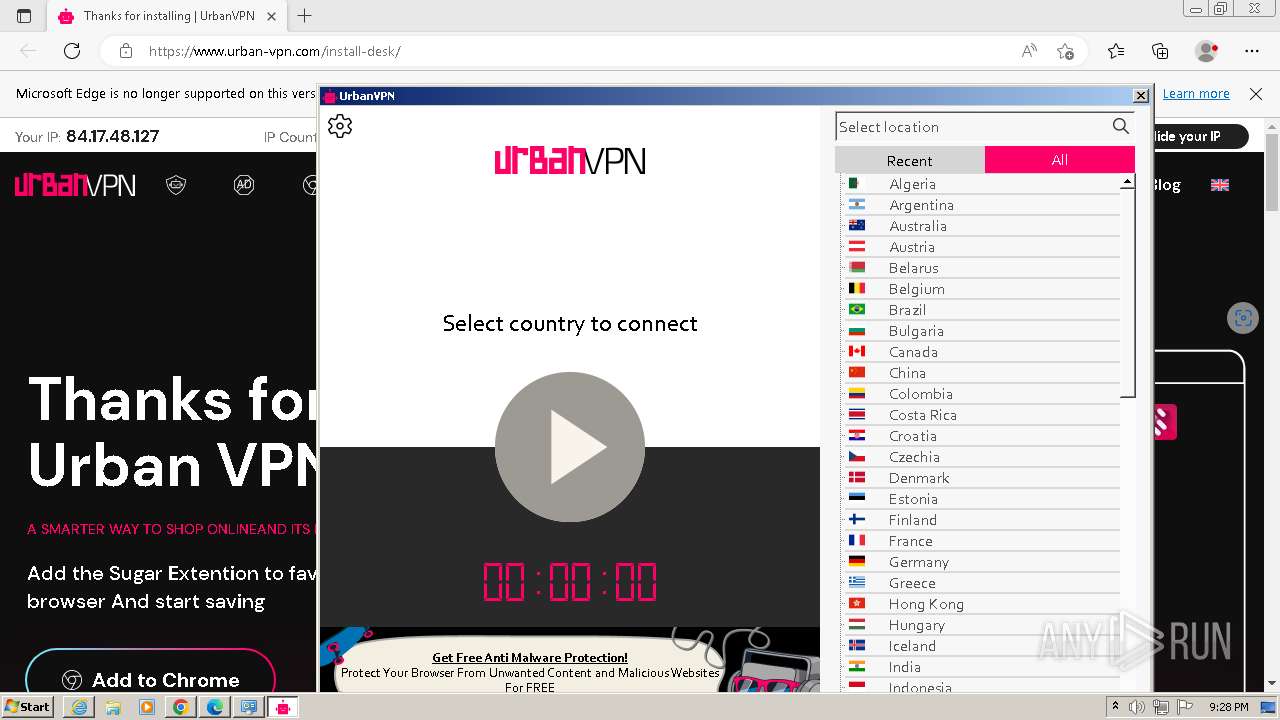
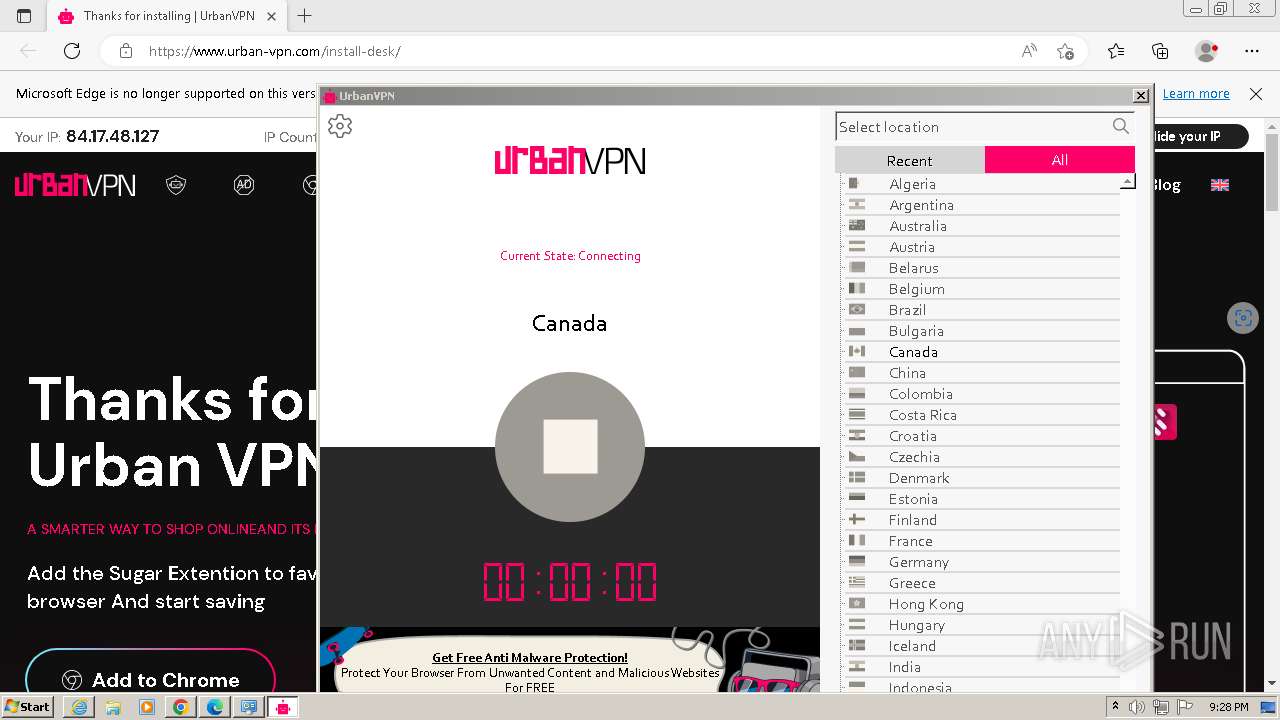
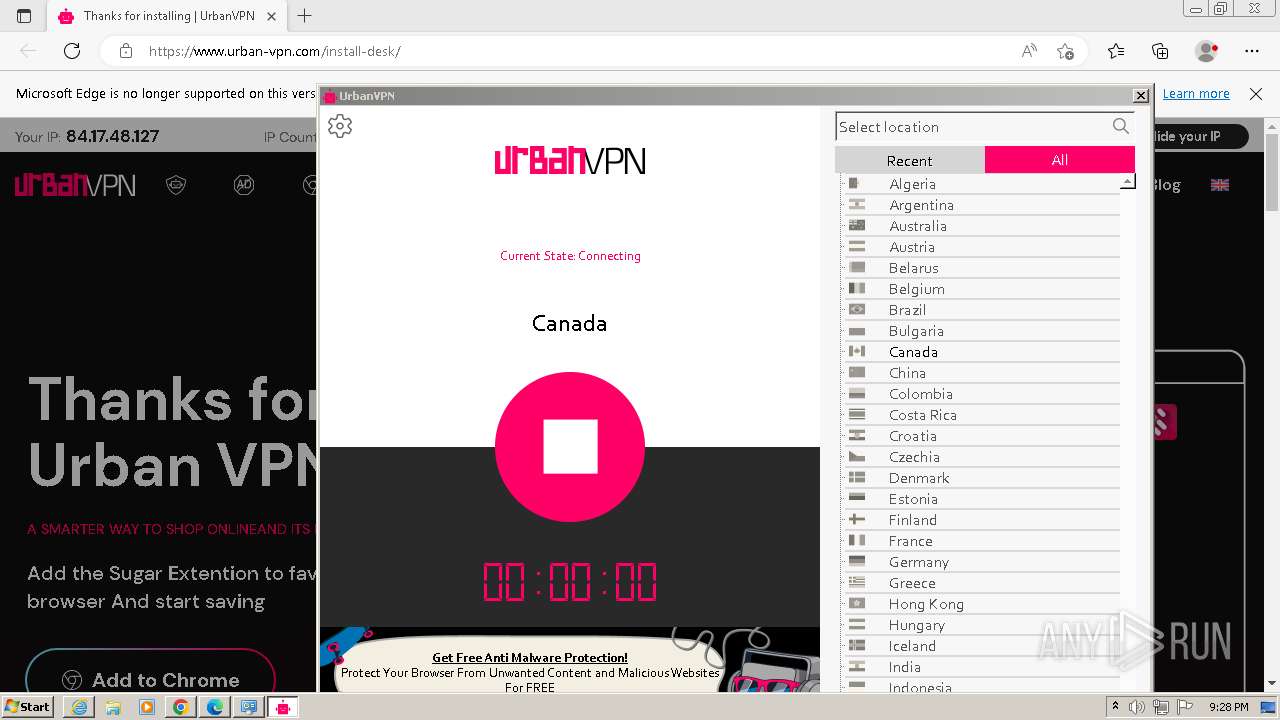
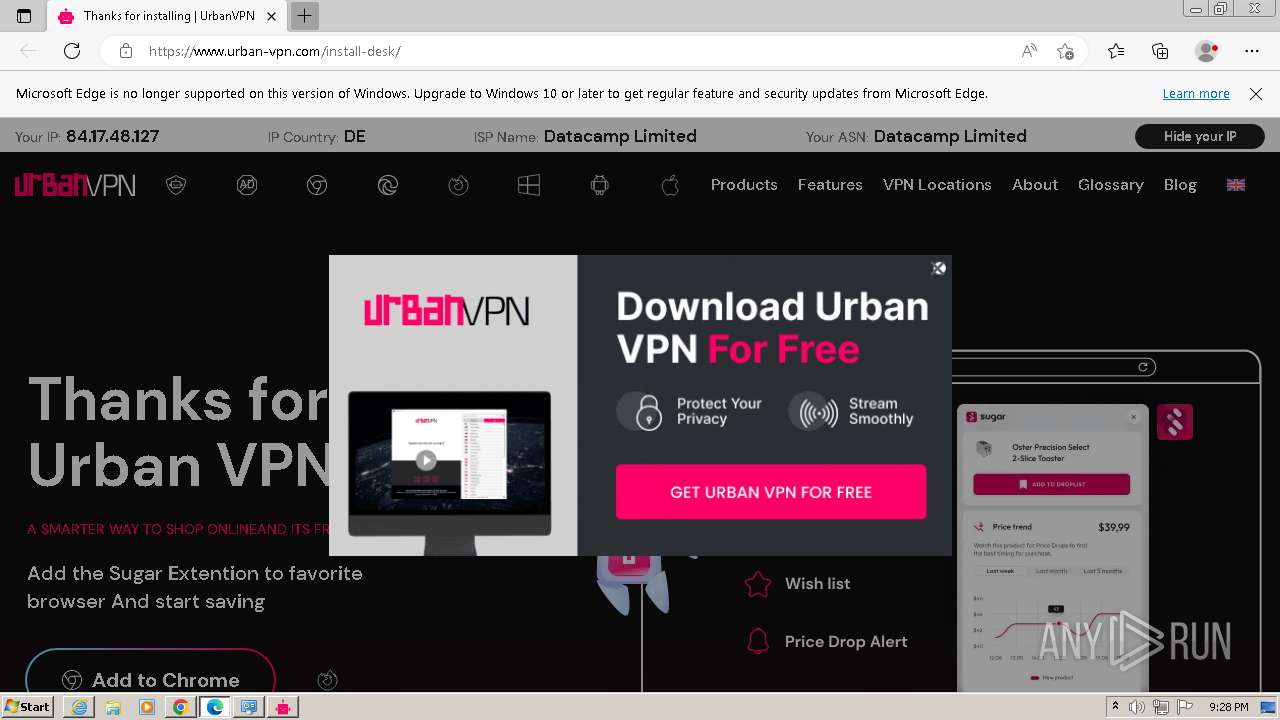
| URL: | https://urban-vpn.com/ |
| Full analysis: | https://app.any.run/tasks/6d8912e1-9f48-4b0d-bf48-f27b5fb62968 |
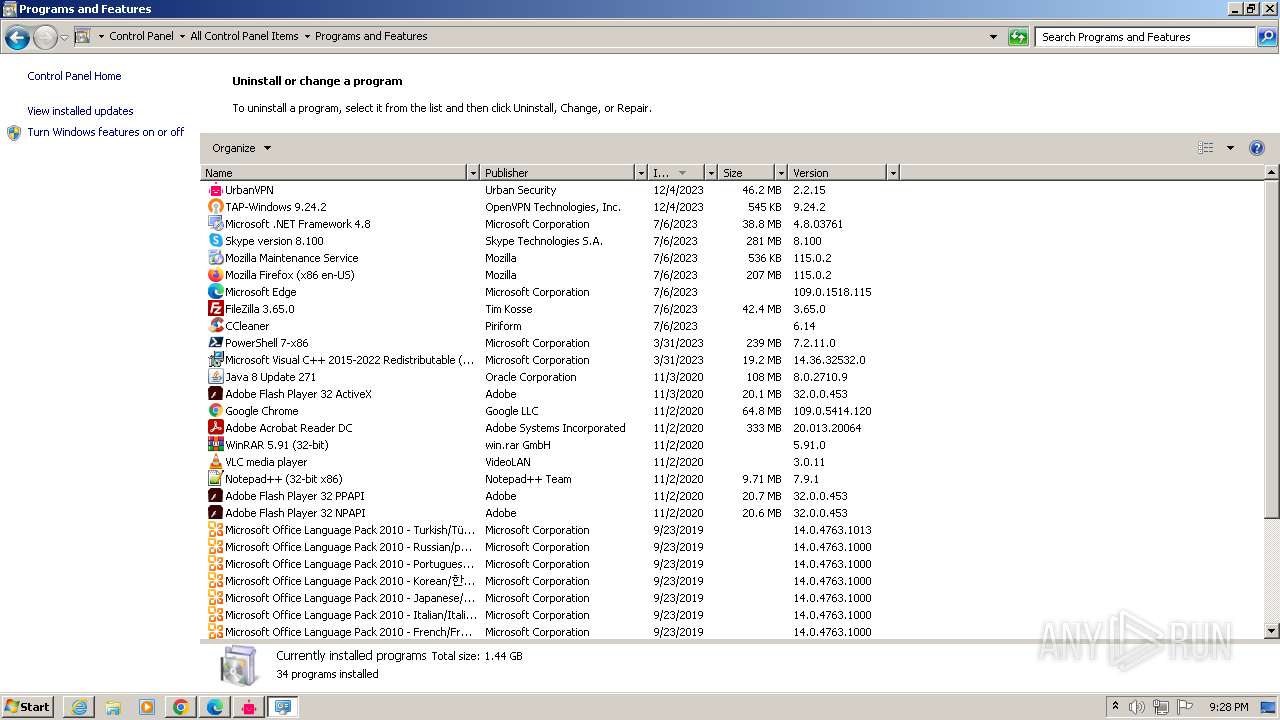
| Verdict: | Malicious activity |
| Analysis date: | December 04, 2023, 21:26:07 |
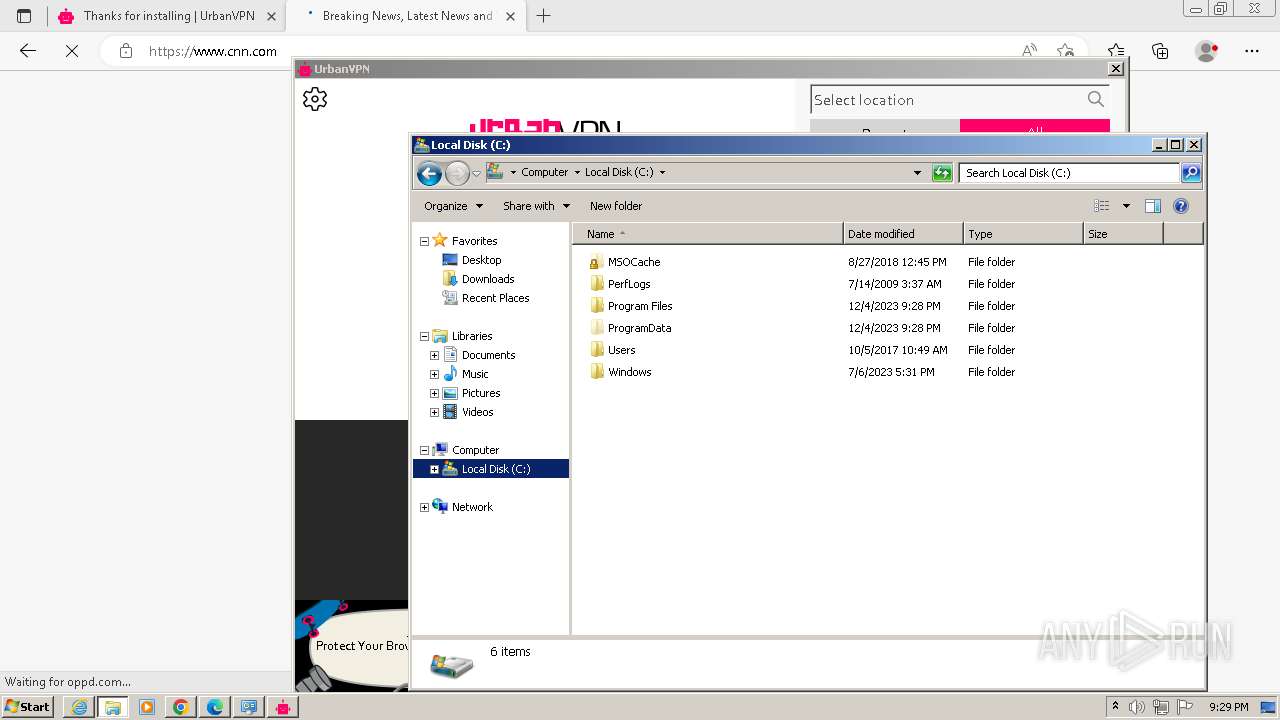
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 45264243BB54A00D5304203CCB8E9720 |
| SHA1: | D2CDE0A6D2305D619F374B3FE59075CC4F6A1B29 |
| SHA256: | AA94D9AAE484E0825CCB28BDD326CEAD54134038E40833382D8689ADB4750769 |
| SSDEEP: | 3:N8aihK:2aT |
MALICIOUS
Drops the executable file immediately after the start
- UrbanVPN.exe (PID: 2084)
- msiexec.exe (PID: 1852)
- MSIF149.tmp (PID: 1948)
- tapinstall.exe (PID: 2748)
- drvinst.exe (PID: 1008)
- drvinst.exe (PID: 2544)
The DLL Hijacking
- msiexec.exe (PID: 3152)
Creates a writable file in the system directory
- drvinst.exe (PID: 1008)
- drvinst.exe (PID: 2544)
SUSPICIOUS
Reads security settings of Internet Explorer
- UrbanVPN.exe (PID: 2084)
- UrbanVPN.exe (PID: 3304)
- tapinstall.exe (PID: 2748)
- UrbanVPNUpdater.exe (PID: 2888)
Reads settings of System Certificates
- UrbanVPN.exe (PID: 2084)
- UrbanVPN.exe (PID: 3304)
- tapinstall.exe (PID: 2748)
- rundll32.exe (PID: 1448)
- urbanvpn-gui.exe (PID: 3128)
- UrbanVPNUpdater.exe (PID: 2888)
Checks Windows Trust Settings
- UrbanVPN.exe (PID: 2084)
- msiexec.exe (PID: 1852)
- UrbanVPN.exe (PID: 3304)
- tapinstall.exe (PID: 2748)
- drvinst.exe (PID: 1008)
- drvinst.exe (PID: 2544)
- UrbanVPNUpdater.exe (PID: 2888)
Reads the Windows owner or organization settings
- UrbanVPN.exe (PID: 2084)
- UrbanVPN.exe (PID: 3304)
Checks for Java to be installed
- msiexec.exe (PID: 3152)
Reads Internet Explorer settings
- UrbanVPN.exe (PID: 2084)
Reads the Internet Settings
- UrbanVPN.exe (PID: 2084)
- MSI3328.tmp (PID: 304)
- UrbanVPNUpdater.exe (PID: 2888)
- urbanvpn-gui.exe (PID: 3128)
Reads Microsoft Outlook installation path
- UrbanVPN.exe (PID: 2084)
Application launched itself
- UrbanVPN.exe (PID: 2084)
Executes as Windows Service
- VSSVC.exe (PID: 3204)
- urbanvpnserv.exe (PID: 3384)
Malware-specific behavior (creating "System.dll" in Temp)
- MSIF149.tmp (PID: 1948)
The process creates files with name similar to system file names
- MSIF149.tmp (PID: 1948)
- msiexec.exe (PID: 1852)
Drops a system driver (possible attempt to evade defenses)
- MSIF149.tmp (PID: 1948)
- tapinstall.exe (PID: 2748)
- drvinst.exe (PID: 1008)
- drvinst.exe (PID: 2544)
Starts application with an unusual extension
- MSIF149.tmp (PID: 1948)
Creates files in the driver directory
- drvinst.exe (PID: 1008)
- drvinst.exe (PID: 2544)
Connects to unusual port
- msiexec.exe (PID: 2116)
- urbanvpnserv.exe (PID: 3384)
INFO
Checks supported languages
- wmpnscfg.exe (PID: 1560)
- UrbanVPN.exe (PID: 2084)
- msiexec.exe (PID: 1852)
- msiexec.exe (PID: 3152)
- msiexec.exe (PID: 2116)
- UrbanVPN.exe (PID: 3304)
- MSIF149.tmp (PID: 1948)
- tapinstall.exe (PID: 2096)
- nsF242.tmp (PID: 2828)
- tapinstall.exe (PID: 2748)
- nsF2C0.tmp (PID: 1588)
- drvinst.exe (PID: 1008)
- drvinst.exe (PID: 2544)
- msiexec.exe (PID: 2992)
- MSI3328.tmp (PID: 304)
- urbanvpn-gui.exe (PID: 3128)
- urbanvpn.exe (PID: 3036)
- UrbanVPNUpdater.exe (PID: 1888)
- urbanvpnserv.exe (PID: 3384)
- UrbanVPNUpdater.exe (PID: 2888)
- urbanvpn.exe (PID: 4728)
- wmpnscfg.exe (PID: 6060)
- wmpnscfg.exe (PID: 1620)
- wmpnscfg.exe (PID: 5188)
- wmpnscfg.exe (PID: 5444)
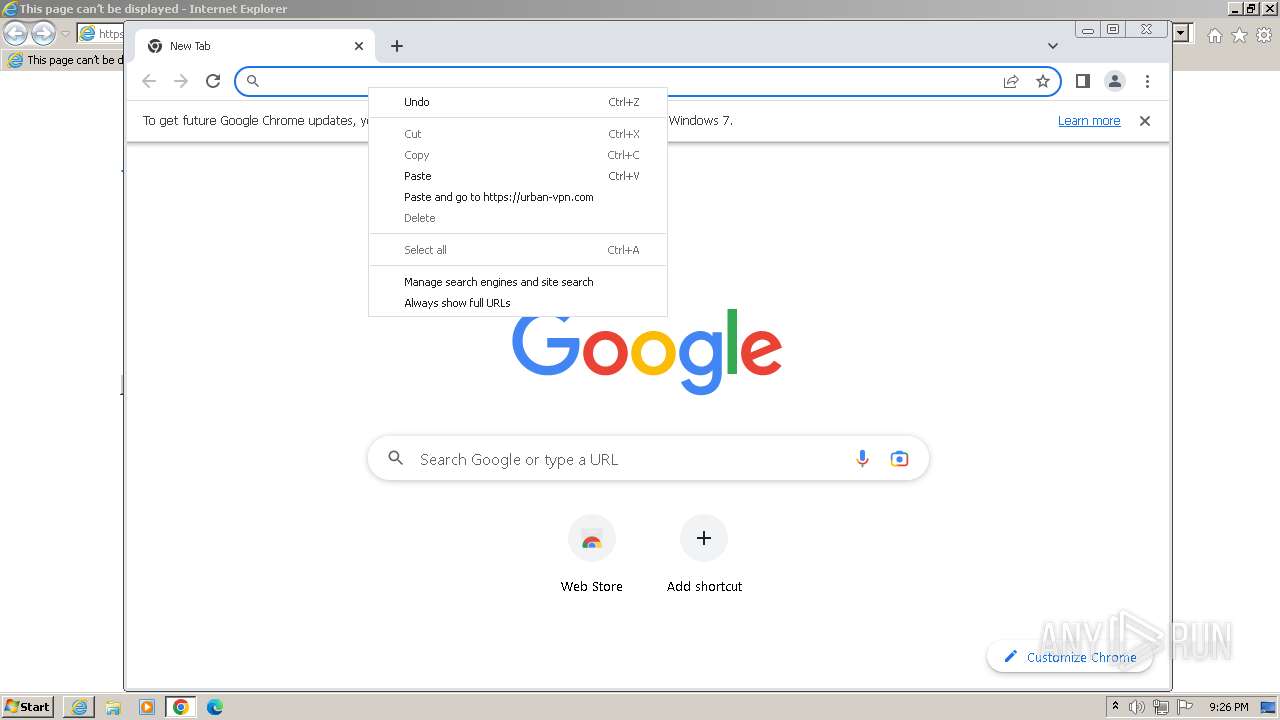
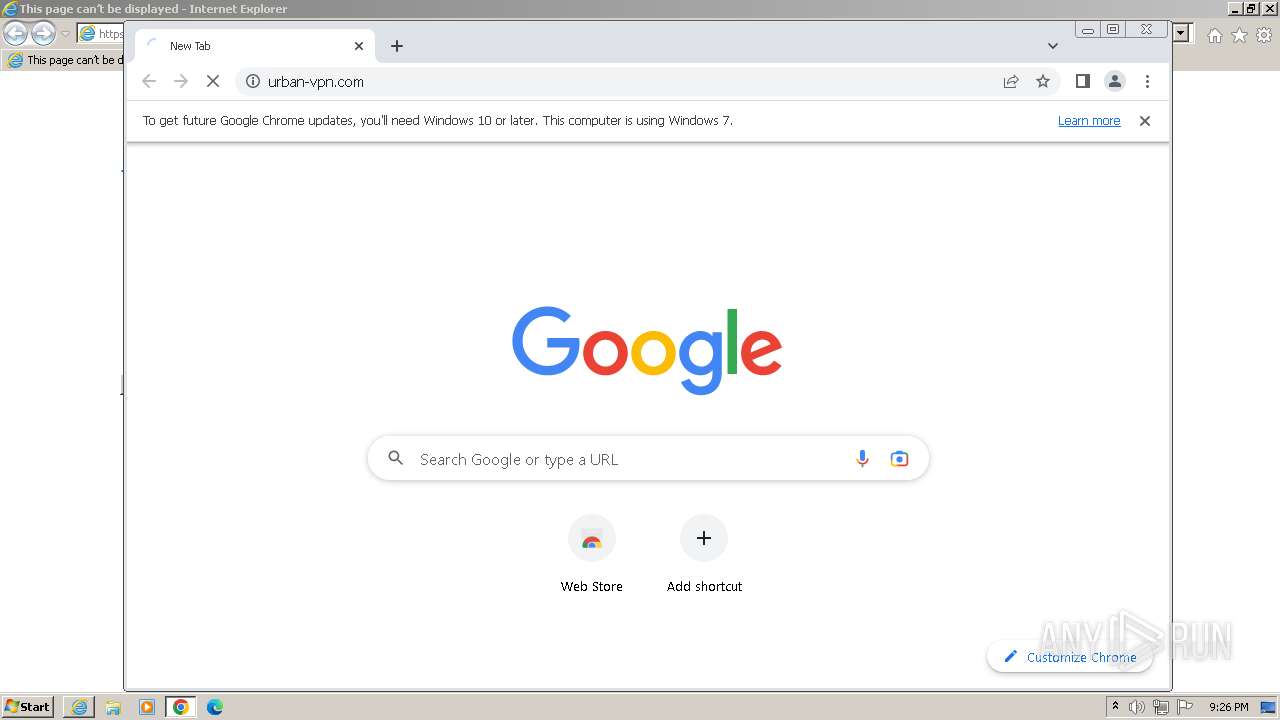
Application launched itself
- iexplore.exe (PID: 1236)
- chrome.exe (PID: 2332)
- msiexec.exe (PID: 1852)
- msedge.exe (PID: 3048)
- msedge.exe (PID: 3444)
Reads the computer name
- wmpnscfg.exe (PID: 1560)
- UrbanVPN.exe (PID: 2084)
- msiexec.exe (PID: 1852)
- UrbanVPN.exe (PID: 3304)
- msiexec.exe (PID: 2116)
- MSIF149.tmp (PID: 1948)
- tapinstall.exe (PID: 2096)
- tapinstall.exe (PID: 2748)
- drvinst.exe (PID: 1008)
- drvinst.exe (PID: 2544)
- MSI3328.tmp (PID: 304)
- msiexec.exe (PID: 2992)
- urbanvpn-gui.exe (PID: 3128)
- UrbanVPNUpdater.exe (PID: 2888)
- UrbanVPNUpdater.exe (PID: 1888)
- urbanvpnserv.exe (PID: 3384)
- urbanvpn.exe (PID: 4728)
- msiexec.exe (PID: 3152)
- wmpnscfg.exe (PID: 5444)
- wmpnscfg.exe (PID: 6060)
- wmpnscfg.exe (PID: 1620)
- wmpnscfg.exe (PID: 5188)
Manual execution by a user
- wmpnscfg.exe (PID: 1560)
- chrome.exe (PID: 2332)
- msedge.exe (PID: 3444)
- UrbanVPNUpdater.exe (PID: 2888)
- wmpnscfg.exe (PID: 5444)
- wmpnscfg.exe (PID: 6060)
- explorer.exe (PID: 6080)
- wmpnscfg.exe (PID: 1620)
- wmpnscfg.exe (PID: 5188)
Drops the executable file immediately after the start
- chrome.exe (PID: 2332)
- chrome.exe (PID: 1696)
- chrome.exe (PID: 4472)
The process uses the downloaded file
- chrome.exe (PID: 2392)
- chrome.exe (PID: 2332)
- UrbanVPN.exe (PID: 2084)
Creates files or folders in the user directory
- UrbanVPN.exe (PID: 2084)
- urbanvpn-gui.exe (PID: 3128)
Reads the machine GUID from the registry
- UrbanVPN.exe (PID: 2084)
- msiexec.exe (PID: 1852)
- msiexec.exe (PID: 3152)
- UrbanVPN.exe (PID: 3304)
- msiexec.exe (PID: 2116)
- tapinstall.exe (PID: 2748)
- drvinst.exe (PID: 1008)
- drvinst.exe (PID: 2544)
- MSI3328.tmp (PID: 304)
- msiexec.exe (PID: 2992)
- urbanvpnserv.exe (PID: 3384)
- urbanvpn-gui.exe (PID: 3128)
- UrbanVPNUpdater.exe (PID: 2888)
- urbanvpn.exe (PID: 4728)
Create files in a temporary directory
- UrbanVPN.exe (PID: 2084)
- msiexec.exe (PID: 3152)
- msiexec.exe (PID: 2116)
- msiexec.exe (PID: 1852)
- MSIF149.tmp (PID: 1948)
- tapinstall.exe (PID: 2748)
- MSI3328.tmp (PID: 304)
Reads Environment values
- UrbanVPN.exe (PID: 2084)
- msiexec.exe (PID: 3152)
- UrbanVPN.exe (PID: 3304)
- msiexec.exe (PID: 2116)
- drvinst.exe (PID: 2544)
- urbanvpnserv.exe (PID: 3384)
- UrbanVPNUpdater.exe (PID: 2888)
Process checks Powershell version
- msiexec.exe (PID: 3152)
Reads Microsoft Office registry keys
- msiexec.exe (PID: 3152)
Checks proxy server information
- UrbanVPN.exe (PID: 2084)
- UrbanVPNUpdater.exe (PID: 2888)
Process checks are UAC notifies on
- msiexec.exe (PID: 2116)
Starts application with an unusual extension
- msiexec.exe (PID: 1852)
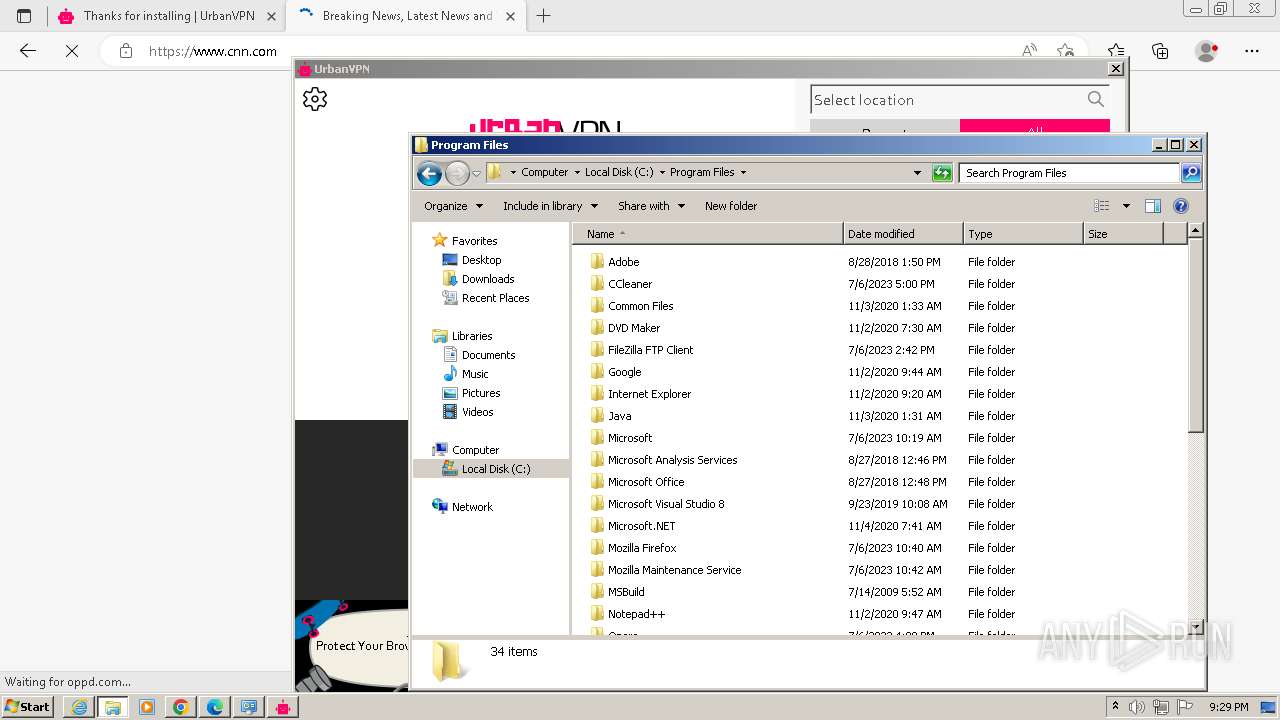
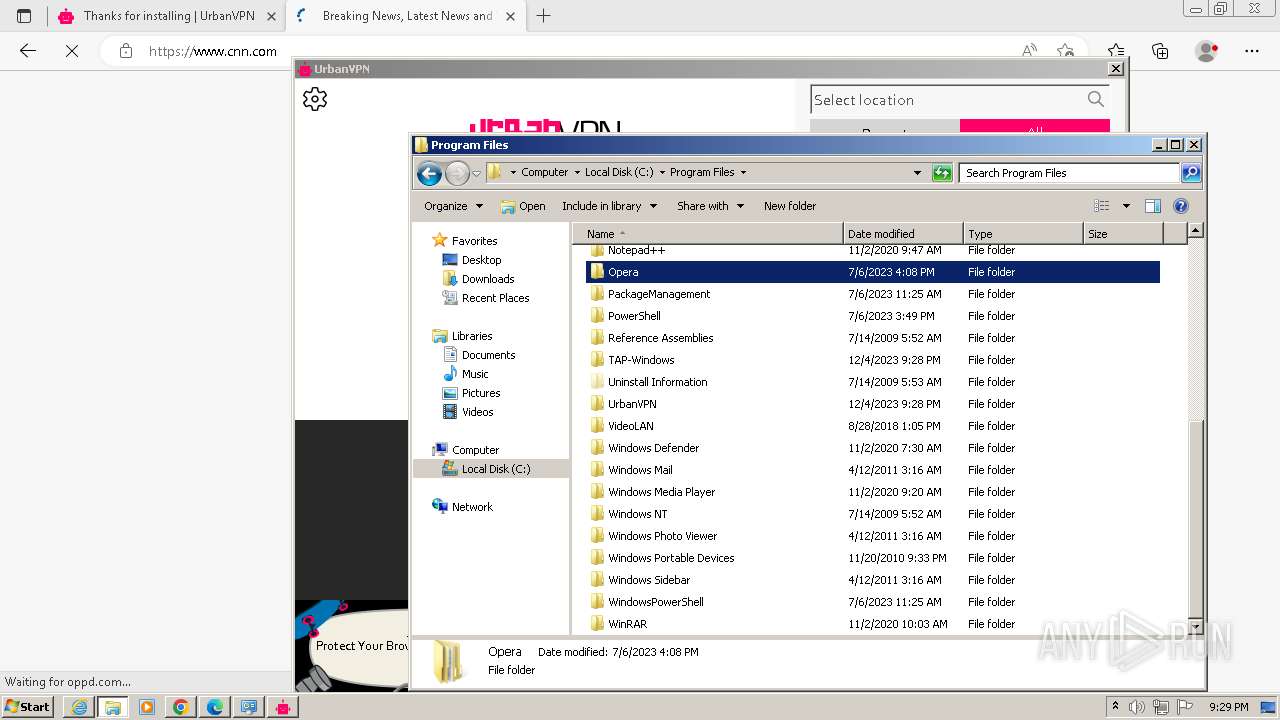
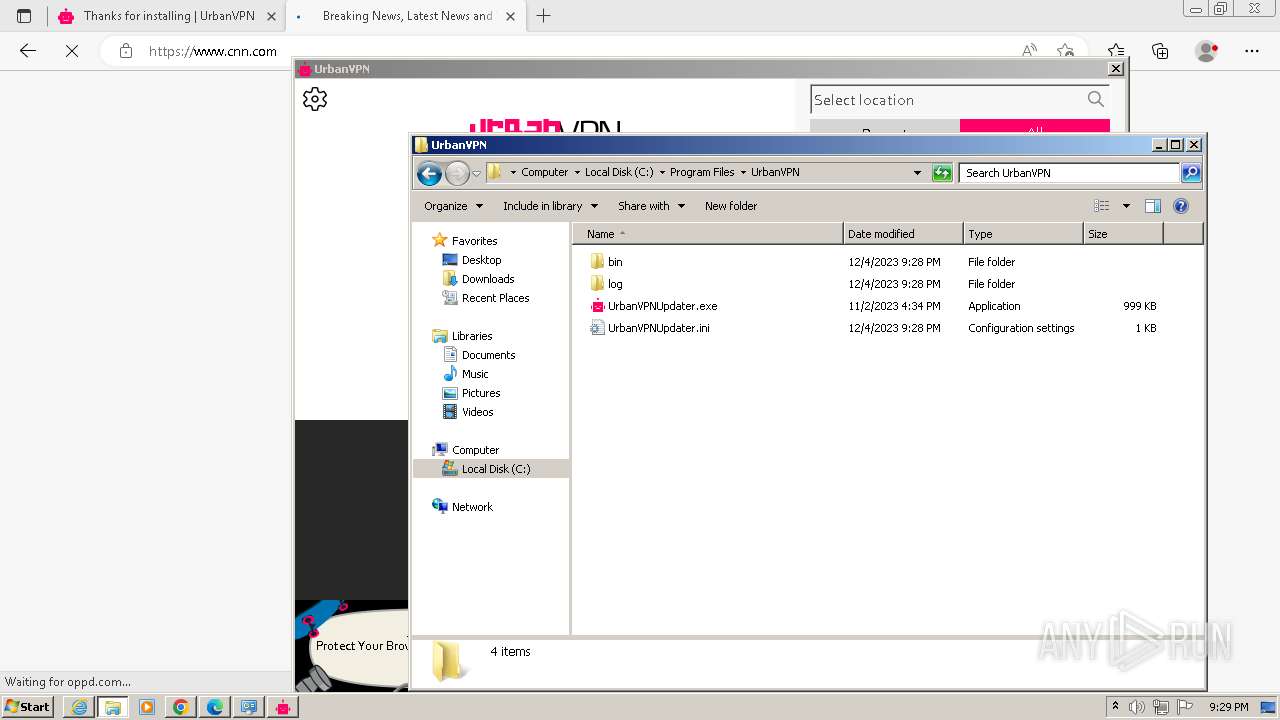
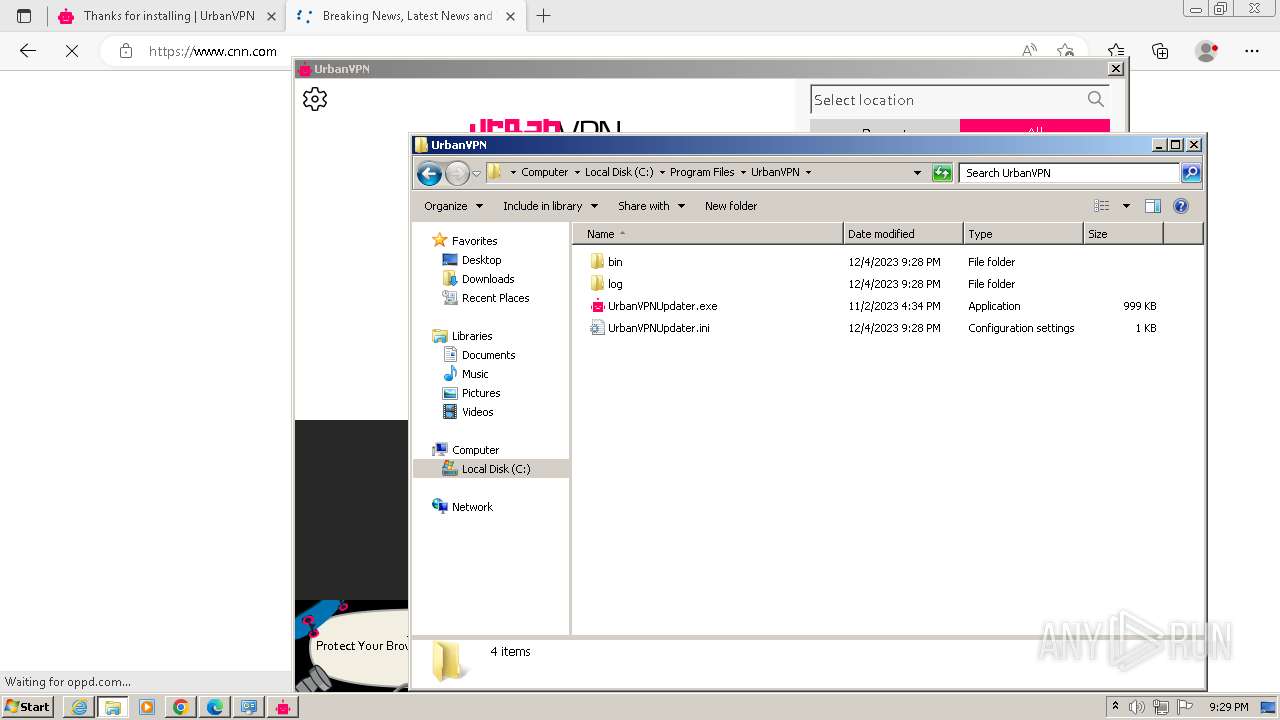
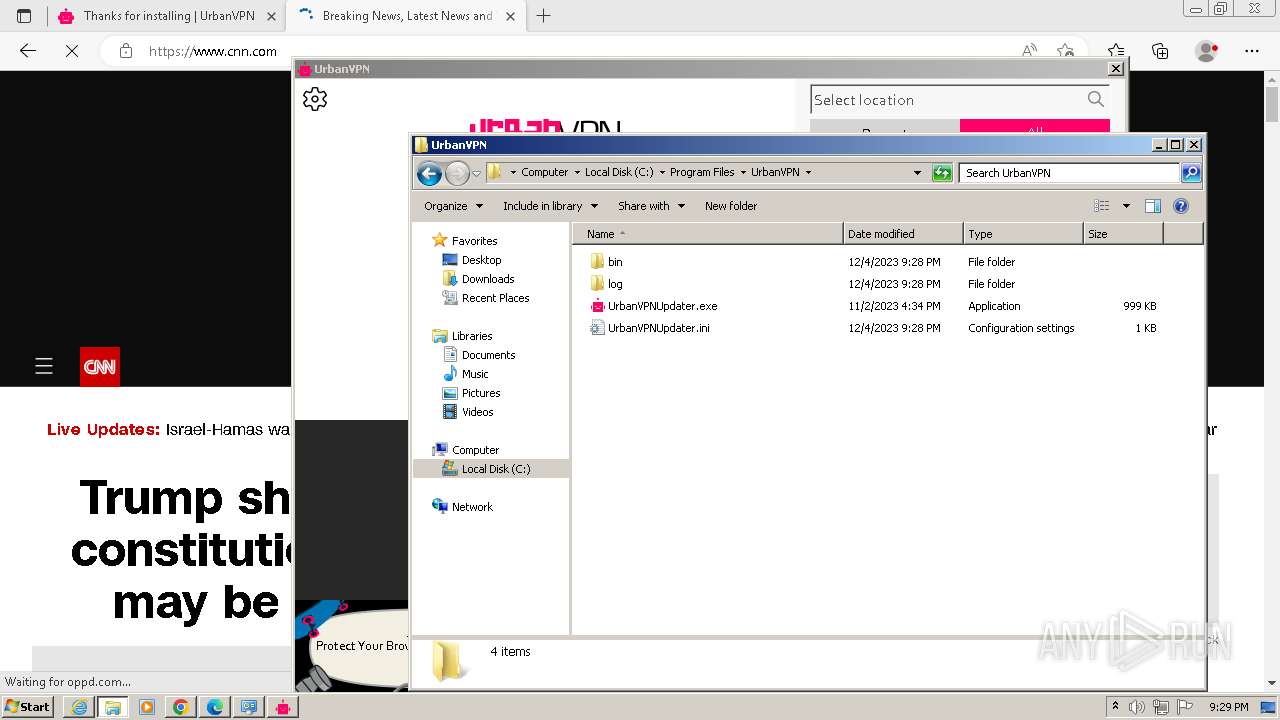
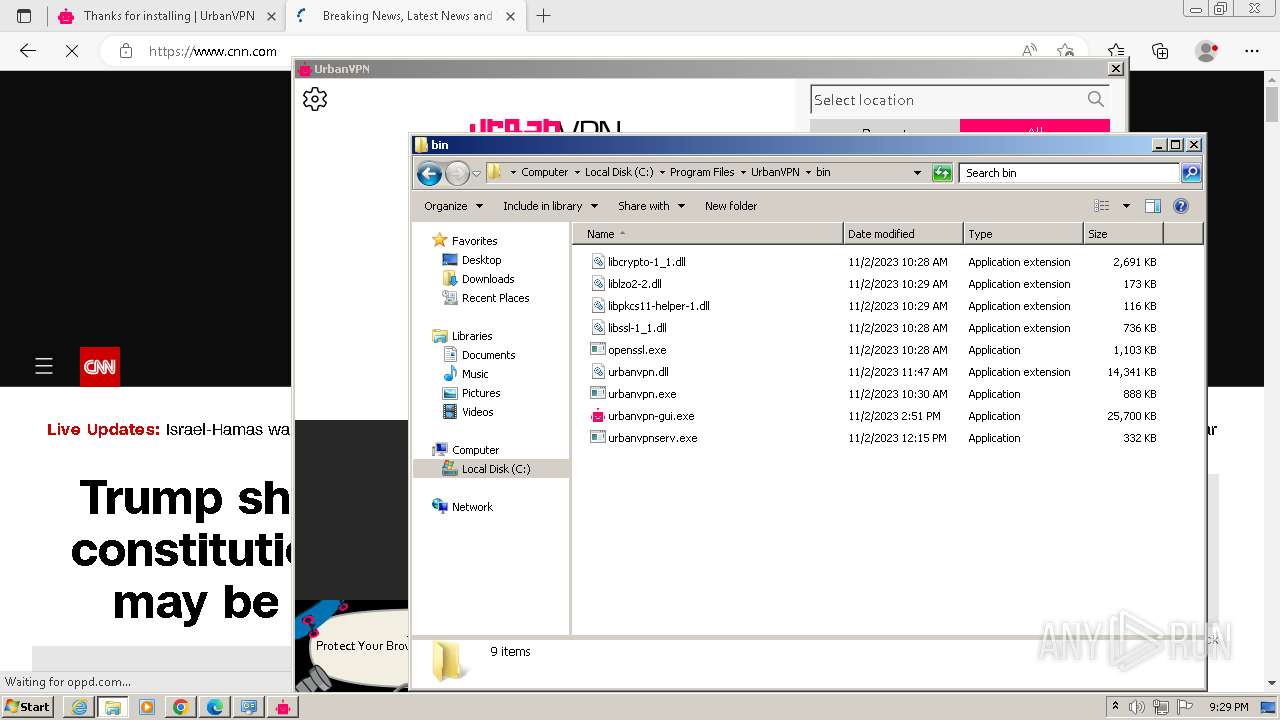
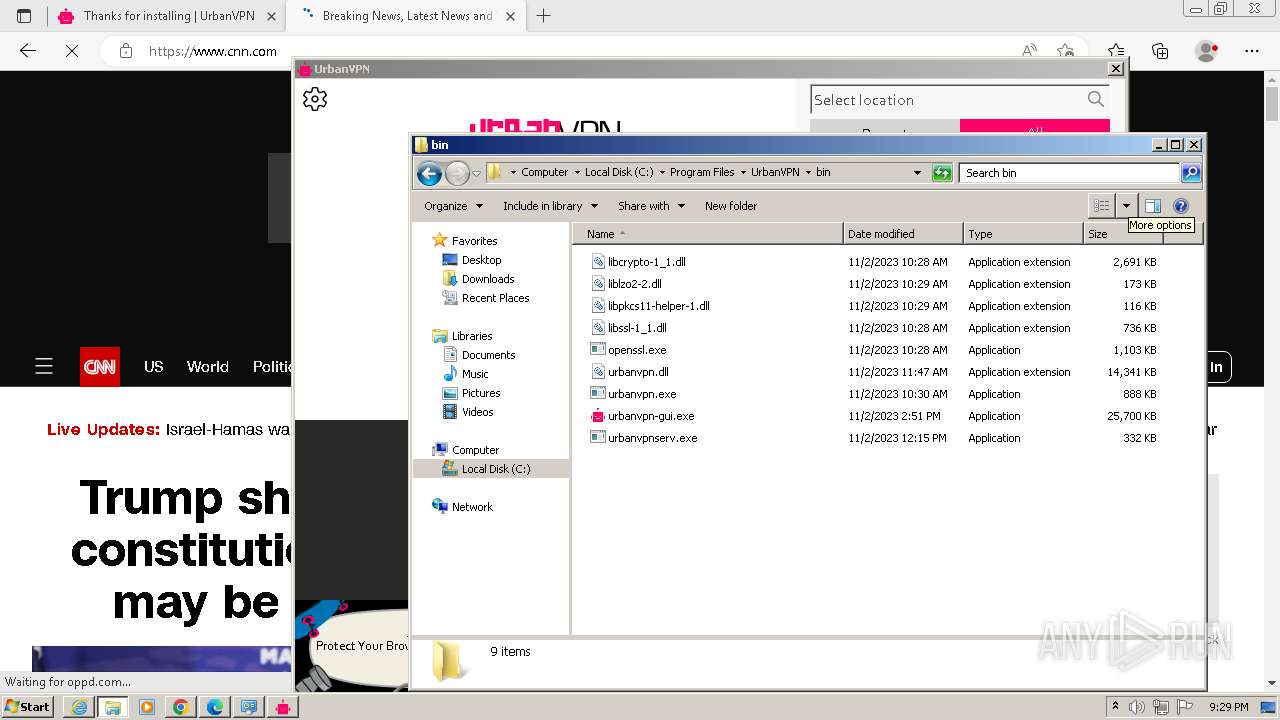
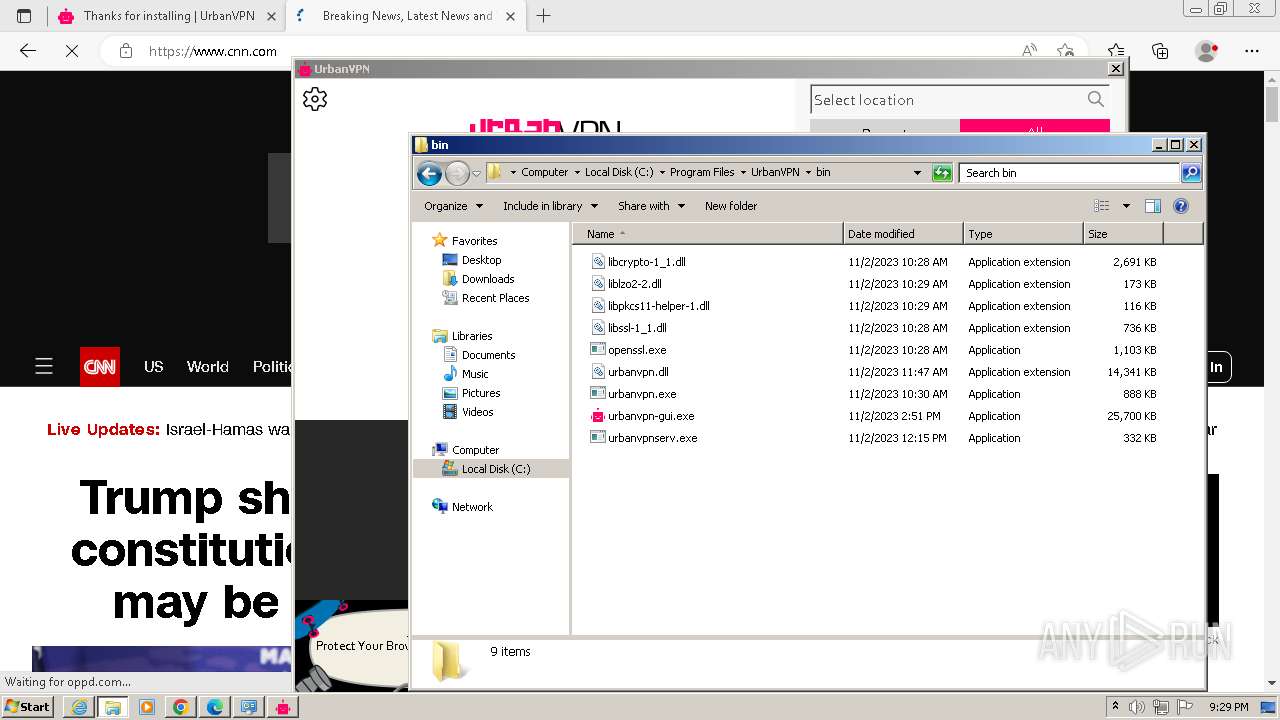
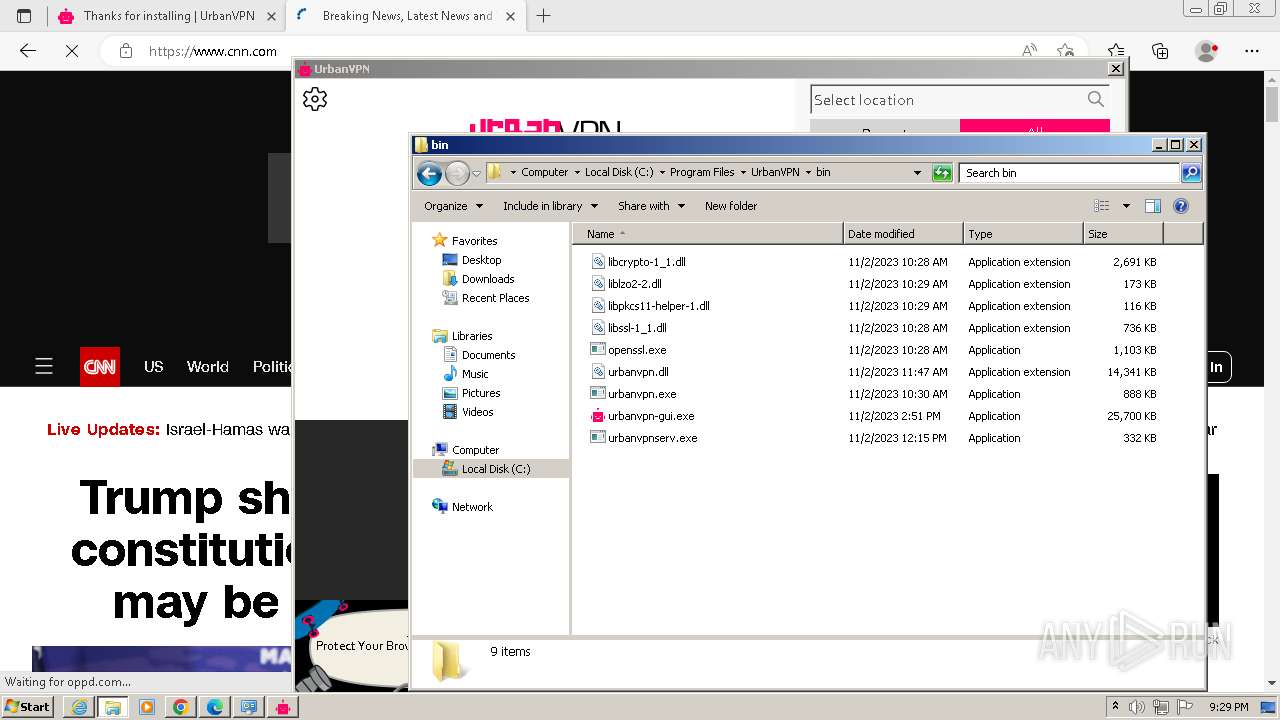
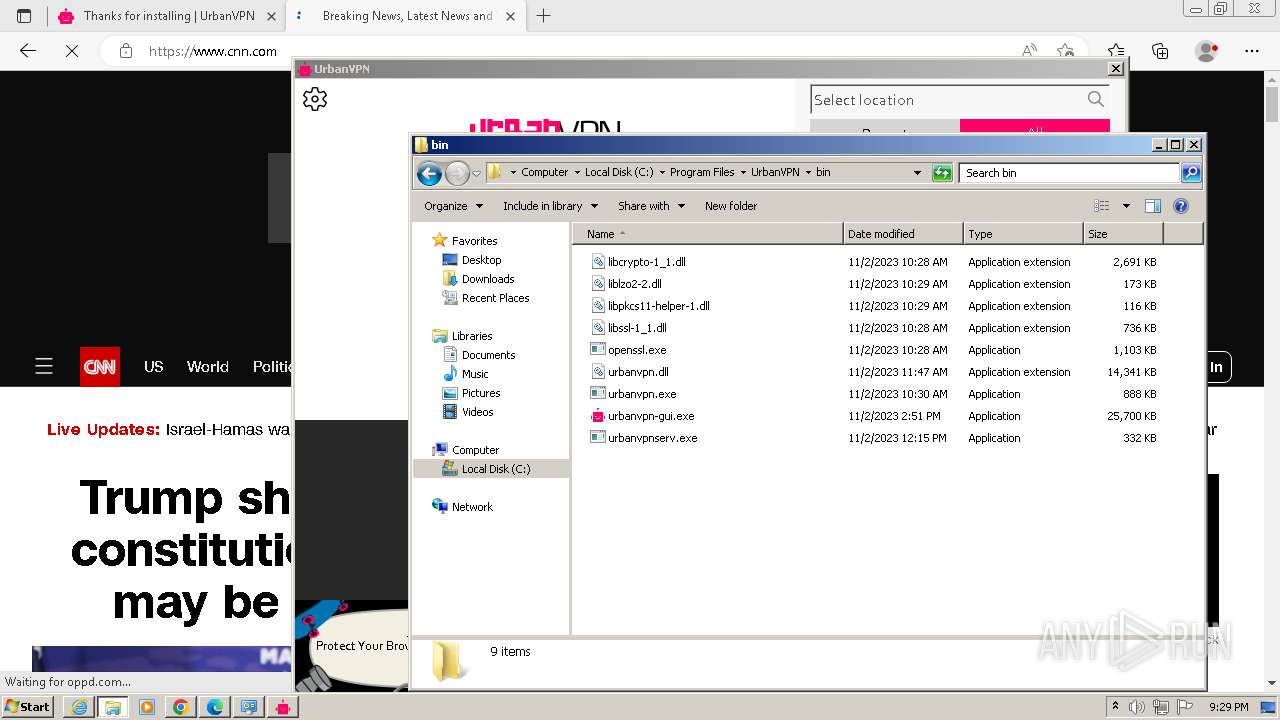
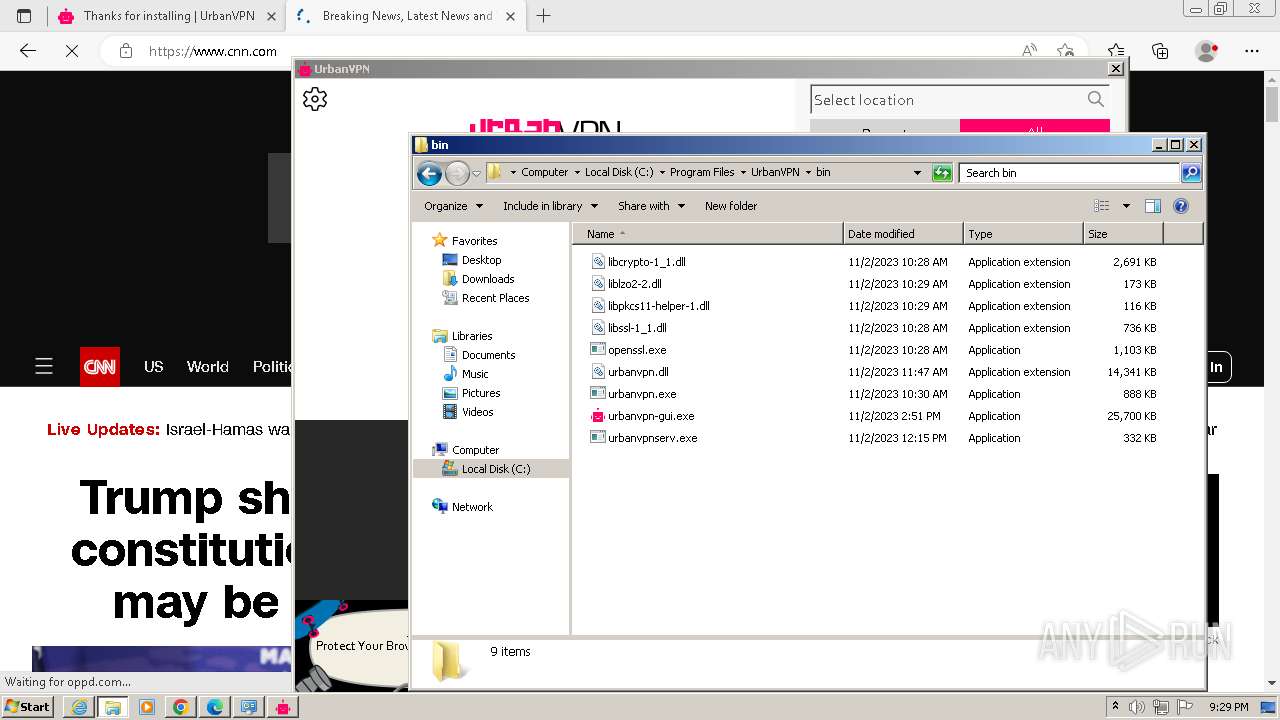
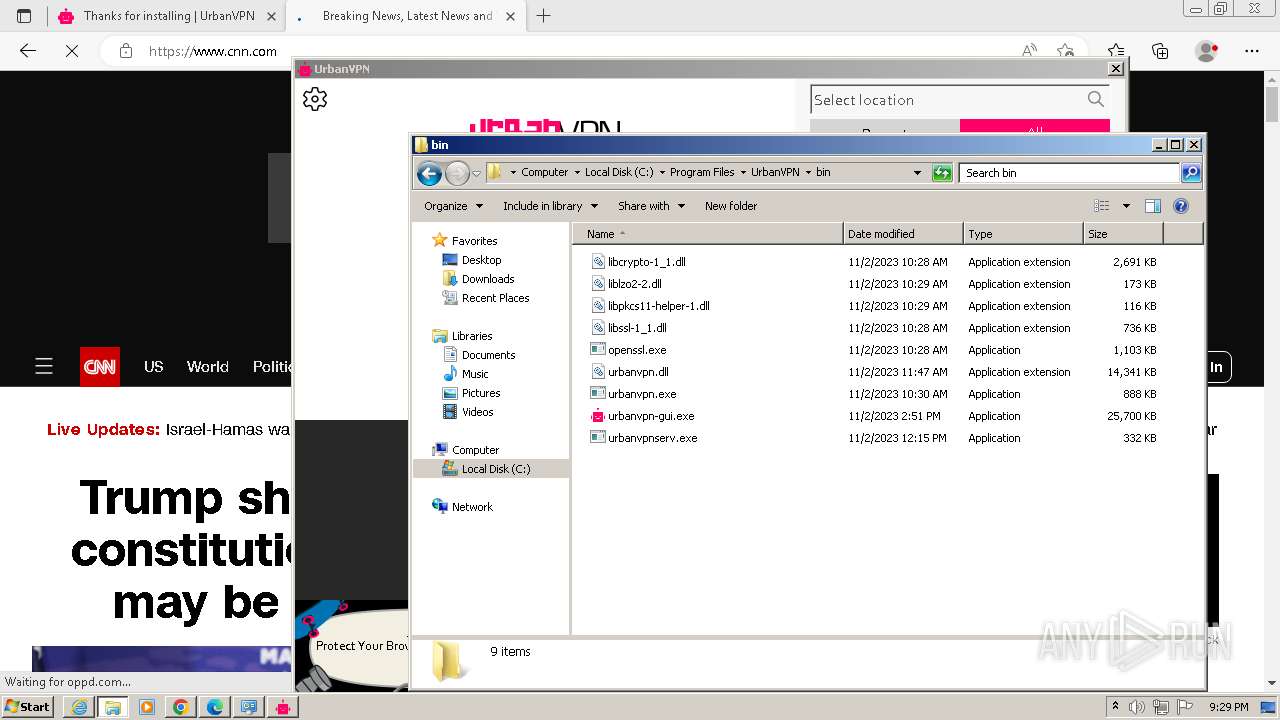
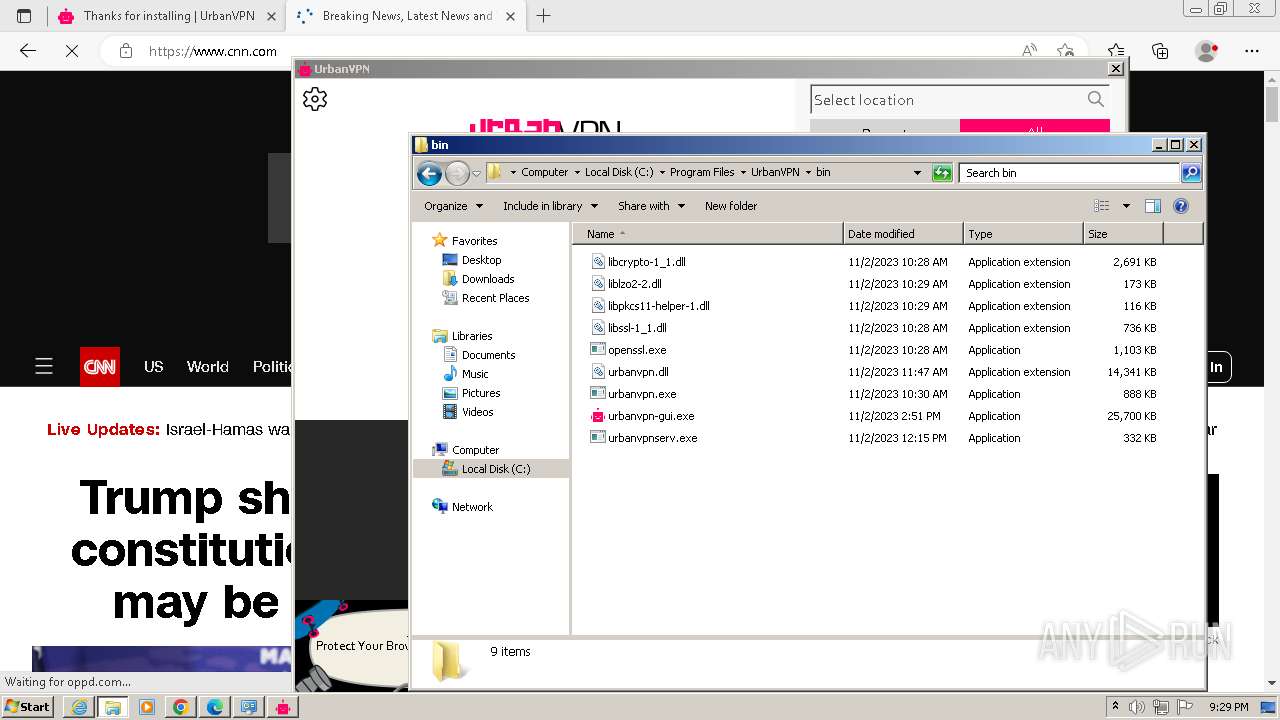
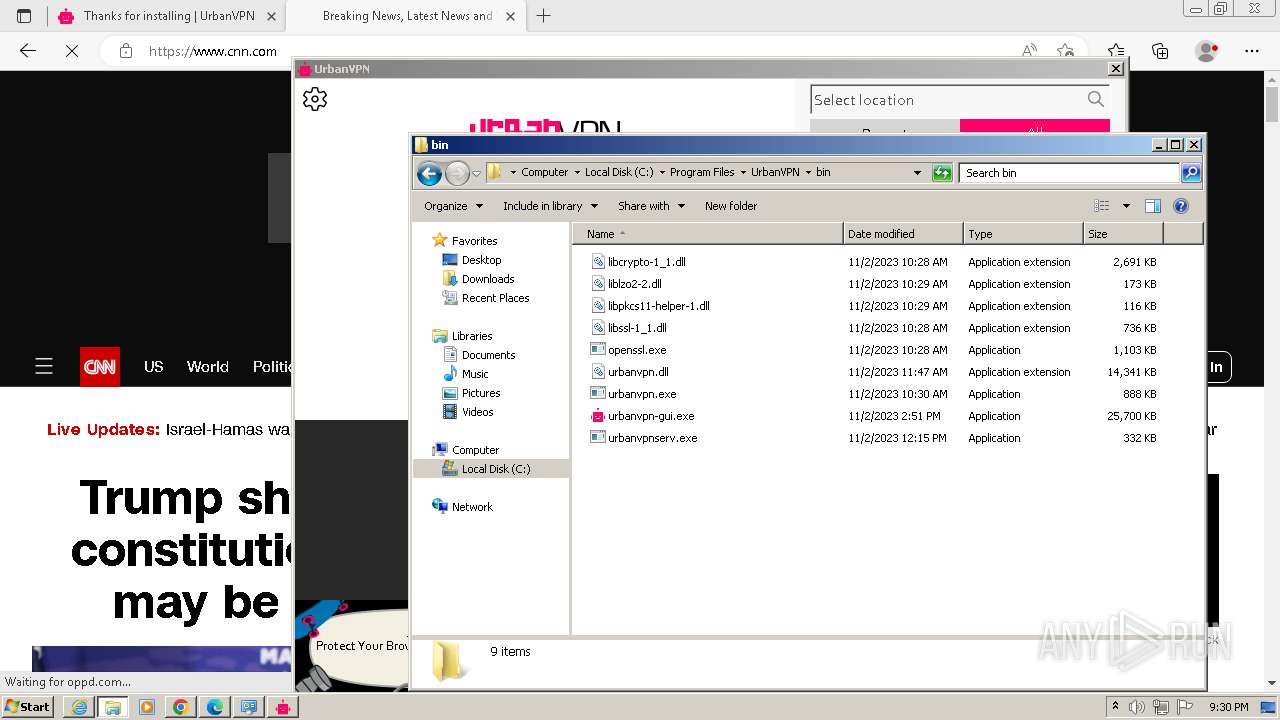
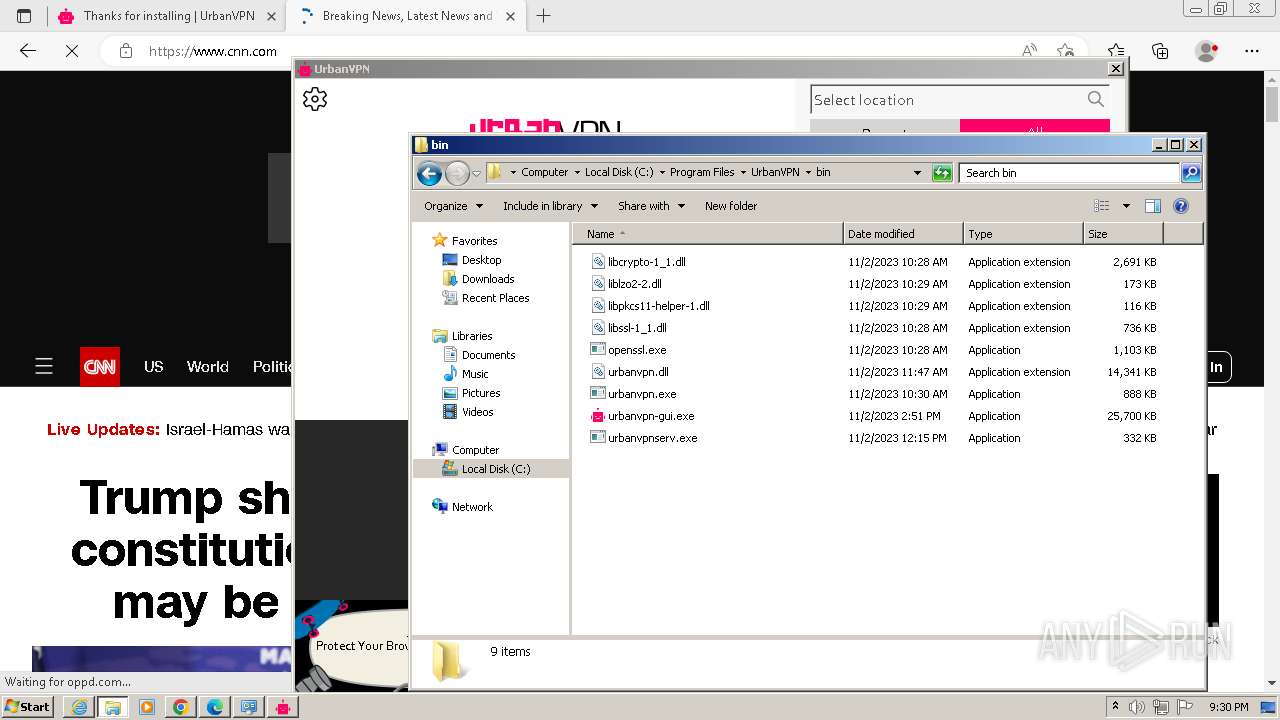
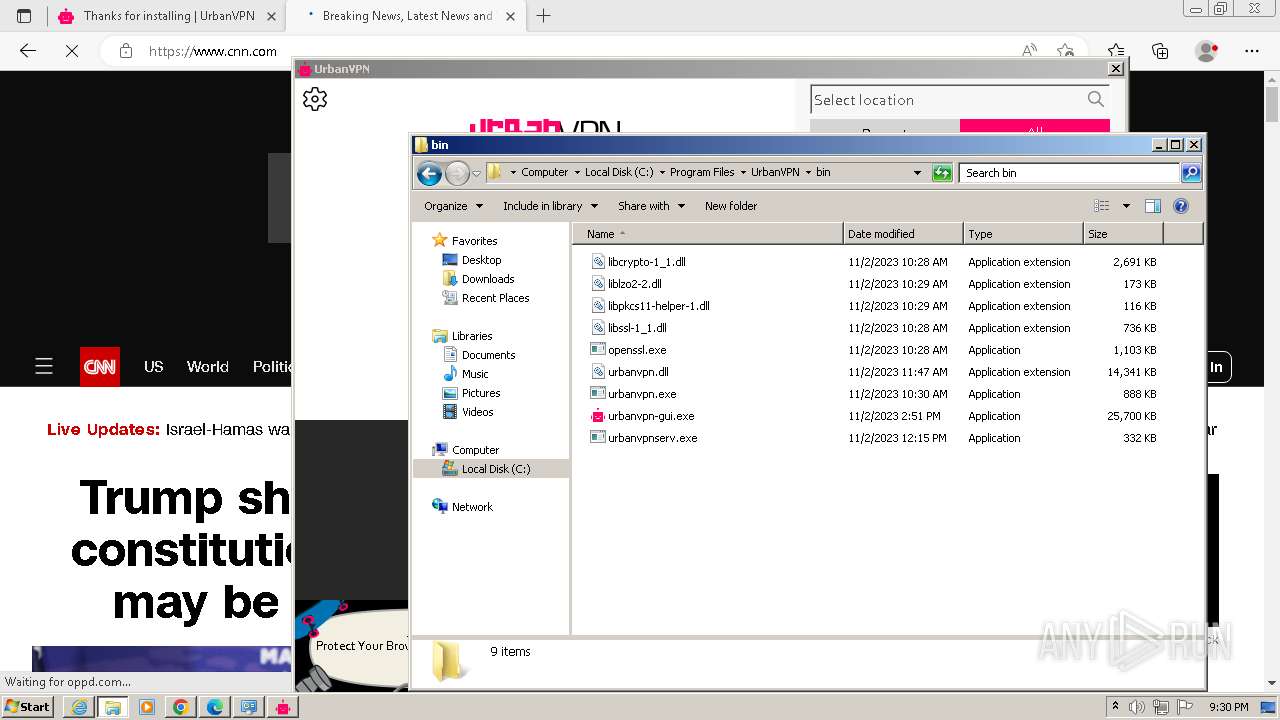
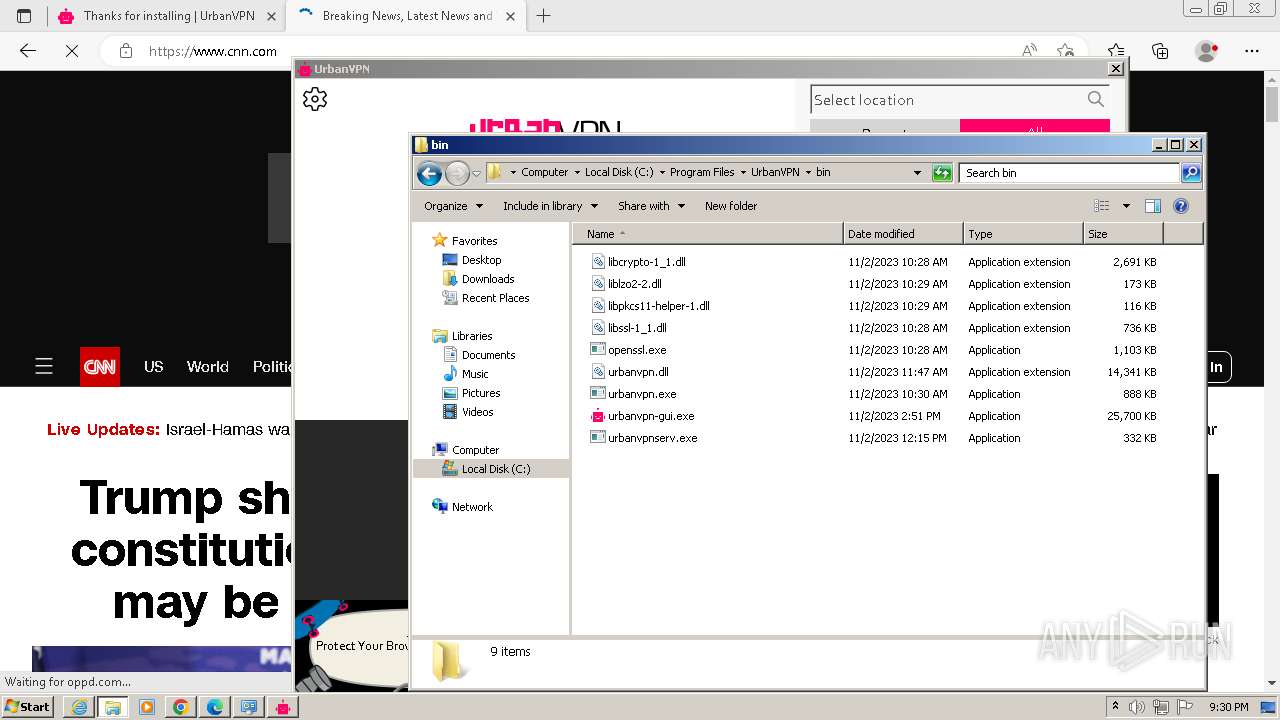
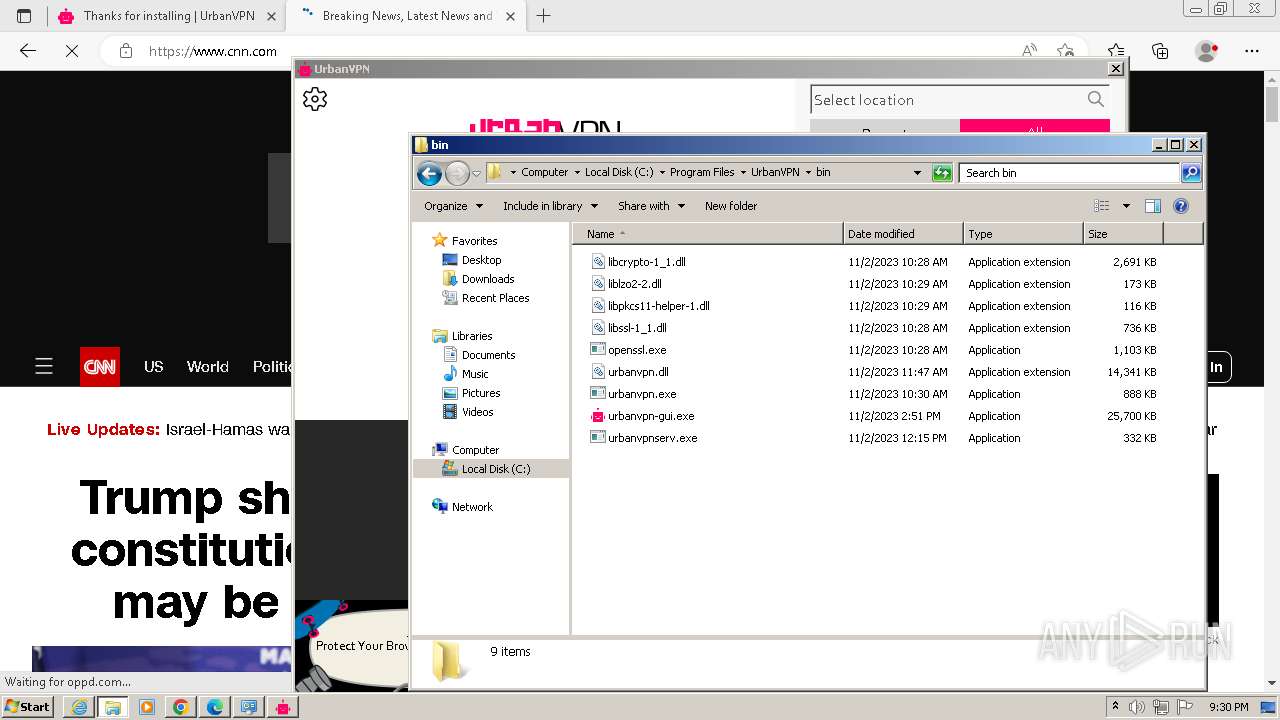
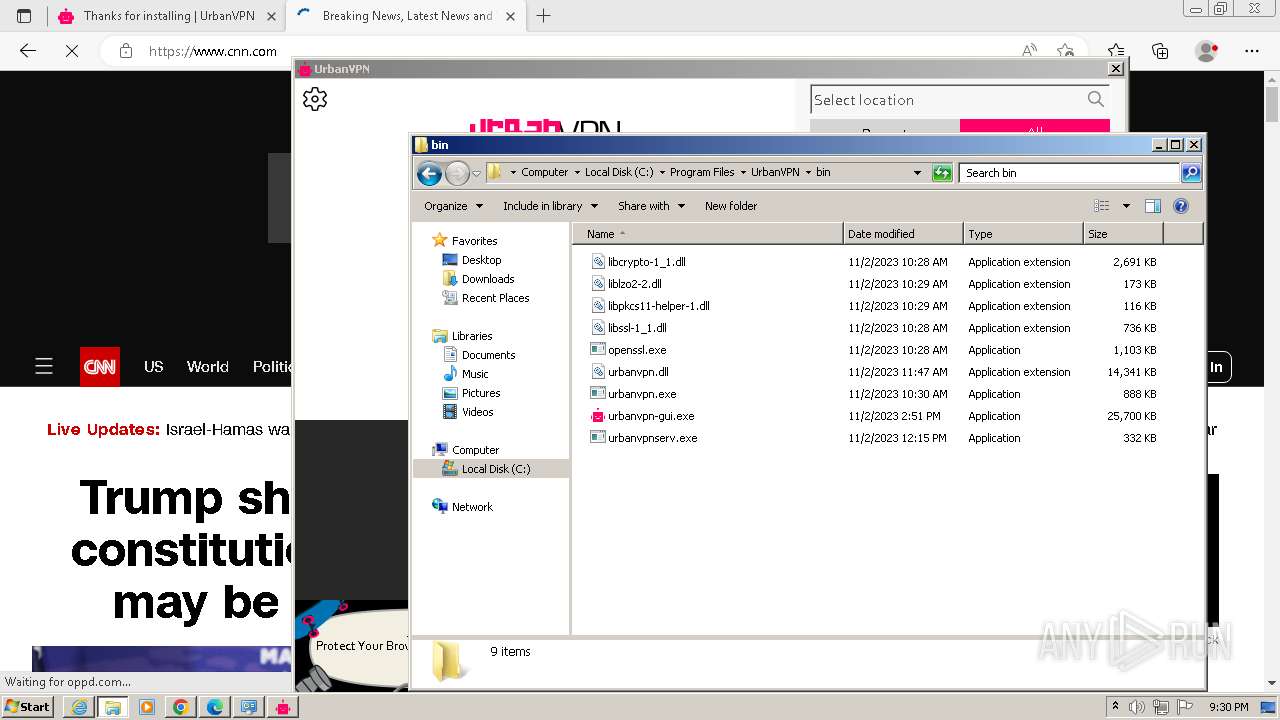
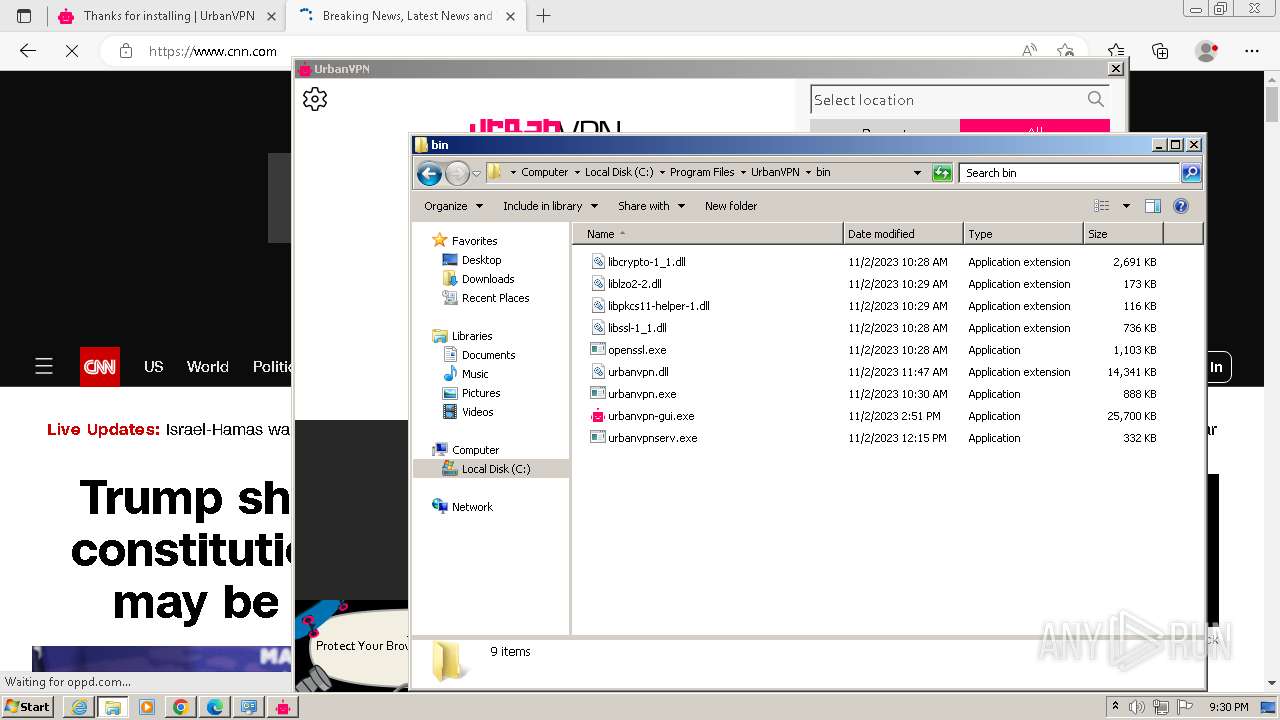
Creates files in the program directory
- MSIF149.tmp (PID: 1948)
- UrbanVPNUpdater.exe (PID: 2888)
- urbanvpn-gui.exe (PID: 3128)
Reads security settings of Internet Explorer
- rundll32.exe (PID: 1448)
Checks transactions between databases Windows and Oracle
- msiexec.exe (PID: 2992)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
140
Monitored processes
88
Malicious processes
13
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 304 | "C:\Windows\Installer\MSI3328.tmp" https://www.urban-vpn.com/install-desk/ | C:\Windows\Installer\MSI3328.tmp | — | msiexec.exe | |||||||||||
User: admin Company: Caphyon LTD Integrity Level: HIGH Description: File that launches another file Exit code: 0 Version: 19.3.0.0 Modules
| |||||||||||||||
| 544 | "C:\Users\admin\Downloads\UrbanVPN.exe" | C:\Users\admin\Downloads\UrbanVPN.exe | — | chrome.exe | |||||||||||
User: admin Company: Urban Security Integrity Level: MEDIUM Description: UrbanVPN Installer Exit code: 3221226540 Version: 2.2.15 Modules
| |||||||||||||||
| 644 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=1608 --field-trial-handle=1152,i,14935333470582423287,18215980254398581010,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1008 | DrvInst.exe "4" "0" "C:\Users\admin\AppData\Local\Temp\{3e5c48d7-edb2-3ce5-b332-8f60e03fdc7c}\oemvista.inf" "0" "6d14a44ff" "00000064" "WinSta0\Default" "000004E0" "208" "c:\program files\tap-windows\driver" | C:\Windows\System32\drvinst.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1028 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=4020 --field-trial-handle=1336,i,13242005862582440561,15575868762960670932,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 1228 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1236 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1236 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://urban-vpn.com/" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1276 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgAAAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --mojo-platform-channel-handle=1084 --field-trial-handle=1152,i,14935333470582423287,18215980254398581010,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1348 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=1820 --field-trial-handle=1152,i,14935333470582423287,18215980254398581010,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1416 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=asset_store.mojom.AssetStoreService --lang=en-US --service-sandbox-type=asset_store_service --mojo-platform-channel-handle=3776 --field-trial-handle=1336,i,13242005862582440561,15575868762960670932,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
Total events
75 412
Read events
74 792
Write events
552
Delete events
68
Modification events
| (PID) Process: | (1236) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 0 | |||
| (PID) Process: | (1236) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30847387 | |||
| (PID) Process: | (1236) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30847437 | |||
| (PID) Process: | (1236) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1236) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1236) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (1236) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1236) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (1236) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (1236) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
130
Suspicious files
497
Text files
153
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2332 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF2084a5.TMP | — | |
MD5:— | SHA256:— | |||
| 2332 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2332 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Variations | binary | |
MD5:961E3604F228B0D10541EBF921500C86 | SHA256:F7B24F2EB3D5EB0550527490395D2F61C3D2FE74BB9CB345197DAD81B58B5FED | |||
| 2332 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF208699.TMP | — | |
MD5:— | SHA256:— | |||
| 2332 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2332 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF2084a5.TMP | text | |
MD5:E91E138A25FD7E5BCA5E60111F39C91A | SHA256:B1F7E3537A31A4B847F862858E5D2581993CC9372F19ABF19EA2A9185FE42A4F | |||
| 2332 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:8175FB7046E977DAAD01289080C116EF | SHA256:19E403B4BEF7D83DD425AB6A54DE943D244A16E5EA121DEC91C417608AEAACB7 | |||
| 2332 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old | text | |
MD5:23C08E7178FEB5BA68E821CD2D35736E | SHA256:5471CBD1BD61B917801D71D41A45B2CEEE3FE6837782DDD47D84424BFD938BFD | |||
| 2332 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 2332 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF208495.TMP | text | |
MD5:513218482935B0D388C0A990D868387A | SHA256:8E39CBAAF4AACC3A01AFA74EA8C30FB24FE69A22B8B30728AFB1614FD68809D9 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
59
TCP/UDP connections
230
DNS requests
196
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1236 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?3121f6cf0a82b697 | unknown | compressed | 4.66 Kb | unknown |
1236 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAzlnDD9eoNTLi0BRrMy%2BWU%3D | unknown | binary | 313 b | unknown |
1236 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?9c39c51ec95c49f5 | unknown | compressed | 4.66 Kb | unknown |
1236 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | binary | 471 b | unknown |
1080 | svchost.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?d3beddd762d67162 | unknown | compressed | 65.2 Kb | unknown |
1236 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA177el9ggmWelJjG4vdGL0%3D | unknown | binary | 471 b | unknown |
1236 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAqvpsXKY8RRQeo74ffHUxc%3D | unknown | binary | 471 b | unknown |
868 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | — | — | unknown |
1236 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | binary | 471 b | unknown |
2116 | msiexec.exe | POST | 200 | 148.72.152.126:40000 | http://analytics.urban-vpn.com:40000/tickets | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1228 | iexplore.exe | 18.239.69.123:443 | urban-vpn.com | — | US | unknown |
2588 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
1236 | iexplore.exe | 92.123.104.19:443 | www.bing.com | Akamai International B.V. | DE | unknown |
2332 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
1696 | chrome.exe | 142.250.181.227:443 | clientservices.googleapis.com | GOOGLE | US | whitelisted |
1696 | chrome.exe | 108.177.15.84:443 | accounts.google.com | GOOGLE | US | unknown |
1696 | chrome.exe | 172.217.18.100:443 | www.google.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
urban-vpn.com |
| unknown |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
www.urban-vpn.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3384 | urbanvpnserv.exe | Misc activity | ET USER_AGENTS Go HTTP Client User-Agent |
3384 | urbanvpnserv.exe | Misc activity | ET INFO SSH-2.0-Go version string Observed in Network Traffic - Outbound |
3384 | urbanvpnserv.exe | Misc activity | ET USER_AGENTS Go HTTP Client User-Agent |
3384 | urbanvpnserv.exe | Misc activity | ET USER_AGENTS Go HTTP Client User-Agent |
Process | Message |
|---|---|
msiexec.exe | Logger::SetLogFile( C:\Users\admin\AppData\Roaming\Caphyon\Advanced Installer\AI_ResourceCleaner.log ) while OLD path is: |
UrbanVPNUpdater.exe | Logger::SetLogFile( C:\ProgramData\UrbanVPN\updates\updater.log ) while OLD path is: |
msiexec.exe | Logger::SetLogFile( C:\Users\admin\AppData\Roaming\Caphyon\Advanced Installer\AI_ResourceCleaner.log ) while OLD path is: |
msiexec.exe | Logger::SetLogFile( C:\Users\admin\AppData\Roaming\Caphyon\Advanced Installer\AI_ResourceCleaner.log ) while OLD path is: |
UrbanVPNUpdater.exe | Logger::SetLogFile( C:\ProgramData\UrbanVPN\updates\updater.log ) while OLD path is: |
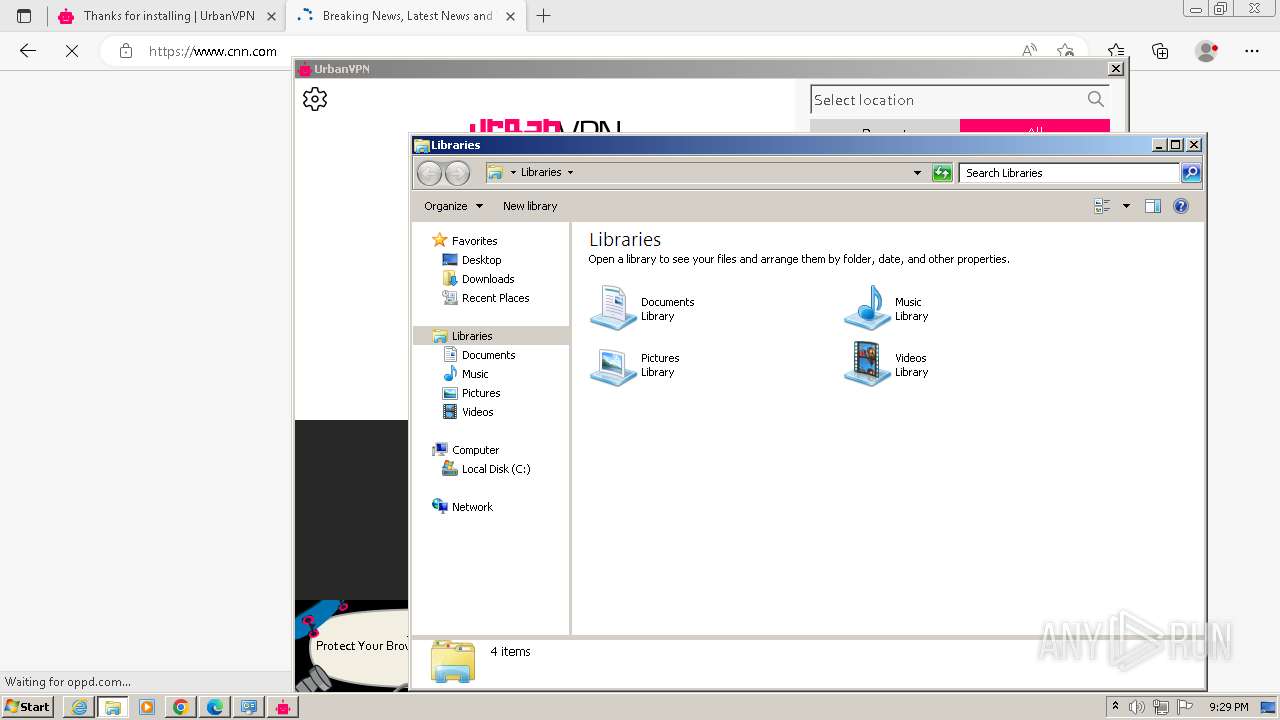
urbanvpn-gui.exe | First instance of UrbanVPN was started.
|