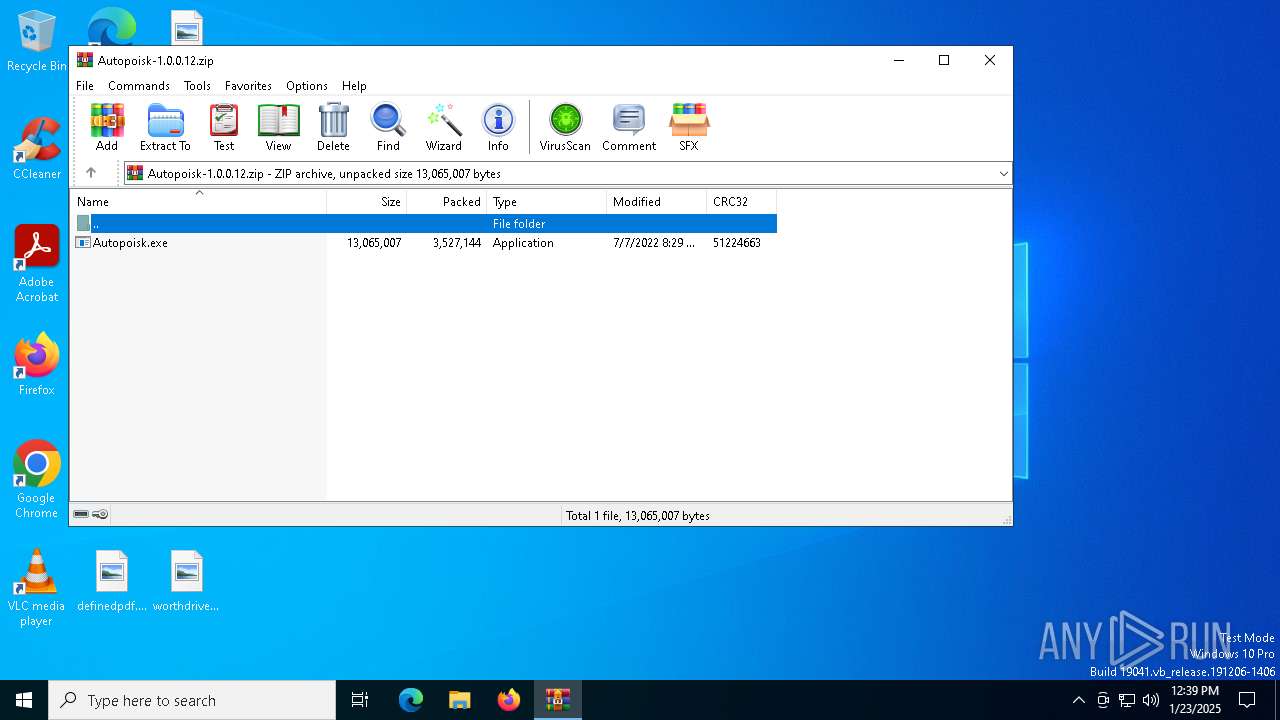
| File name: | Autopoisk-1.0.0.12.zip |
| Full analysis: | https://app.any.run/tasks/00e3d9ff-bf59-4ca1-90b9-962f20c9453b |
| Verdict: | Malicious activity |
| Analysis date: | January 23, 2025, 12:39:33 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | F3043E5083C37651E743F4C533BA6201 |
| SHA1: | 1C4CAEF3DCE550C05684BFEA893912F0C475651E |
| SHA256: | AA74F38FC6C18E67FA83E6FBAC025F76B13D8FA174BC8F87F042FE462F4FFA13 |
| SSDEEP: | 98304:Zc80ookIZUZ0gBGcFg4XgQbrjy4ujLUGnk1WNG6eh05YYXYmgMvdLXkXfnm0c+wi:GLkj995 |
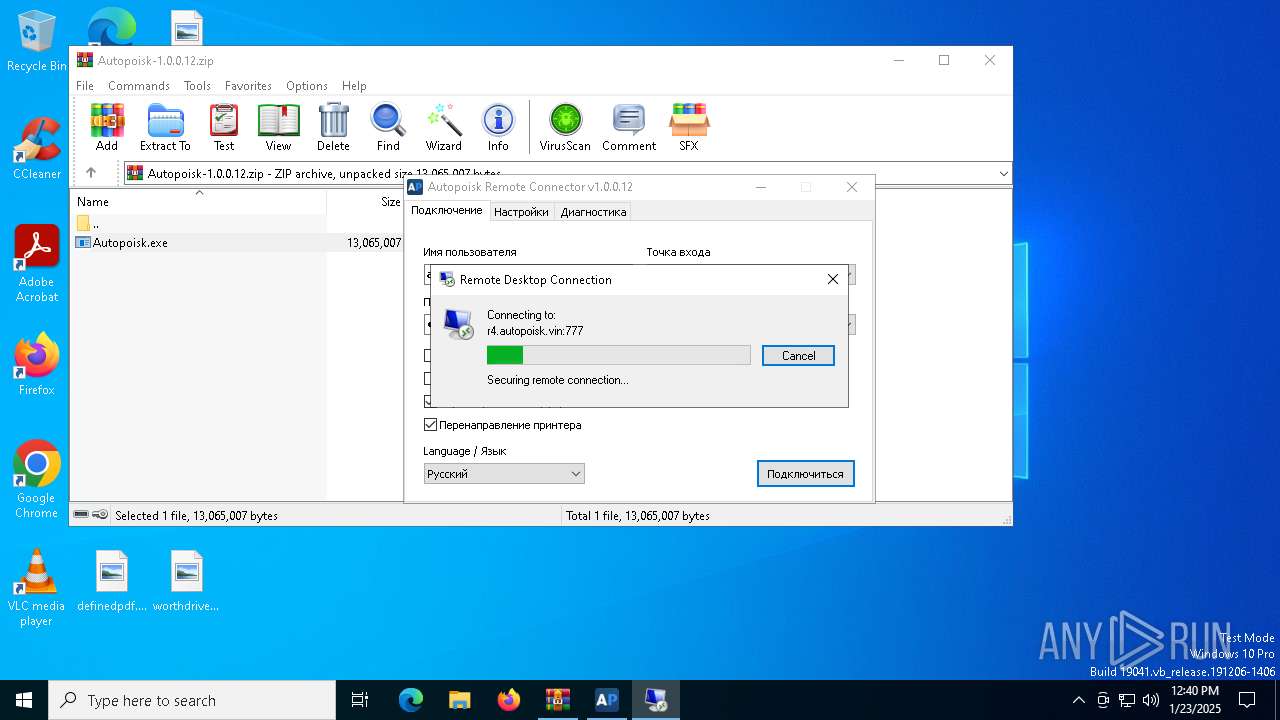
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 6516)
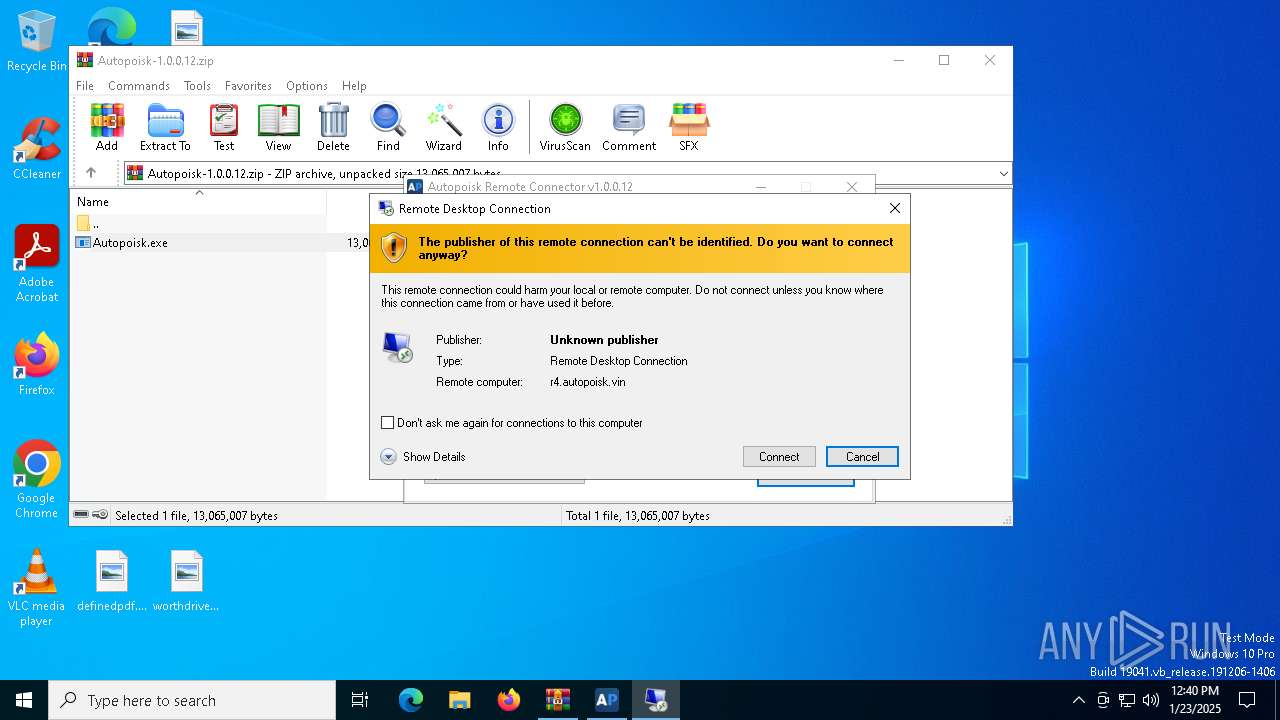
Reads the history of recent RDP connections
- mstsc.exe (PID: 4052)
- mstsc.exe (PID: 1064)
Connects to unusual port
- mstsc.exe (PID: 1064)
INFO
The sample compiled with english language support
- WinRAR.exe (PID: 6516)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 6516)
Checks supported languages
- Autopoisk.exe (PID: 4512)
Reads the computer name
- Autopoisk.exe (PID: 4512)
Checks proxy server information
- mstsc.exe (PID: 1064)
Creates files or folders in the user directory
- Autopoisk.exe (PID: 4512)
- mstsc.exe (PID: 1064)
Reads the software policy settings
- mstsc.exe (PID: 1064)
The process uses the downloaded file
- WinRAR.exe (PID: 6516)
Reads security settings of Internet Explorer
- mstsc.exe (PID: 1064)
- mstsc.exe (PID: 4052)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2022:07:07 11:29:44 |
| ZipCRC: | 0x51224663 |
| ZipCompressedSize: | 3527144 |
| ZipUncompressedSize: | 13065007 |
| ZipFileName: | Autopoisk.exe |
Total processes
132
Monitored processes
4
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
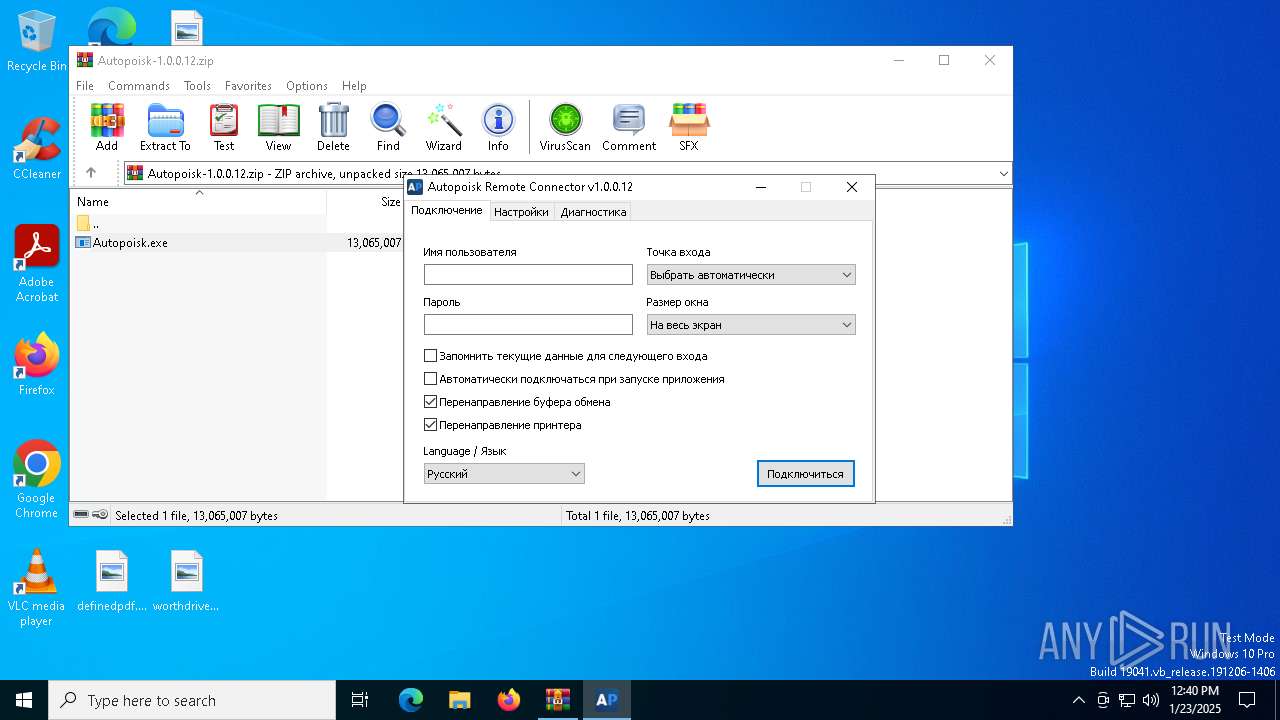
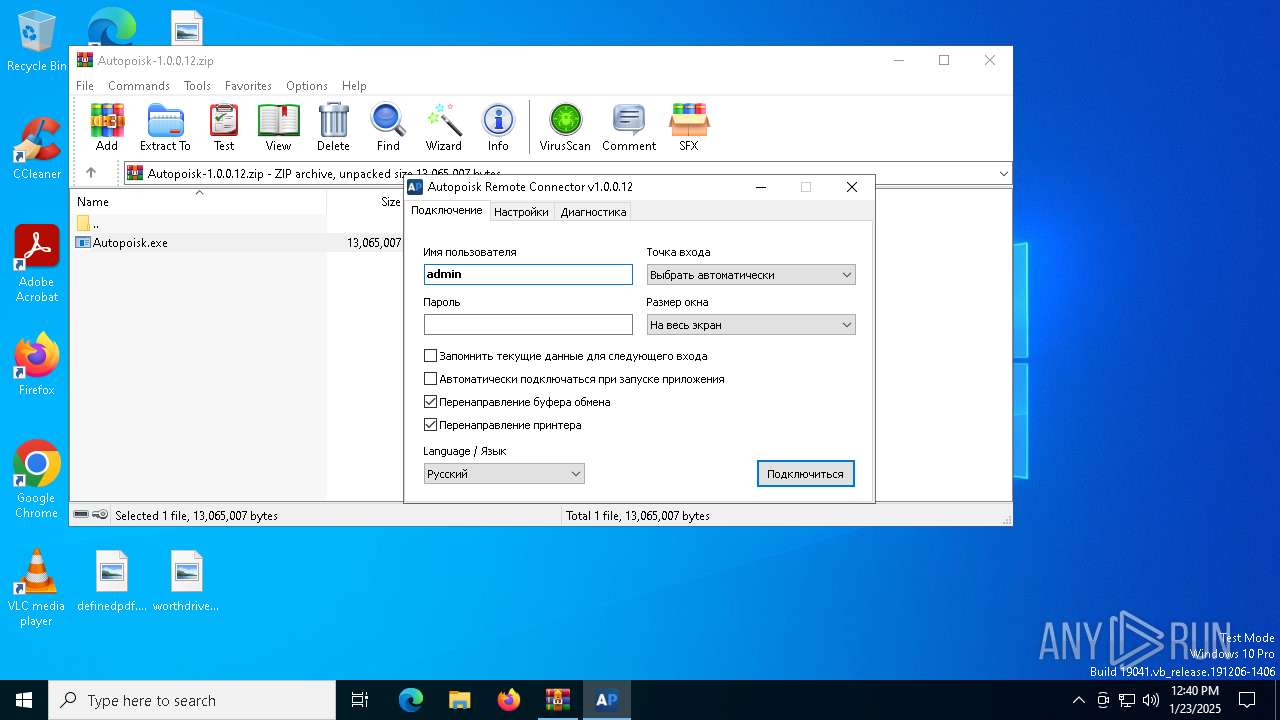
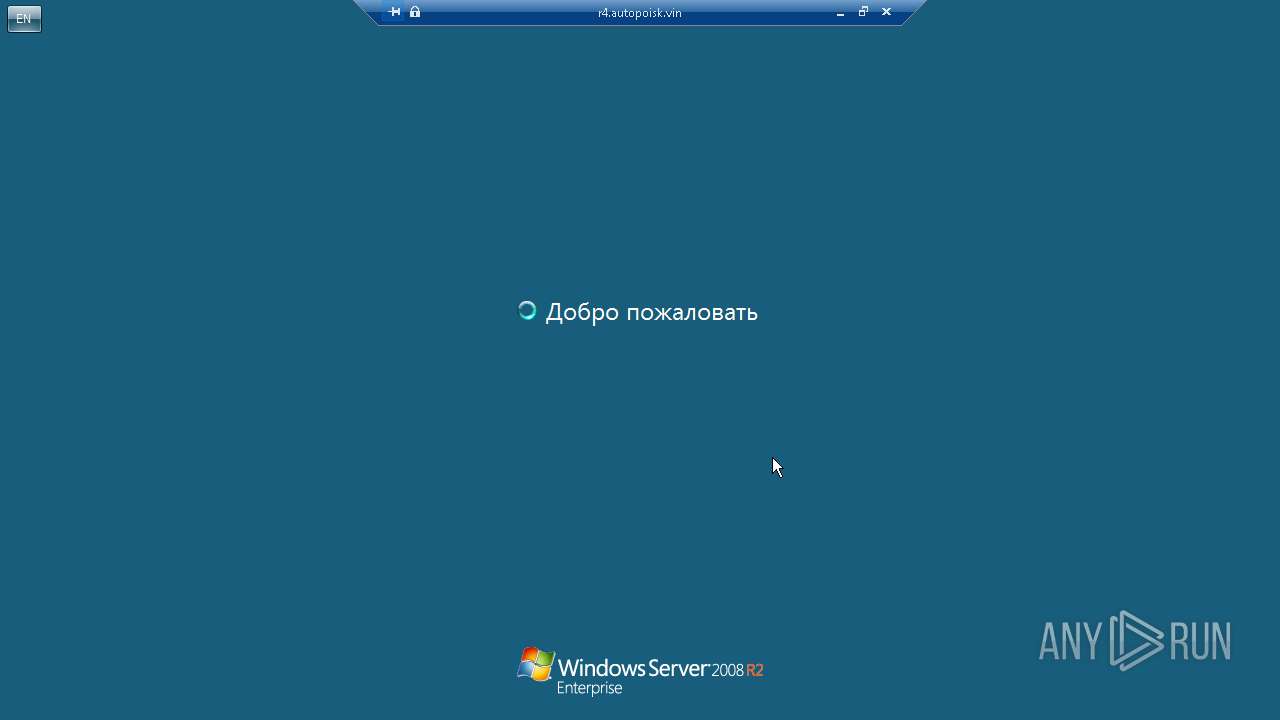
| 1064 | mstsc.exe "C:\Users\admin\AppData\Local\ARC\Autopoisk.rdp" /v:r4.autopoisk.vin:777 | C:\Windows\System32\mstsc.exe | mstsc.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Remote Desktop Connection Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4052 | mstsc.exe "C:\Users\admin\AppData\Local\ARC\Autopoisk.rdp" /v:r4.autopoisk.vin:777 | C:\Windows\SysWOW64\mstsc.exe | — | Autopoisk.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Remote Desktop Connection Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4512 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa6516.32654\Autopoisk.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa6516.32654\Autopoisk.exe | WinRAR.exe | ||||||||||||
User: admin Company: Autopoisk Integrity Level: MEDIUM Description: Autopoisk Remote Connector Version: 1.0.0.12 Modules
| |||||||||||||||
| 6516 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\Autopoisk-1.0.0.12.zip | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
Total events
4 376
Read events
4 368
Write events
8
Delete events
0
Modification events
| (PID) Process: | (6516) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (6516) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (6516) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (6516) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Autopoisk-1.0.0.12.zip | |||
| (PID) Process: | (6516) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6516) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6516) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6516) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
1
Suspicious files
5
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1064 | mstsc.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\439F613B3D55693954E1B080DE3085B4_13A9E648A032C61467BDA0380F67EA43 | binary | |
MD5:4D3E5399AB8E1824E9082F2FC554FDBC | SHA256:5BF2BFC313EB97F7A3A9EF0C37726267E26FB90B89642BD025B3A1F6AFEFCCD0 | |||
| 4512 | Autopoisk.exe | C:\Users\admin\AppData\Local\ARC\Autopoisk.rdp | binary | |
MD5:5403577E2D870B01840453CBF26C1618 | SHA256:21AAC147F9F2CAEB3E7B6C8496B6576A8959C406D305CB159FB8FB5F24ED73D7 | |||
| 6516 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa6516.32654\Autopoisk.exe | executable | |
MD5:E66D46D21CFD0EEBFBFD8A1D5C5B66A7 | SHA256:A9BDA3E785367821BE8AEA456B52A3A722486DDE3F5AB106E8B982A500850447 | |||
| 1064 | mstsc.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\94929790B3119AF4B3F5D66C747B122B_22A8AFCA6D1D25543ACF1AAD994E51F3 | binary | |
MD5:EDE342B6901FD2B379B7129F80390786 | SHA256:48863B94BA6EF6C975CAF0E4FDFFB4ACEF921C276A0630B7AD8D40AD6635E056 | |||
| 1064 | mstsc.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\94929790B3119AF4B3F5D66C747B122B_22A8AFCA6D1D25543ACF1AAD994E51F3 | binary | |
MD5:354B3DD3F8AD0A37D58EA8657FA5F1AC | SHA256:226845E6B2085E3A04A1AD5B49444F9970D86530E436970DEF7BB05ADEBA1F0E | |||
| 1064 | mstsc.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\439F613B3D55693954E1B080DE3085B4_13A9E648A032C61467BDA0380F67EA43 | binary | |
MD5:F6156E715A85646637BDC9AEA1209D1C | SHA256:4AEB4889EC495AB13CCD108A34BC0CC5C73DDEF325AC2AA1D03AA5CFED170E85 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
31
DNS requests
21
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
4536 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
4536 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
760 | lsass.exe | GET | 200 | 104.18.20.226:80 | http://ocsp.globalsign.com/gsgccr6alphasslca2023/ME0wSzBJMEcwRTAJBgUrDgMCGgUABBTYuQbxgZqJCf3D06HBxH57o5XEXgQUvQW384qTPHPLefoPhRKhd5YYkXQCDAjiLNTtTYgsXQ%2B4CA%3D%3D | unknown | — | — | whitelisted |
4512 | Autopoisk.exe | GET | 301 | 82.97.242.231:80 | http://upd.autopoisk.su/files/version | unknown | — | — | unknown |
760 | lsass.exe | GET | 200 | 151.101.194.133:80 | http://ocsp2.globalsign.com/rootr6/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRi%2B7TJbHYn9EmJ9W03lecB7P%2BG7QQUrmwFo5MT4qLn4tcc1sfwf8hnU6ACEH8fLJAug9Djtvs77keLXoA%3D | unknown | — | — | whitelisted |
1064 | mstsc.exe | GET | 200 | 151.101.194.133:80 | http://ocsp2.globalsign.com/rootr6/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRi%2B7TJbHYn9EmJ9W03lecB7P%2BG7QQUrmwFo5MT4qLn4tcc1sfwf8hnU6ACEH8fLJAug9Djtvs77keLXoA%3D | unknown | — | — | whitelisted |
1064 | mstsc.exe | GET | 200 | 104.18.20.226:80 | http://ocsp.globalsign.com/gsgccr6alphasslca2023/ME0wSzBJMEcwRTAJBgUrDgMCGgUABBTYuQbxgZqJCf3D06HBxH57o5XEXgQUvQW384qTPHPLefoPhRKhd5YYkXQCDAjiLNTtTYgsXQ%2B4CA%3D%3D | unknown | — | — | whitelisted |
6296 | backgroundTaskHost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1176 | svchost.exe | 40.126.32.76:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1076 | svchost.exe | 184.28.89.167:443 | go.microsoft.com | AKAMAI-AS | US | whitelisted |
2736 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1684 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4536 | SIHClient.exe | 172.202.163.200:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | GB | whitelisted |
4536 | SIHClient.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
r3.autopoisk.vin |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
4512 | Autopoisk.exe | Potentially Bad Traffic | ET INFO HTTP Request to .su TLD (Soviet Union) Often Malware Related |