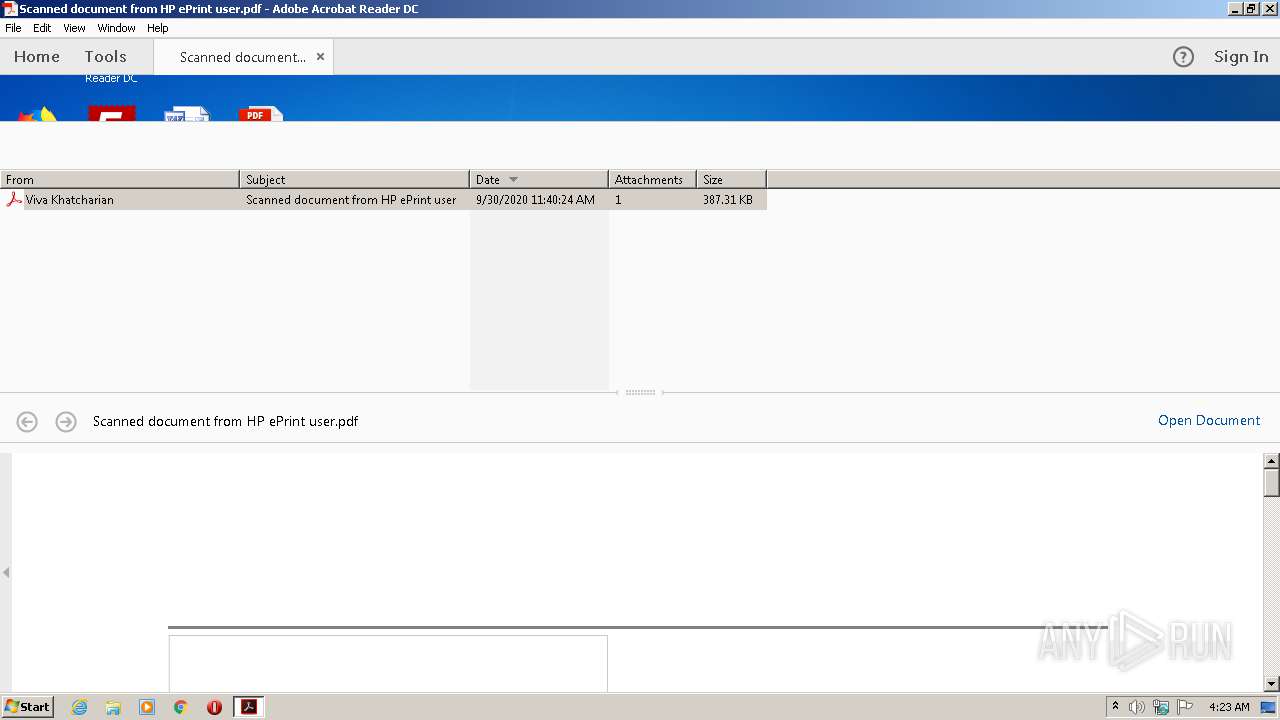
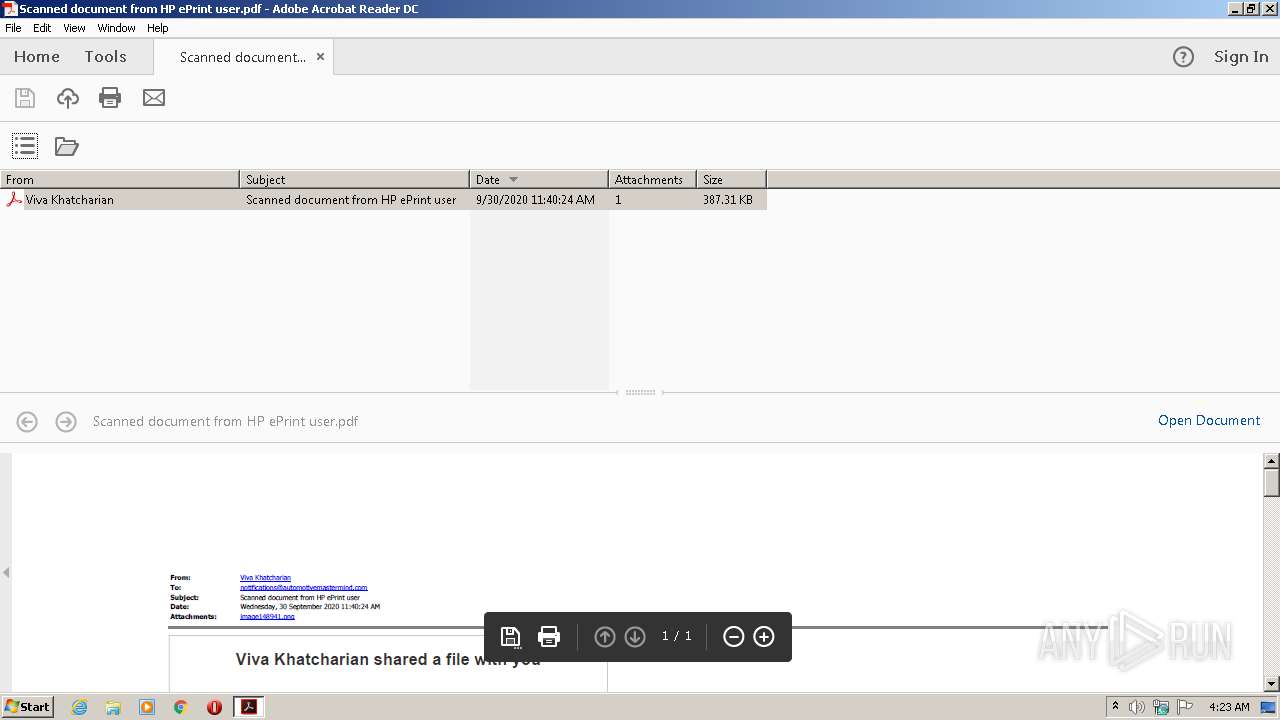
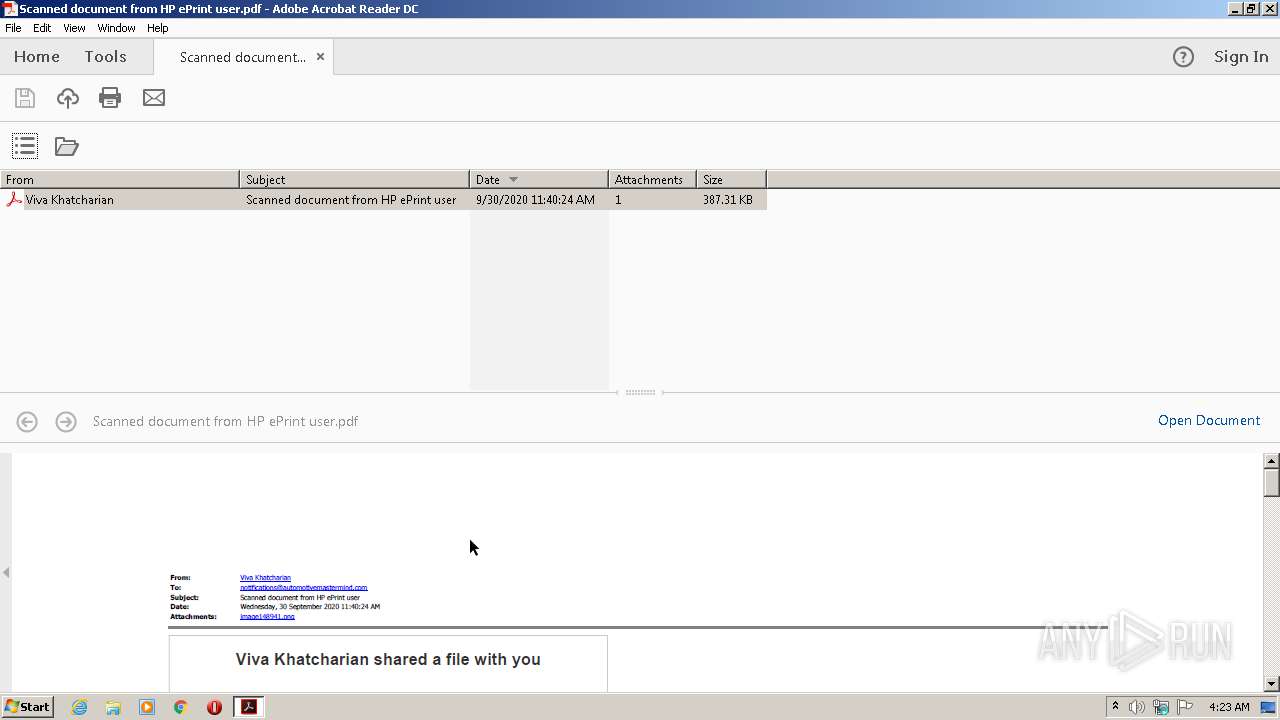
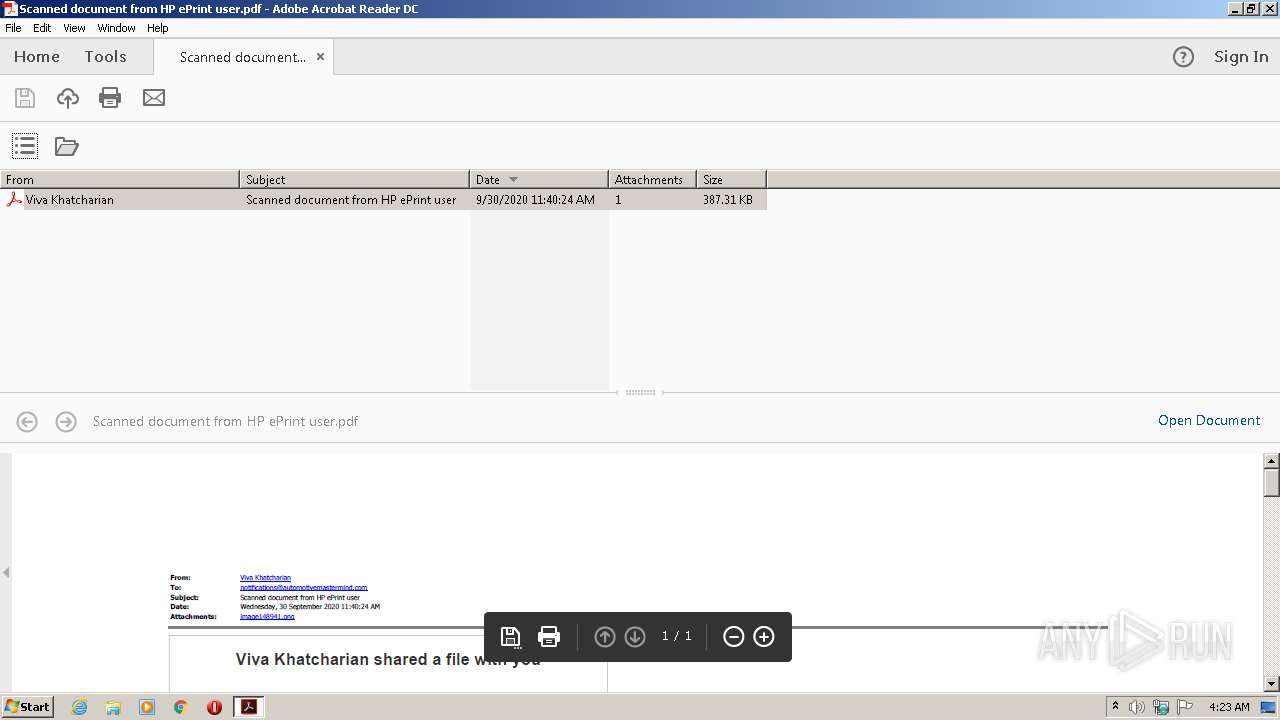
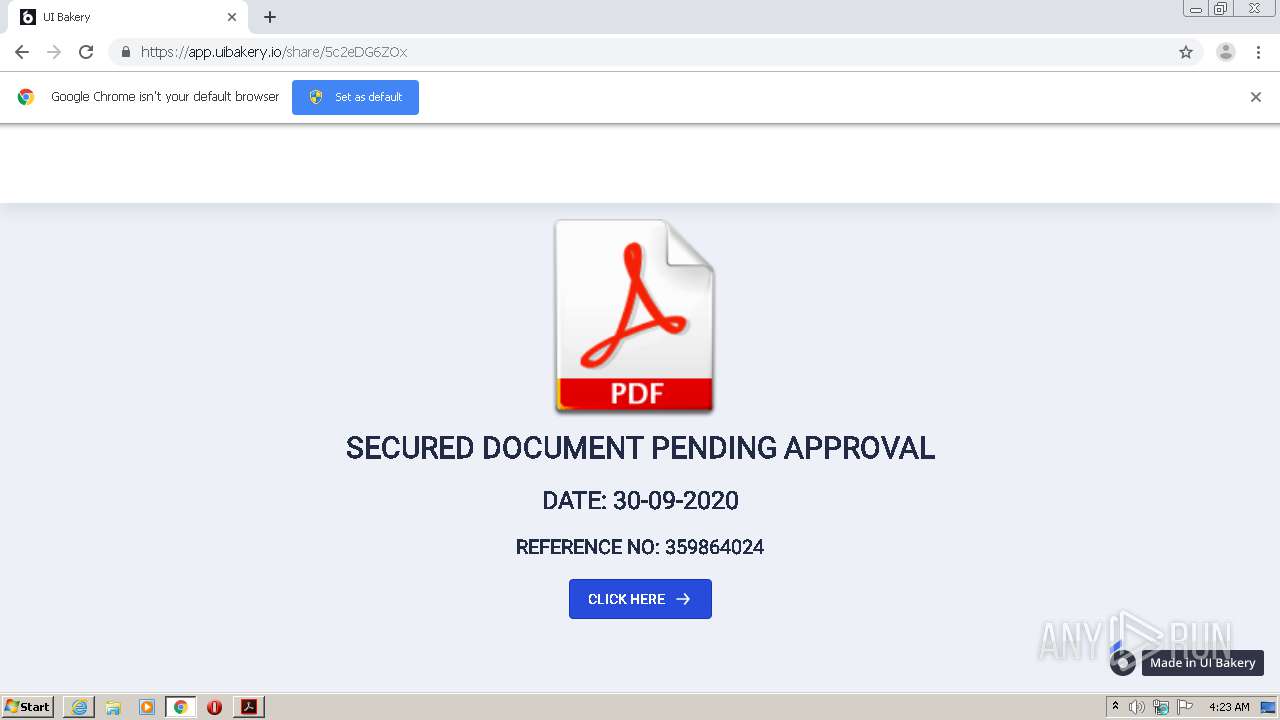
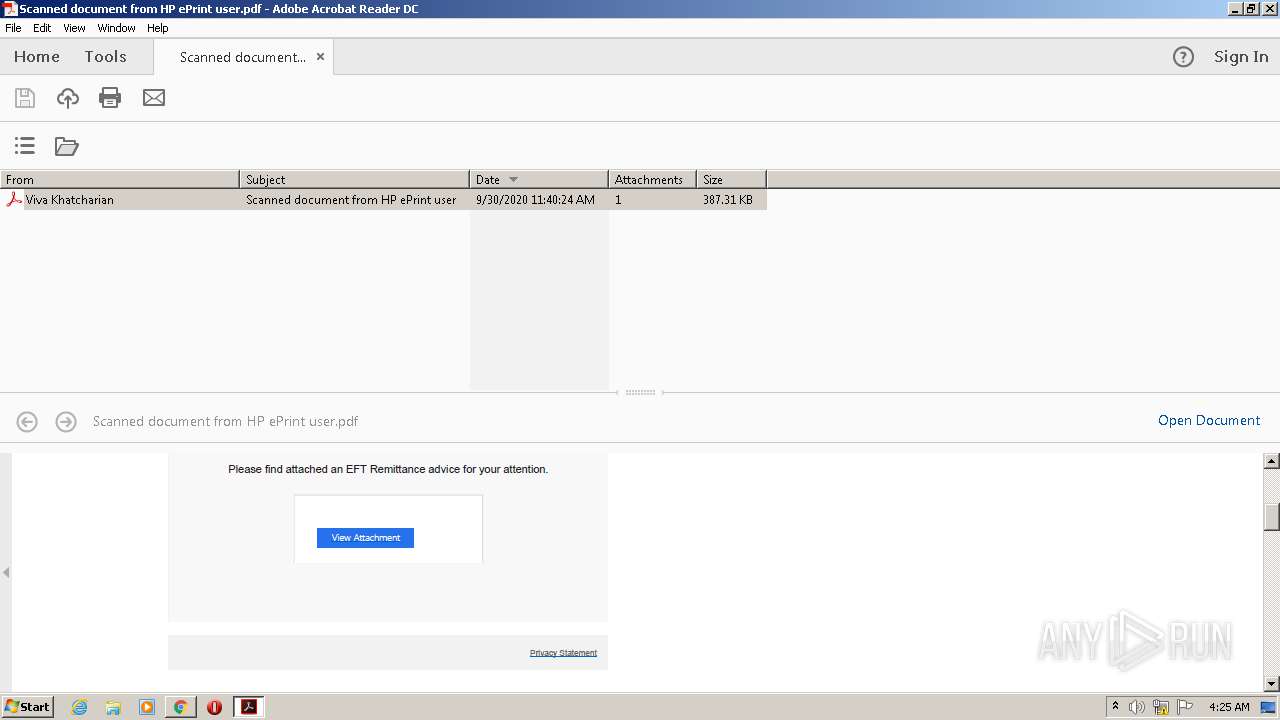
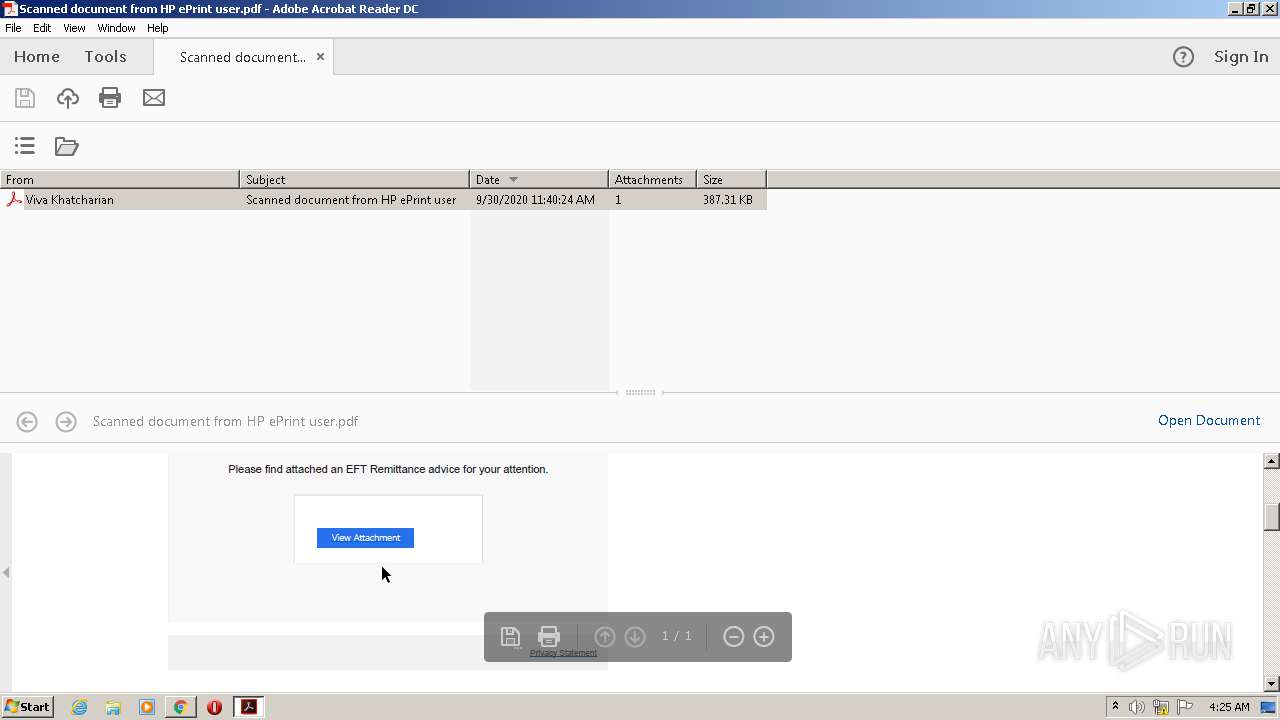
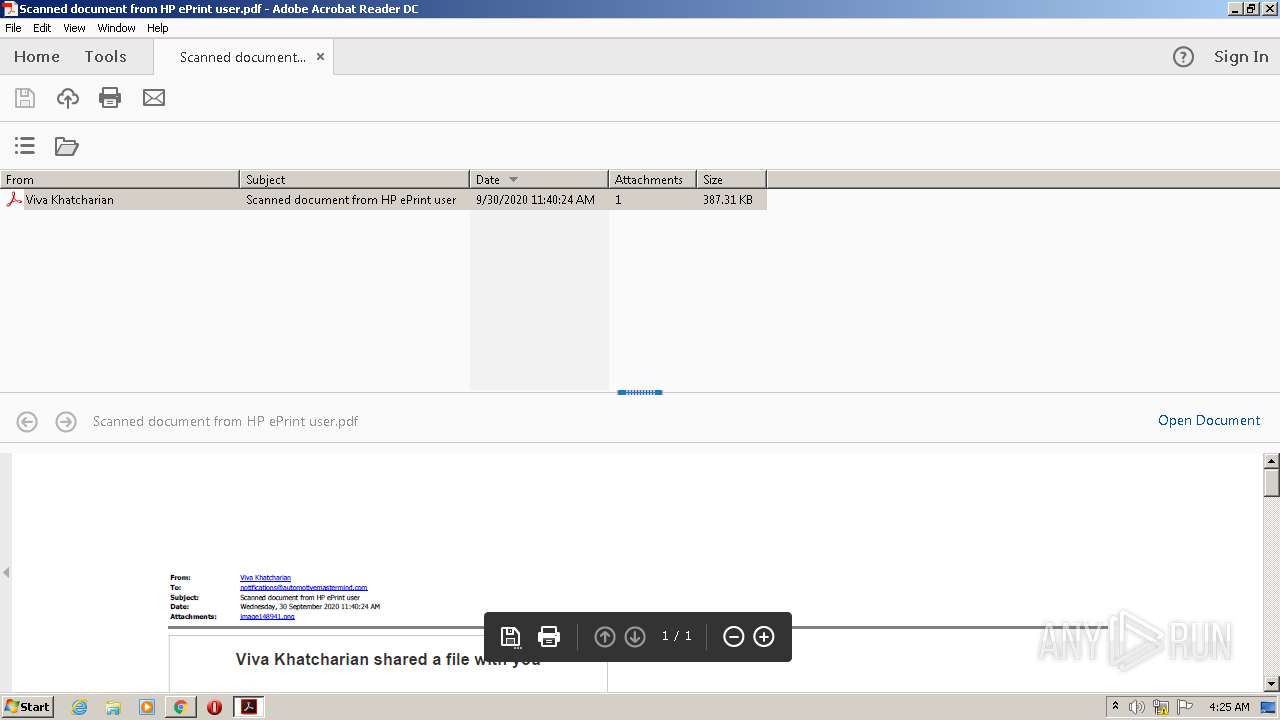
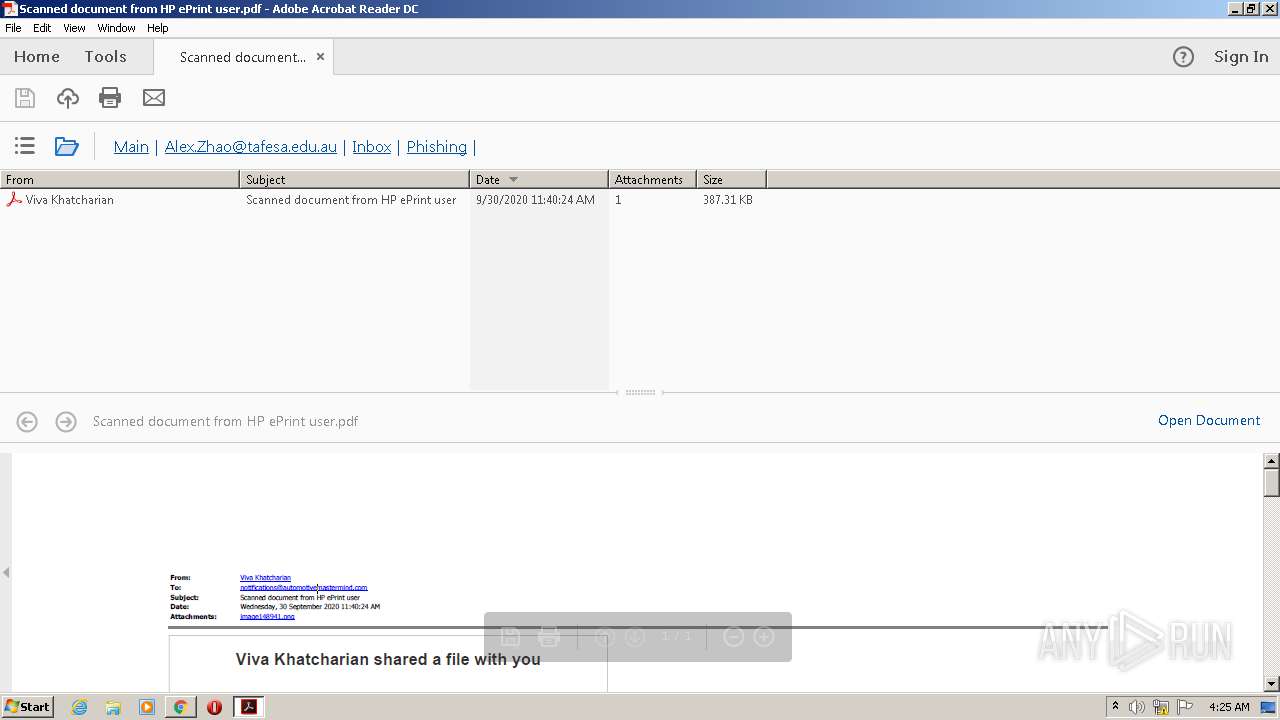
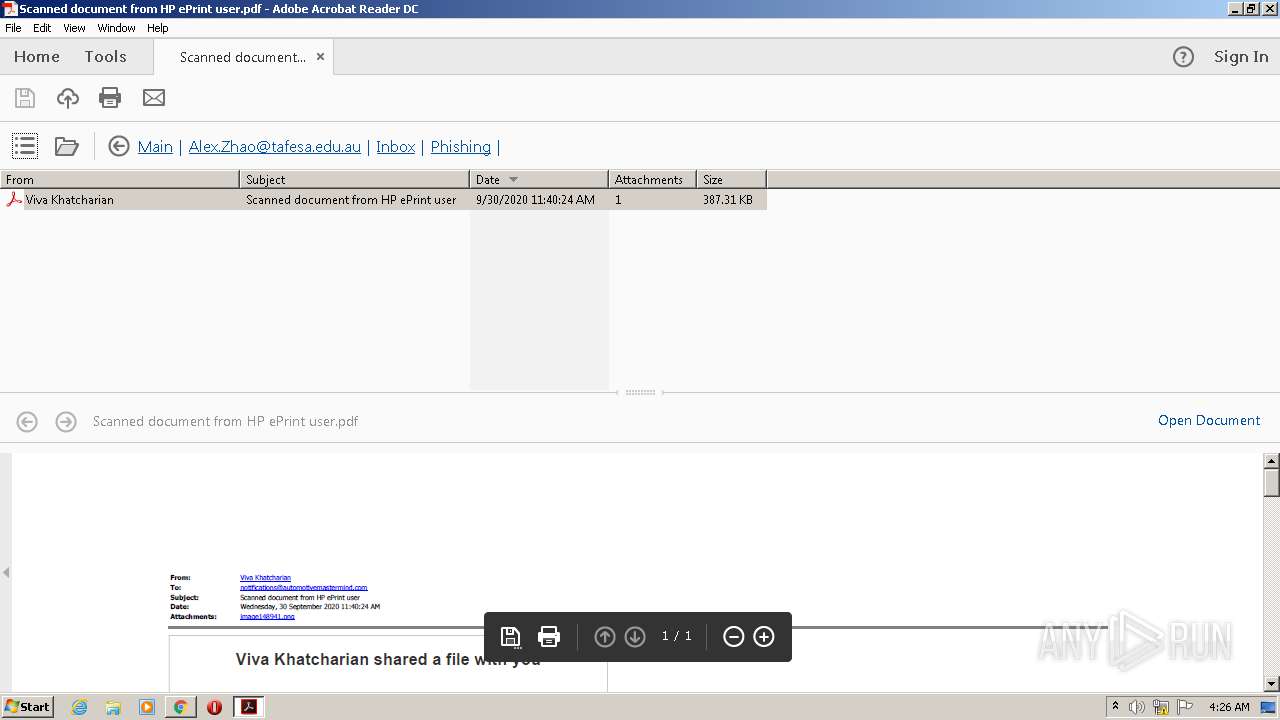
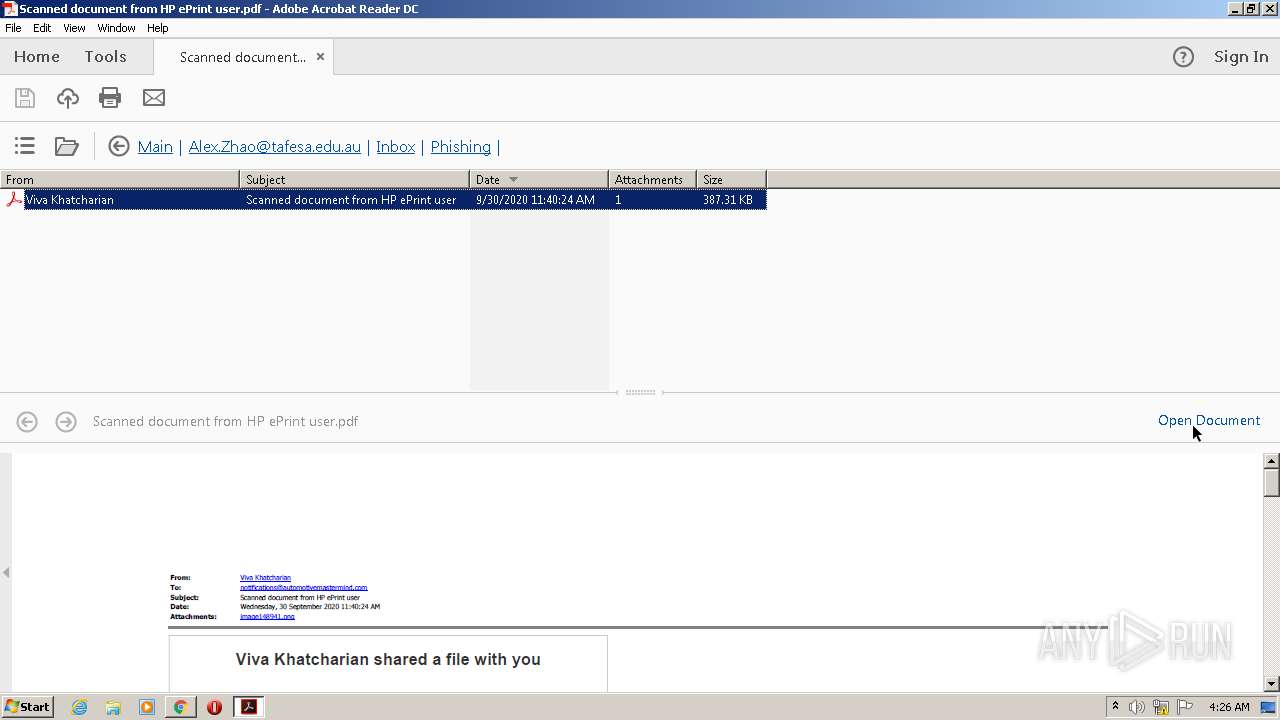
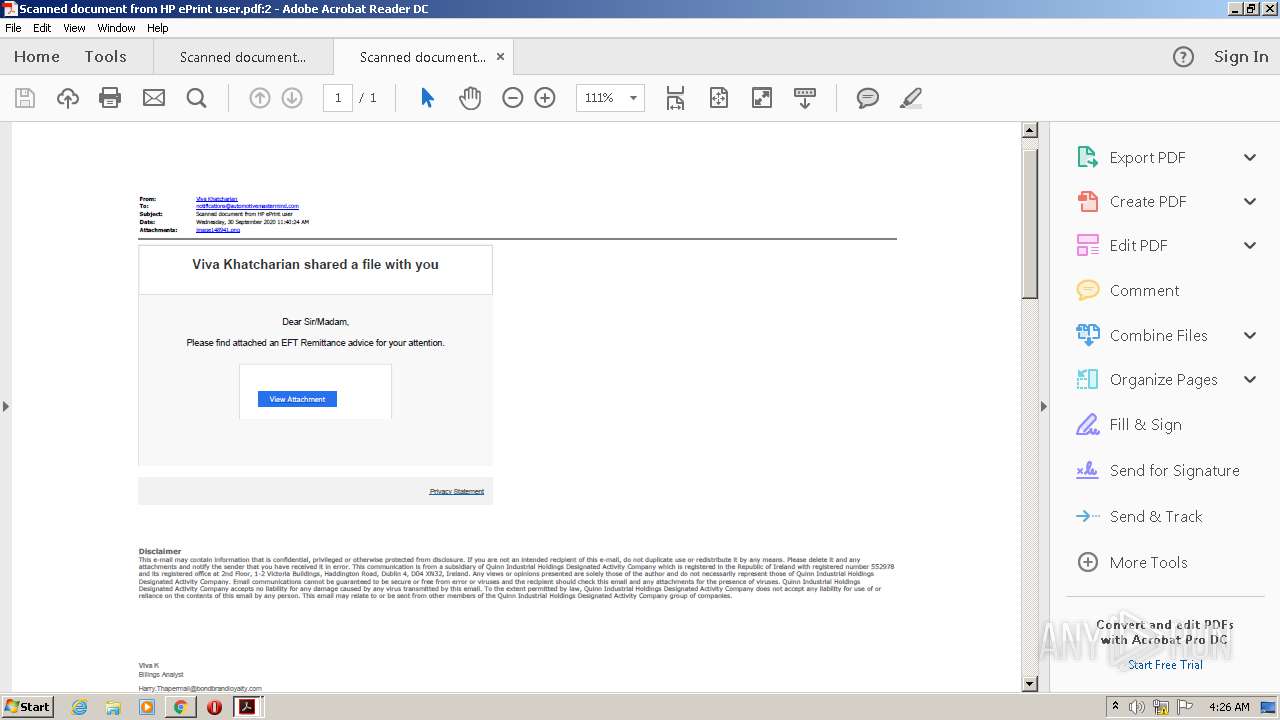
| File name: | Scanned document from HP ePrint user.pdf |
| Full analysis: | https://app.any.run/tasks/0d13f45c-b143-4072-a234-97750f3443f2 |
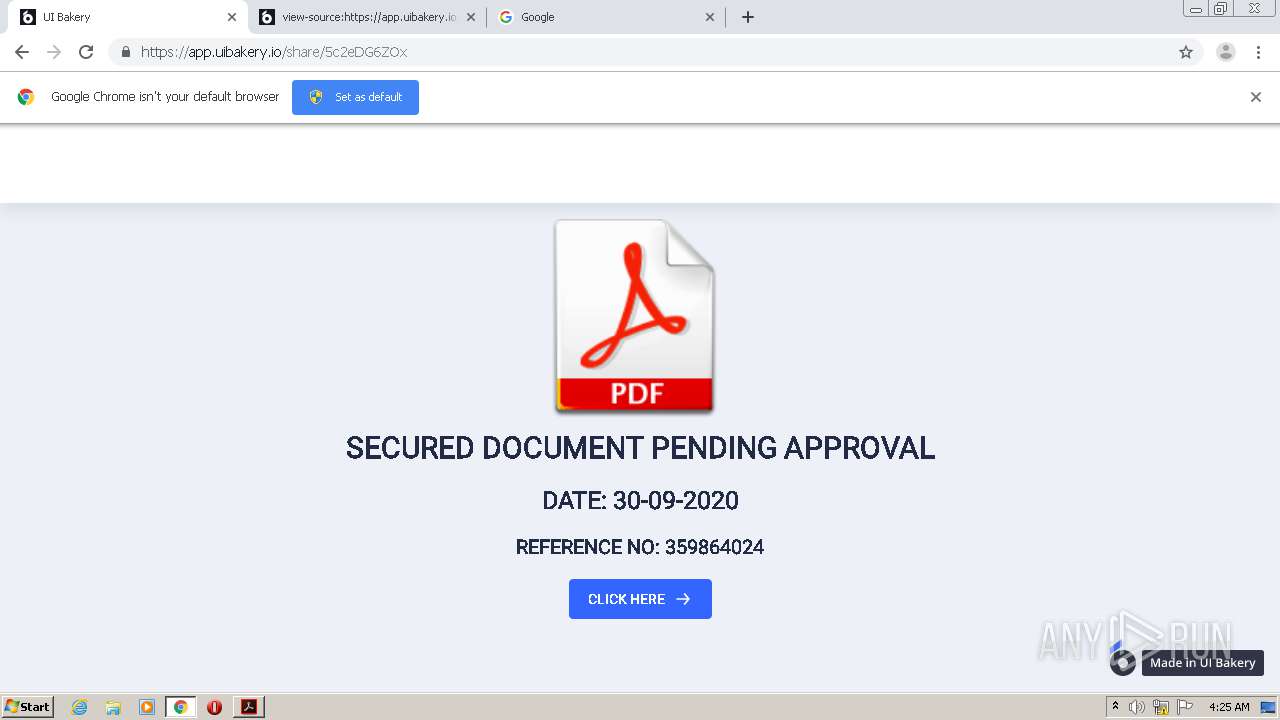
| Verdict: | Malicious activity |
| Analysis date: | September 30, 2020, 03:22:49 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/pdf |
| File info: | PDF document, version 1.7 |
| MD5: | E07855A3907F29FABF59C89050EA09B6 |
| SHA1: | 1F0728B19370484DDE759263DC609B3B3D7083FC |
| SHA256: | AA650E0C410767EA664D4A2EB02B33F0949879B9EBB50EE5A3C9D367A066756D |
| SSDEEP: | 12288:BCrFGKFkSTV8IPfniKNvSyExNWP2rRyTFeiK:ErFGKFkSTV8IPfnvvEjWPGcTwiK |
MALICIOUS
No malicious indicators.SUSPICIOUS
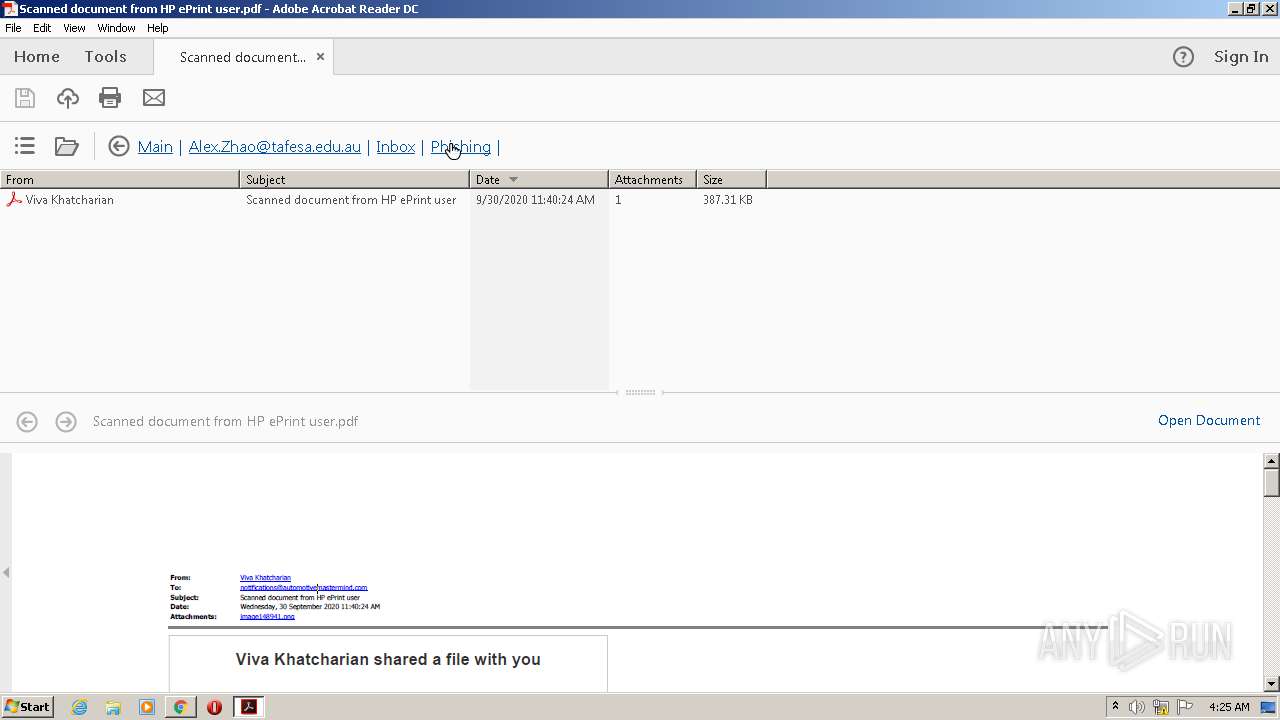
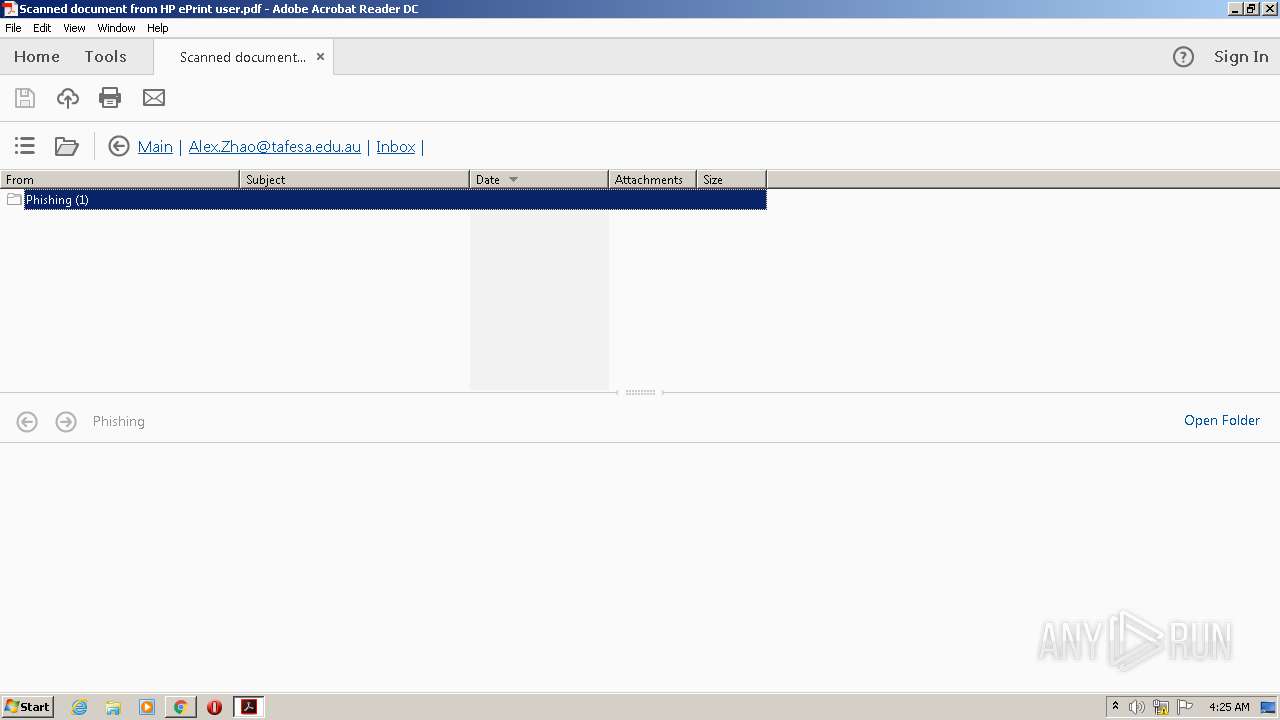
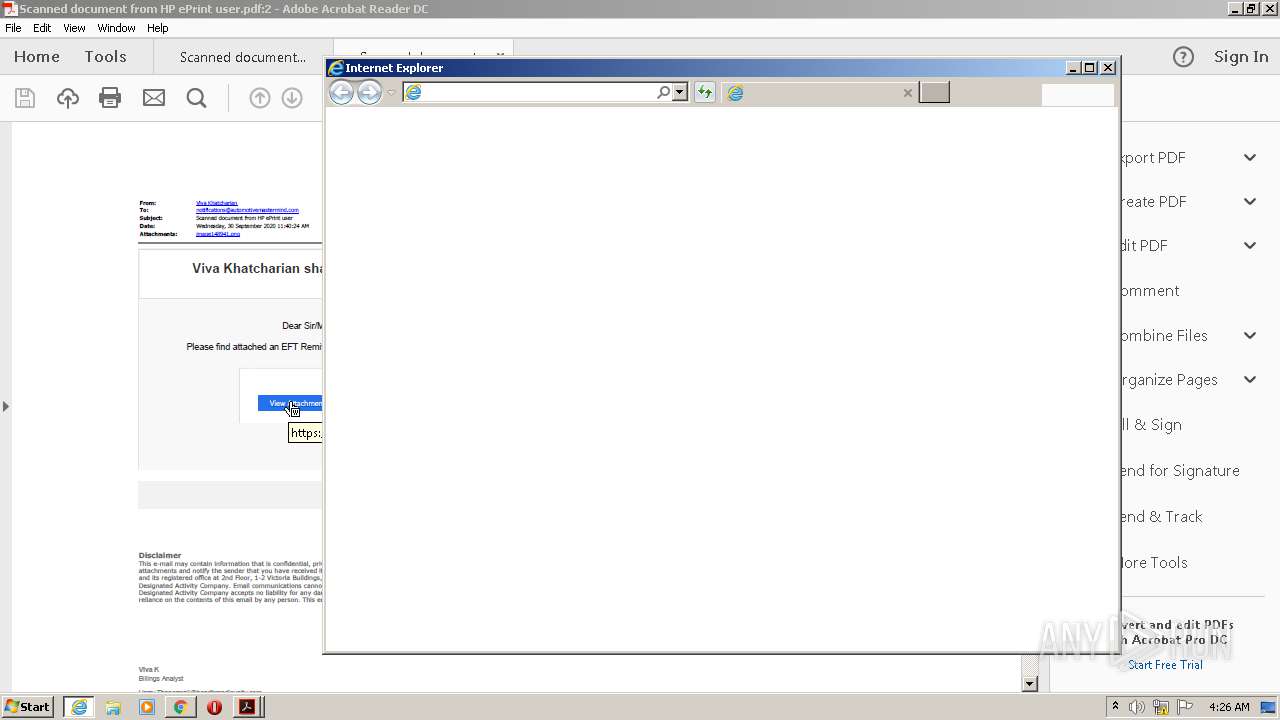
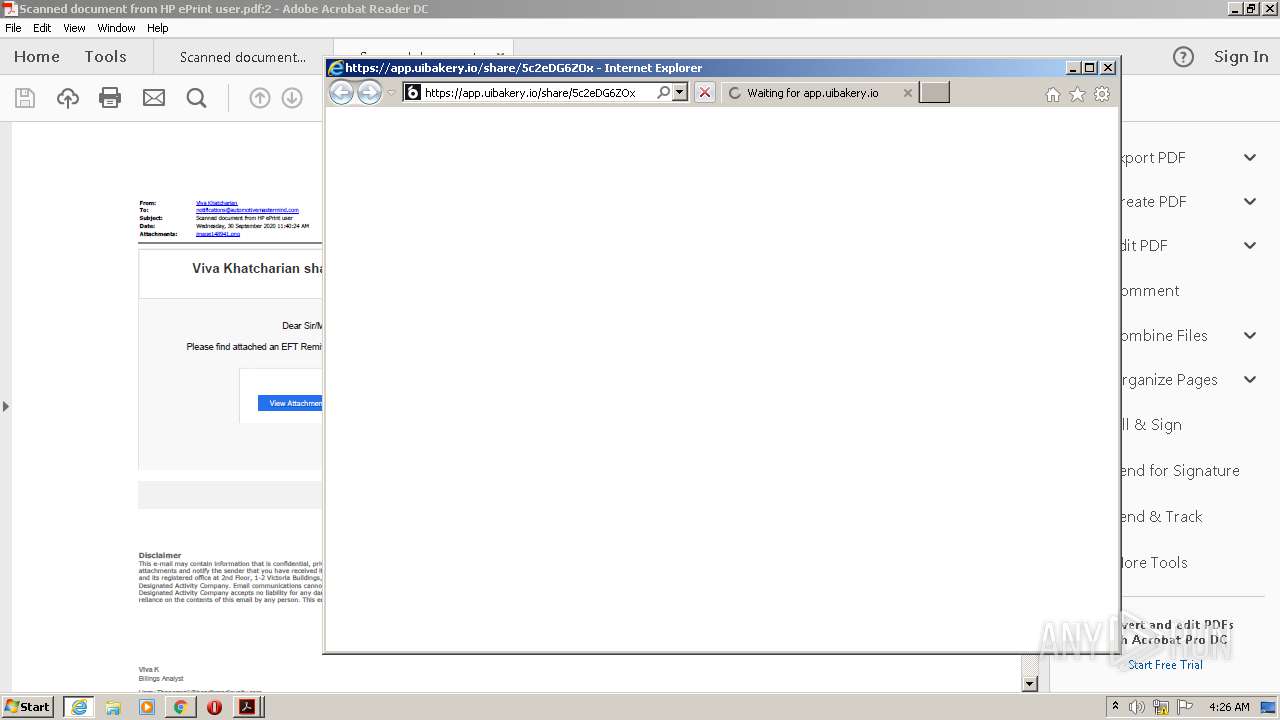
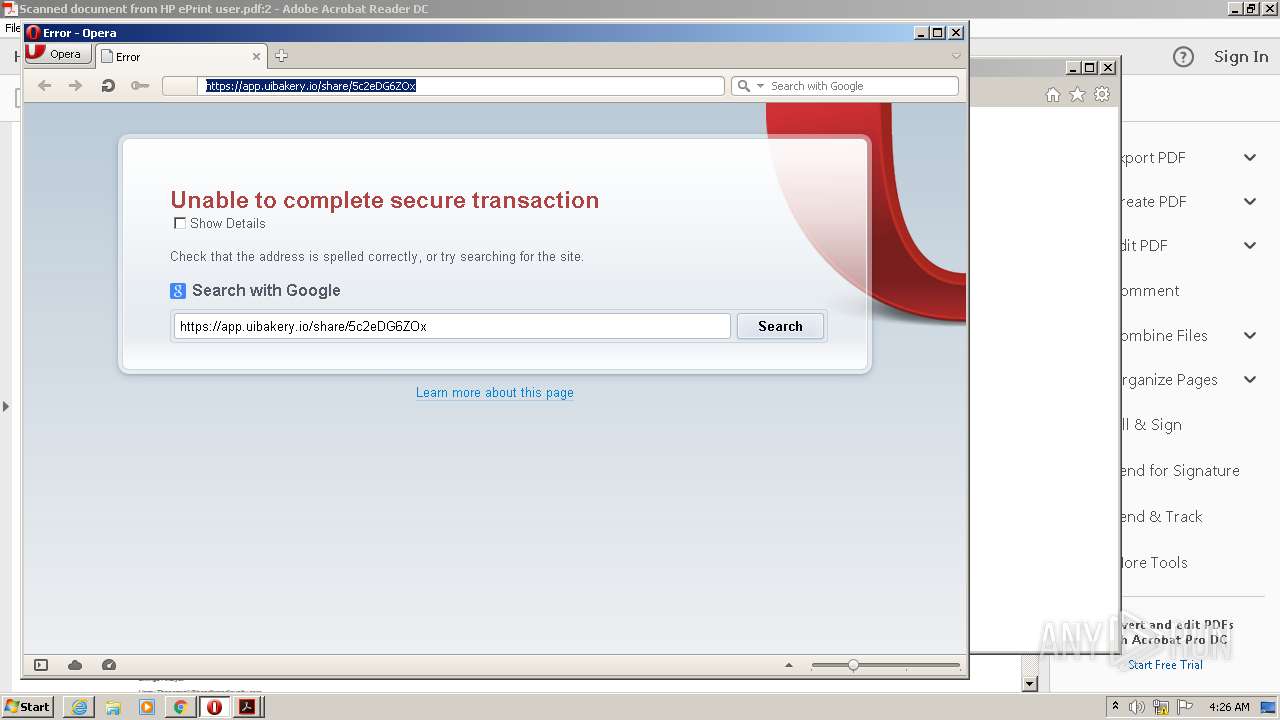
Changes IE settings (feature browser emulation)
- AcroRd32.exe (PID: 968)
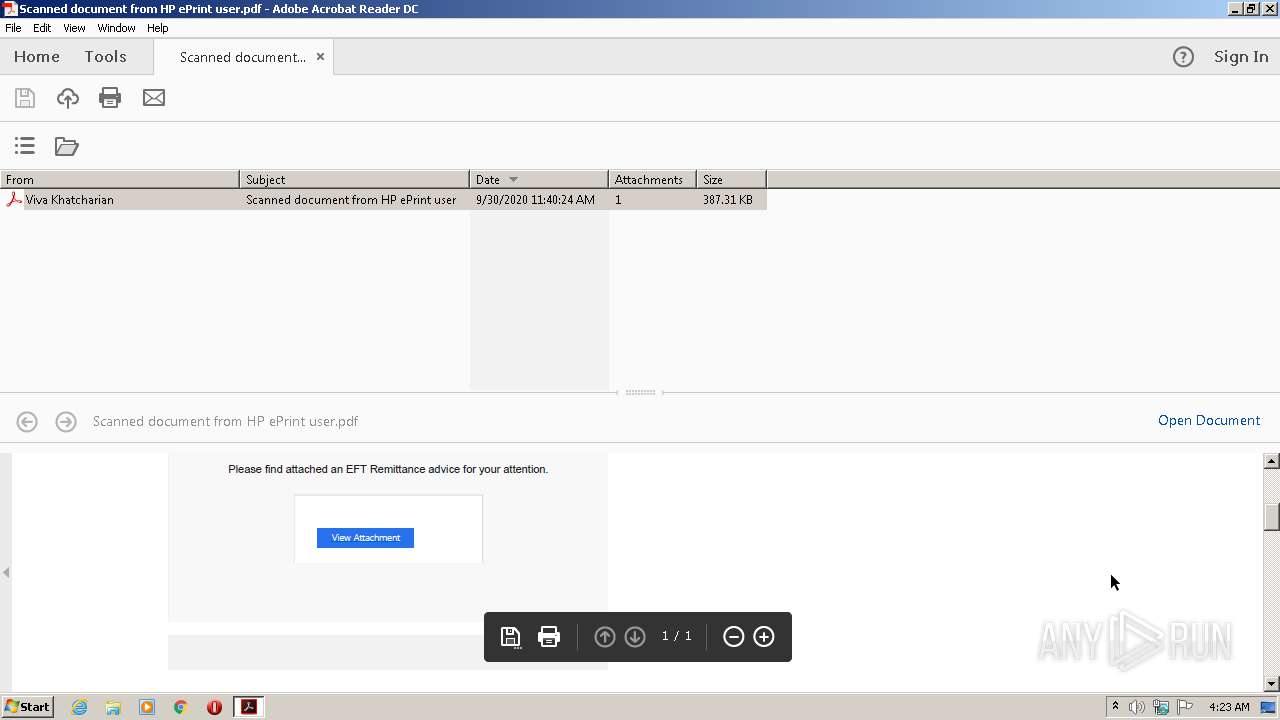
Starts Internet Explorer
- AcroRd32.exe (PID: 968)
Creates files in the program directory
- AdobeARM.exe (PID: 1700)
Executable content was dropped or overwritten
- AdobeARM.exe (PID: 1700)
INFO
Application launched itself
- AcroRd32.exe (PID: 968)
- iexplore.exe (PID: 896)
- RdrCEF.exe (PID: 3940)
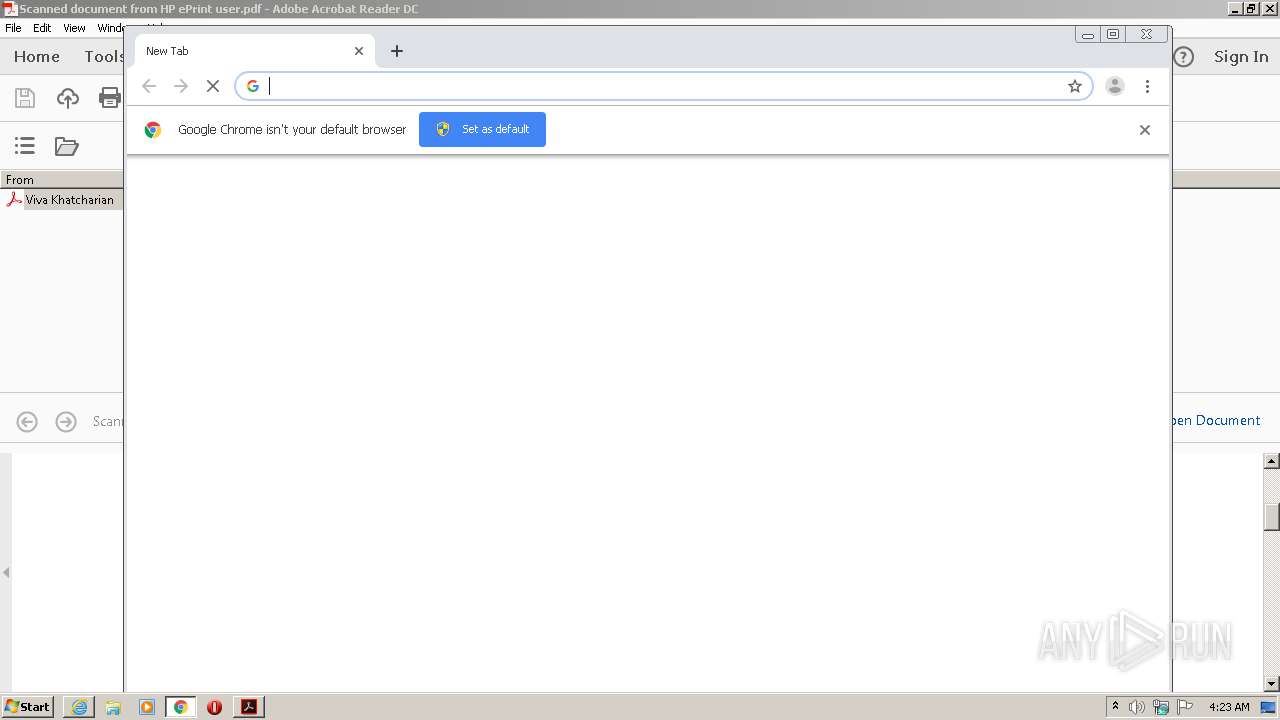
- chrome.exe (PID: 3824)
- iexplore.exe (PID: 3972)
Reads the hosts file
- RdrCEF.exe (PID: 3940)
- chrome.exe (PID: 3824)
- chrome.exe (PID: 3192)
Reads Internet Cache Settings
- AcroRd32.exe (PID: 996)
- iexplore.exe (PID: 896)
- iexplore.exe (PID: 2296)
- AcroRd32.exe (PID: 968)
- iexplore.exe (PID: 3972)
- iexplore.exe (PID: 3828)
Reads internet explorer settings
- iexplore.exe (PID: 2296)
- iexplore.exe (PID: 3828)
Changes settings of System certificates
- iexplore.exe (PID: 896)
Adds / modifies Windows certificates
- iexplore.exe (PID: 896)
Changes internet zones settings
- iexplore.exe (PID: 896)
- iexplore.exe (PID: 3972)
Creates files in the user directory
- iexplore.exe (PID: 2296)
- iexplore.exe (PID: 896)
- chrome.exe (PID: 3824)
- opera.exe (PID: 3960)
Reads settings of System Certificates
- iexplore.exe (PID: 896)
- iexplore.exe (PID: 2296)
- AcroRd32.exe (PID: 968)
- chrome.exe (PID: 3192)
- iexplore.exe (PID: 3828)
Manual execution by user
- chrome.exe (PID: 3824)
- opera.exe (PID: 3960)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| | | Adobe Portable Document Format (100) |
EXIF
| PDFVersion: | 1.7 |
|---|---|
| Linearized: | No |
| CreateDate: | 2020:09:30 11:48:20+09:30 |
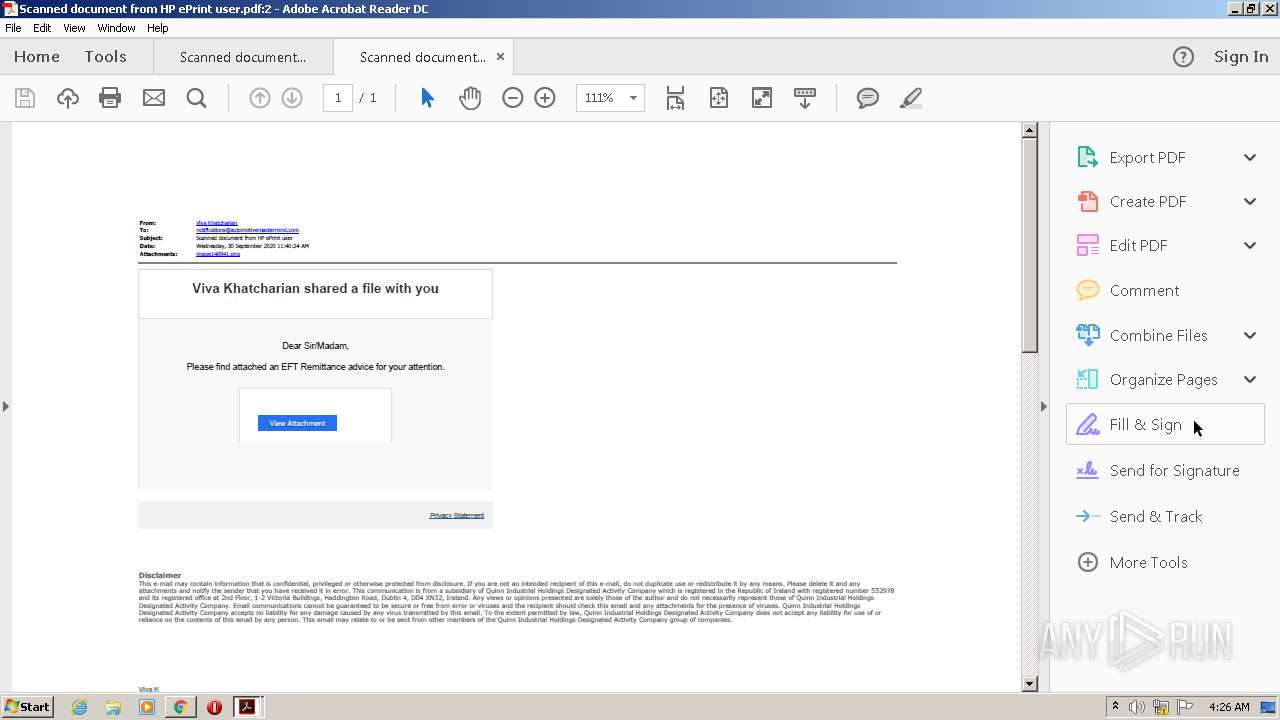
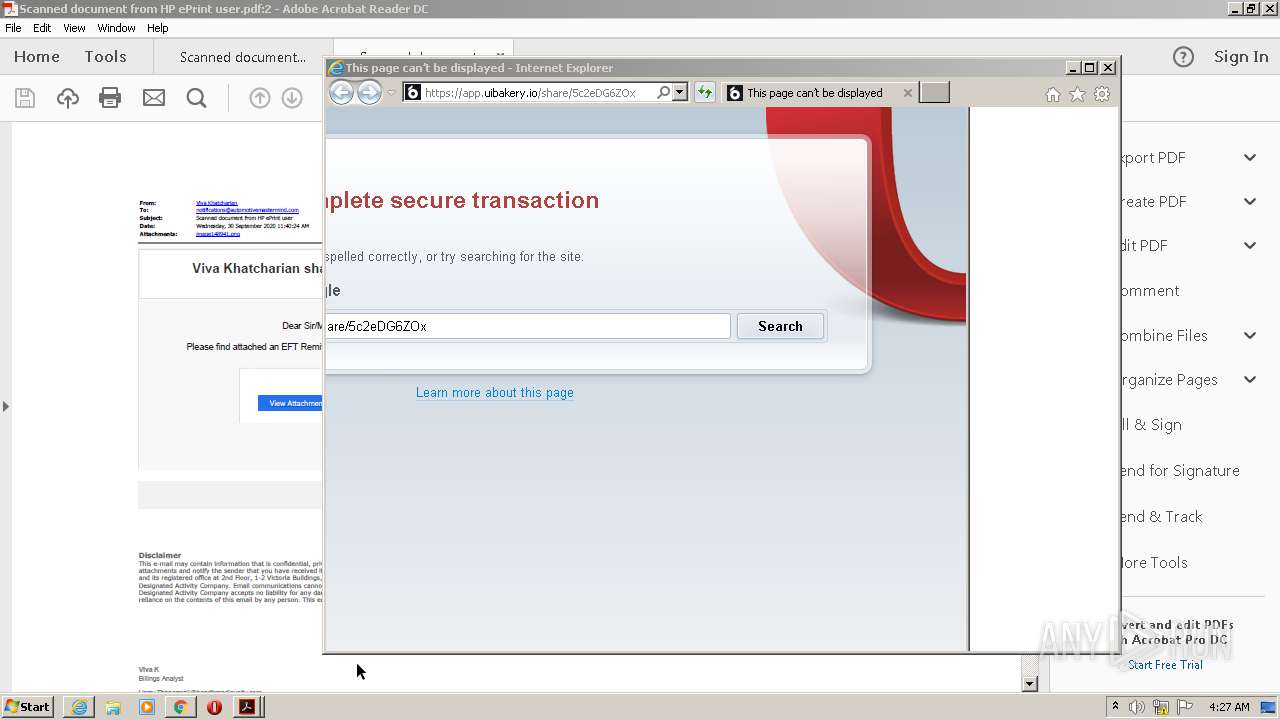
| Creator: | Acrobat PDFMaker 20 for Microsoft Outlook |
| ModifyDate: | 2020:09:30 11:48:27+09:30 |
| Producer: | Adobe PDF Library 20.9.95 |
| Title: | - |
| TaggedPDF: | Yes |
| PageMode: | UseAttachments |
| PageCount: | 1 |
XMP
| XMPToolkit: | Adobe XMP Core 5.6-c017 91.164374, 2020/03/05-20:41:30 |
|---|---|
| ModifyDate: | 2020:09:30 11:48:27+09:30 |
| CreateDate: | 2020:09:30 11:48:20+09:30 |
| MetadataDate: | 2020:09:30 11:48:27+09:30 |
| CreatorTool: | Acrobat PDFMaker 20 for Microsoft Outlook |
| DocumentID: | uuid:b4e24dd1-7929-4212-8949-83cff789c6eb |
| InstanceID: | uuid:9e393554-f179-4a97-9dc8-02eb004ce206 |
| Format: | application/pdf |
| Title: | - |
| Producer: | Adobe PDF Library 20.9.95 |
Total processes
75
Monitored processes
38
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 804 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\Reader_sl.exe" | C:\Program Files\Adobe\Acrobat Reader DC\Reader\Reader_sl.exe | — | AdobeARM.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe Acrobat SpeedLauncher Exit code: 0 Version: 15.23.20053.211670 Modules
| |||||||||||||||
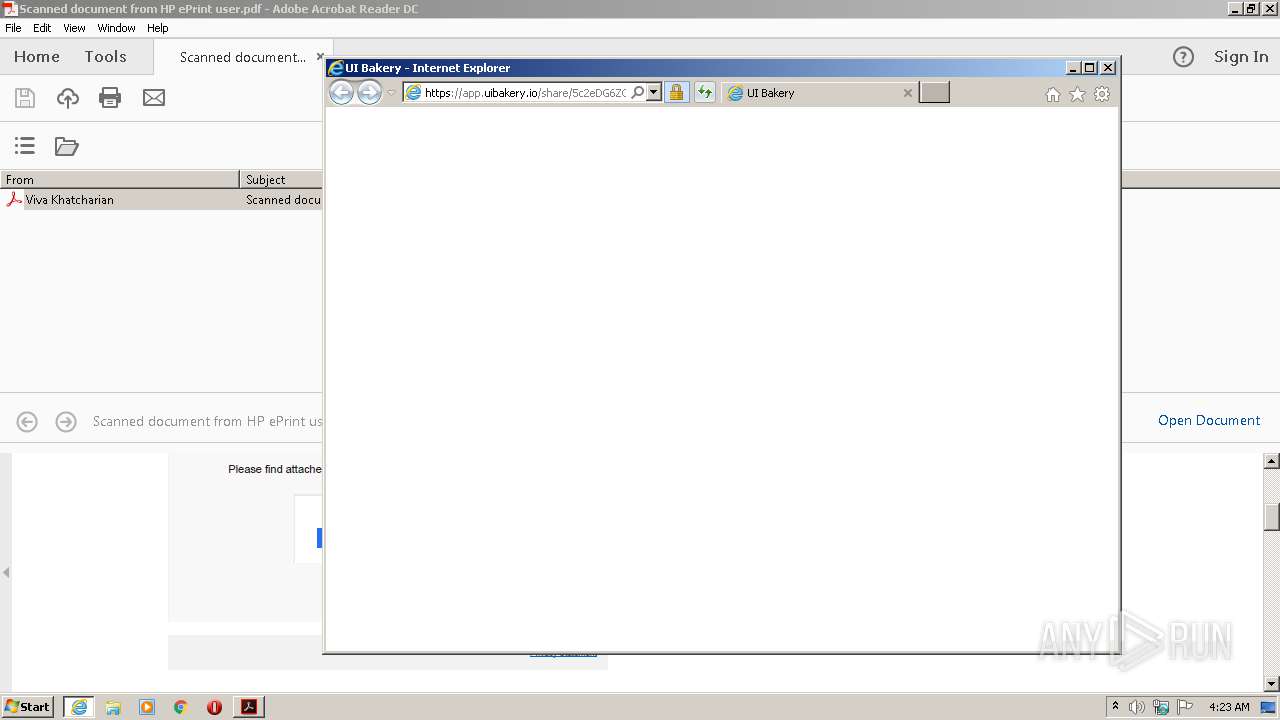
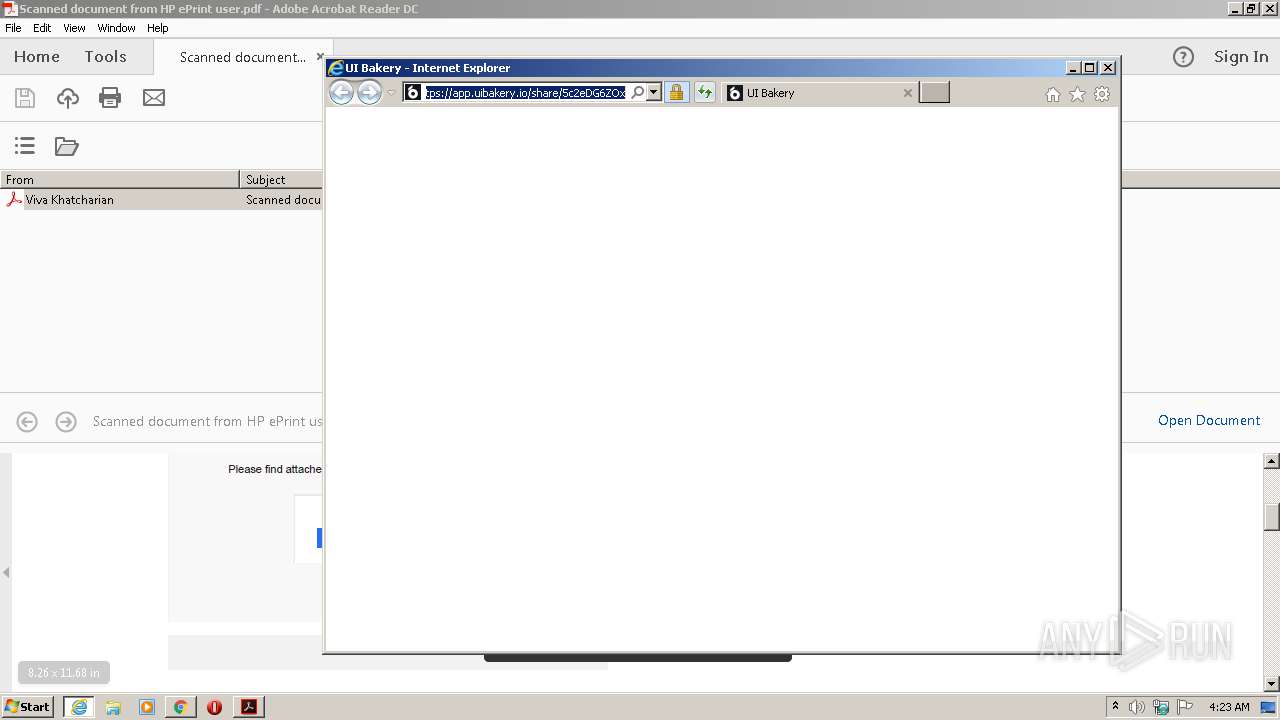
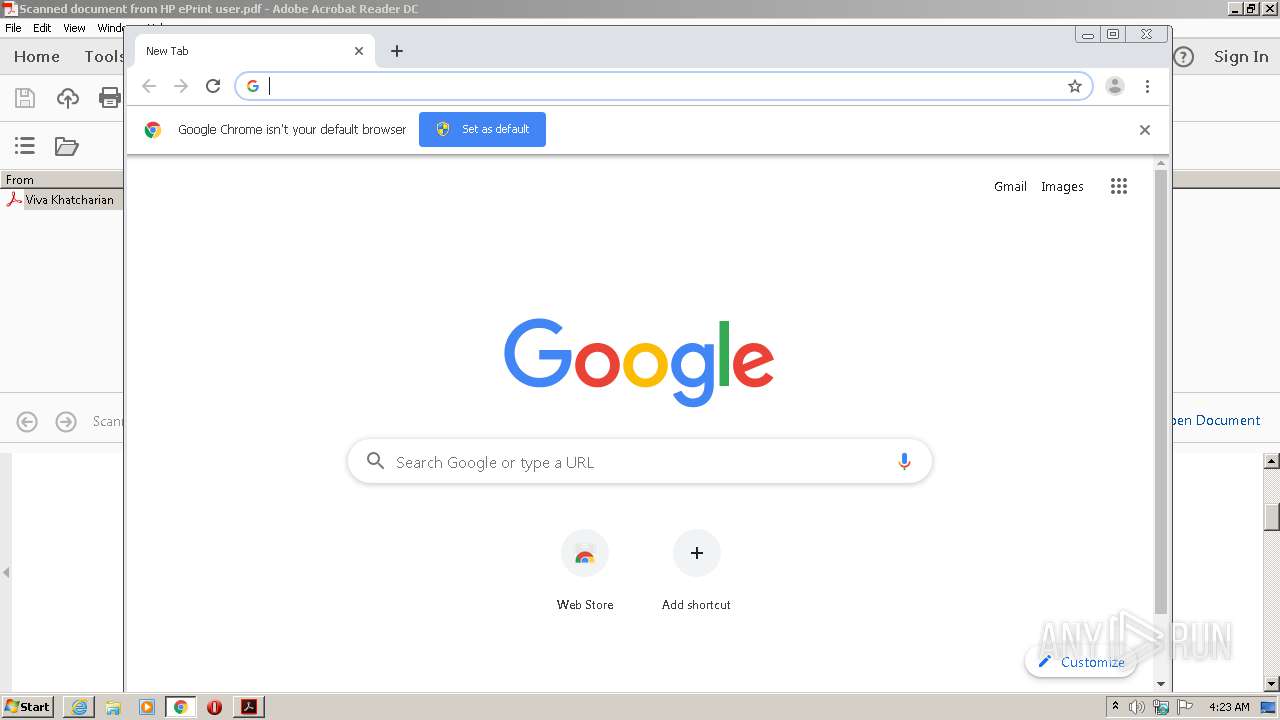
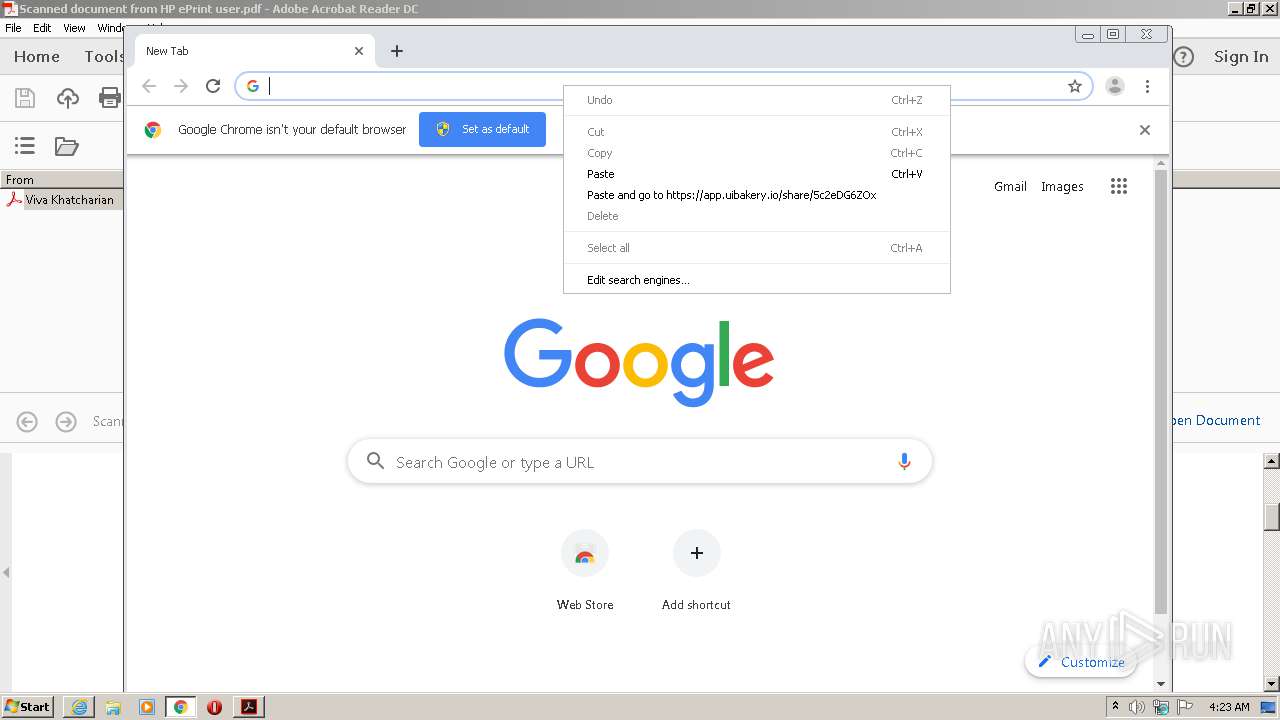
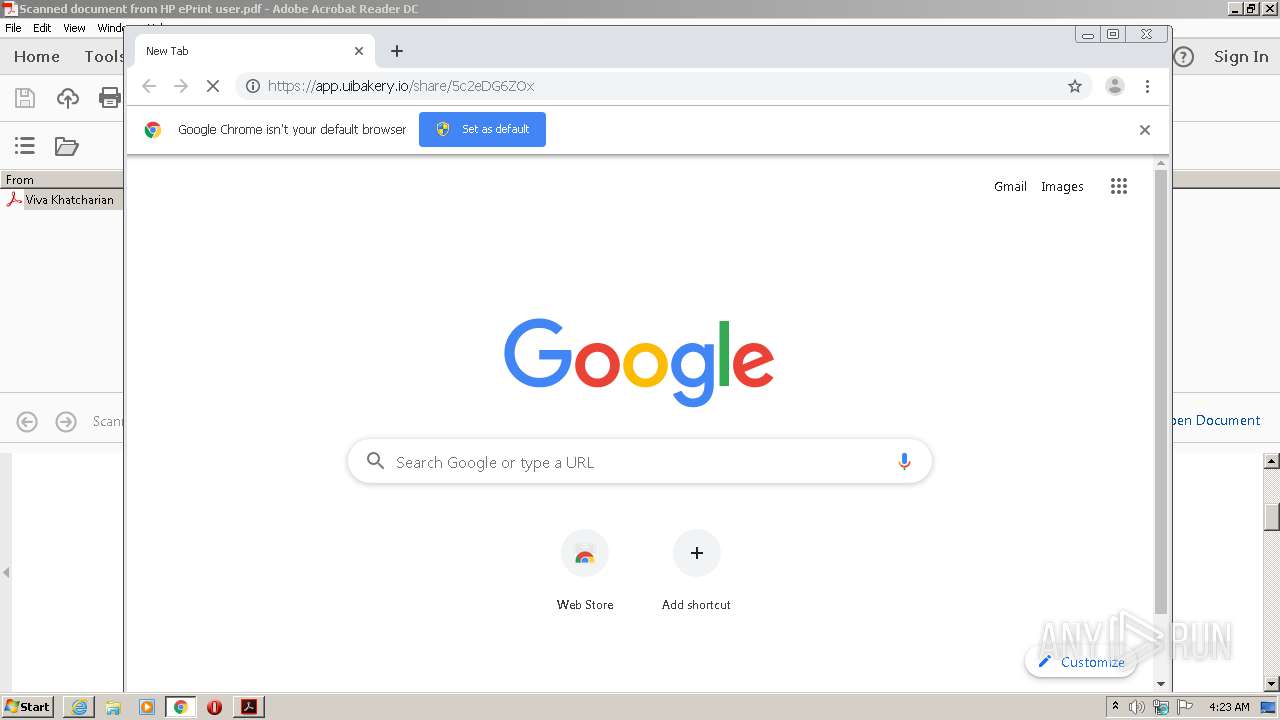
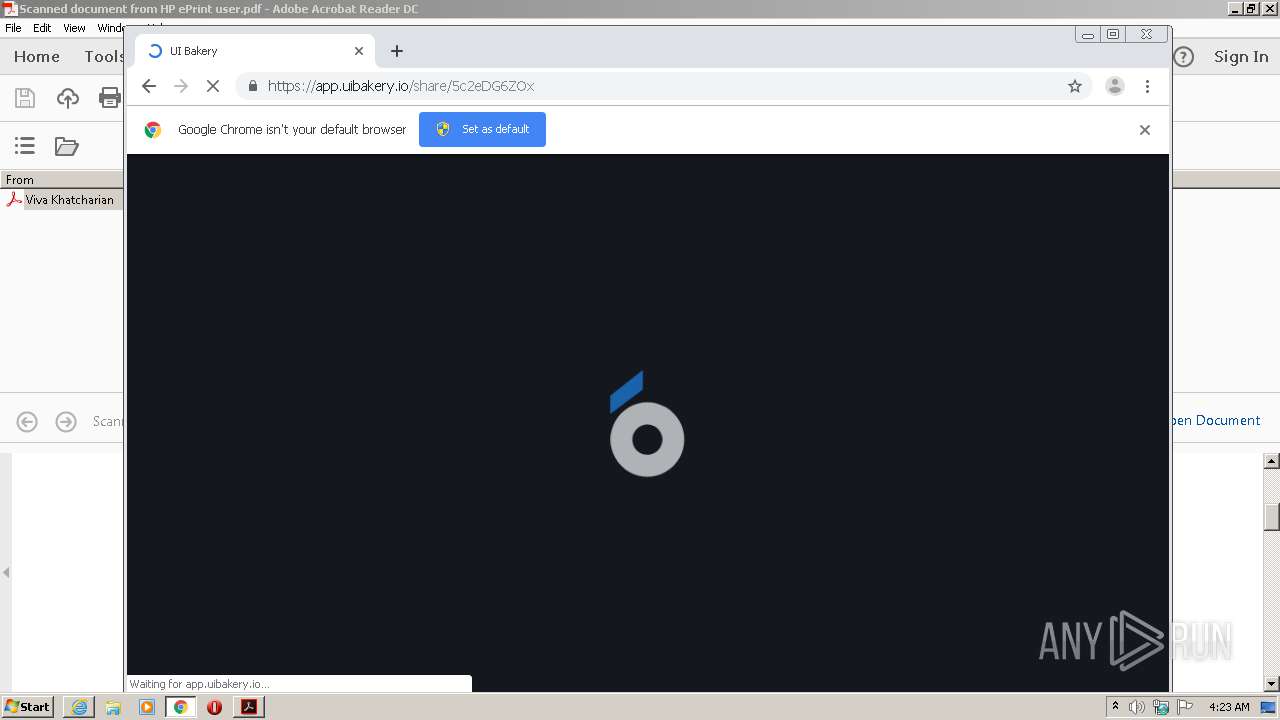
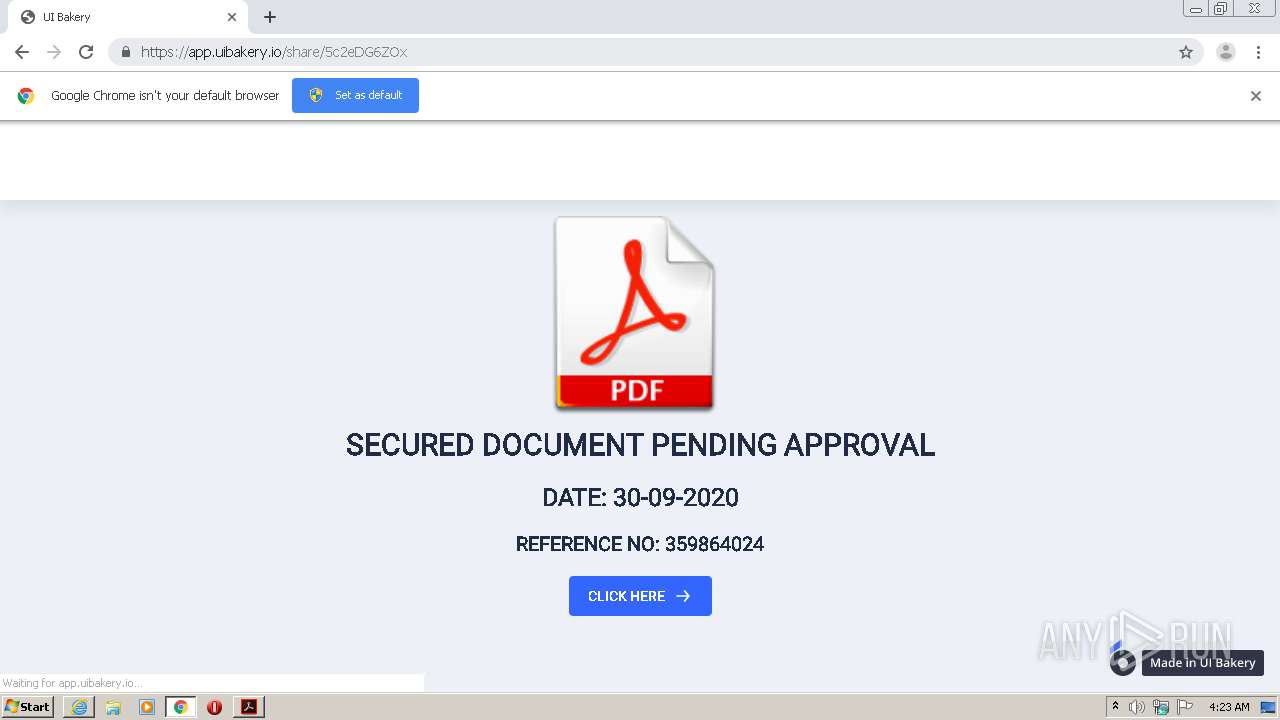
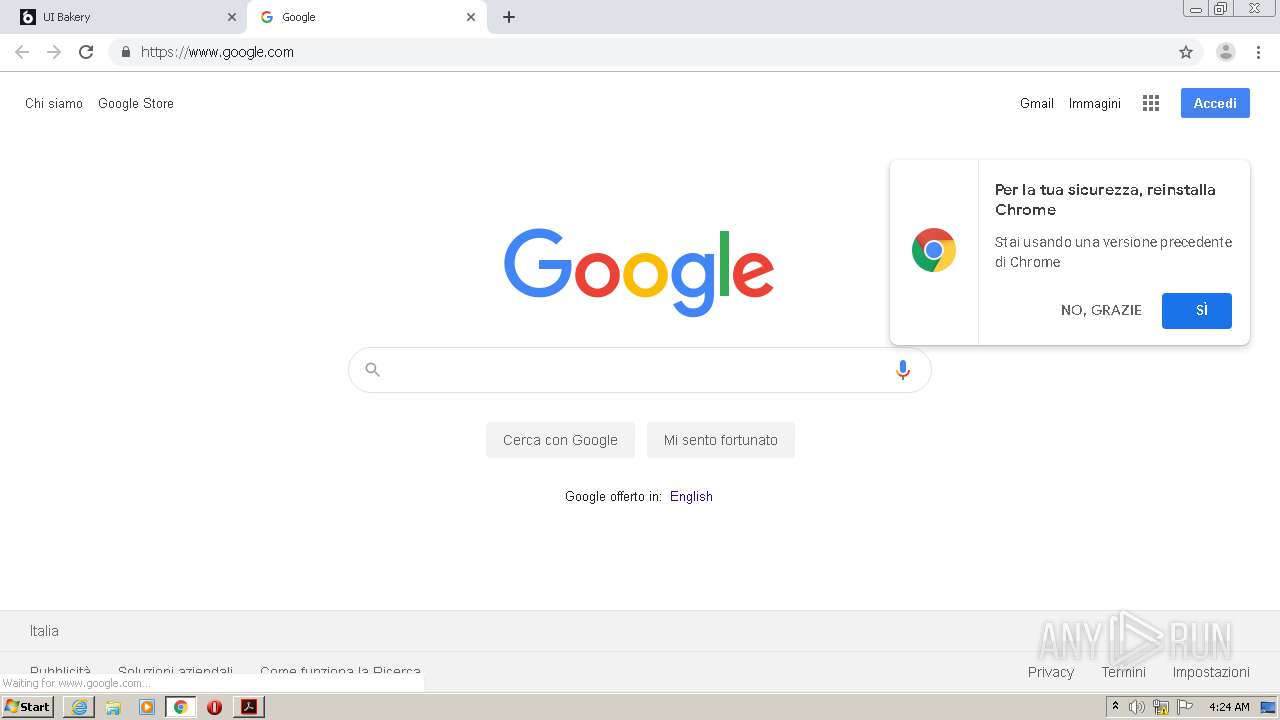
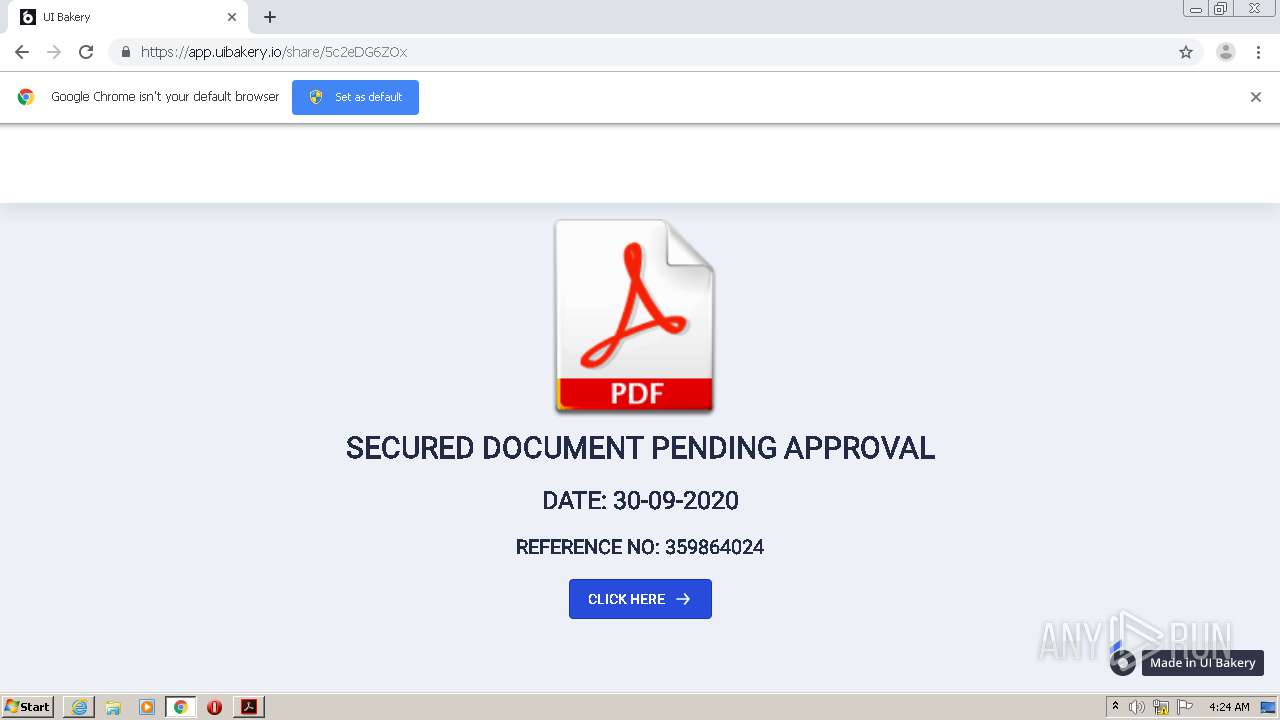
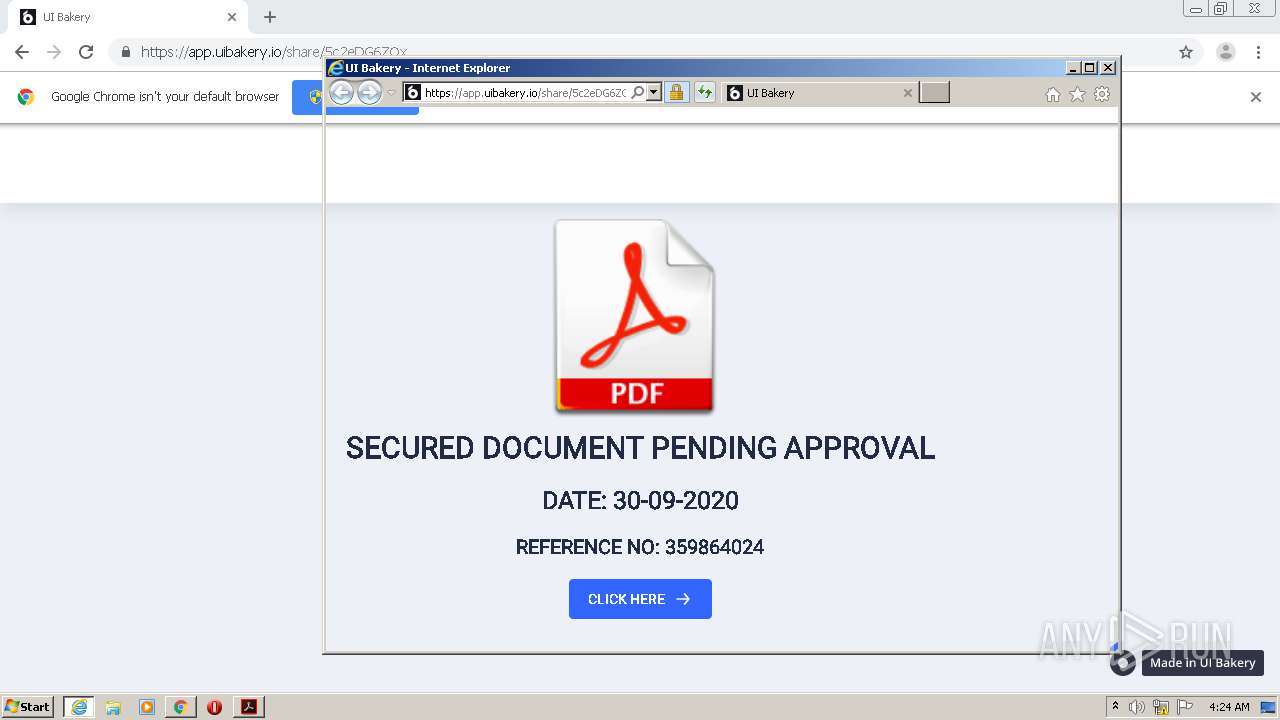
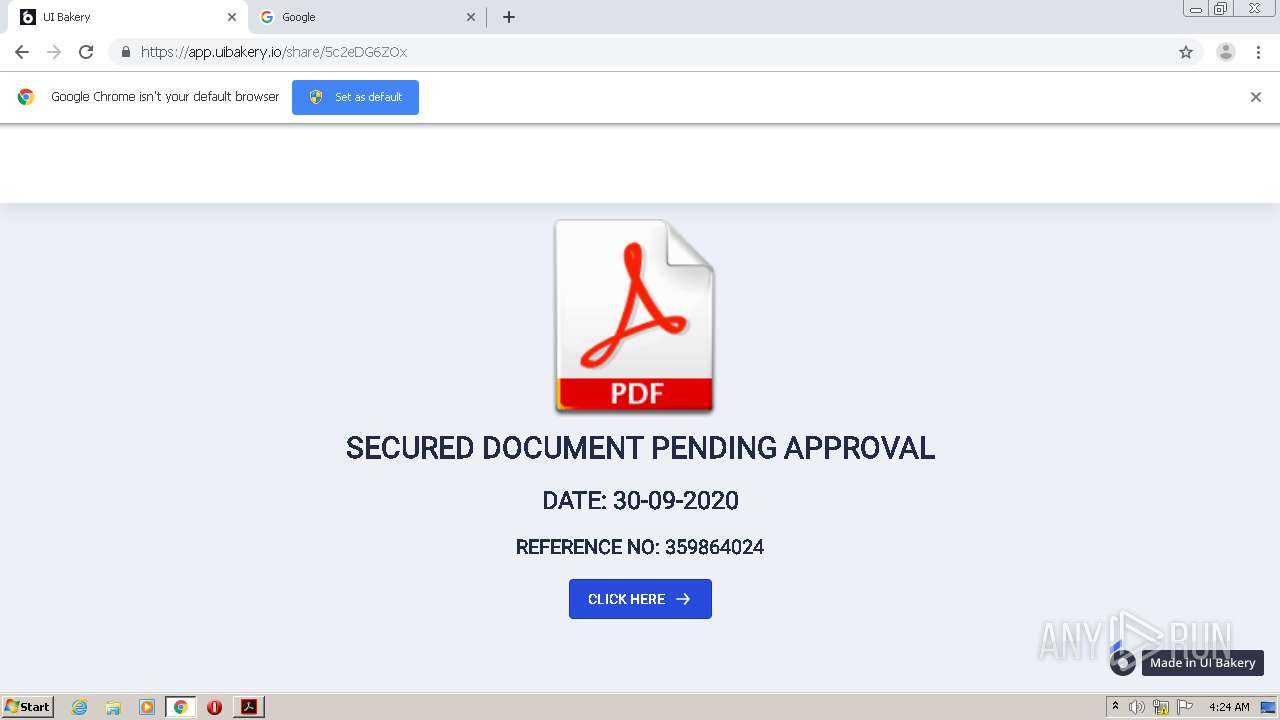
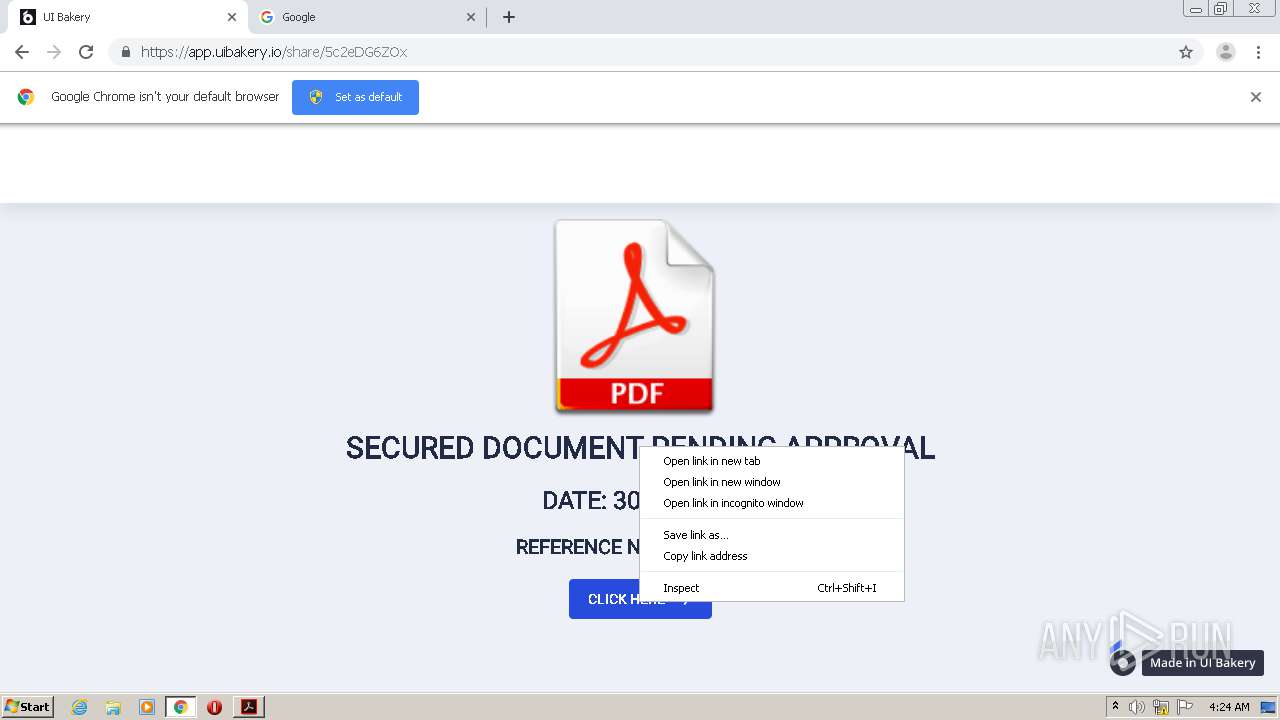
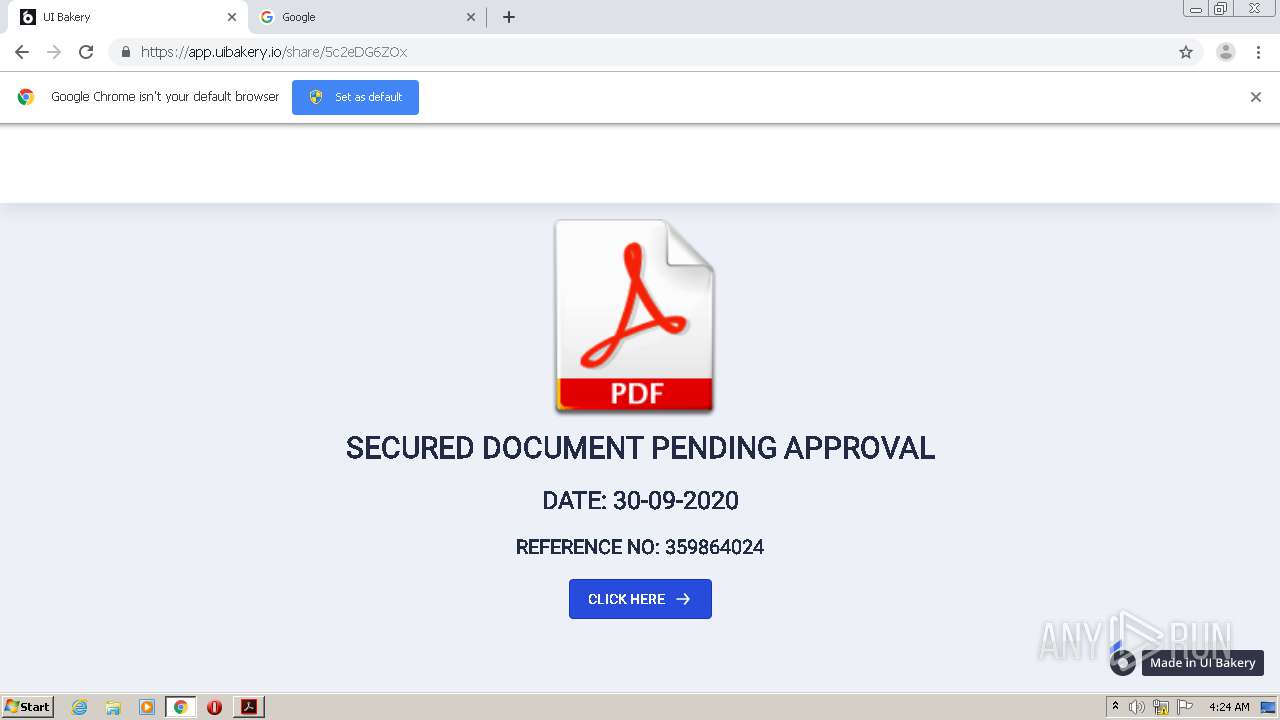
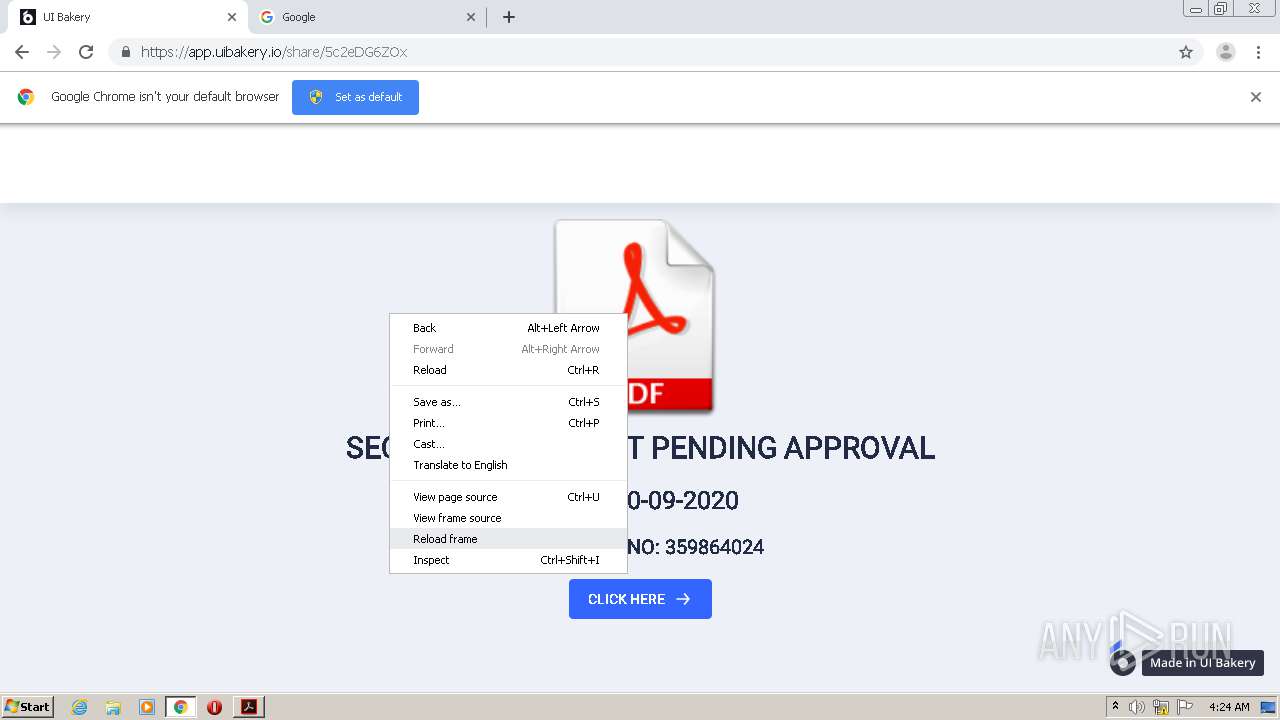
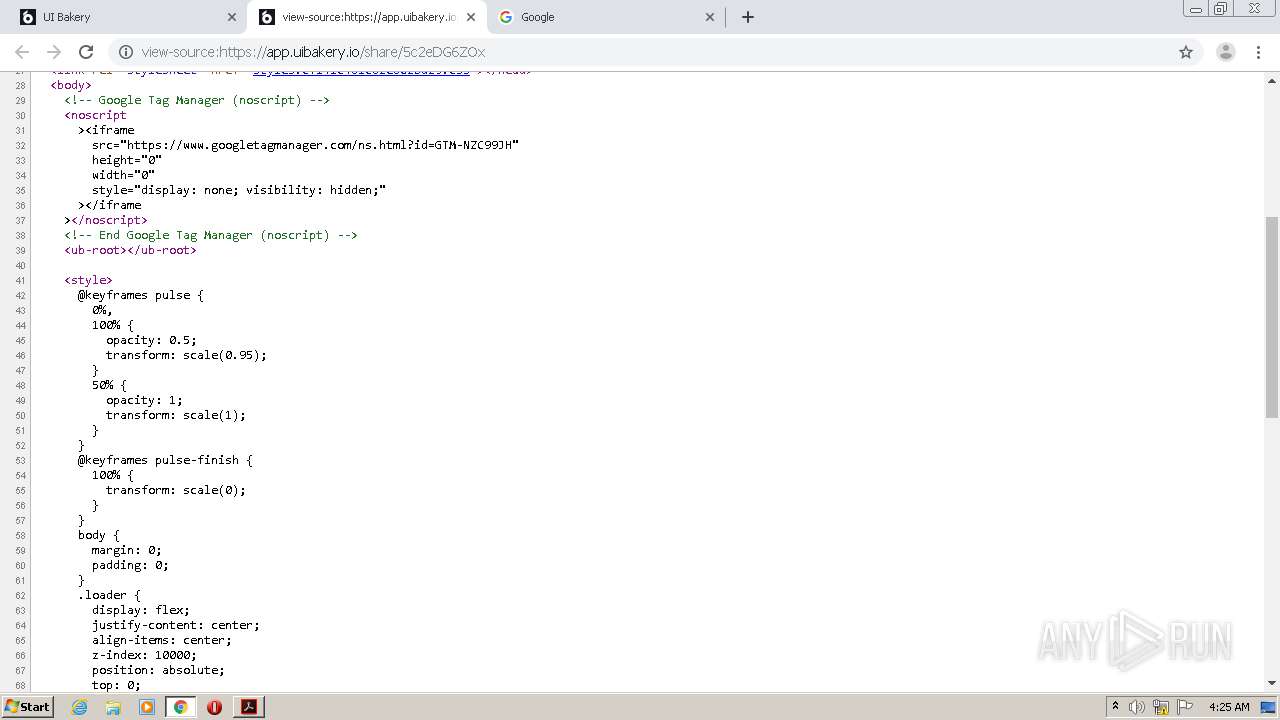
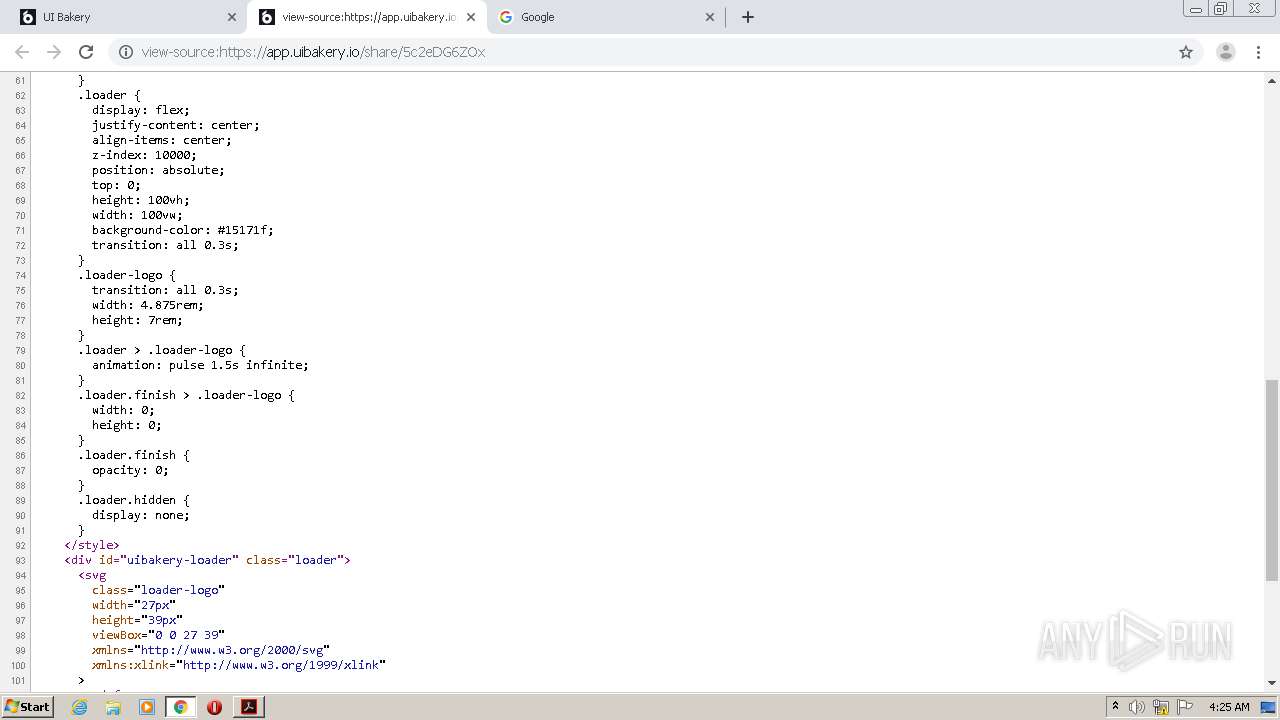
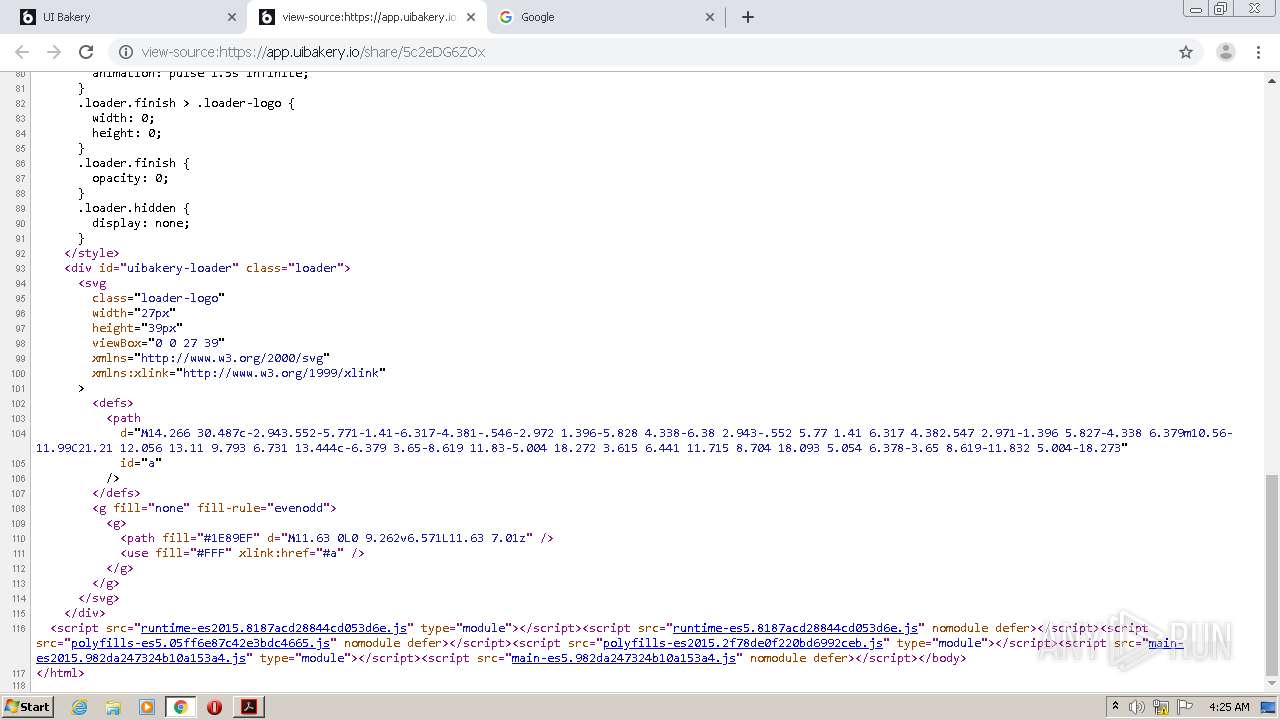
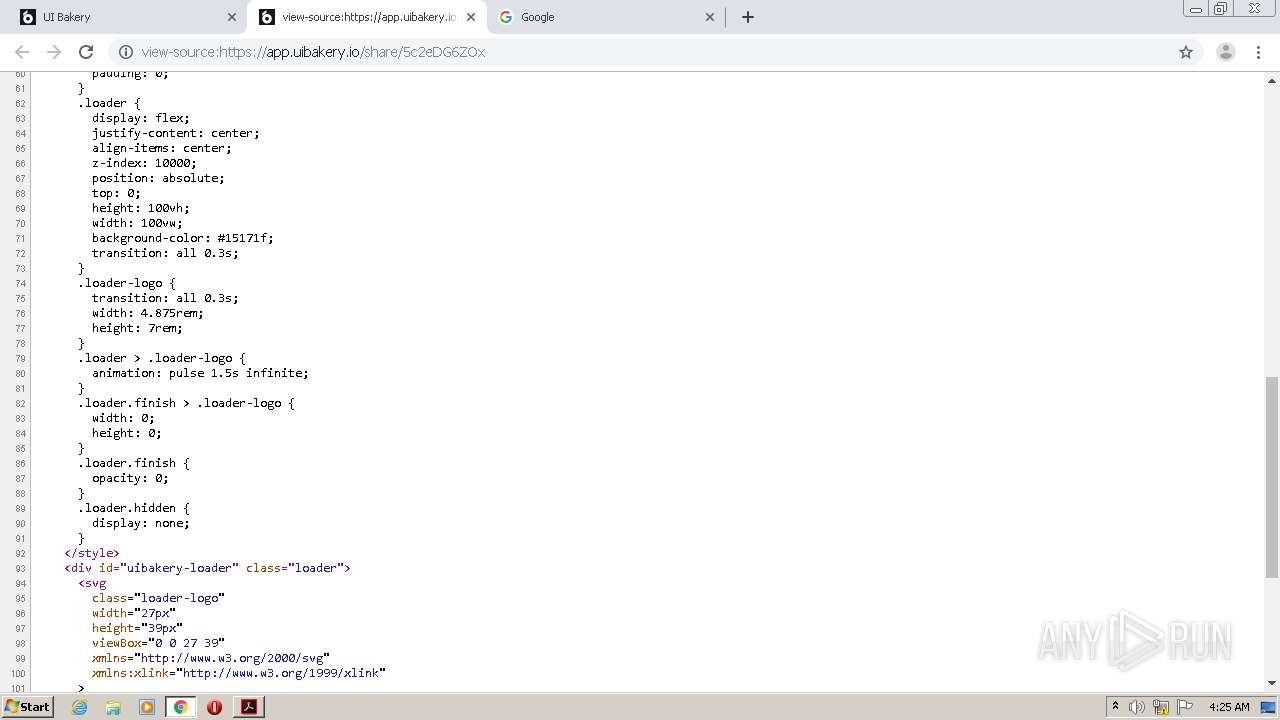
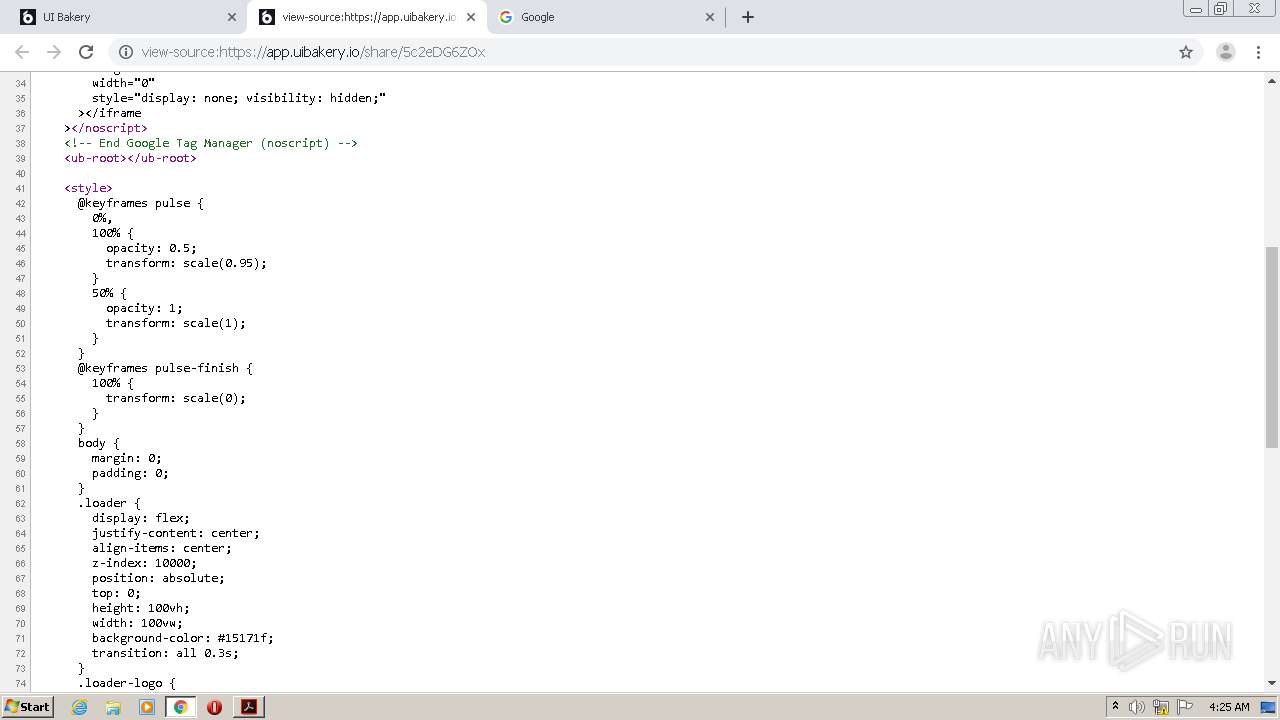
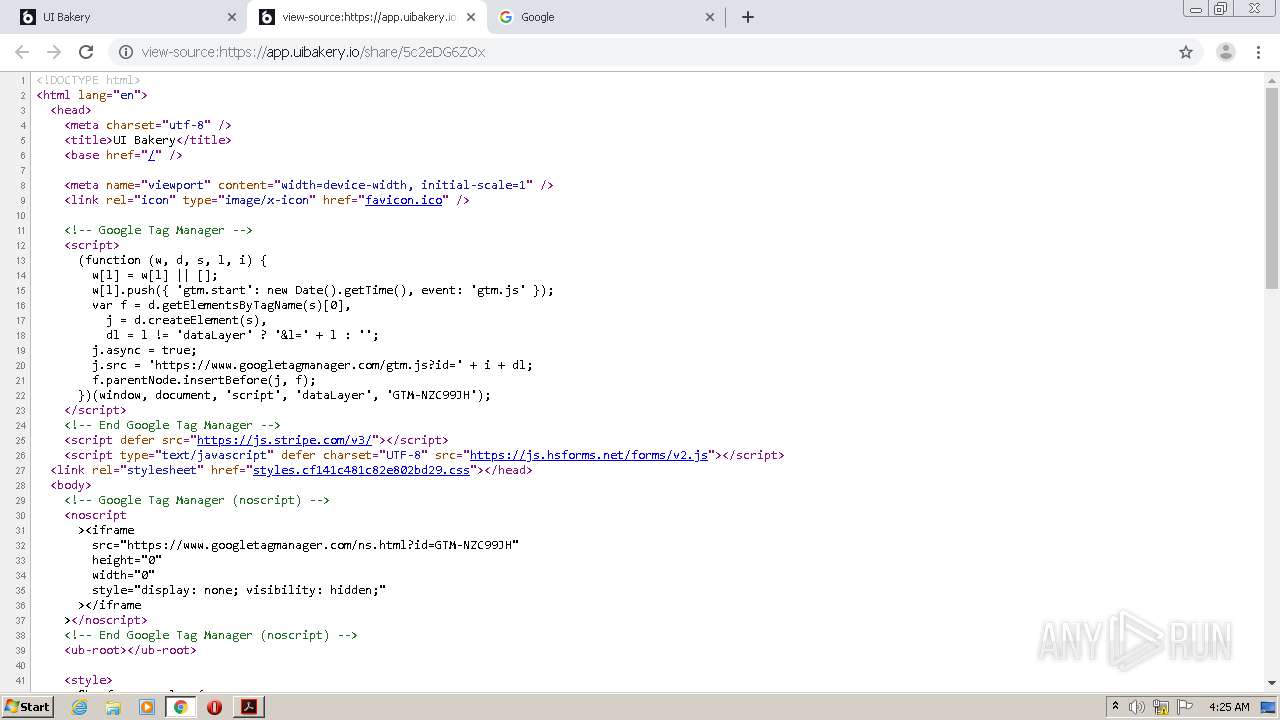
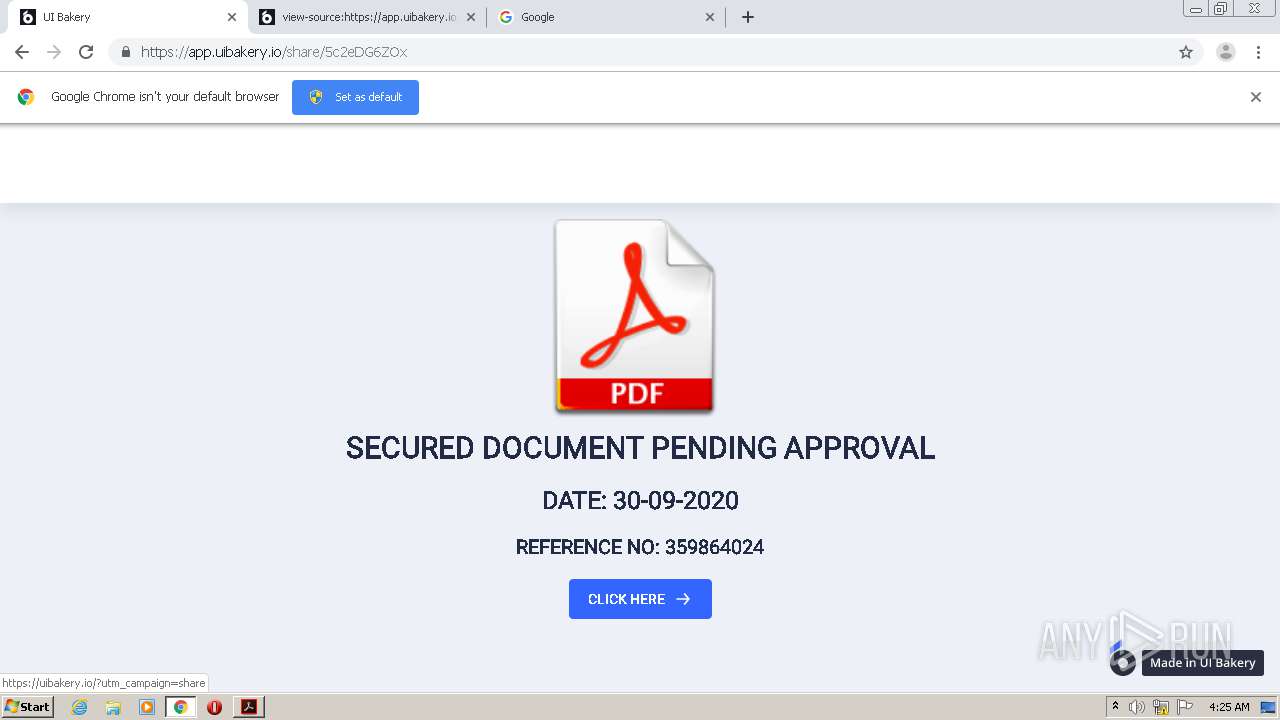
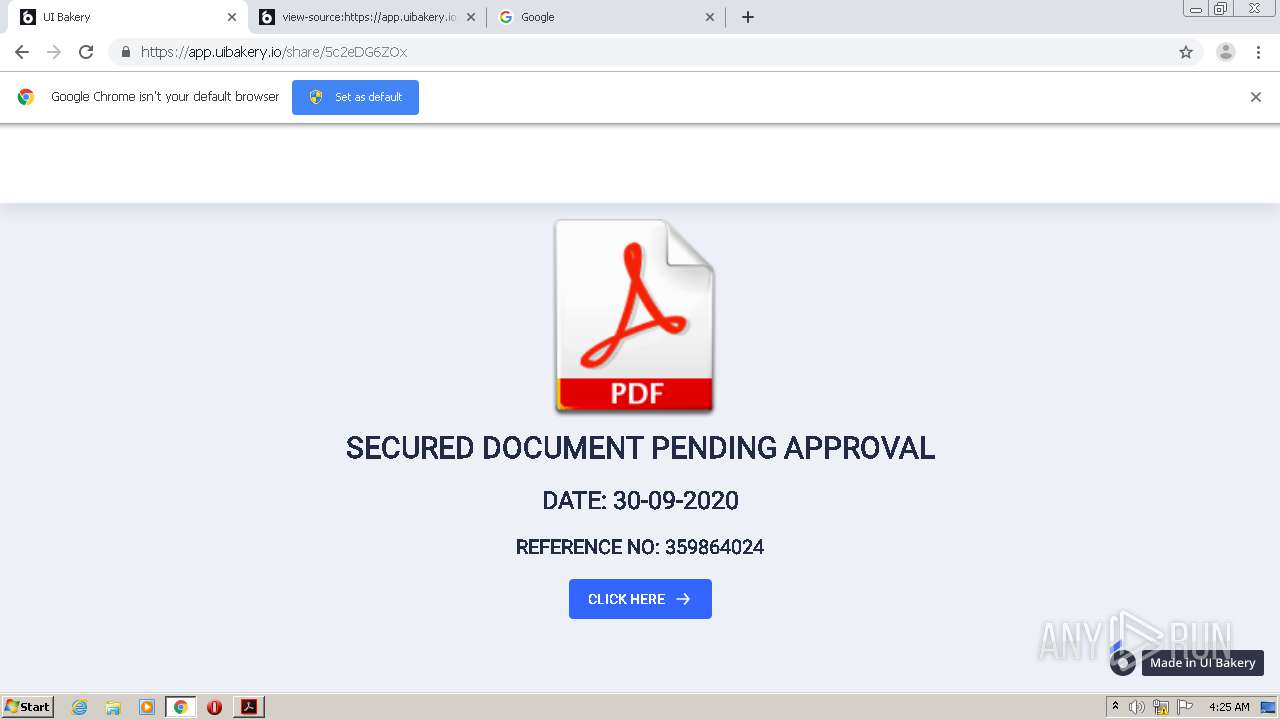
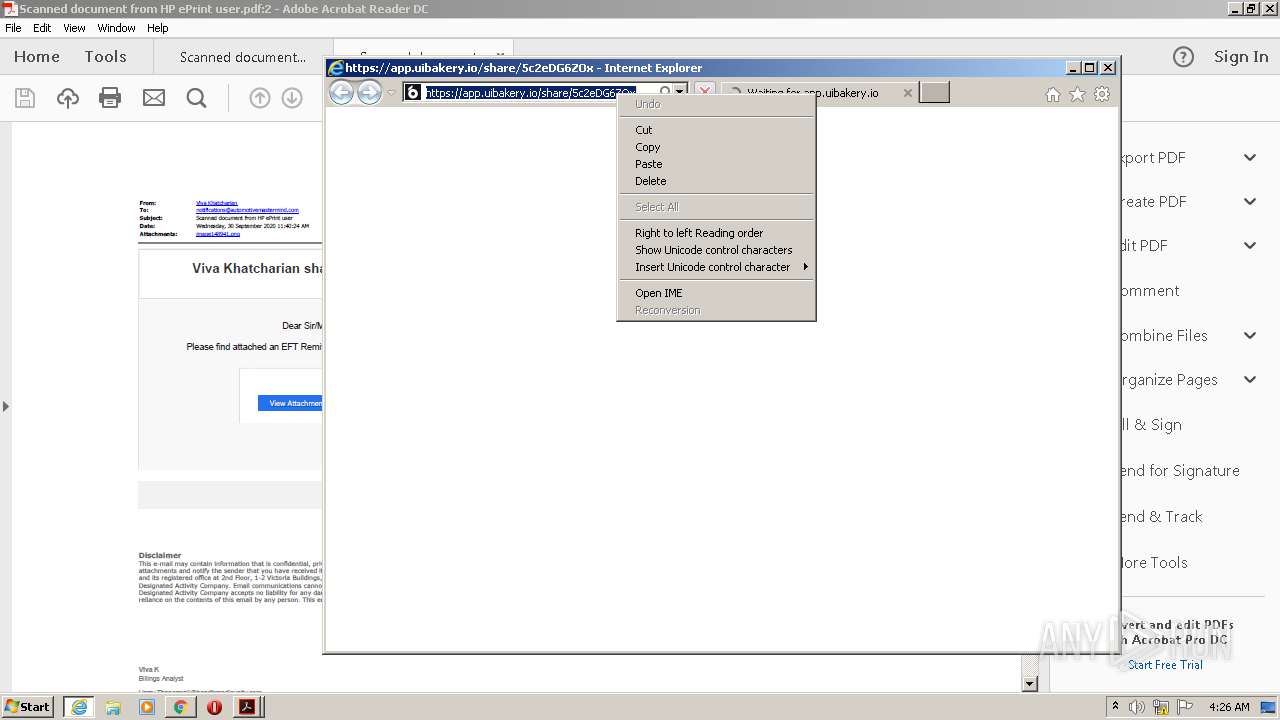
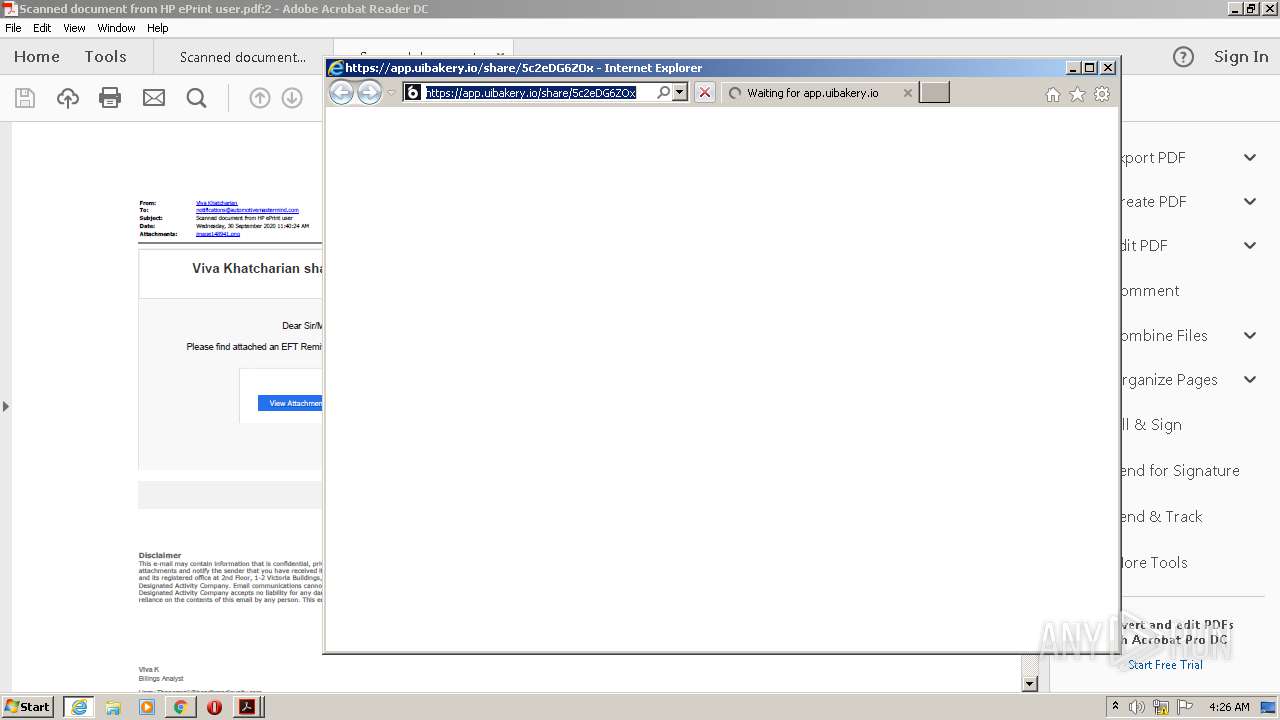
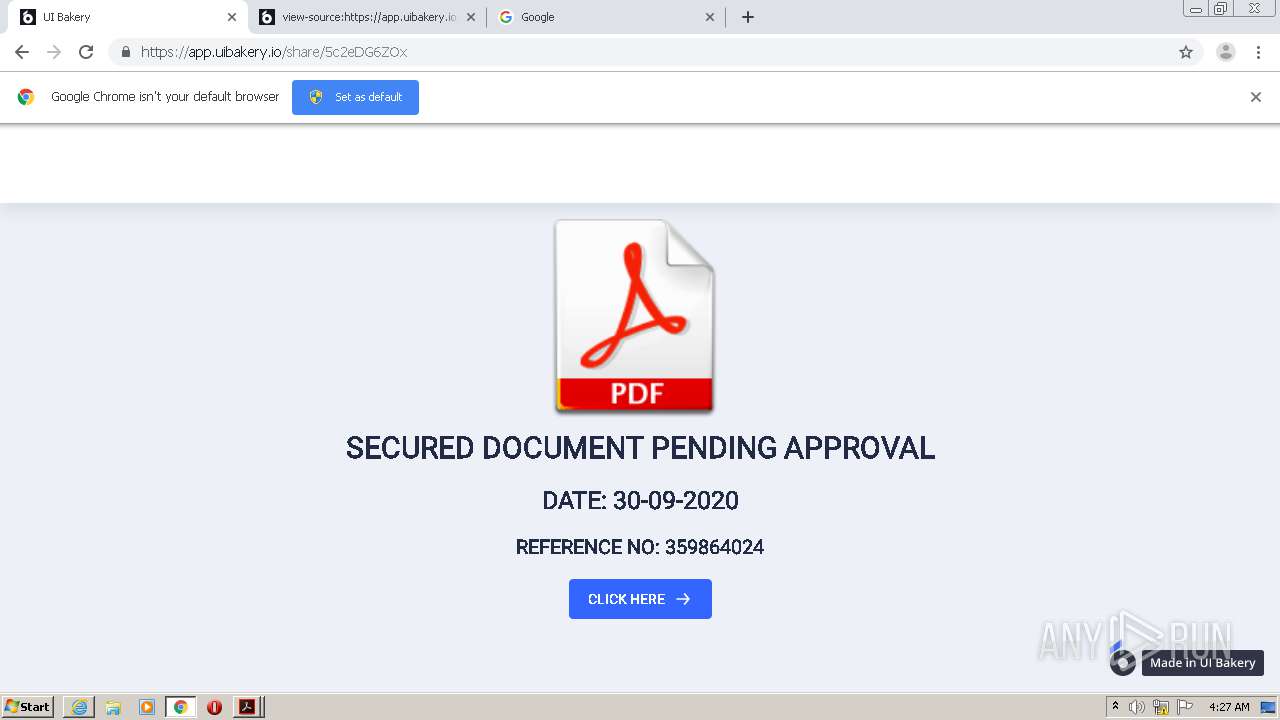
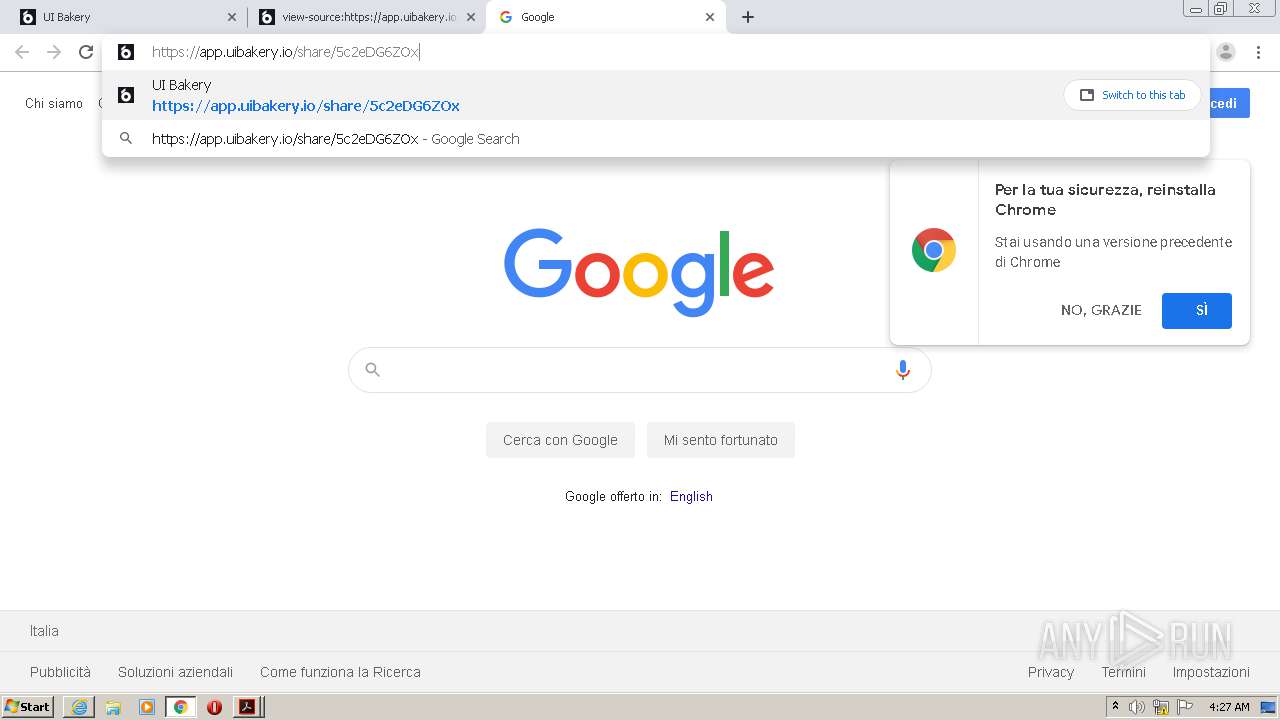
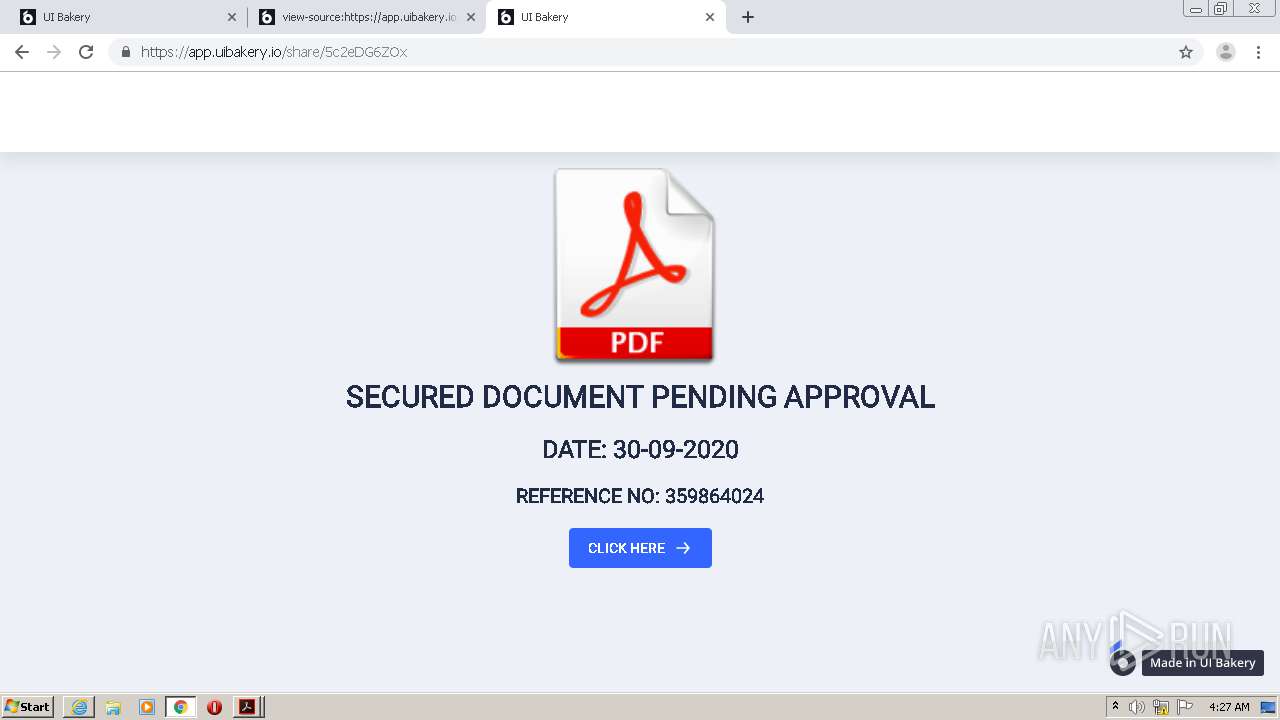
| 896 | "C:\Program Files\Internet Explorer\iexplore.exe" https://app.uibakery.io/share/5c2eDG6ZOx | C:\Program Files\Internet Explorer\iexplore.exe | AcroRd32.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 968 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe" "C:\Users\admin\Desktop\Scanned document from HP ePrint user.pdf" | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe | explorer.exe | ||||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe Acrobat Reader DC Exit code: 0 Version: 15.23.20070.215641 Modules
| |||||||||||||||
| 996 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe" --type=renderer "C:\Users\admin\Desktop\Scanned document from HP ePrint user.pdf" | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe | — | AcroRd32.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe Acrobat Reader DC Exit code: 0 Version: 15.23.20070.215641 Modules
| |||||||||||||||
| 1036 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,10328245585807017117,6369907905306808263,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6700335776930785962 --renderer-client-id=25 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3620 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1508 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=960,10328245585807017117,6369907905306808263,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=16723424403266195636 --mojo-platform-channel-handle=3616 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1700 | "C:\Program Files\Common Files\Adobe\ARM\1.0\AdobeARM.exe" /PRODUCT:Reader /VERSION:15.0 /MODE:3 | C:\Program Files\Common Files\Adobe\ARM\1.0\AdobeARM.exe | AcroRd32.exe | ||||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe Reader and Acrobat Manager Exit code: 0 Version: 1.824.27.2646 Modules
| |||||||||||||||
| 1836 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=960,10328245585807017117,6369907905306808263,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=7719873356351099443 --mojo-platform-channel-handle=2100 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2052 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=960,10328245585807017117,6369907905306808263,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=6510653334450523060 --mojo-platform-channel-handle=3200 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2160 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,10328245585807017117,6369907905306808263,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13002730864602986621 --renderer-client-id=14 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3752 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
8 399
Read events
7 930
Write events
462
Delete events
7
Modification events
| (PID) Process: | (996) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Adobe\Acrobat Reader\DC\ExitSection |
| Operation: | write | Name: | bLastExitNormal |
Value: 0 | |||
| (PID) Process: | (968) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Adobe\Acrobat Reader\DC\AVGeneral\cRecentFiles\c1 |
| Operation: | write | Name: | aFS |
Value: DOS | |||
| (PID) Process: | (968) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Adobe\Acrobat Reader\DC\AVGeneral\cRecentFiles\c1 |
| Operation: | write | Name: | tDIText |
Value: /C/Users/admin/Desktop/Scanned document from HP ePrint user.pdf | |||
| (PID) Process: | (968) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Adobe\Acrobat Reader\DC\AVGeneral\cRecentFiles\c1 |
| Operation: | write | Name: | tFileName |
Value: Scanned document from HP ePrint user.pdf | |||
| (PID) Process: | (968) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Adobe\Acrobat Reader\DC\AVGeneral\cRecentFiles\c1 |
| Operation: | write | Name: | tFileSource |
Value: local | |||
| (PID) Process: | (968) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Adobe\Acrobat Reader\DC\AVGeneral\cRecentFiles\c1 |
| Operation: | write | Name: | sFileAncestors |
Value: 5B5D00 | |||
| (PID) Process: | (968) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Adobe\Acrobat Reader\DC\AVGeneral\cRecentFiles\c1 |
| Operation: | write | Name: | sDI |
Value: 2F432F55736572732F61646D696E2F4465736B746F702F5363616E6E656420646F63756D656E742066726F6D20485020655072696E7420757365722E70646600 | |||
| (PID) Process: | (968) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Adobe\Acrobat Reader\DC\AVGeneral\cRecentFiles\c1 |
| Operation: | write | Name: | sDate |
Value: 443A32303230303933303034323330392B30312730302700 | |||
| (PID) Process: | (968) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Adobe\Acrobat Reader\DC\AVGeneral\cRecentFiles\c1 |
| Operation: | write | Name: | uFileSize |
Value: 406824 | |||
| (PID) Process: | (968) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Adobe\Acrobat Reader\DC\AVGeneral\cRecentFiles\c1 |
| Operation: | write | Name: | uPageCount |
Value: 1 | |||
Executable files
2
Suspicious files
266
Text files
232
Unknown types
64
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 996 | AcroRd32.exe | C:\Users\admin\AppData\LocalLow\Adobe\Acrobat\DC\ReaderMessages-journal | — | |
MD5:— | SHA256:— | |||
| 996 | AcroRd32.exe | C:\Users\admin\AppData\Local\Temp\acrord32_sbx\A9R12ha4o9_1jr995w_ro.tmp | — | |
MD5:— | SHA256:— | |||
| 996 | AcroRd32.exe | C:\Users\admin\AppData\Local\Temp\acrord32_sbx\A9R1vmlyit_1jr995v_ro.tmp | — | |
MD5:— | SHA256:— | |||
| 996 | AcroRd32.exe | C:\Users\admin\AppData\Local\Temp\acrord32_sbx\A9R24q0mb_1jr995u_ro.tmp | — | |
MD5:— | SHA256:— | |||
| 996 | AcroRd32.exe | C:\Users\admin\AppData\Local\Temp\acrord32_sbx\A9R8wzoar_1jr995t_ro.tmp | — | |
MD5:— | SHA256:— | |||
| 968 | AcroRd32.exe | C:\Users\admin\AppData\Local\Temp\CabB197.tmp | — | |
MD5:— | SHA256:— | |||
| 968 | AcroRd32.exe | C:\Users\admin\AppData\Local\Temp\TarB198.tmp | — | |
MD5:— | SHA256:— | |||
| 2296 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\CabB466.tmp | — | |
MD5:— | SHA256:— | |||
| 2296 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\TarB467.tmp | — | |
MD5:— | SHA256:— | |||
| 968 | AcroRd32.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\7423F88C7F265F0DEFC08EA88C3BDE45_D975BBA8033175C8D112023D8A7A8AD6 | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
45
TCP/UDP connections
161
DNS requests
121
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
968 | AcroRd32.exe | GET | 304 | 2.16.177.91:80 | http://acroipm2.adobe.com/15/rdr/ENU/win/nooem/none/consumer/278_15_23_20070.zip | unknown | — | — | whitelisted |
2296 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQS14tALDViBvqCf47YkiQRtKz1BAQUpc436uuwdQ6UZ4i0RfrZJBCHlh8CEAElRPacIqHhL0rJdQWs5%2Fg%3D | US | der | 280 b | whitelisted |
968 | AcroRd32.exe | GET | 304 | 2.16.177.91:80 | http://acroipm2.adobe.com/15/rdr/ENU/win/nooem/none/consumer/277_15_23_20070.zip | unknown | — | — | whitelisted |
968 | AcroRd32.exe | GET | 304 | 2.16.177.91:80 | http://acroipm2.adobe.com/15/rdr/ENU/win/nooem/none/consumer/280_15_23_20070.zip | unknown | — | — | whitelisted |
2296 | iexplore.exe | GET | 200 | 142.250.74.195:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQDqXuNQ97mPtAIAAAAAektt | US | der | 472 b | whitelisted |
2296 | iexplore.exe | GET | 200 | 142.250.74.195:80 | http://ocsp.pki.goog/gts1o1core/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEAyDrs7o0RpNCAAAAABXoKo%3D | US | der | 471 b | whitelisted |
2296 | iexplore.exe | GET | 200 | 142.250.74.195:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
968 | AcroRd32.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAH9o%2BtuynXIiEOLckvPvJE%3D | US | der | 471 b | whitelisted |
2296 | iexplore.exe | GET | 200 | 142.250.74.195:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQDqXuNQ97mPtAIAAAAAektt | US | der | 472 b | whitelisted |
2296 | iexplore.exe | GET | 200 | 142.250.74.195:80 | http://ocsp.pki.goog/gts1o1core/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEAyDrs7o0RpNCAAAAABXoKo%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
968 | AcroRd32.exe | 2.21.36.203:443 | armmf.adobe.com | GTT Communications Inc. | FR | suspicious |
968 | AcroRd32.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
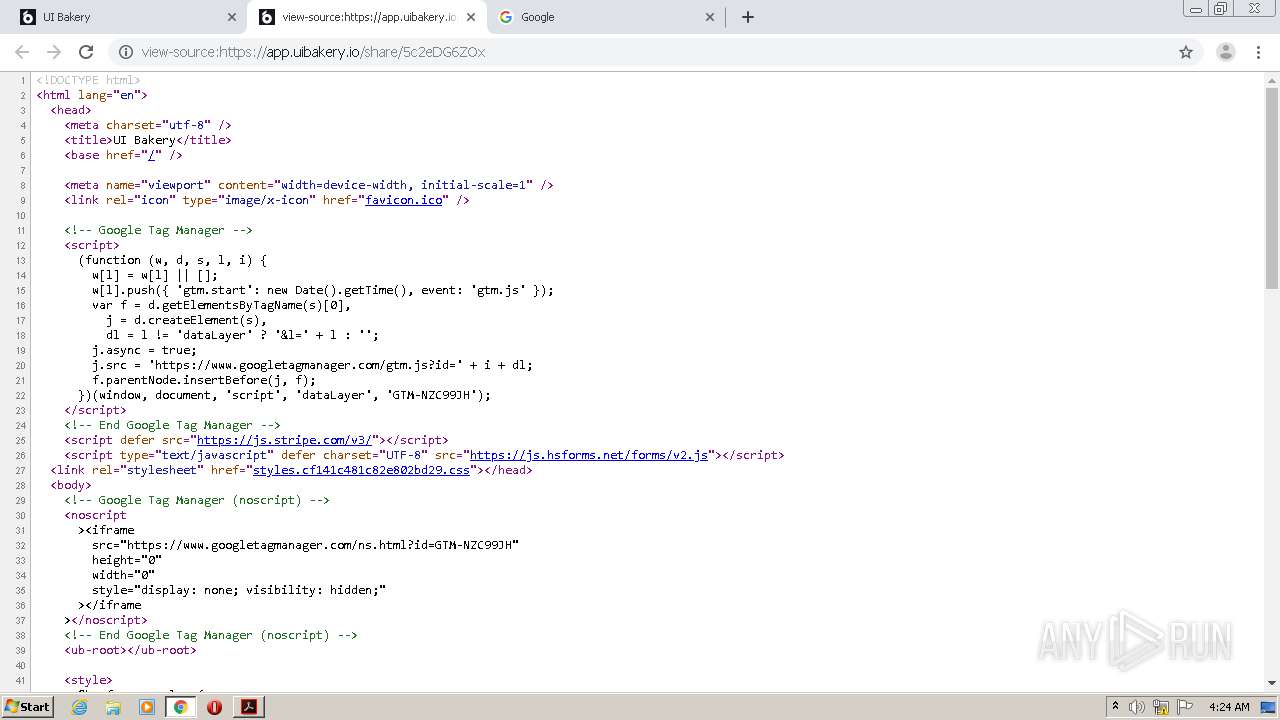
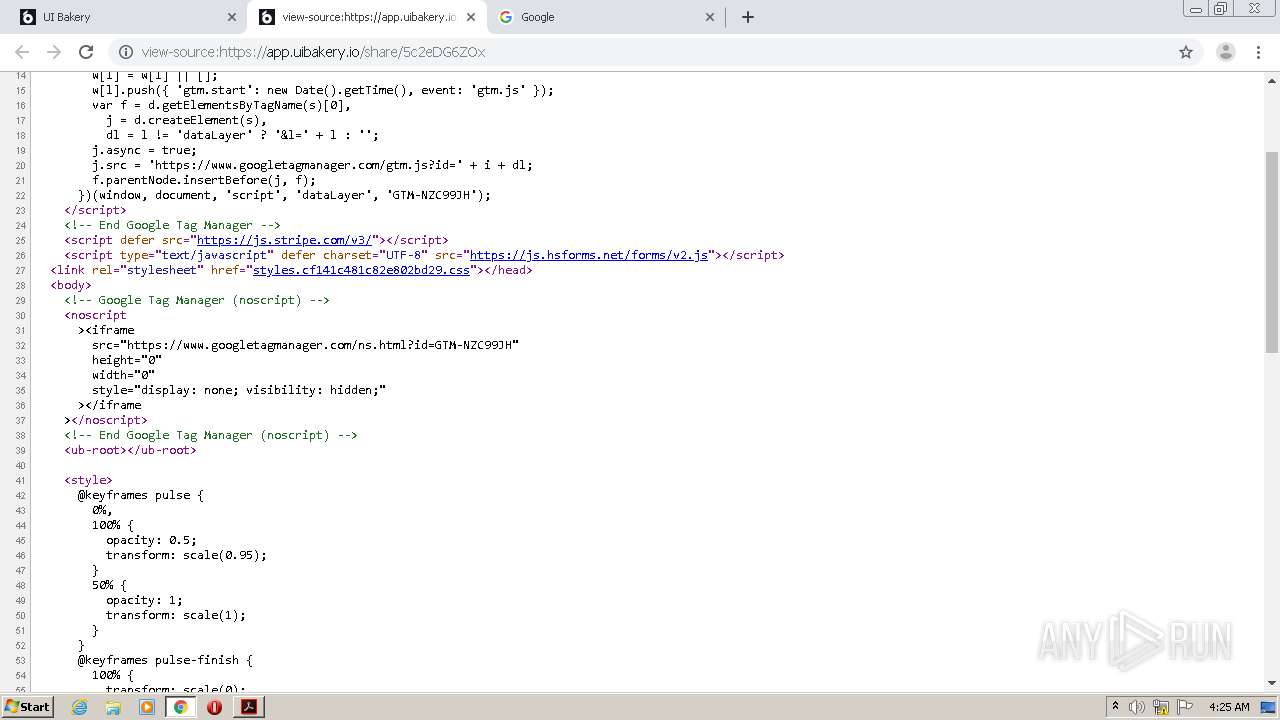
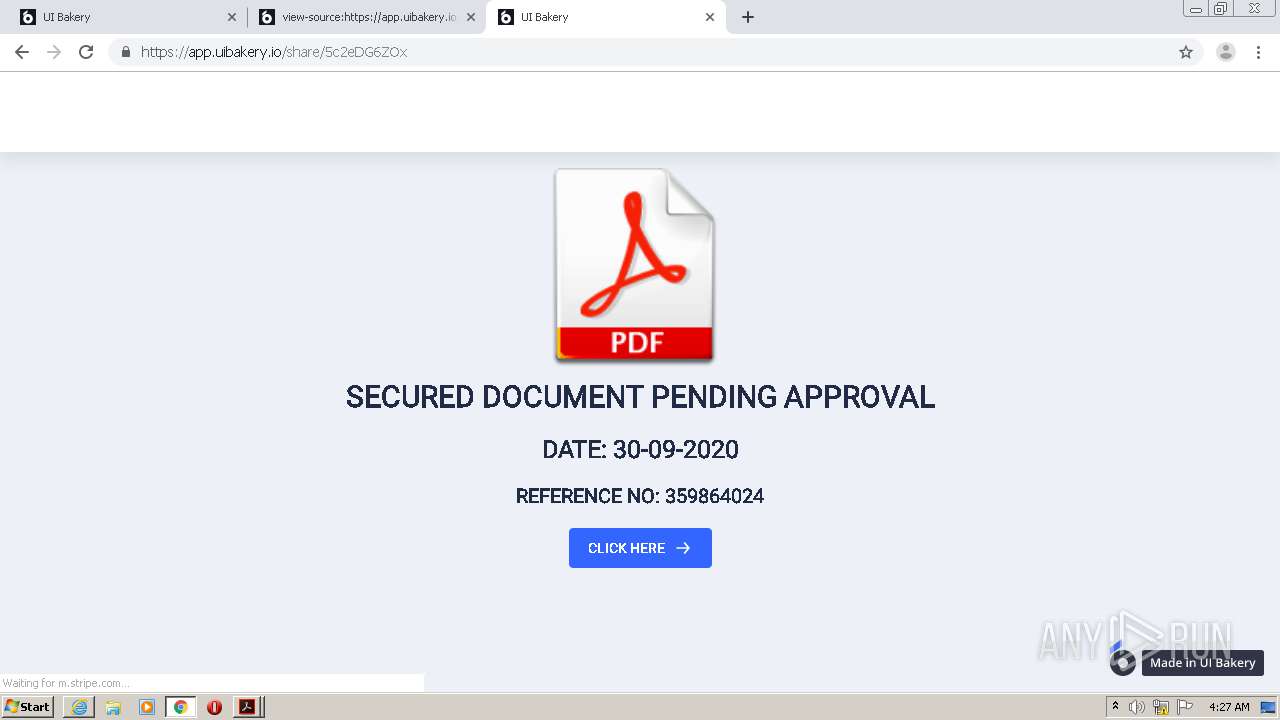
2296 | iexplore.exe | 104.24.99.226:443 | app.uibakery.io | Cloudflare Inc | US | suspicious |
2296 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2296 | iexplore.exe | 151.101.0.176:443 | js.stripe.com | Fastly | US | suspicious |
2296 | iexplore.exe | 104.17.185.73:443 | js.hsforms.net | Cloudflare Inc | US | shared |
2296 | iexplore.exe | 142.250.74.195:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
2296 | iexplore.exe | 216.58.205.234:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2296 | iexplore.exe | 143.204.208.75:443 | cdn.amplitude.com | — | US | suspicious |
2296 | iexplore.exe | 143.204.208.165:80 | o.ss2.us | — | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
app.uibakery.io |
| suspicious |
acroipm2.adobe.com |
| whitelisted |
armmf.adobe.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
js.stripe.com |
| shared |
js.hsforms.net |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
cdn.amplitude.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3960 | opera.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
3960 | opera.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
3960 | opera.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |