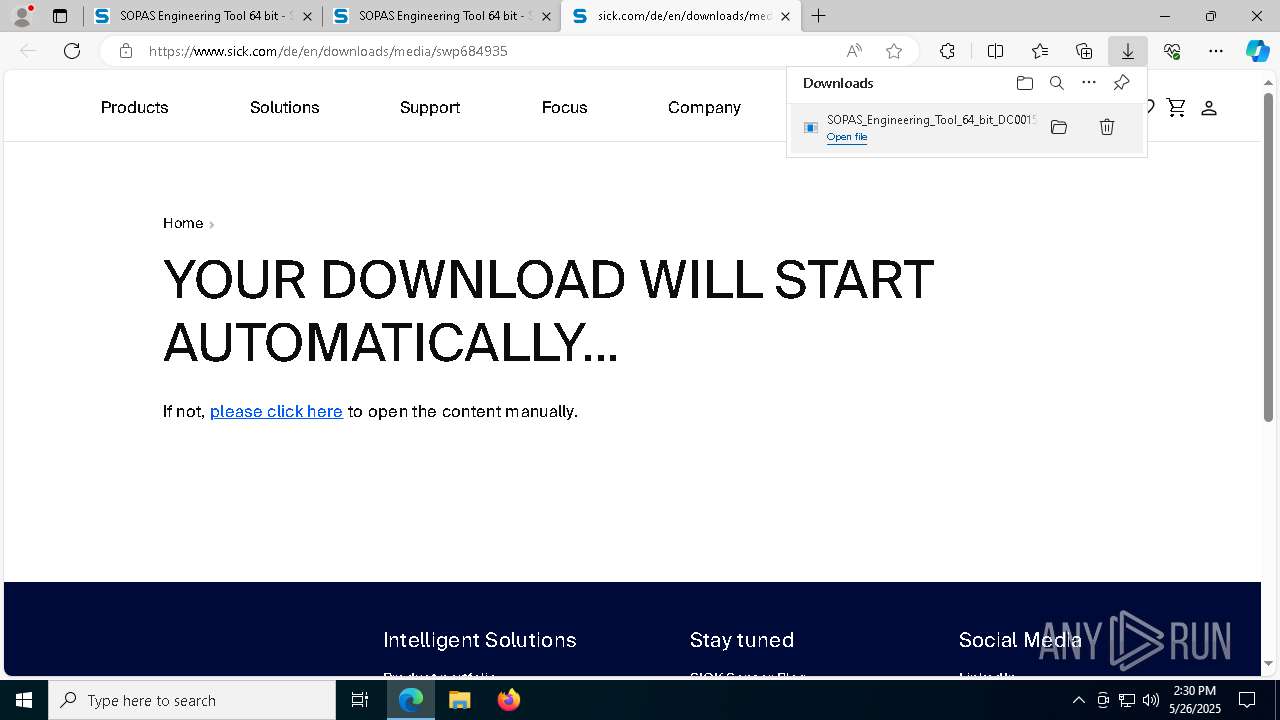
| URL: | https://www.sick.com/gb/en/catalog/products/digital-services-and-software/engineering-tools/sopas-et/sopas-engineering-tool-64-bit/p/p684930?tab=detail#technical-details |
| Full analysis: | https://app.any.run/tasks/653cc35a-2704-48ce-84fc-d427660e8edb |
| Verdict: | Malicious activity |
| Analysis date: | May 26, 2025, 14:27:59 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 21057277D4BCDD0040DF0A468D58CFFF |
| SHA1: | 68DCFDDEFA38949E81C7E1EF0B52B7B1F49D3AEE |
| SHA256: | AA47CF7B89895C22113F340606CAAB907CD92D97EE25DB8F6B5ED5C1F7B06F8E |
| SSDEEP: | 3:N8DSLJdUbxKChTRWaMPRe6rKD0wfnN2ARKN2ALP0jfERIs0O3nwiHYBAvJXawJK:2OLkNXRWHPReqKAOngzN2Z74IdOlYBAI |
MALICIOUS
Checks whether a specified folder exists (SCRIPT)
- msiexec.exe (PID: 3300)
Changes the autorun value in the registry
- SOPAS_Engineering_Tool_64_bit_DC0015791.EXE (PID: 7144)
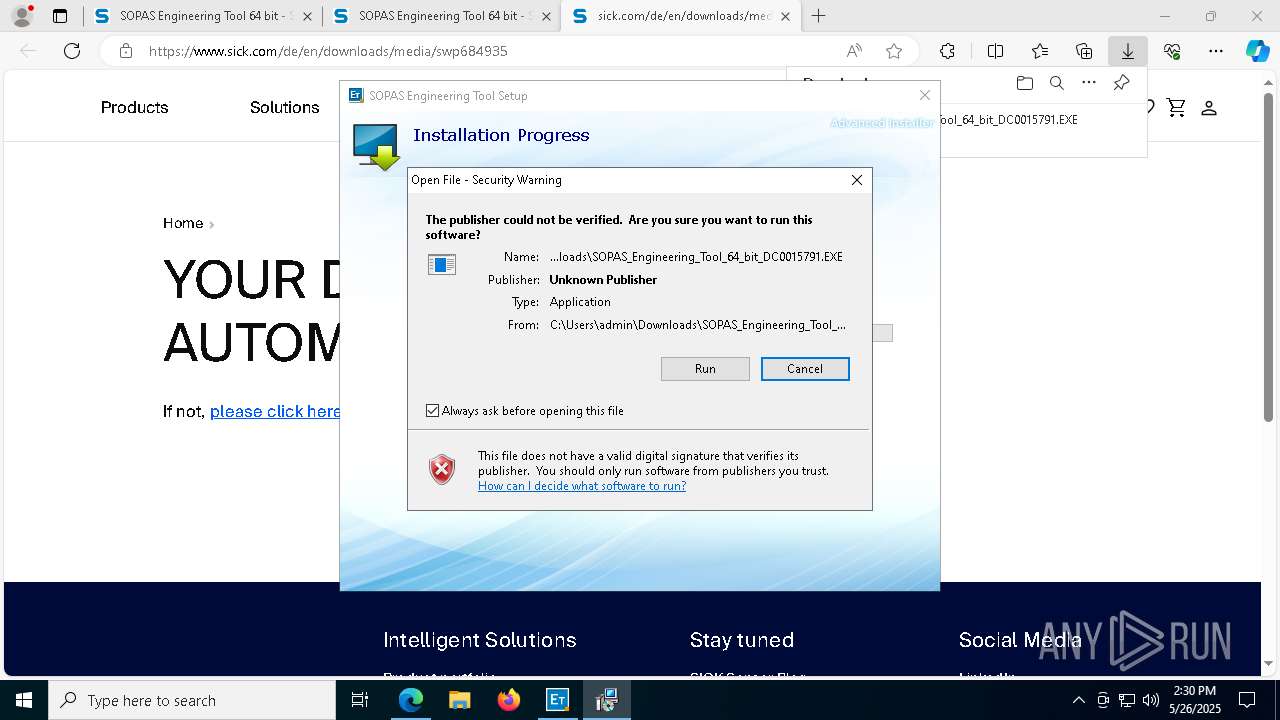
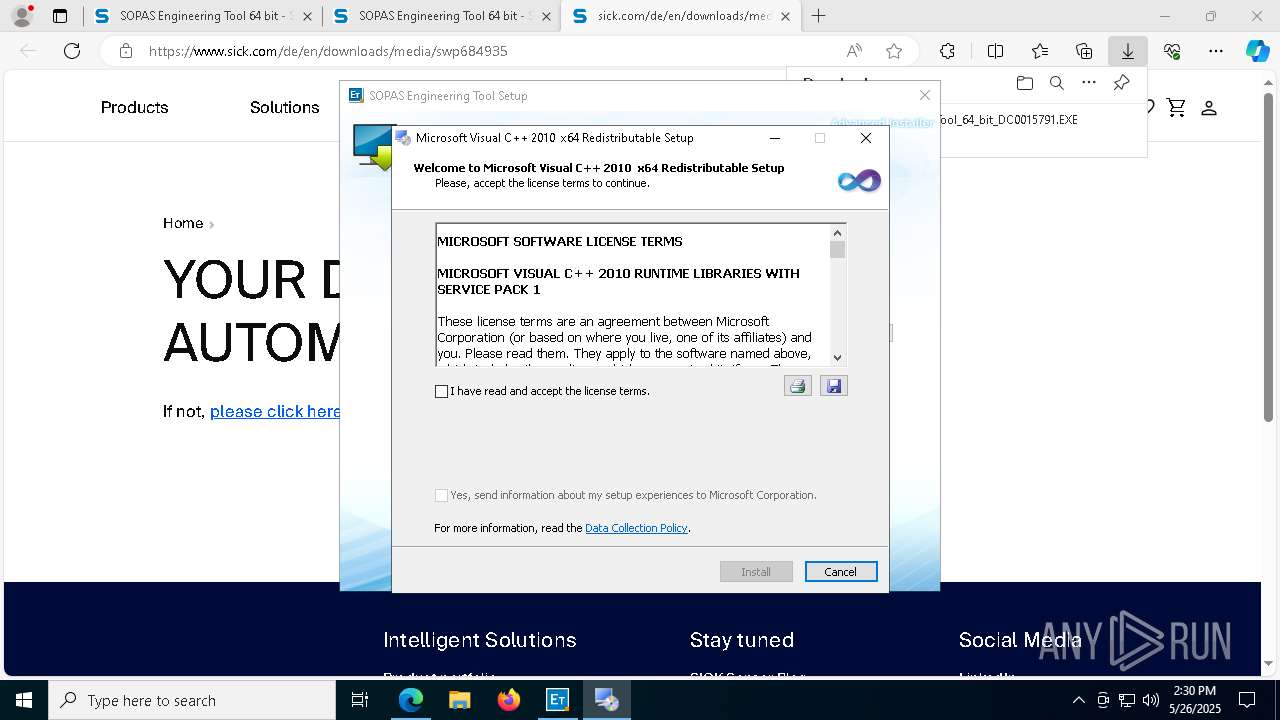
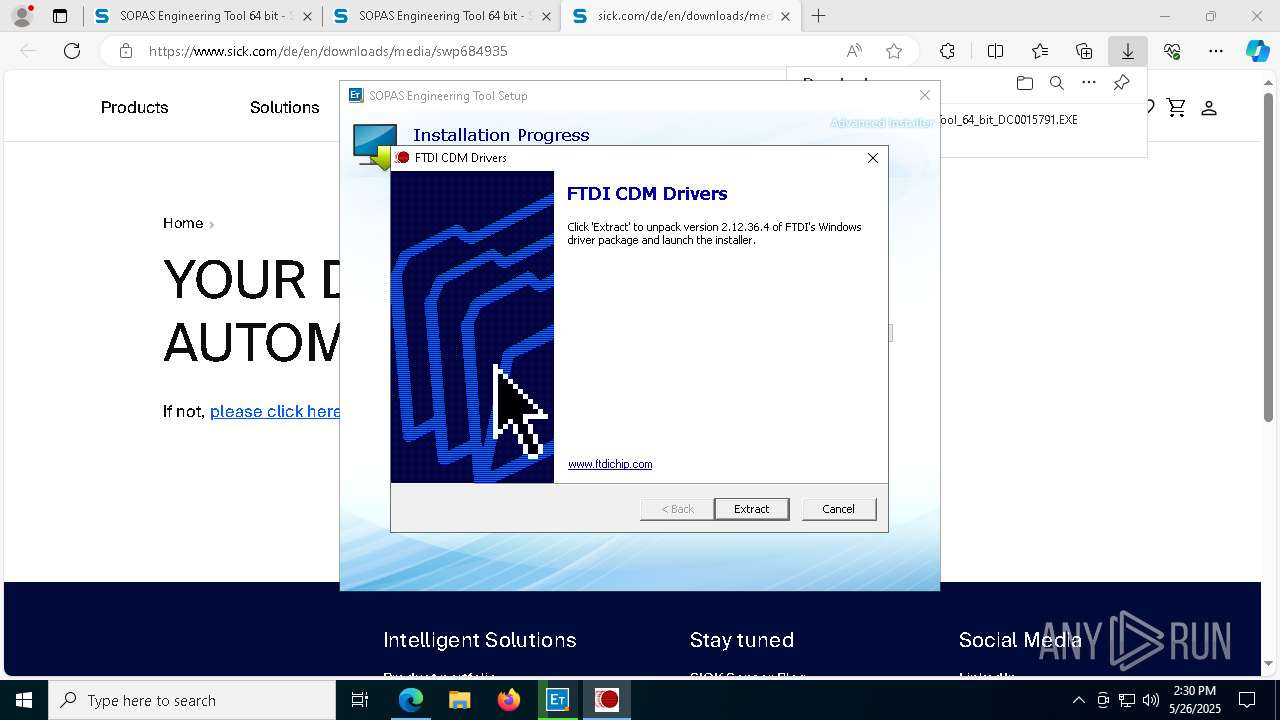
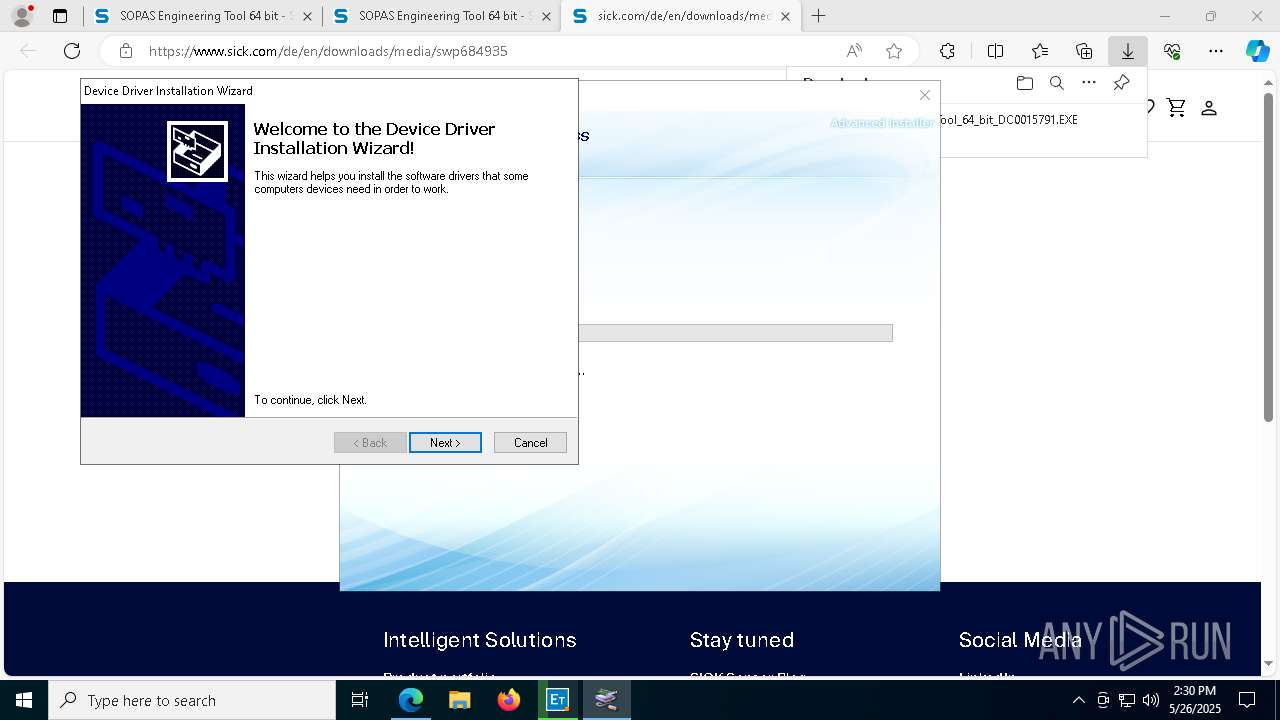
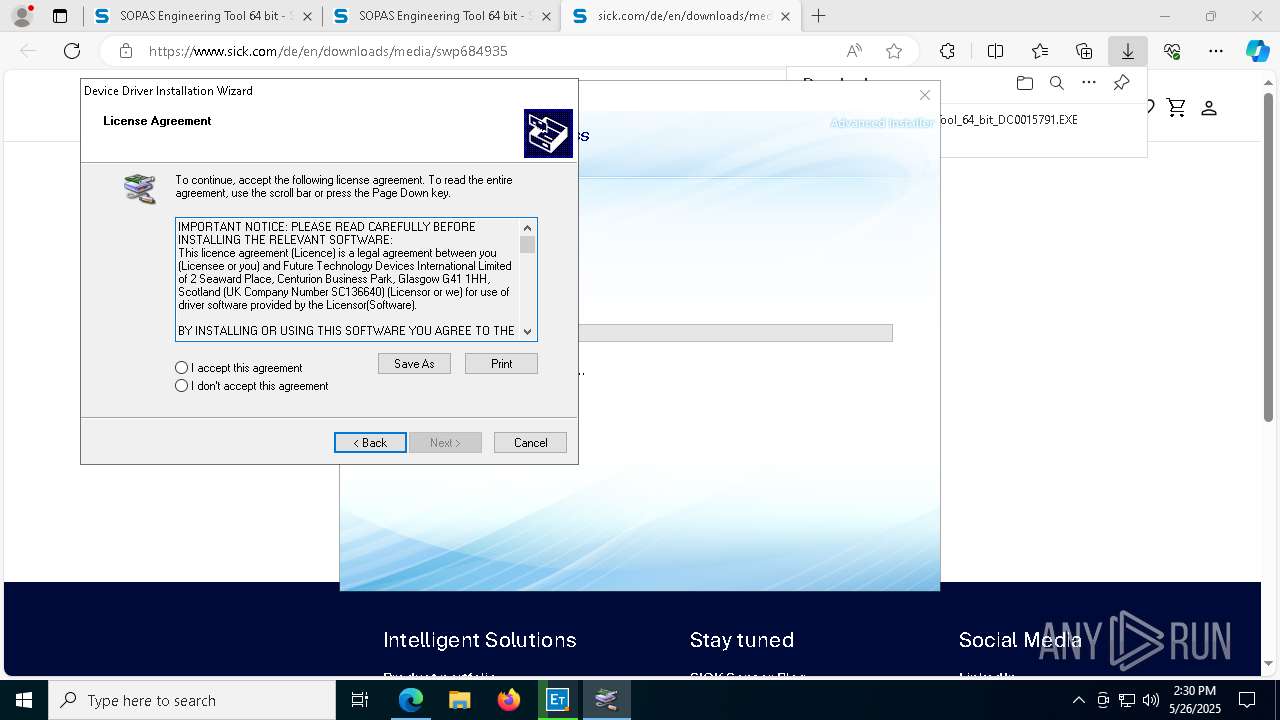
Executing a file with an untrusted certificate
- Setup.exe (PID: 6032)
- CDM212364_Setup.exe (PID: 872)
- dp-chooser.exe (PID: 2516)
- dpinst-amd64.exe (PID: 6656)
SUSPICIOUS
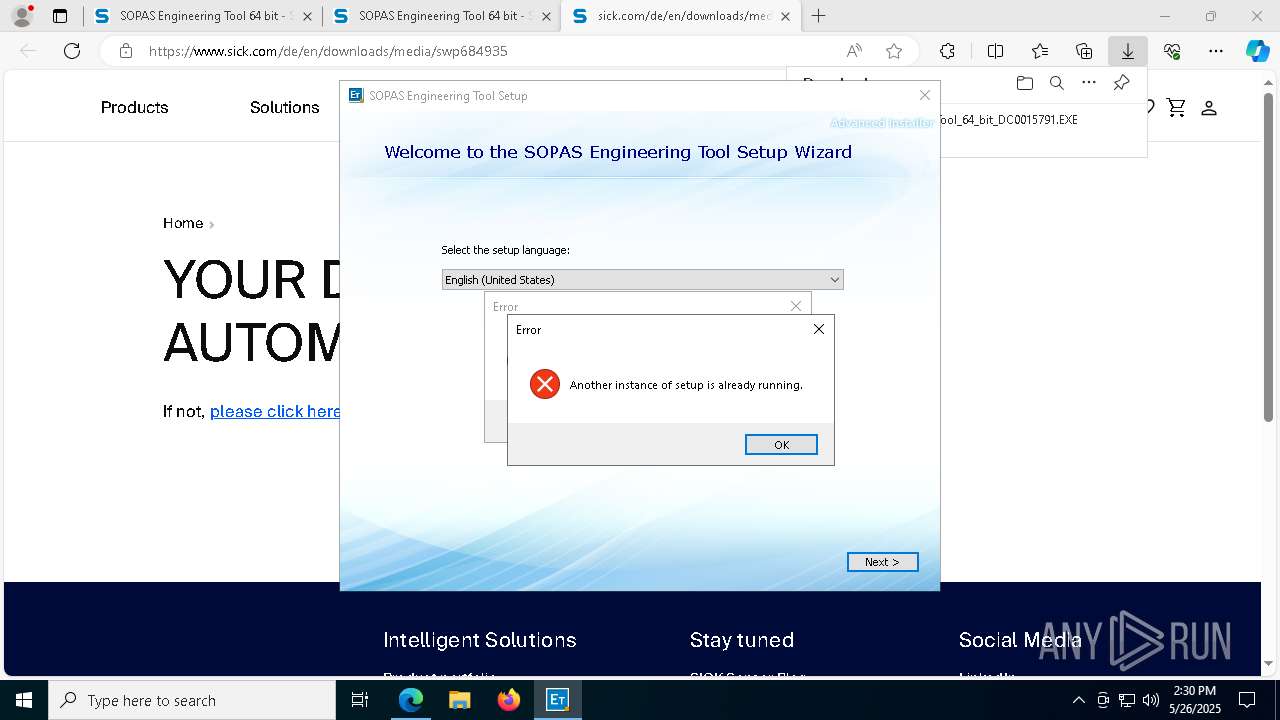
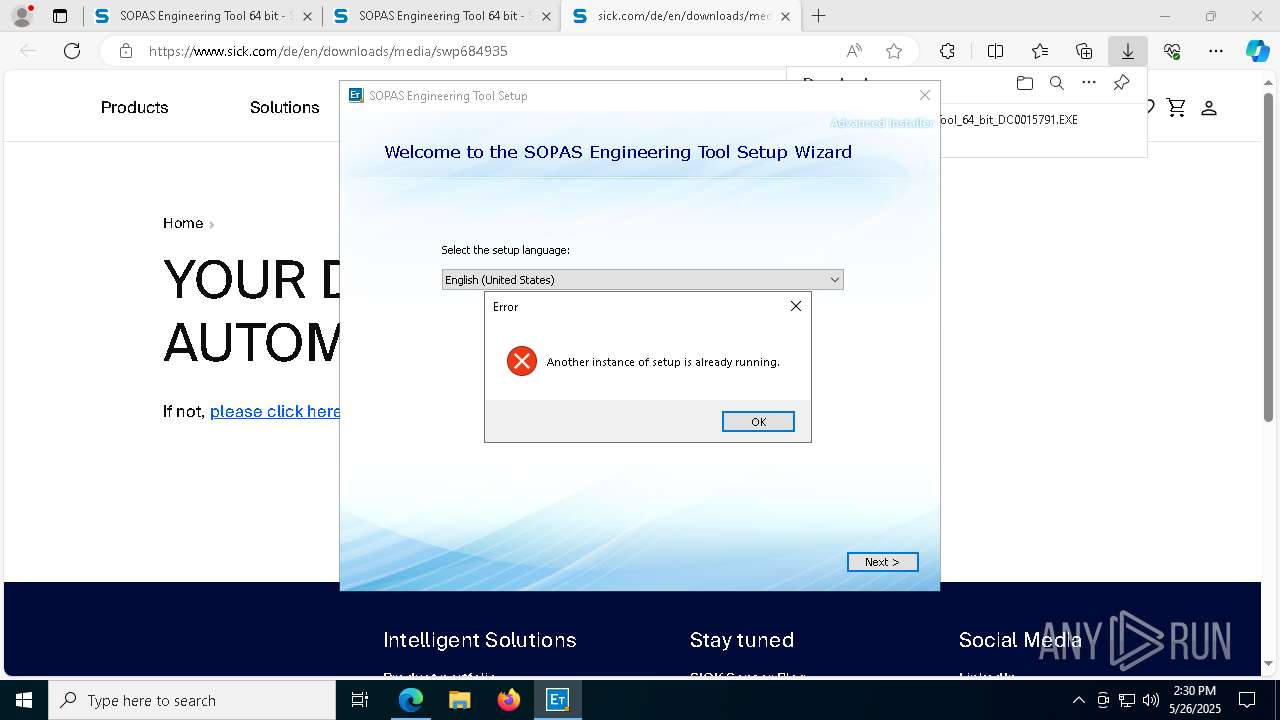
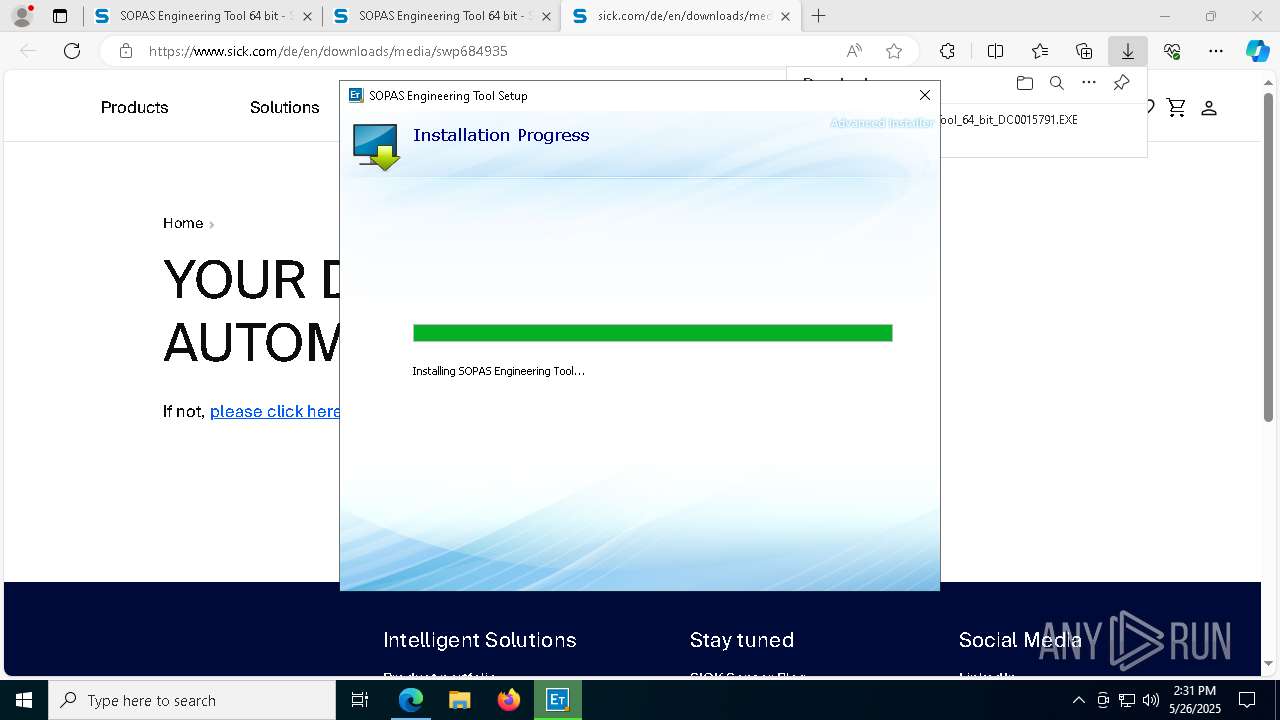
ADVANCEDINSTALLER mutex has been found
- SOPAS_Engineering_Tool_64_bit_DC0015791.EXE (PID: 7144)
- SOPAS_Engineering_Tool_64_bit_DC0015791.EXE (PID: 1096)
- SOPAS_Engineering_Tool_64_bit_DC0015791.EXE (PID: 8160)
Reads the Windows owner or organization settings
- SOPAS_Engineering_Tool_64_bit_DC0015791.EXE (PID: 7144)
- msiexec.exe (PID: 6384)
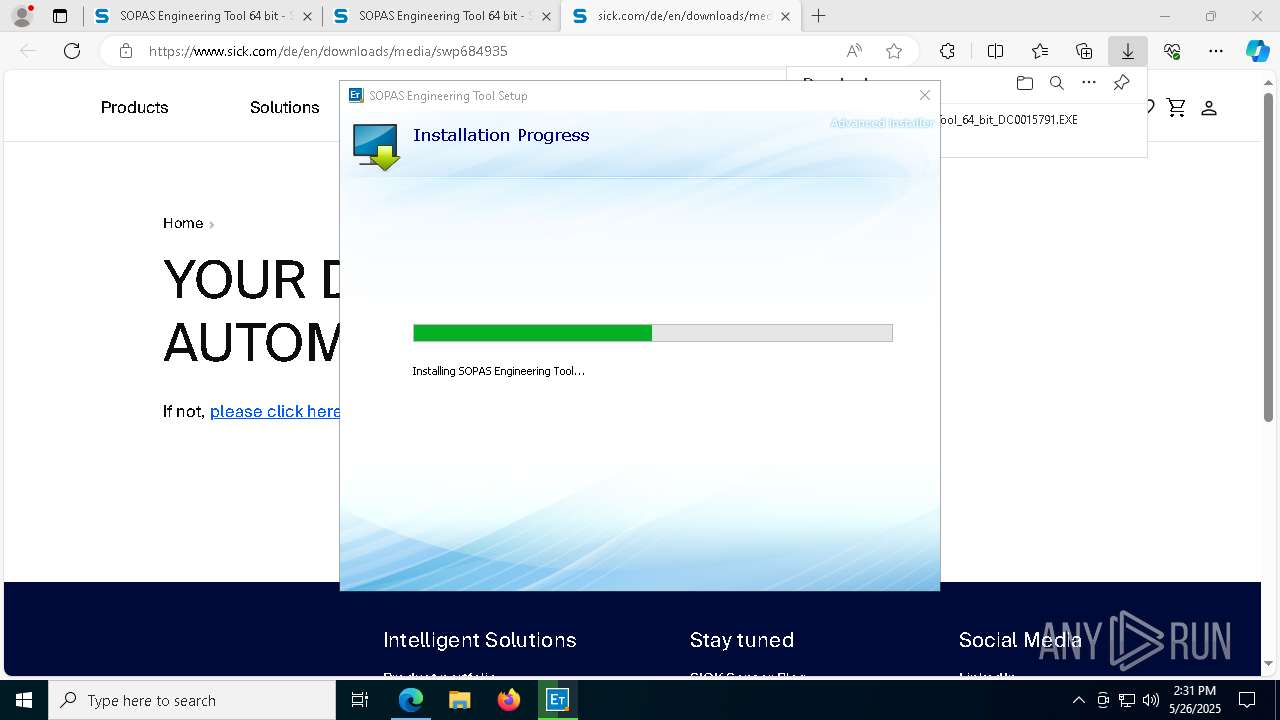
Process drops legitimate windows executable
- SOPAS_Engineering_Tool_64_bit_DC0015791.EXE (PID: 7144)
- msiexec.exe (PID: 3300)
- SOPAS_Engineering_Tool_64_bit_DC0015791.EXE (PID: 2772)
- vcredist_x64.exe (PID: 7284)
- msiexec.exe (PID: 6384)
- CDM212364_Setup.exe (PID: 872)
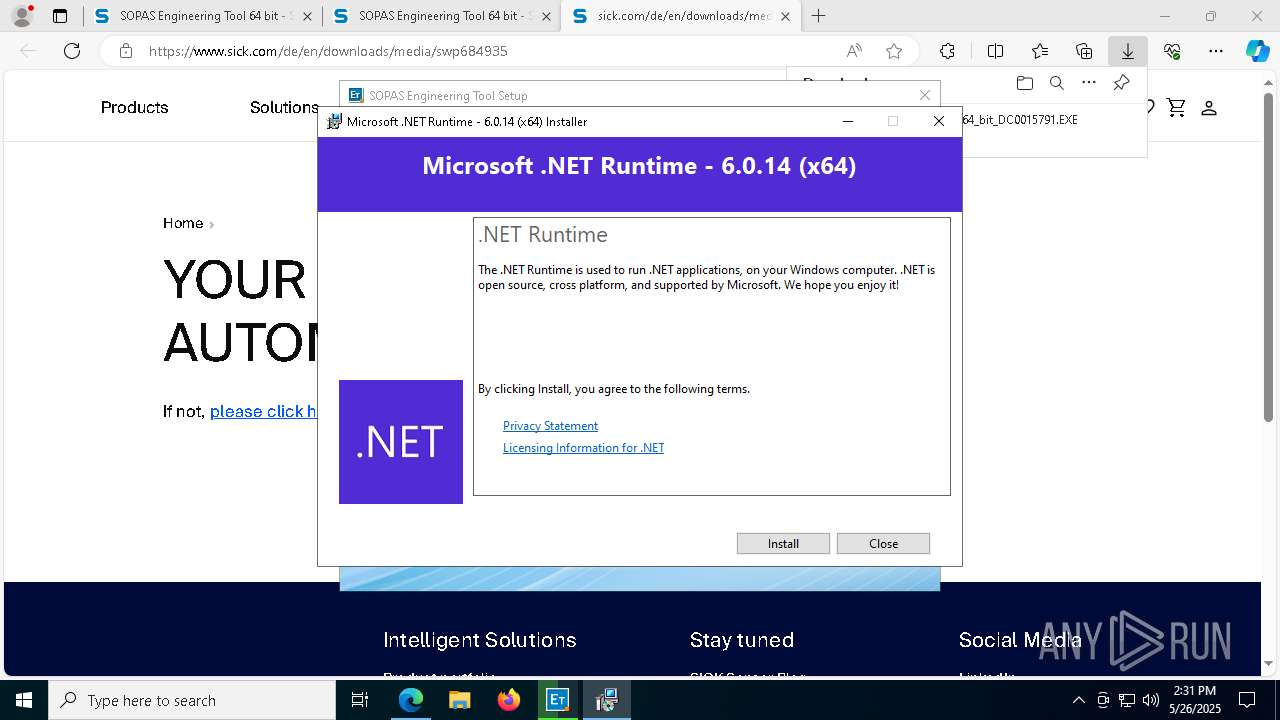
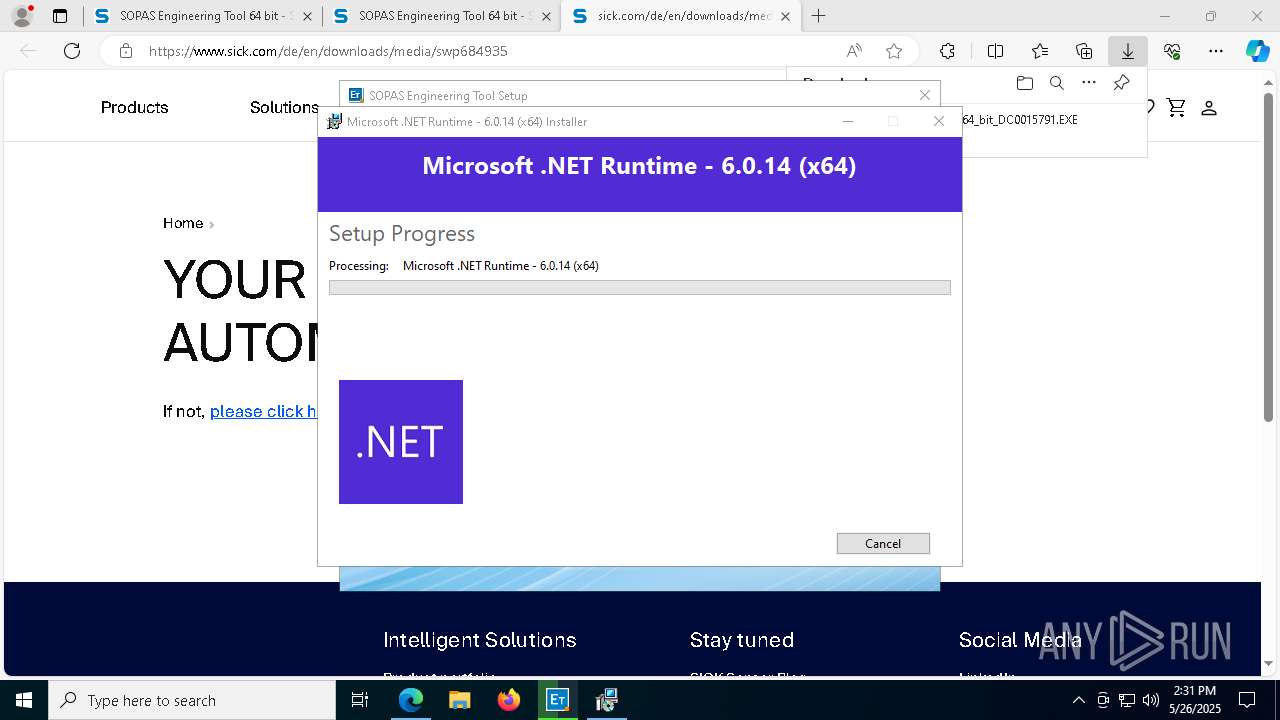
- dotnet-runtime-6.0.14-win-x64.exe (PID: 5416)
- dotnet-runtime-6.0.14-win-x64.exe (PID: 5176)
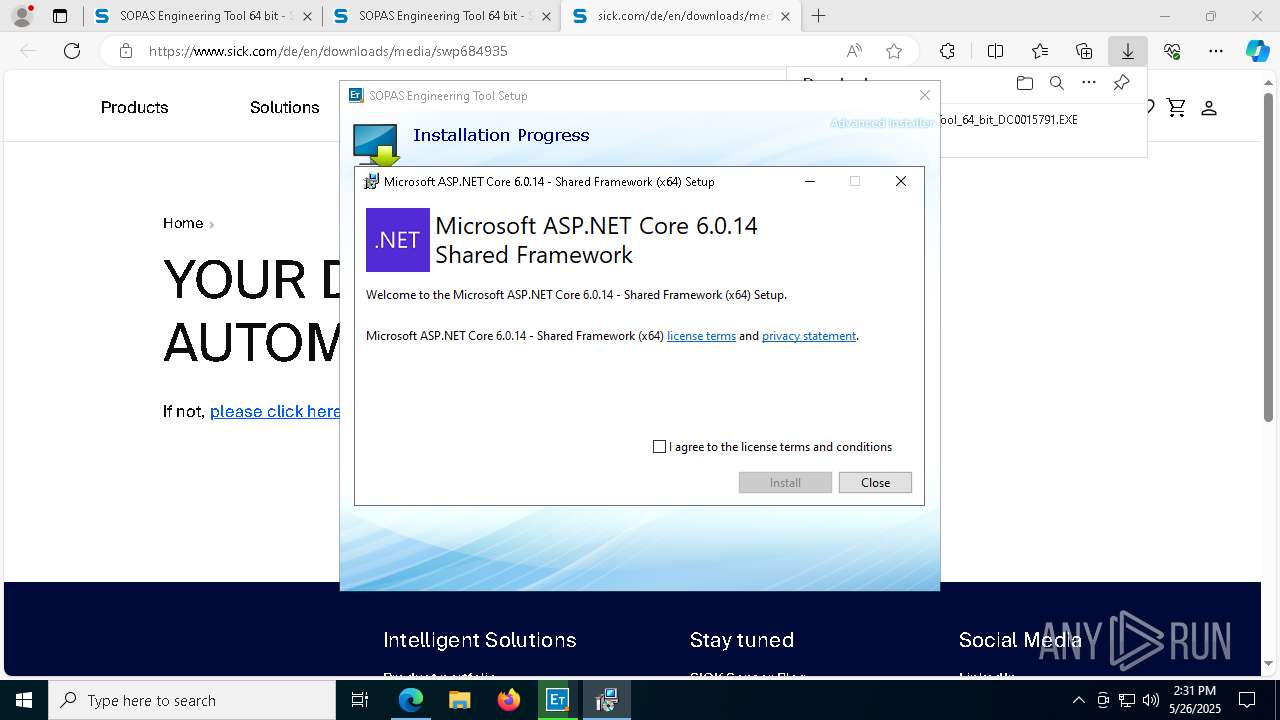
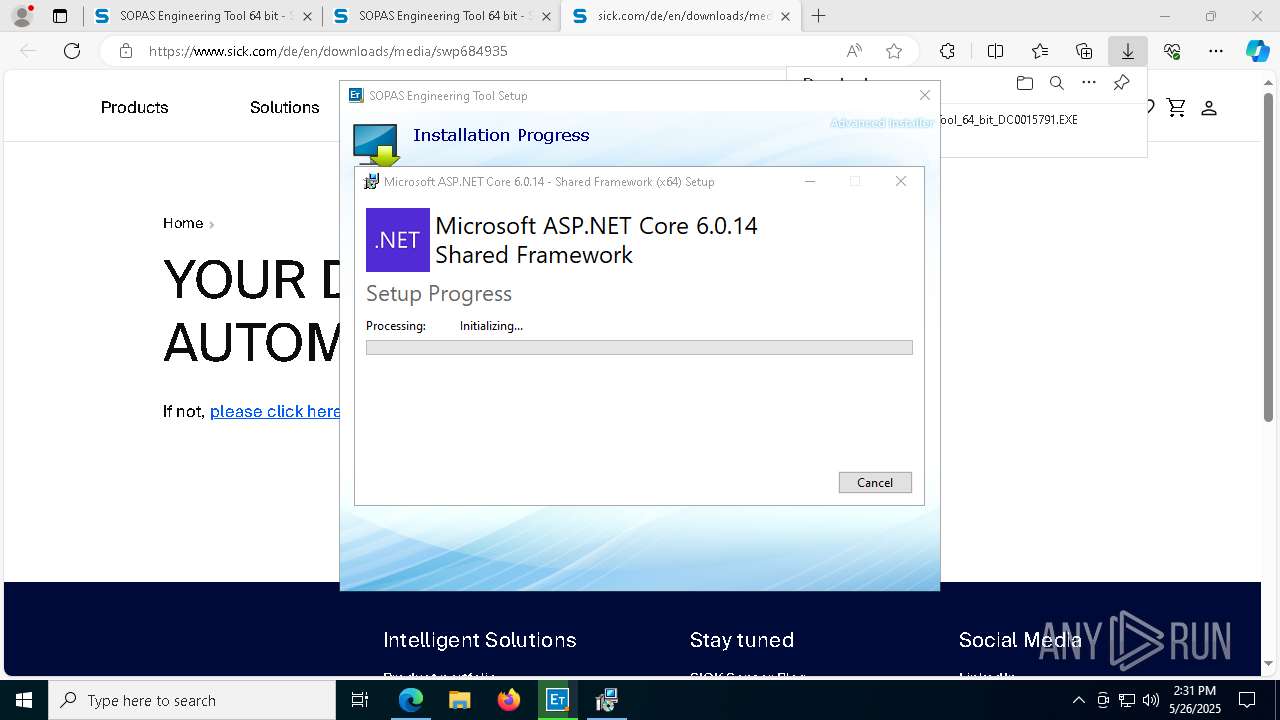
- aspnetcore-runtime-6.0.14-win-x64.exe (PID: 6900)
- aspnetcore-runtime-6.0.14-win-x64.exe (PID: 5968)
- aspnetcore-runtime-6.0.14-win-x64.exe (PID: 5772)
- dotnet-runtime-6.0.14-win-x64.exe (PID: 660)
- msiexec.exe (PID: 1852)
- SOPAS_Engineering_Tool_64_bit_DC0015791.EXE (PID: 2560)
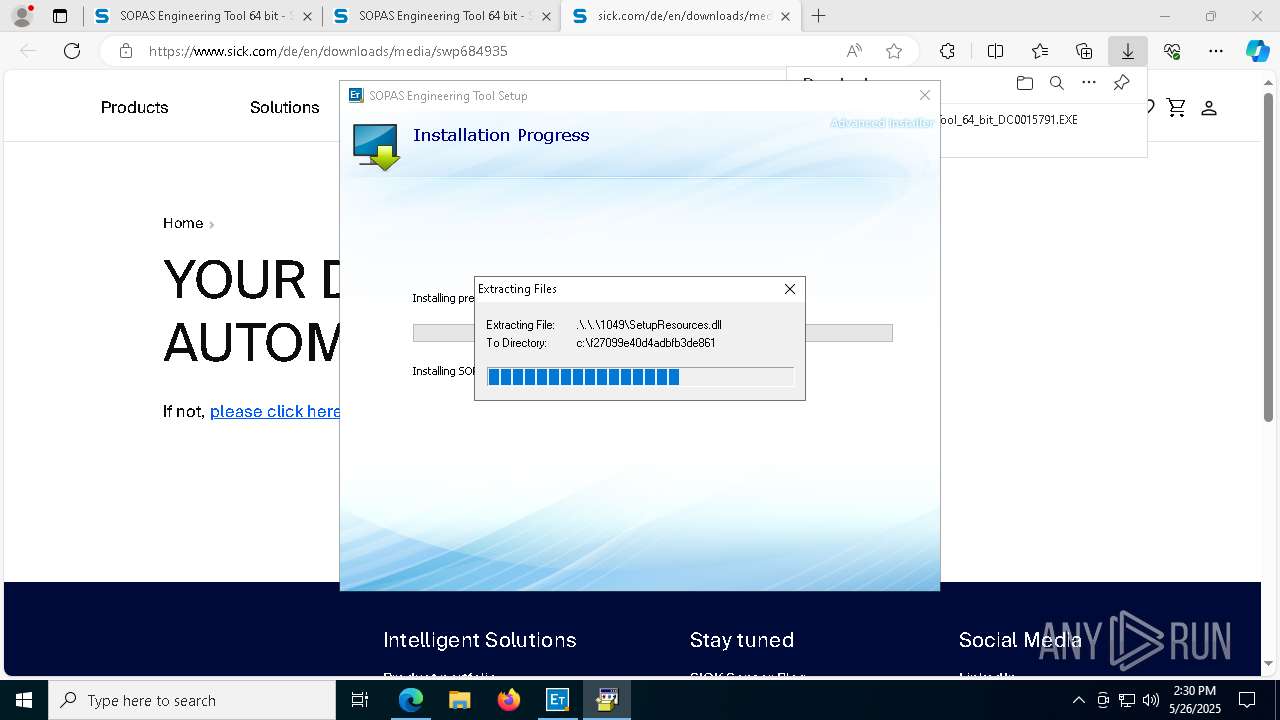
Executable content was dropped or overwritten
- SOPAS_Engineering_Tool_64_bit_DC0015791.EXE (PID: 7144)
- SOPAS_Engineering_Tool_64_bit_DC0015791.EXE (PID: 2772)
- vcredist_x64.exe (PID: 7284)
- CDM212364_Setup.exe (PID: 872)
- dpinst-amd64.exe (PID: 6656)
- drvinst.exe (PID: 5044)
- dotnet-runtime-6.0.14-win-x64.exe (PID: 5416)
- dotnet-runtime-6.0.14-win-x64.exe (PID: 5176)
- drvinst.exe (PID: 456)
- aspnetcore-runtime-6.0.14-win-x64.exe (PID: 5968)
- aspnetcore-runtime-6.0.14-win-x64.exe (PID: 5772)
- dotnet-runtime-6.0.14-win-x64.exe (PID: 660)
- SOPAS_Engineering_Tool_64_bit_DC0015791.EXE (PID: 2560)
- aspnetcore-runtime-6.0.14-win-x64.exe (PID: 6900)
The process drops C-runtime libraries
- SOPAS_Engineering_Tool_64_bit_DC0015791.EXE (PID: 7144)
- msiexec.exe (PID: 6384)
Reads security settings of Internet Explorer
- msiexec.exe (PID: 3300)
- SOPAS_Engineering_Tool_64_bit_DC0015791.EXE (PID: 7144)
- Setup.exe (PID: 6032)
There is functionality for taking screenshot (YARA)
- SOPAS_Engineering_Tool_64_bit_DC0015791.EXE (PID: 7144)
- CDM212364_Setup.exe (PID: 872)
Reads Internet Explorer settings
- SOPAS_Engineering_Tool_64_bit_DC0015791.EXE (PID: 7144)
Creates FileSystem object to access computer's file system (SCRIPT)
- msiexec.exe (PID: 3300)
Detects AdvancedInstaller (YARA)
- SOPAS_Engineering_Tool_64_bit_DC0015791.EXE (PID: 7144)
Creates file in the systems drive root
- vcredist_x64.exe (PID: 7284)
Searches for installed software
- MSI403B.tmp (PID: 2392)
Starts application with an unusual extension
- SOPAS_Engineering_Tool_64_bit_DC0015791.EXE (PID: 7144)
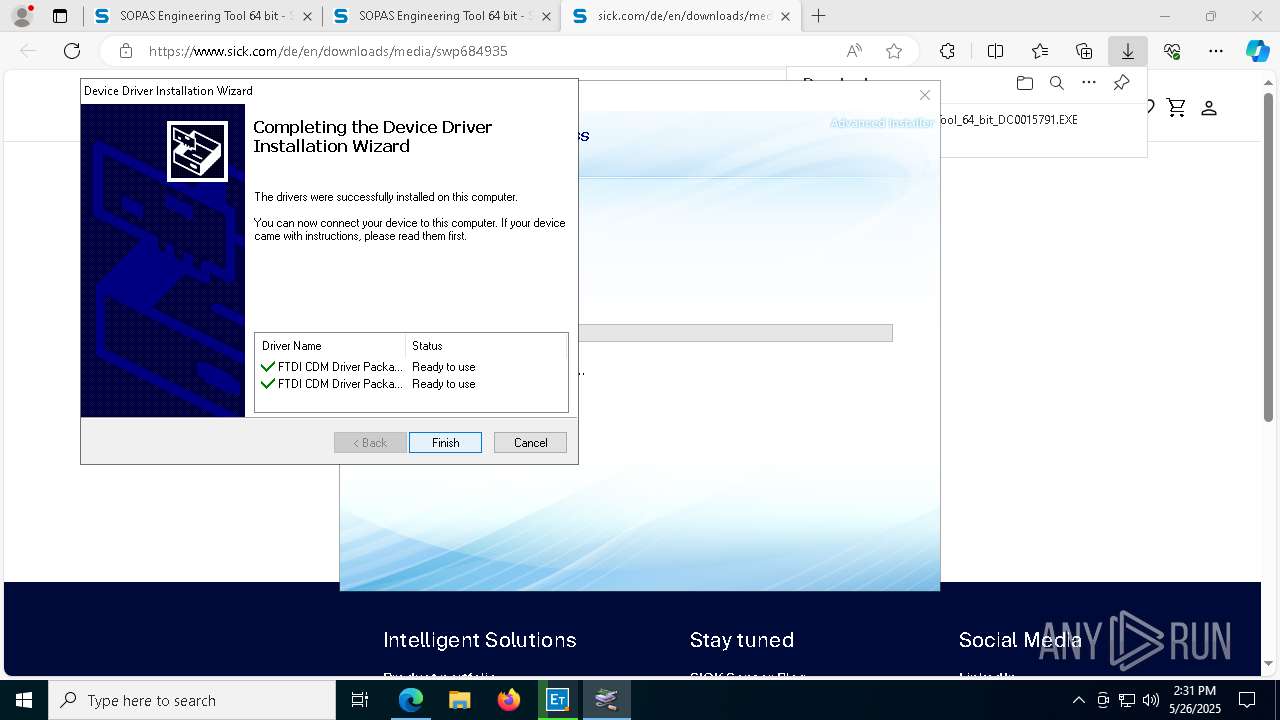
Drops a system driver (possible attempt to evade defenses)
- CDM212364_Setup.exe (PID: 872)
- drvinst.exe (PID: 456)
- dpinst-amd64.exe (PID: 6656)
- drvinst.exe (PID: 5044)
Starts a Microsoft application from unusual location
- dpinst-amd64.exe (PID: 6656)
- dotnet-runtime-6.0.14-win-x64.exe (PID: 5176)
- dotnet-runtime-6.0.14-win-x64.exe (PID: 660)
- aspnetcore-runtime-6.0.14-win-x64.exe (PID: 5968)
- aspnetcore-runtime-6.0.14-win-x64.exe (PID: 5772)
Creates files in the driver directory
- drvinst.exe (PID: 456)
Starts itself from another location
- dotnet-runtime-6.0.14-win-x64.exe (PID: 5176)
- aspnetcore-runtime-6.0.14-win-x64.exe (PID: 5968)
Executes as Windows Service
- VSSVC.exe (PID: 5376)
Application launched itself
- SOPAS_Engineering_Tool_64_bit_DC0015791.EXE (PID: 7144)
INFO
Application launched itself
- msedge.exe (PID: 7480)
Reads the computer name
- identity_helper.exe (PID: 2096)
- SOPAS_Engineering_Tool_64_bit_DC0015791.EXE (PID: 7144)
- msiexec.exe (PID: 6384)
- msiexec.exe (PID: 3300)
- SOPAS_Engineering_Tool_64_bit_DC0015791.EXE (PID: 1096)
- SOPAS_Engineering_Tool_64_bit_DC0015791.EXE (PID: 8160)
- vcredist_x64.exe (PID: 7284)
- Setup.exe (PID: 6032)
- CDM212364_Setup.exe (PID: 872)
- dpinst-amd64.exe (PID: 6656)
Reads Environment values
- identity_helper.exe (PID: 2096)
- SOPAS_Engineering_Tool_64_bit_DC0015791.EXE (PID: 7144)
- msiexec.exe (PID: 3300)
Checks supported languages
- identity_helper.exe (PID: 2096)
- msiexec.exe (PID: 3300)
- SOPAS_Engineering_Tool_64_bit_DC0015791.EXE (PID: 7144)
- msiexec.exe (PID: 6384)
- SOPAS_Engineering_Tool_64_bit_DC0015791.EXE (PID: 1096)
- SOPAS_Engineering_Tool_64_bit_DC0015791.EXE (PID: 8160)
- ACSCB77.exe (PID: 2896)
- SOPAS_Engineering_Tool_64_bit_DC0015791.EXE (PID: 2772)
- vcredist_x64.exe (PID: 7284)
- Setup.exe (PID: 6032)
- MSI403B.tmp (PID: 2392)
- CDM212364_Setup.exe (PID: 872)
- dp-chooser.exe (PID: 2516)
- dpinst-amd64.exe (PID: 6656)
- drvinst.exe (PID: 456)
Creates files or folders in the user directory
- SOPAS_Engineering_Tool_64_bit_DC0015791.EXE (PID: 7144)
- SOPAS_Engineering_Tool_64_bit_DC0015791.EXE (PID: 2772)
- msiexec.exe (PID: 6384)
Launch of the file from Downloads directory
- msedge.exe (PID: 8096)
Executable content was dropped or overwritten
- msedge.exe (PID: 7480)
- msiexec.exe (PID: 3300)
- msedge.exe (PID: 5892)
- msiexec.exe (PID: 6384)
- msiexec.exe (PID: 1852)
Checks proxy server information
- slui.exe (PID: 4728)
Reads the software policy settings
- slui.exe (PID: 1764)
- slui.exe (PID: 4728)
- Setup.exe (PID: 6032)
- msiexec.exe (PID: 6384)
- drvinst.exe (PID: 456)
The sample compiled with english language support
- SOPAS_Engineering_Tool_64_bit_DC0015791.EXE (PID: 7144)
- msiexec.exe (PID: 3300)
- msedge.exe (PID: 5892)
- SOPAS_Engineering_Tool_64_bit_DC0015791.EXE (PID: 2772)
- vcredist_x64.exe (PID: 7284)
- msiexec.exe (PID: 6384)
- CDM212364_Setup.exe (PID: 872)
- dpinst-amd64.exe (PID: 6656)
- dotnet-runtime-6.0.14-win-x64.exe (PID: 5416)
- drvinst.exe (PID: 5044)
- dotnet-runtime-6.0.14-win-x64.exe (PID: 5176)
- drvinst.exe (PID: 456)
- aspnetcore-runtime-6.0.14-win-x64.exe (PID: 6900)
- aspnetcore-runtime-6.0.14-win-x64.exe (PID: 5968)
- aspnetcore-runtime-6.0.14-win-x64.exe (PID: 5772)
- dotnet-runtime-6.0.14-win-x64.exe (PID: 660)
- msiexec.exe (PID: 1852)
- SOPAS_Engineering_Tool_64_bit_DC0015791.EXE (PID: 2560)
Create files in a temporary directory
- SOPAS_Engineering_Tool_64_bit_DC0015791.EXE (PID: 7144)
- msiexec.exe (PID: 3300)
- Setup.exe (PID: 6032)
- CDM212364_Setup.exe (PID: 872)
- dpinst-amd64.exe (PID: 6656)
Process checks computer location settings
- msiexec.exe (PID: 3300)
- SOPAS_Engineering_Tool_64_bit_DC0015791.EXE (PID: 7144)
Reads the machine GUID from the registry
- msiexec.exe (PID: 3300)
- vcredist_x64.exe (PID: 7284)
- Setup.exe (PID: 6032)
- msiexec.exe (PID: 6384)
- drvinst.exe (PID: 456)
Launch of the file from Registry key
- SOPAS_Engineering_Tool_64_bit_DC0015791.EXE (PID: 7144)
The sample compiled with chinese language support
- vcredist_x64.exe (PID: 7284)
- msiexec.exe (PID: 6384)
The sample compiled with korean language support
- vcredist_x64.exe (PID: 7284)
- msiexec.exe (PID: 6384)
The sample compiled with japanese language support
- vcredist_x64.exe (PID: 7284)
- msiexec.exe (PID: 6384)
The sample compiled with french language support
- vcredist_x64.exe (PID: 7284)
- msiexec.exe (PID: 6384)
The sample compiled with Italian language support
- vcredist_x64.exe (PID: 7284)
- msiexec.exe (PID: 6384)
The sample compiled with spanish language support
- vcredist_x64.exe (PID: 7284)
- msiexec.exe (PID: 6384)
The sample compiled with german language support
- vcredist_x64.exe (PID: 7284)
- msiexec.exe (PID: 6384)
- SOPAS_Engineering_Tool_64_bit_DC0015791.EXE (PID: 7144)
The sample compiled with russian language support
- vcredist_x64.exe (PID: 7284)
- msiexec.exe (PID: 6384)
Reads CPU info
- Setup.exe (PID: 6032)
Creates a software uninstall entry
- msiexec.exe (PID: 6384)
The sample compiled with arabic language support
- CDM212364_Setup.exe (PID: 872)
Manages system restore points
- SrTasks.exe (PID: 536)
- SrTasks.exe (PID: 6972)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
242
Monitored processes
97
Malicious processes
11
Suspicious processes
8
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 456 | DrvInst.exe "4" "0" "C:\Users\admin\AppData\Local\Temp\{7a6a16a1-e148-024b-86fc-d78e6f4df8c0}\ftdibus.inf" "9" "4a9ba6403" "00000000000001C4" "WinSta0\Default" "00000000000001E4" "208" "c:\users\admin\appdata\local\temp\ftdi-driver" | C:\Windows\System32\drvinst.exe | svchost.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 496 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_xpay_wallet.mojom.EdgeXPayWalletService --lang=en-US --service-sandbox-type=utility --no-appcompat-clear --mojo-platform-channel-handle=4372 --field-trial-handle=2288,i,16102125114016149917,5678369163941459983,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 536 | C:\WINDOWS\system32\srtasks.exe ExecuteScopeRestorePoint /WaitForRestorePoint:11 | C:\Windows\System32\SrTasks.exe | — | dllhost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft® Windows System Protection background tasks. Exit code: 2147942487 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 660 | "C:\WINDOWS\Temp\{0BFCCF0C-0A6A-44CB-A5F8-96F50D054411}\.be\dotnet-runtime-6.0.14-win-x64.exe" -q -burn.elevated BurnPipe.{DF47C07B-5E9D-4C30-A838-BD77EE8BC796} {7F9D2AA4-51BE-4EBD-9D75-2F2C1AC8C3F4} 5176 | C:\Windows\Temp\{0BFCCF0C-0A6A-44CB-A5F8-96F50D054411}\.be\dotnet-runtime-6.0.14-win-x64.exe | dotnet-runtime-6.0.14-win-x64.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft .NET Runtime - 6.0.14 (x64) Exit code: 0 Version: 6.0.14.32123 Modules
| |||||||||||||||
| 720 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_search_indexer.mojom.SearchIndexerInterfaceBroker --lang=en-US --service-sandbox-type=search_indexer --message-loop-type-ui --no-appcompat-clear --mojo-platform-channel-handle=5440 --field-trial-handle=2288,i,16102125114016149917,5678369163941459983,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 736 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_collections.mojom.CollectionsDataManager --lang=en-US --service-sandbox-type=collections --no-appcompat-clear --mojo-platform-channel-handle=6576 --field-trial-handle=2288,i,16102125114016149917,5678369163941459983,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 872 | "C:\Users\admin\AppData\Roaming\SICK AG\SOPAS Engineering Tool\prerequisites\FTDI Drivers\CDM212364_Setup.exe" | C:\Users\admin\AppData\Roaming\SICK AG\SOPAS Engineering Tool\prerequisites\FTDI Drivers\CDM212364_Setup.exe | SOPAS_Engineering_Tool_64_bit_DC0015791.EXE | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 1 Modules
| |||||||||||||||
| 1072 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5756 --field-trial-handle=2288,i,16102125114016149917,5678369163941459983,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1072 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=7124 --field-trial-handle=2288,i,16102125114016149917,5678369163941459983,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1096 | "C:\Users\admin\Downloads\SOPAS_Engineering_Tool_64_bit_DC0015791.EXE" | C:\Users\admin\Downloads\SOPAS_Engineering_Tool_64_bit_DC0015791.EXE | msedge.exe | ||||||||||||
User: admin Company: SICK AG Integrity Level: HIGH Description: SOPAS Engineering Tool Installer Exit code: 0 Version: 5.4.1 Modules
| |||||||||||||||
Total events
35 278
Read events
33 145
Write events
2 030
Delete events
103
Modification events
| (PID) Process: | (7480) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (7480) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (7480) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (7480) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (7480) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 653C110AA1942F00 | |||
| (PID) Process: | (7480) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 0D401B0AA1942F00 | |||
| (PID) Process: | (7480) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\524974 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {71E5914C-19A1-4C11-88F8-28783F5970CC} | |||
| (PID) Process: | (7480) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\524974 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {0E3768CB-754F-4127-8119-2FEB37680B74} | |||
| (PID) Process: | (7480) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\524974 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {CC706C0E-44F2-4A27-947E-CC0015CE3194} | |||
| (PID) Process: | (7480) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\524974 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {E92F5C2D-BA86-4367-B8E8-143E9DEC79EE} | |||
Executable files
864
Suspicious files
491
Text files
515
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7480 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10b7c9.TMP | — | |
MD5:— | SHA256:— | |||
| 7480 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7480 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10b7d8.TMP | — | |
MD5:— | SHA256:— | |||
| 7480 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10b7d8.TMP | — | |
MD5:— | SHA256:— | |||
| 7480 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7480 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7480 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10b7d8.TMP | — | |
MD5:— | SHA256:— | |||
| 7480 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7480 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10b807.TMP | — | |
MD5:— | SHA256:— | |||
| 7480 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
47
TCP/UDP connections
93
DNS requests
100
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.216.77.38:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
2644 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/785ebce5-e97a-4cfb-ae4e-1848681d5fca?P1=1748852895&P2=404&P3=2&P4=TXHxLLdo9KXrYsvKkflXbhuKM%2fg5M4xcxDE0G%2bn8Yj8WdwDZ5BUtArTXYLYQnPGThbZjV5CTWqL9o6xsxK5HOw%3d%3d | unknown | — | — | whitelisted |
7036 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7036 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
2644 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/785ebce5-e97a-4cfb-ae4e-1848681d5fca?P1=1748852895&P2=404&P3=2&P4=TXHxLLdo9KXrYsvKkflXbhuKM%2fg5M4xcxDE0G%2bn8Yj8WdwDZ5BUtArTXYLYQnPGThbZjV5CTWqL9o6xsxK5HOw%3d%3d | unknown | — | — | whitelisted |
2644 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/785ebce5-e97a-4cfb-ae4e-1848681d5fca?P1=1748852895&P2=404&P3=2&P4=TXHxLLdo9KXrYsvKkflXbhuKM%2fg5M4xcxDE0G%2bn8Yj8WdwDZ5BUtArTXYLYQnPGThbZjV5CTWqL9o6xsxK5HOw%3d%3d | unknown | — | — | whitelisted |
2644 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/785ebce5-e97a-4cfb-ae4e-1848681d5fca?P1=1748852895&P2=404&P3=2&P4=TXHxLLdo9KXrYsvKkflXbhuKM%2fg5M4xcxDE0G%2bn8Yj8WdwDZ5BUtArTXYLYQnPGThbZjV5CTWqL9o6xsxK5HOw%3d%3d | unknown | — | — | whitelisted |
2644 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/785ebce5-e97a-4cfb-ae4e-1848681d5fca?P1=1748852895&P2=404&P3=2&P4=TXHxLLdo9KXrYsvKkflXbhuKM%2fg5M4xcxDE0G%2bn8Yj8WdwDZ5BUtArTXYLYQnPGThbZjV5CTWqL9o6xsxK5HOw%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 23.216.77.38:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7480 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7760 | msedge.exe | 13.107.43.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7760 | msedge.exe | 92.123.104.34:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
7760 | msedge.exe | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7760 | msedge.exe | 13.107.246.45:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
www.sick.com |
| whitelisted |
business.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |