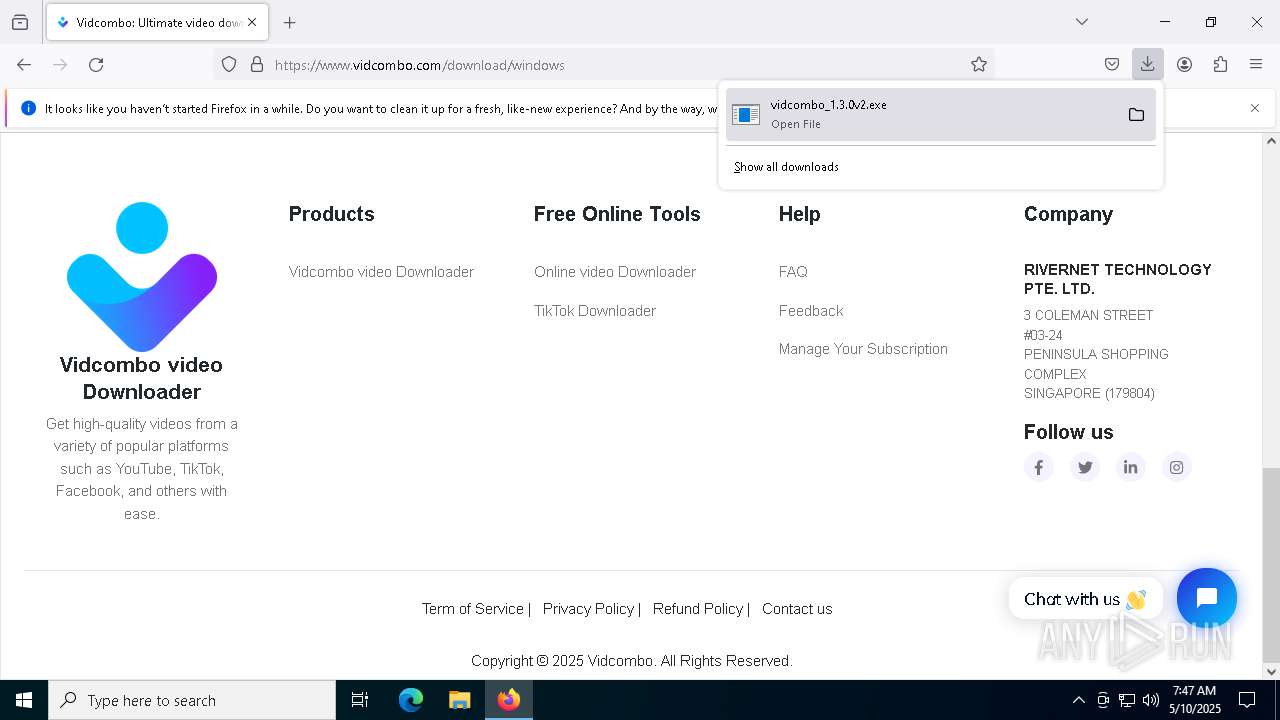
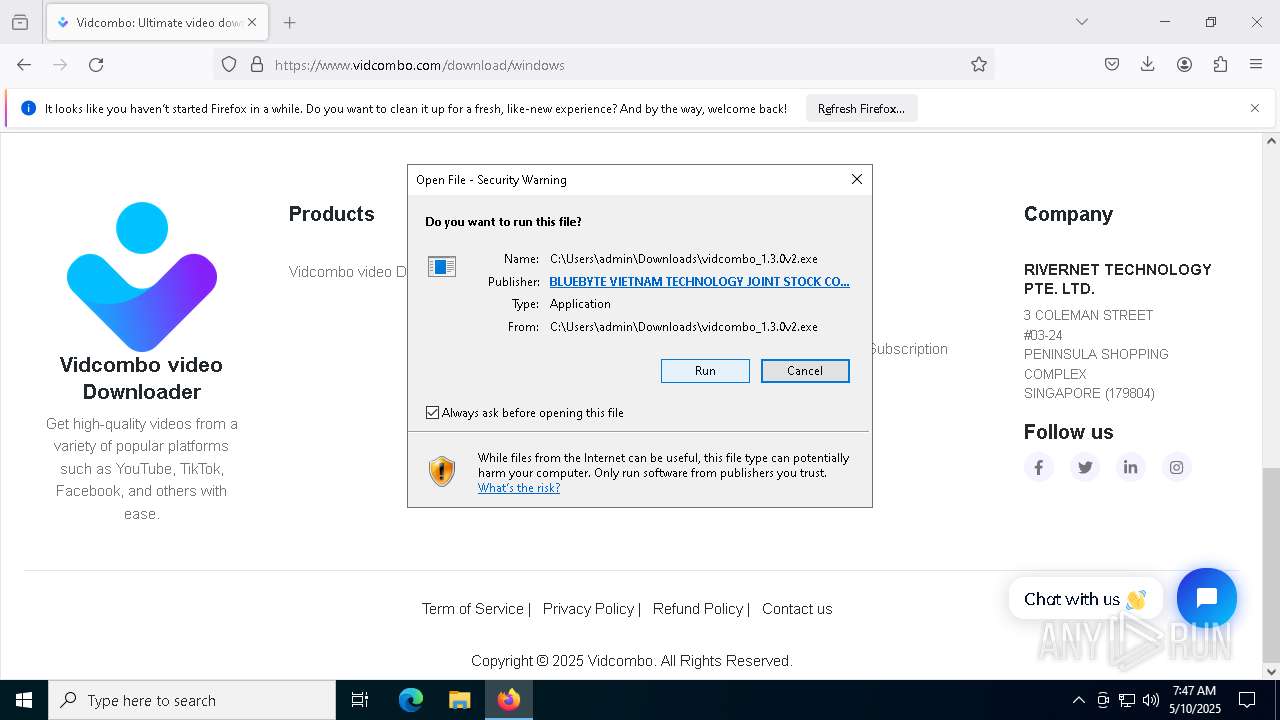
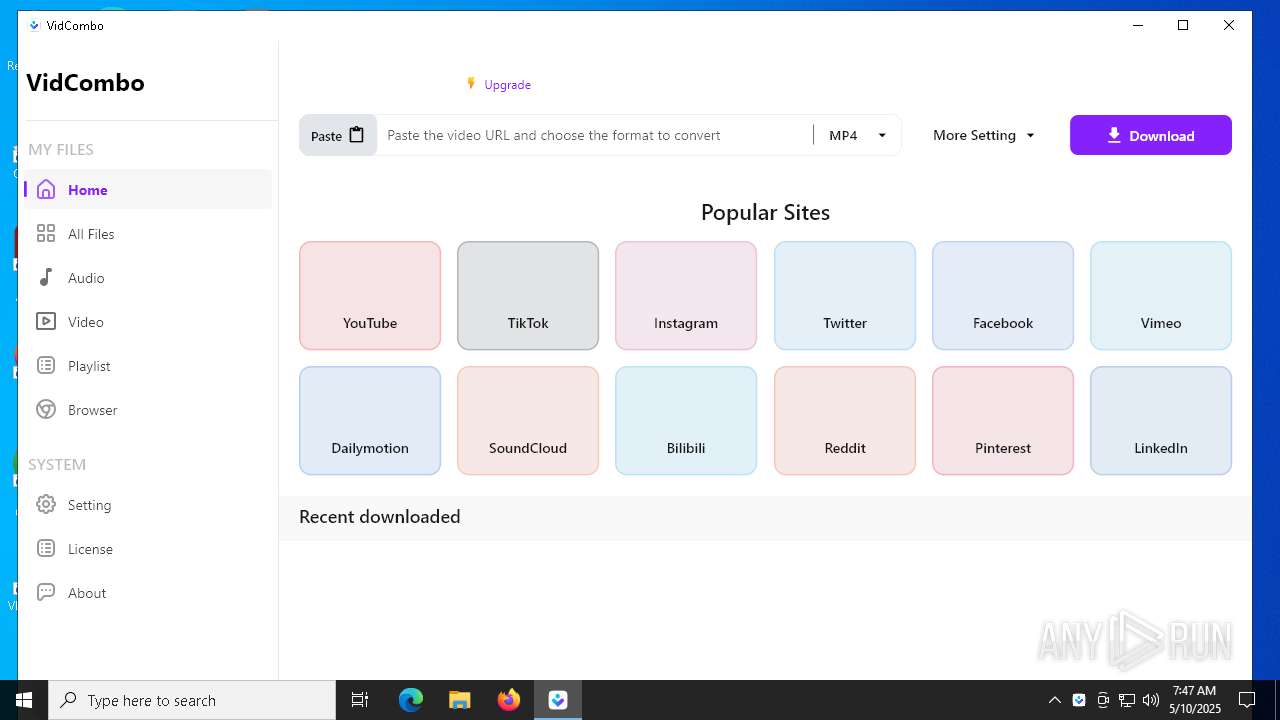
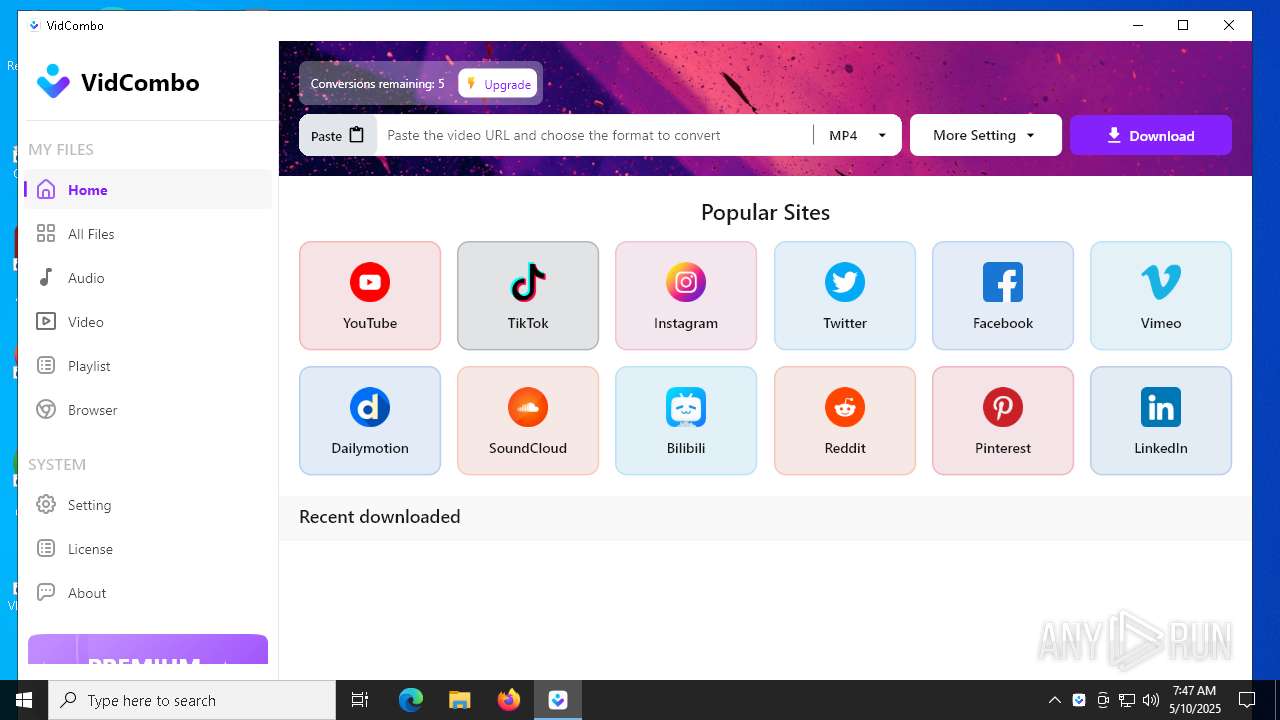
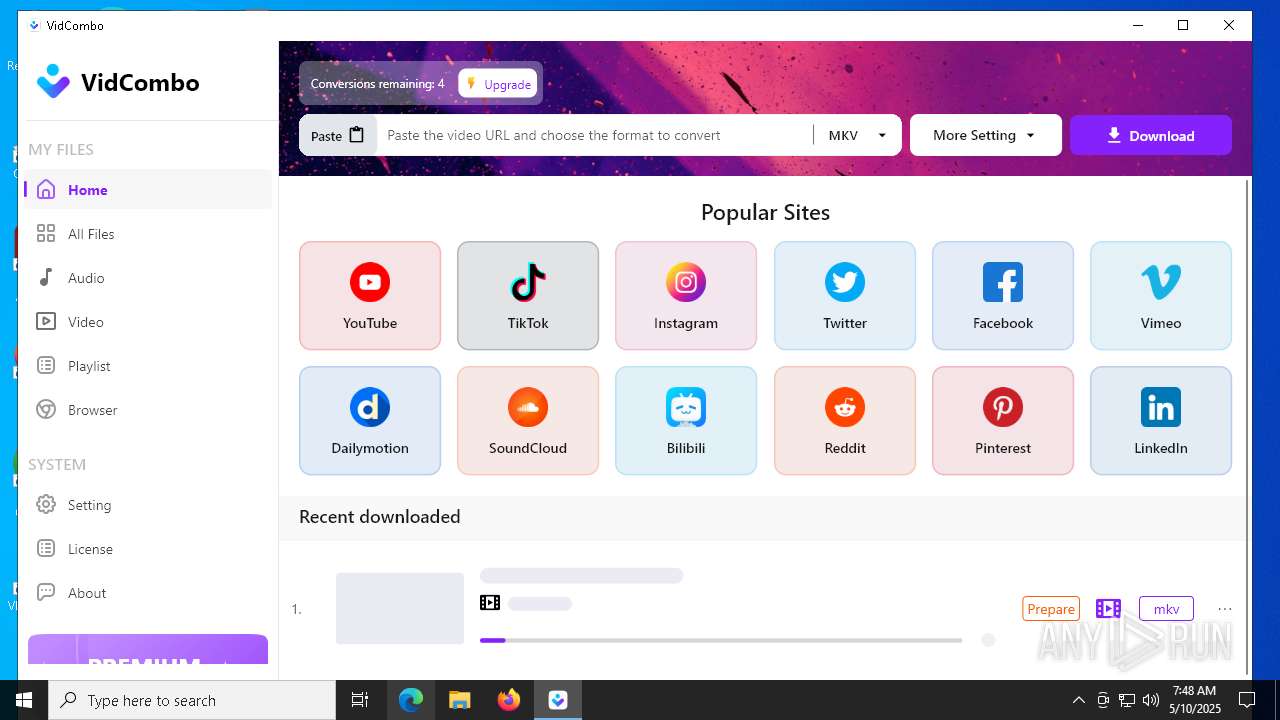
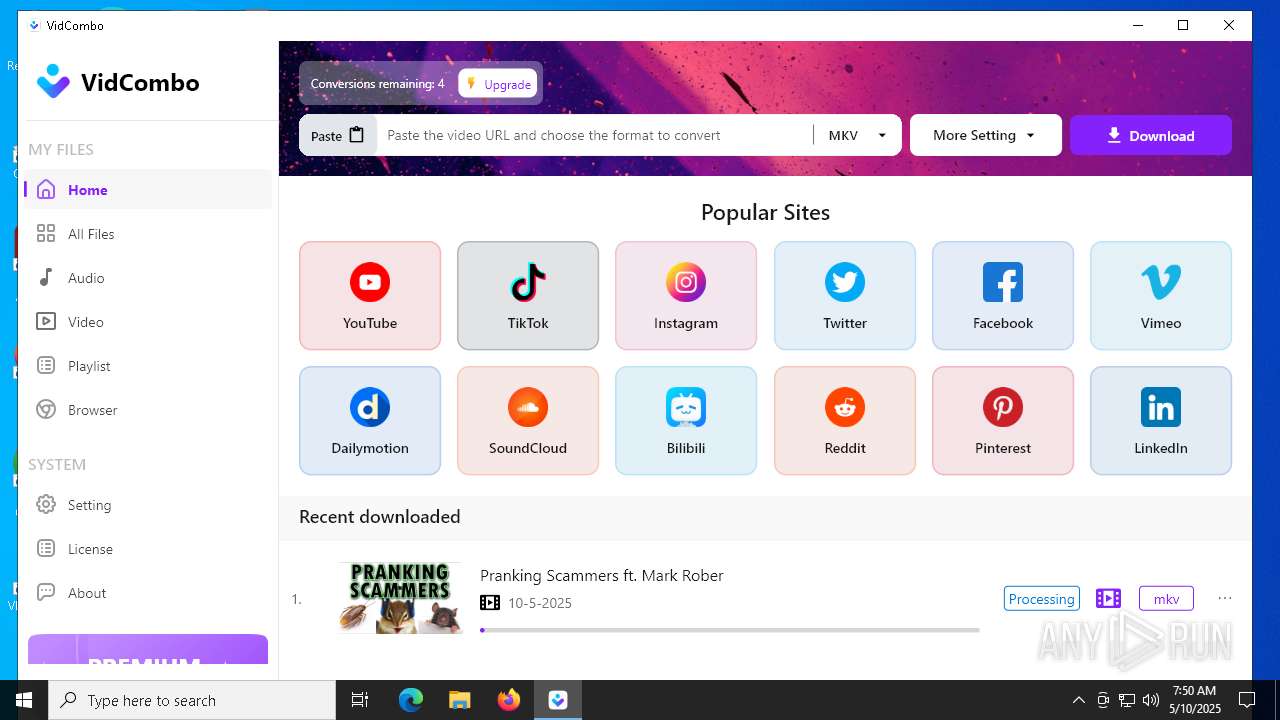
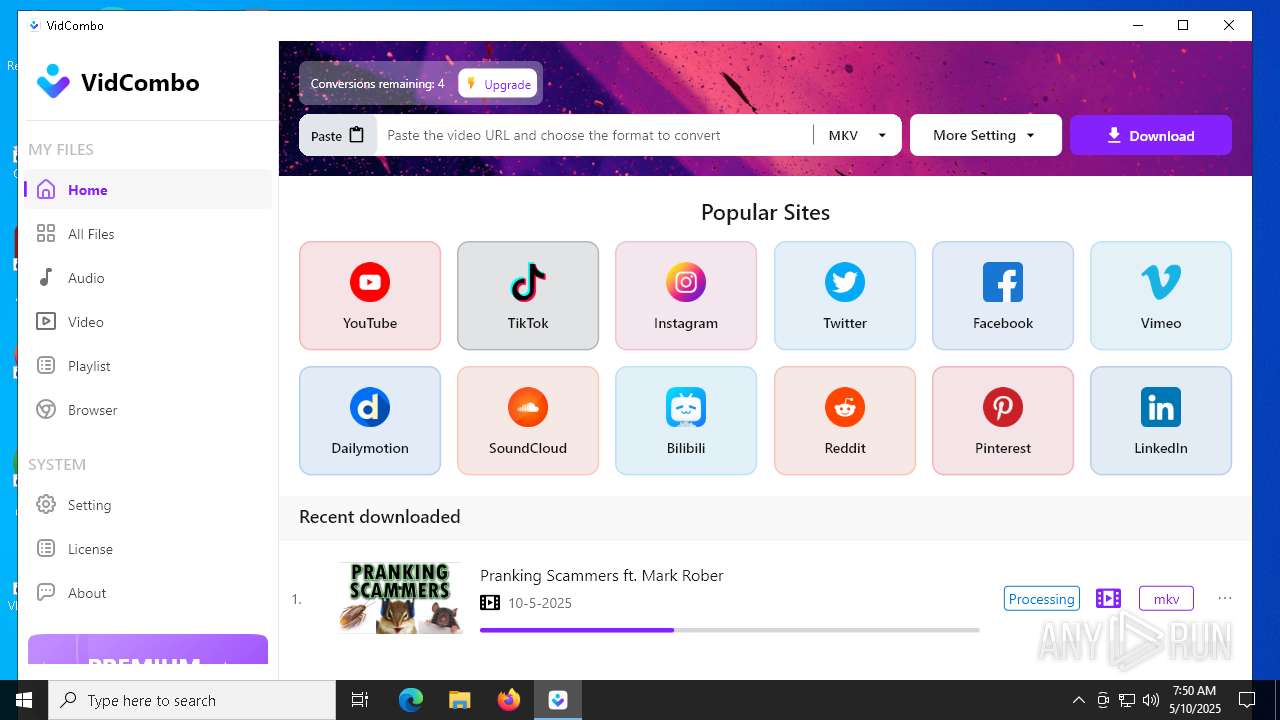
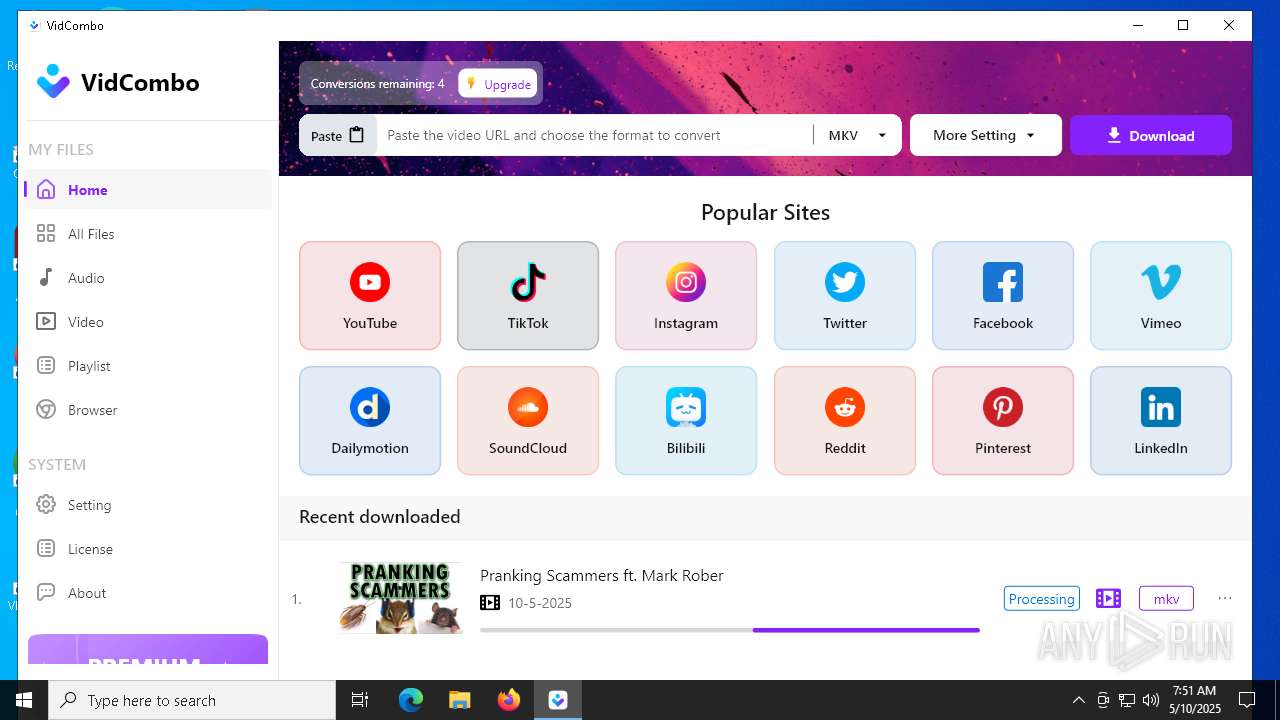
| URL: | https://www.vidcombo.com/ |
| Full analysis: | https://app.any.run/tasks/21dd0dd3-0602-4885-aec0-54ec2063dcf8 |
| Verdict: | Malicious activity |
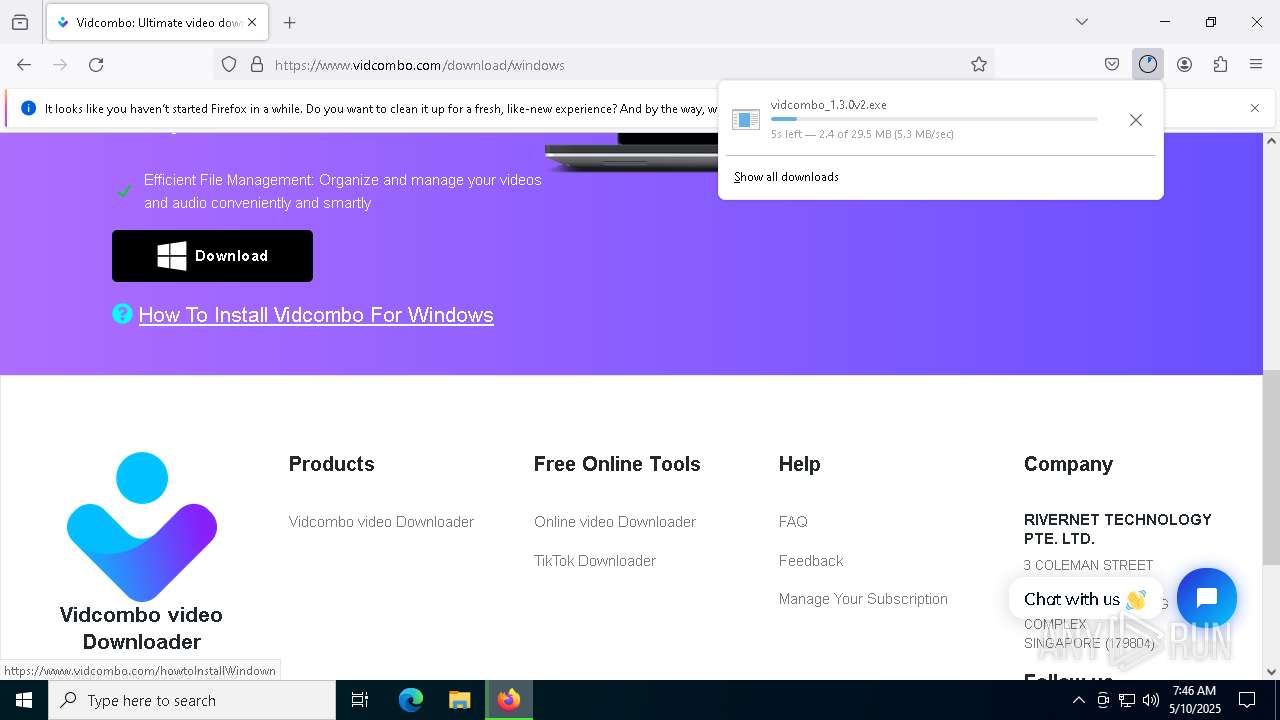
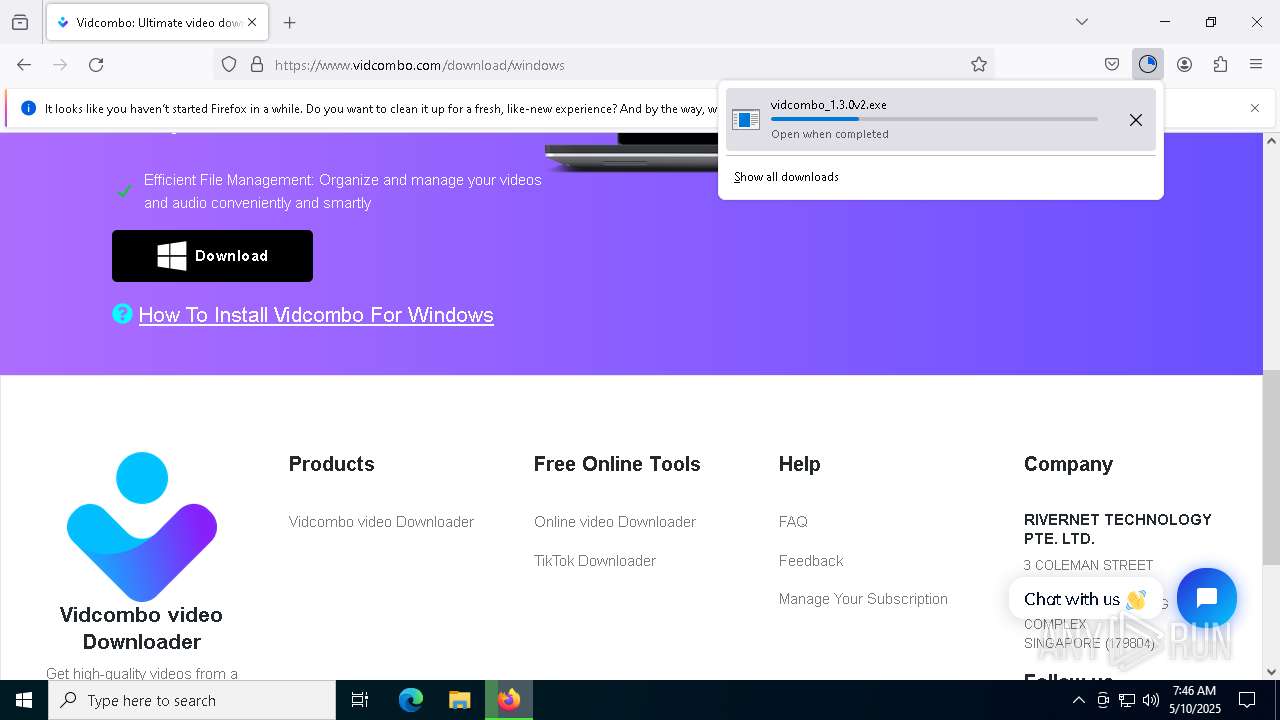
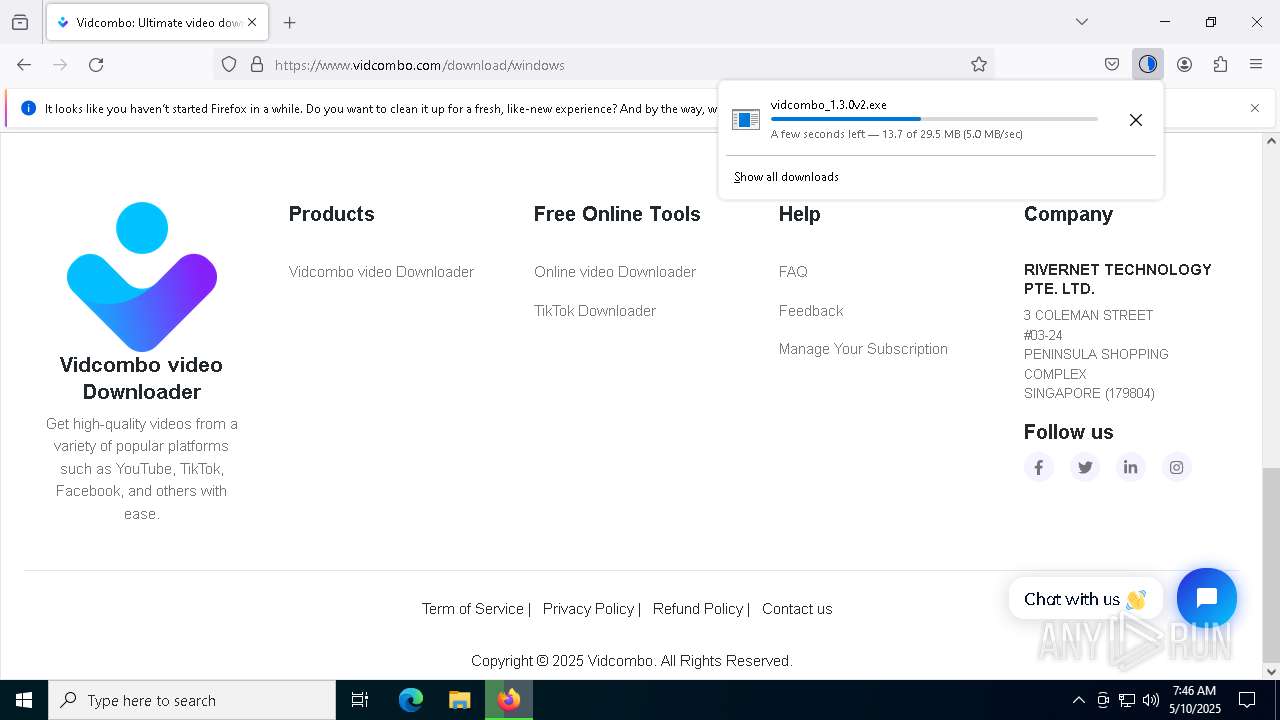
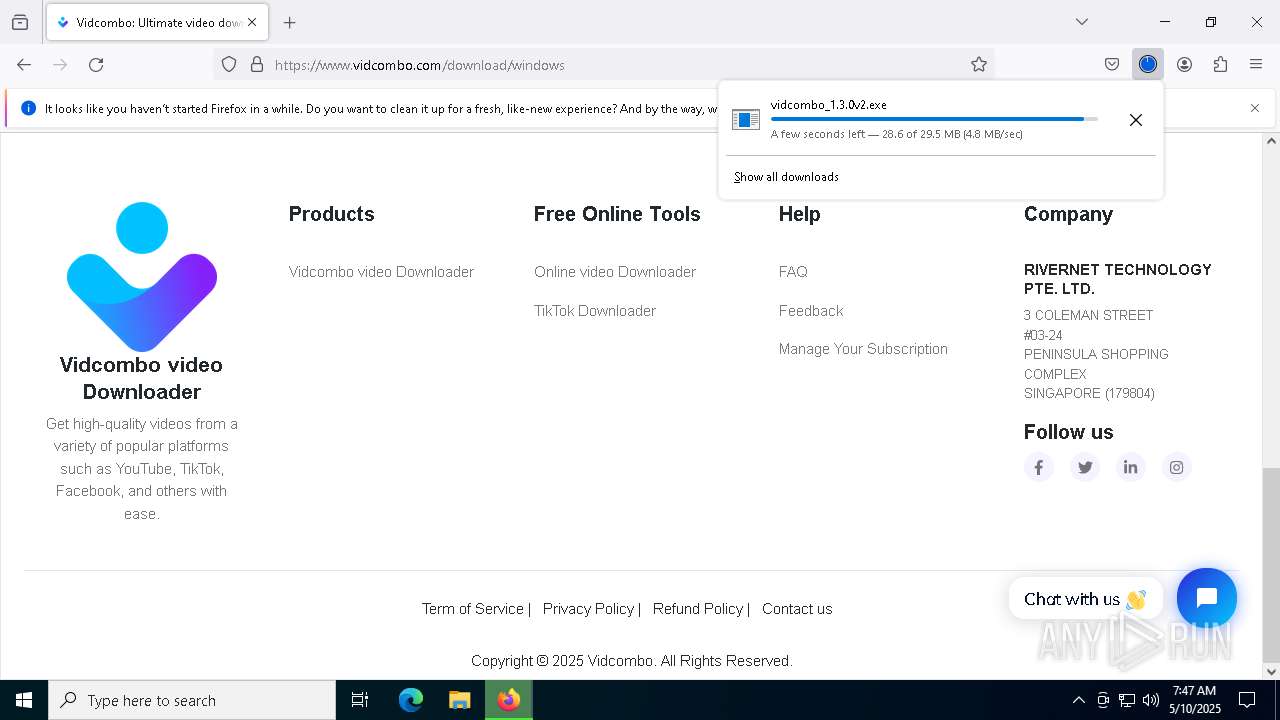
| Analysis date: | May 10, 2025, 07:46:32 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 5B86E12AA235B5DE52F110A9AC5C2E8B |
| SHA1: | 22D123ED255B73021638127215B578174CEC5756 |
| SHA256: | AA42EB345246B1ABBF9FD7AAC11F440234800F5F1A8ACF6CE9525680EB83553E |
| SSDEEP: | 3:N8DSLABGTwGG:2OLAlR |
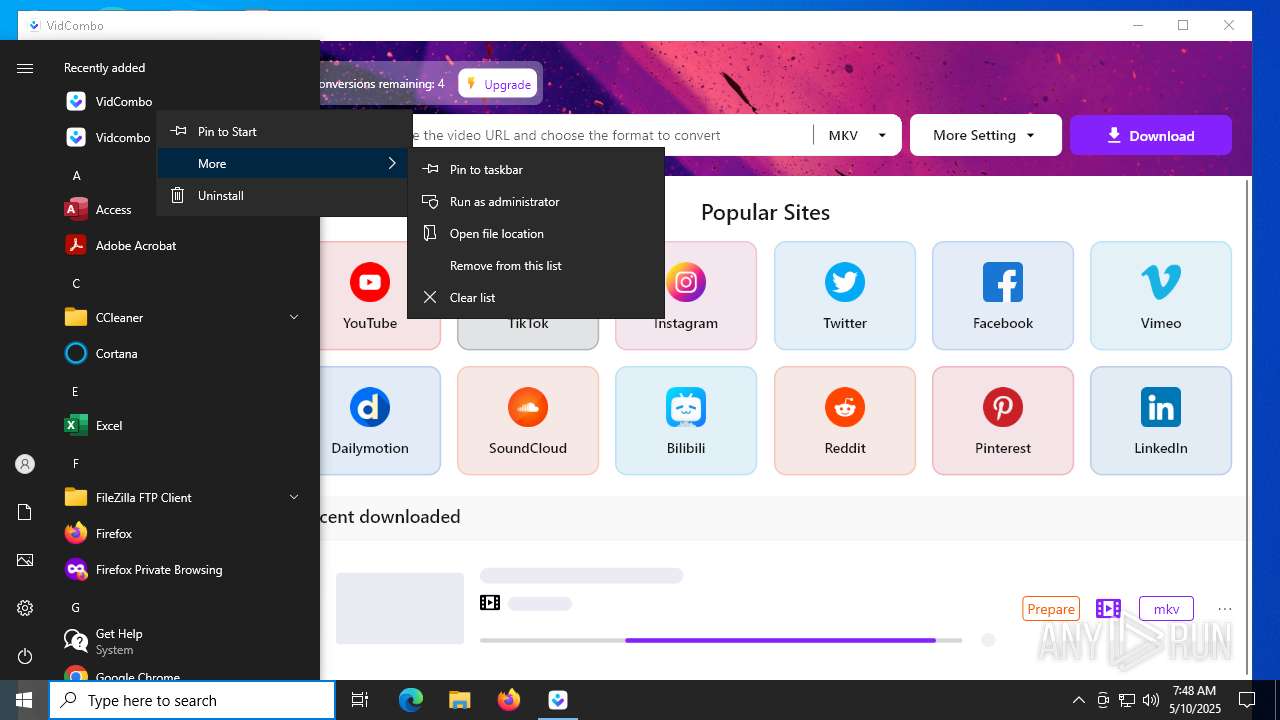
MALICIOUS
No malicious indicators.SUSPICIOUS
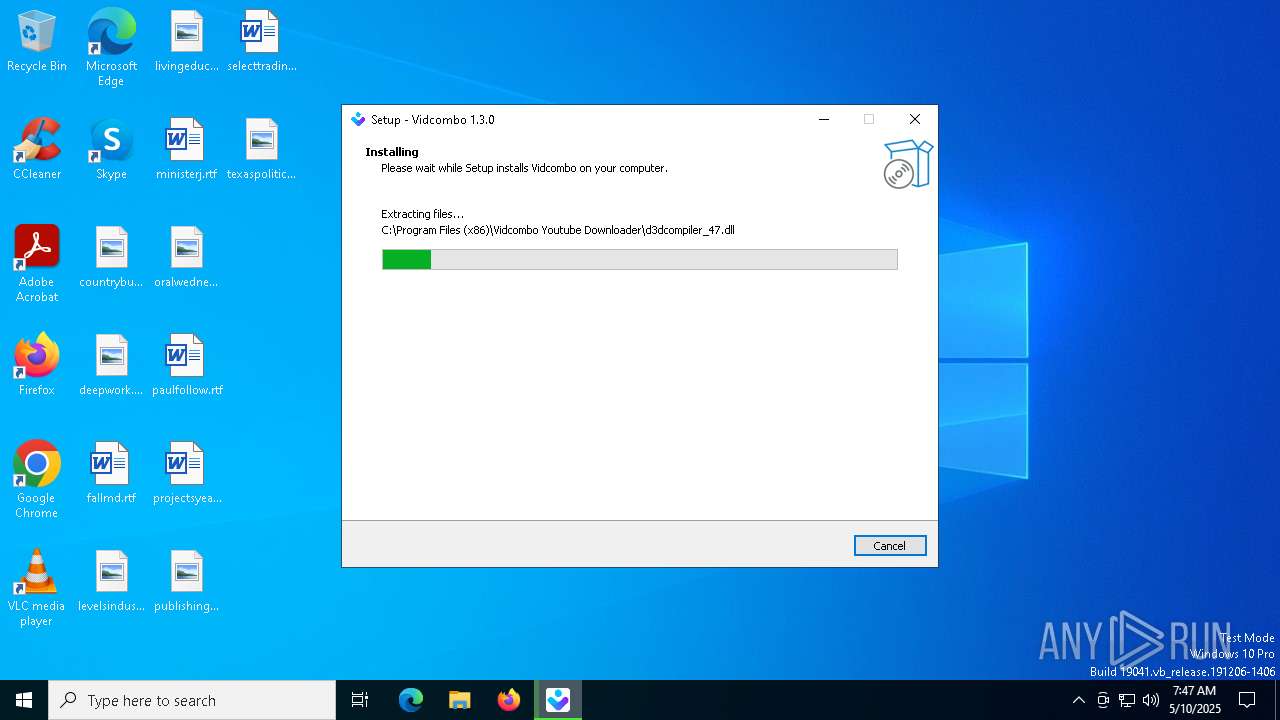
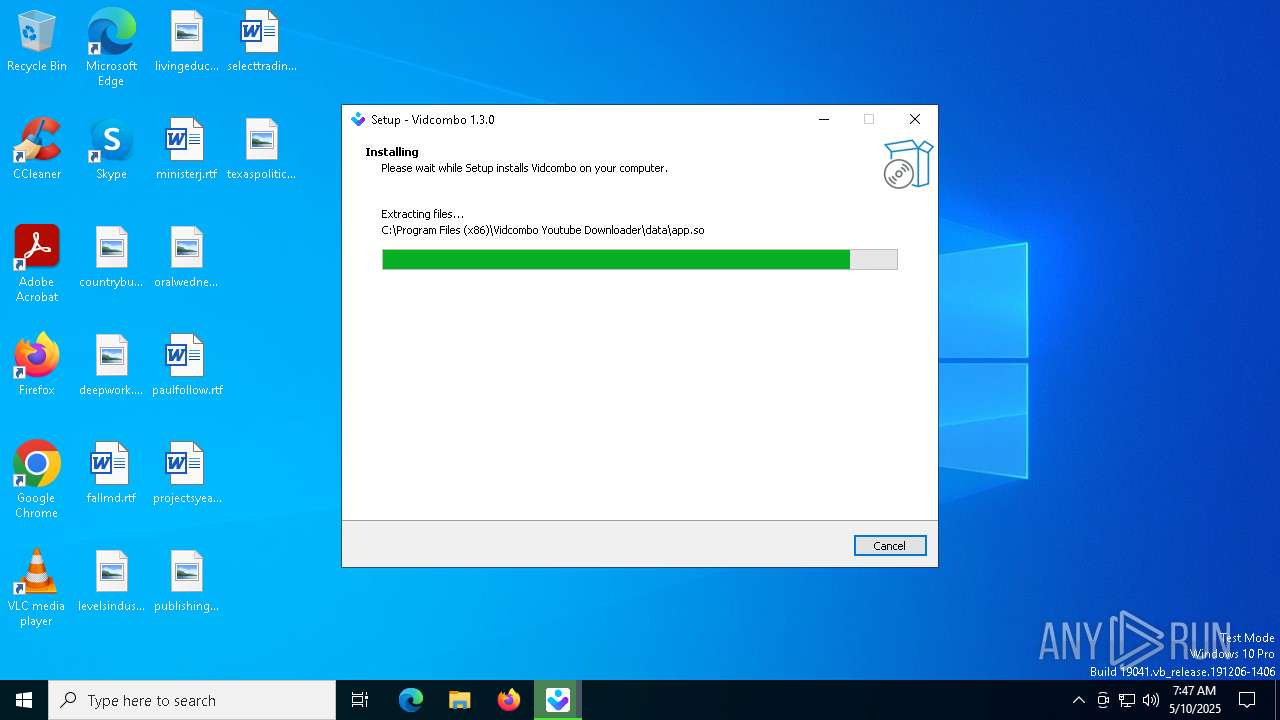
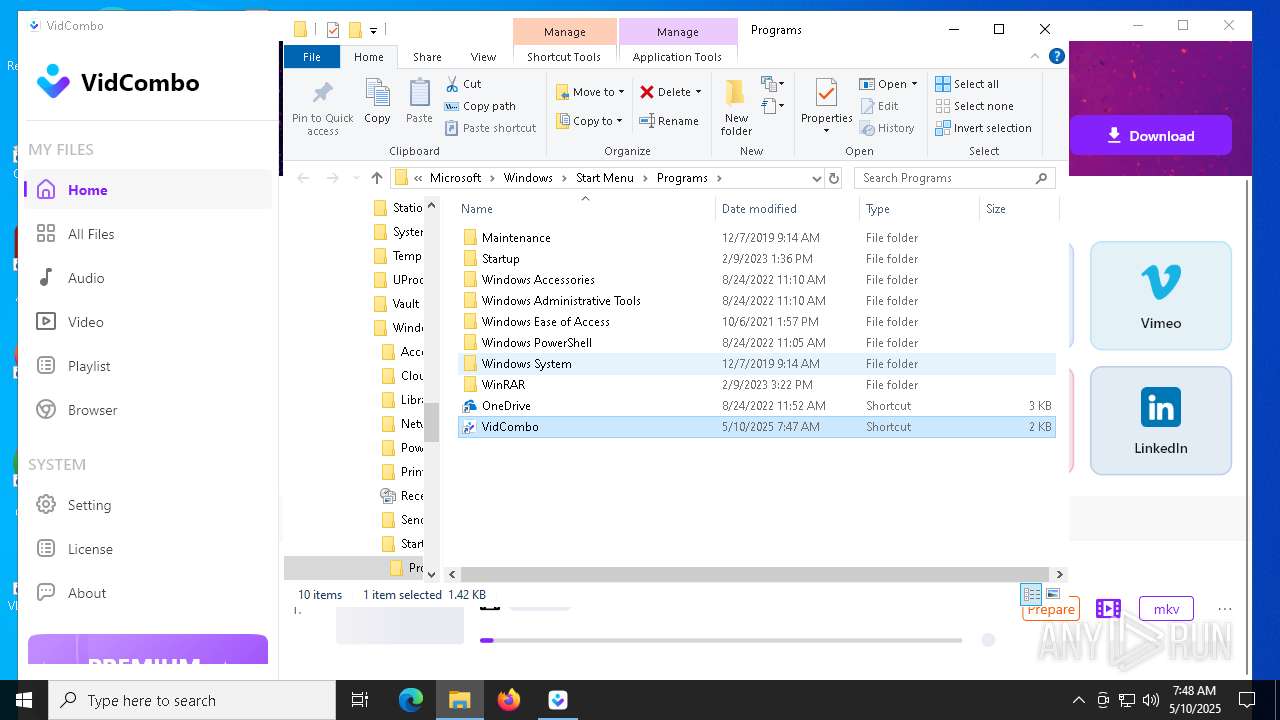
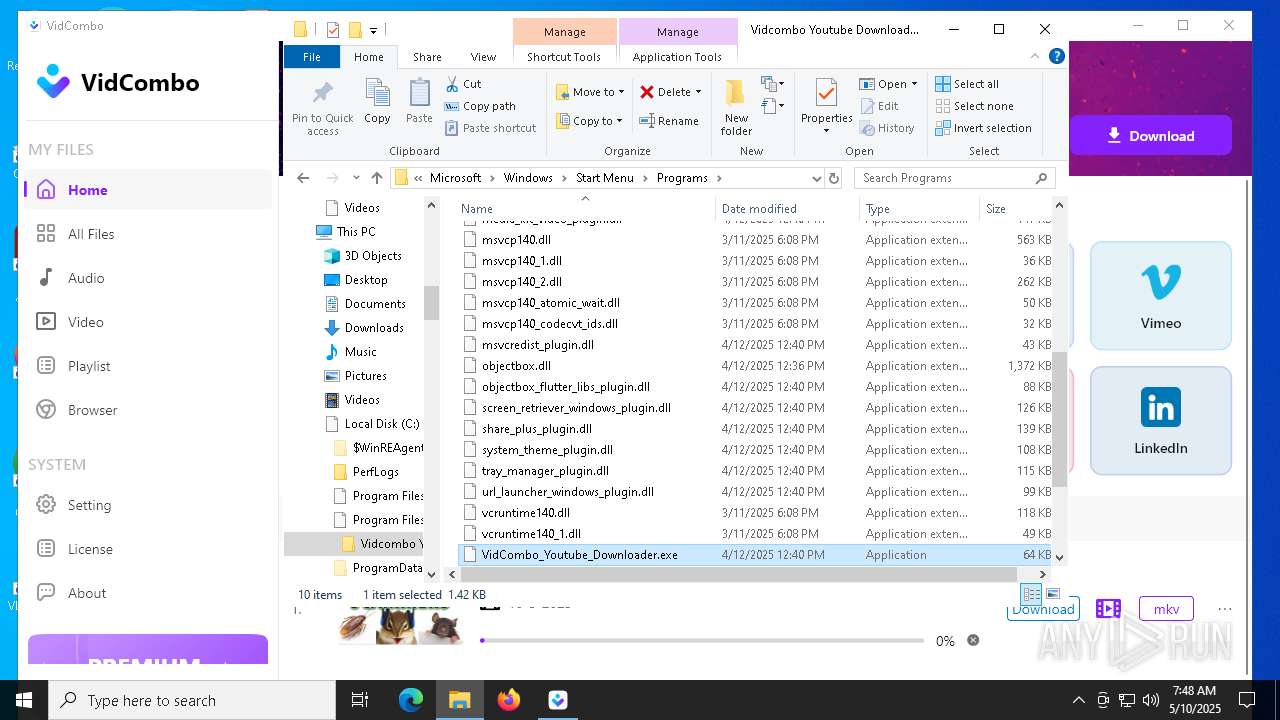
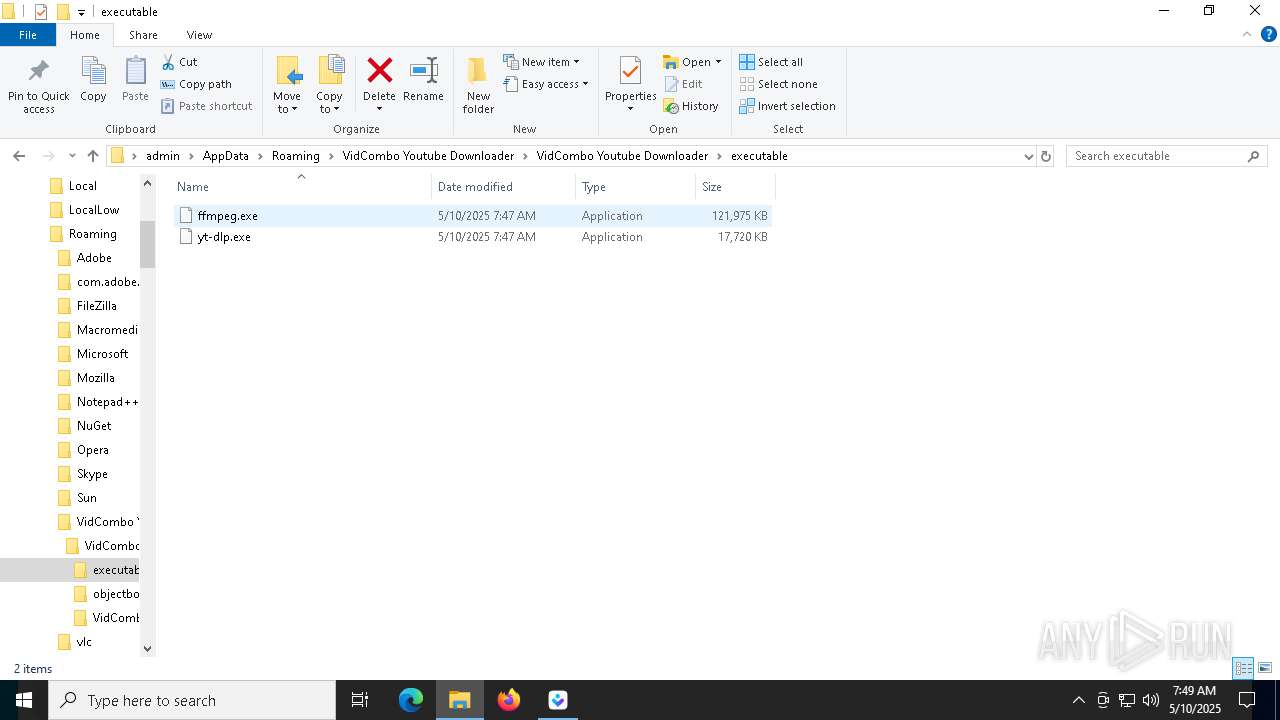
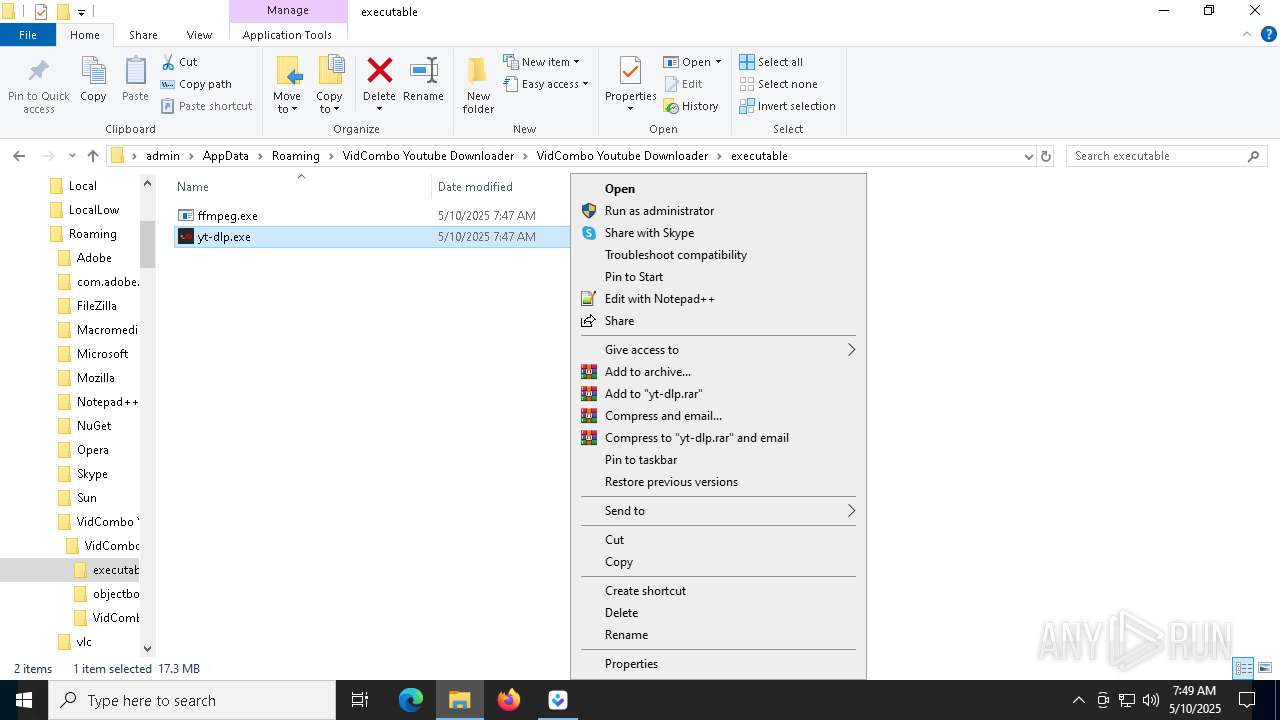
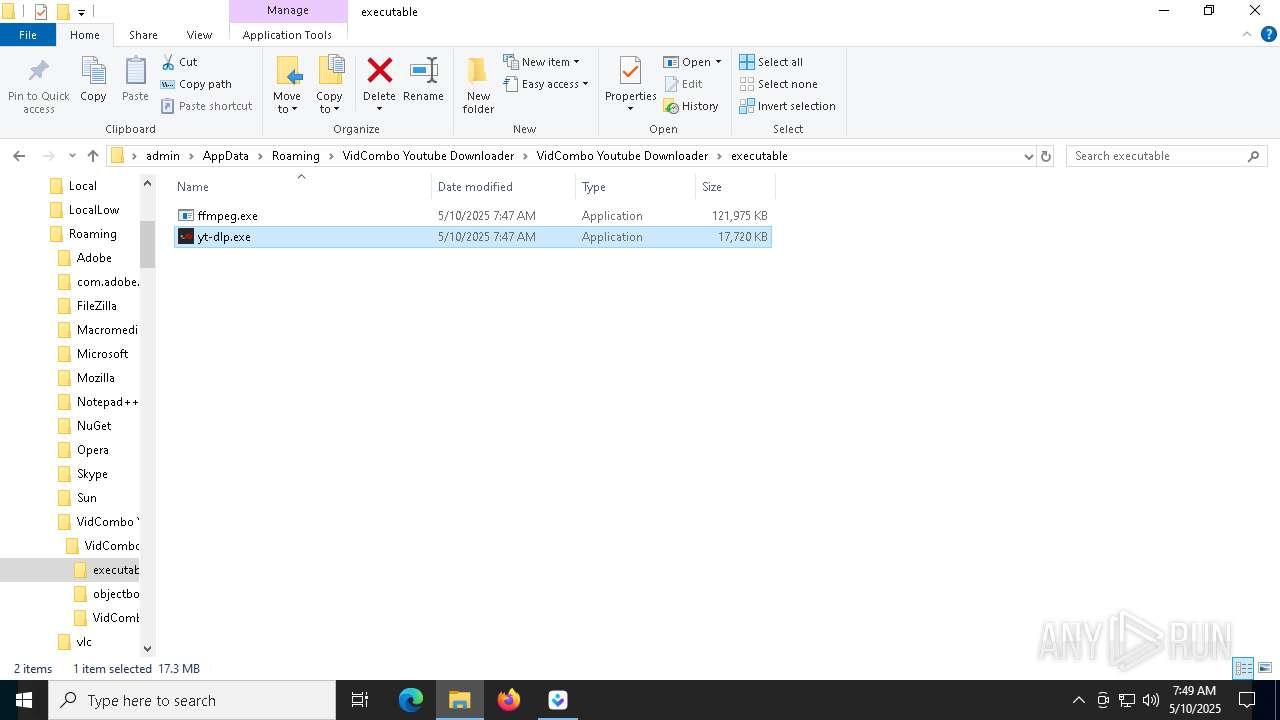
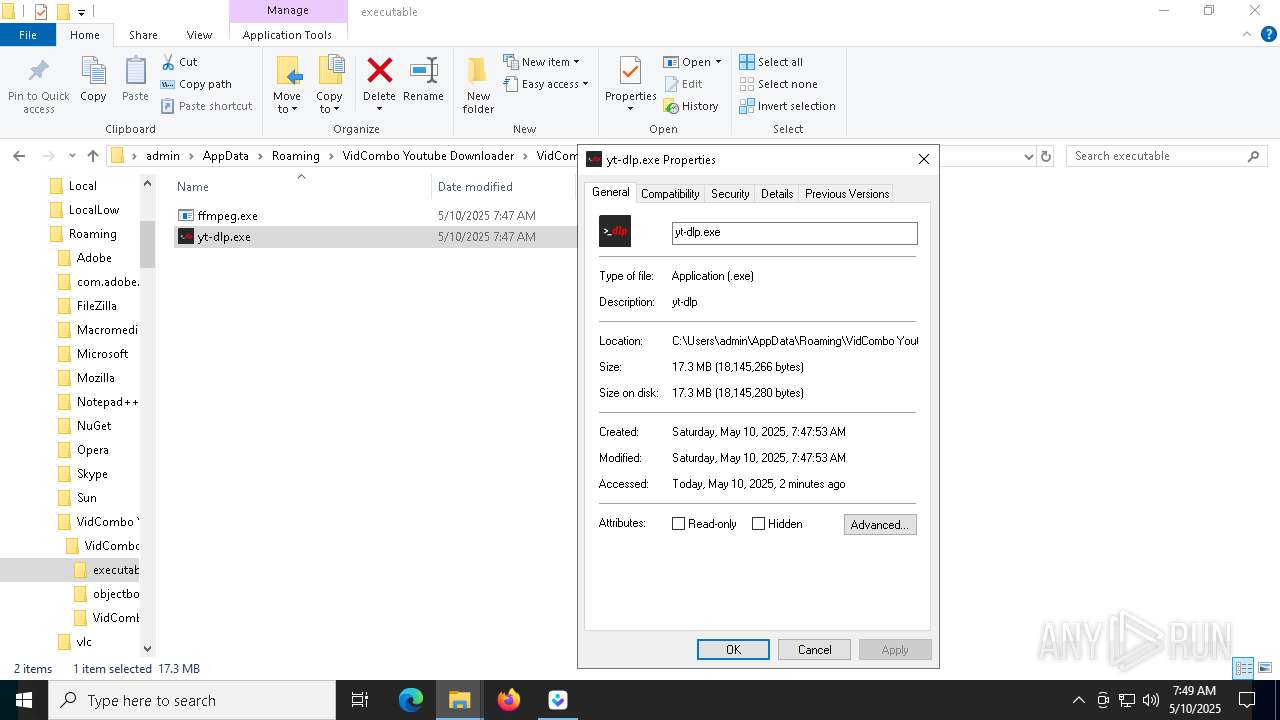
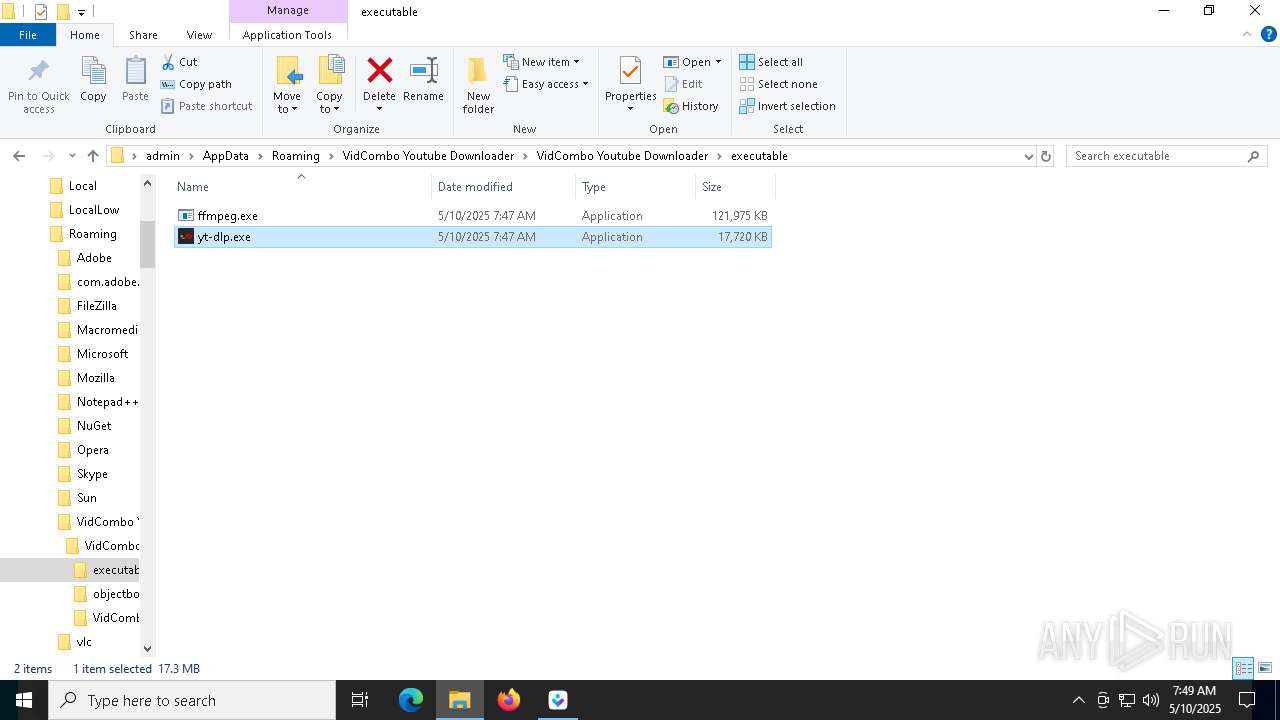
Executable content was dropped or overwritten
- vidcombo_1.3.0v2.exe (PID: 9092)
- vidcombo_1.3.0v2.exe (PID: 9204)
- vidcombo_1.3.0v2.tmp (PID: 8236)
- yt-dlp.exe (PID: 7844)
- VidCombo_Youtube_Downloader.exe (PID: 8740)
- yt-dlp.exe (PID: 9032)
Reads security settings of Internet Explorer
- vidcombo_1.3.0v2.tmp (PID: 9112)
Reads the Windows owner or organization settings
- vidcombo_1.3.0v2.tmp (PID: 8236)
- VidCombo_Youtube_Downloader.exe (PID: 8740)
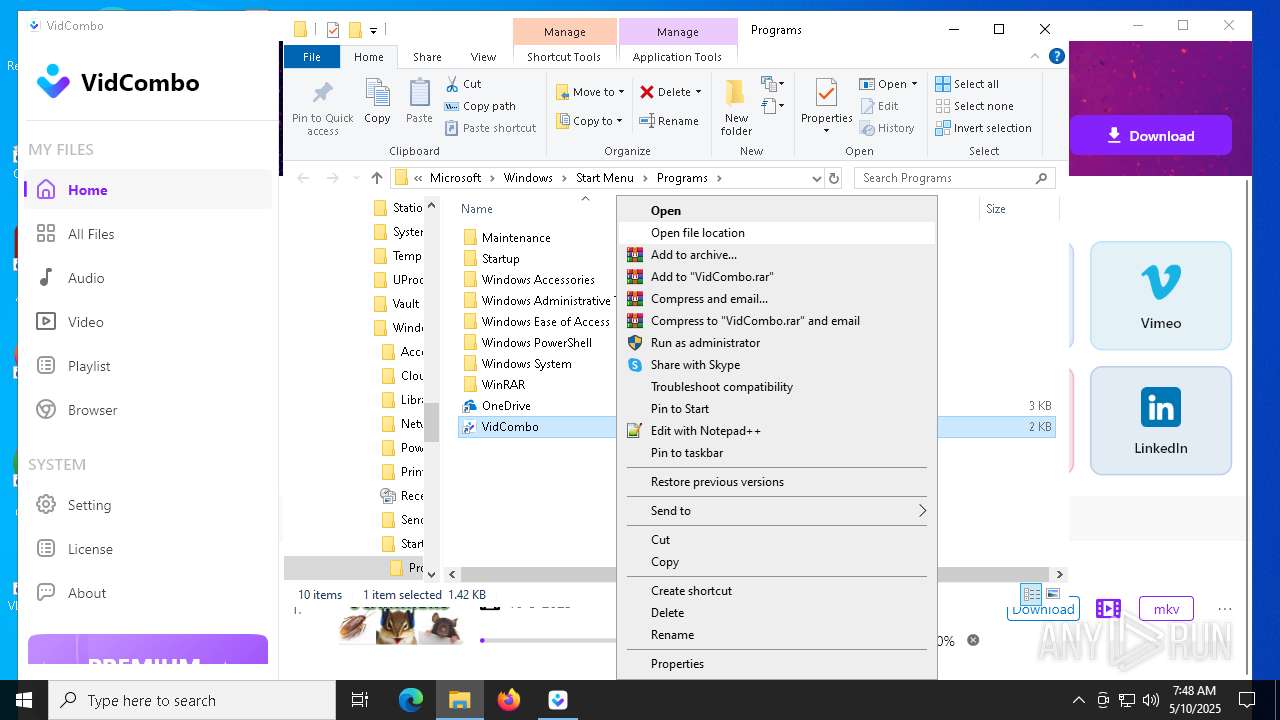
Uses TASKKILL.EXE to kill process
- vidcombo_1.3.0v2.tmp (PID: 8236)
- cmd.exe (PID: 4724)
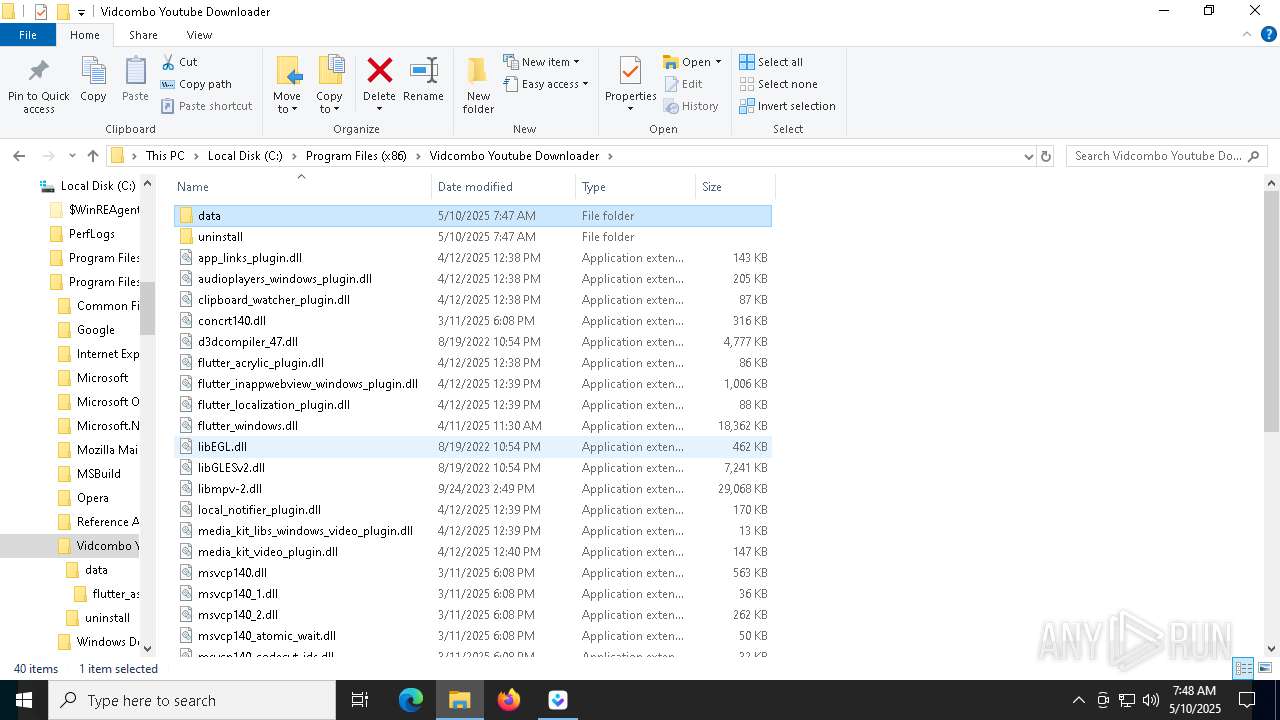
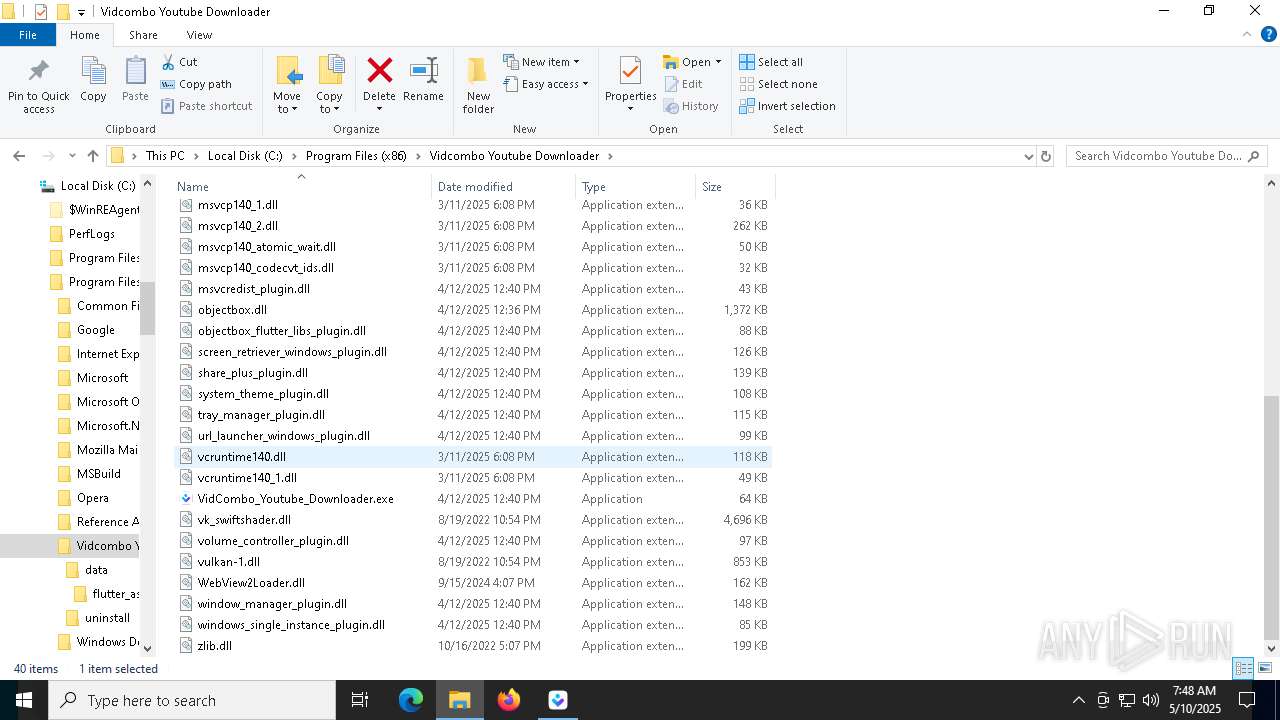
Process drops legitimate windows executable
- vidcombo_1.3.0v2.tmp (PID: 8236)
- yt-dlp.exe (PID: 7844)
- yt-dlp.exe (PID: 9032)
Starts CMD.EXE for commands execution
- vidcombo_1.3.0v2.tmp (PID: 8236)
- yt-dlp.exe (PID: 8152)
- yt-dlp.exe (PID: 4040)
Executes application which crashes
- VidCombo_Youtube_Downloader.exe (PID: 5984)
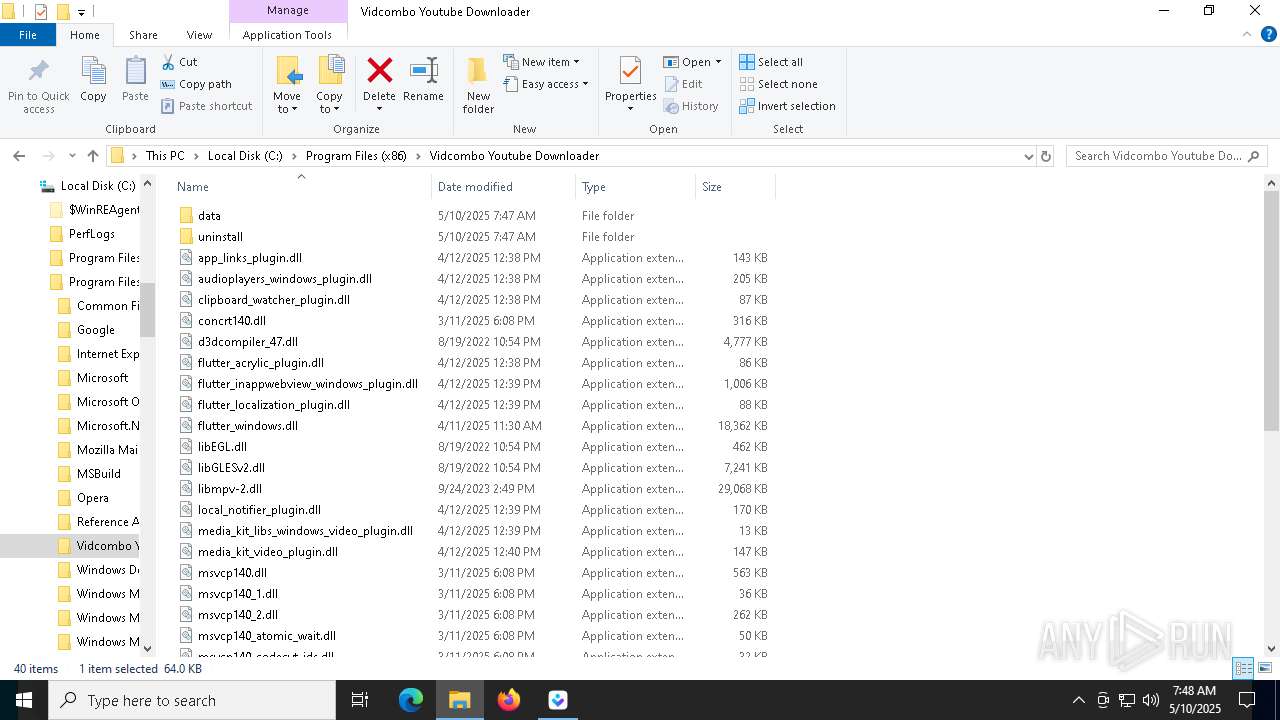
The process drops C-runtime libraries
- vidcombo_1.3.0v2.tmp (PID: 8236)
- yt-dlp.exe (PID: 7844)
- yt-dlp.exe (PID: 9032)
Uses WMIC.EXE to obtain operating system information
- VidCombo_Youtube_Downloader.exe (PID: 8740)
Uses WMIC.EXE to obtain CPU information
- VidCombo_Youtube_Downloader.exe (PID: 8740)
There is functionality for taking screenshot (YARA)
- VidCombo_Youtube_Downloader.exe (PID: 8740)
Process drops python dynamic module
- yt-dlp.exe (PID: 7844)
- yt-dlp.exe (PID: 9032)
Application launched itself
- yt-dlp.exe (PID: 7844)
- yt-dlp.exe (PID: 9032)
Reads the date of Windows installation
- VidCombo_Youtube_Downloader.exe (PID: 8740)
Found regular expressions for crypto-addresses (YARA)
- yt-dlp.exe (PID: 4040)
INFO
Checks supported languages
- vidcombo_1.3.0v2.exe (PID: 9092)
- vidcombo_1.3.0v2.tmp (PID: 9112)
- vidcombo_1.3.0v2.exe (PID: 9204)
- vidcombo_1.3.0v2.tmp (PID: 8236)
- VidCombo_Youtube_Downloader.exe (PID: 5984)
- VidCombo_Youtube_Downloader.exe (PID: 8740)
Executable content was dropped or overwritten
- firefox.exe (PID: 5048)
Application launched itself
- firefox.exe (PID: 5048)
- firefox.exe (PID: 6264)
Reads the computer name
- vidcombo_1.3.0v2.tmp (PID: 9112)
- vidcombo_1.3.0v2.exe (PID: 9204)
- vidcombo_1.3.0v2.tmp (PID: 8236)
- VidCombo_Youtube_Downloader.exe (PID: 5984)
- VidCombo_Youtube_Downloader.exe (PID: 8740)
Create files in a temporary directory
- vidcombo_1.3.0v2.exe (PID: 9092)
- vidcombo_1.3.0v2.exe (PID: 9204)
- vidcombo_1.3.0v2.tmp (PID: 8236)
Process checks computer location settings
- vidcombo_1.3.0v2.tmp (PID: 9112)
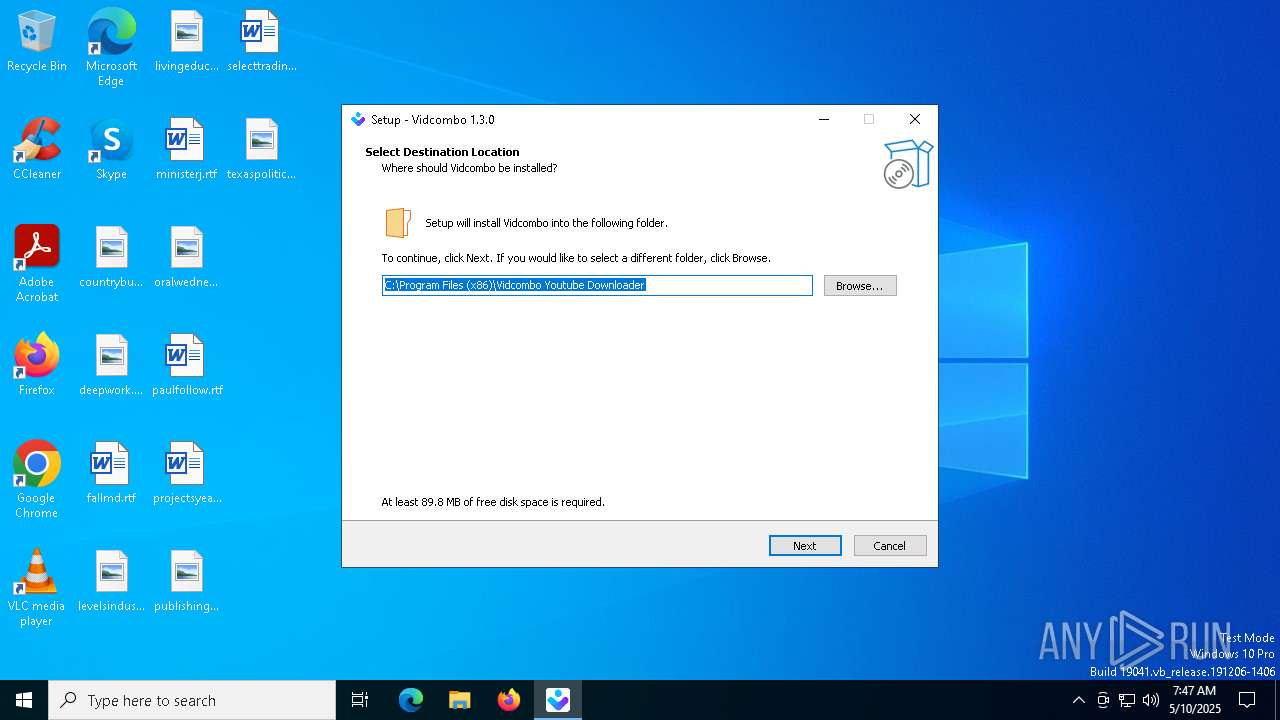
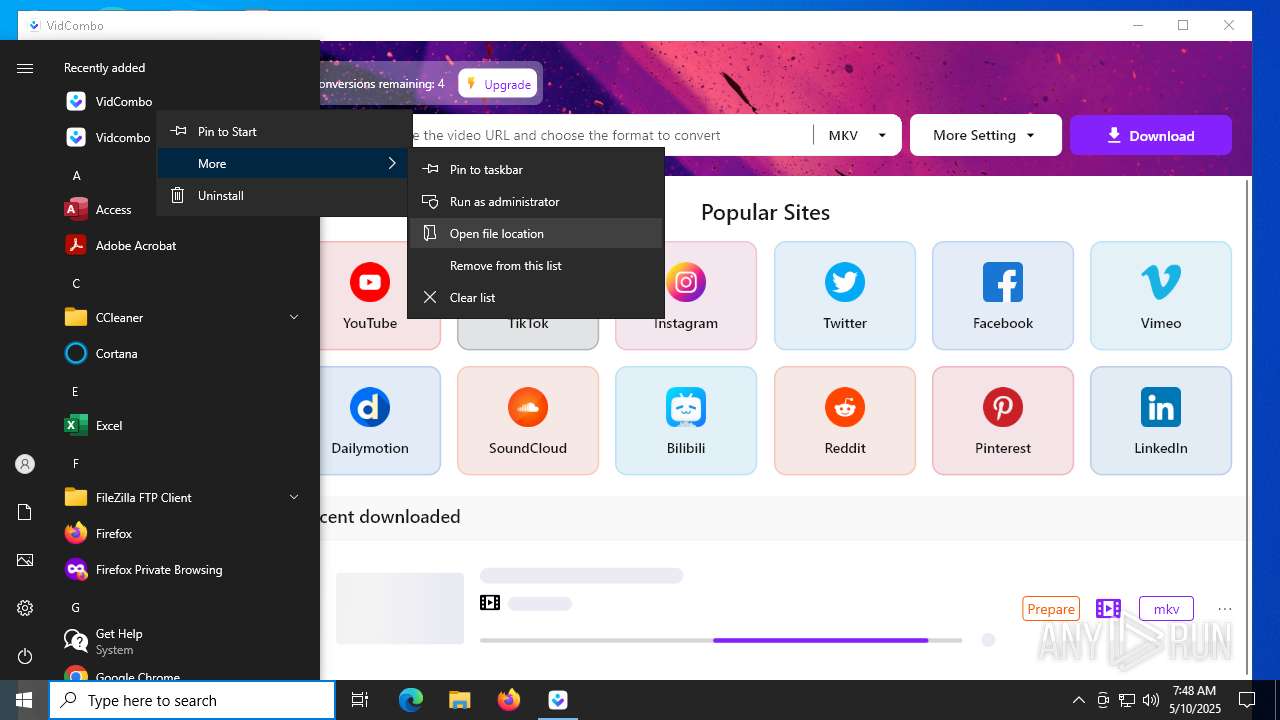
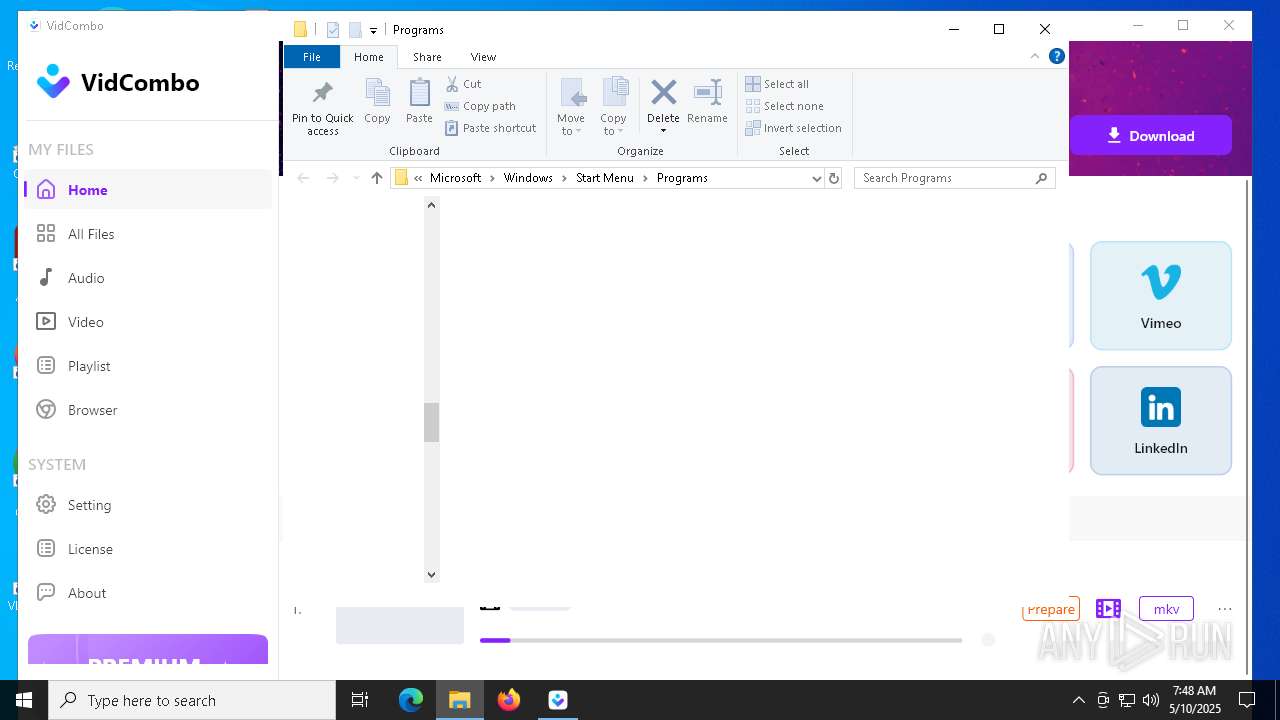
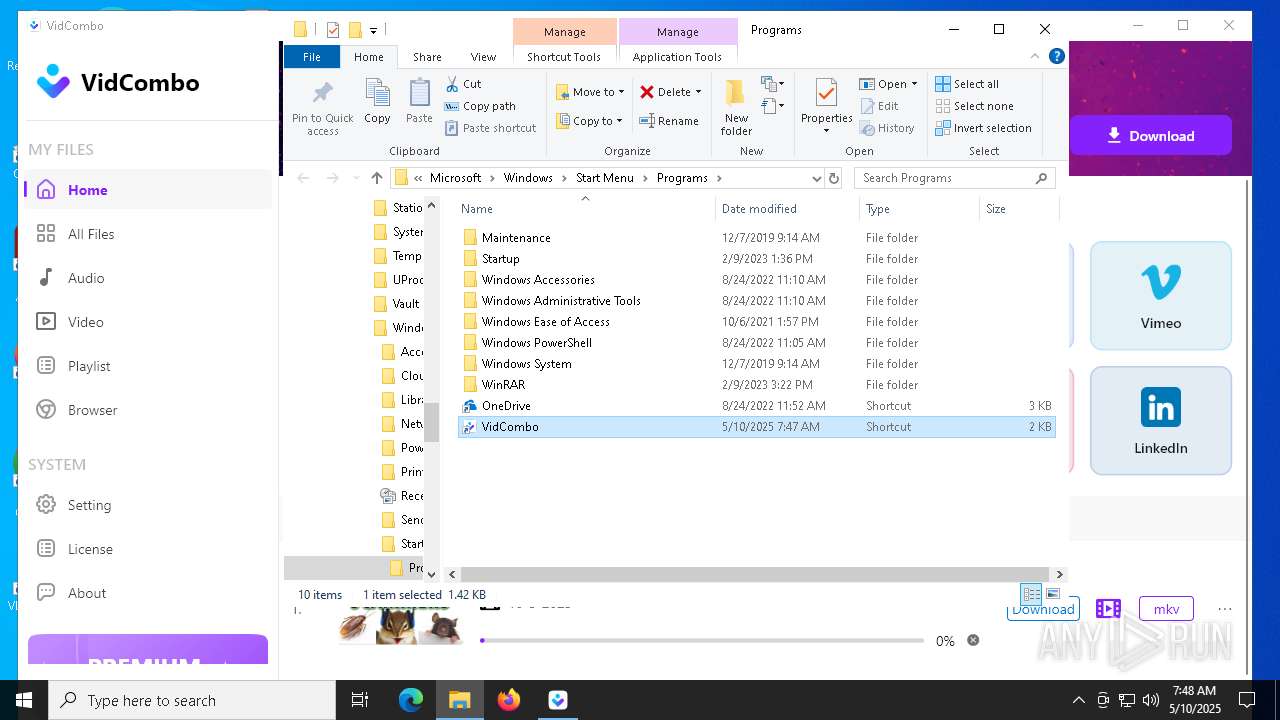
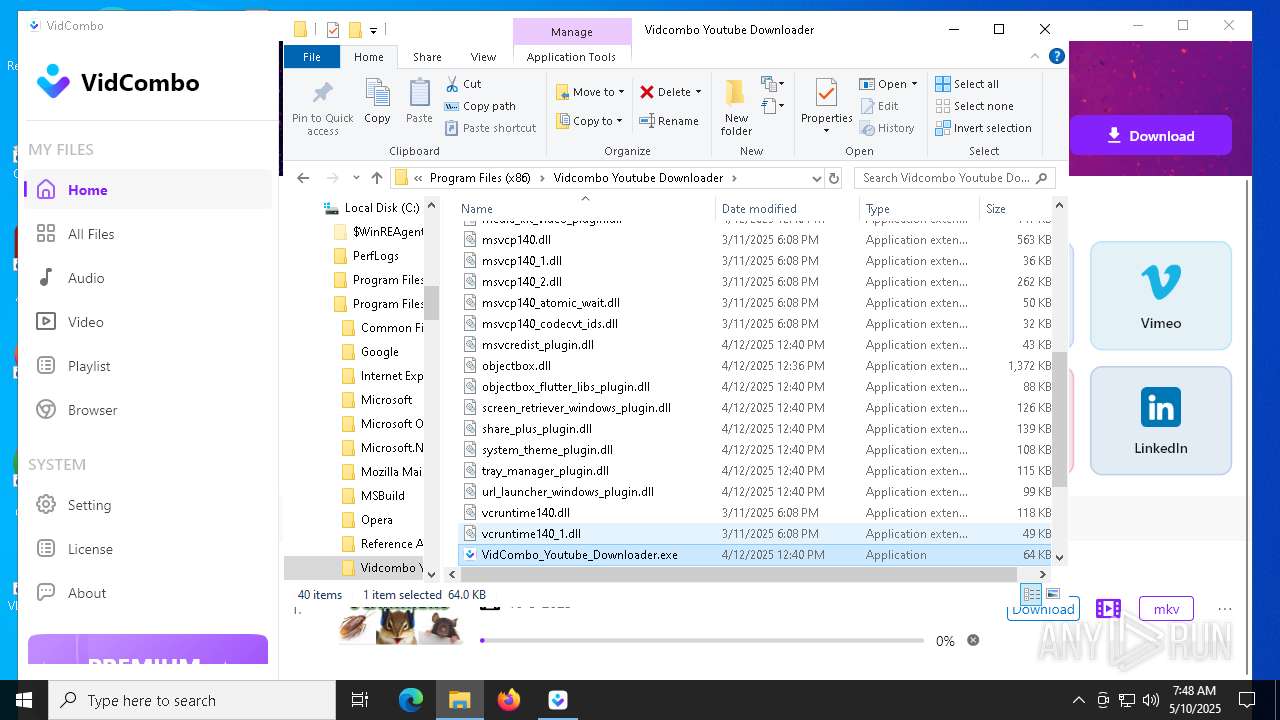
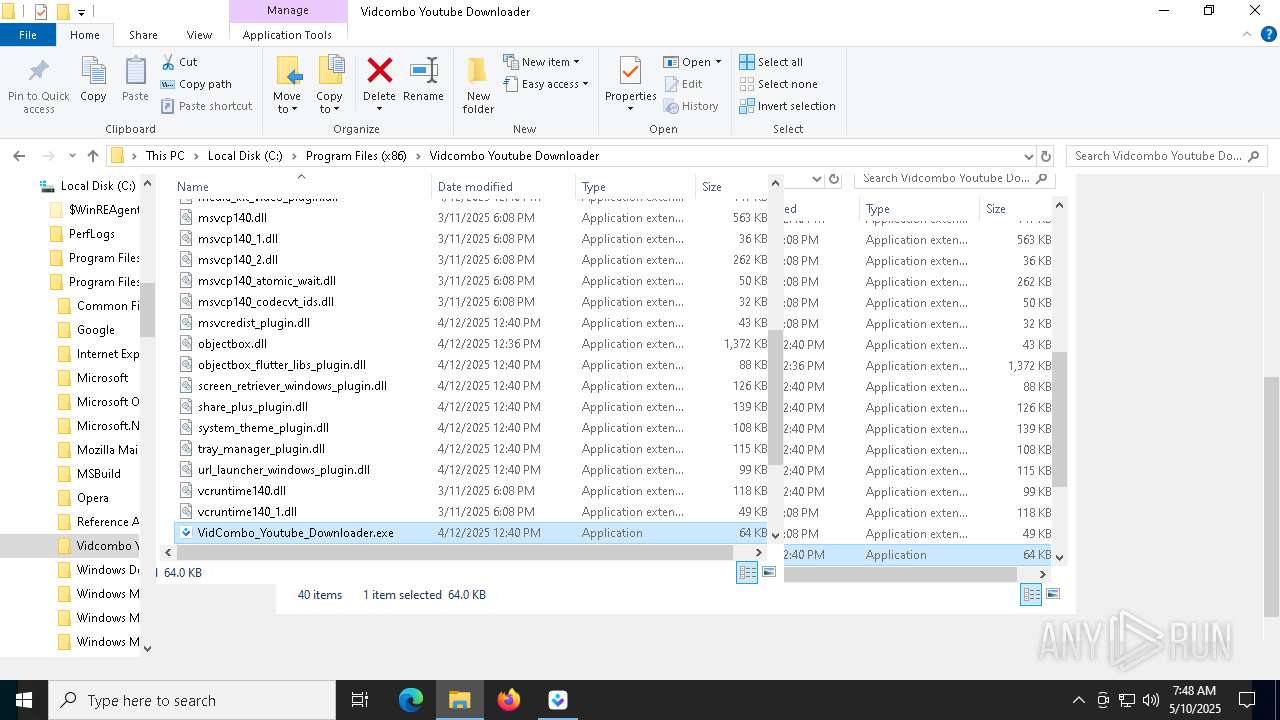
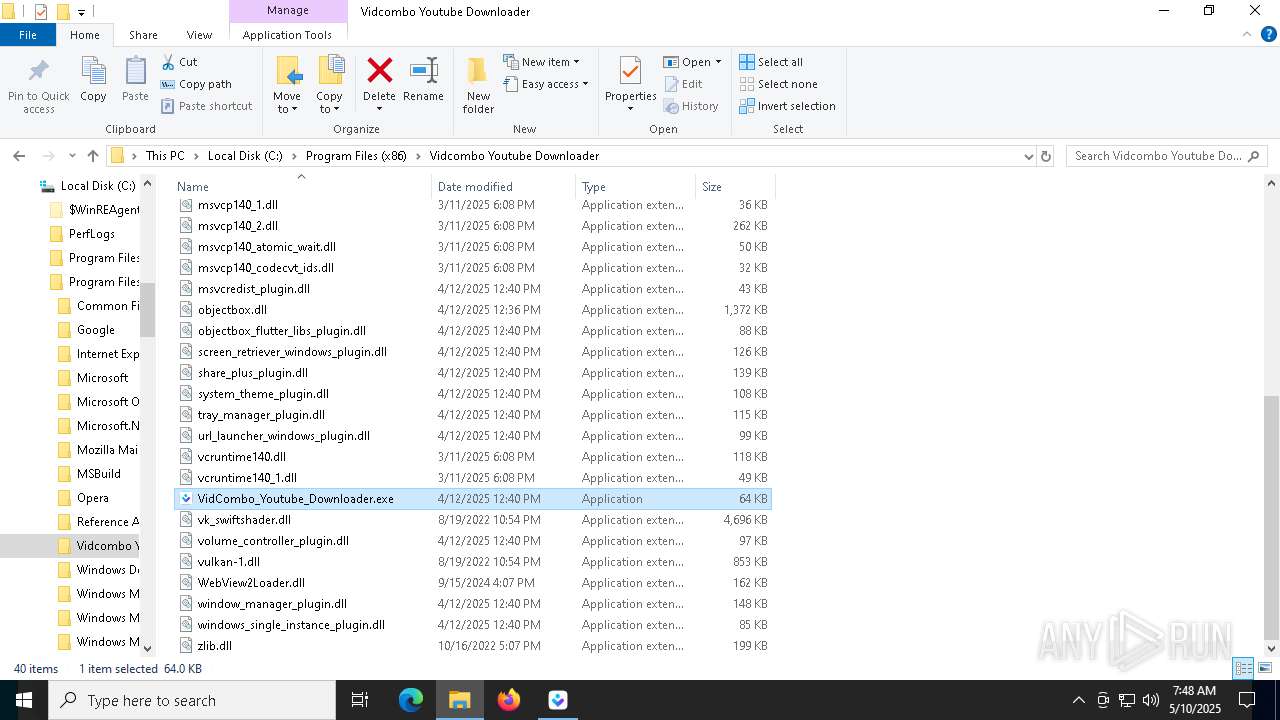
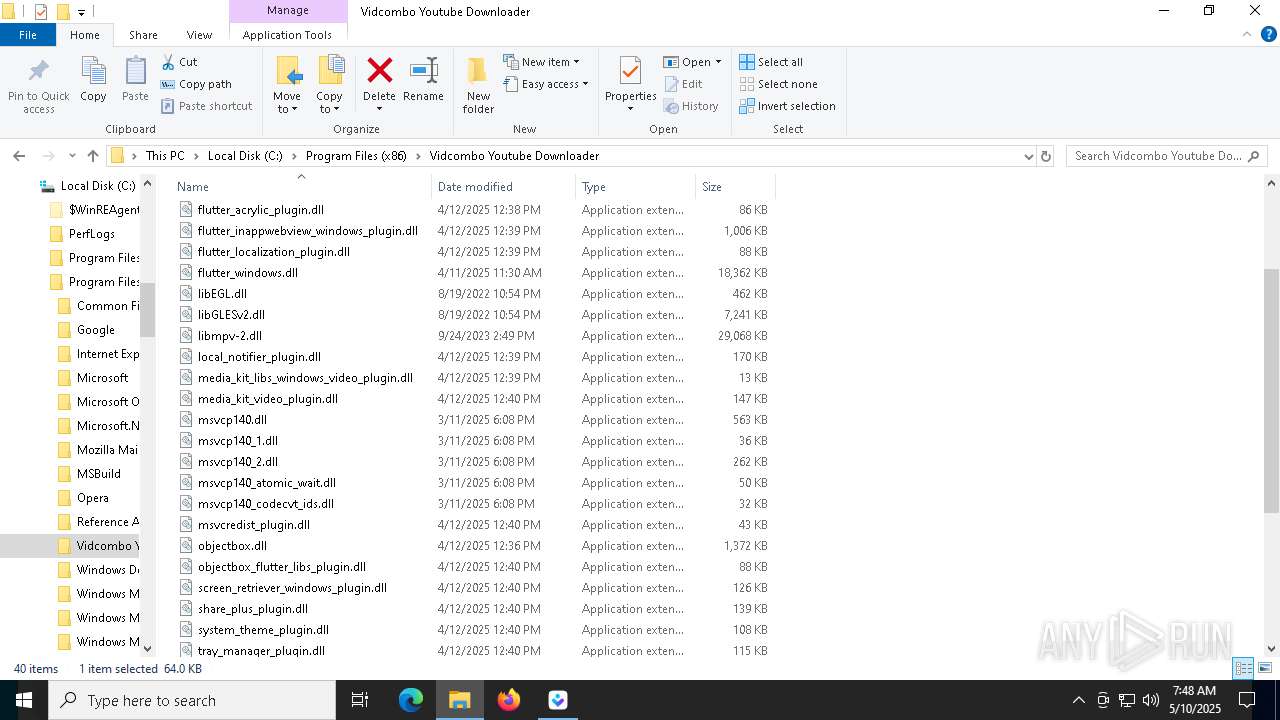
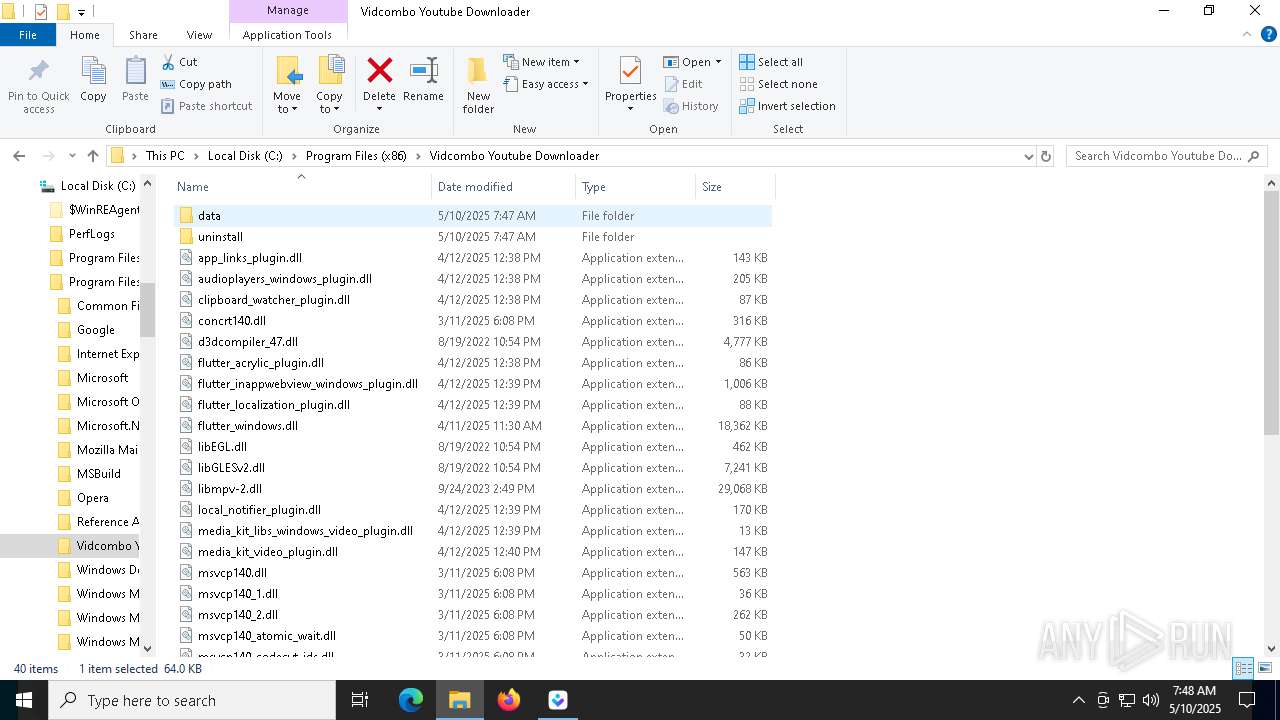
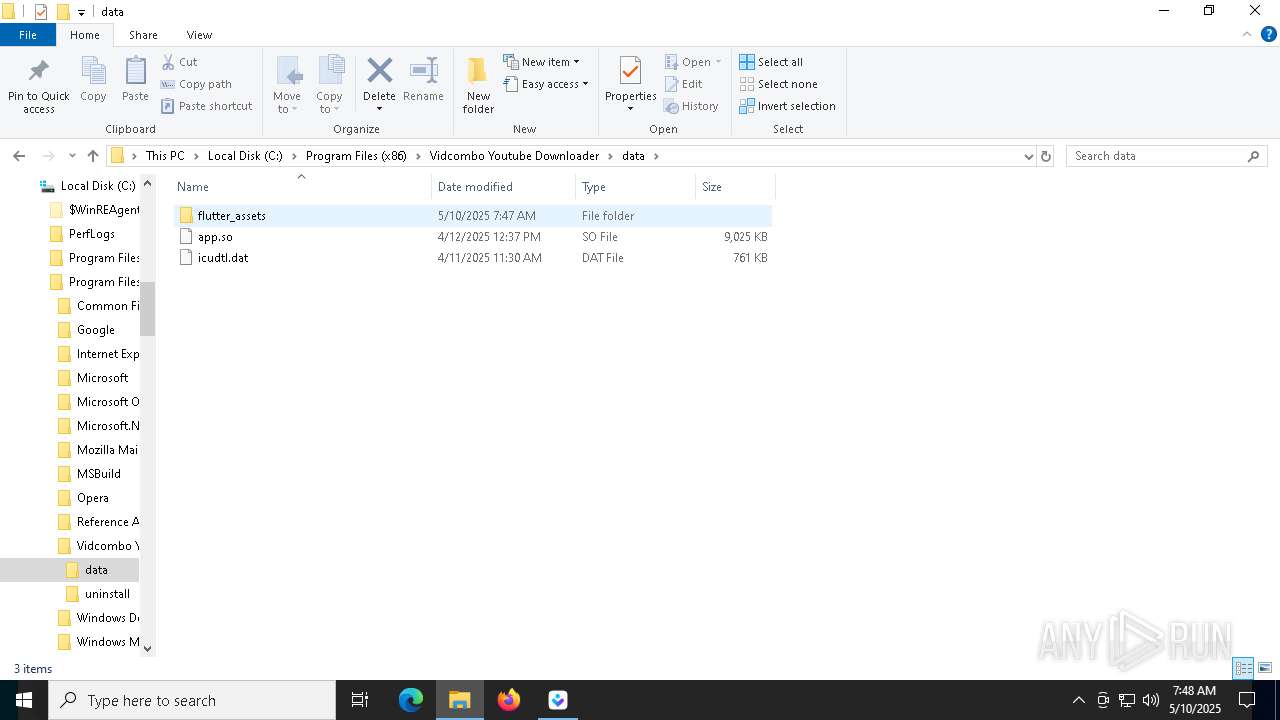
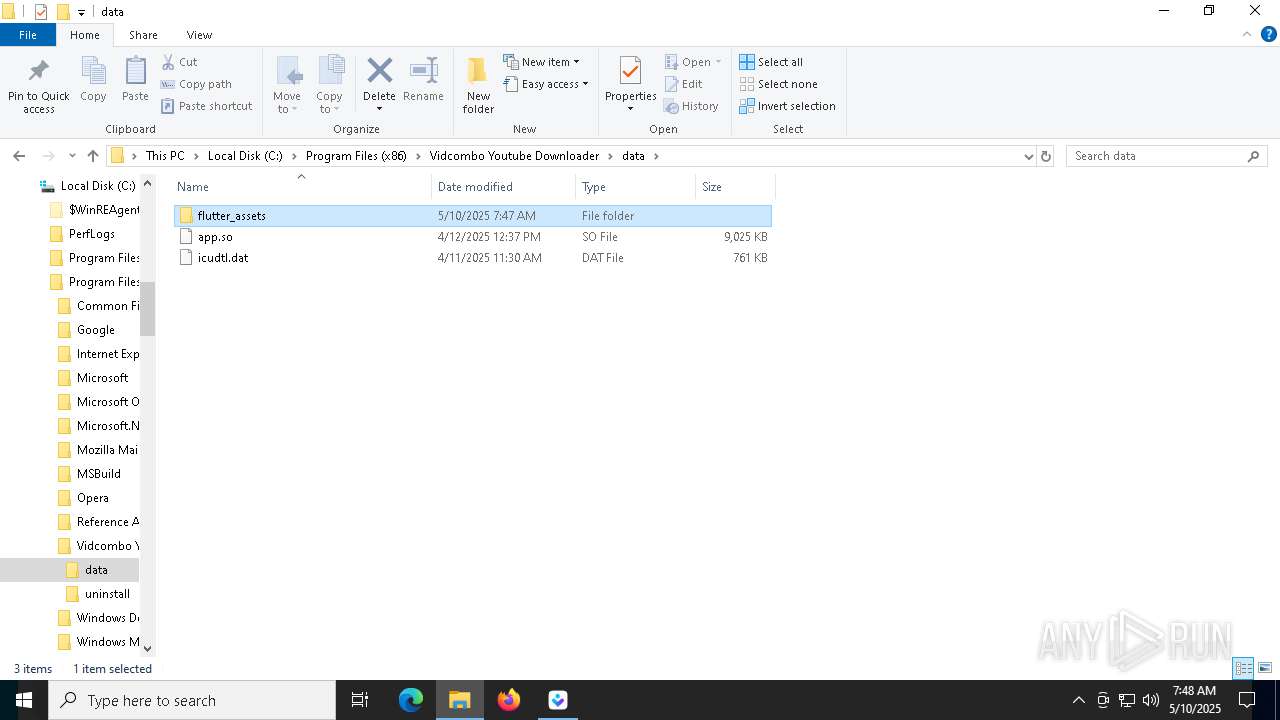
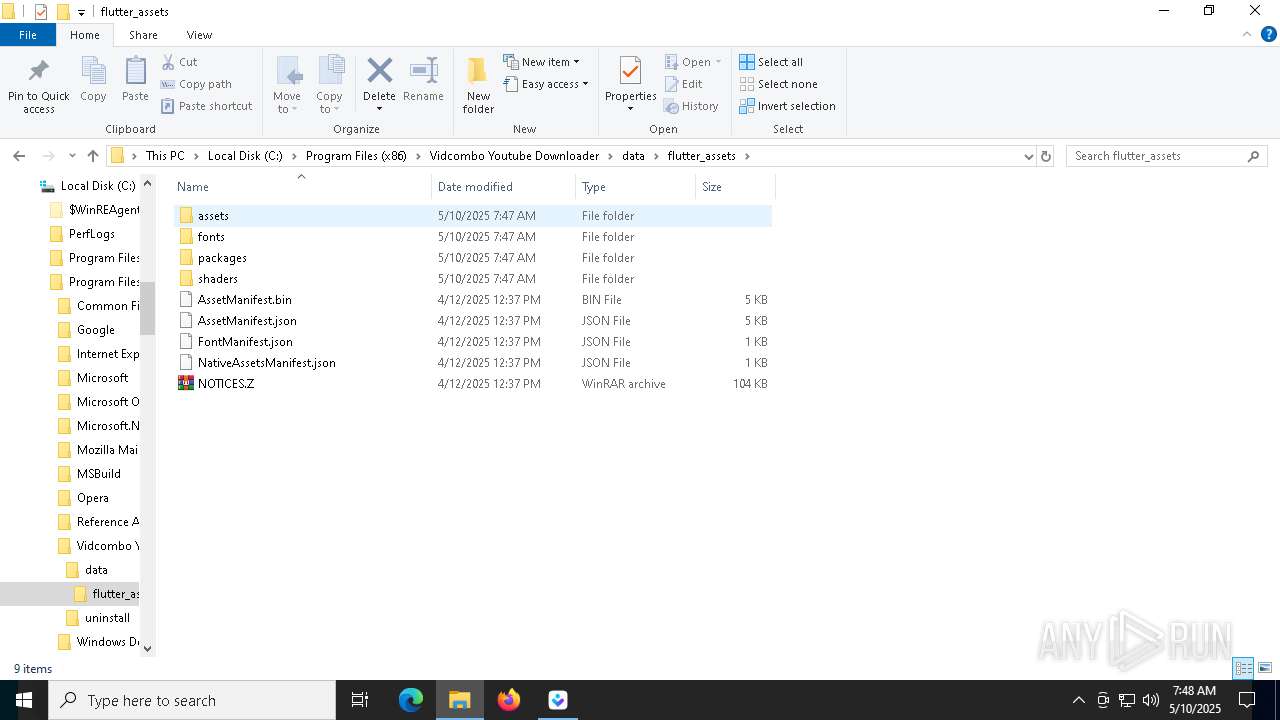
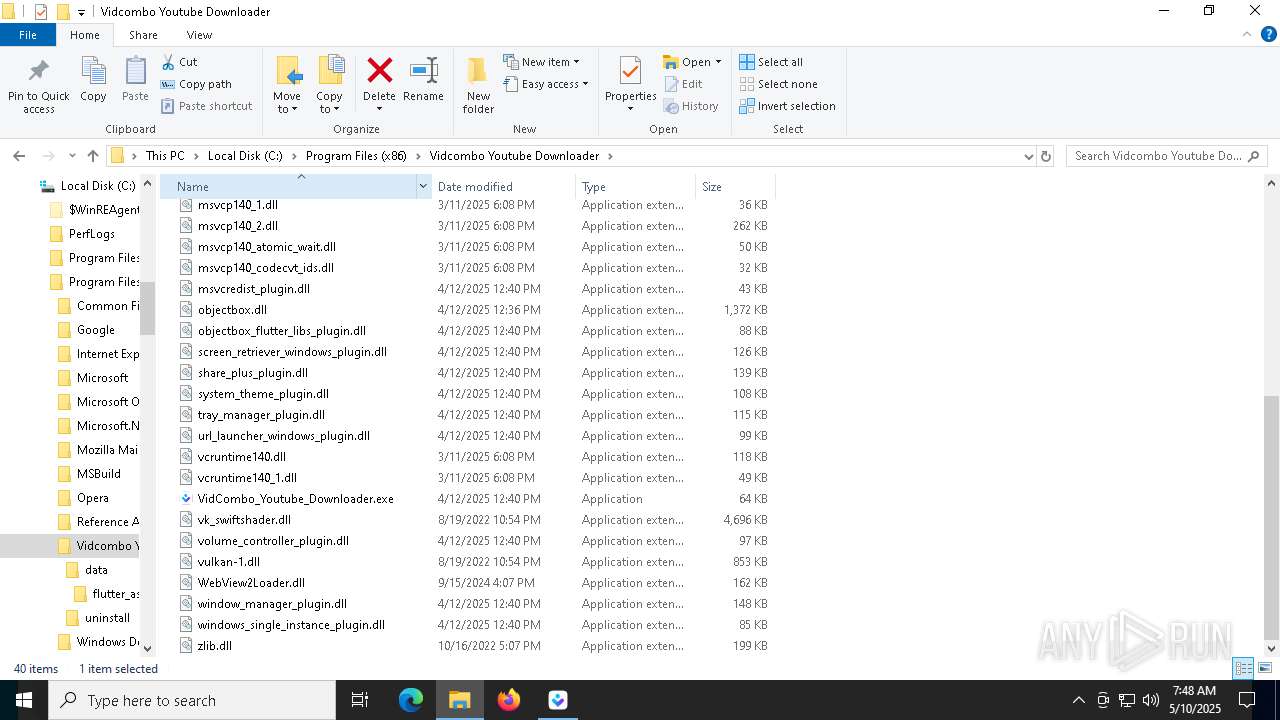
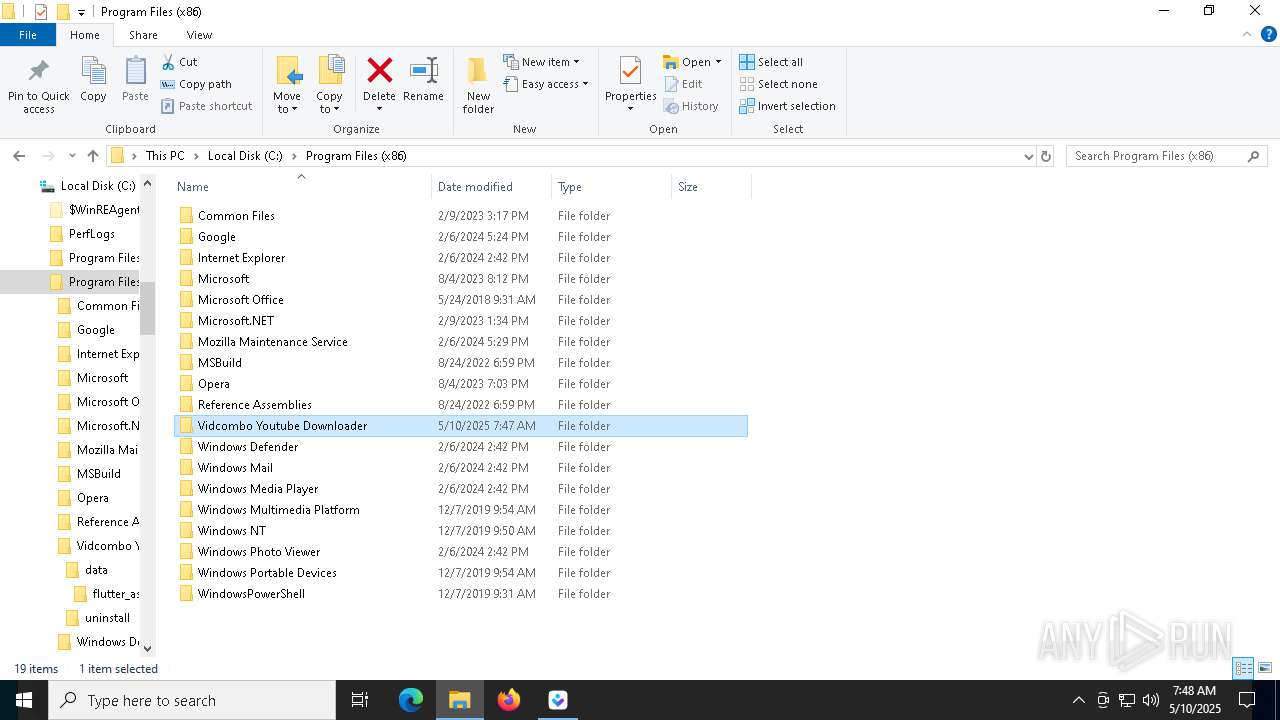
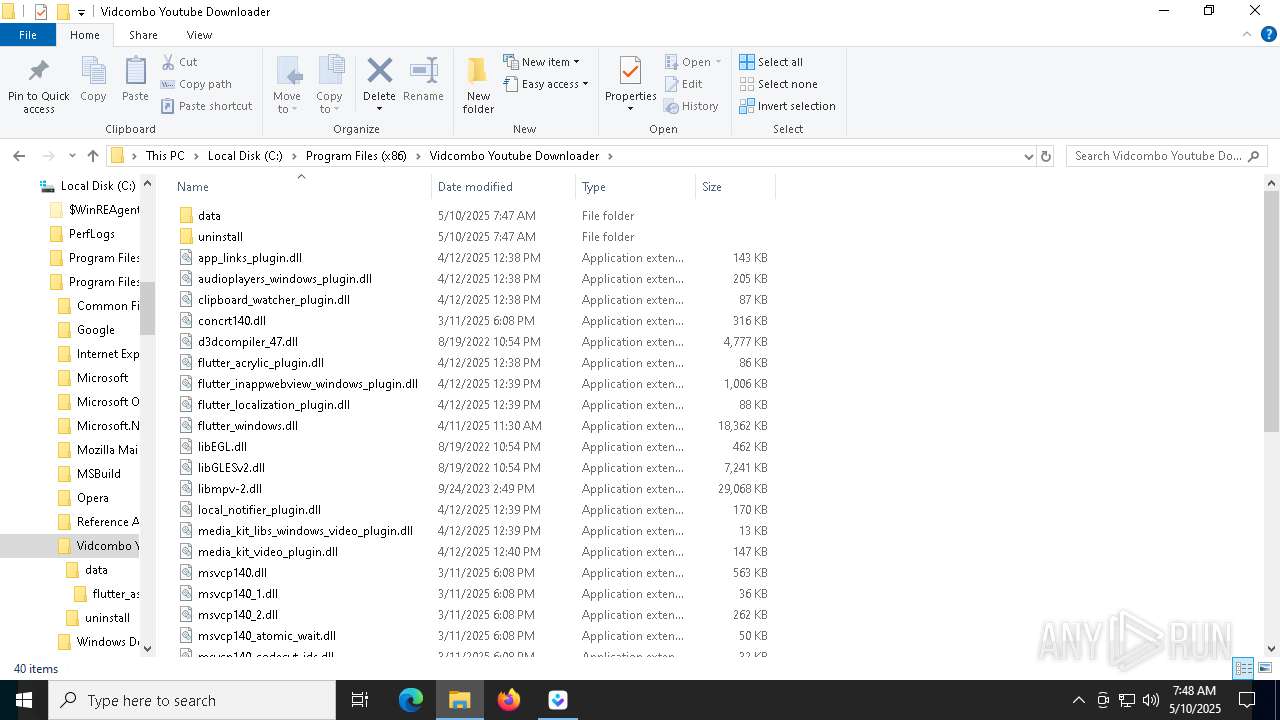
Creates files in the program directory
- vidcombo_1.3.0v2.tmp (PID: 8236)
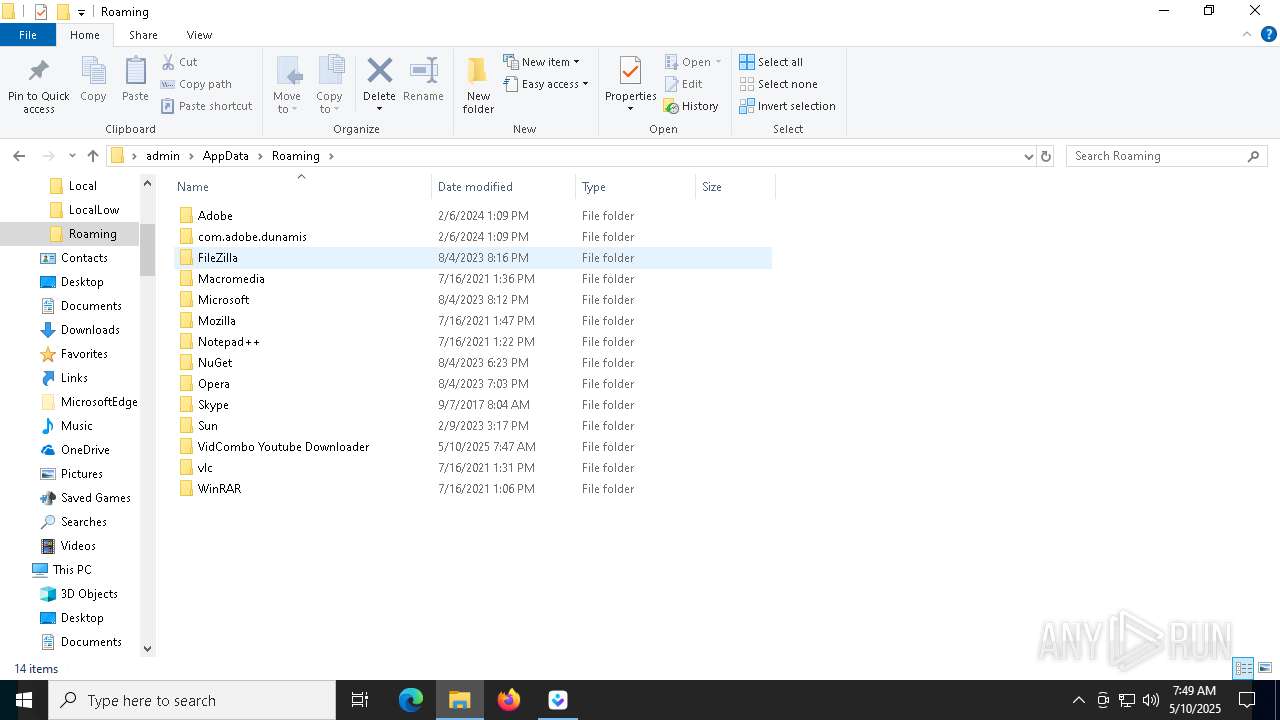
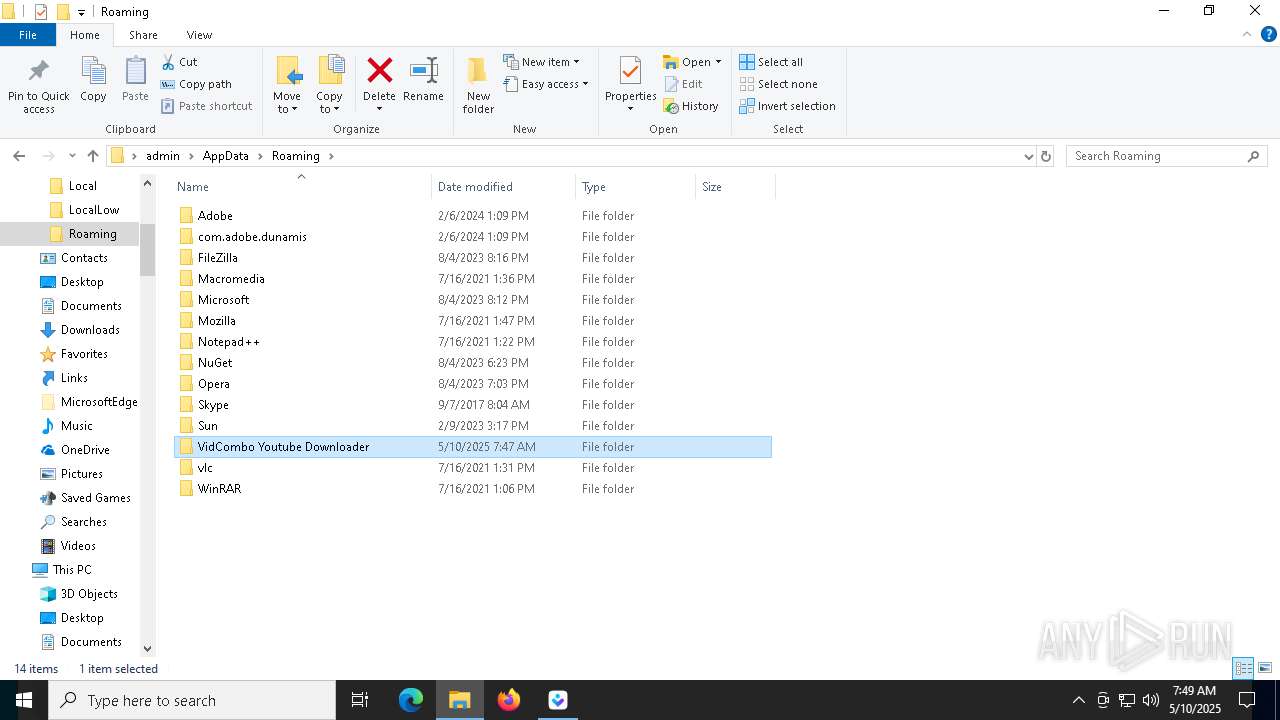
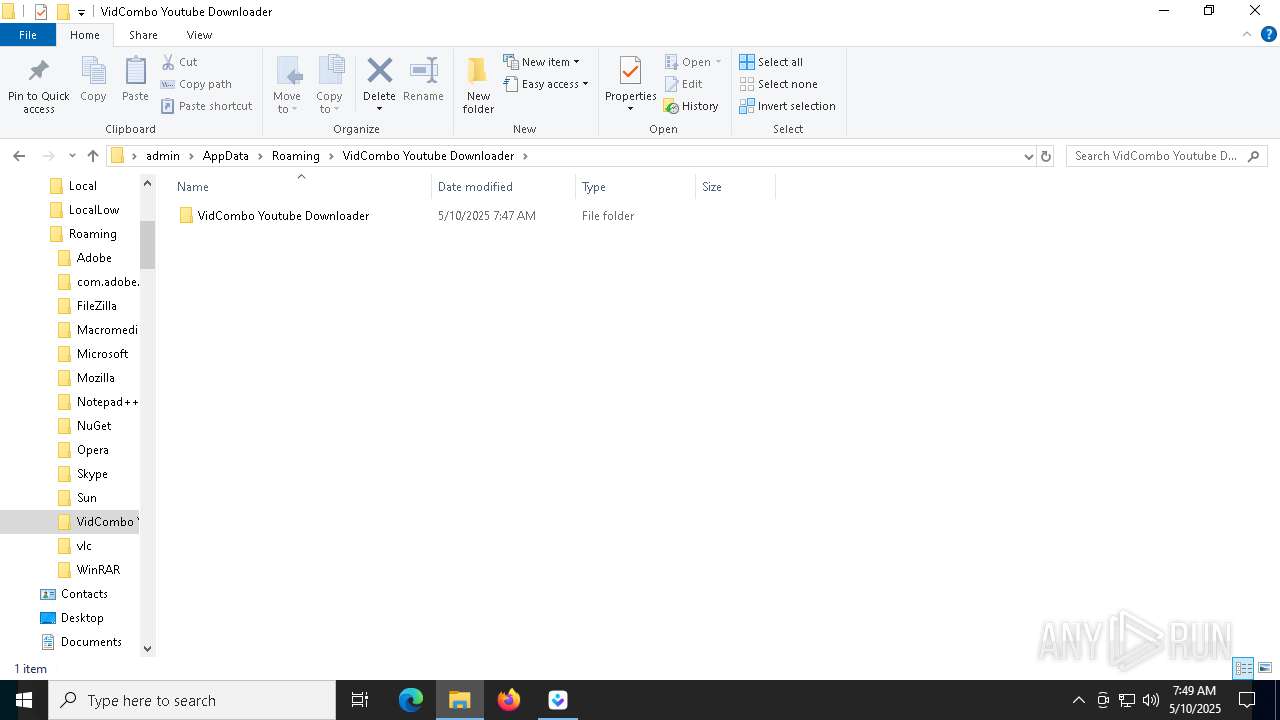
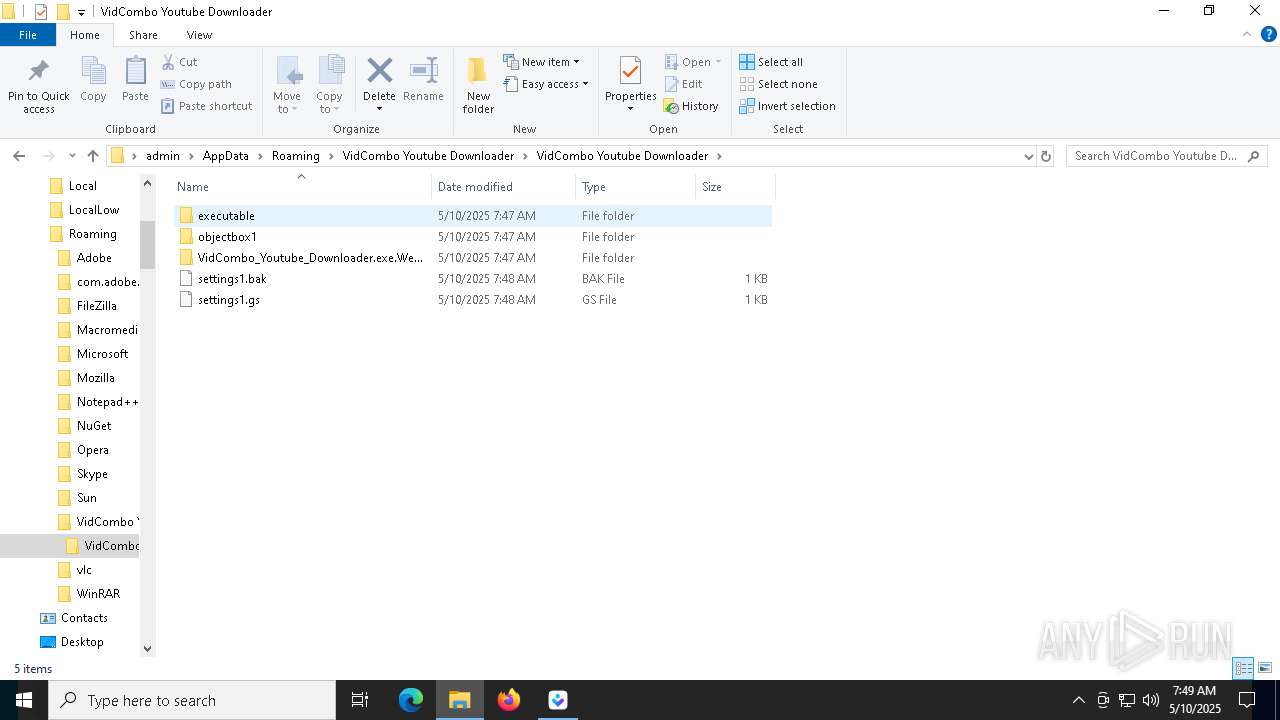
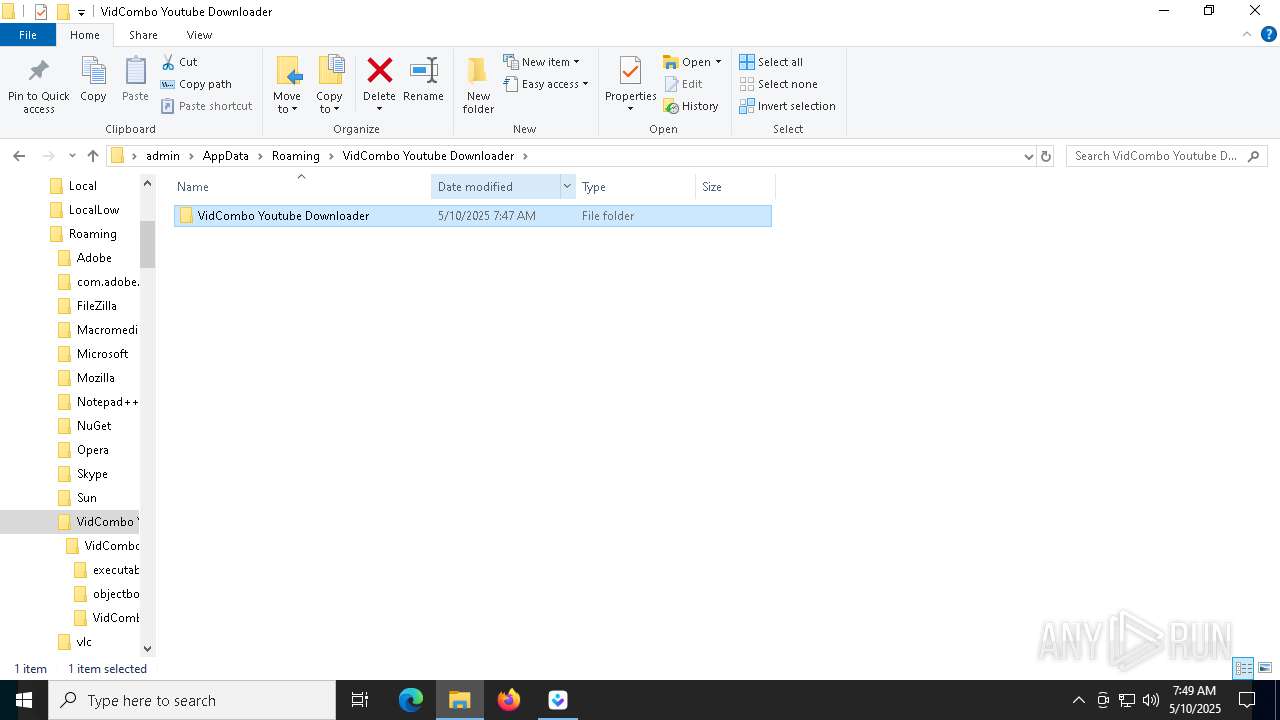
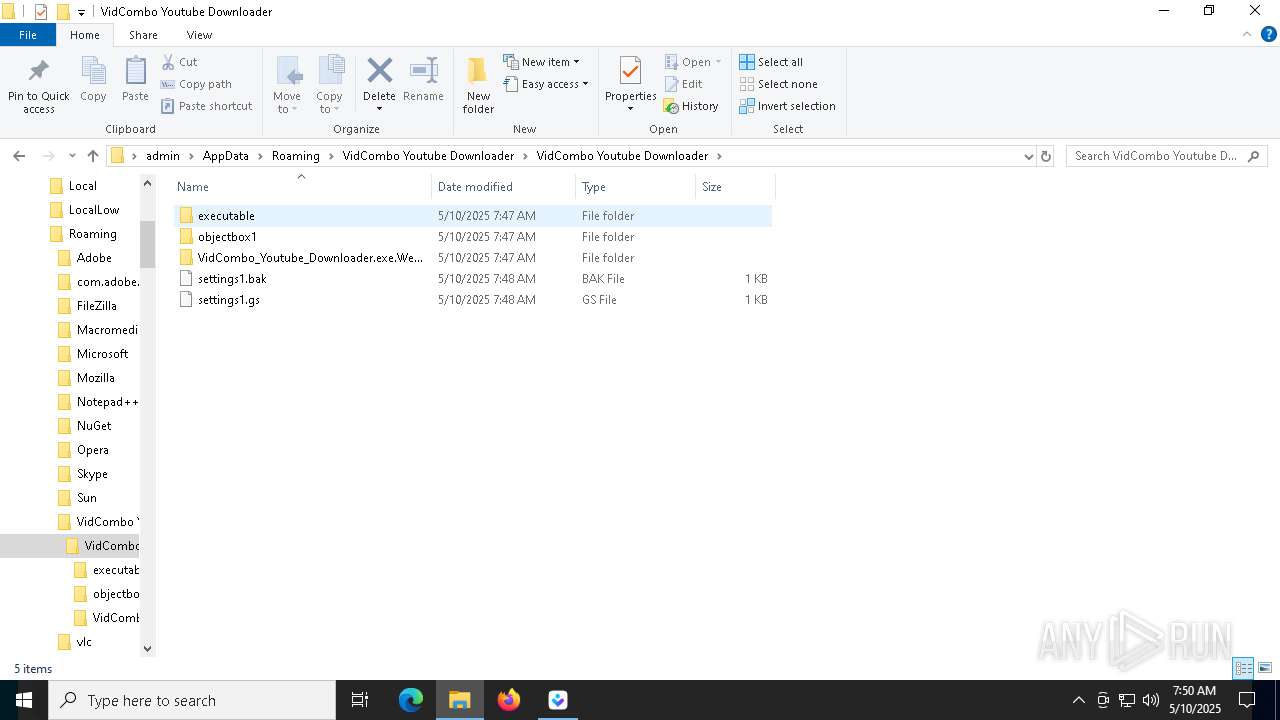
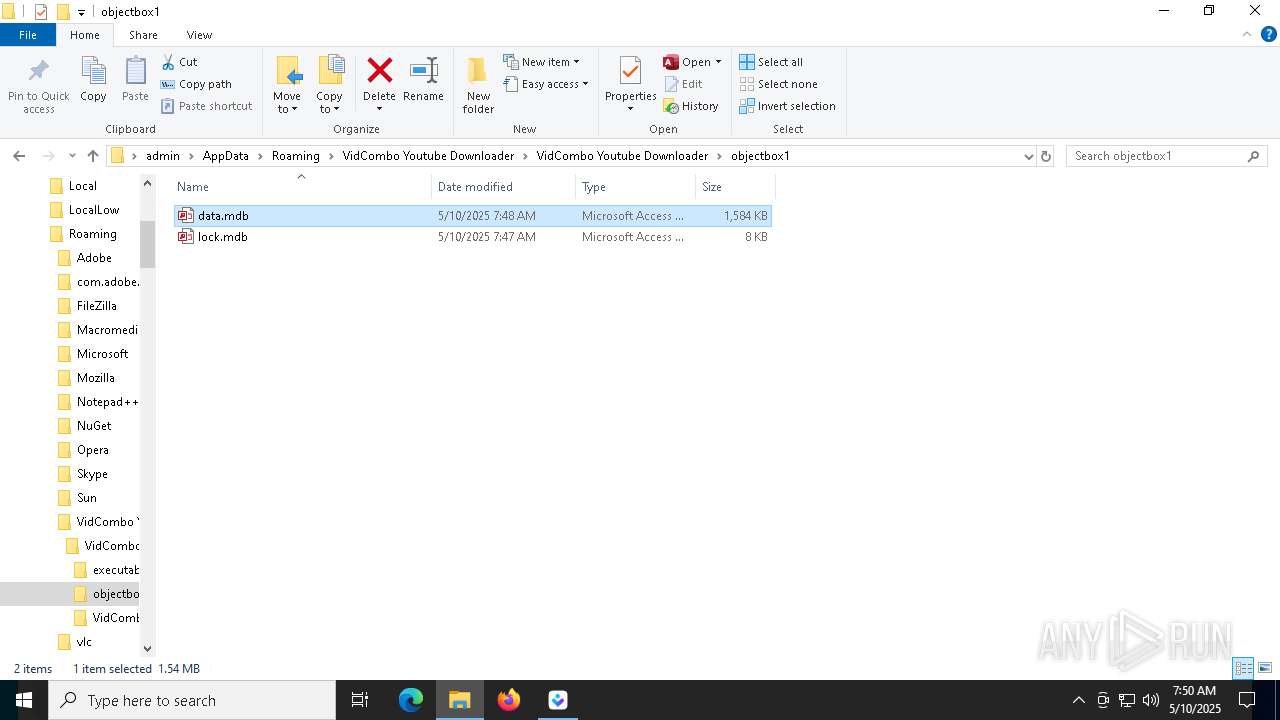
Creates files or folders in the user directory
- VidCombo_Youtube_Downloader.exe (PID: 8740)
- VidCombo_Youtube_Downloader.exe (PID: 5984)
- WerFault.exe (PID: 1240)
The sample compiled with english language support
- vidcombo_1.3.0v2.tmp (PID: 8236)
- VidCombo_Youtube_Downloader.exe (PID: 8740)
- yt-dlp.exe (PID: 7844)
- yt-dlp.exe (PID: 9032)
Detects InnoSetup installer (YARA)
- vidcombo_1.3.0v2.exe (PID: 9092)
Compiled with Borland Delphi (YARA)
- vidcombo_1.3.0v2.exe (PID: 9092)
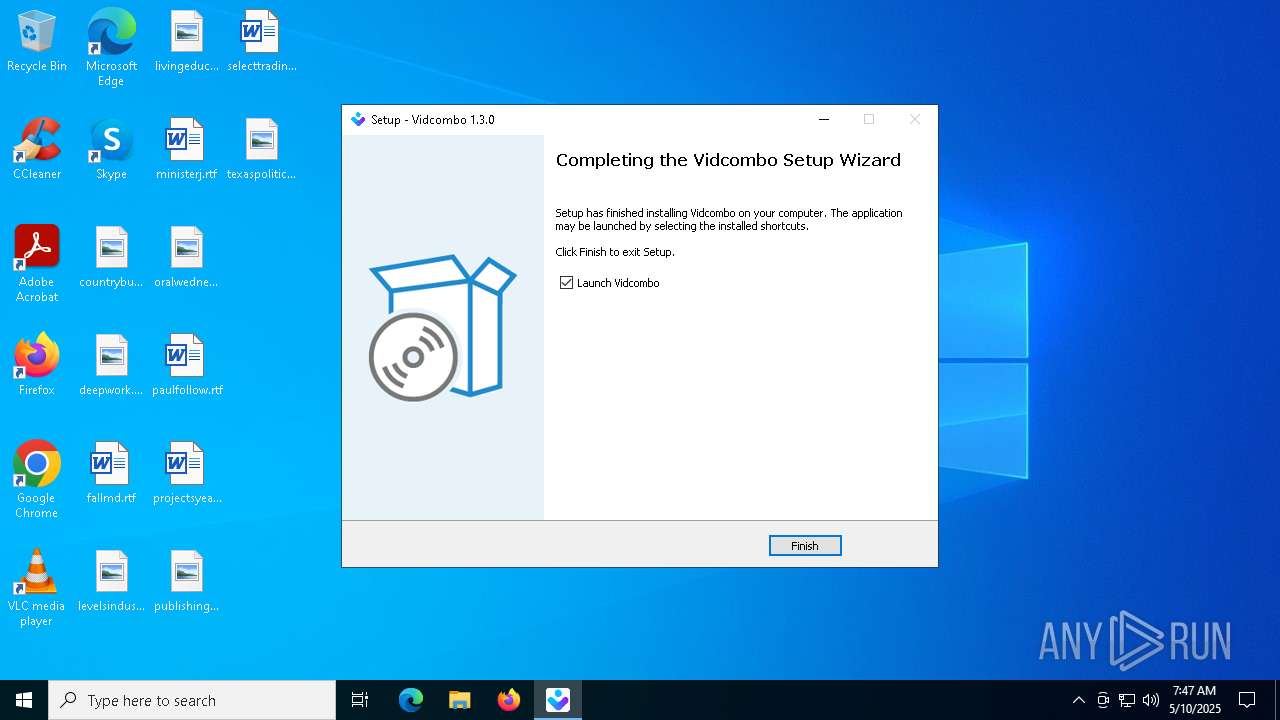
Creates a software uninstall entry
- vidcombo_1.3.0v2.tmp (PID: 8236)
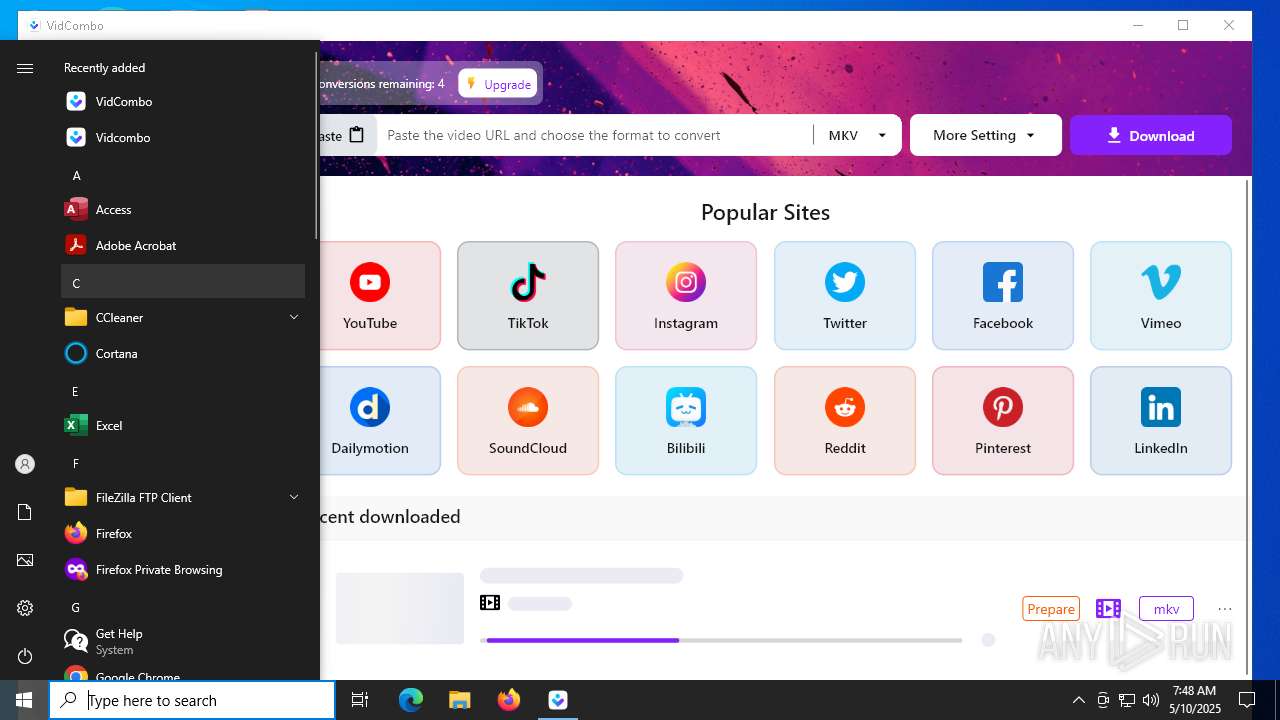
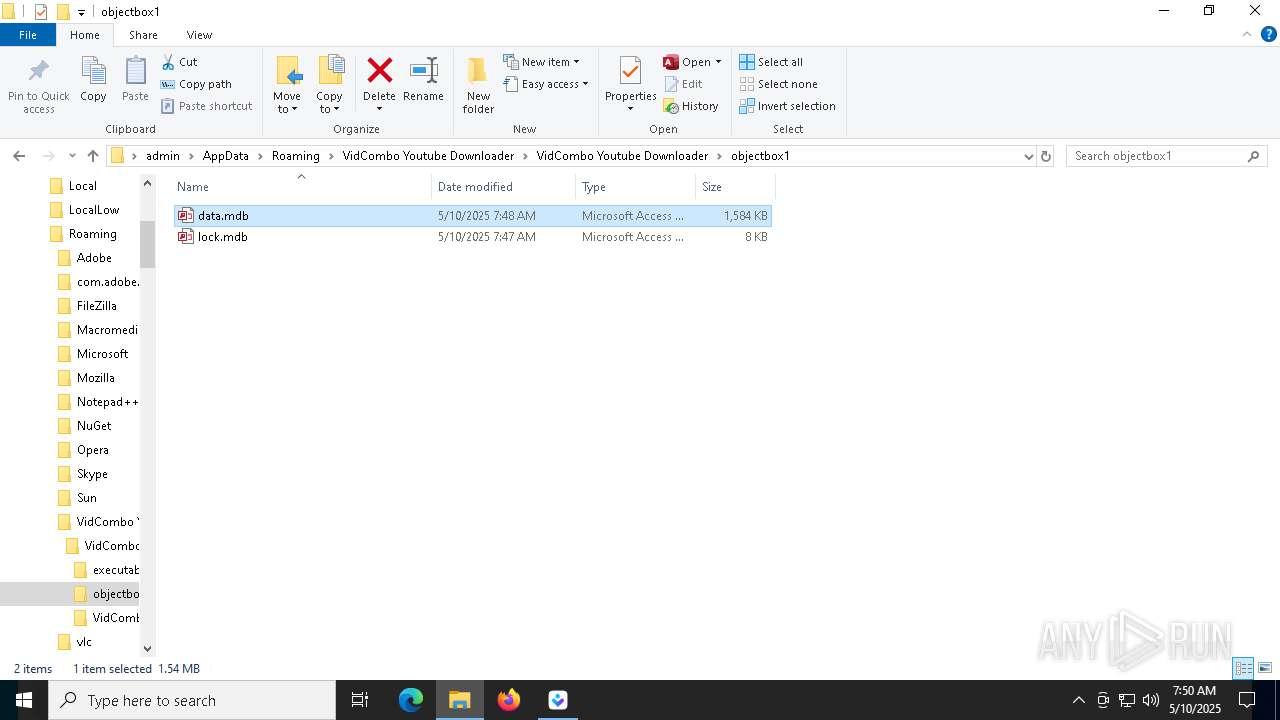
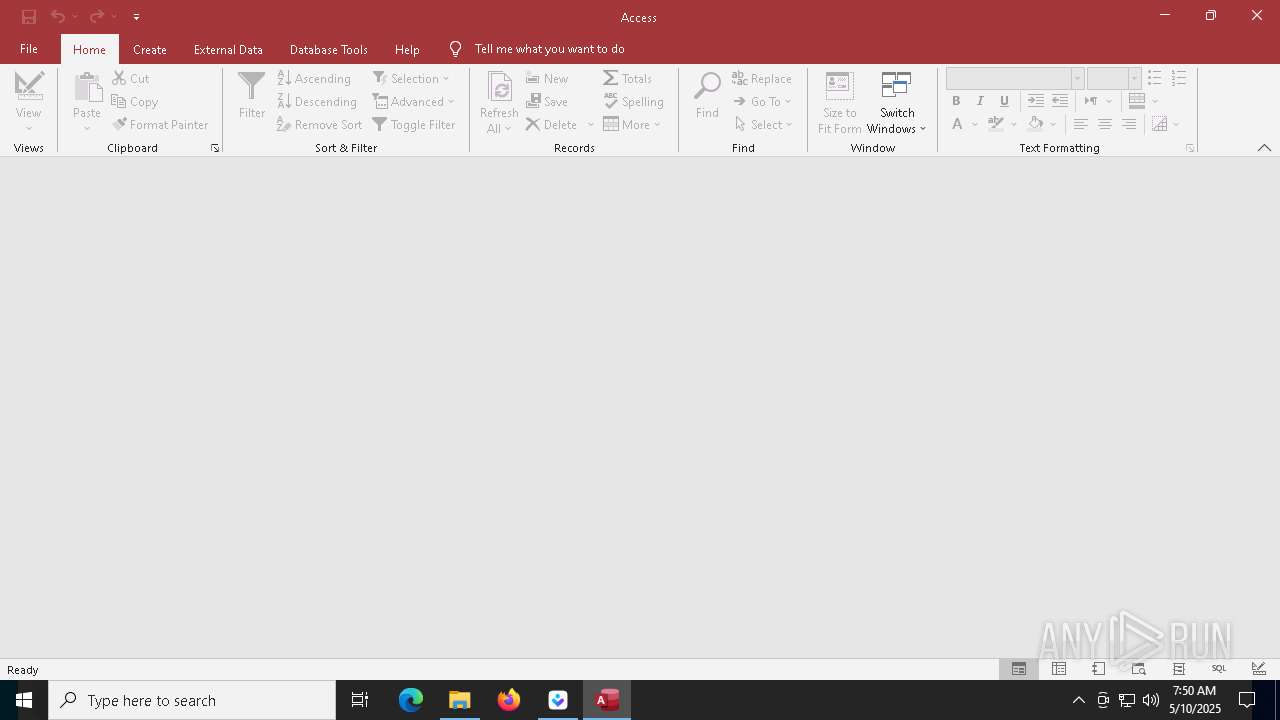
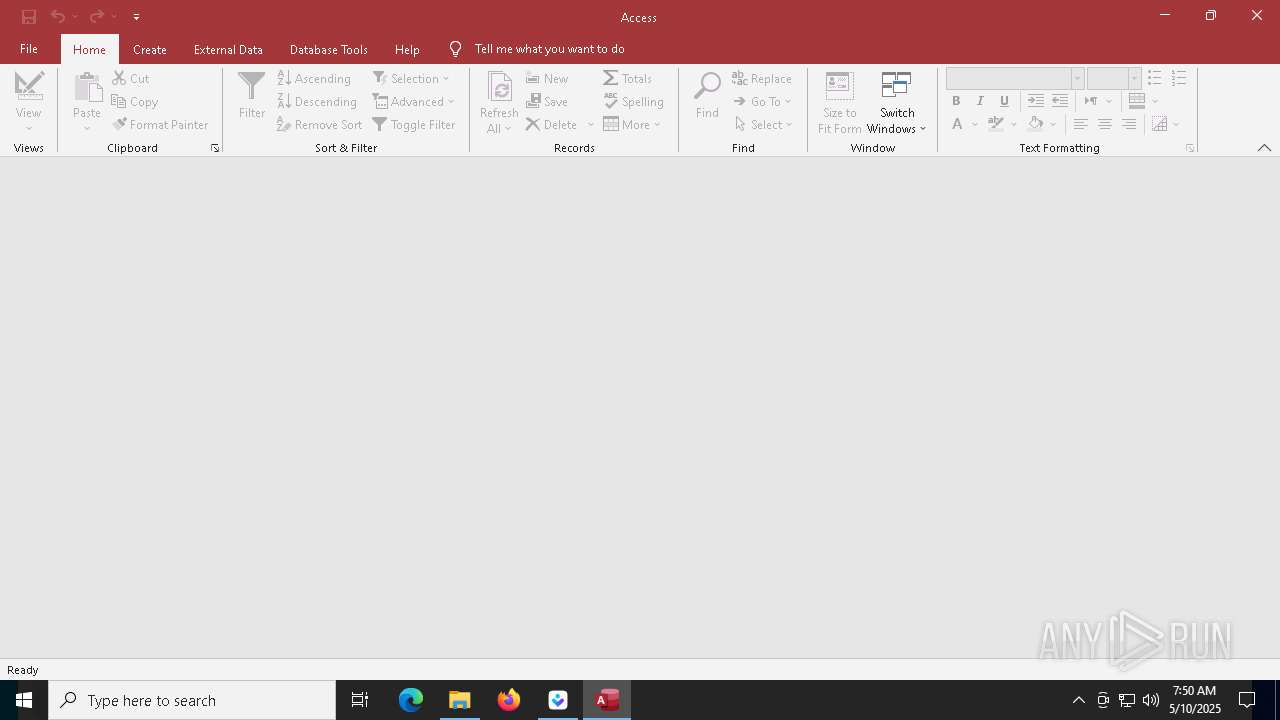
Manual execution by a user
- VidCombo_Youtube_Downloader.exe (PID: 8740)
- MSACCESS.EXE (PID: 7680)
Reads Windows Product ID
- VidCombo_Youtube_Downloader.exe (PID: 8740)
Reads product name
- VidCombo_Youtube_Downloader.exe (PID: 8740)
Reads security settings of Internet Explorer
- WMIC.exe (PID: 6964)
- WMIC.exe (PID: 2316)
- WMIC.exe (PID: 8992)
Reads the software policy settings
- slui.exe (PID: 8320)
Checks operating system version
- yt-dlp.exe (PID: 8152)
- yt-dlp.exe (PID: 4040)
Reads Environment values
- VidCombo_Youtube_Downloader.exe (PID: 8740)
PyInstaller has been detected (YARA)
- yt-dlp.exe (PID: 9032)
- yt-dlp.exe (PID: 4040)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
197
Monitored processes
52
Malicious processes
6
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1180 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1240 | C:\WINDOWS\system32\WerFault.exe -u -p 5984 -s 1728 | C:\Windows\System32\WerFault.exe | — | VidCombo_Youtube_Downloader.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2316 | wmic OS get Version /VALUE | C:\Windows\System32\wbem\WMIC.exe | — | VidCombo_Youtube_Downloader.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: WMI Commandline Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2560 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | WMIC.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3896 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | taskkill.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
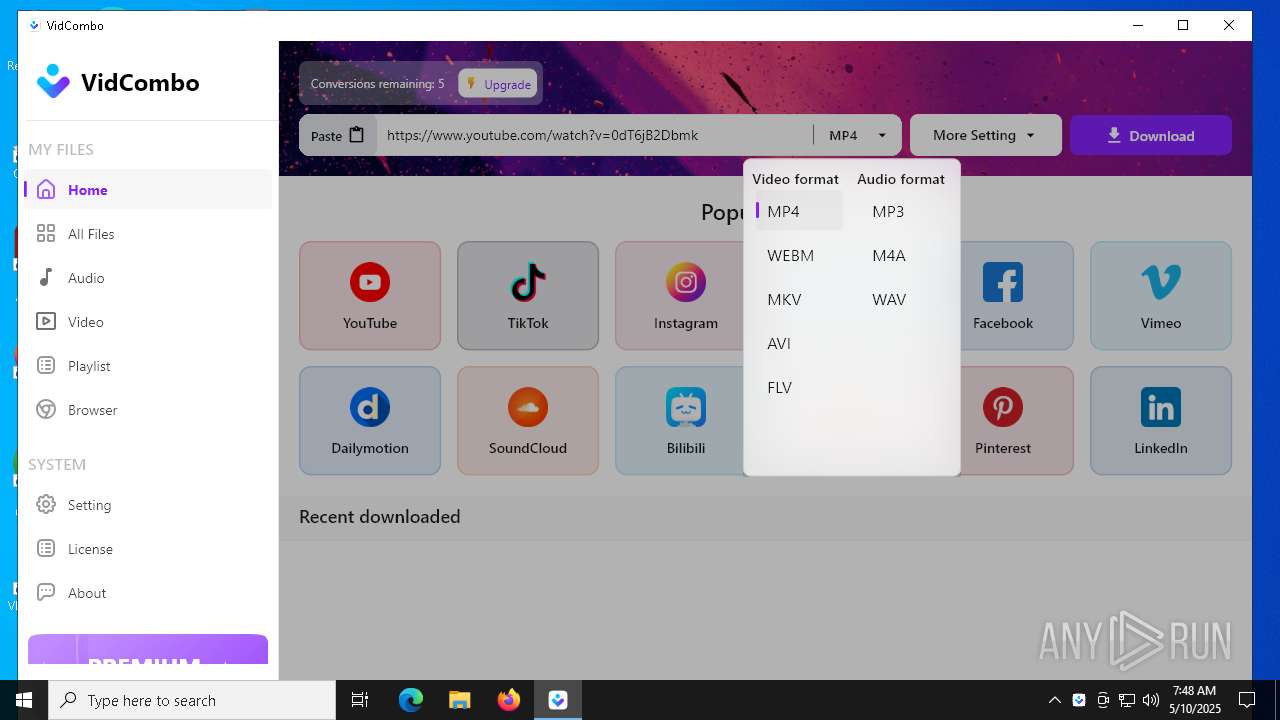
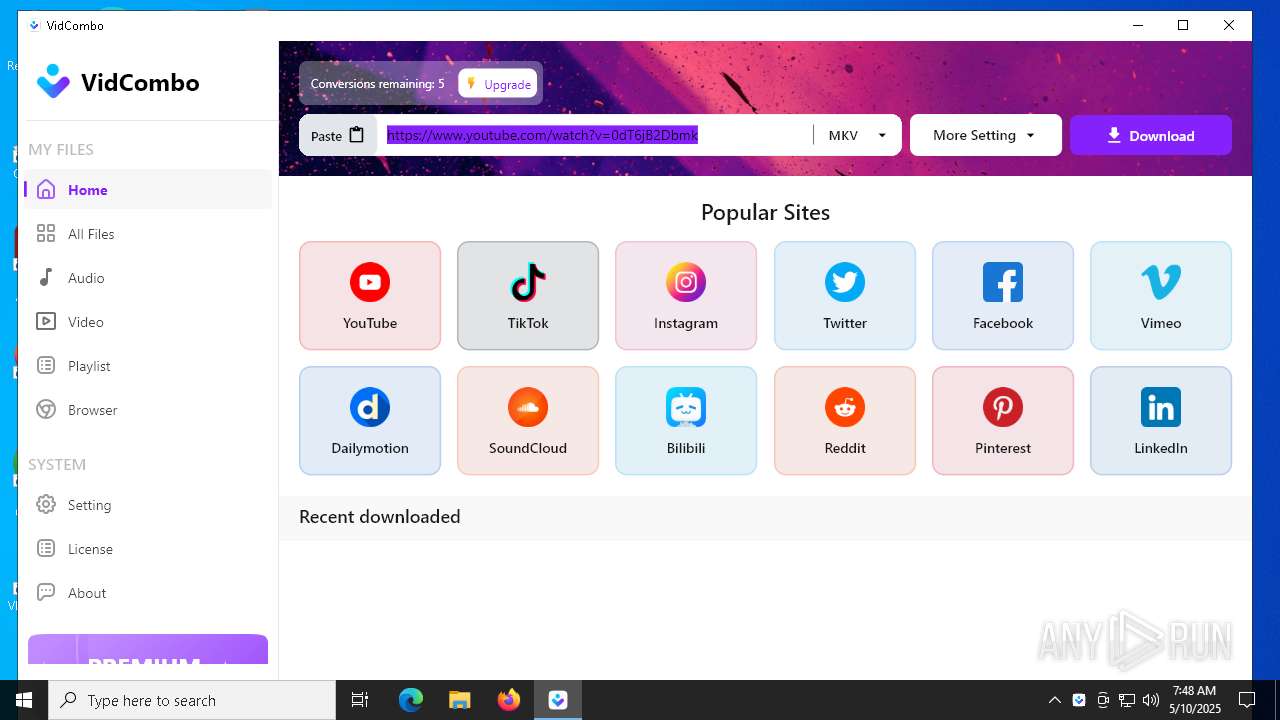
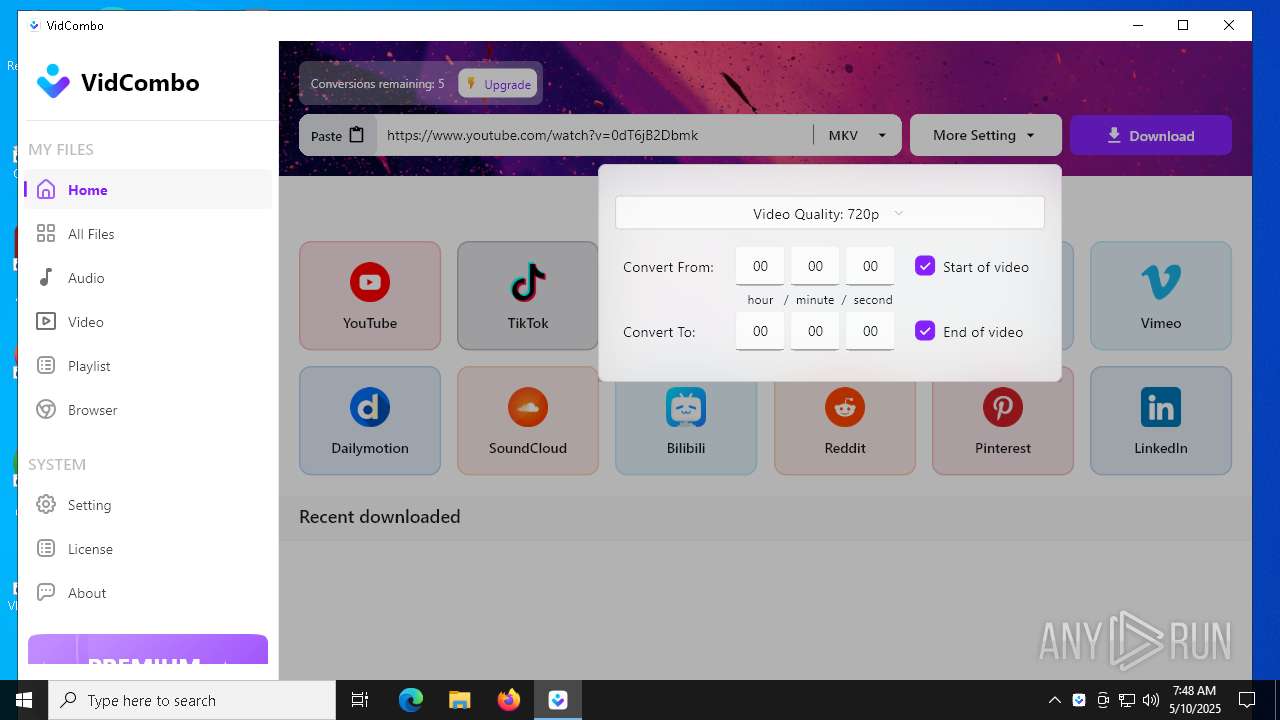
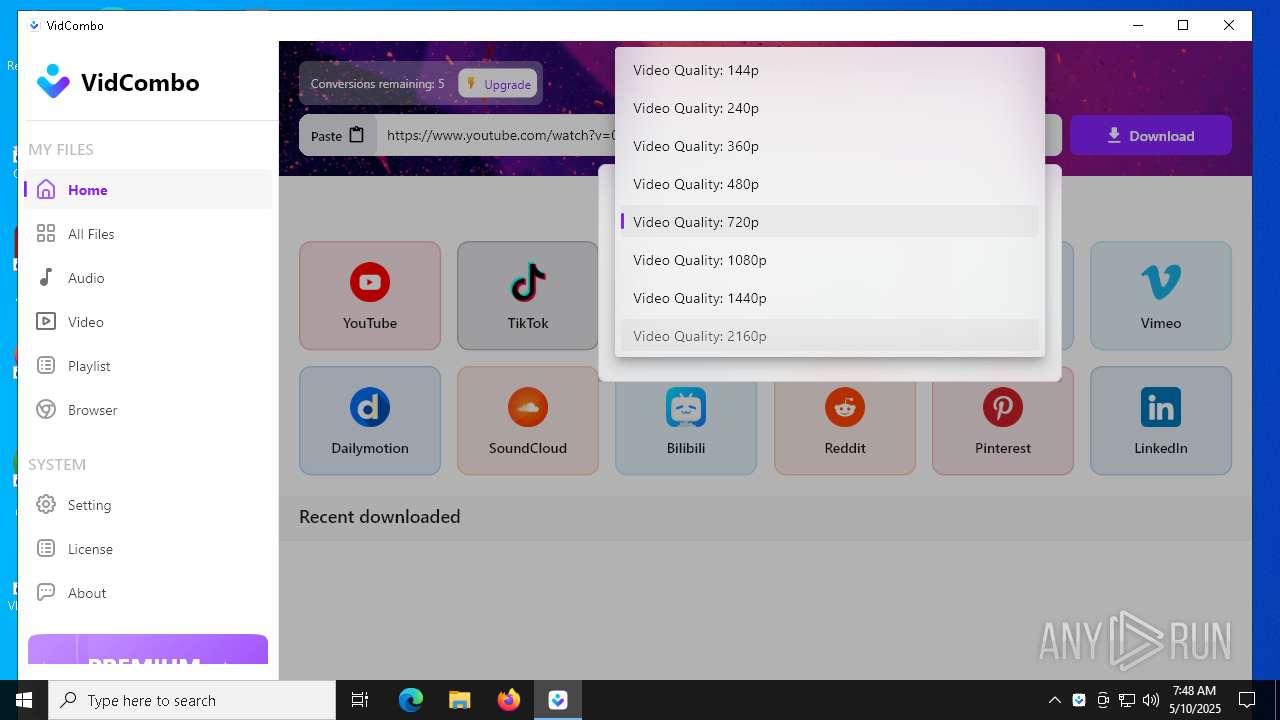
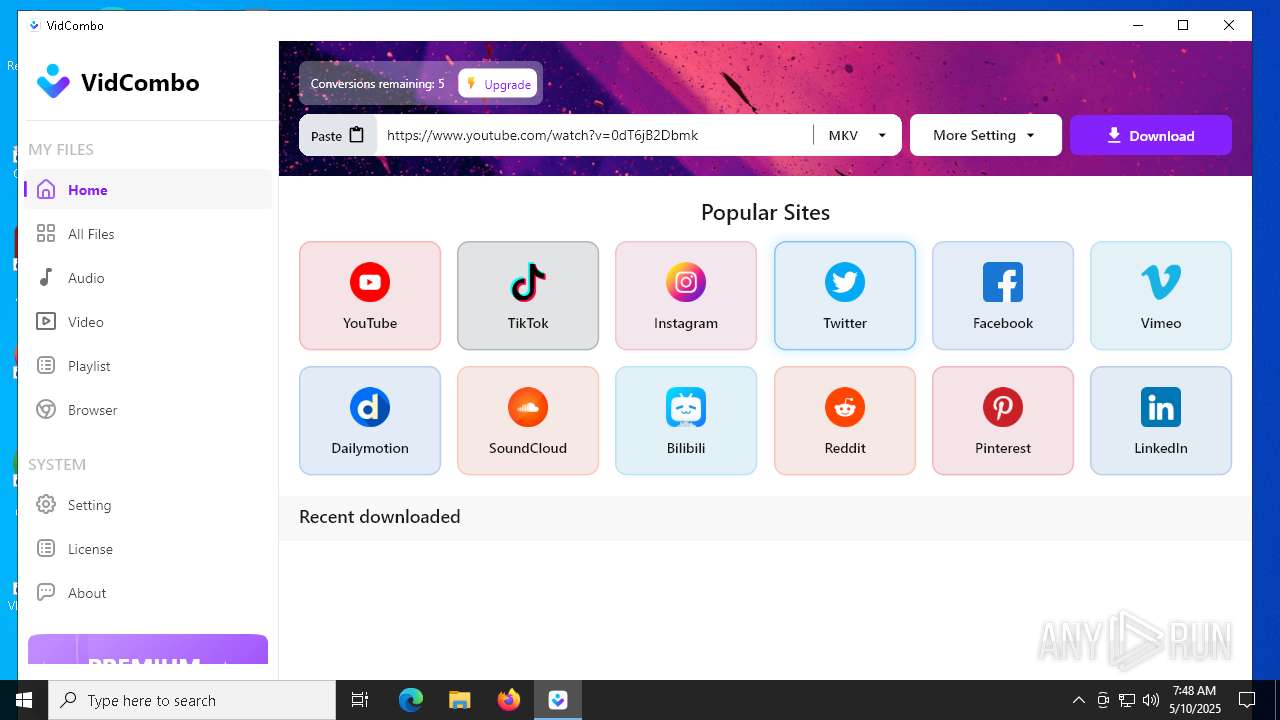
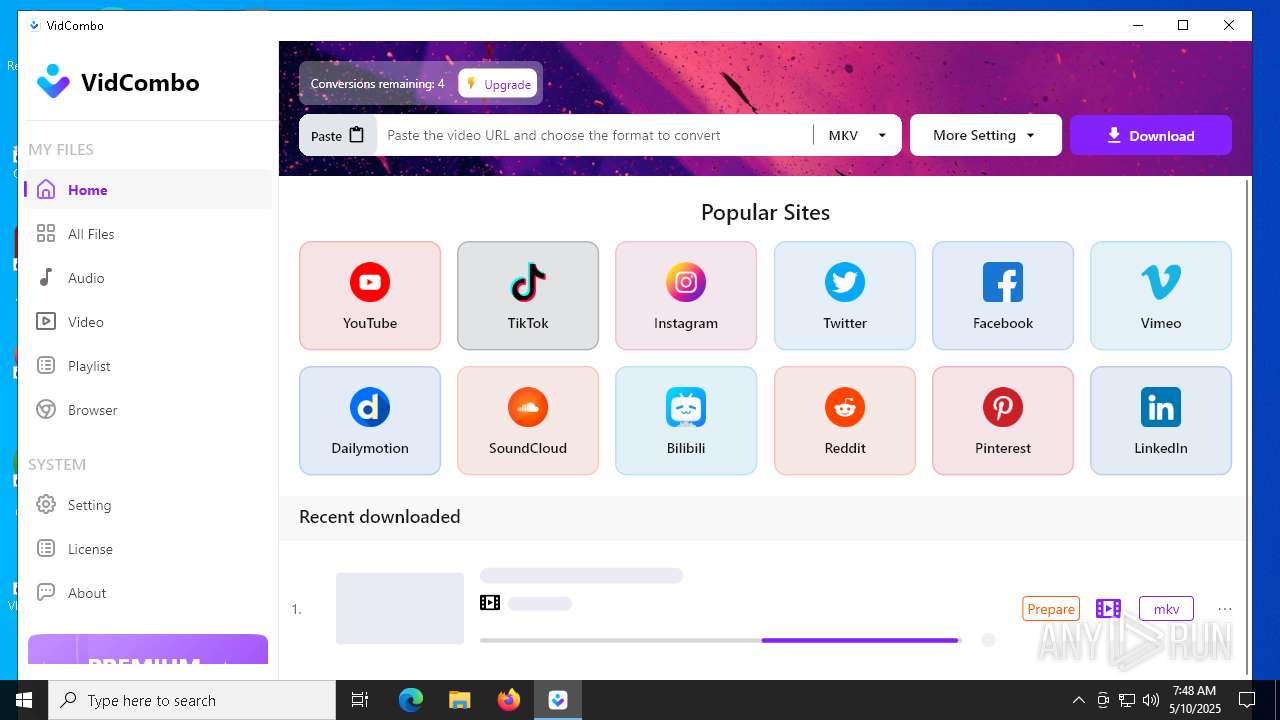
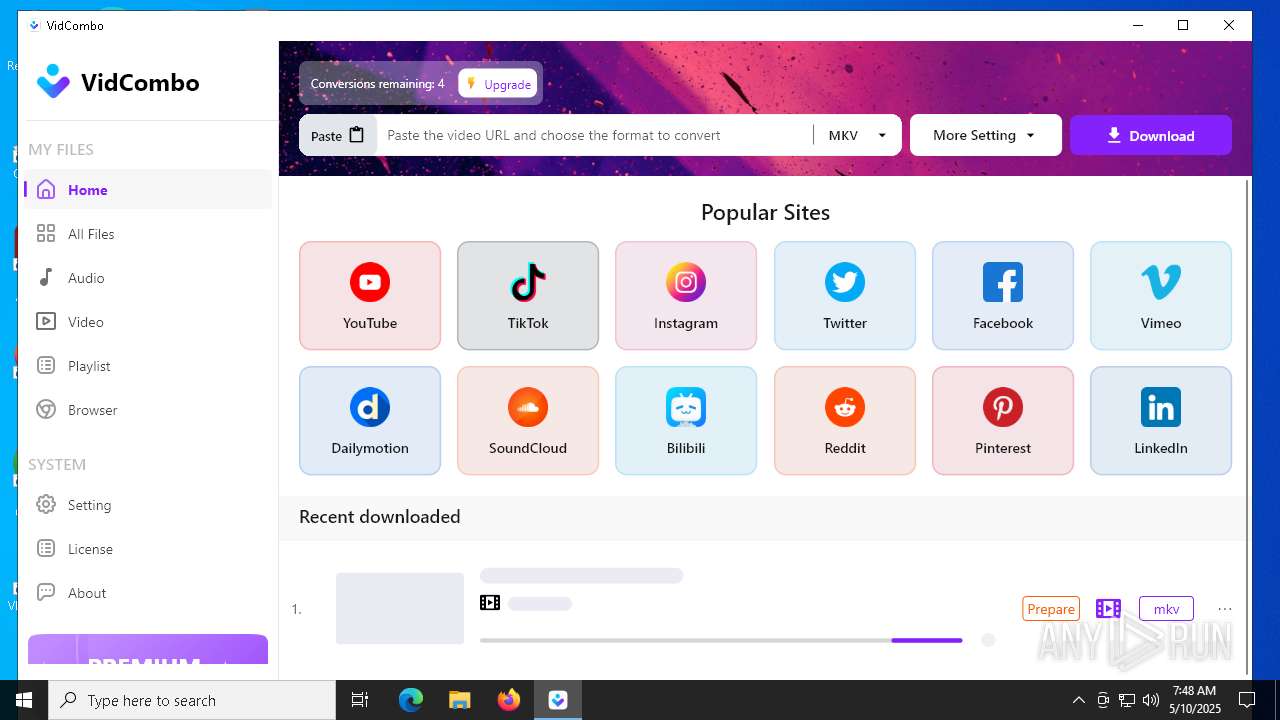
| 4040 | "C:\Users\admin\AppData\Roaming\VidCombo Youtube Downloader\VidCombo Youtube Downloader\executable\yt-dlp.exe" --load-info-json C:\Users\admin\Documents\VidCombo\1\meta.info.json -f bv*[ext=mp4]+ba[ext=m4a]/b -S +res:1080,ext,proto --recode-video mkv -o C:\Users\admin\Documents\VidCombo\1\input.%(ext)s --ffmpeg-location "C:\Users\admin\AppData\Roaming\VidCombo Youtube Downloader\VidCombo Youtube Downloader\executable\ffmpeg.exe" https://www.youtube.com/watch?v=0dT6jB2Dbmk --no-playlist | C:\Users\admin\AppData\Roaming\VidCombo Youtube Downloader\VidCombo Youtube Downloader\executable\yt-dlp.exe | yt-dlp.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 4724 | "C:\WINDOWS\system32\cmd.exe" /C taskkill /F /IM VidCombo_Youtube_Downloader.exe /T | C:\Windows\SysWOW64\cmd.exe | — | vidcombo_1.3.0v2.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 128 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
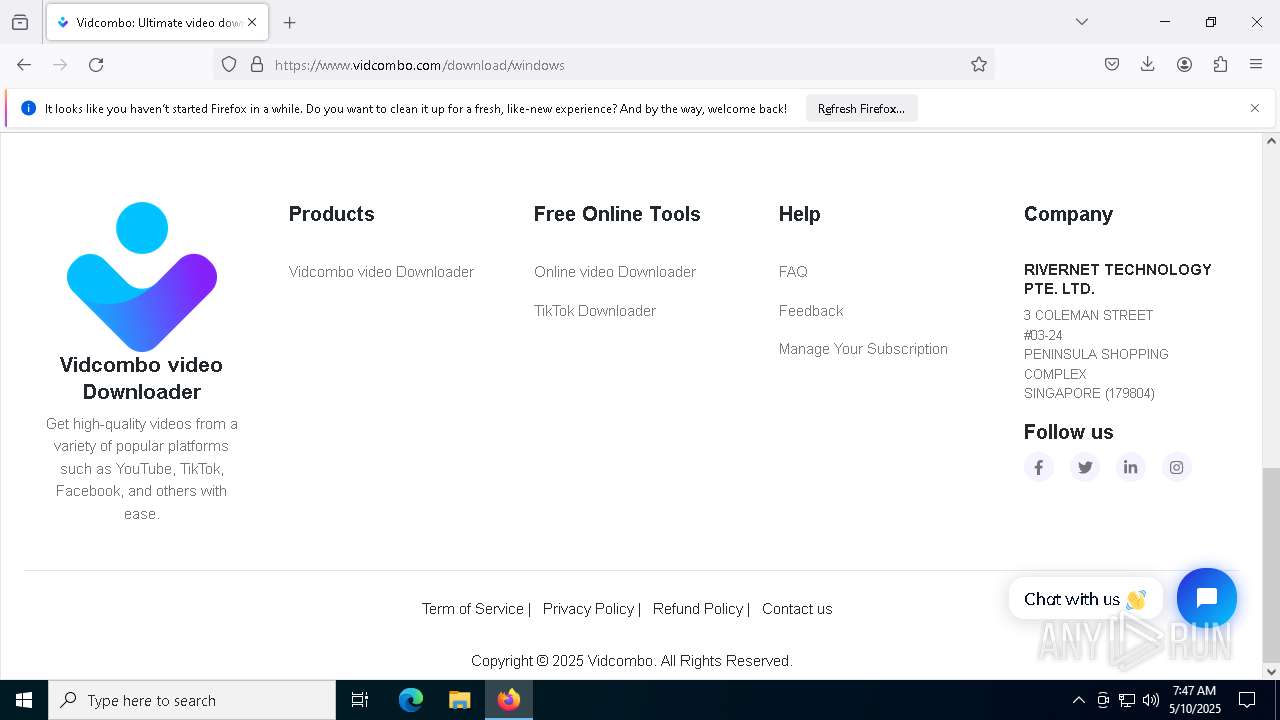
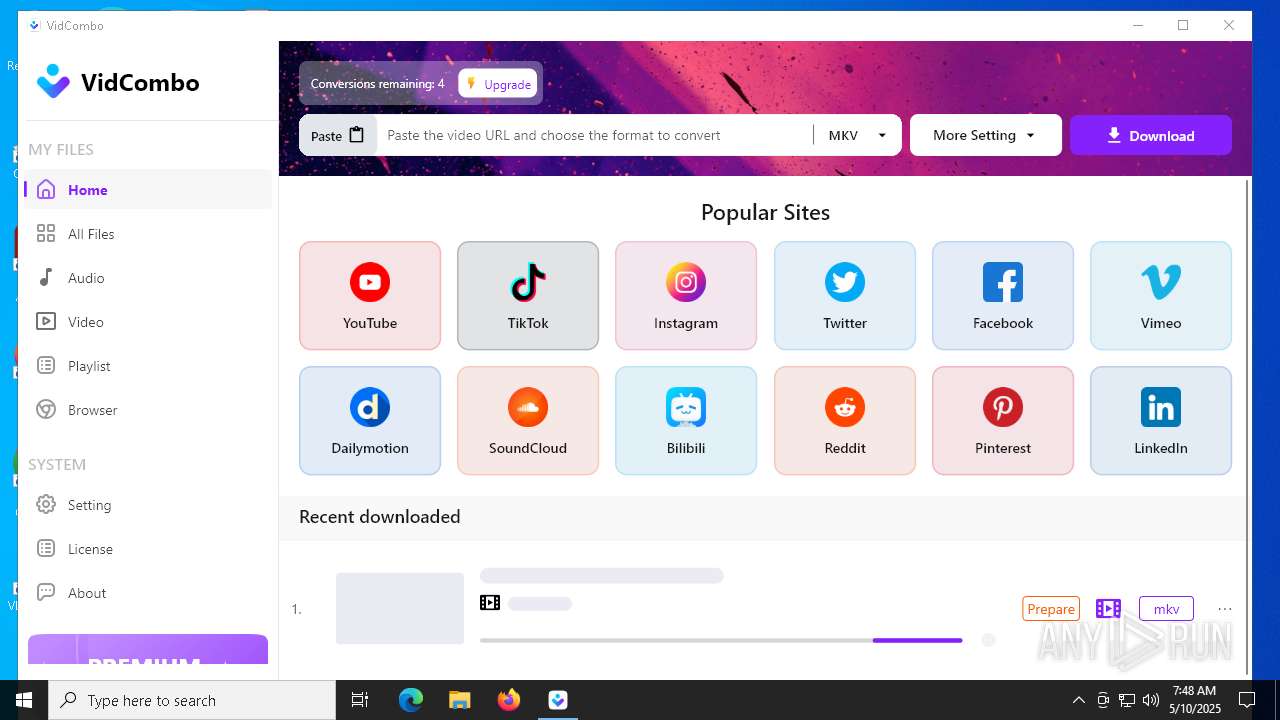
| 5048 | "C:\Program Files\Mozilla Firefox\firefox.exe" https://www.vidcombo.com/ | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 5408 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | WMIC.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5984 | "C:\Program Files (x86)\Vidcombo Youtube Downloader\VidCombo_Youtube_Downloader.exe" | C:\Program Files (x86)\Vidcombo Youtube Downloader\VidCombo_Youtube_Downloader.exe | vidcombo_1.3.0v2.tmp | ||||||||||||
User: admin Company: VidCombo Youtube Downloader Integrity Level: MEDIUM Description: VidCombo Youtube Downloader Exit code: 3221225477 Version: 1.3.0+1 Modules
| |||||||||||||||
Total events
32 254
Read events
31 842
Write events
378
Delete events
34
Modification events
| (PID) Process: | (5048) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\DllPrefetchExperiment |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe |
Value: 0 | |||
| (PID) Process: | (5048) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | SlowContextMenuEntries |
Value: 6024B221EA3A6910A2DC08002B30309D0A010000BD0E0C47735D584D9CEDE91E22E23282770100000114020000000000C0000000000000468D0000006078A409B011A54DAFA526D86198A780390100009AD298B2EDA6DE11BA8CA68E55D895936E000000 | |||
| (PID) Process: | (8236) vidcombo_1.3.0v2.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{C6BC5050-3D98-47F7-8F1E-3DC53963381A}_is1 |
| Operation: | write | Name: | MinorVersion |
Value: 3 | |||
| (PID) Process: | (8236) vidcombo_1.3.0v2.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{C6BC5050-3D98-47F7-8F1E-3DC53963381A}_is1 |
| Operation: | write | Name: | VersionMajor |
Value: 1 | |||
| (PID) Process: | (8236) vidcombo_1.3.0v2.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{C6BC5050-3D98-47F7-8F1E-3DC53963381A}_is1 |
| Operation: | write | Name: | VersionMinor |
Value: 3 | |||
| (PID) Process: | (8236) vidcombo_1.3.0v2.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{C6BC5050-3D98-47F7-8F1E-3DC53963381A}_is1 |
| Operation: | write | Name: | EstimatedSize |
Value: 91886 | |||
| (PID) Process: | (8236) vidcombo_1.3.0v2.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\.myp\OpenWithProgids |
| Operation: | write | Name: | VidcomboFile.myp |
Value: | |||
| (PID) Process: | (8236) vidcombo_1.3.0v2.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{C6BC5050-3D98-47F7-8F1E-3DC53963381A}_is1 |
| Operation: | write | Name: | Inno Setup: Setup Version |
Value: 6.4.2 | |||
| (PID) Process: | (8236) vidcombo_1.3.0v2.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{C6BC5050-3D98-47F7-8F1E-3DC53963381A}_is1 |
| Operation: | write | Name: | Inno Setup: App Path |
Value: C:\Program Files (x86)\Vidcombo Youtube Downloader | |||
| (PID) Process: | (8236) vidcombo_1.3.0v2.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{C6BC5050-3D98-47F7-8F1E-3DC53963381A}_is1 |
| Operation: | write | Name: | InstallLocation |
Value: C:\Program Files (x86)\Vidcombo Youtube Downloader\ | |||
Executable files
316
Suspicious files
237
Text files
200
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5048 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 5048 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\sessionCheckpoints.json | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
| 5048 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\scriptCache-child-current.bin | binary | |
MD5:C95DDC2B1A525D1A243E4C294DA2F326 | SHA256:3A5919E086BFB31E36110CF636D2D5109EB51F2C410B107F126126AB25D67363 | |||
| 5048 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\prefs.js | text | |
MD5:2C99A16AED3906D92FFE3EF1808E2753 | SHA256:08412578CC3BB4922388F8FF8C23962F616B69A1588DA720ADE429129C73C452 | |||
| 5048 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\prefs-1.js | text | |
MD5:2C99A16AED3906D92FFE3EF1808E2753 | SHA256:08412578CC3BB4922388F8FF8C23962F616B69A1588DA720ADE429129C73C452 | |||
| 5048 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite | — | |
MD5:— | SHA256:— | |||
| 5048 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\SiteSecurityServiceState.bin | binary | |
MD5:BAD406480E50FEC8956978F7FE331991 | SHA256:AA07E227121171B851F7202696A0C00ACB3390A7B8FC222EC81D44FAAD5B9F2C | |||
| 5048 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3561288849sdhlie.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 5048 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\datareporting\glean\db\data.safe.bin | binary | |
MD5:3B156E12141F8CBCE9D60CDCE2077617 | SHA256:E6287E44B44ABEA20E1B2E3F415D22B9E5E5FBBC155AD9DADBABA63951B2AF6F | |||
| 5048 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\2823318777ntouromlalnodry--naod.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
33
TCP/UDP connections
160
DNS requests
152
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5048 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | unknown | — | — | whitelisted |
5048 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | unknown | — | — | whitelisted |
5048 | firefox.exe | POST | 200 | 184.24.77.56:80 | http://r11.o.lencr.org/ | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5048 | firefox.exe | POST | 200 | 184.24.77.56:80 | http://r11.o.lencr.org/ | unknown | — | — | whitelisted |
5048 | firefox.exe | POST | 200 | 142.250.184.227:80 | http://o.pki.goog/s/wr3/FIY | unknown | — | — | whitelisted |
5048 | firefox.exe | POST | 200 | 142.250.184.227:80 | http://o.pki.goog/we2 | unknown | — | — | whitelisted |
5048 | firefox.exe | POST | 200 | 184.24.77.57:80 | http://r10.o.lencr.org/ | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 23.48.23.156:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5048 | firefox.exe | 104.21.35.139:443 | www.vidcombo.com | CLOUDFLARENET | — | unknown |
5048 | firefox.exe | 34.107.221.82:80 | detectportal.firefox.com | GOOGLE | US | whitelisted |
5048 | firefox.exe | 34.36.137.203:443 | contile.services.mozilla.com | GOOGLE-CLOUD-PLATFORM | US | whitelisted |
3216 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
5048 | firefox.exe | 34.160.144.191:443 | content-signature-2.cdn.mozilla.net | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
detectportal.firefox.com |
| whitelisted |
www.vidcombo.com |
| unknown |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
example.org |
| whitelisted |
ipv4only.arpa |
| whitelisted |
contile.services.mozilla.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |