| File name: | 2020 changing.rtf |
| Full analysis: | https://app.any.run/tasks/5e3fcba8-7486-485e-b646-674b0e9abb1e |
| Verdict: | Malicious activity |
| Analysis date: | February 21, 2020, 19:11:56 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/rtf |
| File info: | Rich Text Format data, version 1, ANSI |
| MD5: | DDD16573305B56DF277078FF605A167C |
| SHA1: | 7424BA298AE218B4E3C8619673CF8975604CF622 |
| SHA256: | AA40F830AEA68D7BD45D15CC9FB0396F107C373B0933D02D4B518F75C3AF0D4A |
| SSDEEP: | 48:MUK2kJfM4m6qQrMrdYSDMMsUn6dDB9QmUCOve0Dvi5xEr+2:MxfMYrMrdHDMInWl9FUg02GC2 |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads Internet Cache Settings
- WINWORD.EXE (PID: 2952)
Unusual connect from Microsoft Office
- WINWORD.EXE (PID: 2952)
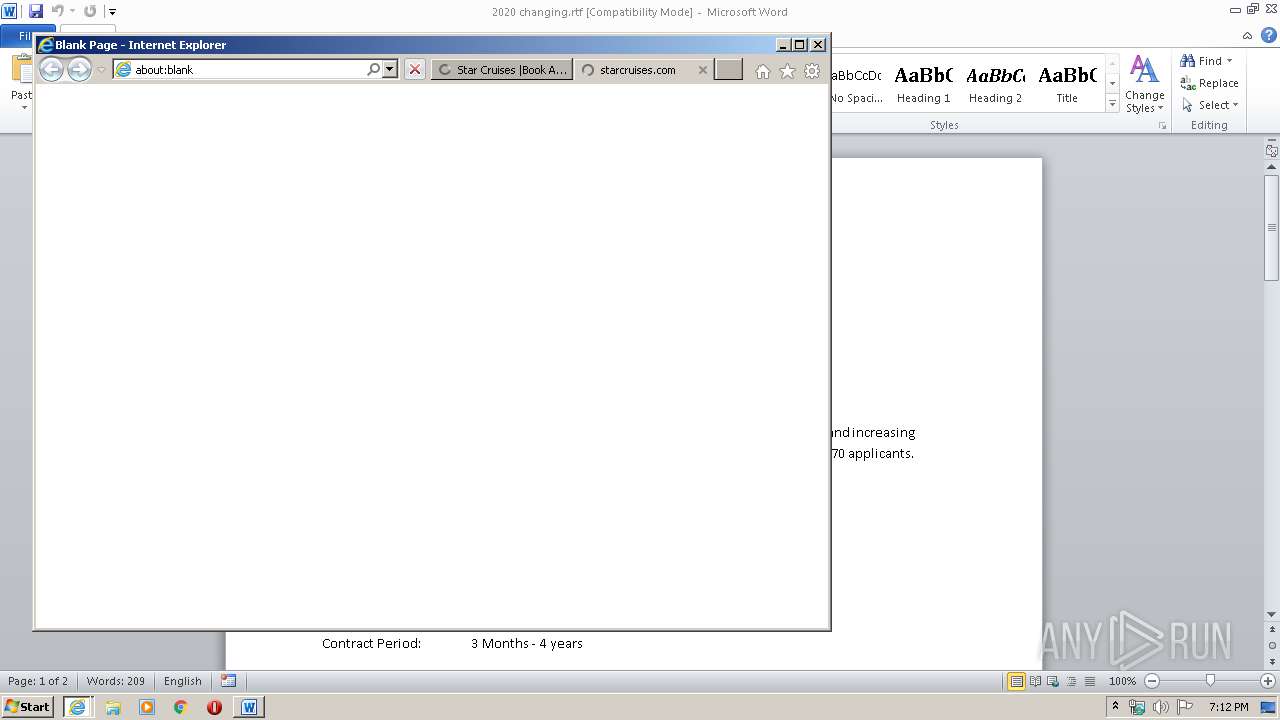
Executed via COM
- iexplore.exe (PID: 3620)
Reads internet explorer settings
- WINWORD.EXE (PID: 2952)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 2952)
- iexplore.exe (PID: 3716)
- iexplore.exe (PID: 2916)
Reads Internet Cache Settings
- iexplore.exe (PID: 3620)
- iexplore.exe (PID: 3716)
- iexplore.exe (PID: 2916)
Application launched itself
- iexplore.exe (PID: 3620)
Changes internet zones settings
- iexplore.exe (PID: 3620)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2952)
Reads internet explorer settings
- iexplore.exe (PID: 2916)
- iexplore.exe (PID: 3716)
- iexplore.exe (PID: 256)
Reads settings of System Certificates
- iexplore.exe (PID: 3716)
- iexplore.exe (PID: 2916)
- iexplore.exe (PID: 3620)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3620)
Changes settings of System certificates
- iexplore.exe (PID: 3620)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rtf | | | Rich Text Format (100) |
|---|
Total processes
40
Monitored processes
5
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 256 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3620 CREDAT:144385 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2916 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3620 CREDAT:464132 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2952 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\2020 changing.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3620 | "C:\Program Files\Internet Explorer\iexplore.exe" -startmediumtab -Embedding | C:\Program Files\Internet Explorer\iexplore.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3716 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3620 CREDAT:333058 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
6 657
Read events
2 194
Write events
3 099
Delete events
1 364
Modification events
| (PID) Process: | (2952) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | 41 |
Value: 20343100880B0000010000000000000000000000 | |||
| (PID) Process: | (2952) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2952) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2952) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2952) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2952) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2952) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2952) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2952) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2952) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
0
Suspicious files
44
Text files
98
Unknown types
30
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2952 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR6C20.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2952 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\Cab9331.tmp | — | |
MD5:— | SHA256:— | |||
| 2952 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\Tar9341.tmp | — | |
MD5:— | SHA256:— | |||
| 3716 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\CabA4A5.tmp | — | |
MD5:— | SHA256:— | |||
| 3716 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\TarA4A6.tmp | — | |
MD5:— | SHA256:— | |||
| 2952 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF9BB6852C7D1AA976.TMP | — | |
MD5:— | SHA256:— | |||
| 2952 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2952 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$20 changing.rtf | pgc | |
MD5:— | SHA256:— | |||
| 3716 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\en[1].htm | html | |
MD5:— | SHA256:— | |||
| 3716 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\style[1].css | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
26
TCP/UDP connections
73
DNS requests
25
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
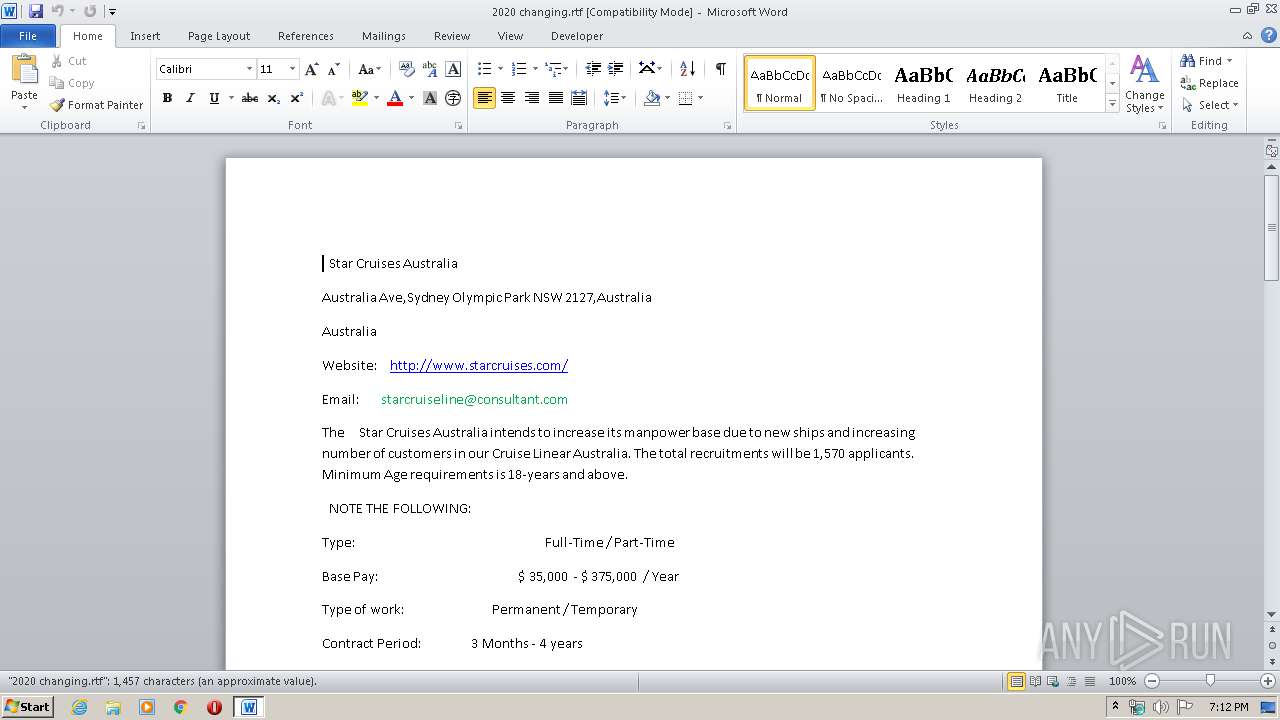
2952 | WINWORD.EXE | GET | 301 | 152.199.16.36:80 | http://www.starcruises.com/ | US | — | — | whitelisted |
2952 | WINWORD.EXE | GET | 301 | 152.199.16.36:80 | http://www.starcruises.com/lt/en | US | — | — | whitelisted |
2952 | WINWORD.EXE | GET | 301 | 152.199.16.36:80 | http://www.starcruises.com/sg/en | US | — | — | whitelisted |
3716 | iexplore.exe | GET | 200 | 172.217.16.131:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
3716 | iexplore.exe | GET | 200 | 172.217.16.131:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
3716 | iexplore.exe | GET | 200 | 172.217.16.131:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
3716 | iexplore.exe | GET | 200 | 172.217.16.131:80 | http://ocsp.pki.goog/gts1o1/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQCgdZM8AVzzKAgAAAAALnDU | US | der | 472 b | whitelisted |
3716 | iexplore.exe | GET | 200 | 172.217.16.131:80 | http://ocsp.pki.goog/gts1o1/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQCgdZM8AVzzKAgAAAAALnDU | US | der | 472 b | whitelisted |
3716 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAVG%2Fhgj9%2BGUHaOfzhTEYXM%3D | US | der | 471 b | whitelisted |
3716 | iexplore.exe | GET | 200 | 172.217.16.131:80 | http://ocsp.pki.goog/gts1o1/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQCgdZM8AVzzKAgAAAAALnDU | US | der | 472 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3716 | iexplore.exe | 172.217.16.131:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
2952 | WINWORD.EXE | 152.199.16.36:80 | www.starcruises.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2952 | WINWORD.EXE | 152.199.16.36:443 | www.starcruises.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2952 | WINWORD.EXE | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3716 | iexplore.exe | 152.199.16.36:443 | www.starcruises.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3716 | iexplore.exe | 52.74.87.144:443 | media.starcruises.com | Amazon.com, Inc. | SG | unknown |
3716 | iexplore.exe | 185.60.216.19:443 | connect.facebook.net | Facebook, Inc. | IE | whitelisted |
3716 | iexplore.exe | 87.248.118.23:443 | s.yimg.com | Yahoo! UK Services Limited | GB | malicious |
3716 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3716 | iexplore.exe | 23.61.210.48:443 | cdn-akamai.mookie1.com | Akamai Technologies, Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.starcruises.com |
| unknown |
ocsp.digicert.com |
| whitelisted |
media.starcruises.com |
| unknown |
www.google-analytics.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
connect.facebook.net |
| whitelisted |
s.yimg.com |
| shared |
cdn-akamai.mookie1.com |
| whitelisted |
d.line-scdn.net |
| whitelisted |