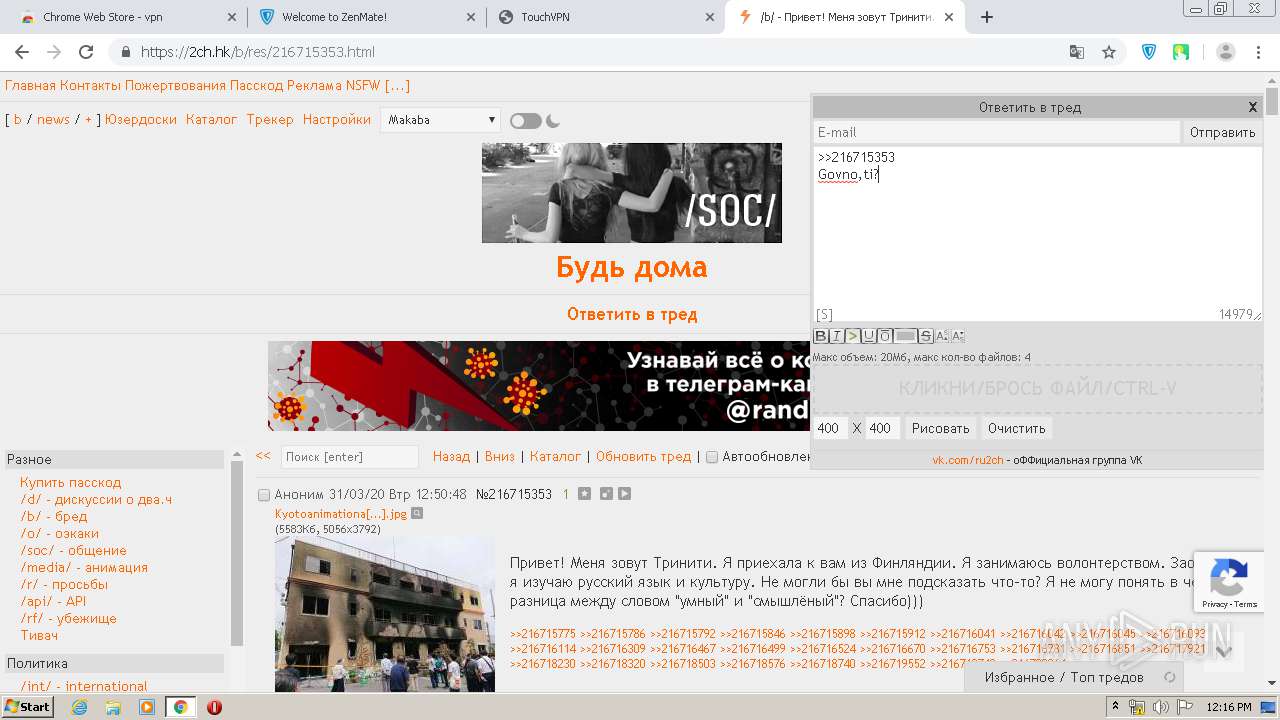
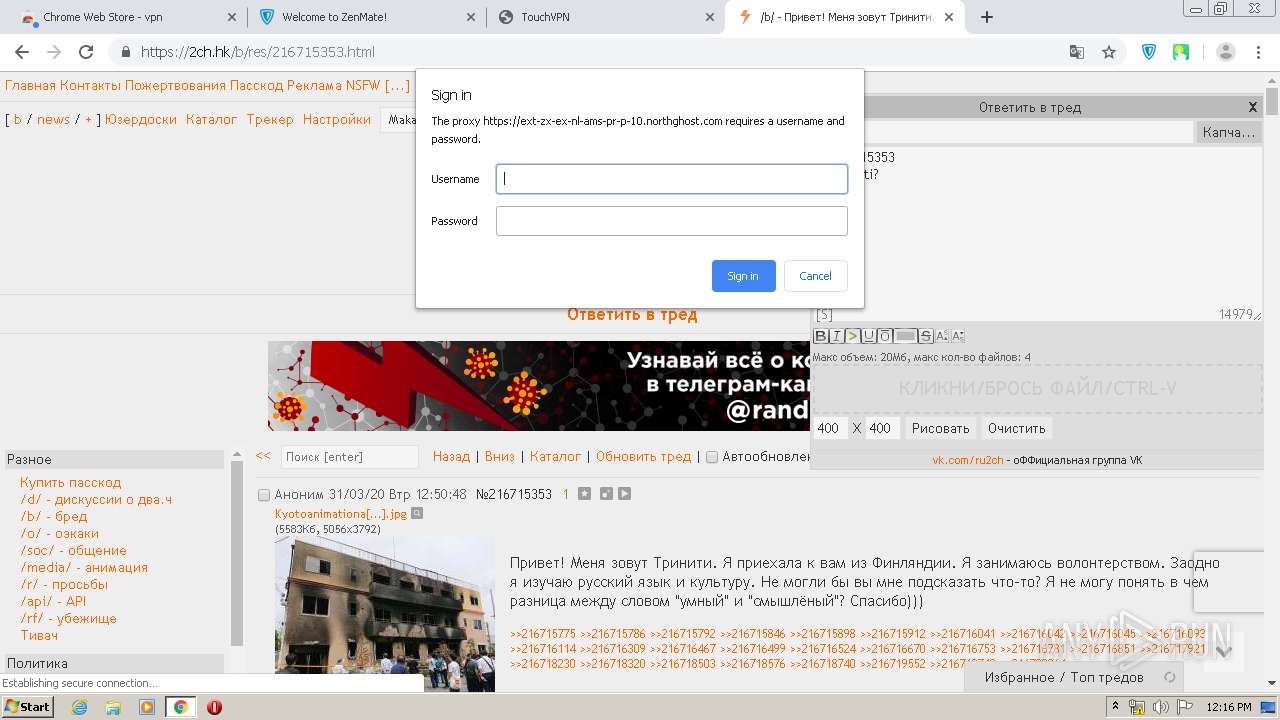
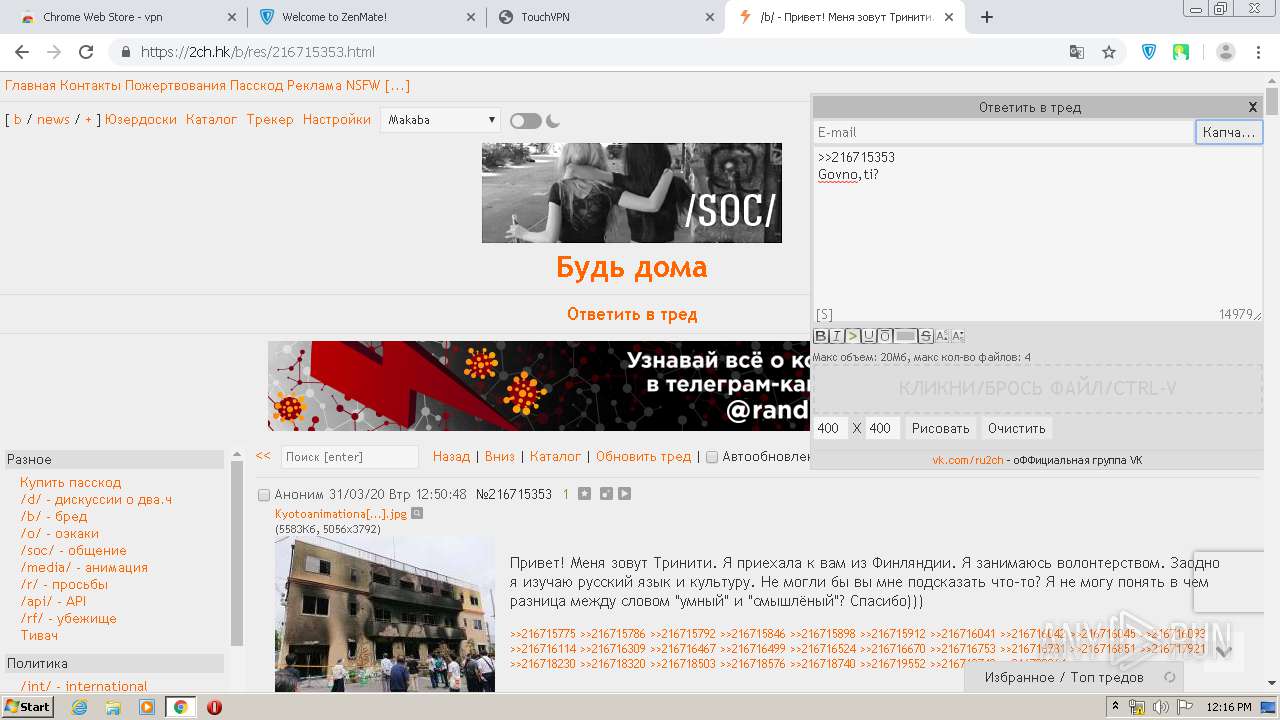
| URL: | https://clck.ru/MkBy2 |
| Full analysis: | https://app.any.run/tasks/e0289180-d4fe-40e1-93d2-1bc283d721e4 |
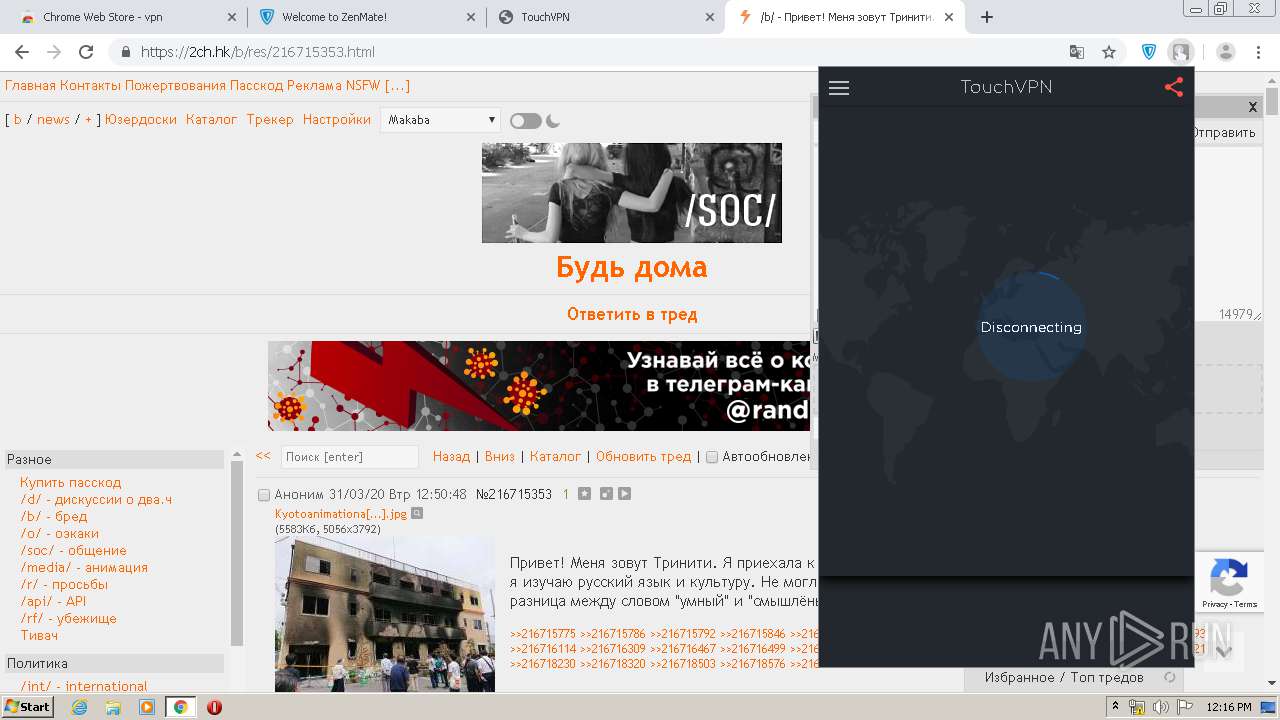
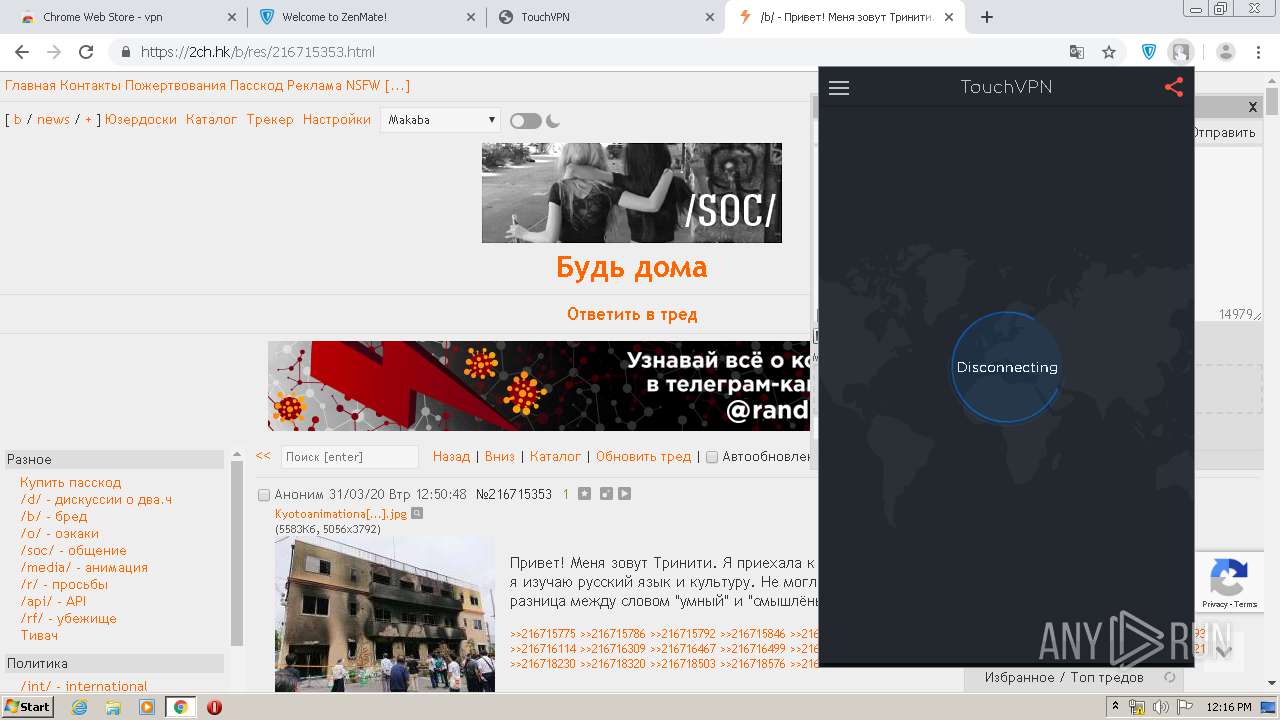
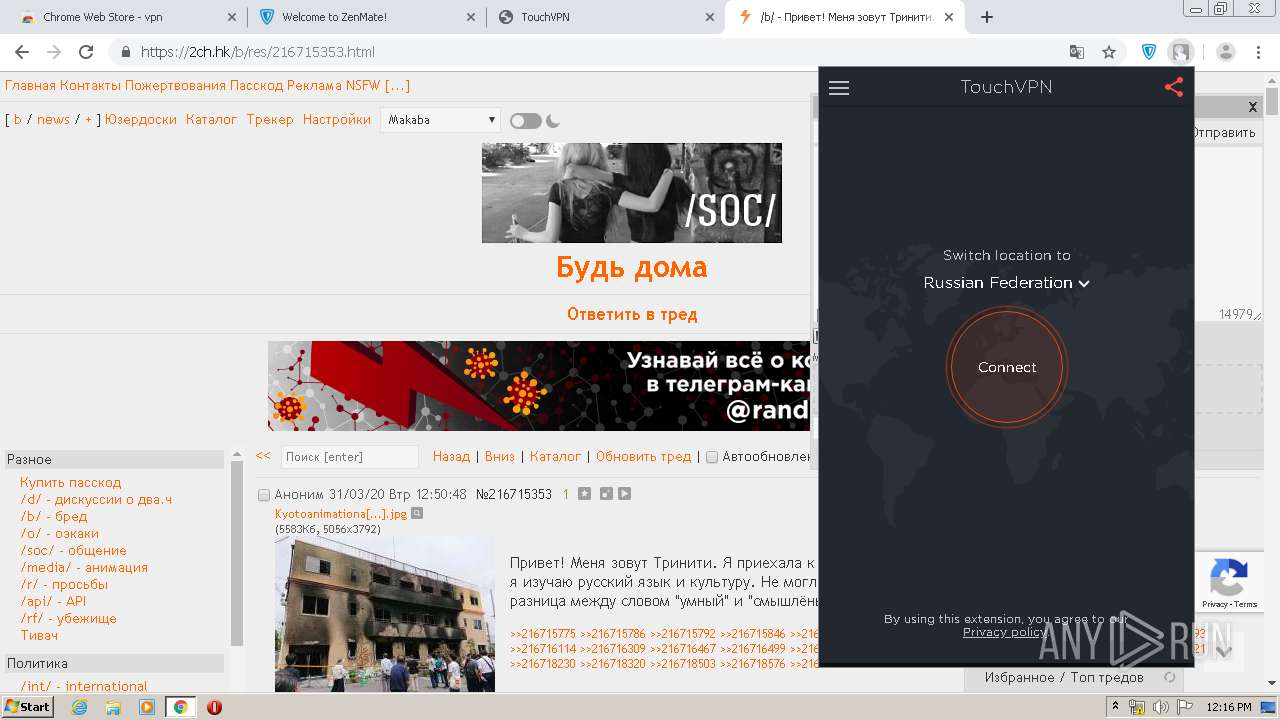
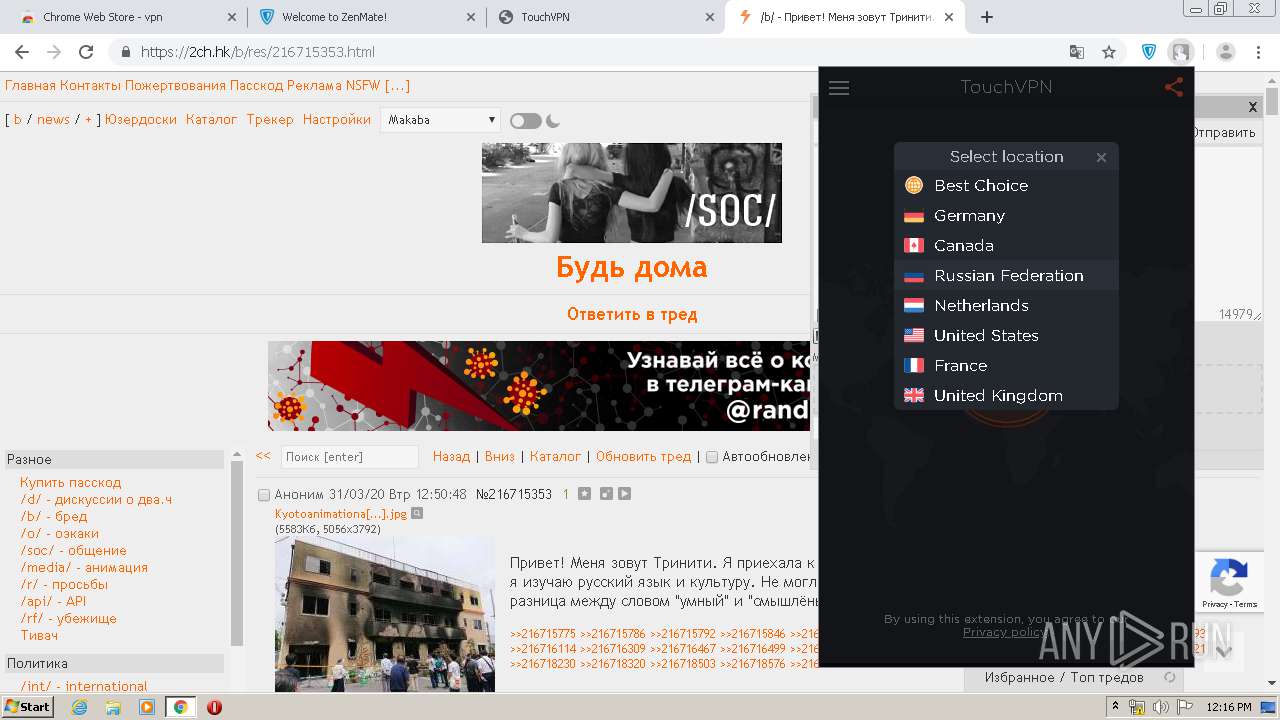
| Verdict: | Malicious activity |
| Analysis date: | March 31, 2020, 11:13:05 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 1FBF5B9D398306E2BA2114503126A9A2 |
| SHA1: | 8D11CDB090E5C06F17555BB95716A337B4A56850 |
| SHA256: | AA3FCC4F443FFDF5FC95F1267B107A8D815E21A6136F8FC36313EA81EC906389 |
| SSDEEP: | 3:N8UZLXQKq:2U5q |
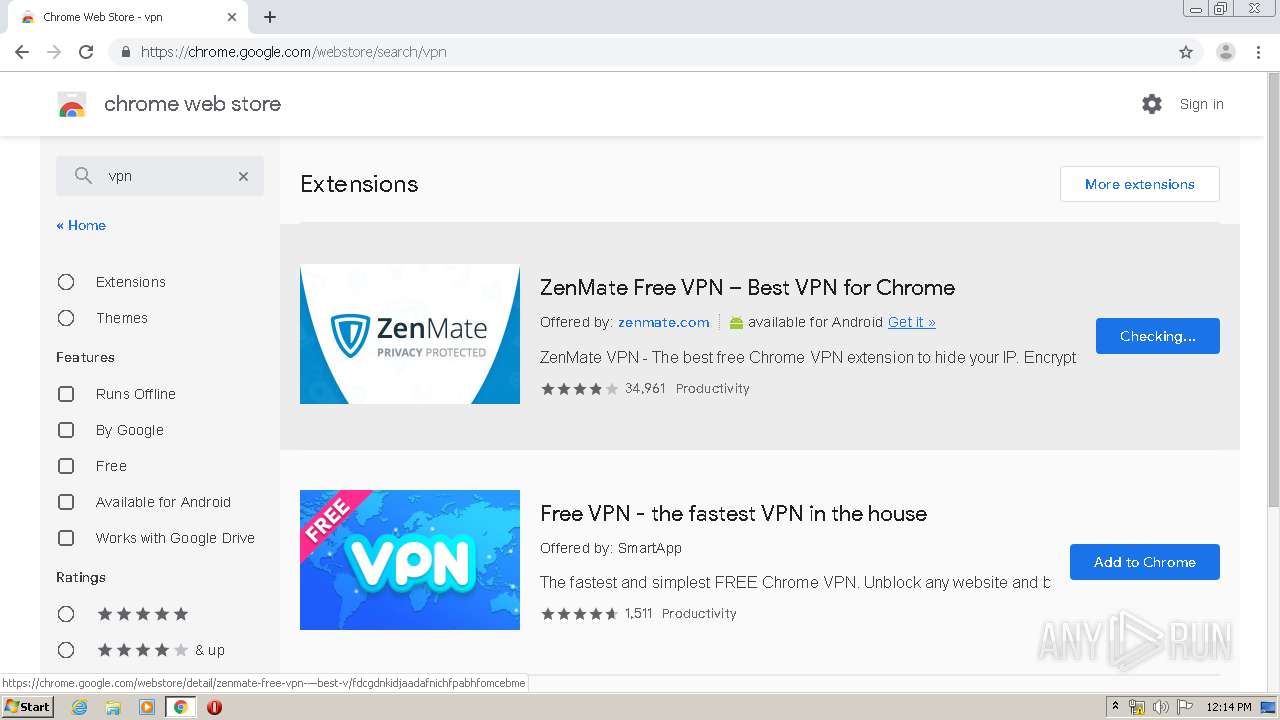
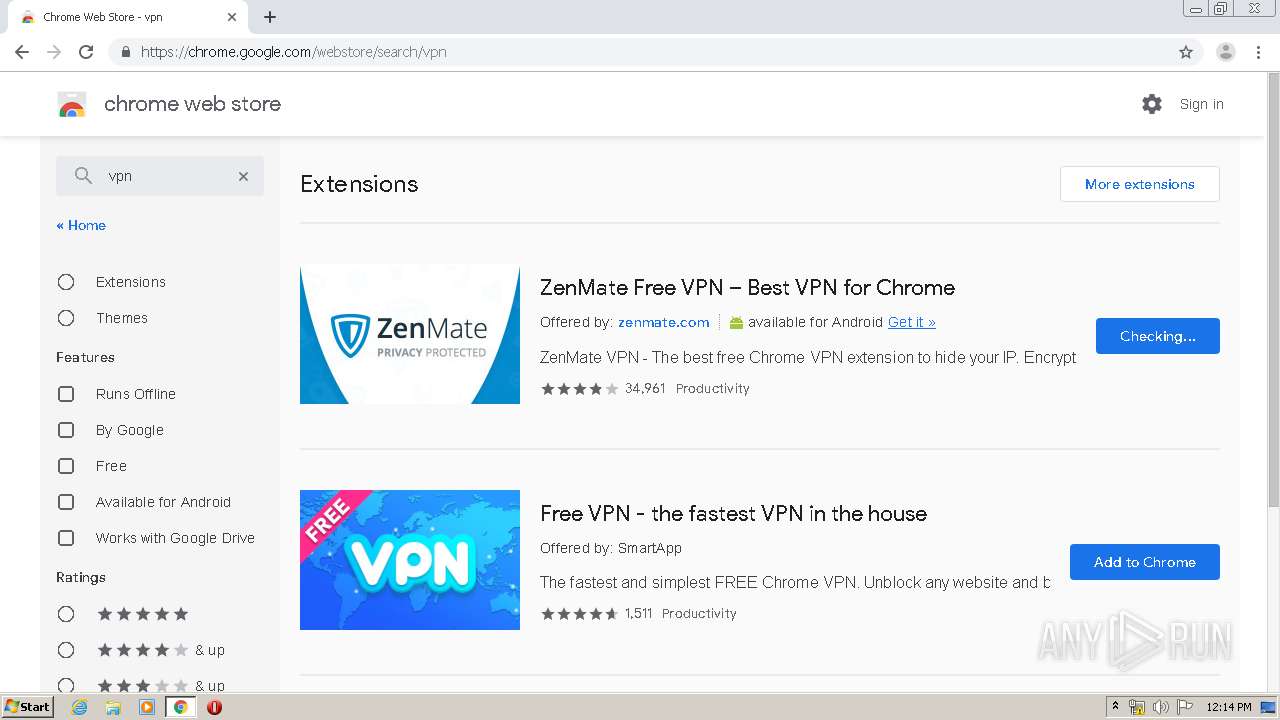
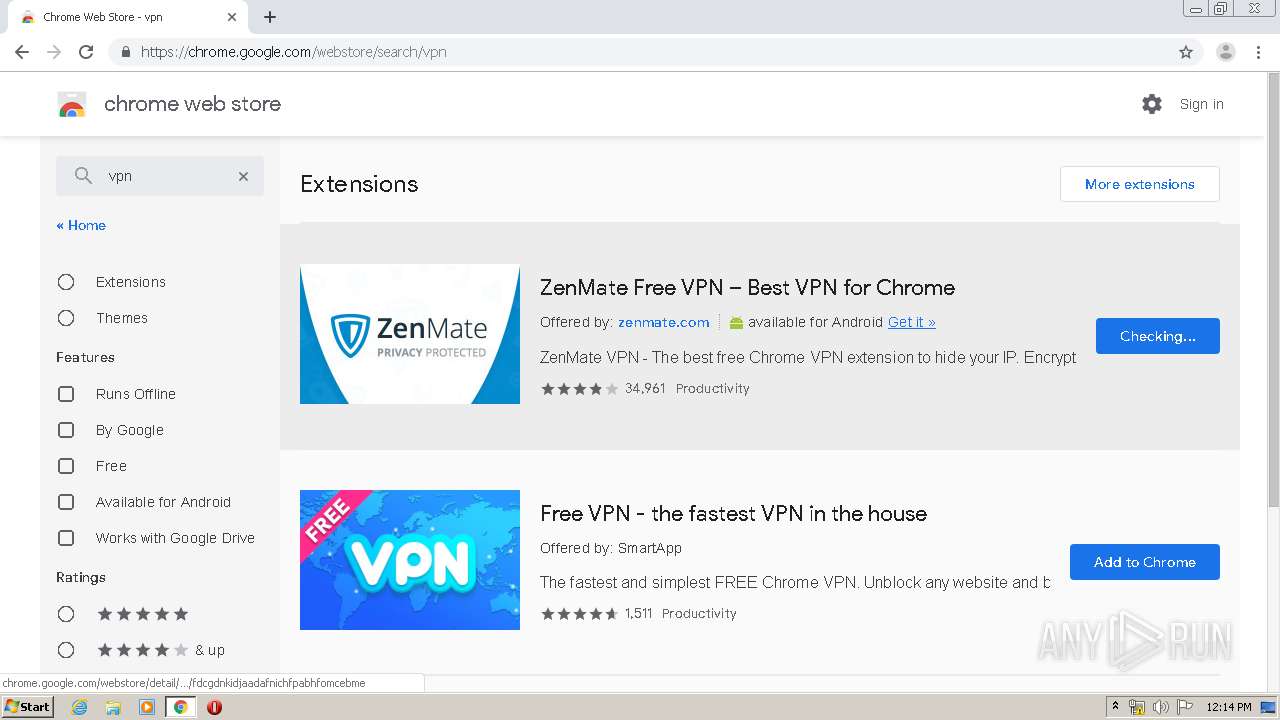
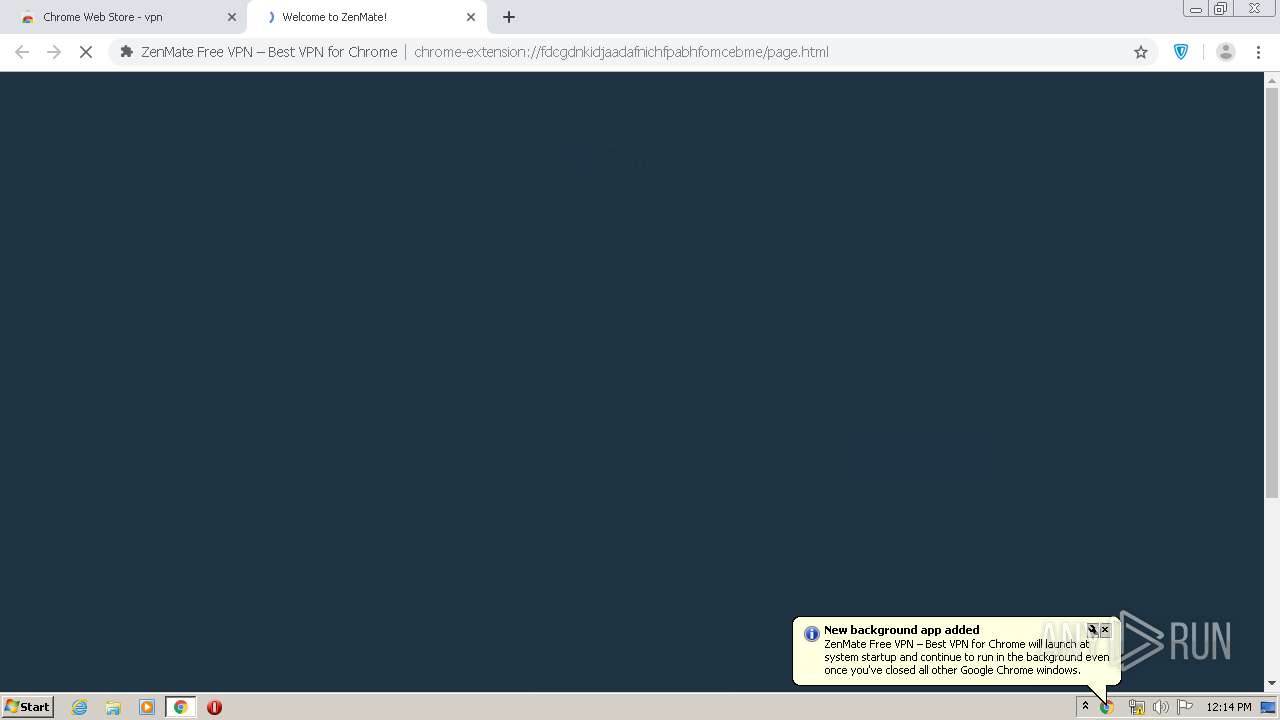
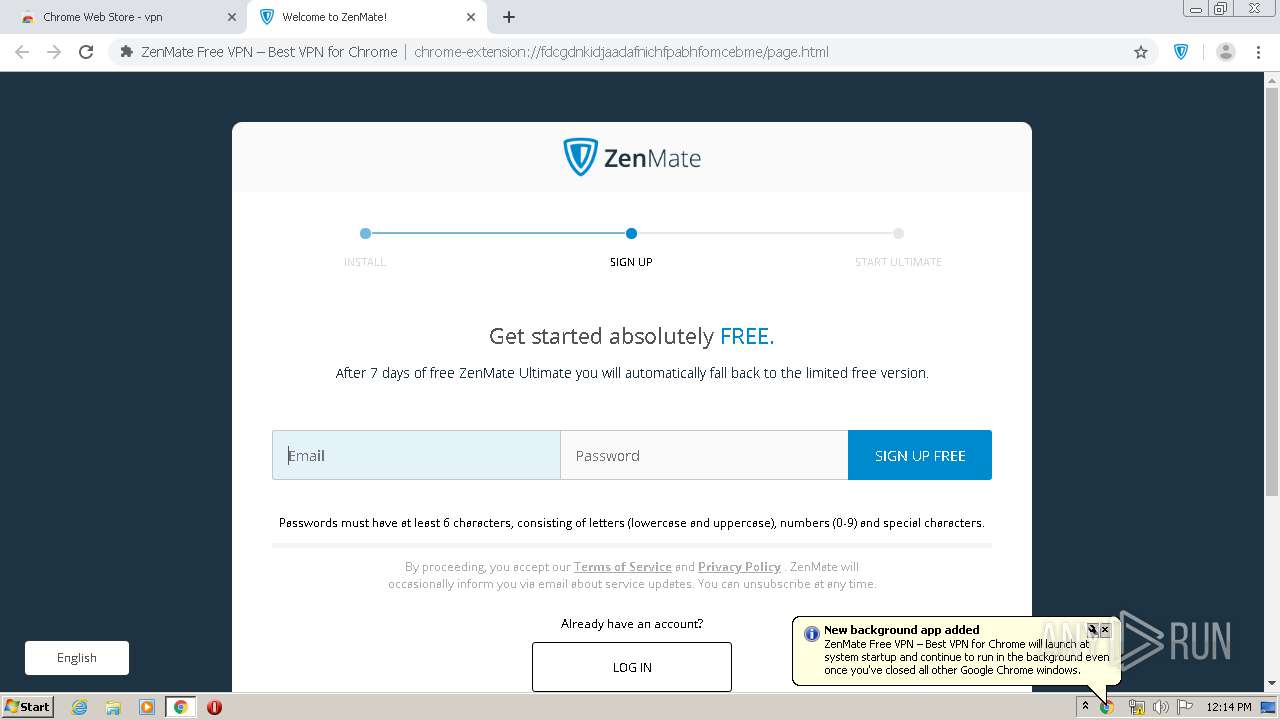
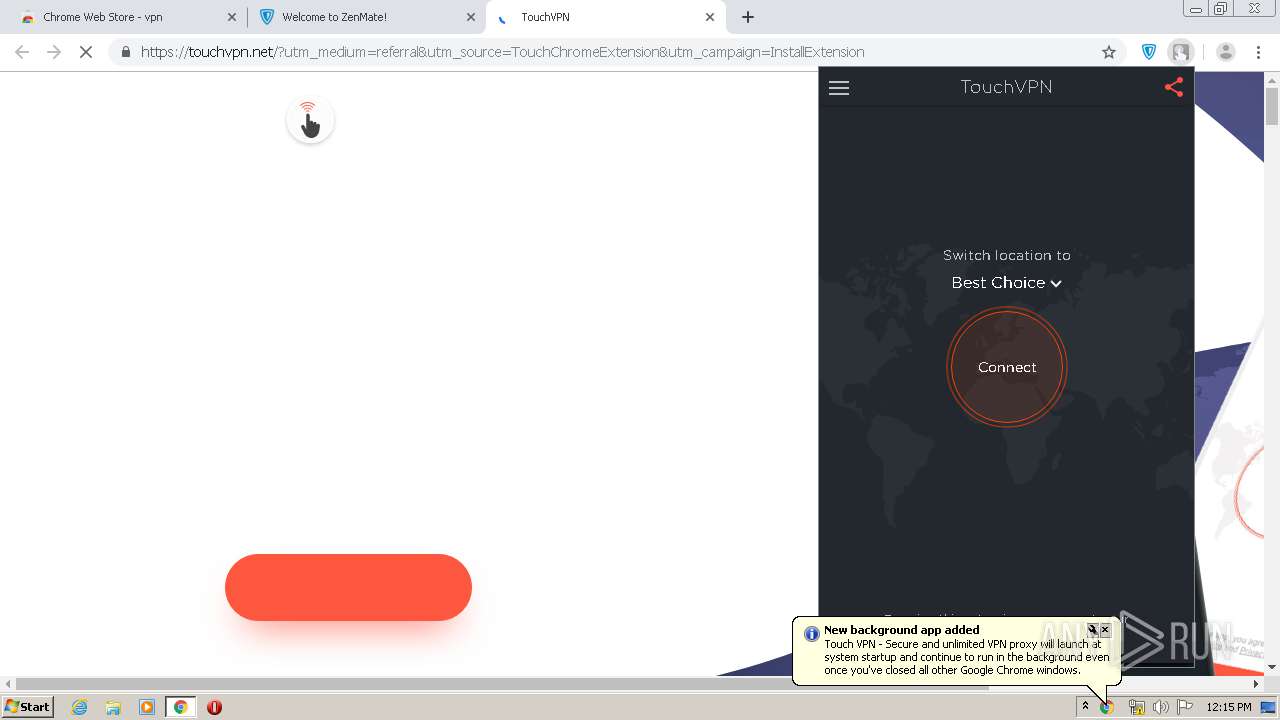
MALICIOUS
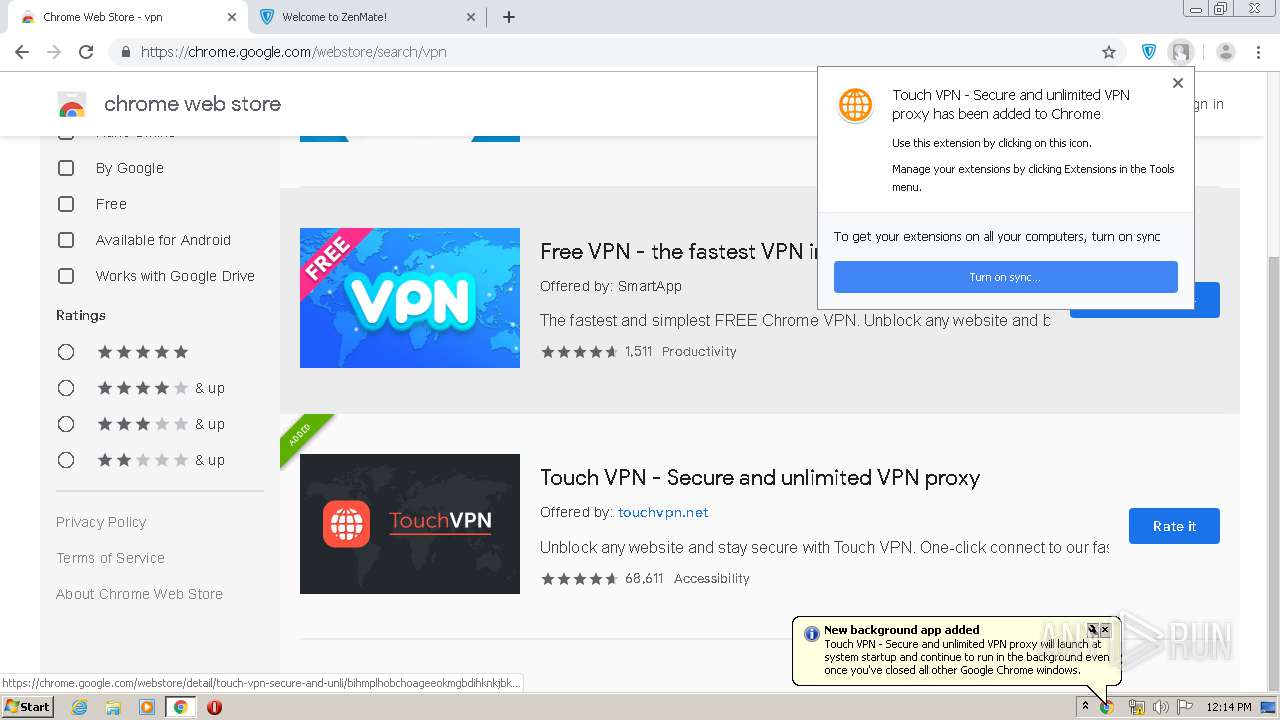
Changes the autorun value in the registry
- chrome.exe (PID: 3892)
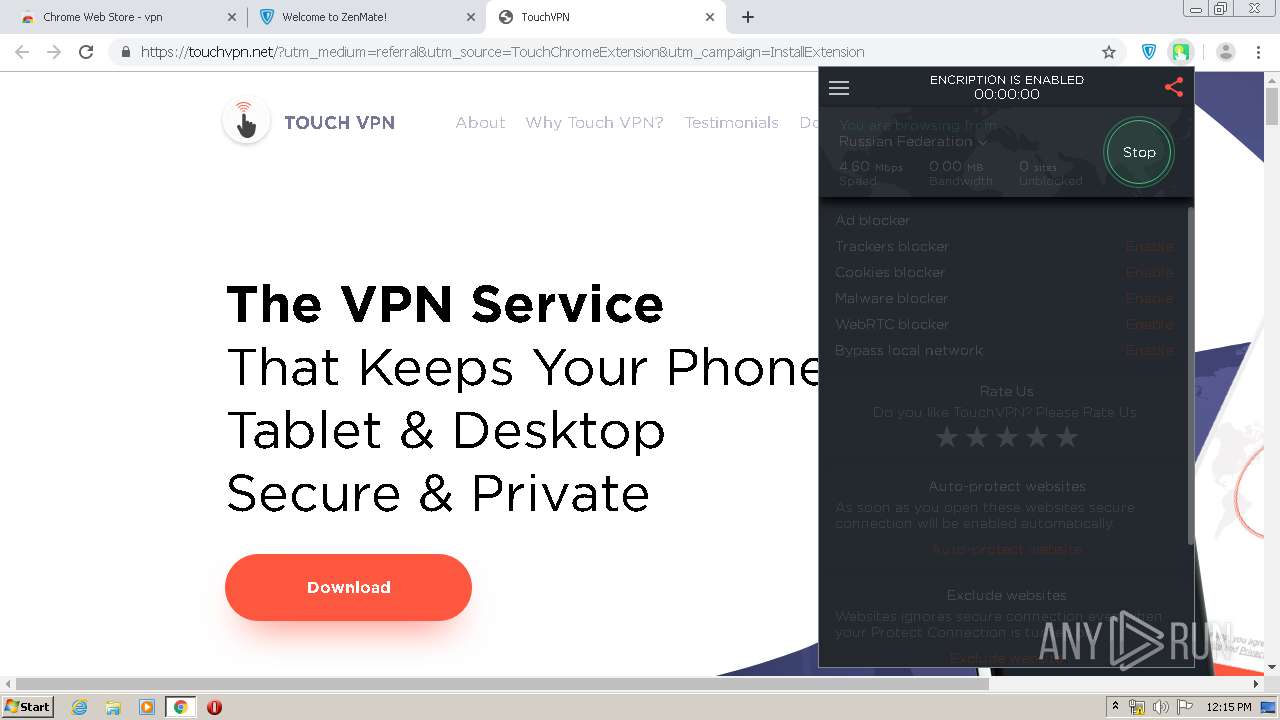
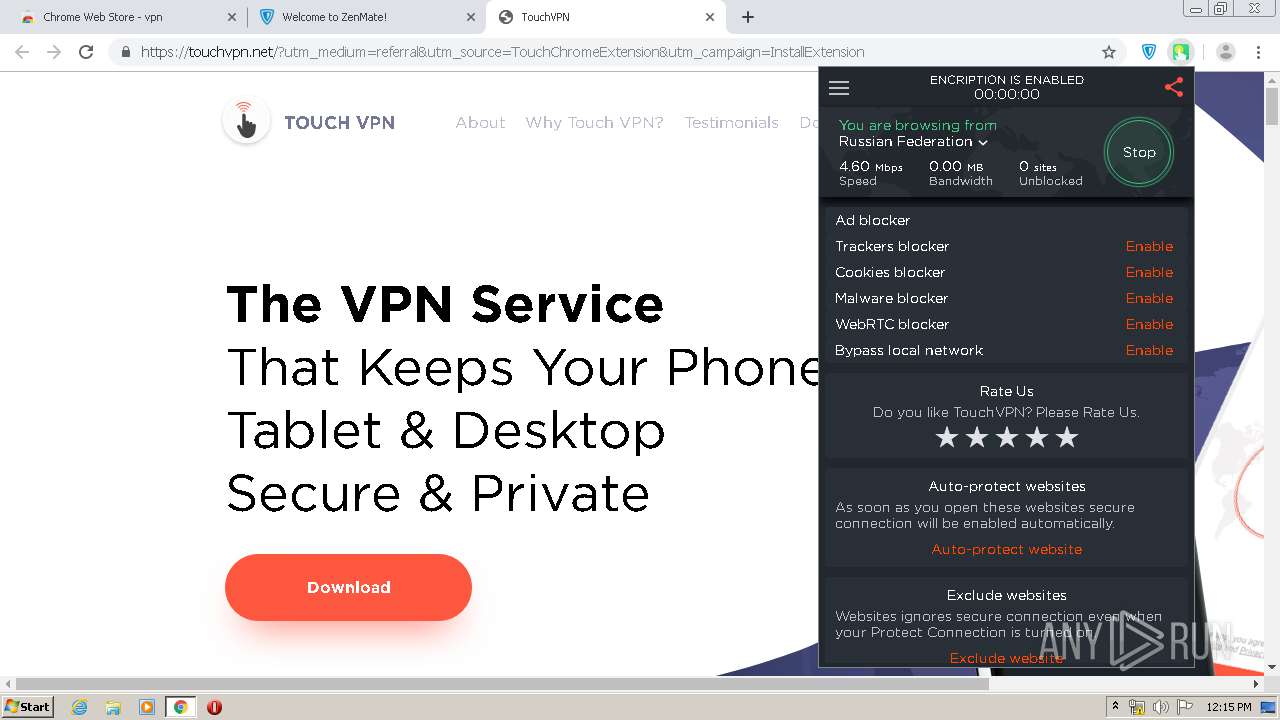
SUSPICIOUS
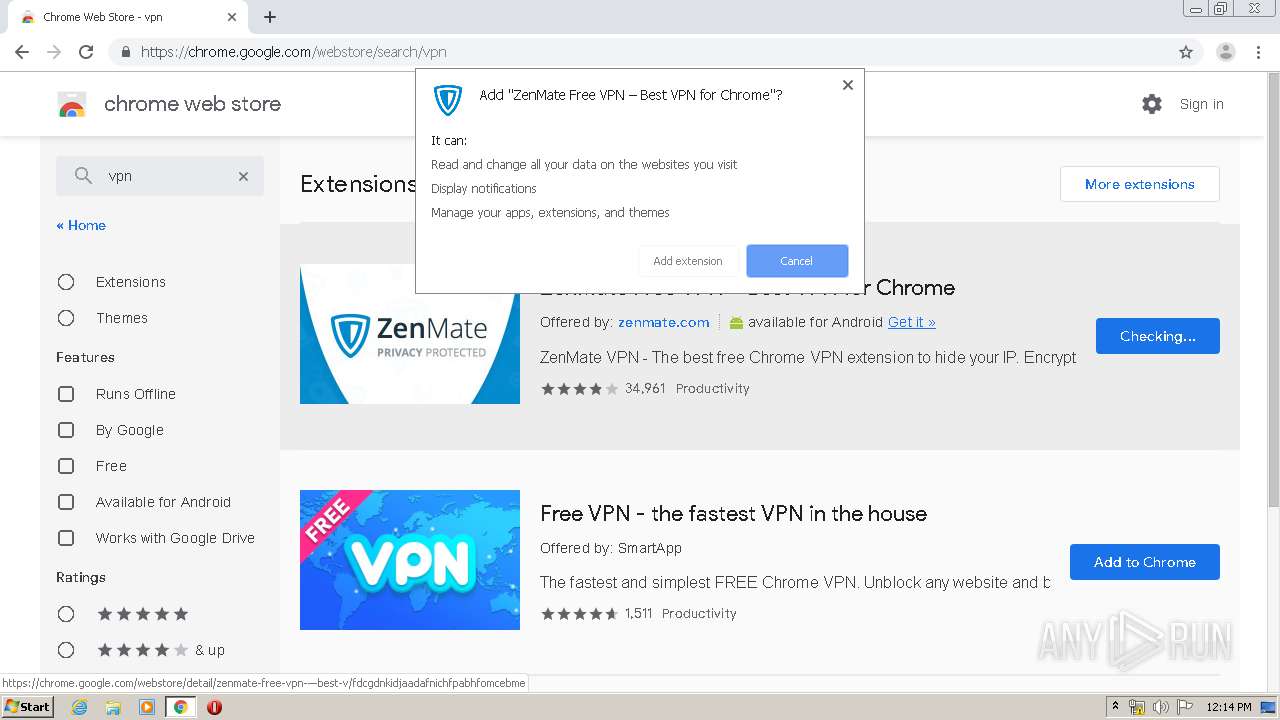
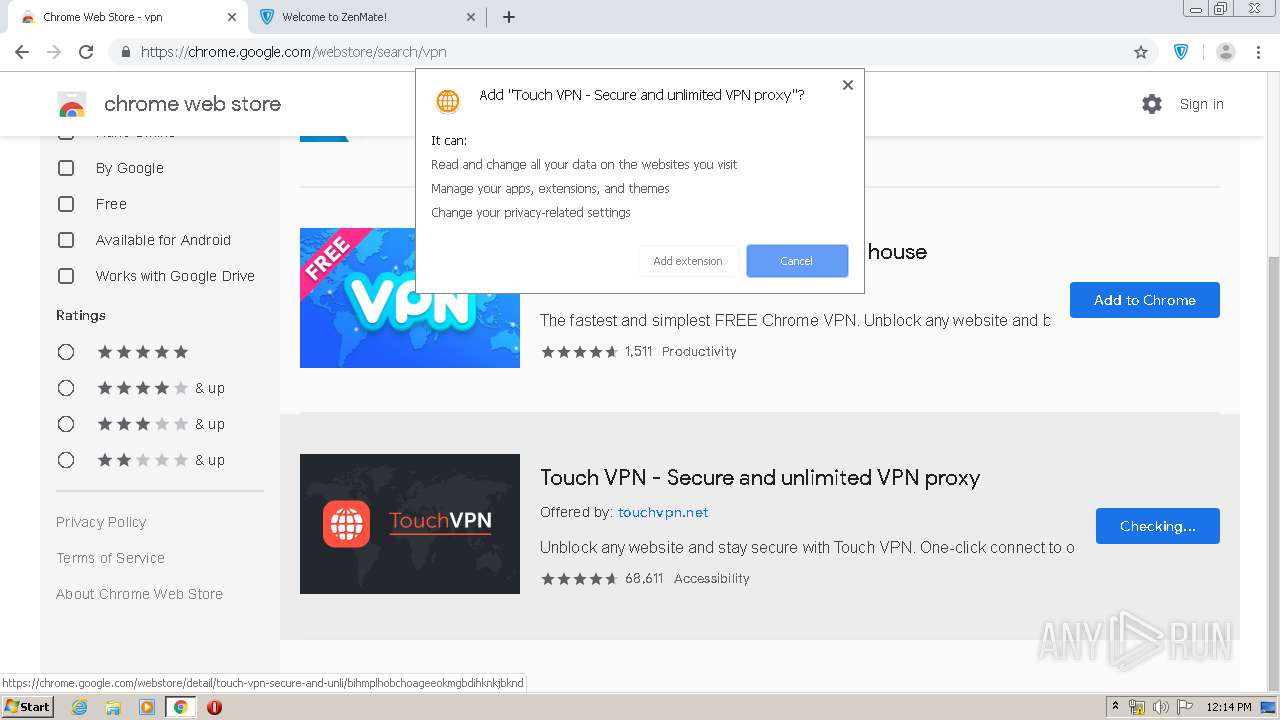
Modifies files in Chrome extension folder
- chrome.exe (PID: 3892)
INFO
Reads the hosts file
- chrome.exe (PID: 3252)
- chrome.exe (PID: 3892)
Reads Internet Cache Settings
- chrome.exe (PID: 3892)
Dropped object may contain Bitcoin addresses
- chrome.exe (PID: 3892)
Application launched itself
- chrome.exe (PID: 3892)
Changes settings of System certificates
- chrome.exe (PID: 3252)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
90
Monitored processes
54
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 272 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,14134417760950761469,12088534520466632996,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=15542768801943835023 --mojo-platform-channel-handle=3972 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 348 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,14134417760950761469,12088534520466632996,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9504648360976557515 --renderer-client-id=48 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4896 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 528 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,14134417760950761469,12088534520466632996,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=6493597574842648468 --mojo-platform-channel-handle=3256 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 816 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,14134417760950761469,12088534520466632996,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=17691052820028336957 --mojo-platform-channel-handle=4108 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1172 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,14134417760950761469,12088534520466632996,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=14370247088291346505 --mojo-platform-channel-handle=3256 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1296 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,14134417760950761469,12088534520466632996,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=7221083062601994499 --mojo-platform-channel-handle=3688 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1332 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,14134417760950761469,12088534520466632996,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2761756174395481511 --renderer-client-id=26 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3960 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1636 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,14134417760950761469,12088534520466632996,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=10252676162761092089 --mojo-platform-channel-handle=4260 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1640 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,14134417760950761469,12088534520466632996,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4105958111734812529 --renderer-client-id=34 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3004 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1720 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1000,14134417760950761469,12088534520466632996,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=15543207693313426907 --mojo-platform-channel-handle=4320 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
807
Read events
621
Write events
176
Delete events
10
Modification events
| (PID) Process: | (3892) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3892) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3892) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3892) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3892) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2108) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3892-13230126800396750 |
Value: 259 | |||
| (PID) Process: | (3892) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3892) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3892) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3120-13213713943555664 |
Value: 0 | |||
| (PID) Process: | (3892) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
96
Text files
848
Unknown types
22
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3892 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5E8325D0-F34.pma | — | |
MD5:— | SHA256:— | |||
| 3892 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\34a5572f-0dfd-49f0-a9c7-e506aa5ce5e2.tmp | — | |
MD5:— | SHA256:— | |||
| 3892 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3892 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3892 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3892 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3892 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RFa66bc2.TMP | text | |
MD5:— | SHA256:— | |||
| 3892 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RFa66bb2.TMP | text | |
MD5:— | SHA256:— | |||
| 3892 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3892 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RFa66d39.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
14
TCP/UDP connections
98
DNS requests
35
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
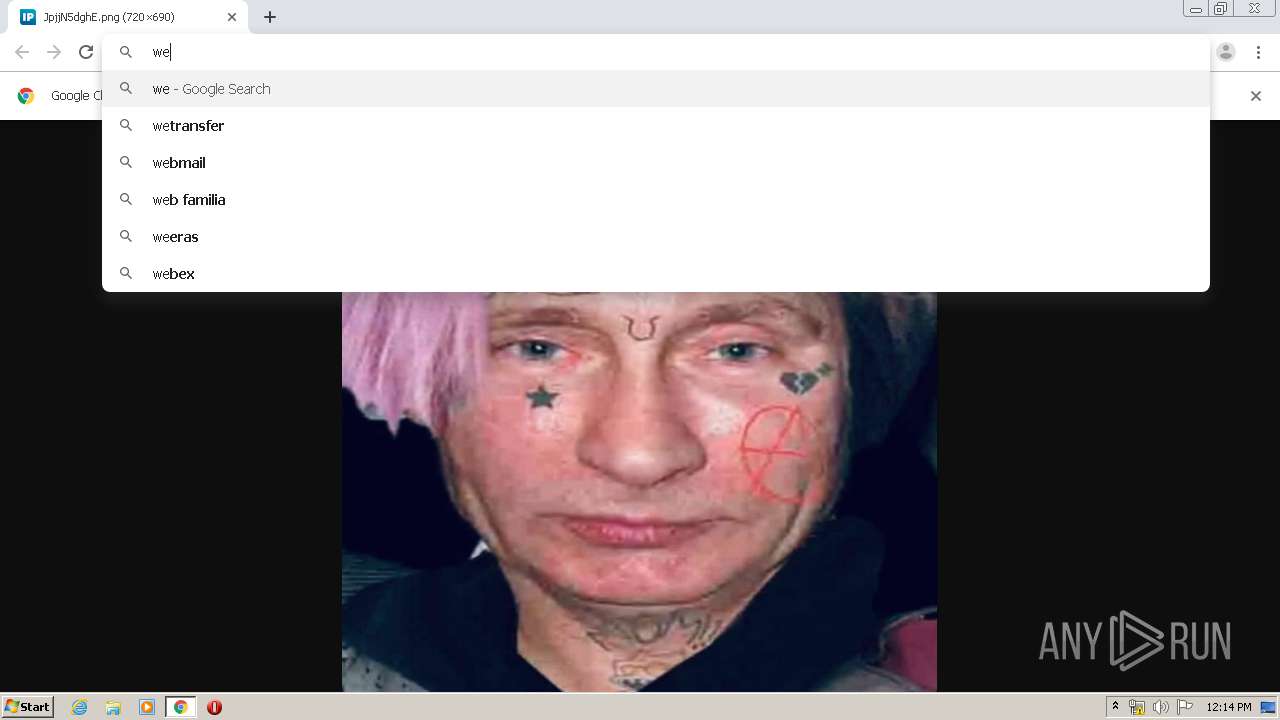
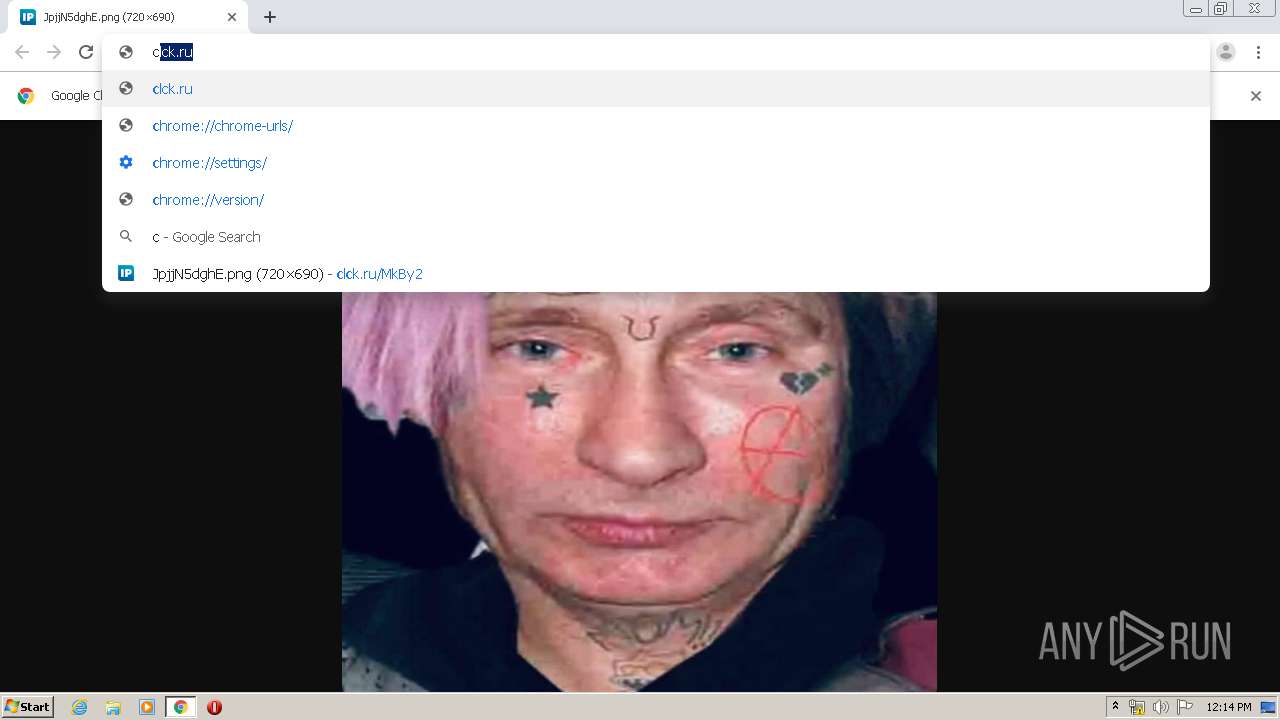
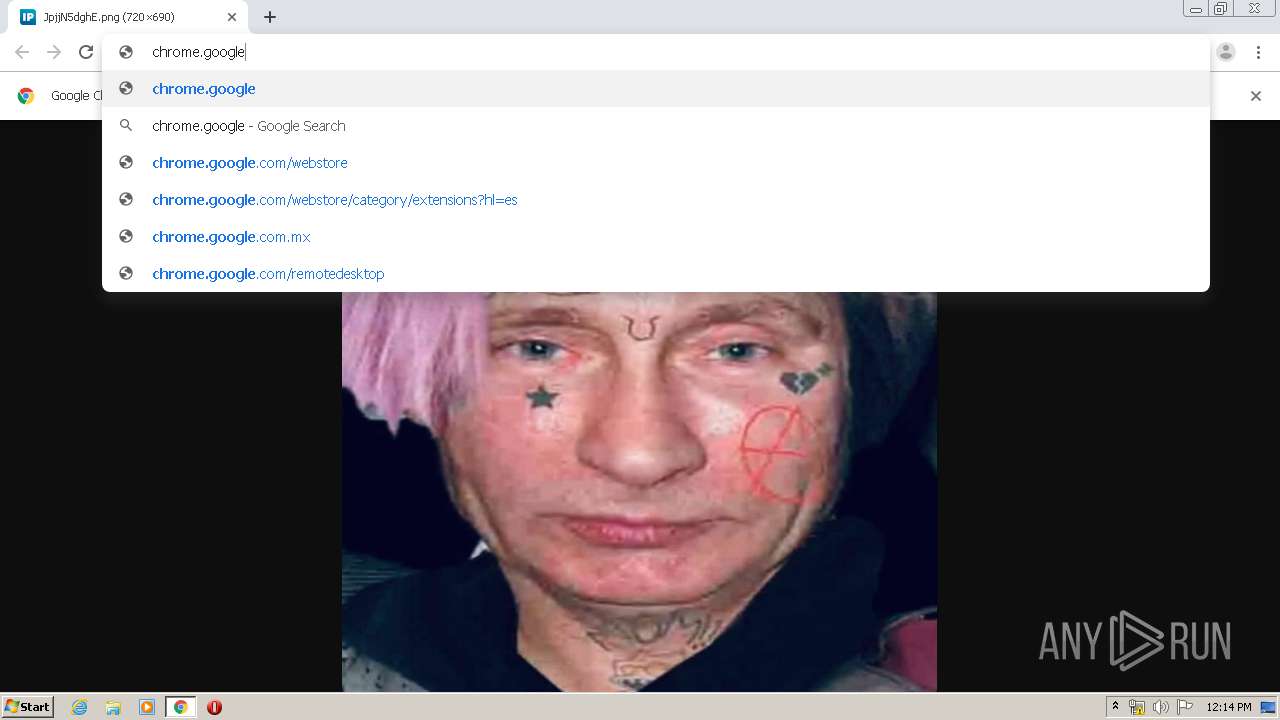
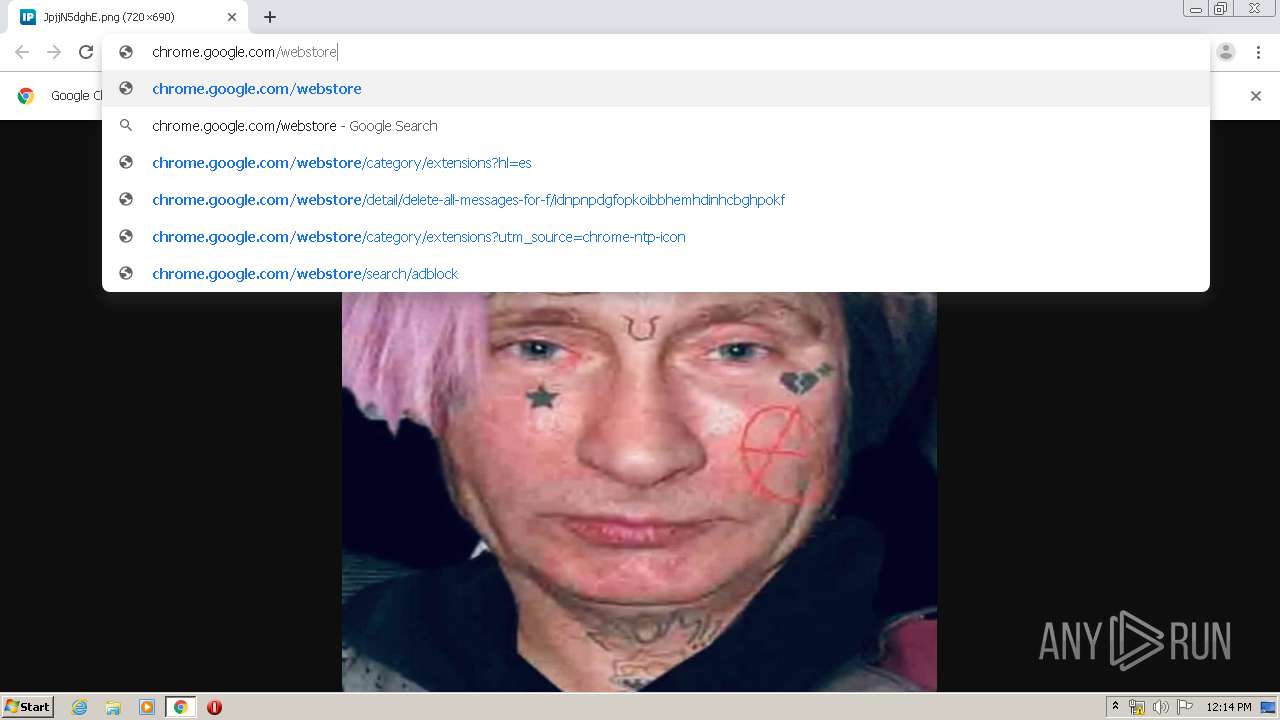
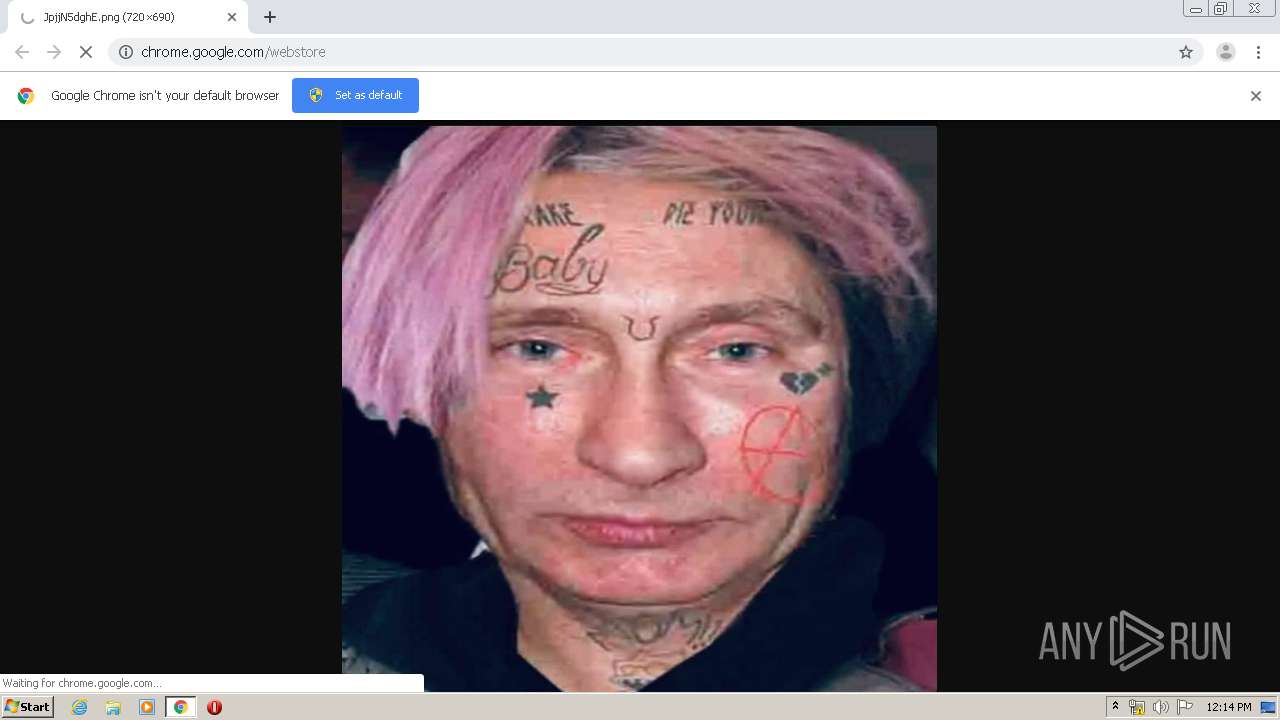
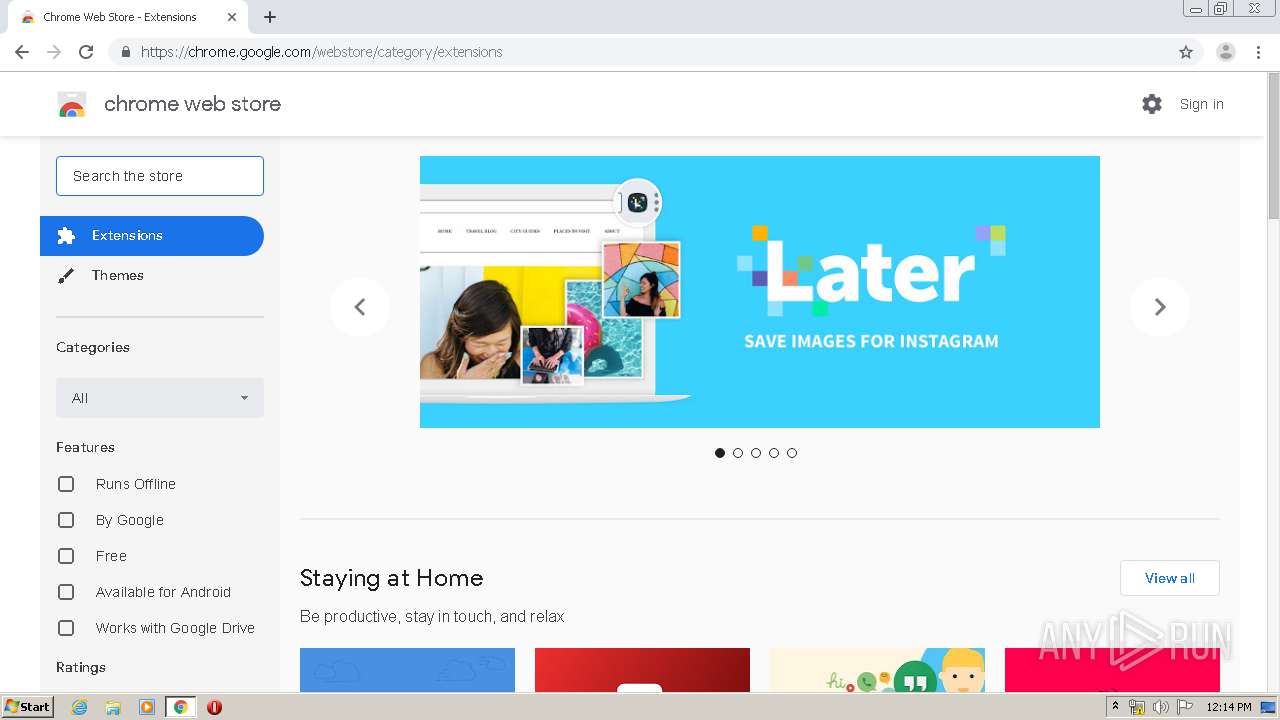
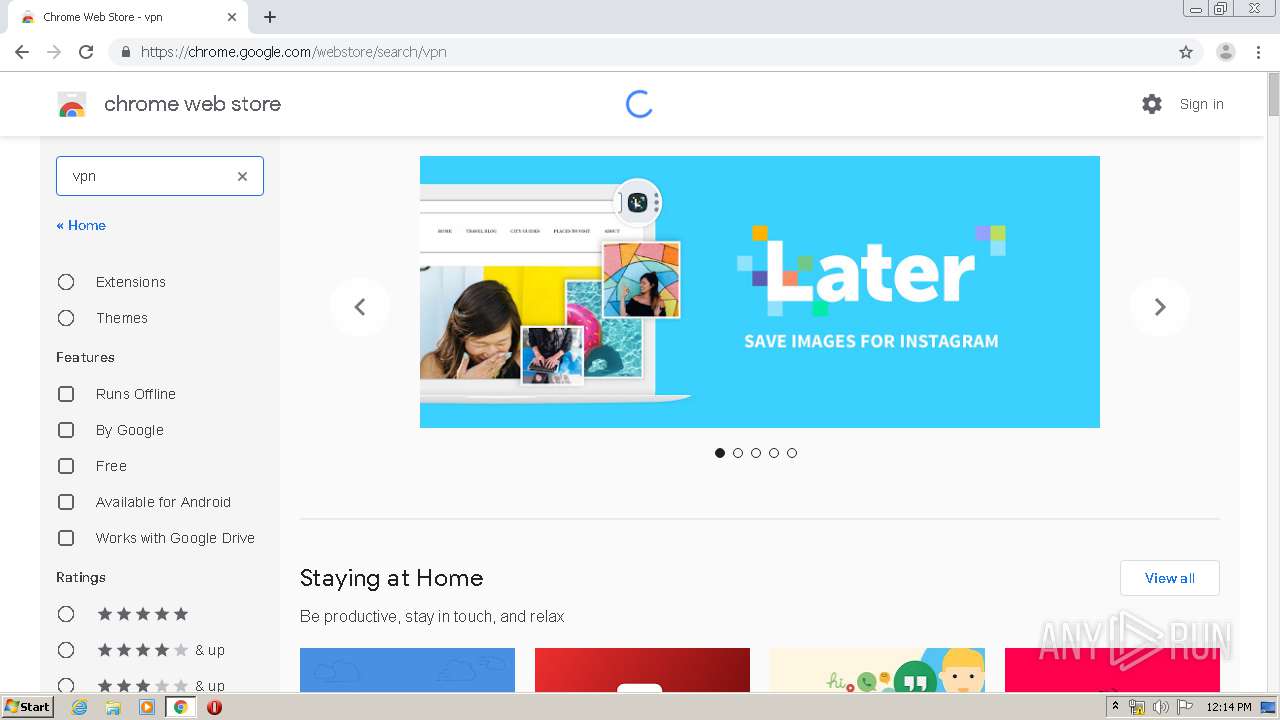
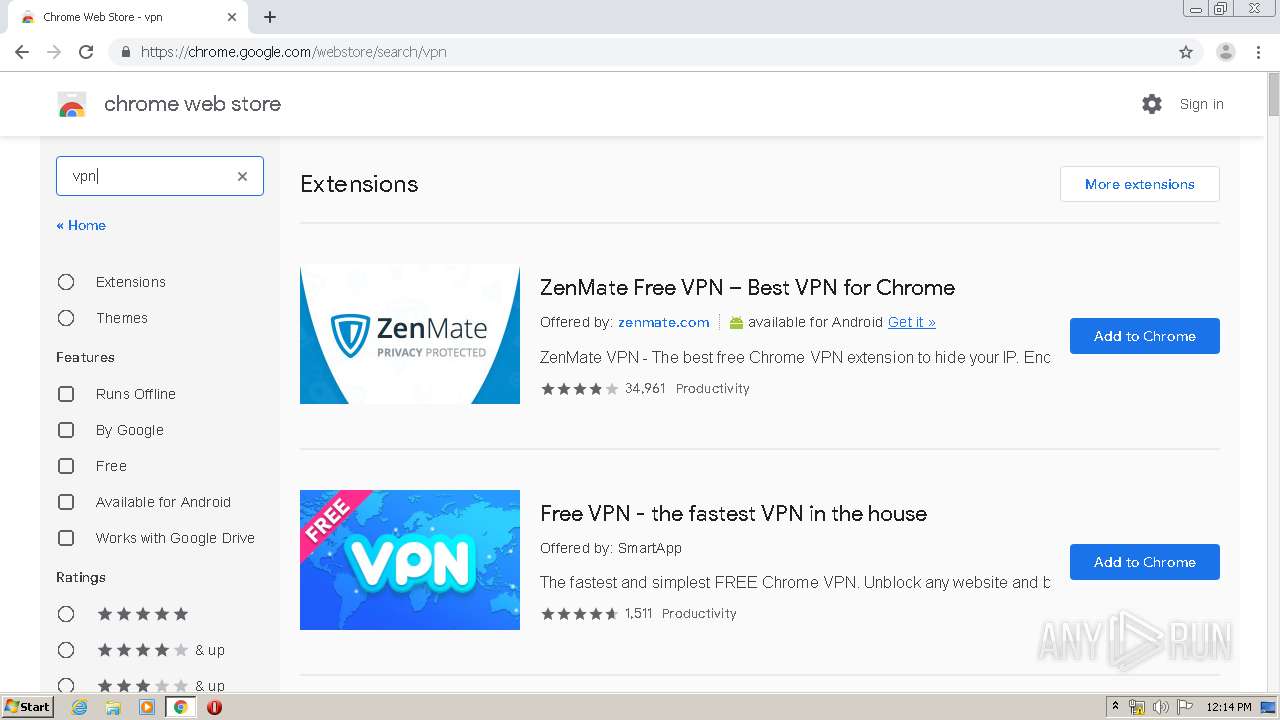
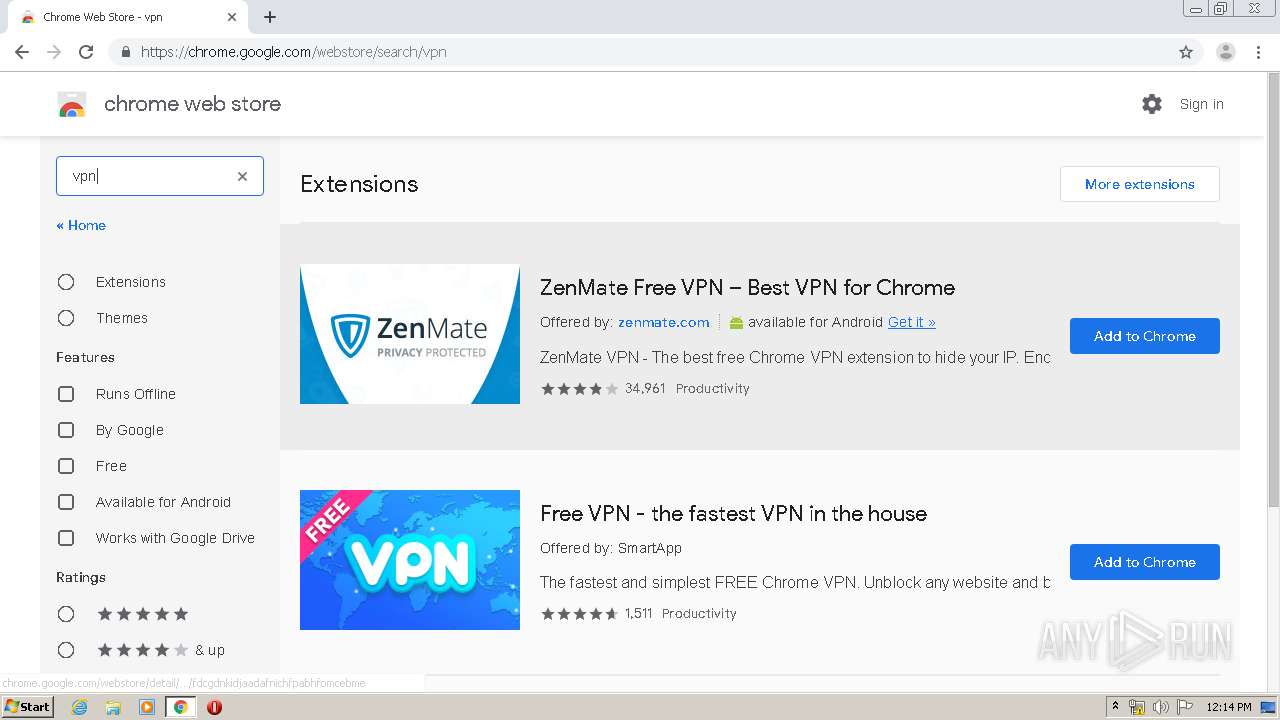
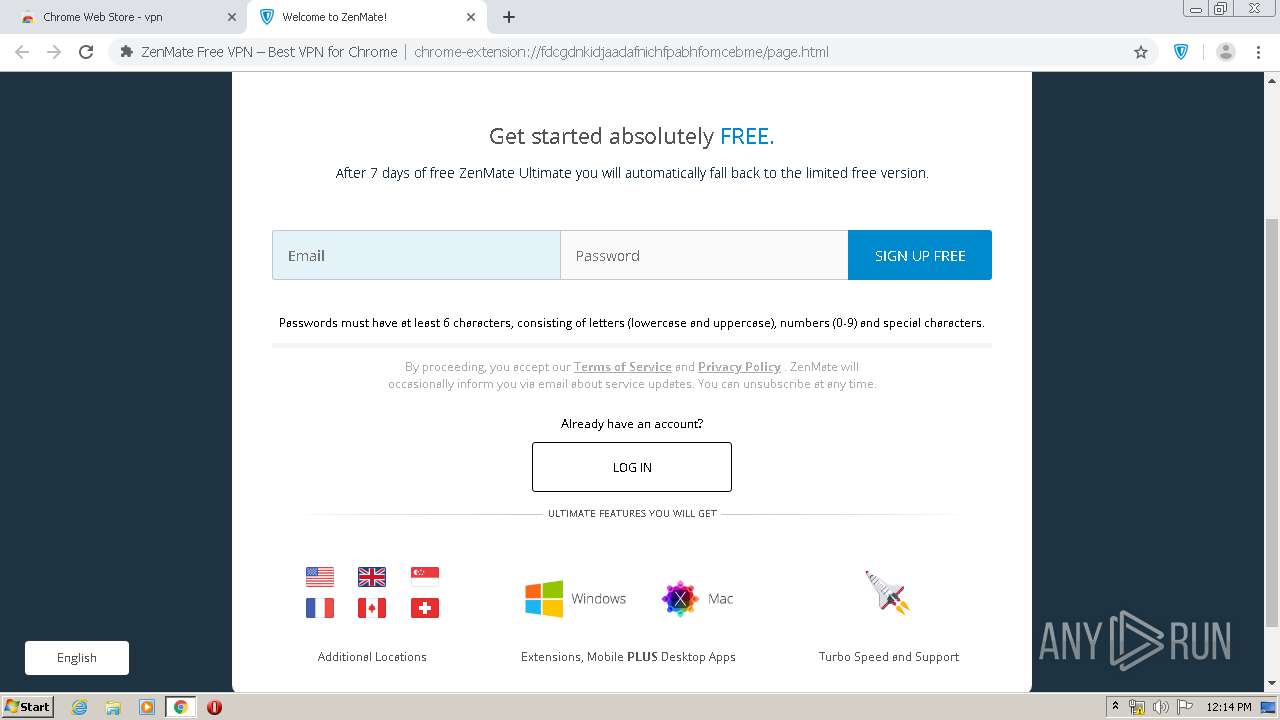
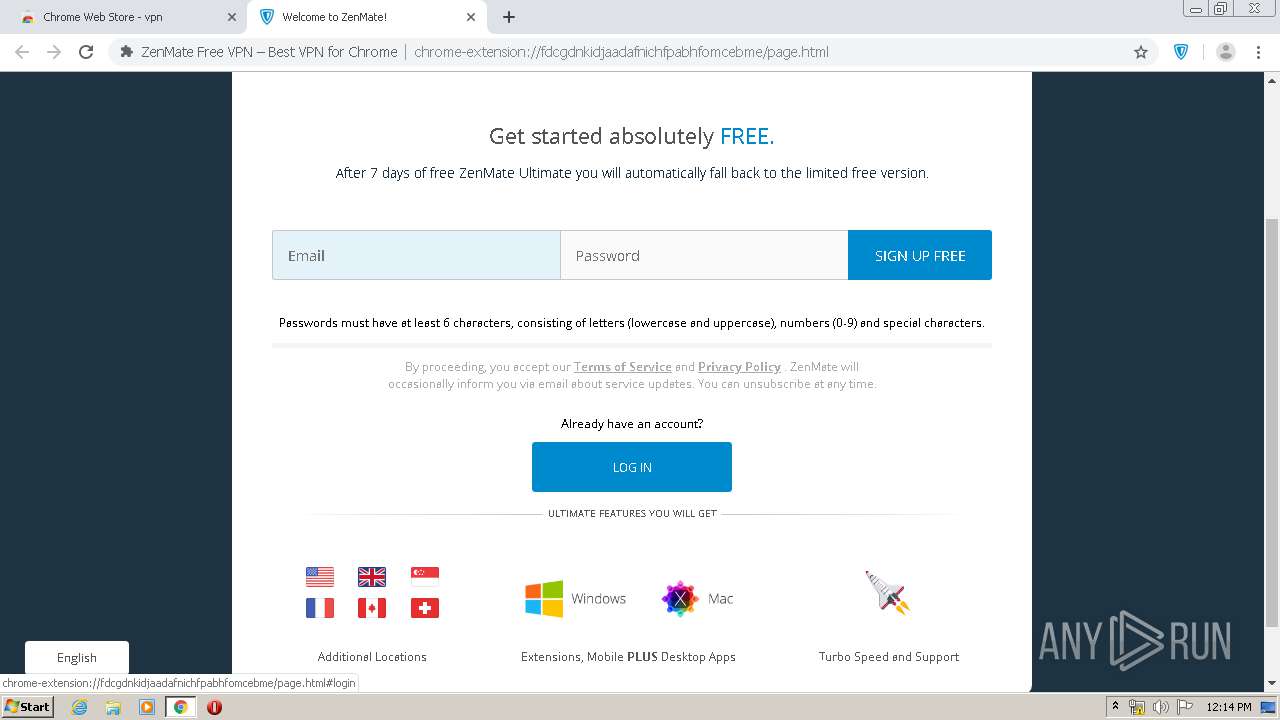
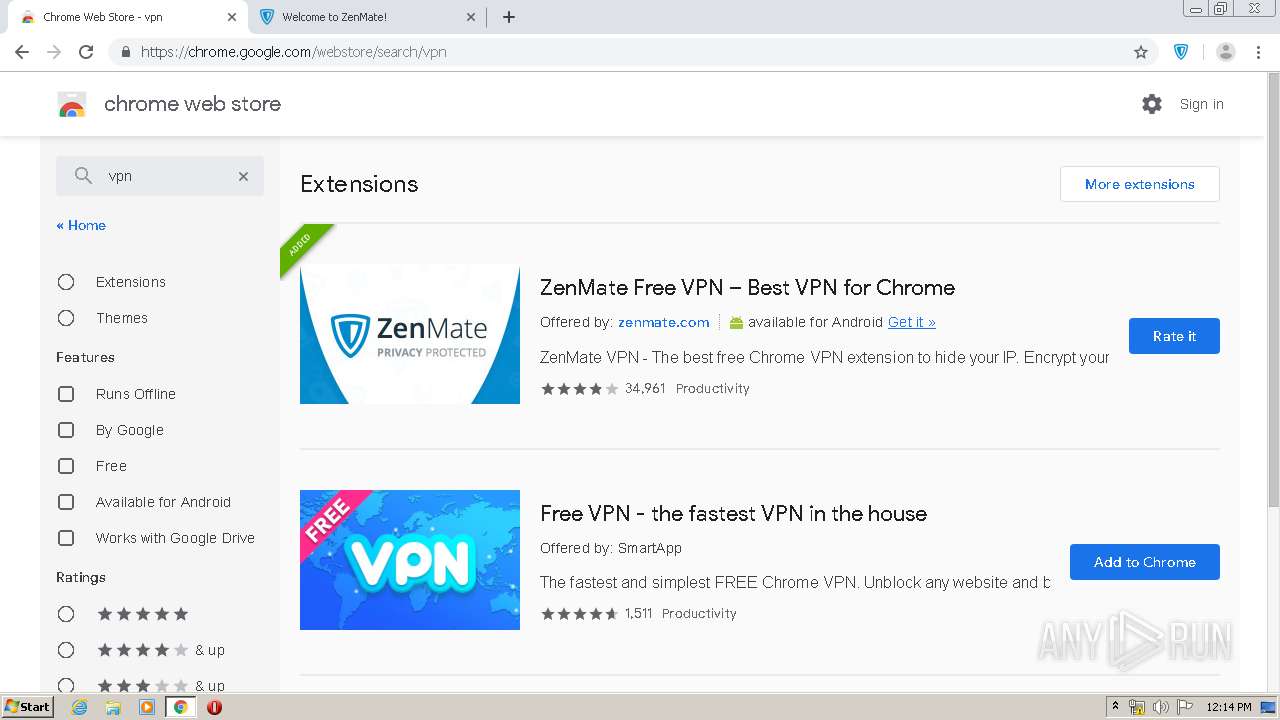
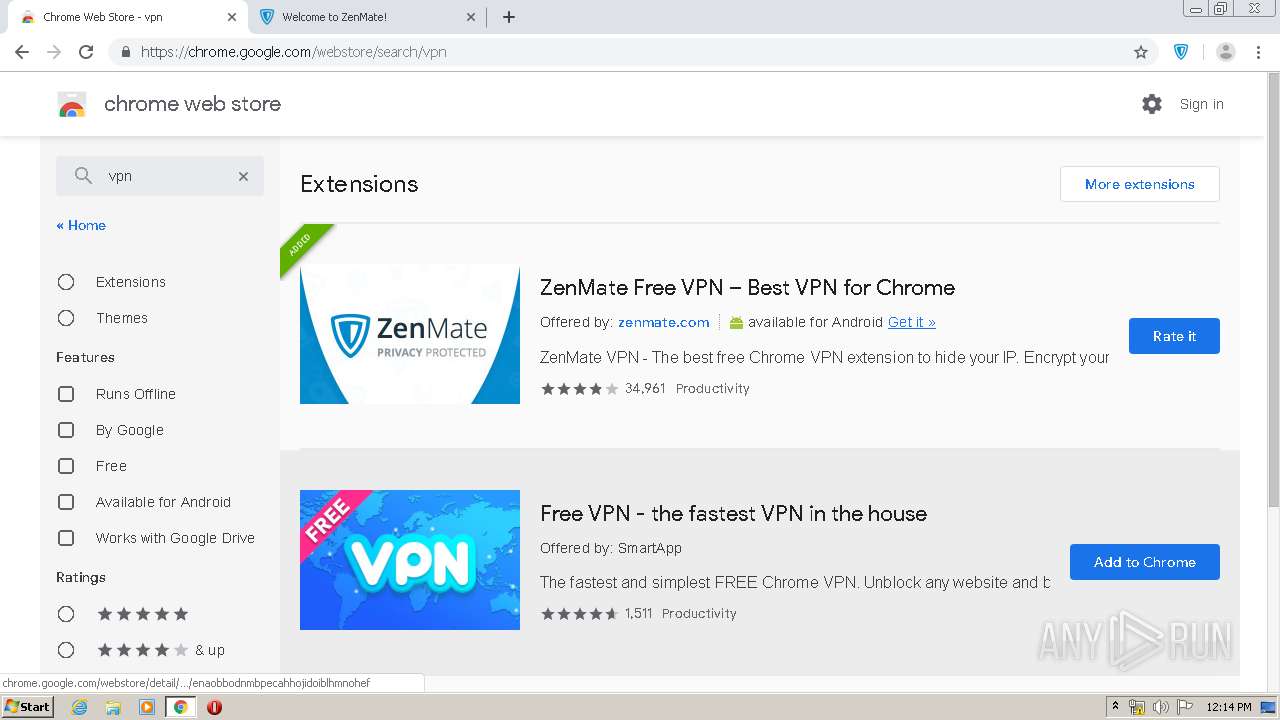
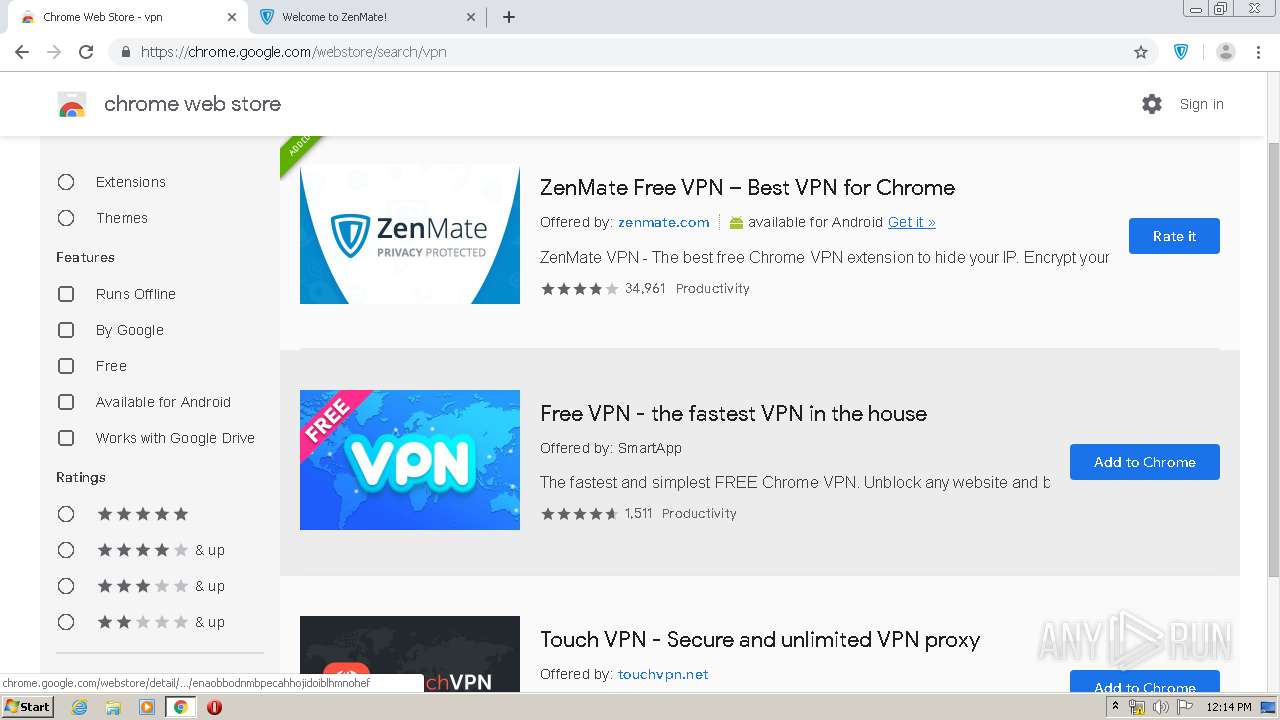
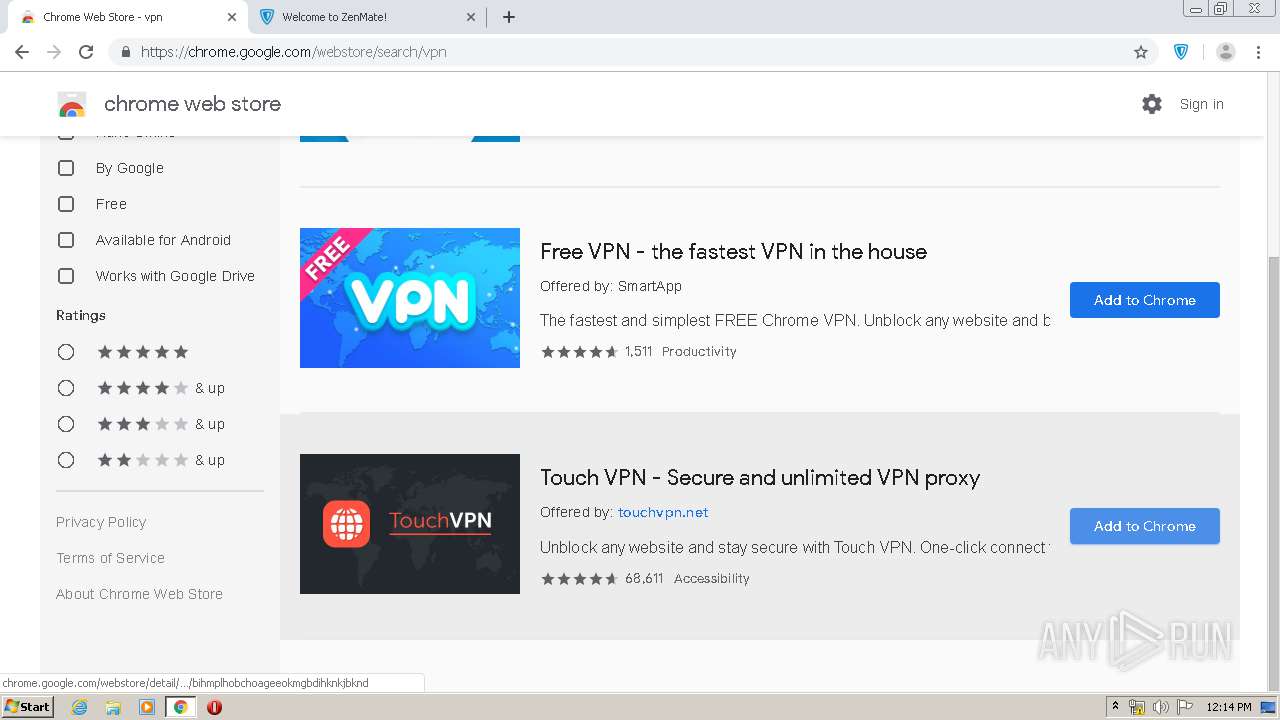
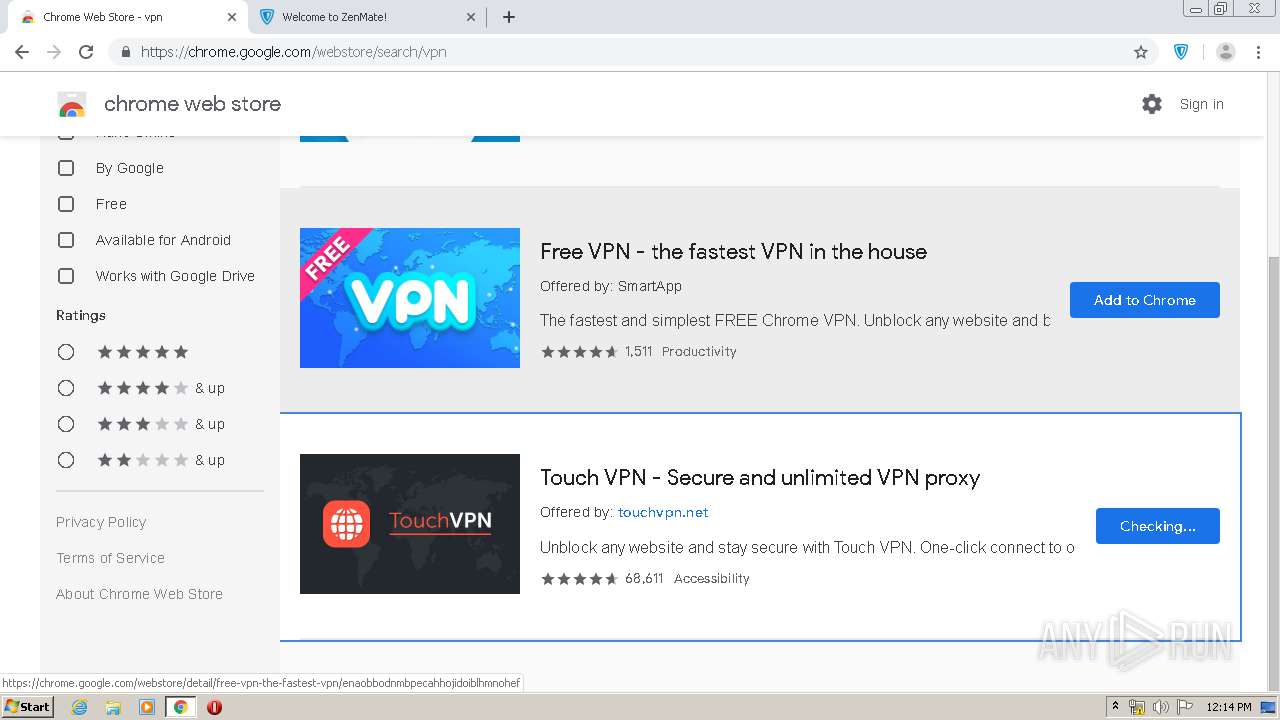
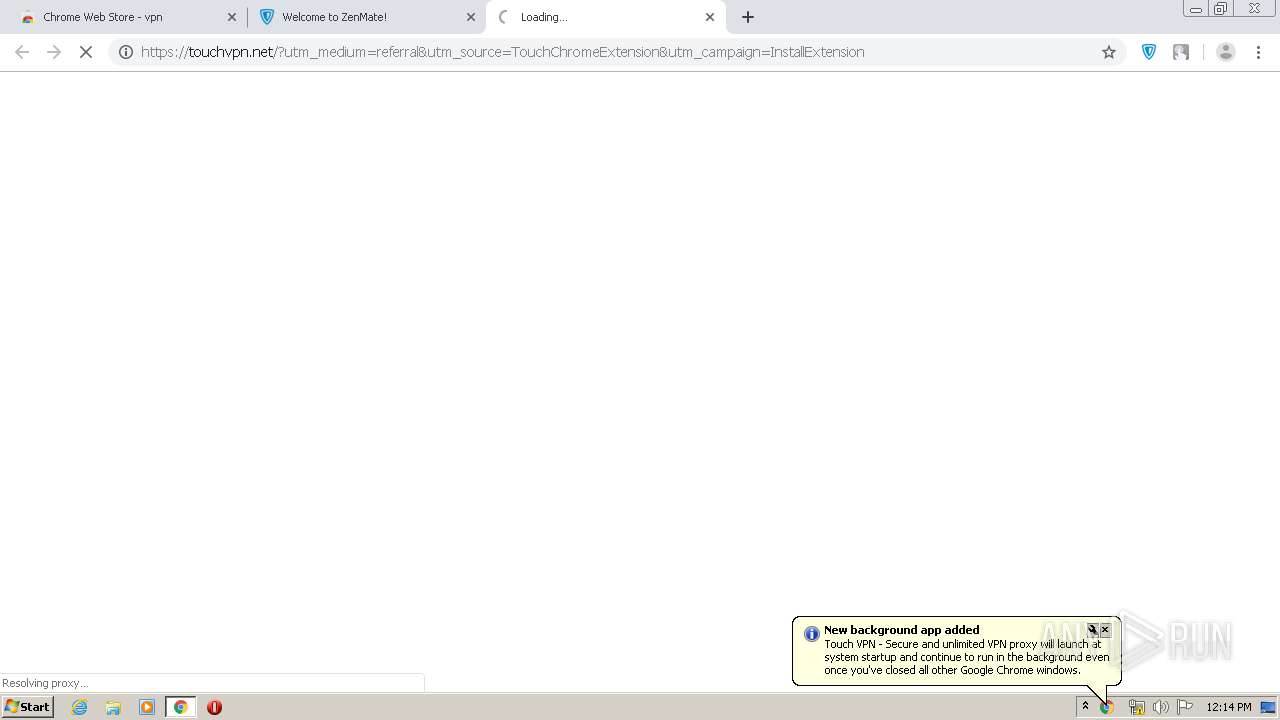
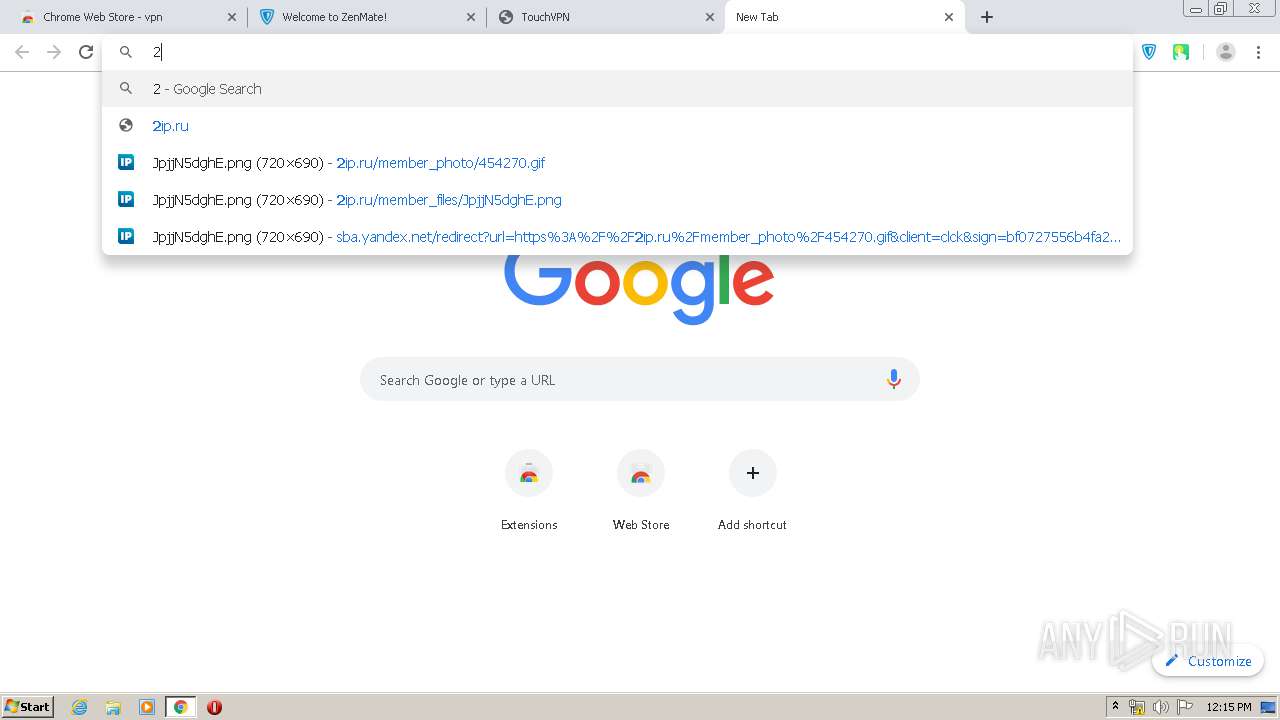
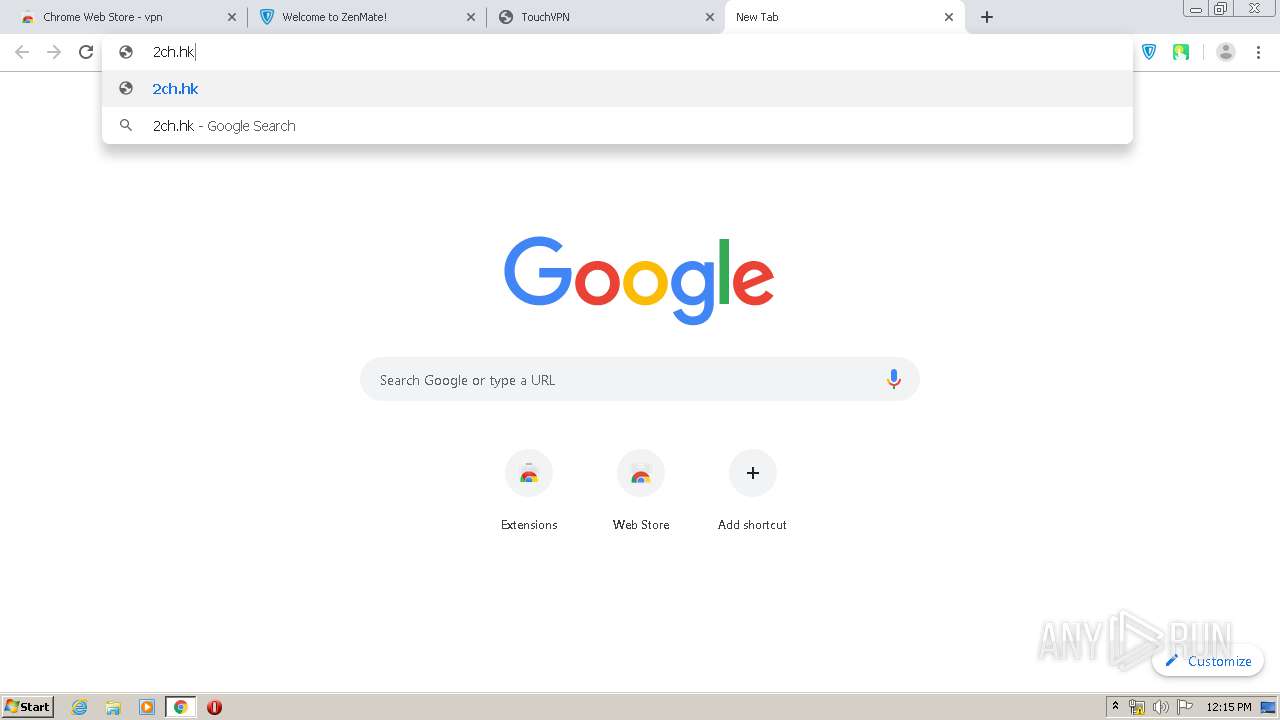
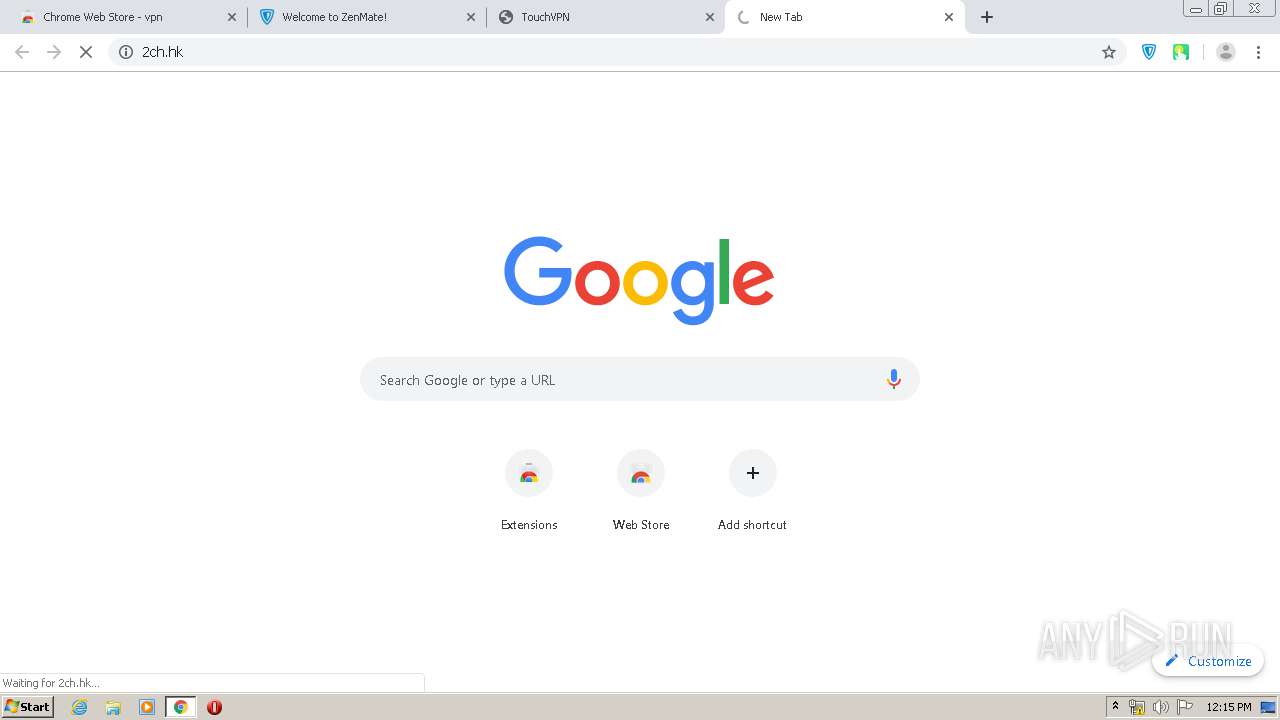
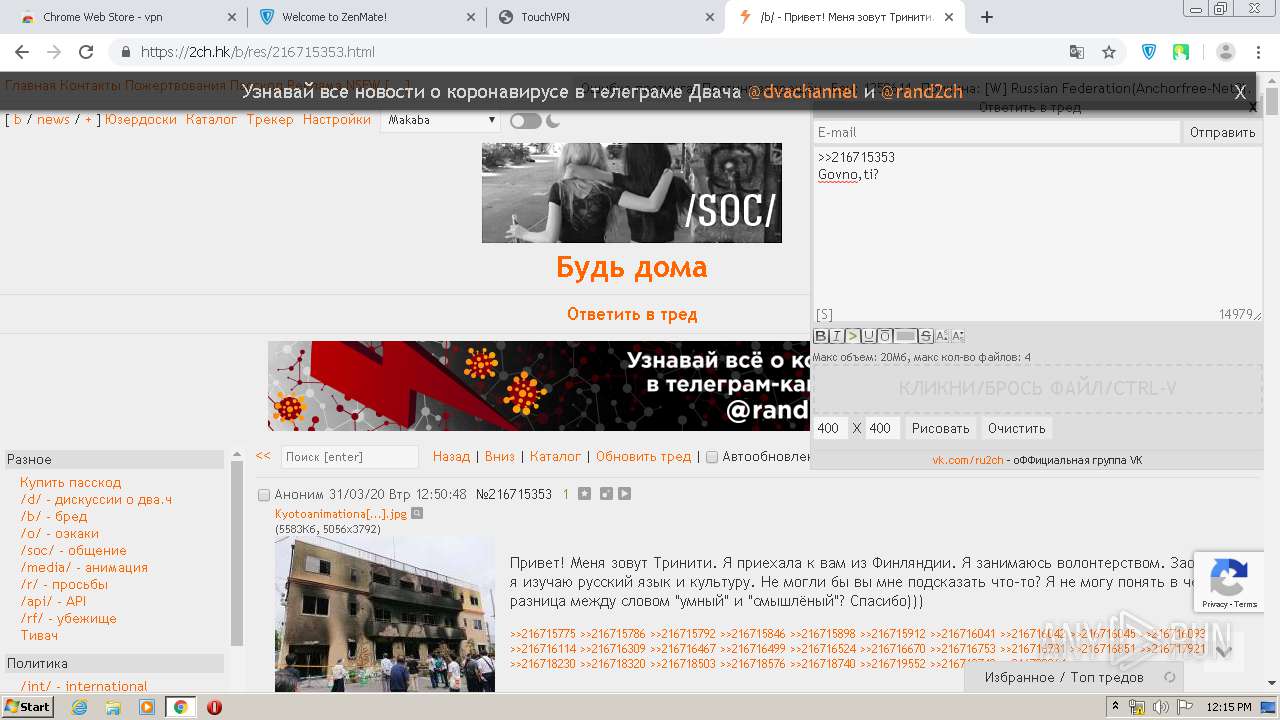
3252 | chrome.exe | GET | 301 | 172.217.16.142:80 | http://chrome.google.com/webstore | US | — | — | whitelisted |
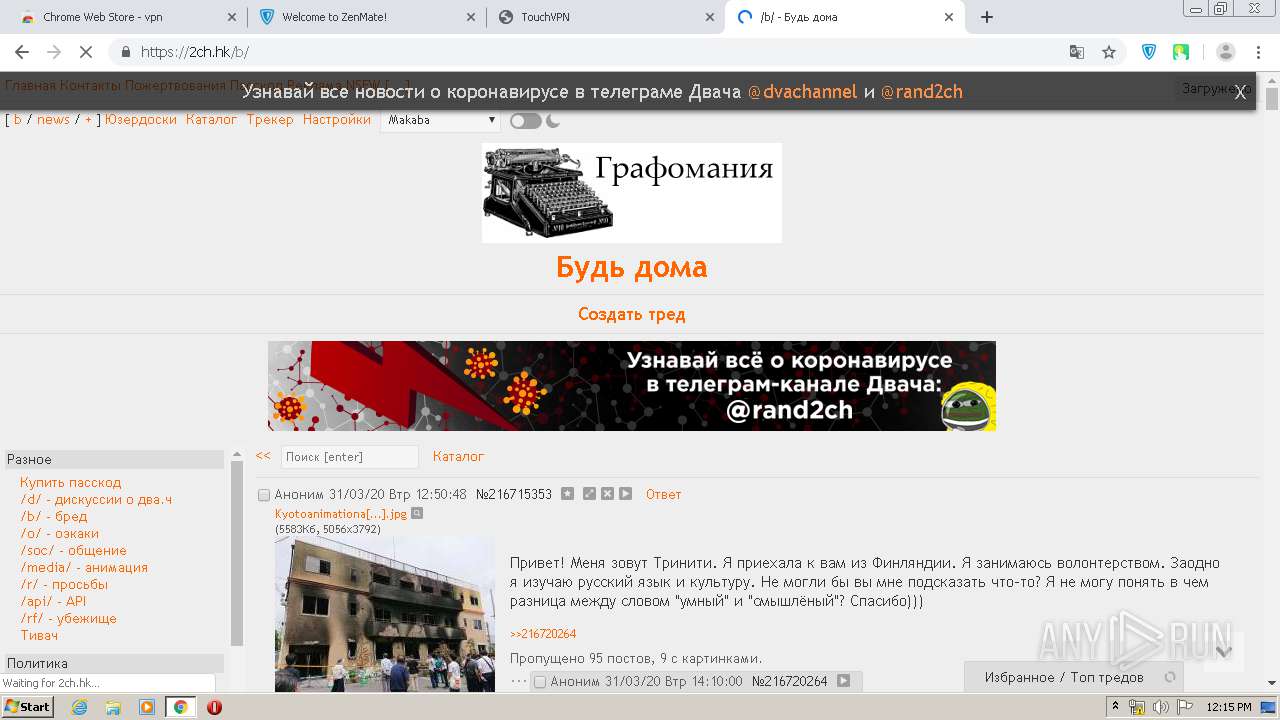
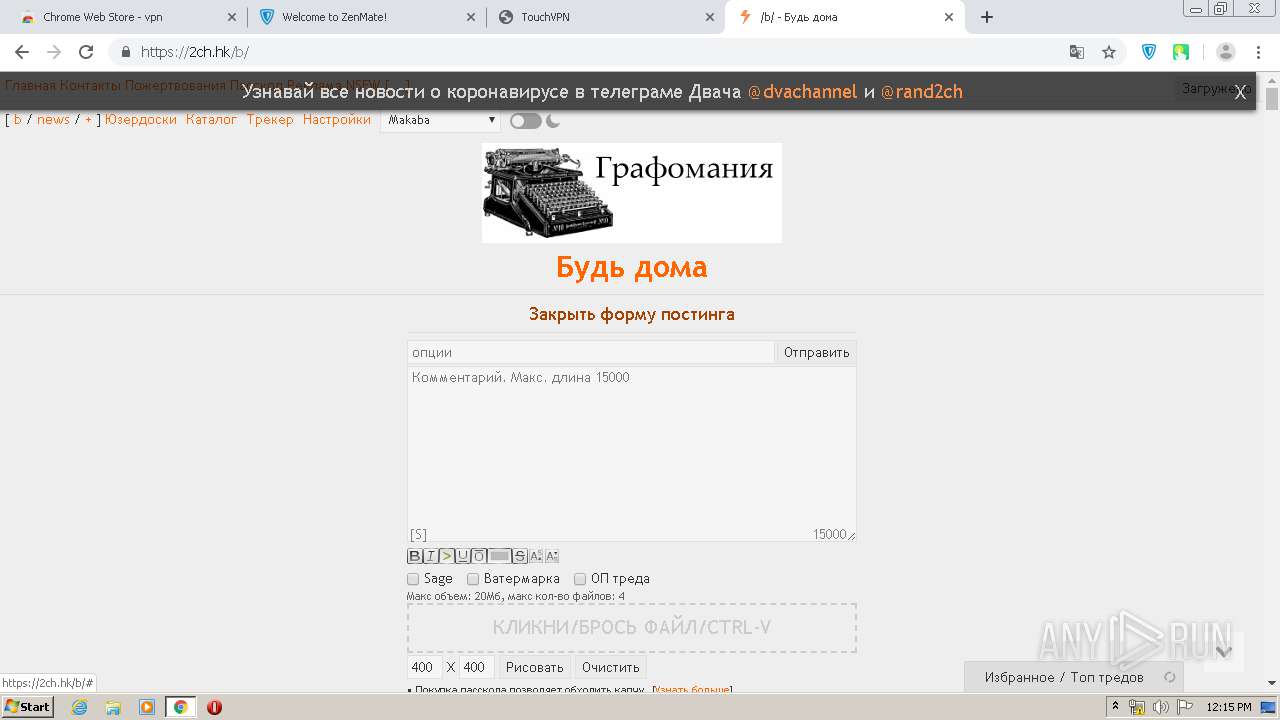
3252 | chrome.exe | GET | 200 | 195.201.201.32:80 | http://2ip.ru/member_files/JpjjN5dghE.png | RU | image | 427 Kb | shared |
3252 | chrome.exe | GET | 200 | 195.201.201.32:80 | http://2ip.ru/favicon.ico | RU | image | 1.12 Kb | shared |
3252 | chrome.exe | GET | 302 | 172.217.16.142:80 | http://www.google-analytics.com/r/__utm.gif?utmwv=5.7.2&utms=1&utmn=1932711176&utmhn=fdcgdnkidjaadafnichfpabhfomcebme&utmcs=UTF-8&utmsr=1280x720&utmvp=1264x620&utmsc=24-bit&utmul=en-us&utmje=0&utmfl=-&utmdt=Welcome%20to%20ZenMate!&utmhid=900063186&utmr=-&utmp=%2Fextension-welcome&utmht=1585653278537&utmac=UA-40329910-24&utmcc=__utma%3D194824314.96611138.1585653279.1585653279.1585653279.1%3B%2B__utmz%3D194824314.1585653279.1.1.utmcsr%3D(direct)%7Cutmccn%3D(direct)%7Cutmcmd%3D(none)%3B&utmjid=1121217788&utmredir=1&utmu=qACAAAAAAAAAAAAAAAAAAAAE~ | US | html | 370 b | whitelisted |
3252 | chrome.exe | GET | 302 | 172.217.16.206:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 519 b | whitelisted |
3252 | chrome.exe | GET | 302 | 172.217.16.206:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 524 b | whitelisted |
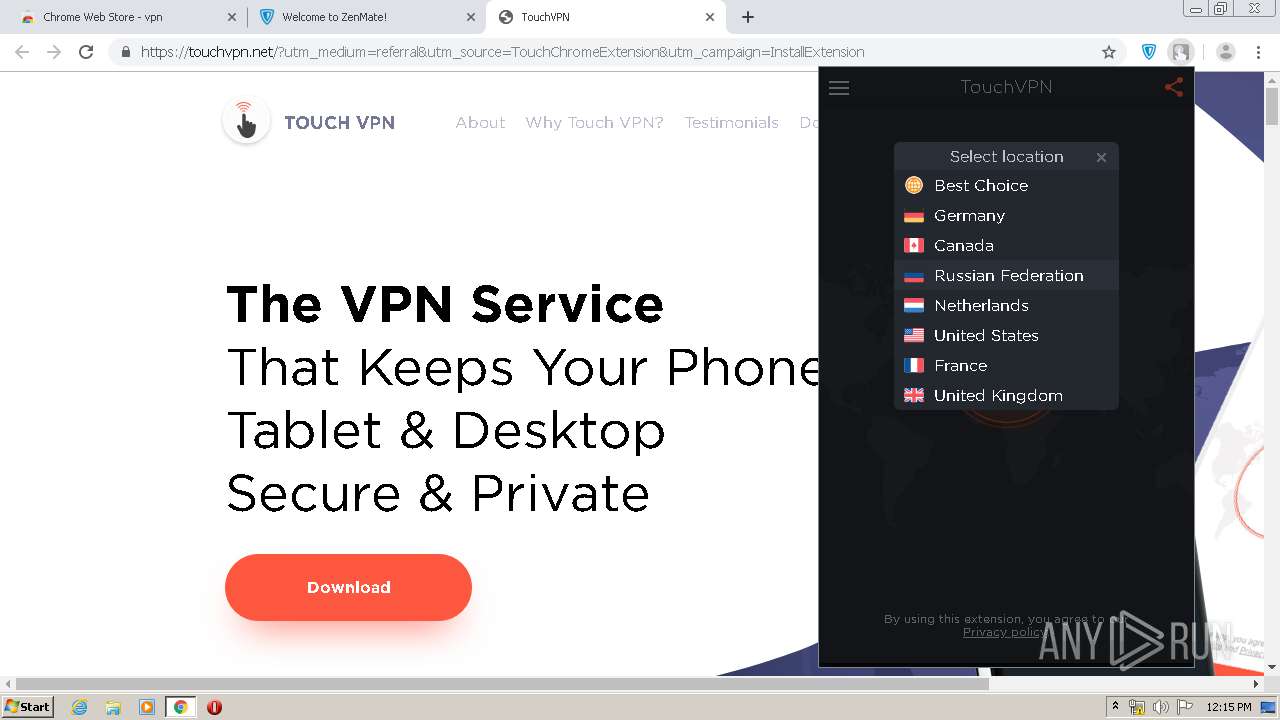
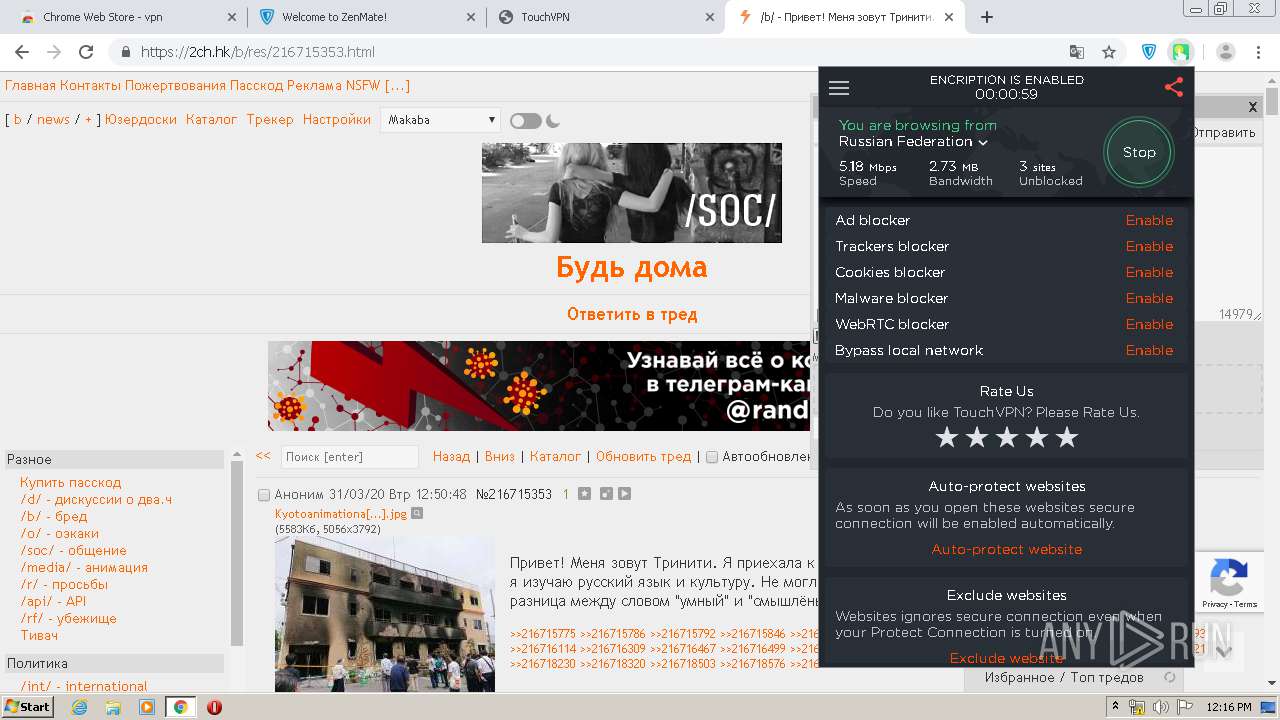
3252 | chrome.exe | GET | 200 | 173.194.182.136:80 | http://r3---sn-hpa7znsz.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mh=QJ&mip=82.102.26.195&mm=28&mn=sn-hpa7znsz&ms=nvh&mt=1585653136&mv=m&mvi=2&pl=25&shardbypass=yes | US | crx | 293 Kb | whitelisted |
3252 | chrome.exe | GET | 200 | 173.194.182.136:80 | http://r3---sn-hpa7znsz.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mh=bs&mip=82.102.26.195&mm=28&mn=sn-hpa7znsz&ms=nvh&mt=1585653136&mv=m&mvi=2&pl=25&shardbypass=yes | US | crx | 862 Kb | whitelisted |
3252 | chrome.exe | POST | 200 | 172.217.16.142:80 | http://www.google-analytics.com/collect | US | image | 35 b | whitelisted |
3252 | chrome.exe | POST | 200 | 172.217.16.142:80 | http://www.google-analytics.com/collect | US | image | 35 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3252 | chrome.exe | 172.217.18.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3252 | chrome.exe | 213.180.204.221:443 | clck.ru | YANDEX LLC | RU | whitelisted |
3252 | chrome.exe | 213.180.193.232:443 | sba.yandex.net | YANDEX LLC | RU | whitelisted |
3252 | chrome.exe | 195.201.201.32:443 | 2ip.ru | Awanti Ltd. | RU | malicious |
3252 | chrome.exe | 172.217.22.68:443 | www.google.com | Google Inc. | US | whitelisted |
3252 | chrome.exe | 172.217.16.206:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
3252 | chrome.exe | 173.194.182.136:80 | r3---sn-hpa7znsz.gvt1.com | Google Inc. | US | whitelisted |
3252 | chrome.exe | 172.217.16.205:443 | accounts.google.com | Google Inc. | US | whitelisted |
3252 | chrome.exe | 172.217.21.193:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
3252 | chrome.exe | 172.217.23.163:443 | www.google.es | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clck.ru |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
sba.yandex.net |
| whitelisted |
2ip.ru |
| shared |
www.google.com |
| malicious |
clients2.google.com |
| whitelisted |
redirector.gvt1.com |
| whitelisted |
r3---sn-hpa7znsz.gvt1.com |
| whitelisted |
clients2.googleusercontent.com |
| whitelisted |
Threats
3 ETPRO signatures available at the full report