| File name: | runme.exe |
| Full analysis: | https://app.any.run/tasks/a402eaec-4246-4710-9c5a-56bc623f3bf2 |
| Verdict: | Malicious activity |
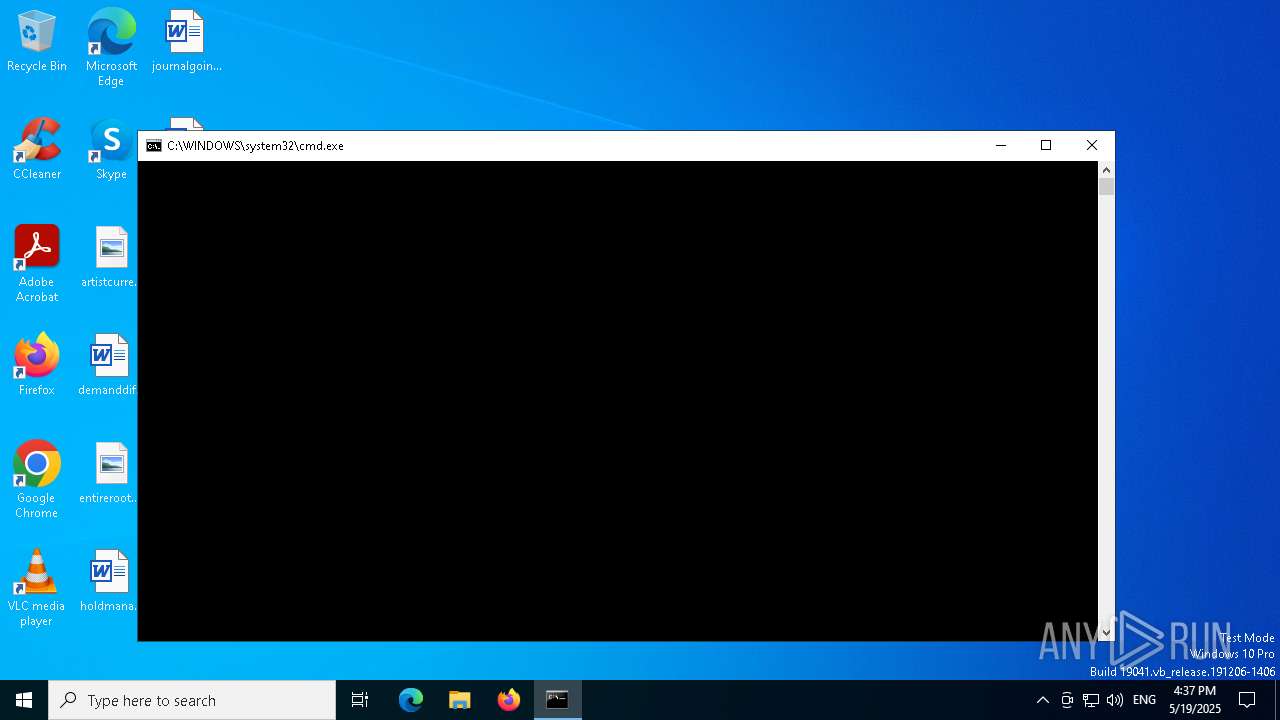
| Analysis date: | May 19, 2025, 15:37:07 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (console) Intel 80386 Mono/.Net assembly, for MS Windows, 3 sections |
| MD5: | 631131FB538B04A0D933F1C1DC6687E9 |
| SHA1: | 217BA59053FF88F9DBF3CA4F66AE5ED514E736E1 |
| SHA256: | AA3D3C44AF6DE324ADDC43F2ACD8F7B4F7F80DA78F8F4E2146BB91263FBDBC77 |
| SSDEEP: | 768:rjihtLef0Zp2zOOrWYj+M41v1xbVP3smnMlcw5Z:rjih40Zp2zOOrHydJ3jM5Z |
MALICIOUS
Run PowerShell with an invisible window
- powershell.exe (PID: 1164)
- powershell.exe (PID: 5640)
SUSPICIOUS
Reads security settings of Internet Explorer
- runme.exe (PID: 5680)
- runme.exe (PID: 4040)
BASE64 encoded PowerShell command has been detected
- runme.exe (PID: 5680)
- runme.exe (PID: 4040)
Starts POWERSHELL.EXE for commands execution
- runme.exe (PID: 5680)
- runme.exe (PID: 4040)
The process hide an interactive prompt from the user
- runme.exe (PID: 5680)
- runme.exe (PID: 4040)
Base64-obfuscated command line is found
- runme.exe (PID: 5680)
- runme.exe (PID: 4040)
INFO
Checks supported languages
- runme.exe (PID: 5680)
- runme.exe (PID: 4040)
Reads the computer name
- runme.exe (PID: 5680)
- runme.exe (PID: 4040)
Create files in a temporary directory
- runme.exe (PID: 5680)
- runme.exe (PID: 4040)
Reads Environment values
- runme.exe (PID: 5680)
- runme.exe (PID: 4040)
Reads the machine GUID from the registry
- runme.exe (PID: 5680)
- runme.exe (PID: 4040)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 1164)
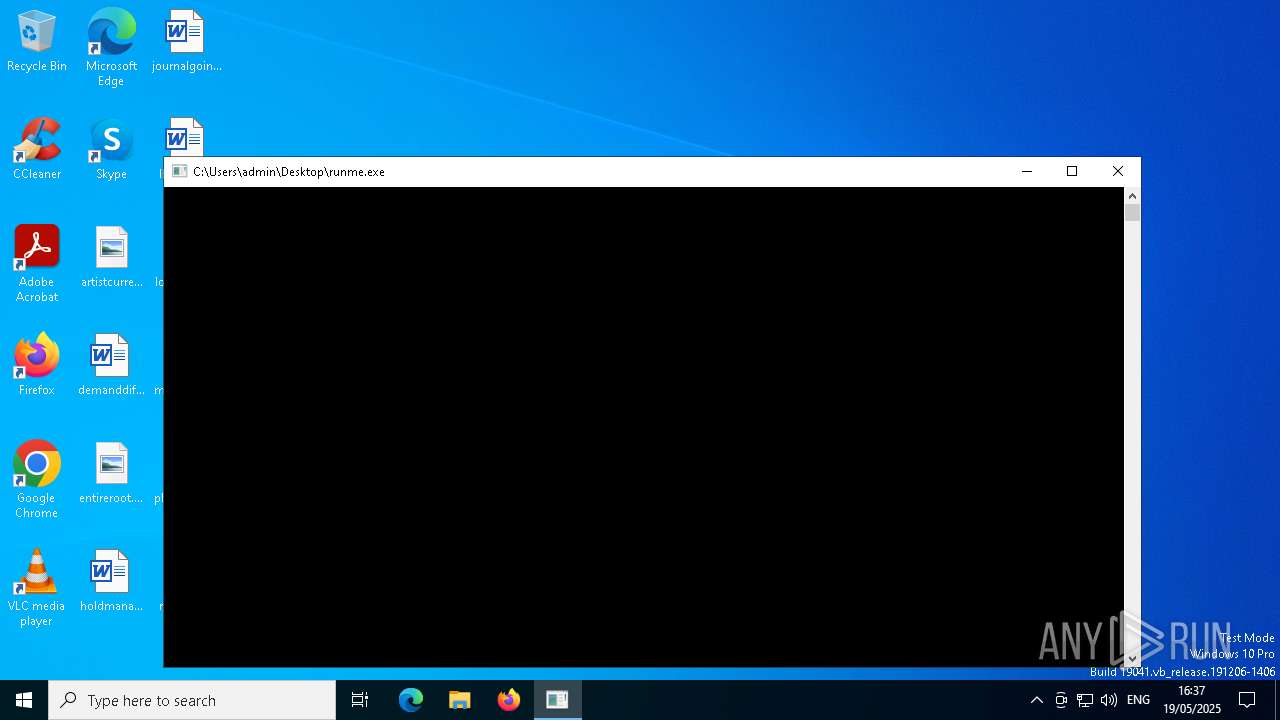
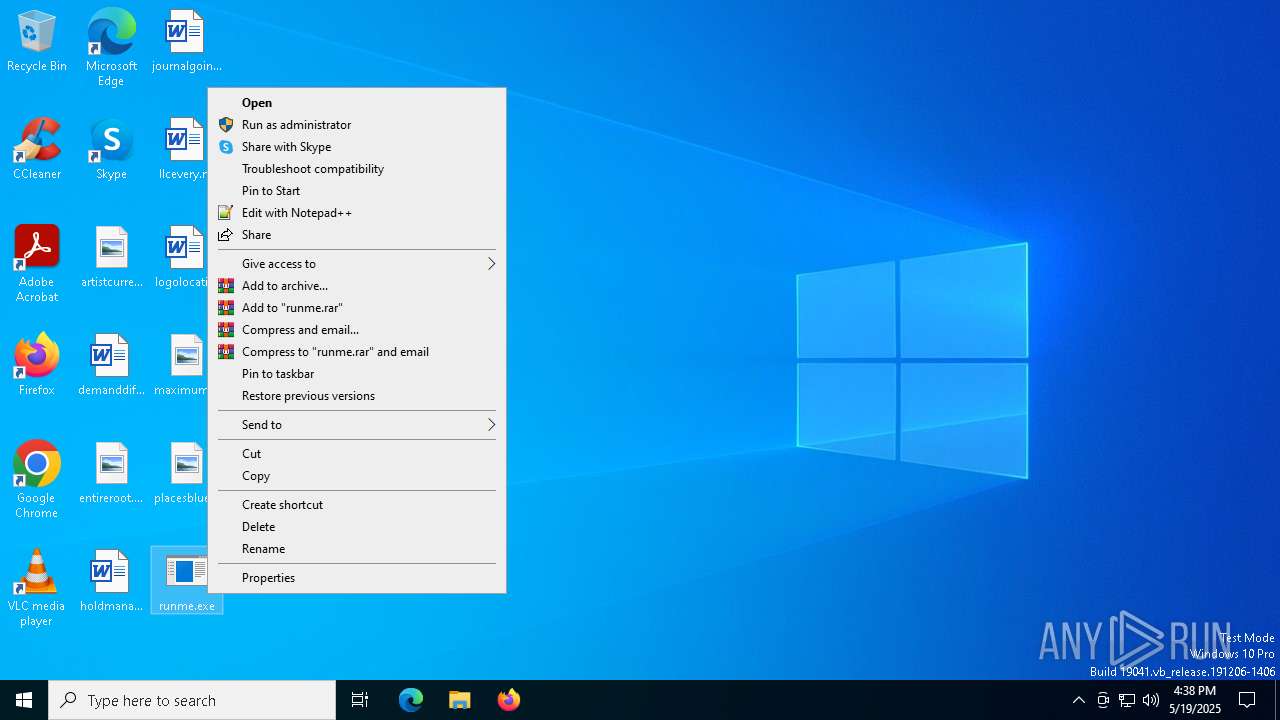
Manual execution by a user
- runme.exe (PID: 4040)
Reads the software policy settings
- slui.exe (PID: 4024)
Checks proxy server information
- slui.exe (PID: 4024)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (63.1) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (23.8) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.6) |
| .exe | | | Win32 Executable (generic) (3.8) |
| .exe | | | Generic Win/DOS Executable (1.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2025:05:19 15:34:43+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 11 |
| CodeSize: | 23552 |
| InitializedDataSize: | 2048 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x7a9e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows command line |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| FileDescription: | |
| FileVersion: | 0.0.0.0 |
| InternalName: | runme.exe |
| LegalCopyright: | |
| OriginalFileName: | runme.exe |
| ProductVersion: | 0.0.0.0 |
| AssemblyVersion: | 0.0.0.0 |
Total processes
142
Monitored processes
12
Malicious processes
0
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 616 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | runme.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 864 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1164 | "C:\WINDOWS\System32\WindowsPowerShell\v1.0\powershell.exe" -noninteractive -WindowStyle hidden -encodedCommand SQBuAHMAdABhAGwAbAAtAEwAYQBuAGcAdQBhAGcAZQAgAC0ATABhAG4AZwB1AGEAZwBlACAAYQByAC0AUwBBACAALQBDAG8AcAB5AFQAbwBTAGUAdAB0AGkAbgBnAHMAOwAgAFMAZQB0AC0AVwBpAG4AUwB5AHMAdABlAG0ATABvAGMAYQBsAGUAIABhAHIALQBTAEEAOwAgAFMAZQB0AC0AVwBpAG4AVQBzAGUAcgBMAGEAbgBnAHUAYQBnAGUATABpAHMAdAAgAGEAcgAtAFMAQQAgAC0ARgBvAHIAYwBlADsAIABTAGUAdAAtAFMAeQBzAHQAZQBtAFAAcgBlAGYAZQByAHIAZQBkAFUASQBMAGEAbgBnAHUAYQBnAGUAIAAtAEwAYQBuAGcAdQBhAGcAZQAgAGEAcgAtAFMAQQA7ACAAQwBvAHAAeQAtAFUAcwBlAHIASQBuAHQAZQByAG4AYQB0AGkAbwBuAGEAbABTAGUAdAB0AGkAbgBnAHMAVABvAFMAeQBzAHQAZQBtACAALQBXAGUAbABjAG8AbQBlAFMAYwByAGUAZQBuACAAJAB0AHIAdQBlACAALQBOAGUAdwBVAHMAZQByACAAJAB0AHIAdQBlADsAIABSAGUAcwB0AGEAcgB0AC0AQwBvAG0AcAB1AHQAZQByAA== -inputFormat xml -outputFormat xml | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | runme.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1328 | C:\WINDOWS\winsxs\amd64_microsoft-windows-servicingstack_31bf3856ad364e35_10.0.19041.3989_none_7ddb45627cb30e03\TiWorker.exe -Embedding | C:\Windows\WinSxS\amd64_microsoft-windows-servicingstack_31bf3856ad364e35_10.0.19041.3989_none_7ddb45627cb30e03\TiWorker.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Modules Installer Worker Version: 10.0.19041.3989 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3008 | C:\Windows\System32\coredpussvr.exe -Embedding | C:\Windows\System32\coredpussvr.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: coredpussvr.exe Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3240 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | runme.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4024 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4040 | "C:\Users\admin\Desktop\runme.exe" | C:\Users\admin\Desktop\runme.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Exit code: 3221225786 Version: 0.0.0.0 Modules
| |||||||||||||||
| 5640 | "C:\WINDOWS\System32\WindowsPowerShell\v1.0\powershell.exe" -noninteractive -WindowStyle hidden -encodedCommand SQBuAHMAdABhAGwAbAAtAEwAYQBuAGcAdQBhAGcAZQAgAC0ATABhAG4AZwB1AGEAZwBlACAAYQByAC0AUwBBACAALQBDAG8AcAB5AFQAbwBTAGUAdAB0AGkAbgBnAHMAOwAgAFMAZQB0AC0AVwBpAG4AUwB5AHMAdABlAG0ATABvAGMAYQBsAGUAIABhAHIALQBTAEEAOwAgAFMAZQB0AC0AVwBpAG4AVQBzAGUAcgBMAGEAbgBnAHUAYQBnAGUATABpAHMAdAAgAGEAcgAtAFMAQQAgAC0ARgBvAHIAYwBlADsAIABTAGUAdAAtAFMAeQBzAHQAZQBtAFAAcgBlAGYAZQByAHIAZQBkAFUASQBMAGEAbgBnAHUAYQBnAGUAIAAtAEwAYQBuAGcAdQBhAGcAZQAgAGEAcgAtAFMAQQA7ACAAQwBvAHAAeQAtAFUAcwBlAHIASQBuAHQAZQByAG4AYQB0AGkAbwBuAGEAbABTAGUAdAB0AGkAbgBnAHMAVABvAFMAeQBzAHQAZQBtACAALQBXAGUAbABjAG8AbQBlAFMAYwByAGUAZQBuACAAJAB0AHIAdQBlACAALQBOAGUAdwBVAHMAZQByACAAJAB0AHIAdQBlADsAIABSAGUAcwB0AGEAcgB0AC0AQwBvAG0AcAB1AHQAZQByAA== -inputFormat xml -outputFormat xml | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | runme.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5680 | "C:\Users\admin\Desktop\runme.exe" | C:\Users\admin\Desktop\runme.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Exit code: 0 Version: 0.0.0.0 Modules
| |||||||||||||||
Total events
19 596
Read events
19 480
Write events
103
Delete events
13
Modification events
| (PID) Process: | (1164) powershell.exe | Key: | HKEY_CURRENT_USER\Control Panel\International\User Profile\ar-SA |
| Operation: | write | Name: | CachedLanguageName |
Value: @Winlangdb.dll,-1021 | |||
| (PID) Process: | (1164) powershell.exe | Key: | HKEY_CURRENT_USER\Control Panel\International |
| Operation: | write | Name: | iLZero |
Value: 1 | |||
| (PID) Process: | (1164) powershell.exe | Key: | HKEY_CURRENT_USER\Control Panel\International |
| Operation: | write | Name: | iNegNumber |
Value: 1 | |||
| (PID) Process: | (1164) powershell.exe | Key: | HKEY_CURRENT_USER\Control Panel\International |
| Operation: | write | Name: | sNativeDigits |
Value: 0123456789 | |||
| (PID) Process: | (1164) powershell.exe | Key: | HKEY_CURRENT_USER\Control Panel\International |
| Operation: | write | Name: | NumShape |
Value: 1 | |||
| (PID) Process: | (1164) powershell.exe | Key: | HKEY_CURRENT_USER\Control Panel\International |
| Operation: | write | Name: | iMeasure |
Value: 1 | |||
| (PID) Process: | (1164) powershell.exe | Key: | HKEY_CURRENT_USER\Control Panel\International |
| Operation: | write | Name: | iFirstDayOfWeek |
Value: 6 | |||
| (PID) Process: | (1164) powershell.exe | Key: | HKEY_CURRENT_USER\Control Panel\International |
| Operation: | write | Name: | iFirstWeekOfYear |
Value: 0 | |||
| (PID) Process: | (1164) powershell.exe | Key: | HKEY_CURRENT_USER\Control Panel\International |
| Operation: | write | Name: | sGrouping |
Value: 3;0 | |||
| (PID) Process: | (1164) powershell.exe | Key: | HKEY_CURRENT_USER\Control Panel\International |
| Operation: | write | Name: | sMonGrouping |
Value: 3;0 | |||
Executable files
0
Suspicious files
3
Text files
11
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5680 | runme.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_xes3l1vc.ohp.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 1164 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_1g0004qn.5mz.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 1164 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_mwuxybuh.0zw.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 1164 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_dmv2tmy1.bv3.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5680 | runme.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_xxgpyc1s.05t.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 4040 | runme.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_fxzwbeej.4fn.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 1164 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_jsoyzkax.rkz.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 4040 | runme.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_0vunelxm.ppb.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5640 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_5pnhoseg.aej.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5640 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_k3y4xtr4.vcx.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
66
DNS requests
20
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5384 | SIHClient.exe | GET | 200 | 69.192.161.161:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.1.crl | unknown | — | — | whitelisted |
5384 | SIHClient.exe | GET | 200 | 23.216.77.30:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut_2010-06-23.crl | unknown | — | — | whitelisted |
5384 | SIHClient.exe | GET | 200 | 23.216.77.30:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5384 | SIHClient.exe | GET | 200 | 69.192.161.161:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5384 | SIHClient.exe | GET | 200 | 23.216.77.30:80 | http://crl.microsoft.com/pki/crl/products/MicTimStaPCA_2010-07-01.crl | unknown | — | — | whitelisted |
5384 | SIHClient.exe | GET | 200 | 69.192.161.161:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.1.crl | unknown | — | — | whitelisted |
5384 | SIHClient.exe | GET | 200 | 69.192.161.161:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.2.crl | unknown | — | — | whitelisted |
5384 | SIHClient.exe | GET | 200 | 69.192.161.161:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.2.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
3216 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5384 | SIHClient.exe | 4.175.87.197:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5384 | SIHClient.exe | 23.216.77.30:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5384 | SIHClient.exe | 69.192.161.161:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5384 | SIHClient.exe | 13.95.31.18:443 | fe3cr.delivery.mp.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4208 | slui.exe | 40.91.76.224:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |
login.live.com |
| whitelisted |