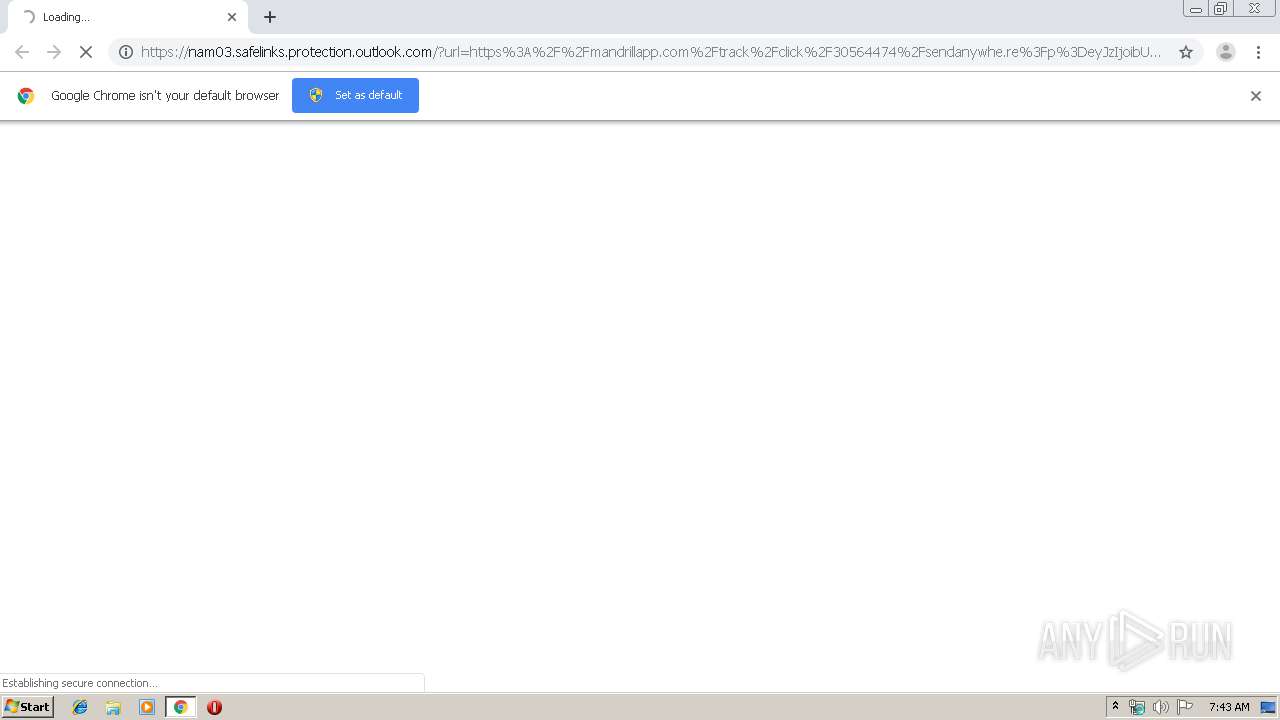
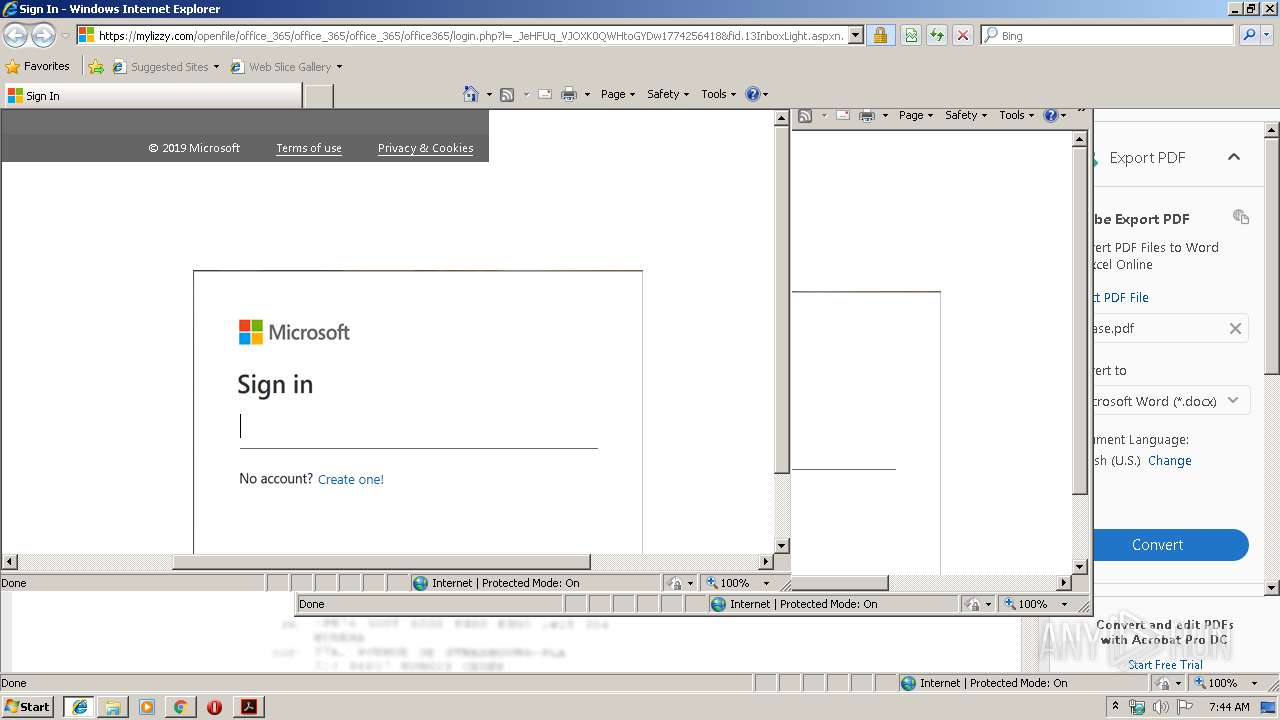
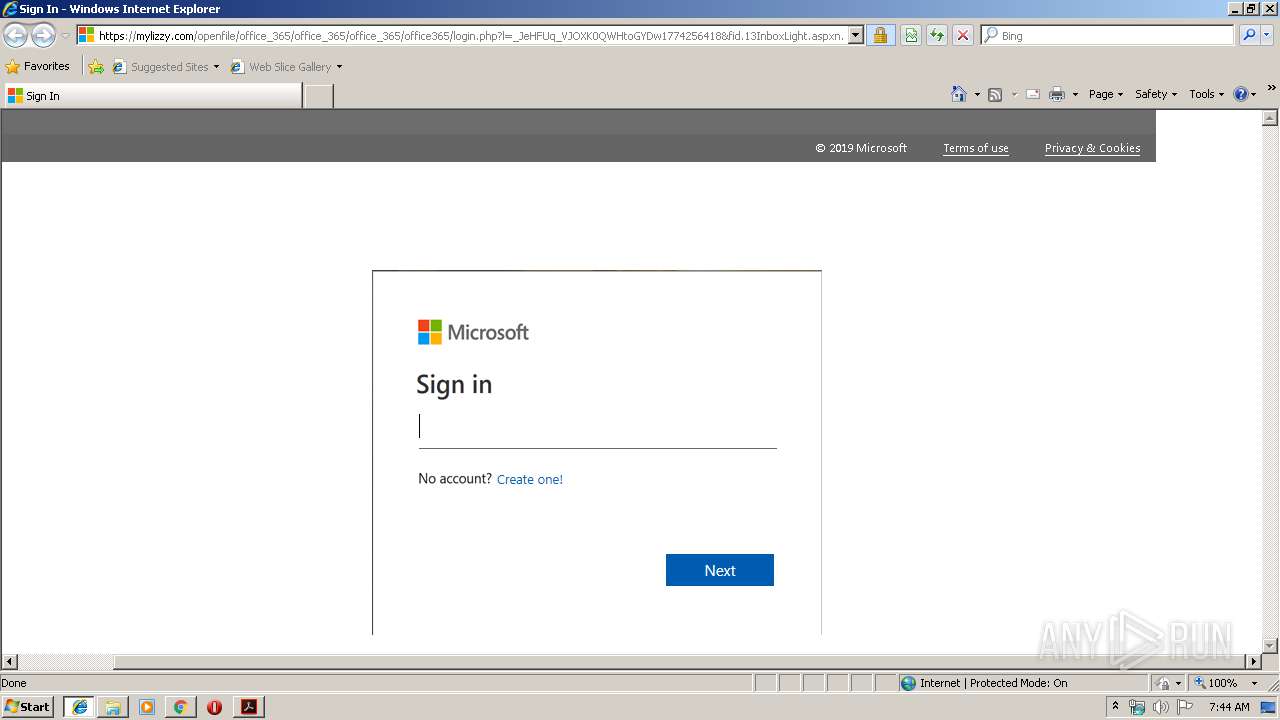
| URL: | https://nam03.safelinks.protection.outlook.com/?url=https%3A%2F%2Fmandrillapp.com%2Ftrack%2Fclick%2F30564474%2Fsendanywhe.re%3Fp%3DeyJzIjoibUhhMk1taDhERTNWWXR2OWxJbC0xam91ek9JIiwidiI6MSwicCI6IntcInVcIjozMDU2NDQ3NCxcInZcIjoxLFwidXJsXCI6XCJodHRwOlxcXC9cXFwvc2VuZGFueXdoZS5yZVxcXC8wOE5PQlVJTlwiLFwiaWRcIjpcIjI4NTNiMjVhYmZlNTQzYjM4NmQ1MTVjMjc0YjUwMWUxXCIsXCJ1cmxfaWRzXCI6W1wiMWY1NmQ1NmNlMmNiMWRmNjRmOGM2YjZiMTBjMTk2ZmYzYmNkOTMzYVwiXX0ifQ&data=01%7C01%7CGary.Bischoping%40varian.com%7C7ebac692185d4b2da9ac08d74e511d74%7Cc49d9c494b114ccdb13772f88c68a252%7C1&sdata=kFd59HDnKI9pOQT1Cth%2BEuINat3umO1EGf6jYBZFN68%3D&reserved=0 |
| Full analysis: | https://app.any.run/tasks/4e323f1f-4e1a-4e7d-b601-b1235afef72f |
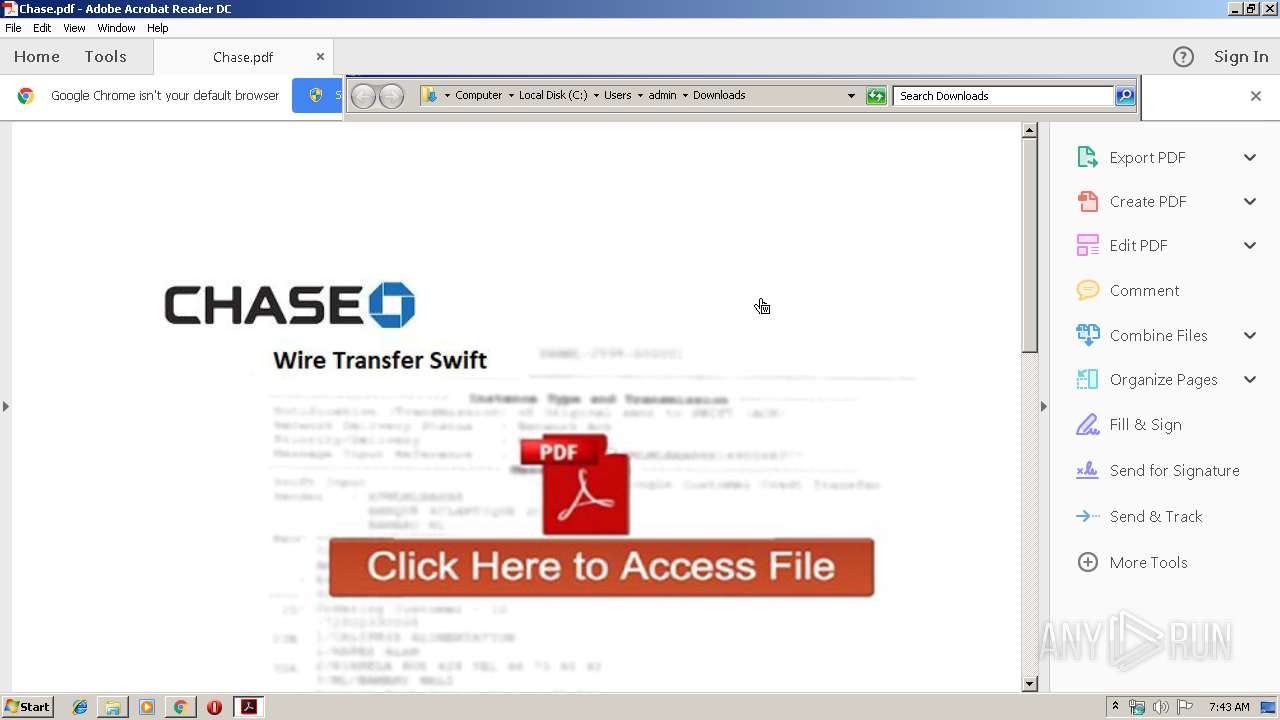
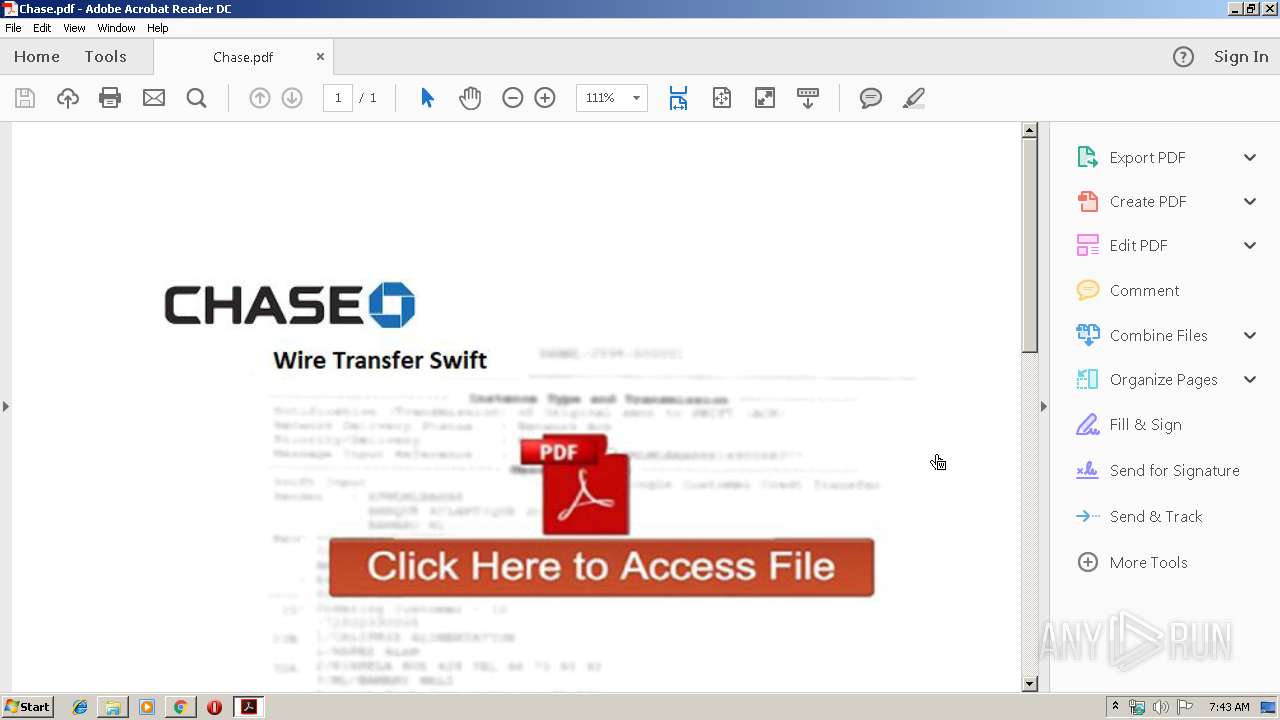
| Verdict: | Malicious activity |
| Analysis date: | October 14, 2019, 06:43:18 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 95769CFD1C245B62A2BD4BA329A9787C |
| SHA1: | 4B95558989904B513AE546A07099AD93DA59D0E4 |
| SHA256: | AA22EBE069F5301D72366AE4FCB303B9F9C0020530FD547334A04C9E160FF118 |
| SSDEEP: | 12:2qqxYx8yNHlCkAyVO1cVVjxOc3+slxwXIFY63AddwlqRCiE+kyIQ:2qqo8yHoyVscP/xSzulSEoj |
MALICIOUS
No malicious indicators.SUSPICIOUS
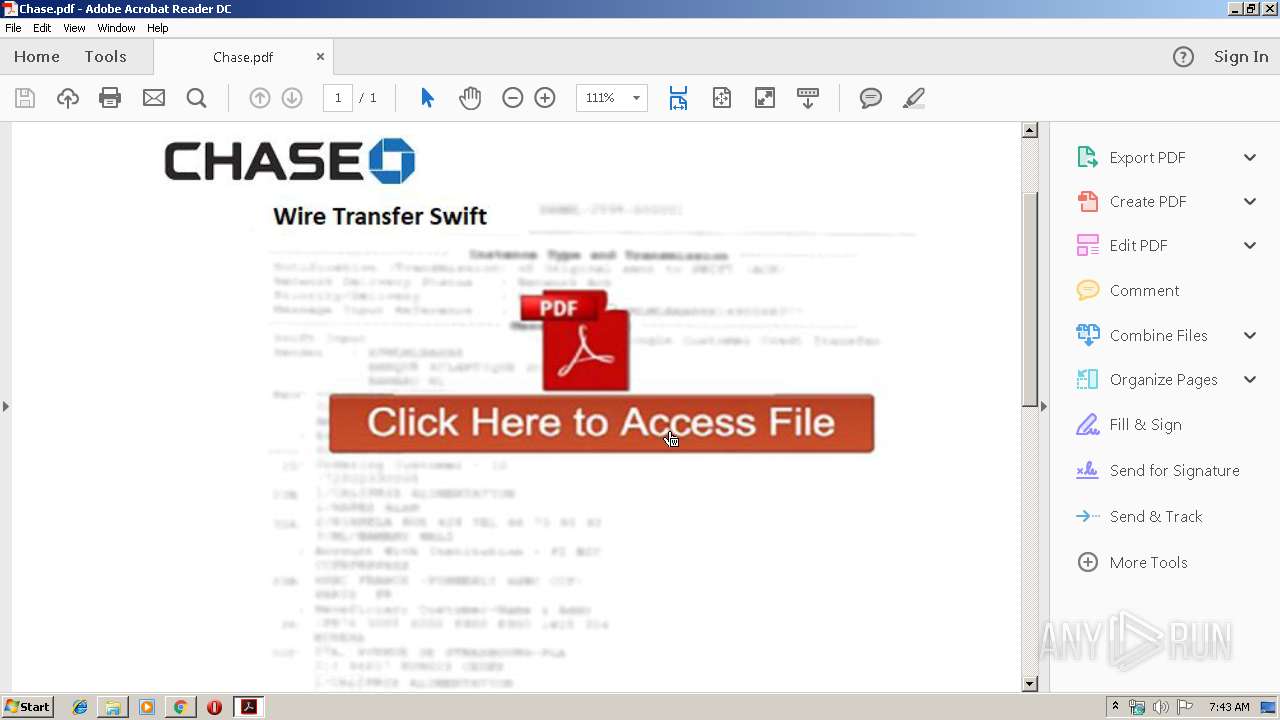
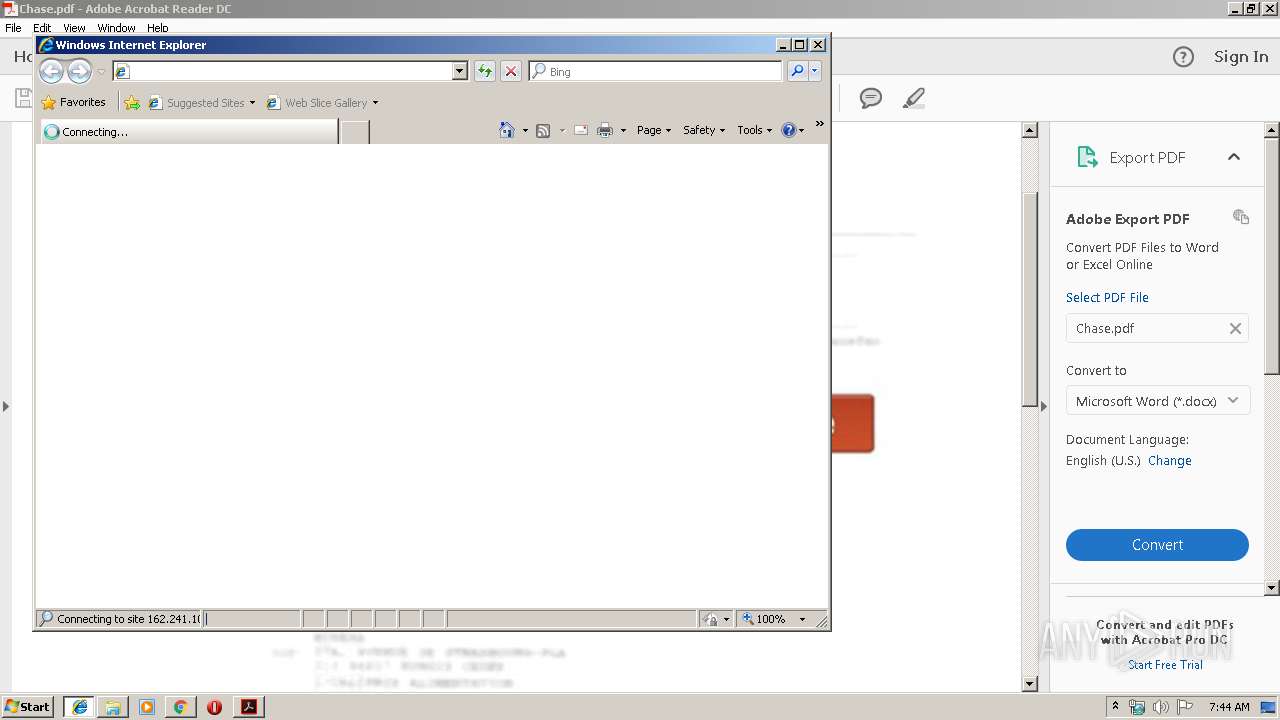
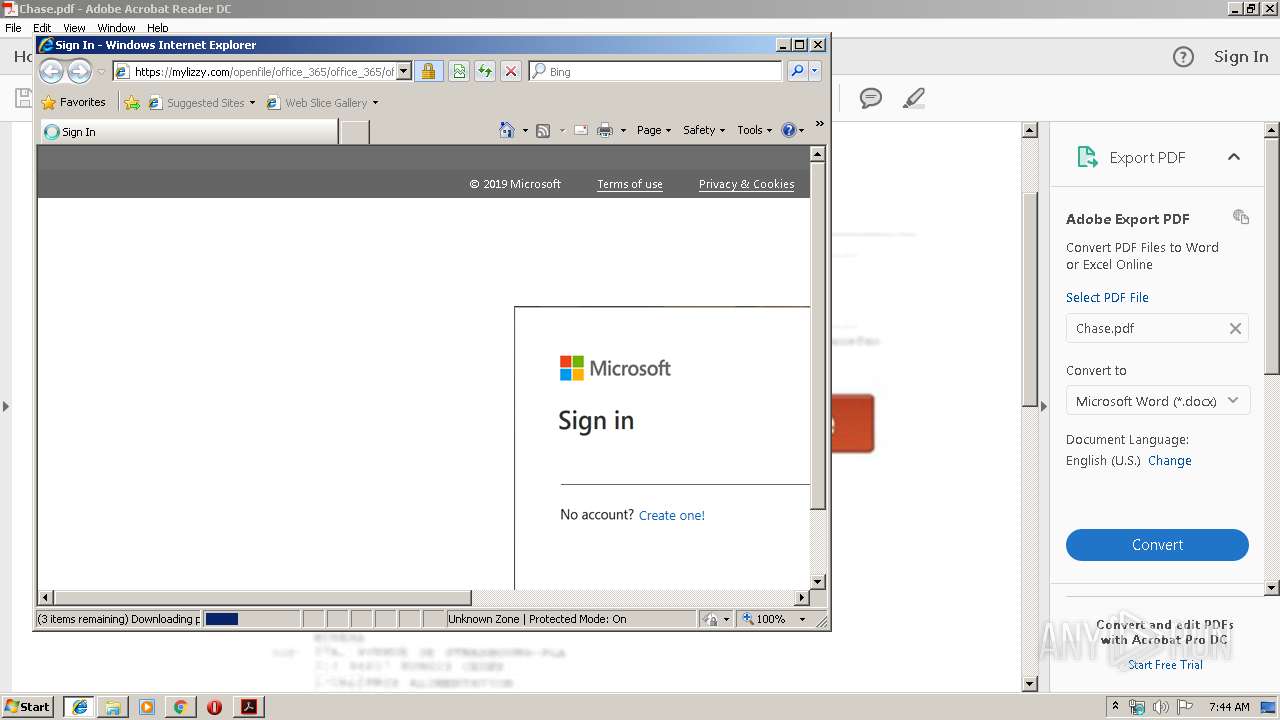
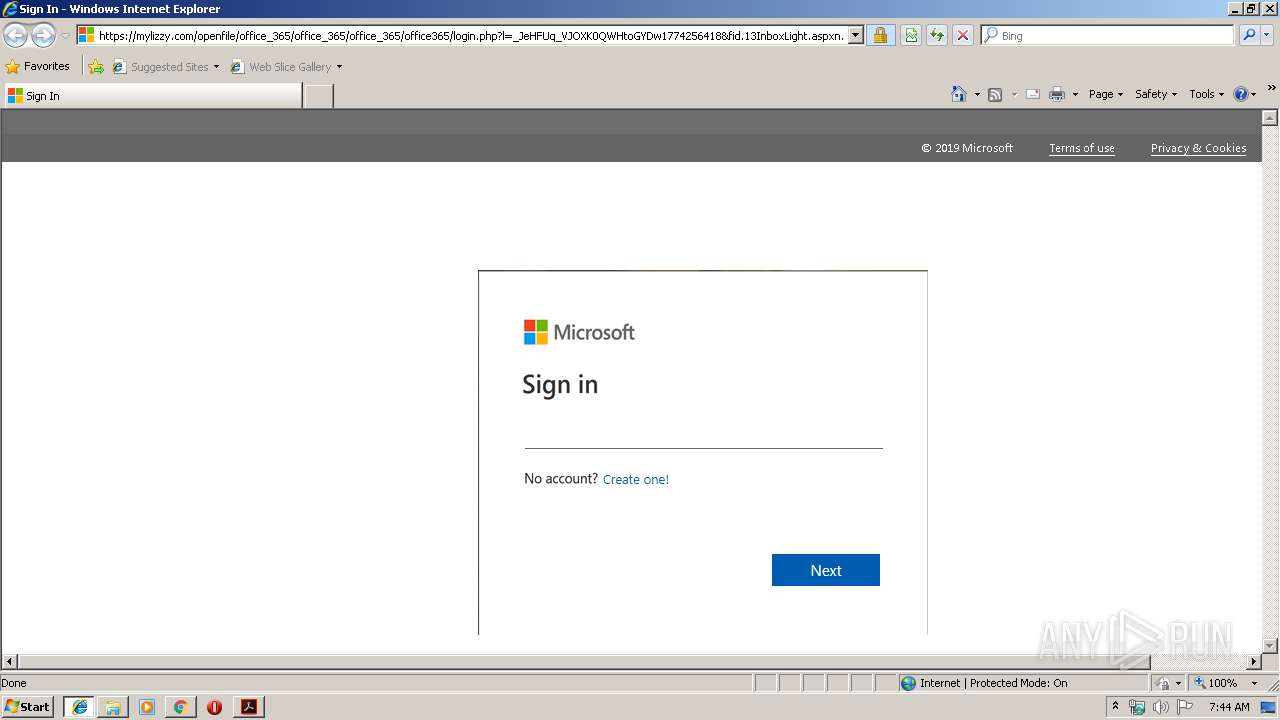
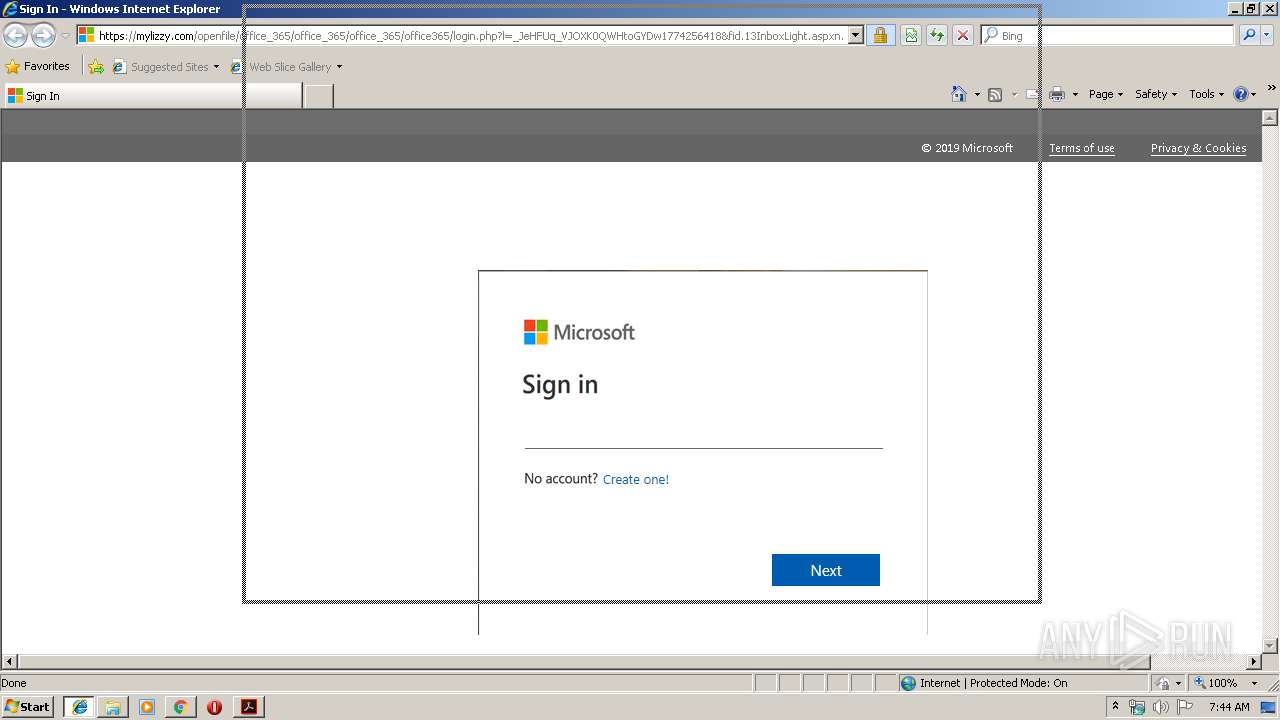
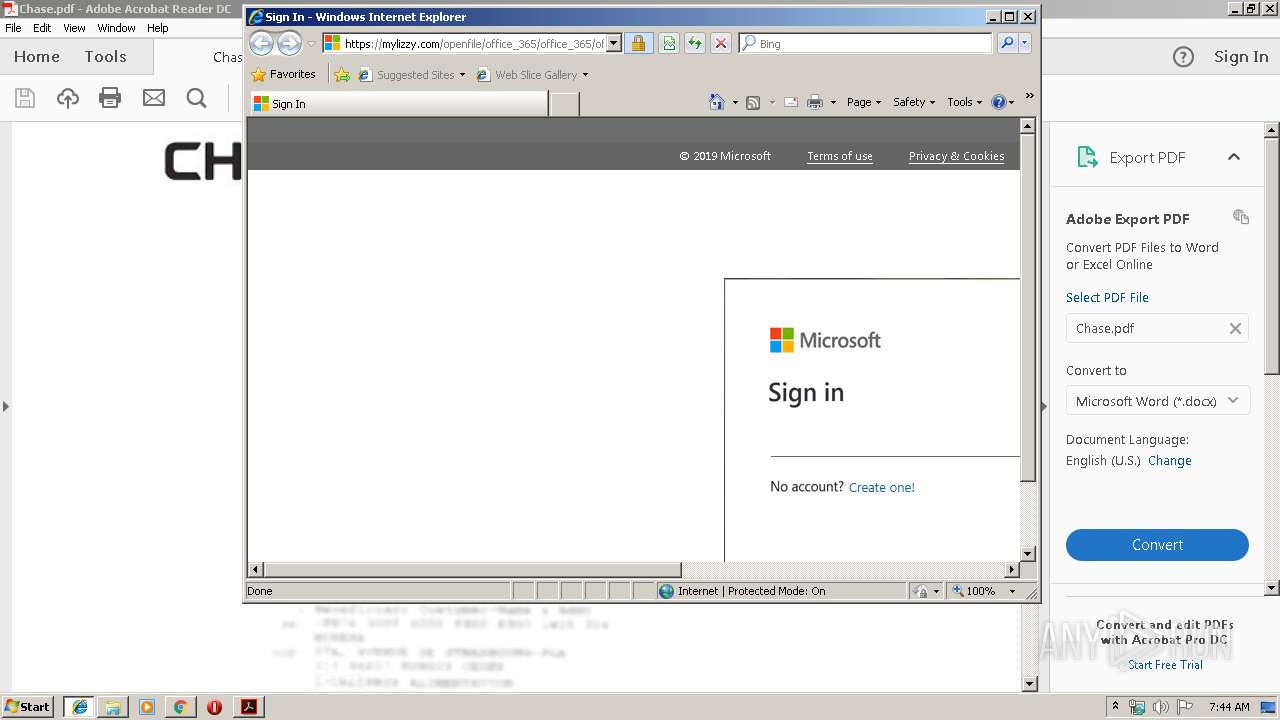
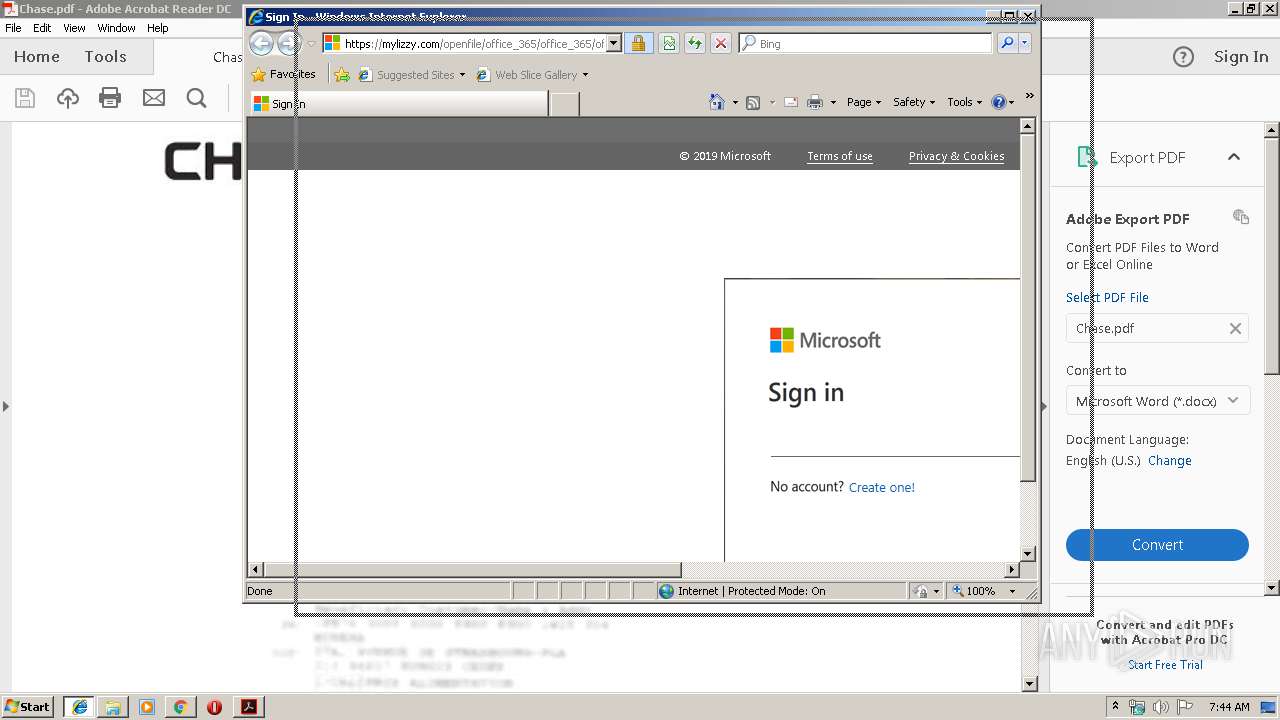
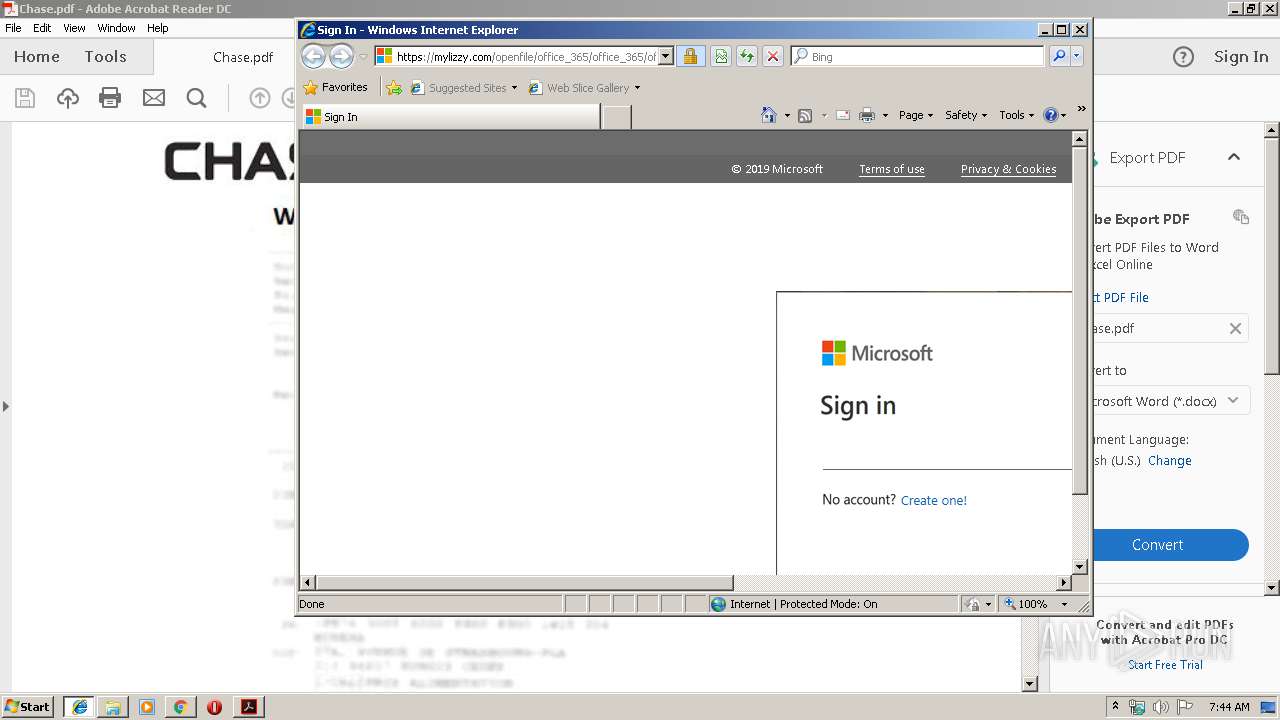
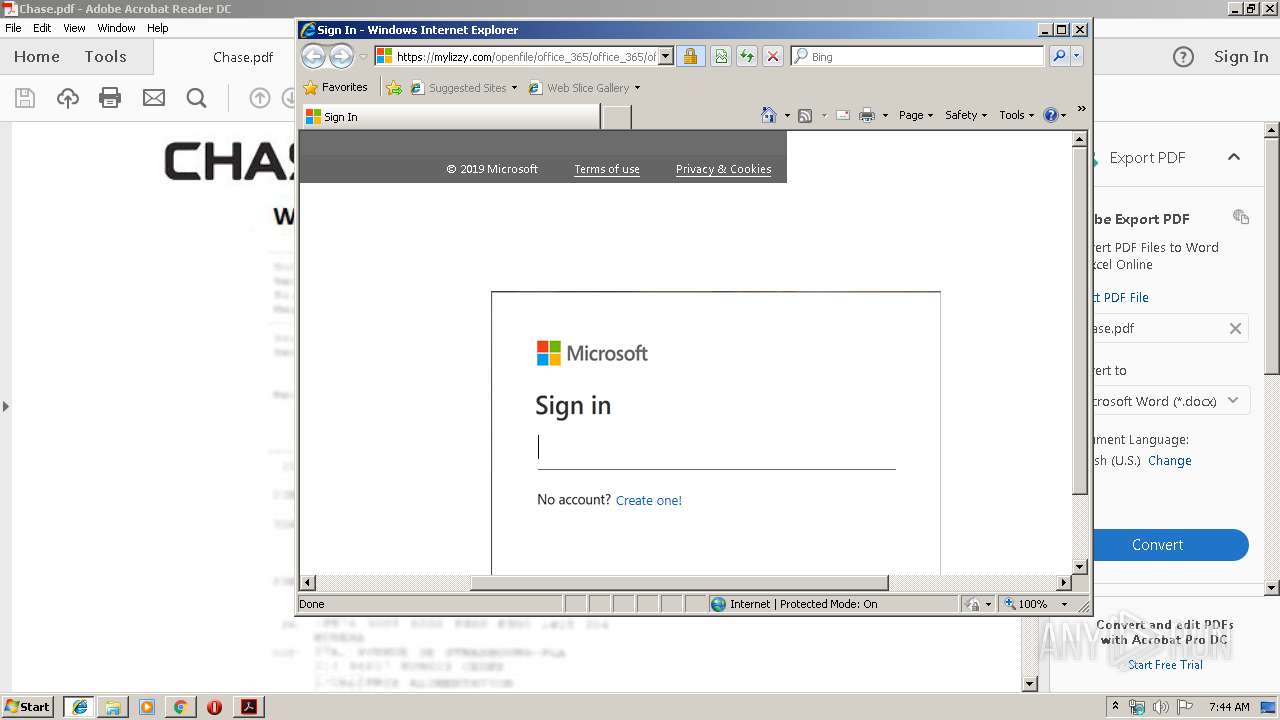
Starts Internet Explorer
- AcroRd32.exe (PID: 2648)
Modifies files in Chrome extension folder
- chrome.exe (PID: 2380)
INFO
Reads the hosts file
- RdrCEF.exe (PID: 4092)
- chrome.exe (PID: 1600)
- chrome.exe (PID: 2380)
Changes internet zones settings
- iexplore.exe (PID: 3768)
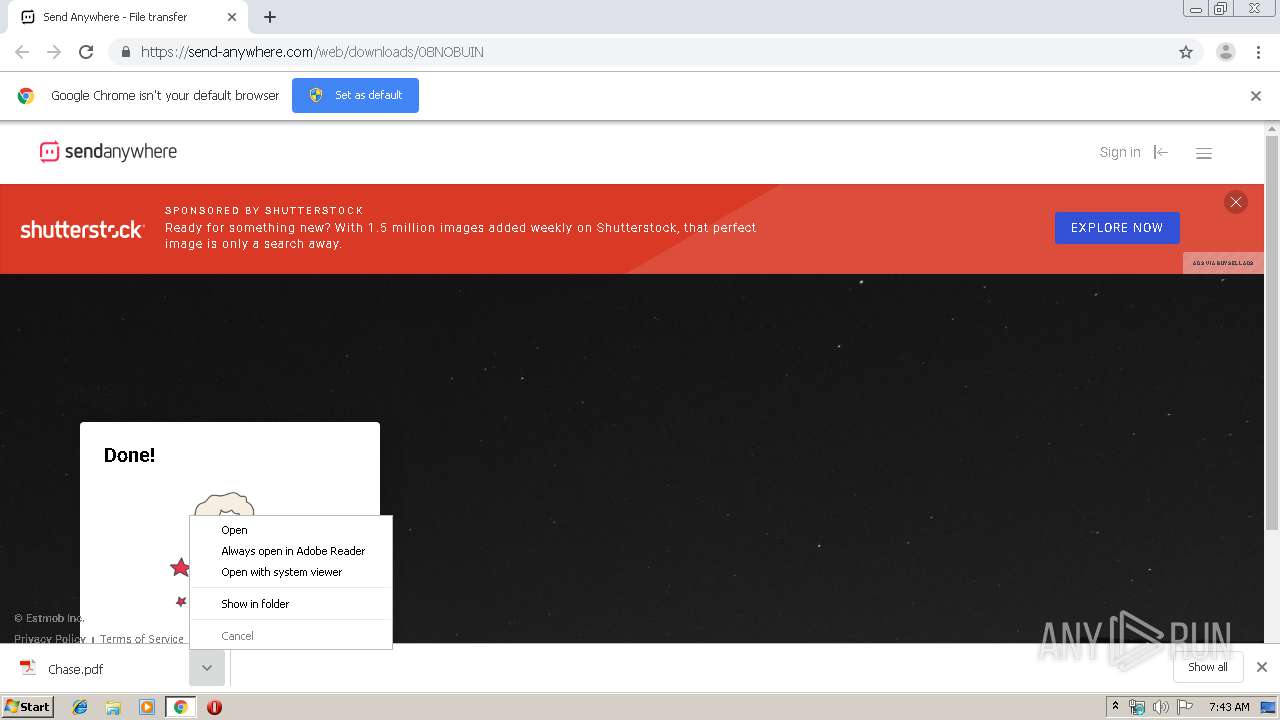
Manual execution by user
- AcroRd32.exe (PID: 2648)
Application launched itself
- AcroRd32.exe (PID: 2648)
- RdrCEF.exe (PID: 4092)
- iexplore.exe (PID: 3768)
- chrome.exe (PID: 2380)
Reads Internet Cache Settings
- chrome.exe (PID: 2380)
- iexplore.exe (PID: 2092)
Reads internet explorer settings
- iexplore.exe (PID: 2092)
Changes settings of System certificates
- iexplore.exe (PID: 3768)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3768)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
76
Monitored processes
39
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 436 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1020,13295521692237414746,15435509559317568879,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=7864429634730890960 --mojo-platform-channel-handle=1044 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 564 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,13295521692237414746,15435509559317568879,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=11646151732760150712 --mojo-platform-channel-handle=5152 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 940 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,13295521692237414746,15435509559317568879,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=1668535625129968196 --mojo-platform-channel-handle=4368 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1160 | "C:\Program Files\Common Files\Adobe\ARM\1.0\AdobeARM.exe" /PRODUCT:Reader /VERSION:15.0 /MODE:3 | C:\Program Files\Common Files\Adobe\ARM\1.0\AdobeARM.exe | — | AcroRd32.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe Reader and Acrobat Manager Exit code: 0 Version: 1.824.27.2646 Modules
| |||||||||||||||
| 1600 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,13295521692237414746,15435509559317568879,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=14348337125152877781 --mojo-platform-channel-handle=1572 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1856 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,13295521692237414746,15435509559317568879,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=14567626417259111295 --mojo-platform-channel-handle=5320 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1892 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe" --type=renderer --disable-3d-apis --disable-databases --disable-direct-npapi-requests --disable-file-system --disable-notifications --disable-shared-workers --disable-direct-write --lang=en-US --lang=en-US --log-severity=disable --product-version="ReaderServices/15.23.20053 Chrome/45.0.2454.85" --device-scale-factor=1 --enable-delegated-renderer --num-raster-threads=2 --gpu-rasterization-msaa-sample-count=8 --content-image-texture-target=3553 --video-image-texture-target=3553 --disable-accelerated-video-decode --disable-webrtc-hw-encoding --disable-gpu-compositing --channel="4092.0.1567443054\2005791095" --allow-no-sandbox-job /prefetch:673131151 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe | — | RdrCEF.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe RdrCEF Exit code: 0 Version: 15.23.20053.211670 Modules
| |||||||||||||||
| 1972 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,13295521692237414746,15435509559317568879,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=13556586587023489442 --mojo-platform-channel-handle=5160 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2092 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3768 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2132 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,13295521692237414746,15435509559317568879,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=11475537138018051770 --mojo-platform-channel-handle=5648 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
2 005
Read events
1 777
Write events
219
Delete events
9
Modification events
| (PID) Process: | (2380) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2380) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2380) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2380) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2380) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2172) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2380-13215509012803500 |
Value: 259 | |||
| (PID) Process: | (2380) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2380) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2380) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (2380) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
52
Text files
237
Unknown types
34
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2380 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2380 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\53e495f5-9d2e-4026-9771-1264c74bf299.tmp | — | |
MD5:— | SHA256:— | |||
| 2380 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2380 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF39a8ae.TMP | text | |
MD5:— | SHA256:— | |||
| 2380 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2380 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2380 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF39a8fc.TMP | text | |
MD5:— | SHA256:— | |||
| 2380 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2380 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old~RF39a91b.TMP | text | |
MD5:— | SHA256:— | |||
| 2380 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF39a89e.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
14
TCP/UDP connections
73
DNS requests
47
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2648 | AcroRd32.exe | GET | 304 | 2.16.186.97:80 | http://acroipm2.adobe.com/15/rdr/ENU/win/nooem/none/consumer/281_15_23_20070.zip | unknown | — | — | whitelisted |
2648 | AcroRd32.exe | GET | 304 | 2.16.186.97:80 | http://acroipm2.adobe.com/15/rdr/ENU/win/nooem/none/consumer/280_15_23_20070.zip | unknown | — | — | whitelisted |
2648 | AcroRd32.exe | GET | 304 | 2.16.186.97:80 | http://acroipm2.adobe.com/15/rdr/ENU/win/nooem/none/consumer/message.zip | unknown | — | — | whitelisted |
2648 | AcroRd32.exe | GET | 304 | 2.16.186.97:80 | http://acroipm2.adobe.com/15/rdr/ENU/win/nooem/none/consumer/278_15_23_20070.zip | unknown | — | — | whitelisted |
1600 | chrome.exe | GET | 302 | 172.217.18.174:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 514 b | whitelisted |
1600 | chrome.exe | GET | 302 | 172.217.18.174:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 514 b | whitelisted |
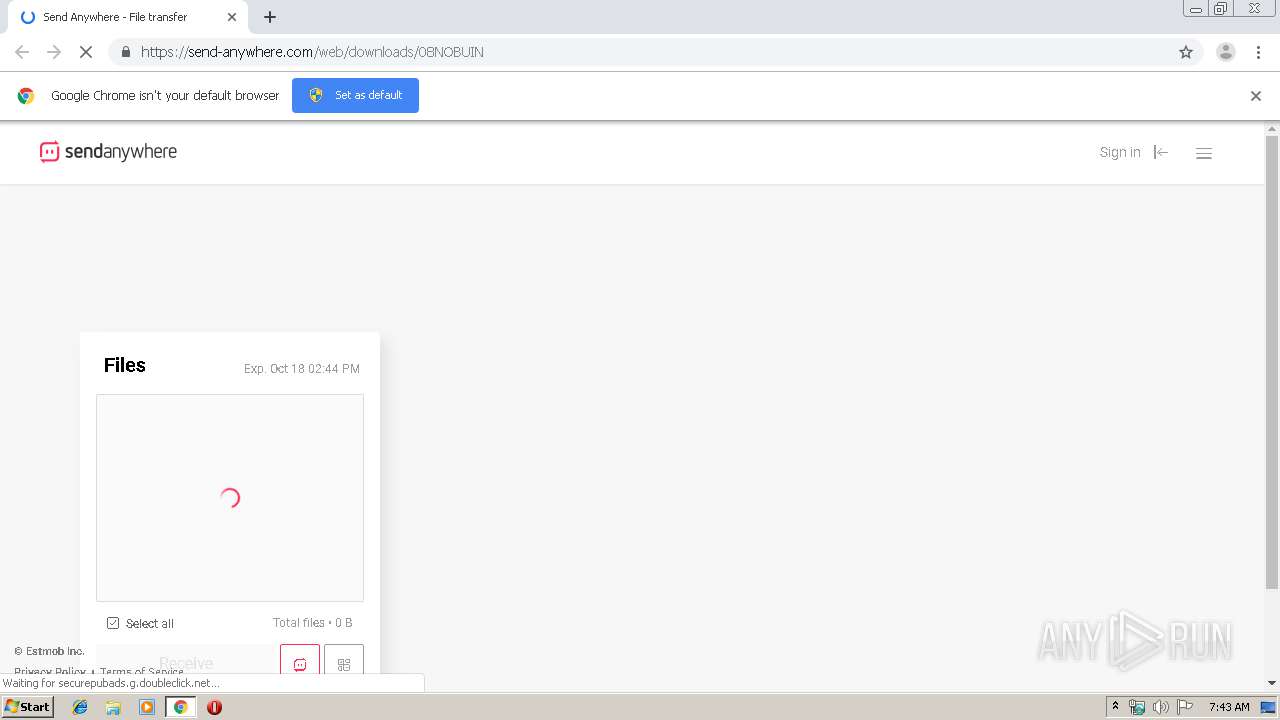
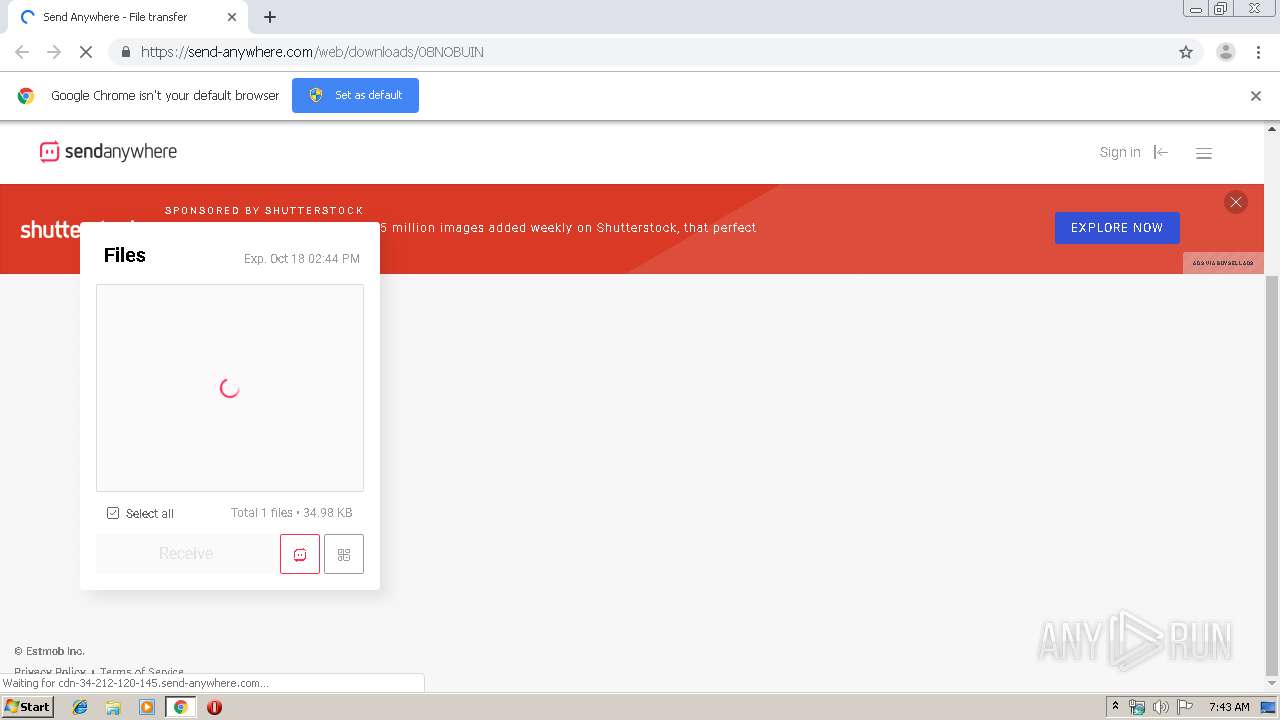
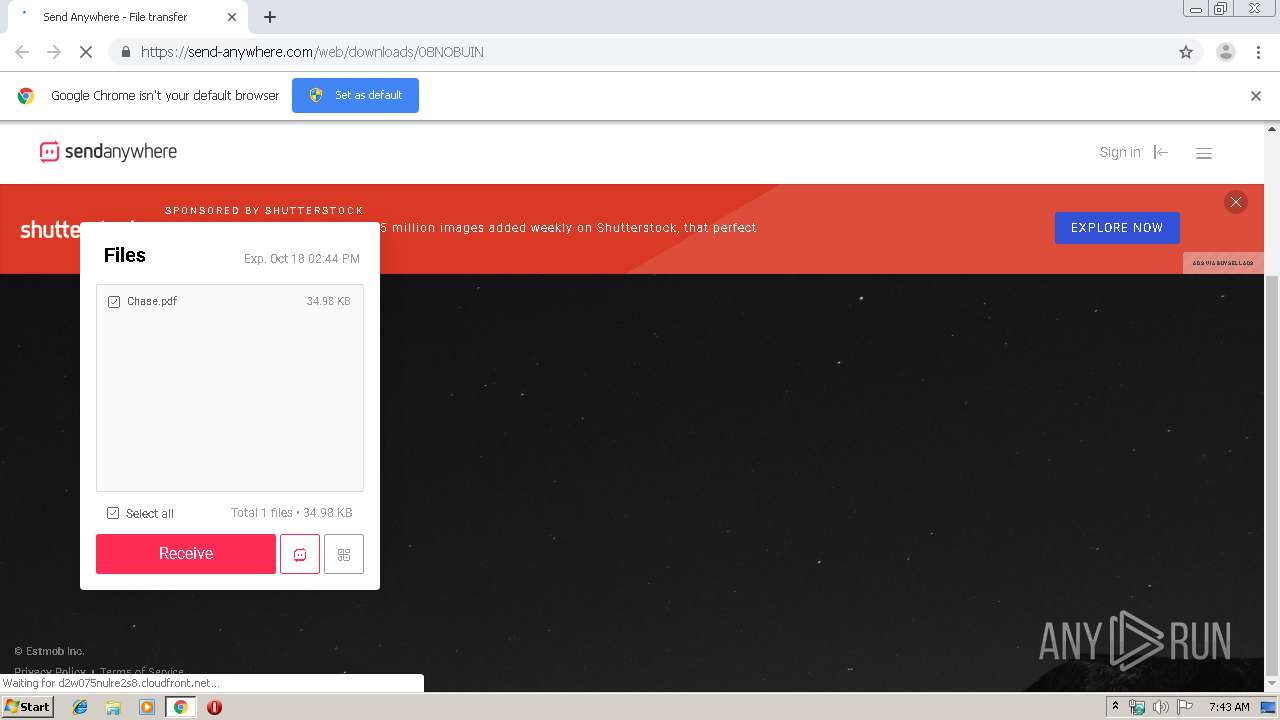
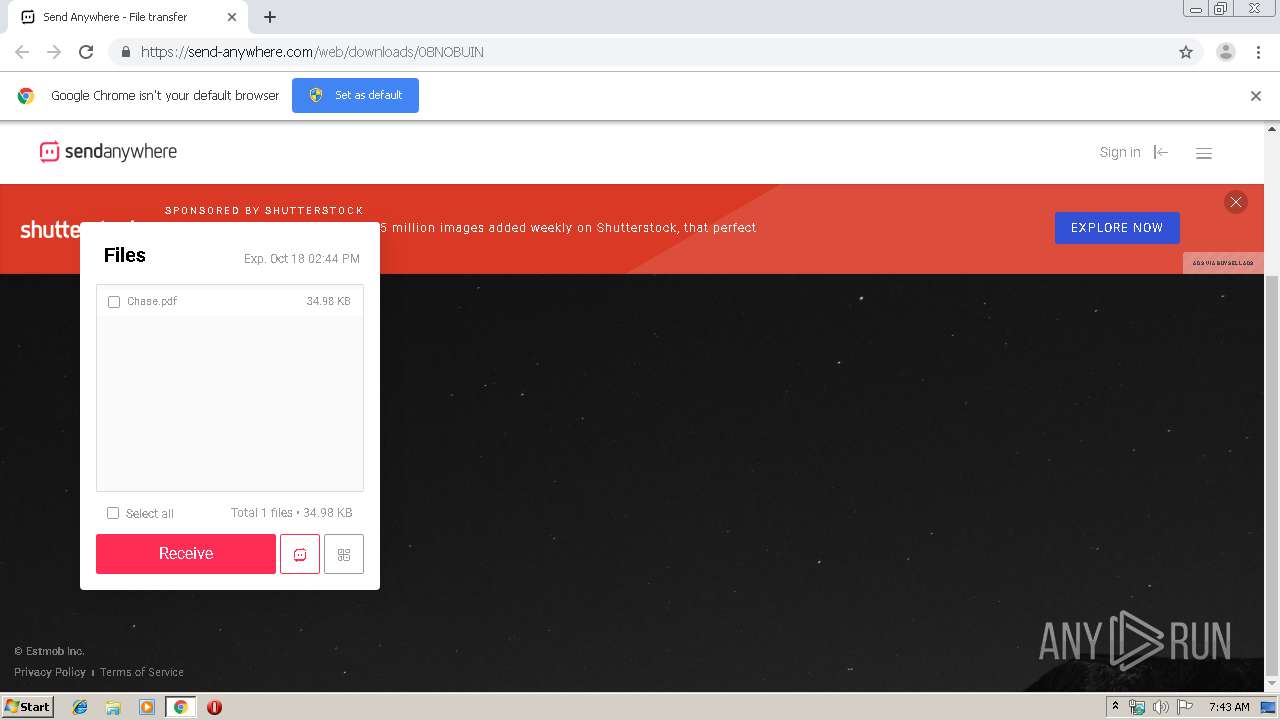
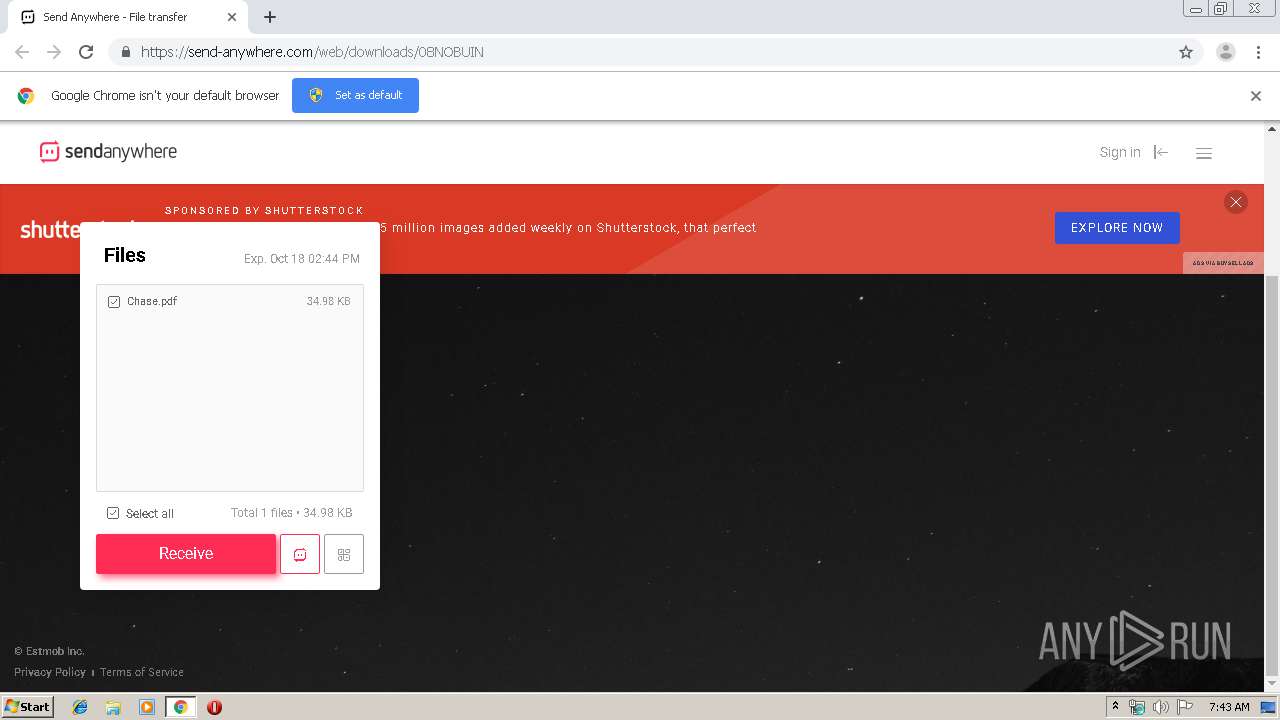
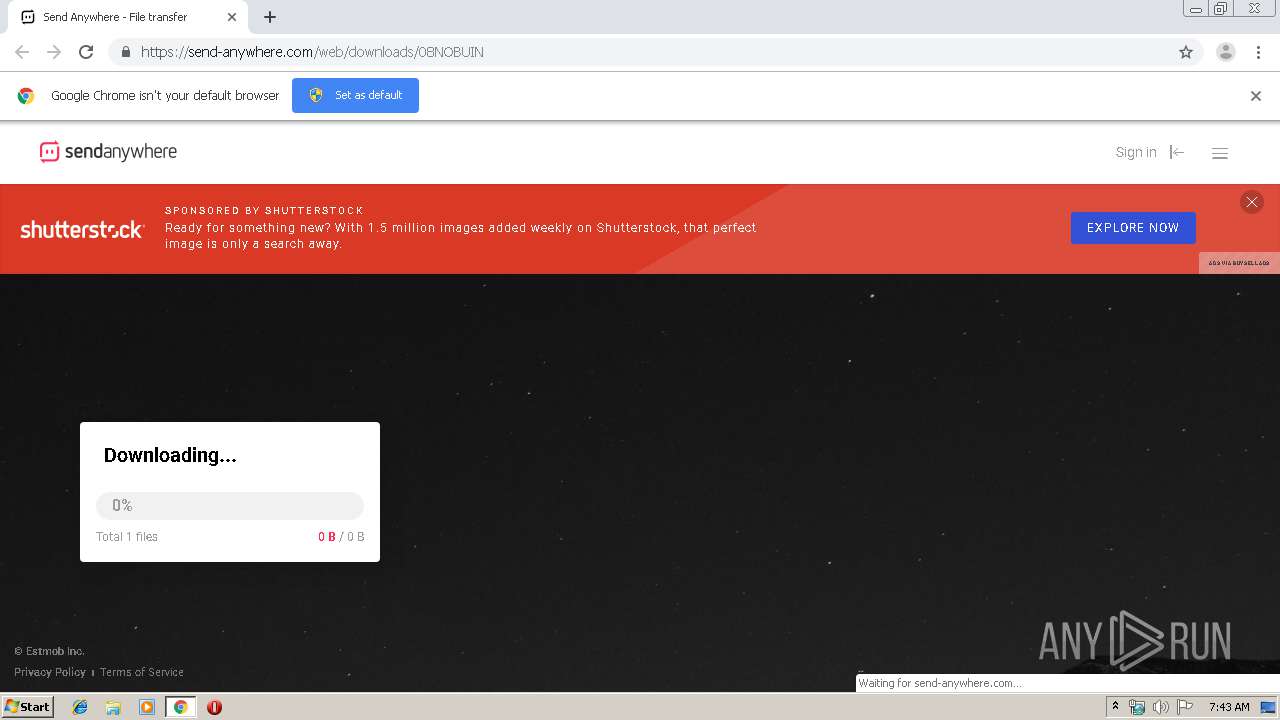
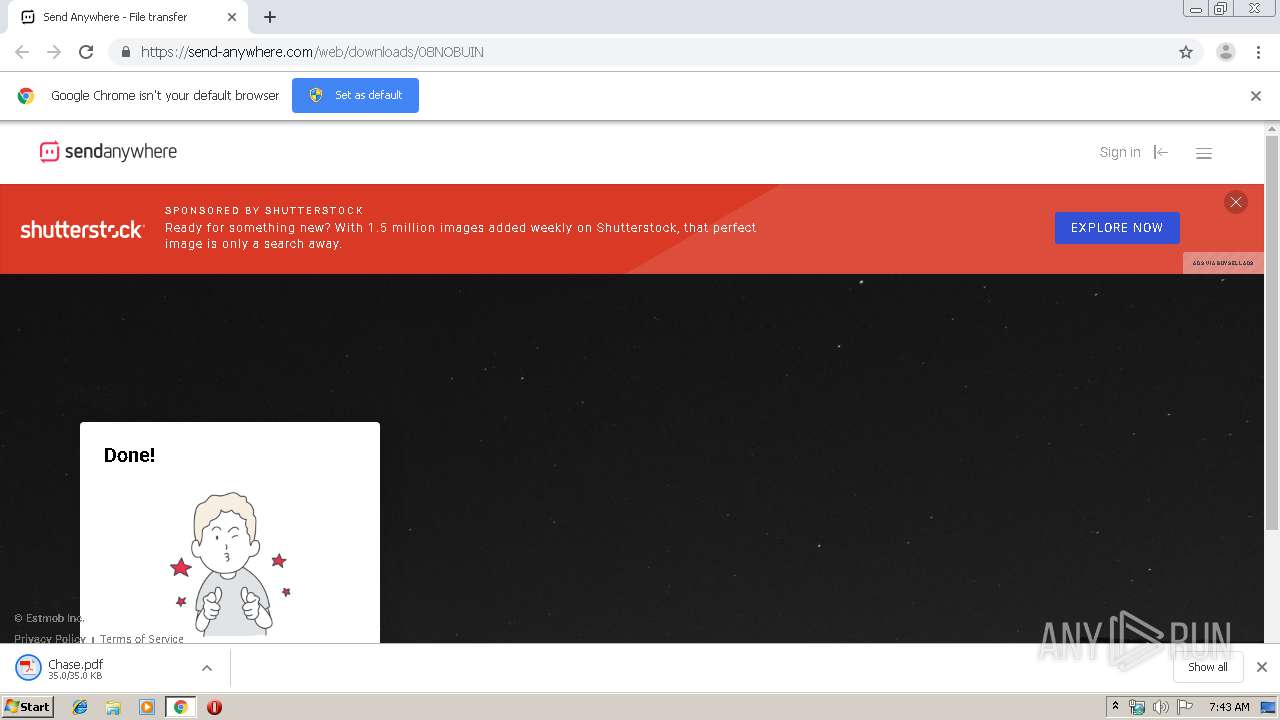
1600 | chrome.exe | GET | 302 | 54.69.225.42:80 | http://sendanywhe.re/08NOBUIN | US | html | 161 b | suspicious |
1600 | chrome.exe | GET | 200 | 173.194.187.104:80 | http://r3---sn-4g5e6nsr.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=82.102.26.195&mm=28&mn=sn-4g5e6nsr&ms=nvh&mt=1571035043&mv=u&mvi=2&pl=25&shardbypass=yes | US | crx | 862 Kb | whitelisted |
3768 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
2648 | AcroRd32.exe | GET | 304 | 2.16.186.97:80 | http://acroipm2.adobe.com/15/rdr/ENU/win/nooem/none/consumer/277_15_23_20070.zip | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1600 | chrome.exe | 172.217.23.131:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
1600 | chrome.exe | 172.217.18.98:443 | pagead2.googlesyndication.com | Google Inc. | US | whitelisted |
1600 | chrome.exe | 172.217.16.141:443 | accounts.google.com | Google Inc. | US | suspicious |
— | — | 54.69.225.42:80 | sendanywhe.re | Amazon.com, Inc. | US | unknown |
1600 | chrome.exe | 13.224.196.32:443 | send-anywhere.com | — | US | unknown |
1600 | chrome.exe | 104.19.199.151:443 | cdnjs.cloudflare.com | Cloudflare Inc | US | shared |
1600 | chrome.exe | 172.217.18.110:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
1600 | chrome.exe | 52.222.157.105:443 | d31qbv1cthcecs.cloudfront.net | Amazon.com, Inc. | US | whitelisted |
1600 | chrome.exe | 172.217.18.174:443 | apis.google.com | Google Inc. | US | whitelisted |
1600 | chrome.exe | 172.217.23.162:443 | www.googletagservices.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
nam03.safelinks.protection.outlook.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
mandrillapp.com |
| whitelisted |
sendanywhe.re |
| suspicious |
send-anywhere.com |
| whitelisted |
cdnjs.cloudflare.com |
| whitelisted |
apis.google.com |
| whitelisted |
www.googletagservices.com |
| whitelisted |
pagead2.googlesyndication.com |
| whitelisted |