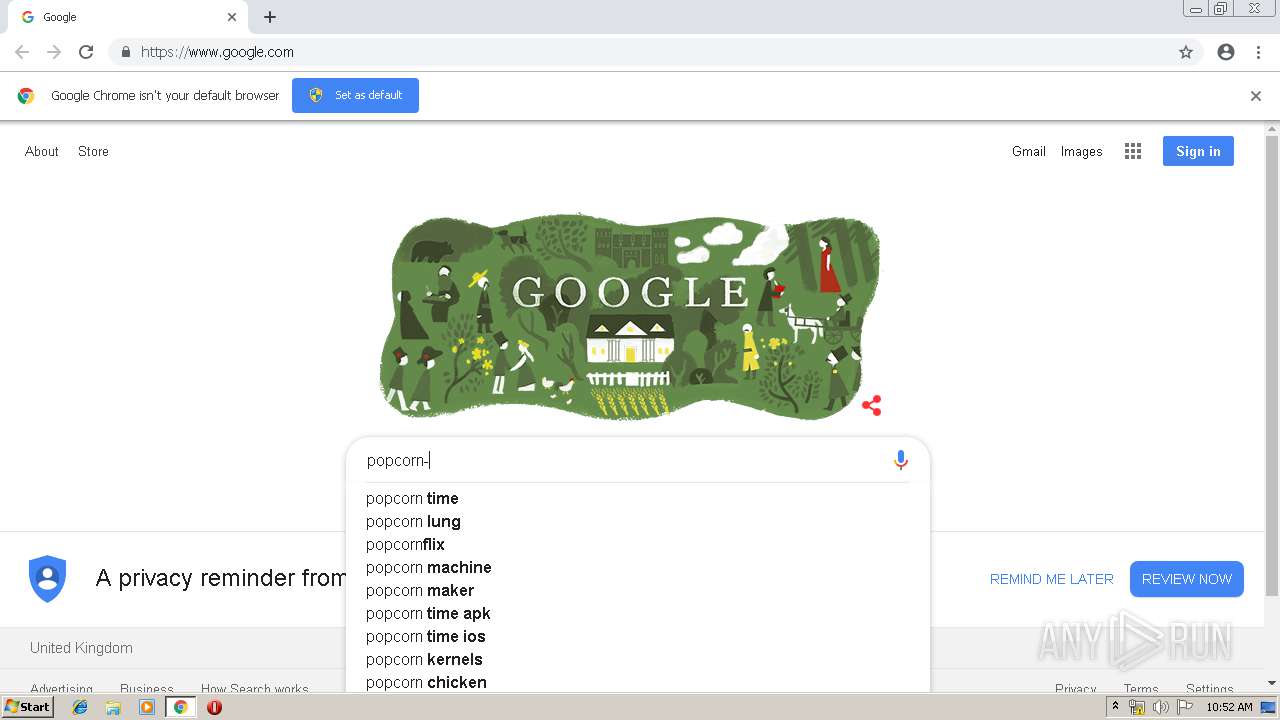
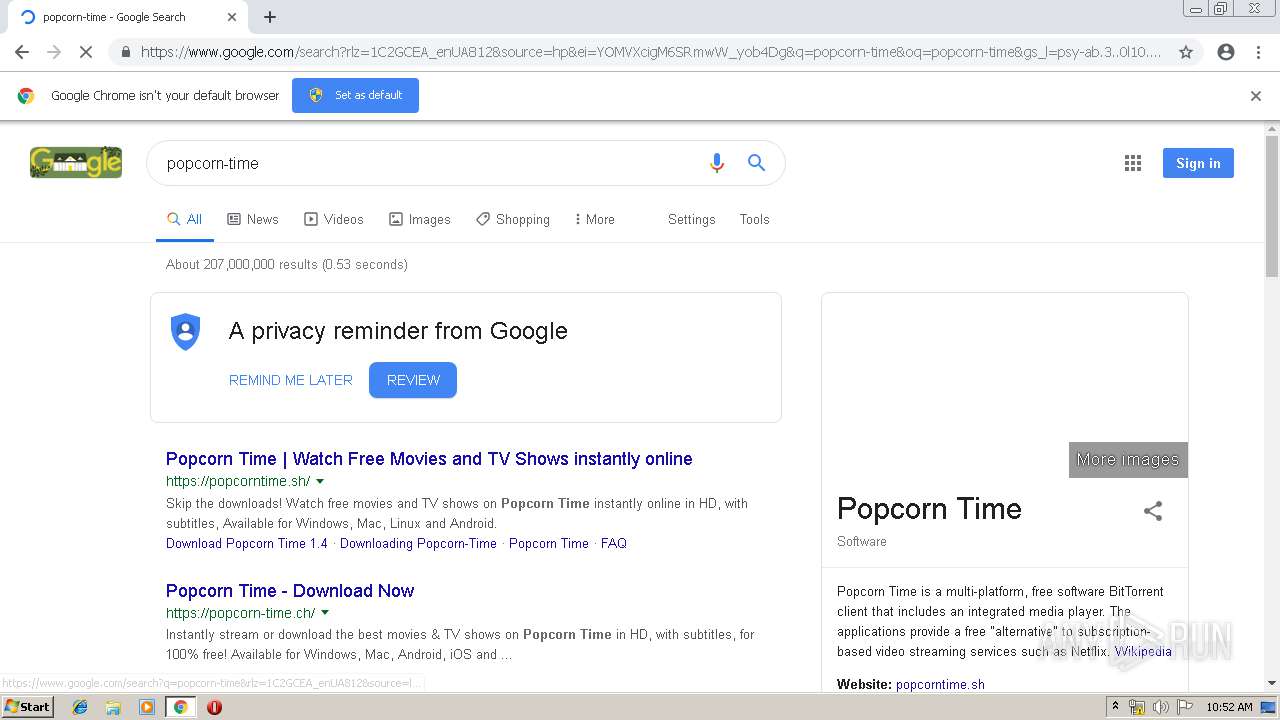
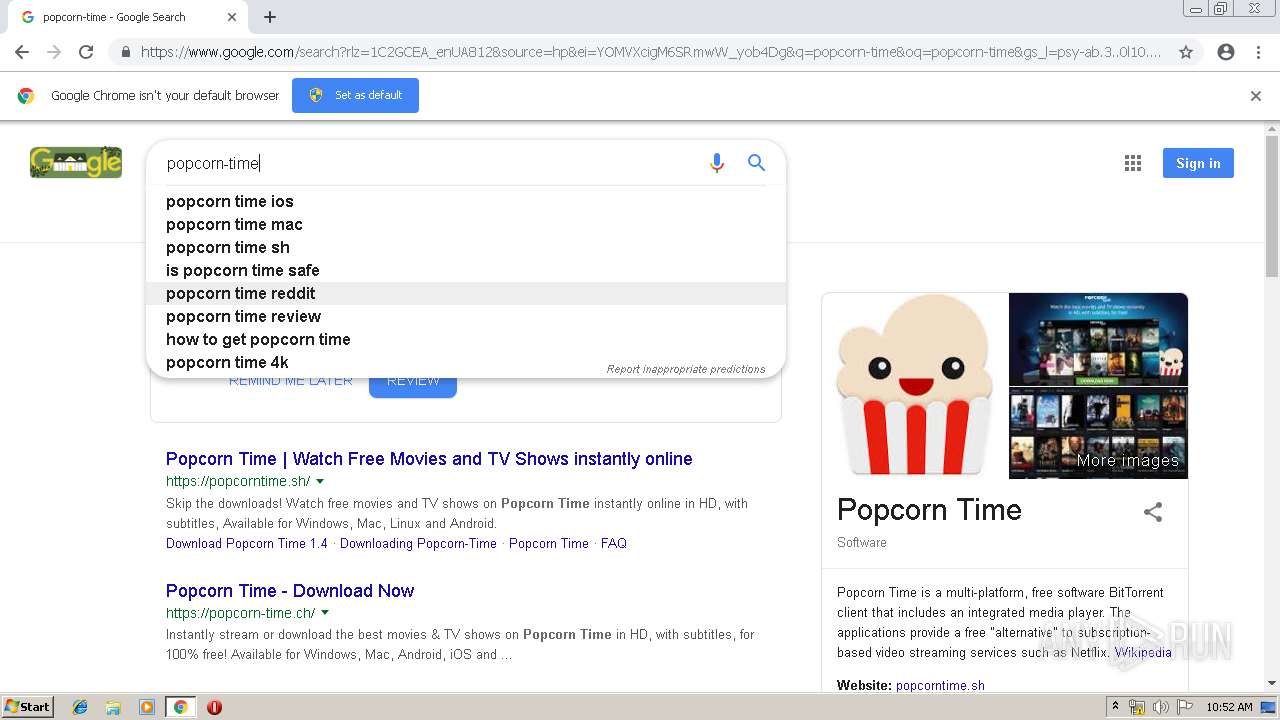
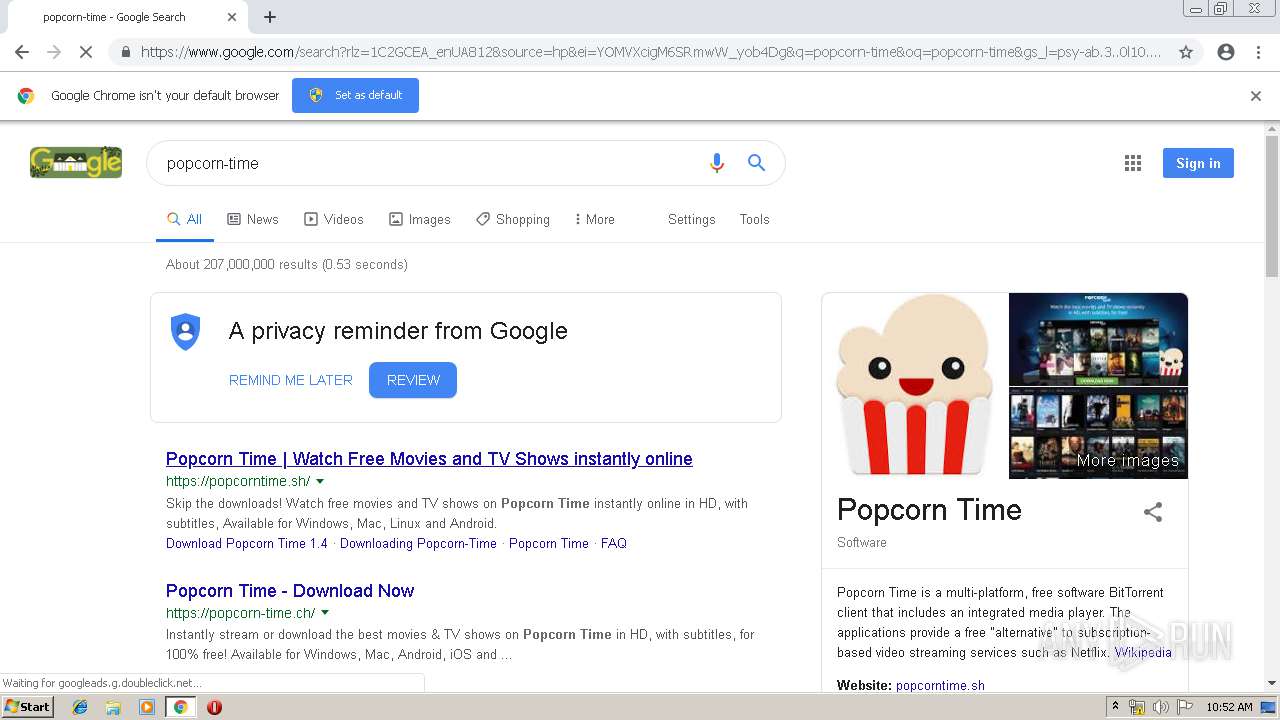
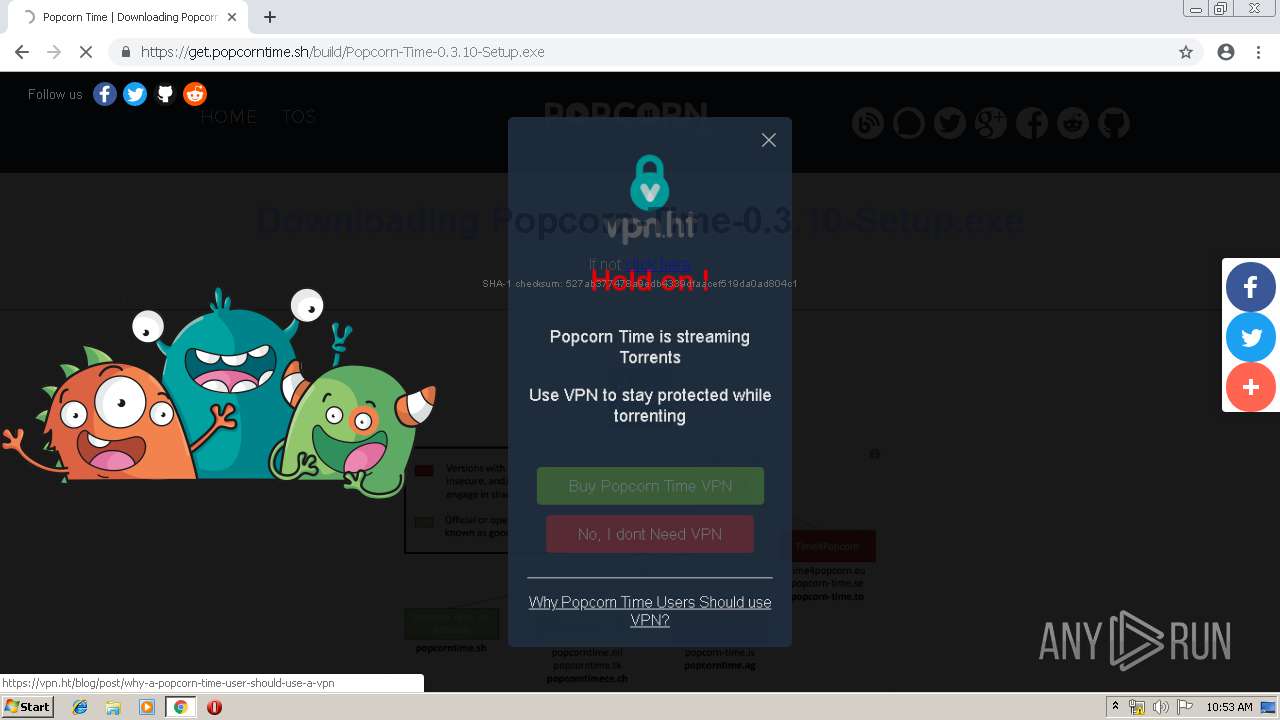
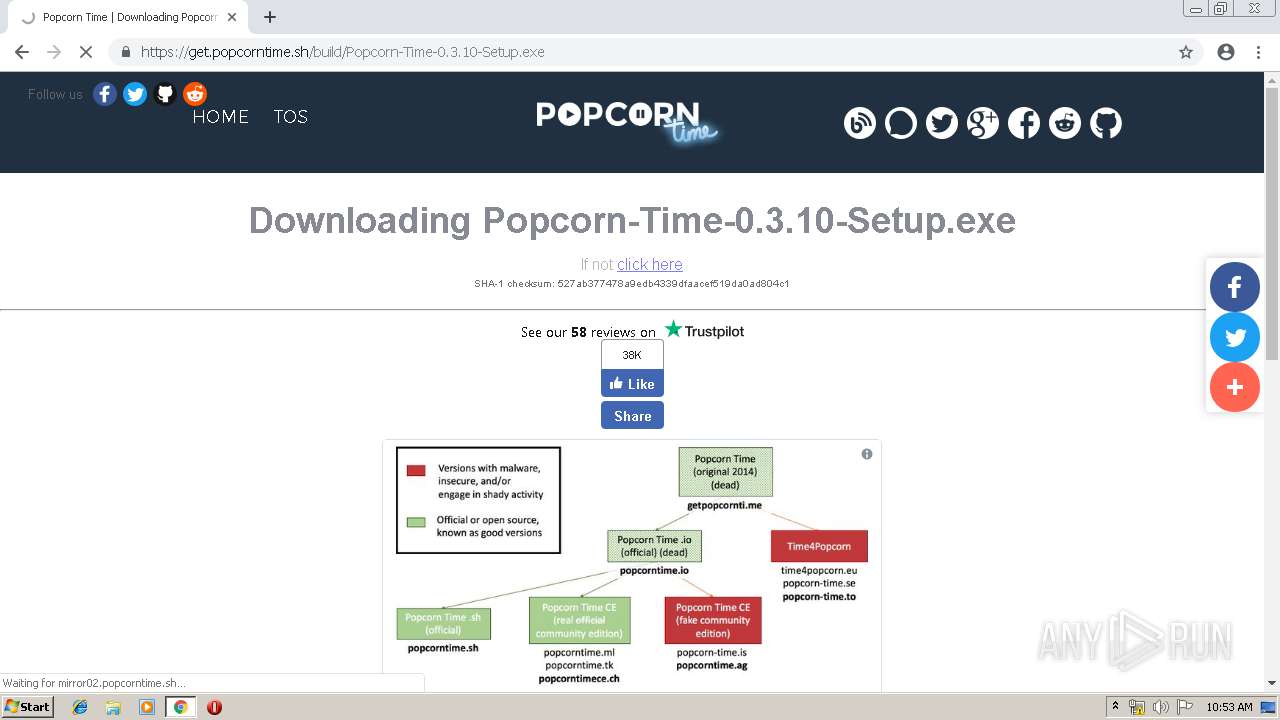
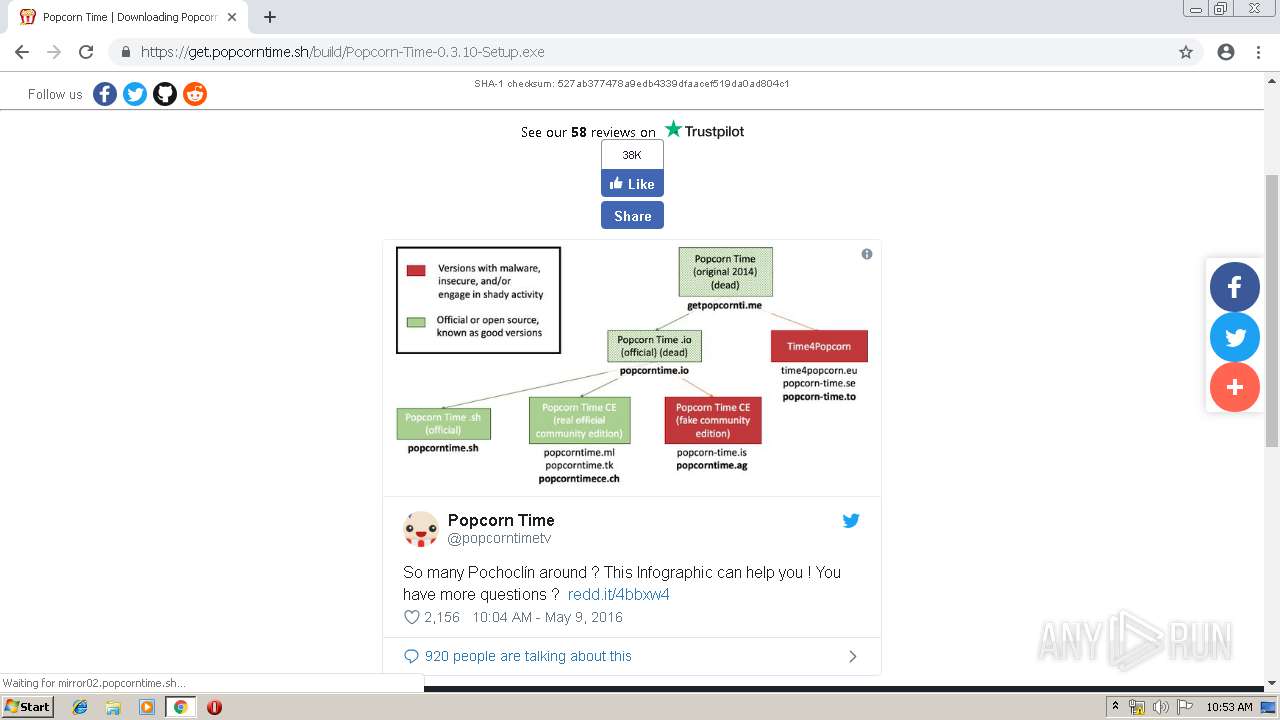
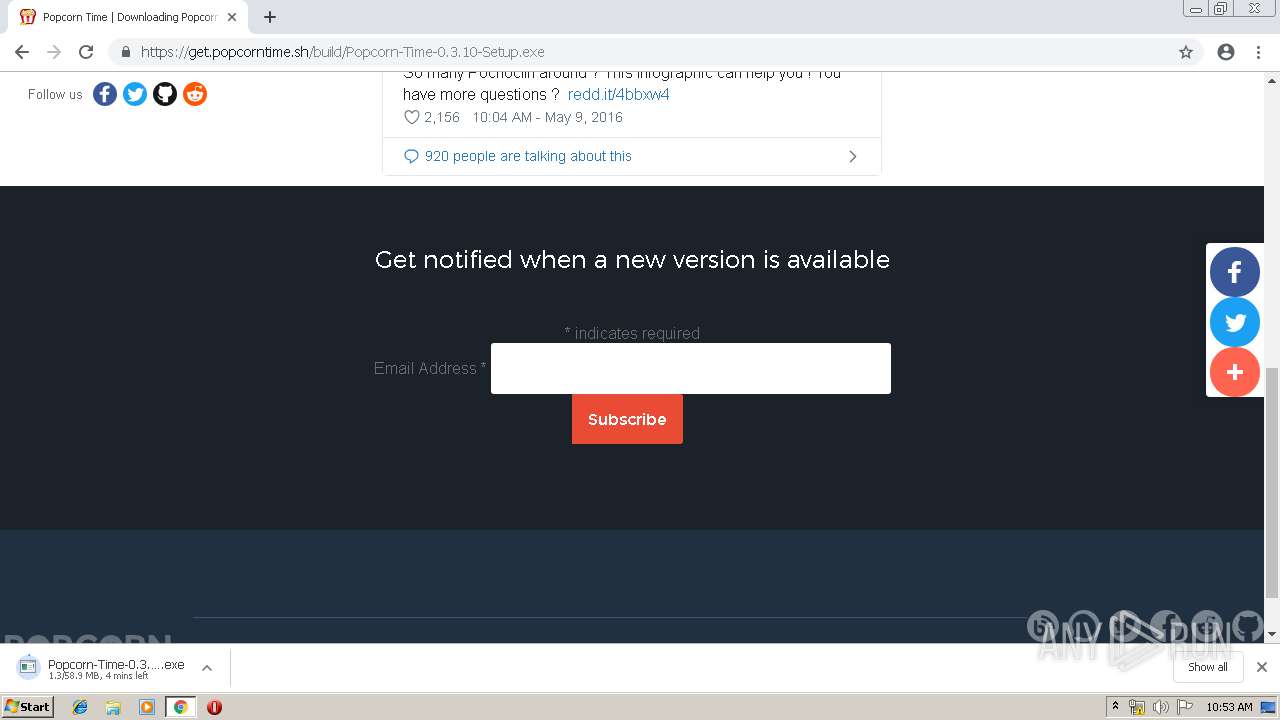
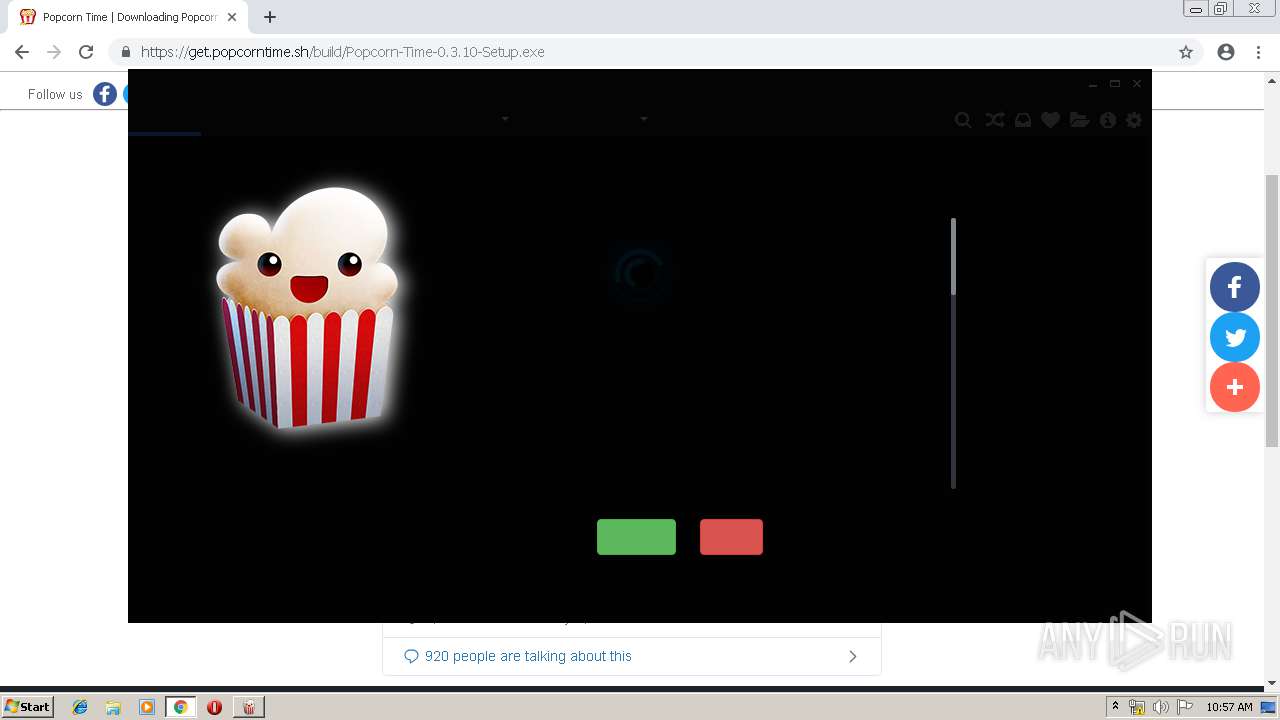
| URL: | http://google.com |
| Full analysis: | https://app.any.run/tasks/9e35be42-80b5-4fed-a15b-c72c61dbbdb1 |
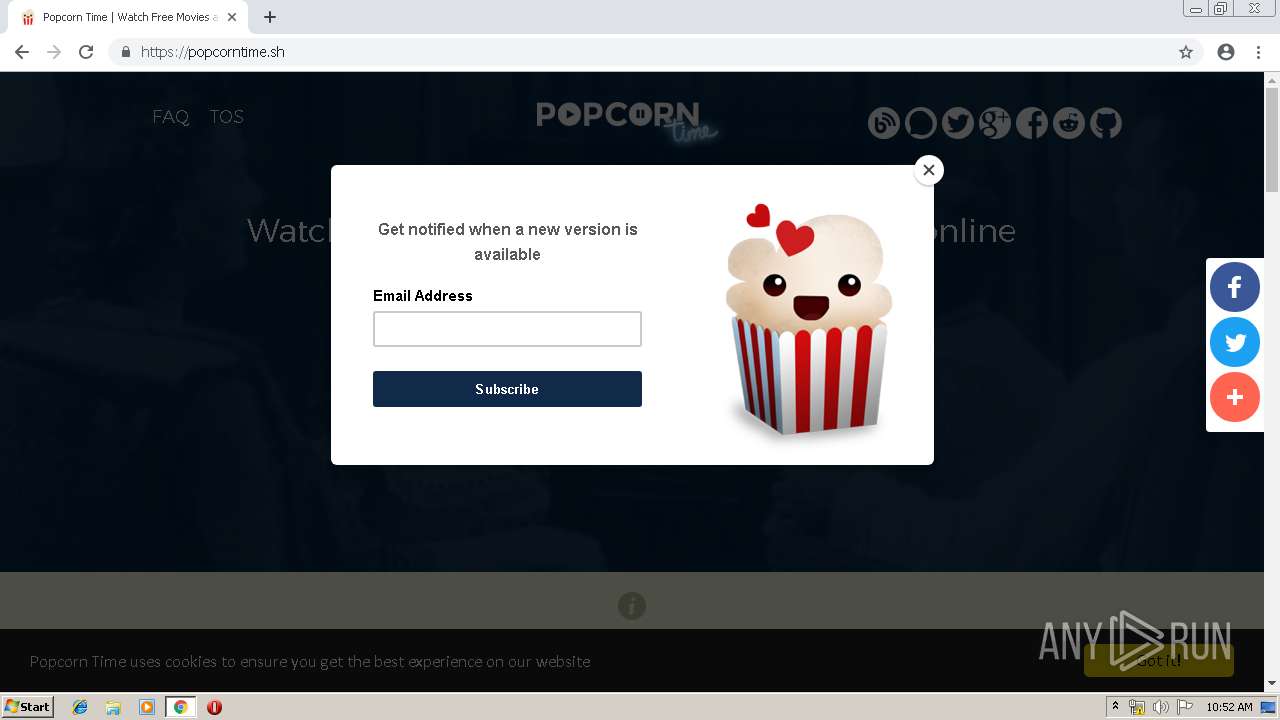
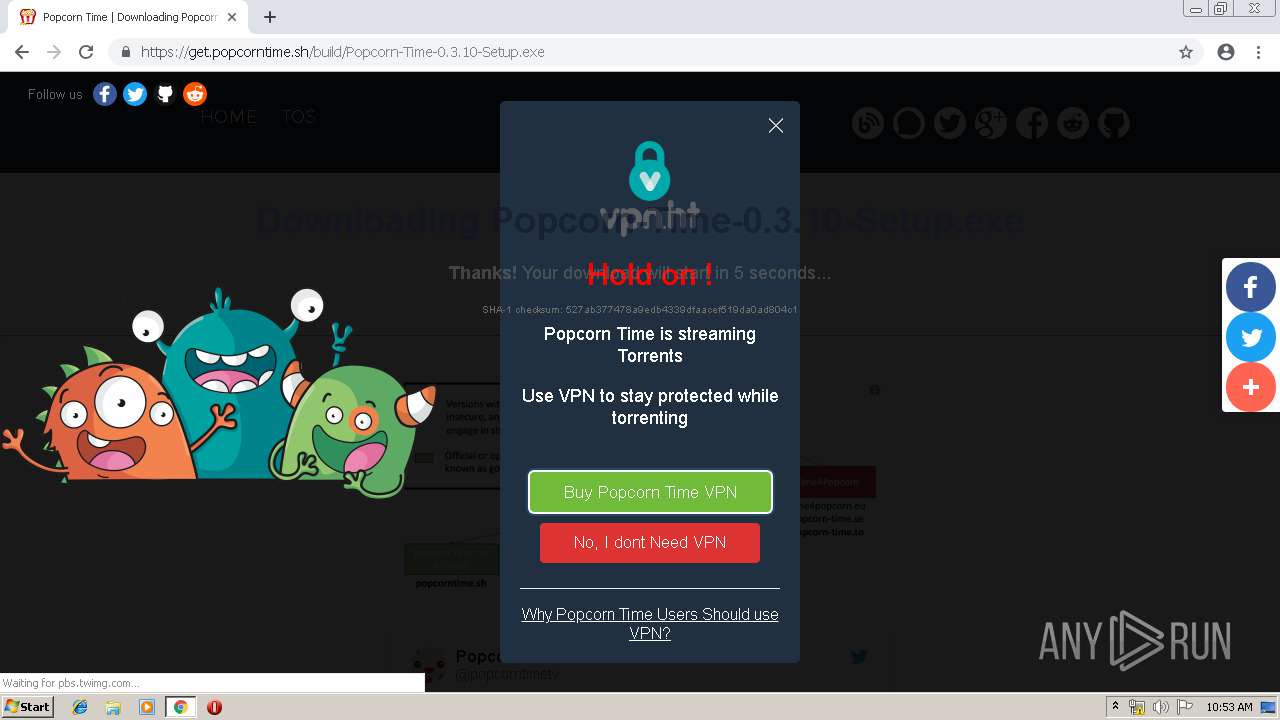
| Verdict: | Malicious activity |
| Analysis date: | June 28, 2019, 09:52:04 |
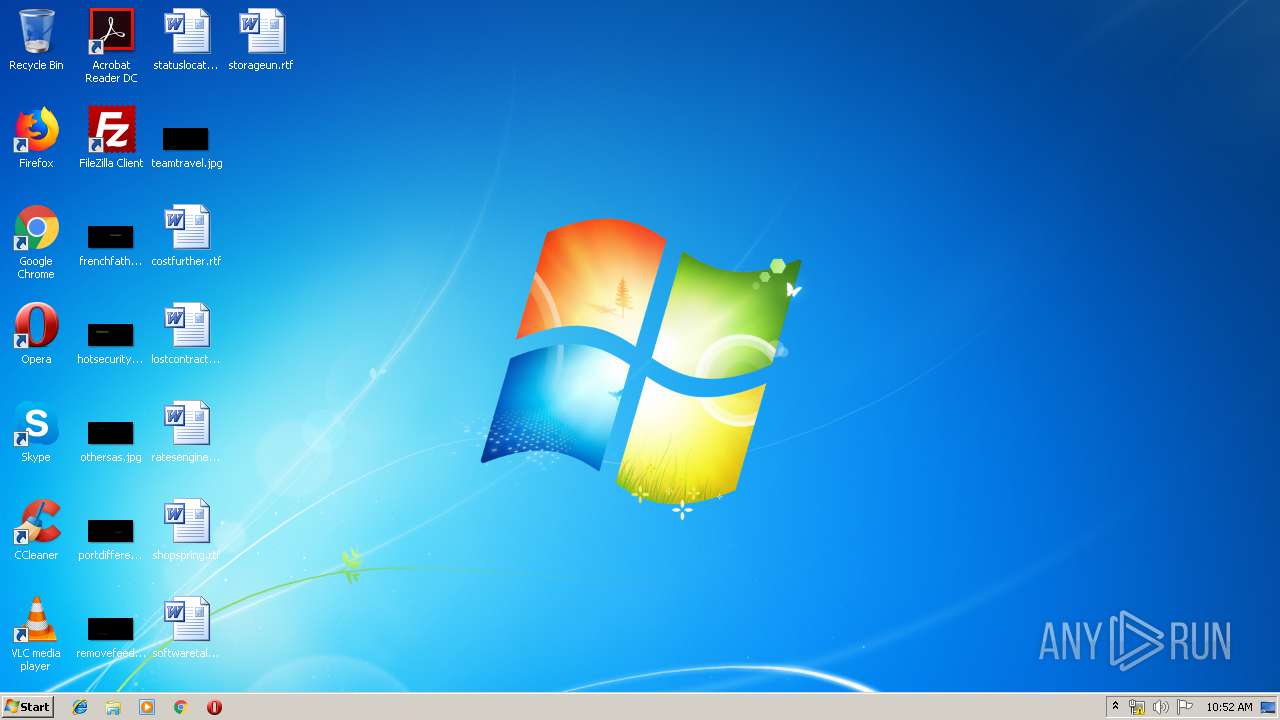
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | C7B920F57E553DF2BB68272F61570210 |
| SHA1: | 234988566C9A0A9CF952CEC82B143BF9C207AC16 |
| SHA256: | AA2239C17609B21EBA034C564AF878F3EEC8CE83ED0F2768597D2BC2FD4E4DA5 |
| SSDEEP: | 3:N1KZK3uK:C03uK |
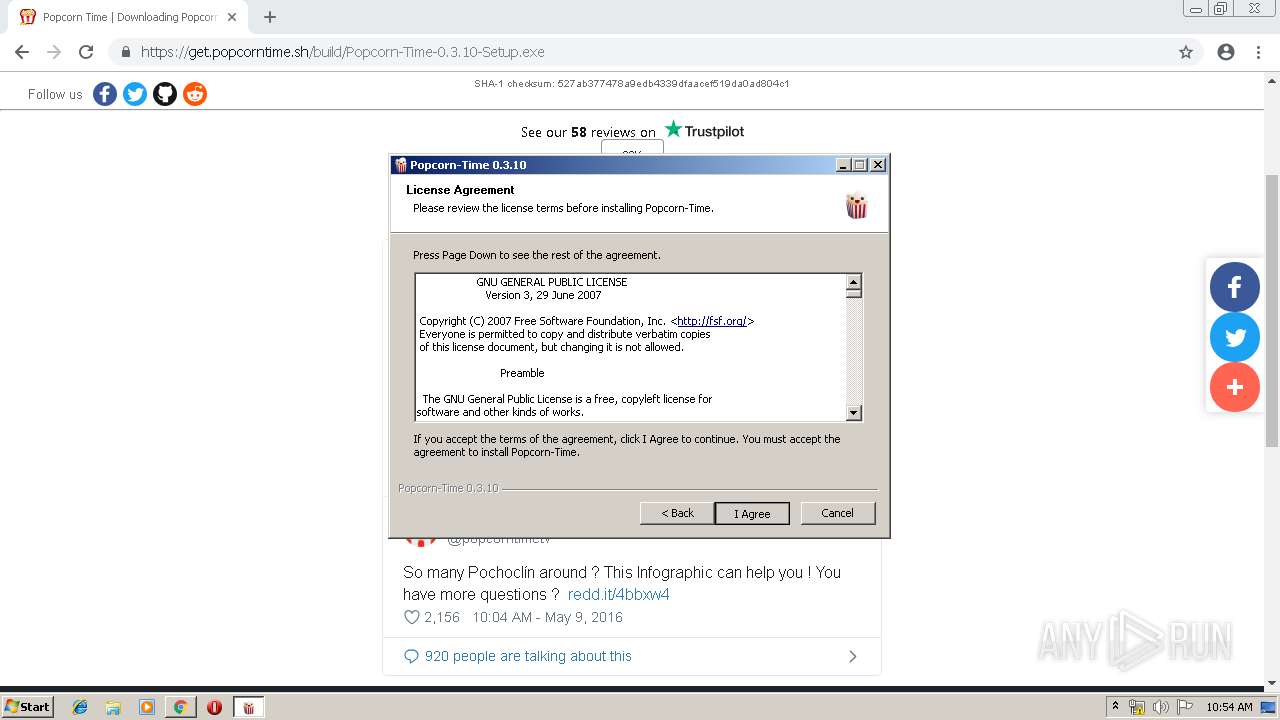
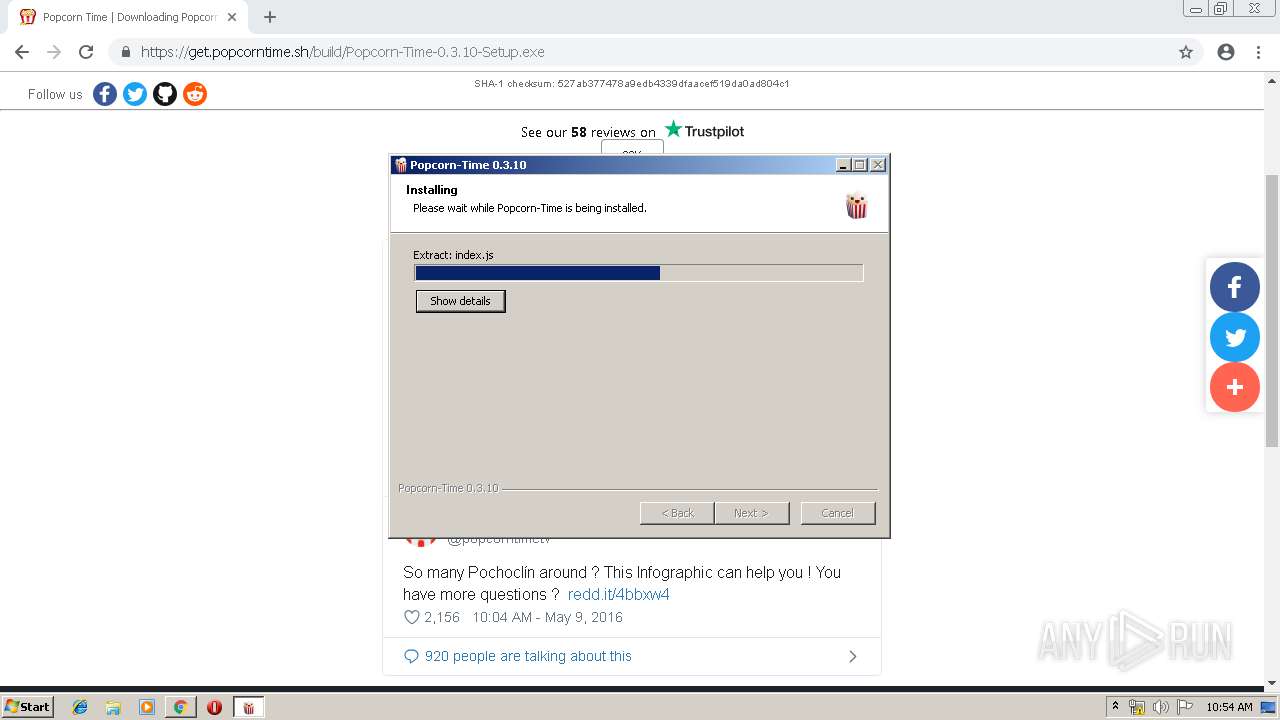
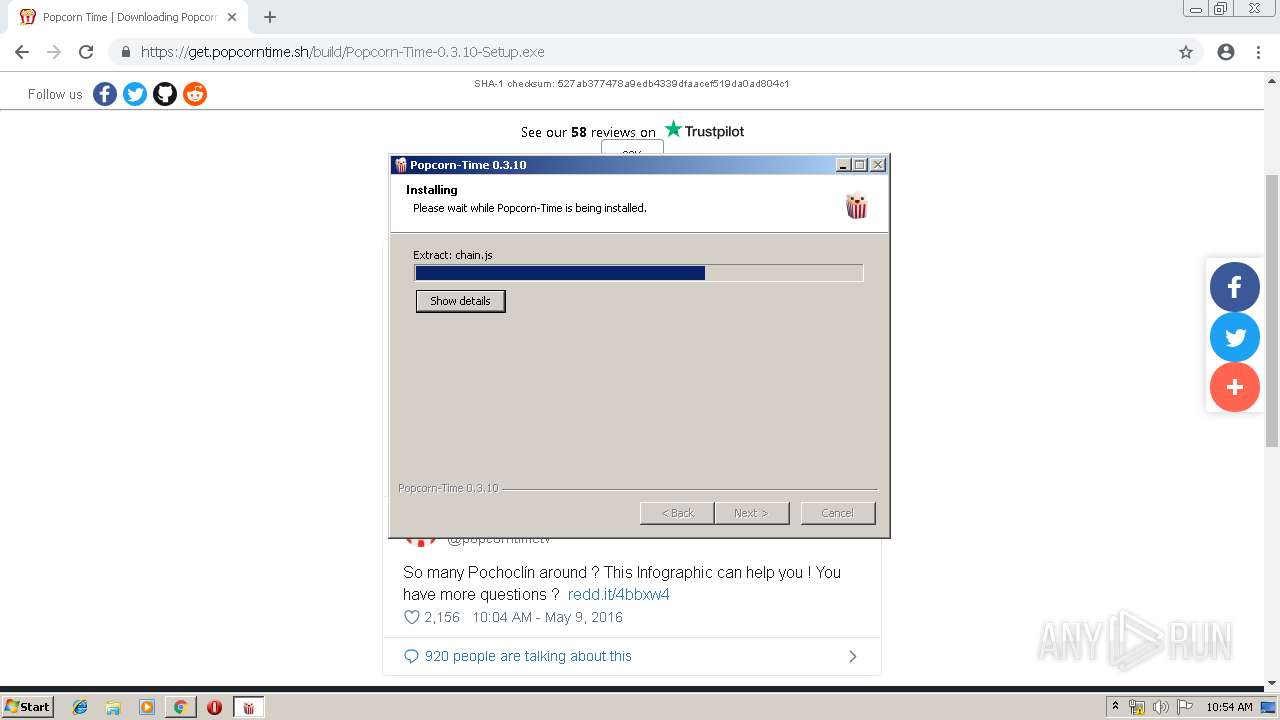
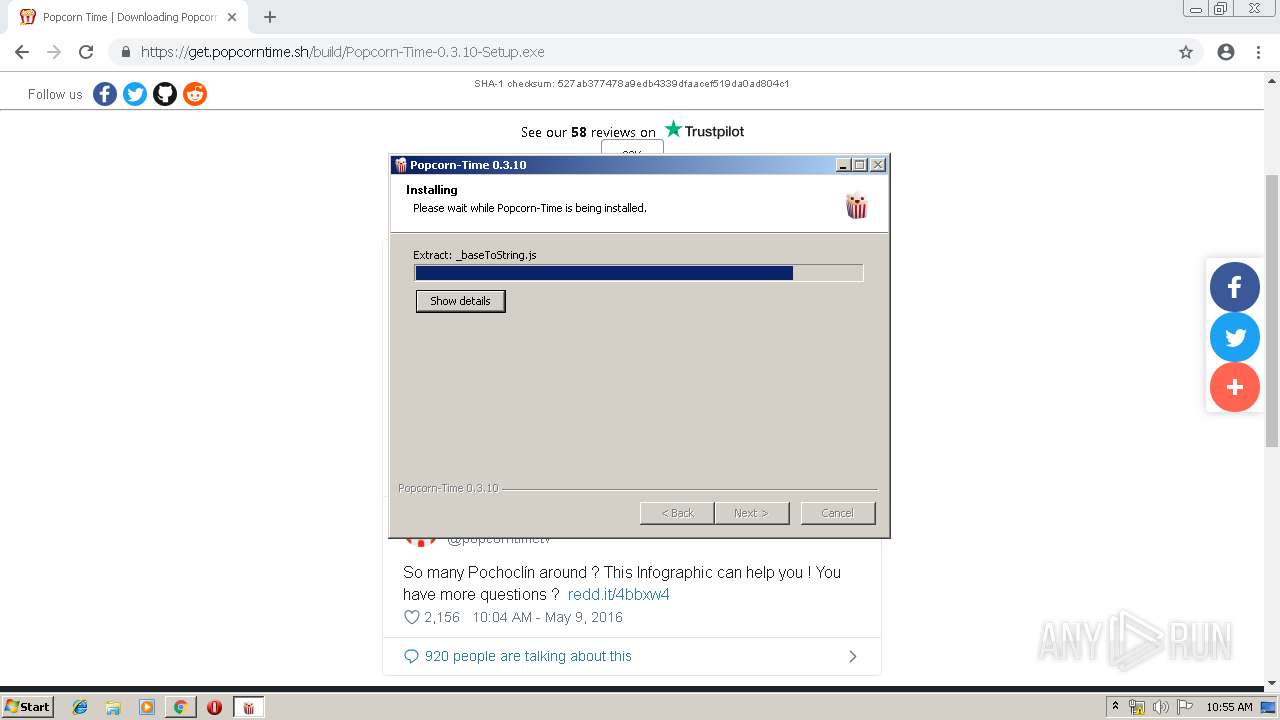
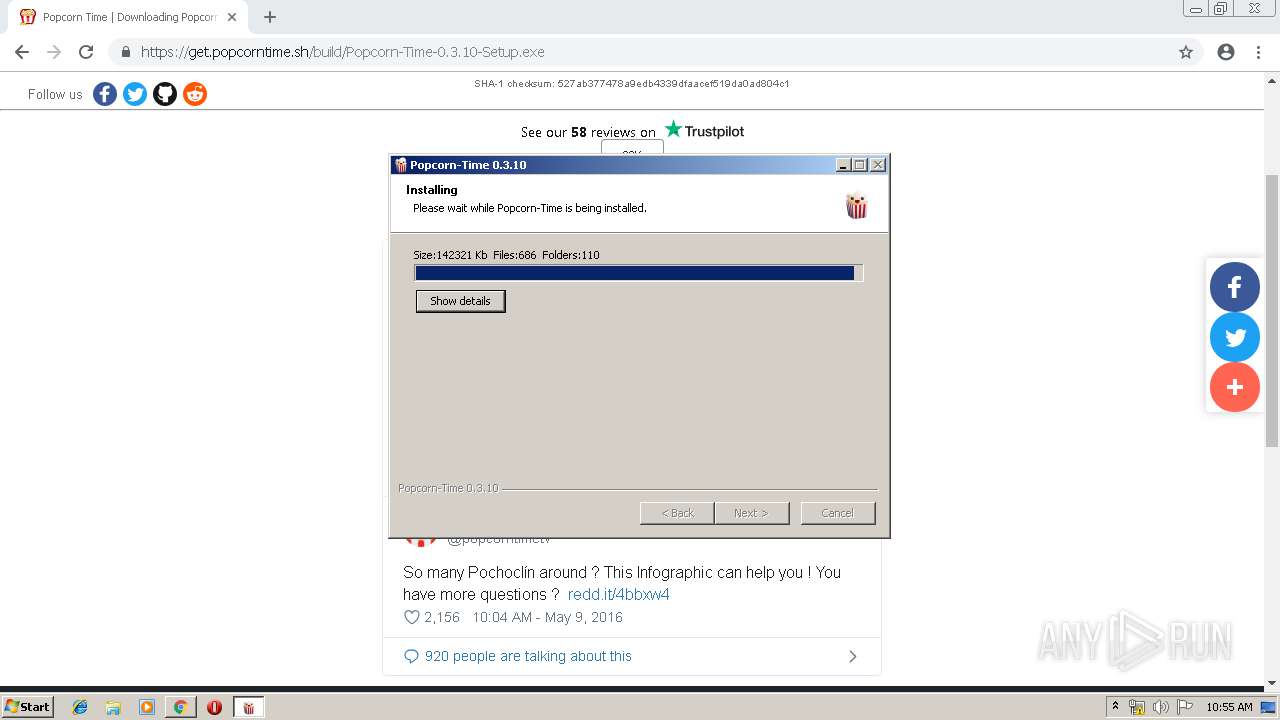
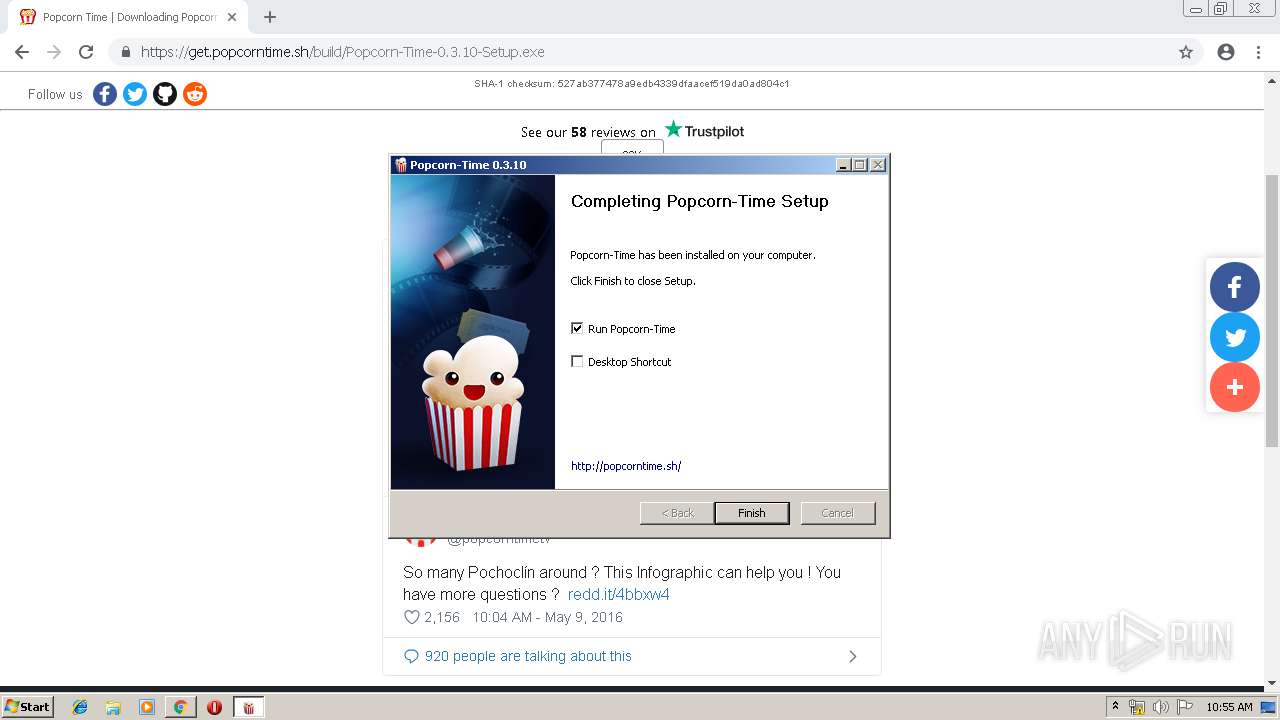
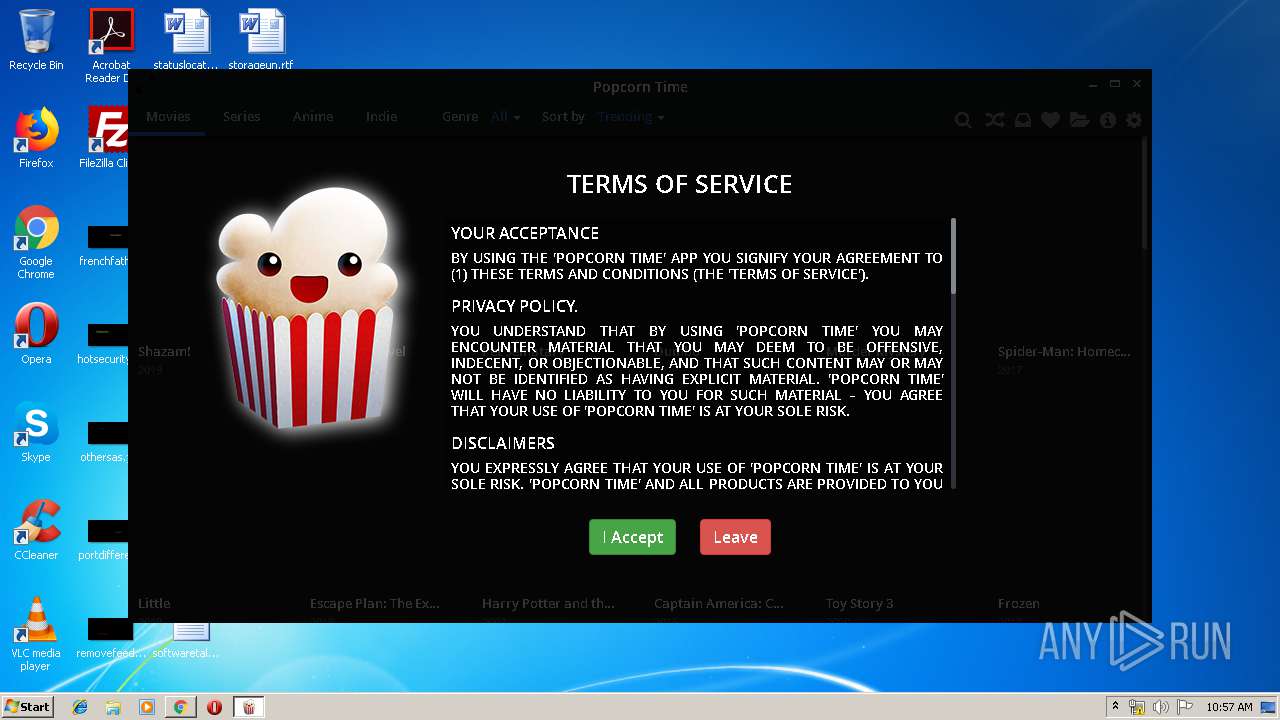
MALICIOUS
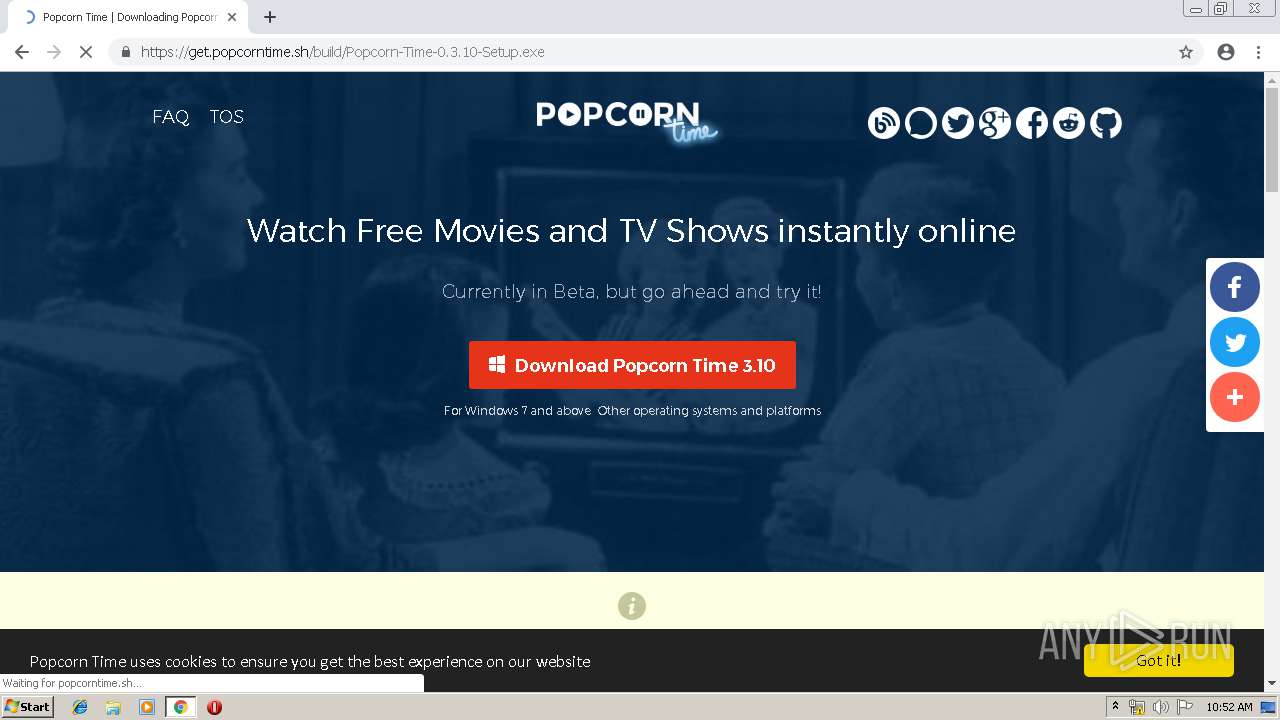
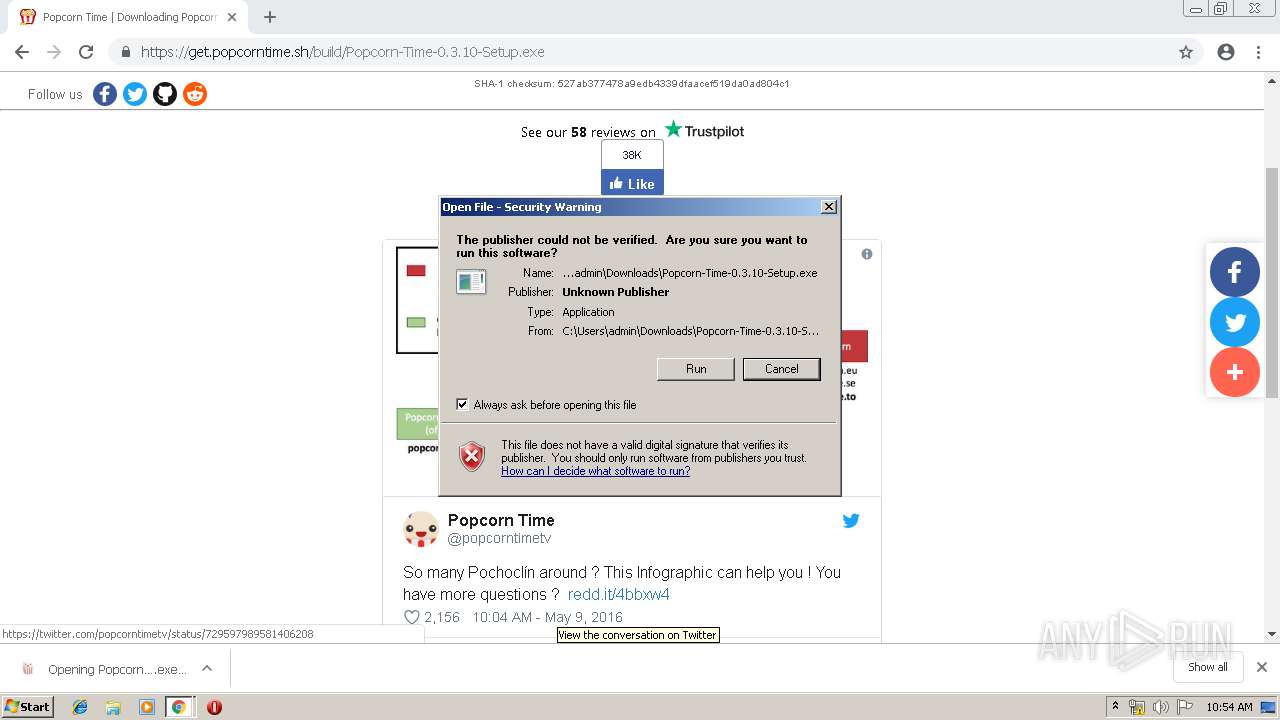
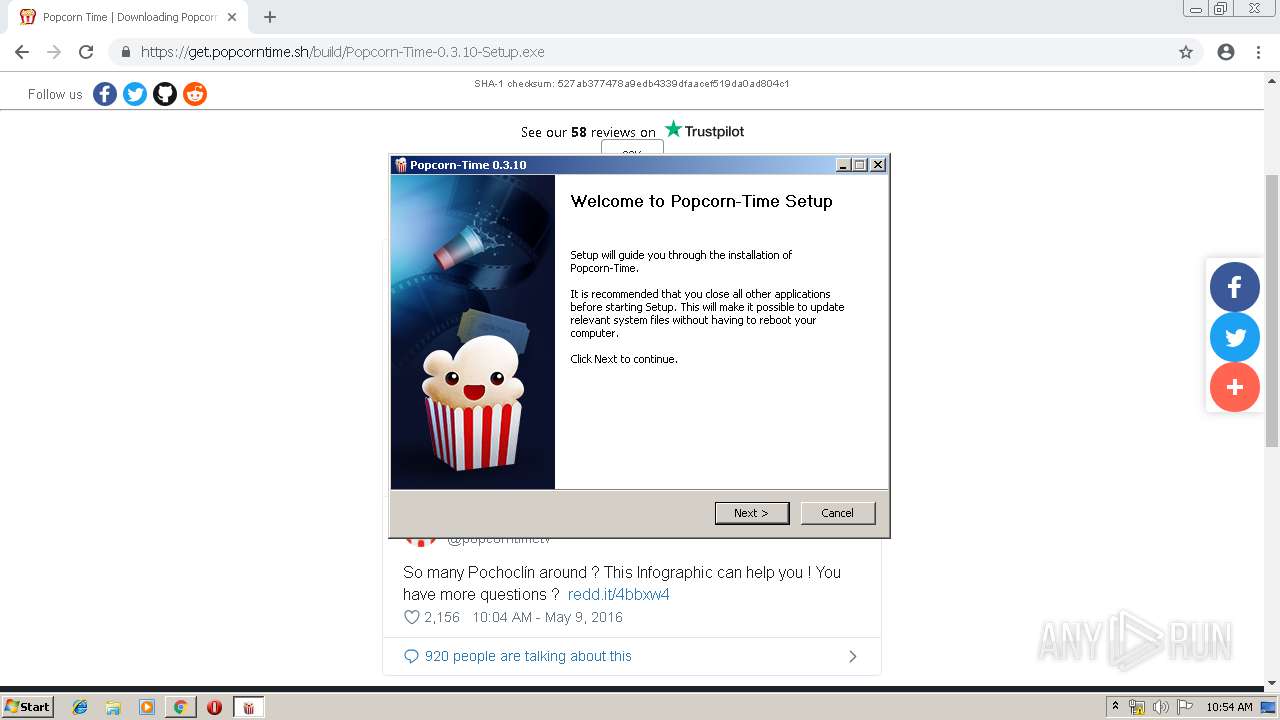
Application was dropped or rewritten from another process
- Popcorn-Time-0.3.10-Setup.exe (PID: 3148)
- Popcorn-Time.exe (PID: 2996)
- Popcorn-Time.exe (PID: 3396)
- Popcorn-Time.exe (PID: 2440)
- Popcorn-Time.exe (PID: 2596)
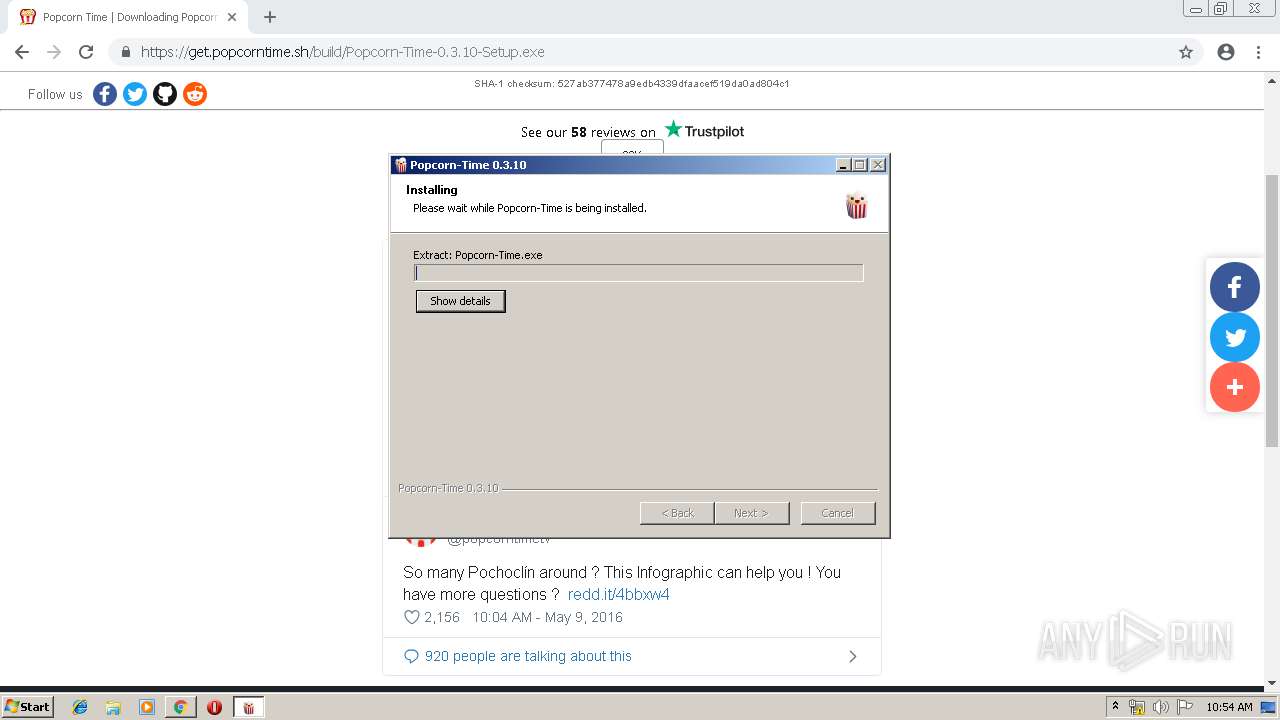
Loads dropped or rewritten executable
- Popcorn-Time-0.3.10-Setup.exe (PID: 3148)
- Popcorn-Time.exe (PID: 2996)
- Popcorn-Time.exe (PID: 3396)
- Popcorn-Time.exe (PID: 2440)
- Popcorn-Time.exe (PID: 2596)
SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 2140)
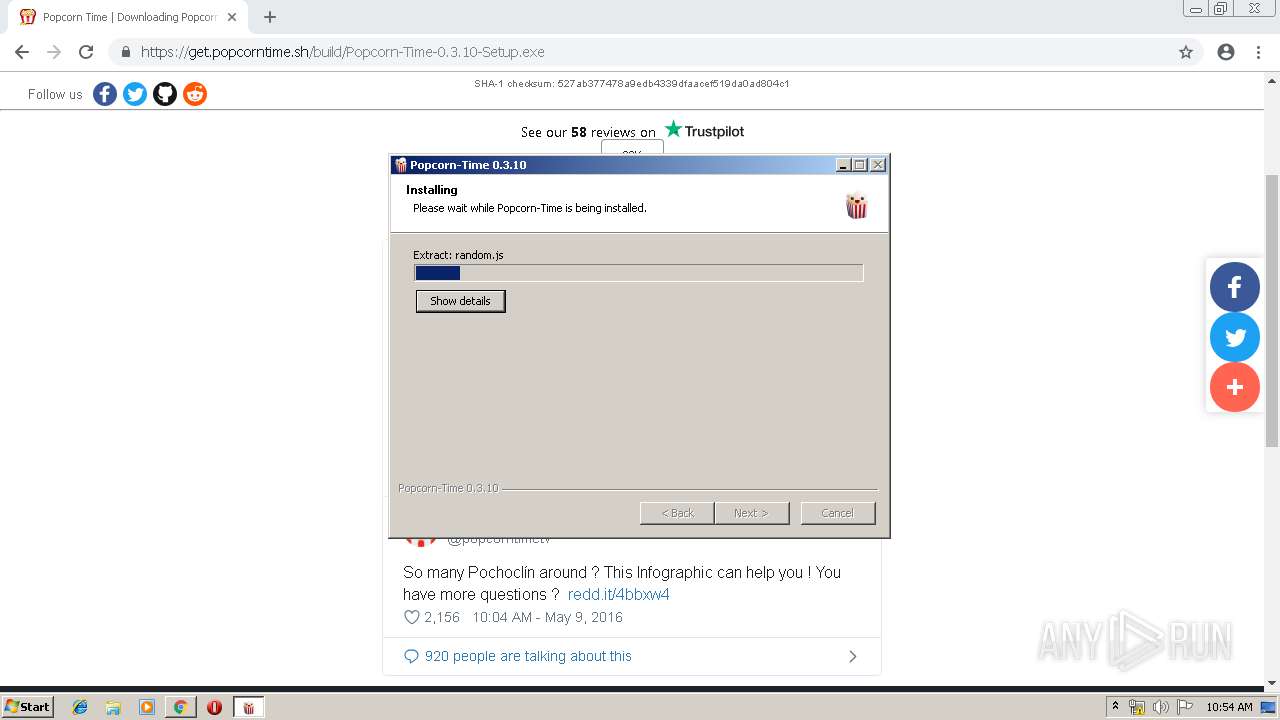
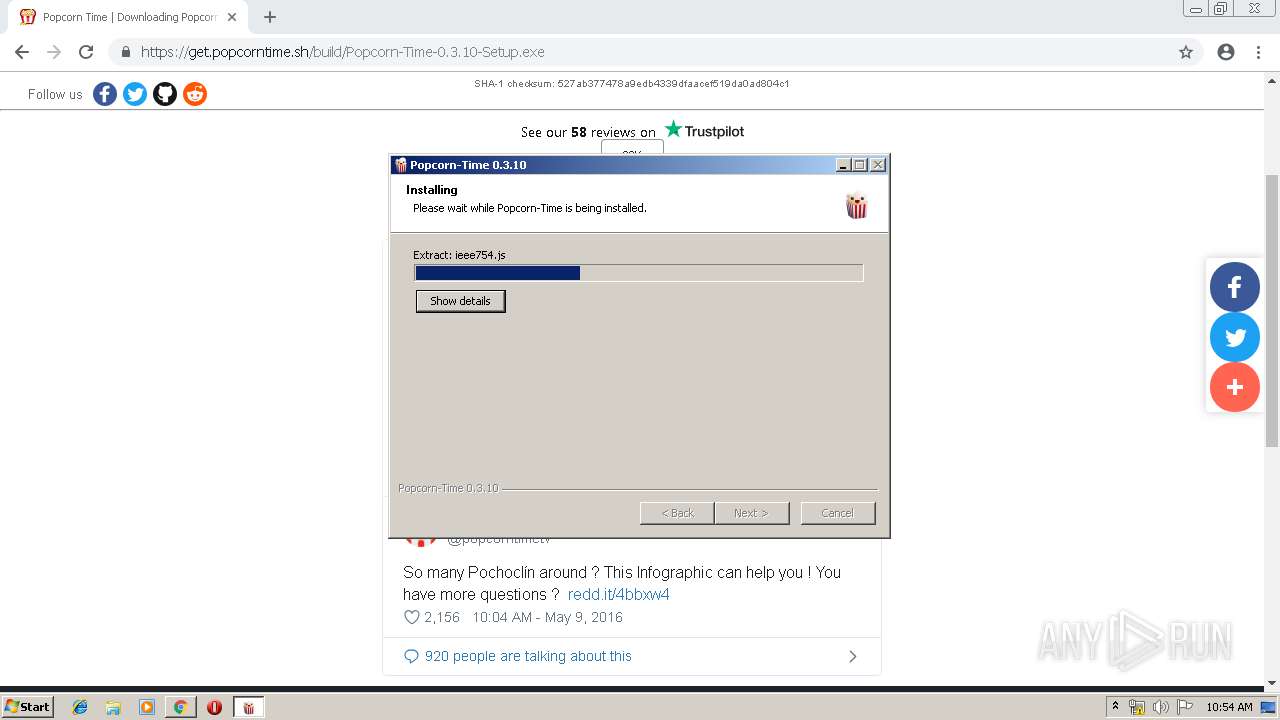
Executable content was dropped or overwritten
- chrome.exe (PID: 2140)
- Popcorn-Time-0.3.10-Setup.exe (PID: 3148)
Creates files in the user directory
- Popcorn-Time-0.3.10-Setup.exe (PID: 3148)
Creates a software uninstall entry
- Popcorn-Time-0.3.10-Setup.exe (PID: 3148)
Modifies the open verb of a shell class
- Popcorn-Time-0.3.10-Setup.exe (PID: 3148)
Application launched itself
- Popcorn-Time.exe (PID: 2996)
INFO
Reads settings of System Certificates
- chrome.exe (PID: 2140)
Reads Internet Cache Settings
- chrome.exe (PID: 2140)
Application launched itself
- chrome.exe (PID: 2140)
Creates files in the user directory
- chrome.exe (PID: 2140)
Dropped object may contain Bitcoin addresses
- Popcorn-Time-0.3.10-Setup.exe (PID: 3148)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
65
Monitored processes
34
Malicious processes
3
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 728 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,10475201787745855185,11569598025373852412,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=2647052863144575784 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2647052863144575784 --renderer-client-id=19 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3508 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 920 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=960,10475201787745855185,11569598025373852412,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=16696719730842560893 --mojo-platform-channel-handle=3960 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1092 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=960,10475201787745855185,11569598025373852412,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=2540575499773730872 --mojo-platform-channel-handle=3952 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1132 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,10475201787745855185,11569598025373852412,131072 --enable-features=PasswordImport --service-pipe-token=5535311646725513885 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5535311646725513885 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2032 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1140 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=960,10475201787745855185,11569598025373852412,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=7823460144730354765 --mojo-platform-channel-handle=3936 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1480 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,10475201787745855185,11569598025373852412,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=8810239742735524644 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8810239742735524644 --renderer-client-id=22 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3732 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1532 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=960,10475201787745855185,11569598025373852412,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwAAAQAAAAAAAAAAAGAAAAAAAAEAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=15920027177994419801 --mojo-platform-channel-handle=952 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1688 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,10475201787745855185,11569598025373852412,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=14457566819148061124 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14457566819148061124 --renderer-client-id=18 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3460 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1848 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,10475201787745855185,11569598025373852412,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=5334969885016821161 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5334969885016821161 --renderer-client-id=17 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4432 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1928 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,10475201787745855185,11569598025373852412,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=9139517453232417890 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9139517453232417890 --renderer-client-id=25 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=5216 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
Total events
1 413
Read events
1 267
Write events
140
Delete events
6
Modification events
| (PID) Process: | (2140) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2140) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2140) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2140) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2140) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3332) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2140-13206189150159875 |
Value: 259 | |||
| (PID) Process: | (2140) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2140) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2140) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3488-13197474229333984 |
Value: 0 | |||
| (PID) Process: | (2140) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2140-13206189150159875 |
Value: 259 | |||
Executable files
16
Suspicious files
193
Text files
12 666
Unknown types
59
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2140 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 2140 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 2140 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2140 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 2140 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
| 2140 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\9ff35f5d-3ee7-476a-8a5b-6ac34ab0bca0.tmp | — | |
MD5:— | SHA256:— | |||
| 2140 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 2140 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 2140 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2140 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
59
TCP/UDP connections
243
DNS requests
64
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
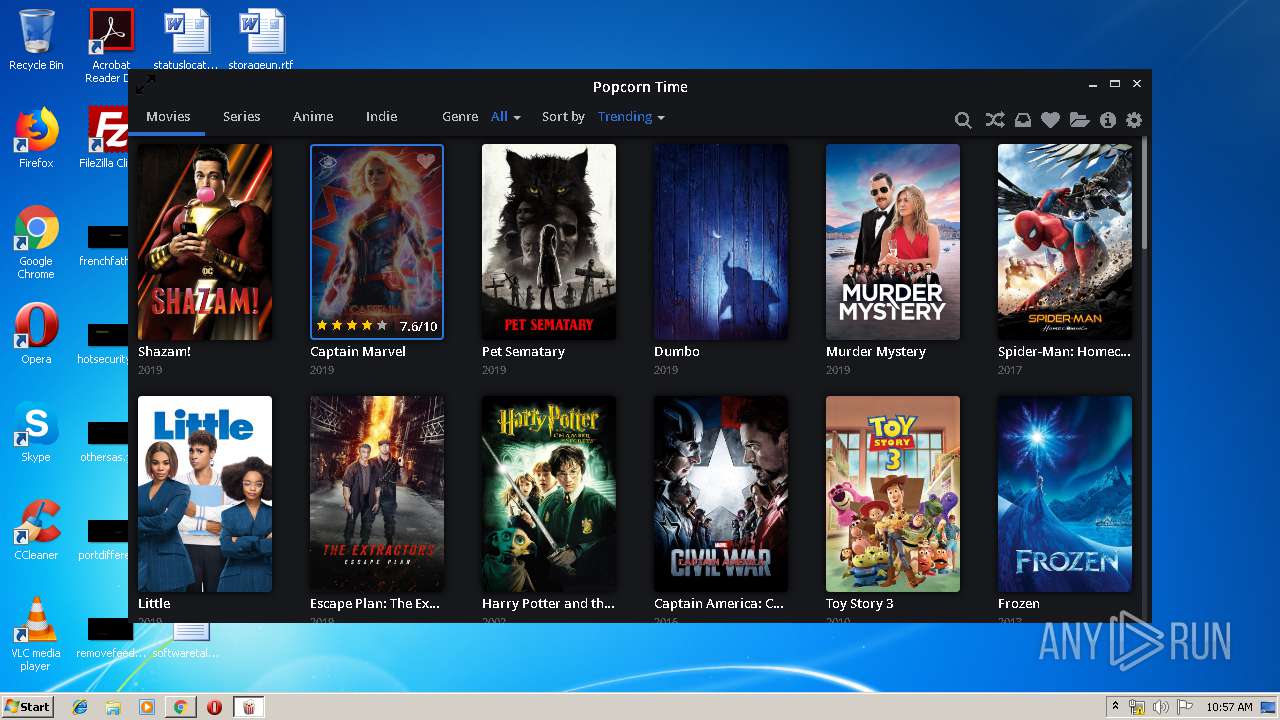
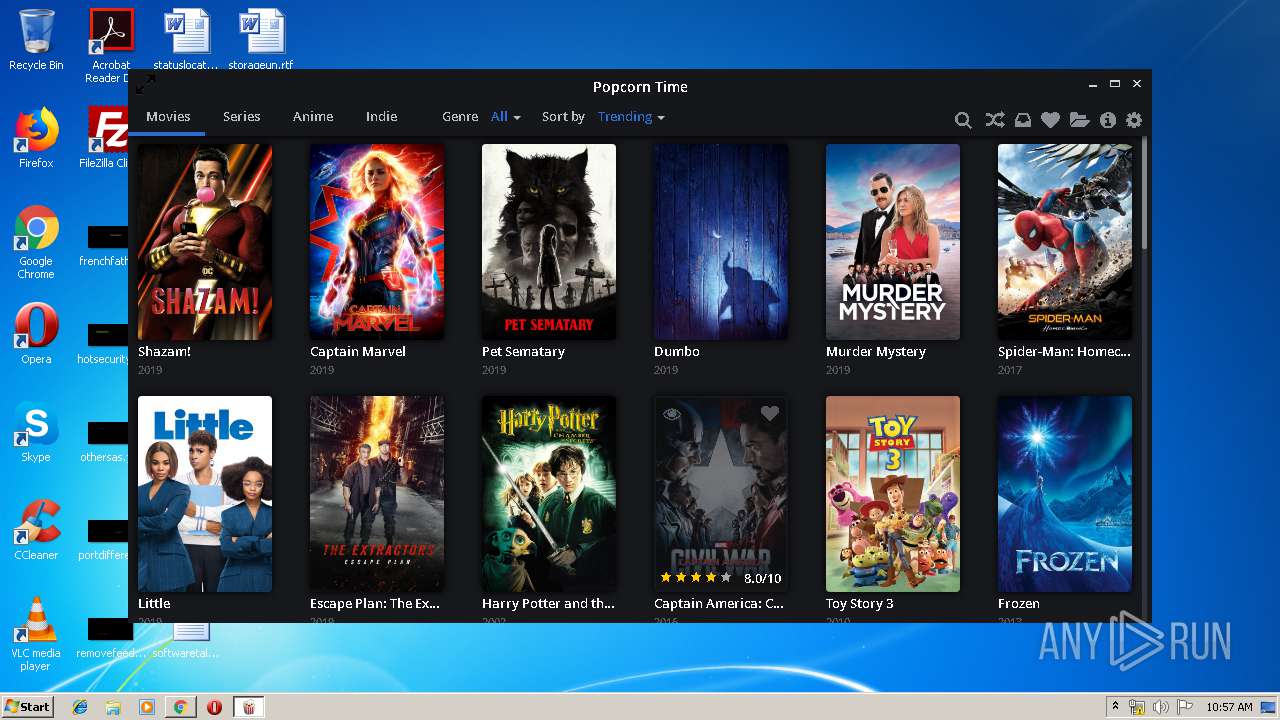
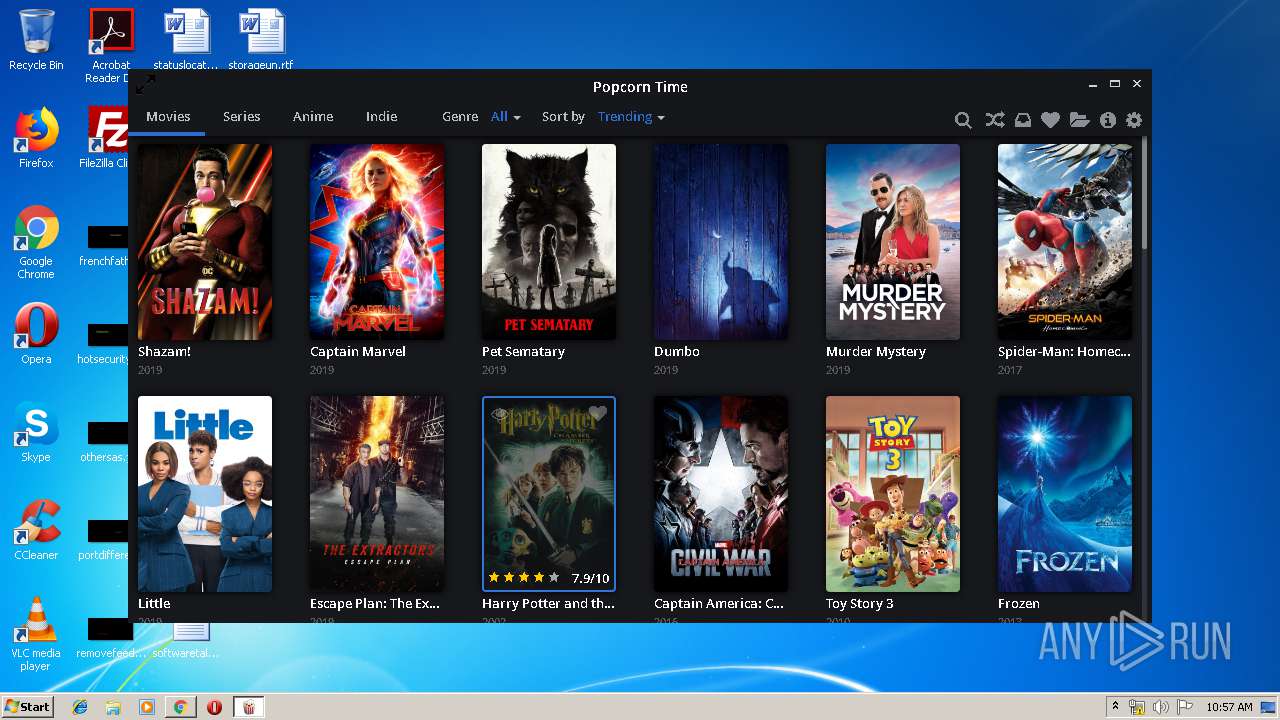
2996 | Popcorn-Time.exe | GET | — | 104.16.60.155:80 | http://image.tmdb.org/t/p/w500/ydUpl3QkVUCHCq1VWvo2rW4Sf7y.jpg | US | — | — | whitelisted |
2996 | Popcorn-Time.exe | GET | — | 104.16.60.155:80 | http://image.tmdb.org/t/p/w500/5aGhaIHYuQbqlHWvWYqMCnj40y2.jpg | US | — | — | whitelisted |
2596 | Popcorn-Time.exe | GET | — | 104.16.229.14:80 | http://104.16.229.14:80/api/7B95D15E1BE1D75A/languages.xml | US | — | — | shared |
2996 | Popcorn-Time.exe | GET | — | 104.16.60.155:80 | http://image.tmdb.org/t/p/w500/Z020zFirgLav9IckjYTmjyEwX8.jpg | US | — | — | whitelisted |
2996 | Popcorn-Time.exe | GET | — | 104.16.60.155:80 | http://image.tmdb.org/t/p/w500/uMZqKhT4YA6mqo2yczoznv7IDmv.jpg | US | — | — | whitelisted |
2996 | Popcorn-Time.exe | GET | — | 104.16.60.155:80 | http://image.tmdb.org/t/p/w500/7SPhr7Qj39vbnfF9O2qHRYaKHAL.jpg | US | — | — | whitelisted |
2996 | Popcorn-Time.exe | GET | — | 104.16.60.155:80 | http://image.tmdb.org/t/p/w500/lLbcqa8YnO2Qz4ggflhwglwXI8R.jpg | US | — | — | whitelisted |
2996 | Popcorn-Time.exe | GET | — | 104.16.60.155:80 | http://image.tmdb.org/t/p/w500/bSMSO9xupd4R4vwTPqigHn2quLN.jpg | US | — | — | whitelisted |
2996 | Popcorn-Time.exe | GET | — | 104.16.60.155:80 | http://image.tmdb.org/t/p/w500/wMq9kQXTeQCHUZOG4fAe5cAxyUA.jpg | US | — | — | whitelisted |
2996 | Popcorn-Time.exe | GET | — | 104.16.60.155:80 | http://image.tmdb.org/t/p/w500/1AreNcL9s24Qfghbzomy0IlzCFk.jpg | US | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
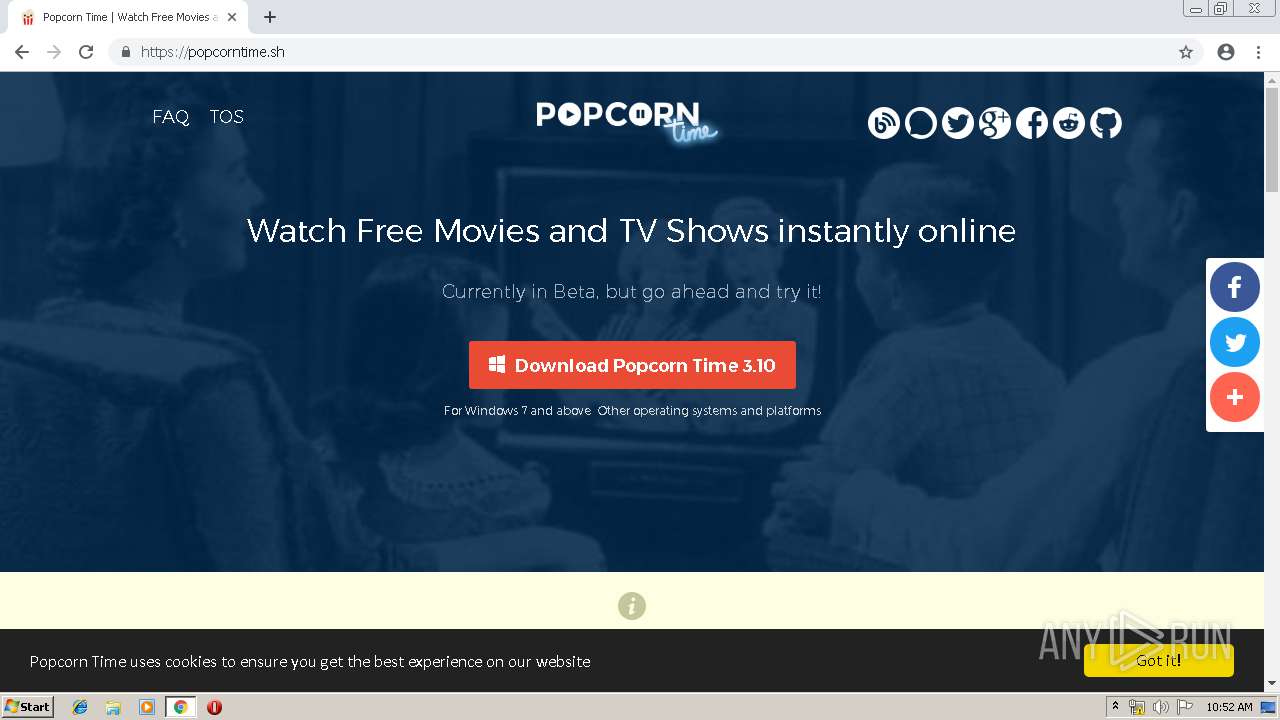
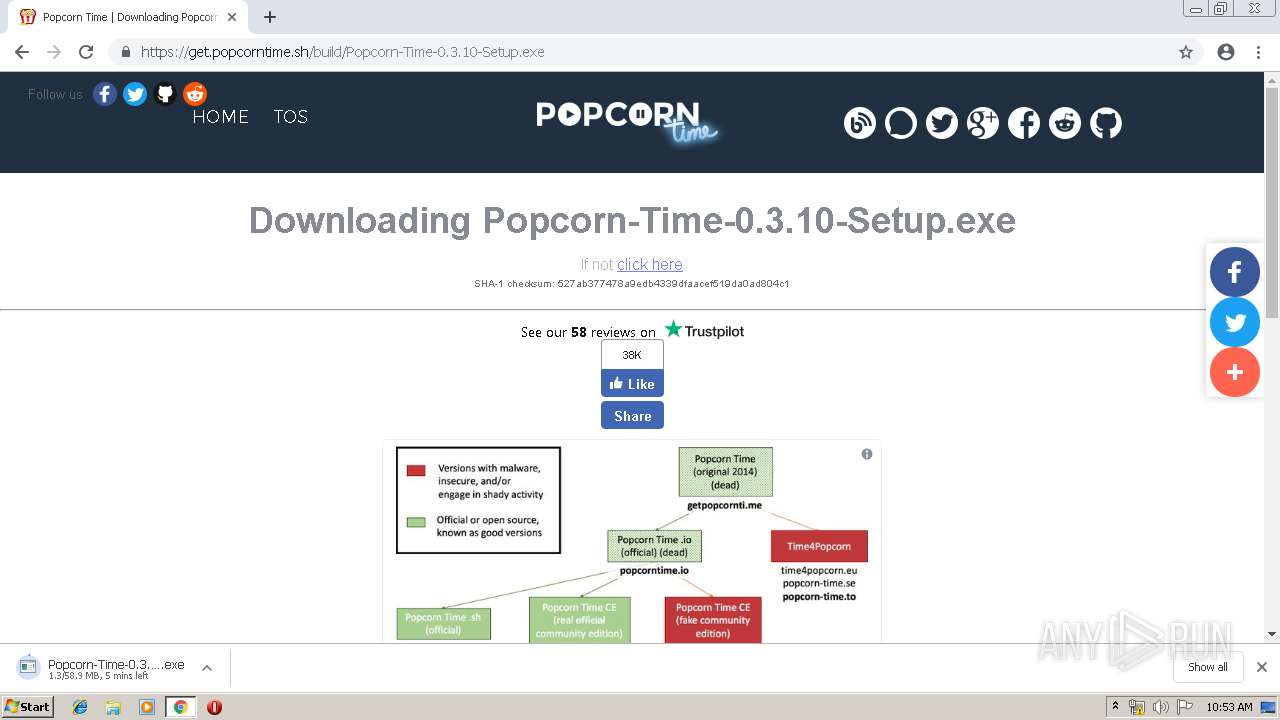
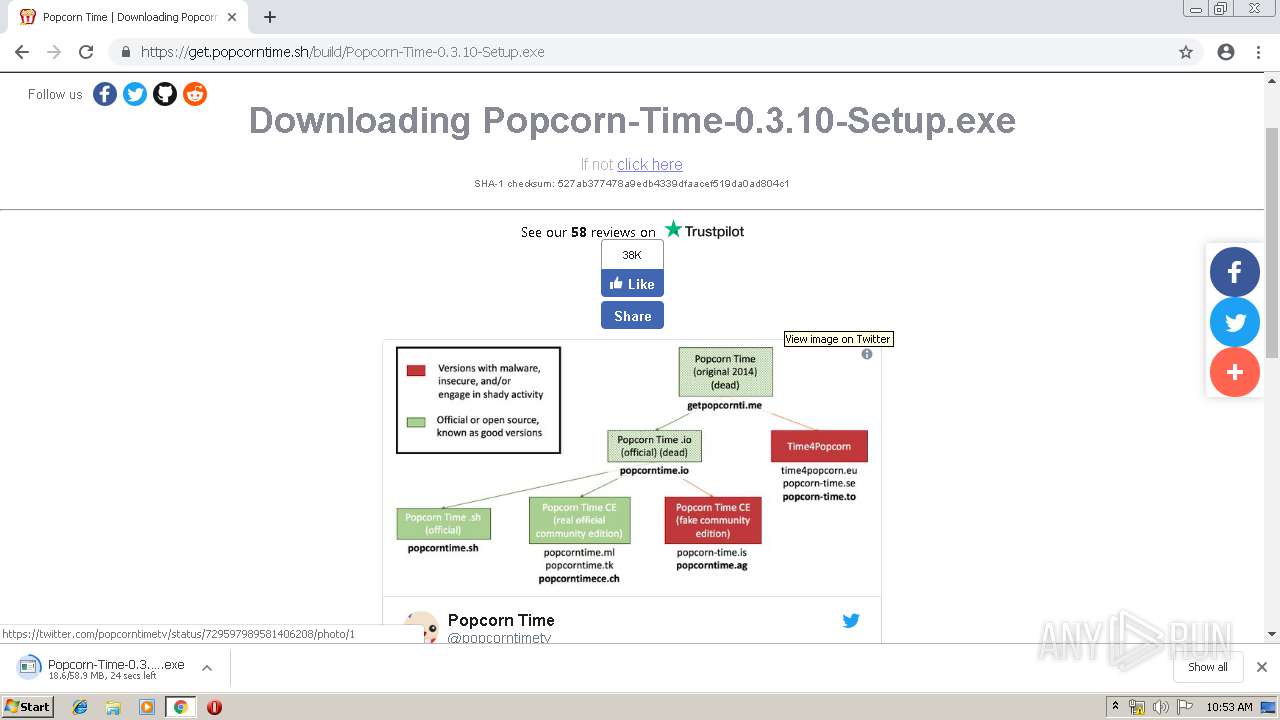
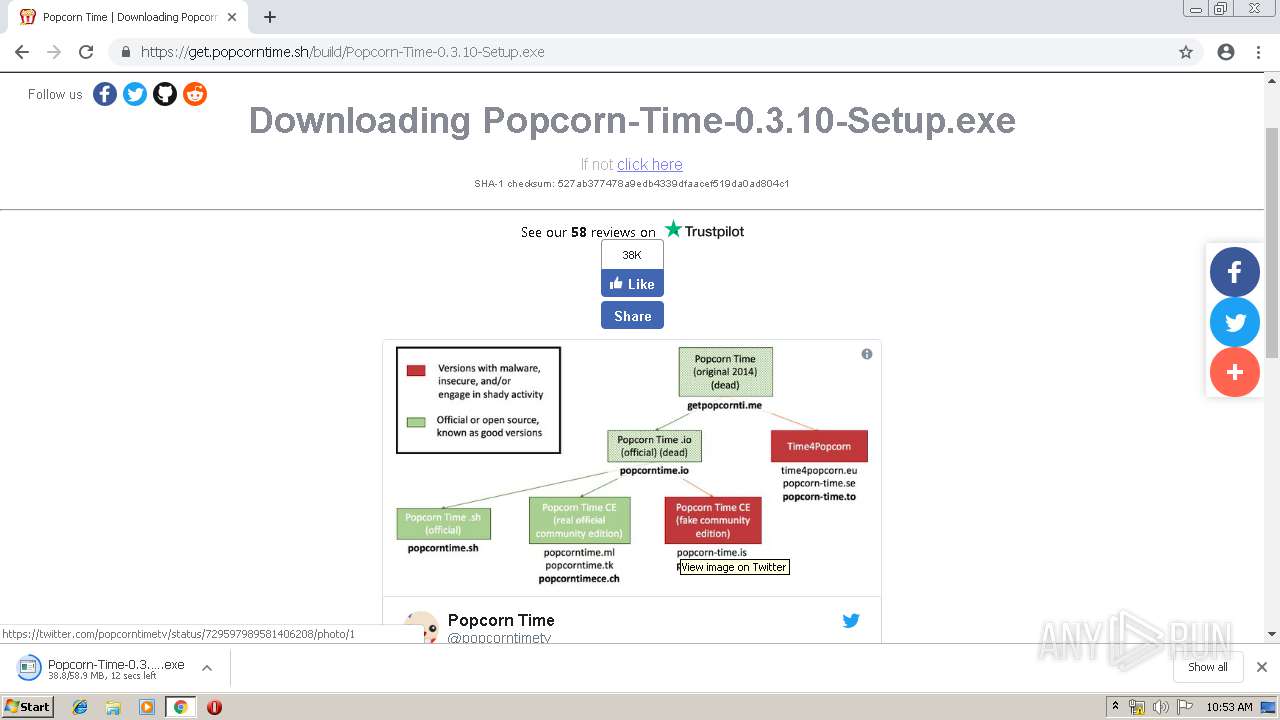
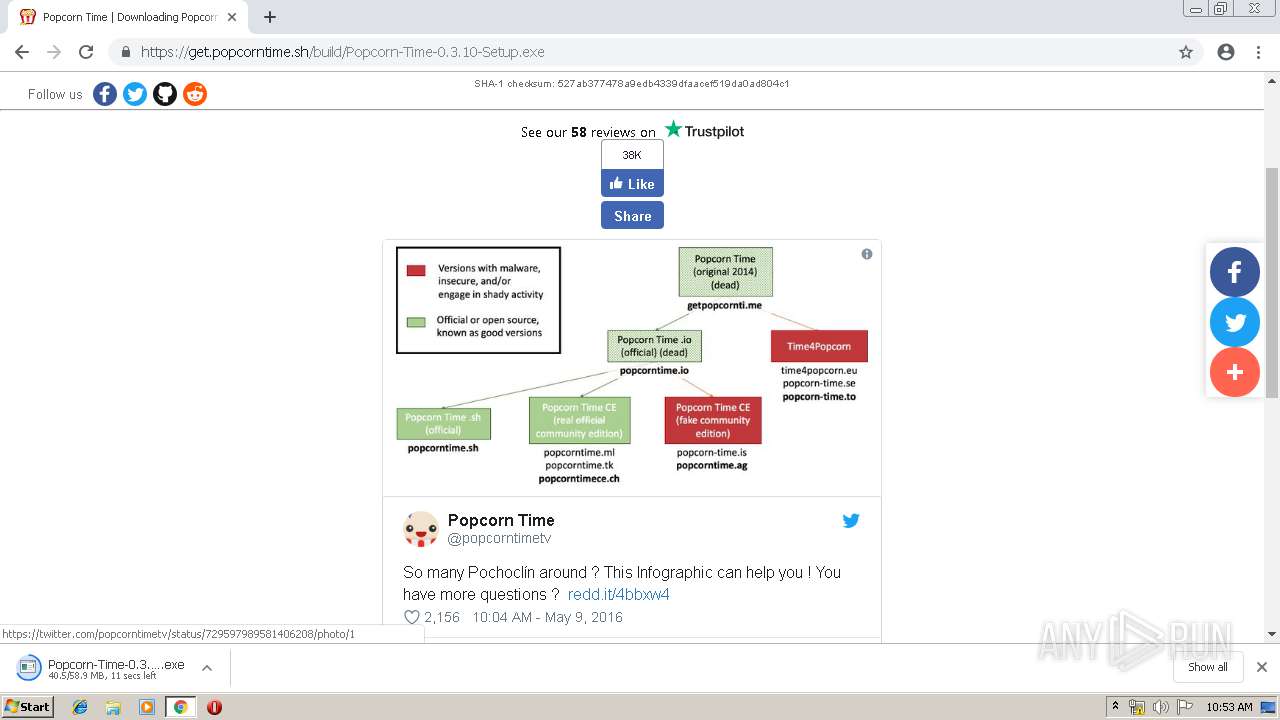
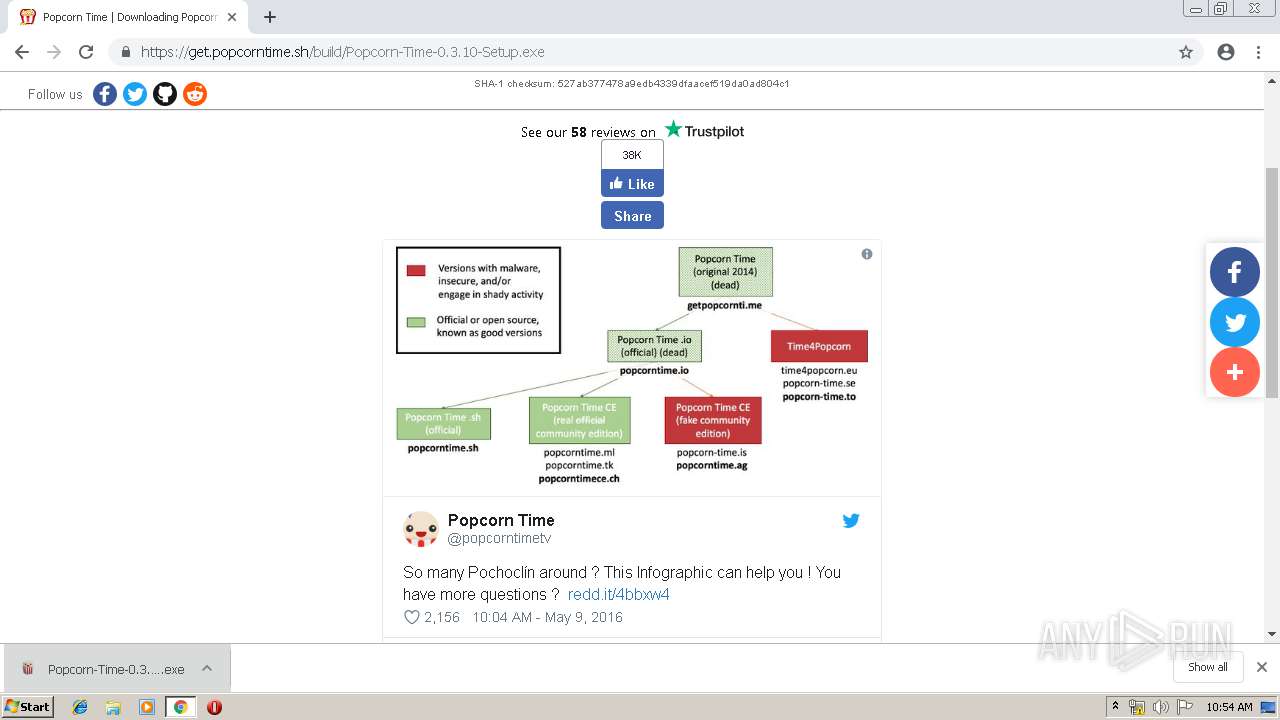
2140 | chrome.exe | 104.20.5.128:443 | popcorntime.sh | Cloudflare Inc | US | shared |
2140 | chrome.exe | 172.217.23.131:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
— | — | 172.217.22.14:80 | google.com | Google Inc. | US | whitelisted |
2140 | chrome.exe | 172.217.22.14:80 | google.com | Google Inc. | US | whitelisted |
2140 | chrome.exe | 216.58.208.36:443 | www.google.com | Google Inc. | US | whitelisted |
2140 | chrome.exe | 172.217.18.110:443 | consent.google.com | Google Inc. | US | whitelisted |
2140 | chrome.exe | 216.58.208.35:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2140 | chrome.exe | 216.58.206.14:443 | clients1.google.com | Google Inc. | US | whitelisted |
2140 | chrome.exe | 216.58.206.3:443 | www.google.co.uk | Google Inc. | US | whitelisted |
2140 | chrome.exe | 172.217.16.162:443 | adservice.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
google.com |
| malicious |
accounts.google.com |
| shared |
www.google.com |
| malicious |
consent.google.com |
| shared |
ssl.gstatic.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
clients1.google.com |
| whitelisted |
www.google.co.uk |
| whitelisted |
apis.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
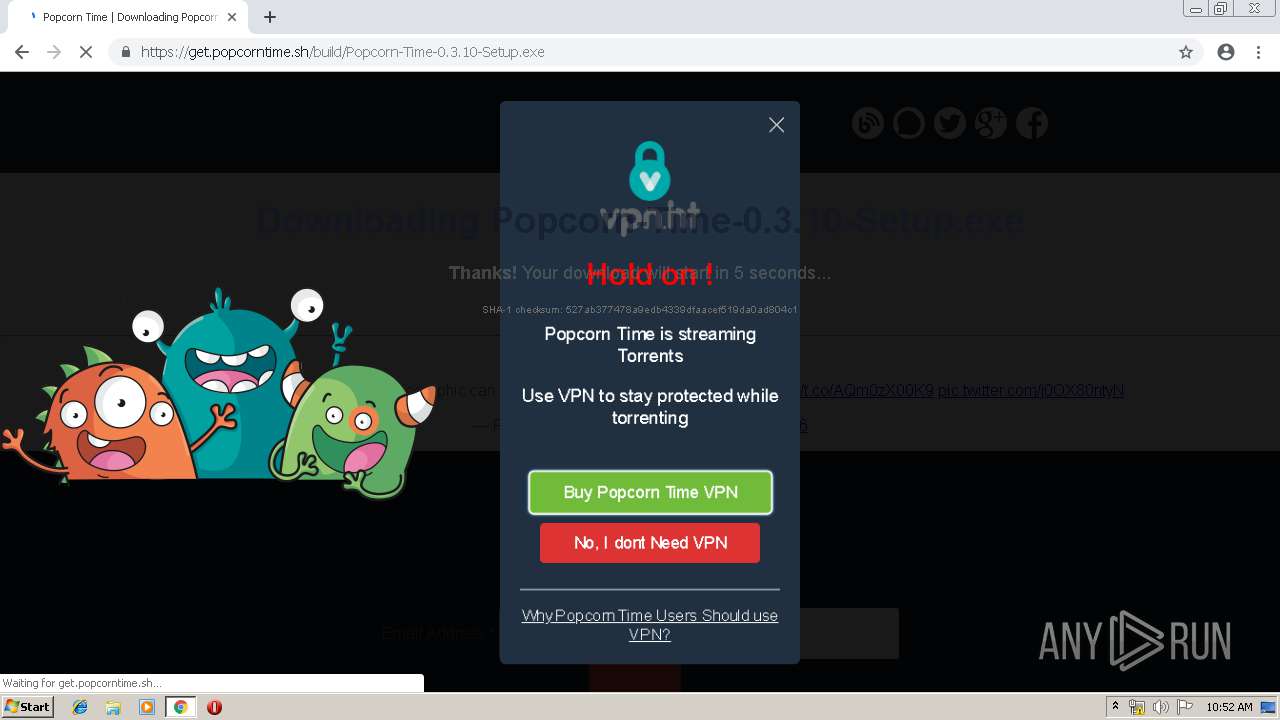
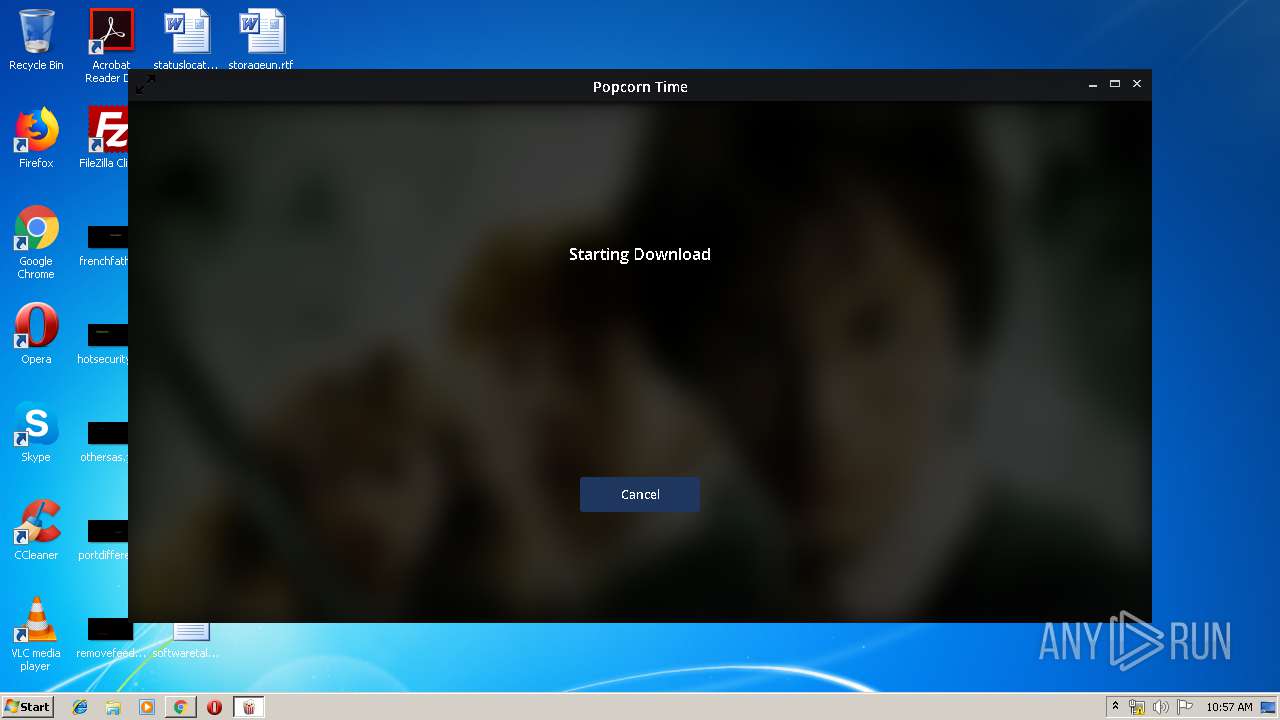
2596 | Popcorn-Time.exe | Potential Corporate Privacy Violation | ET P2P BitTorrent DHT ping request |
2596 | Popcorn-Time.exe | Potential Corporate Privacy Violation | ET P2P Vuze BT UDP Connection (5) |
— | — | Potential Corporate Privacy Violation | ET P2P BitTorrent DHT nodes reply |
Process | Message |
|---|---|
Popcorn-Time.exe | RecursiveDirectoryCreate( C:\Users\admin\AppData\Local directory exists )
|