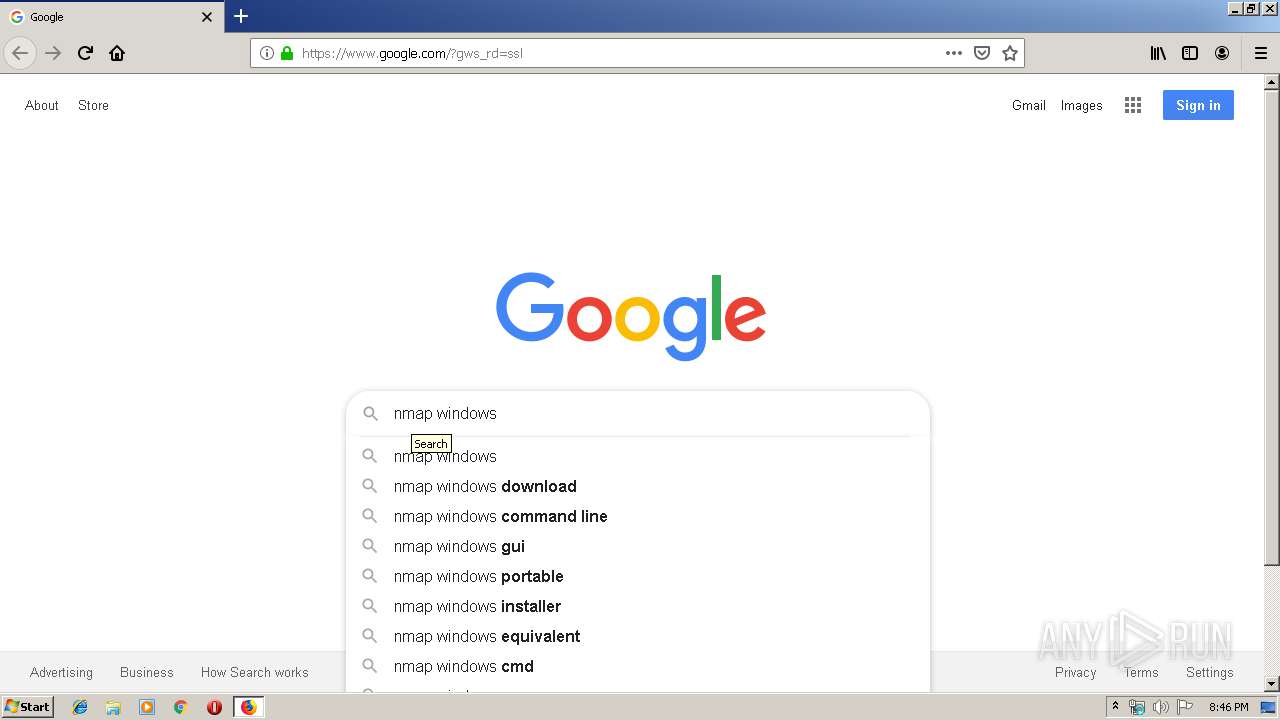
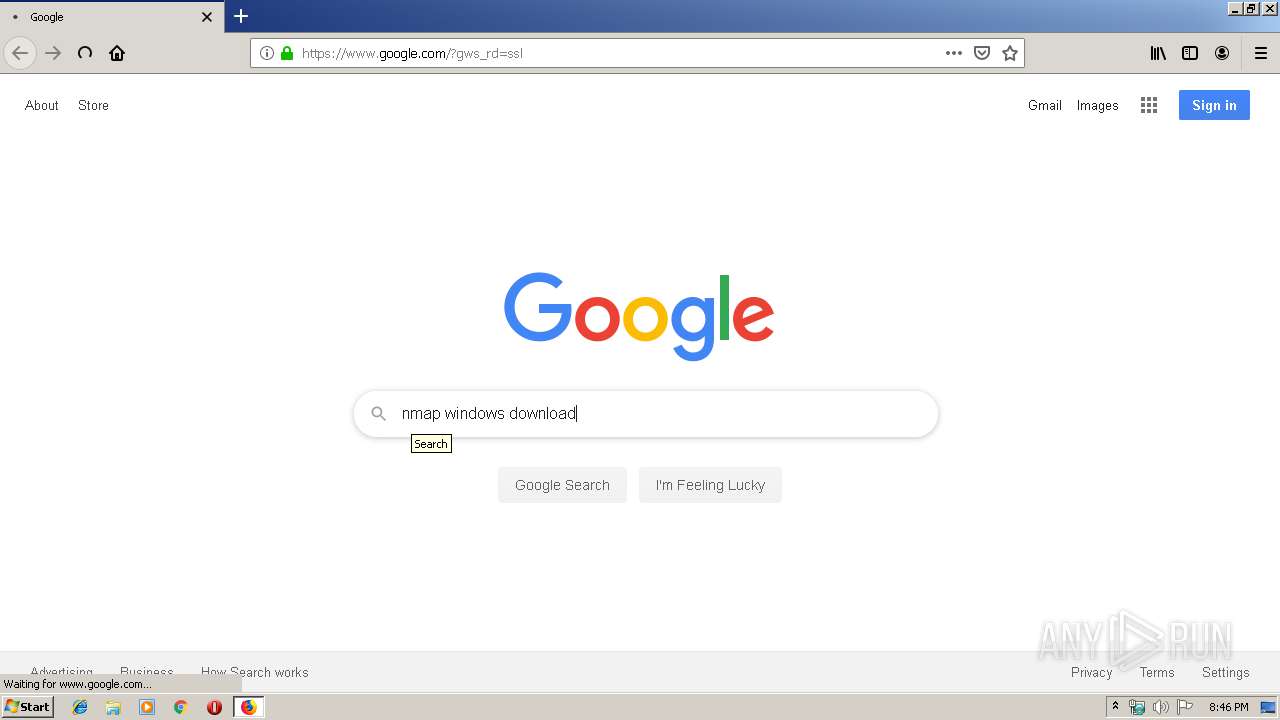
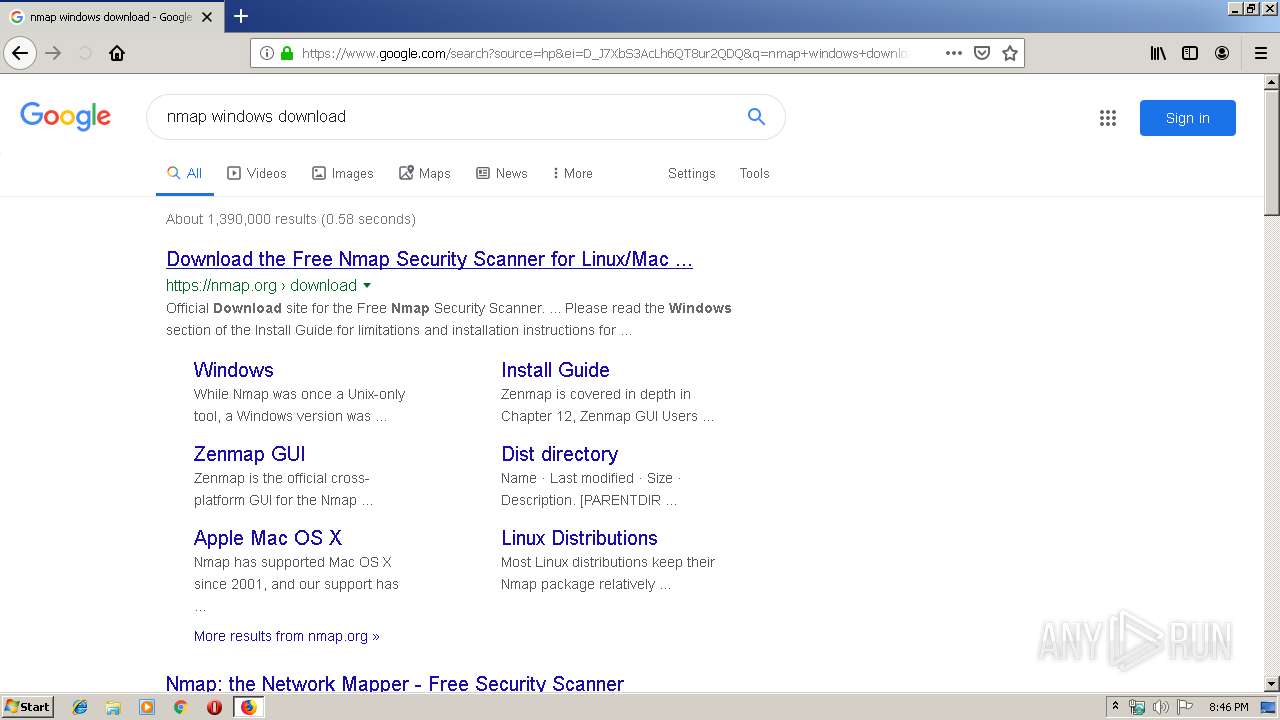
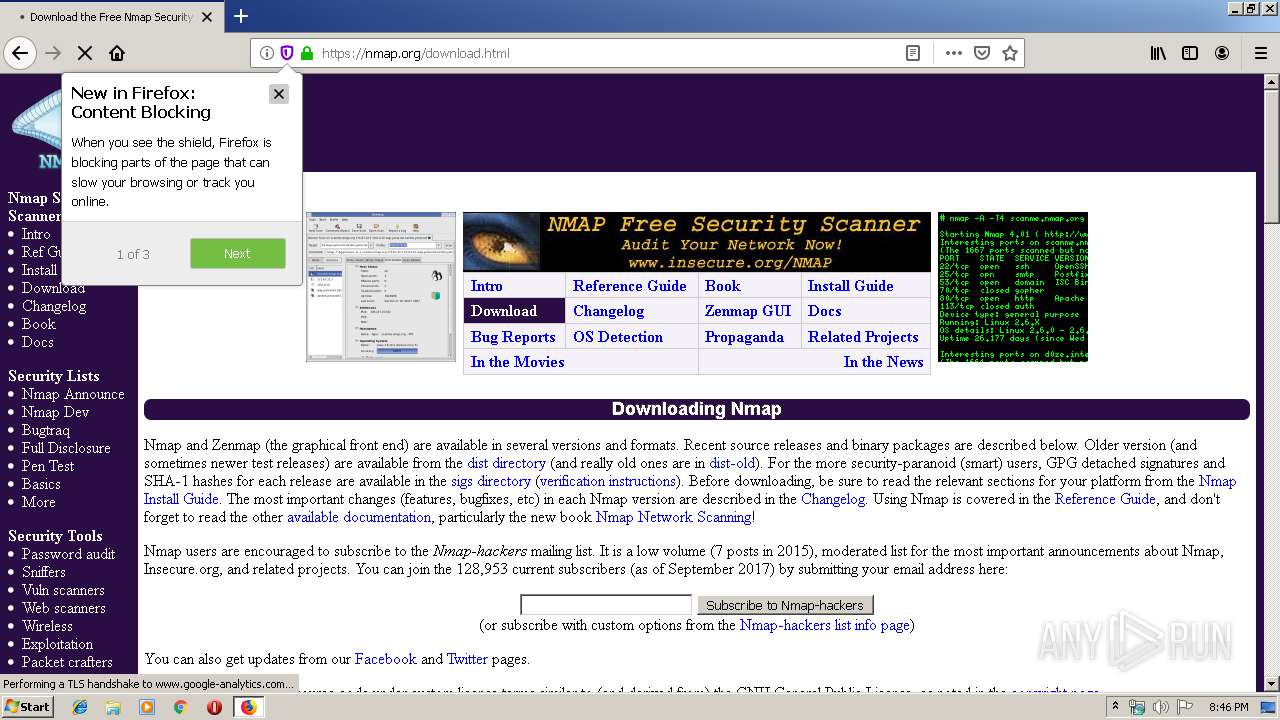
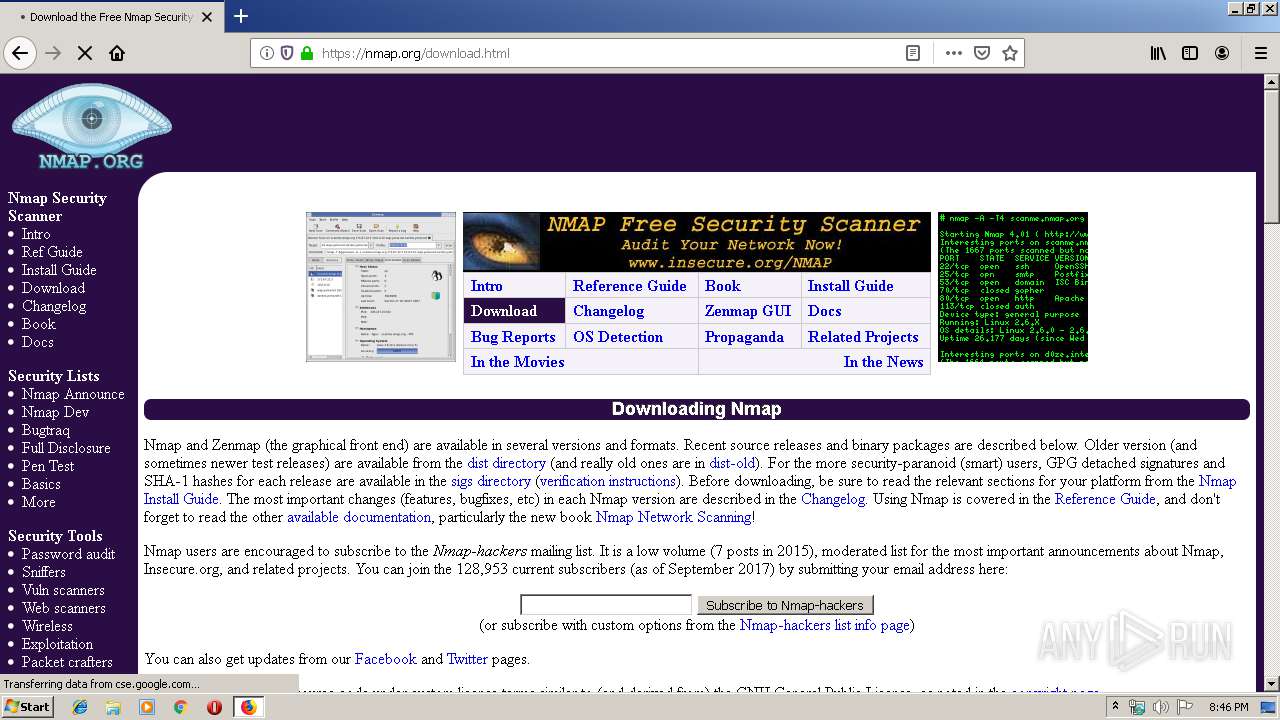
| URL: | http://google.com |
| Full analysis: | https://app.any.run/tasks/02a4e39d-ad32-442c-887a-4b11aaa8c2f5 |
| Verdict: | Malicious activity |
| Analysis date: | September 13, 2019, 19:46:03 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | C7B920F57E553DF2BB68272F61570210 |
| SHA1: | 234988566C9A0A9CF952CEC82B143BF9C207AC16 |
| SHA256: | AA2239C17609B21EBA034C564AF878F3EEC8CE83ED0F2768597D2BC2FD4E4DA5 |
| SSDEEP: | 3:N1KZK3uK:C03uK |
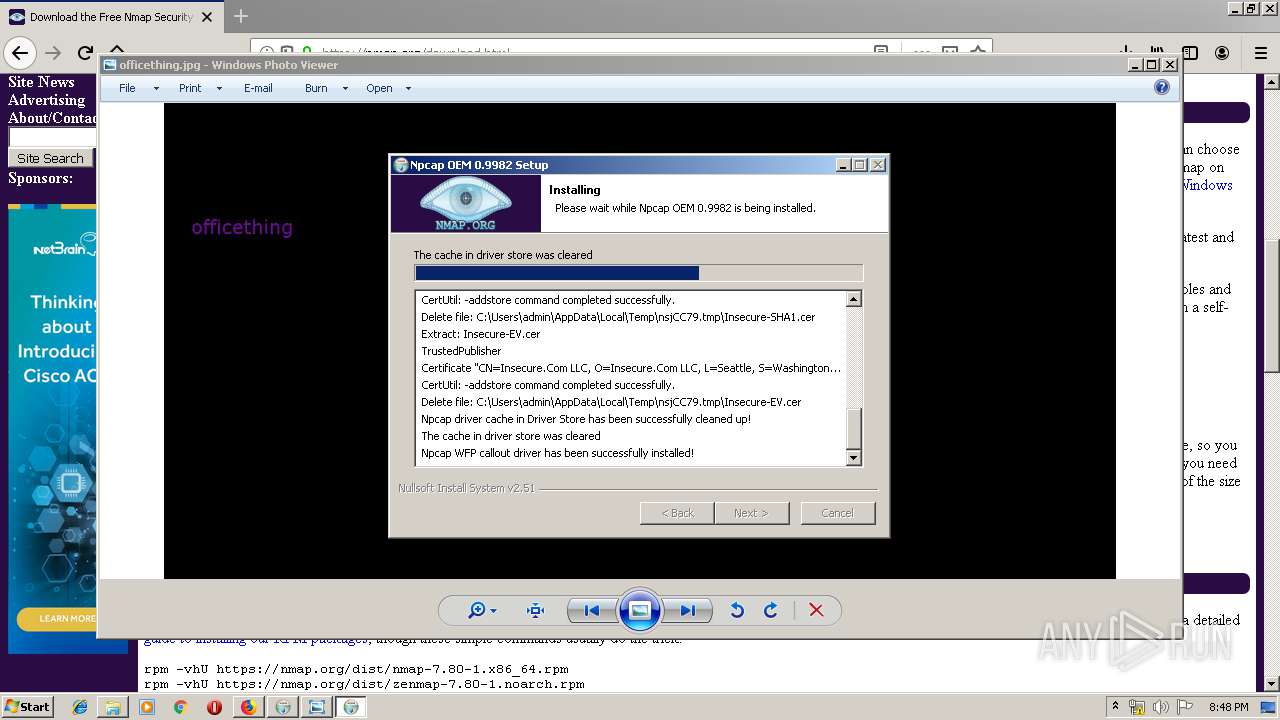
MALICIOUS
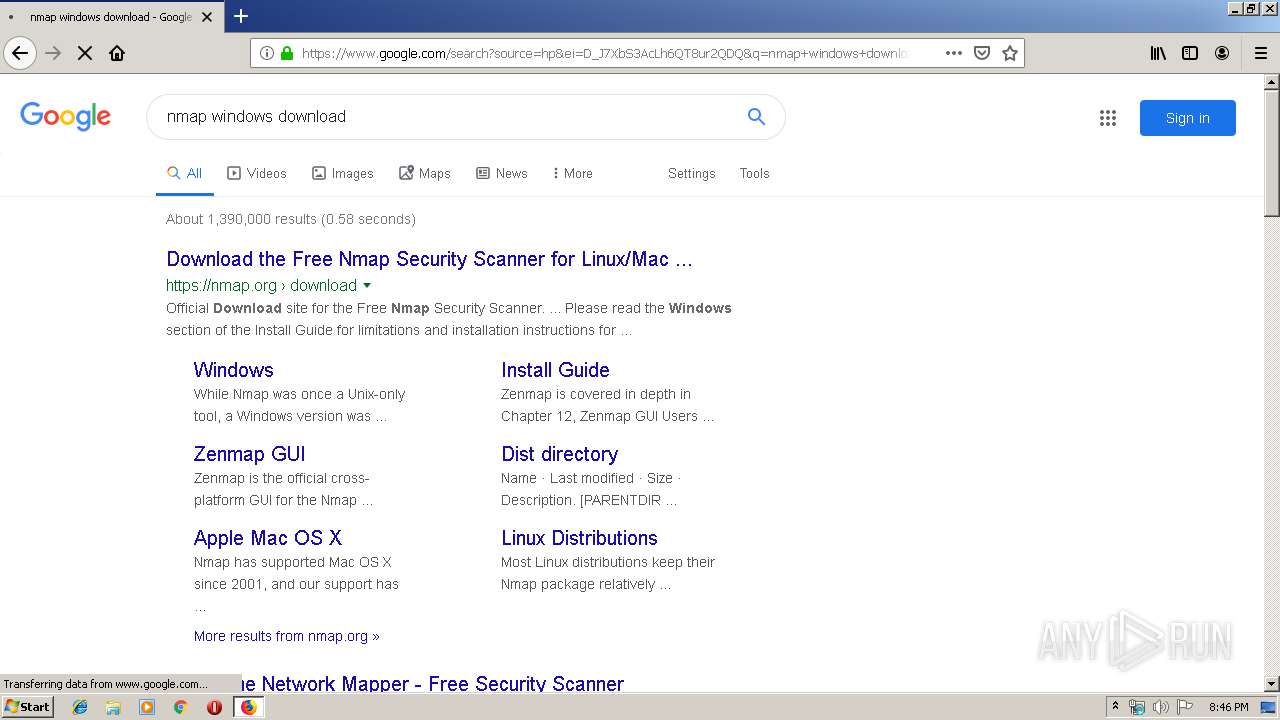
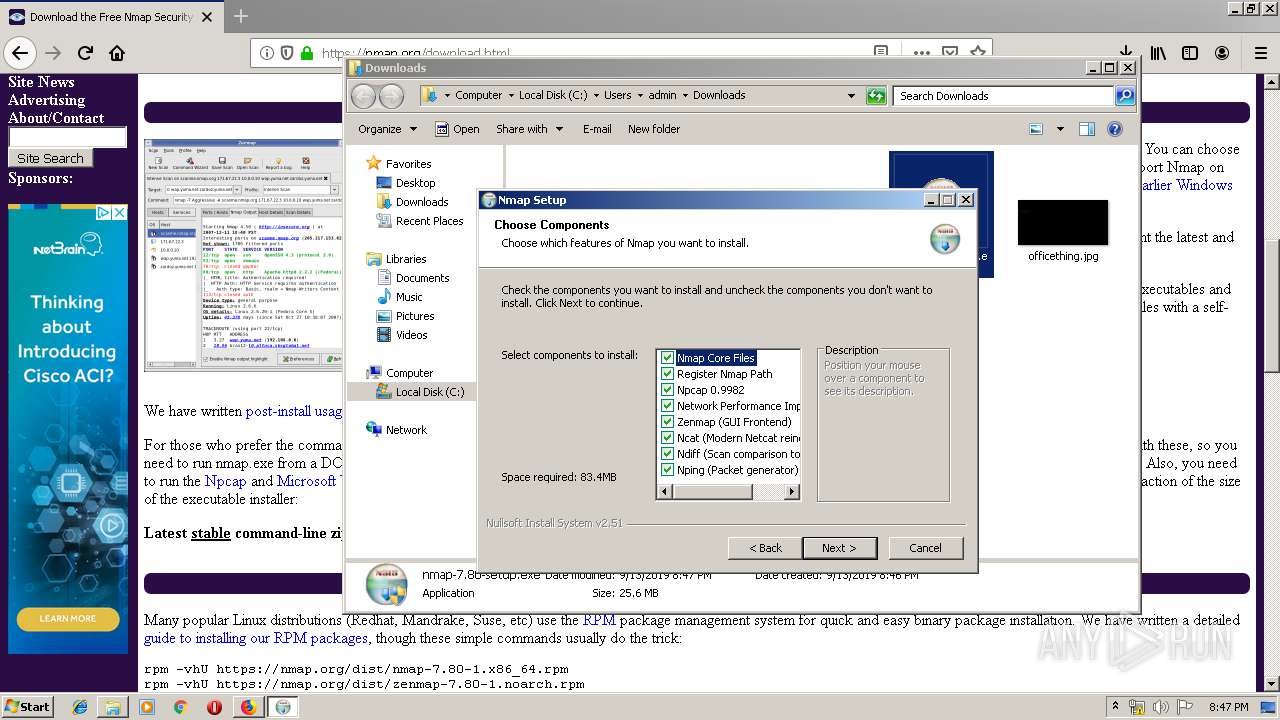
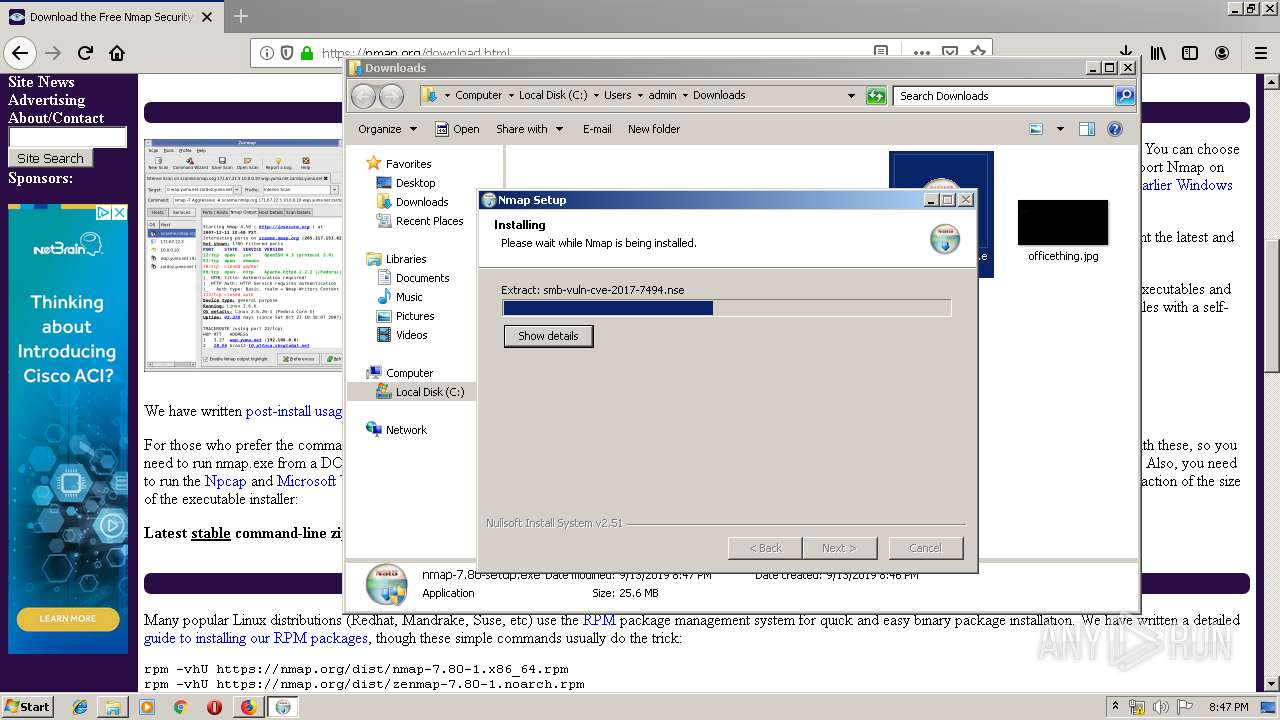
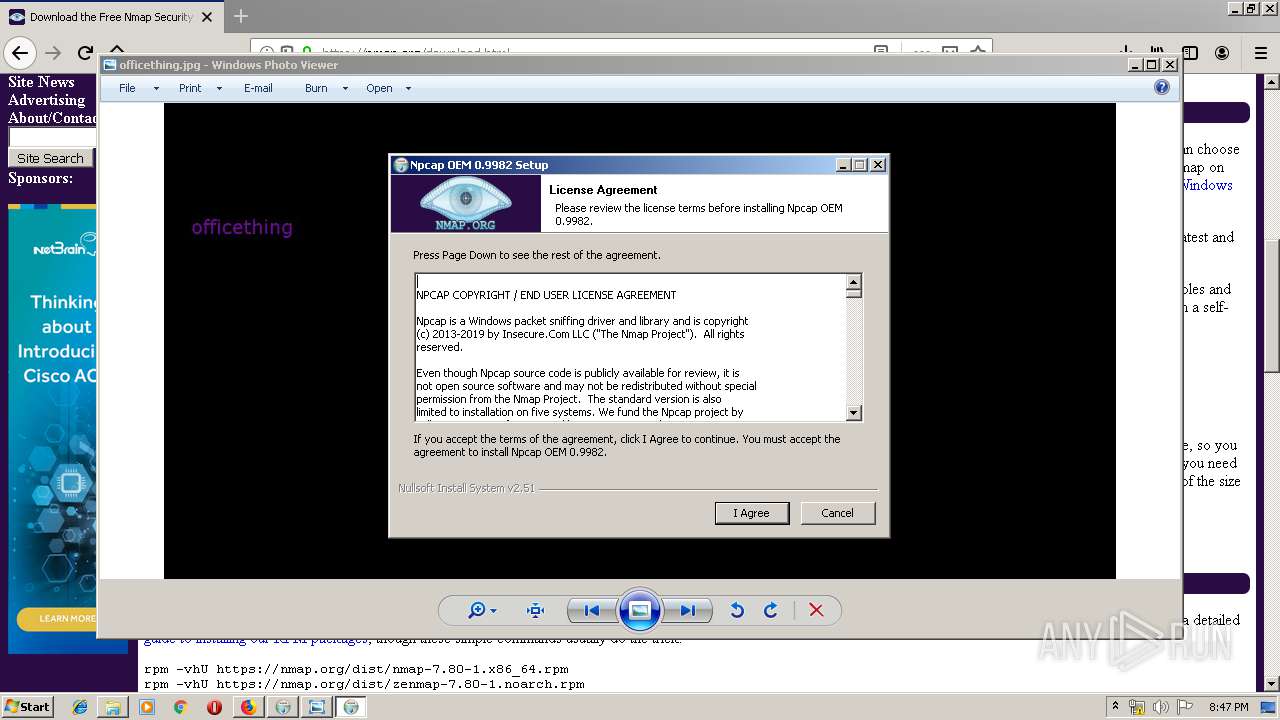
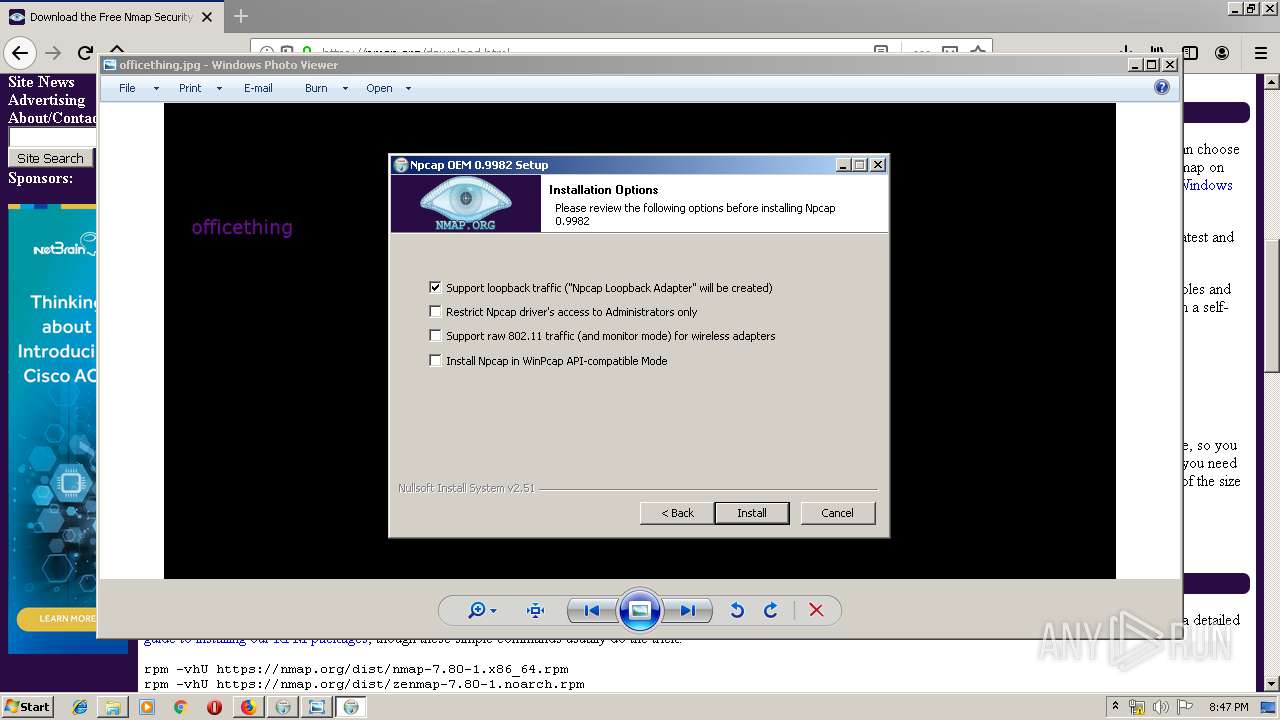
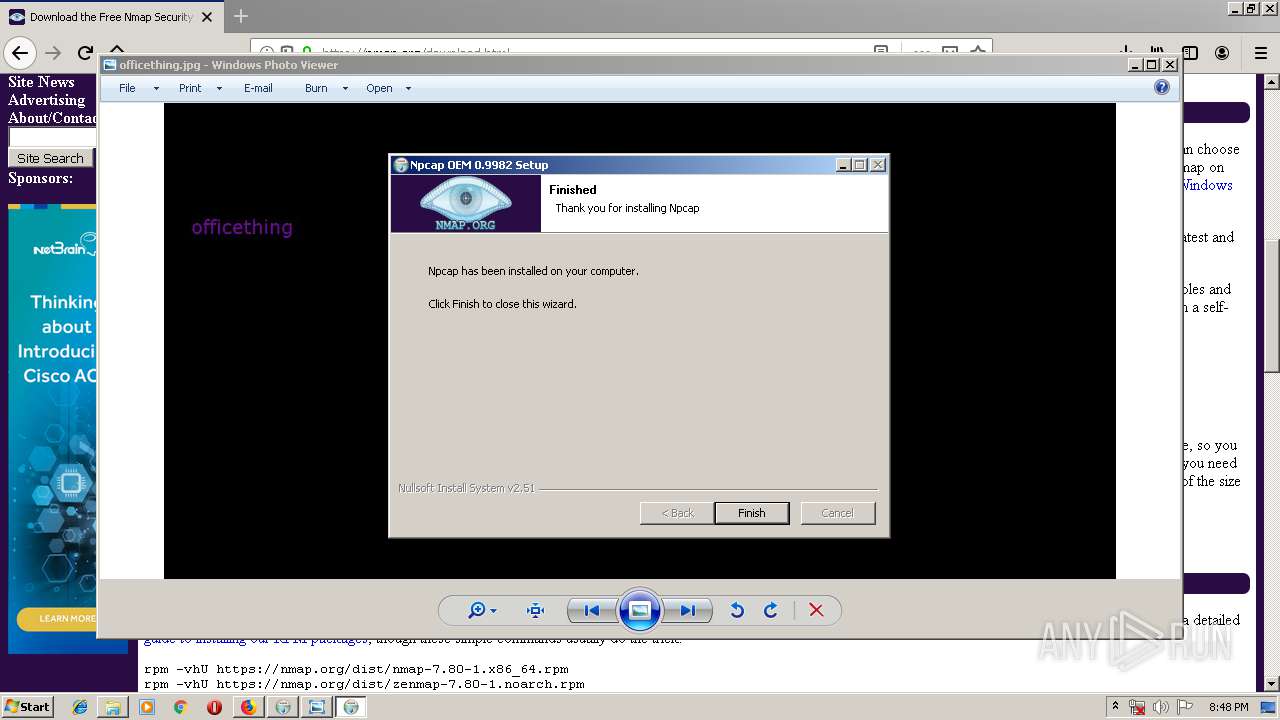
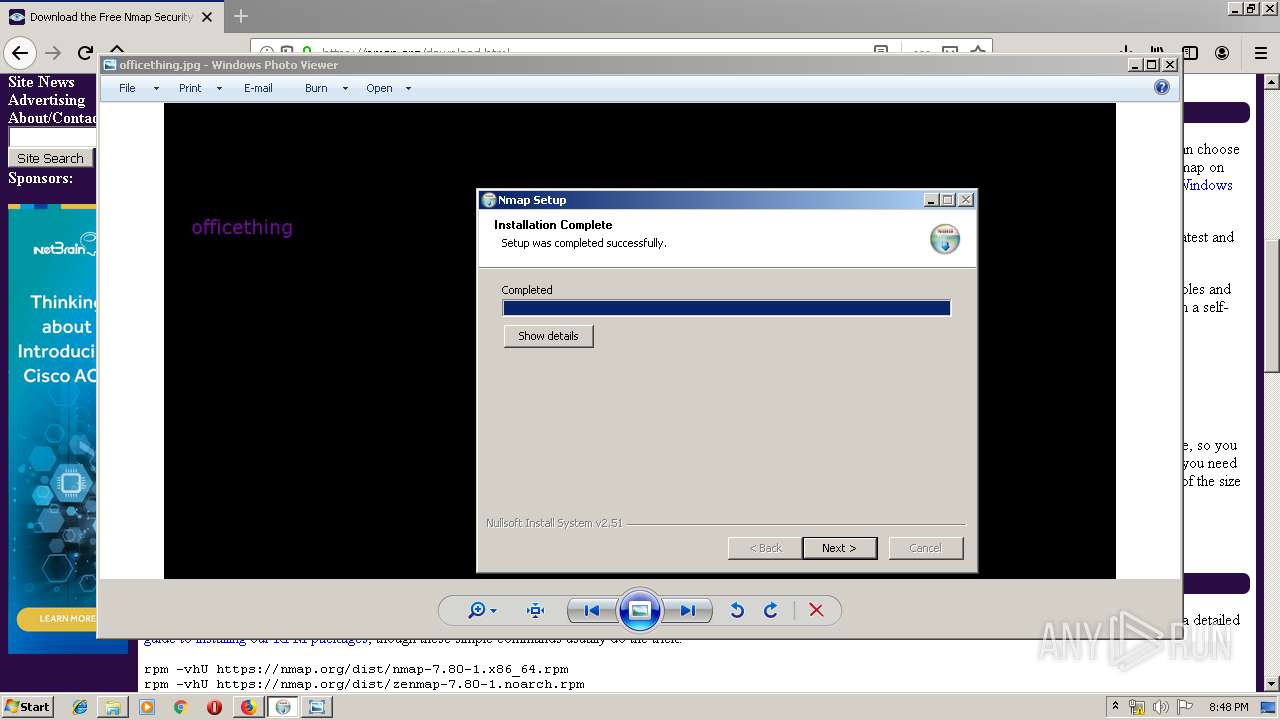
Loads dropped or rewritten executable
- npcap-0.9982-oem.exe (PID: 3724)
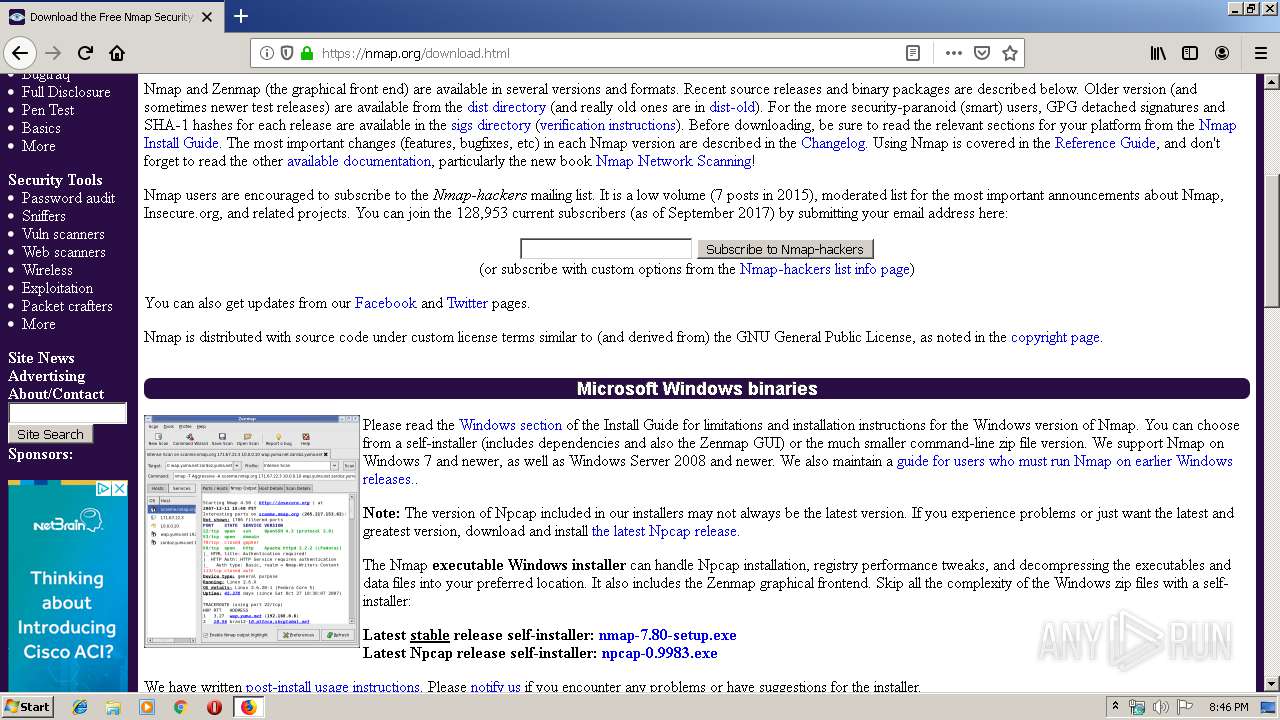
- nmap-7.80-setup.exe (PID: 3876)
- zenmap.exe (PID: 3908)
- nmap.exe (PID: 2336)
Application was dropped or rewritten from another process
- npcap-0.9982-oem.exe (PID: 3724)
- nmap-7.80-setup.exe (PID: 3240)
- nmap-7.80-setup.exe (PID: 3876)
- NPFInstall.exe (PID: 2204)
- NPFInstall.exe (PID: 3064)
- nsF91A.tmp (PID: 3940)
- nsF6E6.tmp (PID: 2900)
- nsF83F.tmp (PID: 2100)
- nsFB4F.tmp (PID: 2508)
- NPFInstall.exe (PID: 3380)
- nsFA73.tmp (PID: 4028)
- ns43B3.tmp (PID: 3120)
- ns449E.tmp (PID: 3296)
- NPFInstall.exe (PID: 3636)
- NPFInstall.exe (PID: 2900)
- ns676A.tmp (PID: 3352)
- zenmap.exe (PID: 3908)
- nmap.exe (PID: 2336)
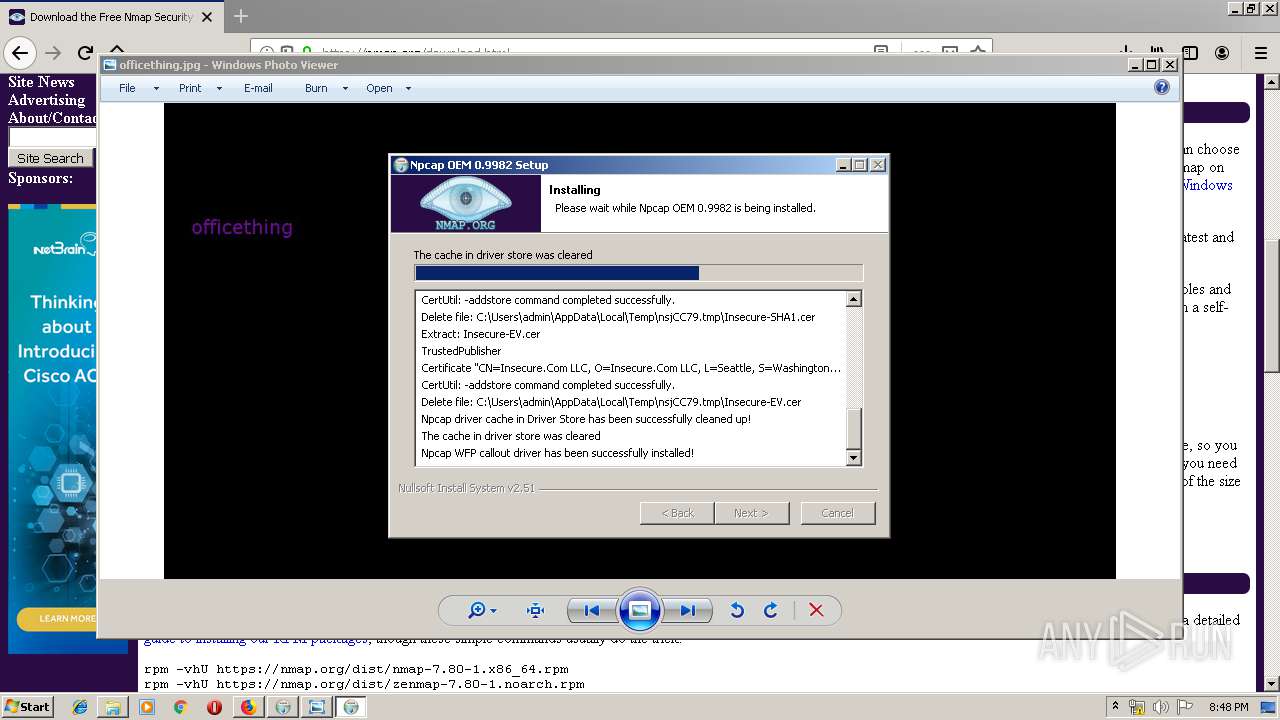
Changes settings of System certificates
- certutil.exe (PID: 3548)
- certutil.exe (PID: 2300)
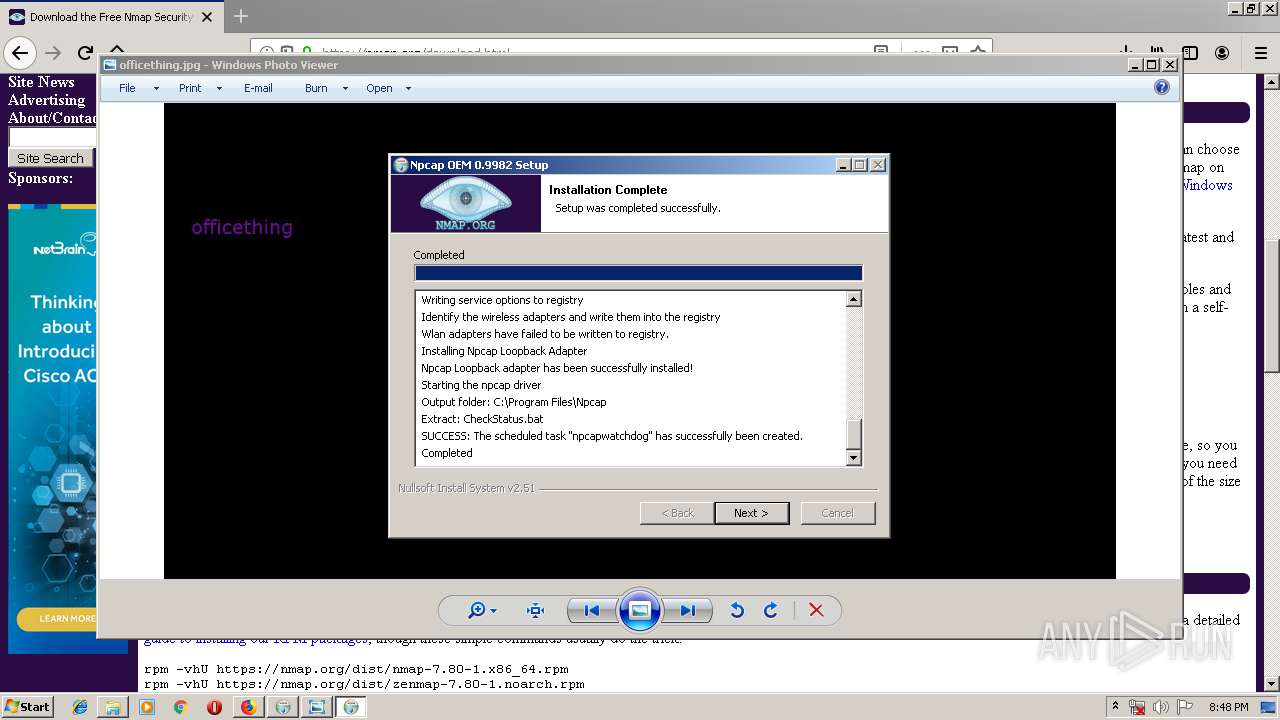
Uses Task Scheduler to run other applications
- ns676A.tmp (PID: 3352)
Loads the Task Scheduler COM API
- SCHTASKS.EXE (PID: 1856)
SUSPICIOUS
Executable content was dropped or overwritten
- npcap-0.9982-oem.exe (PID: 3724)
- firefox.exe (PID: 3664)
- nmap-7.80-setup.exe (PID: 3876)
- NPFInstall.exe (PID: 3380)
- DrvInst.exe (PID: 3992)
- DrvInst.exe (PID: 1736)
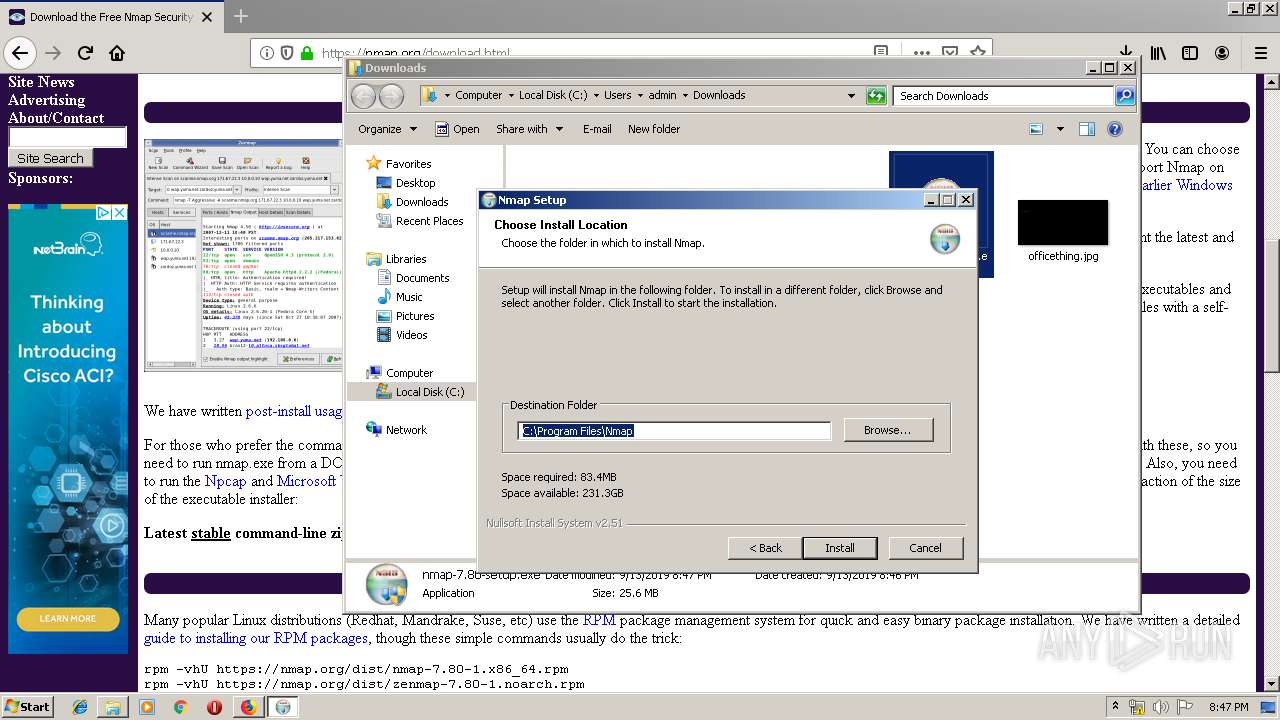
Creates files in the program directory
- npcap-0.9982-oem.exe (PID: 3724)
- nmap-7.80-setup.exe (PID: 3876)
- NPFInstall.exe (PID: 2204)
- NPFInstall.exe (PID: 2900)
Creates a software uninstall entry
- nmap-7.80-setup.exe (PID: 3876)
- npcap-0.9982-oem.exe (PID: 3724)
Executed via COM
- DllHost.exe (PID: 996)
- DrvInst.exe (PID: 1736)
- DrvInst.exe (PID: 3992)
- DrvInst.exe (PID: 1464)
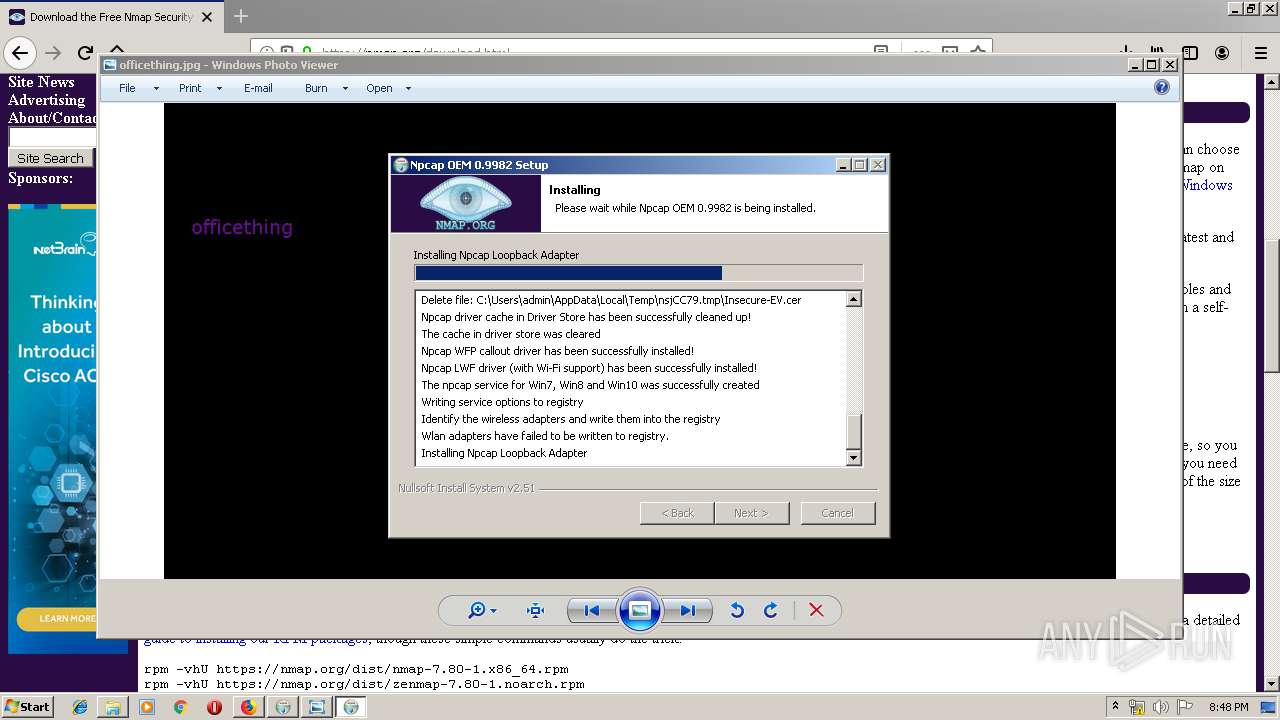
Creates files in the Windows directory
- npcap-0.9982-oem.exe (PID: 3724)
- certutil.exe (PID: 2300)
- certutil.exe (PID: 3548)
- pnputil.exe (PID: 3572)
- NPFInstall.exe (PID: 3380)
- DrvInst.exe (PID: 3992)
- DrvInst.exe (PID: 1736)
Starts application with an unusual extension
- npcap-0.9982-oem.exe (PID: 3724)
Removes files from Windows directory
- certutil.exe (PID: 3548)
- certutil.exe (PID: 2300)
- DrvInst.exe (PID: 1736)
- DrvInst.exe (PID: 3992)
- NPFInstall.exe (PID: 3380)
Creates files in the driver directory
- DrvInst.exe (PID: 1736)
- NPFInstall.exe (PID: 3380)
- DrvInst.exe (PID: 3992)
Executed as Windows Service
- vssvc.exe (PID: 3608)
Creates or modifies windows services
- npcap-0.9982-oem.exe (PID: 3724)
- DrvInst.exe (PID: 3992)
Creates files in the user directory
- nmap-7.80-setup.exe (PID: 3876)
Loads Python modules
- zenmap.exe (PID: 3908)
INFO
Application launched itself
- firefox.exe (PID: 2772)
- firefox.exe (PID: 3664)
Reads Internet Cache Settings
- firefox.exe (PID: 3664)
Reads CPU info
- firefox.exe (PID: 3664)
Reads settings of System Certificates
- firefox.exe (PID: 3664)
- NPFInstall.exe (PID: 3380)
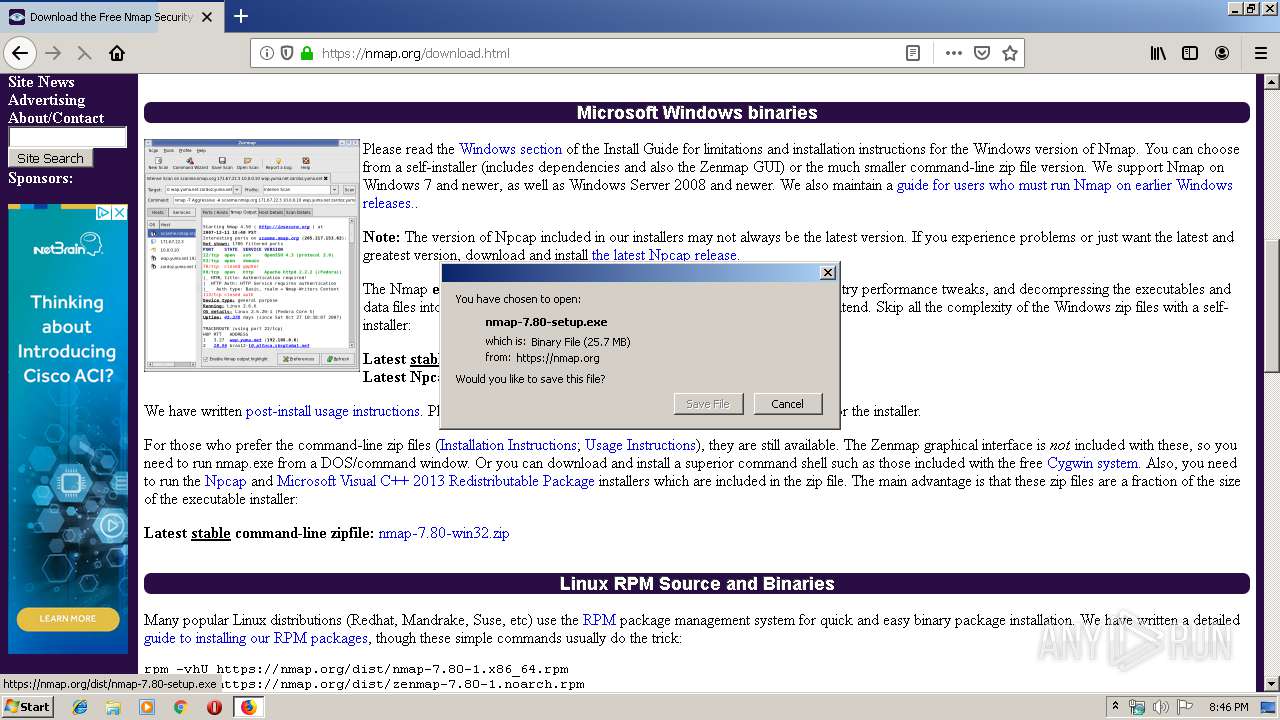
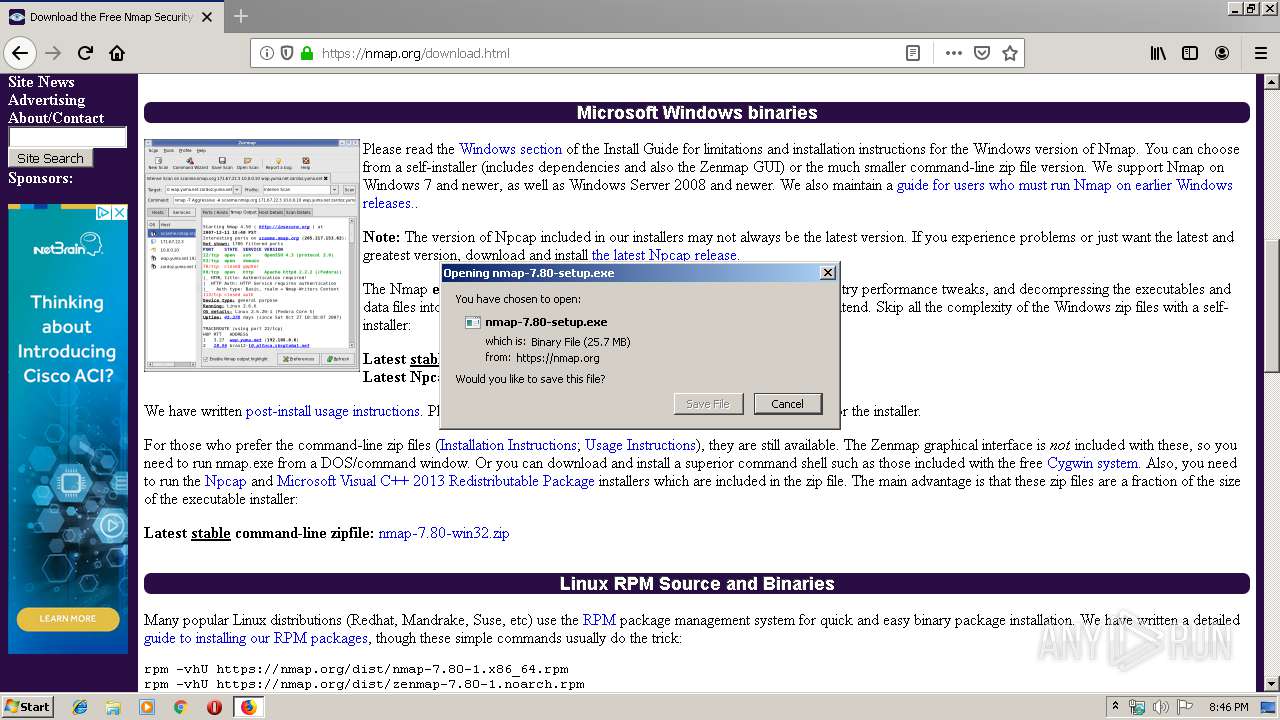
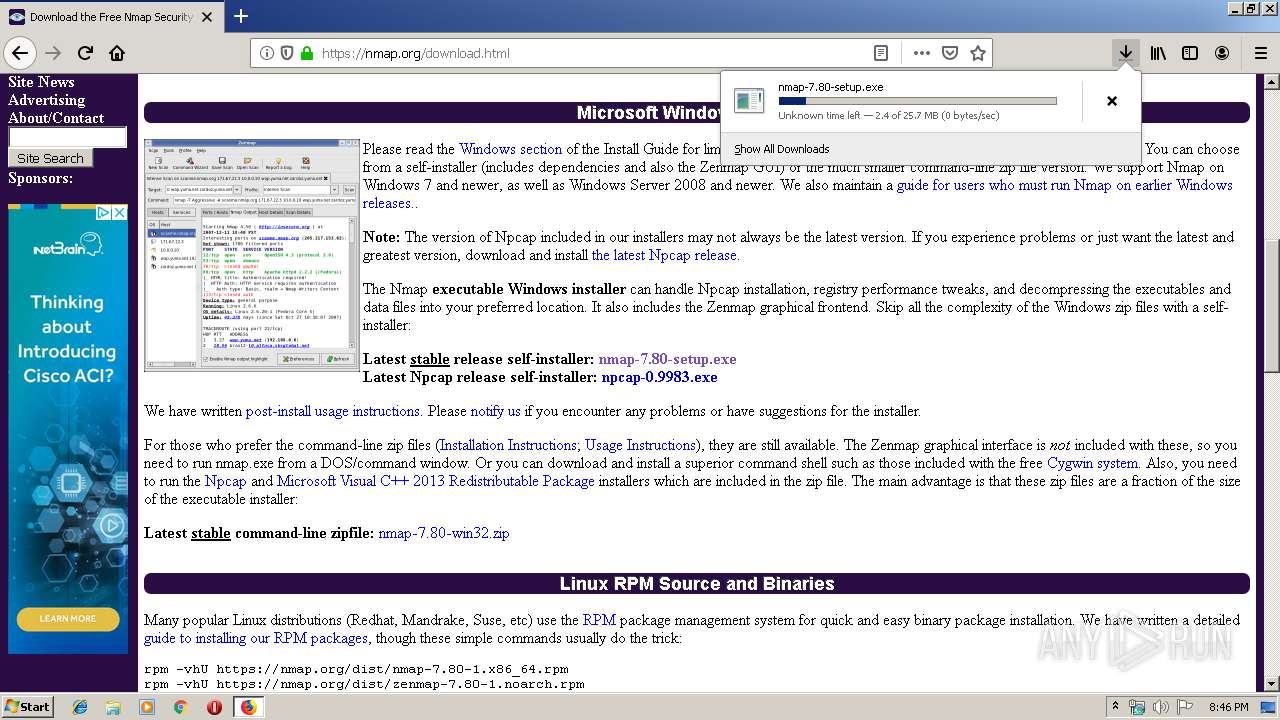
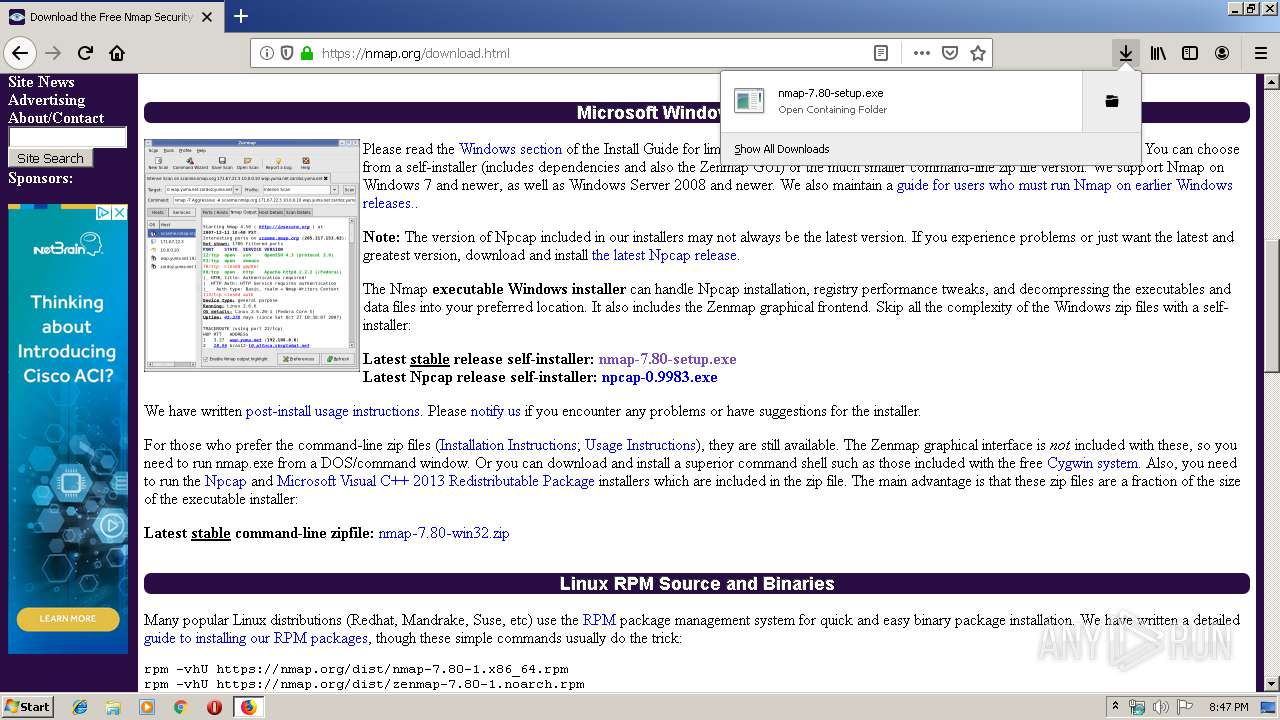
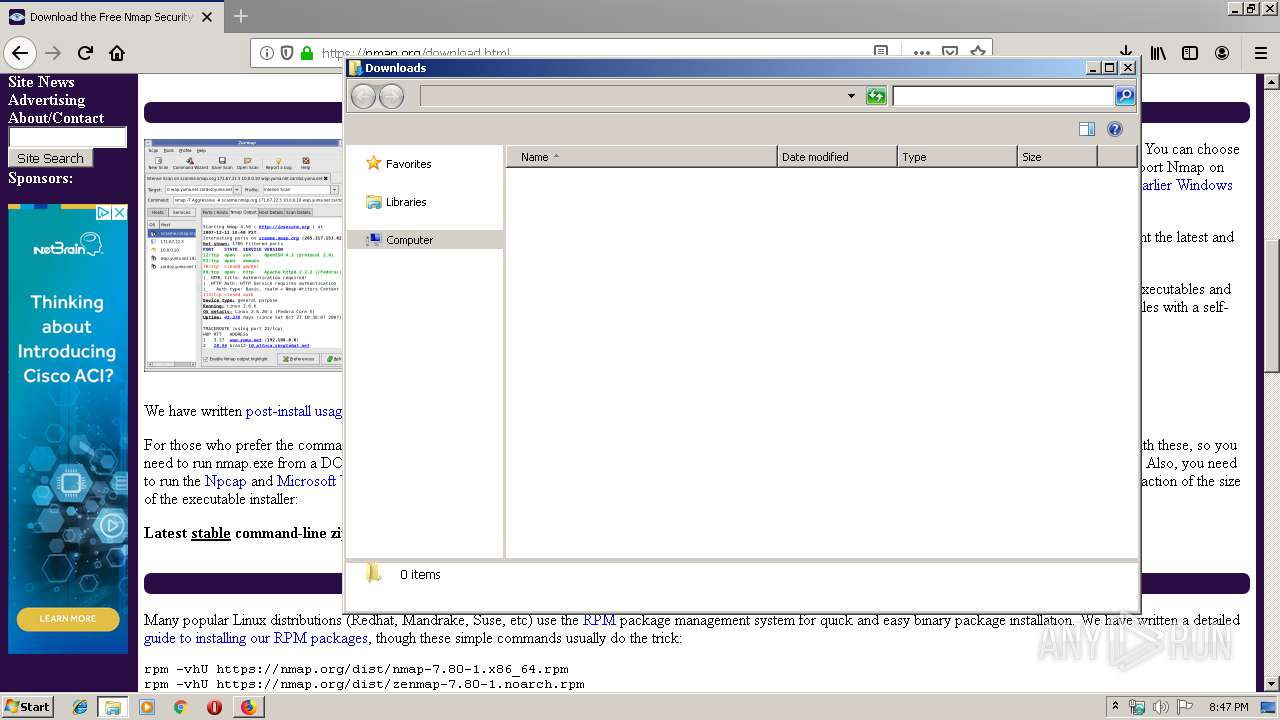
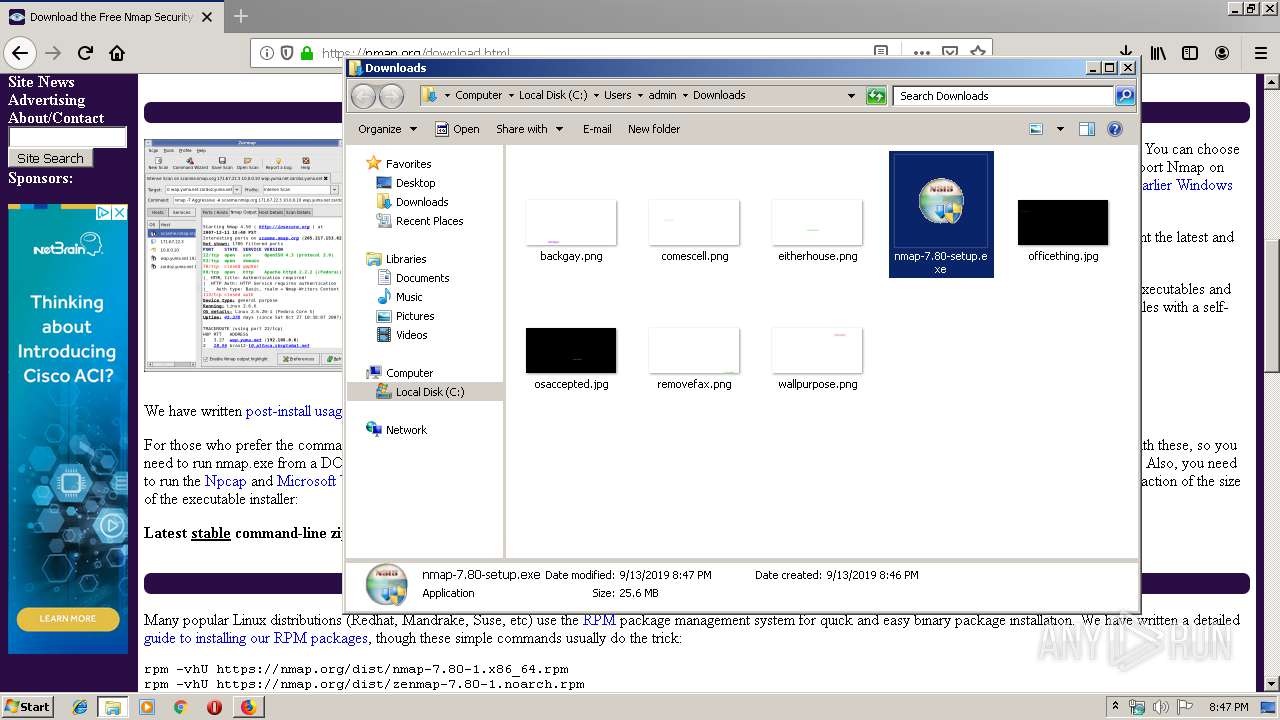
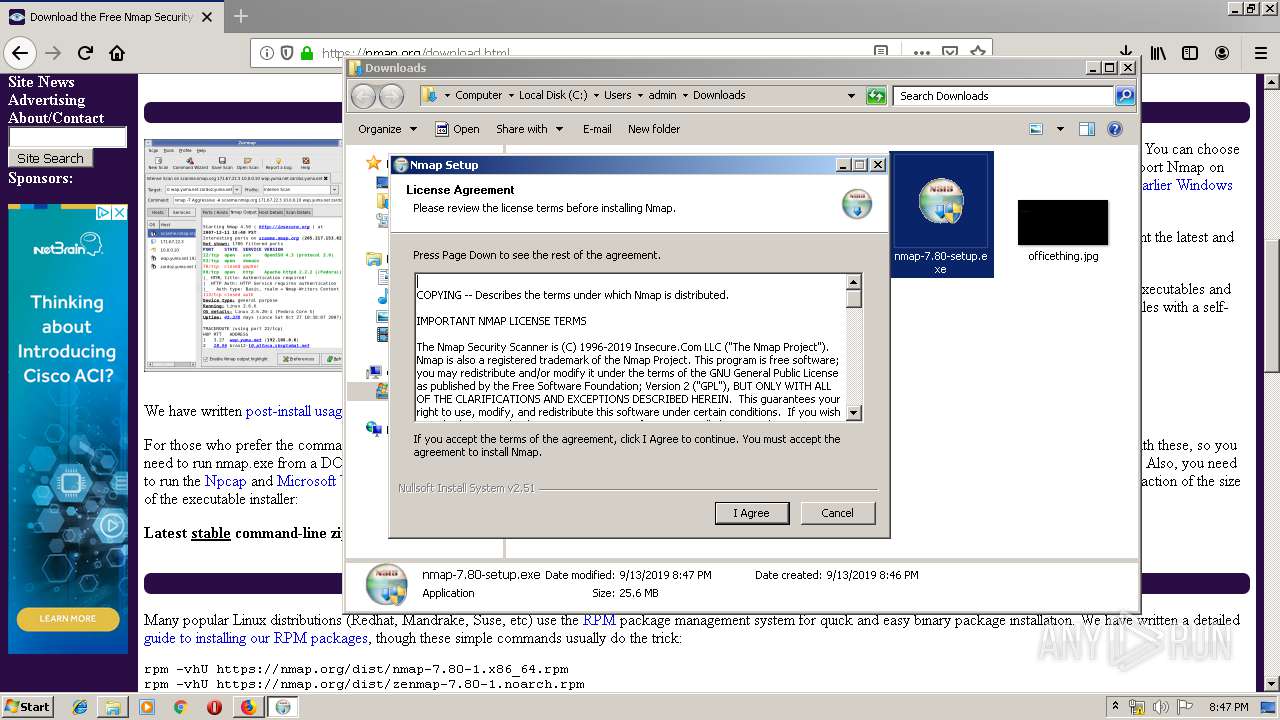
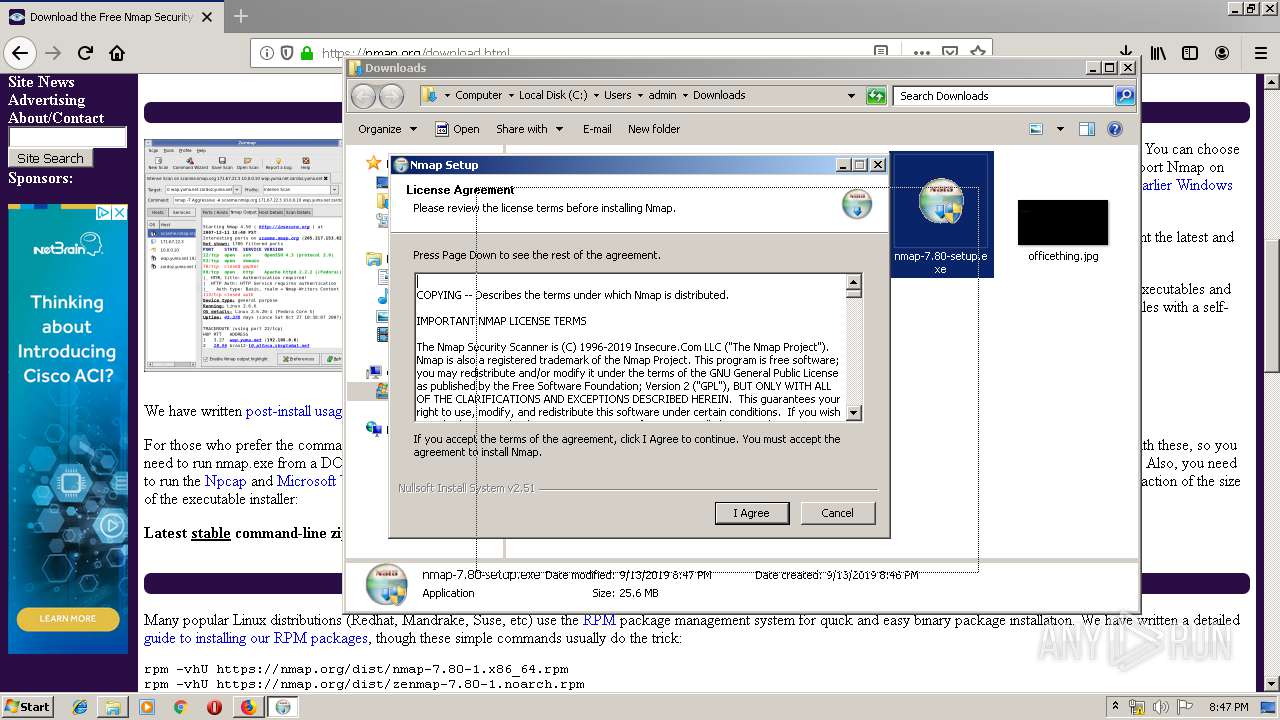
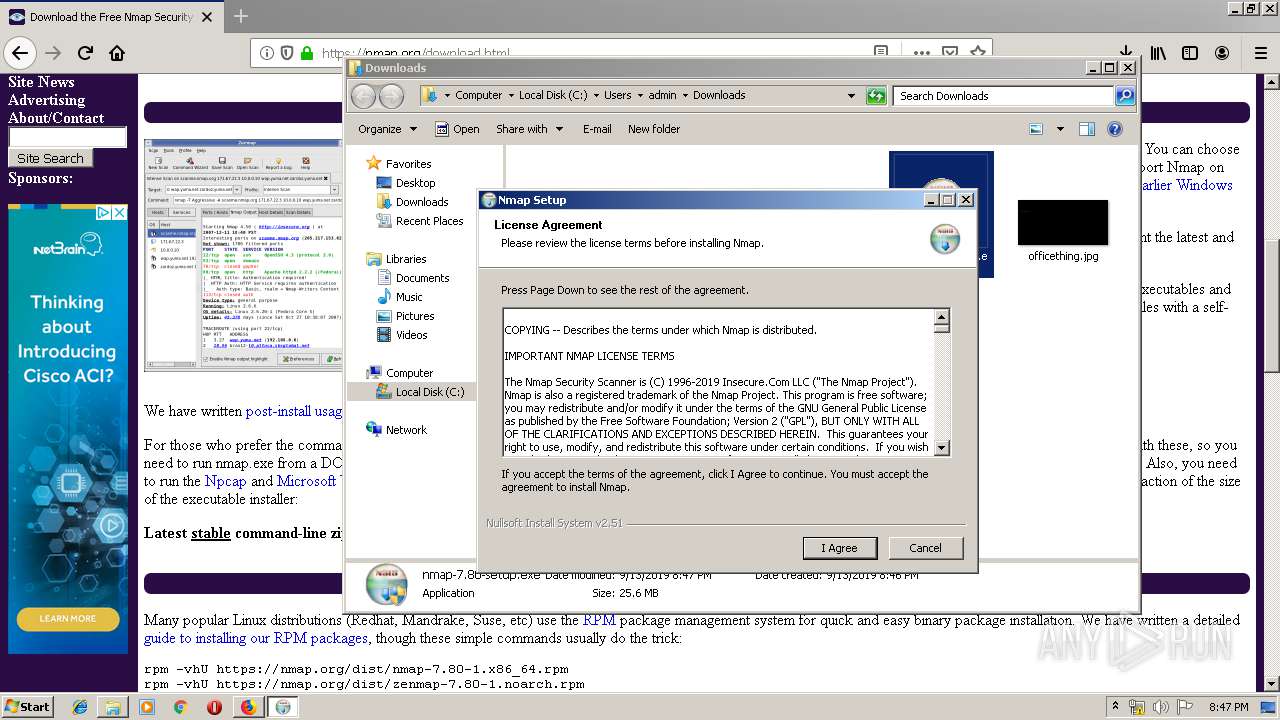
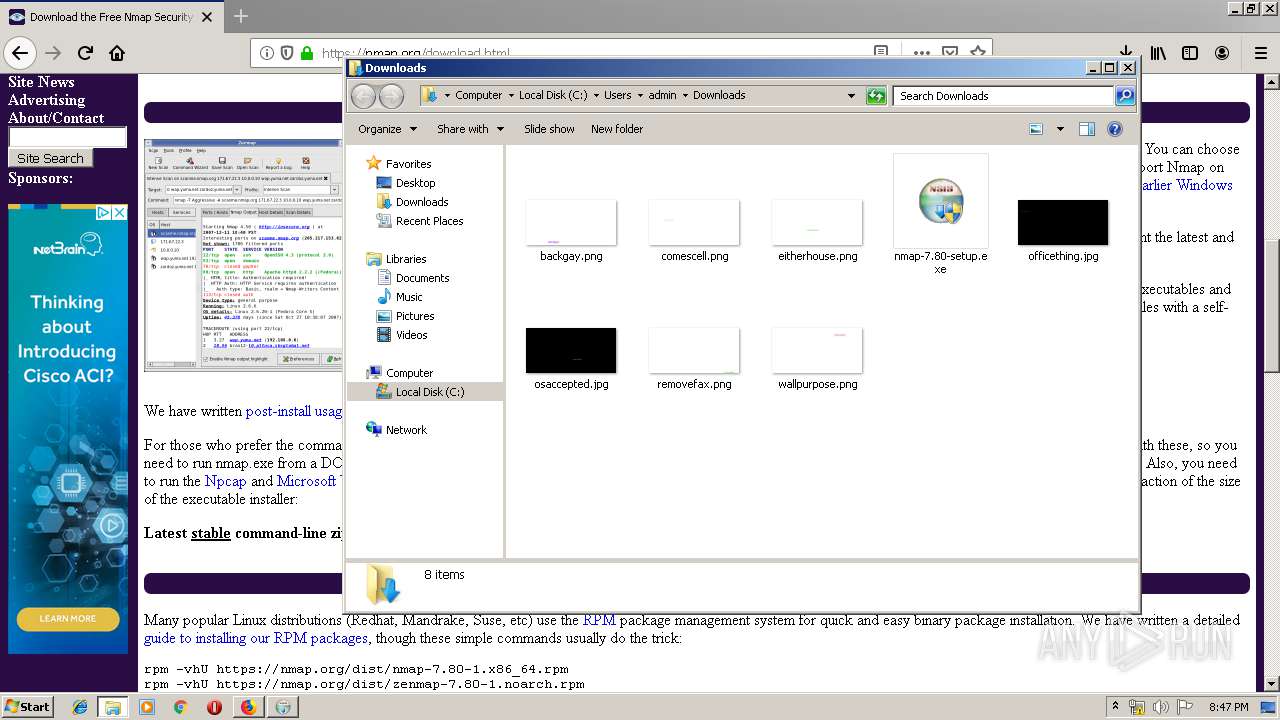
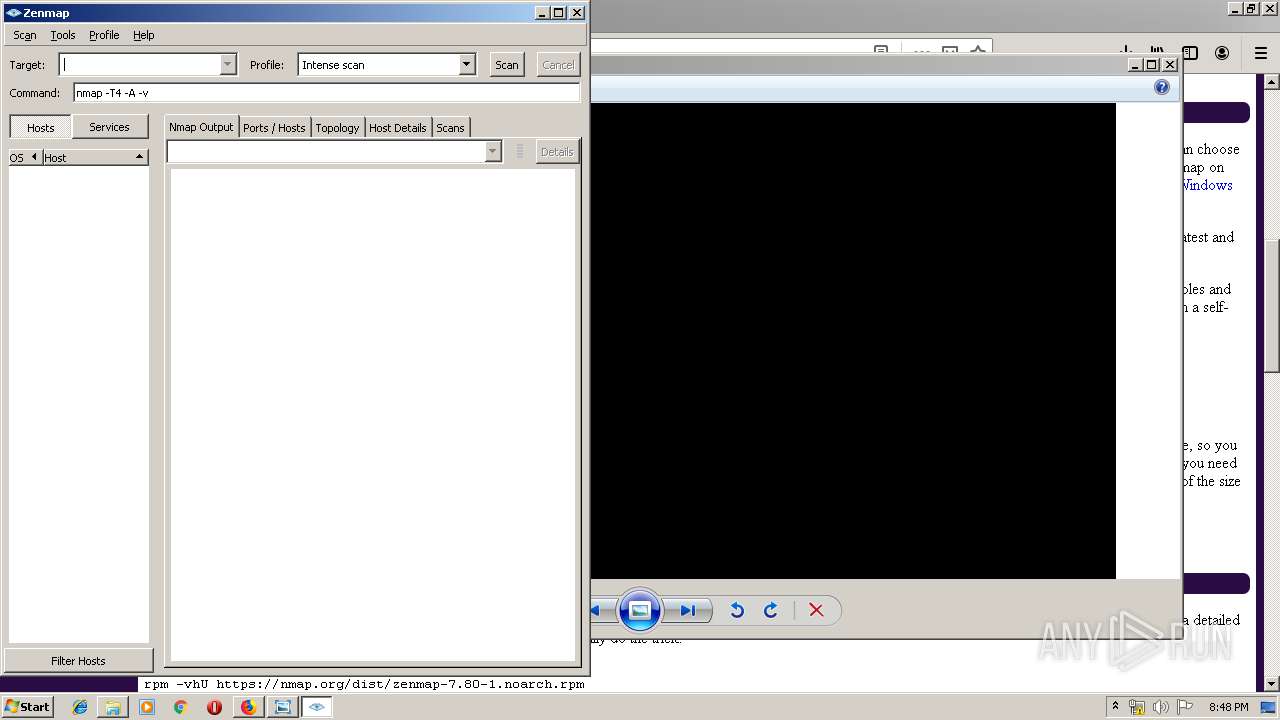
Manual execution by user
- nmap-7.80-setup.exe (PID: 3876)
- nmap-7.80-setup.exe (PID: 3240)
- zenmap.exe (PID: 3908)
Creates files in the user directory
- firefox.exe (PID: 3664)
Dropped object may contain Bitcoin addresses
- nmap-7.80-setup.exe (PID: 3876)
Searches for installed software
- DrvInst.exe (PID: 1736)
Low-level read access rights to disk partition
- vssvc.exe (PID: 3608)
Reads the hosts file
- nmap.exe (PID: 2336)
Changes settings of System certificates
- DrvInst.exe (PID: 1736)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
86
Monitored processes
35
Malicious processes
8
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 996 | C:\Windows\system32\DllHost.exe /Processid:{76D0CB12-7604-4048-B83C-1005C7DDC503} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1464 | DrvInst.exe "1" "200" "STORAGE\VolumeSnapshot\HarddiskVolumeSnapshot22" "" "" "695c3f483" "00000000" "000005E4" "000005E0" | C:\Windows\system32\DrvInst.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1736 | DrvInst.exe "4" "0" "C:\Users\admin\AppData\Local\Temp\{64278112-a73b-2e13-fb4e-9a736849dc3d}\NPCAP.inf" "0" "605306be3" "000003E8" "WinSta0\Default" "00000064" "208" "C:\Program Files\Npcap" | C:\Windows\system32\DrvInst.exe | svchost.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1856 | SCHTASKS.EXE /Create /F /RU SYSTEM /SC ONSTART /TN npcapwatchdog /TR "'C:\Program Files\Npcap\CheckStatus.bat'" /NP | C:\Windows\system32\SCHTASKS.EXE | — | ns676A.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2100 | "C:\Users\admin\AppData\Local\Temp\nsjCC79.tmp\nsF83F.tmp" certutil -addstore -f "TrustedPublisher" "C:\Users\admin\AppData\Local\Temp\nsjCC79.tmp\Insecure-EV.cer" | C:\Users\admin\AppData\Local\Temp\nsjCC79.tmp\nsF83F.tmp | — | npcap-0.9982-oem.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2204 | "C:\Program Files\Npcap\NPFInstall.exe" -n -c | C:\Program Files\Npcap\NPFInstall.exe | — | nsF91A.tmp | |||||||||||
User: admin Company: Insecure.Com LLC. Integrity Level: HIGH Description: A LWF & WFP driver installation tool Exit code: 0 Version: 0.9982 Modules
| |||||||||||||||
| 2292 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3664.13.976912827\1298184220" -childID 2 -isForBrowser -prefsHandle 2876 -prefMapHandle 2880 -prefsLen 5996 -prefMapSize 191824 -parentBuildID 20190717172542 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 3664 "\\.\pipe\gecko-crash-server-pipe.3664" 2888 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 2300 | certutil -addstore -f "TrustedPublisher" "C:\Users\admin\AppData\Local\Temp\nsjCC79.tmp\Insecure-EV.cer" | C:\Windows\system32\certutil.exe | — | nsF83F.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: CertUtil.exe Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
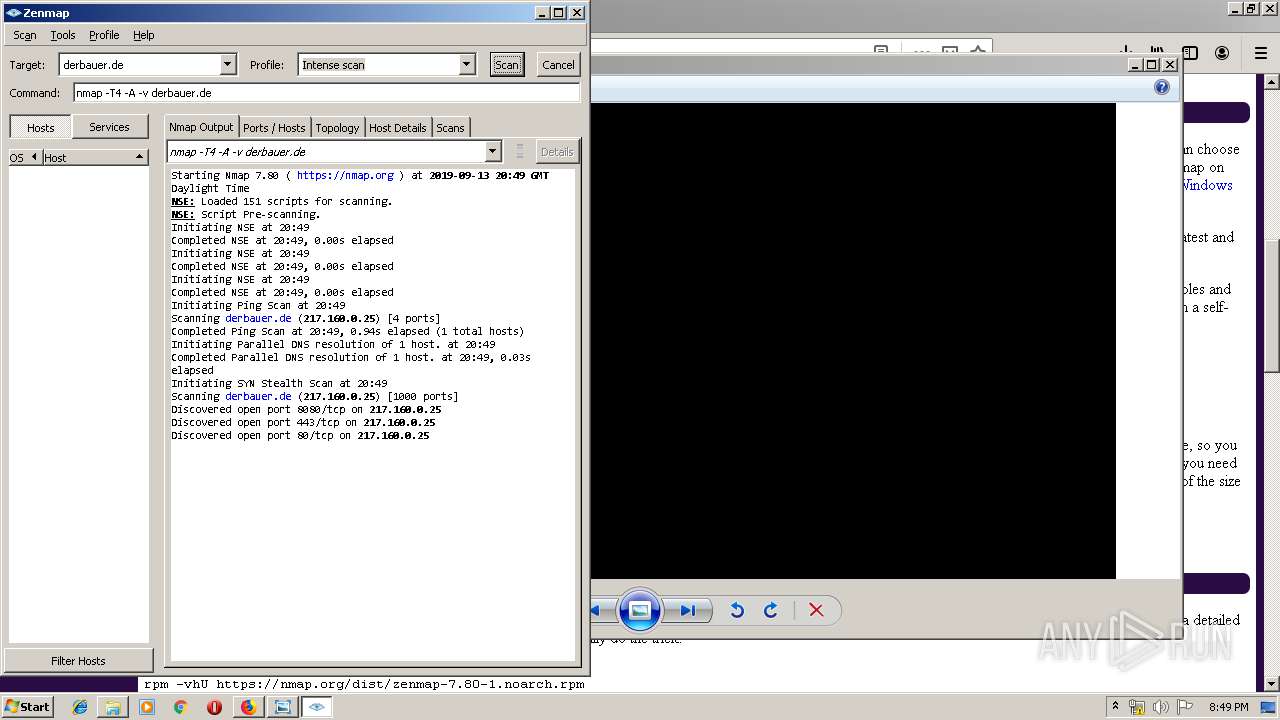
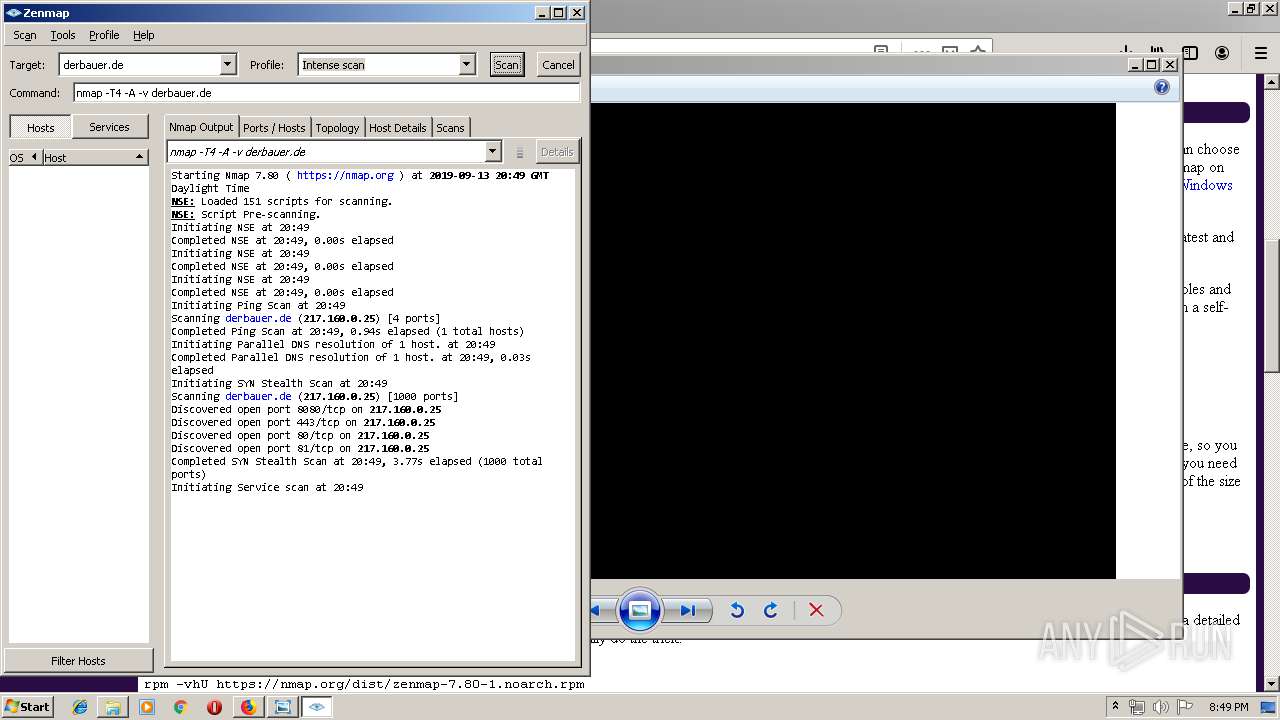
| 2336 | nmap -T4 -A -v -oX c:\users\admin\appdata\local\temp\zenmap-i31zzj.xml derbauer.de | C:\Program Files\Nmap\nmap.exe | zenmap.exe | ||||||||||||
User: admin Company: Insecure.Org Integrity Level: MEDIUM Description: Nmap Exit code: 0 Version: 7.80 Modules
| |||||||||||||||
| 2508 | "C:\Users\admin\AppData\Local\Temp\nsjCC79.tmp\nsFB4F.tmp" "C:\Program Files\Npcap\NPFInstall.exe" -n -i2 | C:\Users\admin\AppData\Local\Temp\nsjCC79.tmp\nsFB4F.tmp | — | npcap-0.9982-oem.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
3 320
Read events
2 554
Write events
719
Delete events
47
Modification events
| (PID) Process: | (2772) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Launcher |
Value: 3BEB6E3601000000 | |||
| (PID) Process: | (3664) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Browser |
Value: 02BE763601000000 | |||
| (PID) Process: | (3664) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Telemetry |
Value: 1 | |||
| (PID) Process: | (3664) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3664) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000092000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3664) firefox.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\72\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3664) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3664) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3876) nmap-7.80-setup.exe | Key: | HKEY_CURRENT_USER\Software\Nmap |
| Operation: | write | Name: | |
Value: C:\Program Files\Nmap | |||
| (PID) Process: | (3876) nmap-7.80-setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Nmap |
| Operation: | write | Name: | DisplayName |
Value: Nmap 7.80 | |||
Executable files
92
Suspicious files
266
Text files
1 459
Unknown types
103
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3664 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 3664 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\cookies.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 3664 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\prefs-1.js | — | |
MD5:— | SHA256:— | |||
| 3664 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\sessionCheckpoints.json.tmp | — | |
MD5:— | SHA256:— | |||
| 3664 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\2918063365piupsah.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 3664 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\1451318868ntouromlalnodry--epcr.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 3664 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\1657114595AmcateirvtiSty.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 3664 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\search.json.mozlz4.tmp | — | |
MD5:— | SHA256:— | |||
| 3664 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\prefs.js | text | |
MD5:— | SHA256:— | |||
| 3664 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\scriptCache-child-current.bin | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
26
TCP/UDP connections
2 065
DNS requests
140
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3664 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
3664 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
3664 | firefox.exe | POST | 200 | 172.217.16.131:80 | http://ocsp.pki.goog/gts1o1 | US | der | 471 b | whitelisted |
3664 | firefox.exe | POST | 200 | 172.217.16.131:80 | http://ocsp.pki.goog/gts1o1 | US | der | 471 b | whitelisted |
3664 | firefox.exe | POST | 200 | 172.217.16.131:80 | http://ocsp.pki.goog/gts1o1 | US | der | 472 b | whitelisted |
3664 | firefox.exe | POST | 200 | 172.217.16.131:80 | http://ocsp.pki.goog/gts1o1 | US | der | 471 b | whitelisted |
3664 | firefox.exe | POST | 200 | 172.217.16.131:80 | http://ocsp.pki.goog/gts1o1 | US | der | 472 b | whitelisted |
3664 | firefox.exe | POST | 200 | 172.217.16.131:80 | http://ocsp.pki.goog/gts1o1 | US | der | 471 b | whitelisted |
3664 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
3664 | firefox.exe | POST | 200 | 172.217.16.131:80 | http://ocsp.pki.goog/gts1o1 | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3664 | firefox.exe | 172.217.22.46:80 | google.com | Google Inc. | US | whitelisted |
3664 | firefox.exe | 2.16.186.50:80 | detectportal.firefox.com | Akamai International B.V. | — | whitelisted |
3664 | firefox.exe | 52.26.8.178:443 | search.services.mozilla.com | Amazon.com, Inc. | US | unknown |
3664 | firefox.exe | 52.24.126.32:443 | push.services.mozilla.com | Amazon.com, Inc. | US | unknown |
3664 | firefox.exe | 52.43.93.252:443 | tiles.services.mozilla.com | Amazon.com, Inc. | US | unknown |
3664 | firefox.exe | 172.217.18.4:80 | www.google.com | Google Inc. | US | whitelisted |
3664 | firefox.exe | 13.224.185.215:443 | snippets.cdn.mozilla.net | — | US | unknown |
3664 | firefox.exe | 216.58.206.10:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
3664 | firefox.exe | 172.217.22.78:443 | ogs.google.com | Google Inc. | US | whitelisted |
3664 | firefox.exe | 172.217.22.3:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| malicious |
detectportal.firefox.com |
| whitelisted |
a1089.dscd.akamai.net |
| whitelisted |
search.services.mozilla.com |
| whitelisted |
search.r53-2.services.mozilla.com |
| whitelisted |
push.services.mozilla.com |
| whitelisted |
autopush.prod.mozaws.net |
| whitelisted |
tiles.services.mozilla.com |
| whitelisted |
tiles.r53-2.services.mozilla.com |
| whitelisted |
snippets.cdn.mozilla.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1060 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
1060 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
2336 | nmap.exe | Generic Protocol Command Decode | SURICATA STREAM CLOSEWAIT FIN out of window |