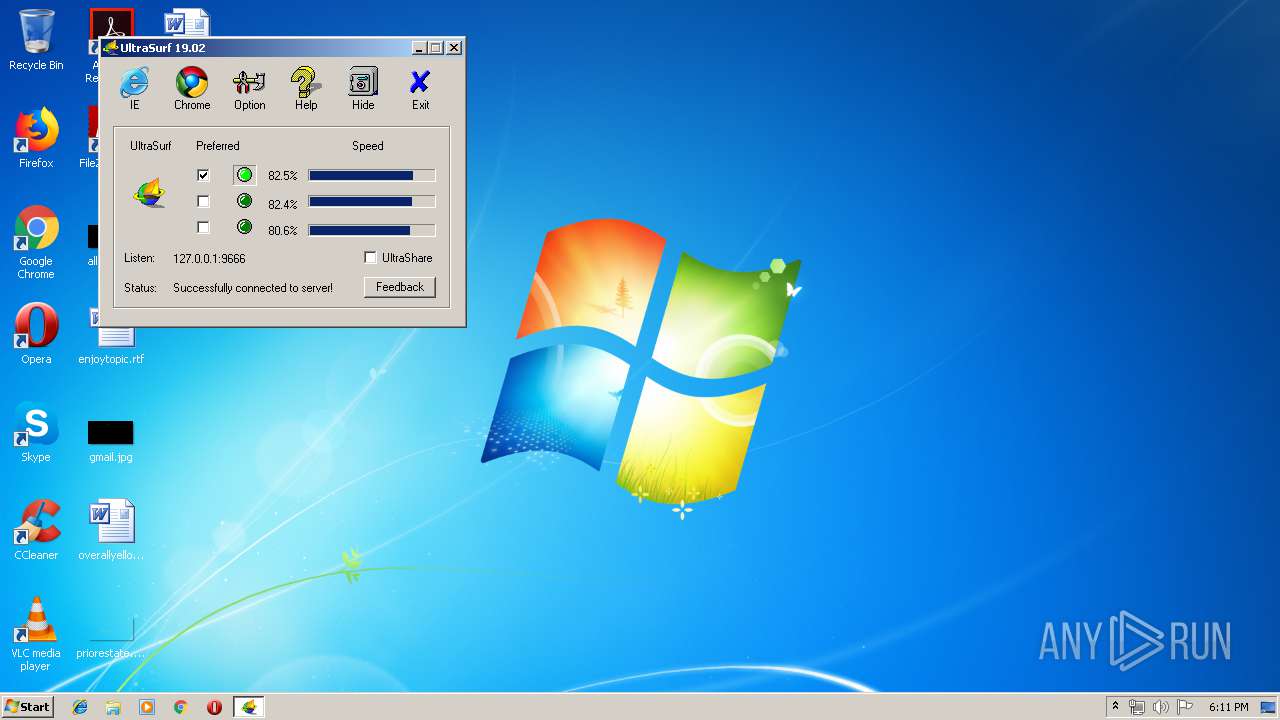
| File name: | u1902.exe |
| Full analysis: | https://app.any.run/tasks/2d89d359-1c70-4fbd-a5ff-86d88b4ed264 |
| Verdict: | Malicious activity |
| Analysis date: | May 07, 2019, 17:10:43 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed |
| MD5: | 19F6A5AE329671CEF916A2B5B976DB38 |
| SHA1: | 8563CAA0AB823C9DCFCFCFB1AE2DF7CEF63E39A0 |
| SHA256: | AA20FC72DFCFCD7EF0FF1438749AFC1F1E4EA67BBBA83D67F7D938B8909A26E1 |
| SSDEEP: | 98304:4XTU15sTq7n6z1gGuHHynaUkbEfN0R+ptpHgdqvPTFtKYaL4frN+7:Ka5sTwXrQa1gl0R6pHgd+ptXPTI7 |
MALICIOUS
Changes internet zones settings
- u1902.exe (PID: 3136)
Application was dropped or rewritten from another process
- u.exe (PID: 4020)
SUSPICIOUS
Reads Internet Cache Settings
- rundll32.exe (PID: 3784)
- rundll32.exe (PID: 3676)
- rundll32.exe (PID: 3536)
- rundll32.exe (PID: 3440)
Uses RUNDLL32.EXE to load library
- u1902.exe (PID: 3136)
Executable content was dropped or overwritten
- u1902.exe (PID: 3136)
Creates files in the user directory
- rundll32.exe (PID: 3784)
INFO
Application launched itself
- chrome.exe (PID: 2904)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (39.3) |
|---|---|---|
| .exe | | | Win32 EXE Yoda's Crypter (38.6) |
| .dll | | | Win32 Dynamic Link Library (generic) (9.5) |
| .exe | | | Win32 Executable (generic) (6.5) |
| .exe | | | Generic Win/DOS Executable (2.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:02:12 21:12:13+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 3665920 |
| InitializedDataSize: | 12288 |
| UninitializedDataSize: | 1306624 |
| EntryPoint: | 0x4bec90 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 12-Feb-2019 20:12:13 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000F0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 12-Feb-2019 20:12:13 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
UPX0 | 0x00001000 | 0x0013F000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
UPX1 | 0x00140000 | 0x0037F000 | 0x0037F000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.82006 |
.rsrc | 0x004BF000 | 0x00003000 | 0x00002400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.66596 |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.DLL |
NETAPI32.dll |
SHELL32.dll |
USER32.dll |
WININET.dll |
WINMM.dll |
WINSPOOL.DRV |
Total processes
51
Monitored processes
21
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1628 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,13579907694601049836,15219587429204675696,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=3415754664709634400 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3415754664709634400 --renderer-client-id=11 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4148 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2300 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,13579907694601049836,15219587429204675696,131072 --enable-features=PasswordImport --service-pipe-token=8313124389089827808 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8313124389089827808 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1988 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2444 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=960,13579907694601049836,15219587429204675696,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=15162234041385866255 --mojo-platform-channel-handle=3852 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2484 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=960,13579907694601049836,15219587429204675696,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAACAAwAAAQAAAAAAAAAAAGAAAAAAAAEAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=5953970733802551730 --mojo-platform-channel-handle=3900 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2616 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,13579907694601049836,15219587429204675696,131072 --enable-features=PasswordImport --service-pipe-token=2611056553598099488 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2611056553598099488 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2032 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2624 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2908 --on-initialized-event-handle=308 --parent-handle=312 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2780 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,13579907694601049836,15219587429204675696,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=10158150224924121128 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10158150224924121128 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3520 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2852 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=960,13579907694601049836,15219587429204675696,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=6469859909561598006 --mojo-platform-channel-handle=3868 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2904 | "C:\Program Files\Google\Chrome\Application\chrome.exe" http://ultrasurf.us/search.htm | C:\Program Files\Google\Chrome\Application\chrome.exe | u1902.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 3221225547 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2936 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=960,13579907694601049836,15219587429204675696,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=12134804636110983913 --mojo-platform-channel-handle=3748 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
Total events
308
Read events
170
Write events
134
Delete events
4
Modification events
| (PID) Process: | (3136) u1902.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\u1902_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3136) u1902.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\u1902_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3136) u1902.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\u1902_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3136) u1902.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\u1902_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3136) u1902.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\u1902_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (3136) u1902.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\u1902_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (3136) u1902.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\u1902_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3136) u1902.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\u1902_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3136) u1902.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\u1902_RASMANCS |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3136) u1902.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\u1902_RASMANCS |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
Executable files
1
Suspicious files
41
Text files
101
Unknown types
12
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2904 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 2904 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 2904 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2904 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 2904 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
| 3136 | u1902.exe | C:\Users\admin\AppData\Local\Temp\utmp\~jhbrhetoi1y3e6r | binary | |
MD5:— | SHA256:— | |||
| 3136 | u1902.exe | C:\Users\admin\AppData\Local\Temp\utmp\~gfdabzjnb6s8s2z | binary | |
MD5:— | SHA256:— | |||
| 3136 | u1902.exe | C:\Users\admin\AppData\Local\Temp\utmp\~ddlszjwdv5v8m5z | binary | |
MD5:— | SHA256:— | |||
| 3784 | rundll32.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\index.dat | dat | |
MD5:— | SHA256:— | |||
| 2904 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
7
DNS requests
2
Threats
3
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4020 | u.exe | 13.35.253.36:443 | www.tsx.com | — | US | suspicious |
4020 | u.exe | 99.86.5.69:443 | dq33tynpwunh.cloudfront.net | AT&T Services, Inc. | US | unknown |
4020 | u.exe | 74.82.60.75:20613 | — | Hurricane Electric, Inc. | US | unknown |
4020 | u.exe | 74.82.63.109:443 | — | Hurricane Electric, Inc. | US | suspicious |
4020 | u.exe | 74.82.63.104:443 | — | Hurricane Electric, Inc. | US | suspicious |
4020 | u.exe | 74.82.63.112:26675 | — | Hurricane Electric, Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.tsx.com |
| whitelisted |
dq33tynpwunh.cloudfront.net |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
4020 | u.exe | Potential Corporate Privacy Violation | POLICY [PTsecurity] Possible JA3 UltraSurf Proxy Anonymizer |
4020 | u.exe | Potential Corporate Privacy Violation | POLICY [PTsecurity] Possible JA3 UltraSurf Proxy Anonymizer |
4020 | u.exe | Potential Corporate Privacy Violation | POLICY [PTsecurity] Possible JA3 UltraSurf Proxy Anonymizer |