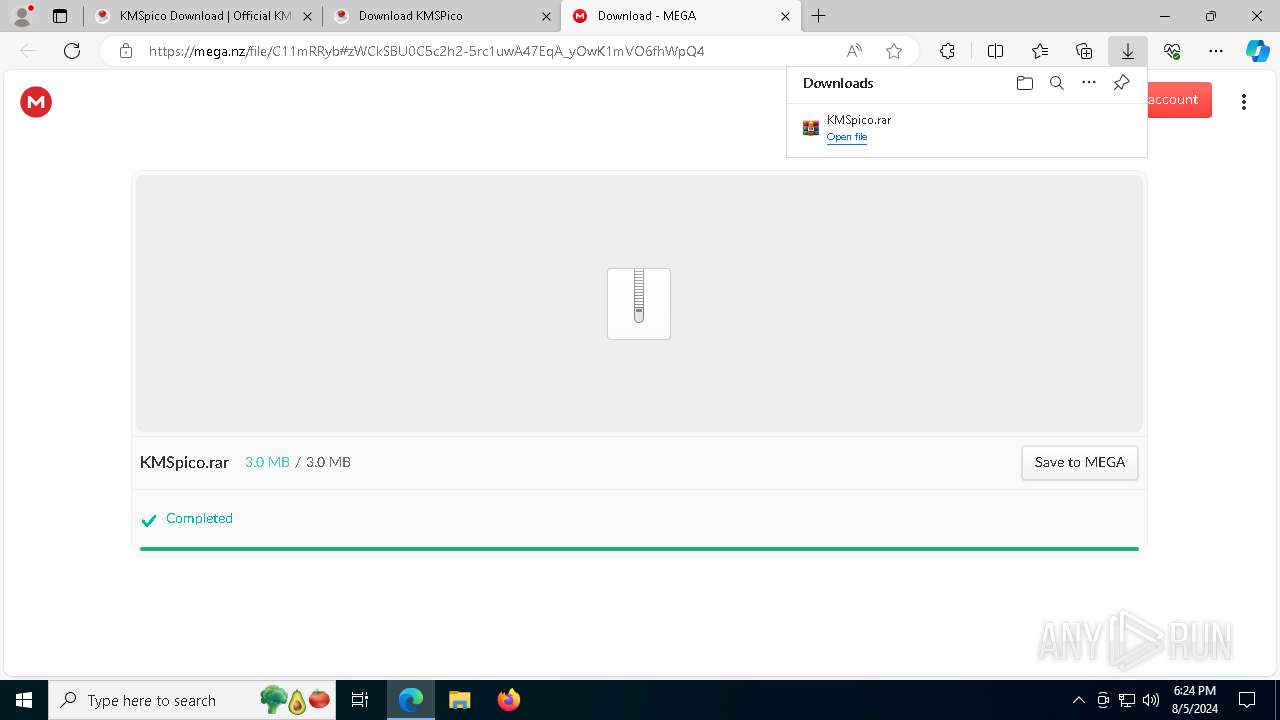
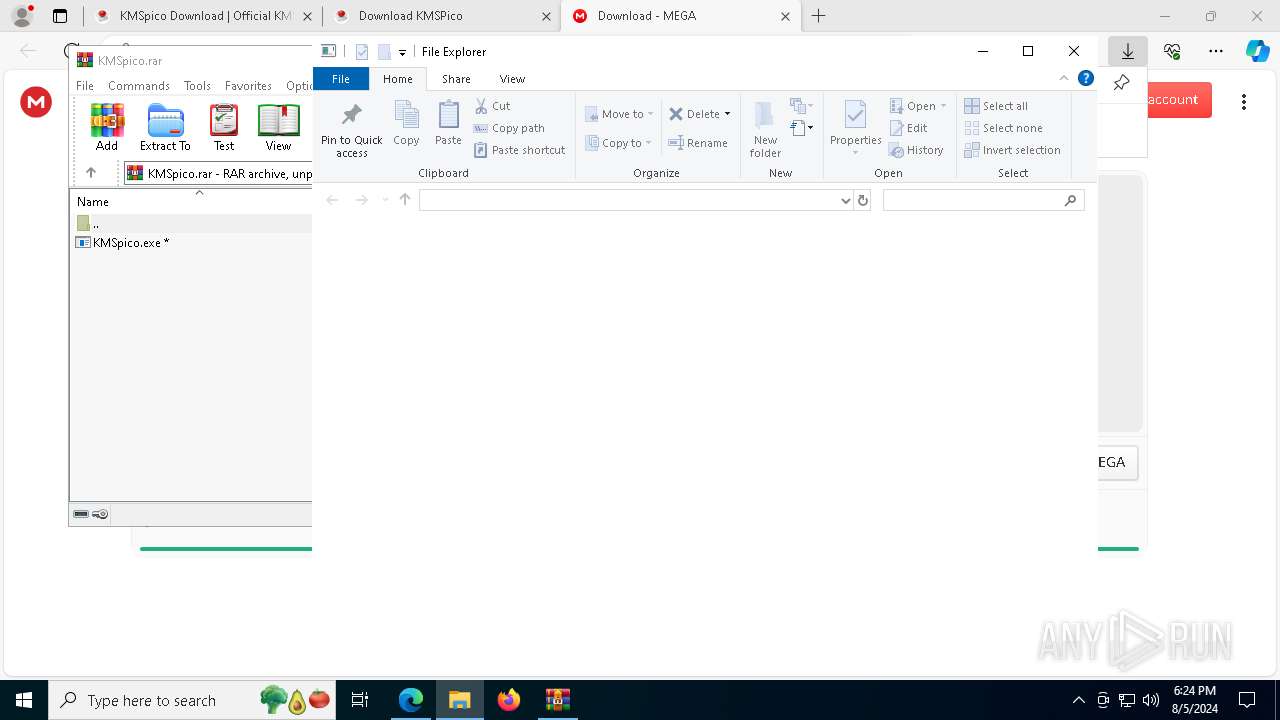
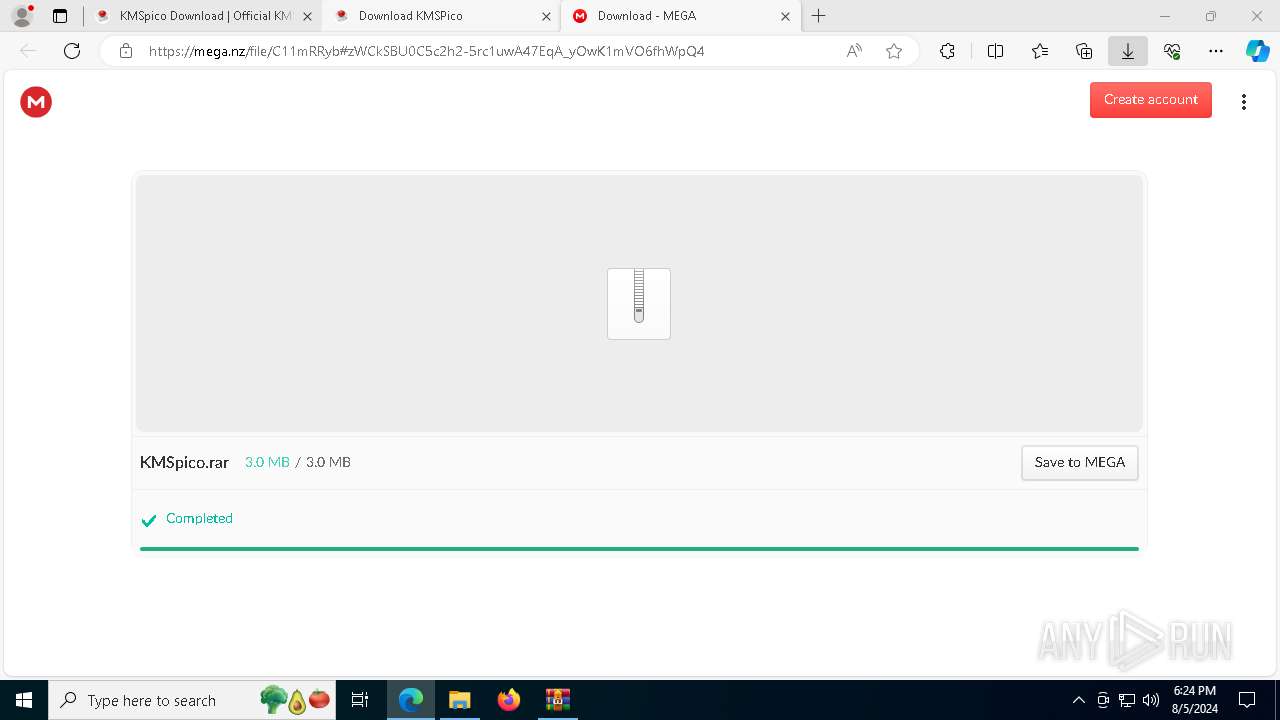
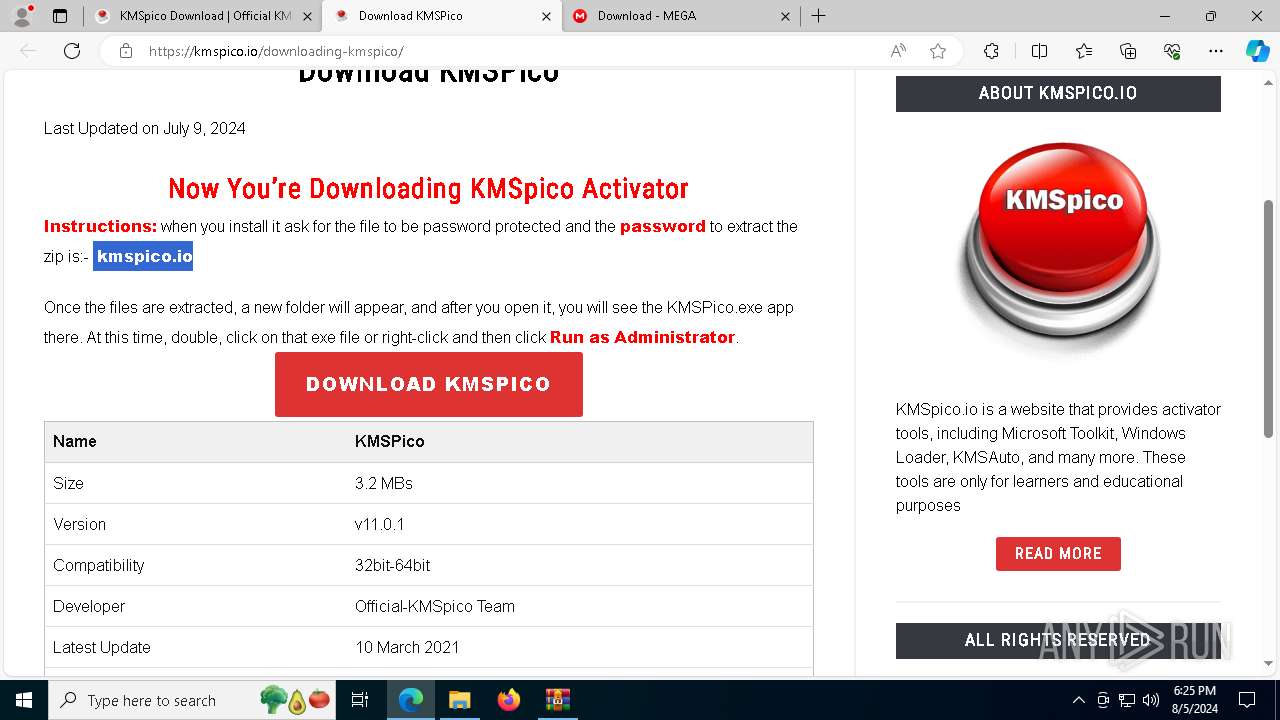
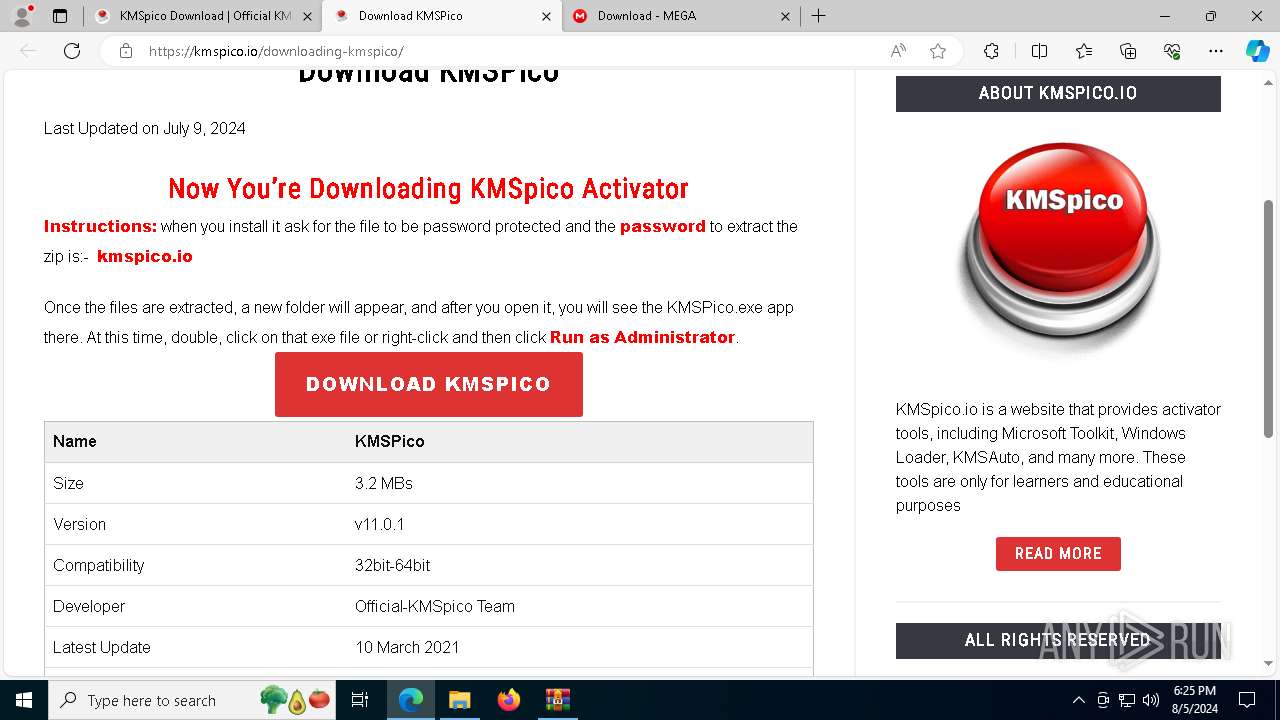
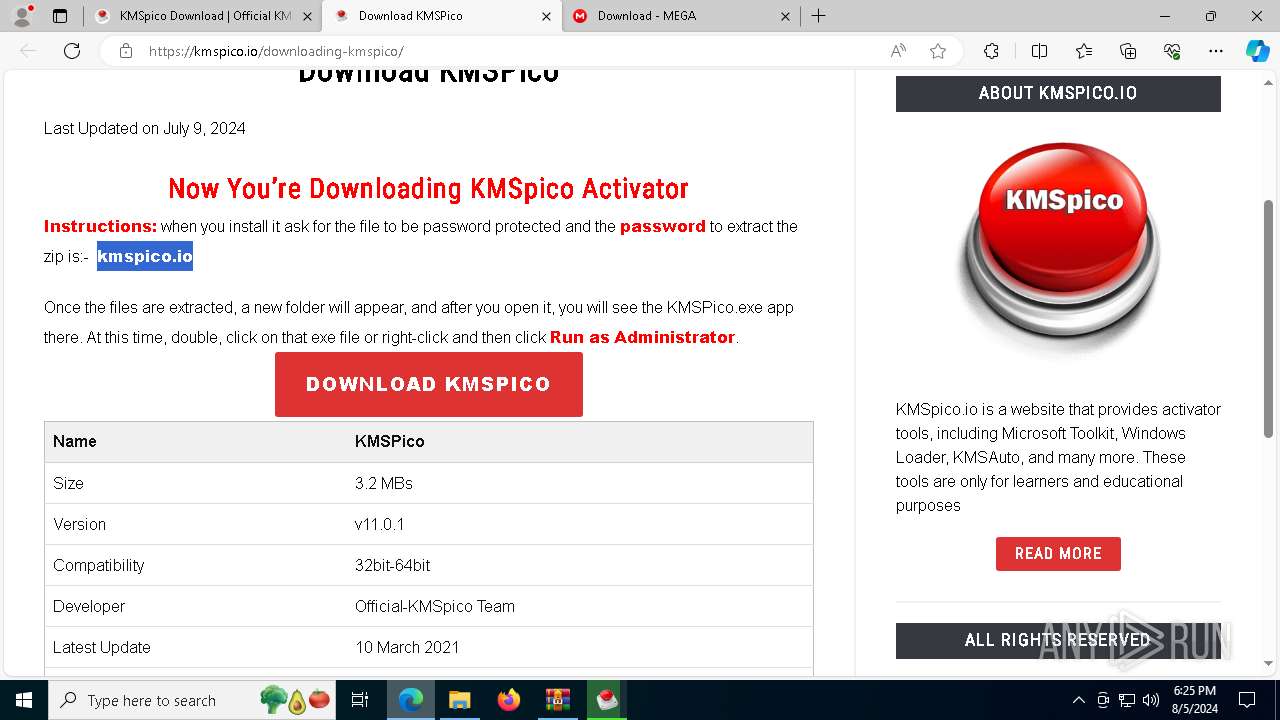
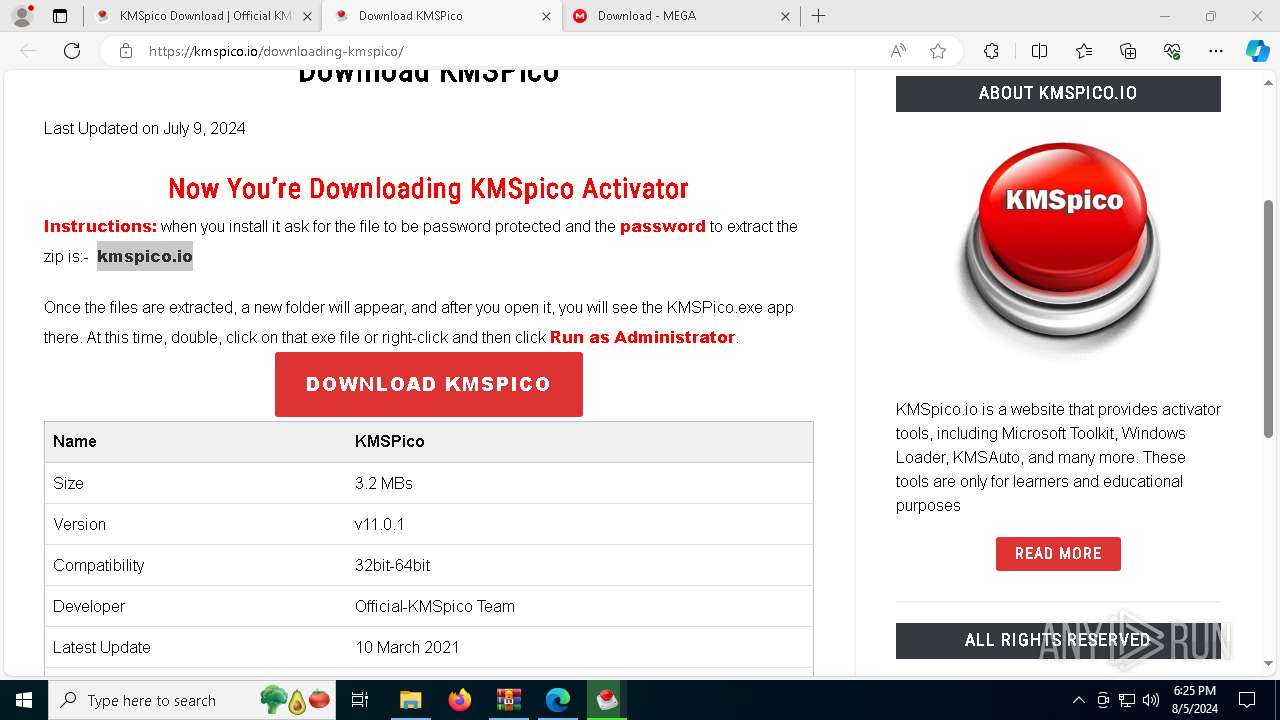
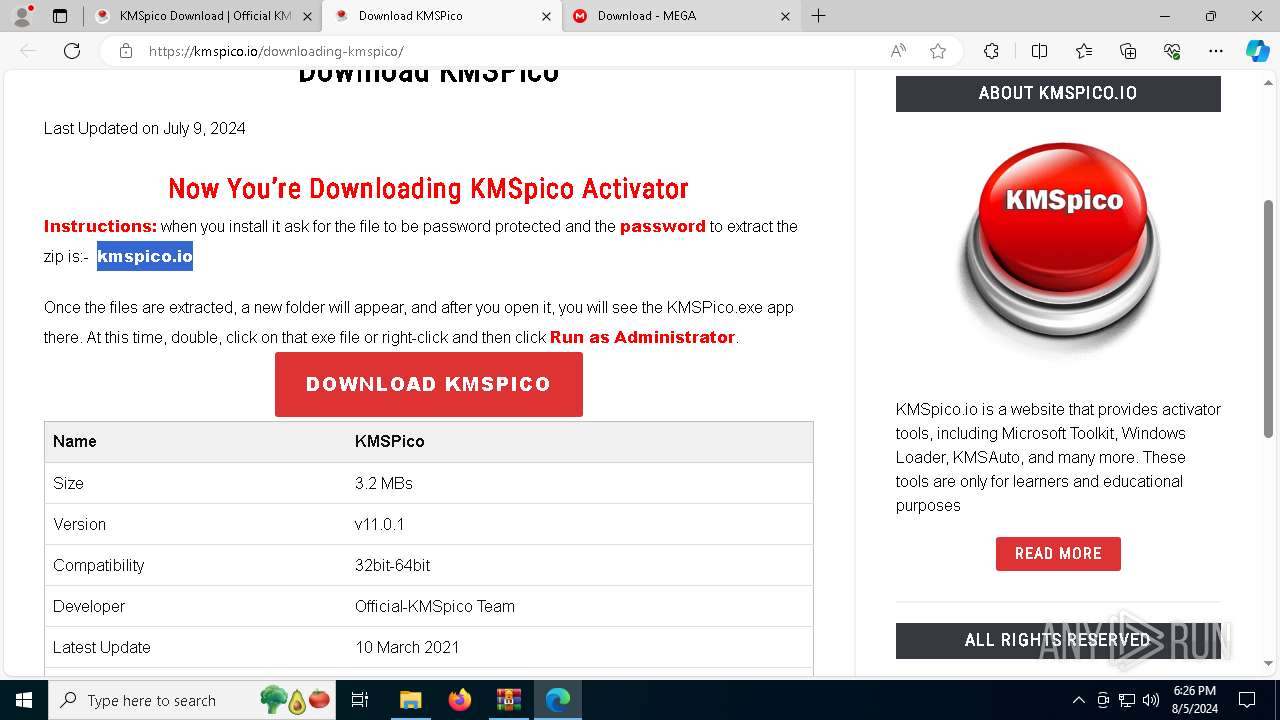
| URL: | kmspico.io |
| Full analysis: | https://app.any.run/tasks/8528cd0a-32b0-4103-bfff-6e6fa1b9b955 |
| Verdict: | Malicious activity |
| Analysis date: | August 05, 2024, 18:24:02 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MD5: | CDFA9B3709EE060A4BECE6FCCC5A9F66 |
| SHA1: | AD8ECBEB0C58236D94E85BE6FA7644647D2A87BD |
| SHA256: | AA0CFEA953F3EE084C0F287C2D06EF13DA9AC1CDF98A6F3493319852D95376DC |
| SSDEEP: | 3:/G0n:x |
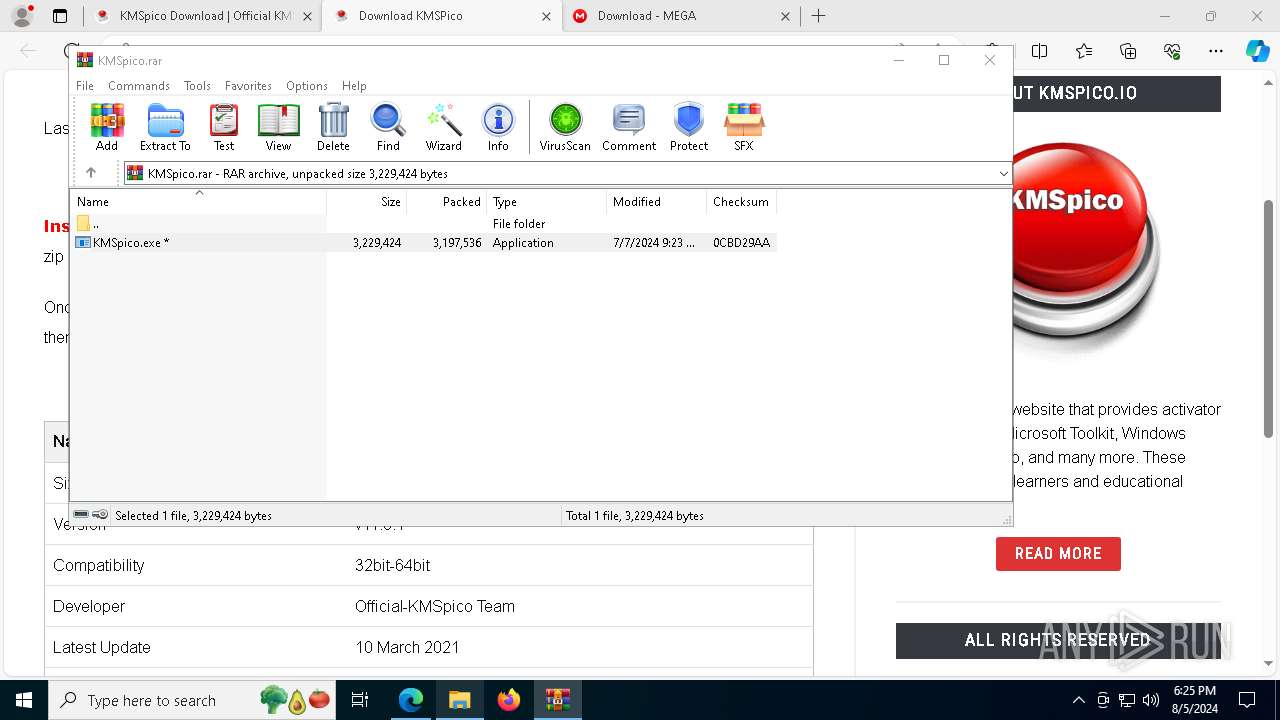
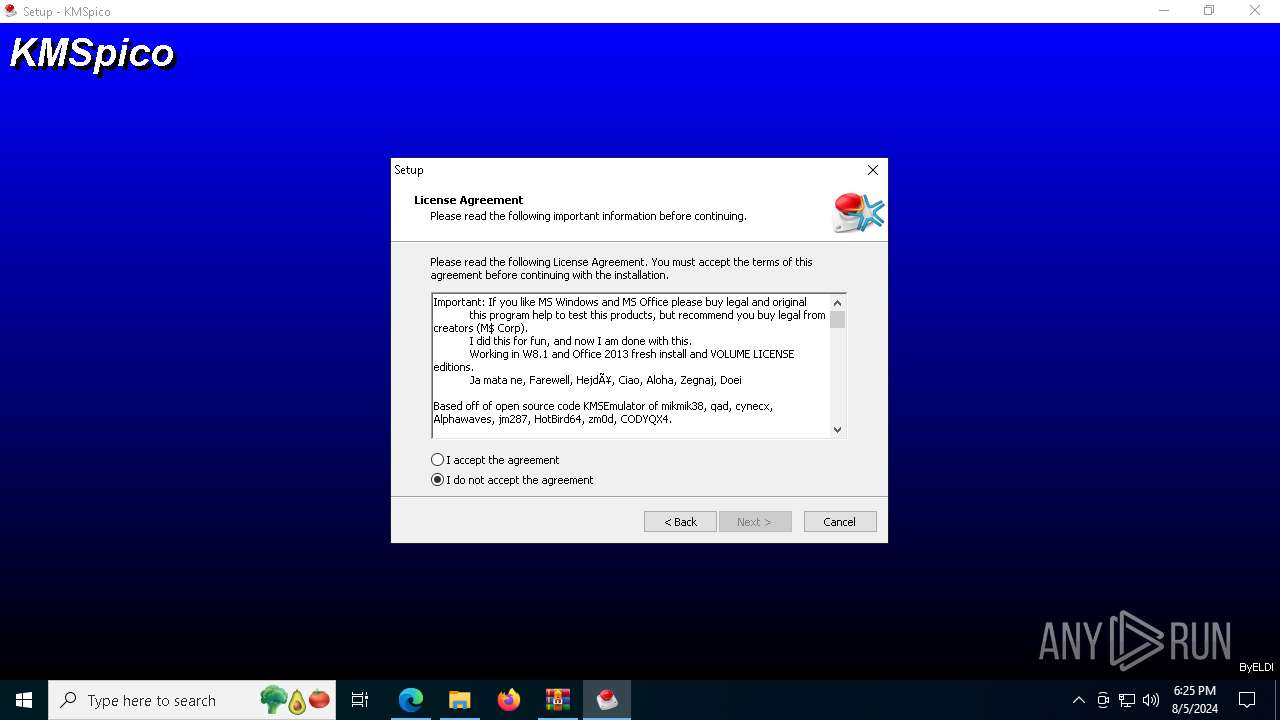
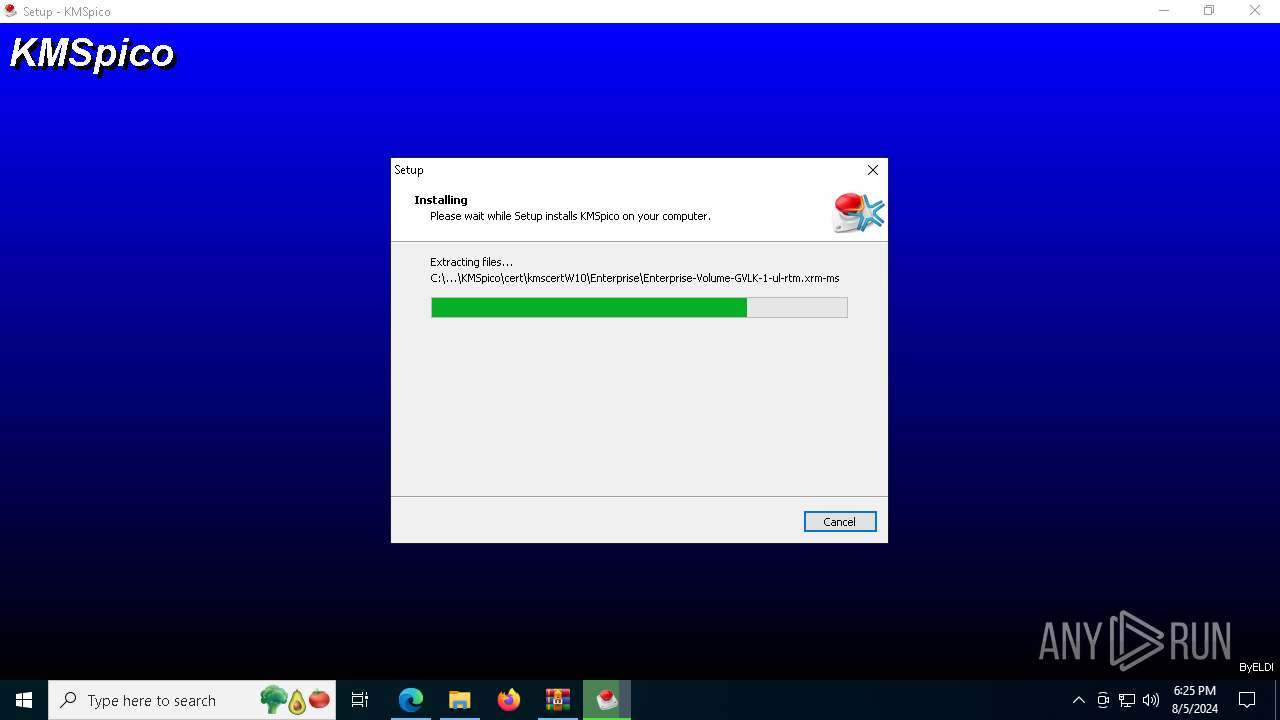
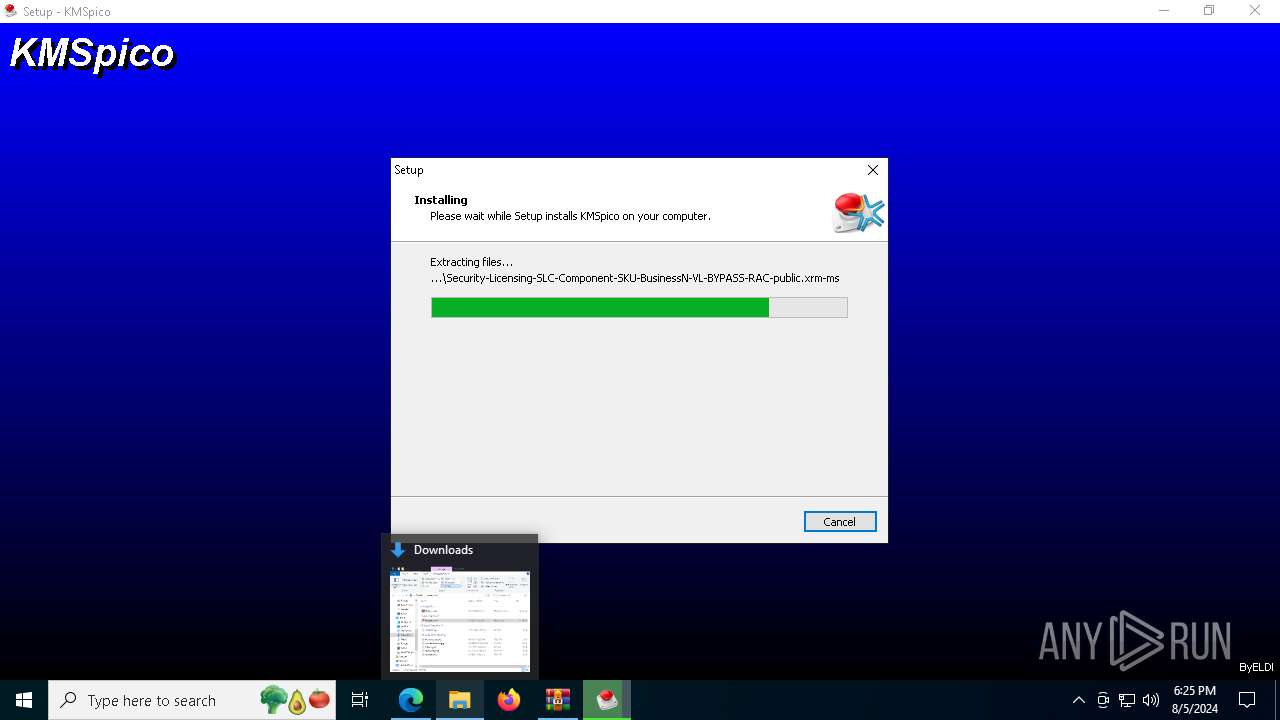
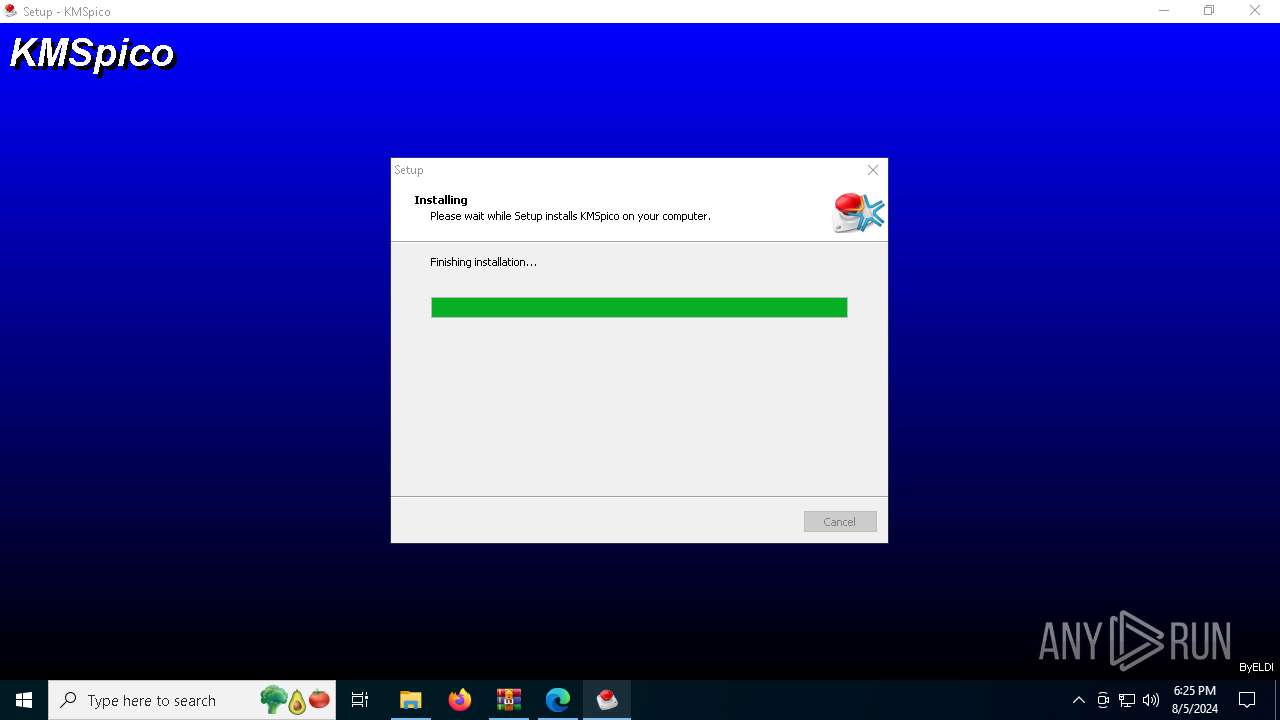
MALICIOUS
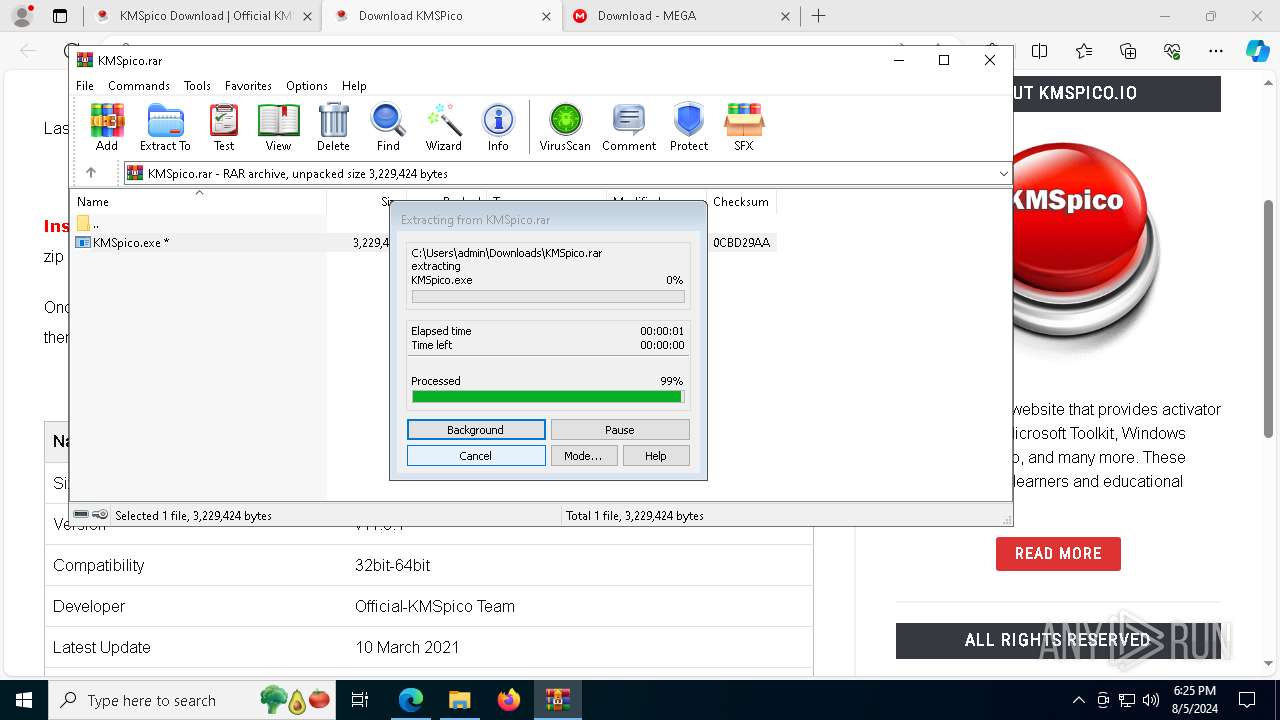
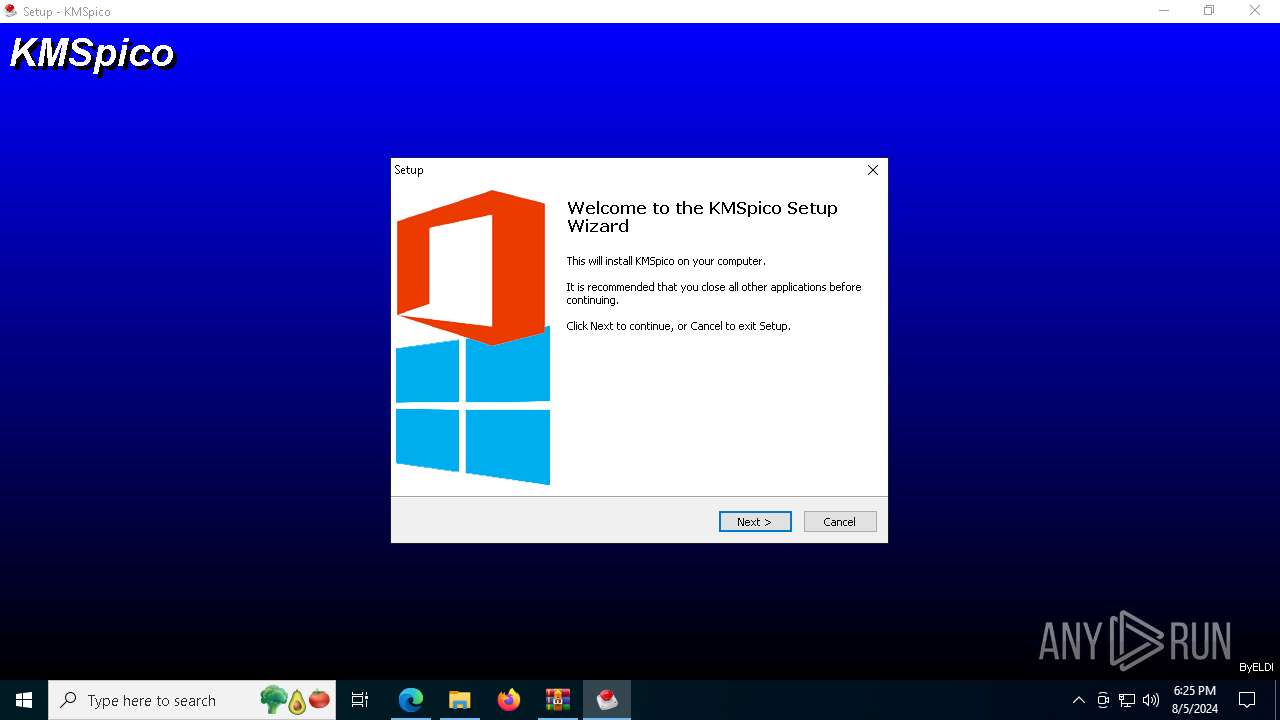
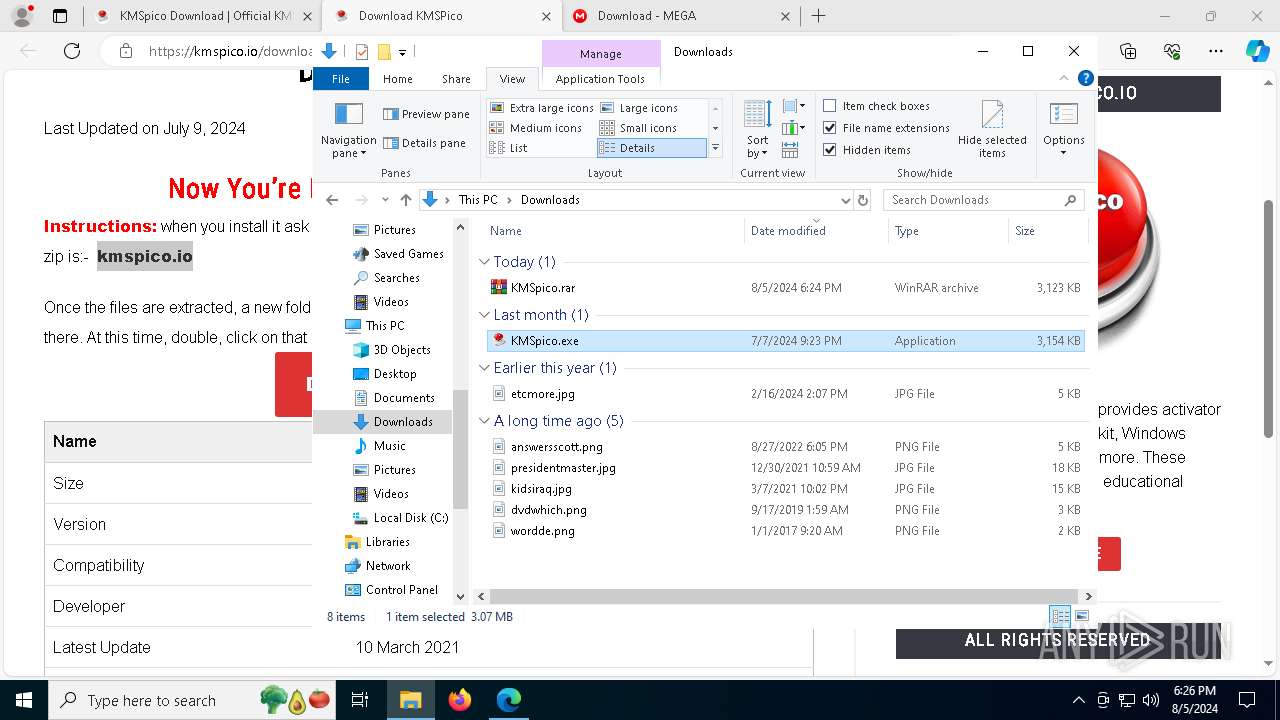
Drops the executable file immediately after the start
- KMSpico.exe (PID: 7728)
- KMSpico.tmp (PID: 7212)
- KMSELDI.exe (PID: 5084)
- KMSpico.exe (PID: 7056)
Changes image file execution options
- KMSELDI.exe (PID: 5084)
- AutoPico.exe (PID: 7336)
- KMSELDI.exe (PID: 7916)
Uses Task Scheduler to run other applications
- cmd.exe (PID: 5136)
SUSPICIOUS
Reads security settings of Internet Explorer
- KMSpico.tmp (PID: 7696)
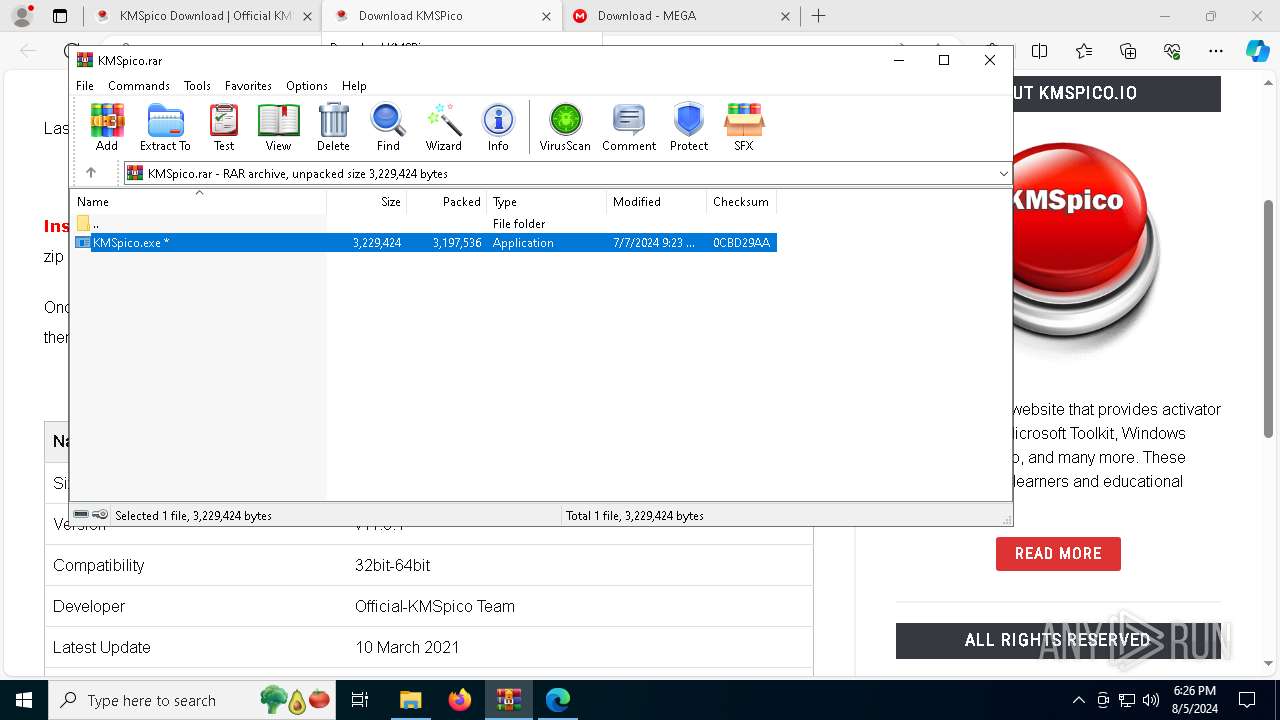
Executable content was dropped or overwritten
- KMSpico.exe (PID: 7056)
- KMSpico.exe (PID: 7728)
- KMSpico.tmp (PID: 7212)
- KMSELDI.exe (PID: 5084)
Reads the date of Windows installation
- KMSpico.tmp (PID: 7696)
Reads the Windows owner or organization settings
- KMSpico.tmp (PID: 7212)
Process drops legitimate windows executable
- KMSpico.tmp (PID: 7212)
Modifies the phishing filter of IE
- KMSpico.tmp (PID: 7212)
Starts CMD.EXE for commands execution
- KMSpico.tmp (PID: 7212)
Starts SC.EXE for service management
- cmd.exe (PID: 3032)
Executing commands from ".cmd" file
- KMSpico.tmp (PID: 7212)
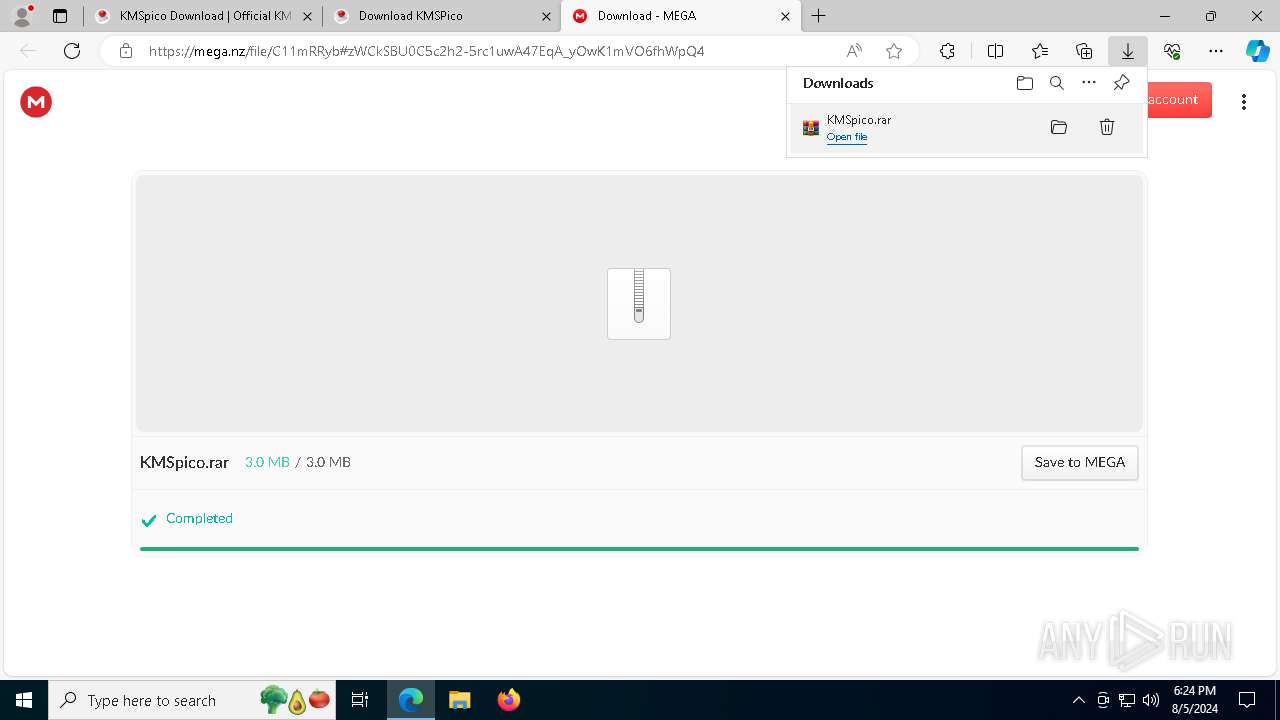
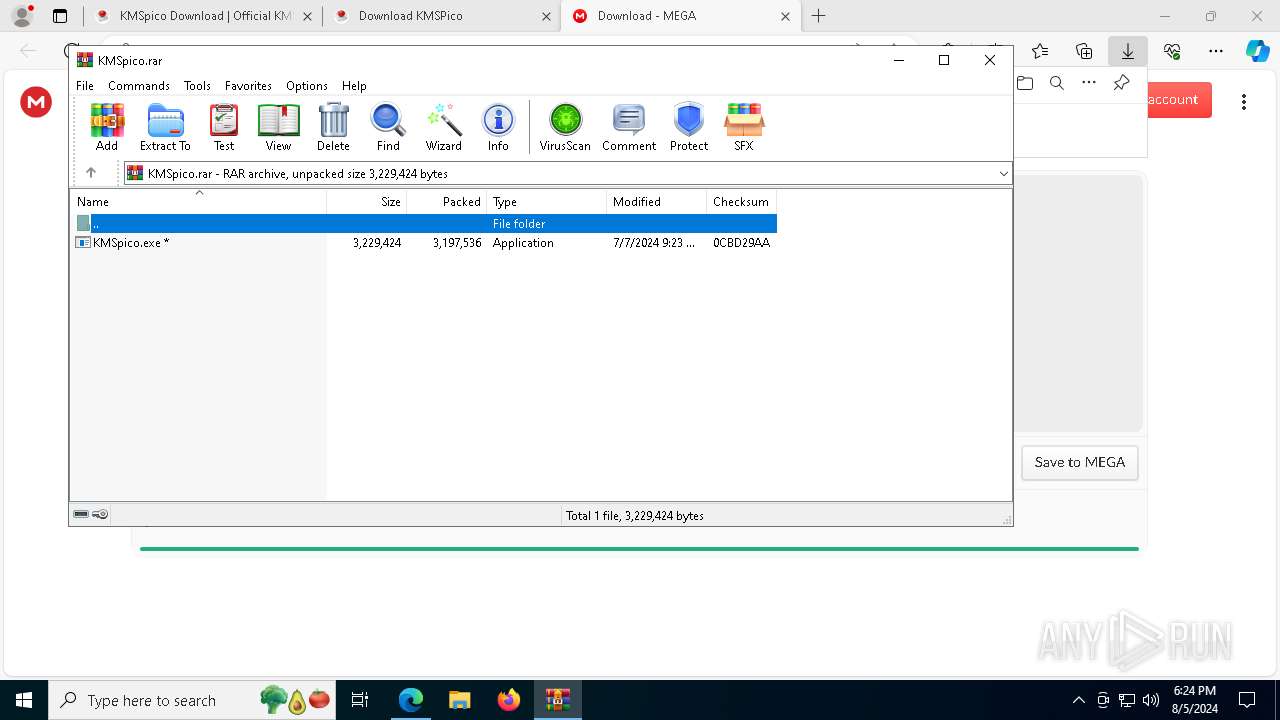
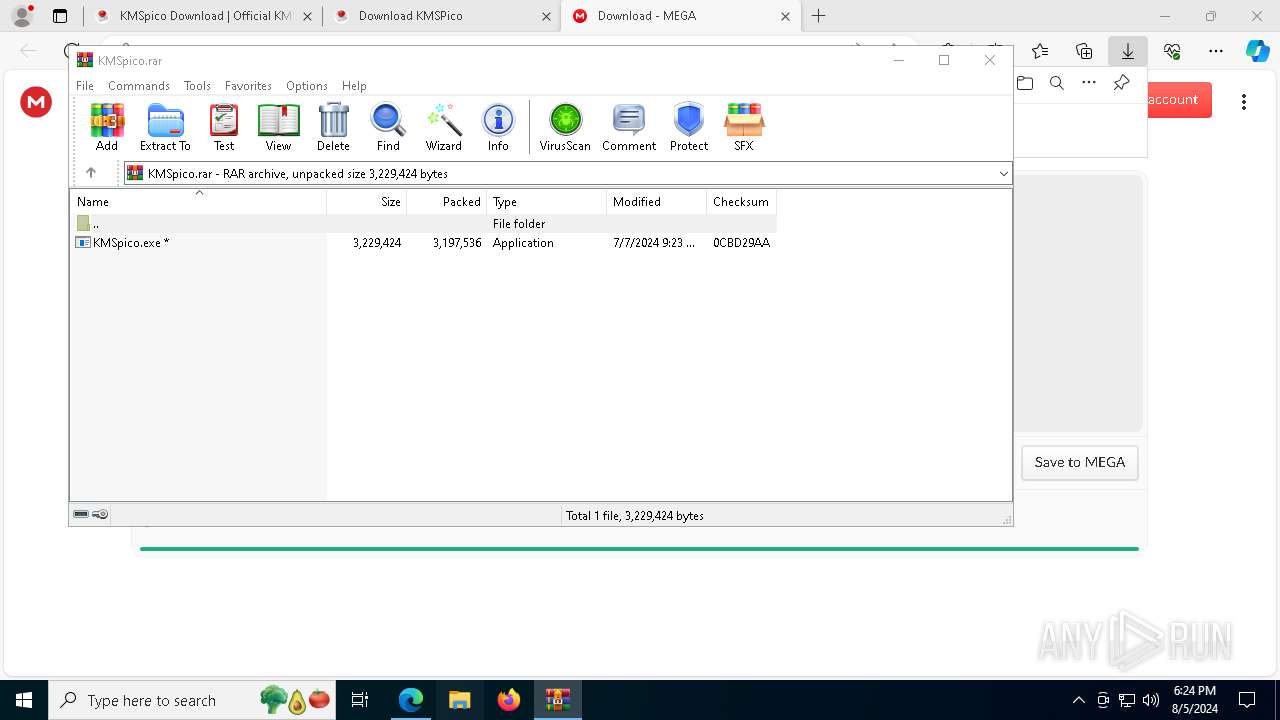
INFO
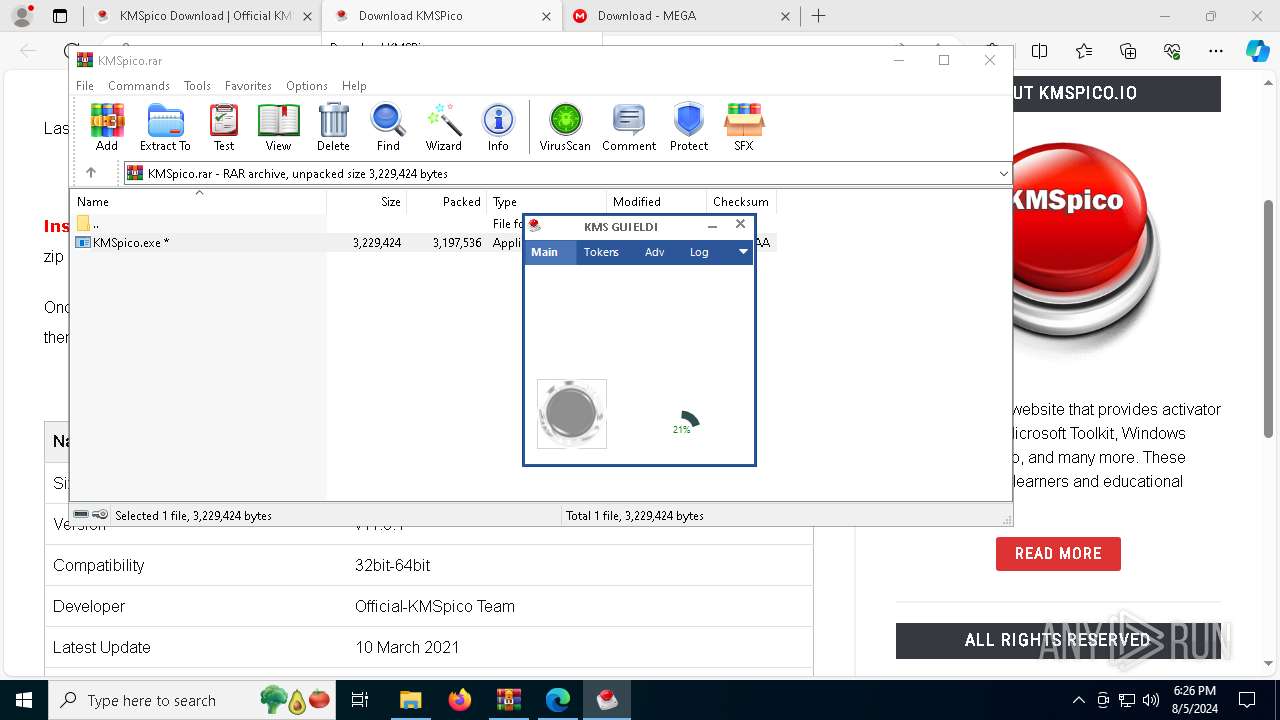
The process uses the downloaded file
- msedge.exe (PID: 8036)
- msedge.exe (PID: 6268)
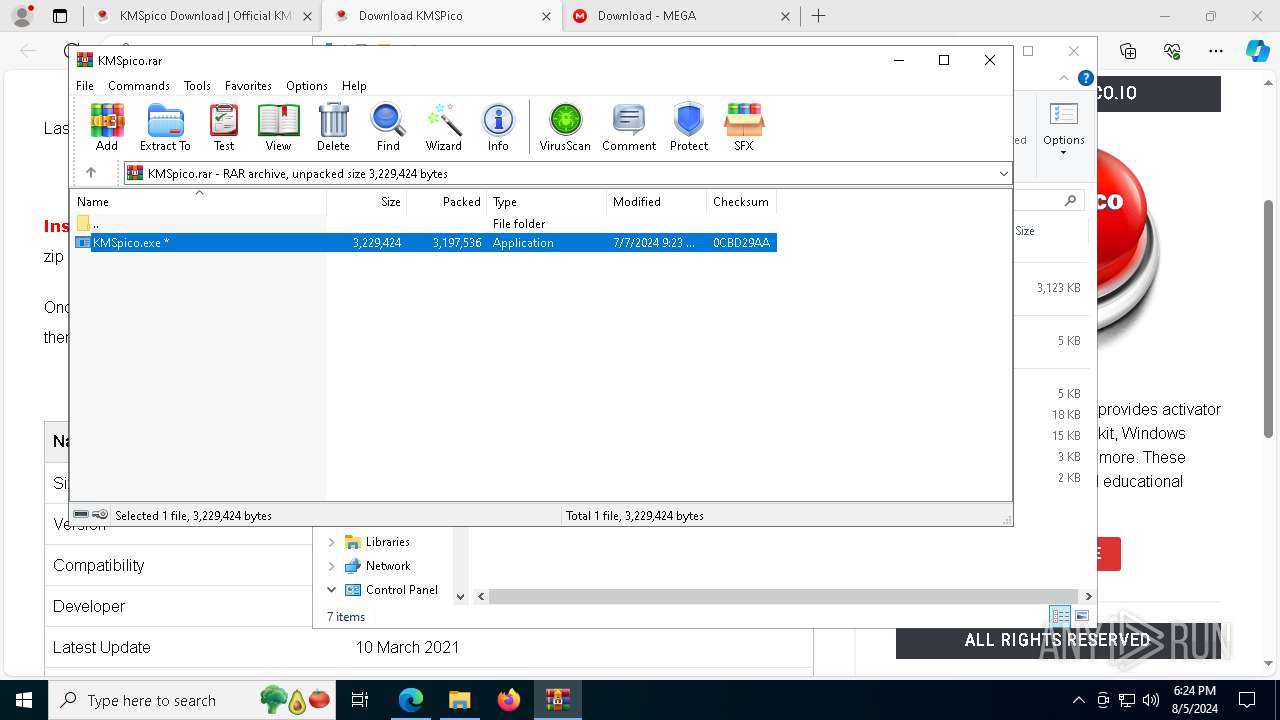
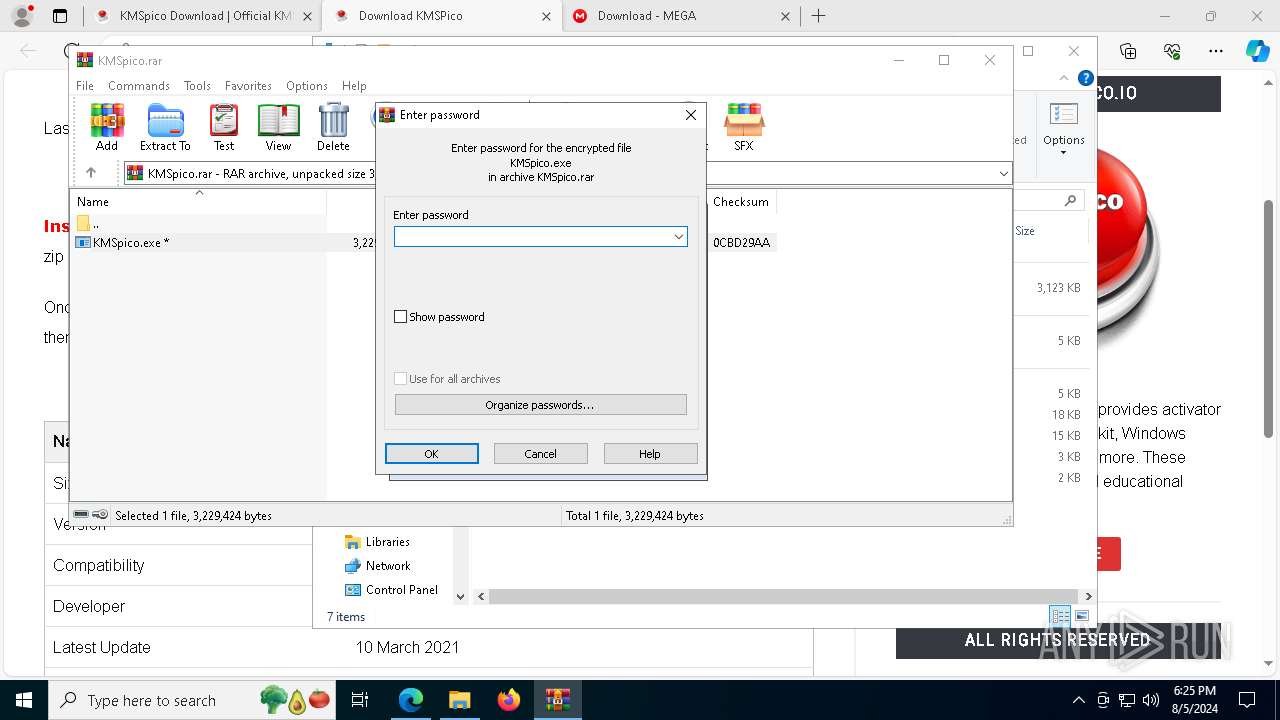
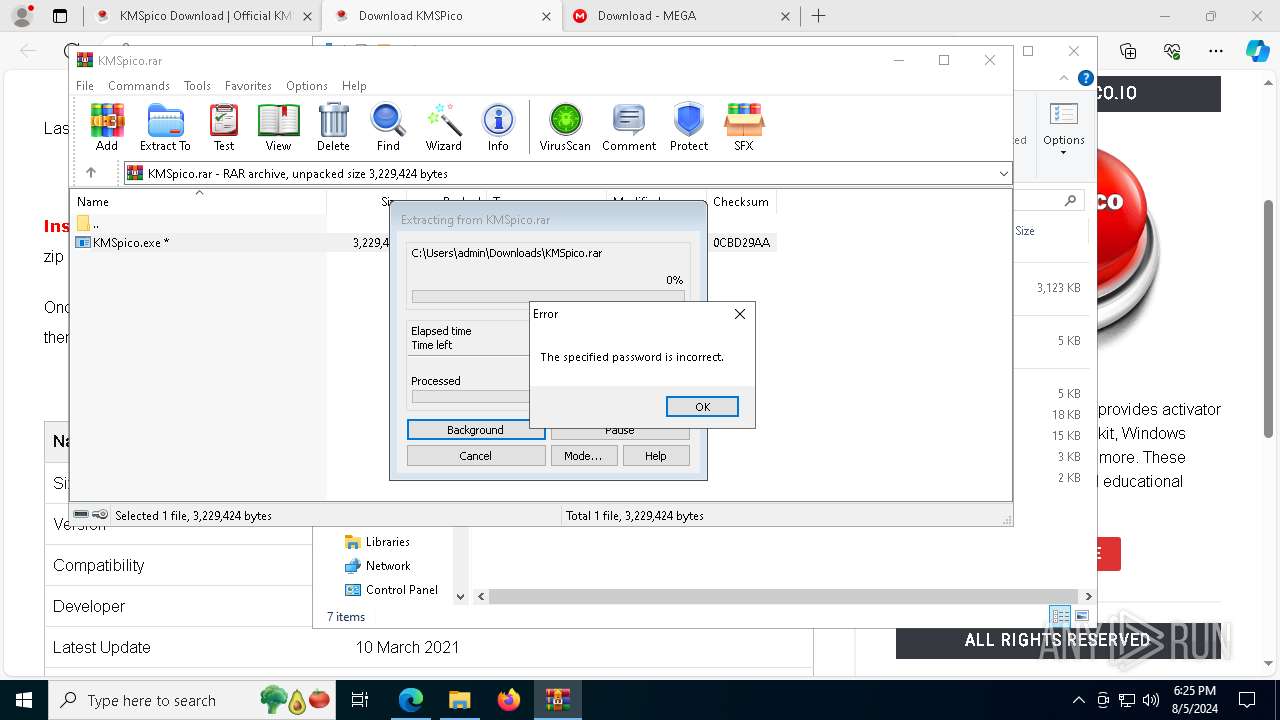
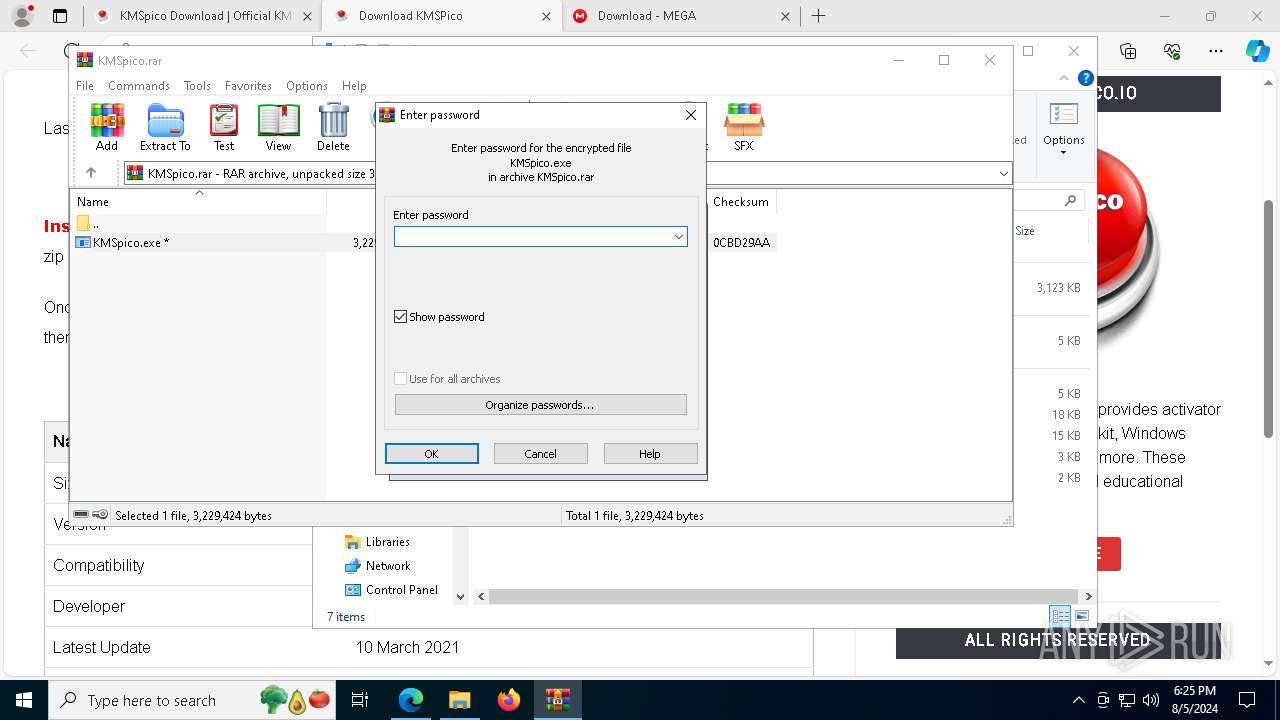
- WinRAR.exe (PID: 5032)
Reads Environment values
- identity_helper.exe (PID: 5656)
- KMSELDI.exe (PID: 5084)
- AutoPico.exe (PID: 7336)
- KMSELDI.exe (PID: 7916)
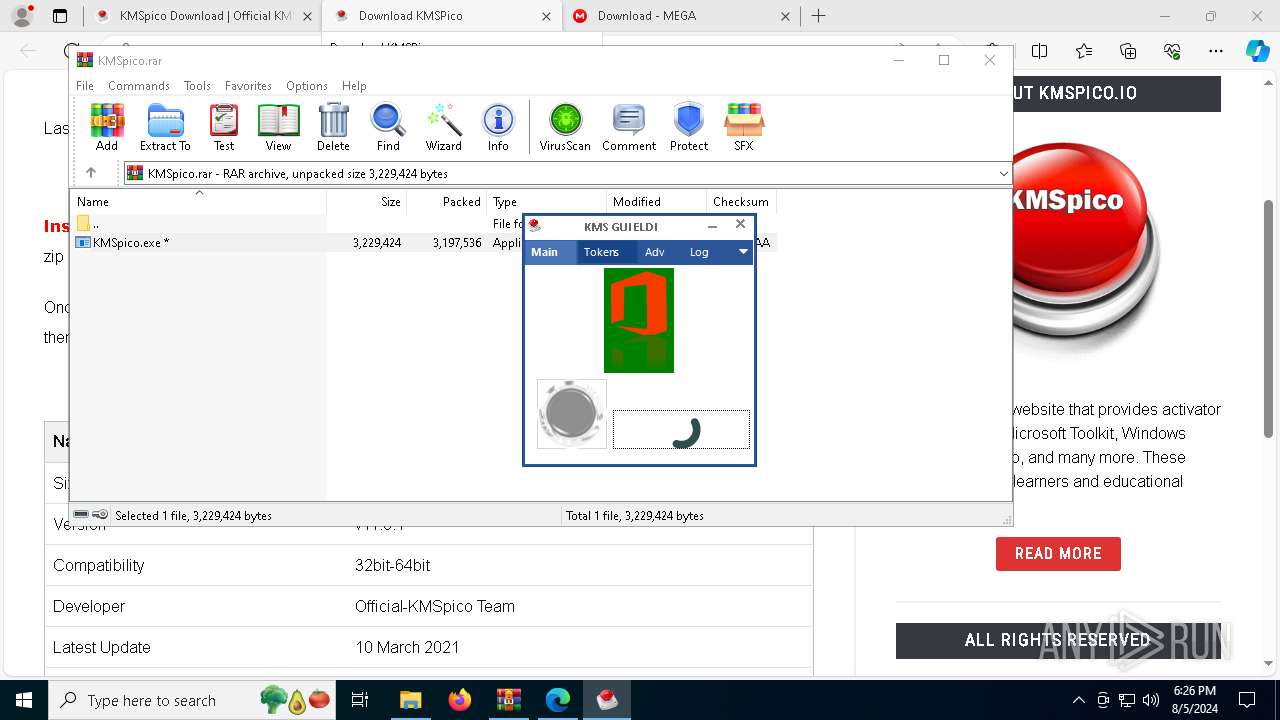
Reads Microsoft Office registry keys
- msedge.exe (PID: 6268)
- AutoPico.exe (PID: 7336)
- KMSELDI.exe (PID: 5084)
- KMSELDI.exe (PID: 7916)
Application launched itself
- msedge.exe (PID: 6268)
Checks supported languages
- KMSpico.tmp (PID: 7696)
- identity_helper.exe (PID: 5656)
- KMSpico.tmp (PID: 7212)
- KMSpico.exe (PID: 7728)
- KMSELDI.exe (PID: 5084)
- UninsHs.exe (PID: 5880)
- AutoPico.exe (PID: 7336)
- SECOH-QAD.exe (PID: 8136)
- TextInputHost.exe (PID: 6996)
- KMSELDI.exe (PID: 7916)
- KMSpico.exe (PID: 7056)
Reads the computer name
- KMSpico.tmp (PID: 7696)
- identity_helper.exe (PID: 5656)
- KMSpico.tmp (PID: 7212)
- KMSELDI.exe (PID: 5084)
- AutoPico.exe (PID: 7336)
- TextInputHost.exe (PID: 6996)
- KMSELDI.exe (PID: 7916)
Process checks computer location settings
- KMSpico.tmp (PID: 7696)
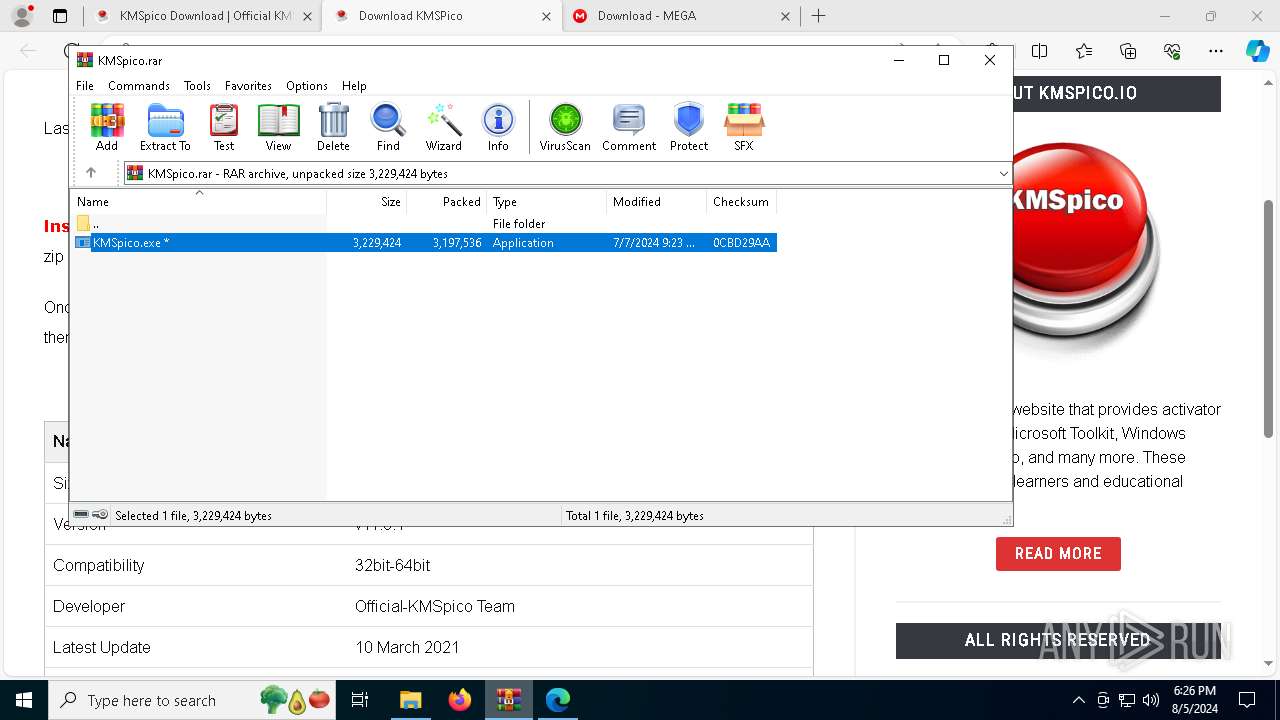
Executable content was dropped or overwritten
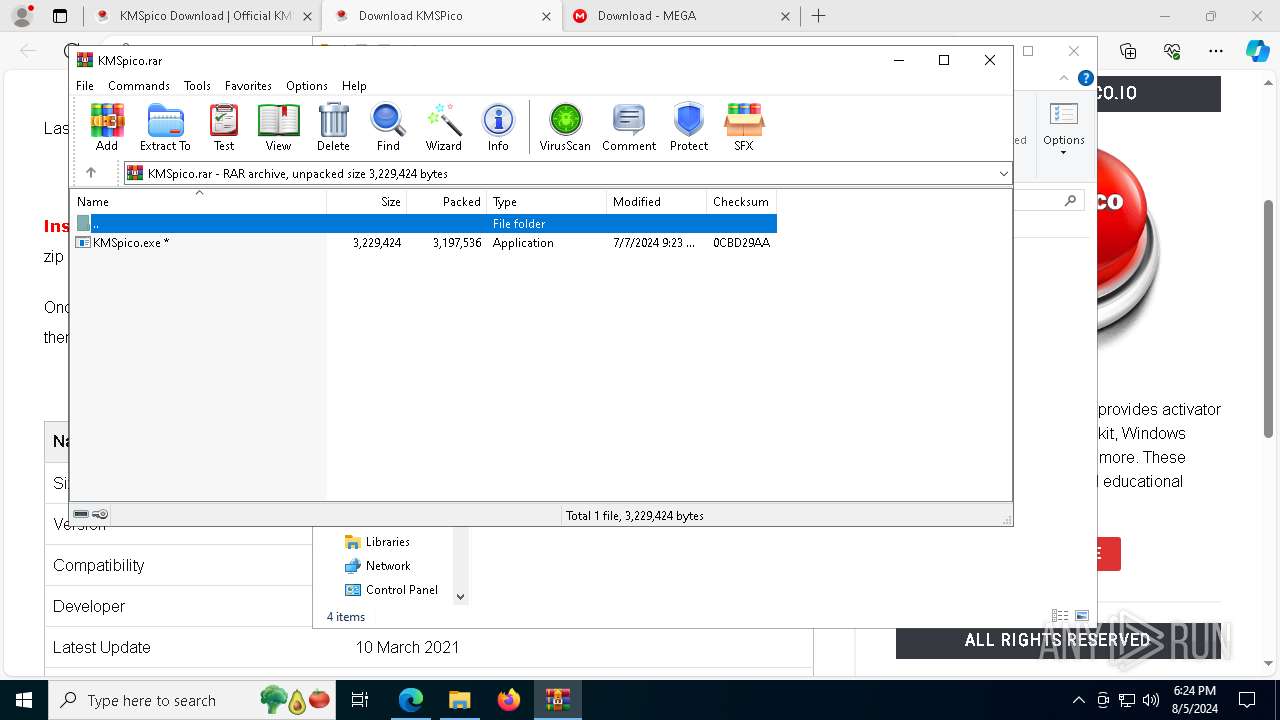
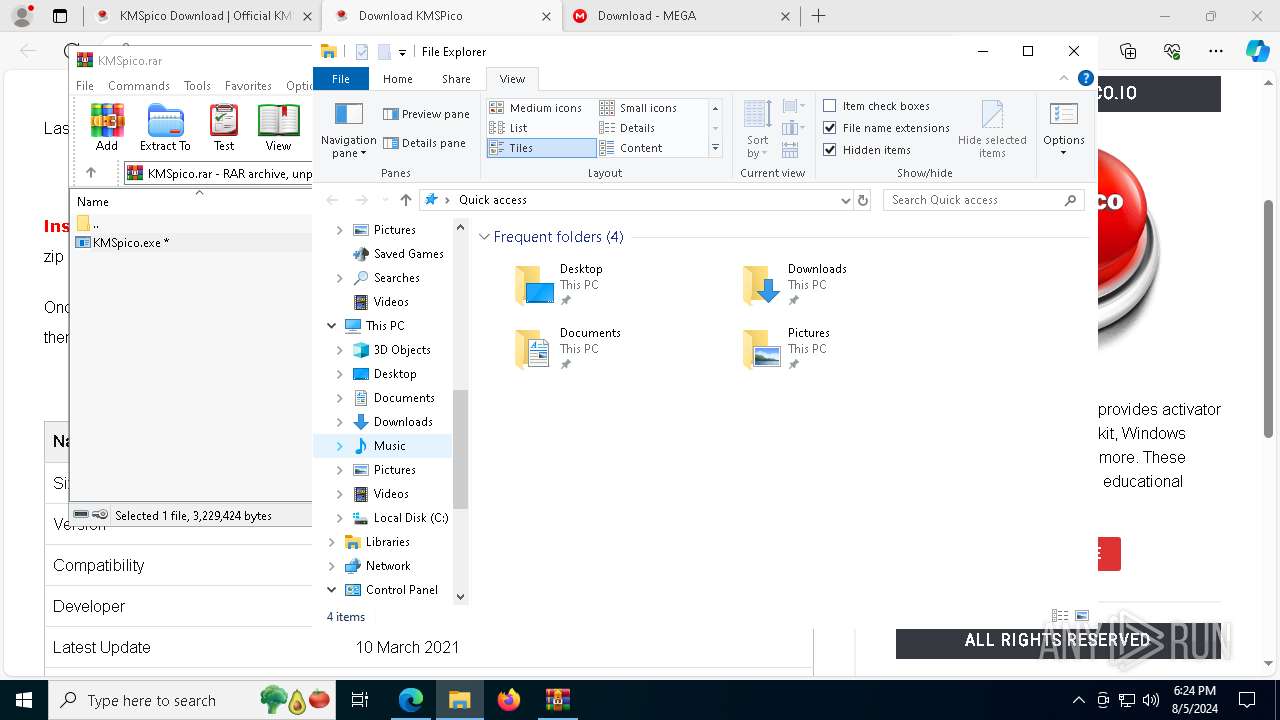
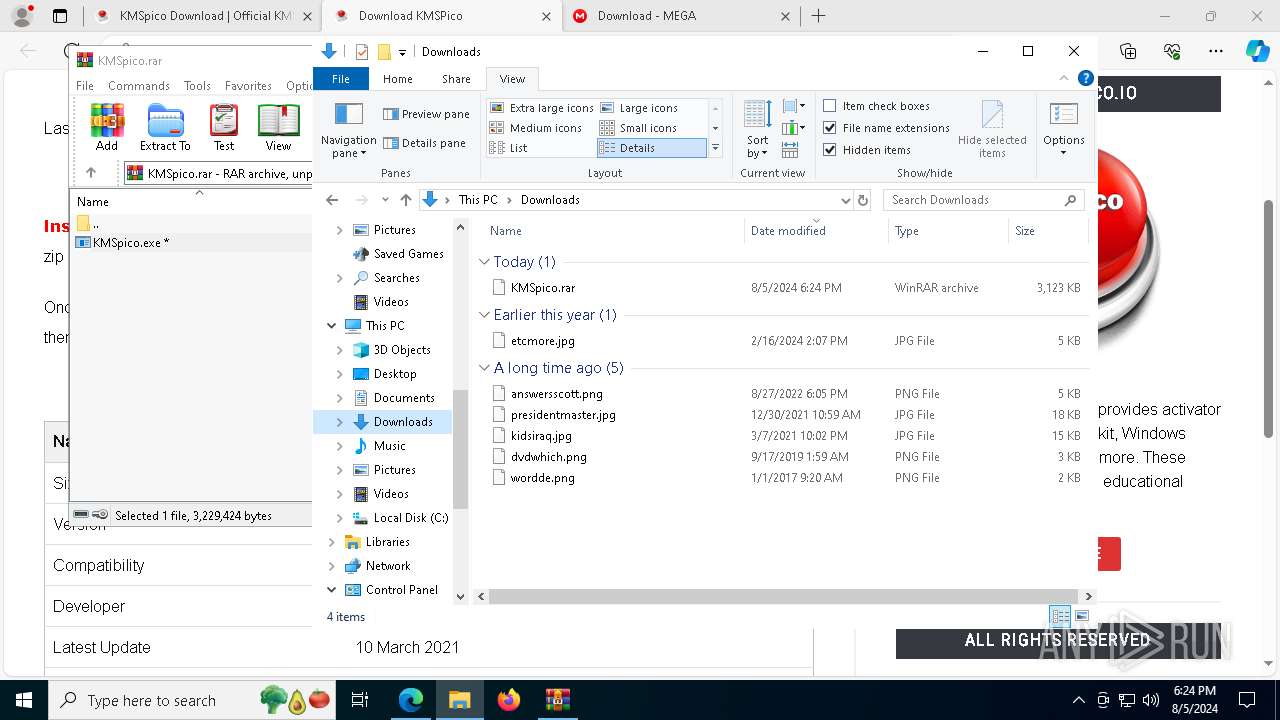
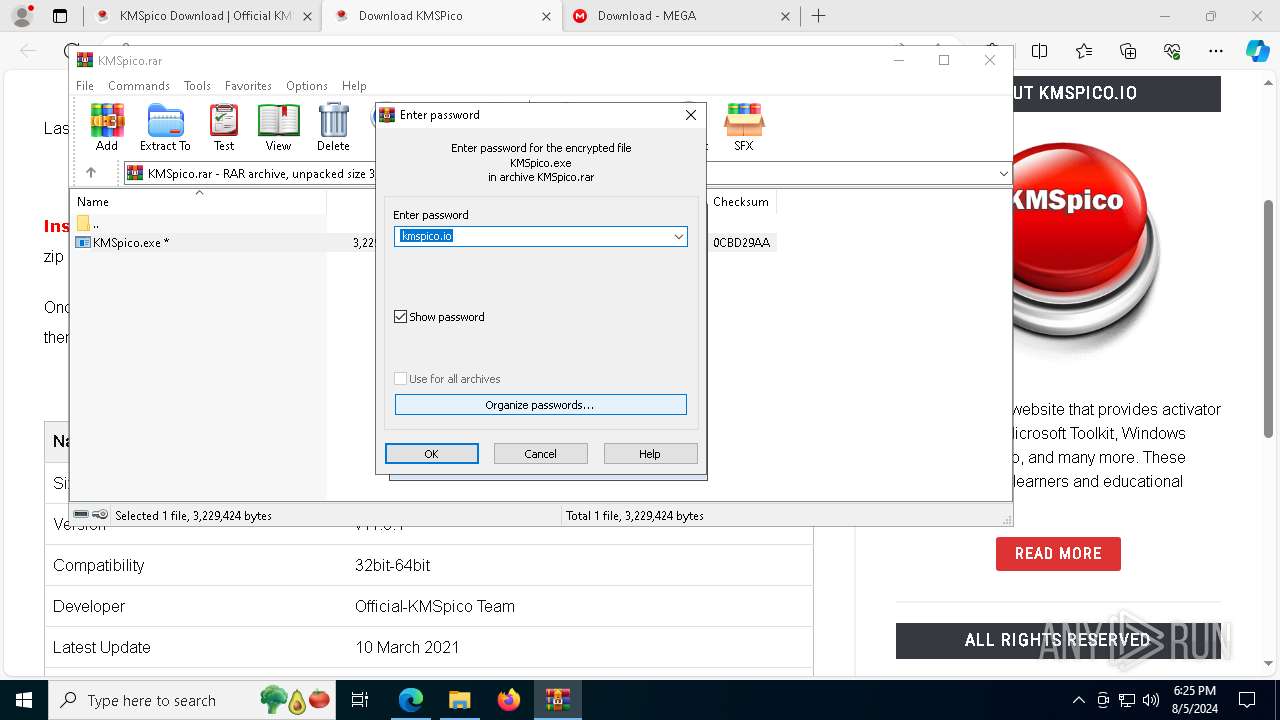
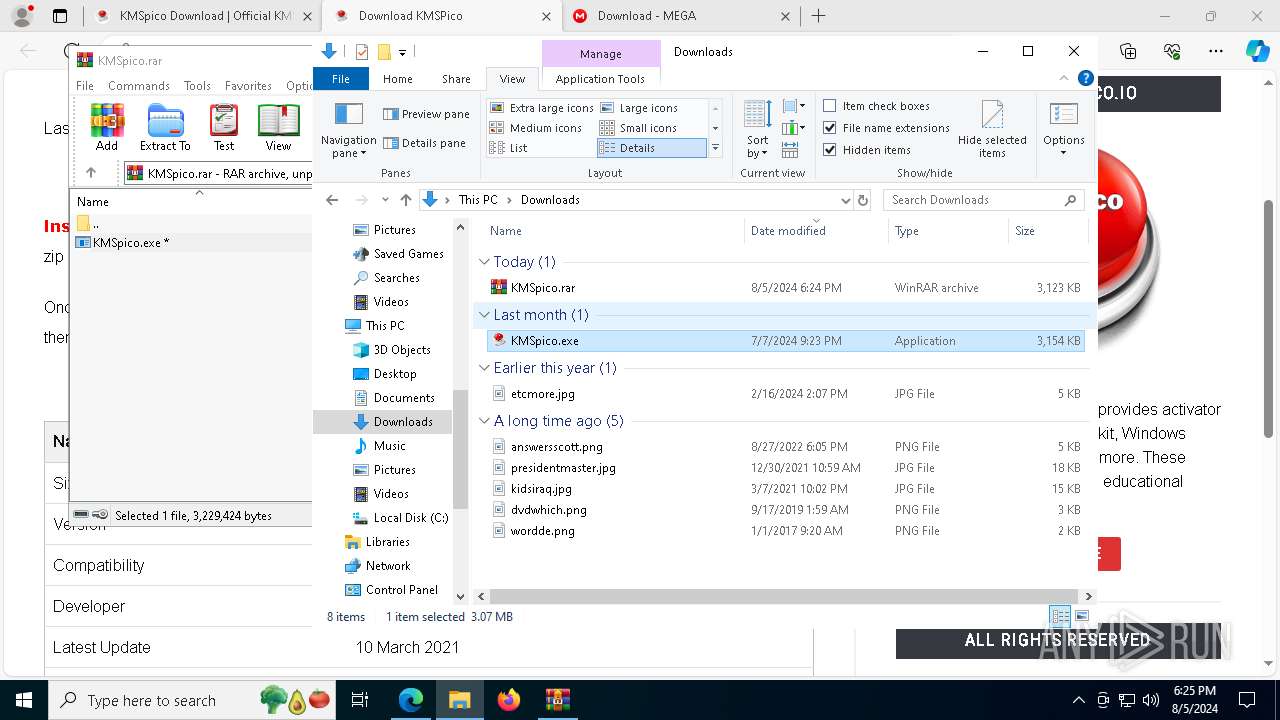
- WinRAR.exe (PID: 5032)
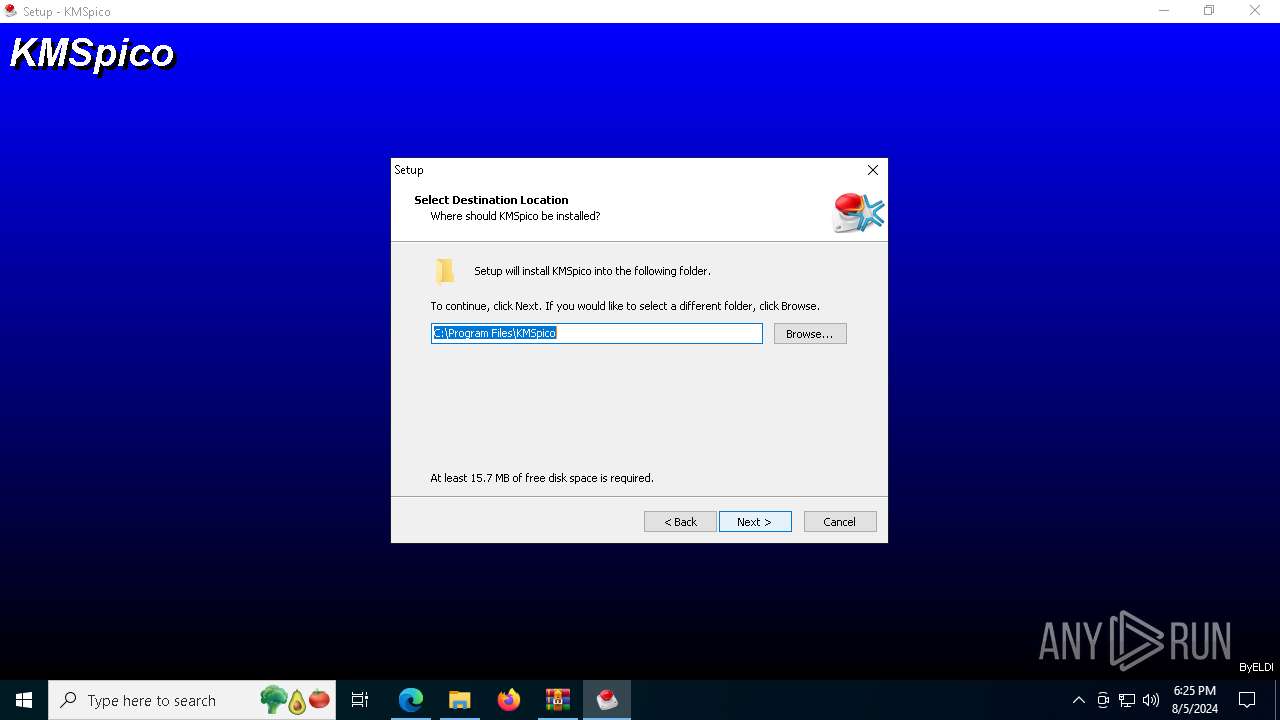
Create files in a temporary directory
- KMSpico.exe (PID: 7728)
- KMSpico.tmp (PID: 7212)
- KMSpico.exe (PID: 7056)
Creates a software uninstall entry
- KMSpico.tmp (PID: 7212)
Creates files in the program directory
- KMSpico.tmp (PID: 7212)
- KMSELDI.exe (PID: 5084)
- AutoPico.exe (PID: 7336)
- KMSELDI.exe (PID: 7916)
Reads the machine GUID from the registry
- KMSELDI.exe (PID: 5084)
- AutoPico.exe (PID: 7336)
- KMSELDI.exe (PID: 7916)
Reads product name
- KMSELDI.exe (PID: 5084)
- AutoPico.exe (PID: 7336)
- KMSELDI.exe (PID: 7916)
Manual execution by a user
- KMSELDI.exe (PID: 2464)
- KMSELDI.exe (PID: 7916)
- KMSpico.exe (PID: 7056)
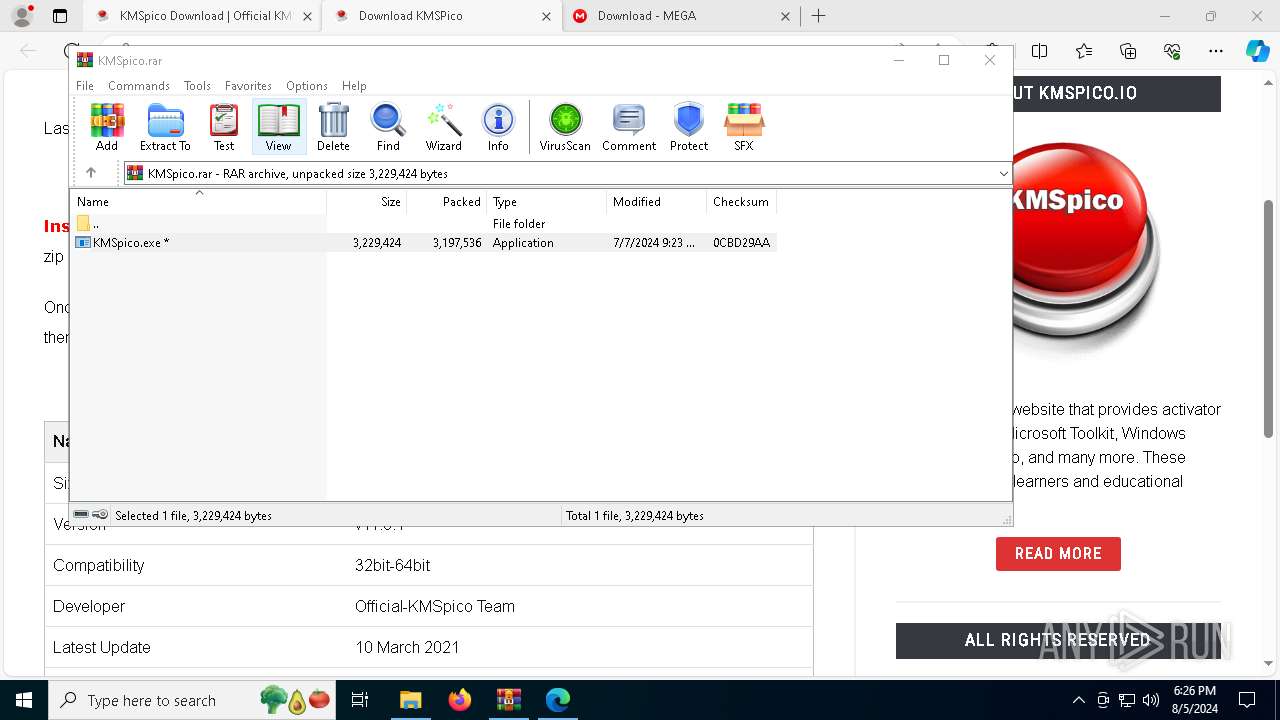
Drops the executable file immediately after the start
- WinRAR.exe (PID: 5032)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
214
Monitored processes
68
Malicious processes
5
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 240 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4352 --field-trial-handle=2316,i,9978885255174973387,15555873660369369307,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 252 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 320 | SCHTASKS /Create /TN "AutoPico Daily Restart" /TR "'C:\Program Files\KMSpico\AutoPico.exe' /silent" /SC DAILY /ST 23:59:59 /RU "NT AUTHORITY\SYSTEM" /RL Highest /F | C:\Windows\System32\schtasks.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 368 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 420 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=3776 --field-trial-handle=2316,i,9978885255174973387,15555873660369369307,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1020 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5572 --field-trial-handle=2316,i,9978885255174973387,15555873660369369307,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1132 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6000 --field-trial-handle=2316,i,9978885255174973387,15555873660369369307,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1360 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=5272 --field-trial-handle=2316,i,9978885255174973387,15555873660369369307,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 3221226029 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1492 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5320 --field-trial-handle=2316,i,9978885255174973387,15555873660369369307,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1688 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_xpay_wallet.mojom.EdgeXPayWalletService --lang=en-US --service-sandbox-type=utility --no-appcompat-clear --mojo-platform-channel-handle=5492 --field-trial-handle=2316,i,9978885255174973387,15555873660369369307,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
29 048
Read events
28 745
Write events
287
Delete events
16
Modification events
| (PID) Process: | (6268) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6268) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6268) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (6268) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (6268) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6268) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\EdgeUpdate\ClientState\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (6268) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6268) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge |
| Operation: | write | Name: | UsageStatsInSample |
Value: 1 | |||
| (PID) Process: | (6268) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (6268) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | urlstats |
Value: 0 | |||
Executable files
27
Suspicious files
195
Text files
819
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6268 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RFe53d8.TMP | — | |
MD5:— | SHA256:— | |||
| 6268 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6268 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RFe53d8.TMP | — | |
MD5:— | SHA256:— | |||
| 6268 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6268 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RFe53e8.TMP | — | |
MD5:— | SHA256:— | |||
| 6268 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6268 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RFe53f8.TMP | — | |
MD5:— | SHA256:— | |||
| 6268 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6268 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RFe53f8.TMP | — | |
MD5:— | SHA256:— | |||
| 6268 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
40
TCP/UDP connections
150
DNS requests
109
Threats
29
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6624 | msedge.exe | GET | 301 | 35.208.62.162:80 | http://kmspico.io/wp-content/uploads/2020/10/download-kmspico.png | US | text | 24 b | malicious |
6624 | msedge.exe | GET | 301 | 35.208.62.162:80 | http://kmspico.io/wp-content/uploads/2020/10/kmspico-activator-1024x703.png | US | text | 24 b | malicious |
6624 | msedge.exe | GET | 301 | 35.208.62.162:80 | http://kmspico.io/wp-content/uploads/2020/10/kmspico-software-1024x553.png | US | text | 24 b | malicious |
6624 | msedge.exe | GET | 301 | 35.208.62.162:80 | http://kmspico.io/wp-content/uploads/2020/10/how-to-install-kmspico-1024x590.png | US | text | 24 b | malicious |
6624 | msedge.exe | GET | 301 | 35.208.62.162:80 | http://kmspico.io/wp-content/uploads/2020/10/kms-pico-1024x576.png | US | text | 24 b | malicious |
6624 | msedge.exe | GET | 301 | 35.208.62.162:80 | http://kmspico.io/wp-content/uploads/2020/10/kmspico-official-download-1024x574.png | US | text | 24 b | malicious |
6624 | msedge.exe | GET | 301 | 35.208.62.162:80 | http://kmspico.io/wp-content/uploads/2020/10/kmspico-tool-1024x576.png | US | text | 24 b | malicious |
6624 | msedge.exe | GET | 301 | 35.208.62.162:80 | http://kmspico.io/wp-content/uploads/2020/10/windows-10-kmspico-1024x506.png | US | text | 24 b | malicious |
6624 | msedge.exe | GET | 301 | 35.208.62.162:80 | http://kmspico.io/wp-content/uploads/2020/10/kmspico-windows-10-1024x576.png | US | text | 24 b | malicious |
6624 | msedge.exe | GET | 301 | 35.208.62.162:80 | http://kmspico.io/wp-content/uploads/2021/03/Activate-Microsoft-Office-With-KMS.jpg | US | text | 24 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1784 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1248 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2120 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6624 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6268 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
6624 | msedge.exe | 13.107.246.45:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
6624 | msedge.exe | 35.208.62.162:80 | kmspico.io | GOOGLE | US | unknown |
6624 | msedge.exe | 13.107.21.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
kmspico.io |
| malicious |
edge-mobile-static.azureedge.net |
| whitelisted |
business.bing.com |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6624 | msedge.exe | Misc activity | ET INFO File Sharing Related Domain in DNS Lookup (mega .nz) |
6624 | msedge.exe | Misc activity | ET INFO File Sharing Domain Observed in TLS SNI (mega .nz) |
6624 | msedge.exe | Misc activity | ET INFO File Sharing Related Domain in DNS Lookup (mega .nz) |
6624 | msedge.exe | Misc activity | ET INFO File Sharing Domain Observed in TLS SNI (mega .nz) |
6624 | msedge.exe | Misc activity | ET INFO Observed DNS Query to Filesharing Service (mega .co .nz) |
6624 | msedge.exe | Misc activity | ET INFO File Sharing Domain Observed in TLS SNI (mega .nz) |
6624 | msedge.exe | Misc activity | ET INFO File Sharing Related Domain in DNS Lookup (mega .nz) |
6624 | msedge.exe | Misc activity | ET INFO Observed DNS Query to Filesharing Service (mega .co .nz) |
6624 | msedge.exe | Misc activity | ET INFO File Sharing Domain Observed in TLS SNI (mega .nz) |
6624 | msedge.exe | Misc activity | ET INFO File Sharing Related Domain in DNS Lookup (mega .nz) |
3 ETPRO signatures available at the full report