| File name: | Tftpd64_Installer_v4.71.exe |
| Full analysis: | https://app.any.run/tasks/b007d5b9-9953-4911-be42-c7a3b2b0ab53 |
| Verdict: | Malicious activity |
| Analysis date: | August 24, 2025, 08:38:48 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive, 5 sections |
| MD5: | C17207B67FA5A02E73E1DF6C3D74C29F |
| SHA1: | 8647D2944C2397432CB1E281E4F6EEF7EE36DD3C |
| SHA256: | AA0B06B5F3C7EA771E78C172F4223C29F01377EE134E6233DDA5C46E1112305C |
| SSDEEP: | 24576:1/JYDpovsLd5kZcdZd9/gIGMzi9a1FZilgWiMgLXvYyYUsLd9bmZImxmpdop:1/JcpovsLd5kZcdZd9/gIGMzi9a13i2f |
MALICIOUS
No malicious indicators.SUSPICIOUS
Malware-specific behavior (creating "System.dll" in Temp)
- Tftpd64_Installer_v4.71.exe (PID: 2192)
Executable content was dropped or overwritten
- Tftpd64_Installer_v4.71.exe (PID: 2192)
Creates a software uninstall entry
- Tftpd64_Installer_v4.71.exe (PID: 2192)
The process creates files with name similar to system file names
- Tftpd64_Installer_v4.71.exe (PID: 2192)
INFO
Reads the computer name
- Tftpd64_Installer_v4.71.exe (PID: 2192)
- tftpd64.exe (PID: 6344)
- tftpd64.exe (PID: 1028)
- tftpd64.exe (PID: 6636)
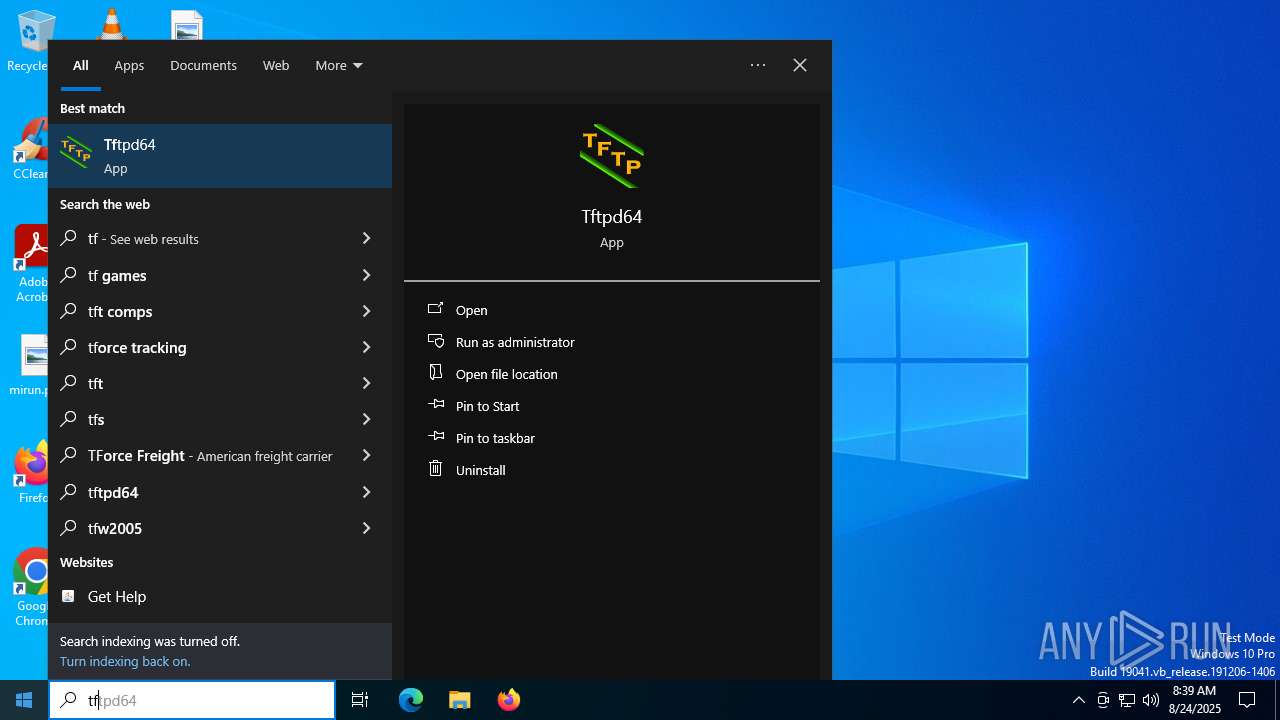
Manual execution by a user
- tftpd64.exe (PID: 6636)
- tftpd64.exe (PID: 6344)
- tftpd64.exe (PID: 1028)
Checks supported languages
- tftpd64.exe (PID: 6636)
- tftpd64.exe (PID: 6344)
- tftpd64.exe (PID: 1028)
- Tftpd64_Installer_v4.71.exe (PID: 2192)
Creates files or folders in the user directory
- Tftpd64_Installer_v4.71.exe (PID: 2192)
Creates files in the program directory
- Tftpd64_Installer_v4.71.exe (PID: 2192)
The sample compiled with french language support
- Tftpd64_Installer_v4.71.exe (PID: 2192)
Create files in a temporary directory
- Tftpd64_Installer_v4.71.exe (PID: 2192)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2025:03:08 23:05:20+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 27136 |
| InitializedDataSize: | 184832 |
| UninitializedDataSize: | 2048 |
| EntryPoint: | 0x358d |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Total processes
144
Monitored processes
6
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1028 | "C:\Program Files\Tftpd64\tftpd64.exe" | C:\Program Files\Tftpd64\tftpd64.exe | explorer.exe | ||||||||||||
User: admin Company: Ph. Jounin Integrity Level: MEDIUM Description: TFTP server Exit code: 0 Modules
| |||||||||||||||
| 1392 | "C:\Users\admin\AppData\Local\Temp\Tftpd64_Installer_v4.71.exe" | C:\Users\admin\AppData\Local\Temp\Tftpd64_Installer_v4.71.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 2192 | "C:\Users\admin\AppData\Local\Temp\Tftpd64_Installer_v4.71.exe" | C:\Users\admin\AppData\Local\Temp\Tftpd64_Installer_v4.71.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 4788 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6344 | "C:\Program Files\Tftpd64\tftpd64.exe" | C:\Program Files\Tftpd64\tftpd64.exe | explorer.exe | ||||||||||||
User: admin Company: Ph. Jounin Integrity Level: MEDIUM Description: TFTP server Exit code: 0 Modules
| |||||||||||||||
| 6636 | "C:\Program Files\Tftpd64\tftpd64.exe" | C:\Program Files\Tftpd64\tftpd64.exe | explorer.exe | ||||||||||||
User: admin Company: Ph. Jounin Integrity Level: MEDIUM Description: TFTP server Exit code: 0 Modules
| |||||||||||||||
Total events
1 305
Read events
1 295
Write events
10
Delete events
0
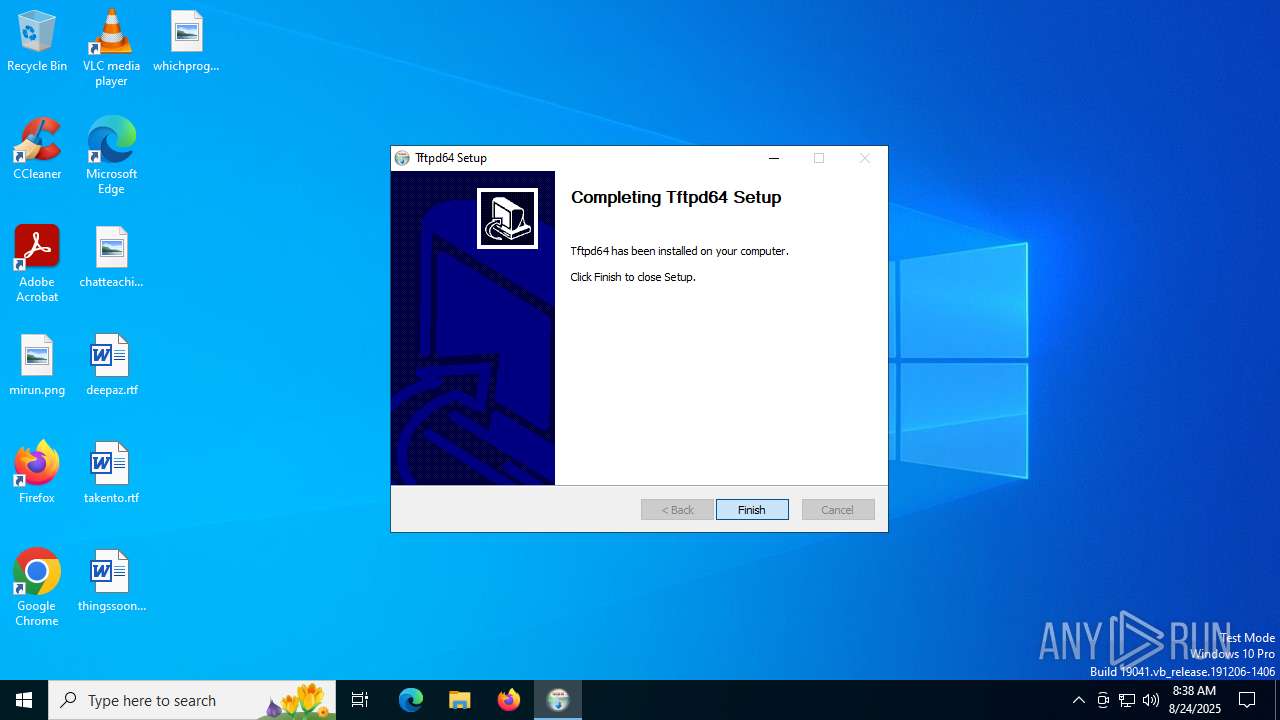
Modification events
| (PID) Process: | (2192) Tftpd64_Installer_v4.71.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\Tftpd64 |
| Operation: | write | Name: | DisplayName |
Value: Tftpd64 | |||
| (PID) Process: | (2192) Tftpd64_Installer_v4.71.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\Tftpd64 |
| Operation: | write | Name: | UninstallString |
Value: C:\Program Files\Tftpd64\uninstall.exe | |||
| (PID) Process: | (2192) Tftpd64_Installer_v4.71.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\Tftpd64 |
| Operation: | write | Name: | DisplayVersion |
Value: 4.71 | |||
| (PID) Process: | (2192) Tftpd64_Installer_v4.71.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\Tftpd64 |
| Operation: | write | Name: | Publisher |
Value: Ph. Jounin | |||
| (PID) Process: | (2192) Tftpd64_Installer_v4.71.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\Tftpd64 |
| Operation: | write | Name: | InstallLocation |
Value: C:\Program Files\Tftpd64 | |||
| (PID) Process: | (2192) Tftpd64_Installer_v4.71.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\Tftpd64 |
| Operation: | write | Name: | DisplayIcon |
Value: C:\Program Files\Tftpd64\tftpd64.exe | |||
| (PID) Process: | (2192) Tftpd64_Installer_v4.71.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Tftpd64 |
| Operation: | write | Name: | InstallPath |
Value: C:\Program Files\Tftpd64 | |||
| (PID) Process: | (1028) tftpd64.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\TFTPD32 |
| Operation: | write | Name: | LastWindowPos |
Value: 60 49 465 390 | |||
| (PID) Process: | (6636) tftpd64.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\TFTPD32 |
| Operation: | write | Name: | LastWindowPos |
Value: 60 49 465 390 | |||
| (PID) Process: | (6344) tftpd64.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\TFTPD32 |
| Operation: | write | Name: | LastWindowPos |
Value: 60 49 465 390 | |||
Executable files
5
Suspicious files
5
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
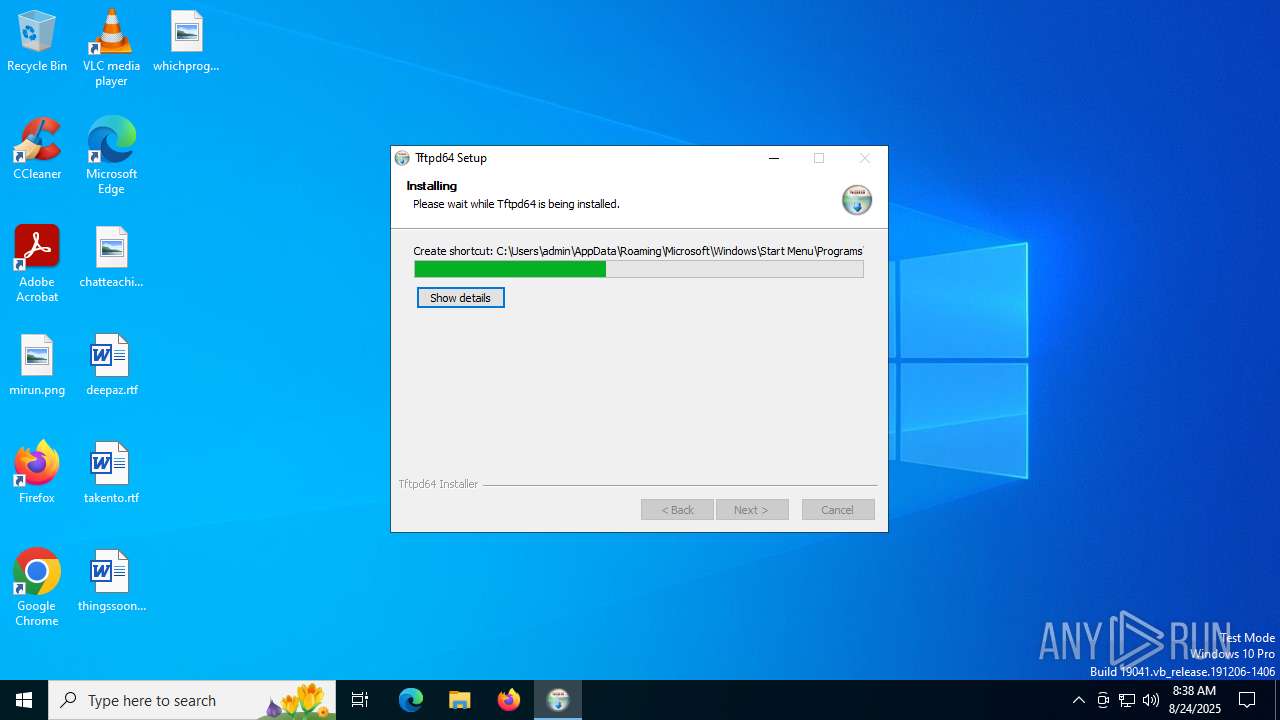
| 2192 | Tftpd64_Installer_v4.71.exe | C:\Users\admin\AppData\Local\Temp\nslCDBC.tmp\modern-wizard.bmp | image | |
MD5:CBE40FD2B1EC96DAEDC65DA172D90022 | SHA256:3AD2DC318056D0A2024AF1804EA741146CFC18CC404649A44610CBF8B2056CF2 | |||
| 2192 | Tftpd64_Installer_v4.71.exe | C:\Users\admin\AppData\Local\Temp\nslCDBC.tmp\System.dll | executable | |
MD5:9B38A1B07A0EBC5C7E59E63346ECC2DB | SHA256:C881253DAFCF1322A771139B1A429EC1E78C507CA81A218A20DC1A4B25ABBFE7 | |||
| 2192 | Tftpd64_Installer_v4.71.exe | C:\Users\admin\AppData\Local\Temp\nslCDBC.tmp\nsDialogs.dll | executable | |
MD5:8F0E7415F33843431DF308BB8E06AF81 | SHA256:BB49F15FA83452370047A7801E39FC7F64E70C7545B8999BB85AA4749EAA048B | |||
| 2192 | Tftpd64_Installer_v4.71.exe | C:\Program Files\Tftpd64\uninstall.exe | executable | |
MD5:D7FFF0C7D9E8351A75456AB0E628FDDC | SHA256:E3109D9381B19064294C50928C9C39FE1100F10DF210951DB744BF33D804EEFB | |||
| 2192 | Tftpd64_Installer_v4.71.exe | C:\Program Files\Tftpd64\EUPL-EN.pdf | ||
MD5:254B5DDBC15269E72BA3A0508681A70C | SHA256:CD5D9E2A925D8DAA92D083FD8C1CEA48DF1BCFFFD857F4F93E2148FDDC5001EC | |||
| 2192 | Tftpd64_Installer_v4.71.exe | C:\Program Files\Tftpd64\tftpd32.chm | binary | |
MD5:DE0095E371874836FB50CD3400D7B204 | SHA256:810A0F52703D051B30D5ECD219C72B0599964DE34D1C1912367271C87D4725BF | |||
| 2192 | Tftpd64_Installer_v4.71.exe | C:\Program Files\Tftpd64\tftpd64.exe | executable | |
MD5:86B6E1F842C5DE92ABCD43490FC253A2 | SHA256:128F15E6E19D6ACADF04F30C3CE898B403D9529F2F2AA59FFB9E810768E5C647 | |||
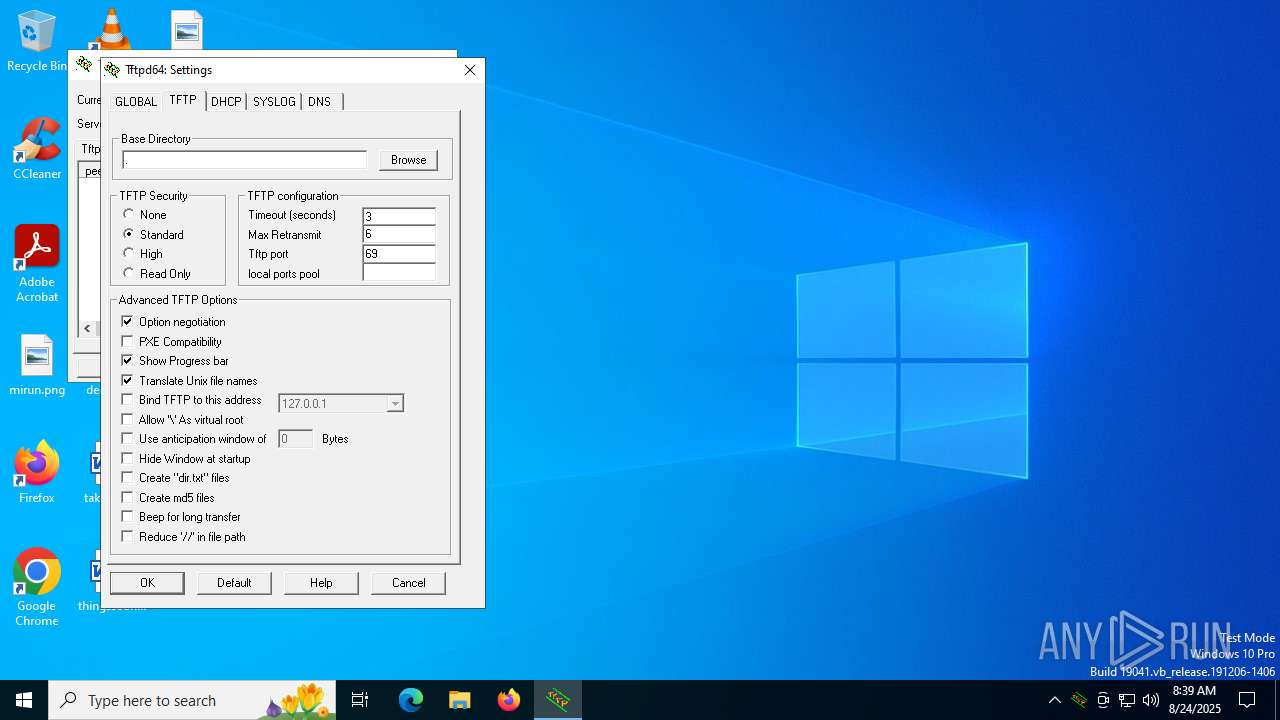
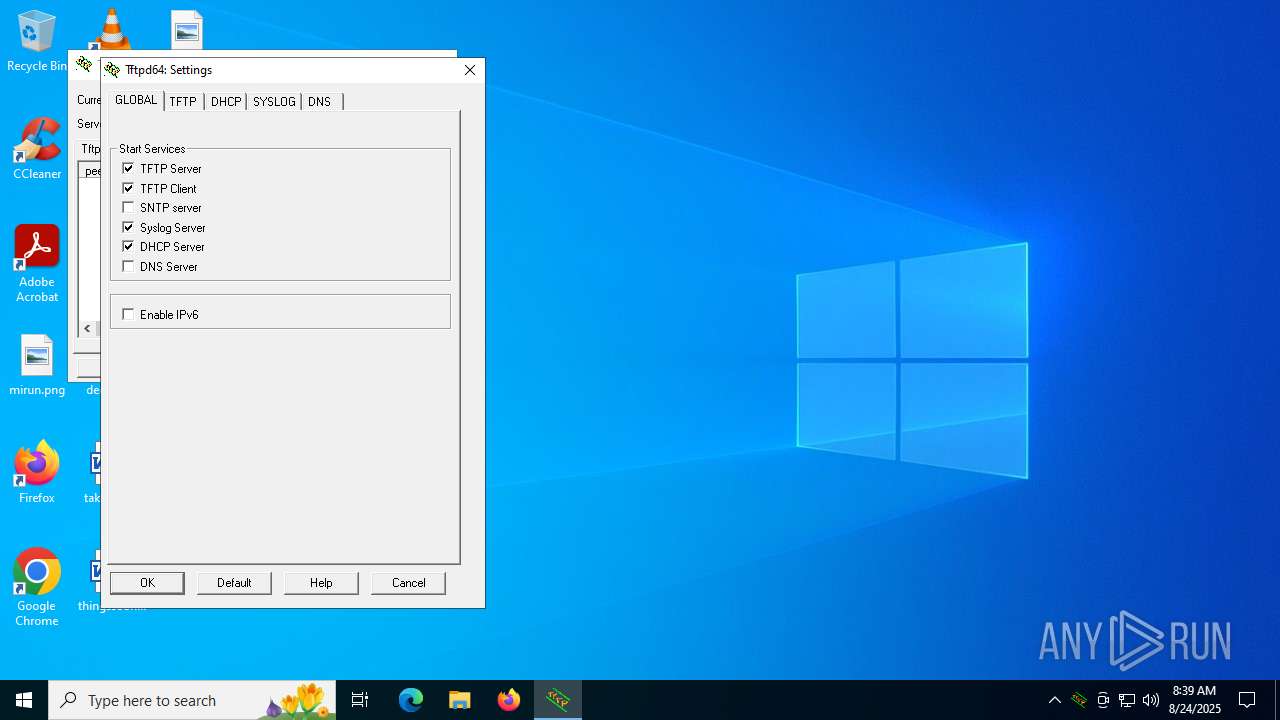
| 2192 | Tftpd64_Installer_v4.71.exe | C:\Program Files\Tftpd64\tftpd32.ini | text | |
MD5:C973075D00B0BF2D5C4CB18155AD92FB | SHA256:0C00CBDAE4E3F2F430CA803E2E08BB3CBBA4E83CF9024DBB64DA212B8034E60D | |||
| 2192 | Tftpd64_Installer_v4.71.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Tftpd64\Tftpd64.lnk | binary | |
MD5:7CC9B86B874BC6B3B8D7B69AEC43E503 | SHA256:927C97B9288E7BEDDFA45F6DC7408B42D34238CFD43E2BC200B0D5F7D825CEC2 | |||
| 2192 | Tftpd64_Installer_v4.71.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Tftpd64\Help.lnk | binary | |
MD5:7A448A937D4A7F7439C153541631601D | SHA256:5E379723F3D10B309487D7685C0F0E968ACD9B8A1BC7087A629994C4DA9F6D3D | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
31
DNS requests
24
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1268 | svchost.exe | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 69.192.161.161:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5328 | SearchApp.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
892 | SIHClient.exe | GET | 200 | 69.192.161.161:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6936 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5328 | SearchApp.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
5328 | SearchApp.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEApDqVCbATUviZV57HIIulA%3D | unknown | — | — | whitelisted |
892 | SIHClient.exe | GET | 200 | 69.192.161.161:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5944 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1268 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5468 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1268 | svchost.exe | 23.216.77.28:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1268 | svchost.exe | 69.192.161.161:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5328 | SearchApp.exe | 2.16.241.205:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
5328 | SearchApp.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
5328 | SearchApp.exe | 204.79.197.222:443 | fp.msedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
fp.msedge.net |
| whitelisted |
login.live.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
Process | Message |
|---|---|
tftpd64.exe | Th 3580 :opening comm socket
|
tftpd64.exe | Th 3580 :Console disconnected |
tftpd64.exe | Th 6820 :Port 17152 may be reused
|
tftpd64.exe | Th 6452 :connected to console
|
tftpd64.exe | Th 3580 :Verify Console/GUI parameters
|
tftpd64.exe | Th 3580 :Version check OK
|
tftpd64.exe | Th 6452 :GUI Version check OK
|
tftpd64.exe | Th 3580 :Console connected |
tftpd64.exe | Th 6796 :Scheduler signal received |
tftpd64.exe | Th 6452 :GUI: new service 4 status 4
|