| File name: | B18903F14C92F3B9D3D08CA13A39EFDD.exe |
| Full analysis: | https://app.any.run/tasks/7d87615f-fb62-484f-9ae7-71330e3b657b |
| Verdict: | No threats detected |
| Analysis date: | March 21, 2019, 01:01:22 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed |
| MD5: | B18903F14C92F3B9D3D08CA13A39EFDD |
| SHA1: | D146AF98EB5CE7A3ECBFF8163EEF002458A1F442 |
| SHA256: | AA00AAD043D88370E5225A1DABAE3EA49CC703A9575EDD41F24263B013C2F949 |
| SSDEEP: | 24576:+PQRqBbikTHaaS3imkNQo1mLw+N4HtSzxGp1XCStb6ZDKb:LpoHar3BMQoEBu6UpNtoDKb |
MALICIOUS
Application was dropped or rewritten from another process
- autorun.exe (PID: 2460)
- PortQry.exe (PID: 2500)
- choice.exe (PID: 3136)
SUSPICIOUS
Executable content was dropped or overwritten
- B18903F14C92F3B9D3D08CA13A39EFDD.exe (PID: 400)
- autorun.exe (PID: 2460)
Starts CMD.EXE for commands execution
- B18903F14C92F3B9D3D08CA13A39EFDD.exe (PID: 400)
- autorun.exe (PID: 2460)
Uses REG.EXE to modify Windows registry
- cmd.exe (PID: 1004)
Reads Environment values
- reg.exe (PID: 2684)
INFO
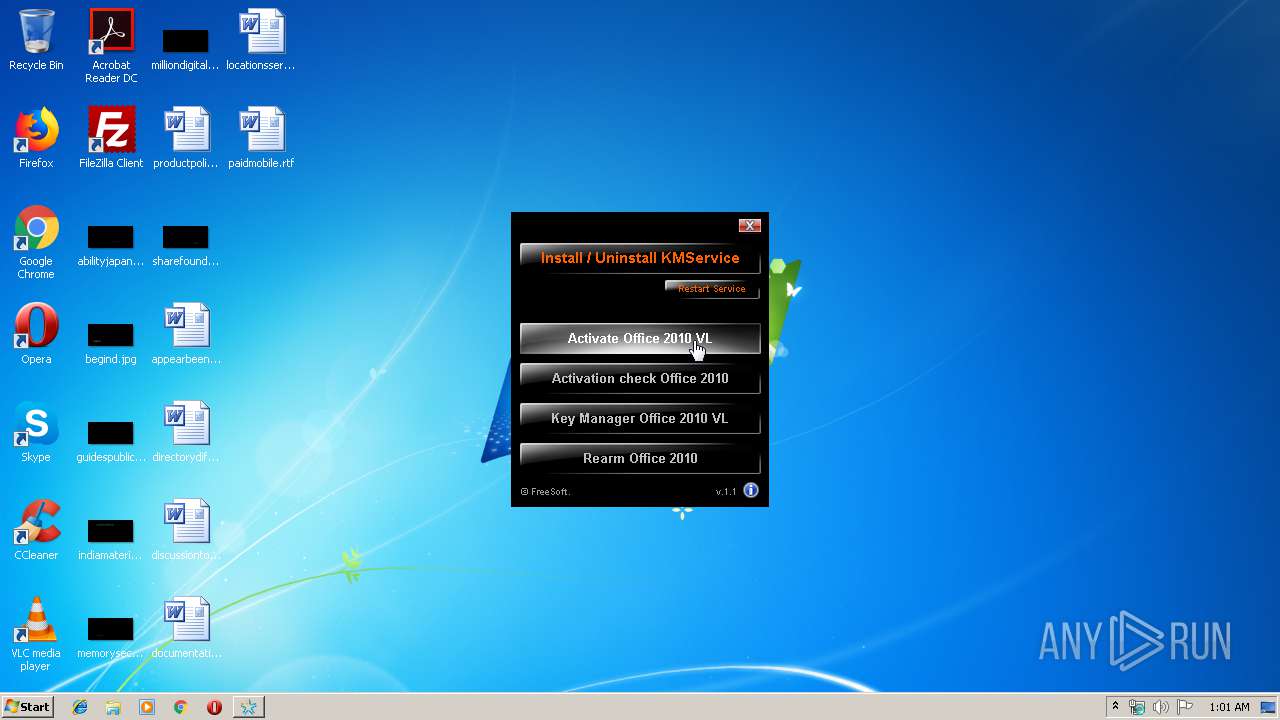
Reads Microsoft Office registry keys
- reg.exe (PID: 2580)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (39.3) |
|---|---|---|
| .exe | | | Win32 EXE Yoda's Crypter (38.6) |
| .dll | | | Win32 Dynamic Link Library (generic) (9.5) |
| .exe | | | Win32 Executable (generic) (6.5) |
| .exe | | | Generic Win/DOS Executable (2.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2009:02:07 07:33:08+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.5 |
| CodeSize: | 1036288 |
| InitializedDataSize: | 32768 |
| UninitializedDataSize: | 1454080 |
| EntryPoint: | 0x25fba0 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.1.0.0 |
| ProductVersionNumber: | 1.1.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | Debug, Pre-release, Private build |
| FileOS: | Windows 16-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
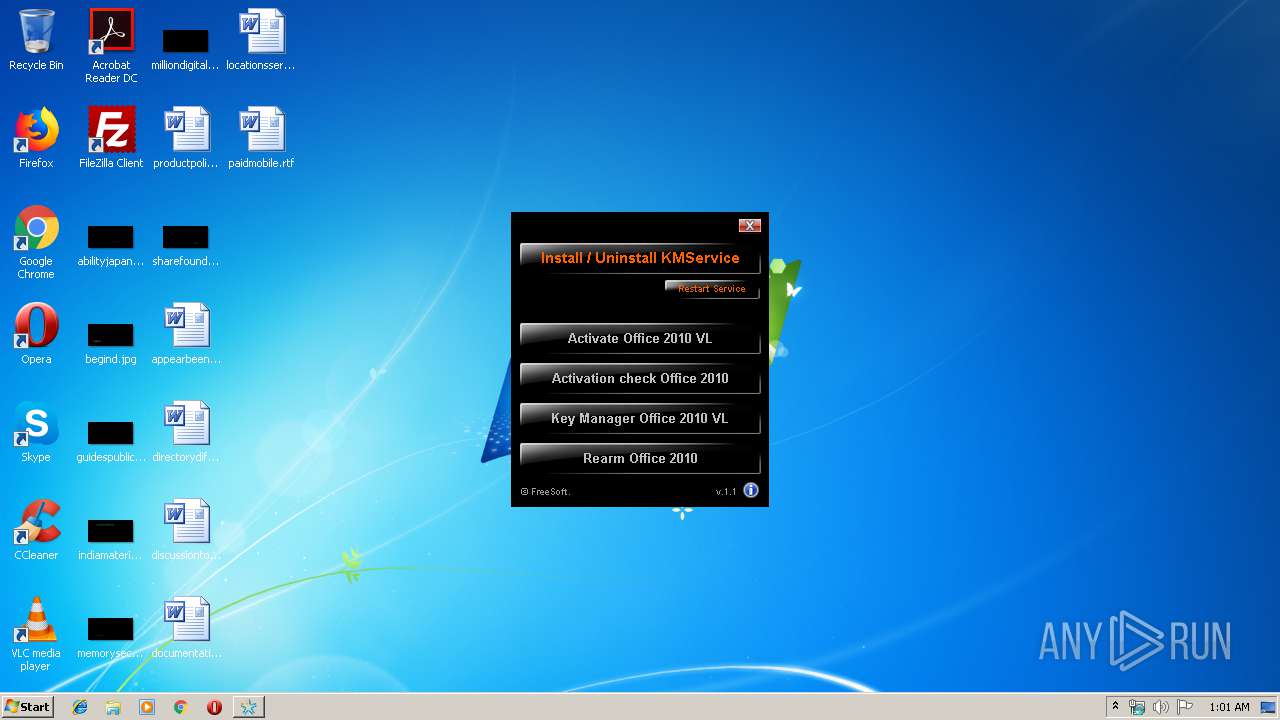
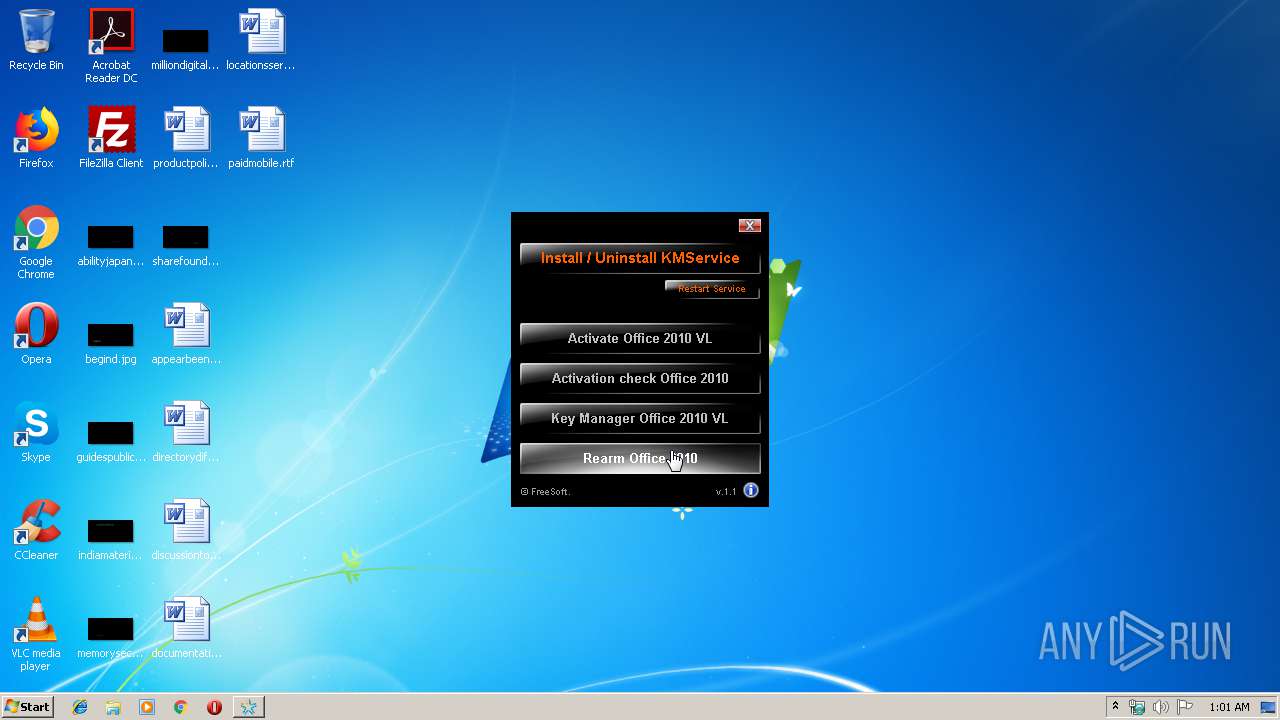
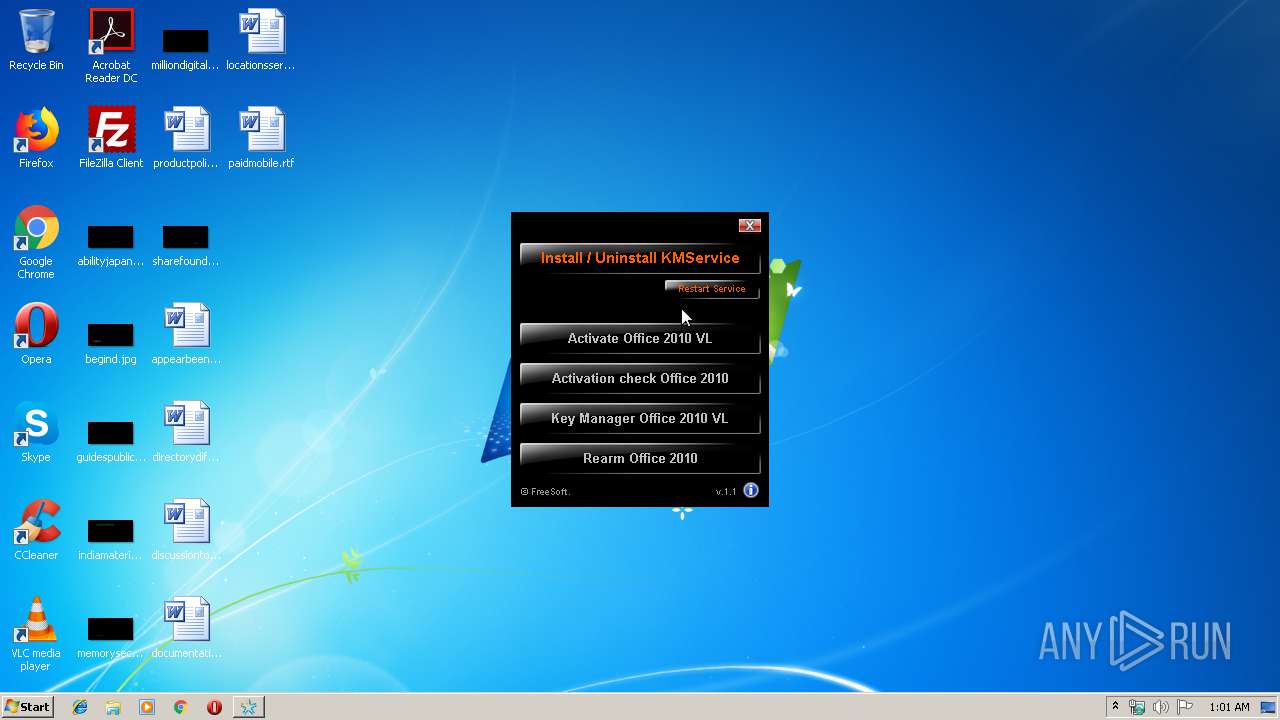
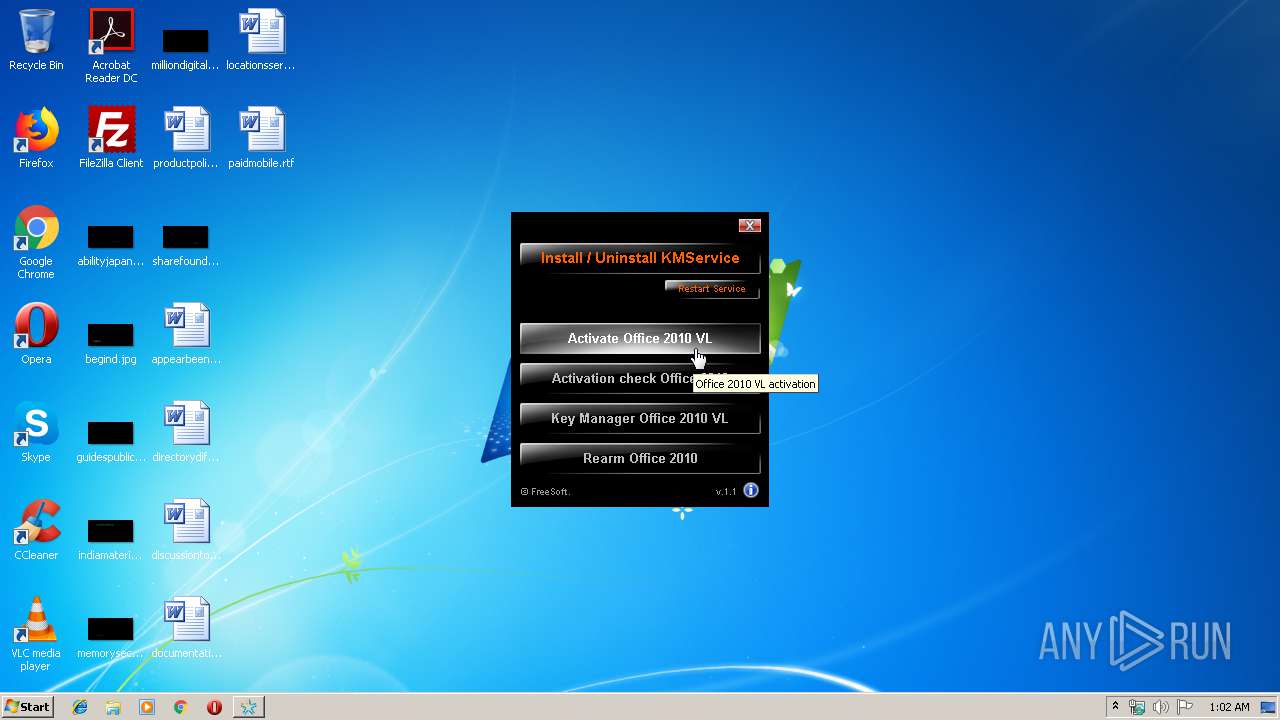
| CompanyName: | FreeSoft |
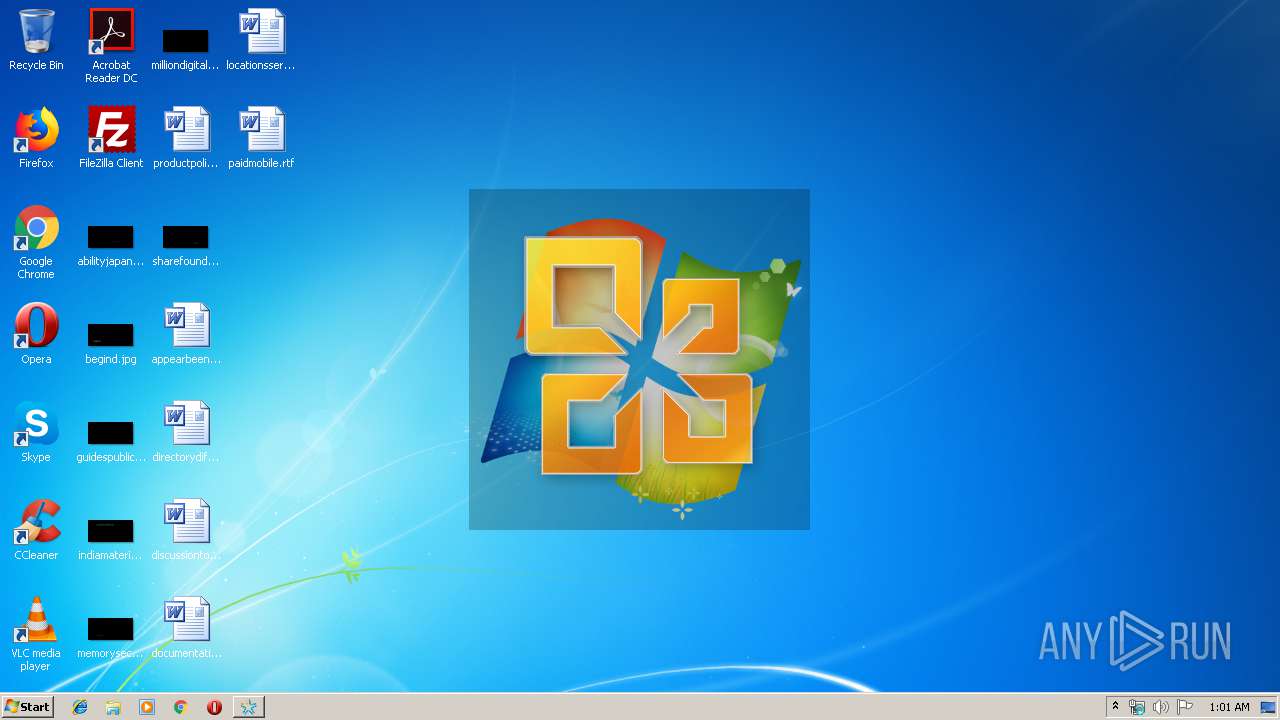
| FileDescription: | mini-KMS Activator |
| FileVersion: | 1,1,0,0 |
| ProductName: | mini-KMS_Activator_v1.1_Office2010_VL.exe |
| InternalName: | mini-KMS Activator v1.1 Office2010 VL |
| ProductVersion: | 1,1,0,0 |
| LegalCopyright: | © 2010, FreeSoft |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 07-Feb-2009 06:33:08 |
| Detected languages: |
|
| CompanyName: | FreeSoft |
| FileDescription: | mini-KMS Activator |
| FileVersion: | 1,1,0,0 |
| ProductName: | mini-KMS_Activator_v1.1_Office2010_VL.exe |
| InternalName: | mini-KMS Activator v1.1 Office2010 VL |
| ProductVersion: | 1,1,0,0 |
| LegalCopyright: | © 2010, FreeSoft |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 07-Feb-2009 06:33:08 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
UPX0 | 0x00001000 | 0x00163000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
UPX1 | 0x00164000 | 0x000FD000 | 0x000FC800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.99975 |
.rsrc | 0x00261000 | 0x00008000 | 0x00007400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.25129 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.09999 | 668 | Latin 1 / Western European | UNKNOWN | RT_MANIFEST |
2 | 4.23303 | 2216 | Latin 1 / Western European | UNKNOWN | RT_ICON |
3 | 3.21662 | 1736 | Latin 1 / Western European | UNKNOWN | RT_ICON |
4 | 1.98904 | 1384 | Latin 1 / Western European | UNKNOWN | RT_ICON |
5 | 3.87329 | 9640 | Latin 1 / Western European | UNKNOWN | RT_ICON |
6 | 4.15792 | 4264 | Latin 1 / Western European | UNKNOWN | RT_ICON |
7 | 4.74851 | 2440 | Latin 1 / Western European | UNKNOWN | RT_ICON |
8 | 5.0637 | 1128 | Latin 1 / Western European | UNKNOWN | RT_ICON |
B | 5.63321 | 51 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
F | 0 | 2401694 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
Imports
COMCTL32.dll |
GDI32.dll |
KERNEL32.DLL |
MSVCRT.dll |
OLE32.dll |
SHELL32.dll |
USER32.dll |
Total processes
45
Monitored processes
11
Malicious processes
0
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 400 | "C:\Users\admin\AppData\Local\Temp\B18903F14C92F3B9D3D08CA13A39EFDD.exe" | C:\Users\admin\AppData\Local\Temp\B18903F14C92F3B9D3D08CA13A39EFDD.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 680 | findstr /i 5.1 | C:\Windows\system32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (QGREP) Utility Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1004 | cmd /c ""C:\Users\admin\AppData\Local\Temp\8DEF.tmp\Act.cmd" " | C:\Windows\system32\cmd.exe | — | autorun.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1016 | "C:\Users\admin\AppData\Local\Temp\B18903F14C92F3B9D3D08CA13A39EFDD.exe" | C:\Users\admin\AppData\Local\Temp\B18903F14C92F3B9D3D08CA13A39EFDD.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 2148 | cmd /c ""C:\Users\admin\AppData\Local\Temp\8DEF.tmp\Start.cmd" " | C:\Windows\system32\cmd.exe | — | B18903F14C92F3B9D3D08CA13A39EFDD.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2460 | autorun.exe | C:\Users\admin\AppData\Local\Temp\8DEF.tmp\autorun.exe | cmd.exe | ||||||||||||
User: admin Company: FreeSoft Integrity Level: HIGH Description: mini-KMS Activator Office 2010 VL Exit code: 0 Version: 1.1.0.0 Modules
| |||||||||||||||
| 2500 | PortQry -n 127.0.0.1 -e 1688 | C:\Users\admin\AppData\Local\Temp\8DEF.tmp\PortQry.exe | cmd.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 1 Modules
| |||||||||||||||
| 2580 | REG QUERY "HKLM\SOFTWARE\Microsoft\Office\14.0" /s | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2684 | REG QUERY "HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion" /v CurrentVersion | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
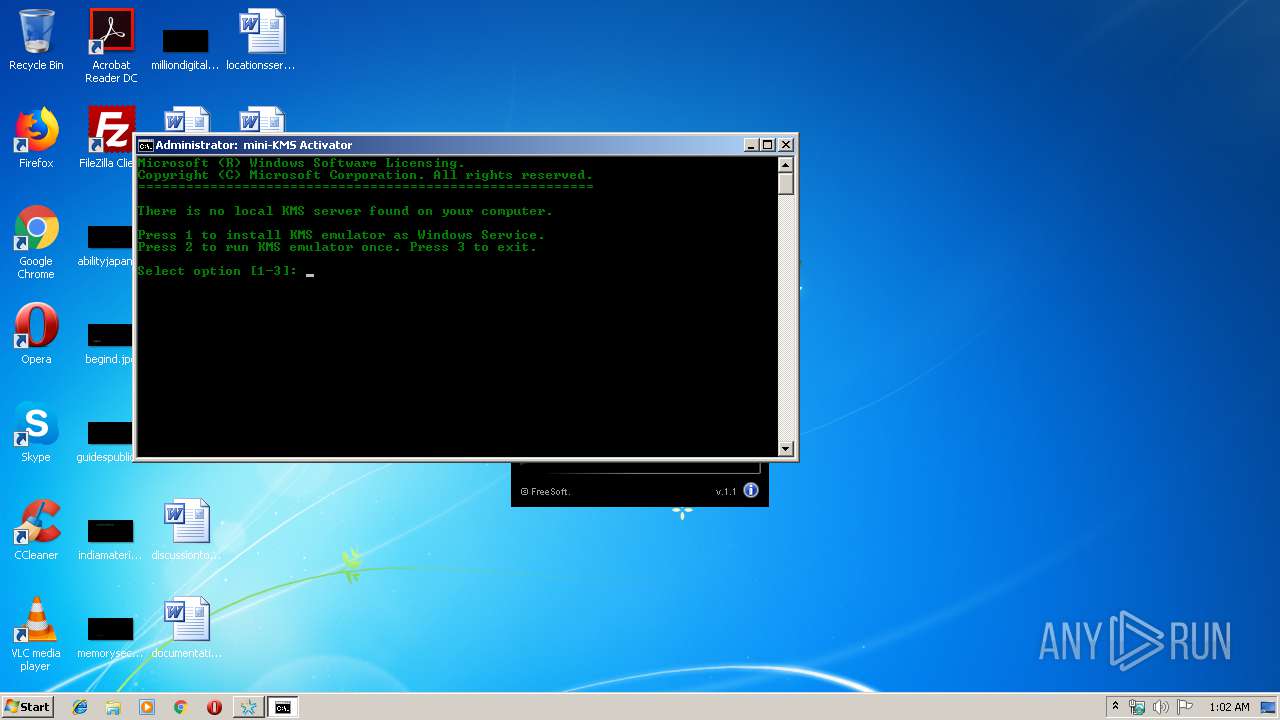
| 3136 | choice /C 123 /N /M "Select option [1-3]: " | C:\Users\admin\AppData\Local\Temp\8DEF.tmp\choice.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Offers the user a choice Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 711
Read events
1 703
Write events
8
Delete events
0
Modification events
| (PID) Process: | (400) B18903F14C92F3B9D3D08CA13A39EFDD.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (400) B18903F14C92F3B9D3D08CA13A39EFDD.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2460) autorun.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2460) autorun.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
11
Suspicious files
0
Text files
14
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 400 | B18903F14C92F3B9D3D08CA13A39EFDD.exe | C:\Users\admin\AppData\Local\Temp\8DEF.tmp\slerror.xml | text | |
MD5:DF1EF05879E06C5F09F3E1022F37B5CB | SHA256:D49ADF2DABBBF6AA43CE4E336AF4F768207DF75302EBF568A94A5350AAC988C5 | |||
| 400 | B18903F14C92F3B9D3D08CA13A39EFDD.exe | C:\Users\admin\AppData\Local\Temp\8DEF.tmp\hidcon.exe | executable | |
MD5:B2DADAB18C318443301D0087CD7200BA | SHA256:B88A4D442BCD94457FC75DC5A541DC3437FD01091A2B6500569C699260E65238 | |||
| 400 | B18903F14C92F3B9D3D08CA13A39EFDD.exe | C:\Users\admin\AppData\Local\Temp\8DEF.tmp\autorun.exe | executable | |
MD5:9756DC84DD17E58C4B4AABA3279364D3 | SHA256:0FCE14A187AAE773CE1A30E331AAD0B36EA5D1B830E450F81EB7E9F4899EE9CC | |||
| 400 | B18903F14C92F3B9D3D08CA13A39EFDD.exe | C:\Users\admin\AppData\Local\Temp\8DEF.tmp\choice.exe | executable | |
MD5:11DDFBF834BB2C6F4D23297D80EE9E45 | SHA256:4108605207EF00FCBBFE7ED7C3F96300601FB79F913D0E290538E8E02082CACC | |||
| 400 | B18903F14C92F3B9D3D08CA13A39EFDD.exe | C:\Users\admin\AppData\Local\Temp\8DEF.tmp\cscript.exe | executable | |
MD5:34098403F9D8F71CE2EC749122168E89 | SHA256:12DF0B06A9B56DCE3EFDB85984F84B387B1A5B61C9EBBF5A3BD61A5FBB996F60 | |||
| 400 | B18903F14C92F3B9D3D08CA13A39EFDD.exe | C:\Users\admin\AppData\Local\Temp\8DEF.tmp\instsrv.exe | executable | |
MD5:9F7ACAAD365AF0D1A3CD9261E3208B9B | SHA256:F7B0A444B590EB8A6B46CEDF544BCB3117C85CAB02B599B45D61B8A590095C9C | |||
| 2460 | autorun.exe | C:\Users\admin\AppData\Local\Temp\apm910C.tmp | — | |
MD5:— | SHA256:— | |||
| 2460 | autorun.exe | C:\Users\admin\AppData\Local\Temp\apm910D.tmp | — | |
MD5:— | SHA256:— | |||
| 400 | B18903F14C92F3B9D3D08CA13A39EFDD.exe | C:\Users\admin\AppData\Local\Temp\8DEF.tmp\KMService.exe | executable | |
MD5:82865FF17BC664C711EFA674759F9991 | SHA256:F85CD6F93BA18E642D50BEC7FC6AEB9D8751CC49B3BE5650DD5C556628545524 | |||
| 400 | B18903F14C92F3B9D3D08CA13A39EFDD.exe | C:\Users\admin\AppData\Local\Temp\8DEF.tmp\PortQry.exe | executable | |
MD5:C6AC67F4076CA431ACC575912C194245 | SHA256:FB6CEBADD49D202C8C7B5CDD641BD16AAC8258429E8FACE365A94BD32E253B00 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report