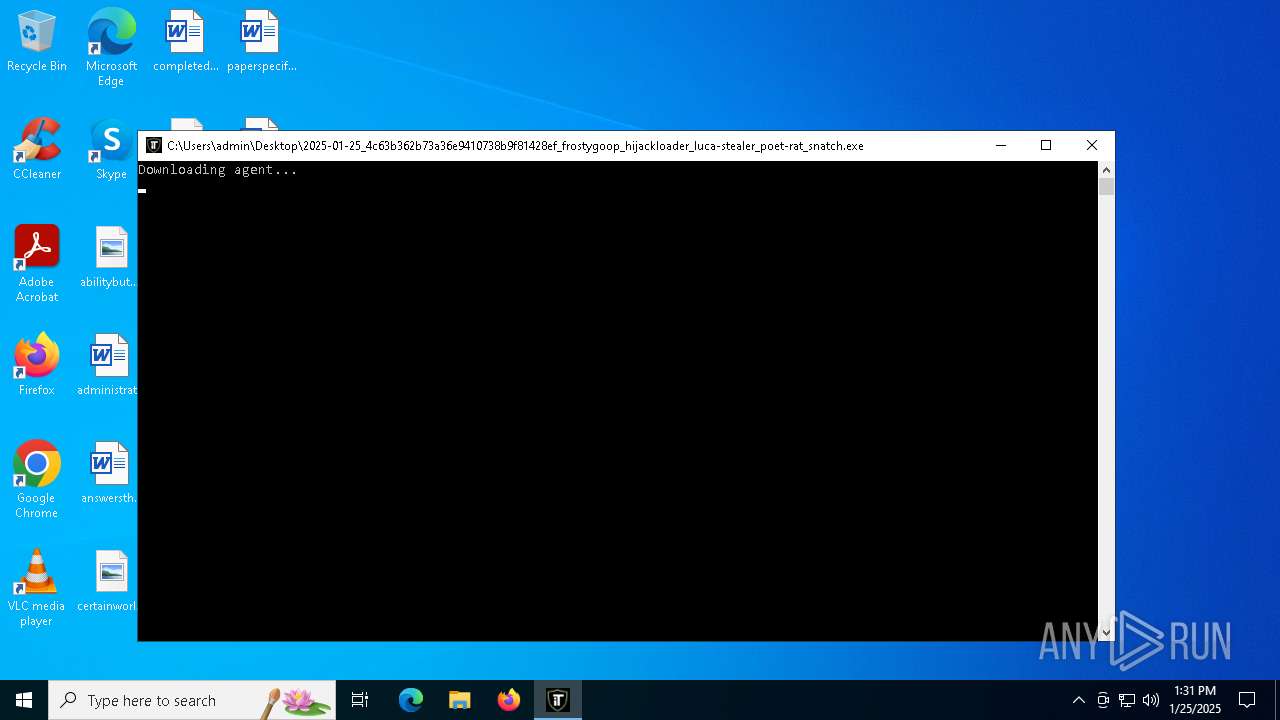
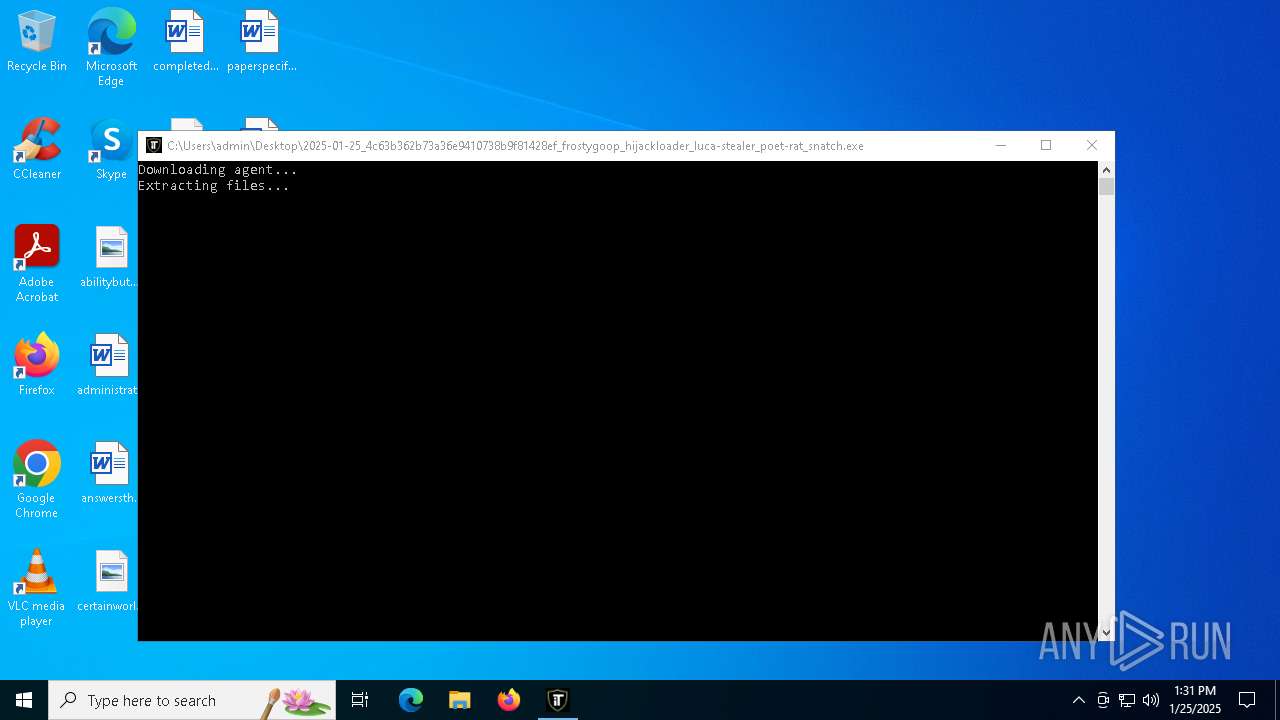
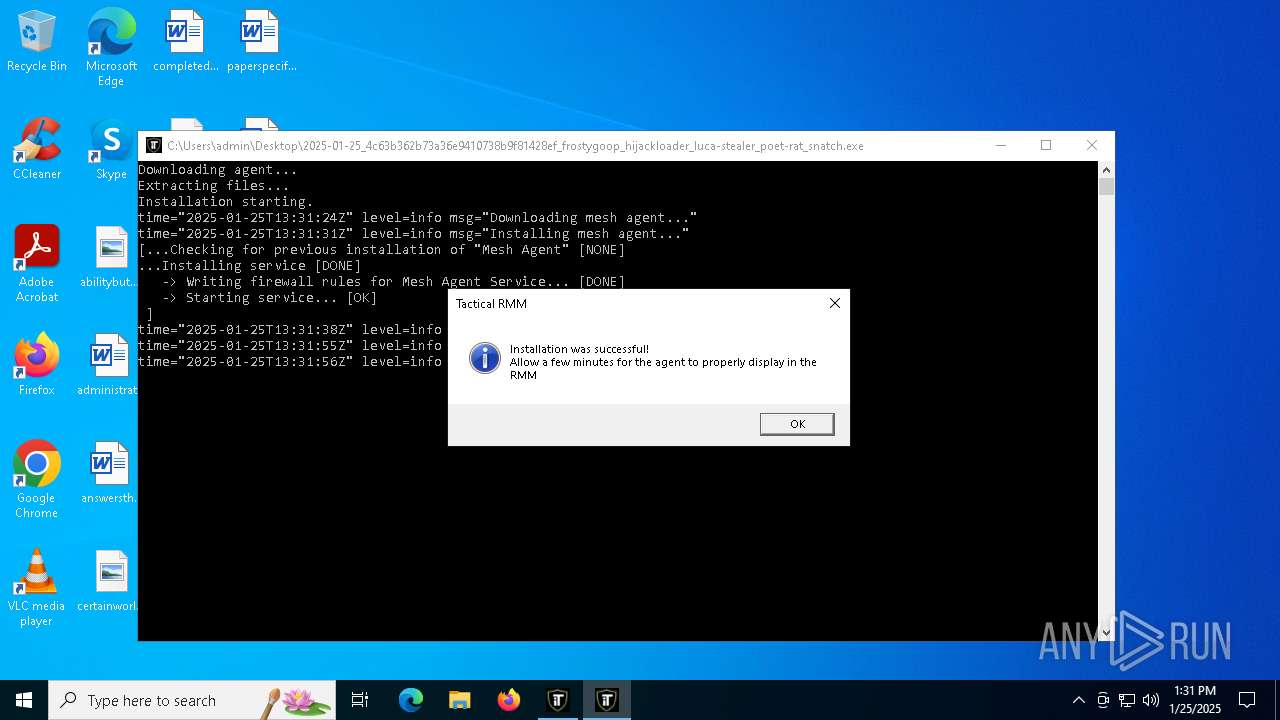
| File name: | 2025-01-25_4c63b362b73a36e9410738b9f81428ef_frostygoop_hijackloader_luca-stealer_poet-rat_snatch |
| Full analysis: | https://app.any.run/tasks/b3b47400-4708-429f-ab0e-cf50bceb970a |
| Verdict: | Malicious activity |
| Threats: | A loader is malicious software that infiltrates devices to deliver malicious payloads. This malware is capable of infecting victims’ computers, analyzing their system information, and installing other types of threats, such as trojans or stealers. Criminals usually deliver loaders through phishing emails and links by relying on social engineering to trick users into downloading and running their executables. Loaders employ advanced evasion and persistence tactics to avoid detection. |
| Analysis date: | January 25, 2025, 13:30:52 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (console) x86-64 (stripped to external PDB), for MS Windows, 7 sections |
| MD5: | 4C63B362B73A36E9410738B9F81428EF |
| SHA1: | 32824D470F193773E515870C9D3CF8DFA076B2A6 |
| SHA256: | A9FCD874776F3F25782F85303CEC11AC2C2E599D05E3D8A3EC3CB5E253BF7D12 |
| SSDEEP: | 98304:f9Ogc4grqaOh8gJphW4ZSCC41ZYQau6qA:XK |
MALICIOUS
Starts NET.EXE for service management
- net.exe (PID: 2084)
- cmd.exe (PID: 3560)
- cmd.exe (PID: 4244)
- net.exe (PID: 5788)
- cmd.exe (PID: 5160)
- net.exe (PID: 2424)
- cmd.exe (PID: 556)
- net.exe (PID: 5764)
- net.exe (PID: 6648)
- powershell.exe (PID: 5544)
- net.exe (PID: 4708)
- net.exe (PID: 5092)
Changes the Windows auto-update feature
- tacticalrmm.exe (PID: 4528)
Bypass execution policy to execute commands
- powershell.exe (PID: 5544)
- powershell.exe (PID: 1140)
- powershell.exe (PID: 4628)
- powershell.exe (PID: 204)
- powershell.exe (PID: 6572)
- powershell.exe (PID: 7136)
Changes powershell execution policy (Bypass)
- tacticalrmm.exe (PID: 3540)
- tacticalrmm.exe (PID: 3632)
- tacticalrmm.exe (PID: 4972)
- tacticalrmm.exe (PID: 3840)
- tacticalrmm.exe (PID: 6400)
- tacticalrmm.exe (PID: 5040)
Executing a file with an untrusted certificate
- rustdesk.exe (PID: 2996)
- rustdesk.exe (PID: 3420)
- rustdesk.exe (PID: 6880)
- rustdesk.exe (PID: 1292)
- rustdesk.exe (PID: 7160)
- rustdesk.exe (PID: 6912)
- rustdesk.exe (PID: 6972)
- rustdesk.exe (PID: 6476)
- rustdesk.exe (PID: 2392)
- rustdesk.exe (PID: 6804)
- rustdesk.exe (PID: 5684)
- rustdesk.exe (PID: 6488)
Create files in the Startup directory
- cmd.exe (PID: 6420)
Downloads the requested resource (POWERSHELL)
- powershell.exe (PID: 7136)
RUSTDESK has been detected (SURICATA)
- svchost.exe (PID: 2192)
- rustdesk.exe (PID: 2392)
- rustdesk.exe (PID: 6912)
SUSPICIOUS
Executable content was dropped or overwritten
- 2025-01-25_4c63b362b73a36e9410738b9f81428ef_frostygoop_hijackloader_luca-stealer_poet-rat_snatch.exe (PID: 5992)
- tacticalagent-v2.8.0-windows-amd64.exe (PID: 2072)
- tacticalagent-v2.8.0-windows-amd64.tmp (PID: 4652)
- tacticalrmm.exe (PID: 4528)
- meshagent.exe (PID: 5236)
- csc.exe (PID: 6904)
- tacticalrmm.exe (PID: 5040)
- rustdesk.exe (PID: 3420)
- xcopy.exe (PID: 6924)
Reads the Windows owner or organization settings
- tacticalagent-v2.8.0-windows-amd64.tmp (PID: 4652)
Runs PING.EXE to delay simulation
- cmd.exe (PID: 3560)
- cmd.exe (PID: 5160)
Starts CMD.EXE for commands execution
- tacticalagent-v2.8.0-windows-amd64.tmp (PID: 4652)
- tacticalrmm.exe (PID: 5236)
- rustdesk.exe (PID: 2996)
- powershell.exe (PID: 5544)
- rustdesk.exe (PID: 6912)
- rustdesk.exe (PID: 2392)
Creates or modifies Windows services
- tacticalrmm.exe (PID: 2632)
- tacticalrmm.exe (PID: 4528)
- meshagent.exe (PID: 5236)
- tacticalrmm.exe (PID: 5040)
- tacticalrmm.exe (PID: 5236)
- tacticalrmm.exe (PID: 4972)
- tacticalrmm.exe (PID: 3840)
- tacticalrmm.exe (PID: 3540)
- tacticalrmm.exe (PID: 2456)
- tacticalrmm.exe (PID: 3632)
- tacticalrmm.exe (PID: 6400)
Windows service management via SC.EXE
- sc.exe (PID: 4716)
- sc.exe (PID: 5920)
- sc.exe (PID: 6316)
- sc.exe (PID: 3820)
- sc.exe (PID: 6336)
- sc.exe (PID: 3208)
- sc.exe (PID: 3936)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 5740)
- rustdesk.exe (PID: 3420)
- cmd.exe (PID: 6420)
- cmd.exe (PID: 6244)
- cmd.exe (PID: 6392)
MeshAgent potential remote access (YARA)
- tacticalrmm.exe (PID: 4528)
There is functionality for taking screenshot (YARA)
- tacticalrmm.exe (PID: 4528)
There is functionality for capture public ip (YARA)
- tacticalrmm.exe (PID: 4528)
Creates a software uninstall entry
- meshagent.exe (PID: 5236)
- reg.exe (PID: 6956)
- reg.exe (PID: 6968)
- reg.exe (PID: 6148)
- reg.exe (PID: 6192)
- reg.exe (PID: 6240)
- reg.exe (PID: 6424)
- reg.exe (PID: 6504)
- reg.exe (PID: 6460)
- reg.exe (PID: 6580)
- reg.exe (PID: 6500)
- reg.exe (PID: 6432)
- reg.exe (PID: 2456)
- reg.exe (PID: 3920)
Executes as Windows Service
- MeshAgent.exe (PID: 5548)
- tacticalrmm.exe (PID: 5040)
- rustdesk.exe (PID: 7160)
- rustdesk.exe (PID: 1668)
- rustdesk.exe (PID: 6780)
Searches for installed software
- tacticalrmm.exe (PID: 4528)
- tacticalrmm.exe (PID: 5040)
- reg.exe (PID: 6956)
- reg.exe (PID: 6968)
- reg.exe (PID: 6148)
- reg.exe (PID: 6192)
- reg.exe (PID: 6460)
- reg.exe (PID: 6424)
- reg.exe (PID: 6240)
- reg.exe (PID: 6504)
- reg.exe (PID: 6580)
- reg.exe (PID: 6432)
- reg.exe (PID: 6500)
- rustdesk.exe (PID: 7160)
- reg.exe (PID: 2456)
- reg.exe (PID: 3920)
- rustdesk.exe (PID: 1668)
- rustdesk.exe (PID: 6912)
- rustdesk.exe (PID: 2996)
- rustdesk.exe (PID: 6476)
- rustdesk.exe (PID: 6972)
- rustdesk.exe (PID: 6804)
- rustdesk.exe (PID: 5684)
- rustdesk.exe (PID: 6780)
- rustdesk.exe (PID: 6488)
- rustdesk.exe (PID: 2392)
Checks for external IP
- svchost.exe (PID: 2192)
- tacticalrmm.exe (PID: 5040)
The process executes via Task Scheduler
- tacticalrmm.exe (PID: 5236)
- tacticalrmm.exe (PID: 3632)
- tacticalrmm.exe (PID: 3840)
- tacticalrmm.exe (PID: 3540)
- tacticalrmm.exe (PID: 4972)
- tacticalrmm.exe (PID: 2456)
Executing commands from a ".bat" file
- tacticalrmm.exe (PID: 5236)
- rustdesk.exe (PID: 2996)
Starts POWERSHELL.EXE for commands execution
- tacticalrmm.exe (PID: 3540)
- tacticalrmm.exe (PID: 3632)
- tacticalrmm.exe (PID: 4972)
- tacticalrmm.exe (PID: 3840)
- tacticalrmm.exe (PID: 6400)
- tacticalrmm.exe (PID: 5040)
The process bypasses the loading of PowerShell profile settings
- tacticalrmm.exe (PID: 3540)
- tacticalrmm.exe (PID: 3632)
- tacticalrmm.exe (PID: 4972)
- tacticalrmm.exe (PID: 3840)
- tacticalrmm.exe (PID: 6400)
- tacticalrmm.exe (PID: 5040)
The process executes Powershell scripts
- tacticalrmm.exe (PID: 3540)
- tacticalrmm.exe (PID: 3632)
- tacticalrmm.exe (PID: 4972)
- tacticalrmm.exe (PID: 3840)
- tacticalrmm.exe (PID: 6400)
- tacticalrmm.exe (PID: 5040)
The process hide an interactive prompt from the user
- tacticalrmm.exe (PID: 3632)
- tacticalrmm.exe (PID: 3540)
- tacticalrmm.exe (PID: 4972)
- tacticalrmm.exe (PID: 3840)
- tacticalrmm.exe (PID: 6400)
- tacticalrmm.exe (PID: 5040)
Uses powercfg.exe to modify the power settings
- cmd.exe (PID: 3816)
Application launched itself
- tacticalrmm.exe (PID: 5040)
- rustdesk.exe (PID: 1668)
- rustdesk.exe (PID: 6912)
- rustdesk.exe (PID: 6780)
- rustdesk.exe (PID: 2392)
CSC.EXE is used to compile C# code
- csc.exe (PID: 6904)
Process drops python dynamic module
- tacticalrmm.exe (PID: 5040)
Process drops legitimate windows executable
- tacticalrmm.exe (PID: 5040)
- rustdesk.exe (PID: 3420)
Gets or sets the security protocol (POWERSHELL)
- powershell.exe (PID: 7136)
Reads the date of Windows installation
- rustdesk.exe (PID: 2996)
Reads security settings of Internet Explorer
- rustdesk.exe (PID: 2996)
Starts application with an unusual extension
- cmd.exe (PID: 6420)
Stops a currently running service
- sc.exe (PID: 4672)
- sc.exe (PID: 7028)
- sc.exe (PID: 1920)
Uses NETSH.EXE to delete a firewall rule or allowed programs
- cmd.exe (PID: 6420)
Starts SC.EXE for service management
- cmd.exe (PID: 6420)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 6420)
Runs shell command (SCRIPT)
- cscript.exe (PID: 432)
- cscript.exe (PID: 7072)
- cscript.exe (PID: 3992)
The process executes VB scripts
- cmd.exe (PID: 6420)
Sets the service to start on system boot
- sc.exe (PID: 3188)
Creates a new Windows service
- sc.exe (PID: 2164)
Starts itself from another location
- rustdesk.exe (PID: 2996)
Uses NETSH.EXE to add a firewall rule or allowed programs
- cmd.exe (PID: 6420)
The process checks if it is being run in the virtual environment
- rustdesk.exe (PID: 6912)
- rustdesk.exe (PID: 2392)
Connects to unusual port
- rustdesk.exe (PID: 6912)
- rustdesk.exe (PID: 2392)
INFO
Creates files in the program directory
- 2025-01-25_4c63b362b73a36e9410738b9f81428ef_frostygoop_hijackloader_luca-stealer_poet-rat_snatch.exe (PID: 5992)
- tacticalrmm.exe (PID: 2632)
- tacticalagent-v2.8.0-windows-amd64.tmp (PID: 4652)
- tacticalrmm.exe (PID: 4528)
- meshagent.exe (PID: 5236)
- MeshAgent.exe (PID: 5548)
- tacticalrmm.exe (PID: 5040)
- tacticalrmm.exe (PID: 3632)
- tacticalrmm.exe (PID: 3540)
- tacticalrmm.exe (PID: 5236)
- tacticalrmm.exe (PID: 2456)
- tacticalrmm.exe (PID: 4972)
- tacticalrmm.exe (PID: 3840)
- tacticalrmm.exe (PID: 6400)
- xcopy.exe (PID: 6924)
- cmd.exe (PID: 6420)
Checks supported languages
- 2025-01-25_4c63b362b73a36e9410738b9f81428ef_frostygoop_hijackloader_luca-stealer_poet-rat_snatch.exe (PID: 5992)
- tacticalagent-v2.8.0-windows-amd64.exe (PID: 2072)
- tacticalagent-v2.8.0-windows-amd64.tmp (PID: 4652)
- tacticalrmm.exe (PID: 2632)
- tacticalrmm.exe (PID: 4528)
- meshagent.exe (PID: 5236)
- MeshAgent.exe (PID: 5548)
- MeshAgent.exe (PID: 628)
- tacticalrmm.exe (PID: 5040)
- tacticalrmm.exe (PID: 3632)
- tacticalrmm.exe (PID: 5236)
- tacticalrmm.exe (PID: 3840)
- tacticalrmm.exe (PID: 3540)
- tacticalrmm.exe (PID: 4972)
- tacticalrmm.exe (PID: 2456)
- tacticalrmm.exe (PID: 6400)
- csc.exe (PID: 6904)
- MeshAgent.exe (PID: 7020)
- cvtres.exe (PID: 6932)
- rustdesk.exe (PID: 3420)
- rustdesk.exe (PID: 2996)
- chcp.com (PID: 4516)
- rustdesk.exe (PID: 1292)
- chcp.com (PID: 5652)
- rustdesk.exe (PID: 6880)
- rustdesk.exe (PID: 7160)
- chcp.com (PID: 1744)
- rustdesk.exe (PID: 1668)
- rustdesk.exe (PID: 6912)
- rustdesk.exe (PID: 6476)
- rustdesk.exe (PID: 6972)
- rustdesk.exe (PID: 6804)
- rustdesk.exe (PID: 6780)
- rustdesk.exe (PID: 5684)
- rustdesk.exe (PID: 6488)
- rustdesk.exe (PID: 2392)
Reads the machine GUID from the registry
- 2025-01-25_4c63b362b73a36e9410738b9f81428ef_frostygoop_hijackloader_luca-stealer_poet-rat_snatch.exe (PID: 5992)
- tacticalrmm.exe (PID: 2632)
- tacticalrmm.exe (PID: 4528)
- MeshAgent.exe (PID: 5548)
- tacticalrmm.exe (PID: 5040)
- tacticalrmm.exe (PID: 3632)
- tacticalrmm.exe (PID: 2456)
- tacticalrmm.exe (PID: 3540)
- tacticalrmm.exe (PID: 5236)
- tacticalrmm.exe (PID: 4972)
- csc.exe (PID: 6904)
- tacticalrmm.exe (PID: 6400)
- tacticalrmm.exe (PID: 3840)
- rustdesk.exe (PID: 6912)
- rustdesk.exe (PID: 6804)
- rustdesk.exe (PID: 5684)
- rustdesk.exe (PID: 2392)
Application based on Golang
- 2025-01-25_4c63b362b73a36e9410738b9f81428ef_frostygoop_hijackloader_luca-stealer_poet-rat_snatch.exe (PID: 5992)
- tacticalrmm.exe (PID: 4528)
Create files in a temporary directory
- tacticalagent-v2.8.0-windows-amd64.exe (PID: 2072)
- tacticalagent-v2.8.0-windows-amd64.tmp (PID: 4652)
The sample compiled with english language support
- 2025-01-25_4c63b362b73a36e9410738b9f81428ef_frostygoop_hijackloader_luca-stealer_poet-rat_snatch.exe (PID: 5992)
- tacticalagent-v2.8.0-windows-amd64.tmp (PID: 4652)
- tacticalrmm.exe (PID: 4528)
- meshagent.exe (PID: 5236)
- tacticalrmm.exe (PID: 5040)
- rustdesk.exe (PID: 3420)
- xcopy.exe (PID: 6924)
Reads the computer name
- 2025-01-25_4c63b362b73a36e9410738b9f81428ef_frostygoop_hijackloader_luca-stealer_poet-rat_snatch.exe (PID: 5992)
- tacticalagent-v2.8.0-windows-amd64.tmp (PID: 4652)
- tacticalrmm.exe (PID: 2632)
- tacticalrmm.exe (PID: 4528)
- meshagent.exe (PID: 5236)
- MeshAgent.exe (PID: 5548)
- MeshAgent.exe (PID: 628)
- tacticalrmm.exe (PID: 5040)
- tacticalrmm.exe (PID: 5236)
- tacticalrmm.exe (PID: 4972)
- tacticalrmm.exe (PID: 3540)
- tacticalrmm.exe (PID: 3840)
- tacticalrmm.exe (PID: 2456)
- tacticalrmm.exe (PID: 3632)
- tacticalrmm.exe (PID: 6400)
- MeshAgent.exe (PID: 7020)
- rustdesk.exe (PID: 2996)
- rustdesk.exe (PID: 6880)
- rustdesk.exe (PID: 1292)
- rustdesk.exe (PID: 7160)
- rustdesk.exe (PID: 1668)
- rustdesk.exe (PID: 6912)
- rustdesk.exe (PID: 6476)
- rustdesk.exe (PID: 6972)
- rustdesk.exe (PID: 6780)
- rustdesk.exe (PID: 5684)
- rustdesk.exe (PID: 6804)
- rustdesk.exe (PID: 6488)
- rustdesk.exe (PID: 2392)
Reads the software policy settings
- 2025-01-25_4c63b362b73a36e9410738b9f81428ef_frostygoop_hijackloader_luca-stealer_poet-rat_snatch.exe (PID: 5992)
- tacticalrmm.exe (PID: 4528)
- tacticalrmm.exe (PID: 5040)
- tacticalrmm.exe (PID: 2456)
- tacticalrmm.exe (PID: 3840)
- tacticalrmm.exe (PID: 3540)
- tacticalrmm.exe (PID: 3632)
- tacticalrmm.exe (PID: 5236)
- tacticalrmm.exe (PID: 4972)
- tacticalrmm.exe (PID: 6400)
- rustdesk.exe (PID: 2392)
Reads product name
- tacticalrmm.exe (PID: 2632)
- tacticalrmm.exe (PID: 4528)
- tacticalrmm.exe (PID: 2456)
- tacticalrmm.exe (PID: 3540)
- tacticalrmm.exe (PID: 4972)
- tacticalrmm.exe (PID: 5236)
- tacticalrmm.exe (PID: 3632)
- tacticalrmm.exe (PID: 3840)
- tacticalrmm.exe (PID: 5040)
- tacticalrmm.exe (PID: 6400)
- rustdesk.exe (PID: 2392)
Creates a software uninstall entry
- tacticalagent-v2.8.0-windows-amd64.tmp (PID: 4652)
Reads Environment values
- tacticalrmm.exe (PID: 2632)
- tacticalrmm.exe (PID: 4528)
- tacticalrmm.exe (PID: 5040)
- tacticalrmm.exe (PID: 5236)
- tacticalrmm.exe (PID: 2456)
- tacticalrmm.exe (PID: 3632)
- tacticalrmm.exe (PID: 3540)
- tacticalrmm.exe (PID: 4972)
- tacticalrmm.exe (PID: 3840)
- tacticalrmm.exe (PID: 6400)
- rustdesk.exe (PID: 2392)
Drops encrypted JS script (Microsoft Script Encoder)
- tacticalrmm.exe (PID: 4528)
- tacticalrmm.exe (PID: 3540)
- tacticalrmm.exe (PID: 3632)
- tacticalrmm.exe (PID: 4972)
- tacticalrmm.exe (PID: 2456)
- tacticalrmm.exe (PID: 3840)
- tacticalrmm.exe (PID: 5040)
- tacticalrmm.exe (PID: 6400)
Disables trace logs
- powershell.exe (PID: 5544)
- powershell.exe (PID: 7136)
Uses string replace method (POWERSHELL)
- powershell.exe (PID: 1140)
- powershell.exe (PID: 5544)
Uses string split method (POWERSHELL)
- powershell.exe (PID: 5544)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 204)
- powershell.exe (PID: 4628)
Changes the display of characters in the console
- cmd.exe (PID: 6420)
Gets data length (POWERSHELL)
- powershell.exe (PID: 5544)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 0000:00:00 00:00:00 |
| ImageFileCharacteristics: | Executable, Large address aware, No debug |
| PEType: | PE32+ |
| LinkerVersion: | 3 |
| CodeSize: | 2520576 |
| InitializedDataSize: | 246784 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x66fe0 |
| OSVersion: | 6.1 |
| ImageVersion: | 1 |
| SubsystemVersion: | 6.1 |
| Subsystem: | Windows command line |
| FileVersionNumber: | 2.0.4.0 |
| ProductVersionNumber: | 2.0.4.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | AmidaWare LLC |
| FileDescription: | Tactical RMM Installer |
| FileVersion: | v2.0.4.0 |
| InternalName: | rmm.exe |
| LegalCopyright: | Copyright (c) 2022 AmidaWare LLC |
| OriginalFileName: | installer.go |
| ProductName: | Tactical RMM Installer |
| ProductVersion: | v2.0.4.0 |
Total processes
278
Monitored processes
154
Malicious processes
23
Suspicious processes
17
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 204 | C:\WINDOWS\System32\WindowsPowerShell\v1.0\powershell.exe -NonInteractive -NoProfile -ExecutionPolicy Bypass C:\ProgramData\TacticalRMM\1065407449.ps1 | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | tacticalrmm.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 432 | cscript "C:\WINDOWS\TEMP\RustDesk_uninstall_shortcut.vbs" | C:\Windows\System32\cscript.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft ® Console Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 556 | "cmd.exe" /c net start tacticalrmm | C:\Windows\SysWOW64\cmd.exe | — | tacticalagent-v2.8.0-windows-amd64.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 2 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 628 | ping 127.0.0.1 -n 2 | C:\Windows\SysWOW64\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: TCP/IP Ping Command Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 628 | "cmd.exe" /c tacticalrmm.exe -m installsvc | C:\Windows\SysWOW64\cmd.exe | — | tacticalagent-v2.8.0-windows-amd64.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 628 | "C:\Program Files\Mesh Agent\MeshAgent.exe" -nodeid | C:\Program Files\Mesh Agent\MeshAgent.exe | — | tacticalrmm.exe | |||||||||||
User: admin Integrity Level: HIGH Description: MeshCentral Background Service Agent Exit code: 0 Version: 2022-Dec-2 11:42:16-0800 Modules
| |||||||||||||||
| 1140 | C:\WINDOWS\System32\WindowsPowerShell\v1.0\powershell.exe -NonInteractive -NoProfile -ExecutionPolicy Bypass C:\ProgramData\TacticalRMM\2101002621.ps1 | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | tacticalrmm.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1228 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | tacticalrmm.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1292 | "C:\WINDOWS\system32\config\systemprofile\AppData\Local\rustdesk\.\rustdesk.exe" --uninstall-amyuni-idd | C:\Windows\System32\config\systemprofile\AppData\Local\rustdesk\rustdesk.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Purslane Ltd Integrity Level: SYSTEM Description: RustDesk Remote Desktop Exit code: 0 Version: 1.3.7+56 Modules
| |||||||||||||||
| 1296 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | taskkill.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
92 545
Read events
92 467
Write events
78
Delete events
0
Modification events
| (PID) Process: | (4652) tacticalagent-v2.8.0-windows-amd64.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{0D34D278-5FAF-4159-A4A0-4E2D2C08139D}_is1 |
| Operation: | write | Name: | Inno Setup: Setup Version |
Value: 6.2.2 | |||
| (PID) Process: | (4652) tacticalagent-v2.8.0-windows-amd64.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{0D34D278-5FAF-4159-A4A0-4E2D2C08139D}_is1 |
| Operation: | write | Name: | Inno Setup: App Path |
Value: C:\Program Files\TacticalAgent | |||
| (PID) Process: | (4652) tacticalagent-v2.8.0-windows-amd64.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{0D34D278-5FAF-4159-A4A0-4E2D2C08139D}_is1 |
| Operation: | write | Name: | InstallLocation |
Value: C:\Program Files\TacticalAgent\ | |||
| (PID) Process: | (4652) tacticalagent-v2.8.0-windows-amd64.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{0D34D278-5FAF-4159-A4A0-4E2D2C08139D}_is1 |
| Operation: | write | Name: | Inno Setup: Icon Group |
Value: (Default) | |||
| (PID) Process: | (4652) tacticalagent-v2.8.0-windows-amd64.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{0D34D278-5FAF-4159-A4A0-4E2D2C08139D}_is1 |
| Operation: | write | Name: | Inno Setup: User |
Value: admin | |||
| (PID) Process: | (4652) tacticalagent-v2.8.0-windows-amd64.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{0D34D278-5FAF-4159-A4A0-4E2D2C08139D}_is1 |
| Operation: | write | Name: | Inno Setup: Language |
Value: english | |||
| (PID) Process: | (4652) tacticalagent-v2.8.0-windows-amd64.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{0D34D278-5FAF-4159-A4A0-4E2D2C08139D}_is1 |
| Operation: | write | Name: | DisplayName |
Value: Tactical RMM Agent | |||
| (PID) Process: | (4652) tacticalagent-v2.8.0-windows-amd64.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{0D34D278-5FAF-4159-A4A0-4E2D2C08139D}_is1 |
| Operation: | write | Name: | DisplayIcon |
Value: C:\Program Files\TacticalAgent\tacticalrmm.exe | |||
| (PID) Process: | (4652) tacticalagent-v2.8.0-windows-amd64.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{0D34D278-5FAF-4159-A4A0-4E2D2C08139D}_is1 |
| Operation: | write | Name: | UninstallString |
Value: "C:\Program Files\TacticalAgent\unins000.exe" | |||
| (PID) Process: | (4652) tacticalagent-v2.8.0-windows-amd64.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{0D34D278-5FAF-4159-A4A0-4E2D2C08139D}_is1 |
| Operation: | write | Name: | QuietUninstallString |
Value: "C:\Program Files\TacticalAgent\unins000.exe" /SILENT | |||
Executable files
158
Suspicious files
49
Text files
1 385
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4652 | tacticalagent-v2.8.0-windows-amd64.tmp | C:\Program Files\TacticalAgent\unins000.exe | executable | |
MD5:5E81857286E2795352225BE245FBD62B | SHA256:2624C22DA19E89717DCD522D22B21849A1C3F0EB781333DF85BE5FCD57597278 | |||
| 4652 | tacticalagent-v2.8.0-windows-amd64.tmp | C:\Program Files\TacticalAgent\is-O6KBF.tmp | executable | |
MD5:5E81857286E2795352225BE245FBD62B | SHA256:2624C22DA19E89717DCD522D22B21849A1C3F0EB781333DF85BE5FCD57597278 | |||
| 4652 | tacticalagent-v2.8.0-windows-amd64.tmp | C:\Users\admin\AppData\Local\Temp\is-5OBKN.tmp\_isetup\_setup64.tmp | executable | |
MD5:E4211D6D009757C078A9FAC7FF4F03D4 | SHA256:388A796580234EFC95F3B1C70AD4CB44BFDDC7BA0F9203BF4902B9929B136F95 | |||
| 2072 | tacticalagent-v2.8.0-windows-amd64.exe | C:\Users\admin\AppData\Local\Temp\is-OMKP6.tmp\tacticalagent-v2.8.0-windows-amd64.tmp | executable | |
MD5:A639312111D278FEE4F70299C134D620 | SHA256:4B0BE5167A31A77E28E3F0A7C83C9D289845075B51E70691236603B1083649DF | |||
| 5992 | 2025-01-25_4c63b362b73a36e9410738b9f81428ef_frostygoop_hijackloader_luca-stealer_poet-rat_snatch.exe | C:\ProgramData\TacticalRMM\tacticalagent-v2.8.0-windows-amd64.exe | executable | |
MD5:2F046950E65922336CD83BF0DBC9DE33 | SHA256:412E1F600251B21911C582E69381F677E663231F5E1D10786D88A026E00EA811 | |||
| 4652 | tacticalagent-v2.8.0-windows-amd64.tmp | C:\Program Files\TacticalAgent\tacticalrmm.exe | executable | |
MD5:BB383B7C3D5E4ACB1001AB099B5B0F3C | SHA256:A6D3159C858AA3704F35D69B27829618AD0D1BAE894C848A5233100C17464F95 | |||
| 4652 | tacticalagent-v2.8.0-windows-amd64.tmp | C:\Program Files\TacticalAgent\is-15CLI.tmp | executable | |
MD5:BB383B7C3D5E4ACB1001AB099B5B0F3C | SHA256:A6D3159C858AA3704F35D69B27829618AD0D1BAE894C848A5233100C17464F95 | |||
| 4652 | tacticalagent-v2.8.0-windows-amd64.tmp | C:\Program Files\TacticalAgent\unins000.dat | binary | |
MD5:520BAE723AD5E7C04E91E9B93EF265C1 | SHA256:F2A64EBB538B253FC60EB23A9F9BF8F6E3B8752DC4FD7D790E0519BC0B463FFA | |||
| 4652 | tacticalagent-v2.8.0-windows-amd64.tmp | C:\Users\admin\AppData\Local\Temp\Setup Log 2025-01-25 #001.txt | text | |
MD5:C6FC90882E963477115B1BCBF690C815 | SHA256:40509564D964BE8681FE3CFE1B57A30CC319B6A2F849E6B96651DCB5F7EB2256 | |||
| 5548 | MeshAgent.exe | C:\Windows\System32\config\systemprofile\AppData\Roaming\Microsoft\SystemCertificates\My\Certificates\3AFD07F95E75DD562CF435E3EC2FF9FE02C468C0 | binary | |
MD5:F0B11F828A2DE36AC71979F27255730E | SHA256:63E8D6877E7DC689A8E350D4F5C01A18155CB4F563C2A22154AB8DFFCA3C5BA1 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
57
TCP/UDP connections
89
DNS requests
23
Threats
18
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.37.237.227:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 101 | 192.243.222.221:443 | https://mesh.trmm.v-consulting.com/agent.ashx | unknown | — | — | unknown |
— | — | GET | 101 | 192.243.222.221:443 | https://api.trmm.v-consulting.com/natsws | unknown | — | — | unknown |
— | — | GET | 101 | 192.243.222.221:443 | https://api.trmm.v-consulting.com/natsws | unknown | — | — | unknown |
— | — | GET | 302 | 140.82.121.4:443 | https://github.com/amidaware/rmmagent/releases/download/v2.8.0/py3.11.9_amd64.zip | unknown | — | — | unknown |
— | — | GET | 101 | 192.243.222.221:443 | https://mesh.trmm.v-consulting.com/agent.ashx | unknown | — | — | unknown |
— | — | GET | 200 | 104.21.12.79:443 | https://agents.tacticalrmm.com/api/v2/agents?version=2.8.0&arch=amd64&token=a8858841-9033-44e6-9c5d-bf84521a4f65&plat=windows&api=api.trmm.v-consulting.com | unknown | executable | 4.30 Mb | unknown |
— | — | POST | 200 | 192.243.222.221:443 | https://api.trmm.v-consulting.com/api/v3/meshexe/ | unknown | executable | 3.31 Mb | unknown |
— | — | GET | 200 | 34.160.111.145:443 | https://ifconfig.me/ip | unknown | text | 39 b | shared |
— | — | POST | 200 | 192.243.222.221:443 | https://api.trmm.v-consulting.com/api/v3/newagent/ | unknown | binary | 61 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6068 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5064 | SearchApp.exe | 2.16.204.153:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5992 | 2025-01-25_4c63b362b73a36e9410738b9f81428ef_frostygoop_hijackloader_luca-stealer_poet-rat_snatch.exe | 172.67.151.233:443 | agents.tacticalrmm.com | CLOUDFLARENET | US | unknown |
6068 | svchost.exe | 23.48.23.143:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.48.23.143:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
6068 | svchost.exe | 23.37.237.227:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.37.237.227:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
agents.tacticalrmm.com |
| unknown |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
api.trmm.v-consulting.com |
| unknown |
mesh.trmm.v-consulting.com |
| unknown |
icanhazip.tacticalrmm.io |
| unknown |
ifconfig.me |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2192 | svchost.exe | Device Retrieving External IP Address Detected | INFO [ANY.RUN] External IP Lookup Domain (ifconfig .me) |
5040 | tacticalrmm.exe | Device Retrieving External IP Address Detected | ET INFO Observed External IP Lookup Domain (icanhazip .com in TLS SNI) |
2192 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (icanhazip .com) |
5040 | tacticalrmm.exe | Potentially Bad Traffic | ET INFO Observed Chocolatey Windows Package Management Domain (chocolatey .org in TLS SNI) |
7136 | powershell.exe | Potentially Bad Traffic | ET INFO Observed Chocolatey Windows Package Management Domain (chocolatey .org in TLS SNI) |
2192 | svchost.exe | Misc activity | ET INFO RustDesk Domain in DNS Lookup |
6912 | rustdesk.exe | Misc activity | ET INFO RustDesk Register Public Key |
2192 | svchost.exe | Misc activity | ET INFO RustDesk Relay Domain in DNS Lookup |
6912 | rustdesk.exe | Misc activity | ET INFO RustDesk Register Public Key |
2392 | rustdesk.exe | Misc activity | ET INFO RustDesk Register Public Key |