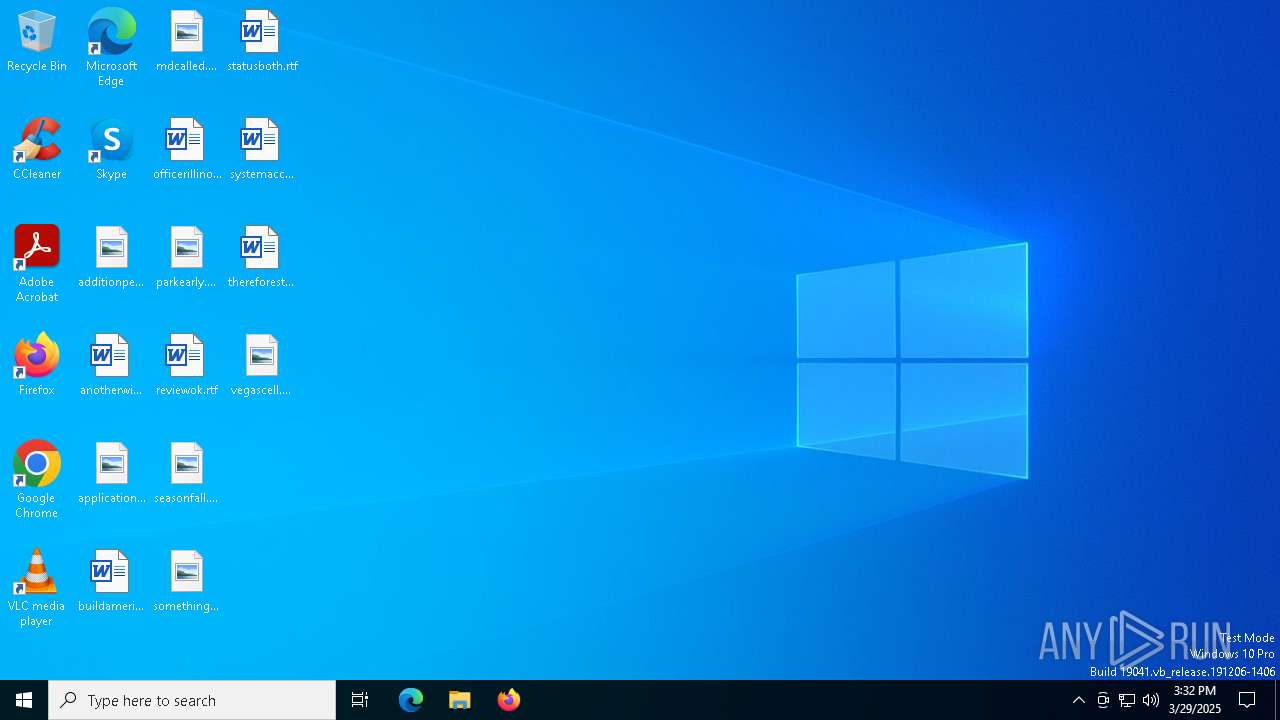
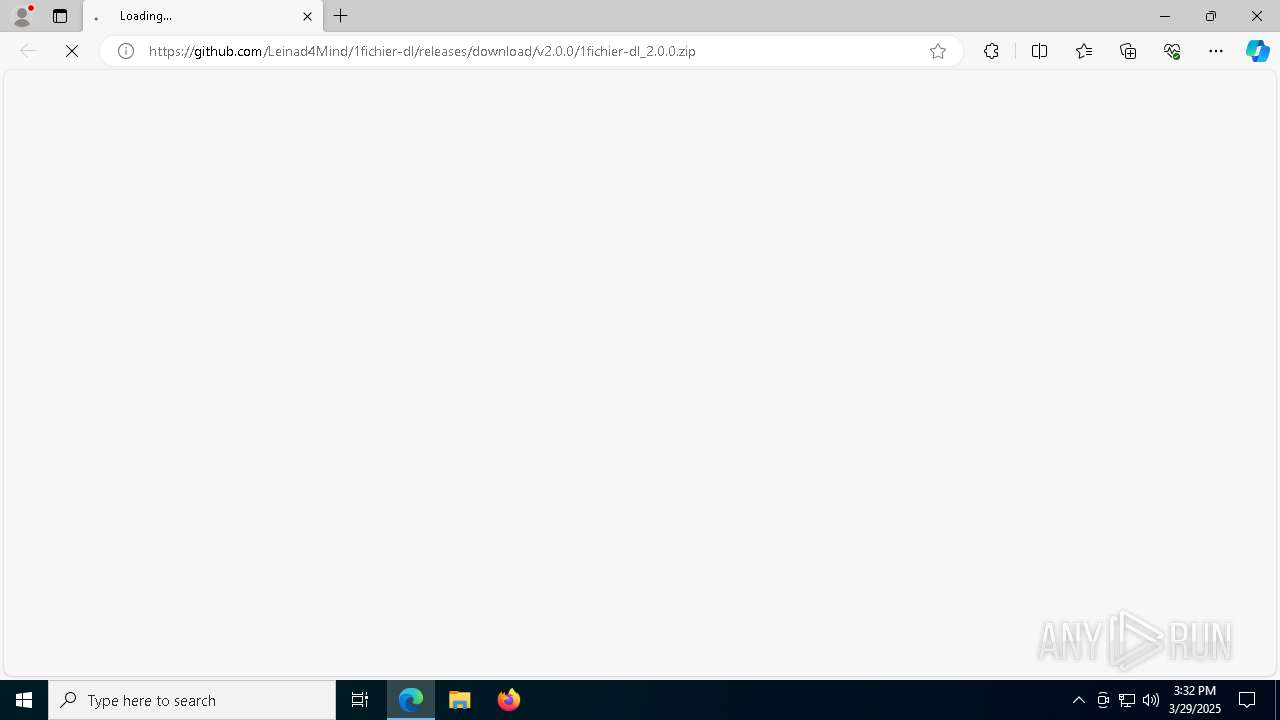
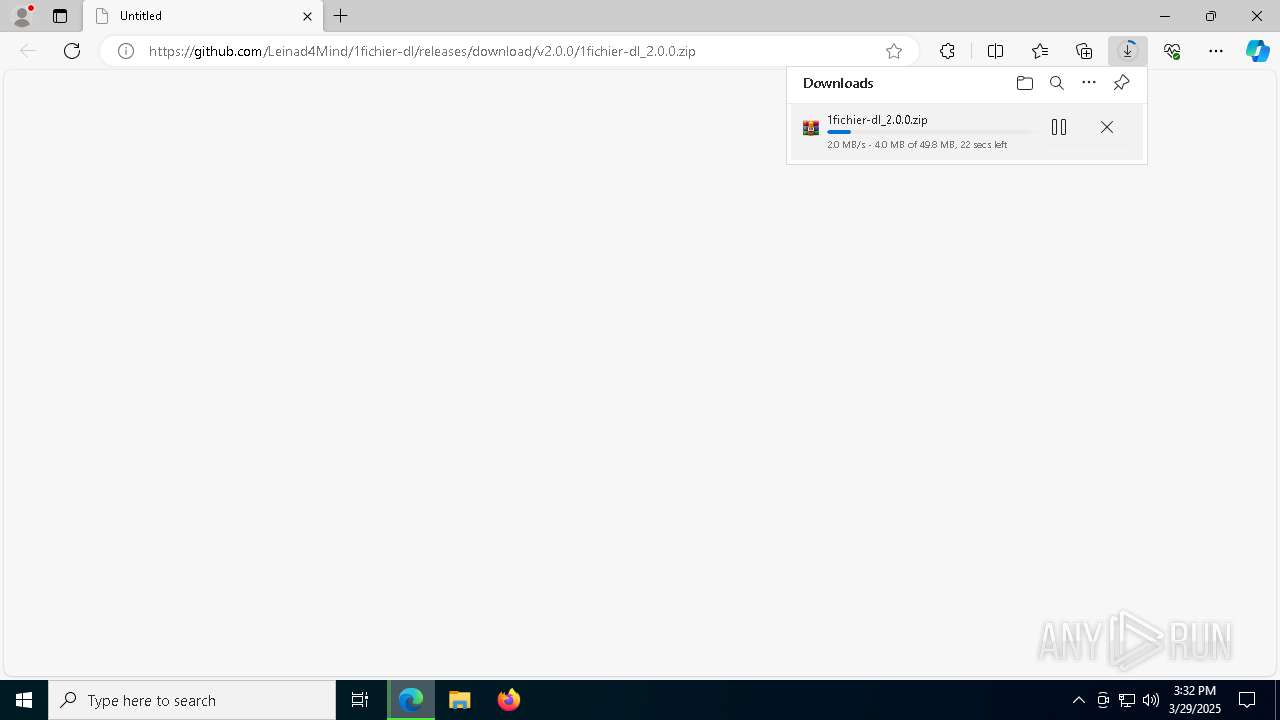
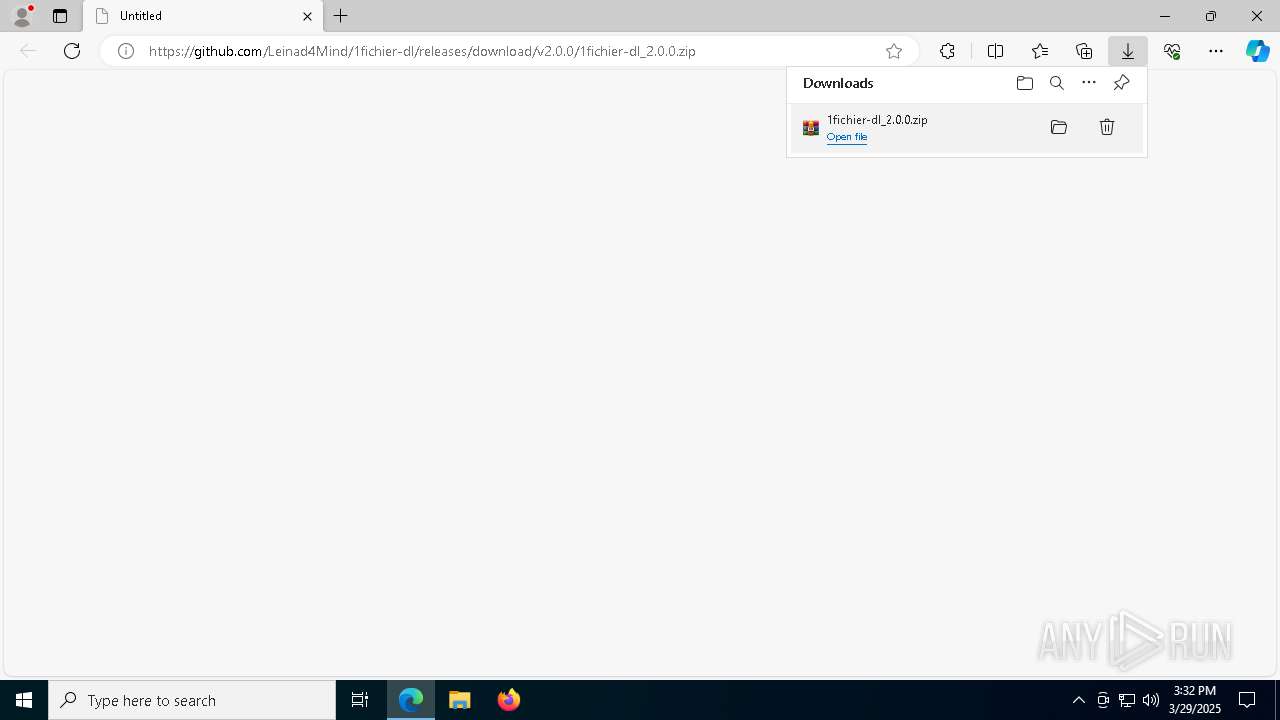
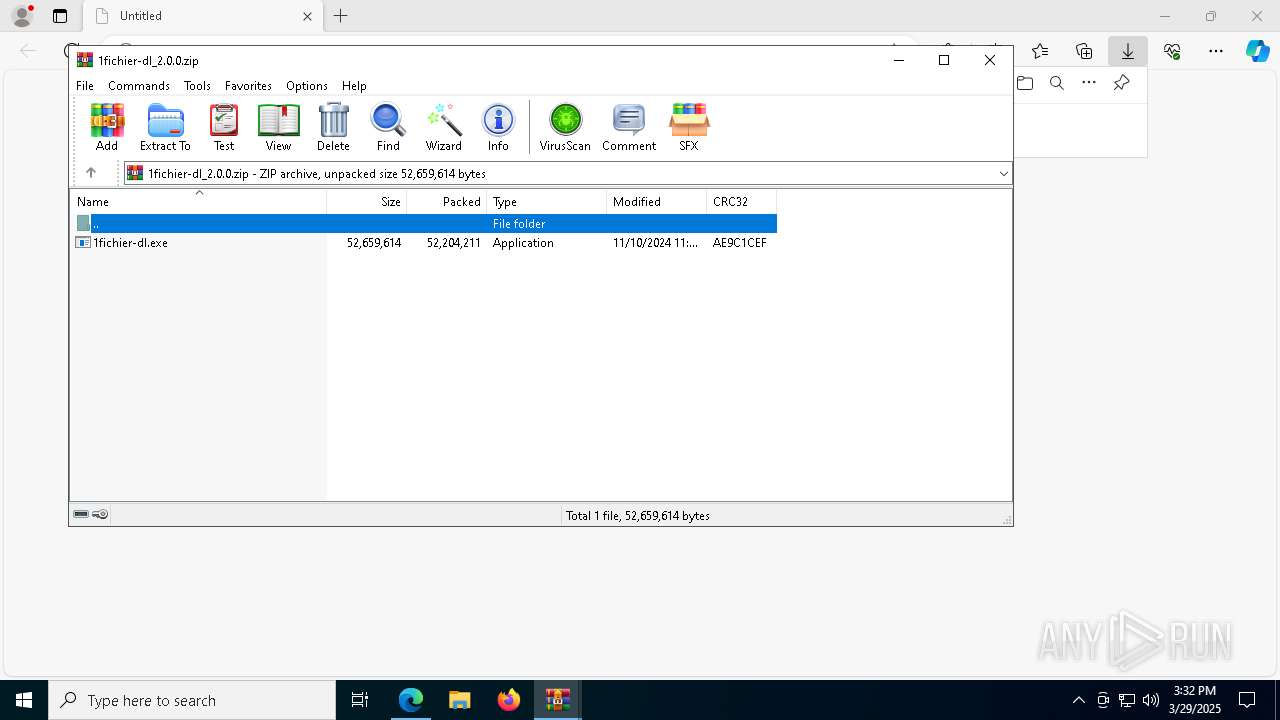
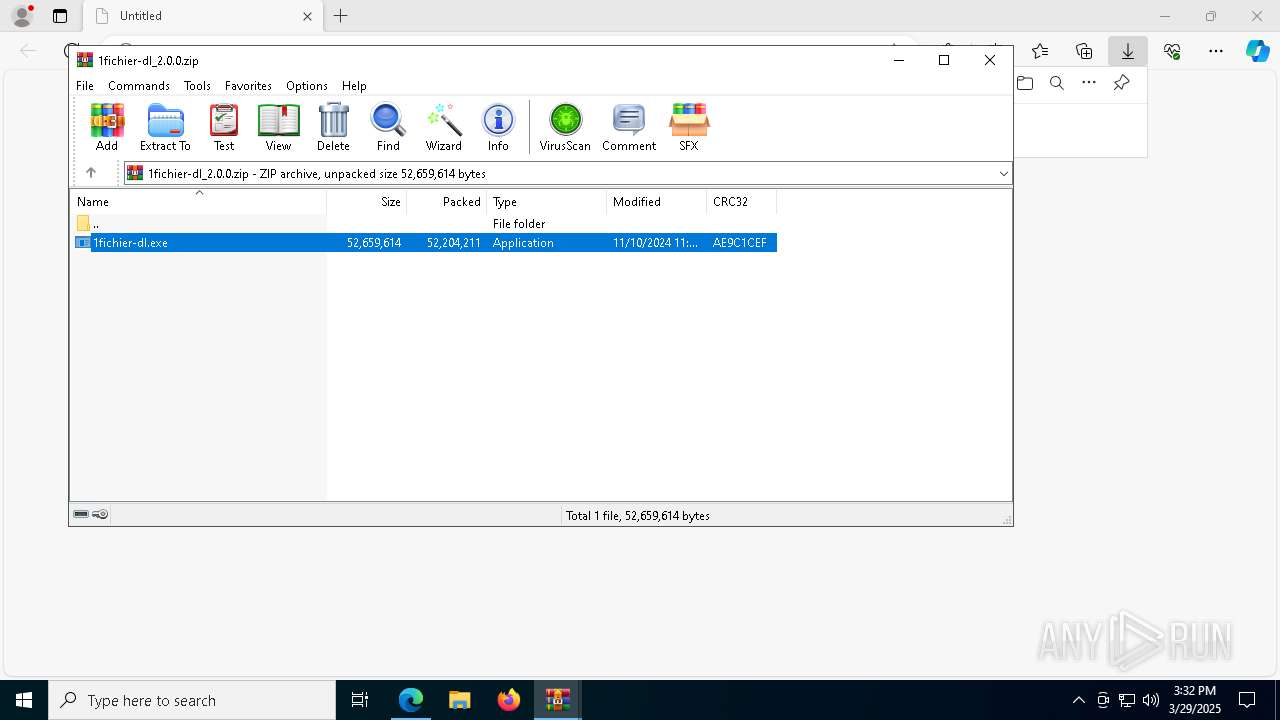
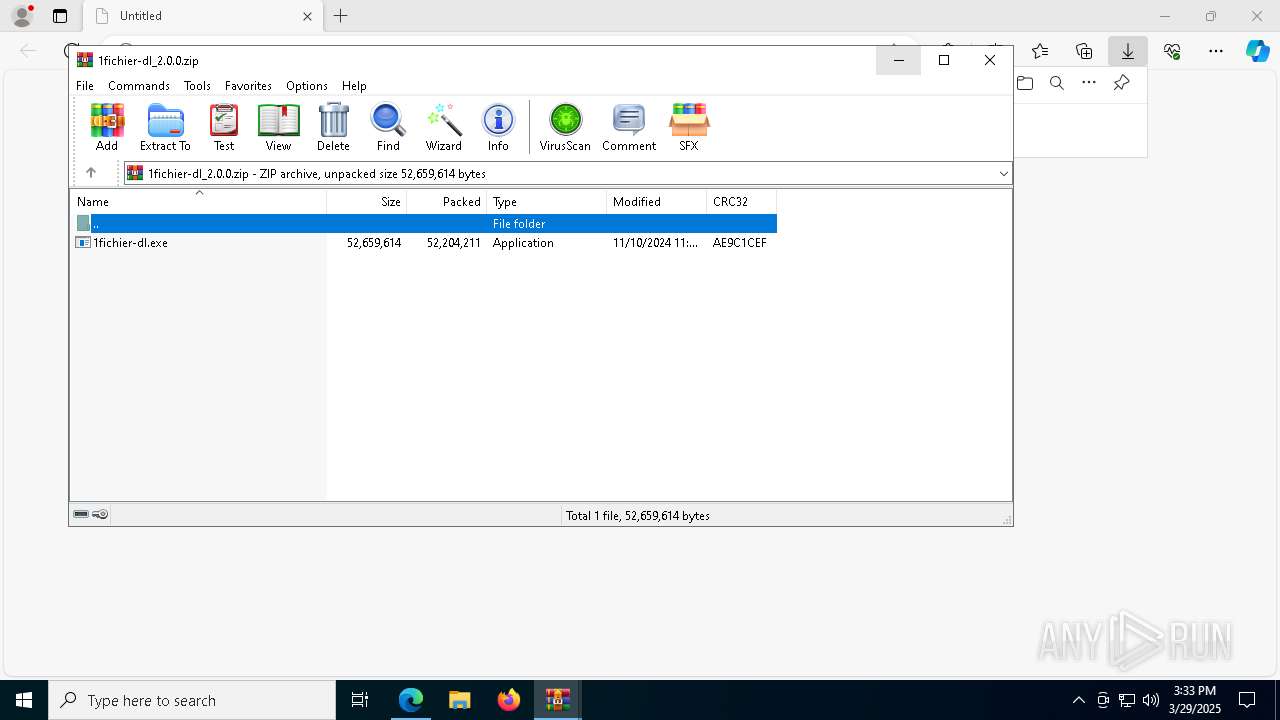
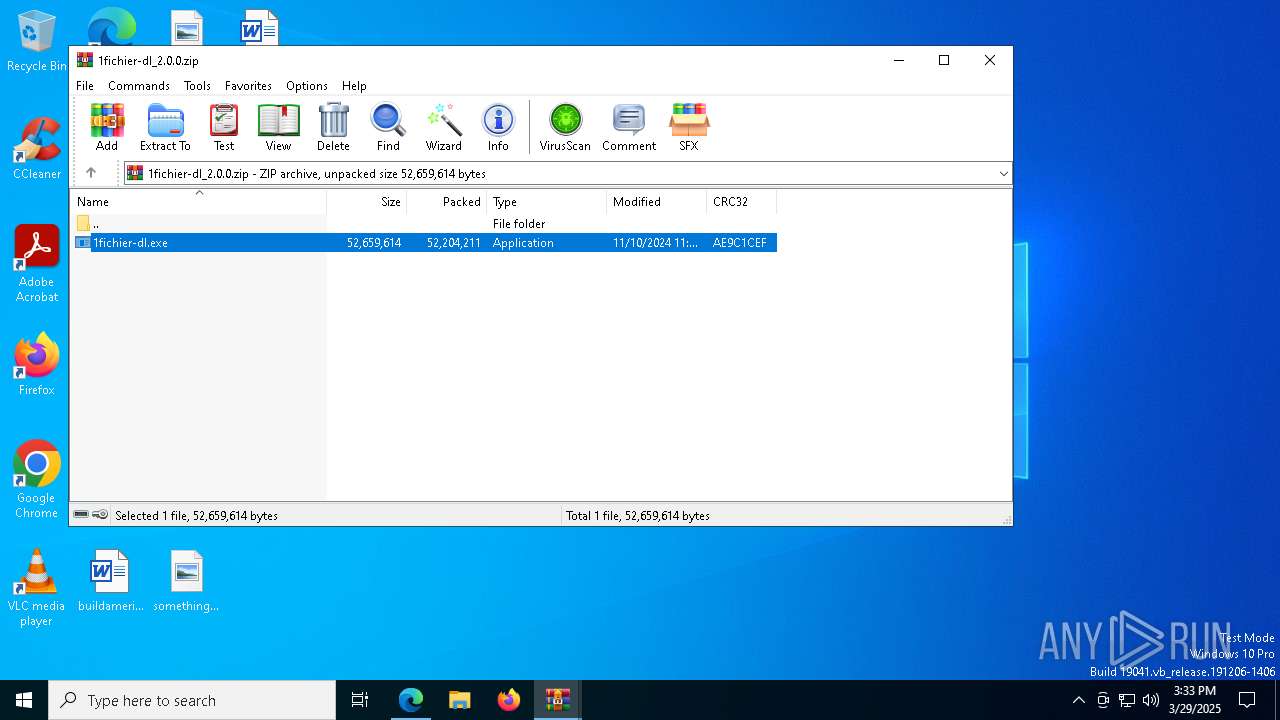
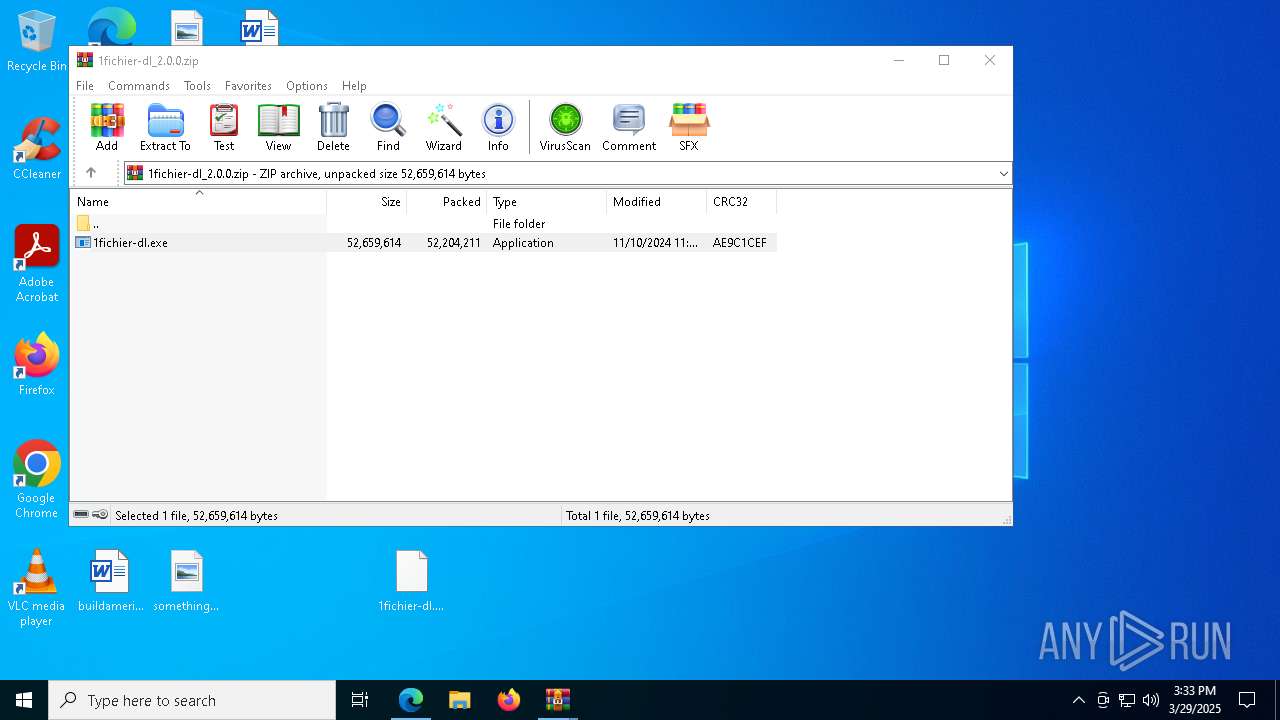
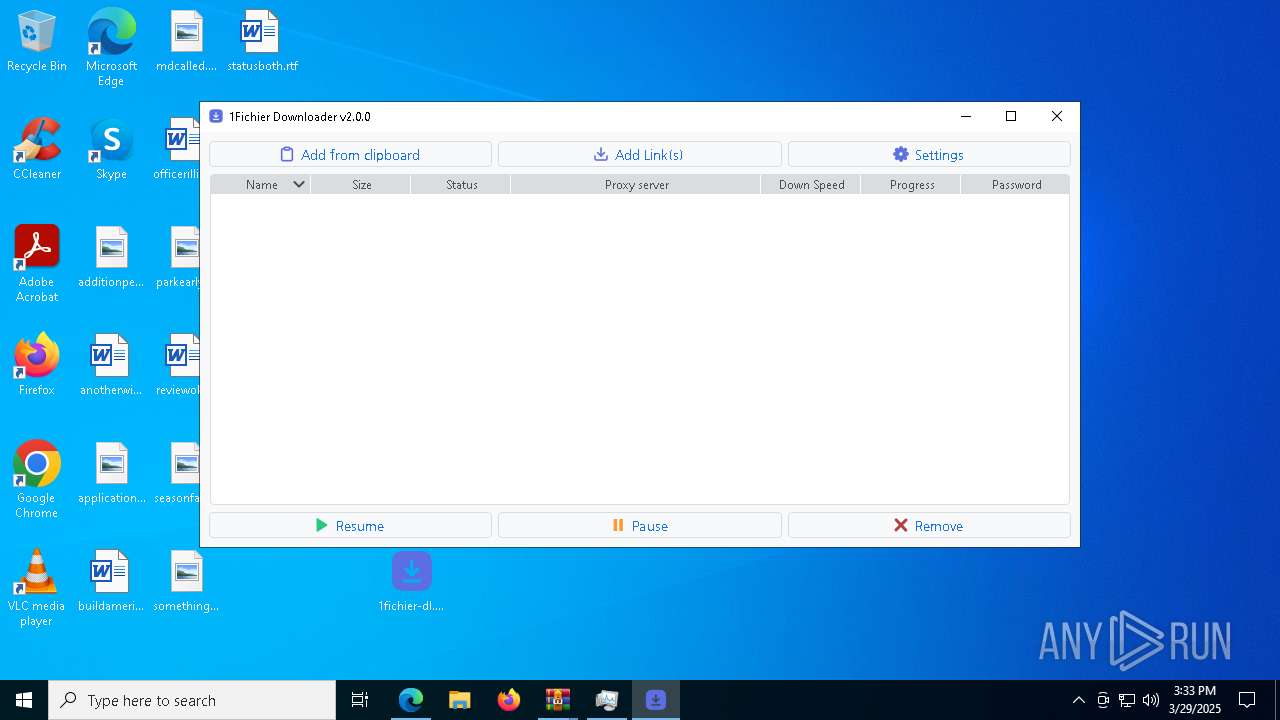
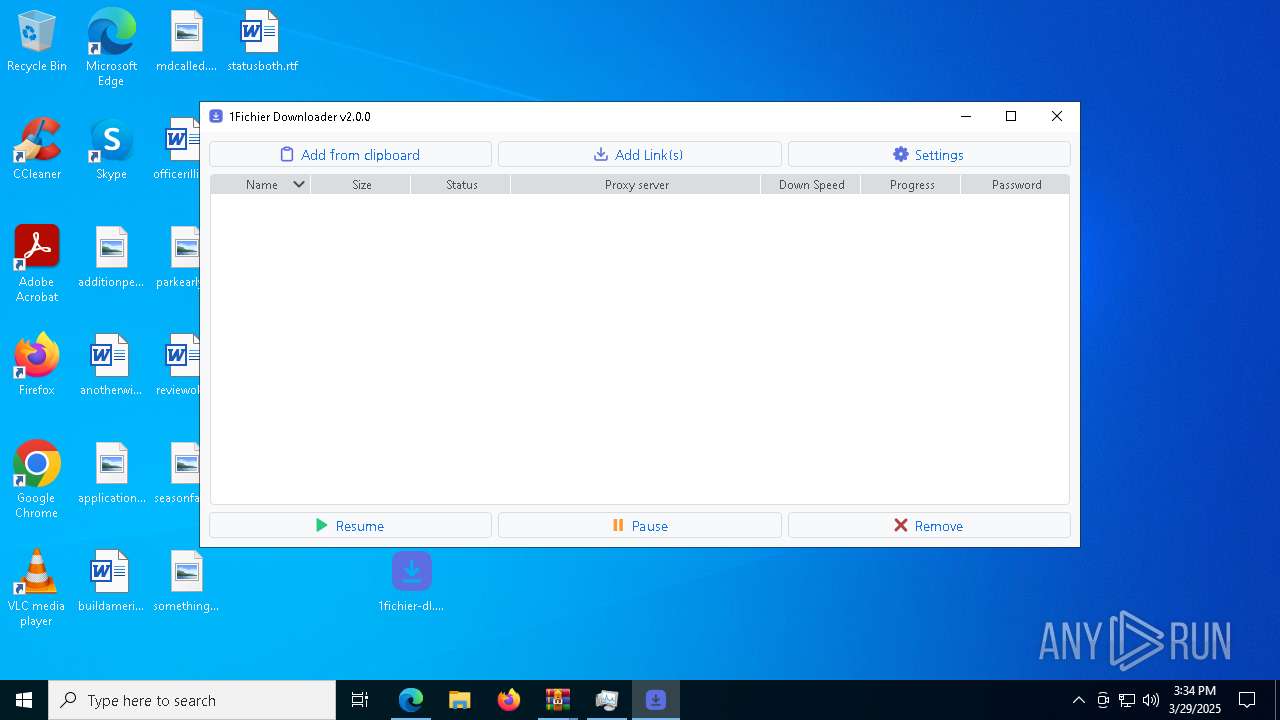
| URL: | https://github.com/Leinad4Mind/1fichier-dl/releases/download/v2.0.0/1fichier-dl_2.0.0.zip |
| Full analysis: | https://app.any.run/tasks/b4f66705-822e-4fd2-9203-bea7e6c3d651 |
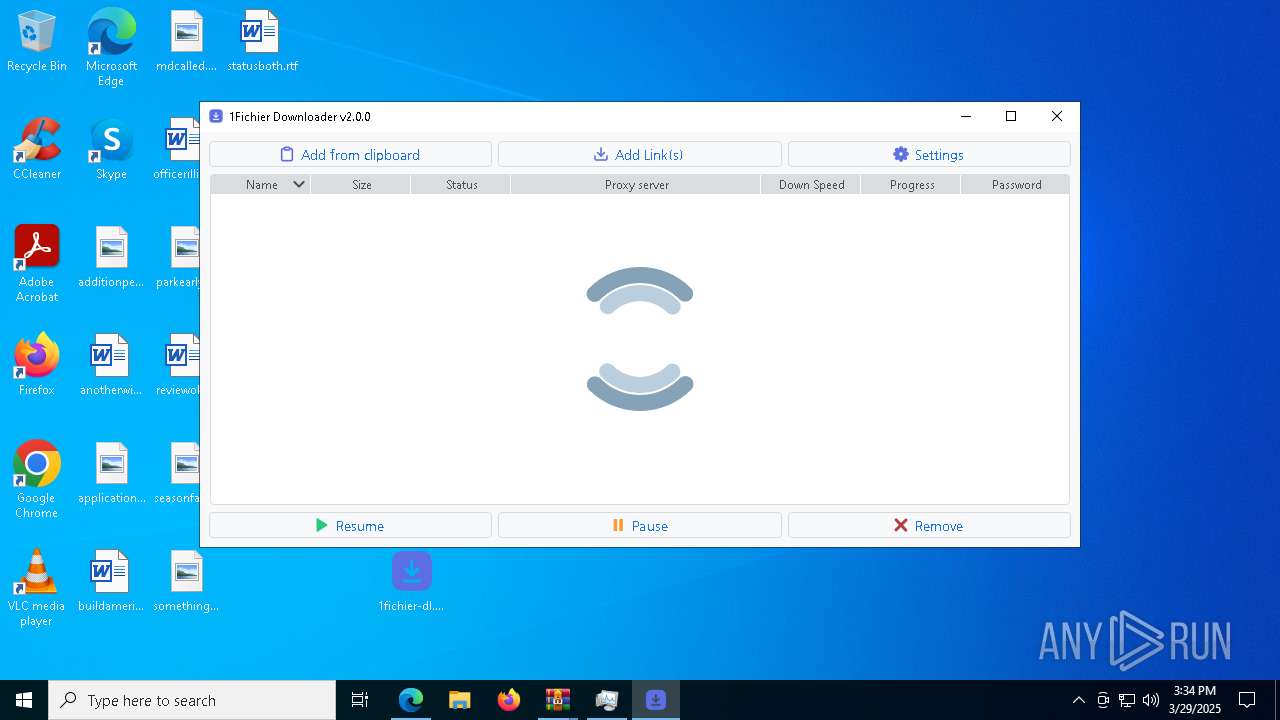
| Verdict: | Malicious activity |
| Analysis date: | March 29, 2025, 15:32:35 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 407A2A55807CFD7B4C8614083FFAAC5D |
| SHA1: | 9170B13A6ACB1F58253423E13EFE8BB1122838A3 |
| SHA256: | A9EA85E9A66C18D8BC71E2C53824FC3AB85E80124D235C6E0E6E672F3C2982C5 |
| SSDEEP: | 3:N8tEdEnRLB7fIBEXdkCZVKUDthIB0H4:2umnz8CXd3gagyH4 |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 5552)
The process drops C-runtime libraries
- 1fichier-dl.exe (PID: 7396)
- 1fichier-dl.exe (PID: 4188)
- 1fichier-dl.exe (PID: 4008)
- 1fichier-dl.exe (PID: 5868)
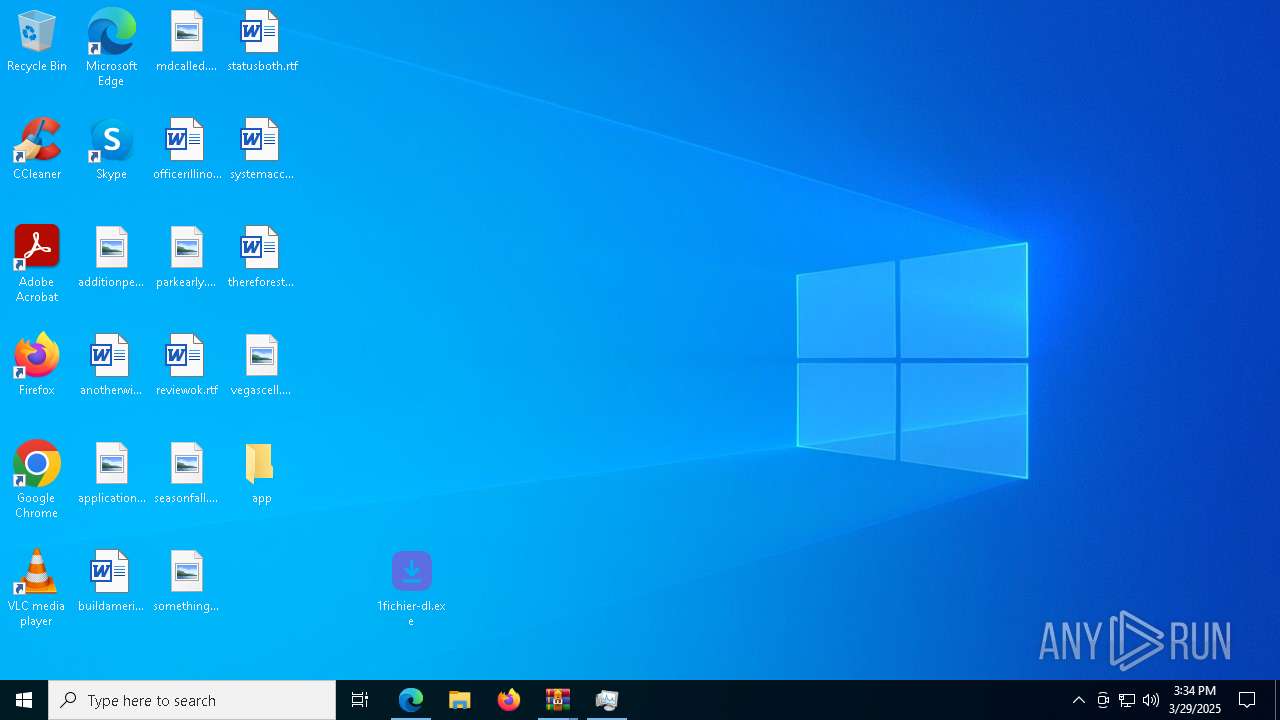
Executable content was dropped or overwritten
- 1fichier-dl.exe (PID: 7396)
- 1fichier-dl.exe (PID: 4188)
- 1fichier-dl.exe (PID: 4008)
- 1fichier-dl.exe (PID: 5868)
Process drops legitimate windows executable
- 1fichier-dl.exe (PID: 7396)
- 1fichier-dl.exe (PID: 4188)
- 1fichier-dl.exe (PID: 4008)
- 1fichier-dl.exe (PID: 5868)
Process drops python dynamic module
- 1fichier-dl.exe (PID: 4188)
- 1fichier-dl.exe (PID: 7396)
- 1fichier-dl.exe (PID: 4008)
- 1fichier-dl.exe (PID: 5868)
There is functionality for taking screenshot (YARA)
- 1fichier-dl.exe (PID: 4188)
- 1fichier-dl.exe (PID: 7396)
Loads Python modules
- 1fichier-dl.exe (PID: 672)
- 1fichier-dl.exe (PID: 5024)
Application launched itself
- 1fichier-dl.exe (PID: 4188)
- 1fichier-dl.exe (PID: 7396)
Starts CMD.EXE for commands execution
- 1fichier-dl.exe (PID: 5024)
- 1fichier-dl.exe (PID: 672)
Executes application which crashes
- 1fichier-dl.exe (PID: 672)
- 1fichier-dl.exe (PID: 5024)
INFO
Application launched itself
- msedge.exe (PID: 7468)
Checks supported languages
- 1fichier-dl.exe (PID: 7396)
- identity_helper.exe (PID: 7204)
- 1fichier-dl.exe (PID: 672)
- 1fichier-dl.exe (PID: 5024)
- 1fichier-dl.exe (PID: 4188)
- 1fichier-dl.exe (PID: 4008)
- 1fichier-dl.exe (PID: 5868)
Reads Environment values
- identity_helper.exe (PID: 7204)
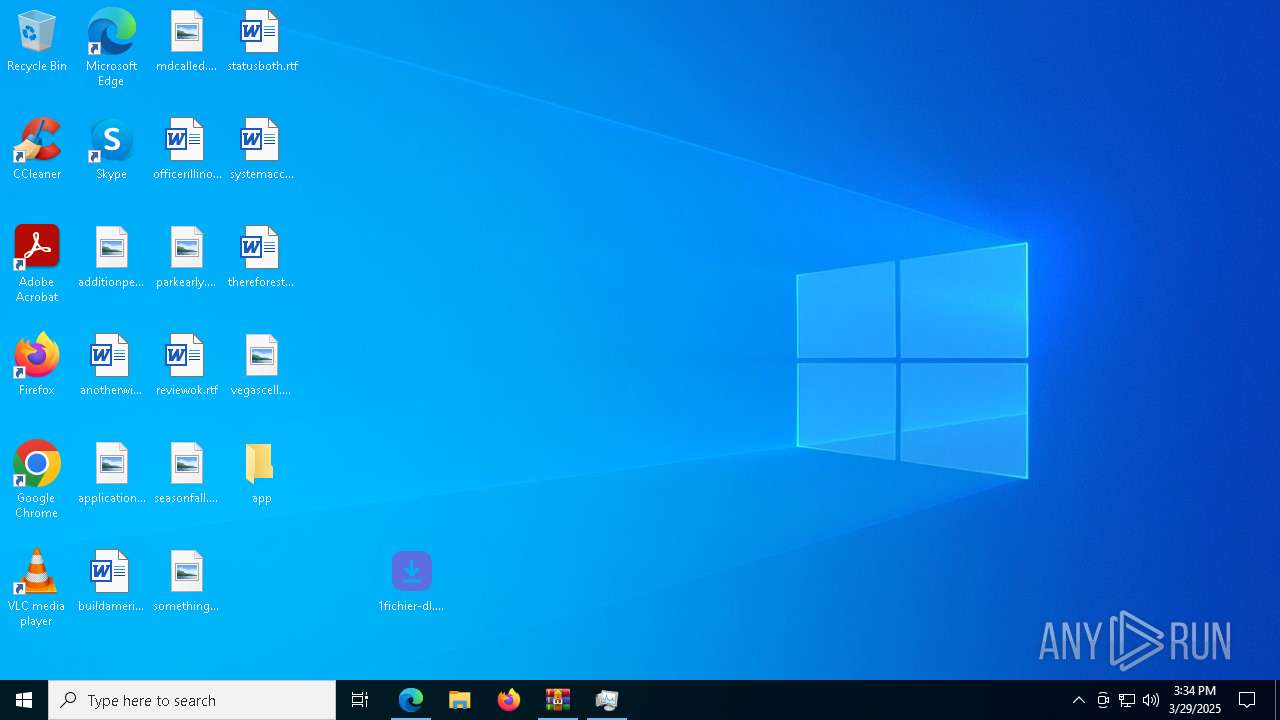
Autorun file from Downloads
- msedge.exe (PID: 864)
Reads the computer name
- identity_helper.exe (PID: 7204)
- 1fichier-dl.exe (PID: 7396)
- 1fichier-dl.exe (PID: 4188)
- 1fichier-dl.exe (PID: 672)
- 1fichier-dl.exe (PID: 4008)
- 1fichier-dl.exe (PID: 5024)
- 1fichier-dl.exe (PID: 5868)
The sample compiled with english language support
- 1fichier-dl.exe (PID: 7396)
- msedge.exe (PID: 7524)
- 1fichier-dl.exe (PID: 4188)
- 1fichier-dl.exe (PID: 4008)
- 1fichier-dl.exe (PID: 5868)
Create files in a temporary directory
- 1fichier-dl.exe (PID: 7396)
- 1fichier-dl.exe (PID: 672)
- 1fichier-dl.exe (PID: 4188)
- 1fichier-dl.exe (PID: 4008)
- 1fichier-dl.exe (PID: 5868)
PyInstaller has been detected (YARA)
- 1fichier-dl.exe (PID: 7396)
- 1fichier-dl.exe (PID: 4188)
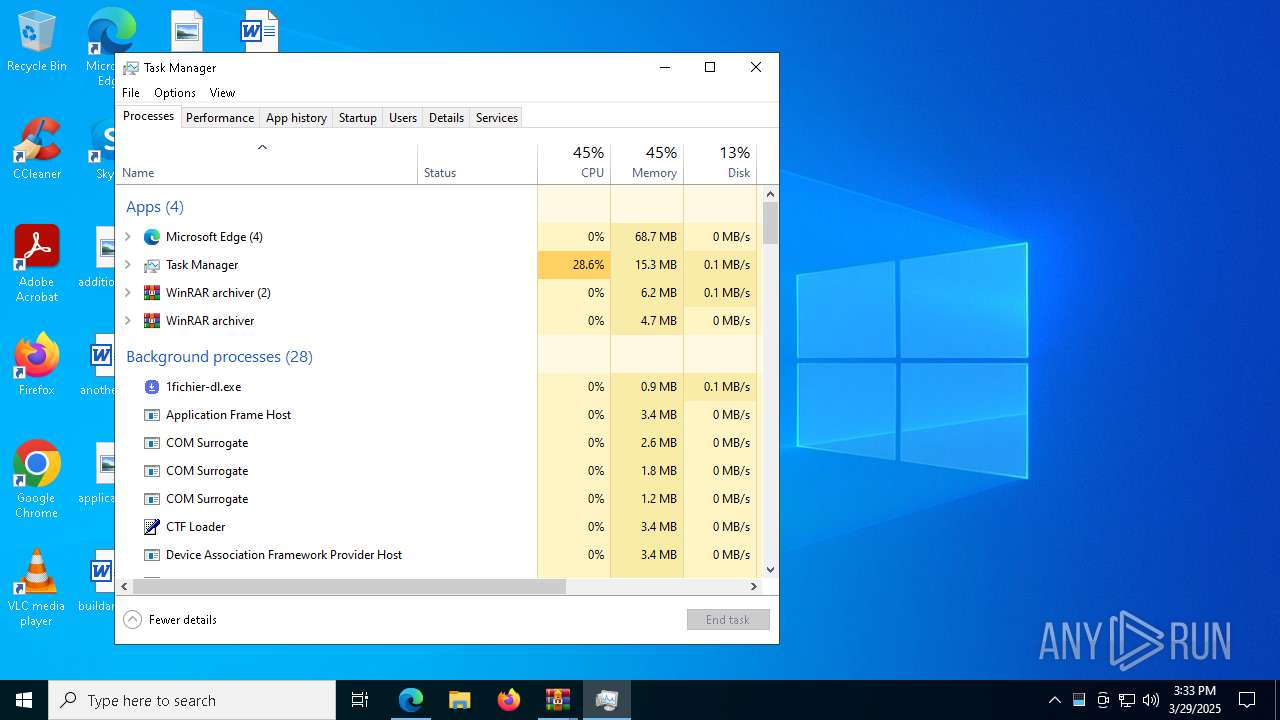
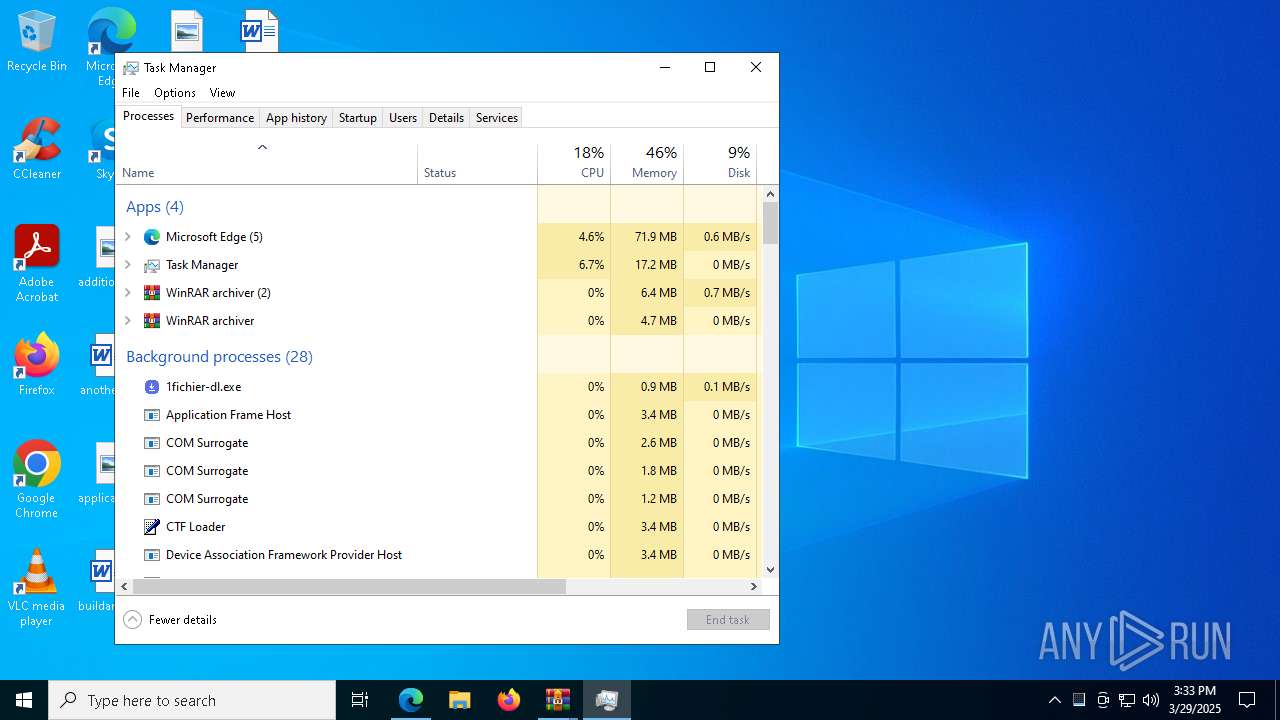
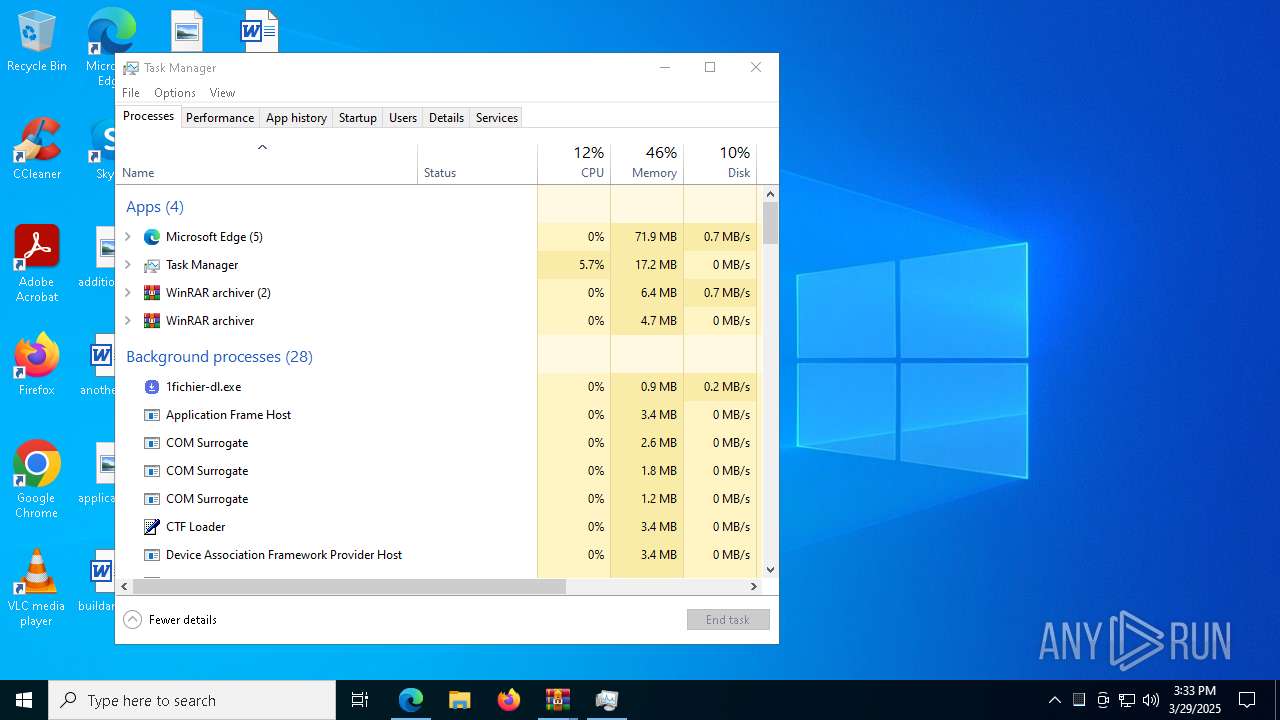
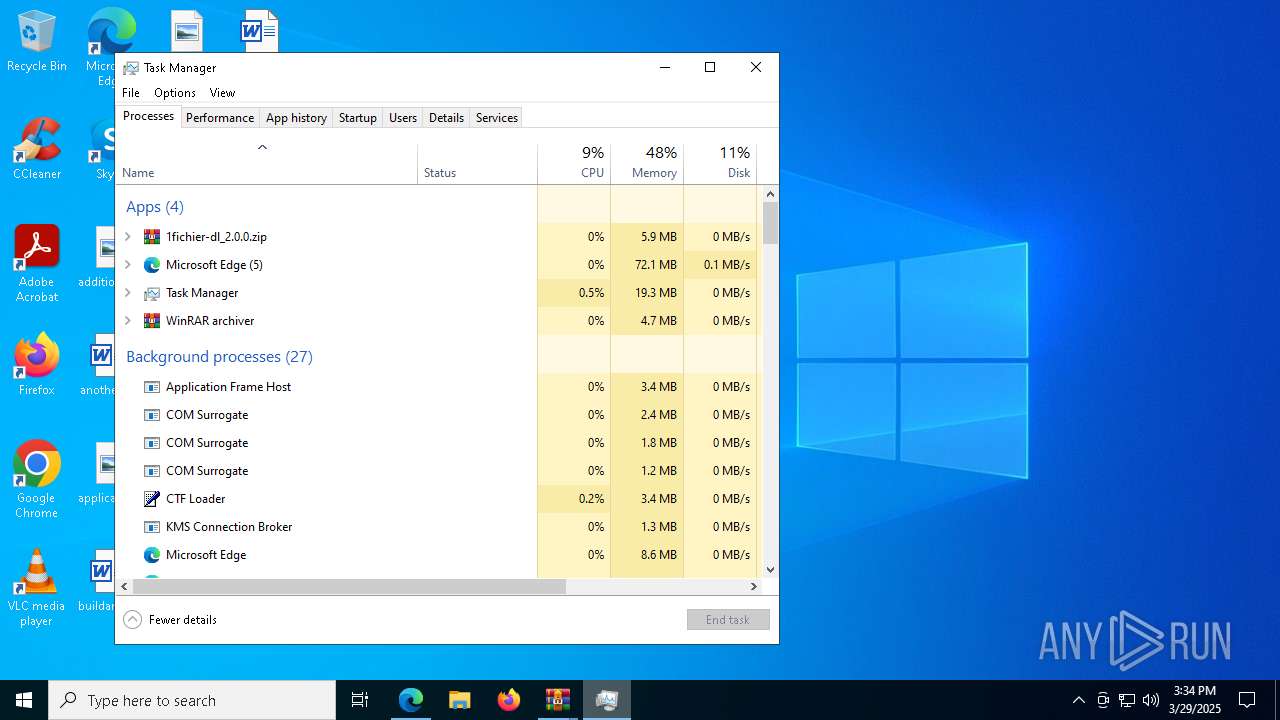
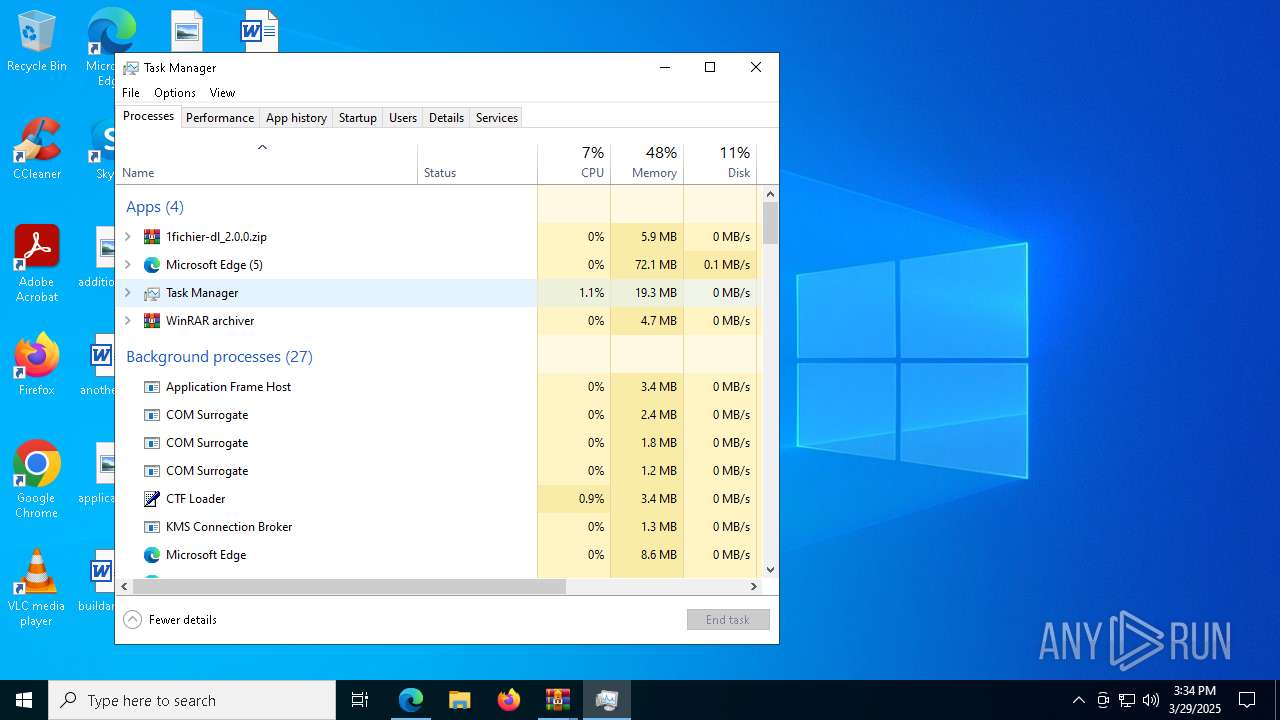
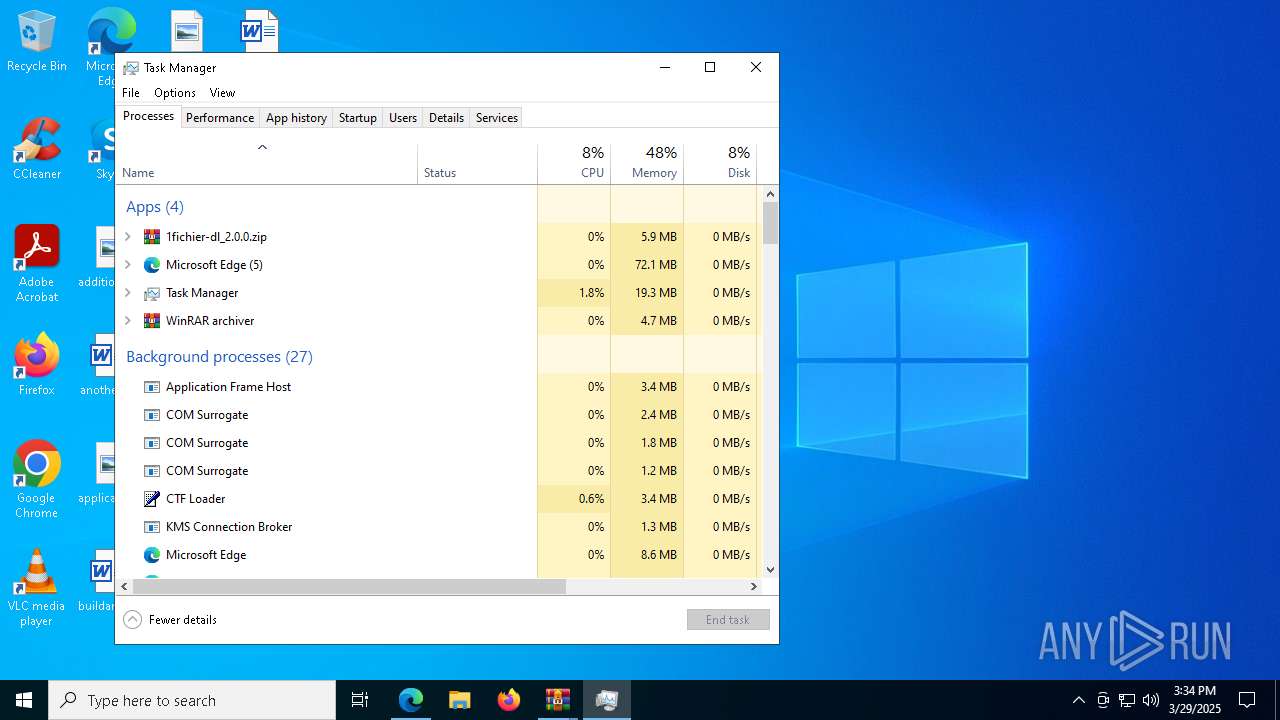
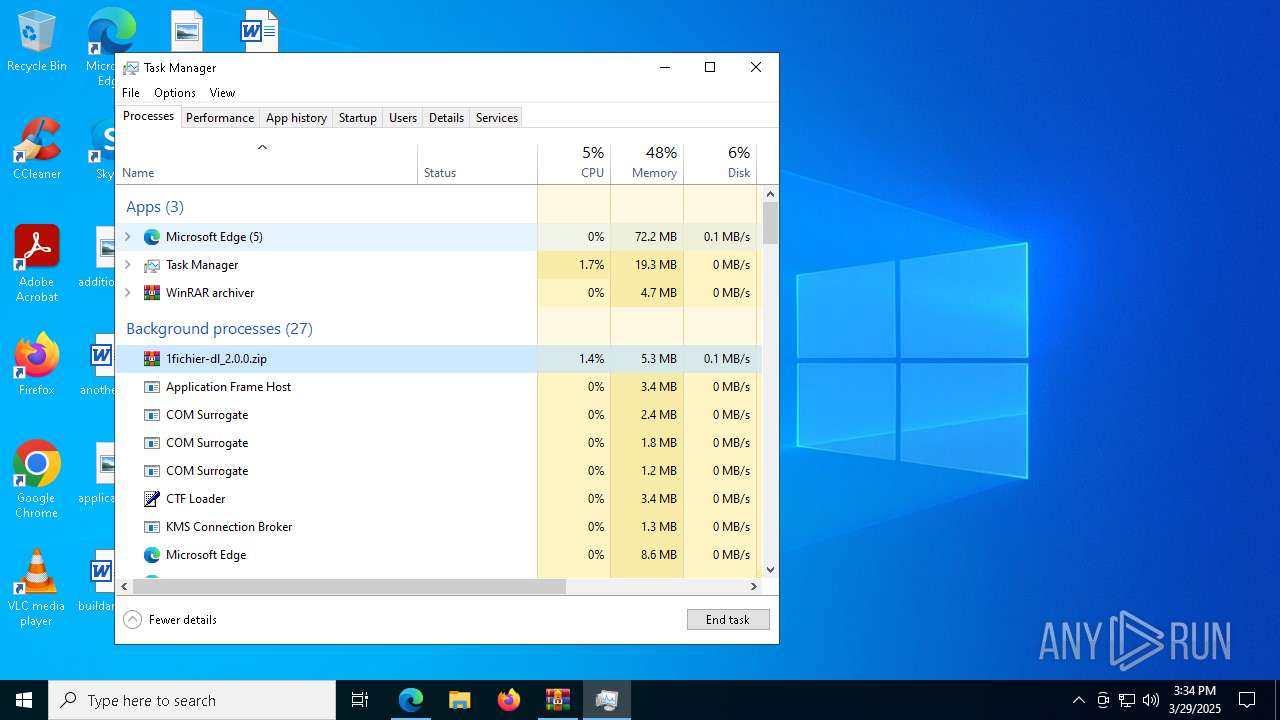
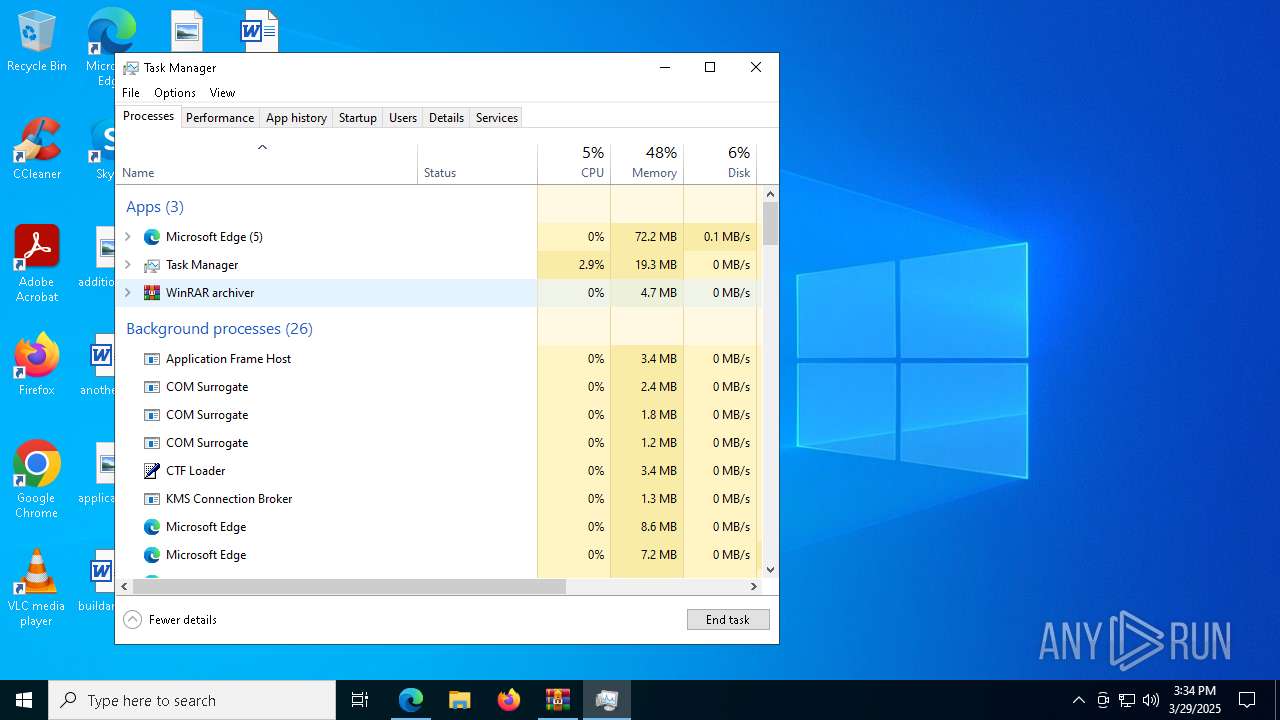
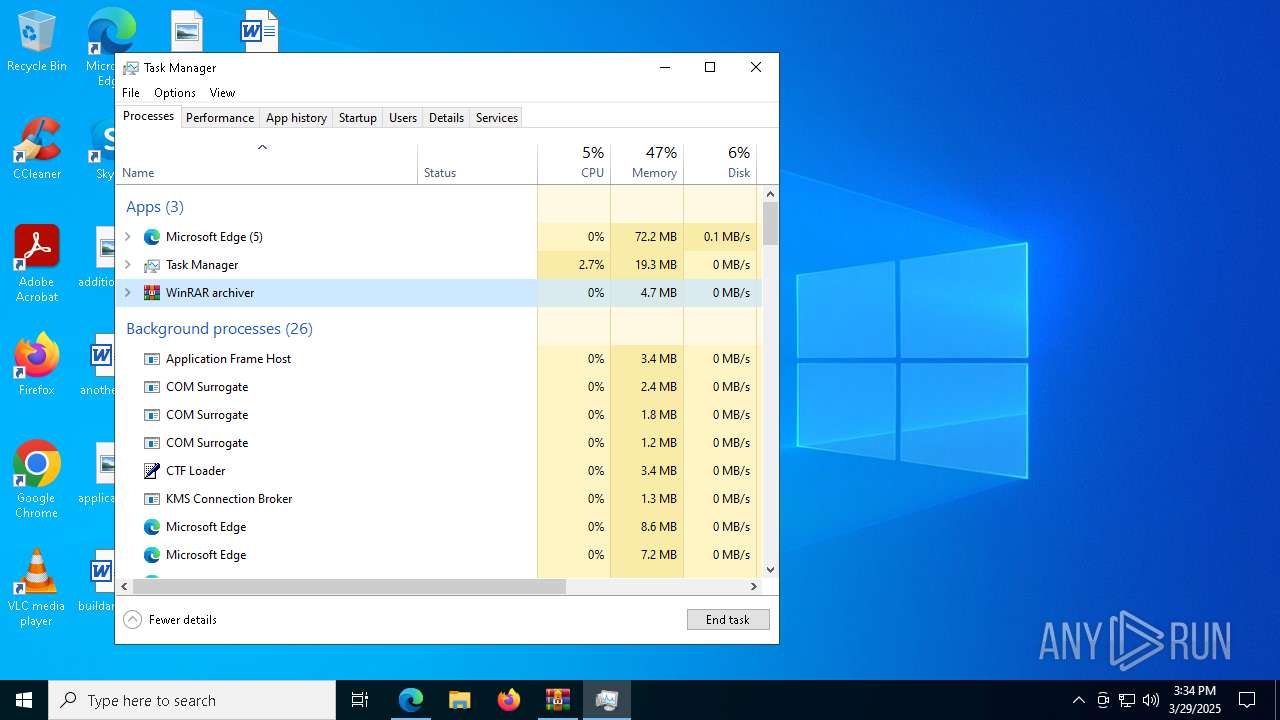
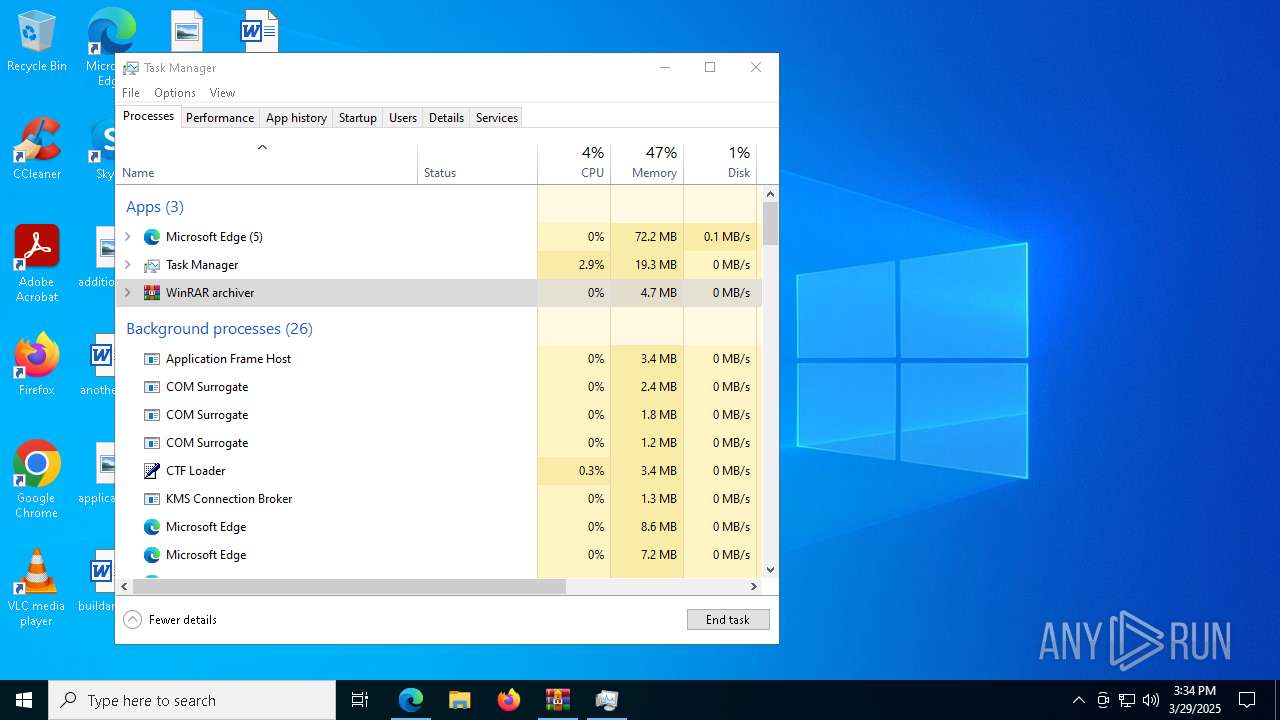
Manual execution by a user
- 1fichier-dl.exe (PID: 4188)
- Taskmgr.exe (PID: 8148)
- Taskmgr.exe (PID: 2960)
- 1fichier-dl.exe (PID: 4008)
- 1fichier-dl.exe (PID: 5868)
Reads security settings of Internet Explorer
- Taskmgr.exe (PID: 8148)
Checks operating system version
- 1fichier-dl.exe (PID: 672)
- 1fichier-dl.exe (PID: 5024)
Reads the machine GUID from the registry
- 1fichier-dl.exe (PID: 672)
- 1fichier-dl.exe (PID: 5024)
Reads the software policy settings
- slui.exe (PID: 5668)
- slui.exe (PID: 2800)
Creates files or folders in the user directory
- WerFault.exe (PID: 6592)
- WerFault.exe (PID: 7664)
Executable content was dropped or overwritten
- msedge.exe (PID: 7524)
Checks proxy server information
- 1fichier-dl.exe (PID: 5024)
- slui.exe (PID: 2800)
- 1fichier-dl.exe (PID: 672)
Reads Microsoft Office registry keys
- msedge.exe (PID: 7468)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
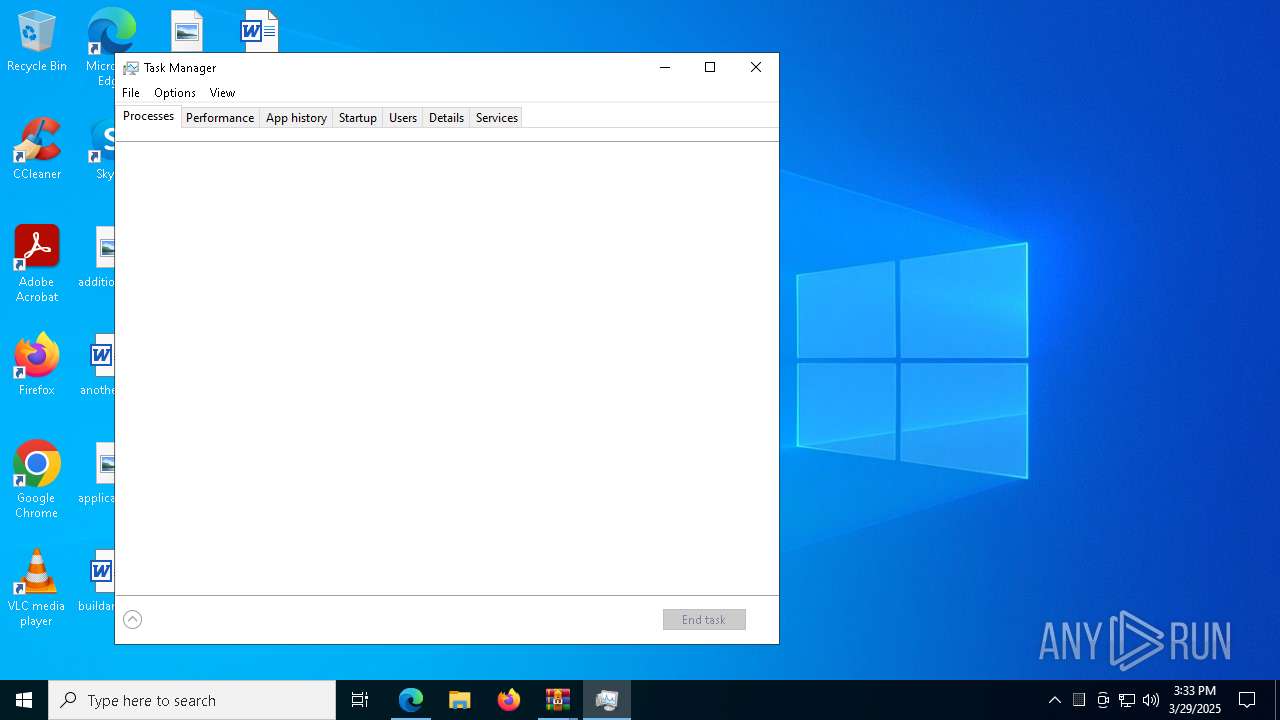
Total processes
192
Monitored processes
56
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 132 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5404 --field-trial-handle=2240,i,4811103562389496402,11665139262996914697,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 456 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --disable-gpu-sandbox --use-gl=disabled --gpu-vendor-id=5140 --gpu-device-id=140 --gpu-sub-system-id=0 --gpu-revision=0 --gpu-driver-version=10.0.19041.3636 --no-appcompat-clear --gpu-preferences=WAAAAAAAAADoAAAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAABEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=6976 --field-trial-handle=2240,i,4811103562389496402,11665139262996914697,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 672 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa5552.18788\1fichier-dl.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa5552.18788\1fichier-dl.exe | 1fichier-dl.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226505 Modules
| |||||||||||||||
| 856 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 864 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=6868 --field-trial-handle=2240,i,4811103562389496402,11665139262996914697,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1056 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=6928 --field-trial-handle=2240,i,4811103562389496402,11665139262996914697,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 3221226029 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1128 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1244 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=7080 --field-trial-handle=2240,i,4811103562389496402,11665139262996914697,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2800 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2960 | "C:\WINDOWS\system32\taskmgr.exe" /4 | C:\Windows\System32\Taskmgr.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Manager Exit code: 3221226540 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
15 756
Read events
15 708
Write events
47
Delete events
1
Modification events
| (PID) Process: | (7468) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (7468) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (7468) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (7468) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (7468) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 578A342E13902F00 | |||
| (PID) Process: | (7468) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 157C3D2E13902F00 | |||
| (PID) Process: | (7468) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197198 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {B892BA9E-F272-4C25-97F3-5DD5CB73A74A} | |||
| (PID) Process: | (7468) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197198 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {B4B7E74F-4665-4499-8012-DD1F0AA1D625} | |||
| (PID) Process: | (7468) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: B1BA9F2E13902F00 | |||
| (PID) Process: | (7468) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\Profiles |
| Operation: | write | Name: | EnhancedLinkOpeningDefault |
Value: Default | |||
Executable files
323
Suspicious files
555
Text files
3 162
Unknown types
12
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7468 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10b4fa.TMP | — | |
MD5:— | SHA256:— | |||
| 7468 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10b4fa.TMP | — | |
MD5:— | SHA256:— | |||
| 7468 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7468 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7468 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10b4fa.TMP | — | |
MD5:— | SHA256:— | |||
| 7468 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7468 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10b4fa.TMP | — | |
MD5:— | SHA256:— | |||
| 7468 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7468 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10b509.TMP | — | |
MD5:— | SHA256:— | |||
| 7468 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
29
TCP/UDP connections
52
DNS requests
59
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5720 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5744 | svchost.exe | HEAD | 200 | 23.48.23.7:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1743715107&P2=404&P3=2&P4=doVo2sML4XQvM9SUfpf9th20a2jbECD0WHN5MITW%2fx2PUPtAxHSGYGs%2fDx5zgQYG4sUuMlFbpgpsgz8t4jQPsA%3d%3d | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5744 | svchost.exe | GET | 206 | 23.48.23.7:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1743715107&P2=404&P3=2&P4=doVo2sML4XQvM9SUfpf9th20a2jbECD0WHN5MITW%2fx2PUPtAxHSGYGs%2fDx5zgQYG4sUuMlFbpgpsgz8t4jQPsA%3d%3d | unknown | — | — | whitelisted |
5744 | svchost.exe | HEAD | 200 | 23.48.23.7:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/b649b6c2-4484-495a-96f2-2fd1ee2b66ca?P1=1743610188&P2=404&P3=2&P4=ageABhyvyjIpa7Rpg3hvKoKBS2dixN9F6n7unpdPtT%2fR8MVIPEjyRQMtsJ%2f1Xgbr84M4%2bcDcqgpD0JLqDmV4Cg%3d%3d | unknown | — | — | whitelisted |
5744 | svchost.exe | GET | 206 | 23.48.23.7:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/b649b6c2-4484-495a-96f2-2fd1ee2b66ca?P1=1743610188&P2=404&P3=2&P4=ageABhyvyjIpa7Rpg3hvKoKBS2dixN9F6n7unpdPtT%2fR8MVIPEjyRQMtsJ%2f1Xgbr84M4%2bcDcqgpD0JLqDmV4Cg%3d%3d | unknown | — | — | whitelisted |
5744 | svchost.exe | HEAD | 200 | 23.48.23.7:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/84d3e481-77df-49da-bc37-0a994069ddb9?P1=1743711880&P2=404&P3=2&P4=AXOEbMg6HPaD5qHlpS1R9hABnAC8uK2R40GN7iOH75VYvOn4gyFqFH3KYAV7gcemyqwSaND%2fsI9cr%2bOw9tmwtA%3d%3d | unknown | — | — | whitelisted |
5744 | svchost.exe | GET | 206 | 23.48.23.7:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/b649b6c2-4484-495a-96f2-2fd1ee2b66ca?P1=1743610188&P2=404&P3=2&P4=ageABhyvyjIpa7Rpg3hvKoKBS2dixN9F6n7unpdPtT%2fR8MVIPEjyRQMtsJ%2f1Xgbr84M4%2bcDcqgpD0JLqDmV4Cg%3d%3d | unknown | — | — | whitelisted |
5744 | svchost.exe | GET | 206 | 23.48.23.7:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/84d3e481-77df-49da-bc37-0a994069ddb9?P1=1743711880&P2=404&P3=2&P4=AXOEbMg6HPaD5qHlpS1R9hABnAC8uK2R40GN7iOH75VYvOn4gyFqFH3KYAV7gcemyqwSaND%2fsI9cr%2bOw9tmwtA%3d%3d | unknown | — | — | whitelisted |
5744 | svchost.exe | GET | 206 | 23.48.23.7:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/84d3e481-77df-49da-bc37-0a994069ddb9?P1=1743711880&P2=404&P3=2&P4=AXOEbMg6HPaD5qHlpS1R9hABnAC8uK2R40GN7iOH75VYvOn4gyFqFH3KYAV7gcemyqwSaND%2fsI9cr%2bOw9tmwtA%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2104 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 23.48.23.143:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
7468 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7732 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7732 | msedge.exe | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7732 | msedge.exe | 13.107.253.45:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7732 | msedge.exe | 140.82.121.3:443 | github.com | GITHUB | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
github.com |
| whitelisted |
business.bing.com |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
objects.githubusercontent.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |