| File name: | DOSBox0.74-3-win32-installer.exe |
| Full analysis: | https://app.any.run/tasks/d149c20f-3b71-4e5a-9249-ce15e22e1e6d |
| Verdict: | Malicious activity |
| Analysis date: | September 24, 2019, 18:58:20 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
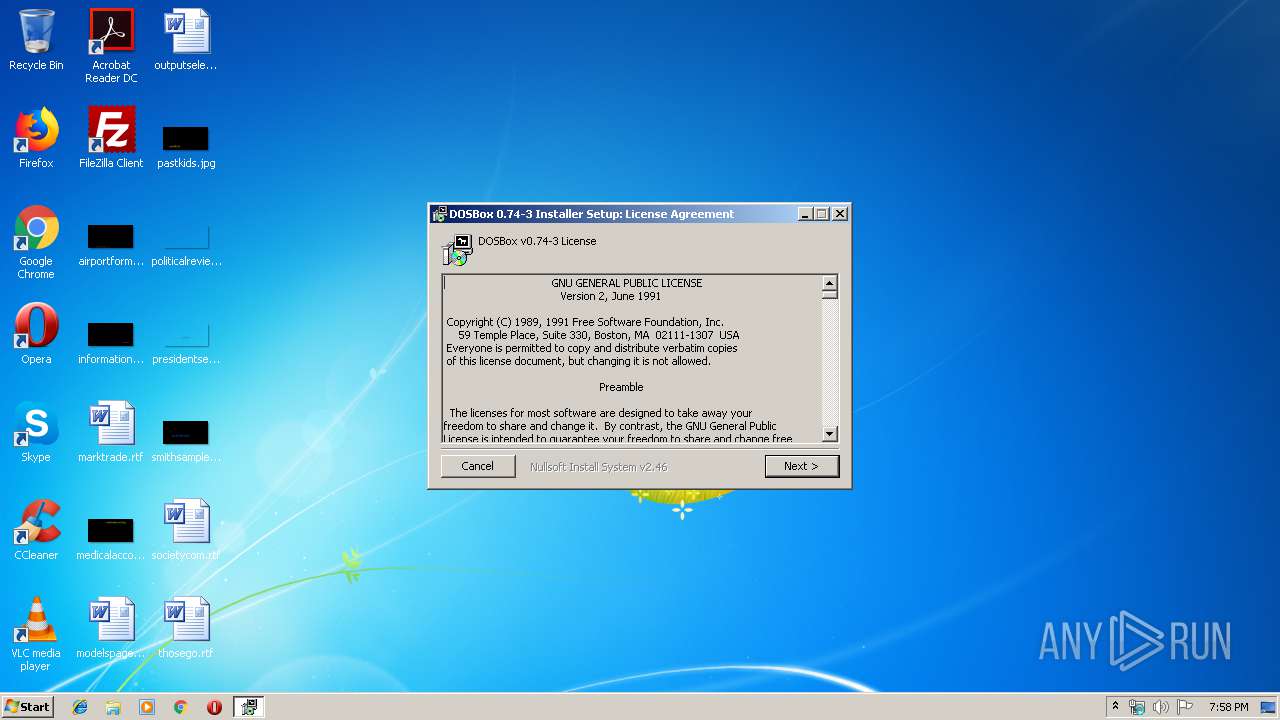
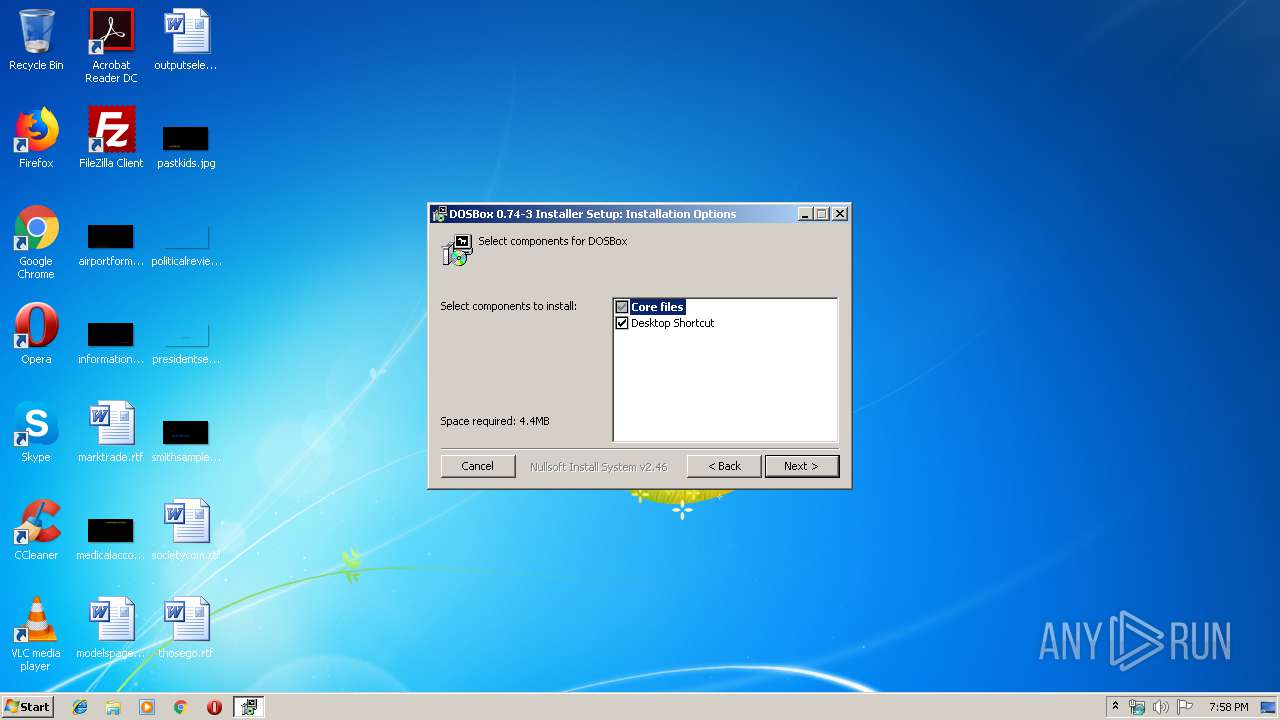
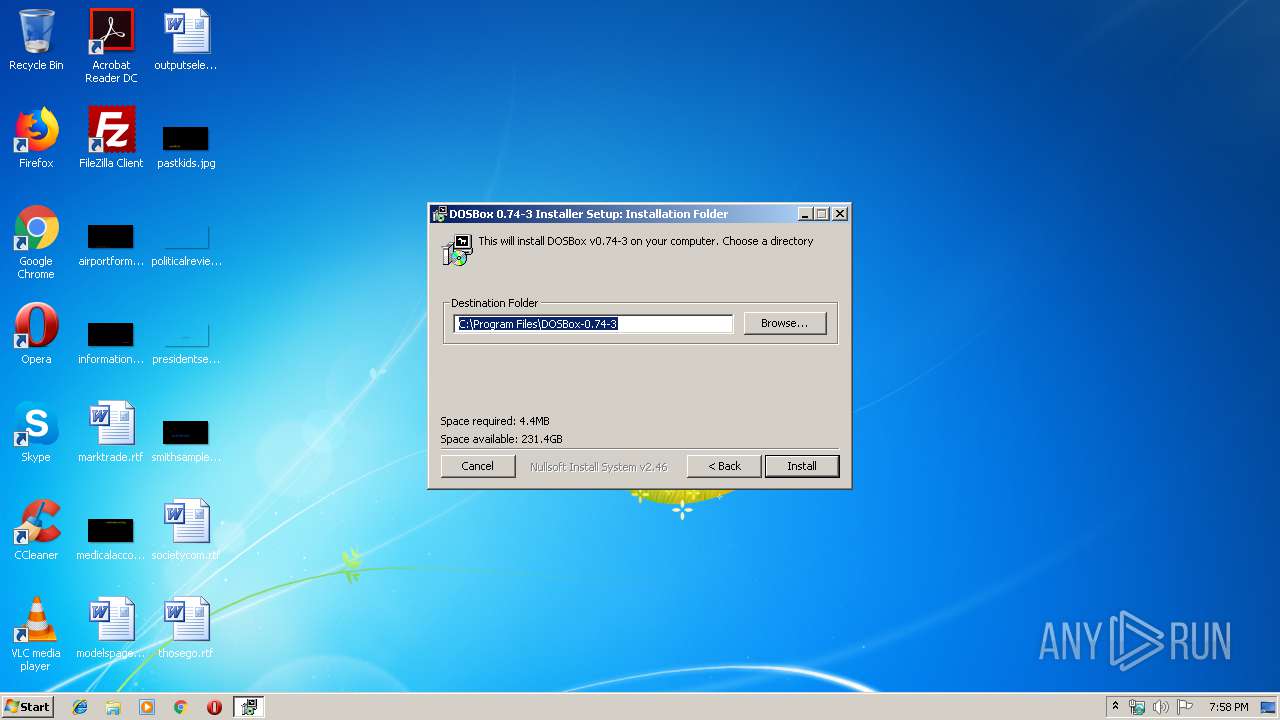
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 10F38D3D4B19C58C04D465BD1ACD24F0 |
| SHA1: | C8C1F5A5D17336607C886444518E74E3D1A4E041 |
| SHA256: | A9E270217D12867C2609D9423D1B2ED83FCF7CD08AEEEE3AB09A4AFDF9E9418E |
| SSDEEP: | 24576:TA3AA3f646/58tQN2UR7l/TR8EalSxNhCkQTCE2wJnGl0uTskAs+giMbfJyDS:QAAS54K2UH/1xw2wJntunAGrjb |
MALICIOUS
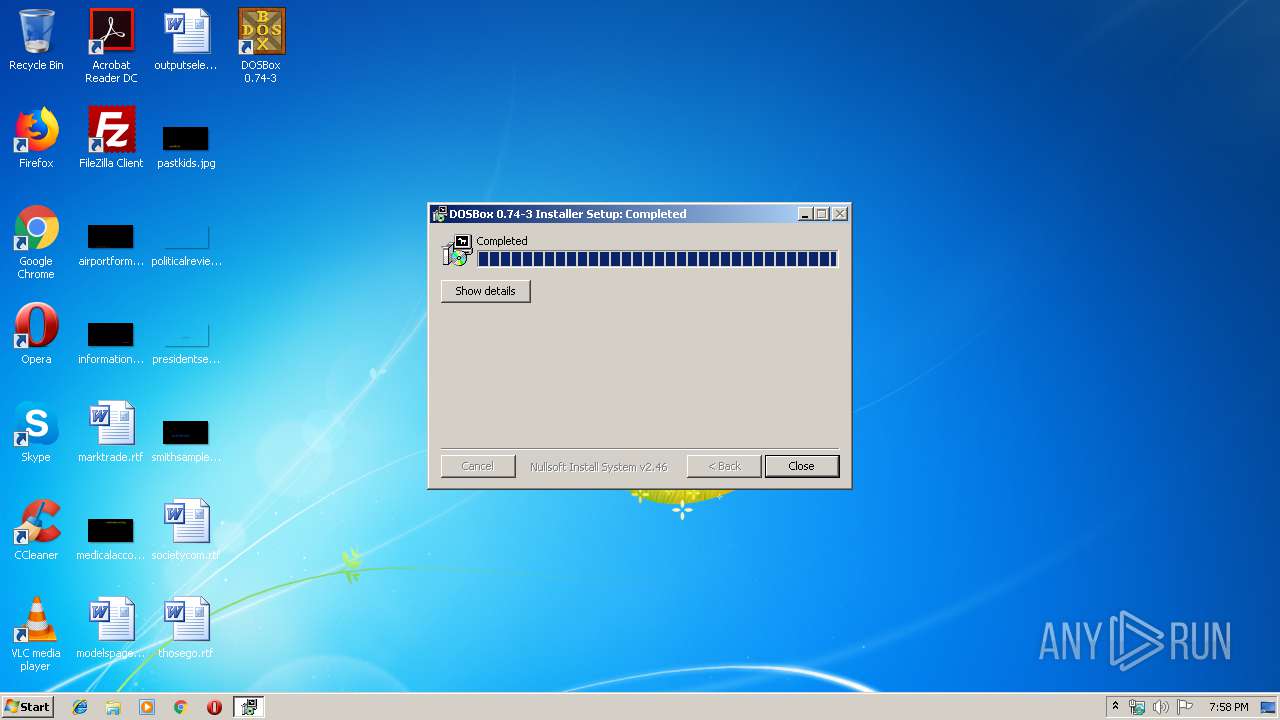
Loads dropped or rewritten executable
- DOSBox.exe (PID: 556)
Application was dropped or rewritten from another process
- DOSBox.exe (PID: 556)
SUSPICIOUS
Executable content was dropped or overwritten
- DOSBox0.74-3-win32-installer.exe (PID: 3508)
Creates files in the program directory
- DOSBox.exe (PID: 556)
- DOSBox0.74-3-win32-installer.exe (PID: 3508)
INFO
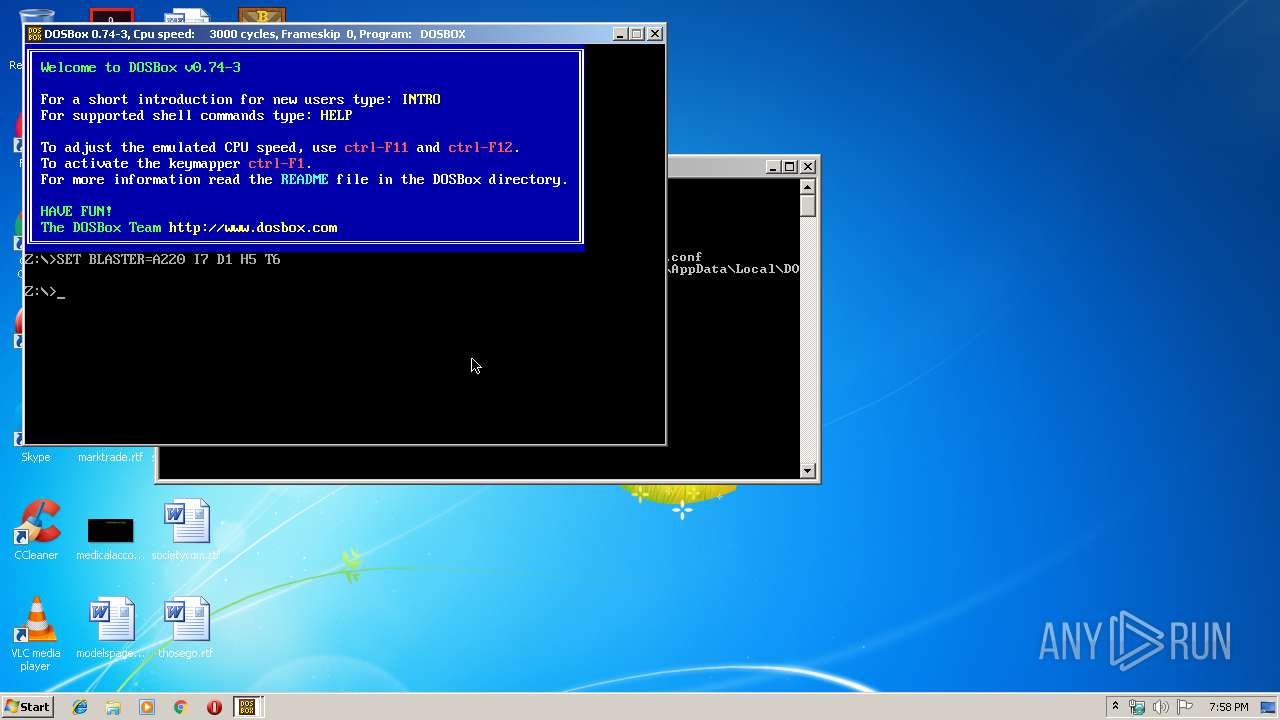
Manual execution by user
- DOSBox.exe (PID: 556)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | NSIS - Nullsoft Scriptable Install System (94.8) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (3.4) |
| .dll | | | Win32 Dynamic Link Library (generic) (0.7) |
| .exe | | | Win32 Executable (generic) (0.5) |
| .exe | | | Generic Win/DOS Executable (0.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2009:12:05 23:50:46+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 23552 |
| InitializedDataSize: | 119808 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x323c |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.74.3.0 |
| ProductVersionNumber: | 0.74.3.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | DOSBox Team |
| FileDescription: | DOSBox Installer |
| FileVersion: | 0.74.3.0 |
| LegalCopyright: | Copyright © 2002-2019 DOSBox Team |
| ProductName: | DOSBox 0.74-3 Installer |
| ProductVersion: | 0, 74, 3, 0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 05-Dec-2009 22:50:46 |
| Detected languages: |
|
| CompanyName: | DOSBox Team |
| FileDescription: | DOSBox Installer |
| FileVersion: | 0.74.3.0 |
| LegalCopyright: | Copyright © 2002-2019 DOSBox Team |
| ProductName: | DOSBox 0.74-3 Installer |
| ProductVersion: | 0, 74, 3, 0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 05-Dec-2009 22:50:46 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00005A5A | 0x00005C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.4177 |
.rdata | 0x00007000 | 0x00001190 | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.18163 |
.data | 0x00009000 | 0x0001AF98 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.70903 |
.ndata | 0x00024000 | 0x00008000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x0002C000 | 0x00001530 | 0x00001600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.20154 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.19512 | 727 | UNKNOWN | English - United States | RT_MANIFEST |
102 | 2.74309 | 184 | UNKNOWN | English - United States | RT_DIALOG |
103 | 2.16096 | 20 | UNKNOWN | English - United States | RT_GROUP_ICON |
104 | 2.6935 | 316 | UNKNOWN | English - United States | RT_DIALOG |
105 | 2.66174 | 256 | UNKNOWN | English - United States | RT_DIALOG |
106 | 2.88094 | 284 | UNKNOWN | English - United States | RT_DIALOG |
107 | 2.62276 | 196 | UNKNOWN | English - United States | RT_DIALOG |
110 | 3.22336 | 872 | UNKNOWN | English - United States | RT_BITMAP |
111 | 2.48825 | 96 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
VERSION.dll |
ole32.dll |
Total processes
40
Monitored processes
3
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 556 | "C:\Program Files\DOSBox-0.74-3\DOSBox.exe" -userconf | C:\Program Files\DOSBox-0.74-3\DOSBox.exe | — | explorer.exe | |||||||||||
User: admin Company: DOSBox Team Integrity Level: MEDIUM Description: DOSBox DOS Emulator Exit code: 0 Version: 0, 74, 3, 0 Modules
| |||||||||||||||
| 3320 | "C:\Users\admin\AppData\Local\Temp\DOSBox0.74-3-win32-installer.exe" | C:\Users\admin\AppData\Local\Temp\DOSBox0.74-3-win32-installer.exe | — | explorer.exe | |||||||||||
User: admin Company: DOSBox Team Integrity Level: MEDIUM Description: DOSBox Installer Exit code: 3221226540 Version: 0.74.3.0 | |||||||||||||||
| 3508 | "C:\Users\admin\AppData\Local\Temp\DOSBox0.74-3-win32-installer.exe" | C:\Users\admin\AppData\Local\Temp\DOSBox0.74-3-win32-installer.exe | explorer.exe | ||||||||||||
User: admin Company: DOSBox Team Integrity Level: HIGH Description: DOSBox Installer Exit code: 0 Version: 0.74.3.0 Modules
| |||||||||||||||
Total events
462
Read events
454
Write events
8
Delete events
0
Modification events
| (PID) Process: | (556) DOSBox.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\DirectDraw\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: DOSBox.exe | |||
| (PID) Process: | (556) DOSBox.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\DirectDraw\MostRecentApplication |
| Operation: | write | Name: | ID |
Value: 1561553625 | |||
| (PID) Process: | (556) DOSBox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\DirectInput\MostRecentApplication |
| Operation: | write | Name: | Version |
Value: 0A050000 | |||
| (PID) Process: | (556) DOSBox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\DirectInput\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: DOSBOX.EXE | |||
| (PID) Process: | (556) DOSBox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\DirectInput\MostRecentApplication |
| Operation: | write | Name: | Id |
Value: DOSBOX.EXE5D136AD900392800 | |||
| (PID) Process: | (556) DOSBox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\DirectInput\MostRecentApplication |
| Operation: | write | Name: | MostRecentStart |
Value: 59E8B3140A73D501 | |||
Executable files
5
Suspicious files
0
Text files
14
Unknown types
11
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3508 | DOSBox0.74-3-win32-installer.exe | C:\Program Files\DOSBox-0.74-3\DOSBox 0.74-3 Manual.txt | text | |
MD5:F9F045EC1C5FFE00476599F50622DE05 | SHA256:63D0A0C6C2D3DB9B070CE83C101BA06EB836F6A6BD187094E9FC6B78EED735D8 | |||
| 3508 | DOSBox0.74-3-win32-installer.exe | C:\Program Files\DOSBox-0.74-3\Documentation\AUTHORS.txt | text | |
MD5:5E2EAB4329111BA8053F8C4AD04A04CE | SHA256:5A0D89DA929C7241B2DA13F2AE9407937F0A7E103698E179E443104E470DFA17 | |||
| 3508 | DOSBox0.74-3-win32-installer.exe | C:\Program Files\DOSBox-0.74-3\Documentation\THANKS.txt | text | |
MD5:366E90C5B46ACA9E238B8590C11CDD24 | SHA256:ACD9CBB904EBCEA9AD6D0D871A1131C5262A0BB8BCE94DFAF21EE4ED5140B45E | |||
| 3508 | DOSBox0.74-3-win32-installer.exe | C:\Program Files\DOSBox-0.74-3\Documentation\INSTALL.txt | text | |
MD5:A1CE6AC808C21C12CE64509B07CC15A6 | SHA256:49F4038A4E453ABDA45D480FC046BD86B6544FDE5A32928EA8557E318A624E2C | |||
| 3508 | DOSBox0.74-3-win32-installer.exe | C:\Program Files\DOSBox-0.74-3\Documentation\COPYING.txt | text | |
MD5:46AAF69A91703493B666F212A04F2D8D | SHA256:DA0ECA0FB517AC939D167924C9D4B3F8750A6B7191932EF2CB145ACFA624AC7E | |||
| 3508 | DOSBox0.74-3-win32-installer.exe | C:\ProgramData\Microsoft\Windows\Start Menu\Programs\DOSBox-0.74-3\DOSBox 0.74-3.lnk | lnk | |
MD5:— | SHA256:— | |||
| 3508 | DOSBox0.74-3-win32-installer.exe | C:\ProgramData\Microsoft\Windows\Start Menu\Programs\DOSBox-0.74-3\Extras\DOSBox 0.74-3 (noconsole).lnk | lnk | |
MD5:— | SHA256:— | |||
| 3508 | DOSBox0.74-3-win32-installer.exe | C:\ProgramData\Microsoft\Windows\Start Menu\Programs\DOSBox-0.74-3\DOSBox 0.74-3 Manual.lnk | lnk | |
MD5:— | SHA256:— | |||
| 3508 | DOSBox0.74-3-win32-installer.exe | C:\Program Files\DOSBox-0.74-3\Documentation\NEWS.txt | text | |
MD5:2BE334FC63E831003BFFFA872183ED18 | SHA256:6A77A8B3EF189D5376854FF4EA9C6F060D676B7A81AAF8DF74DC444AE5B867BD | |||
| 3508 | DOSBox0.74-3-win32-installer.exe | C:\Program Files\DOSBox-0.74-3\Reset Options.bat | text | |
MD5:029A3BEF661B34C3F7C4713544A28DA5 | SHA256:4B340C08696AAB9B06742C763B332F43A4DE9930177A4C9D240B2EA1A0E5E75D | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report