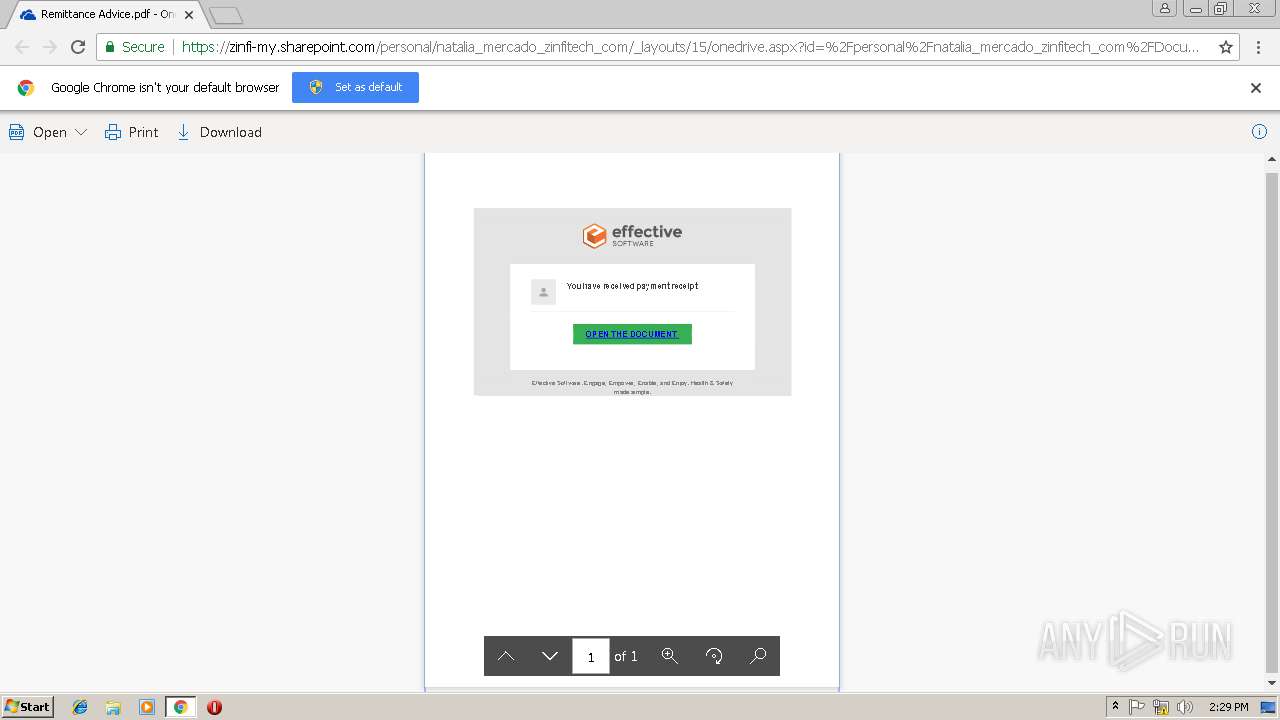
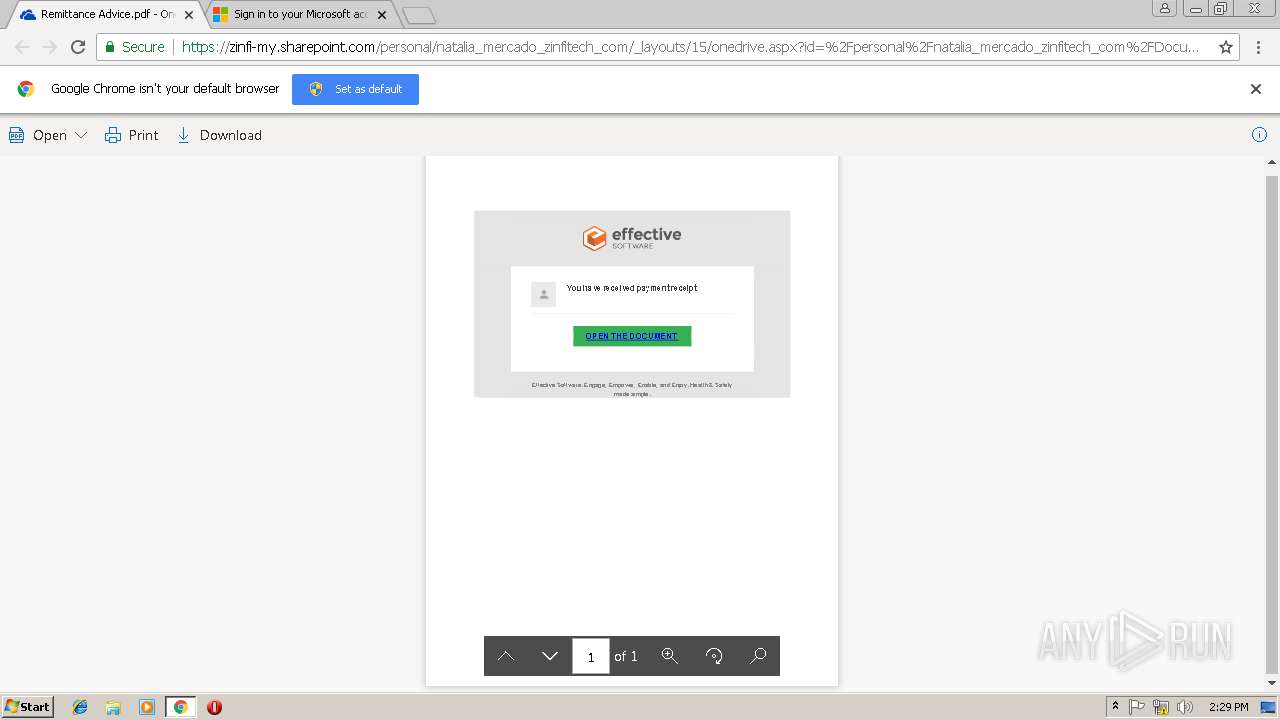
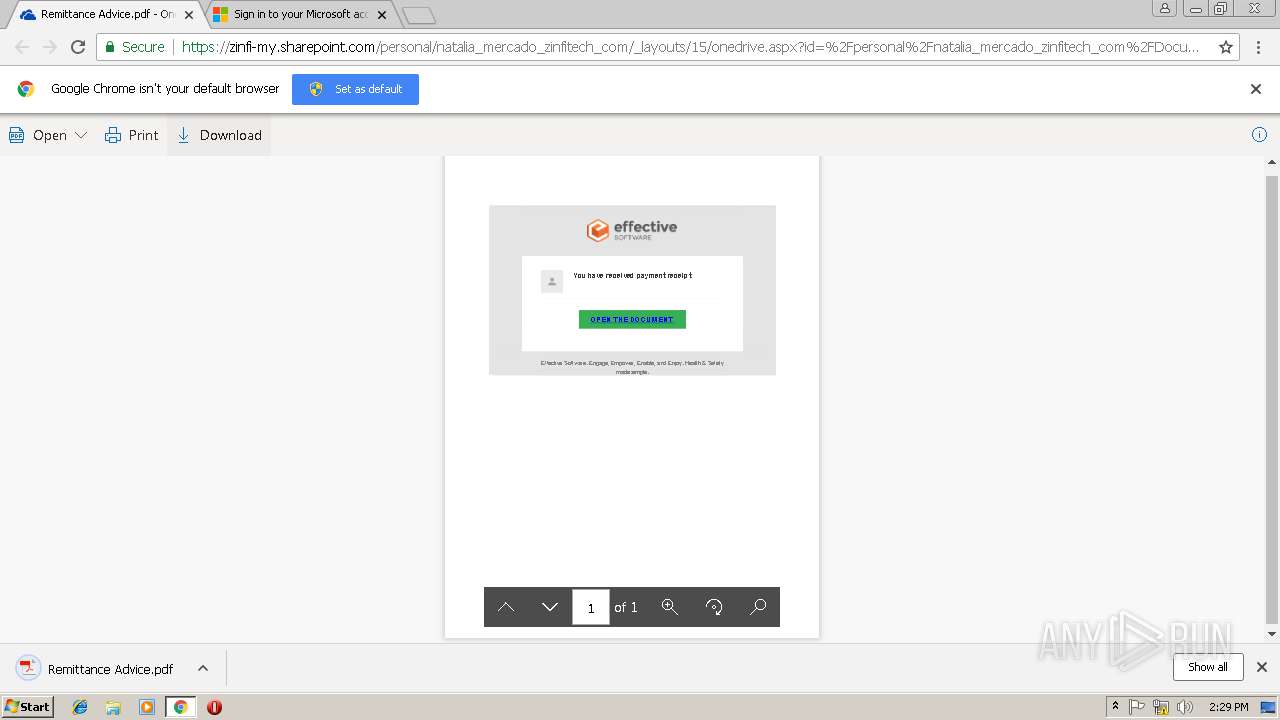
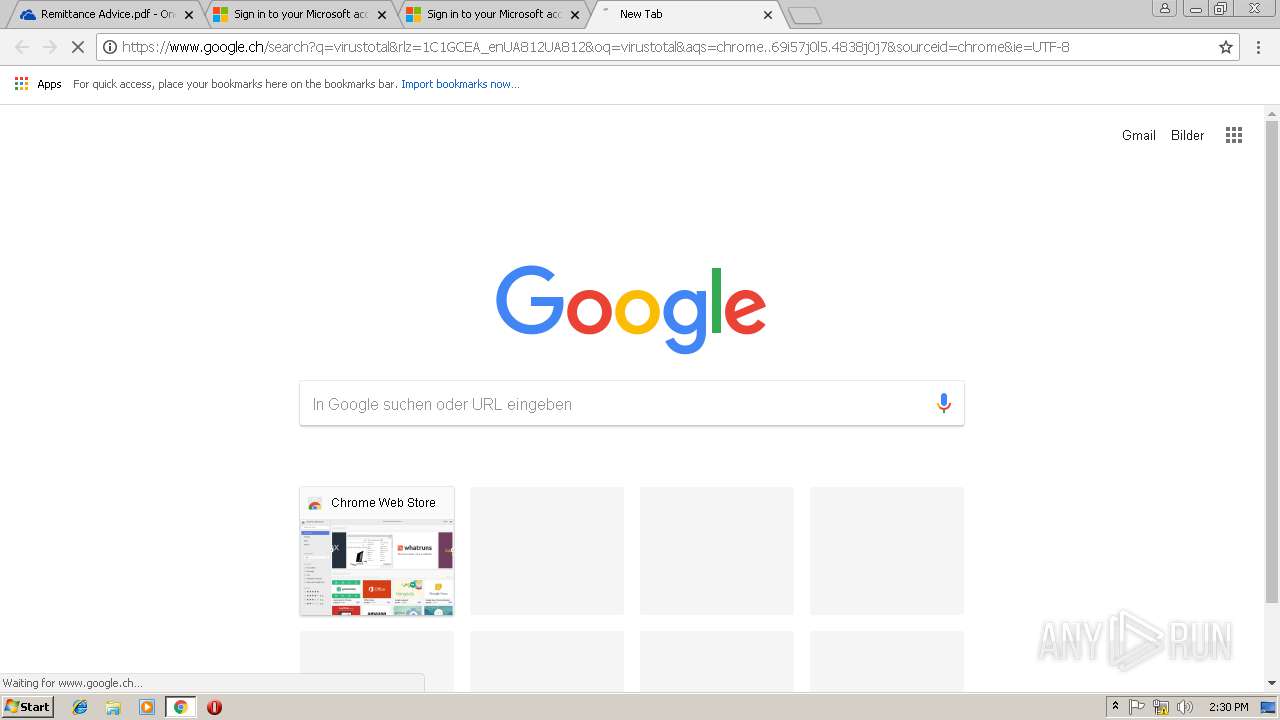
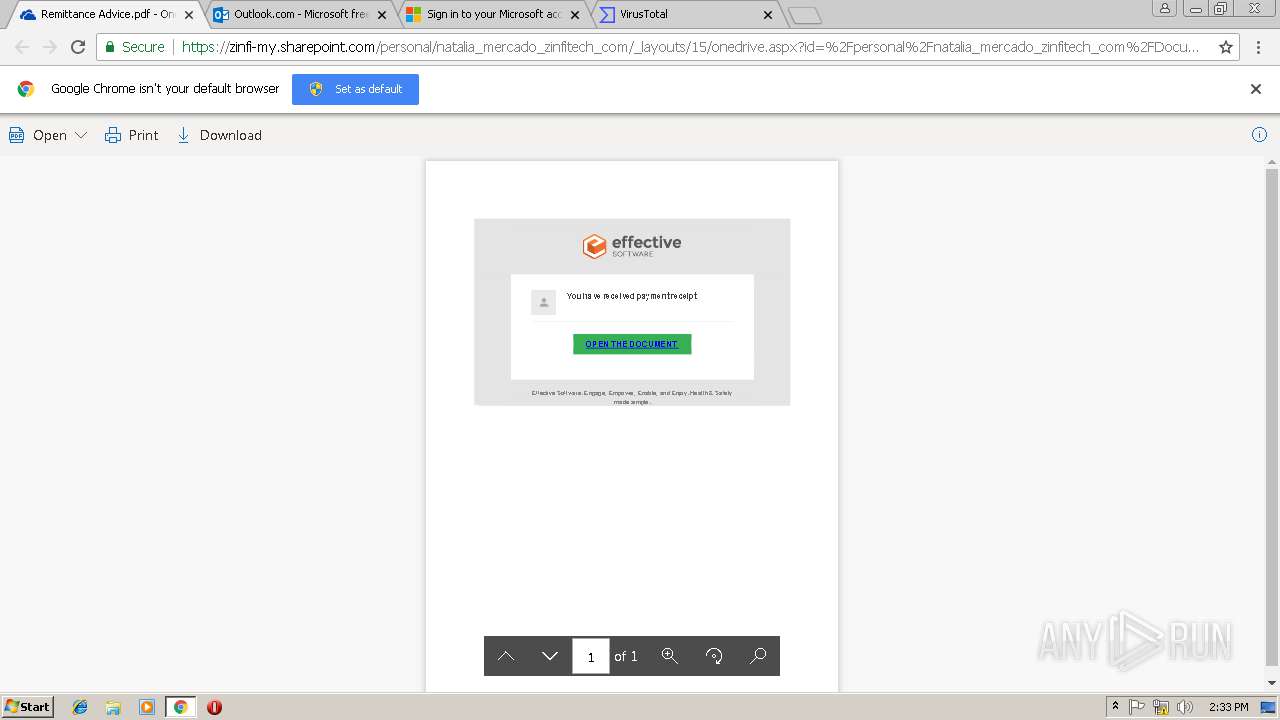
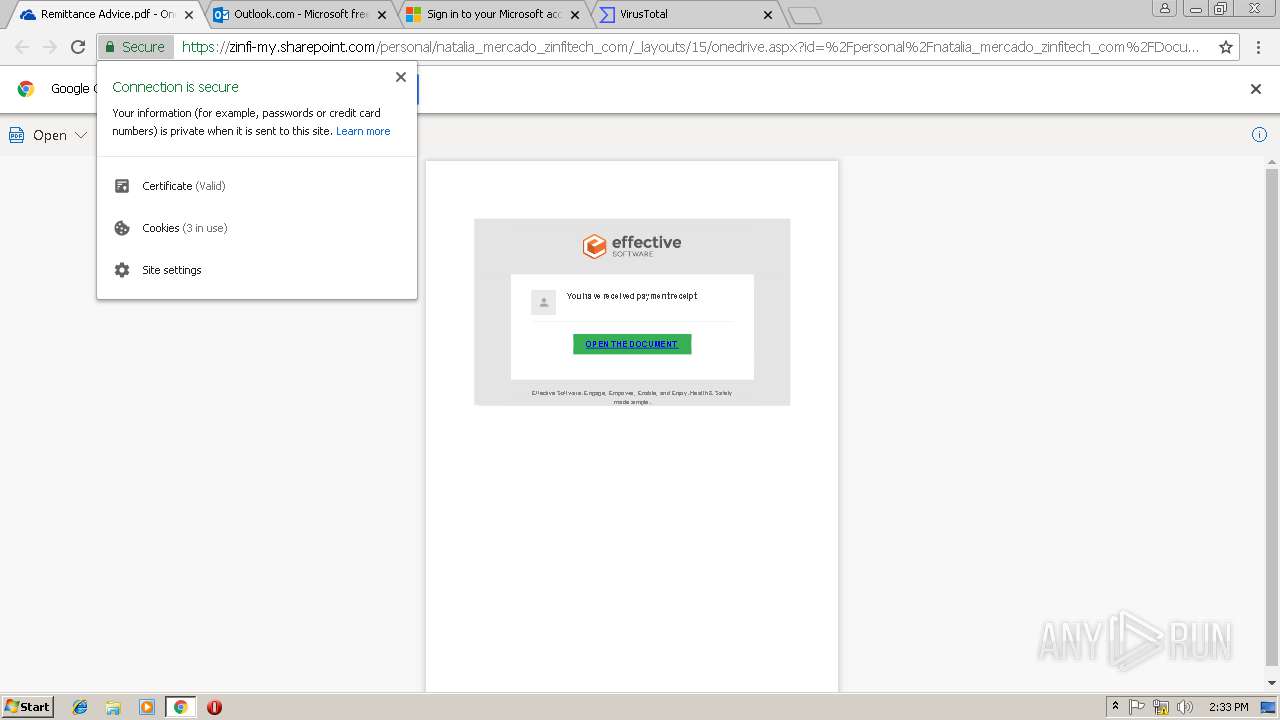
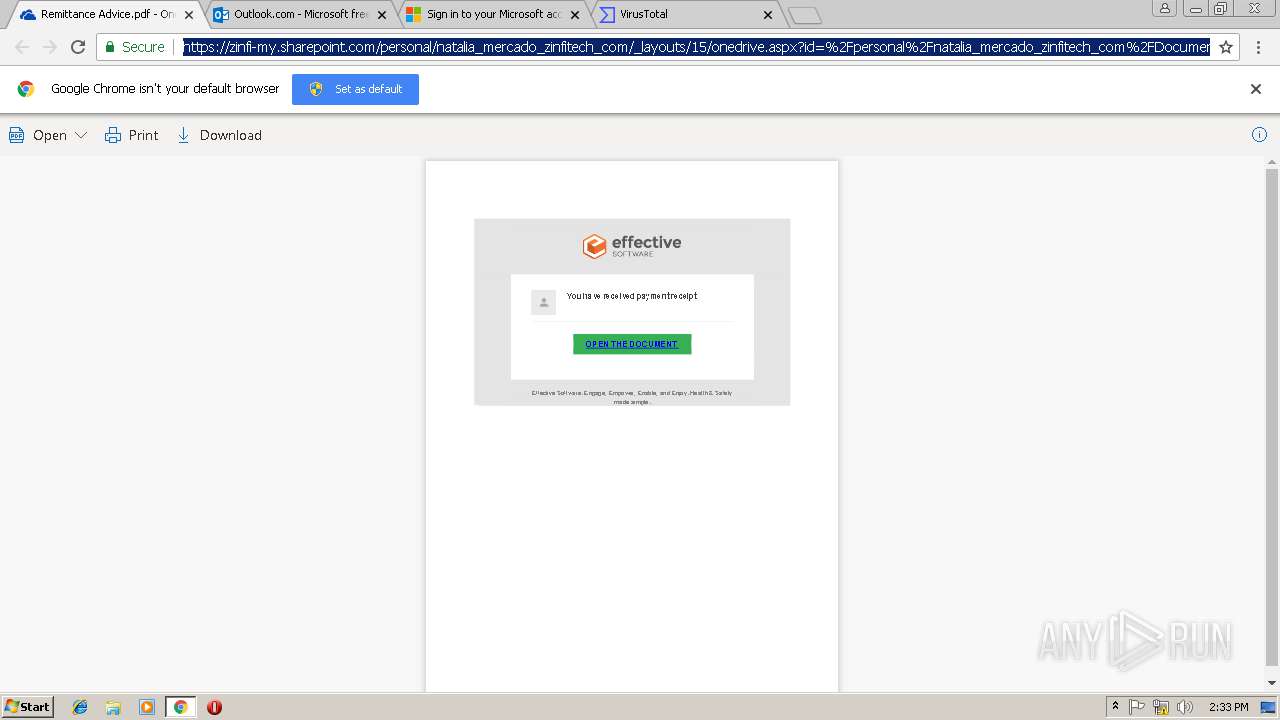
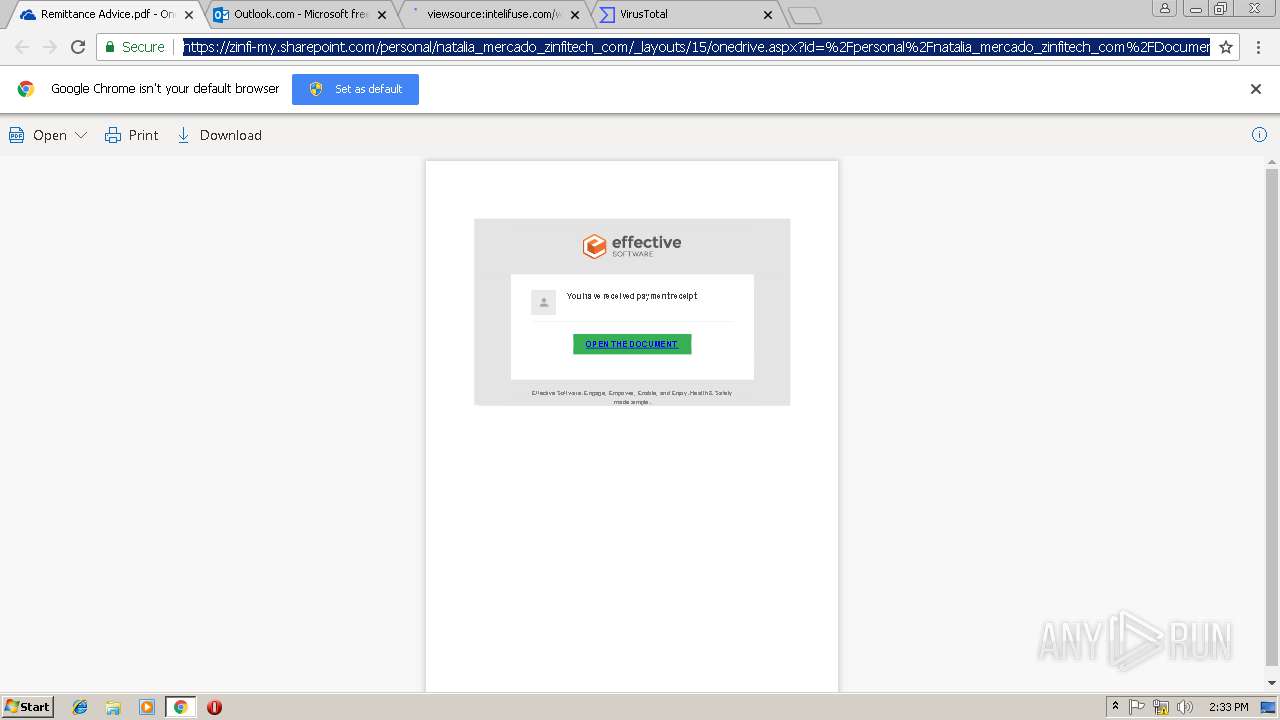
| URL: | https://zinfi-my.sharepoint.com:443/:b:/g/personal/natalia_mercado_zinfitech_com/EenzcDSmlQZBoCNEdDCuhZYBuXw5tHc0LADL0eTLKp5F8Q?e=4%3agm3Gnd&at=9 |
| Full analysis: | https://app.any.run/tasks/0a024c8e-9f7c-4772-b264-1d1bc63e5ca5 |
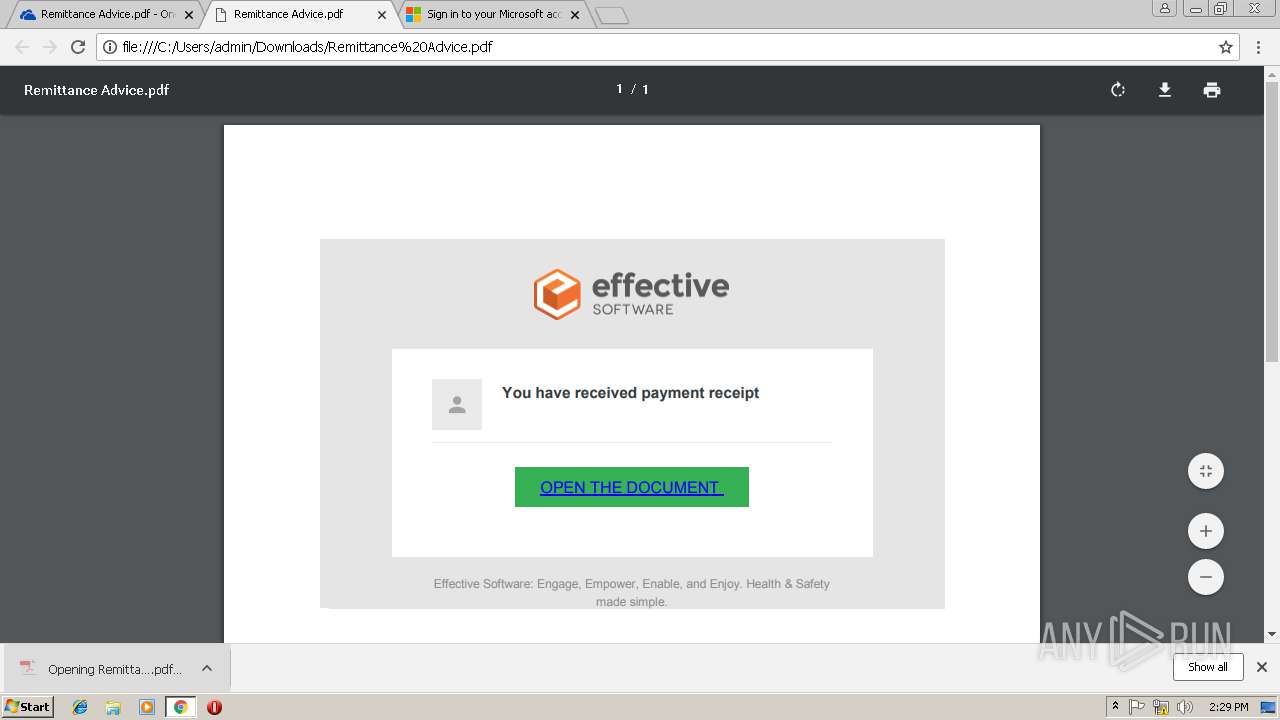
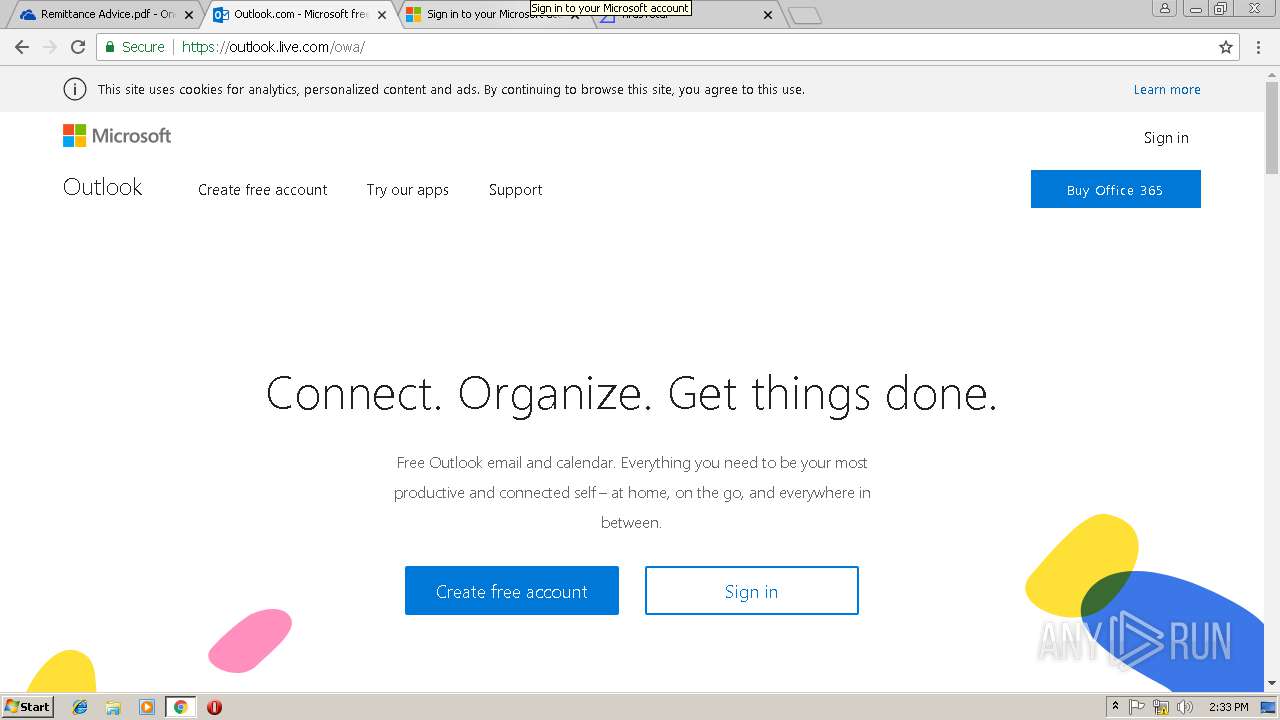
| Verdict: | Malicious activity |
| Analysis date: | March 14, 2019, 14:28:54 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 4AE63B10F79533011E6E37AE5043A727 |
| SHA1: | 3402548AF794CB9441F57251DC3763F4893FF8DB |
| SHA256: | A9D4D470986FDE4147B1932C71CBB836F76E289C063D0F6B73E7A64CF3521243 |
| SSDEEP: | 3:N88IcjArLnuhKqGSLERgtlG8dQh6SmsInVCKA6jdjA8fIlL1Ejn:2ZcjAfuhtERg/G8do6Sh3jhRcn |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- chrome.exe (PID: 3008)
Reads Internet Cache Settings
- chrome.exe (PID: 3008)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
51
Monitored processes
22
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1028 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=980,3031516371800422712,2667241742975915268,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=11BFF5CE3237868FC9DA1CE0606B0AEB --mojo-platform-channel-handle=1040 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 1168 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=980,3031516371800422712,2667241742975915268,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=36E677C6919D4E349CBA64FBE0ABFC08 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=36E677C6919D4E349CBA64FBE0ABFC08 --renderer-client-id=18 --mojo-platform-channel-handle=3556 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 1716 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=980,3031516371800422712,2667241742975915268,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=69A566B0E9E24AF3FA5D55A6D5966237 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=69A566B0E9E24AF3FA5D55A6D5966237 --renderer-client-id=20 --mojo-platform-channel-handle=3640 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 1968 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=980,3031516371800422712,2667241742975915268,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=C9CD61B06156A0E1AAECBD8D7E7FCA4C --mojo-platform-channel-handle=4392 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2100 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=980,3031516371800422712,2667241742975915268,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=ECACD521019436AEC552B9D33C7E1D33 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=ECACD521019436AEC552B9D33C7E1D33 --renderer-client-id=21 --mojo-platform-channel-handle=616 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2172 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=980,3031516371800422712,2667241742975915268,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=1589ED1621EB398A8A2DFB852A1EB9CD --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1589ED1621EB398A8A2DFB852A1EB9CD --renderer-client-id=7 --mojo-platform-channel-handle=4000 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2212 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=980,3031516371800422712,2667241742975915268,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=AD9AFED6430581C0998F609BB4A14815 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=AD9AFED6430581C0998F609BB4A14815 --renderer-client-id=15 --mojo-platform-channel-handle=3416 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2652 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=980,3031516371800422712,2667241742975915268,131072 --enable-features=PasswordImport --service-pipe-token=31EBFD8250B2CB9C630FA4B921D6DC7D --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=31EBFD8250B2CB9C630FA4B921D6DC7D --renderer-client-id=4 --mojo-platform-channel-handle=1888 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2708 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=980,3031516371800422712,2667241742975915268,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=CA63A8B16B2038C884AF5849AC20E6AA --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=CA63A8B16B2038C884AF5849AC20E6AA --renderer-client-id=6 --mojo-platform-channel-handle=3584 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2992 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=3012 --on-initialized-event-handle=304 --parent-handle=308 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
Total events
588
Read events
505
Write events
79
Delete events
4
Modification events
| (PID) Process: | (3008) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3008) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3008) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2992) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3008-13197047349295375 |
Value: 259 | |||
| (PID) Process: | (3008) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3008) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3008) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3516-13180984670829101 |
Value: 0 | |||
| (PID) Process: | (3008) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3008) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3008-13197047349295375 |
Value: 259 | |||
| (PID) Process: | (3008) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
0
Suspicious files
92
Text files
163
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3008 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\78fdda18-02df-428f-8ebf-437b6979f591.tmp | — | |
MD5:— | SHA256:— | |||
| 3008 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3008 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3008 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ae566d00-6197-406d-88f6-52545c55f263.tmp | — | |
MD5:— | SHA256:— | |||
| 3008 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3008 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\Database\LOG.old~RF20e40b.TMP | text | |
MD5:— | SHA256:— | |||
| 3008 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3008 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Thumbnails\LOG.old~RF20e488.TMP | text | |
MD5:— | SHA256:— | |||
| 3008 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\CURRENT | text | |
MD5:EDD71DD3BADE6CD69FF623E1CCF7012D | SHA256:BEFEA596B4676CCF7CC37EA8048044BFA0556C8931D76FDEEB693D20264E50D6 | |||
| 3008 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF20e40b.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
15
TCP/UDP connections
73
DNS requests
37
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
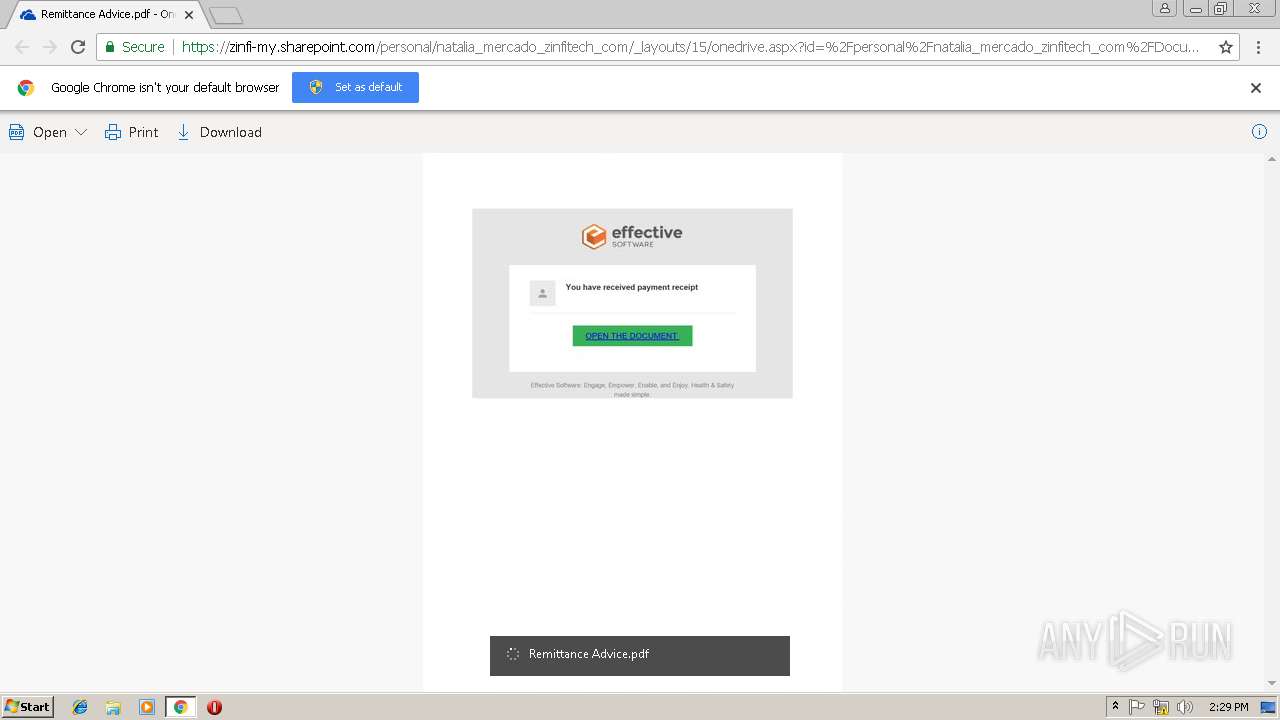
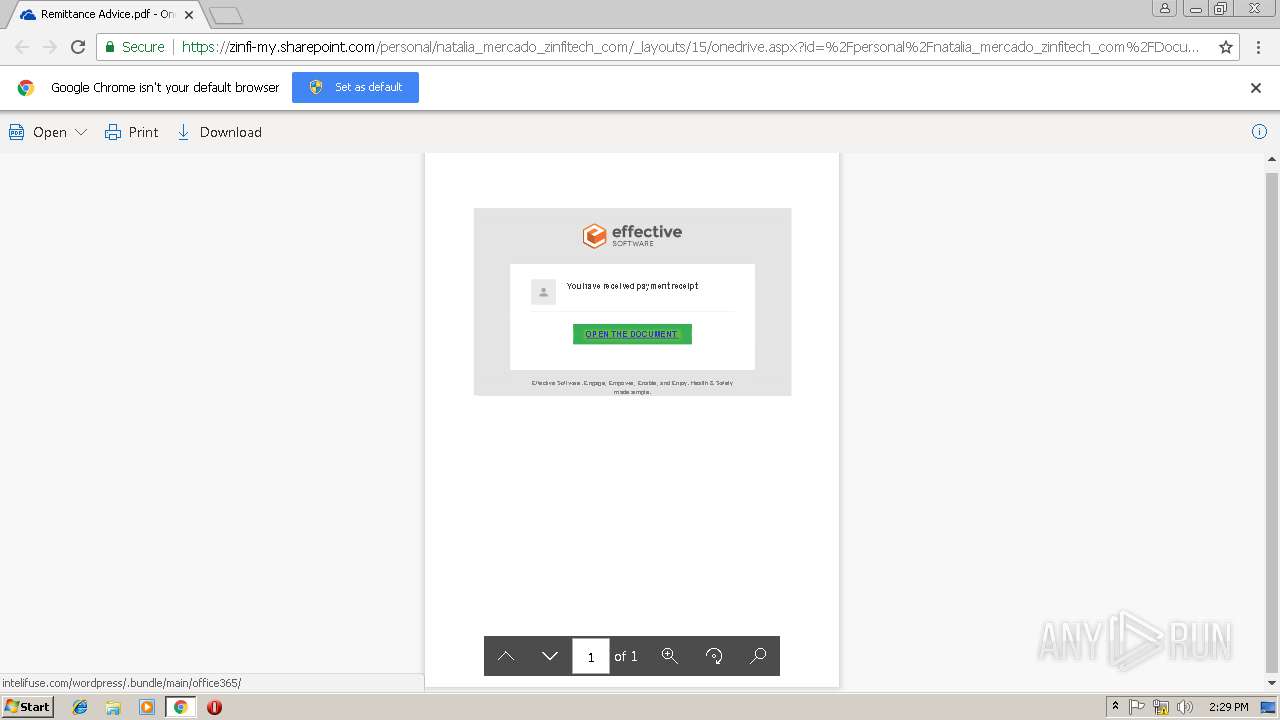
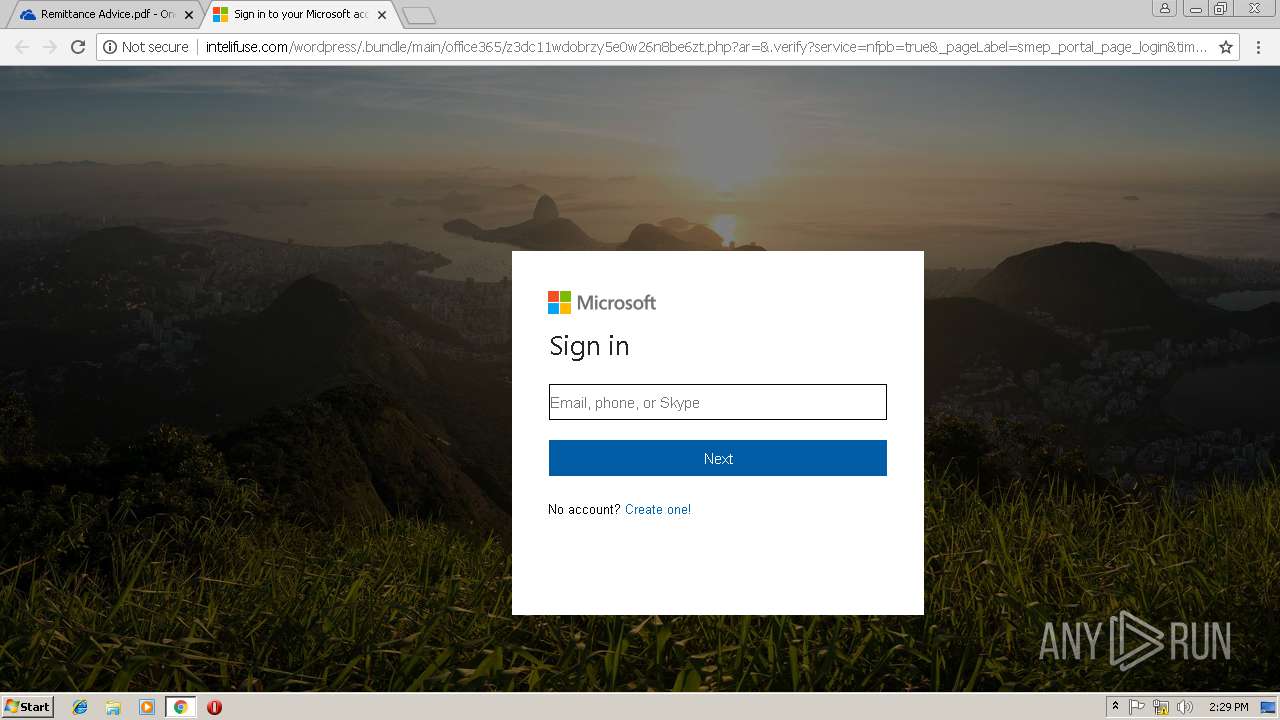
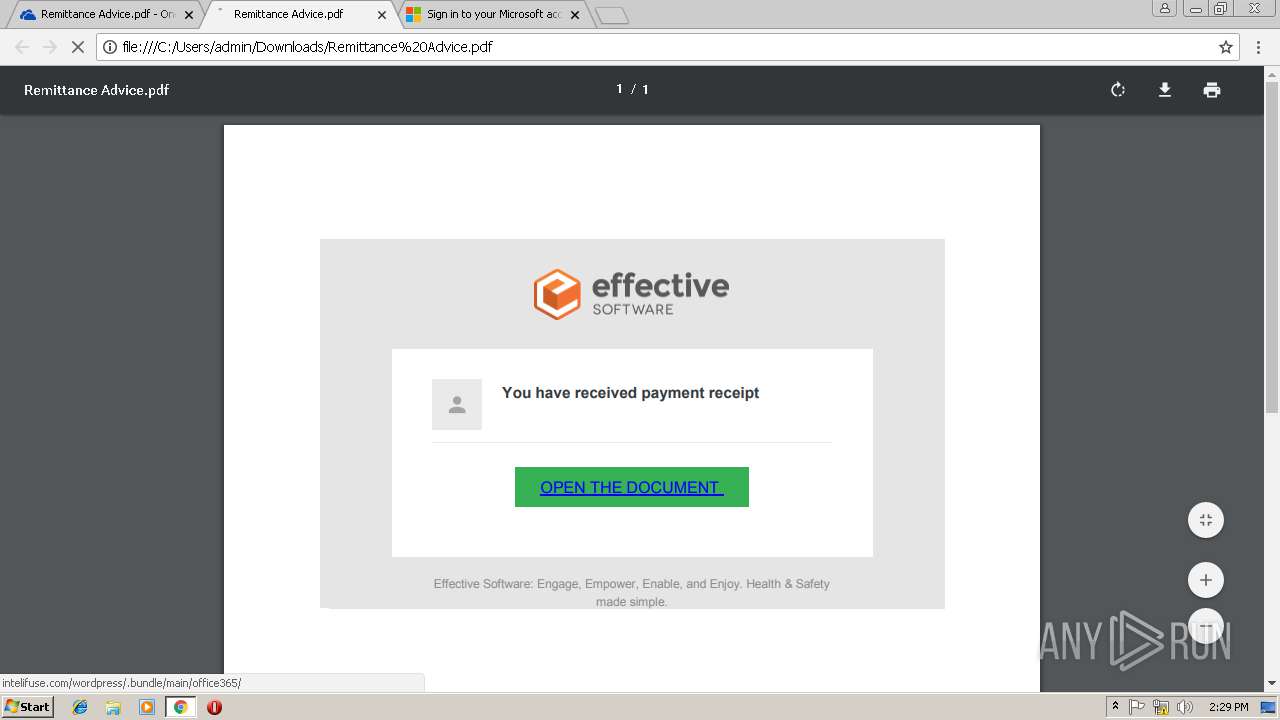
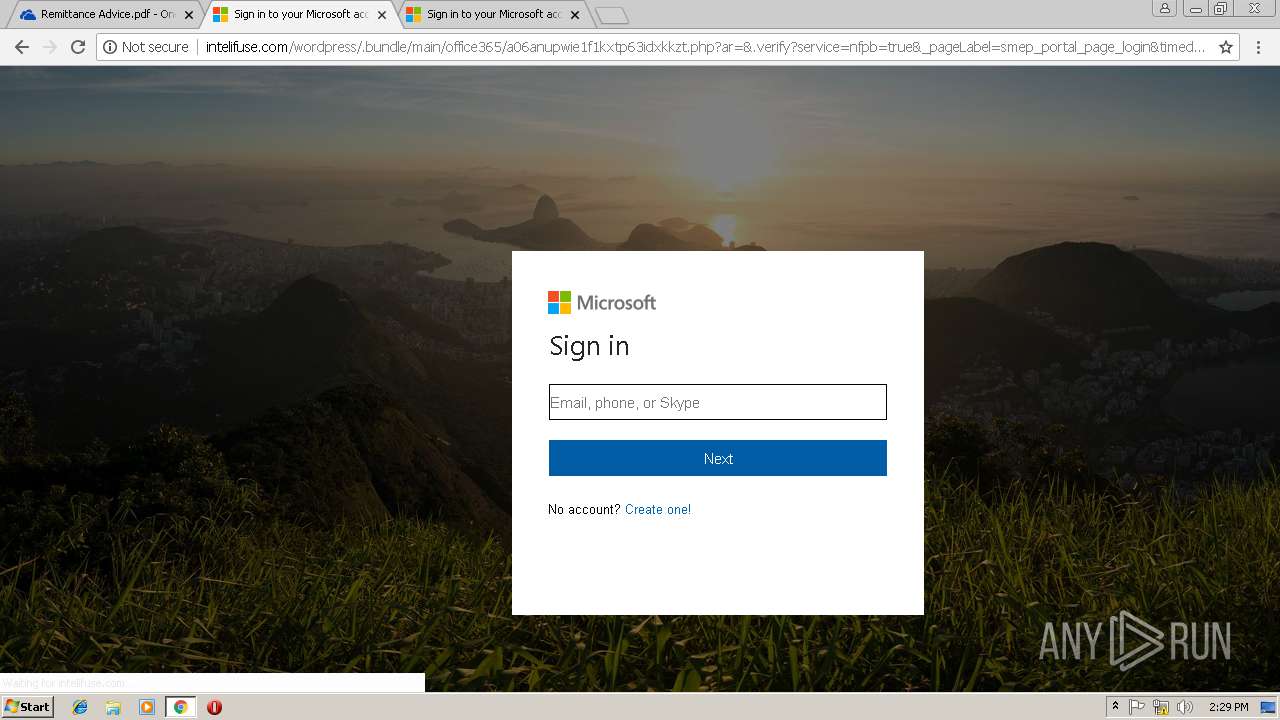
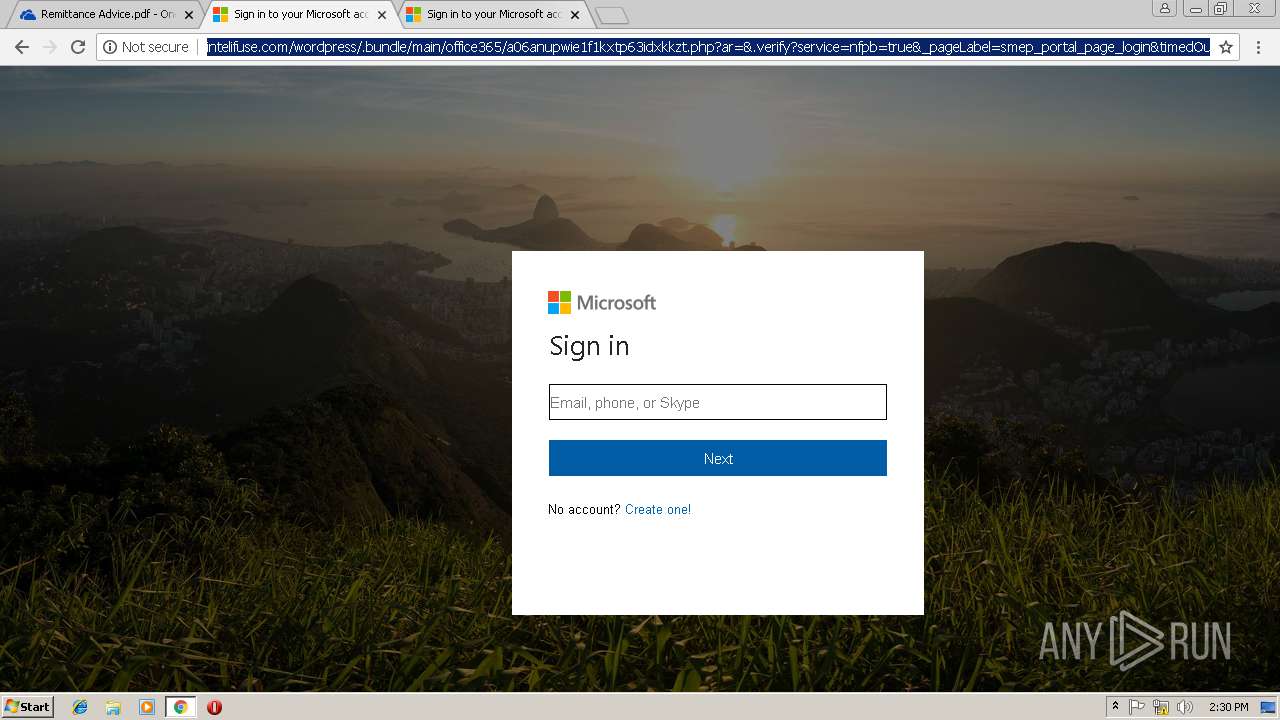
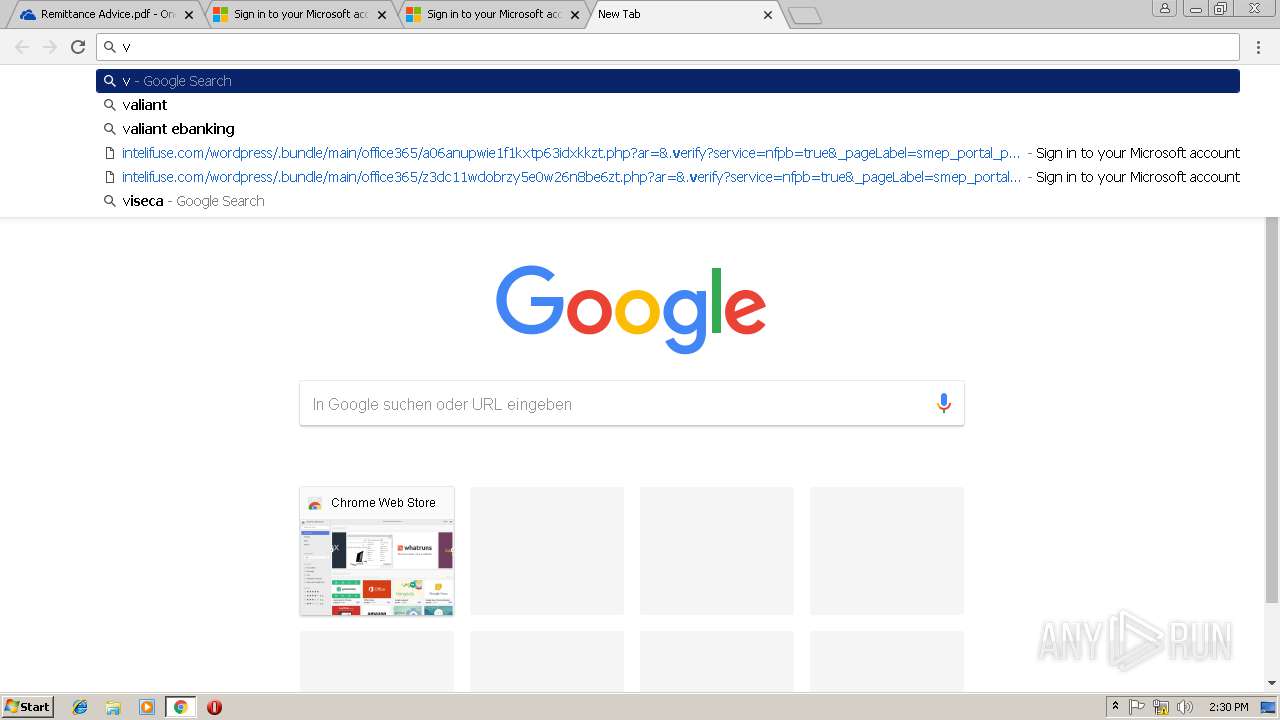
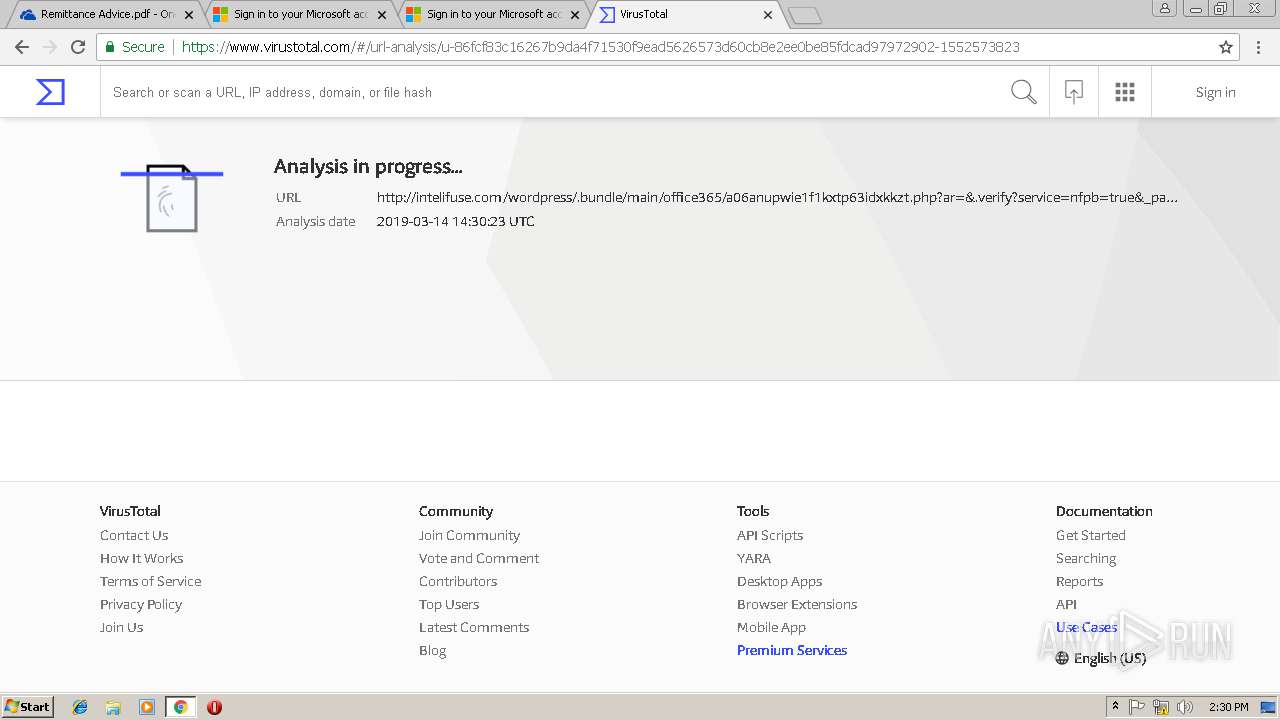
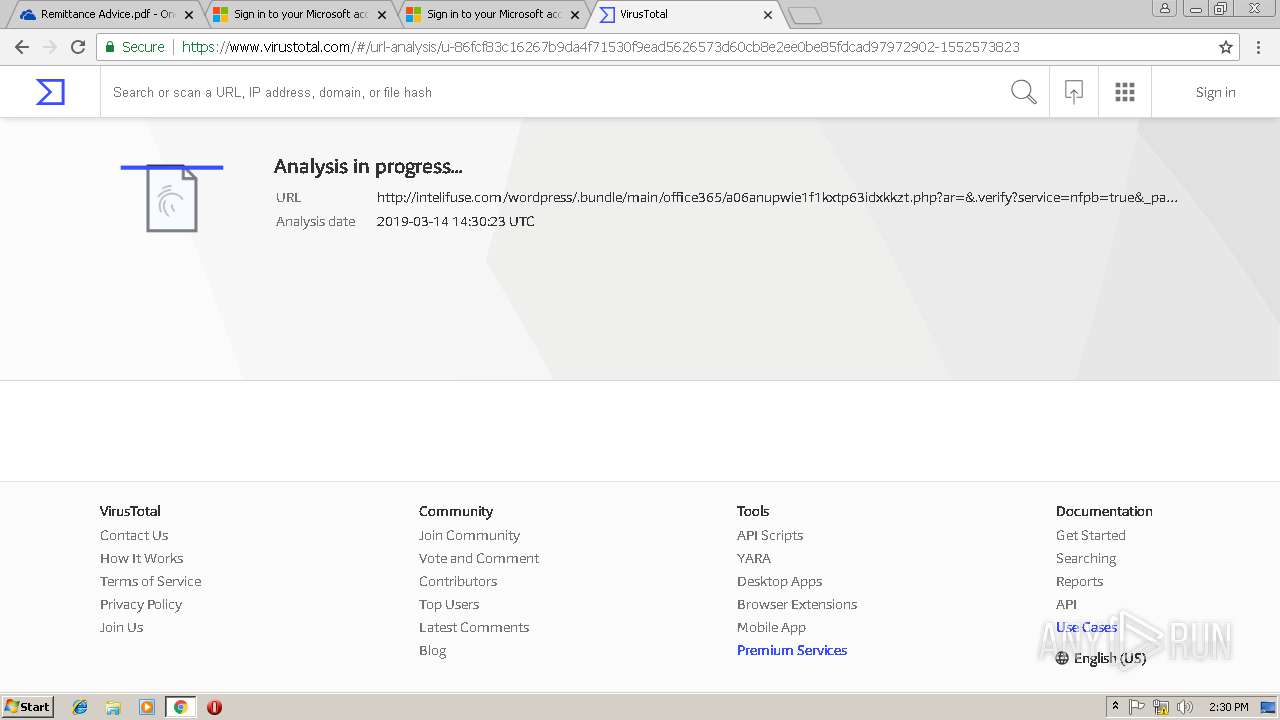
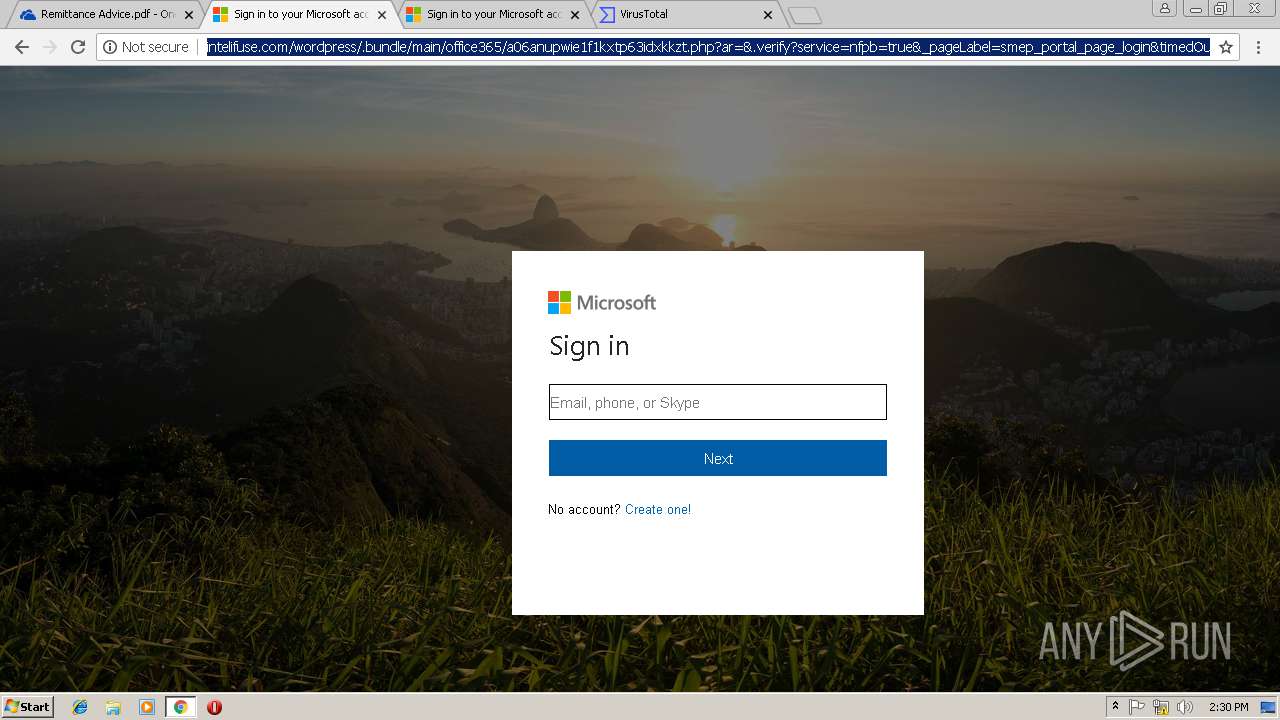
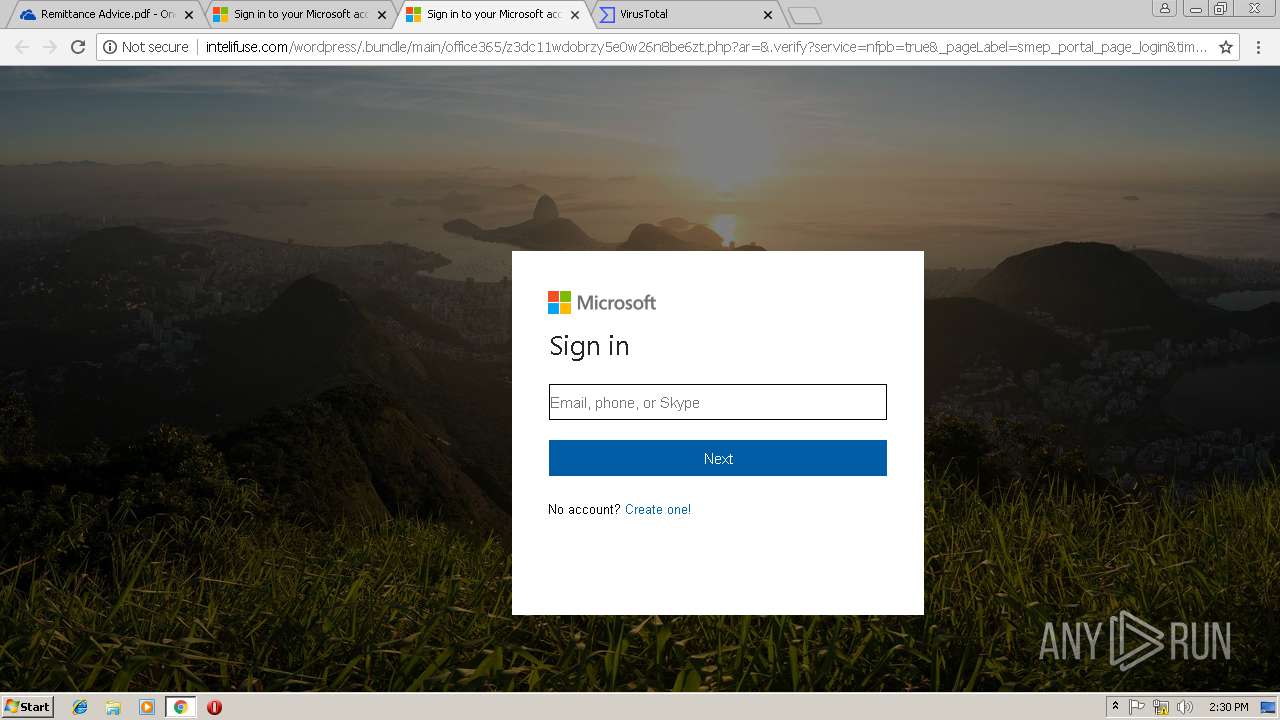
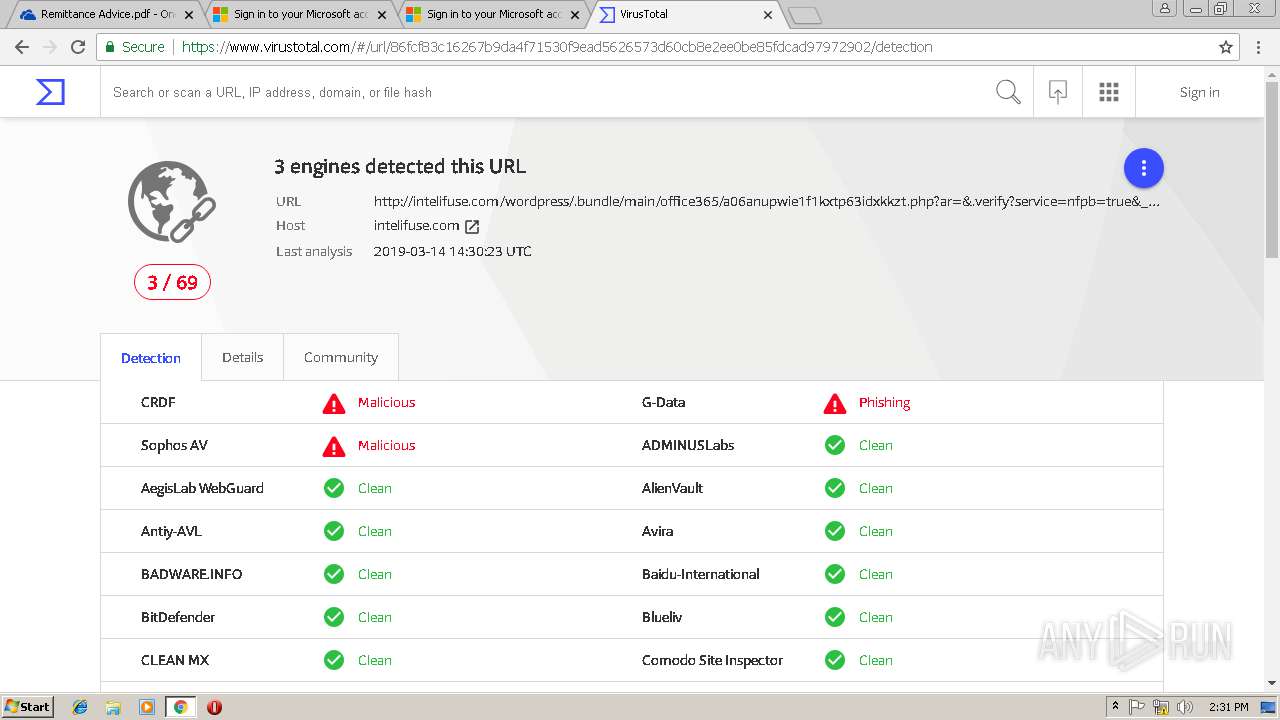
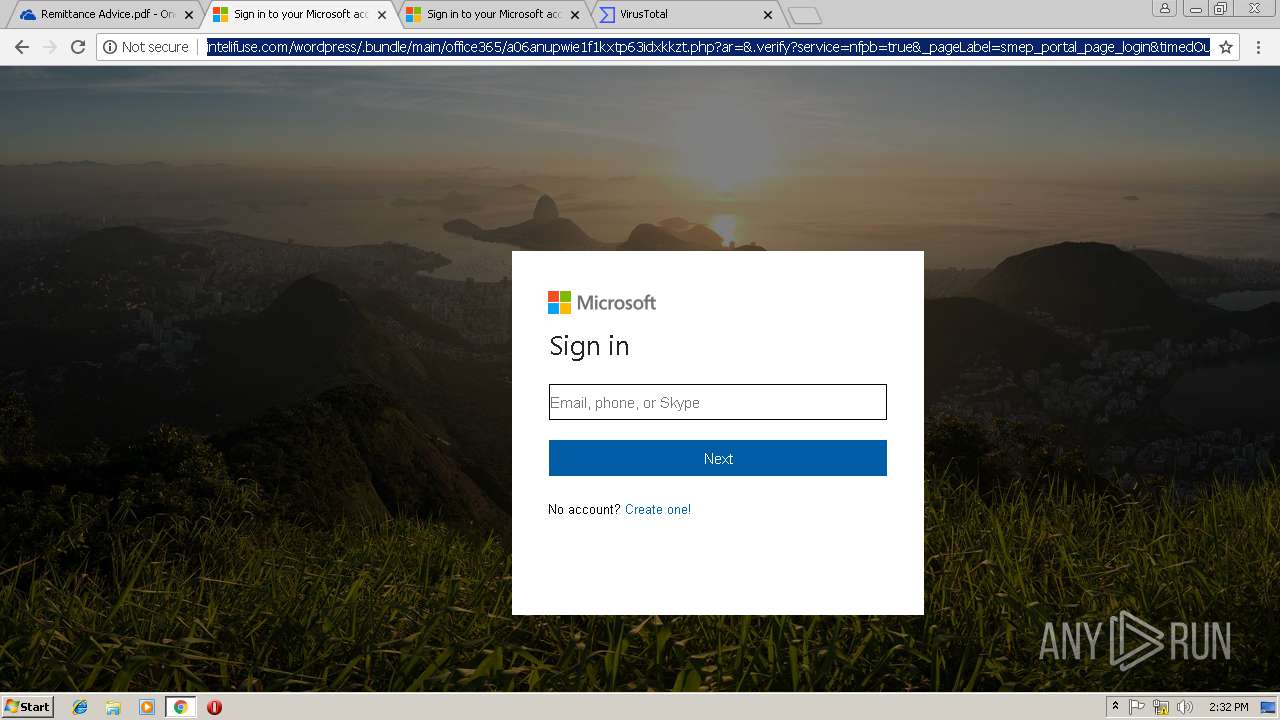
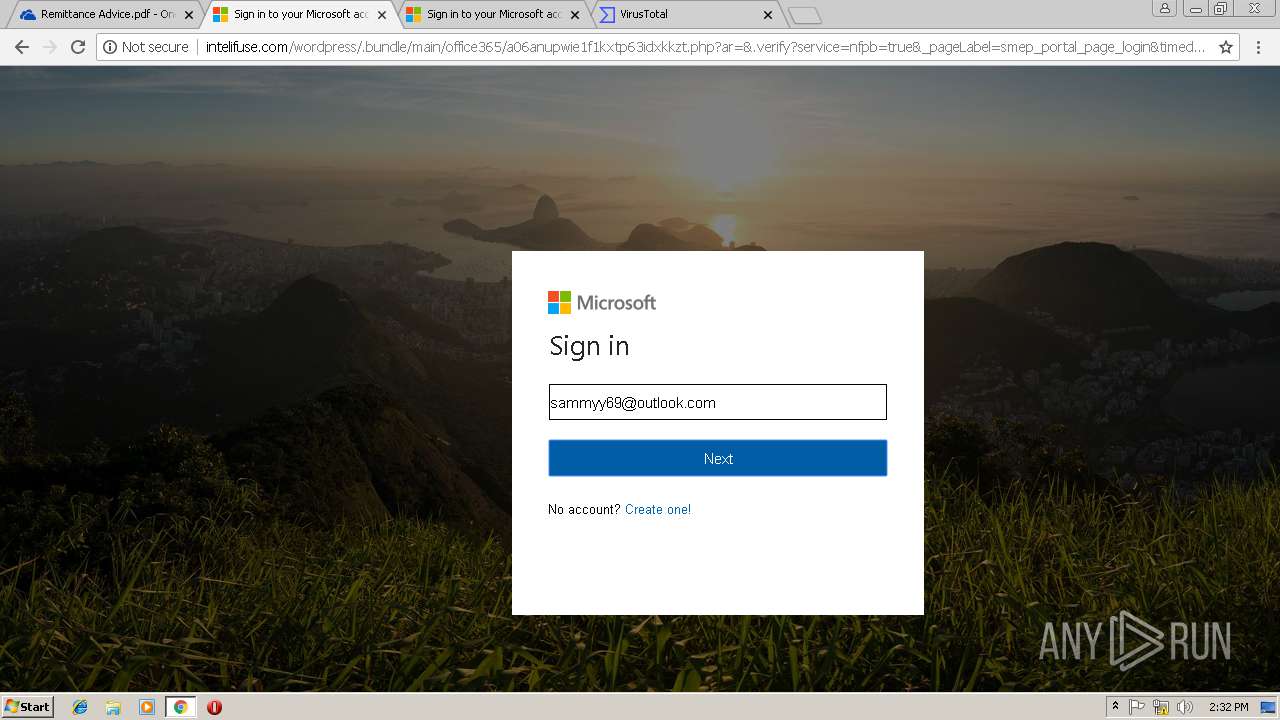
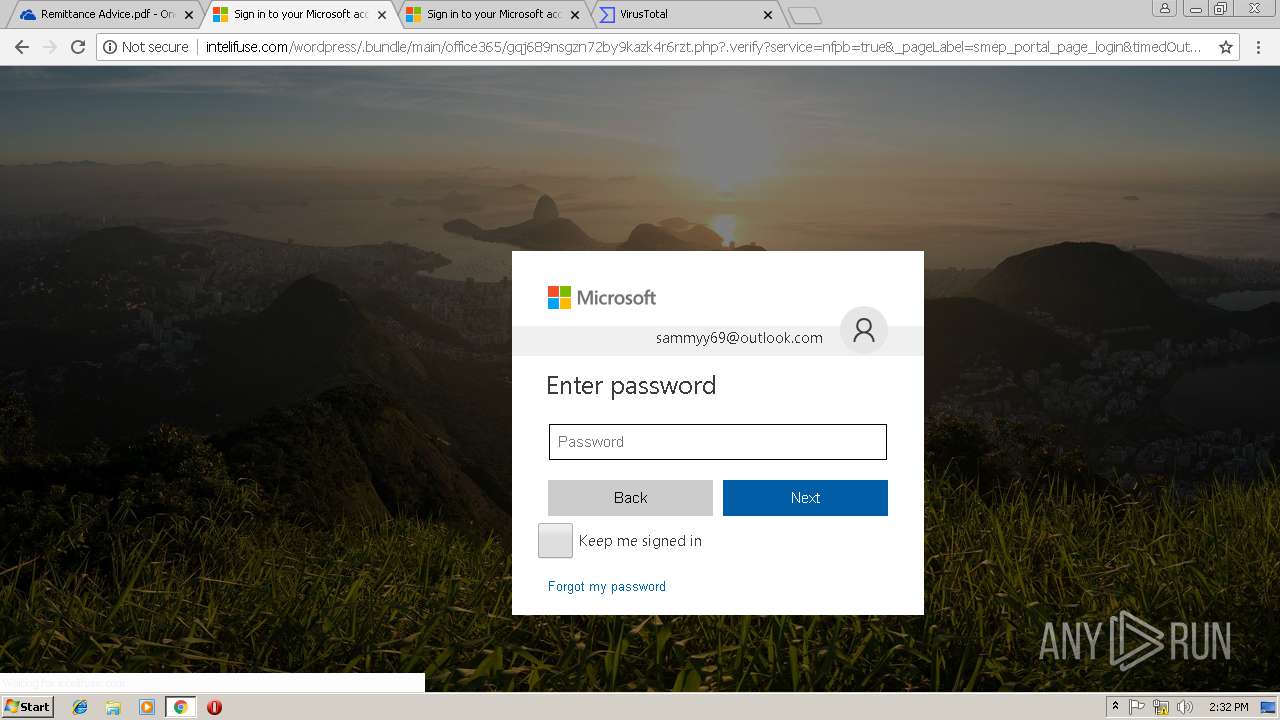
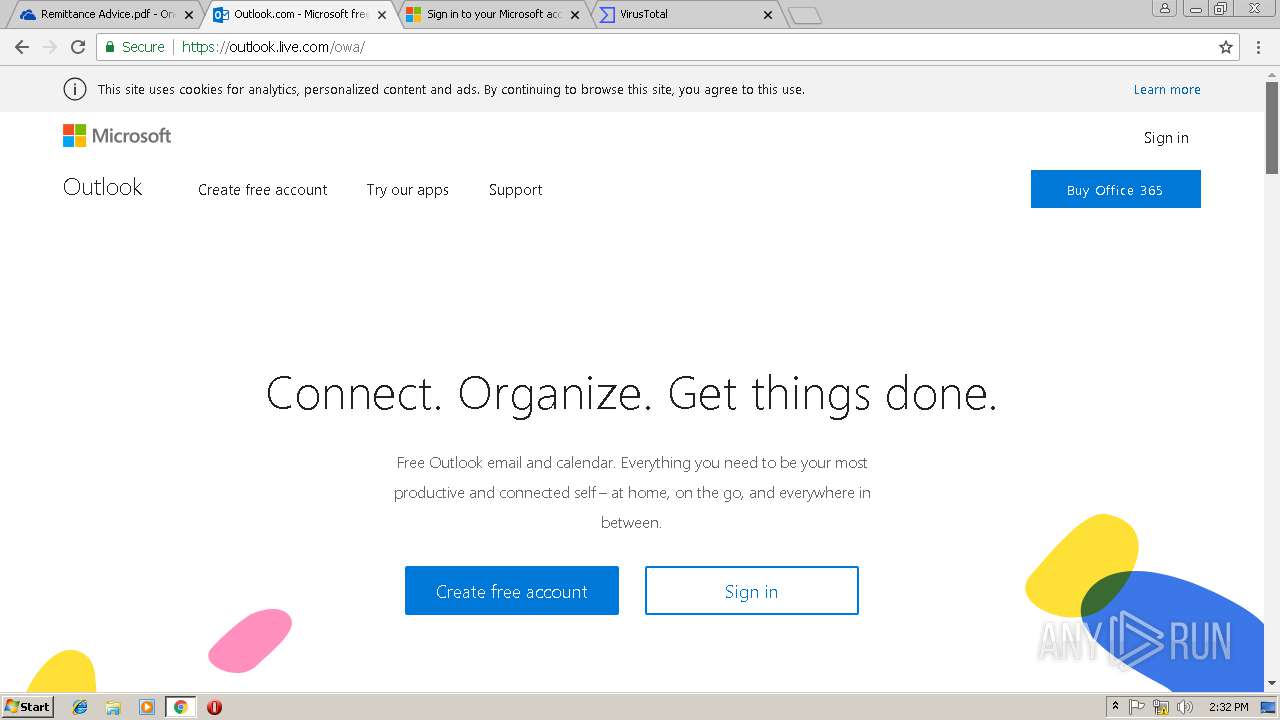
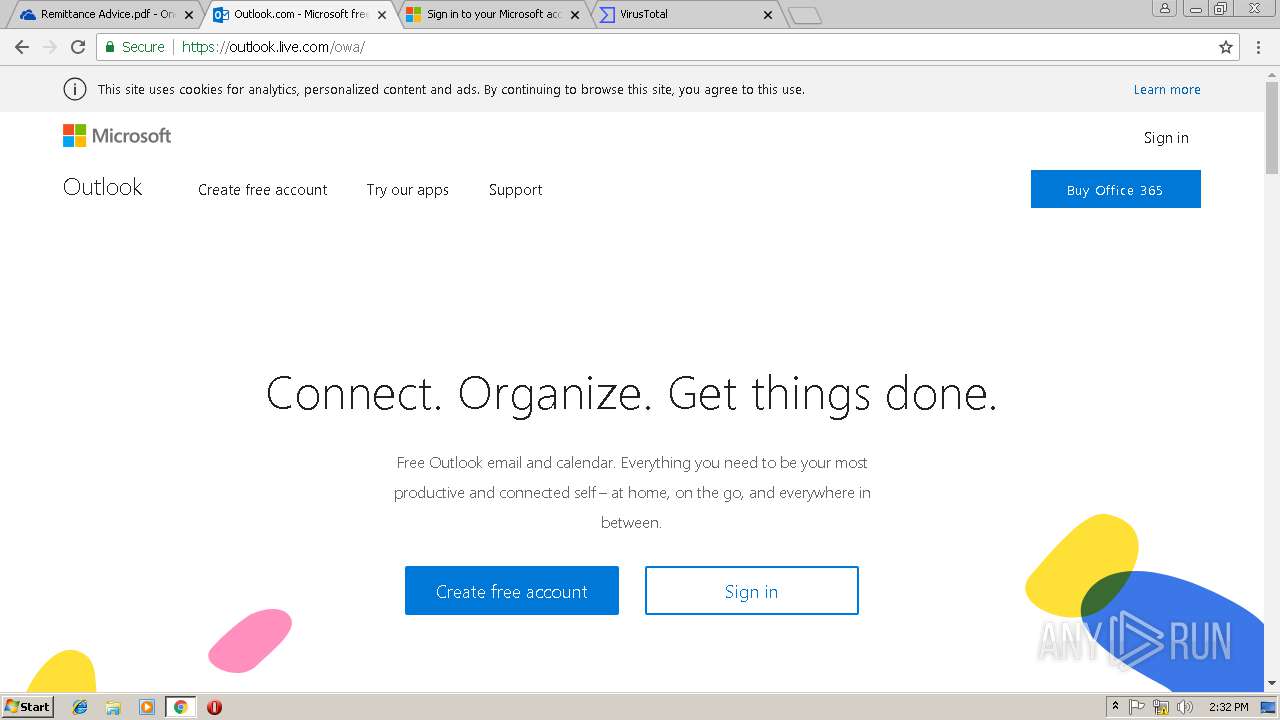
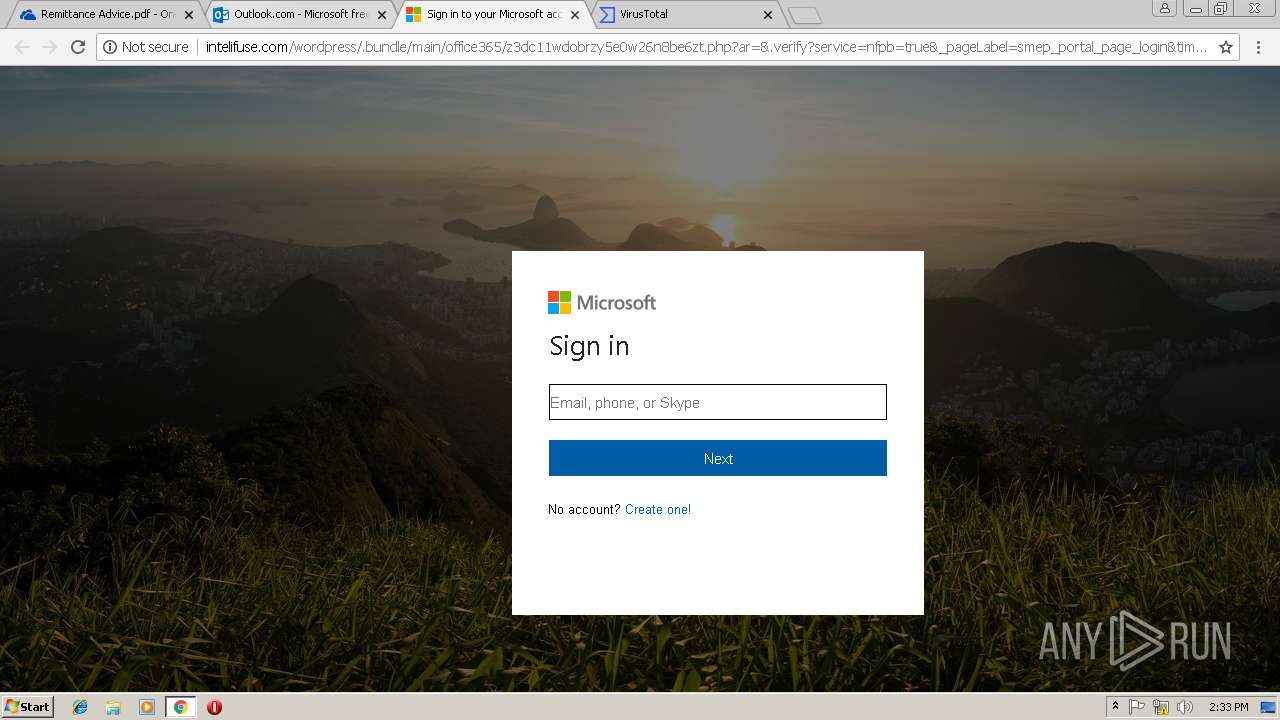
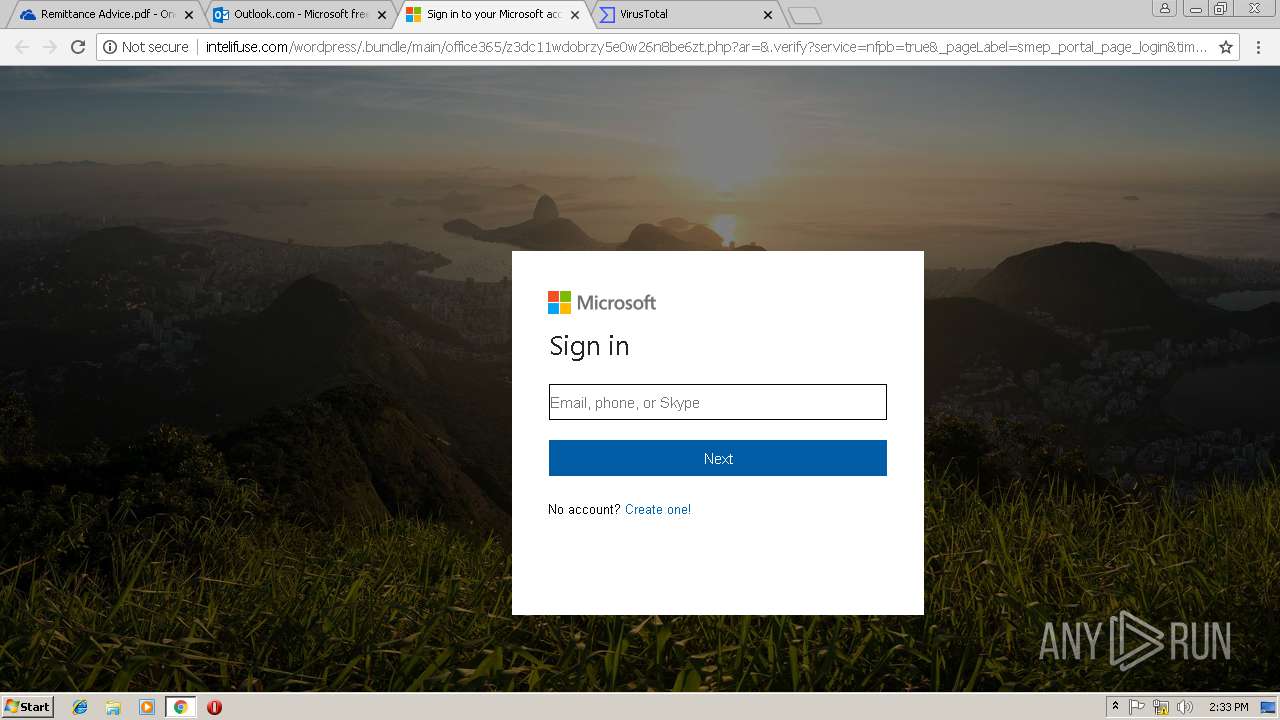
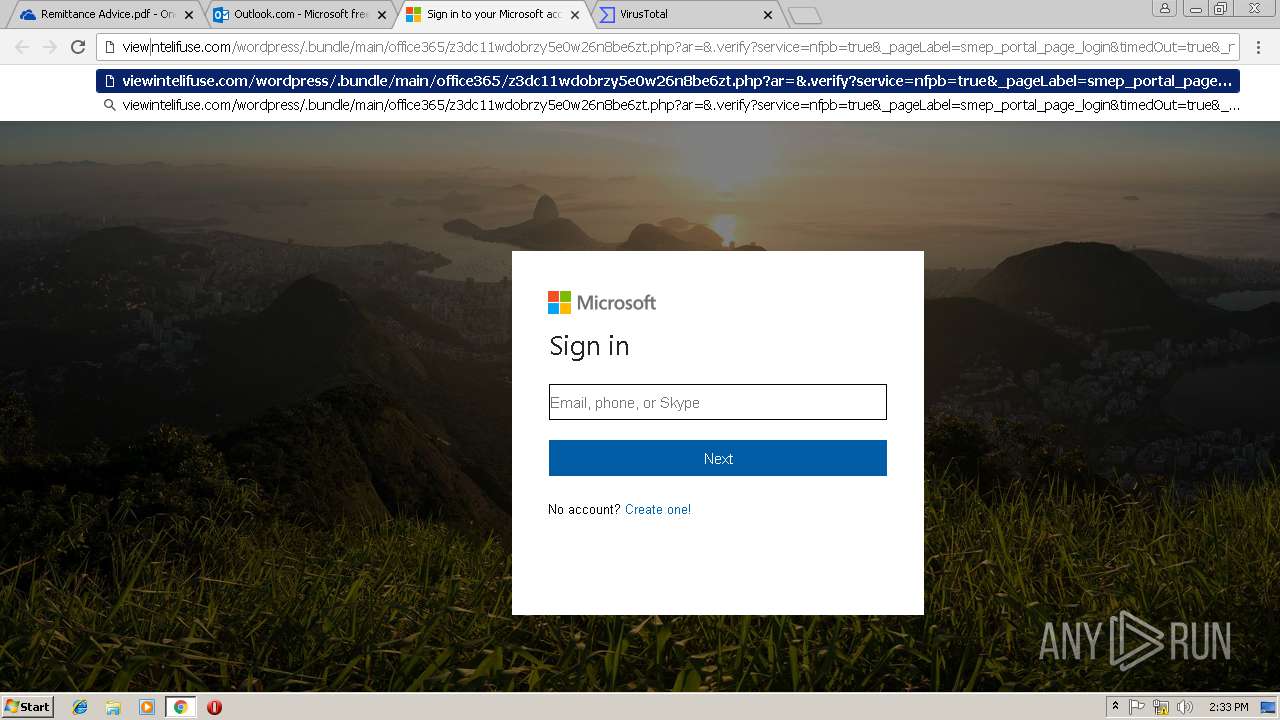
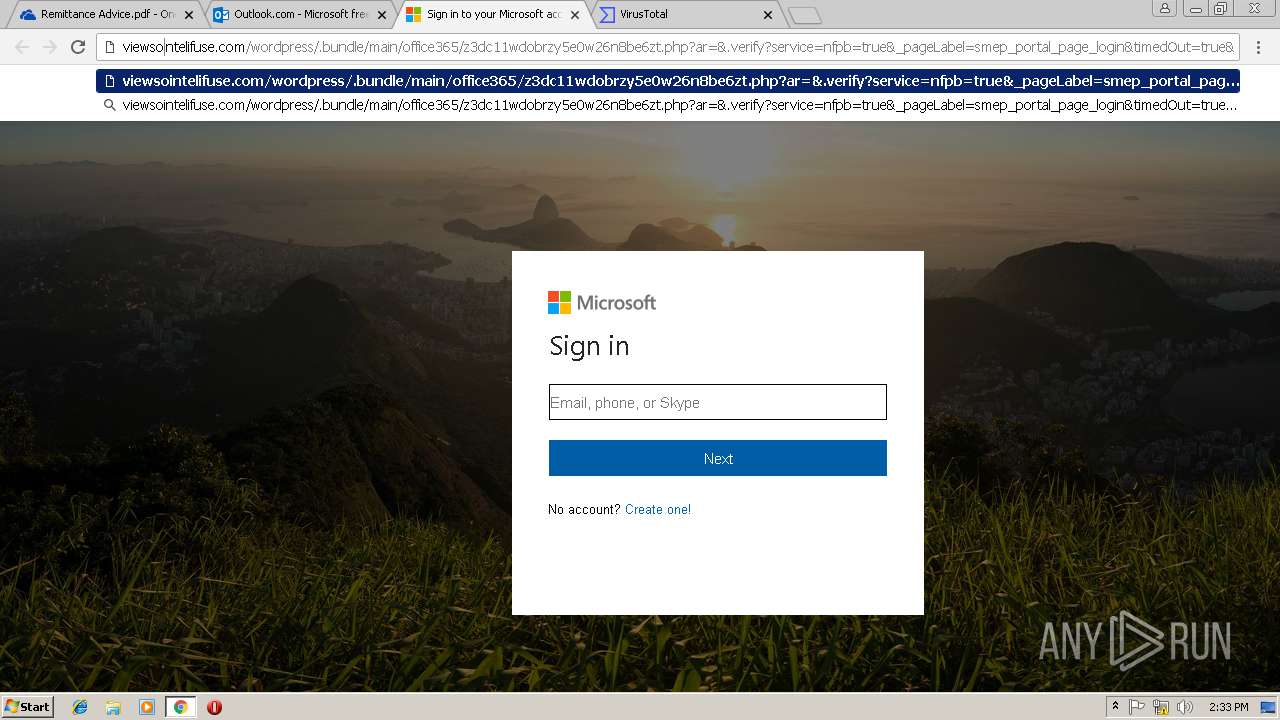
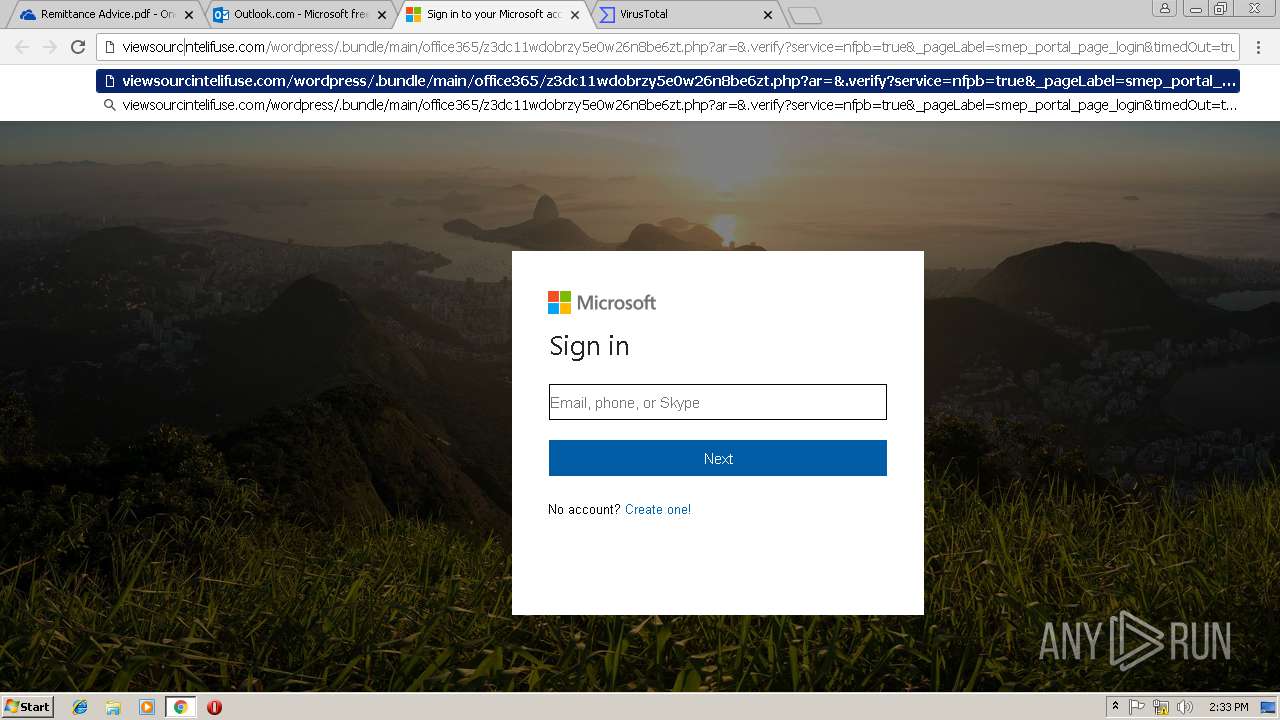
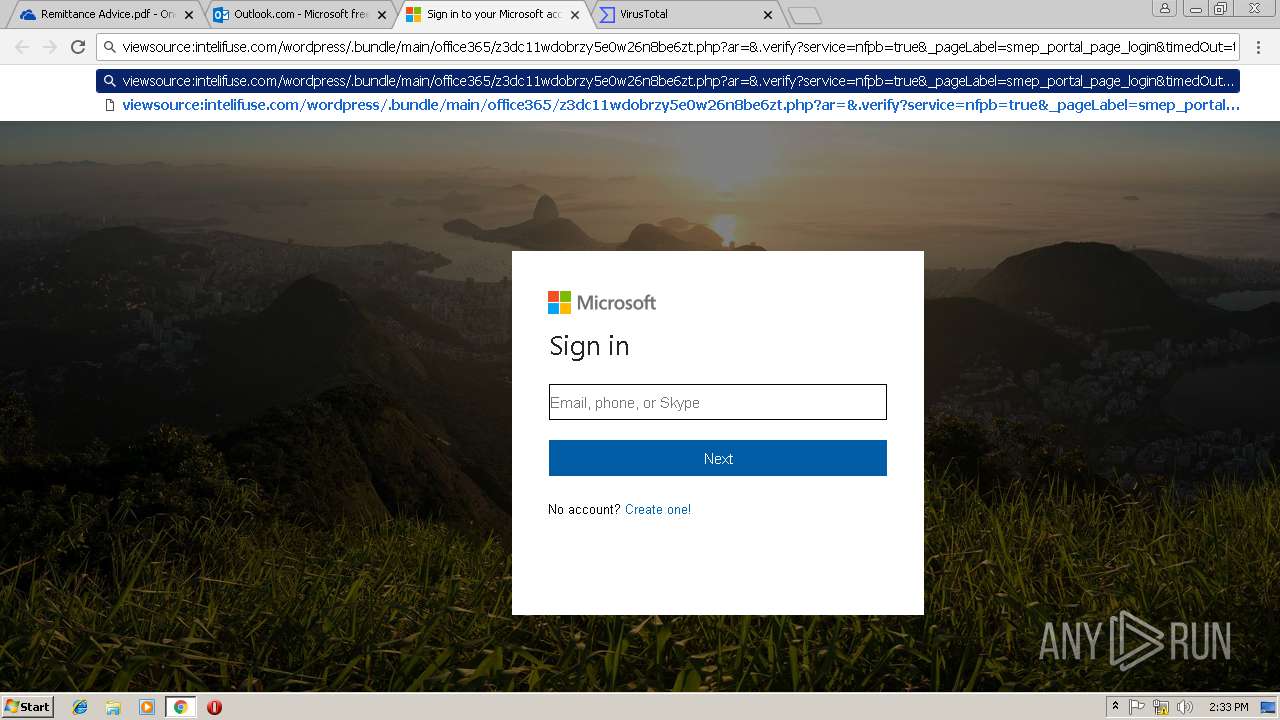
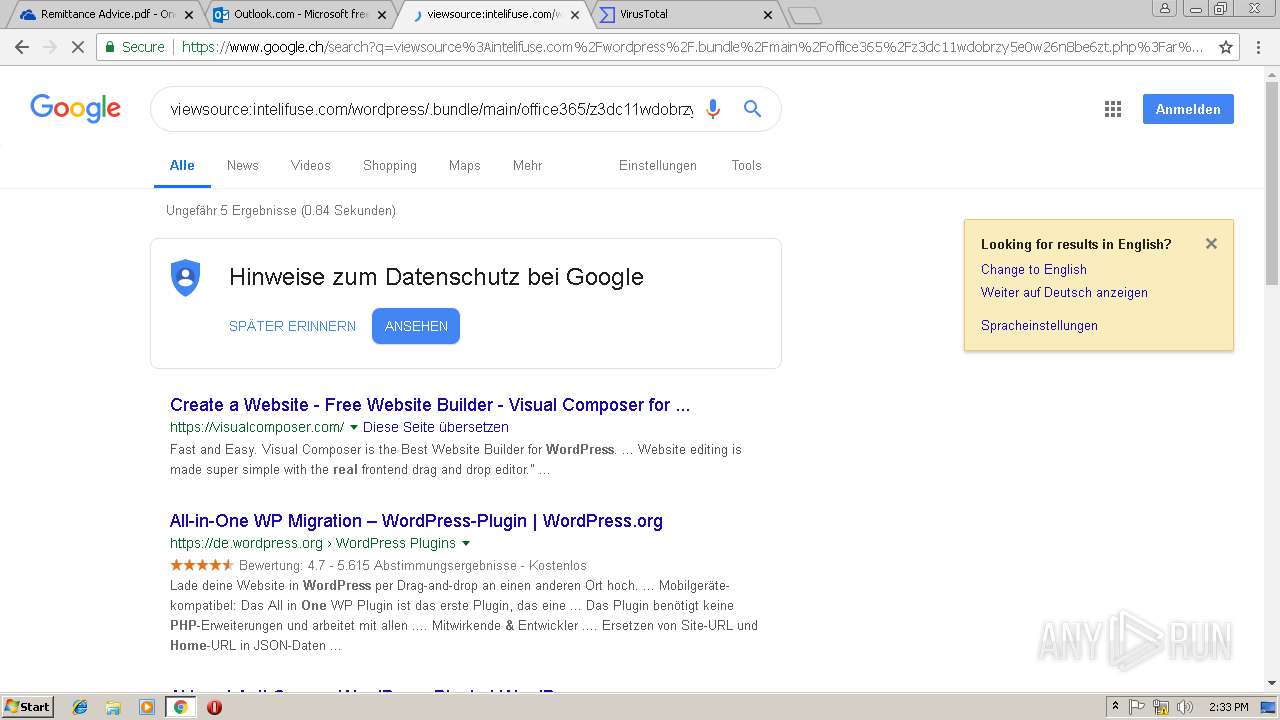
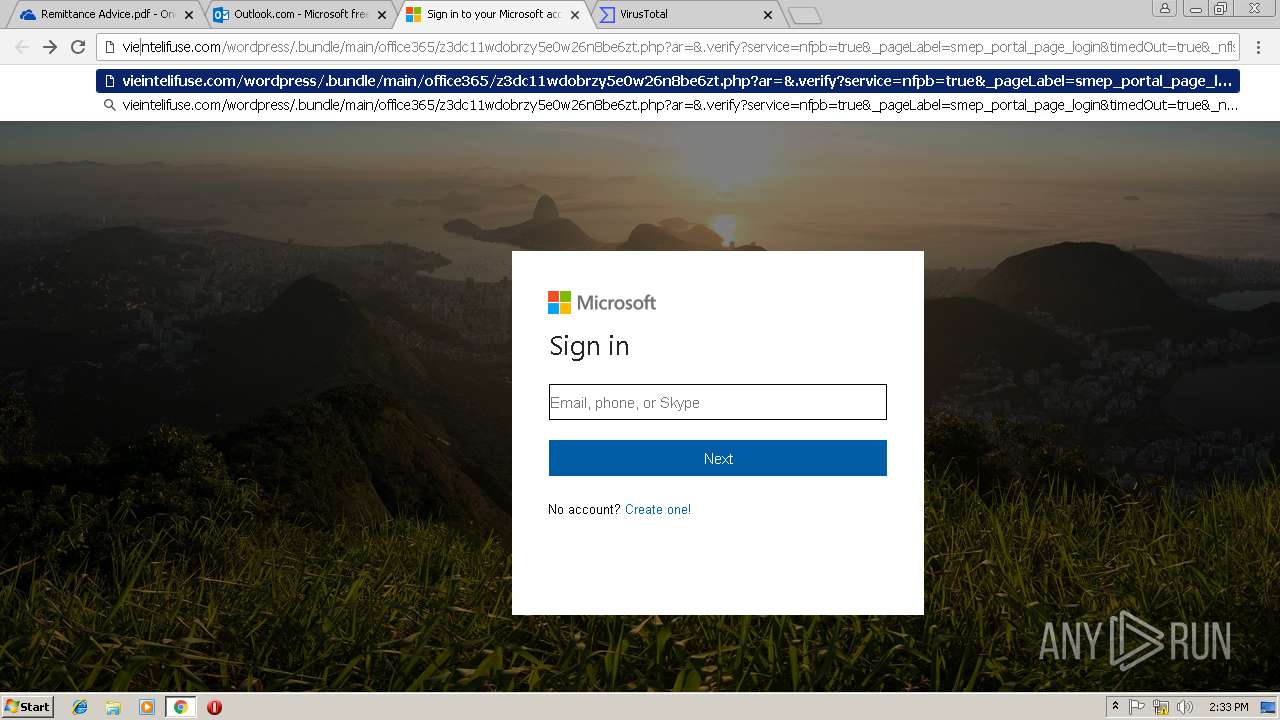
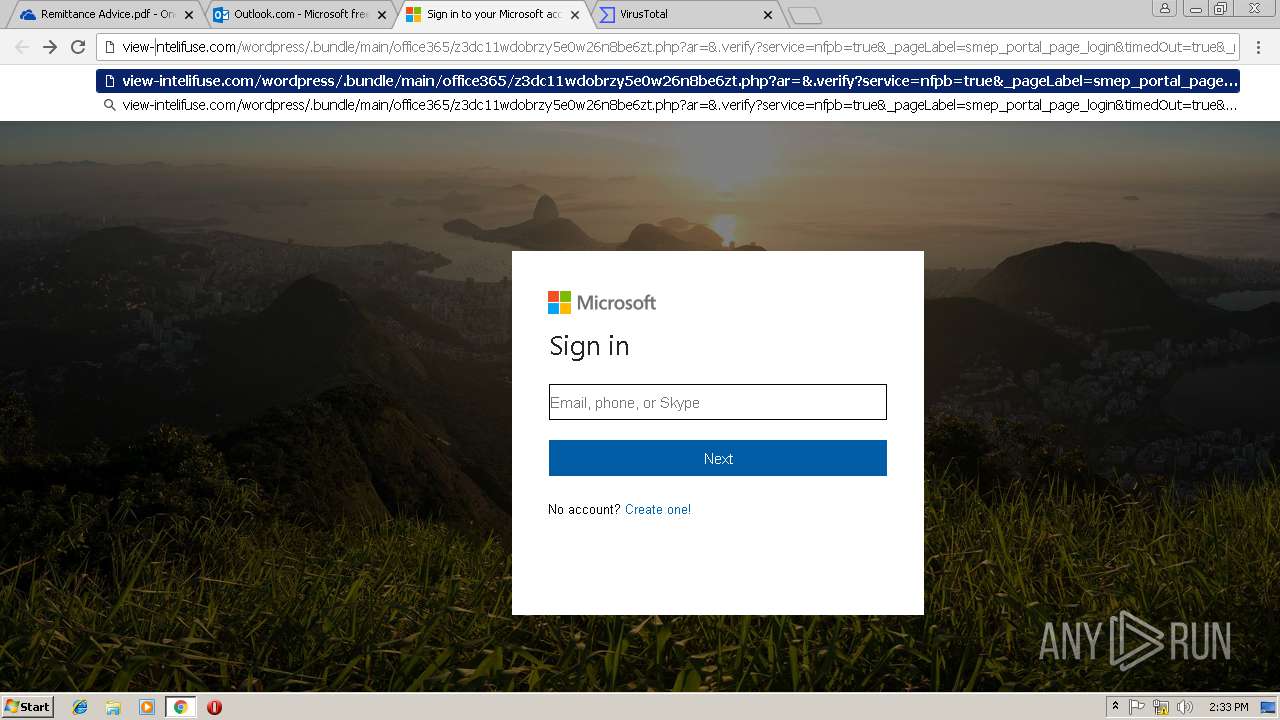
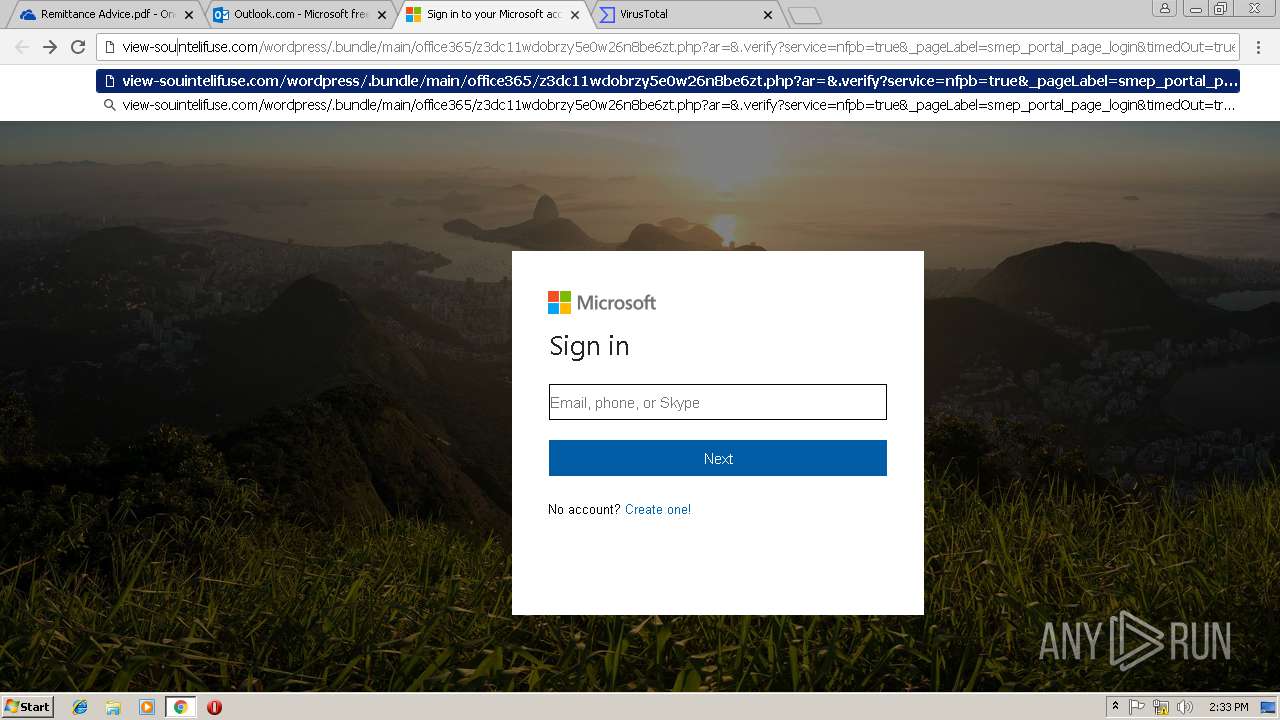
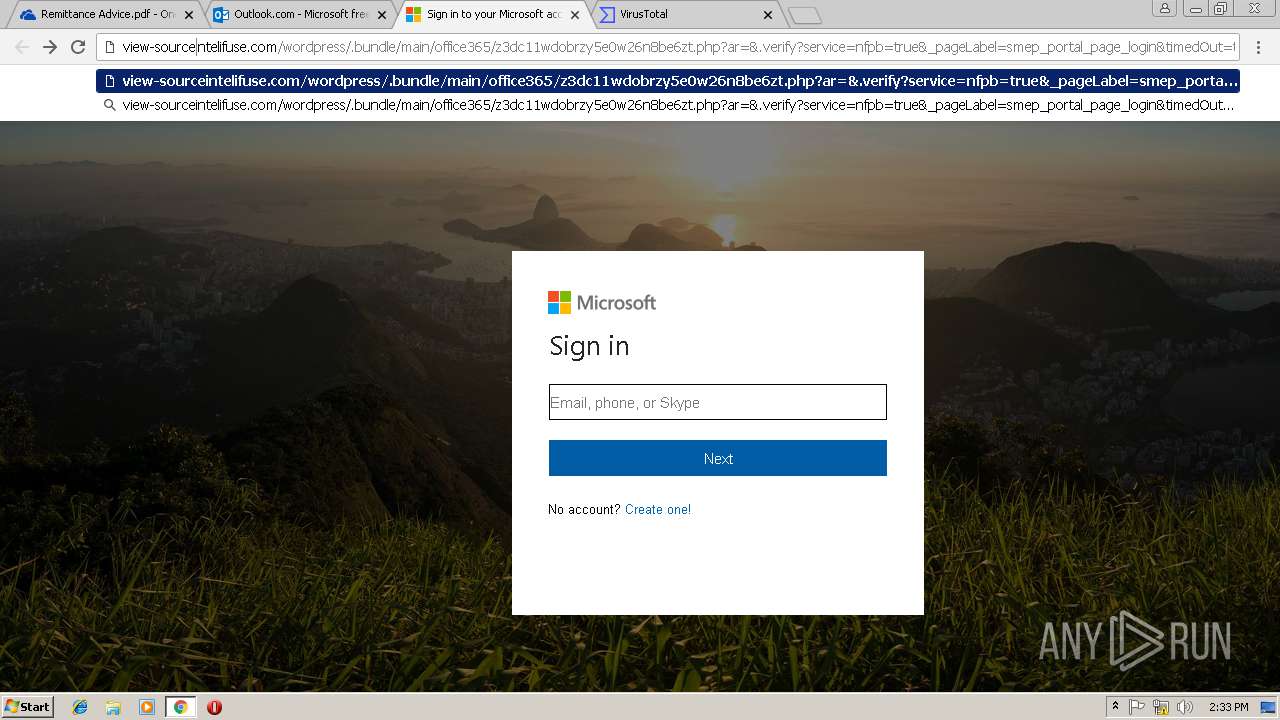
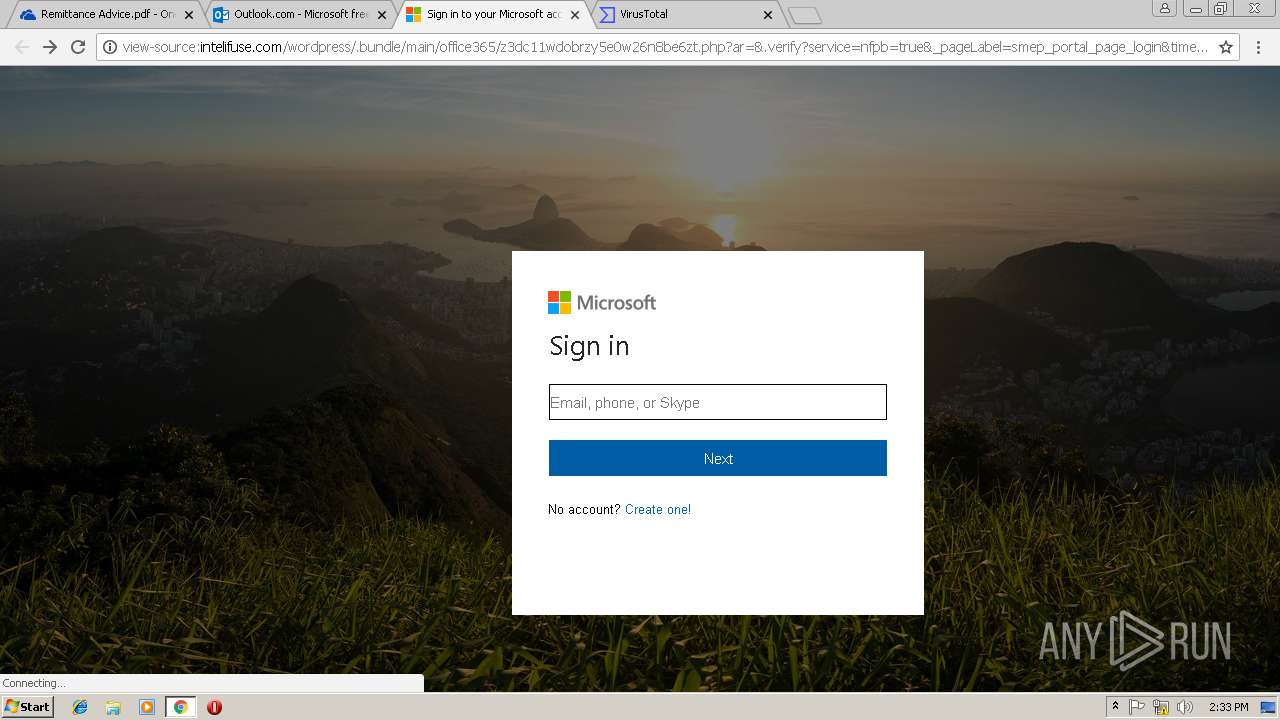
3008 | chrome.exe | GET | 200 | 208.113.217.253:80 | http://intelifuse.com/wordpress/.bundle/main/office365/css.css | US | text | 985 b | suspicious |
3008 | chrome.exe | GET | 200 | 208.113.217.253:80 | http://intelifuse.com/wordpress/.bundle/main/office365/a06anupwie1f1kxtp63idxkkzt.php?ar=&.verify?service=nfpb=true&_pageLabel=smep_portal_page_login&timedOut=true&_nfls=false=&loginID=&. | US | html | 484 b | suspicious |
3008 | chrome.exe | GET | 302 | 208.113.217.253:80 | http://intelifuse.com/wordpress/.bundle/main/office365/ | US | binary | 20 b | suspicious |
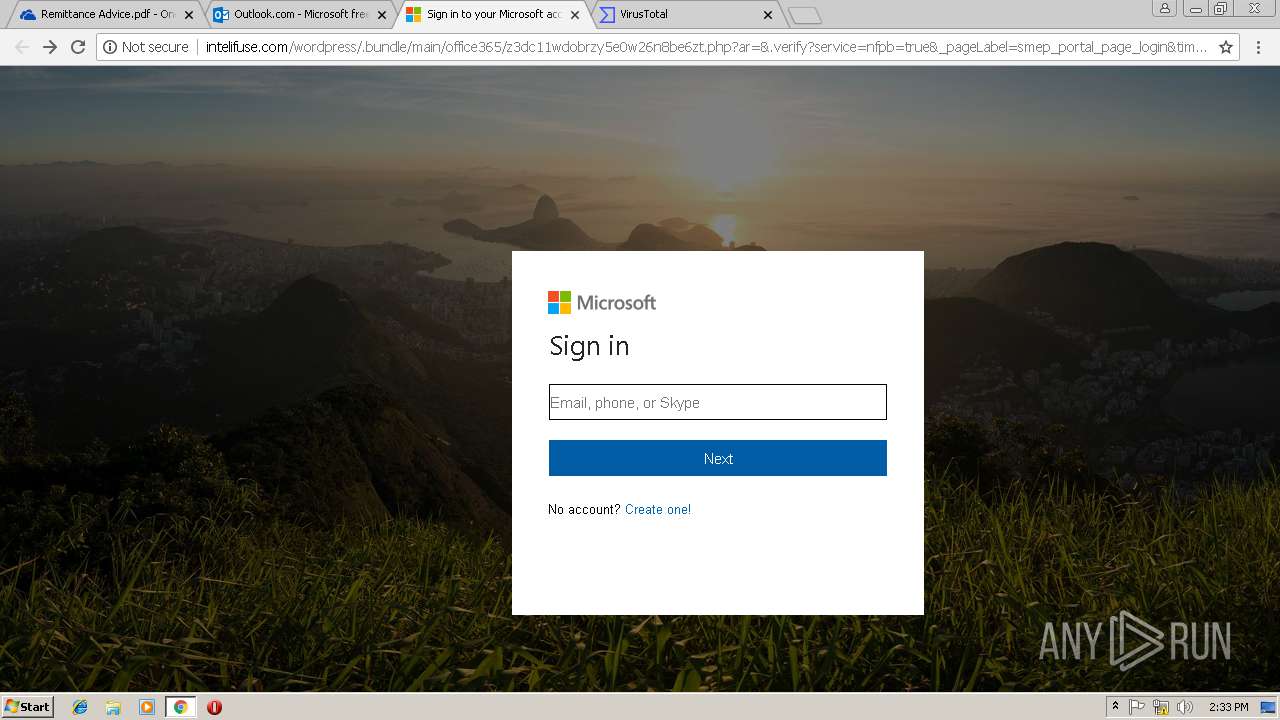
3008 | chrome.exe | GET | 200 | 208.113.217.253:80 | http://intelifuse.com/wordpress/.bundle/main/office365/z3dc11wdobrzy5e0w26n8be6zt.php?ar=&.verify?service=nfpb=true&_pageLabel=smep_portal_page_login&timedOut=true&_nfls=false=&loginID=&. | US | html | 484 b | suspicious |
3008 | chrome.exe | GET | 302 | 208.113.217.253:80 | http://intelifuse.com/wordpress/.bundle/main/office365/ | US | binary | 20 b | suspicious |
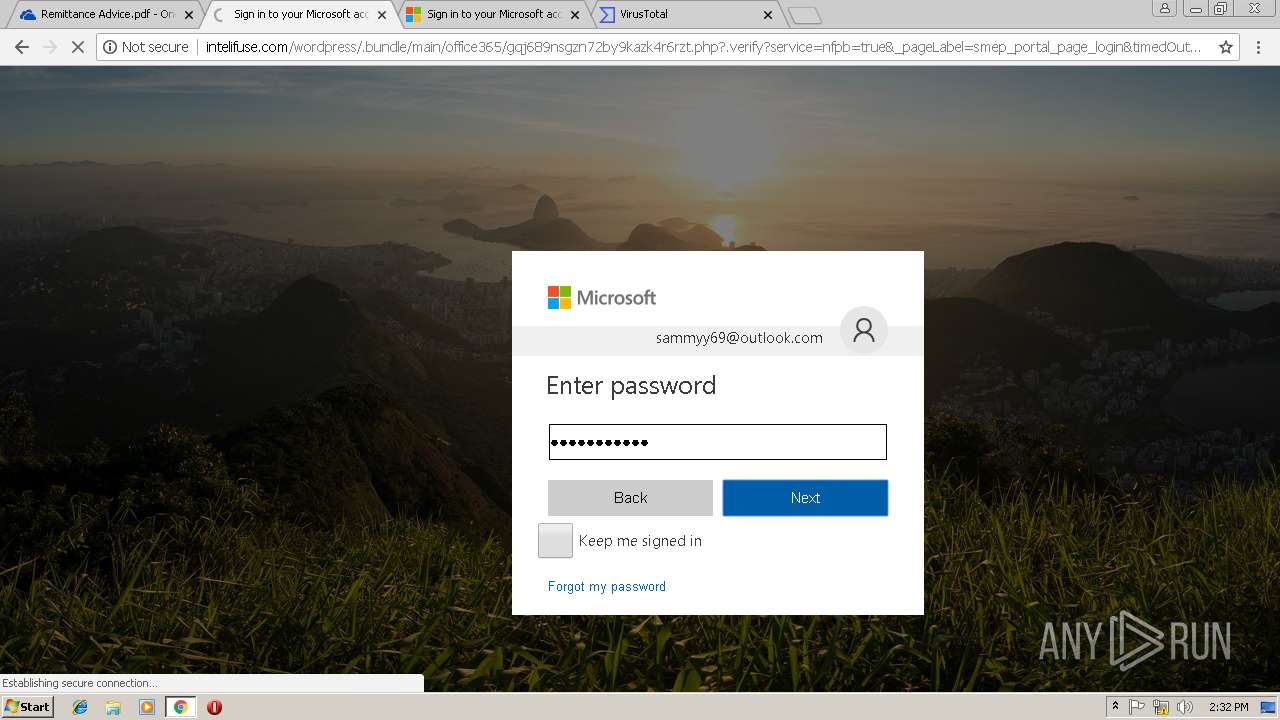
3008 | chrome.exe | GET | 200 | 208.113.217.253:80 | http://intelifuse.com/wordpress/.bundle/main/office365/gqj689nsgzn72by9kazk4r6rzt.php?.verify?service=nfpb=true&_pageLabel=smep_portal_page_login&timedOut=true&_nfls=false=&loginID=1251&log=sammyy69@outlook.com | US | html | 2.18 Kb | suspicious |
3008 | chrome.exe | GET | 200 | 208.113.217.253:80 | http://intelifuse.com/wordpress/.bundle/main/office365/picker_account_msa.svg | US | image | 379 b | suspicious |
3008 | chrome.exe | GET | 200 | 208.113.217.253:80 | http://intelifuse.com/wordpress/.bundle/main/office365/favicon.ico | US | image | 16.7 Kb | suspicious |
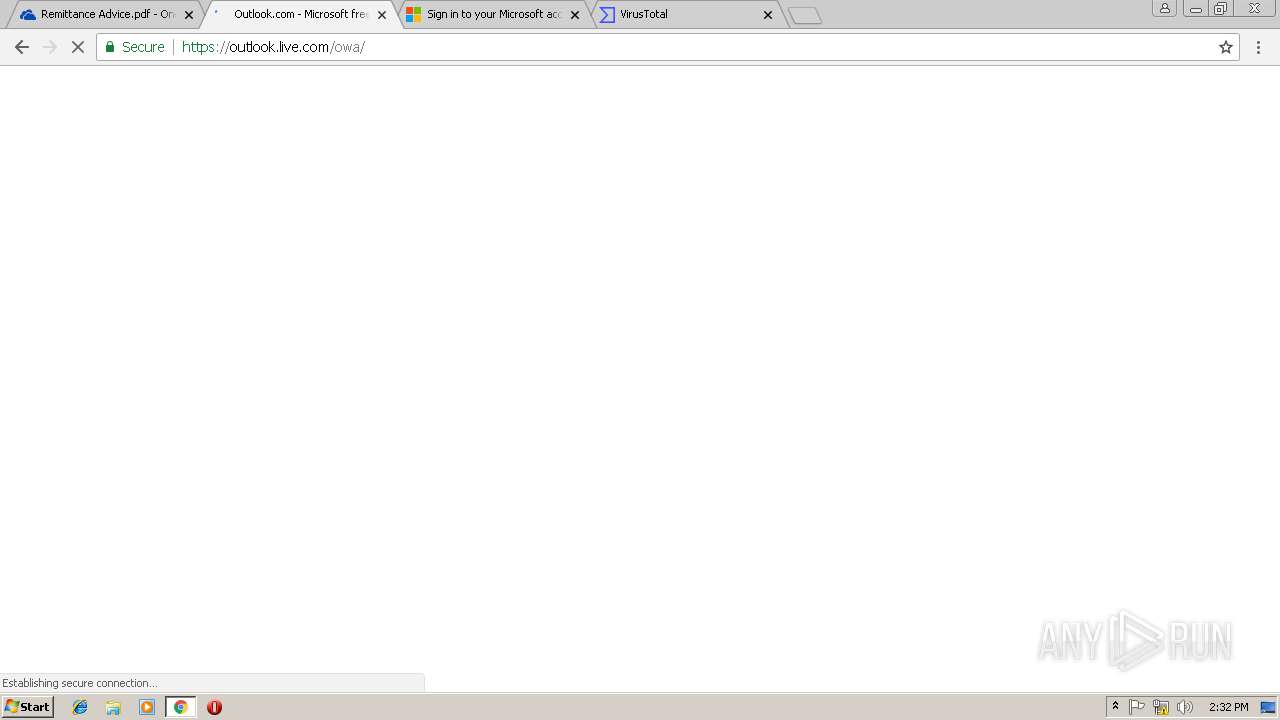
3008 | chrome.exe | POST | 302 | 208.113.217.253:80 | http://intelifuse.com/wordpress/.bundle/main/office365/pwd.php?ervice=mail&dataIGJvZHkgeyBtYXJnaW46logA7IG92ZXJmbG93OiBoaWRkZW47IH0gPC9zdHlsZT4NCiAgPGlm | US | binary | 20 b | suspicious |
3008 | chrome.exe | POST | 302 | 208.113.217.253:80 | http://intelifuse.com/wordpress/.bundle/main/office365/login.php | US | binary | 20 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3008 | chrome.exe | 172.217.23.163:443 | www.gstatic.com | Google Inc. | US | whitelisted |
3008 | chrome.exe | 172.217.18.109:443 | accounts.google.com | Google Inc. | US | suspicious |
3008 | chrome.exe | 13.107.136.9:443 | zinfi-my.sharepoint.com | Microsoft Corporation | US | whitelisted |
3008 | chrome.exe | 2.16.186.40:443 | spoprod-a.akamaihd.net | Akamai International B.V. | — | whitelisted |
3008 | chrome.exe | 104.109.65.225:443 | static2.sharepointonline.com | Akamai International B.V. | NL | whitelisted |
3008 | chrome.exe | 52.114.88.19:443 | browser.pipe.aria.microsoft.com | Microsoft Corporation | GB | unknown |
3008 | chrome.exe | 13.107.136.13:443 | northcentralus1-mediap.svc.ms | Microsoft Corporation | US | suspicious |
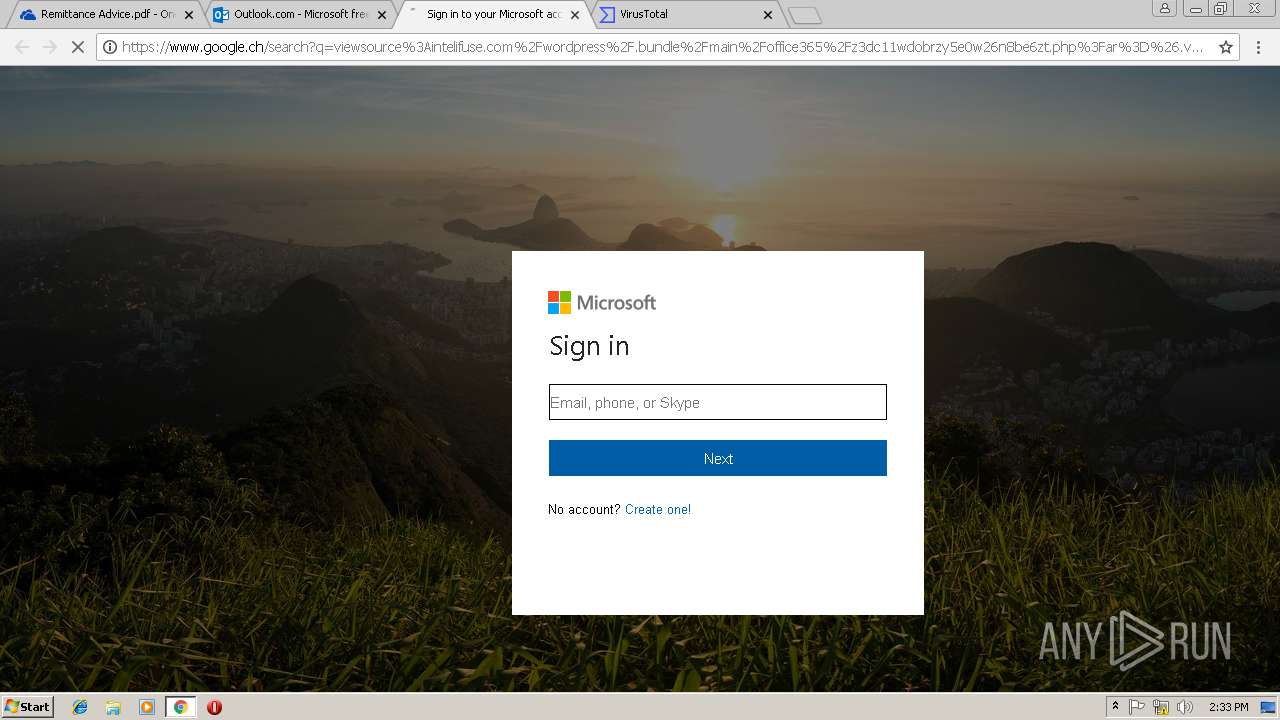
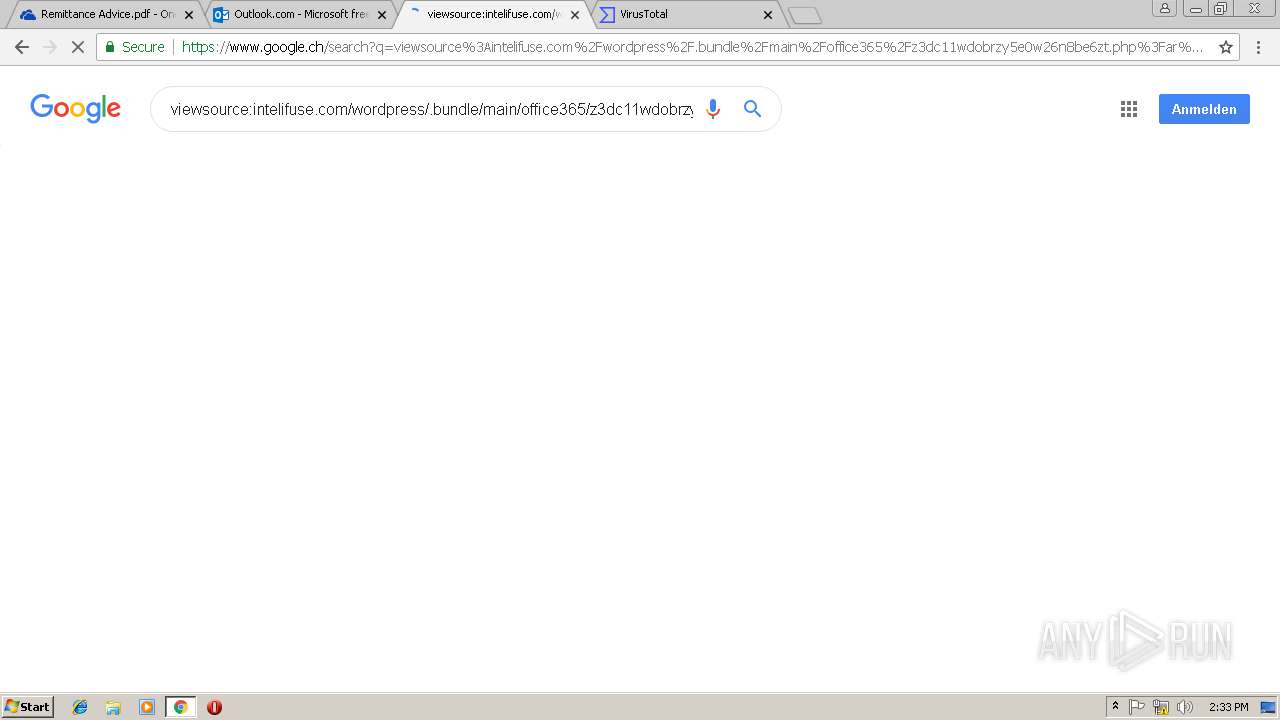
3008 | chrome.exe | 172.217.21.228:443 | www.google.com | Google Inc. | US | whitelisted |
3008 | chrome.exe | 216.58.205.227:443 | id.google.ch | Google Inc. | US | whitelisted |
3008 | chrome.exe | 172.217.22.34:443 | adservice.google.ch | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
zinfi-my.sharepoint.com |
| suspicious |
www.gstatic.com |
| whitelisted |
accounts.google.com |
| shared |
spoprod-a.akamaihd.net |
| whitelisted |
static2.sharepointonline.com |
| whitelisted |
browser.pipe.aria.microsoft.com |
| whitelisted |
northcentralus1-mediap.svc.ms |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
intelifuse.com |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
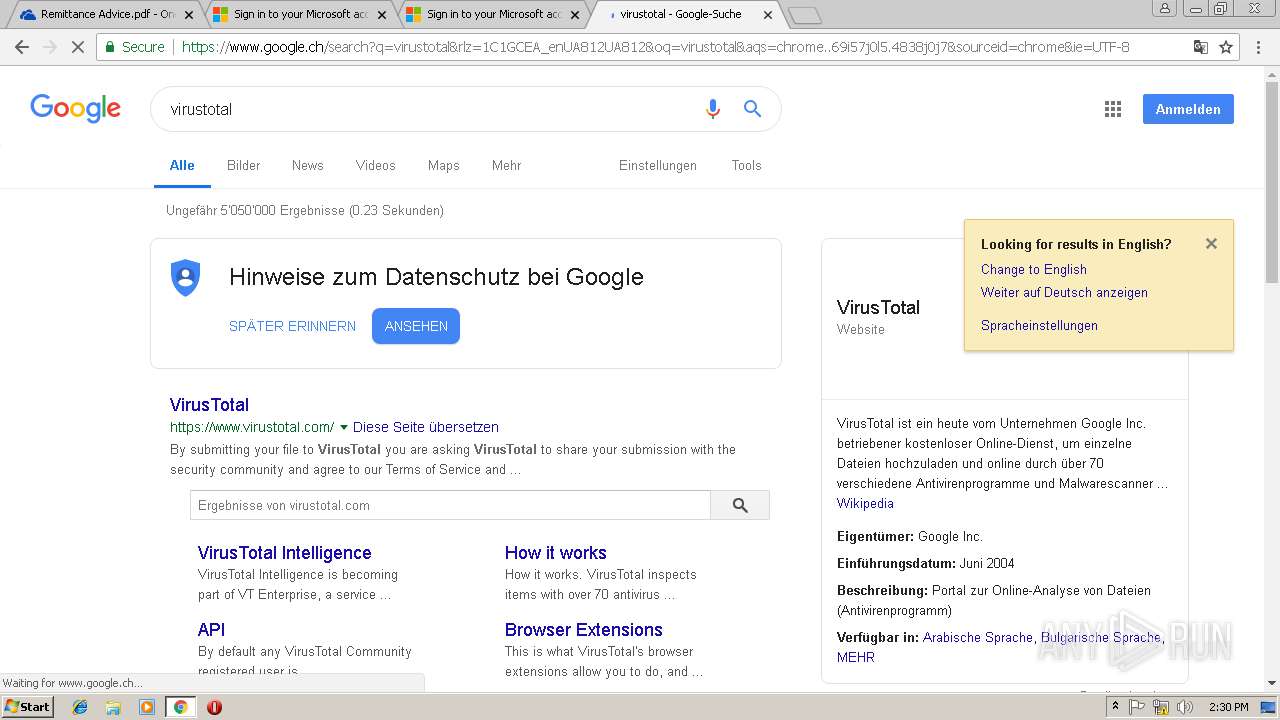
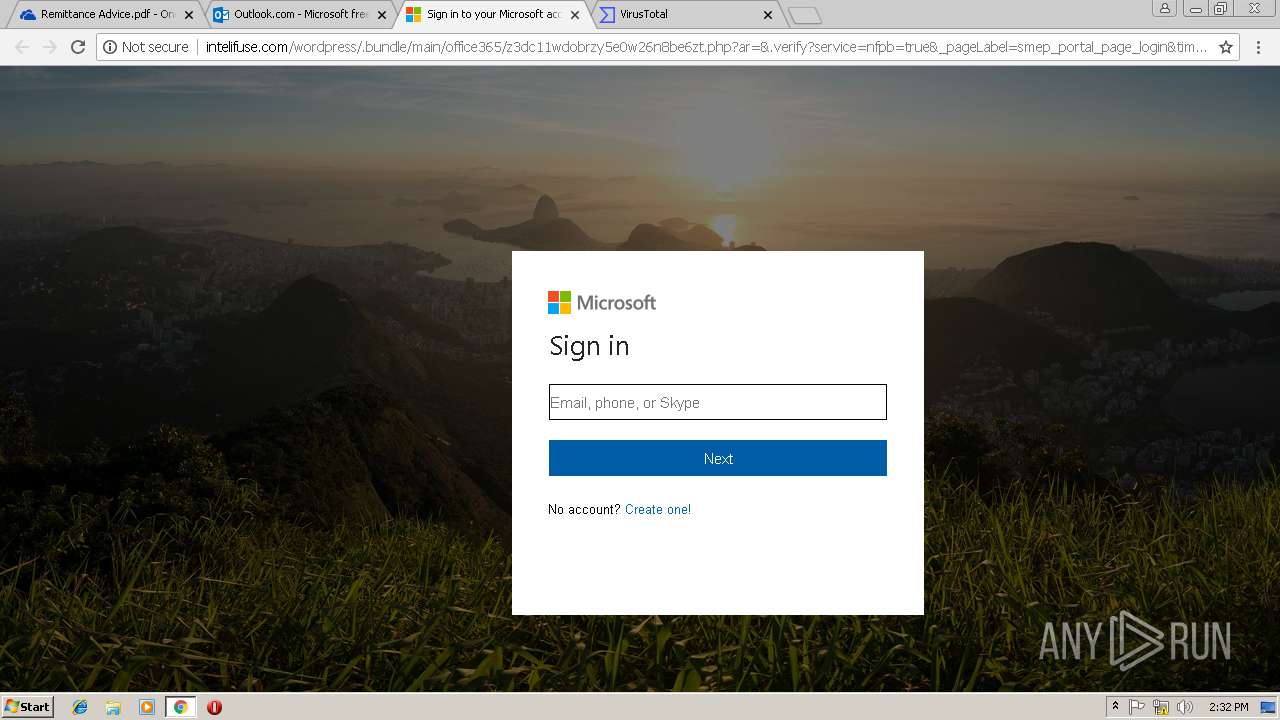
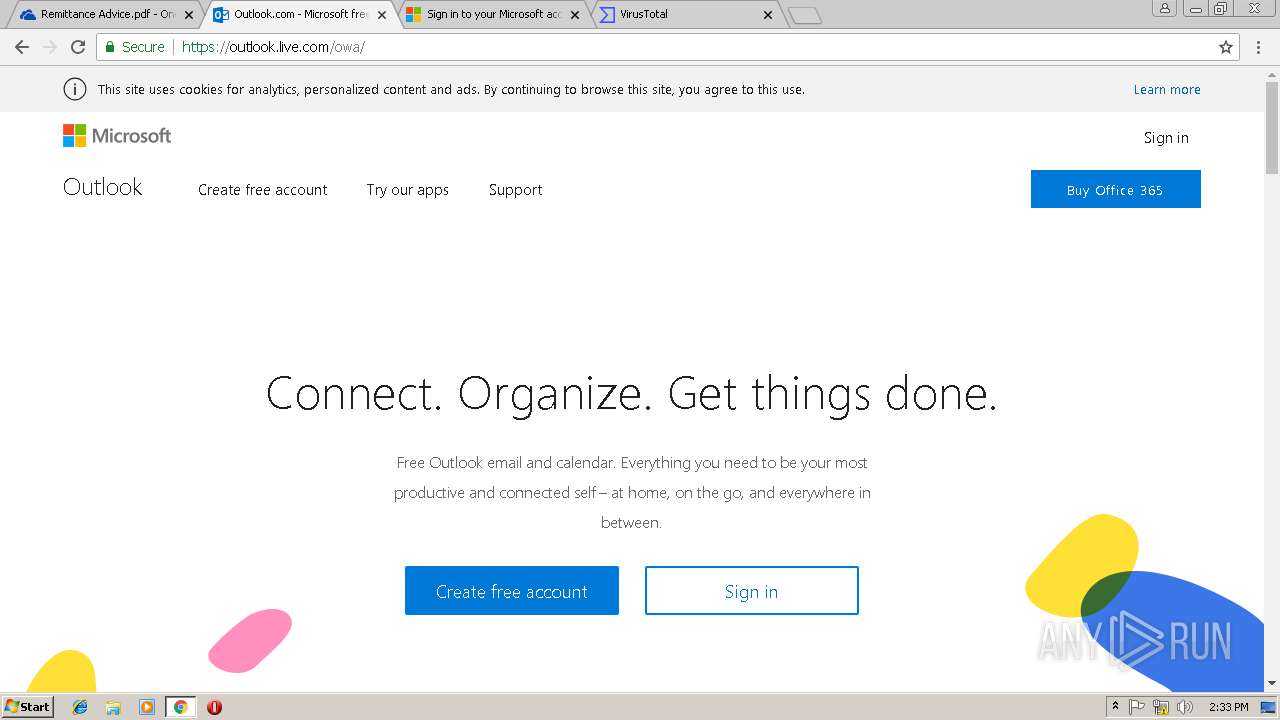
3008 | chrome.exe | Potentially Bad Traffic | ET CURRENT_EVENTS Microsoft Account Phishing Landing 2018-08-07 |
3008 | chrome.exe | Potentially Bad Traffic | ET CURRENT_EVENTS Microsoft Account Phishing Landing 2018-08-07 |
3008 | chrome.exe | Generic Protocol Command Decode | SURICATA STREAM excessive retransmissions |
3008 | chrome.exe | Potentially Bad Traffic | ET CURRENT_EVENTS Microsoft Account Phishing Landing 2018-08-07 |
3008 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY Http Client Body contains pass= in cleartext |
3008 | chrome.exe | Generic Protocol Command Decode | SURICATA STREAM excessive retransmissions |