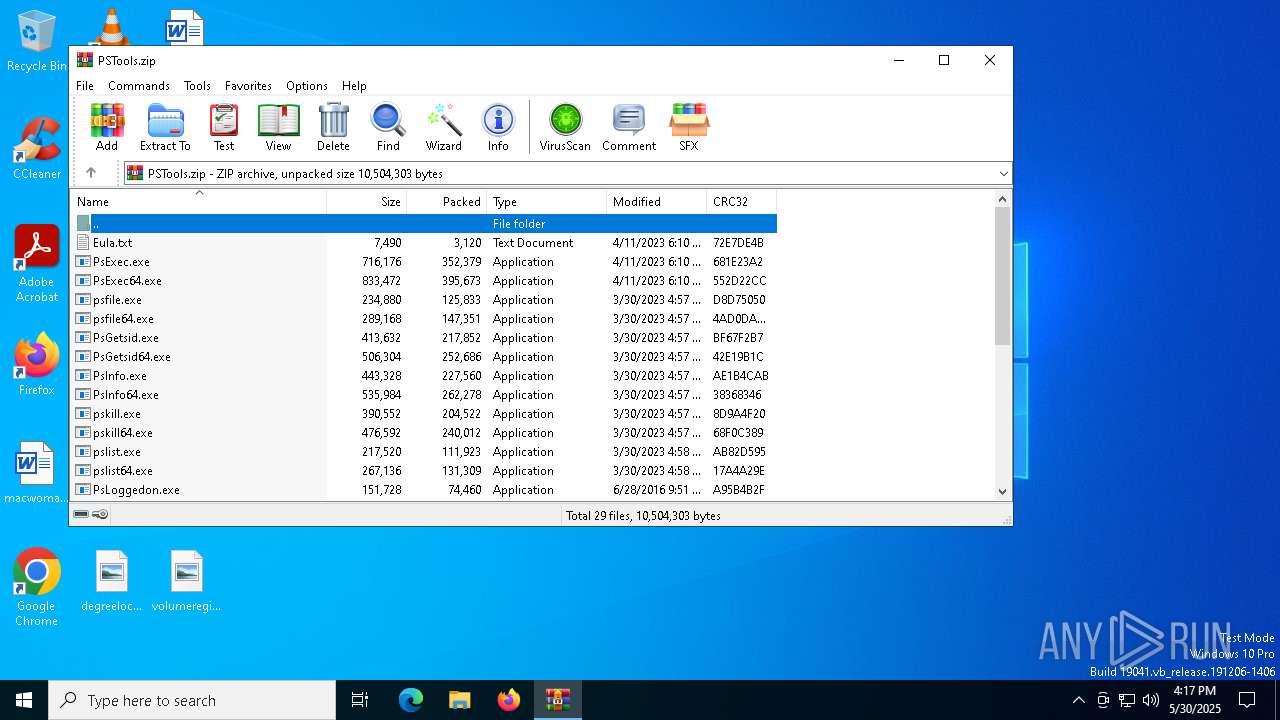
| File name: | PSTools.zip |
| Full analysis: | https://app.any.run/tasks/6b31f43f-fe07-4b73-bfef-82d7c6aaa96e |
| Verdict: | Malicious activity |
| Analysis date: | May 30, 2025, 16:17:30 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | 41EBDADC06B18164DC571F9DB251C01B |
| SHA1: | DDFB009F8B92226AA45C467F8D0EEBB29A8E2FF5 |
| SHA256: | A9CA77DFE03CE15004157727BB43BA66F00CEB215362C9B3D199F000EDAA8D61 |
| SSDEEP: | 98304:w8SK6YhPu87Ci2jqrAAQiu9fffhwqZ4qxIL48xtg6TK/nUjqbprp7sg:wU/h3h0qrAL9fCqZO1Kycbprp7P |
MALICIOUS
Generic archive extractor
- WinRAR.exe (PID: 8056)
SUSPICIOUS
The process creates files with name similar to system file names
- WinRAR.exe (PID: 8056)
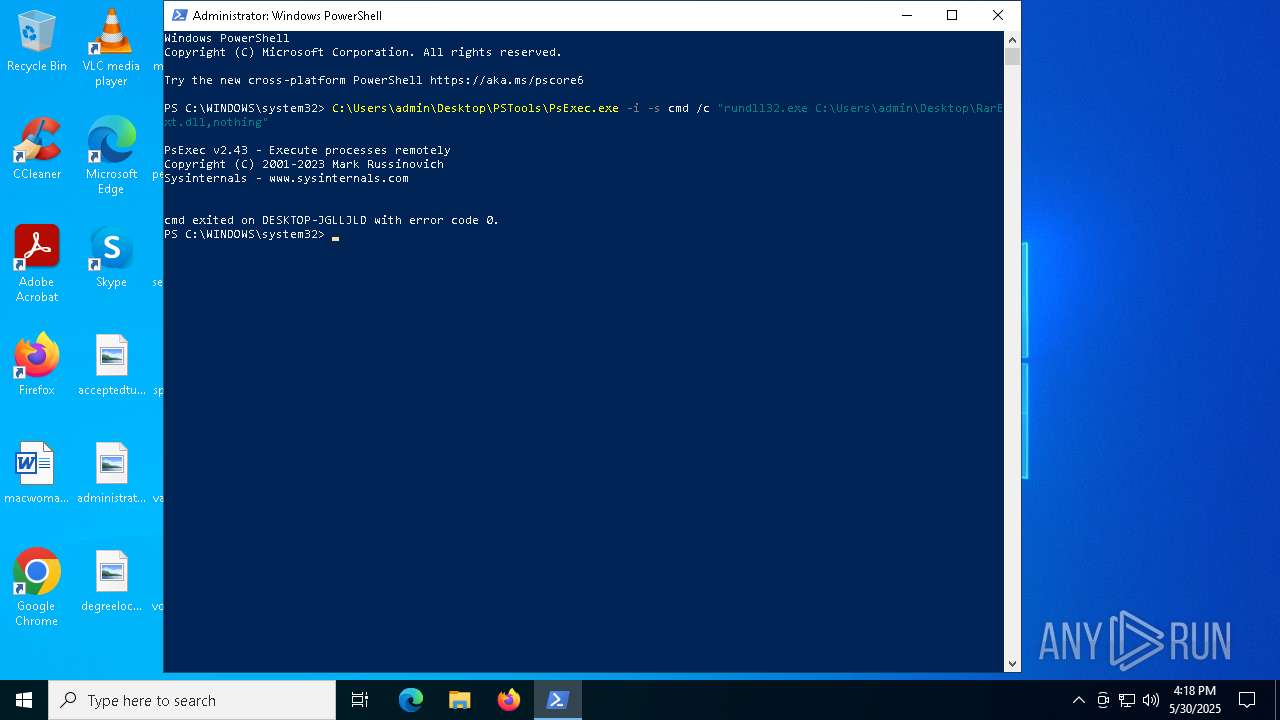
PSEXEC has been detected
- PsExec.exe (PID: 7200)
Executes as Windows Service
- PSEXESVC.exe (PID: 7584)
Executable content was dropped or overwritten
- PsExec.exe (PID: 7200)
Starts CMD.EXE for commands execution
- PSEXESVC.exe (PID: 7584)
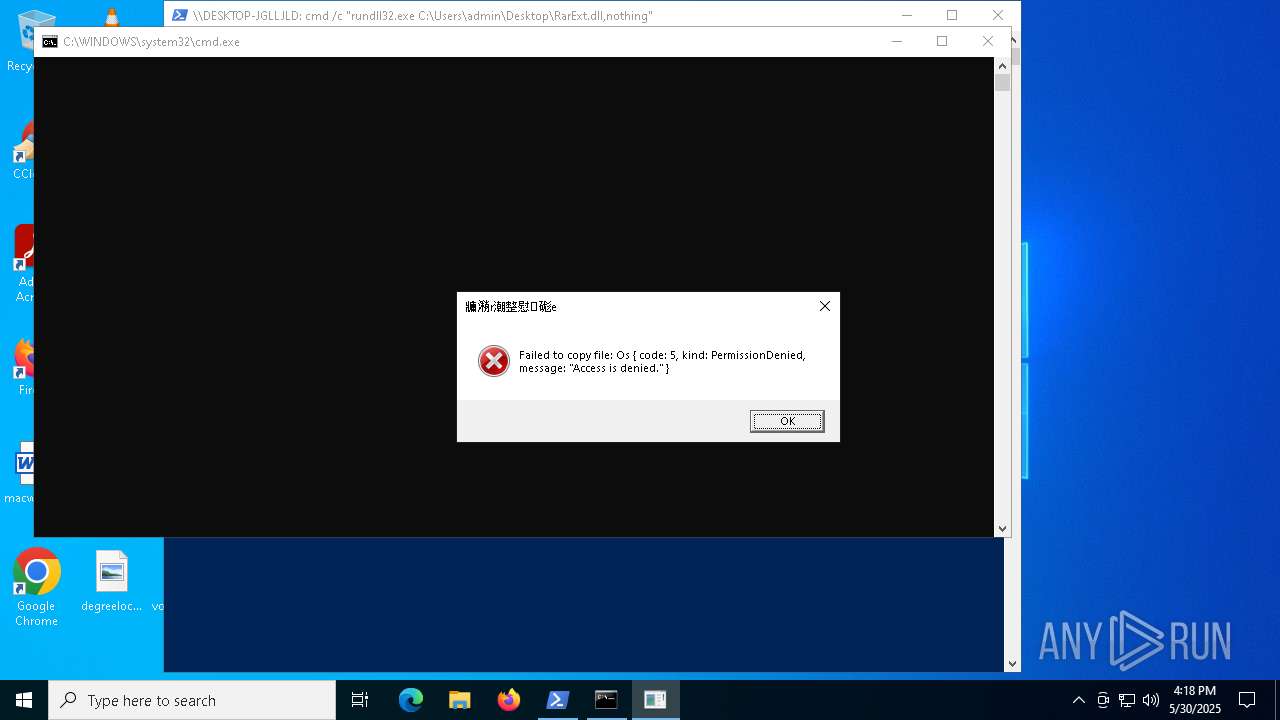
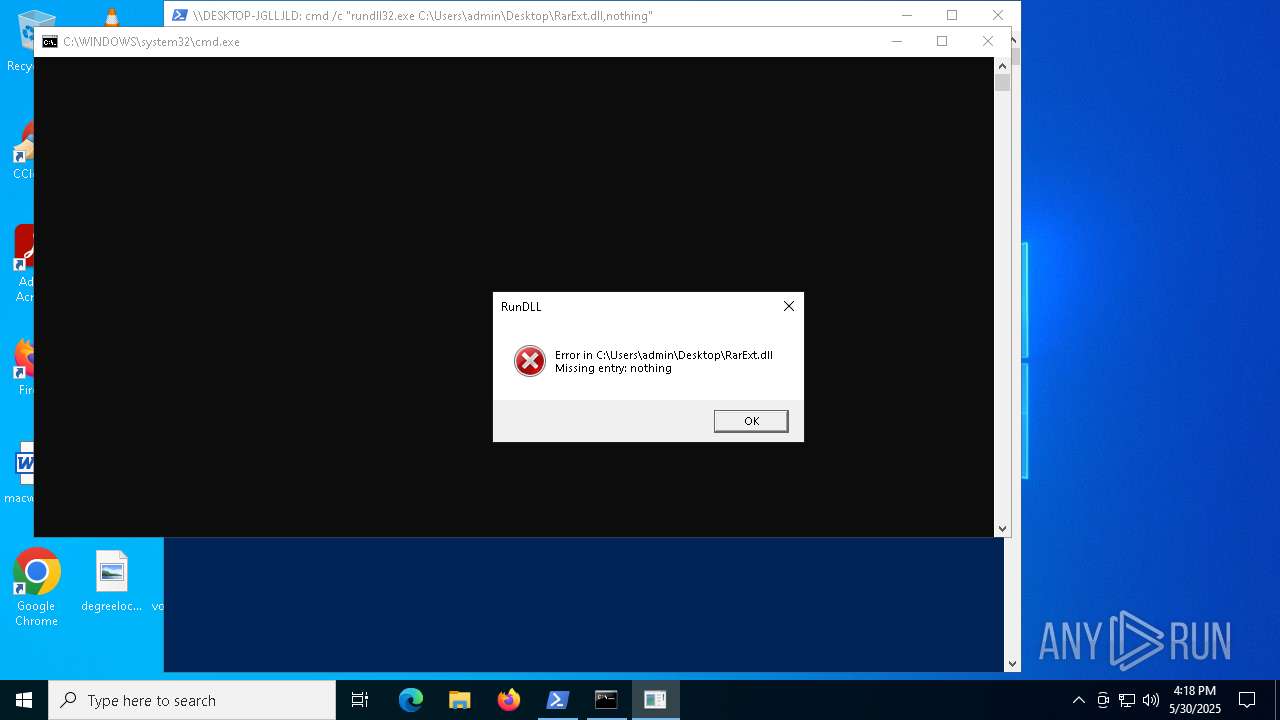
Uses RUNDLL32.EXE to load library
- cmd.exe (PID: 5260)
The process executes via Task Scheduler
- PLUGScheduler.exe (PID: 3576)
INFO
Executable content was dropped or overwritten
- WinRAR.exe (PID: 8056)
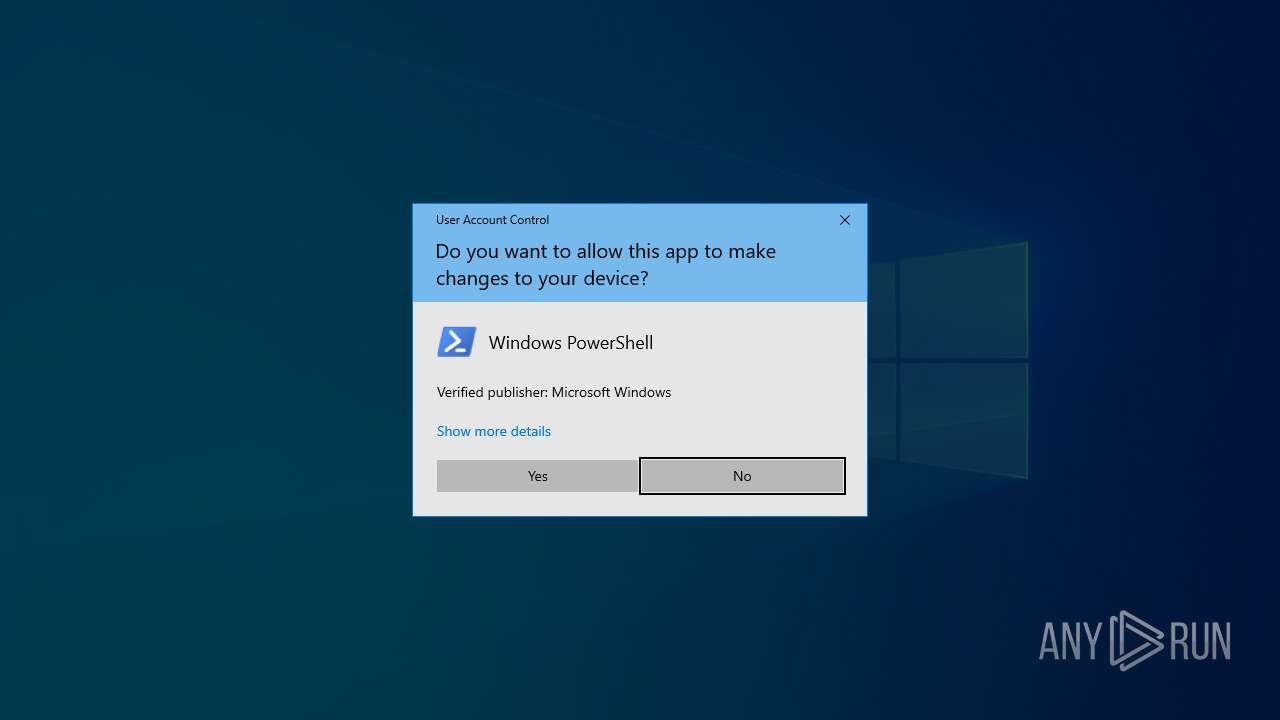
Manual execution by a user
- powershell.exe (PID: 3156)
The sample compiled with english language support
- WinRAR.exe (PID: 8056)
- PsExec.exe (PID: 7200)
Checks current location (POWERSHELL)
- powershell.exe (PID: 3156)
Reads the computer name
- PsExec.exe (PID: 7200)
- PSEXESVC.exe (PID: 7584)
Checks supported languages
- PsExec.exe (PID: 7200)
- PSEXESVC.exe (PID: 7584)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2016:06:28 09:51:40 |
| ZipCRC: | 0xa95b4b2f |
| ZipCompressedSize: | 74460 |
| ZipUncompressedSize: | 151728 |
| ZipFileName: | PsLoggedon.exe |
Total processes
246
Monitored processes
12
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 736 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3156 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1073807364 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3576 | "C:\Program Files\RUXIM\PLUGscheduler.exe" | C:\Program Files\RUXIM\PLUGScheduler.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Update LifeCycle Component Scheduler Exit code: 0 Version: 10.0.19041.3623 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5260 | "cmd" /c "rundll32.exe C:\Users\admin\Desktop\RarExt.dll,nothing" | C:\Windows\System32\cmd.exe | — | PSEXESVC.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
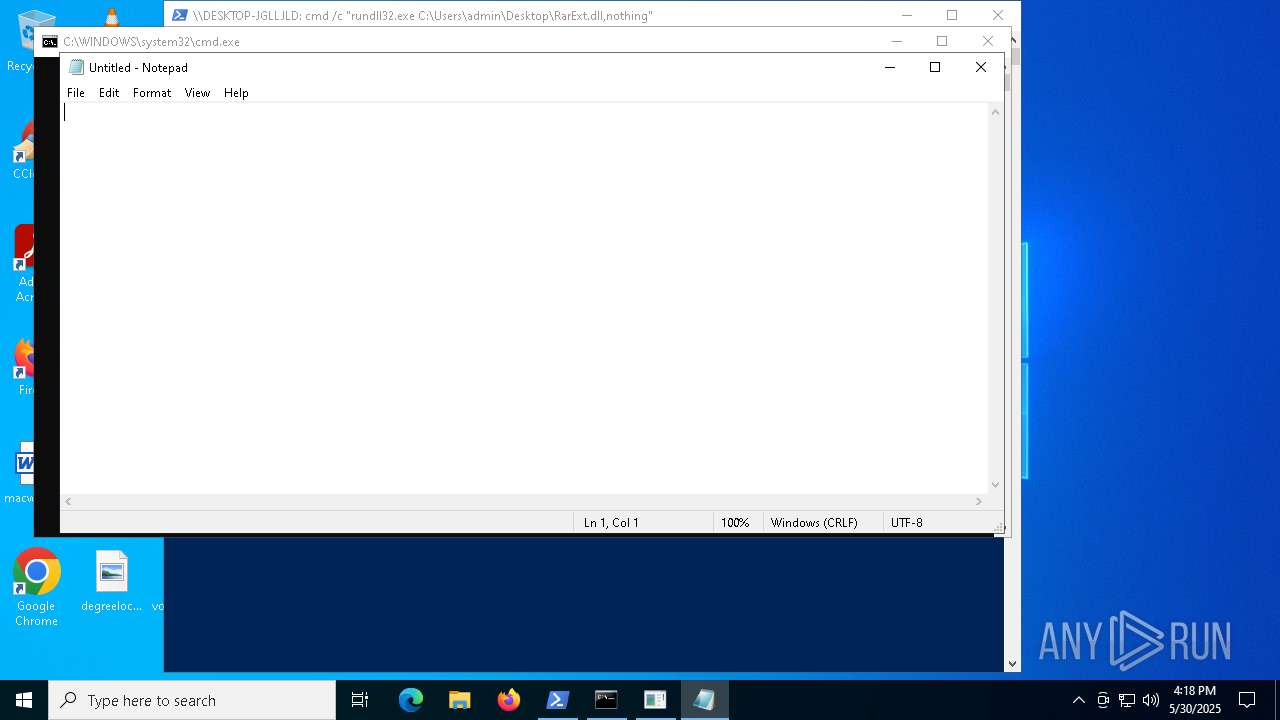
| 6416 | "notepad.exe" | C:\Windows\System32\notepad.exe | — | rundll32.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Notepad Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7184 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7200 | "C:\Users\admin\Desktop\PSTools\PsExec.exe" -i -s cmd /c "rundll32.exe C:\Users\admin\Desktop\RarExt.dll,nothing" | C:\Users\admin\Desktop\PSTools\PsExec.exe | powershell.exe | ||||||||||||
User: admin Company: Sysinternals - www.sysinternals.com Integrity Level: HIGH Description: Execute processes remotely Exit code: 0 Version: 2.43 Modules
| |||||||||||||||
| 7284 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7428 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | — | SppExtComObj.Exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7584 | C:\WINDOWS\PSEXESVC.exe | C:\Windows\PSEXESVC.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Sysinternals Integrity Level: SYSTEM Description: PsExec Service Exit code: 0 Version: 2.43 Modules
| |||||||||||||||
Total events
7 643
Read events
7 599
Write events
31
Delete events
13
Modification events
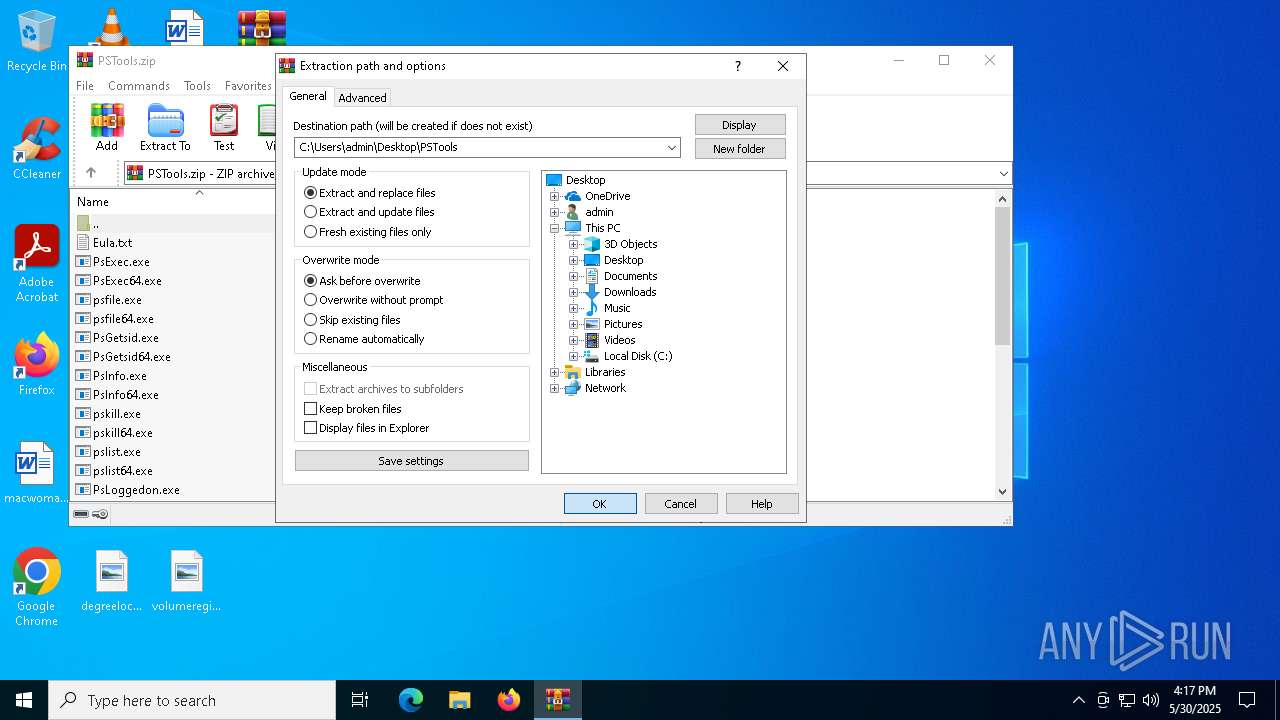
| (PID) Process: | (8056) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (8056) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (8056) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (8056) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\PSTools.zip | |||
| (PID) Process: | (8056) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (8056) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (8056) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (8056) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (8056) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 15 |
Value: | |||
| (PID) Process: | (8056) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 14 |
Value: | |||
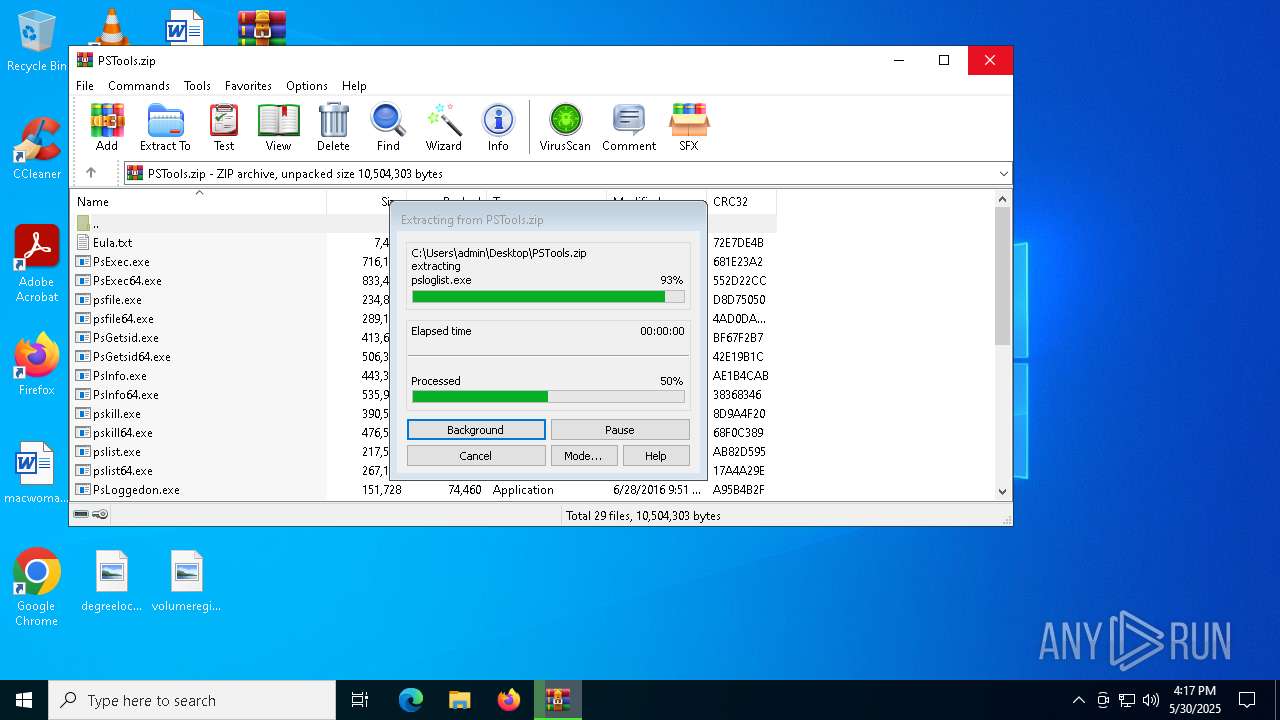
Executable files
27
Suspicious files
4
Text files
5
Unknown types
45
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 8056 | WinRAR.exe | C:\Users\admin\Desktop\PSTools\psshutdown.exe | executable | |
MD5:31E8E12D02A6CAC9088D89215CF4552C | SHA256:13FD3AD690C73CF0AD26C6716D4E9D1581B47C22FB7518B1D3BF9CFB8F9E9123 | |||
| 8056 | WinRAR.exe | C:\Users\admin\Desktop\PSTools\psping.exe | executable | |
MD5:93F162D9E1AE290F47695E71589FD4D4 | SHA256:355B4A82313074999BD8FA1332B1ED00034E63BD2A0D0367E2622F35D75CF140 | |||
| 8056 | WinRAR.exe | C:\Users\admin\Desktop\PSTools\psping64.exe | executable | |
MD5:AD7E3DDF557E1DE0170E384031D3A221 | SHA256:D1F718D219930E57794BDADF9DDA61406294B0759038CEF282F7544B44B92285 | |||
| 8056 | WinRAR.exe | C:\Users\admin\Desktop\PSTools\PsInfo64.exe | executable | |
MD5:86A65CFA9F258B0A46ED54E1AD235078 | SHA256:DE73B73EEB156F877DE61F4A6975D06759292ED69F31AAF06C9811F3311E03E7 | |||
| 8056 | WinRAR.exe | C:\Users\admin\Desktop\PSTools\psloglist64.exe | executable | |
MD5:14B2F5291036BE454AE2FC762FF6EAAA | SHA256:5E55B4CAF47A248A10ABD009617684E969DBE5C448D087EE8178262AAAB68636 | |||
| 8056 | WinRAR.exe | C:\Users\admin\Desktop\PSTools\pspasswd.exe | executable | |
MD5:427214D675B6BCE9F273EB2DDE0AEEFC | SHA256:6ED5D50CF9D07DB73EAA92C5405F6B1BF670028C602C605DFA7D4FCB80EF0801 | |||
| 8056 | WinRAR.exe | C:\Users\admin\Desktop\PSTools\pslist.exe | executable | |
MD5:6C08BAE0981841E0CD22FF0F0E8F7510 | SHA256:ED05F5D462767B3986583188000143F0EB24F7D89605523A28950E72E6B9039A | |||
| 8056 | WinRAR.exe | C:\Users\admin\Desktop\PSTools\pspasswd64.exe | executable | |
MD5:2A23848AC28D73352BA80584327FF713 | SHA256:8D950068F46A04E77AD6637C680CCCF5D703A1828FBD6BDCA513268AF4F2170F | |||
| 8056 | WinRAR.exe | C:\Users\admin\Desktop\PSTools\PsLoggedon.exe | executable | |
MD5:E3EA271E748CCDAD6A6D3E692D6F337E | SHA256:D689CB1DBD2E4C06CD15E51A6871C406C595790DDCDCD7DC8D0401C7183720EF | |||
| 8056 | WinRAR.exe | C:\Users\admin\Desktop\PSTools\PsLoggedon64.exe | executable | |
MD5:07ED30D2343BF8914DAAED872B681118 | SHA256:FDADB6E15C52C41A31E3C22659DD490D5B616E017D1B1AA6070008CE09ED27EA | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
36
DNS requests
19
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
2692 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
2692 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
3576 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
6544 | svchost.exe | 20.190.160.64:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | unknown |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 23.216.77.6:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
6544 | svchost.exe | 40.126.32.74:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
6208 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
7852 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
officeclient.microsoft.com |
| whitelisted |