| File name: | SecuriteInfo.com.HEUR.Trojan.OLE2.Agent.gen.26943.12401 |
| Full analysis: | https://app.any.run/tasks/8c8e509e-8cea-46e1-a13f-ef6aef7f09dd |
| Verdict: | Malicious activity |
| Analysis date: | December 19, 2023, 04:16:58 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-msi |
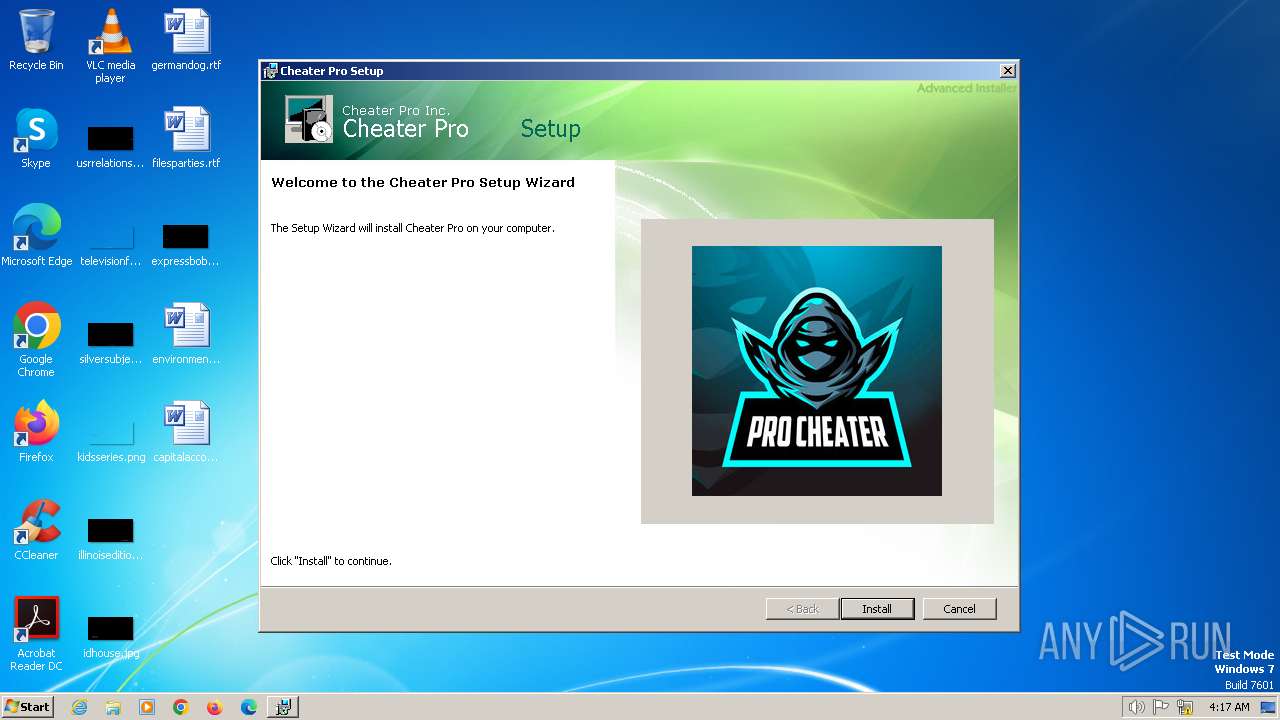
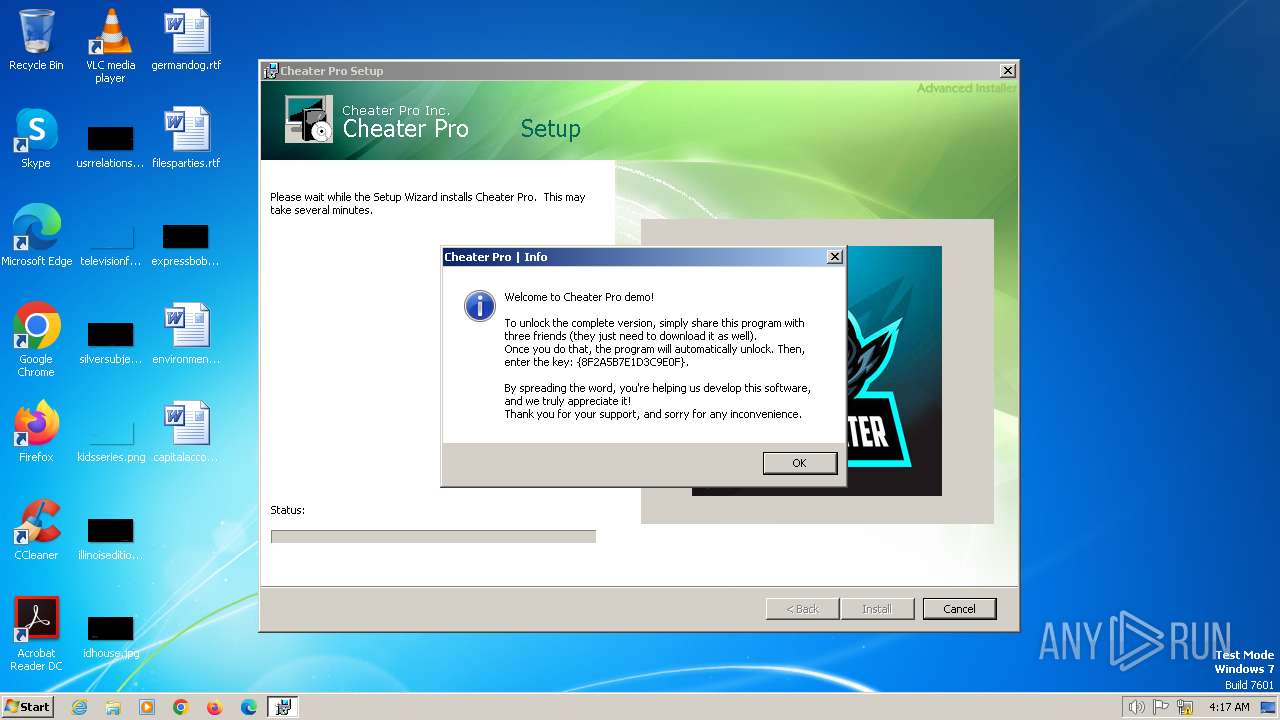
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.3, MSI Installer, Last Printed: Fri Dec 11 11:47:44 2009, Create Time/Date: Fri Dec 11 11:47:44 2009, Last Saved Time/Date: Fri Sep 18 15:06:51 2020, Security: 0, Code page: 1252, Revision Number: {959732BE-53D4-4D93-8FBD-66FB077C59F2}, Number of Words: 2, Subject: Cheater Pro, Author: Cheater Pro Inc., Name of Creating Application: Cheater Pro, Template: ;1033, Comments: This installer database contains the logic and data required to install Cheater Pro., Title: Installation Database, Keywords: Installer, MSI, Database, Number of Pages: 200 |
| MD5: | 3E40AF38940B787932D356D0B7BF4B3D |
| SHA1: | 5422AFE104A7F6A2B09FC6866F776DDF5645AC83 |
| SHA256: | A9C82EBF5E801A134BFB8B38A73138738A71C2CD7F255D886330277EB9E3C4B3 |
| SSDEEP: | 98304:EpTeoreXXiyP4Pr8fJ7Xo/Bef1Rmm2CNwNenuLCIutvZ3IgbrmS:sBuTg |
MALICIOUS
Drops the executable file immediately after the start
- msiexec.exe (PID: 1136)
Changes powershell execution policy (Bypass)
- msiexec.exe (PID: 1840)
Bypass execution policy to execute commands
- powershell.exe (PID: 992)
Run PowerShell with an invisible window
- powershell.exe (PID: 2904)
Adds extension to the Windows Defender exclusion list
- powershell.exe (PID: 992)
SUSPICIOUS
The process bypasses the loading of PowerShell profile settings
- msiexec.exe (PID: 1840)
The process hide an interactive prompt from the user
- msiexec.exe (PID: 1840)
Script adds exclusion extension to Windows Defender
- powershell.exe (PID: 992)
Application launched itself
- powershell.exe (PID: 992)
Starts POWERSHELL.EXE for commands execution
- powershell.exe (PID: 992)
- msiexec.exe (PID: 1840)
The process executes Powershell scripts
- msiexec.exe (PID: 1840)
Reads the Internet Settings
- msiexec.exe (PID: 1148)
- LuaJIT.exe (PID: 2124)
- msiexec.exe (PID: 3064)
Script adds exclusion path to Windows Defender
- powershell.exe (PID: 992)
Checks for external IP
- LuaJIT.exe (PID: 2124)
INFO
Reads the computer name
- msiexec.exe (PID: 1136)
- msiexec.exe (PID: 1840)
- msiexec.exe (PID: 3064)
- msiexec.exe (PID: 1648)
- LuaJIT.exe (PID: 2124)
- msiexec.exe (PID: 1148)
Checks supported languages
- msiexec.exe (PID: 1136)
- msiexec.exe (PID: 1840)
- msiexec.exe (PID: 3064)
- msiexec.exe (PID: 1648)
- LuaJIT.exe (PID: 2124)
- msiexec.exe (PID: 1148)
Create files in a temporary directory
- msiexec.exe (PID: 1840)
- powershell.exe (PID: 992)
- msiexec.exe (PID: 1136)
Reads Environment values
- msiexec.exe (PID: 1840)
Reads the machine GUID from the registry
- msiexec.exe (PID: 1136)
- msiexec.exe (PID: 3064)
- msiexec.exe (PID: 1148)
- msiexec.exe (PID: 1648)
- LuaJIT.exe (PID: 2124)
- msiexec.exe (PID: 1840)
Drops the executable file immediately after the start
- msiexec.exe (PID: 1404)
- msiexec.exe (PID: 2464)
Application launched itself
- msiexec.exe (PID: 3064)
Reads security settings of Internet Explorer
- powershell.exe (PID: 992)
Checks proxy server information
- LuaJIT.exe (PID: 2124)
Creates files or folders in the user directory
- LuaJIT.exe (PID: 2124)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msi | | | Microsoft Windows Installer (81.9) |
|---|---|---|
| .mst | | | Windows SDK Setup Transform Script (9.2) |
| .msp | | | Windows Installer Patch (7.6) |
| .msi | | | Microsoft Installer (100) |
EXIF
FlashPix
| LastPrinted: | 2009:12:11 11:47:44 |
|---|---|
| CreateDate: | 2009:12:11 11:47:44 |
| ModifyDate: | 2020:09:18 14:06:51 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| RevisionNumber: | {959732BE-53D4-4D93-8FBD-66FB077C59F2} |
| Words: | 2 |
| Subject: | Cheater Pro |
| Author: | Cheater Pro Inc. |
| LastModifiedBy: | - |
| Software: | Cheater Pro |
| Template: | ;1033 |
| Comments: | This installer database contains the logic and data required to install Cheater Pro. |
| Title: | Installation Database |
| Keywords: | Installer, MSI, Database |
| Pages: | 200 |
Total processes
62
Monitored processes
10
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 992 | -NoProfile -Noninteractive -ExecutionPolicy Bypass -File "C:\Users\admin\AppData\Local\Temp\pss6DF.ps1" -propFile "C:\Users\admin\AppData\Local\Temp\msi6DC.txt" -scriptFile "C:\Users\admin\AppData\Local\Temp\scr6DD.ps1" -scriptArgsFile "C:\Users\admin\AppData\Local\Temp\scr6DE.txt" -propSep " :<->: " -testPrefix "_testValue." | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 1136 | C:\Windows\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1148 | C:\Windows\syswow64\MsiExec.exe -Embedding 1531E94612451BE11C325C9199ADD04C C | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1404 | "C:\Windows\System32\msiexec.exe" /i "C:\Users\admin\AppData\Local\Temp\SecuriteInfo.com.HEUR.Trojan.OLE2.Agent.gen.26943.12401.msi" | C:\Windows\System32\msiexec.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 1602 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1648 | C:\Windows\syswow64\MsiExec.exe -Embedding 38A775C730AADE8ED3F96ED05E230362 E Global\MSI0000 | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1840 | C:\Windows\syswow64\MsiExec.exe -Embedding 13A1571E54F31A856B4DDFF82700CFB9 | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2124 | "C:\Program Files (x86)\Cheater Pro Inc\Cheater Pro\LuaJIT.exe" "C:\Program Files (x86)\Cheater Pro Inc\Cheater Pro\file" | C:\Program Files (x86)\Cheater Pro Inc\Cheater Pro\LuaJIT.exe | msiexec.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2464 | "C:\Windows\SysWOW64\msiexec.exe" /i "C:\Users\admin\AppData\Local\Temp\SecuriteInfo.com.HEUR.Trojan.OLE2.Agent.gen.26943.12401.msi" | C:\Windows\SysWOW64\msiexec.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2904 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -WindowStyle hidden -Command "& { & 'Add-MpPreference' -ExclusionExtension '.dll', '.exe' -ExclusionPath C: -Force }" | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 3064 | C:\Windows\syswow64\MsiExec.exe -Embedding DDC15E96B25642BB49D7E9594E0E8617 C | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
5 355
Read events
5 311
Write events
34
Delete events
10
Modification events
| (PID) Process: | (3064) msiexec.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3064) msiexec.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3064) msiexec.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3064) msiexec.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (2904) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\15A\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1136) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\MUI\StringCacheSettings |
| Operation: | write | Name: | StringCacheGeneration |
Value: 346 | |||
| (PID) Process: | (1136) msiexec.exe | Key: | HKEY_USERS\.DEFAULT\Software\Classes\Local Settings\MuiCache\15A\52C64B7E |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (1136) msiexec.exe | Key: | HKEY_USERS\.DEFAULT\Software\Classes\Local Settings\MuiCache\15A |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (1136) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\MICROSOFT\Windows\CurrentVersion\Installer\Rollback\Scripts |
| Operation: | delete value | Name: | C:\Config.Msi\f0529.rbs |
Value: 31076914 | |||
| (PID) Process: | (1136) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\MICROSOFT\Windows\CurrentVersion\Installer\Rollback\Scripts |
| Operation: | delete key | Name: | (default) |
Value: | |||
Executable files
22
Suspicious files
14
Text files
3
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1840 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\msi6DC.txt | — | |
MD5:— | SHA256:— | |||
| 1840 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\scr6DD.ps1 | — | |
MD5:— | SHA256:— | |||
| 1840 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\scr6DE.txt | — | |
MD5:— | SHA256:— | |||
| 1840 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\pss6DF.ps1 | — | |
MD5:— | SHA256:— | |||
| 2464 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSIFB65.tmp | executable | |
MD5:475D20C0EA477A35660E3F67ECF0A1DF | SHA256:426E6CF199A8268E8A7763EC3A4DD7ADD982B28C51D89EBEA90CA792CBAE14DD | |||
| 1136 | msiexec.exe | C:\Windows\Installer\f0527.msi | executable | |
MD5:3E40AF38940B787932D356D0B7BF4B3D | SHA256:A9C82EBF5E801A134BFB8B38A73138738A71C2CD7F255D886330277EB9E3C4B3 | |||
| 2464 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSIFB45.tmp | executable | |
MD5:475D20C0EA477A35660E3F67ECF0A1DF | SHA256:426E6CF199A8268E8A7763EC3A4DD7ADD982B28C51D89EBEA90CA792CBAE14DD | |||
| 2464 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSIFB05.tmp | executable | |
MD5:475D20C0EA477A35660E3F67ECF0A1DF | SHA256:426E6CF199A8268E8A7763EC3A4DD7ADD982B28C51D89EBEA90CA792CBAE14DD | |||
| 2464 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSIFB85.tmp | executable | |
MD5:475D20C0EA477A35660E3F67ECF0A1DF | SHA256:426E6CF199A8268E8A7763EC3A4DD7ADD982B28C51D89EBEA90CA792CBAE14DD | |||
| 1136 | msiexec.exe | C:\Windows\Installer\MSI575.tmp | executable | |
MD5:475D20C0EA477A35660E3F67ECF0A1DF | SHA256:426E6CF199A8268E8A7763EC3A4DD7ADD982B28C51D89EBEA90CA792CBAE14DD | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
8
DNS requests
2
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2124 | LuaJIT.exe | GET | 200 | 208.95.112.1:80 | http://ip-api.com/json/?fields=query,status,countryCode,city,timezone | unknown | binary | 116 b | unknown |
2124 | LuaJIT.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/ | unknown | html | 1020 b | unknown |
2124 | LuaJIT.exe | PUT | 200 | 213.248.43.40:80 | http://213.248.43.40/loader/screen/OWYsN2YsN2YsYTAsOWUsODYsOGMsOTYsNjQsN2Ms | unknown | binary | 19 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
352 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
1220 | svchost.exe | 239.255.255.250:3702 | — | — | — | whitelisted |
2124 | LuaJIT.exe | 208.95.112.1:80 | ip-api.com | TUT-AS | US | unknown |
2124 | LuaJIT.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
2124 | LuaJIT.exe | 213.248.43.40:80 | — | LLC Digital Network | RU | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ip-api.com |
| shared |
www.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2124 | LuaJIT.exe | Potential Corporate Privacy Violation | AV POLICY Internal Host Retrieving External IP Address (ip-api. com) |
2124 | LuaJIT.exe | Device Retrieving External IP Address Detected | ET POLICY External IP Lookup ip-api.com |