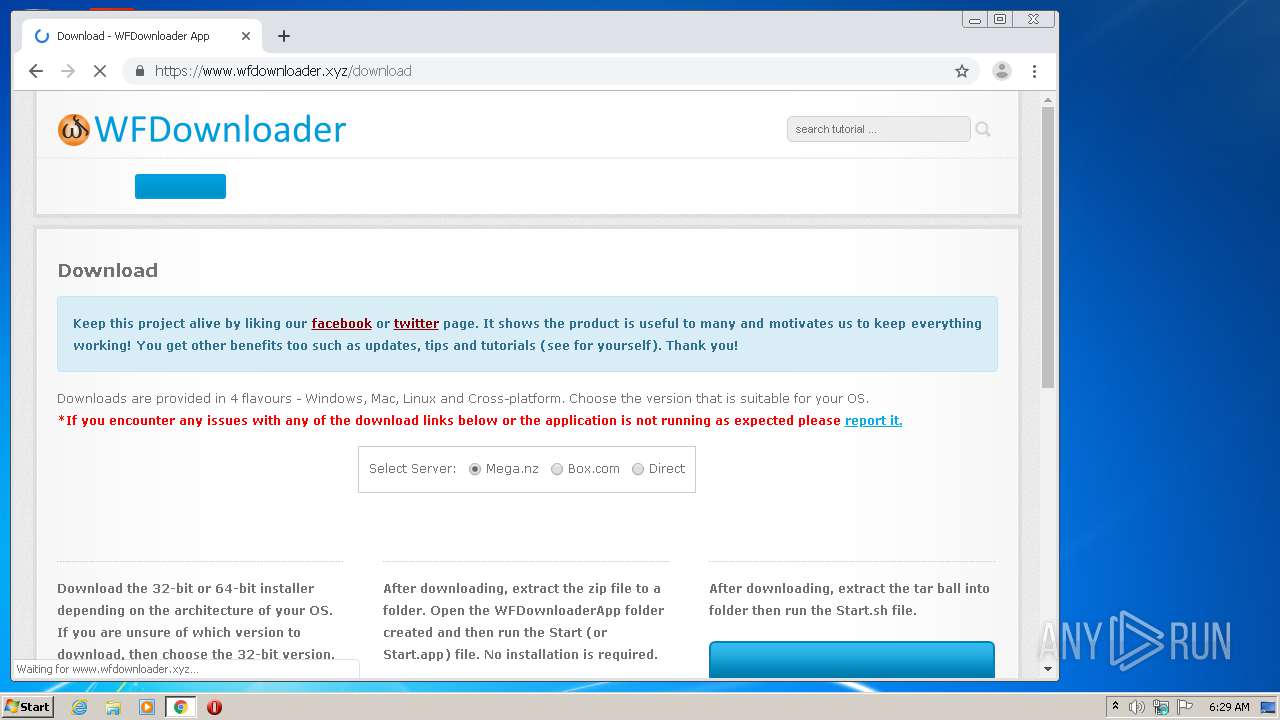
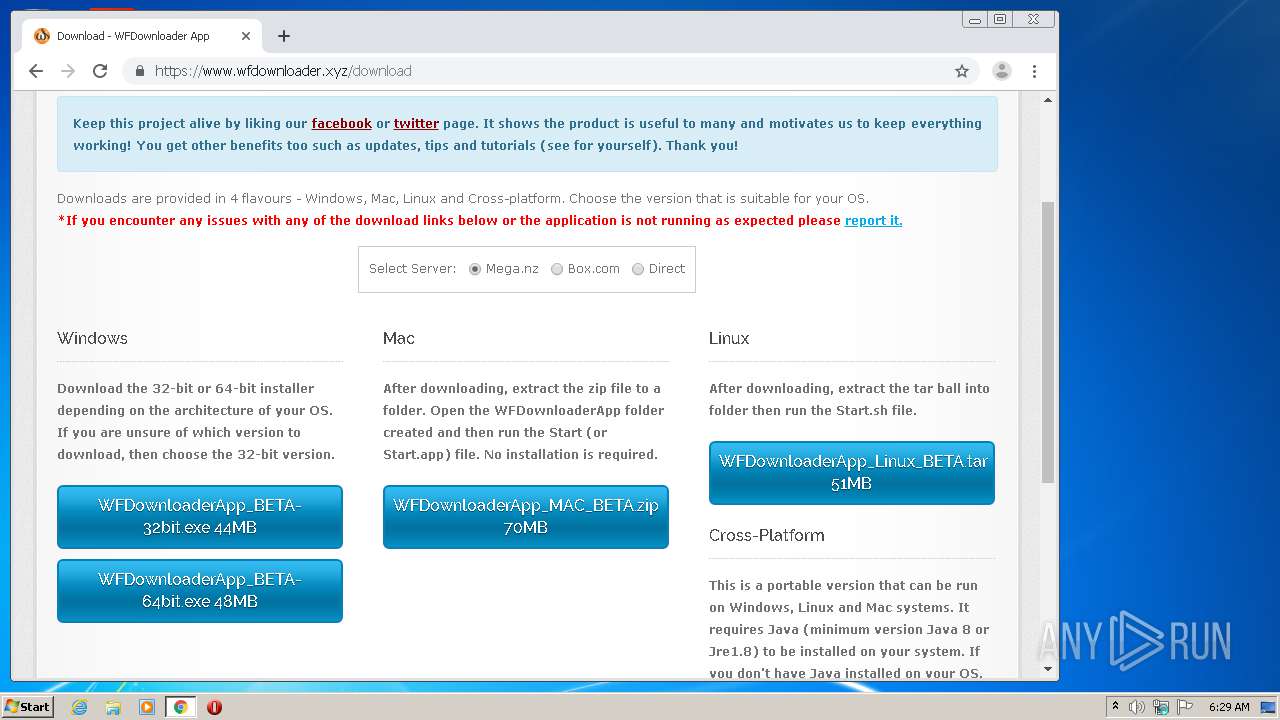
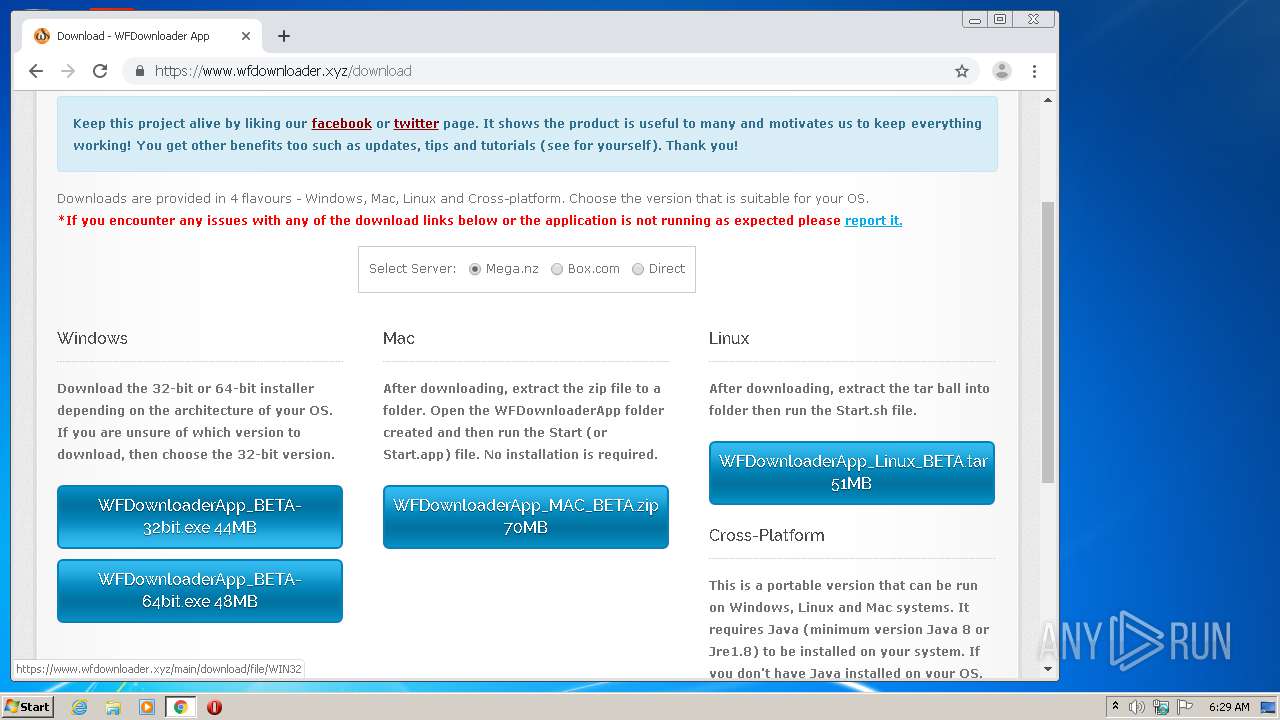
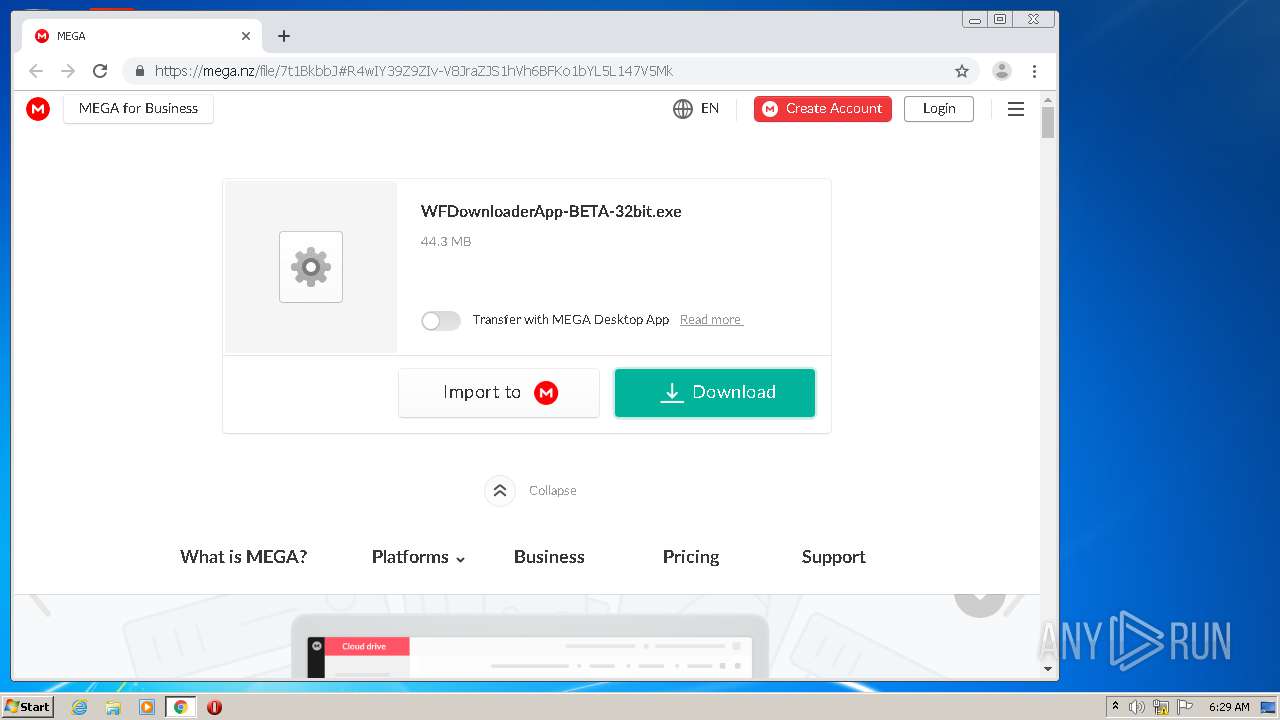
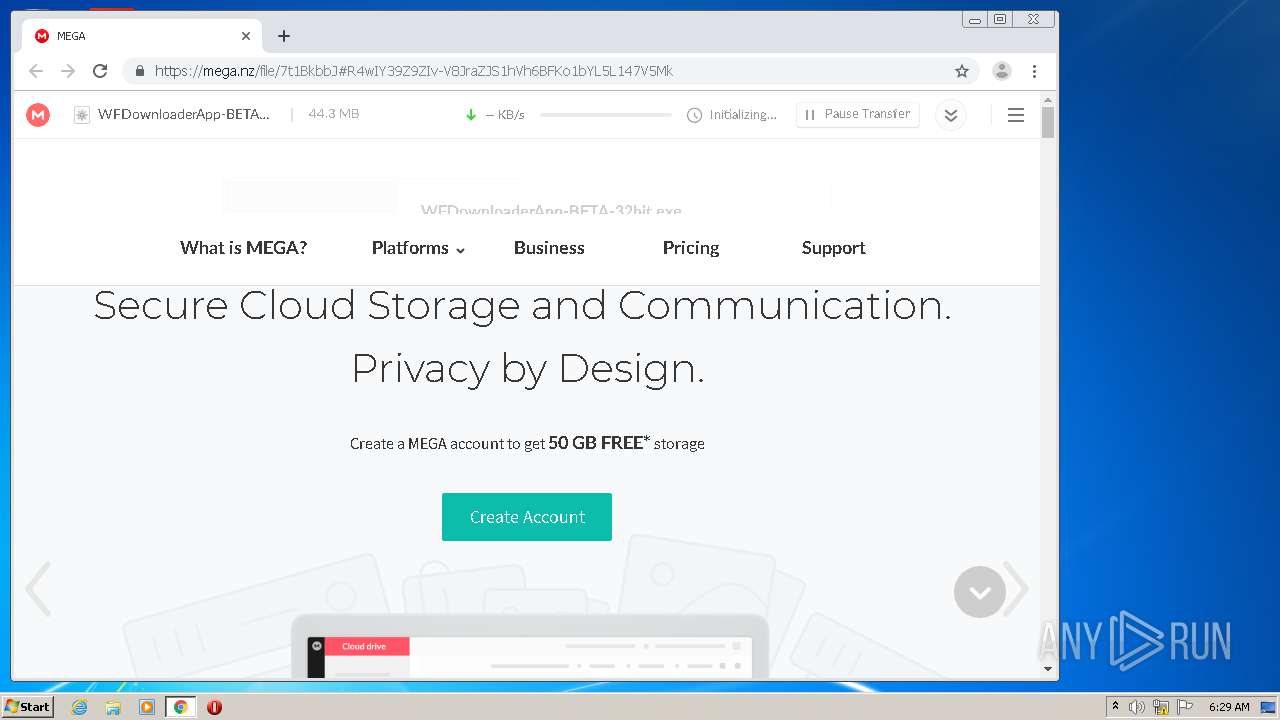
| download: | WIN32 |
| Full analysis: | https://app.any.run/tasks/b50f8fec-2f2f-485b-a99a-a22305720cd5 |
| Verdict: | Malicious activity |
| Analysis date: | July 13, 2020, 05:28:41 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/html |
| File info: | HTML document, ASCII text |
| MD5: | 5A67082B831BCCA01779C5C8CFB2D6C5 |
| SHA1: | 9905BC741EC5BDB16D5DFB7D3088CE0341F8054D |
| SHA256: | A9AAAB1DA817B6B3E8C74FB62AD4D869051F6C6018C8A1C89DDE8F2761C40947 |
| SSDEEP: | 48:/VsCymjZxJup8Vb2L5a6f8Nv3P3msEhb/FUY:/5uWU5a6f8IsEhb/FUY |
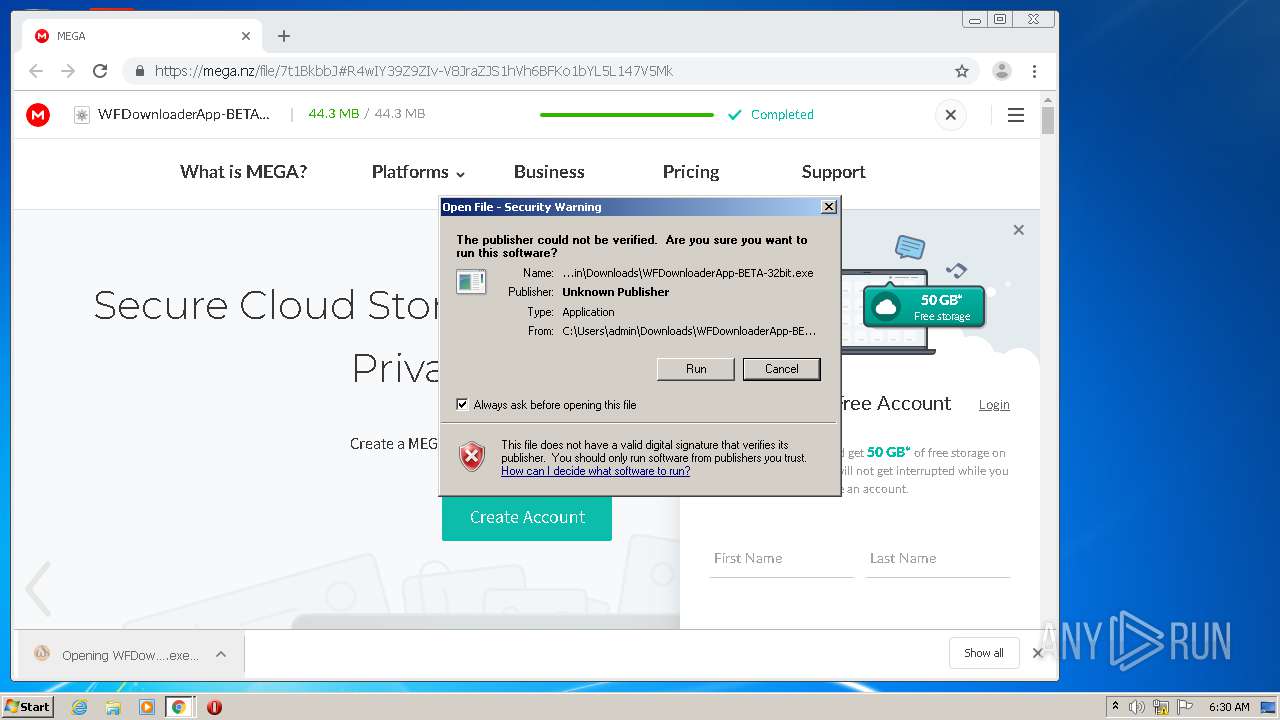
MALICIOUS
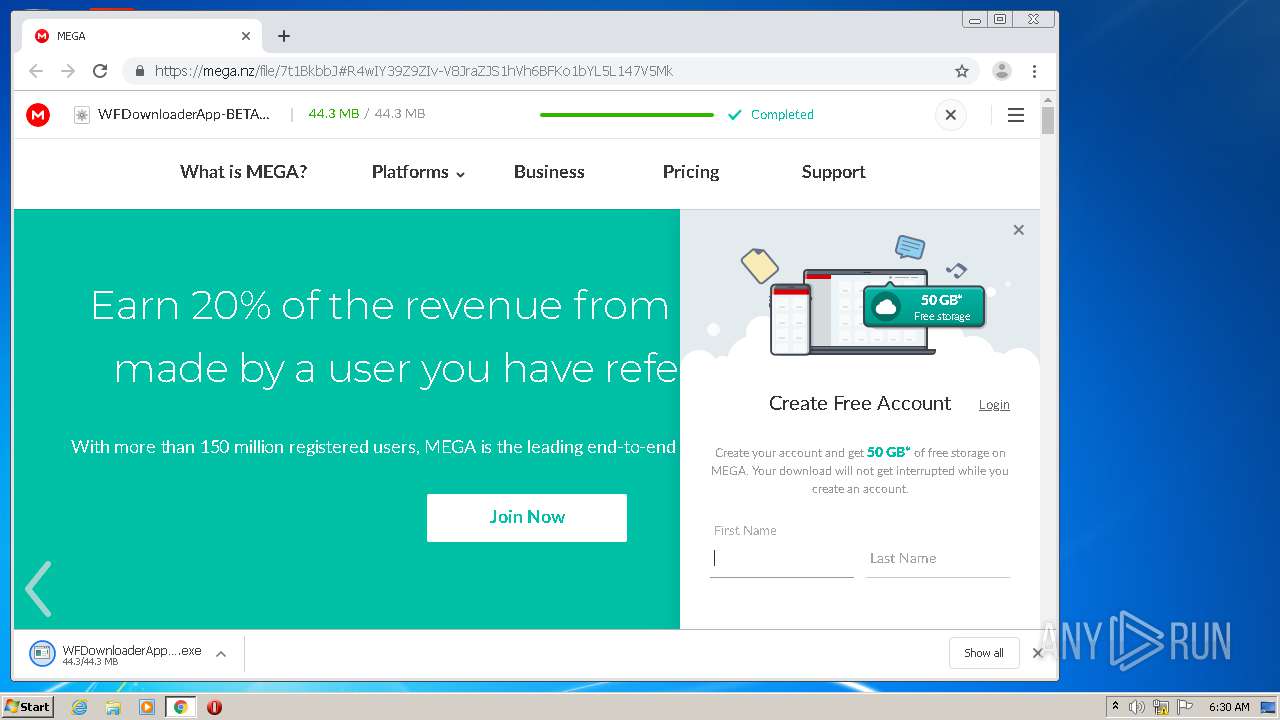
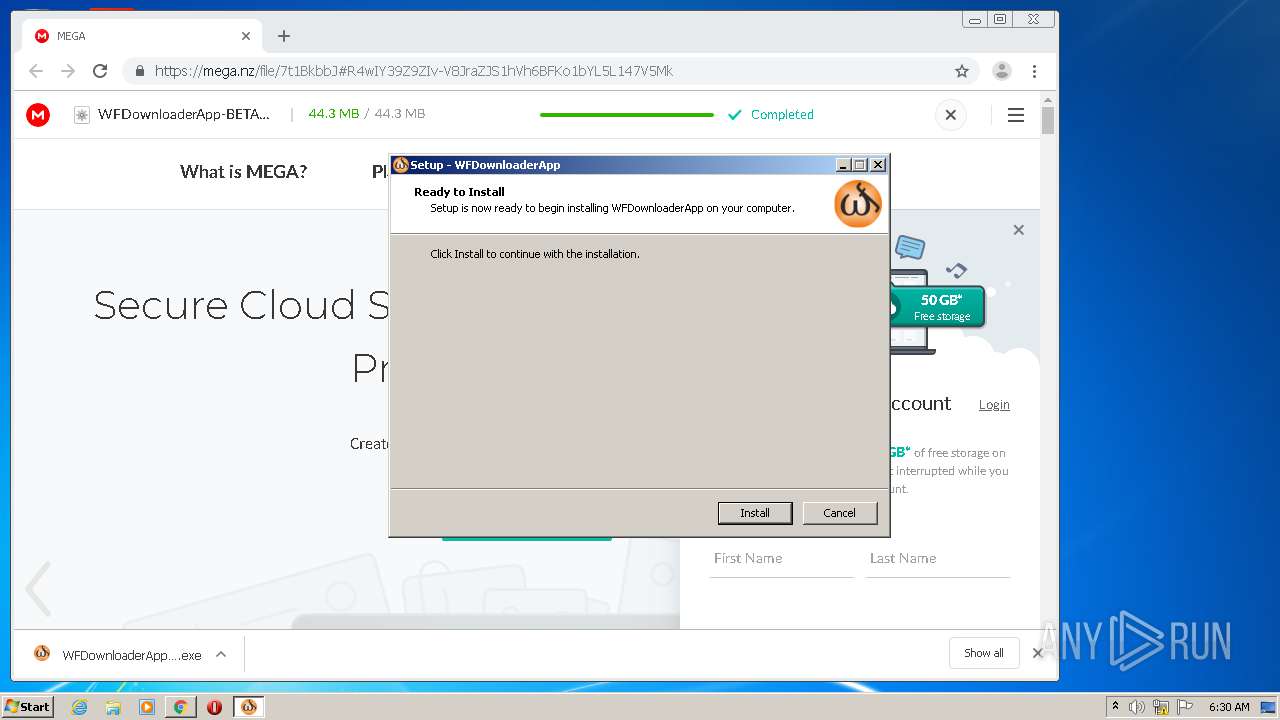
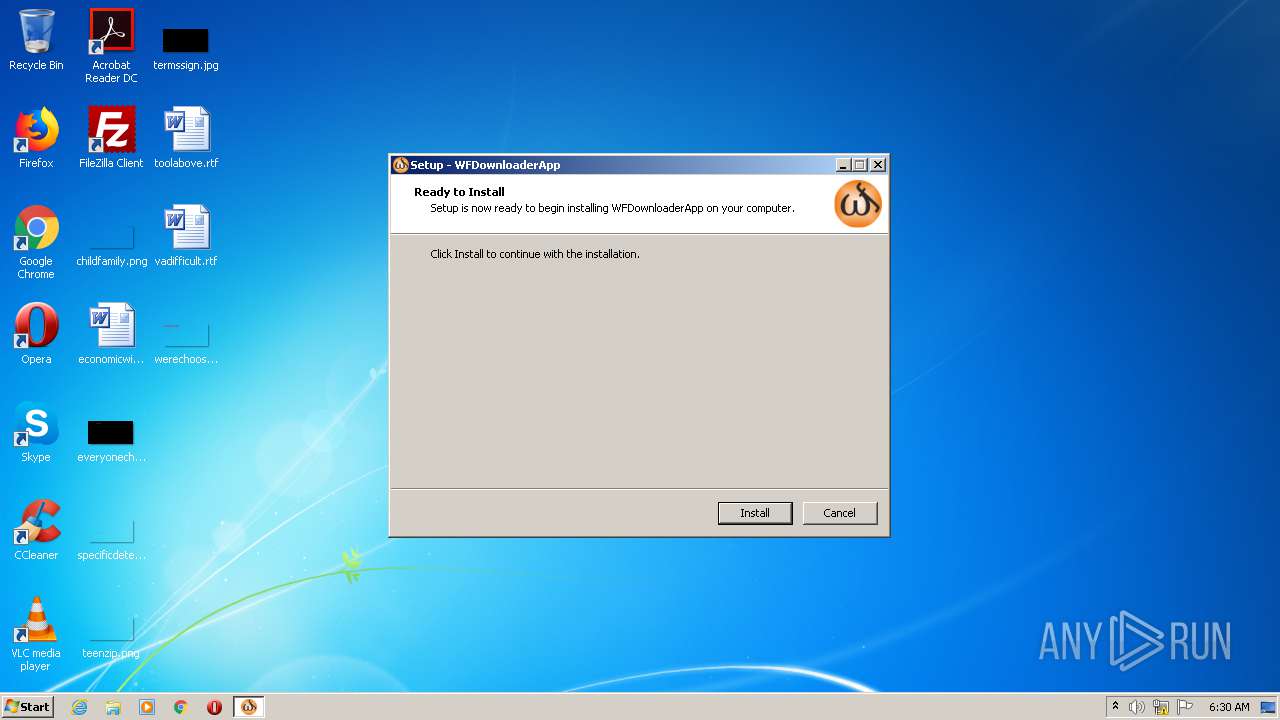
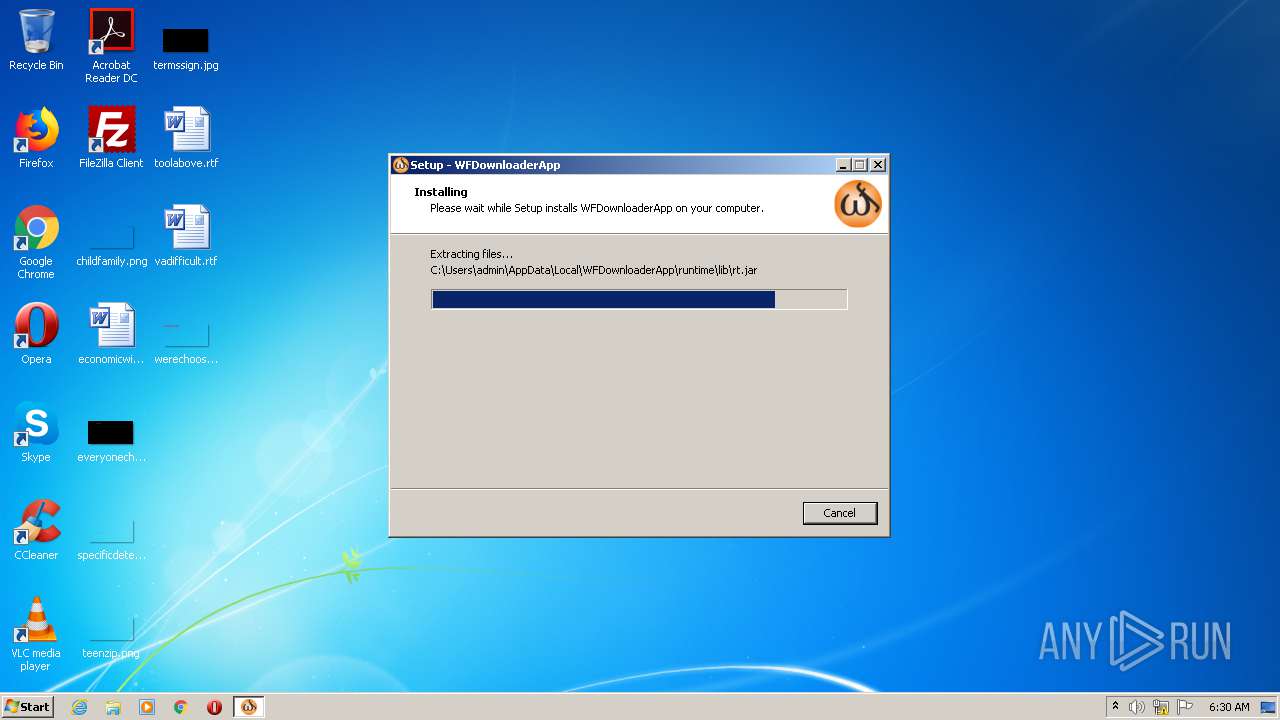
Application was dropped or rewritten from another process
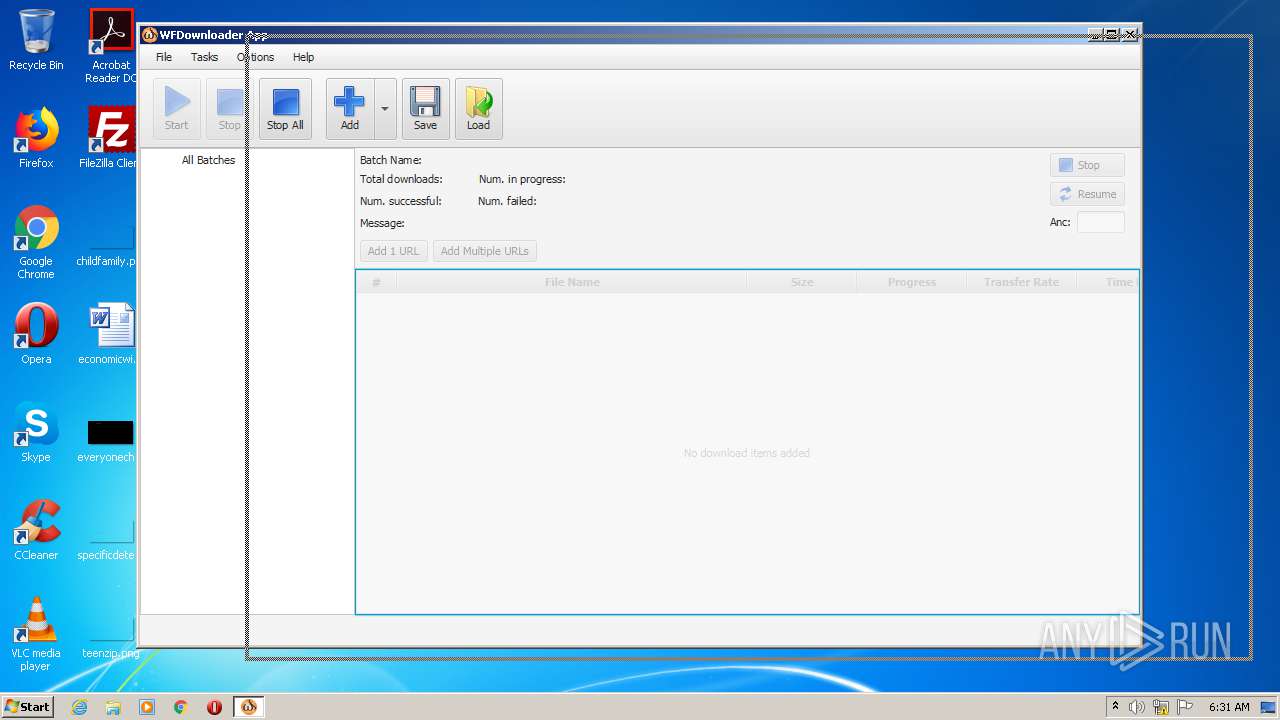
- WFDownloaderApp-BETA-32bit.exe (PID: 1768)
- WFDownloaderApp.exe (PID: 1496)
Loads dropped or rewritten executable
- WFDownloaderApp.exe (PID: 1496)
SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 3816)
Executable content was dropped or overwritten
- chrome.exe (PID: 3816)
- WFDownloaderApp-BETA-32bit.exe (PID: 1768)
- WFDownloaderApp-BETA-32bit.tmp (PID: 2744)
Creates files in the user directory
- WFDownloaderApp-BETA-32bit.tmp (PID: 2744)
INFO
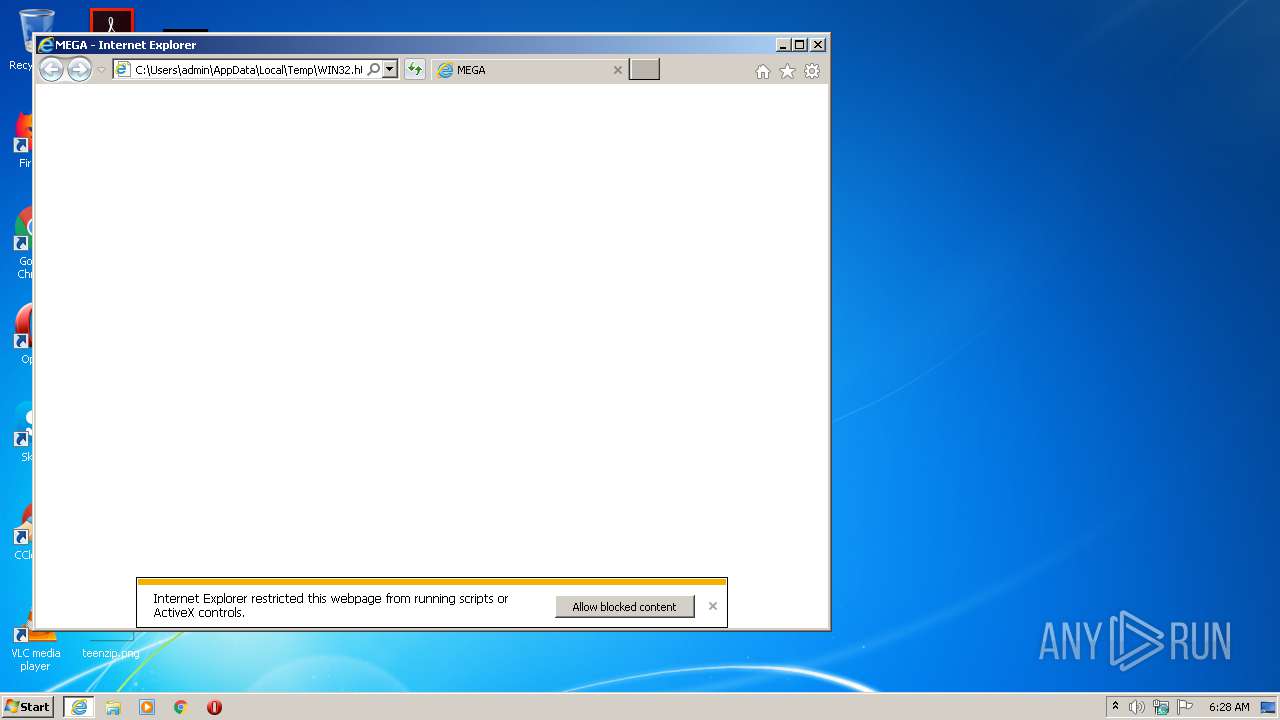
Reads Internet Cache Settings
- iexplore.exe (PID: 2220)
- iexplore.exe (PID: 2872)
Application launched itself
- iexplore.exe (PID: 2220)
- iexplore.exe (PID: 1628)
- chrome.exe (PID: 3816)
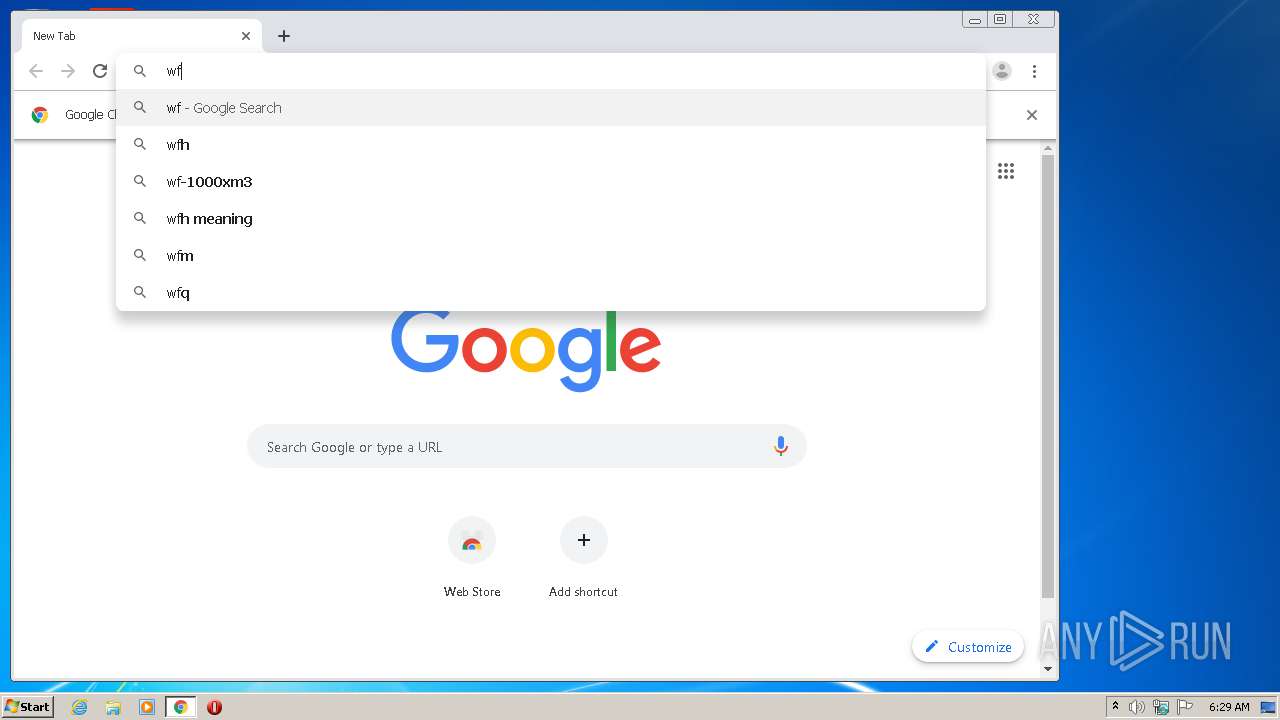
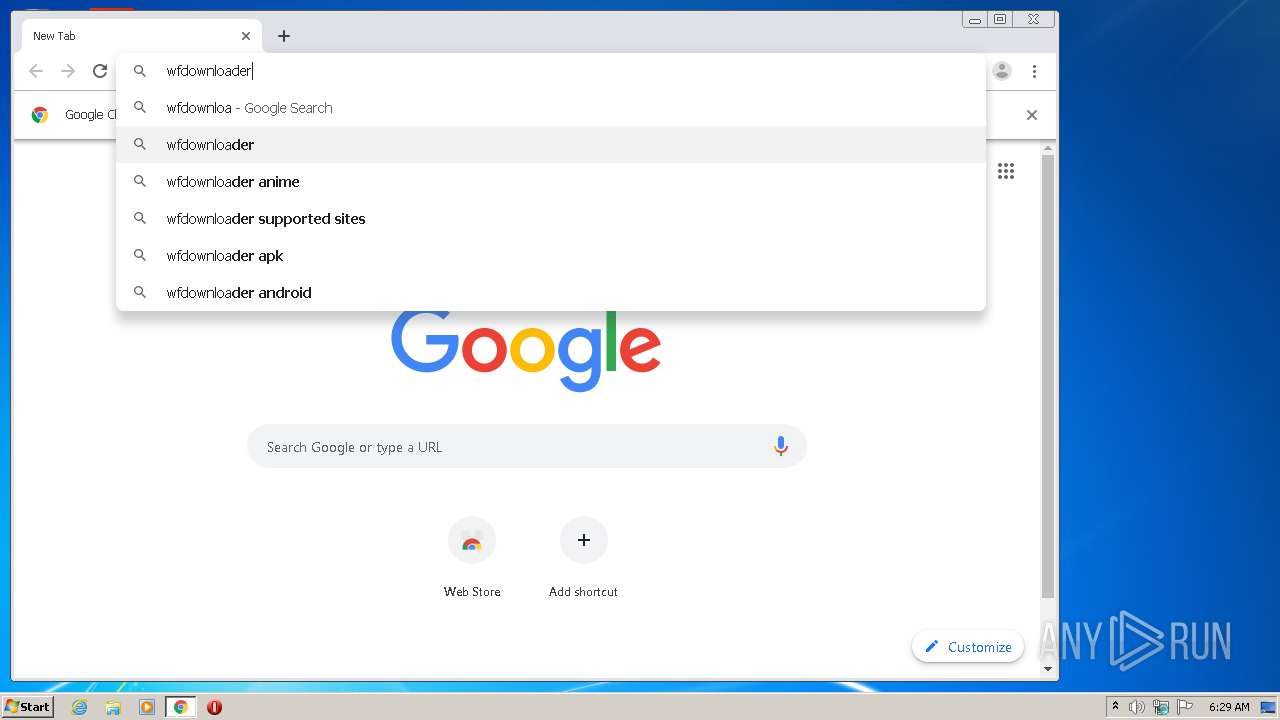
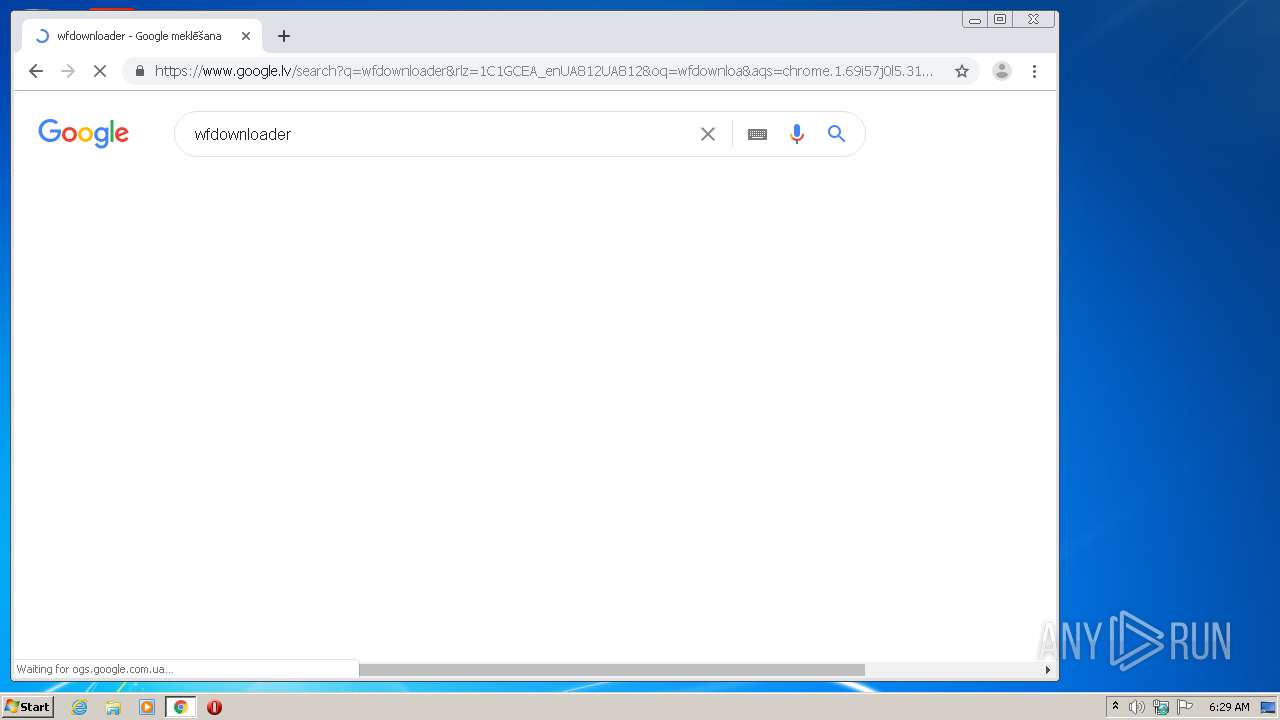
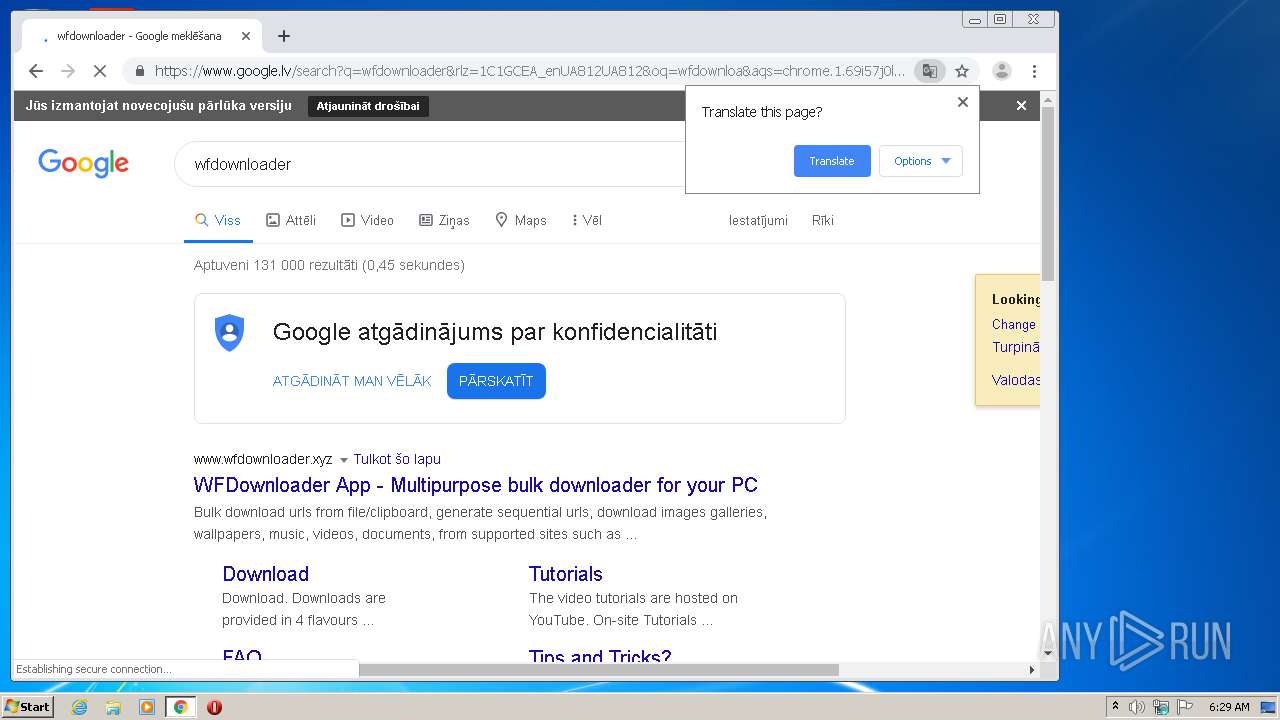
Manual execution by user
- chrome.exe (PID: 3816)
Changes internet zones settings
- iexplore.exe (PID: 2220)
Reads internet explorer settings
- iexplore.exe (PID: 1628)
Reads the hosts file
- chrome.exe (PID: 3816)
- chrome.exe (PID: 2948)
Application was dropped or rewritten from another process
- WFDownloaderApp-BETA-32bit.tmp (PID: 2744)
Loads dropped or rewritten executable
- WFDownloaderApp-BETA-32bit.tmp (PID: 2744)
Creates a software uninstall entry
- WFDownloaderApp-BETA-32bit.tmp (PID: 2744)
Reads settings of System Certificates
- chrome.exe (PID: 2948)
- iexplore.exe (PID: 2220)
Changes settings of System certificates
- iexplore.exe (PID: 2220)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2220)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .html | | | HyperText Markup Language (100) |
|---|
EXIF
HTML
| HTTPEquivXUACompatible: | IE=Edge |
|---|---|
| ContentType: | text/html, charset=UTF-8 |
| viewport: | width=device-width, initial-scale=1.0, maximum-scale=1.0, user-scalable=0 |
| appleItunesApp: | app-id=706857885 |
| Description: | MEGA provides free cloud storage with convenient and powerful always-on privacy. Claim your free 50GB now! |
| Title: | MEGA |
Total processes
78
Monitored processes
40
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 572 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,1069501807398751396,177303217093261121,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=3773269086640519858 --mojo-platform-channel-handle=4016 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 692 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,1069501807398751396,177303217093261121,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5866915127583140869 --renderer-client-id=20 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3604 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 764 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,1069501807398751396,177303217093261121,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=1976513767768371259 --mojo-platform-channel-handle=3796 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 920 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6f58a9d0,0x6f58a9e0,0x6f58a9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 960 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,1069501807398751396,177303217093261121,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14186520313597870997 --renderer-client-id=22 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4172 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1036 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,1069501807398751396,177303217093261121,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11618915733053861309 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2460 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
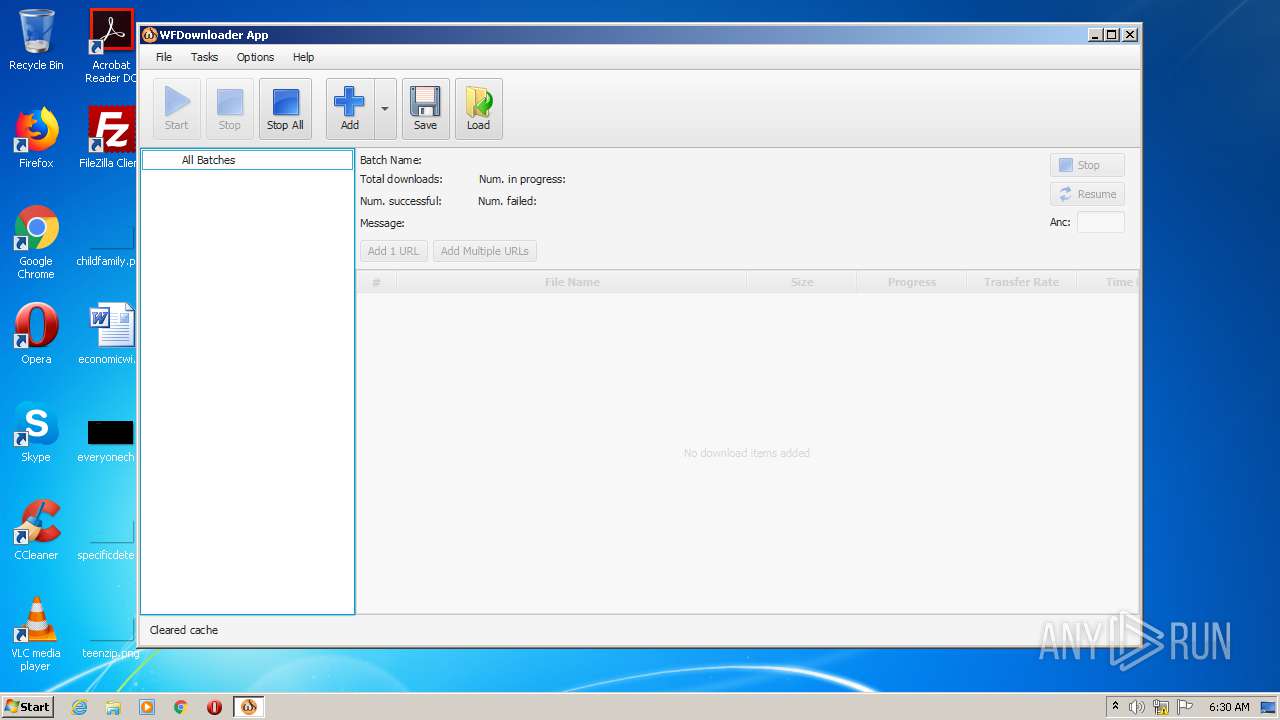
| 1496 | "C:\Users\admin\AppData\Local\WFDownloaderApp\WFDownloaderApp.exe" | C:\Users\admin\AppData\Local\WFDownloaderApp\WFDownloaderApp.exe | WFDownloaderApp-BETA-32bit.tmp | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1536 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,1069501807398751396,177303217093261121,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17353617253542553 --renderer-client-id=16 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3432 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1628 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2220 CREDAT:144385 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
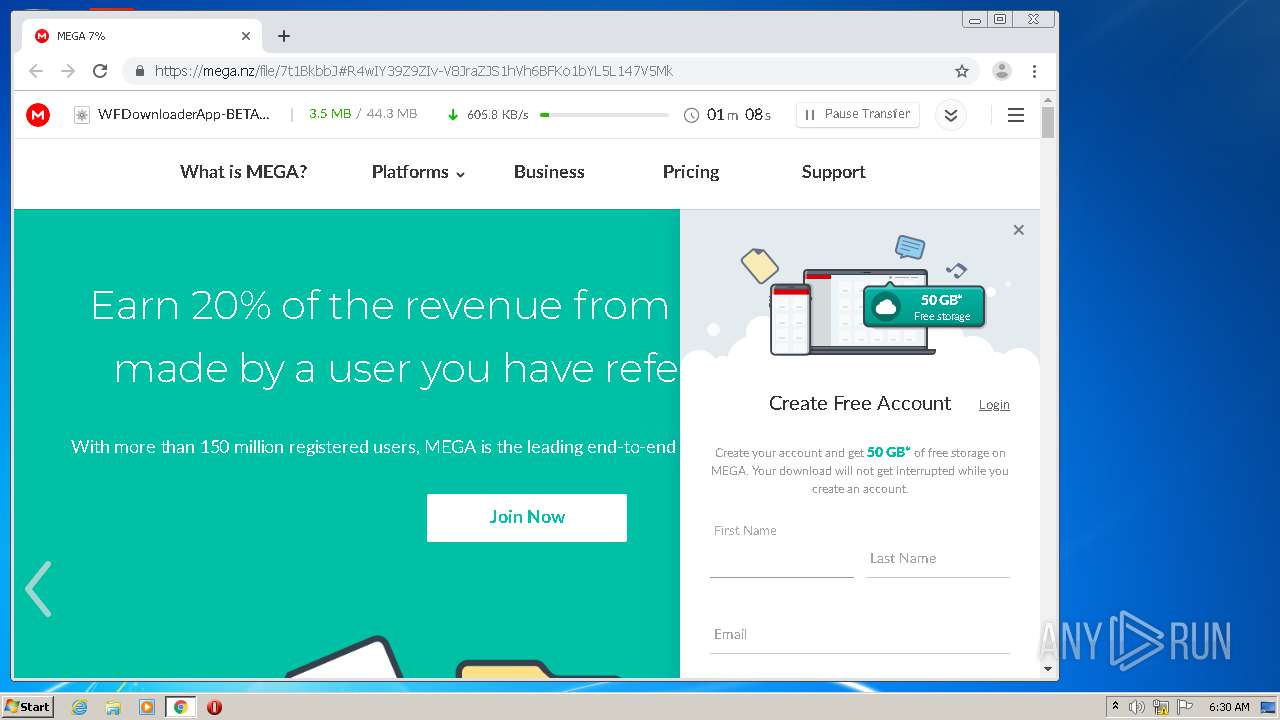
| 1768 | "C:\Users\admin\Downloads\WFDownloaderApp-BETA-32bit.exe" | C:\Users\admin\Downloads\WFDownloaderApp-BETA-32bit.exe | chrome.exe | ||||||||||||
User: admin Company: WFDownloaderApp Integrity Level: MEDIUM Description: WFDownloaderApp Setup Exit code: 0 Version: Modules
| |||||||||||||||
Total events
9 356
Read events
2 470
Write events
4 628
Delete events
2 258
Modification events
| (PID) Process: | (2220) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 2459112298 | |||
| (PID) Process: | (2220) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30824662 | |||
| (PID) Process: | (2220) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2220) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2220) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2220) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2220) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2220) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A1000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2220) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2220) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
126
Suspicious files
144
Text files
354
Unknown types
30
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2220 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2220 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF923AC69887CD9ECE.TMP | — | |
MD5:— | SHA256:— | |||
| 2220 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF900FFBFB61D6CCB3.TMP | — | |
MD5:— | SHA256:— | |||
| 2220 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF8DFBE00B4D559F54.TMP | — | |
MD5:— | SHA256:— | |||
| 2220 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFDCA98196C37FD414.TMP | — | |
MD5:— | SHA256:— | |||
| 3816 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5F0BF136-EE8.pma | — | |
MD5:— | SHA256:— | |||
| 3816 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\140f2806-e789-47b2-83bc-bc1adcb3cfa9.tmp | — | |
MD5:— | SHA256:— | |||
| 2220 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFCF8F2E04D3A6A4A3.TMP | — | |
MD5:— | SHA256:— | |||
| 2220 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\RecoveryStore.{BE4FAE29-C4C9-11EA-9F9D-5254004A04AF}.dat | — | |
MD5:— | SHA256:— | |||
| 3816 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
72
DNS requests
45
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2948 | chrome.exe | GET | 302 | 172.217.16.206:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 527 b | whitelisted |
2948 | chrome.exe | GET | 302 | 172.217.16.206:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvY2Y1QUFXUjZlVjI5UldyLVpDTFJFcEx6QQ/7719.805.0.2_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 532 b | whitelisted |
2220 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
2220 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
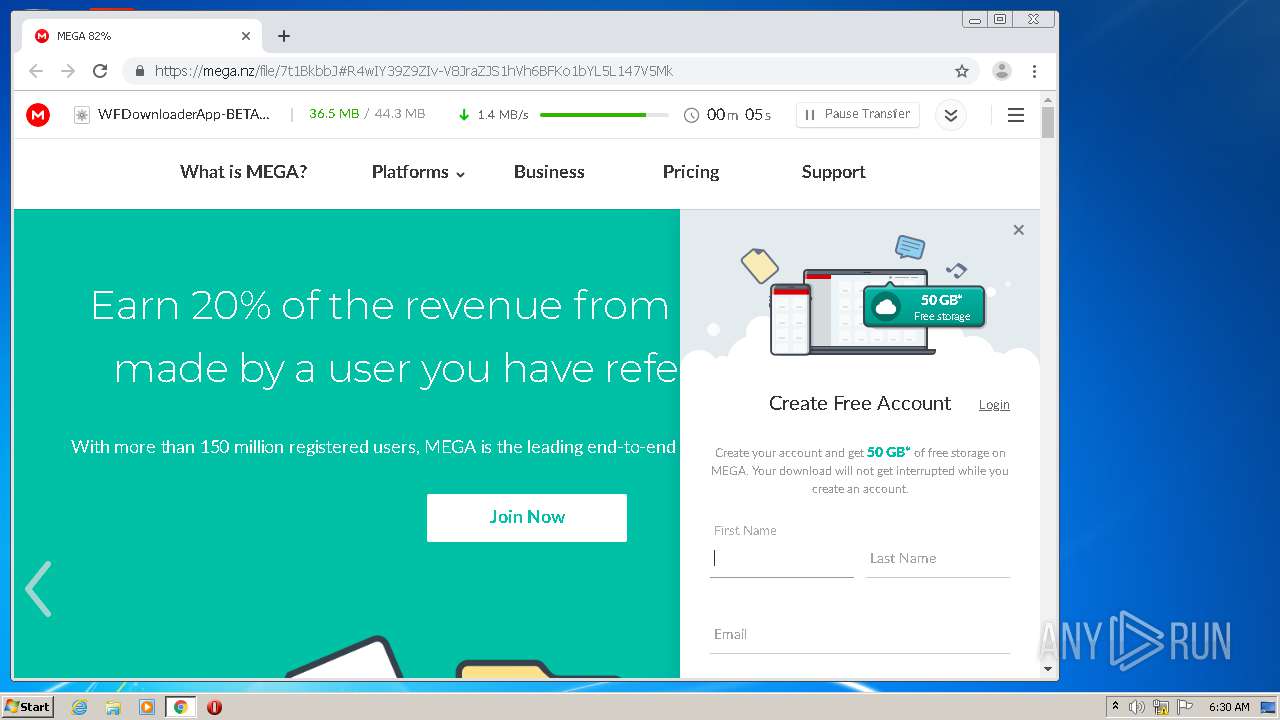
1496 | WFDownloaderApp.exe | GET | 200 | 31.22.4.67:80 | http://wfdownloader.xyz/update/check?v=79 | GB | text | 172 b | suspicious |
1496 | WFDownloaderApp.exe | GET | 200 | 31.22.4.67:80 | http://www.wfdownloader.xyz/update/getlfd?v=79 | GB | compressed | 179 Kb | suspicious |
2948 | chrome.exe | GET | 200 | 159.148.69.143:80 | http://r4---sn-a5uoxu-gpme.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mh=QJ&mip=159.148.186.246&mm=28&mn=sn-a5uoxu-gpme&ms=nvh&mt=1594617487&mv=u&mvi=4&pl=24&shardbypass=yes | LV | crx | 293 Kb | whitelisted |
2220 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
2948 | chrome.exe | GET | 200 | 159.148.69.141:80 | http://r2---sn-a5uoxu-gpme.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvY2Y1QUFXUjZlVjI5UldyLVpDTFJFcEx6QQ/7719.805.0.2_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mh=Nf&mip=159.148.186.246&mm=28&mn=sn-a5uoxu-gpme&ms=nvh&mt=1594617487&mv=u&mvi=2&pl=24&shardbypass=yes | LV | crx | 823 Kb | whitelisted |
2220 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2948 | chrome.exe | 172.217.22.35:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
2948 | chrome.exe | 216.58.208.46:443 | apis.google.com | Google Inc. | US | whitelisted |
2948 | chrome.exe | 172.217.22.46:443 | clients2.google.com | Google Inc. | US | whitelisted |
2948 | chrome.exe | 172.217.22.110:443 | ogs.google.com.ua | Google Inc. | US | whitelisted |
2948 | chrome.exe | 31.22.4.67:443 | www.wfdownloader.xyz | Wildcard UK Limited | GB | suspicious |
2948 | chrome.exe | 159.148.69.143:80 | r4---sn-a5uoxu-gpme.gvt1.com | LATNET SERVISS Ltd. | LV | whitelisted |
2948 | chrome.exe | 172.217.16.206:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
2948 | chrome.exe | 216.58.206.1:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
2220 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2220 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com.ua |
| whitelisted |
www.google.com |
| malicious |
www.google.lv |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2948 | chrome.exe | Potentially Bad Traffic | ET INFO Observed Let's Encrypt Certificate for Suspicious TLD (.xyz) |
2948 | chrome.exe | Potentially Bad Traffic | ET INFO Observed Let's Encrypt Certificate for Suspicious TLD (.xyz) |
1496 | WFDownloaderApp.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
1496 | WFDownloaderApp.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
1 ETPRO signatures available at the full report