| File name: | Win10Tweaker.exe |
| Full analysis: | https://app.any.run/tasks/6ee6bff7-8176-4b68-bb96-8a755052c664 |
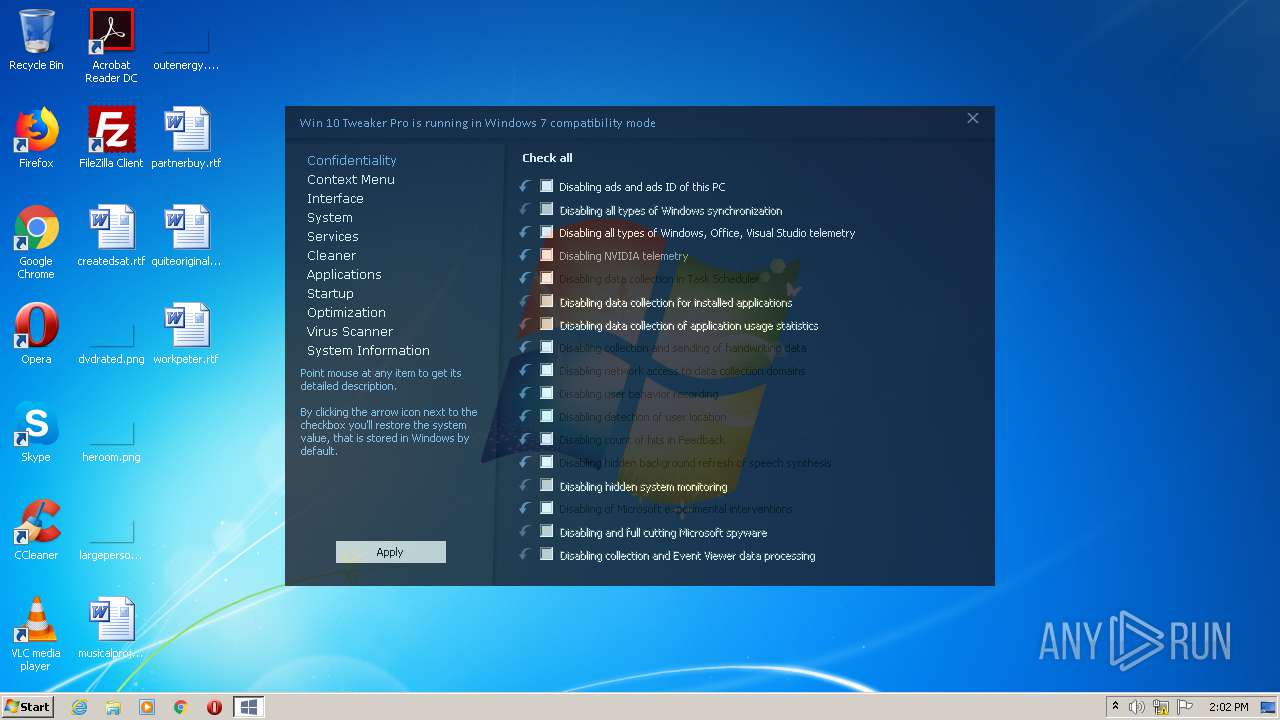
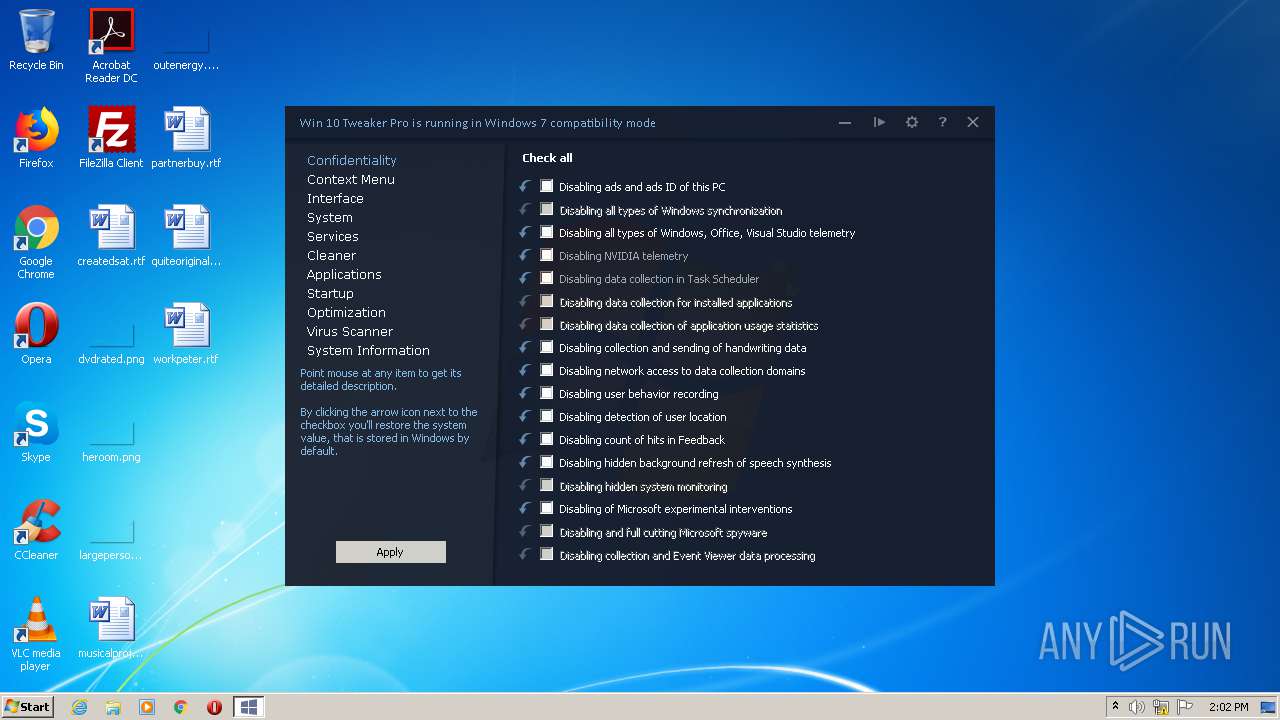
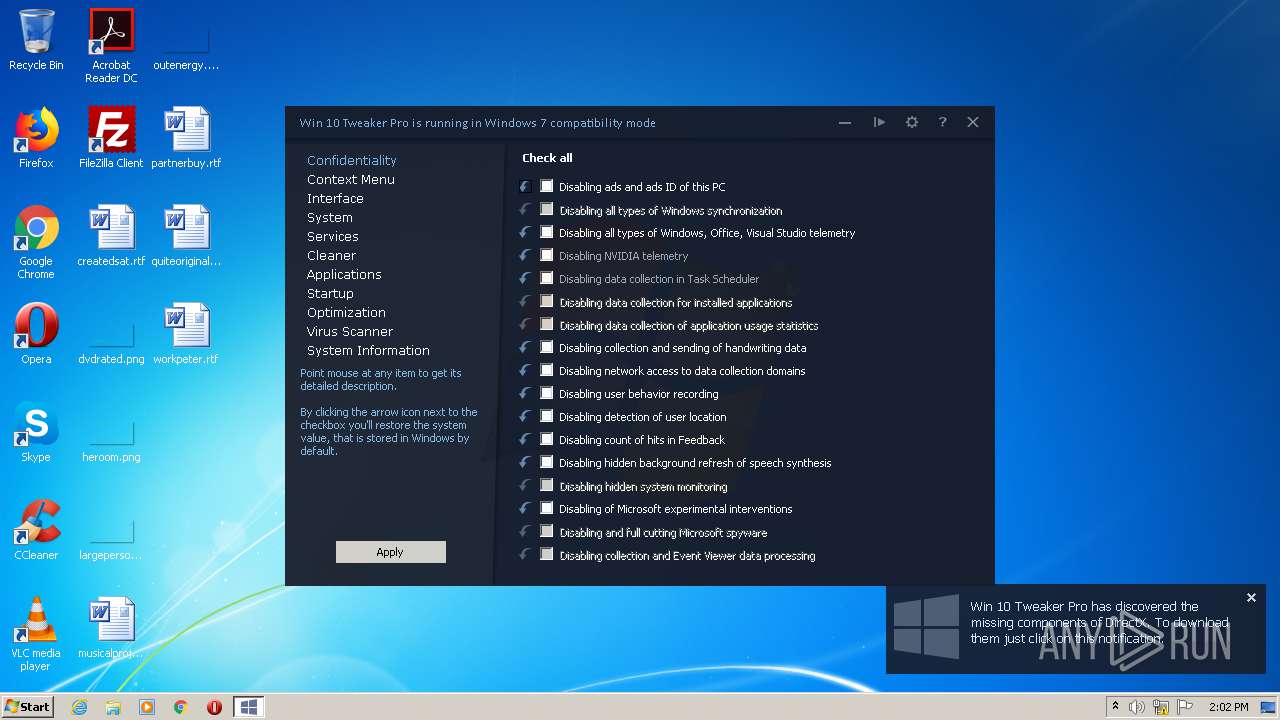
| Verdict: | Malicious activity |
| Analysis date: | October 26, 2020, 14:01:53 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 844D177609C5D9AA1E29E41847BB71D4 |
| SHA1: | 34C8BE068455ABD4C0FC44590DE169861AF0BD3C |
| SHA256: | A99488C139F27B73018DEE745647BAE8D62D225EFB28D336BB97FBC43DAAD627 |
| SSDEEP: | 98304:P6K5k+H7v7lKRtlyTuEnXeJNDGDR4EGy1K8pM6fuqYOuWO0bZZDU5O1:jqsTuKHR4EGB6M6fuqnj |
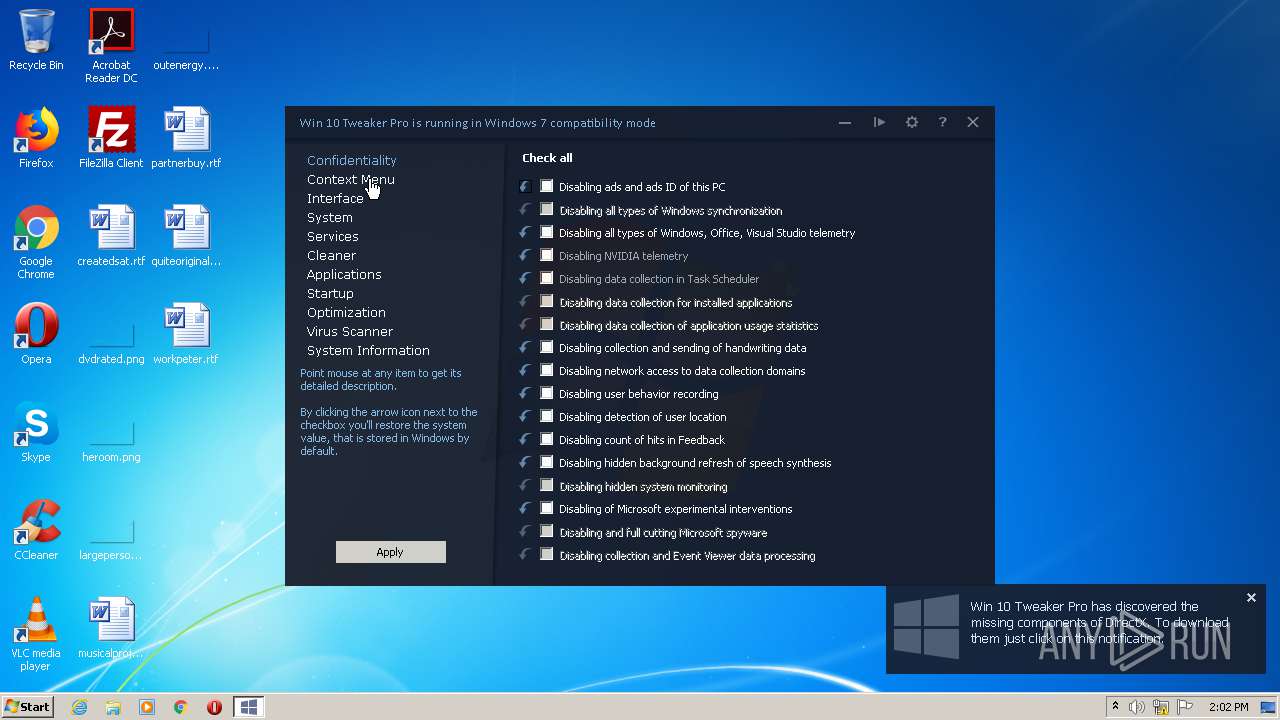
MALICIOUS
Changes the autorun value in the registry
- Win10Tweaker.exe (PID: 2264)
Application was dropped or rewritten from another process
- Win-10-Tweaker-16.1-Pro.exe (PID: 3684)
- Win-10-Tweaker-16.1-Pro.exe (PID: 940)
- Server.exe (PID: 3496)
Writes to a start menu file
- Win10Tweaker.exe (PID: 2264)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 2292)
- schtasks.exe (PID: 4004)
Uses Task Scheduler to run other applications
- cmd.exe (PID: 2592)
- cmd.exe (PID: 860)
SUSPICIOUS
Creates files in the user directory
- Win10Tweaker.exe (PID: 2264)
- powershell.exe (PID: 2560)
Executable content was dropped or overwritten
- Win10Tweaker.exe (PID: 2264)
Reads CPU info
- DoReg.exe (PID: 3488)
- Win 10 Tweaker.exe (PID: 1436)
Starts CMD.EXE for commands execution
- start.exe (PID: 2692)
- Win 10 Tweaker.exe (PID: 1436)
Reads Environment values
- Win 10 Tweaker.exe (PID: 1436)
Starts application with an unusual extension
- cmd.exe (PID: 2592)
- cmd.exe (PID: 860)
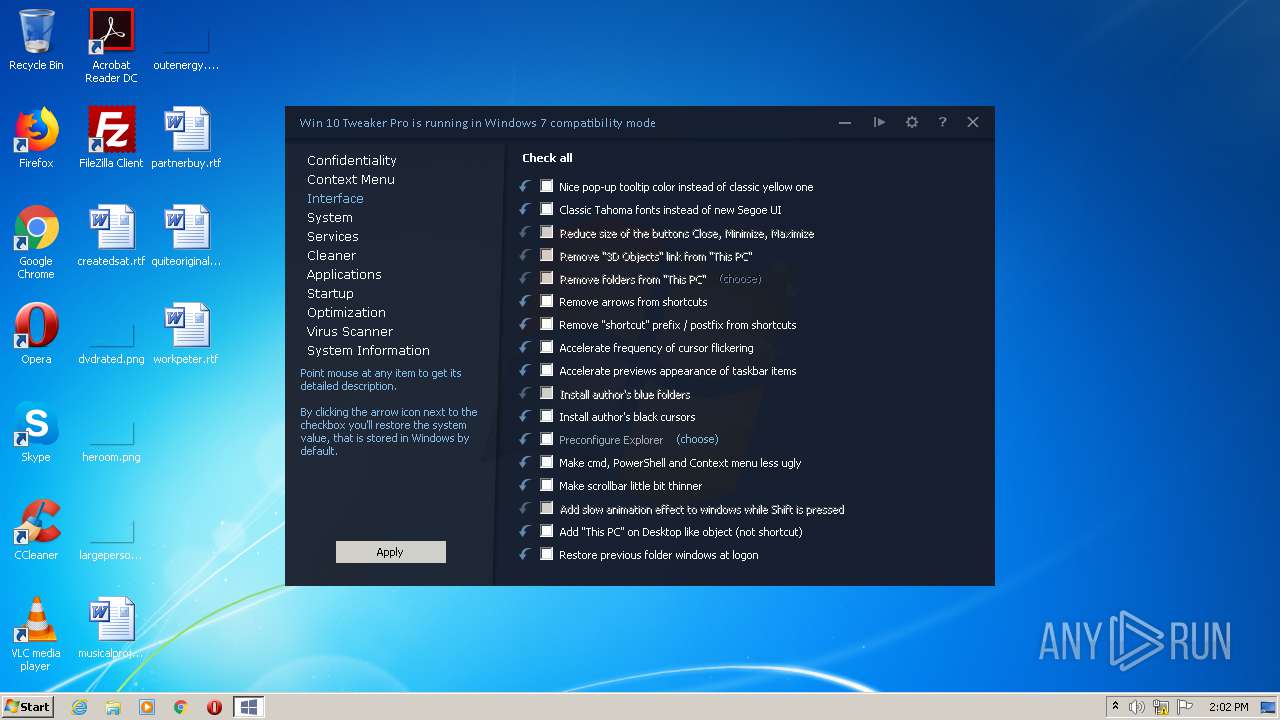
Modifies the open verb of a shell class
- Win 10 Tweaker.exe (PID: 1436)
Reads mouse settings
- Win 10 Tweaker.exe (PID: 1436)
Uses NETSH.EXE for network configuration
- cmd.exe (PID: 2216)
Executes PowerShell scripts
- Win 10 Tweaker.exe (PID: 1436)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 1636)
INFO
Reads the hosts file
- Win 10 Tweaker.exe (PID: 1436)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ 4.x (75) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (15.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (3.6) |
| .exe | | | Win32 Executable (generic) (2.5) |
| .exe | | | Win16/32 Executable Delphi generic (1.1) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2013:06:15 18:44:28+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 5.12 |
| CodeSize: | 3584 |
| InitializedDataSize: | 4578304 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1ae1 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | - |
| FileVersion: | 1.0.0.0 |
| InternalName: | start.exe |
| LegalCopyright: | - |
| OriginalFileName: | start.exe |
| ProductName: | - |
| ProductVersion: | 1.0.0.0 |
| Packager: | Turbo Studio 20 |
| PackagerVersion: | 20.3.1322 |
| VmVersion: | 20.3.1505.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 15-Jun-2013 16:44:28 |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | - |
| FileVersion: | 1.0.0.0 |
| InternalName: | start.exe |
| LegalCopyright: | - |
| OriginalFilename: | start.exe |
| ProductName: | - |
| ProductVersion: | 1.0.0.0 |
| Packager: | Turbo Studio 20 |
| PackagerVersion: | 20.3.1322 |
| VmVersion: | 20.3.1505.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 15-Jun-2013 16:44:28 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00000C26 | 0x00000E00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.14633 |
.rdata | 0x00002000 | 0x000004C0 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.21236 |
.data | 0x00003000 | 0x0000D6F0 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.72555 |
.rsrc | 0x00011000 | 0x0045CEAC | 0x0045D000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.99442 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.21173 | 716 | Latin 1 / Western European | UNKNOWN | RT_VERSION |
2 | 7.99508 | 4533067 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
4097 | 5.83536 | 165 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
Imports
kernel32.dll |
shlwapi.dll |
user32.dll |
Total processes
65
Monitored processes
19
Malicious processes
5
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 584 | "C:\Users\admin\AppData\Local\Turbo.net\Sandbox\1.0.0.0\local\stubexe\0x1A272477D7CEB787\taskkill.exe" /864A627C-C6B2-464A-AA13-25D62F282BD8 | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) | |||||||||||||||
| 860 | "C:\Users\admin\AppData\Local\Turbo.net\Sandbox\1.0.0.0\local\stubexe\0xBE6B63DE76C2CAE4\cmd.exe" /864A627C-C6B2-464A-AA13-25D62F282BD8 | C:\Windows\system32\cmd.exe | — | Win 10 Tweaker.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 940 | "C:\Users\admin\AppData\Local\Temp\Win-10-Tweaker-16.1-Pro.exe" | C:\Users\admin\AppData\Local\Temp\Win-10-Tweaker-16.1-Pro.exe | — | Win10Tweaker.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 1436 | "C:\Users\admin\AppData\Local\Turbo.net\Sandbox\1.0.0.0\local\stubexe\0x0894F1EA07390E93\Win 10 Tweaker.exe" /864A627C-C6B2-464A-AA13-25D62F282BD8 | C:\Win_10_Tweaker_16.1_Pro_beta\Win 10 Tweaker.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1636 | "C:\Users\admin\AppData\Local\Turbo.net\Sandbox\1.0.0.0\local\stubexe\0xBE6B63DE76C2CAE4\cmd.exe" /864A627C-C6B2-464A-AA13-25D62F282BD8 | C:\Windows\System32\cmd.exe | — | Win 10 Tweaker.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2216 | "C:\Users\admin\AppData\Local\Turbo.net\Sandbox\1.0.0.0\local\stubexe\0xBE6B63DE76C2CAE4\cmd.exe" /864A627C-C6B2-464A-AA13-25D62F282BD8 | C:\Windows\system32\cmd.exe | — | Win 10 Tweaker.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2264 | "C:\Users\admin\AppData\Local\Temp\Win10Tweaker.exe" | C:\Users\admin\AppData\Local\Temp\Win10Tweaker.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2292 | "C:\Users\admin\AppData\Local\Turbo.net\Sandbox\1.0.0.0\local\stubexe\0x7D3F5E4331C2272C\schtasks.exe" /864A627C-C6B2-464A-AA13-25D62F282BD8 | C:\Windows\system32\schtasks.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Manages scheduled tasks Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2560 | "C:\Users\admin\AppData\Local\Turbo.net\Sandbox\1.0.0.0\local\stubexe\0x2213A1F68D12A2DD\powershell.exe" /864A627C-C6B2-464A-AA13-25D62F282BD8 | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | Win 10 Tweaker.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2592 | "C:\Users\admin\AppData\Local\Turbo.net\Sandbox\1.0.0.0\local\stubexe\0xBE6B63DE76C2CAE4\cmd.exe" /864A627C-C6B2-464A-AA13-25D62F282BD8 | C:\Windows\system32\cmd.exe | — | Win 10 Tweaker.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
1 004
Read events
821
Write events
183
Delete events
0
Modification events
| (PID) Process: | (2264) Win10Tweaker.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | HHKLMNMDLHBBHEG |
Value: C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\Server.exe | |||
| (PID) Process: | (2264) Win10Tweaker.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2264) Win10Tweaker.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2264) Win10Tweaker.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3496) Server.exe | Key: | HKEY_CURRENT_USER |
| Operation: | write | Name: | di |
Value: ! | |||
| (PID) Process: | (3488) DoReg.exe | Key: | HKEY_CURRENT_USER\Software\Spoon\SandboxCache\098893A451530D56\roaming\modified\@HKCU@\Software\Win 10 Tweaker |
| Operation: | write | Name: | First Run Agreement |
Value: True | |||
| (PID) Process: | (3488) DoReg.exe | Key: | HKEY_CURRENT_USER\Software\Spoon\SandboxCache\098893A451530D56\roaming\modified\@HKCU@\Software\Win 10 Tweaker |
| Operation: | write | Name: | License Key |
Value: adminA180918778486694D564 | |||
| (PID) Process: | (3488) DoReg.exe | Key: | HKEY_CURRENT_USER\Software\Spoon\SandboxCache\098893A451530D56\roaming\modified\@HKCU@\Software\Win 10 Tweaker |
| Operation: | write | Name: | Hash |
Value: AYMLf+ZsIomHSJ8W2cZ/hGIr8XAFgvAVOA7M/B4/t6hULAbkZGeGIjUTLTY3VNDIOLgjJYZlVImWFgEr5rCeJ+eIGduNlbJeQL1PoogyQPOaM5g97qhTH70Fz1brC/XP8NiyQ8rfiFObFCtsIMB7yNvOlHBqxfHIaQ+9Nv4koodKRPPc2QXN1Lim9UaIoegRqdVATlGdtEiHA6GBd8zOHHgESZXLBuYL+uqt0poLuTUShMWvs7w0TmLCWB4b4T0VVzClKqQOaYQT9No15Zbuc+KQNUyU16xFV2daxZYLFSCwBjsKvVWlPJzWigmcMrQE3NMNIK5W3cOAC56Fs24Ovw== | |||
| (PID) Process: | (1436) Win 10 Tweaker.exe | Key: | HKEY_CURRENT_USER\Software\Spoon\SandboxCache\098893A451530D56\roaming\modified\@HKCU@\Software\Win 10 Tweaker |
| Operation: | write | Name: | Skin |
Value: DarkSkin | |||
| (PID) Process: | (1436) Win 10 Tweaker.exe | Key: | HKEY_CURRENT_USER\Control Panel\Keyboard |
| Operation: | write | Name: | InitialKeyboardIndicators |
Value: 2 | |||
Executable files
2
Suspicious files
2
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3684 | Win-10-Tweaker-16.1-Pro.exe | \Device\HarddiskVolume2\Users\admin\AppData\Local\Turbo.net\Sandbox\1.0.0.0\xsandbox.bin | — | |
MD5:— | SHA256:— | |||
| 3684 | Win-10-Tweaker-16.1-Pro.exe | C:\Users\admin\AppData\Local\Turbo.net\Sandbox\1.0.0.0\xsandbox.bin.__tmp__ | — | |
MD5:— | SHA256:— | |||
| 3684 | Win-10-Tweaker-16.1-Pro.exe | \Device\HarddiskVolume2\Users\admin\AppData\Local\Turbo.net\Sandbox\1.0.0.0\local\modified\@SYSDRIVE@\Win_10_Tweaker_16.1_Pro_beta\start.exe | — | |
MD5:— | SHA256:— | |||
| 3684 | Win-10-Tweaker-16.1-Pro.exe | C:\Users\admin\AppData\Local\Turbo.net\Sandbox\1.0.0.0\local\temp\@SYSDRIVE@\Win_10_Tweaker_16.1_Pro_beta\start.exe | — | |
MD5:— | SHA256:— | |||
| 3684 | Win-10-Tweaker-16.1-Pro.exe | \Device\HarddiskVolume2\Users\admin\AppData\Local\Turbo.net\Sandbox\1.0.0.0\local\meta\@SYSDRIVE@\Win_10_Tweaker_16.1_Pro_beta\start.exe.__meta__ | — | |
MD5:— | SHA256:— | |||
| 3684 | Win-10-Tweaker-16.1-Pro.exe | C:\Users\admin\AppData\Local\Turbo.net\Sandbox\1.0.0.0\local\meta\@SYSDRIVE@\Win_10_Tweaker_16.1_Pro_beta\start.exe.__meta__.__tmp__ | — | |
MD5:— | SHA256:— | |||
| 3684 | Win-10-Tweaker-16.1-Pro.exe | \Device\HarddiskVolume2\Users\admin\AppData\Local\Temp\SPOON\CACHE\0x098893A451530D56\sxs\Manifests\start.exe_0xe672098ffef06f28b8a1a216e0ae55cc.1.manifest | — | |
MD5:— | SHA256:— | |||
| 3684 | Win-10-Tweaker-16.1-Pro.exe | C:\Users\admin\AppData\Local\Temp\SPOON\CACHE\0x098893A451530D56\sxs\Manifests\start.exe_0xe672098ffef06f28b8a1a216e0ae55cc.1.manifest.__tmp__ | — | |
MD5:— | SHA256:— | |||
| 3684 | Win-10-Tweaker-16.1-Pro.exe | \Device\HarddiskVolume2\Users\admin\AppData\Local\Temp\SPOON\CACHE\0x098893A451530D56\sxs\Manifests\Win 10 Tweaker.exe_0xa8ed742119fd332084b626db13efd878.1.manifest | — | |
MD5:— | SHA256:— | |||
| 3684 | Win-10-Tweaker-16.1-Pro.exe | C:\Users\admin\AppData\Local\Temp\SPOON\CACHE\0x098893A451530D56\sxs\Manifests\Win 10 Tweaker.exe_0xa8ed742119fd332084b626db13efd878.1.manifest.__tmp__ | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report