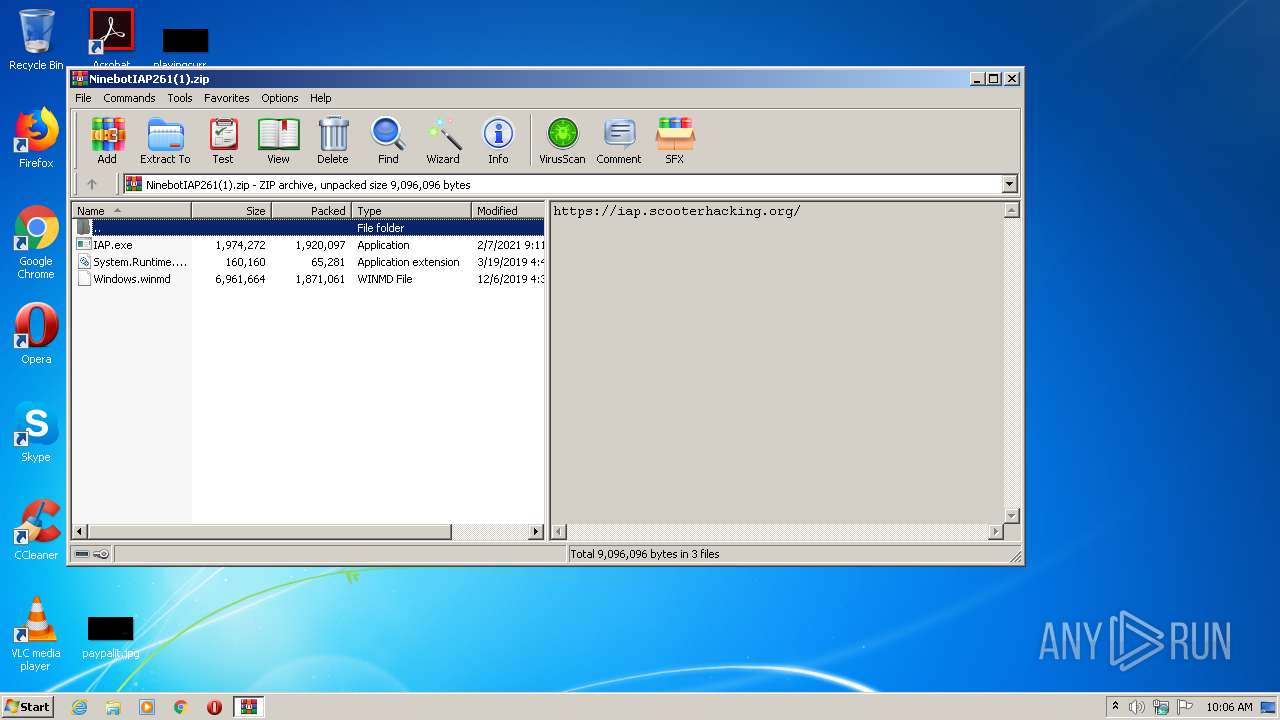
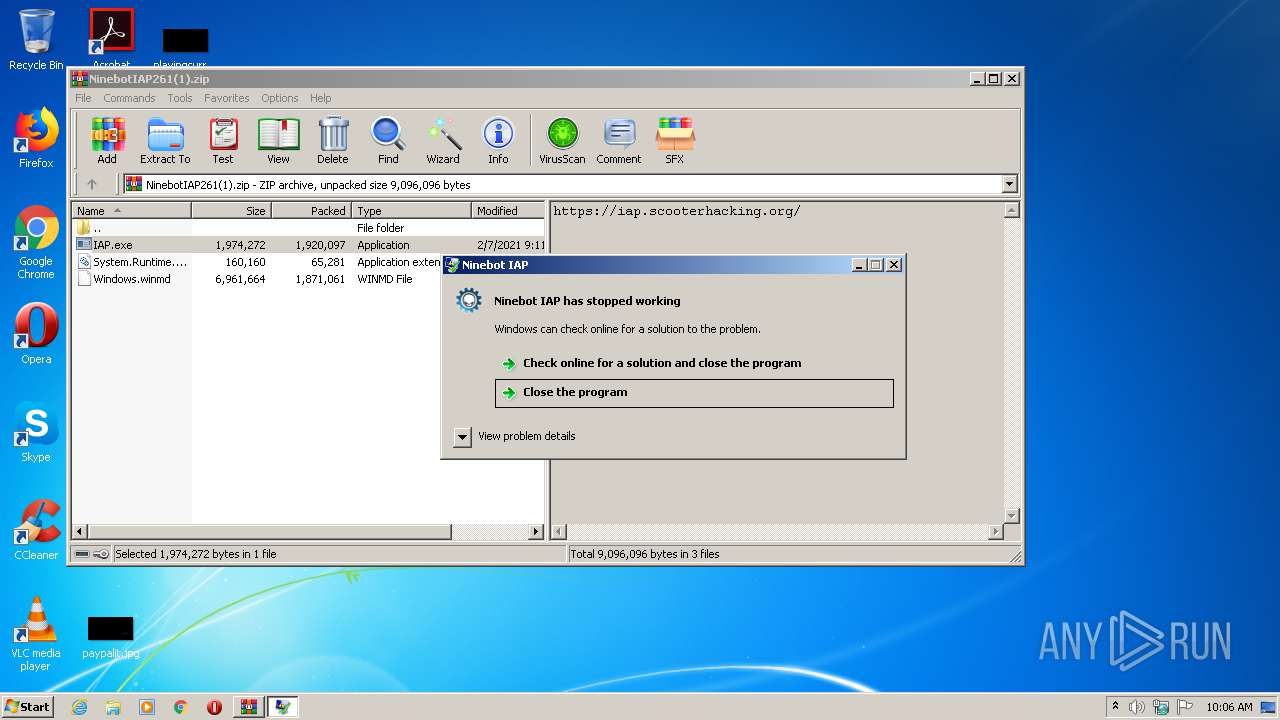
| File name: | NinebotIAP261(1).zip |
| Full analysis: | https://app.any.run/tasks/06e6fd76-f271-45c0-9860-01e49e292c3c |
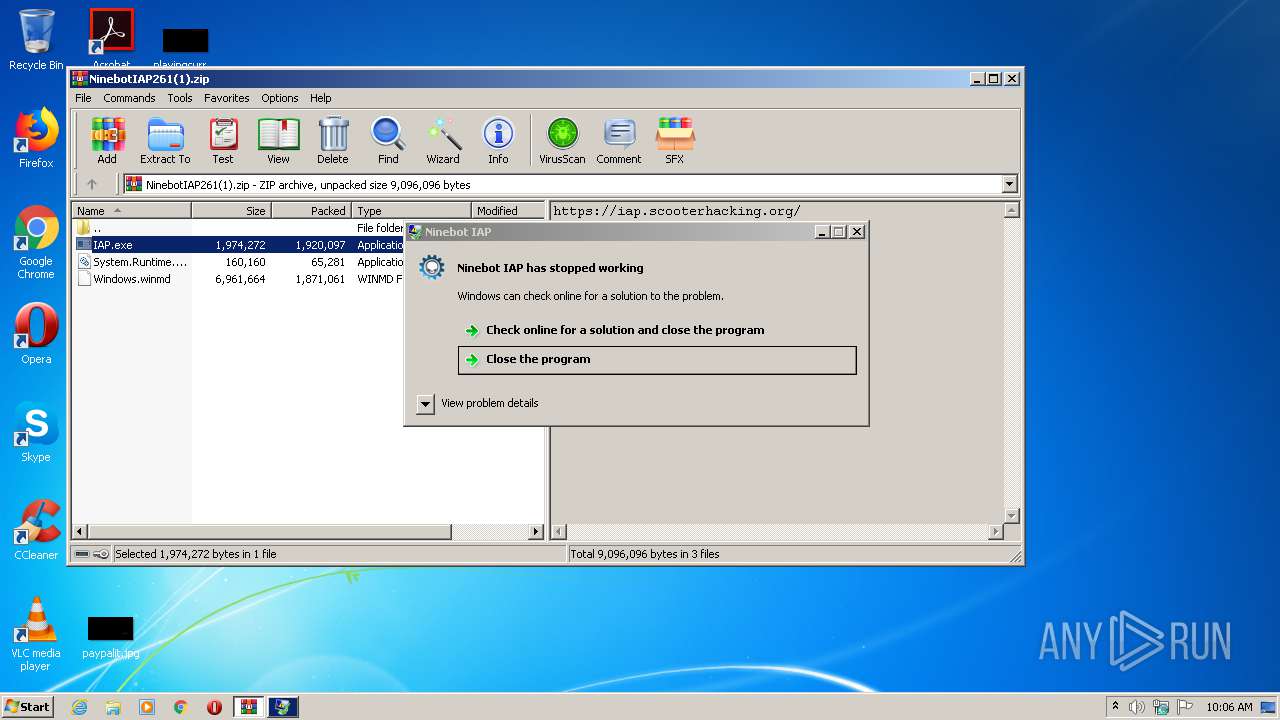
| Verdict: | Malicious activity |
| Analysis date: | June 08, 2021, 09:05:42 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 8113527B3A4D14A919B037A29C3E8BFC |
| SHA1: | 9483281E36352497C13061FFED8317186D87F340 |
| SHA256: | A993D42FEDA9A082384565DE8E5916086701F46BF77017F8F8BDDD0F4E779A35 |
| SSDEEP: | 98304:bTEXKRzWZCzee/XU7AEVbYxxpTD+UNGt4ZE3VkAS8b07dh:caUUzB/FEqpXLm4ylpbidh |
MALICIOUS
Application was dropped or rewritten from another process
- IAP.exe (PID: 2252)
- IAP.exe (PID: 1640)
- IAP.exe (PID: 2840)
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 3592)
SUSPICIOUS
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2380)
Drops a file that was compiled in debug mode
- WinRAR.exe (PID: 2380)
INFO
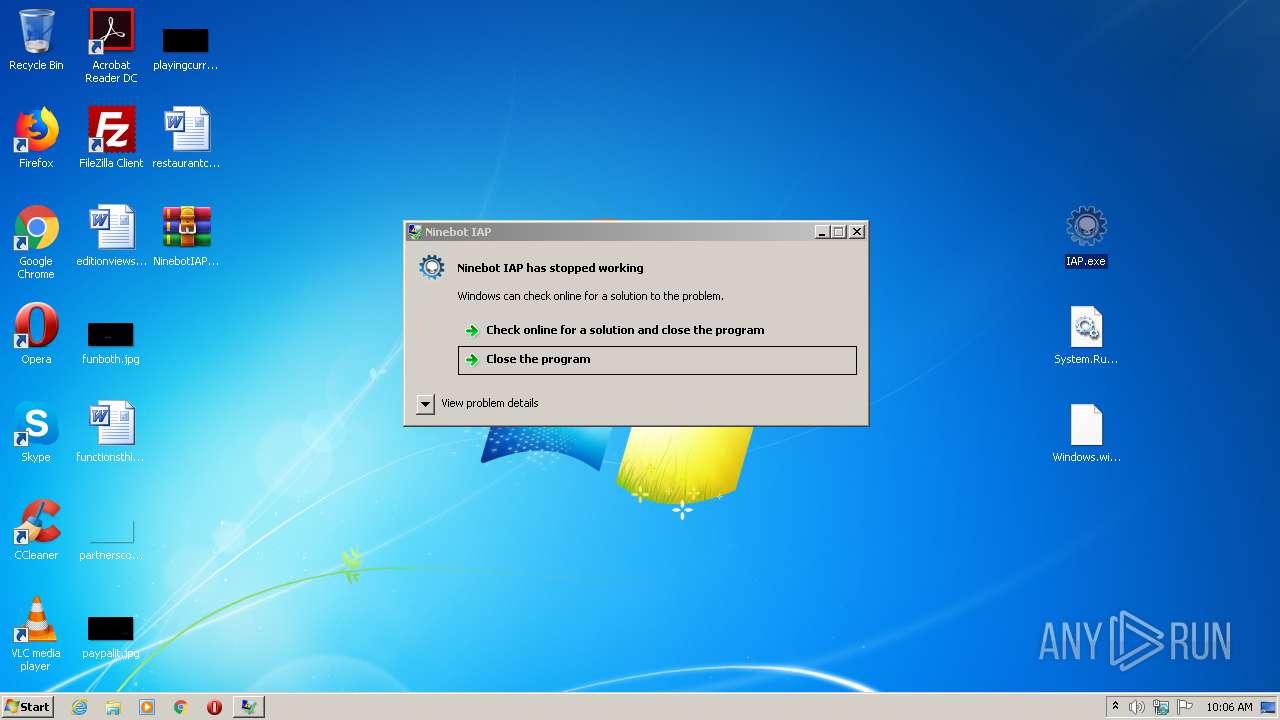
Manual execution by user
- IAP.exe (PID: 2840)
- IAP.exe (PID: 1640)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:03:19 05:46:24 |
| ZipCRC: | 0x6b597e57 |
| ZipCompressedSize: | 65281 |
| ZipUncompressedSize: | 160160 |
| ZipFileName: | System.Runtime.WindowsRuntime.dll |
Total processes
42
Monitored processes
5
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
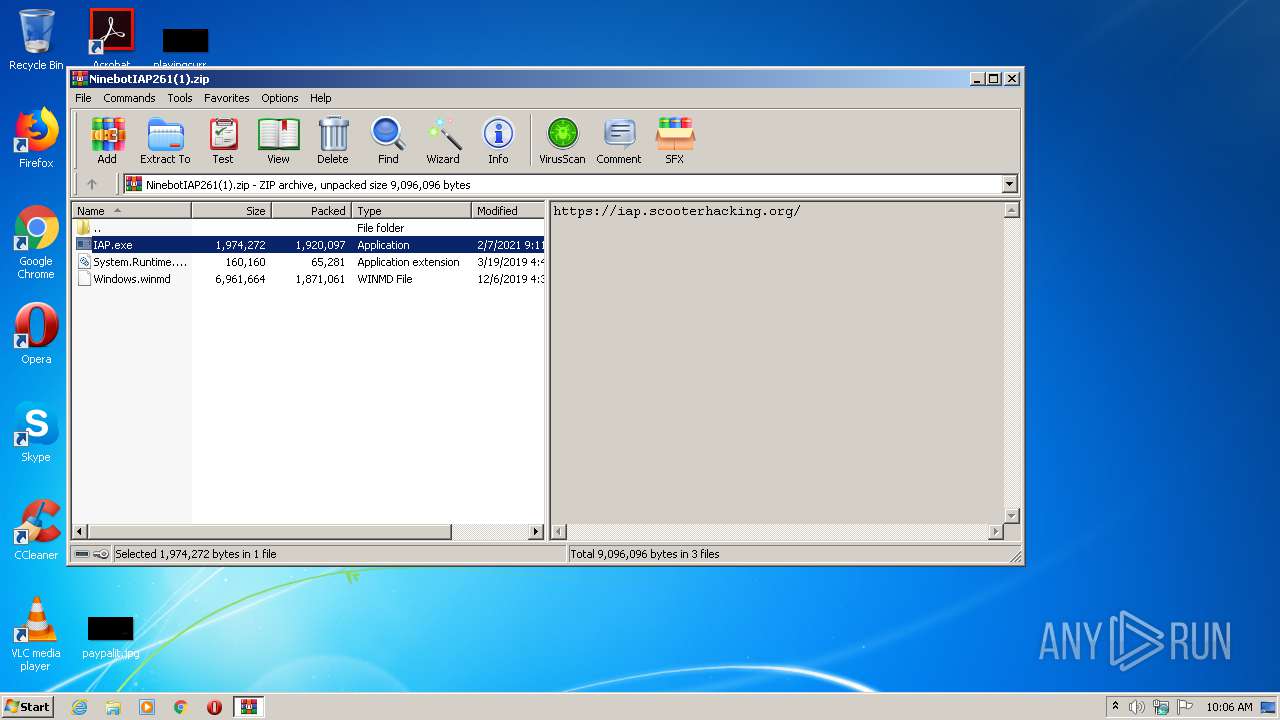
| 1640 | "C:\Users\admin\Desktop\IAP.exe" | C:\Users\admin\Desktop\IAP.exe | explorer.exe | ||||||||||||
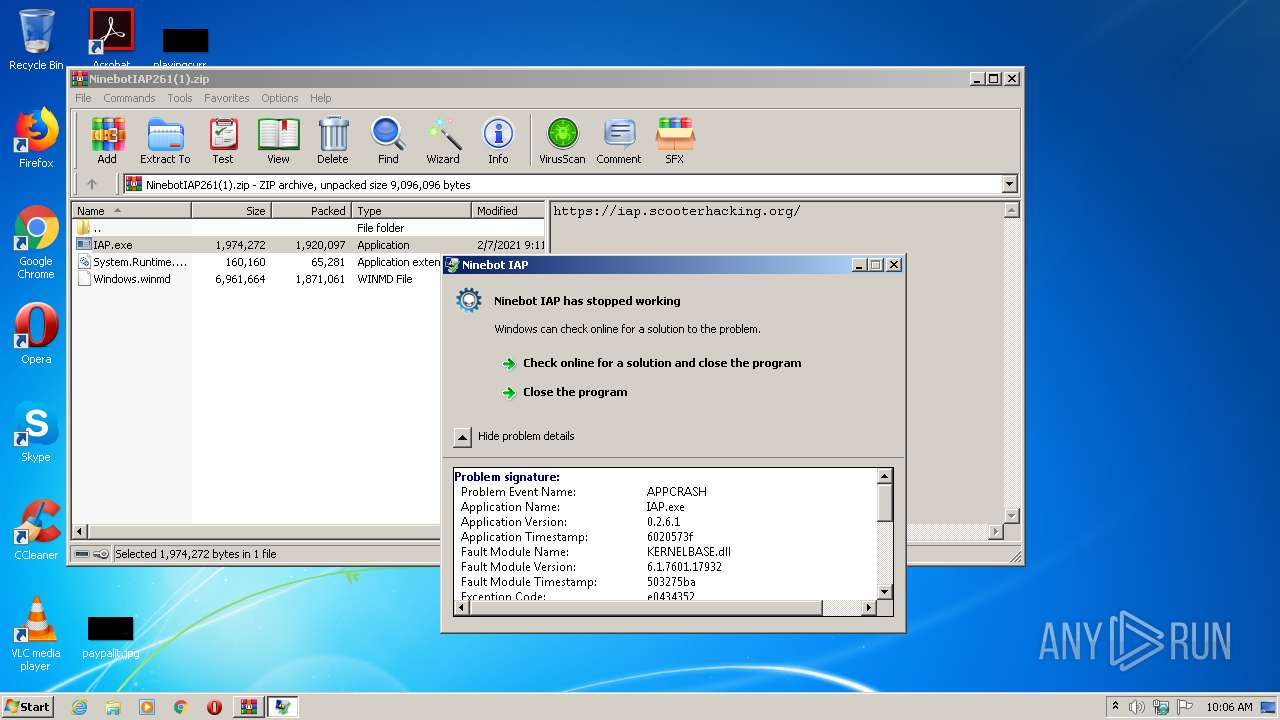
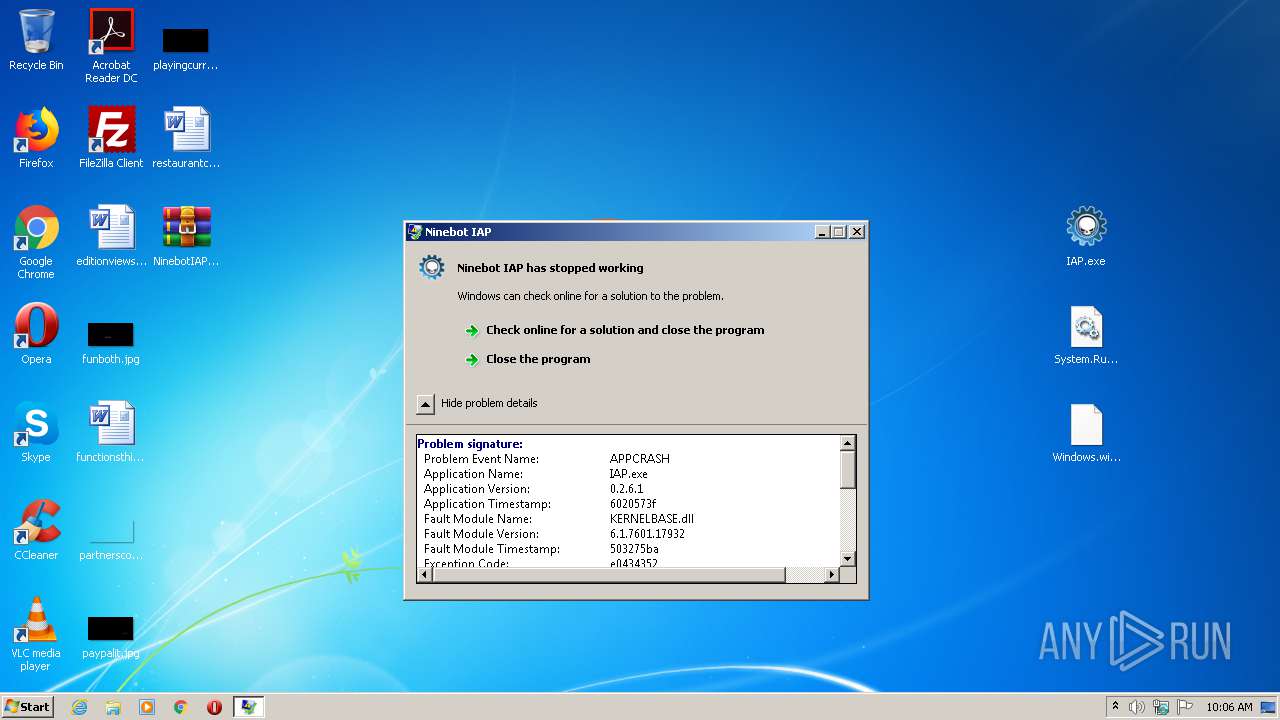
User: admin Company: ScooterHacking.org Integrity Level: MEDIUM Description: Ninebot IAP Exit code: 3762504530 Version: 0.2.6.1 Modules
| |||||||||||||||
| 2252 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa2380.49991\IAP.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa2380.49991\IAP.exe | WinRAR.exe | ||||||||||||
User: admin Company: ScooterHacking.org Integrity Level: MEDIUM Description: Ninebot IAP Exit code: 3762504530 Version: 0.2.6.1 Modules
| |||||||||||||||
| 2380 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\NinebotIAP261(1).zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2840 | "C:\Users\admin\Desktop\IAP.exe" | C:\Users\admin\Desktop\IAP.exe | explorer.exe | ||||||||||||
User: admin Company: ScooterHacking.org Integrity Level: MEDIUM Description: Ninebot IAP Exit code: 0 Version: 0.2.6.1 Modules
| |||||||||||||||
| 3592 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe4_ Global\UsGthrCtrlFltPipeMssGthrPipe4 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\System32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
465
Read events
441
Write events
24
Delete events
0
Modification events
| (PID) Process: | (2380) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2380) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2380) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13D\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2380) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\NinebotIAP261(1).zip | |||
| (PID) Process: | (2380) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2380) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2380) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2380) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2380) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2380) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
5
Suspicious files
0
Text files
0
Unknown types
0
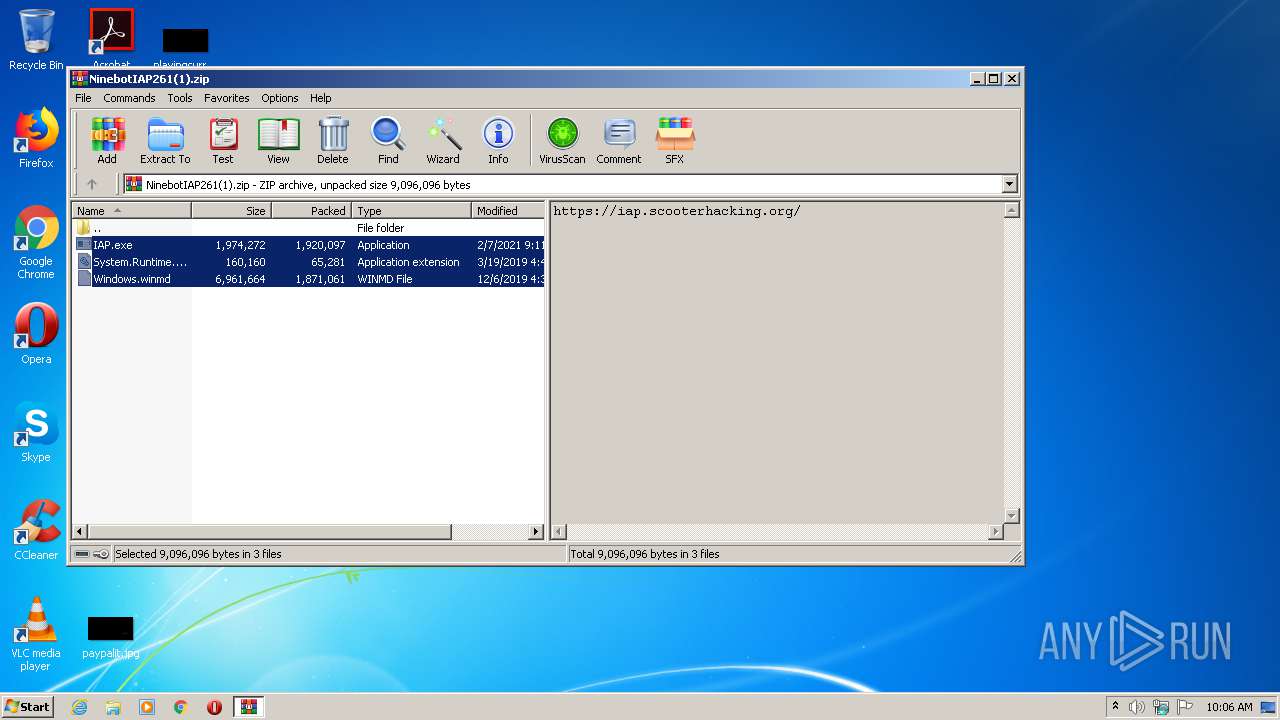
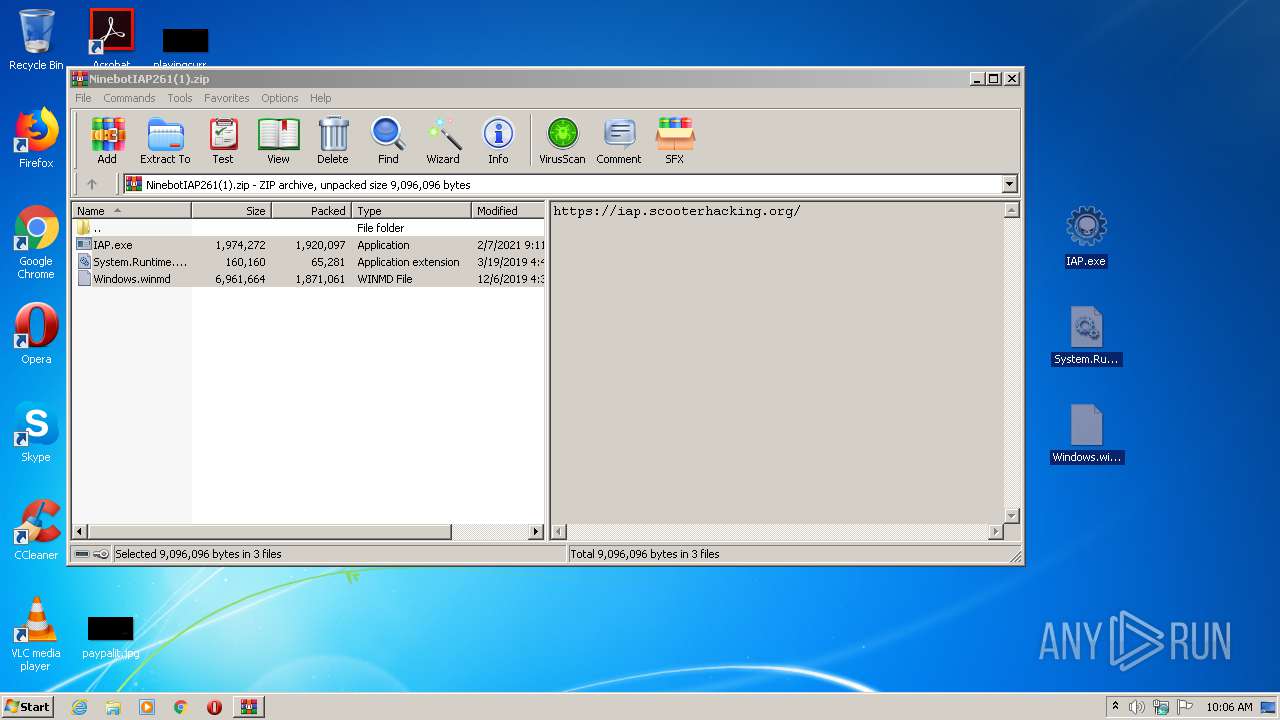
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2380 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2380.847\IAP.exe | — | |
MD5:— | SHA256:— | |||
| 2380 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2380.49991\Windows.winmd | executable | |
MD5:DCF2905F4B6D9B6D5F9C80F1342E92AA | SHA256:27E0620923D051C2C9645762092344D12CD353E9EF1850DA71D379632D30F396 | |||
| 2380 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2380.49991\System.Runtime.WindowsRuntime.dll | executable | |
MD5:0C3EB14C95AFAA3801F4694418293294 | SHA256:26E1C53DA8DE7BA5466F2AB45F43BD21E1FD099CA5B92A2902B74F760F85C540 | |||
| 2380 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2380.49991\IAP.exe | executable | |
MD5:109CEB92FB50B1951138D5A44C3DA5D5 | SHA256:C4928E33E4697295F144CDE80520C95254F9F0C495FAE866A894D7200CD60232 | |||
| 2380 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2380.847\Windows.winmd | executable | |
MD5:DCF2905F4B6D9B6D5F9C80F1342E92AA | SHA256:27E0620923D051C2C9645762092344D12CD353E9EF1850DA71D379632D30F396 | |||
| 2380 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2380.847\System.Runtime.WindowsRuntime.dll | executable | |
MD5:0C3EB14C95AFAA3801F4694418293294 | SHA256:26E1C53DA8DE7BA5466F2AB45F43BD21E1FD099CA5B92A2902B74F760F85C540 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
1
DNS requests
1
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
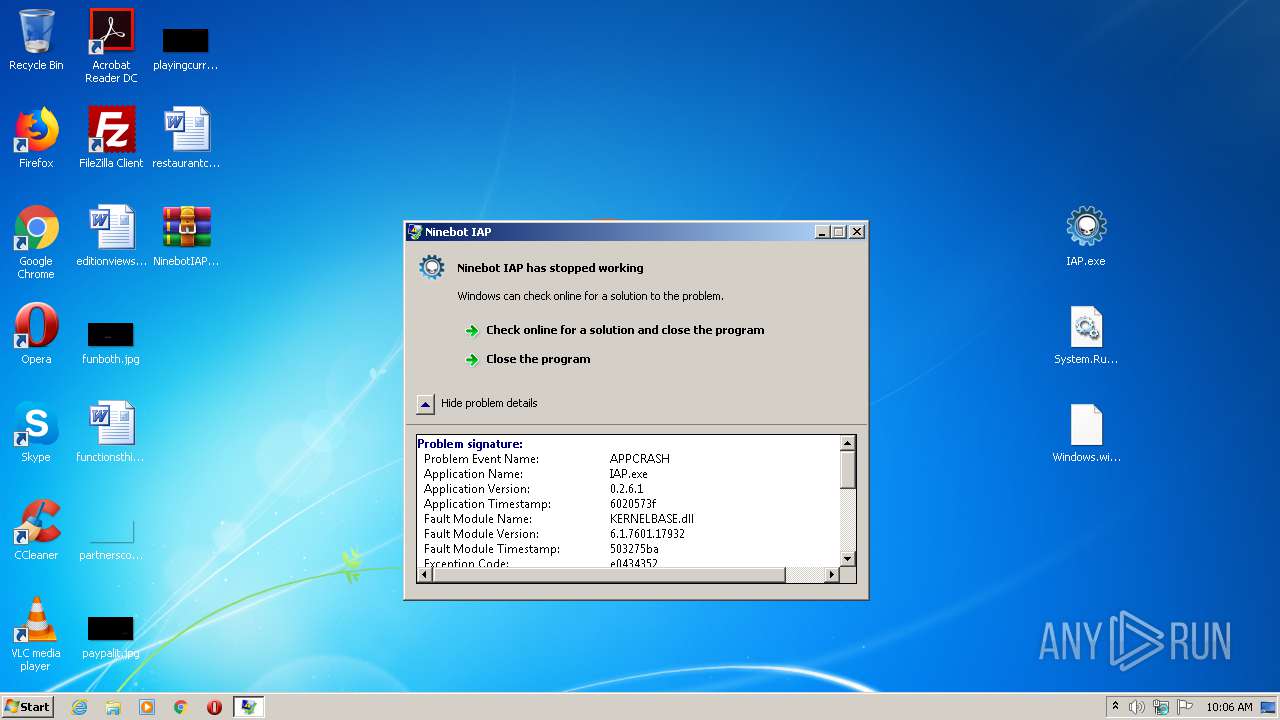
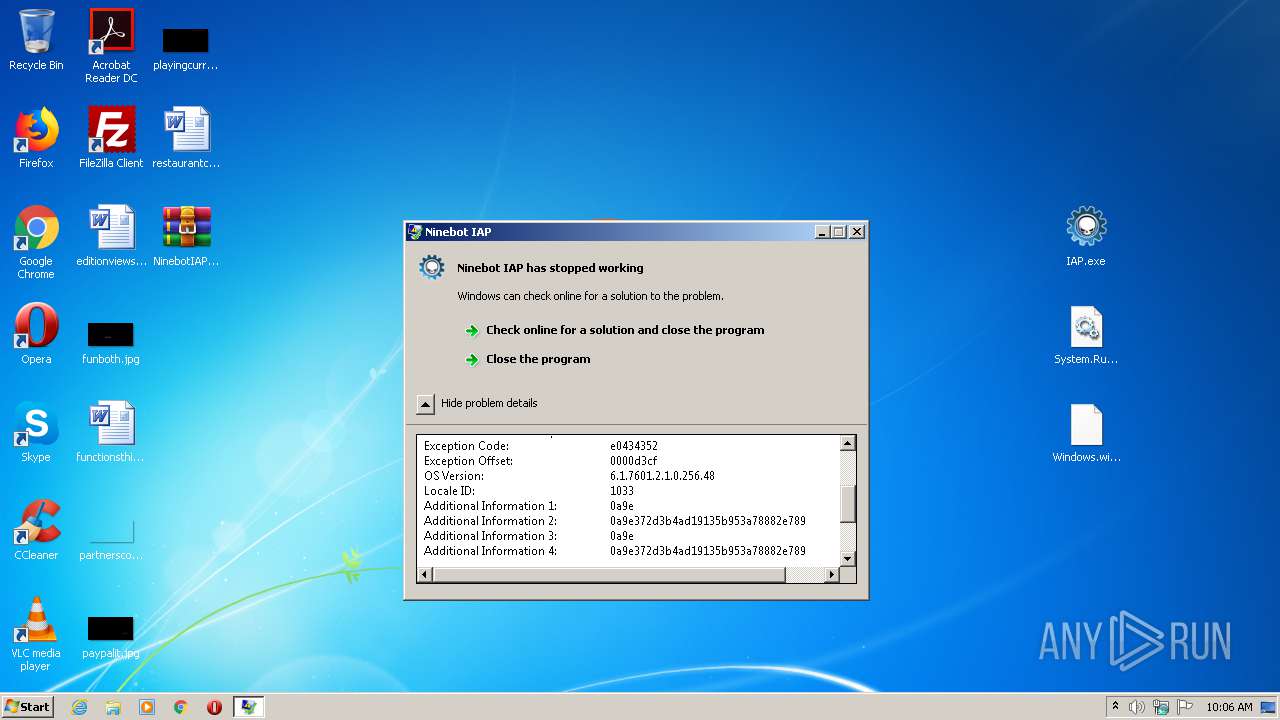
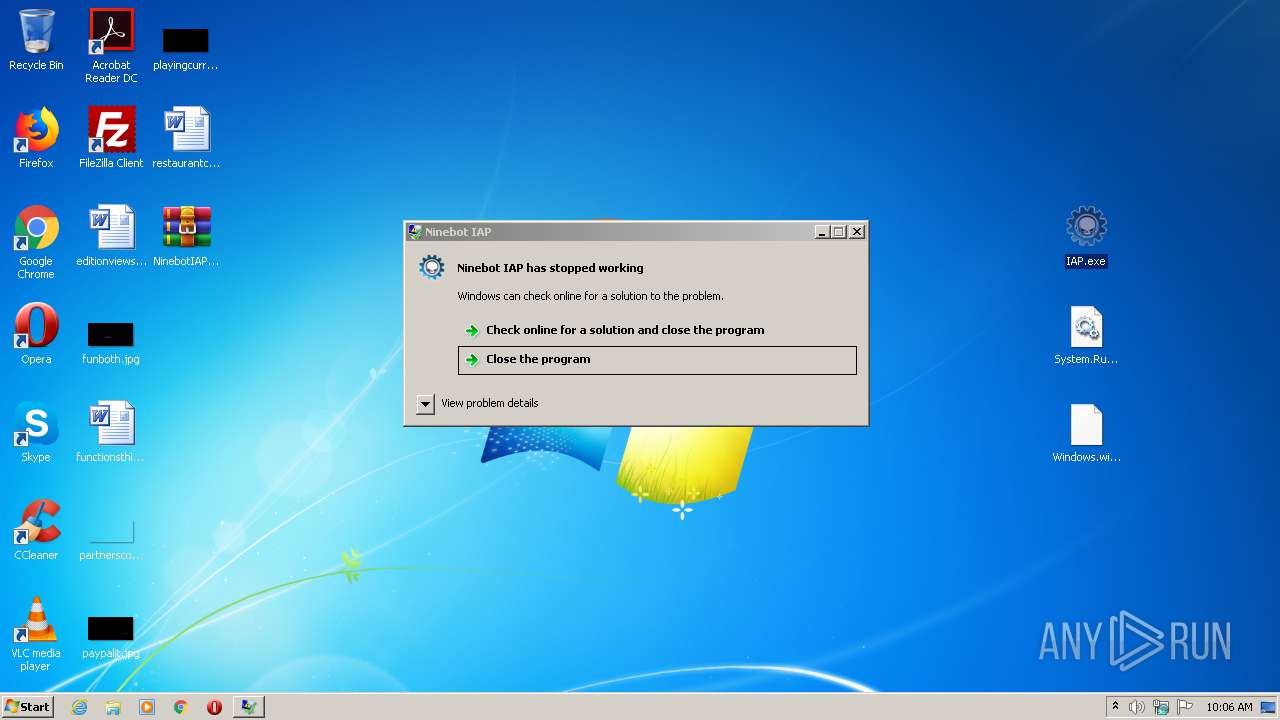
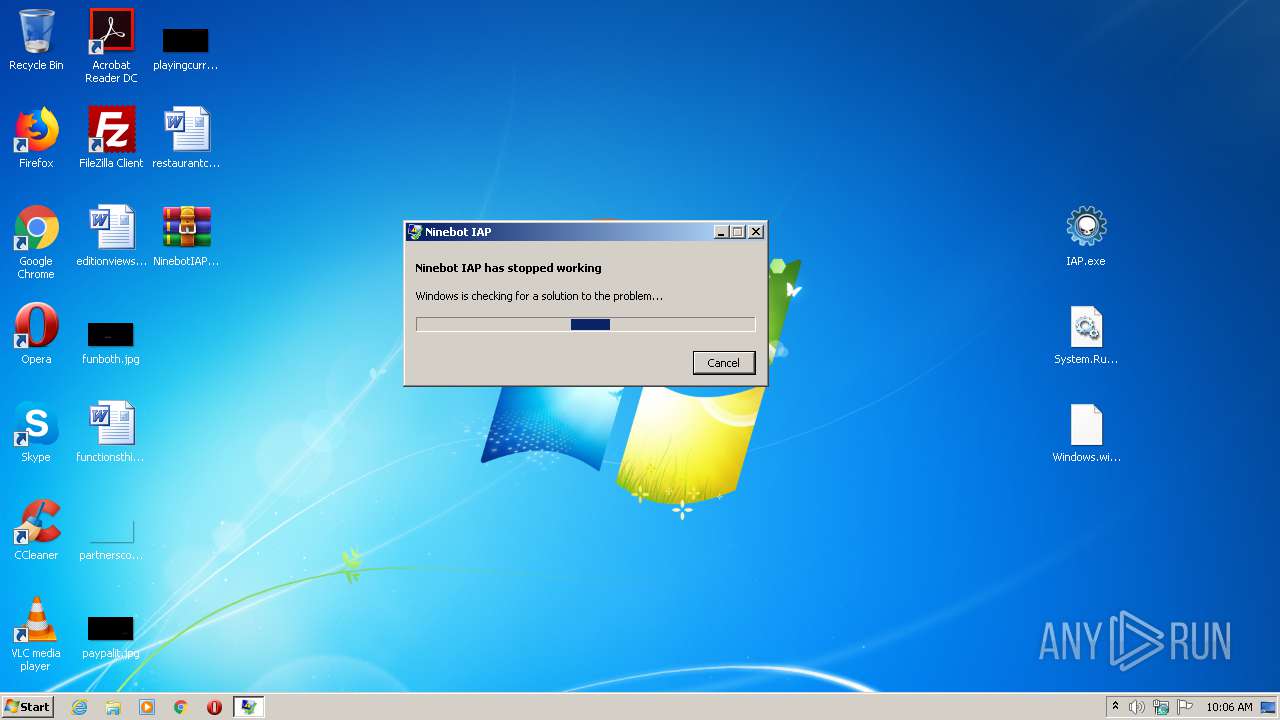
1540 | WerFault.exe | GET | — | 52.255.188.83:80 | http://watson.microsoft.com/StageOne/IAP_exe/0_2_6_1/6020573f/KERNELBASE_dll/6_1_7601_17932/503275ba/e0434352/0000d3cf.htm?LCID=1033&OS=6.1.7601.2.00010100.1.0.48.17514&SM=DELL&SPN=DELL&BV=DELL&MID=3ADE2C42-4AB9-49B7-B142-BE9AEEA69063 | US | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1540 | WerFault.exe | 52.255.188.83:80 | watson.microsoft.com | Microsoft Corporation | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
watson.microsoft.com |
| whitelisted |