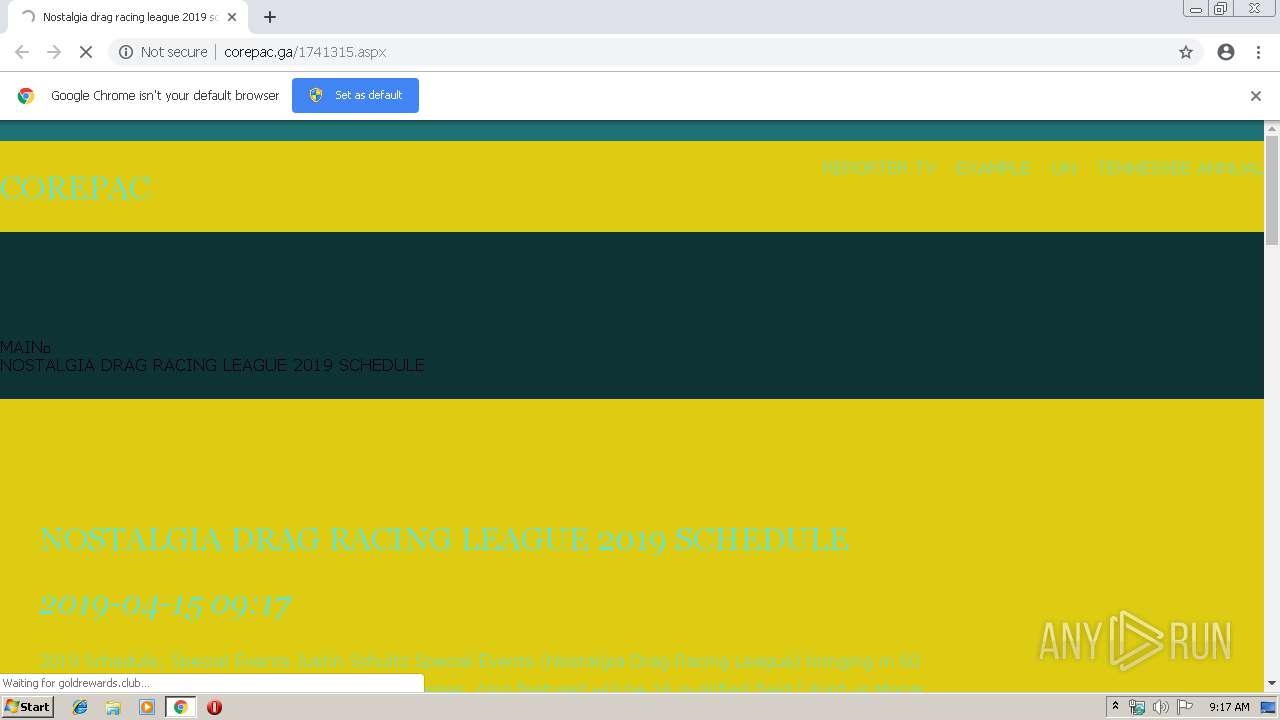
| URL: | http://corepac.ga/1741315.aspx |
| Full analysis: | https://app.any.run/tasks/919d28e8-6daa-489a-91e6-4c86d975ca06 |
| Verdict: | Malicious activity |
| Analysis date: | April 15, 2019, 08:16:53 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 7BDF6E29E596D324A7846B28FDEBB191 |
| SHA1: | E99B4C2196D63E67910759FC05E669782CC423D4 |
| SHA256: | A9889ECB4BEAC5B1E79EE741F46964878F7CDA47BBF529B53BE98AE59ADB209C |
| SSDEEP: | 3:N1KdKXxcCPueESd:CIeCPubu |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 2976)
INFO
Application launched itself
- chrome.exe (PID: 2976)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
50
Monitored processes
19
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 972 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=904,12132489747349107783,13652545710658974701,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=3131710883701112424 --mojo-platform-channel-handle=1508 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1856 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=904,12132489747349107783,13652545710658974701,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=7493822907597921790 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7493822907597921790 --renderer-client-id=8 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2832 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1944 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=904,12132489747349107783,13652545710658974701,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=9292681575738265198 --mojo-platform-channel-handle=3472 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2324 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=904,12132489747349107783,13652545710658974701,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=3424162796390795020 --mojo-platform-channel-handle=3460 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2592 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=904,12132489747349107783,13652545710658974701,131072 --enable-features=PasswordImport --service-pipe-token=16470071749764327395 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16470071749764327395 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2032 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2608 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=904,12132489747349107783,13652545710658974701,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=886584865865787579 --mojo-platform-channel-handle=3528 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2728 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2980 --on-initialized-event-handle=308 --parent-handle=312 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2736 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=904,12132489747349107783,13652545710658974701,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=16823711886434192120 --mojo-platform-channel-handle=2556 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2808 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=904,12132489747349107783,13652545710658974701,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=10158435518583427791 --mojo-platform-channel-handle=3532 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2884 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=904,12132489747349107783,13652545710658974701,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=7903127006753044226 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7903127006753044226 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3036 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
Total events
585
Read events
483
Write events
97
Delete events
5
Modification events
| (PID) Process: | (2728) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2976-13199789829519250 |
Value: 259 | |||
| (PID) Process: | (2976) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2976) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2976) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2976) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2976) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2976) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2976) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2976) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3488-13197474229333984 |
Value: 0 | |||
| (PID) Process: | (2976) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
22
Text files
145
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2976 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 2976 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 2976 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2976 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 2976 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
| 2976 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\161cdf8c-2c06-4f8e-85c5-16f4b2d60f1a.tmp | — | |
MD5:— | SHA256:— | |||
| 2976 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000018.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2976 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 2976 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 2976 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
45
TCP/UDP connections
26
DNS requests
17
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
972 | chrome.exe | GET | 200 | 104.31.74.172:80 | http://corepac.ga/1741315.aspx | US | html | 3.21 Kb | suspicious |
972 | chrome.exe | GET | 200 | 104.31.74.172:80 | http://corepac.ga/style.css | US | text | 3.76 Kb | suspicious |
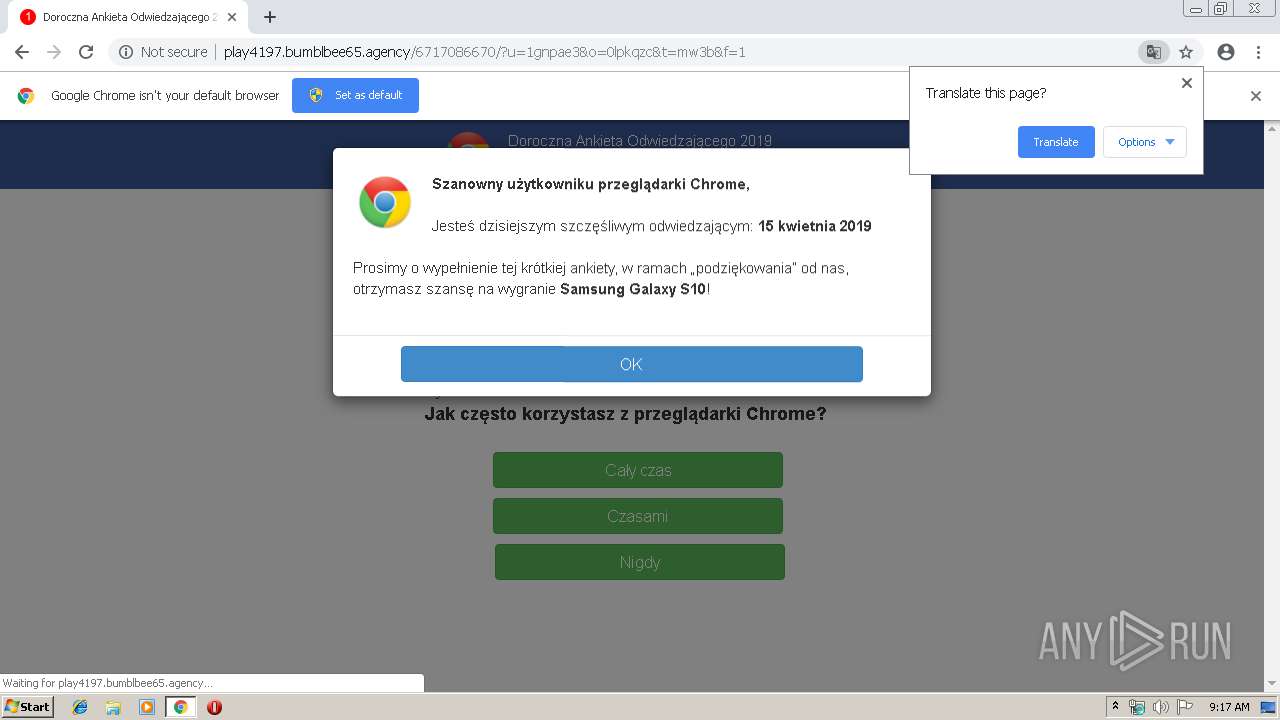
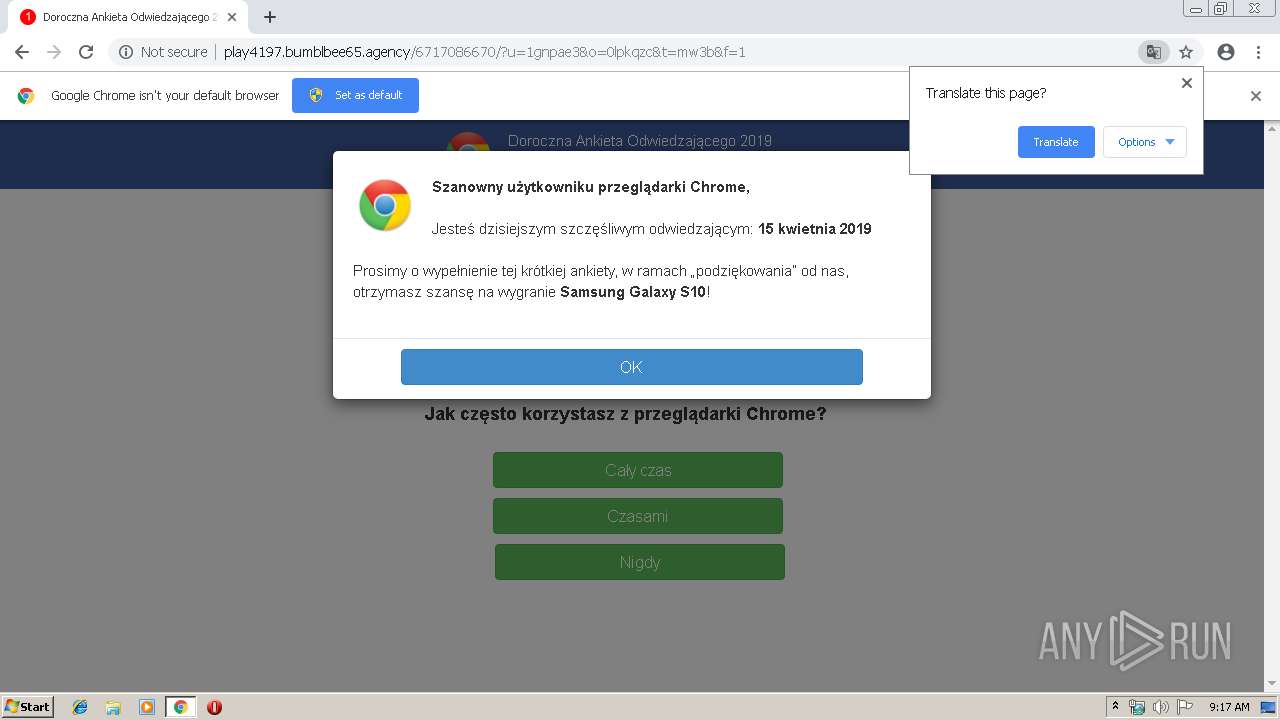
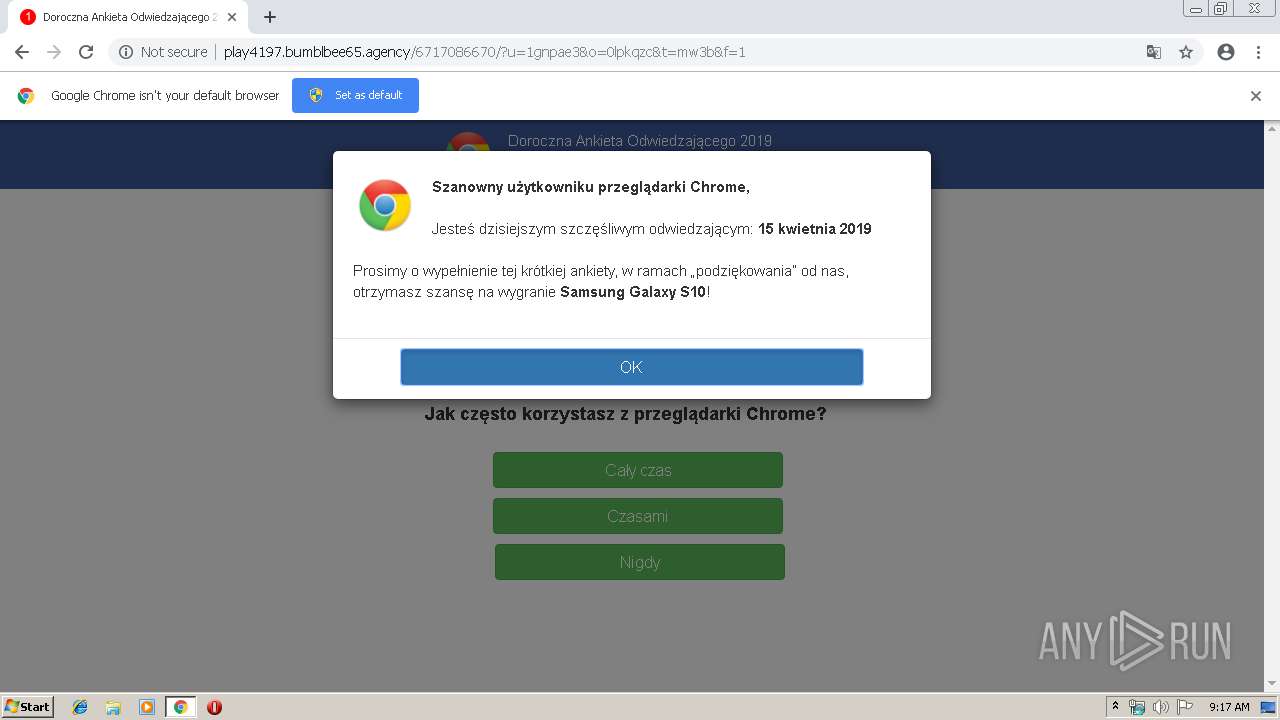
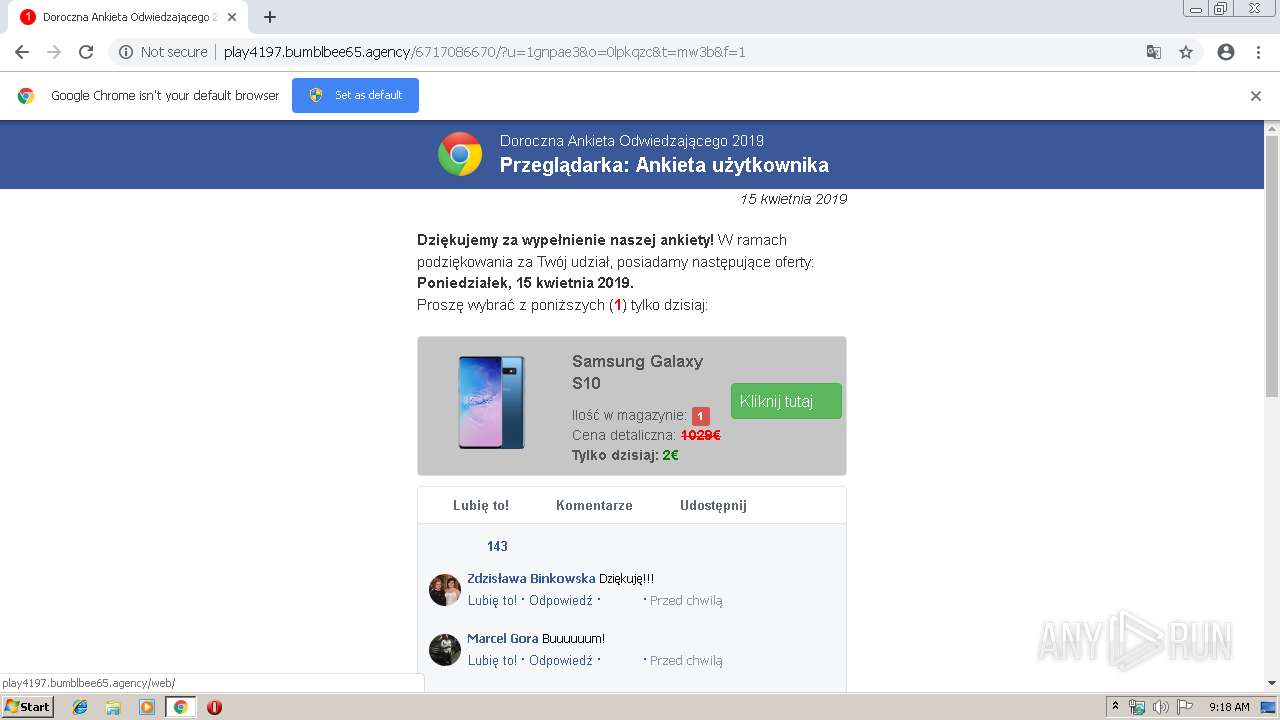
972 | chrome.exe | GET | 302 | 104.18.37.57:80 | http://goldrewards.club/?u=1gnpae3&o=0lpkqzc&t=mw3b | US | html | 205 b | malicious |
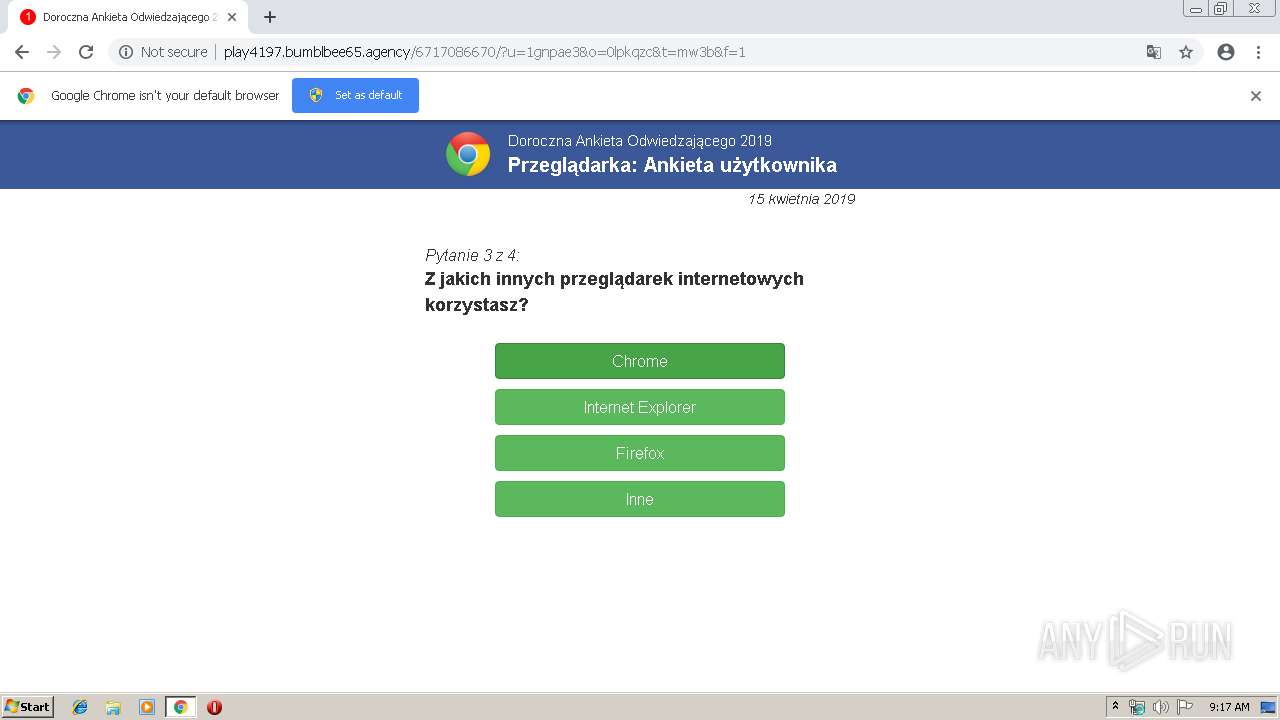
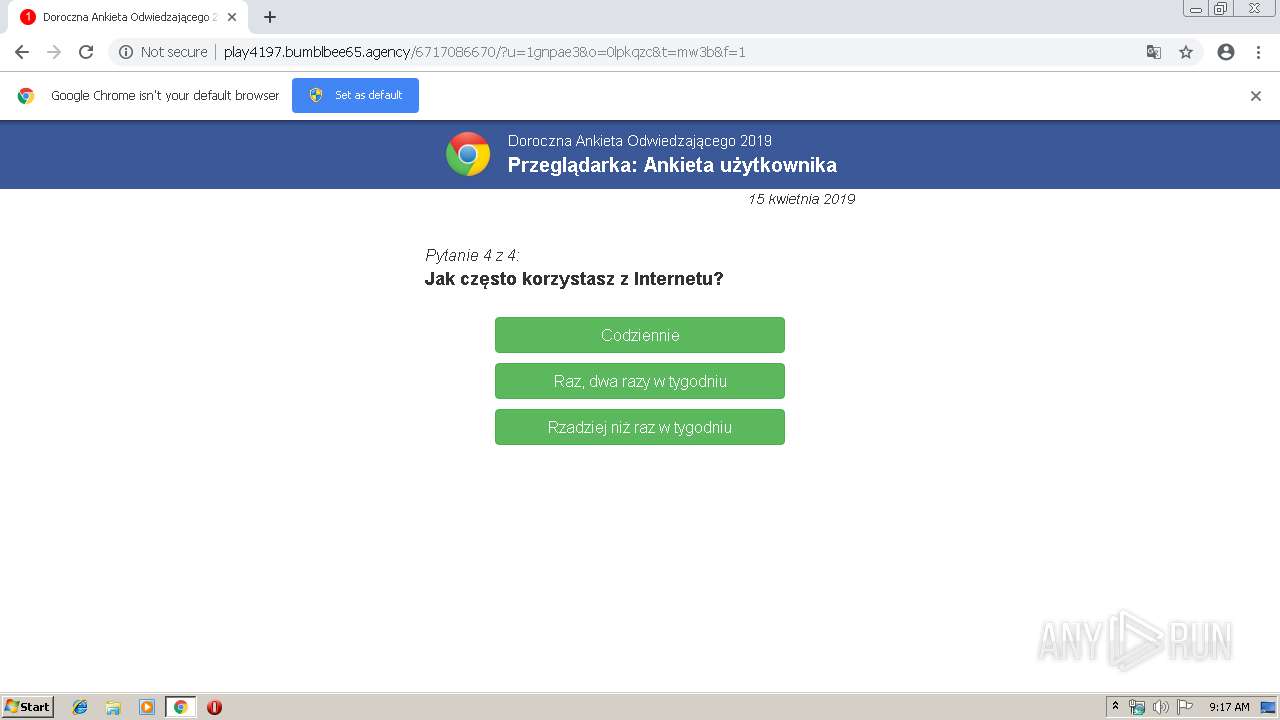
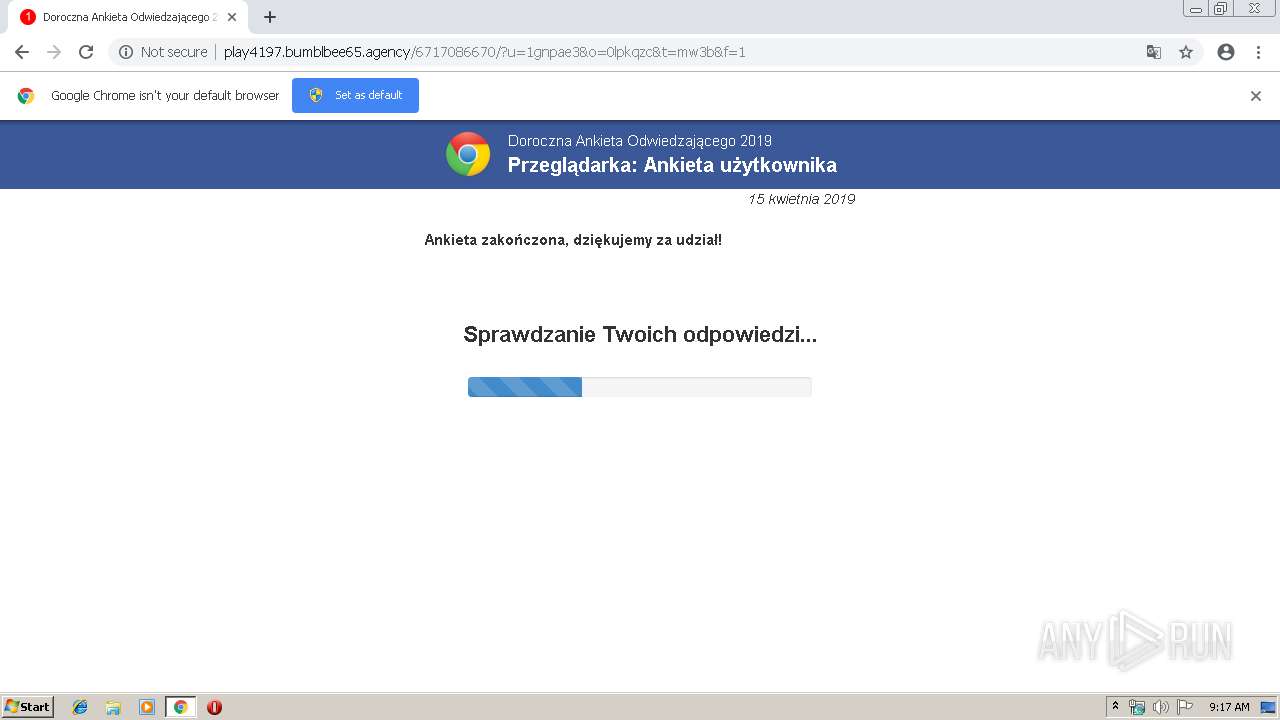
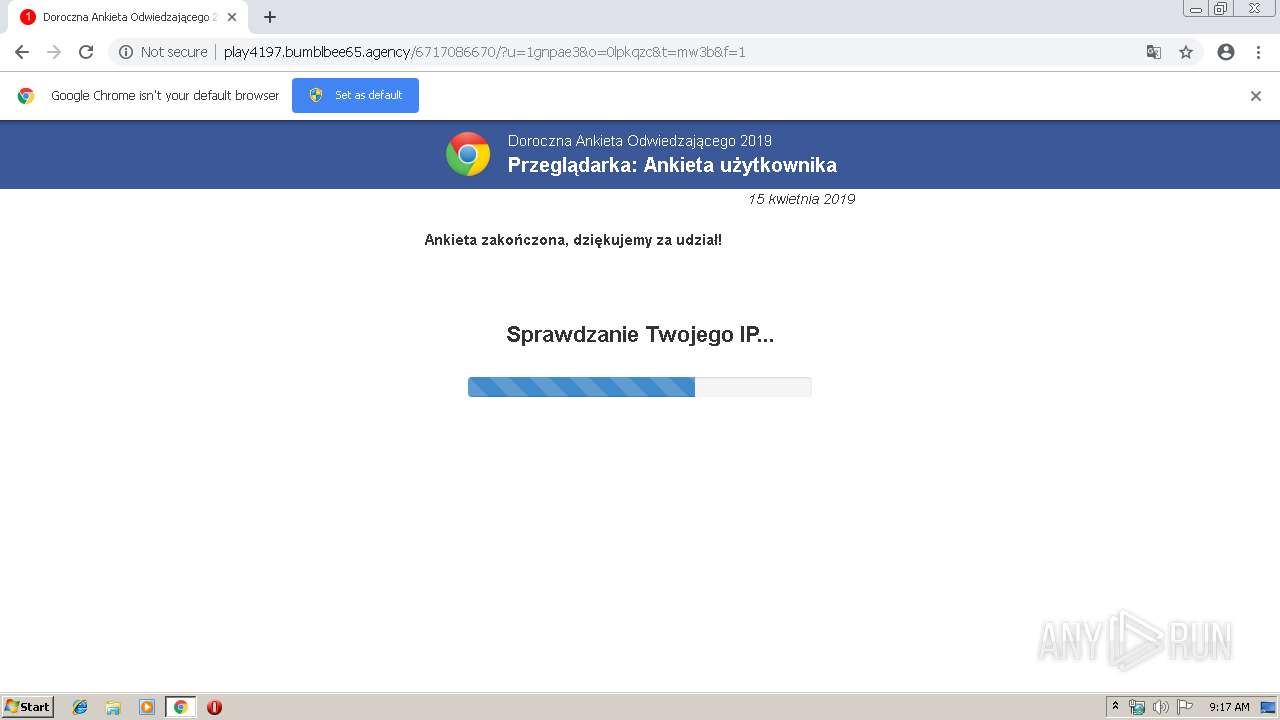
972 | chrome.exe | GET | 200 | 79.110.23.121:80 | http://play4197.bumblbee65.agency/6717086670/?u=1gnpae3&o=0lpkqzc&t=mw3b&f=1 | RO | html | 16.9 Kb | unknown |
972 | chrome.exe | GET | 200 | 104.18.54.68:80 | http://justbusiness.host/?LgTGHf&keyword=Nostalgia%20drag%20racing%20league%202019%20schedule%20%7C%20corepac&se_referrer=& | US | text | 137 b | shared |
972 | chrome.exe | GET | 200 | 79.110.23.121:80 | http://play4197.bumblbee65.agency/media/mainstream/pl/wap/mobsurvey/pl-en.js | RO | text | 5.03 Kb | unknown |
972 | chrome.exe | GET | 200 | 79.110.23.121:80 | http://play4197.bumblbee65.agency/media/mainstream/pl/wap/mobsurvey/font-awesome.css | RO | text | 17.2 Kb | unknown |
972 | chrome.exe | GET | 200 | 79.110.23.121:80 | http://play4197.bumblbee65.agency/media/mainstream/pl/wap/mobsurvey/main.css | RO | text | 10.0 Kb | unknown |
972 | chrome.exe | GET | 200 | 79.110.23.121:80 | http://play4197.bumblbee65.agency/media/mainstream/pl/wap/mobsurvey/modernizr-2.6.2-respond-1.1.0.min.js | RO | html | 17.8 Kb | unknown |
972 | chrome.exe | GET | 200 | 79.110.23.121:80 | http://play4197.bumblbee65.agency/util/utils-ms.js | RO | text | 5.03 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
972 | chrome.exe | 172.217.16.141:443 | accounts.google.com | Google Inc. | US | suspicious |
972 | chrome.exe | 104.31.74.172:80 | corepac.ga | Cloudflare Inc | US | shared |
972 | chrome.exe | 172.217.22.35:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
972 | chrome.exe | 104.19.195.151:443 | cdnjs.cloudflare.com | Cloudflare Inc | US | shared |
— | — | 104.18.54.68:80 | justbusiness.host | Cloudflare Inc | US | shared |
— | — | 104.18.37.57:80 | goldrewards.club | Cloudflare Inc | US | shared |
972 | chrome.exe | 104.18.37.57:80 | goldrewards.club | Cloudflare Inc | US | shared |
972 | chrome.exe | 79.110.23.121:80 | play4197.bumblbee65.agency | LLHost Inc | RO | unknown |
972 | chrome.exe | 46.161.31.141:80 | tdsjsext1.com | — | UA | suspicious |
972 | chrome.exe | 172.217.23.170:443 | translate.googleapis.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
corepac.ga |
| suspicious |
accounts.google.com |
| shared |
clientservices.googleapis.com |
| whitelisted |
cdnjs.cloudflare.com |
| whitelisted |
justbusiness.host |
| unknown |
goldrewards.club |
| malicious |
play4197.bumblbee65.agency |
| unknown |
tdsjsext1.com |
| whitelisted |
translate.googleapis.com |
| whitelisted |
clients2.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1048 | svchost.exe | Potentially Bad Traffic | ET INFO DNS Query for Suspicious .ga Domain |
972 | chrome.exe | Generic Protocol Command Decode | SURICATA STREAM excessive retransmissions |
972 | chrome.exe | Generic Protocol Command Decode | SURICATA STREAM excessive retransmissions |
972 | chrome.exe | Generic Protocol Command Decode | SURICATA STREAM reassembly overlap with different data |
1 ETPRO signatures available at the full report