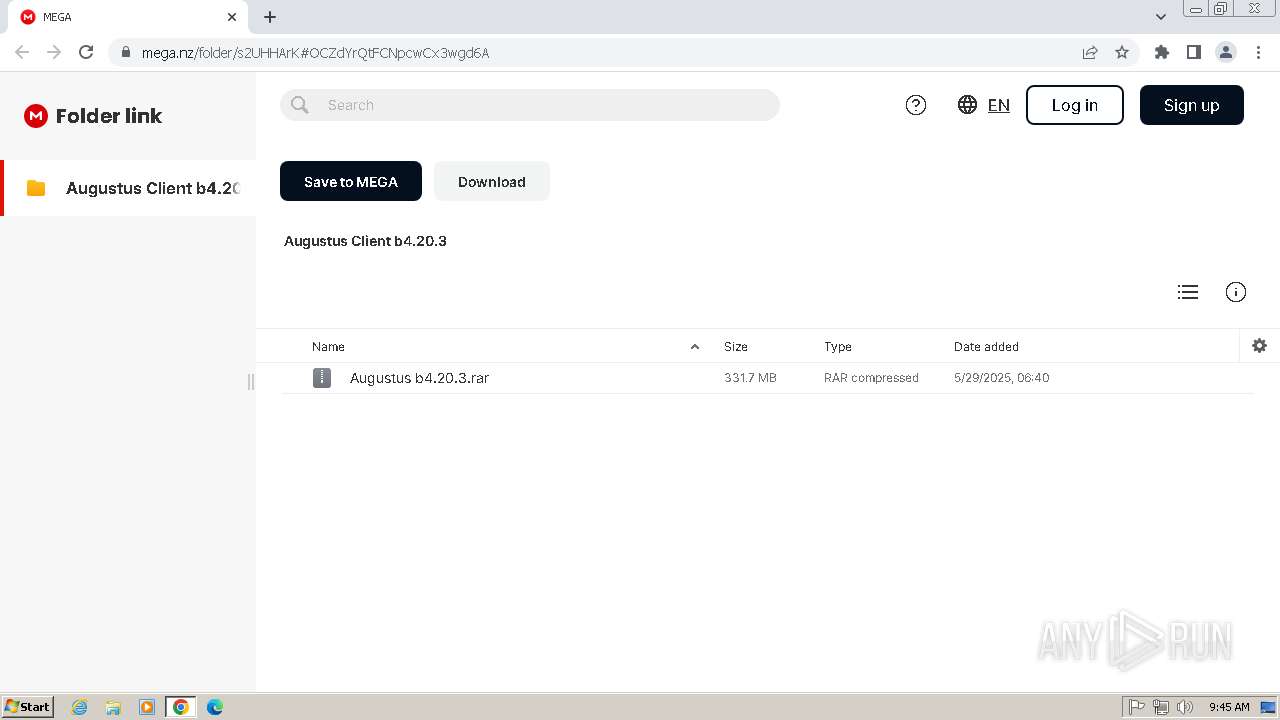
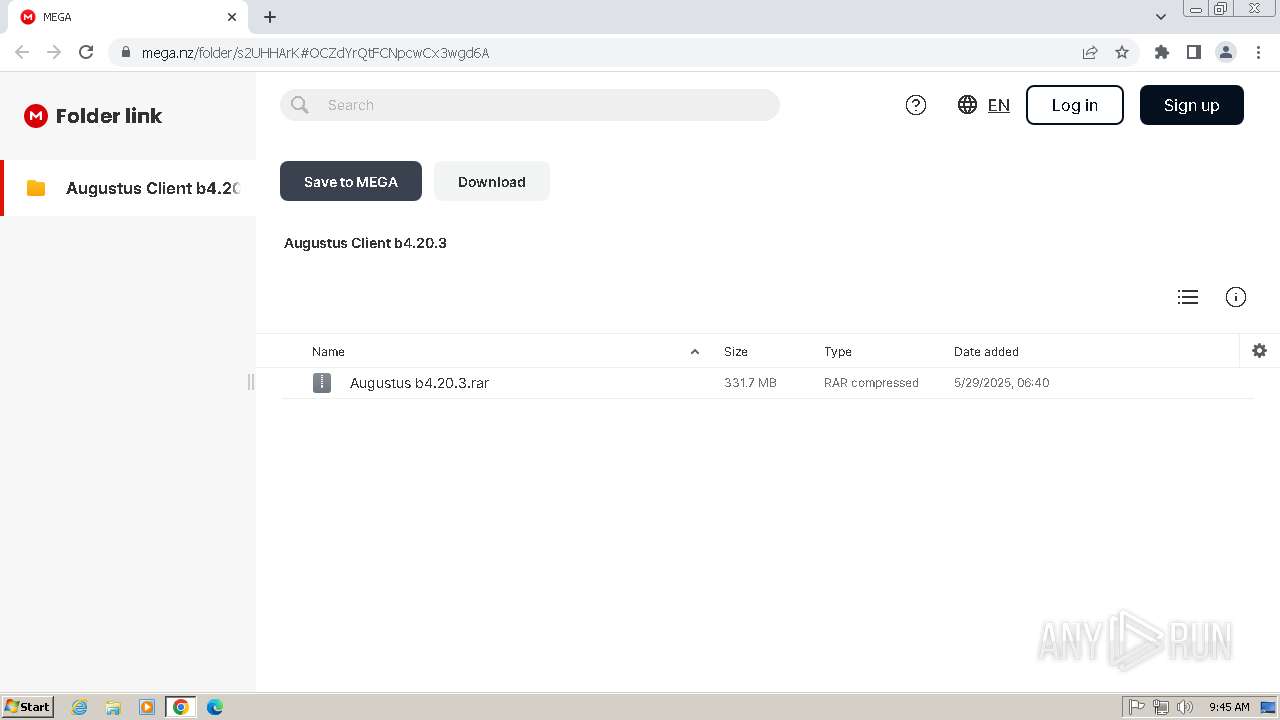
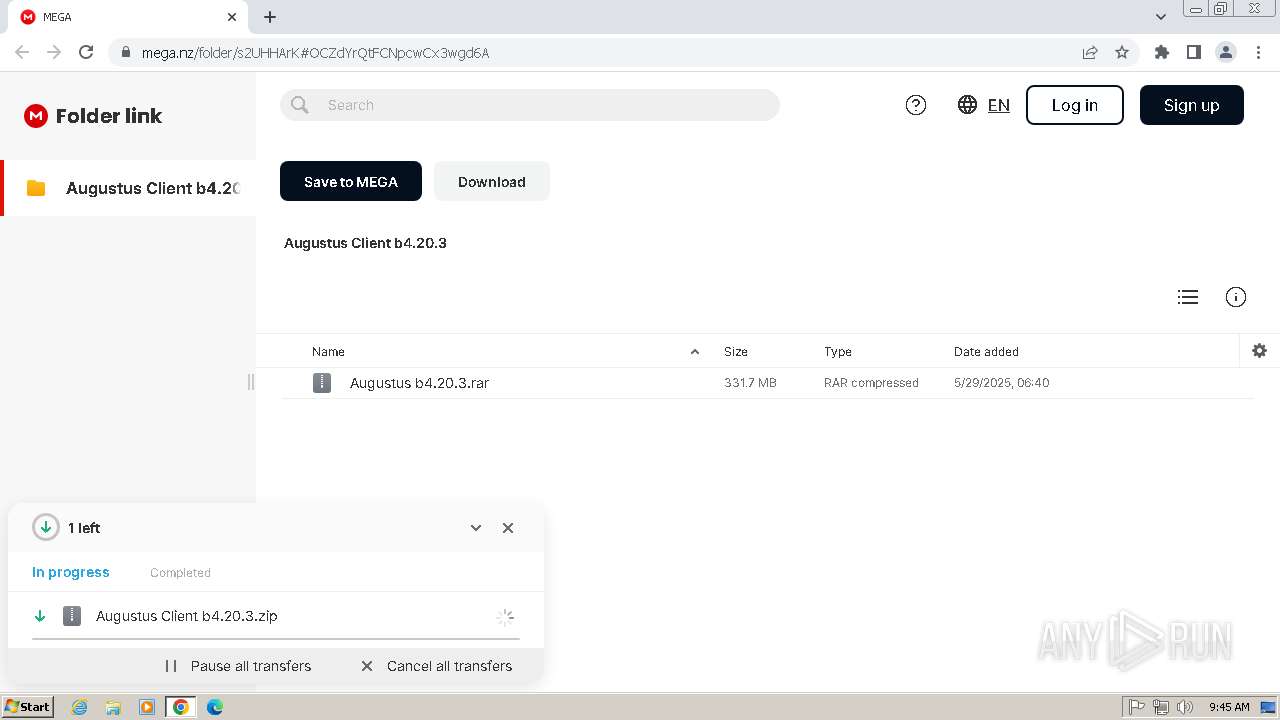
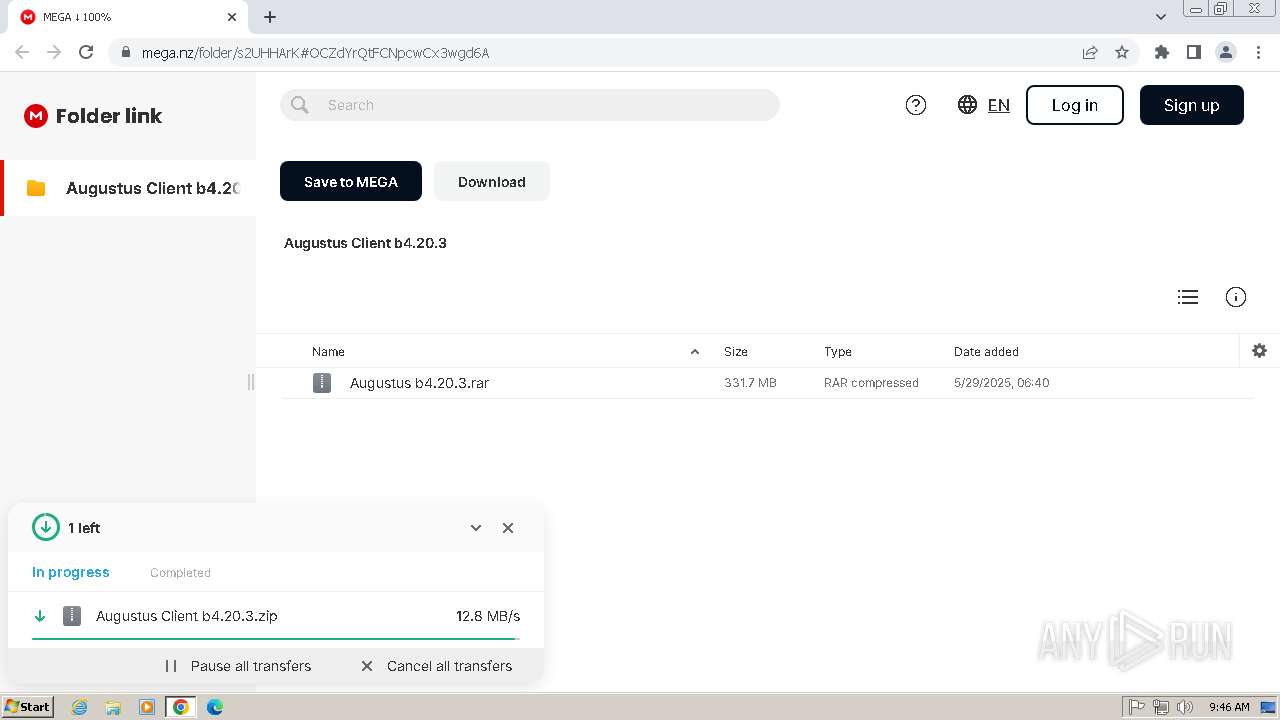
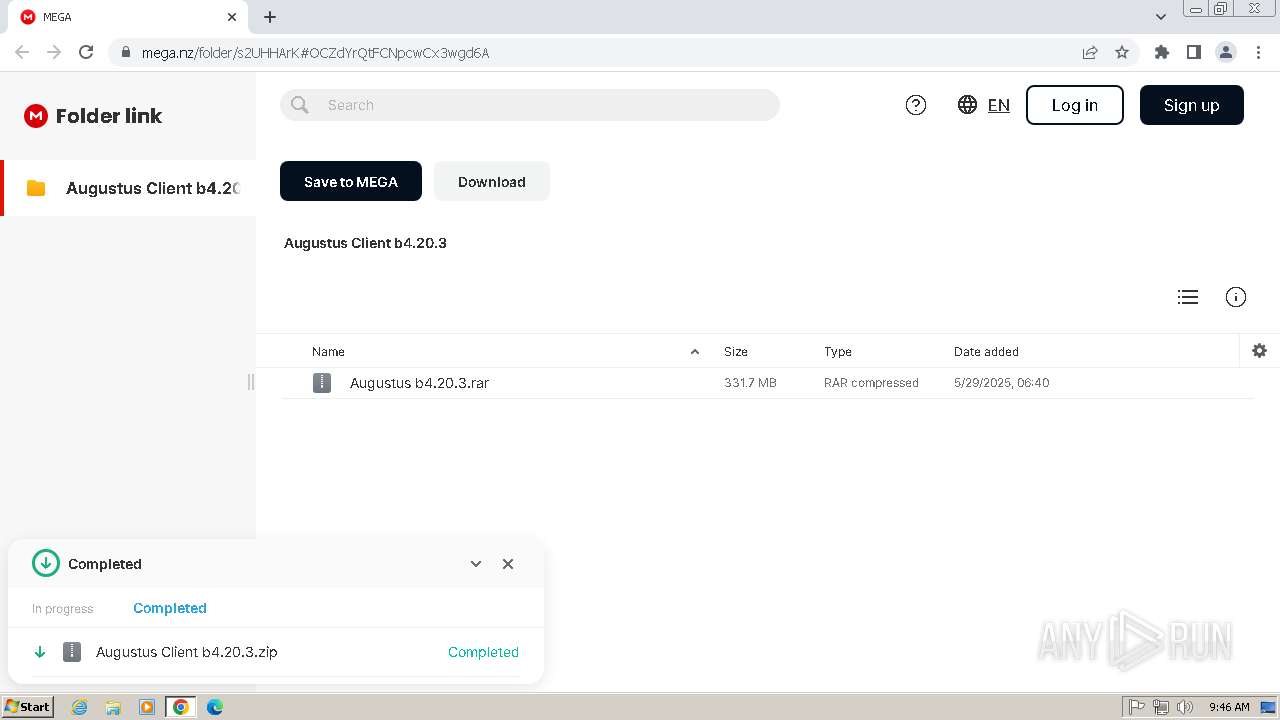
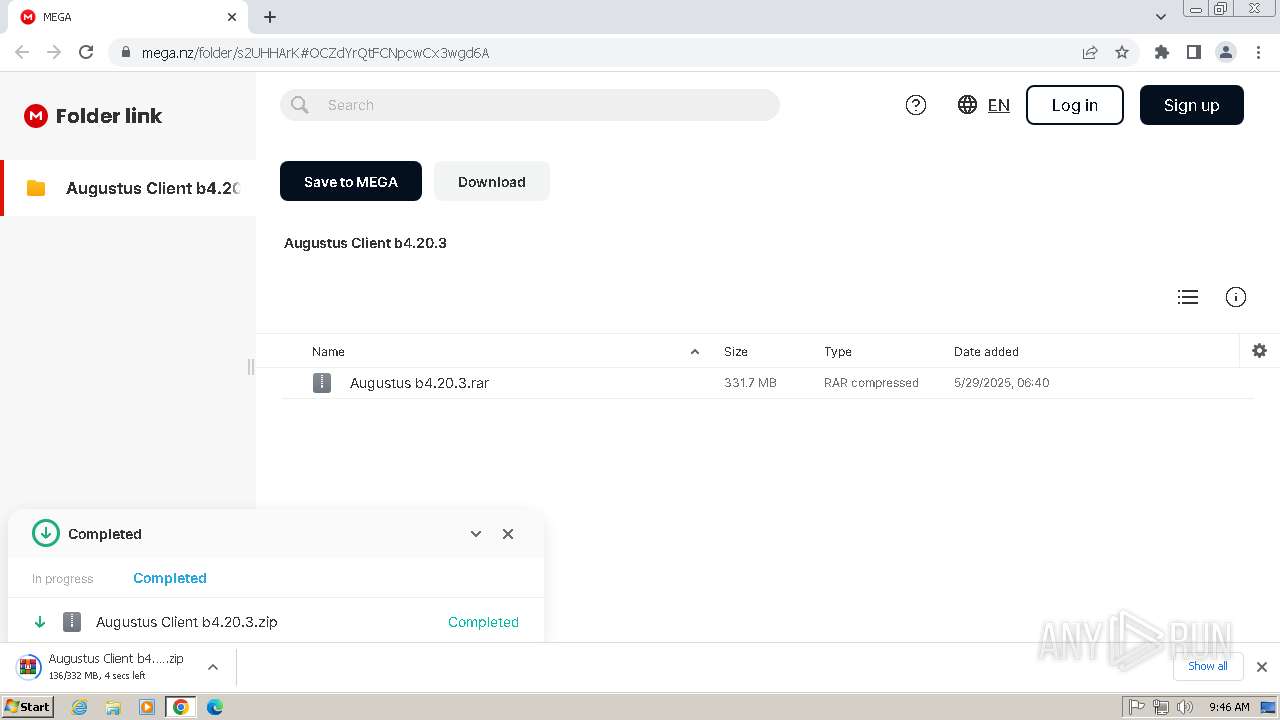
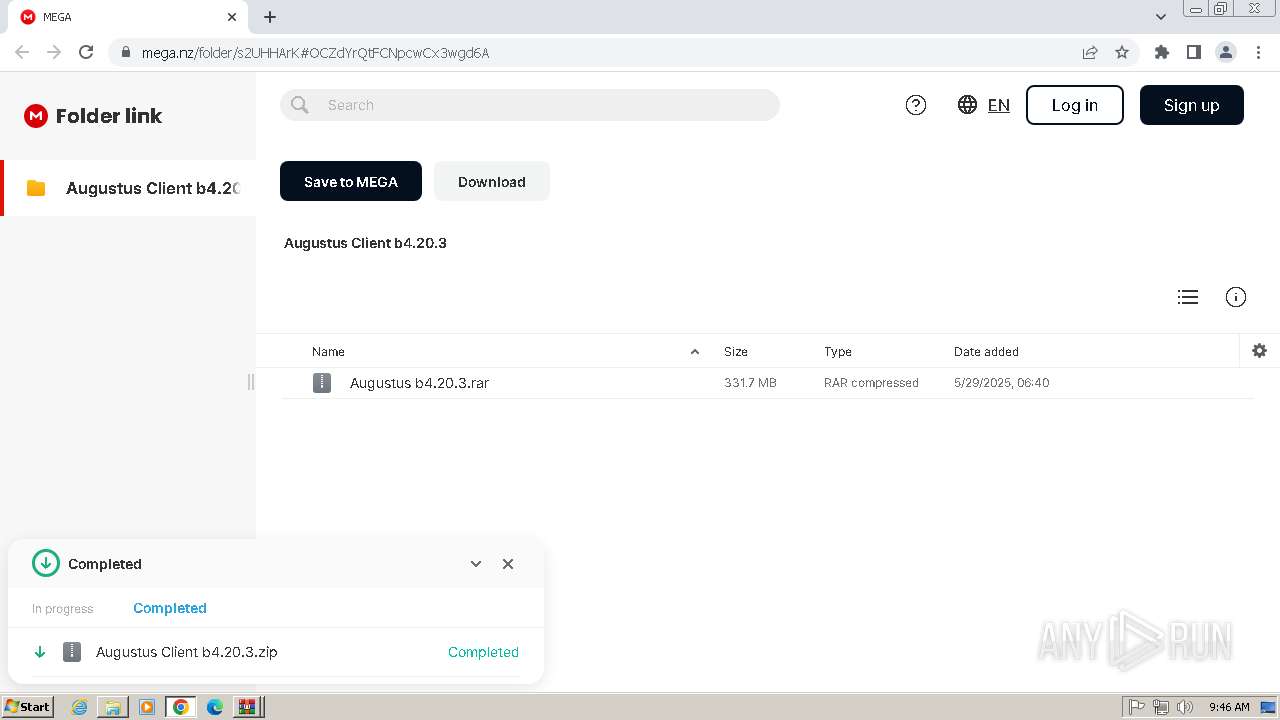
| URL: | https://mega.nz/folder/s2UHHArK#OCZdYrQtFCNpcwCx3wgd6A |
| Full analysis: | https://app.any.run/tasks/521452da-6bb2-43c4-8083-c5ce20a291d2 |
| Verdict: | Malicious activity |
| Analysis date: | June 05, 2025, 08:45:32 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 33783C7A898A22A98A7D7A6D0B499255 |
| SHA1: | 0367F2E462C7464EF22F28BB5CFFEDB2648875BA |
| SHA256: | A97C7E406AEBEF59DCC7FDEBF099B0C0EE8B0C649A62E0296F8D9F38E46F77CD |
| SSDEEP: | 3:N8X/iuyKQY7GqtX0as3ik:26FLAlZk |
MALICIOUS
No malicious indicators.SUSPICIOUS
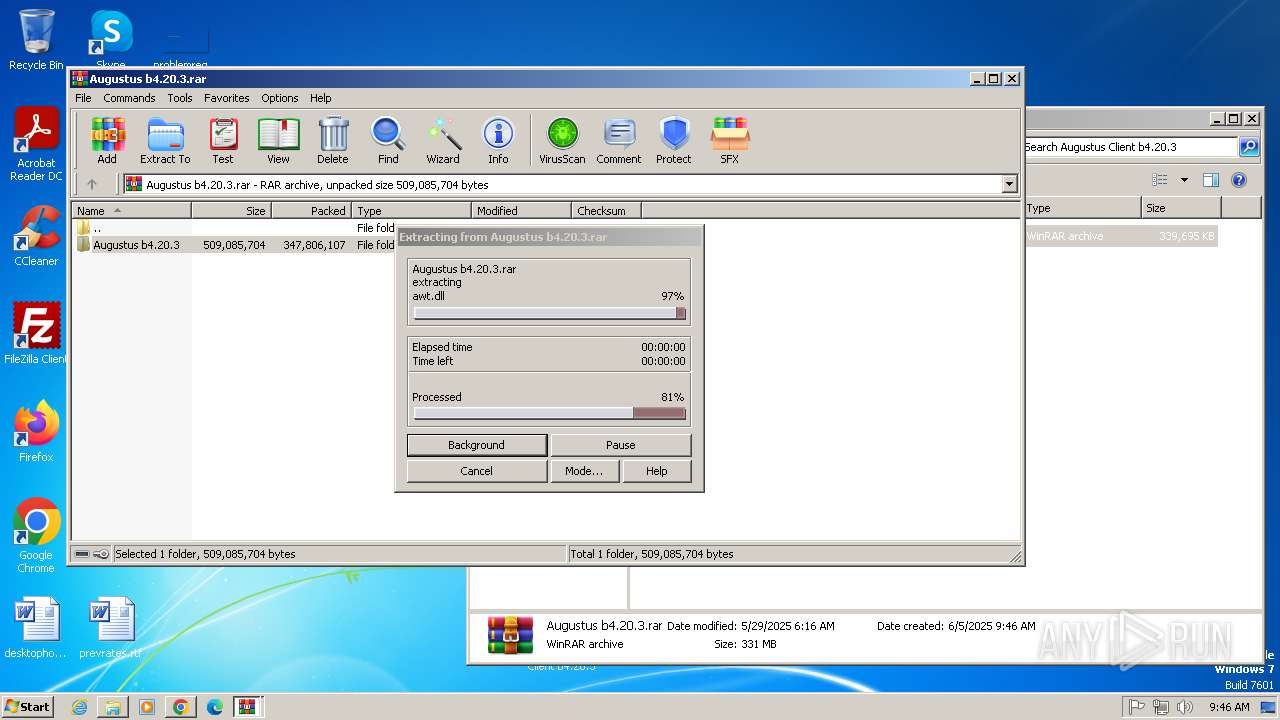
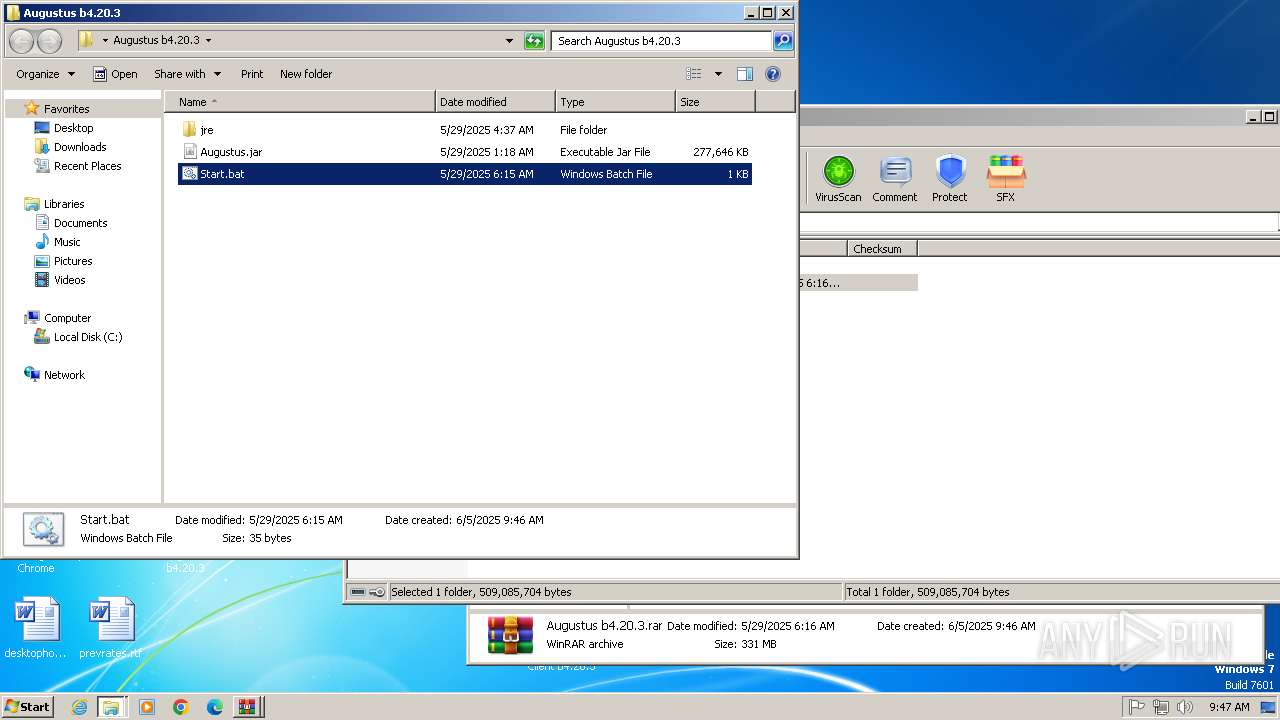
Process drops legitimate windows executable
- WinRAR.exe (PID: 1764)
INFO
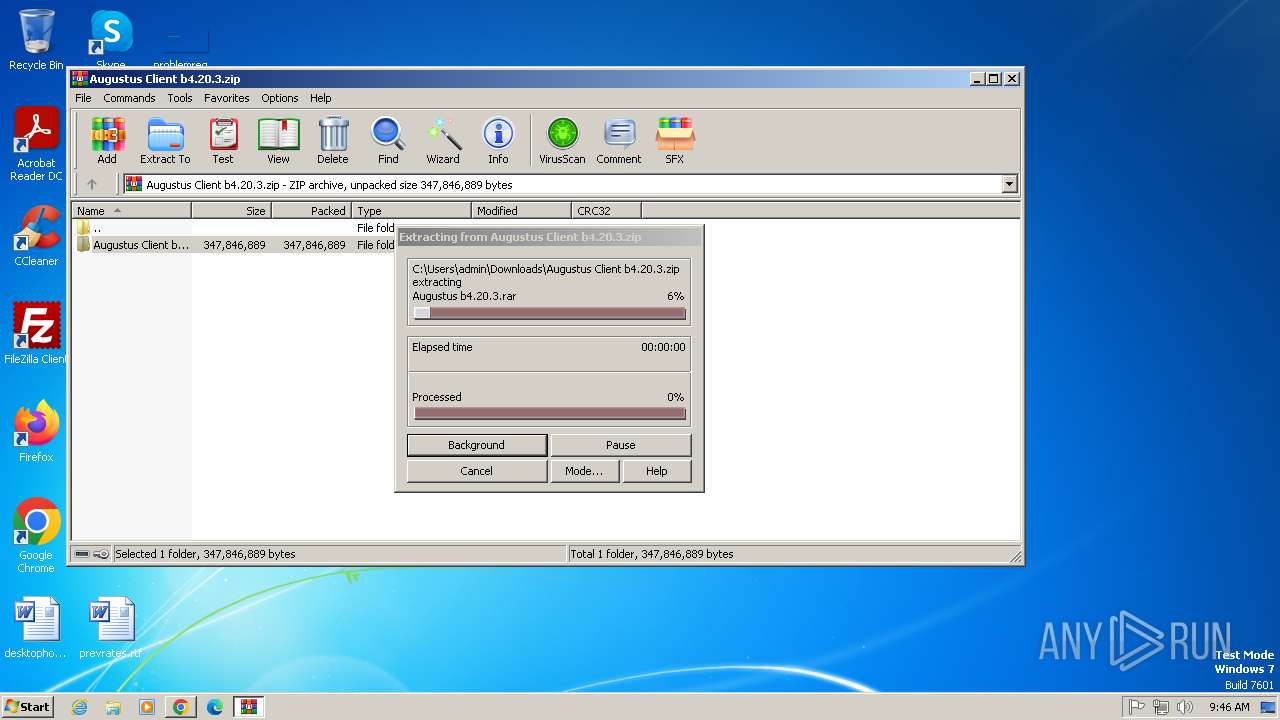
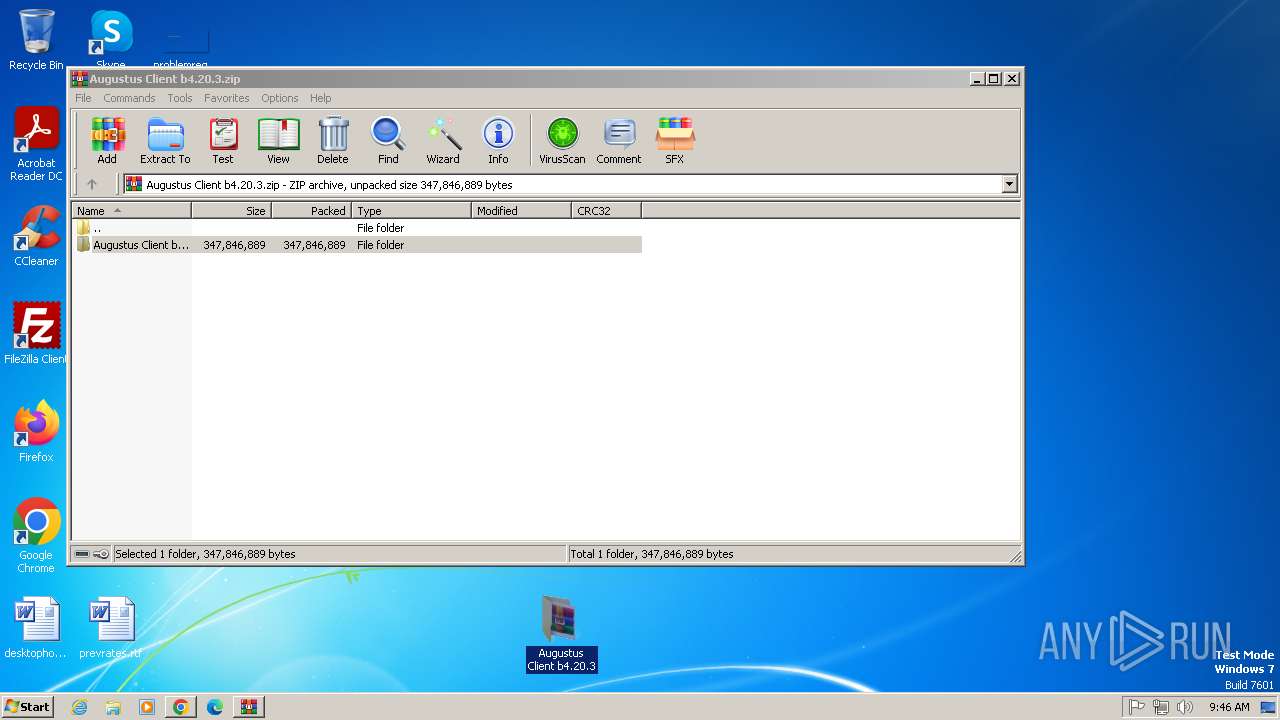
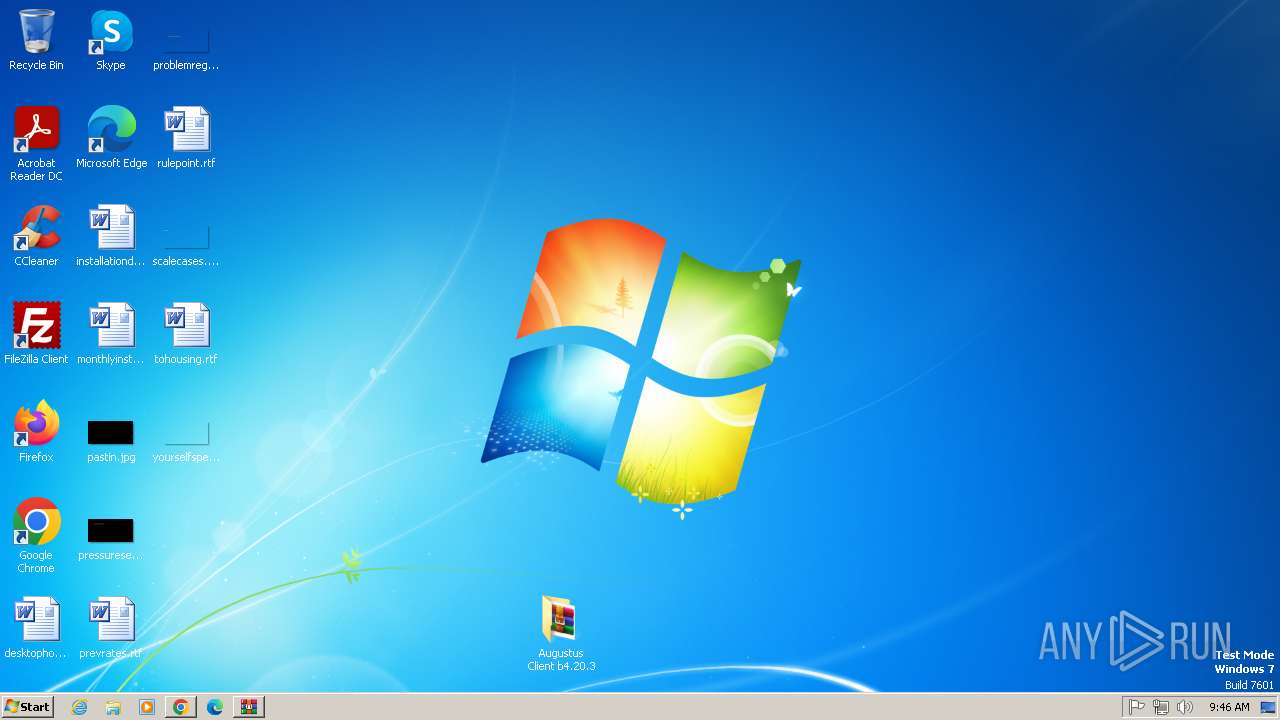
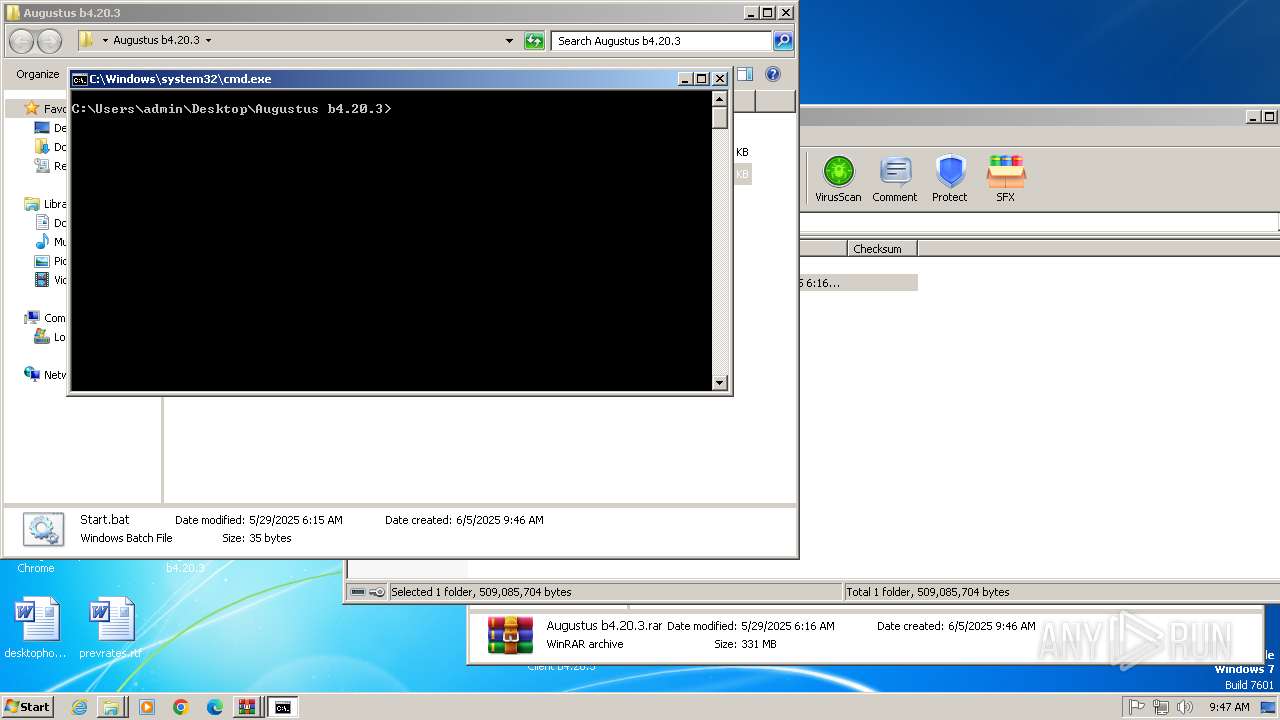
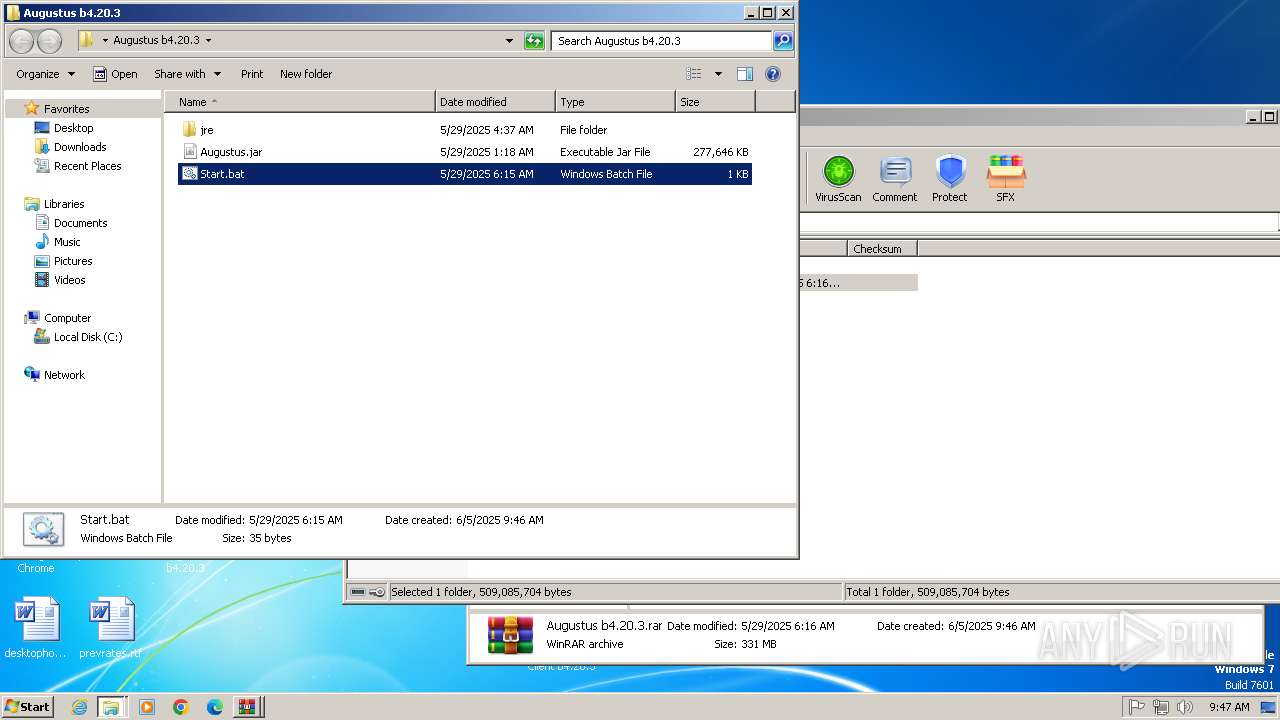
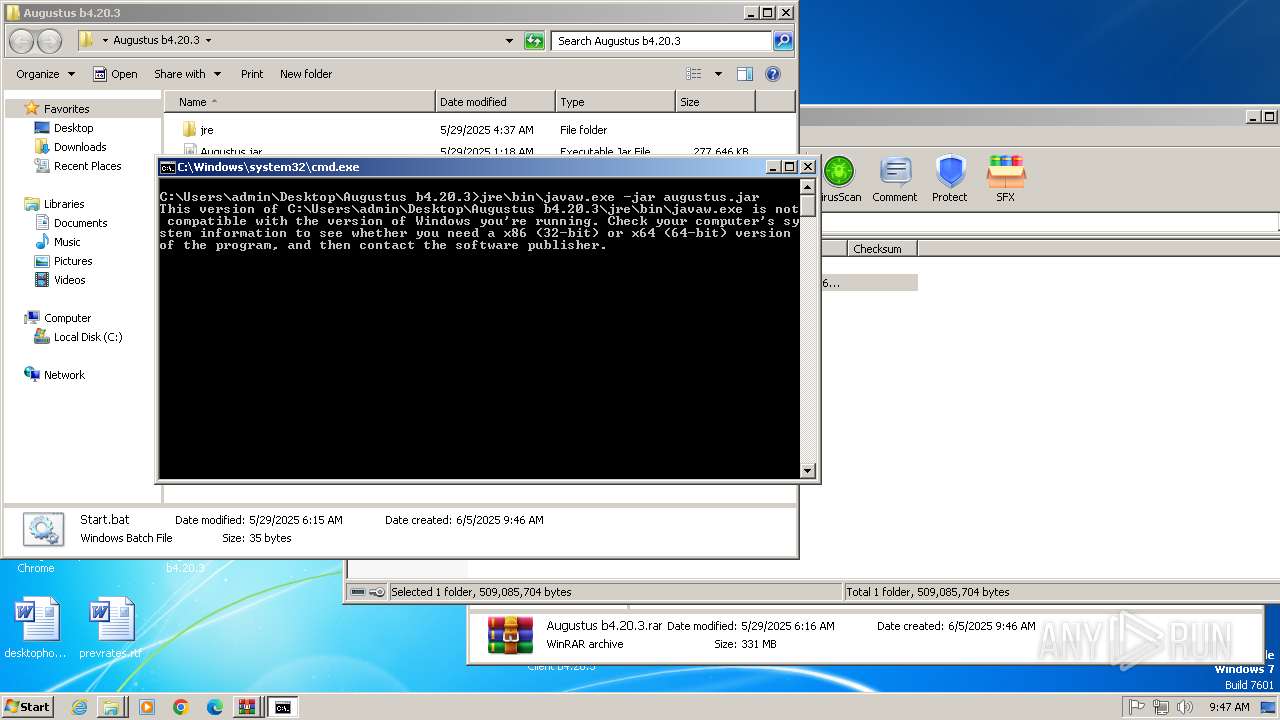
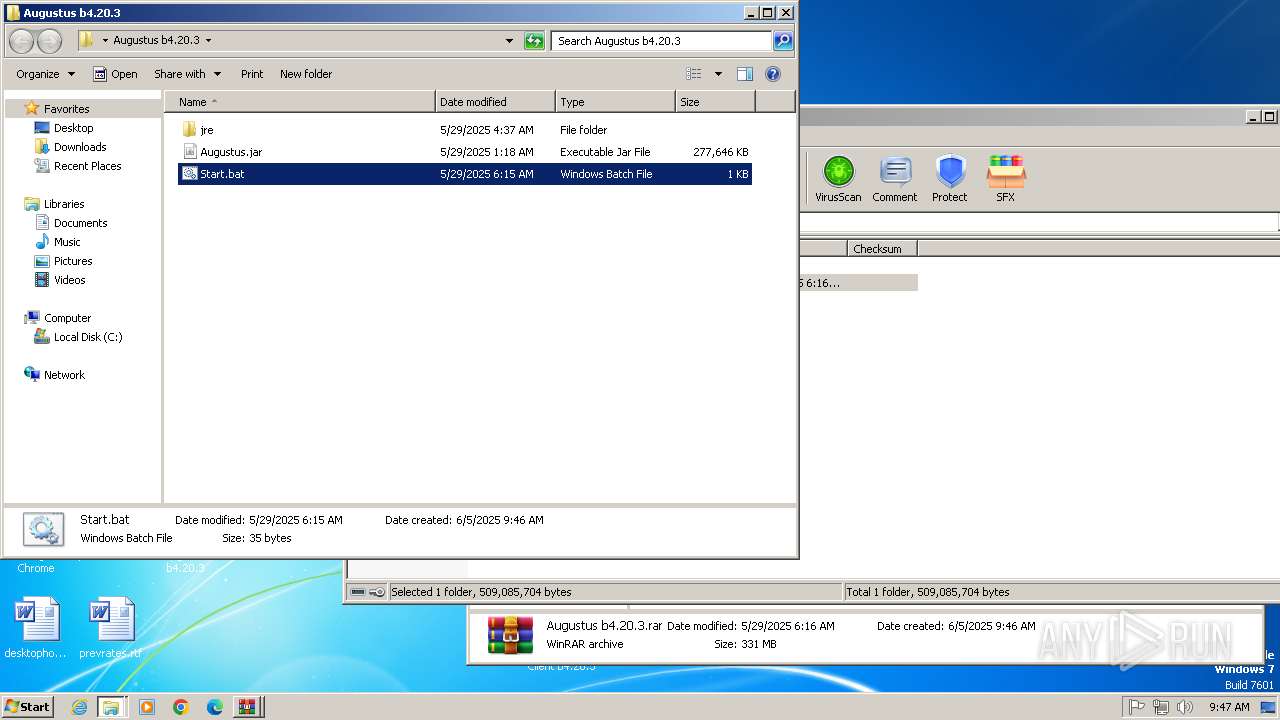
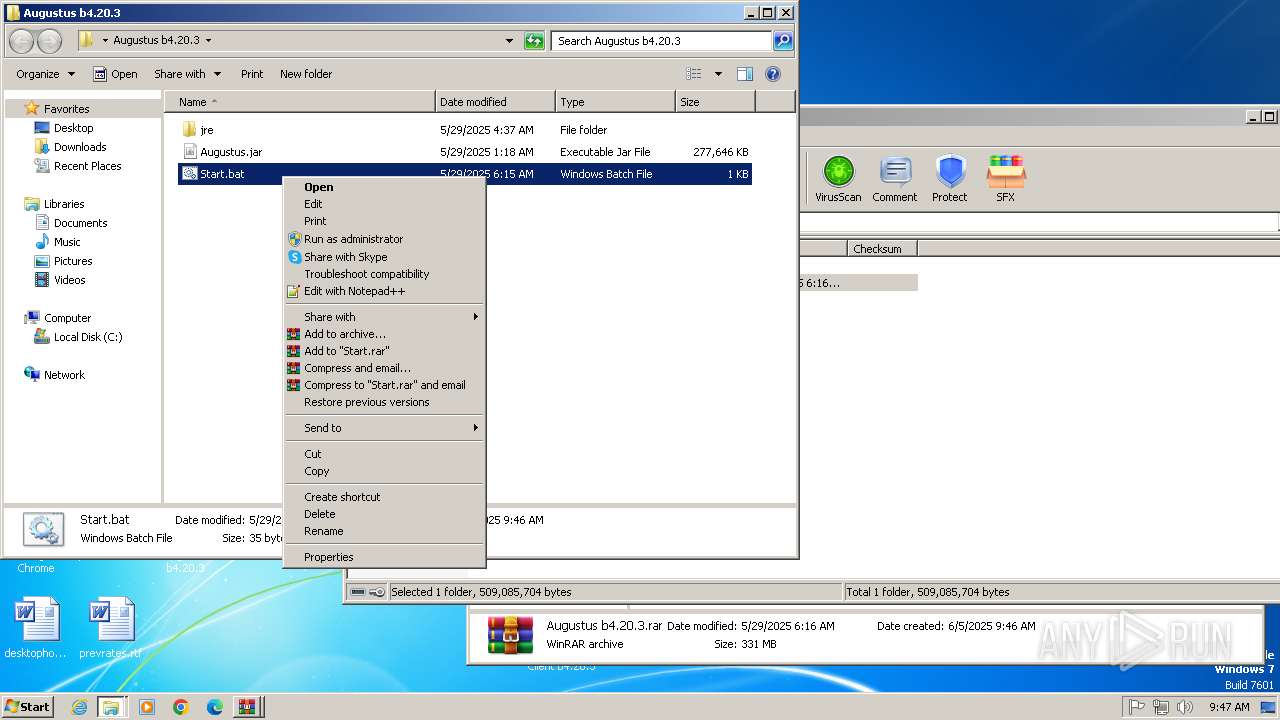
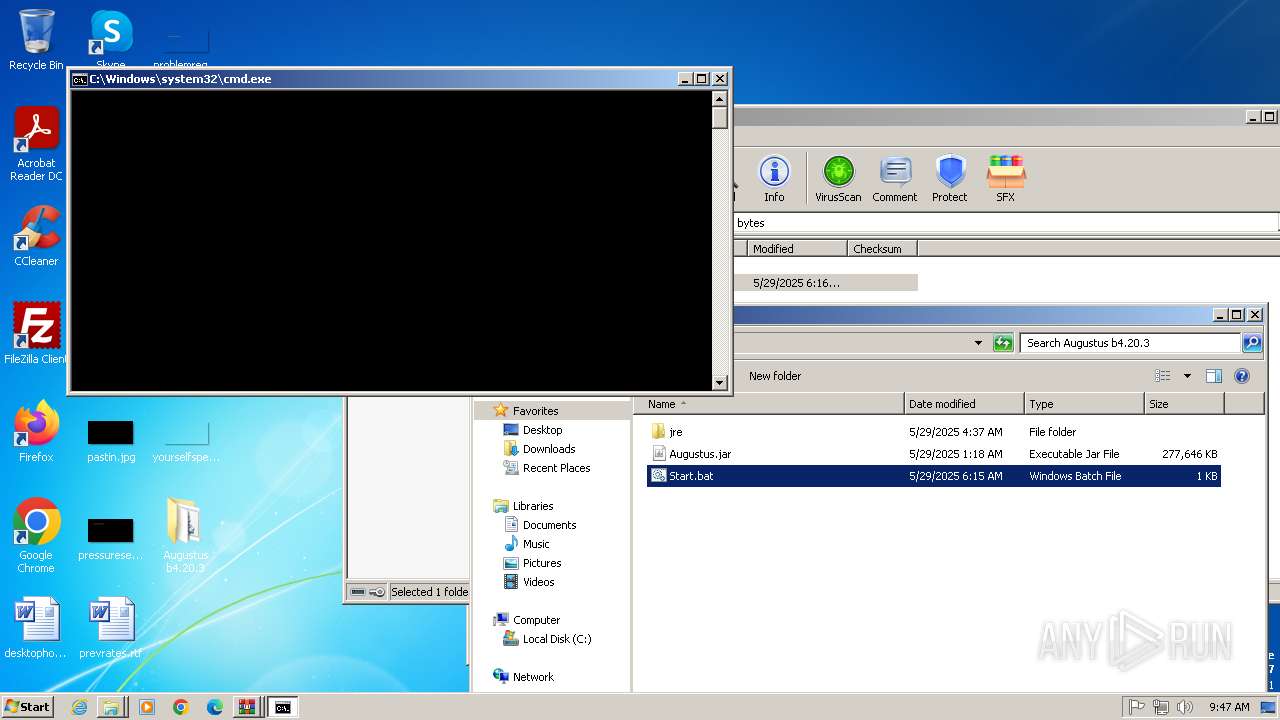
Manual execution by a user
- WinRAR.exe (PID: 1764)
- cmd.exe (PID: 2900)
- cmd.exe (PID: 3416)
- cmd.exe (PID: 2684)
- cmd.exe (PID: 1020)
- cmd.exe (PID: 2068)
- cmd.exe (PID: 2940)
- cmd.exe (PID: 1768)
- cmd.exe (PID: 2732)
- cmd.exe (PID: 3660)
- cmd.exe (PID: 3776)
- cmd.exe (PID: 3888)
- cmd.exe (PID: 3232)
- cmd.exe (PID: 288)
- cmd.exe (PID: 2144)
- cmd.exe (PID: 3484)
- cmd.exe (PID: 3148)
- cmd.exe (PID: 1124)
- cmd.exe (PID: 1448)
- cmd.exe (PID: 3316)
- cmd.exe (PID: 3308)
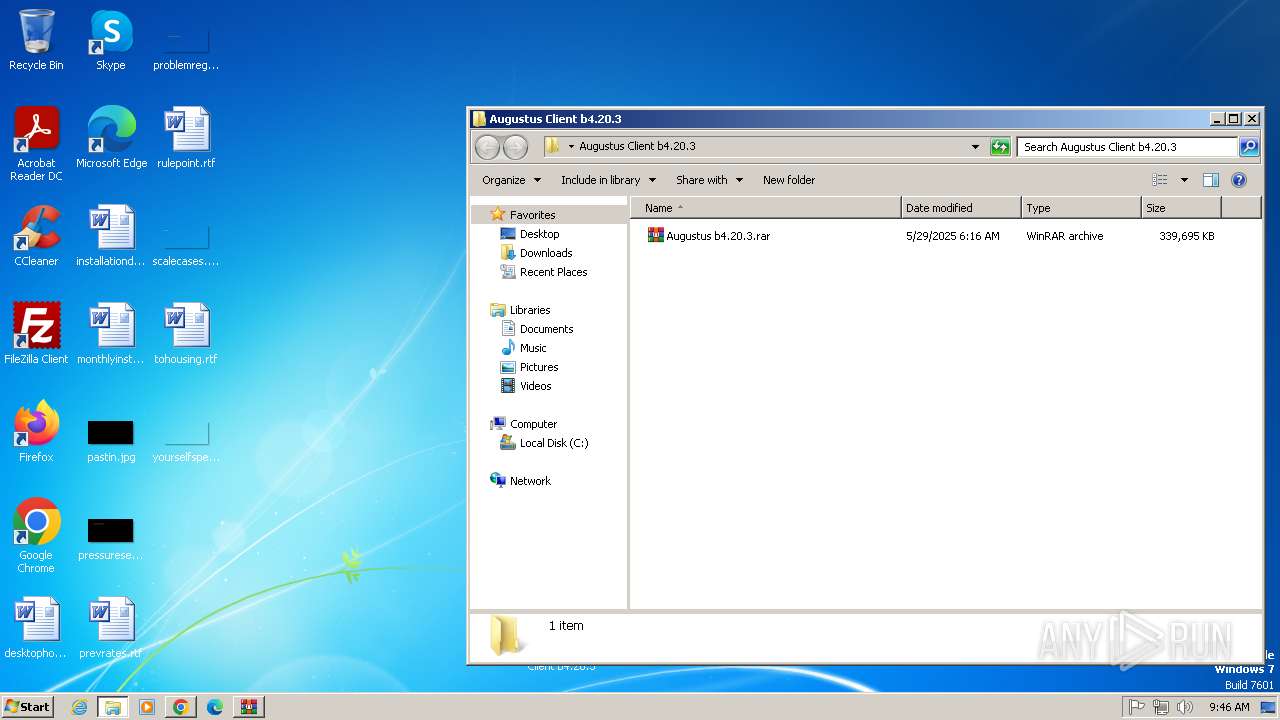
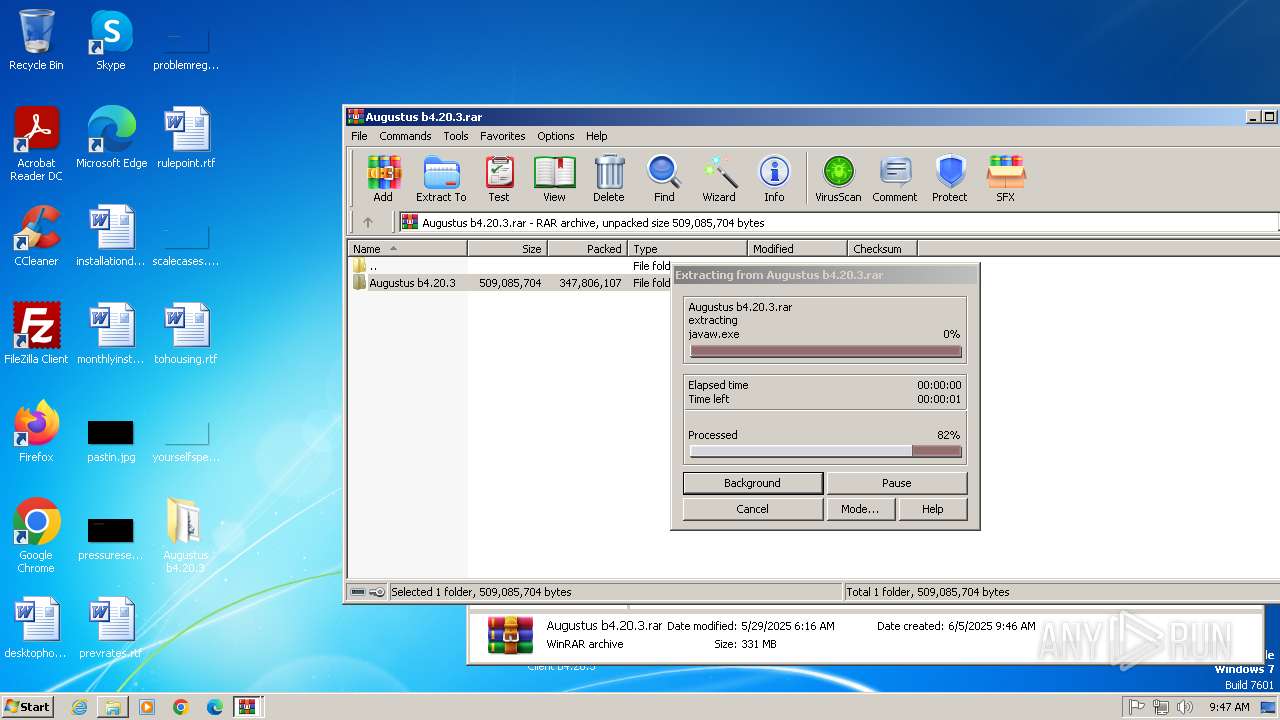
Executable content was dropped or overwritten
- WinRAR.exe (PID: 1764)
The sample compiled with english language support
- WinRAR.exe (PID: 1764)
Application launched itself
- chrome.exe (PID: 3900)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
96
Monitored processes
37
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
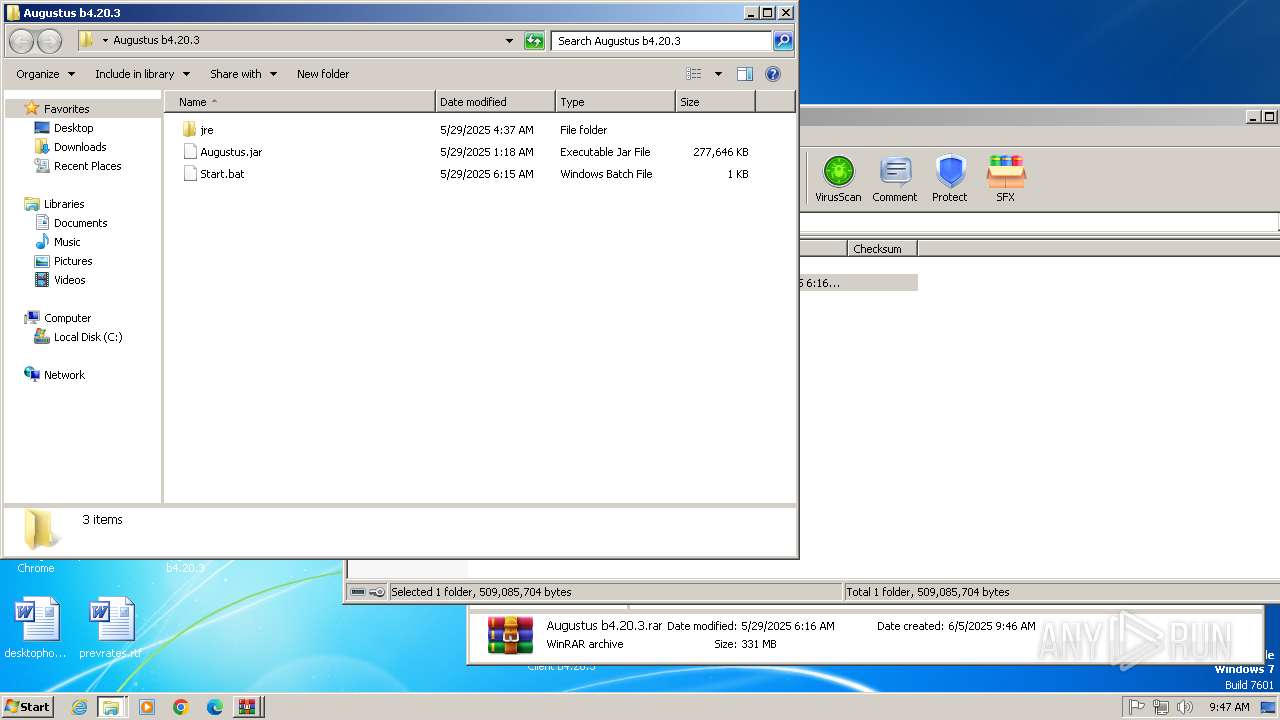
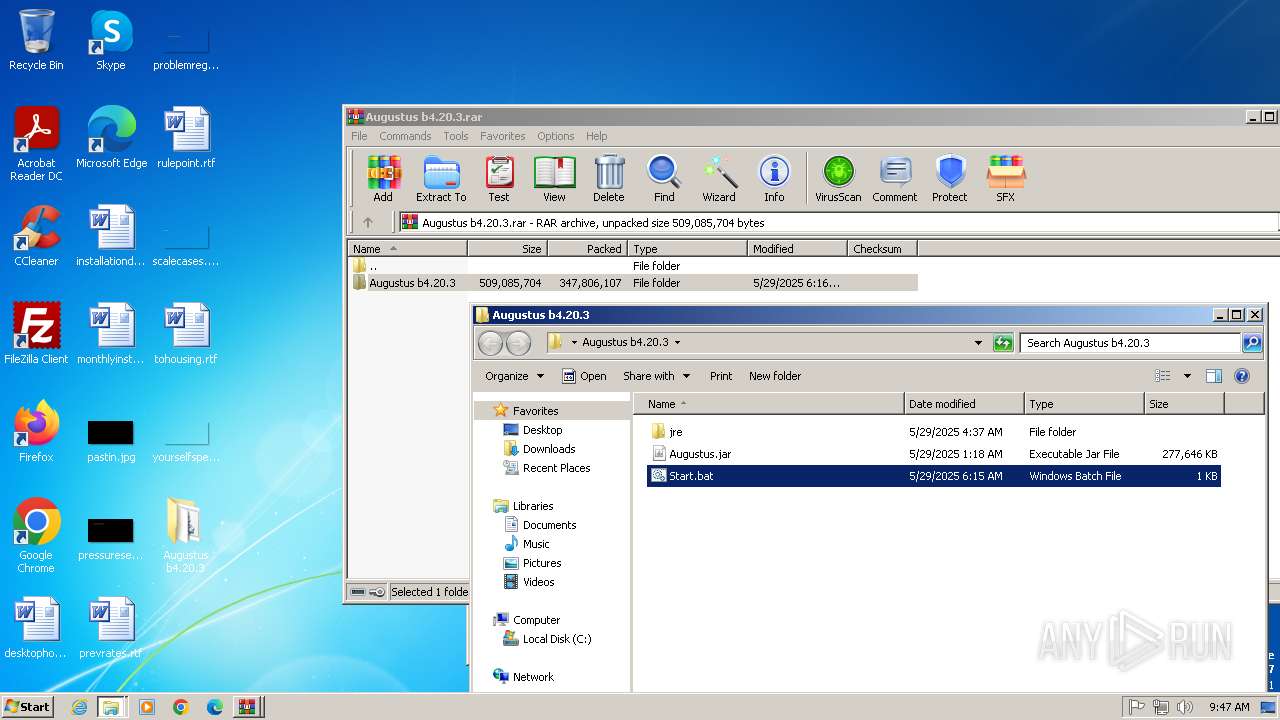
| 288 | C:\Windows\system32\cmd.exe /c ""C:\Users\admin\Desktop\Augustus b4.20.3\Start.bat" " | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 752 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=3628 --field-trial-handle=1144,i,2796398440273287877,12489852972054661906,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1020 | C:\Windows\system32\cmd.exe /c ""C:\Users\admin\Desktop\Augustus b4.20.3\Start.bat" " | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1124 | C:\Windows\system32\cmd.exe /c ""C:\Users\admin\Desktop\Augustus b4.20.3\Start.bat" " | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1168 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgACAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --use-gl=angle --use-angle=swiftshader-webgl --mojo-platform-channel-handle=1392 --field-trial-handle=1144,i,2796398440273287877,12489852972054661906,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1448 | C:\Windows\system32\cmd.exe /c ""C:\Users\admin\Desktop\Augustus b4.20.3\Start.bat" " | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
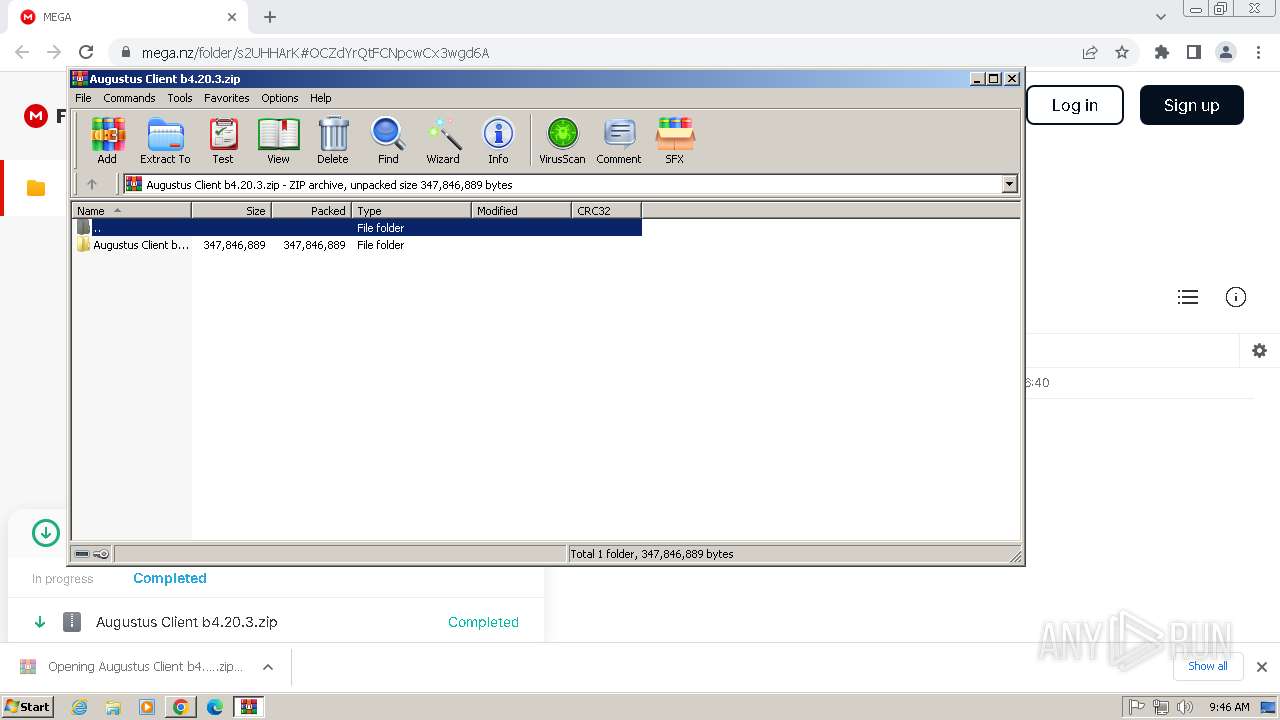
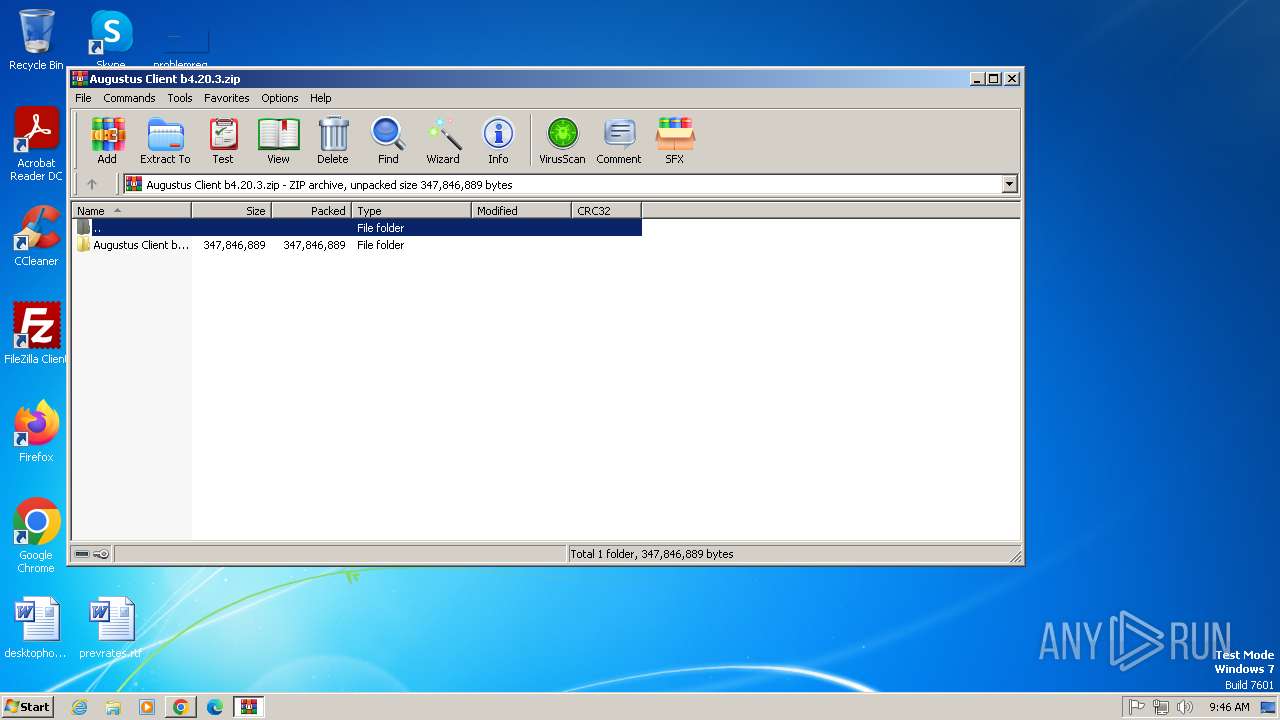
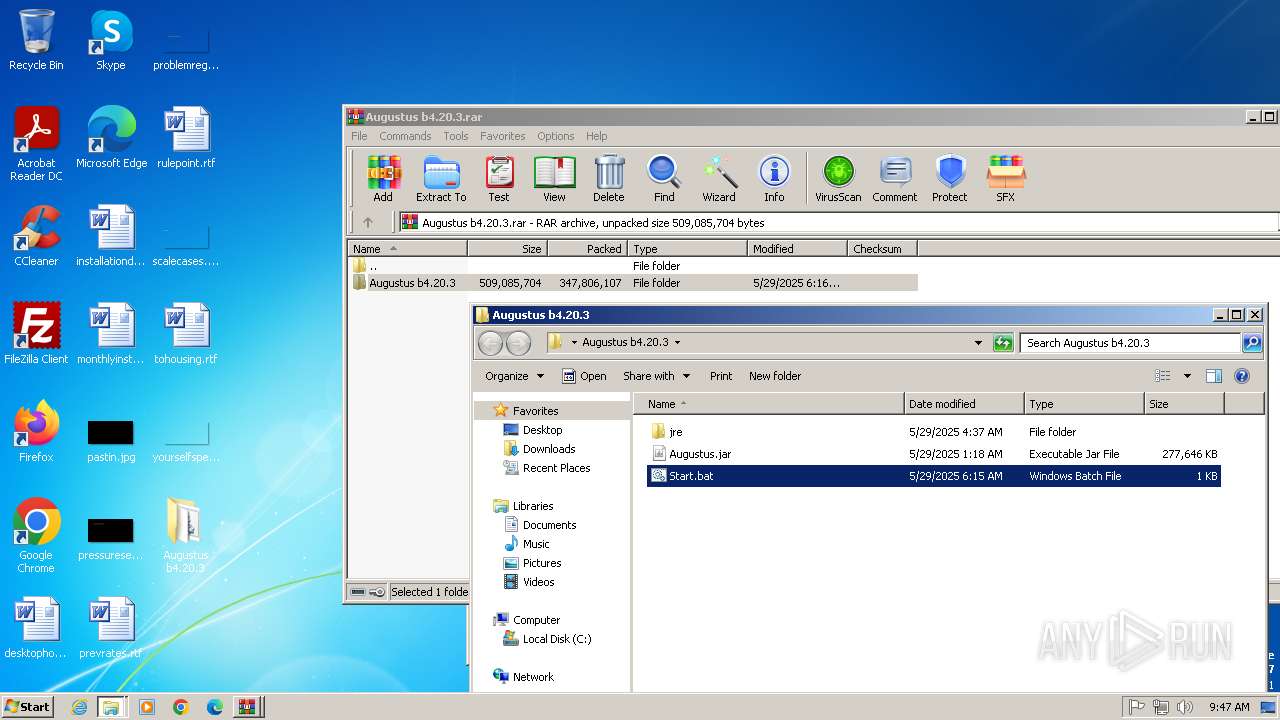
| 1548 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\Augustus Client b4.20.3.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | chrome.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 1584 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.FileUtilService --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=1916 --field-trial-handle=1144,i,2796398440273287877,12489852972054661906,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1592 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=3128 --field-trial-handle=1144,i,2796398440273287877,12489852972054661906,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
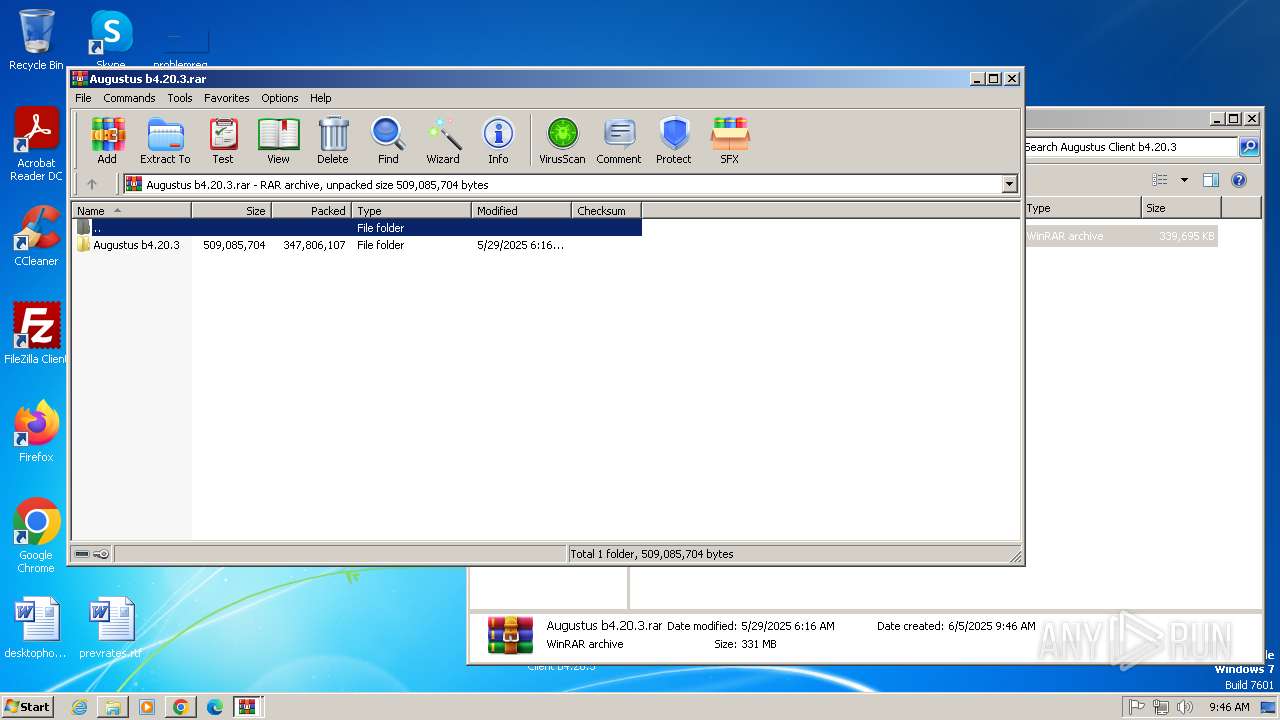
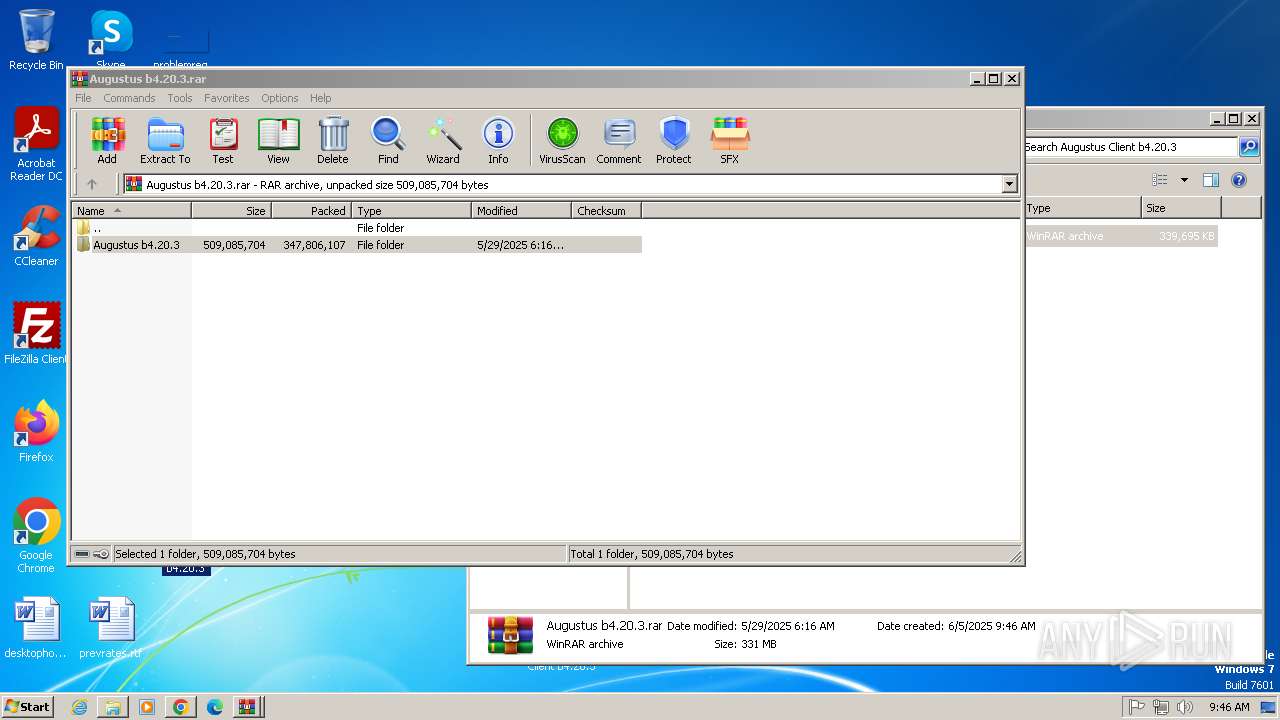
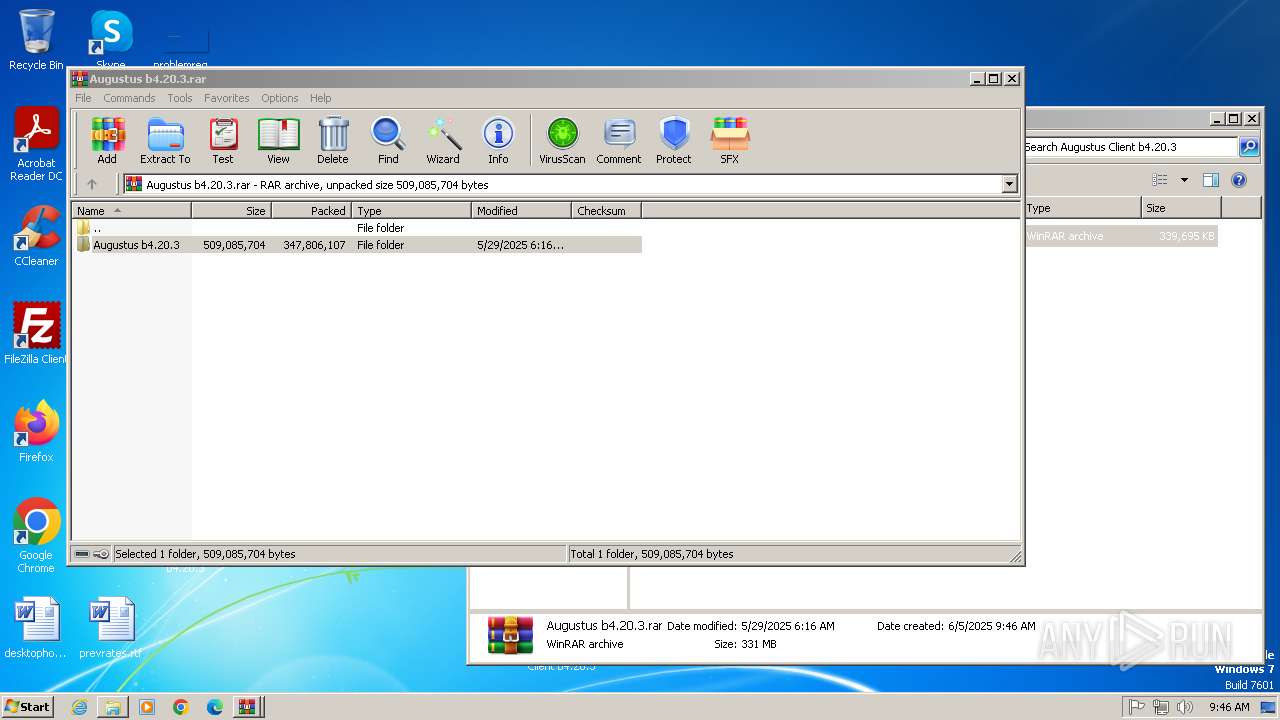
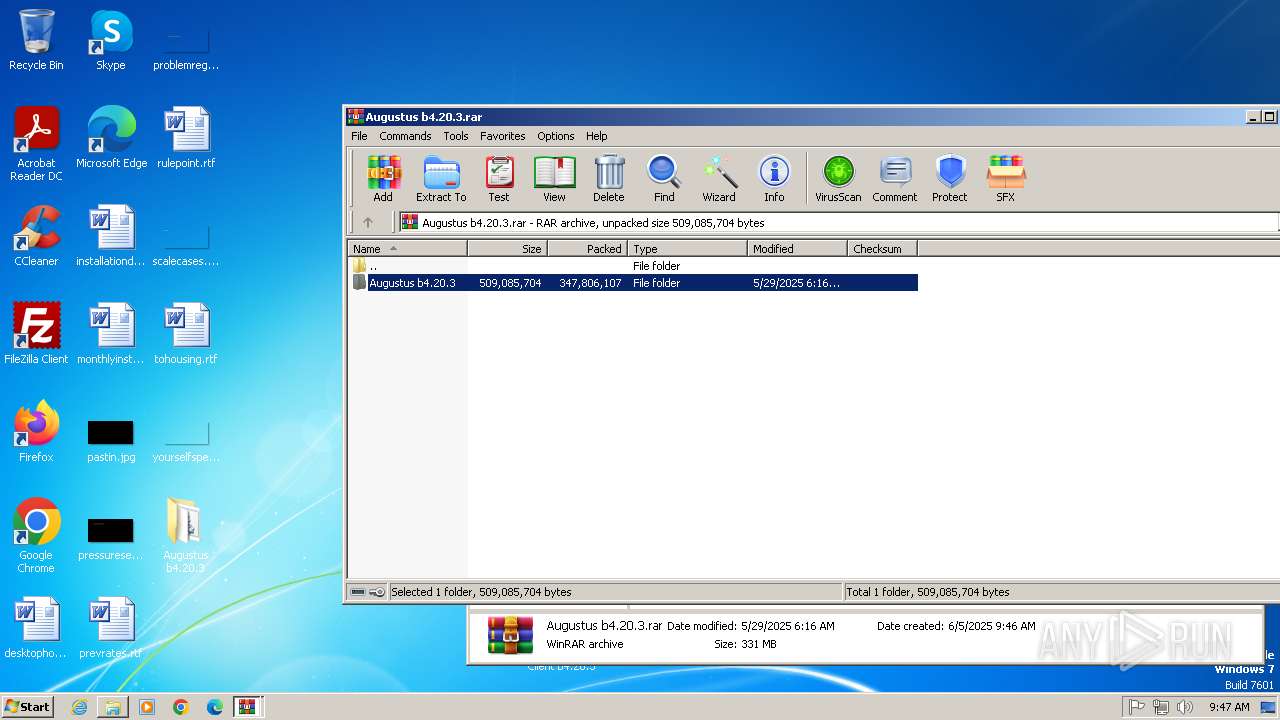
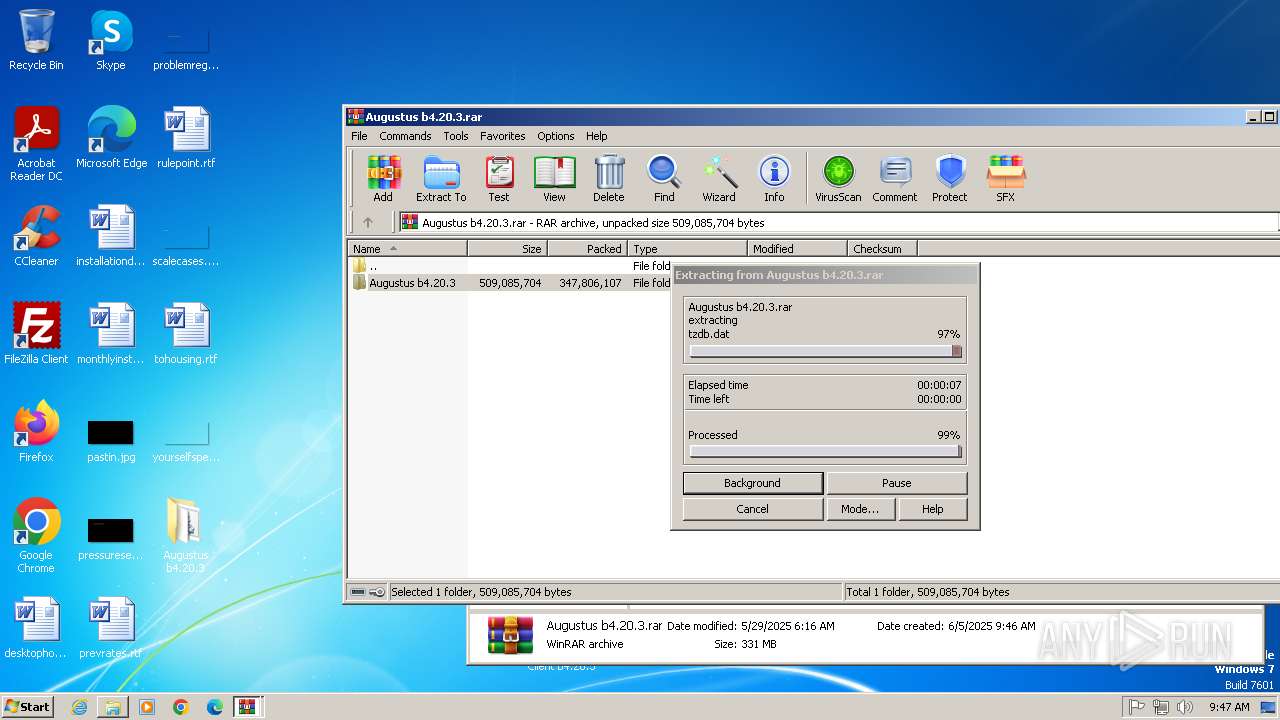
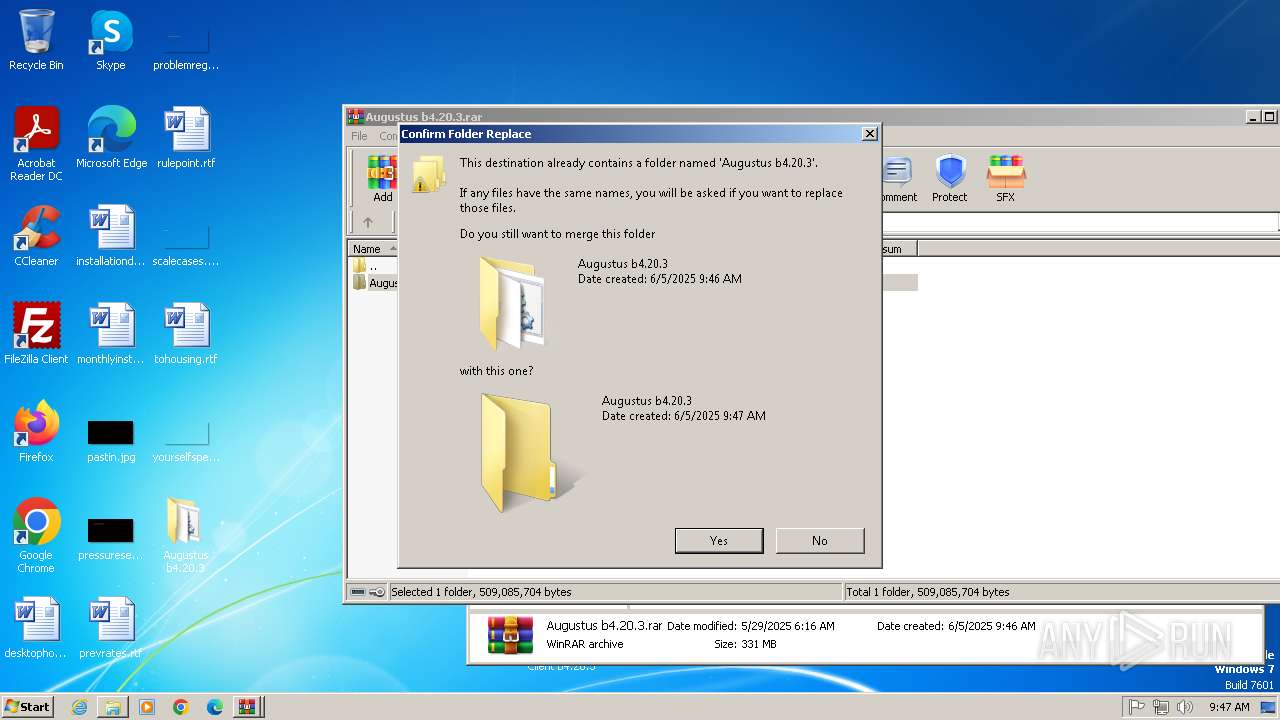
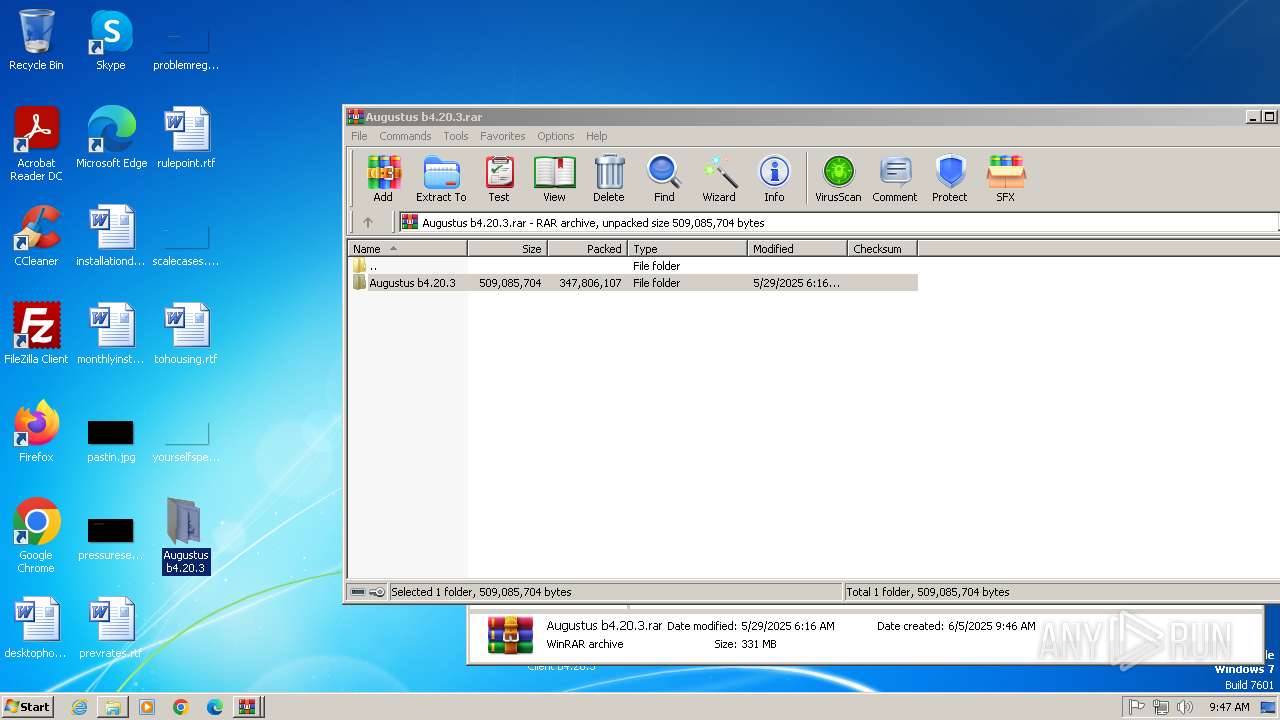
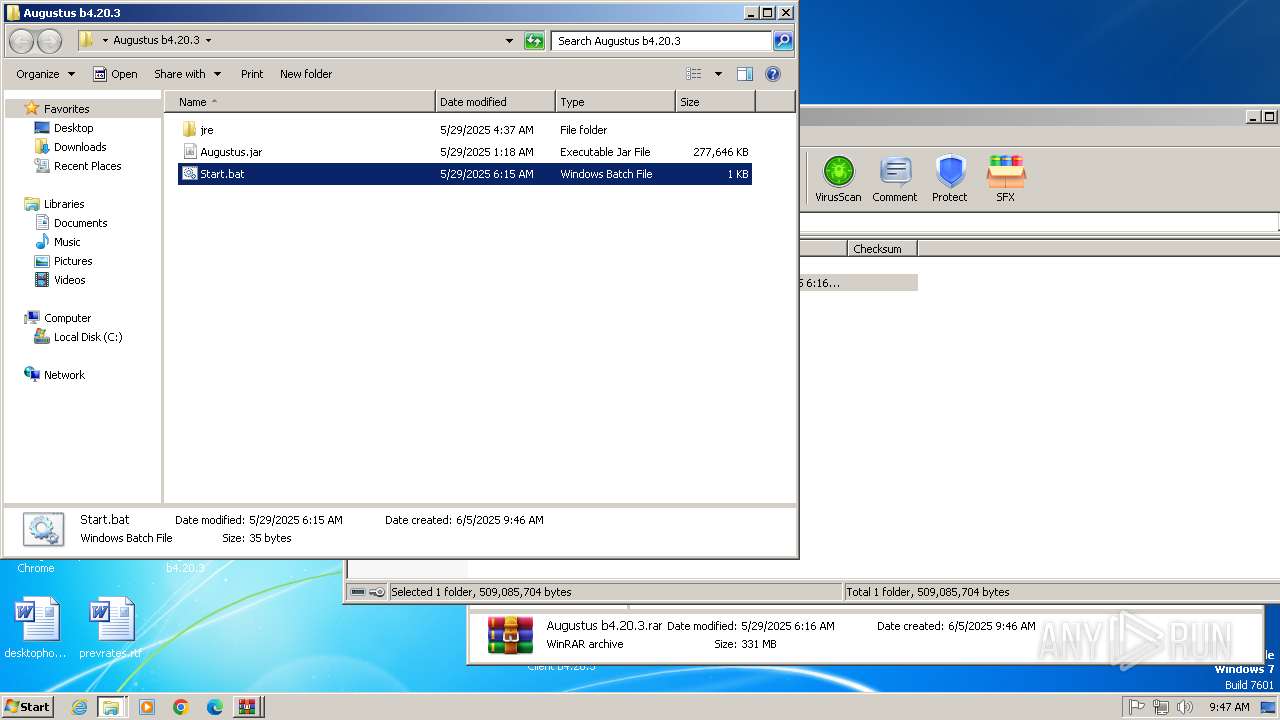
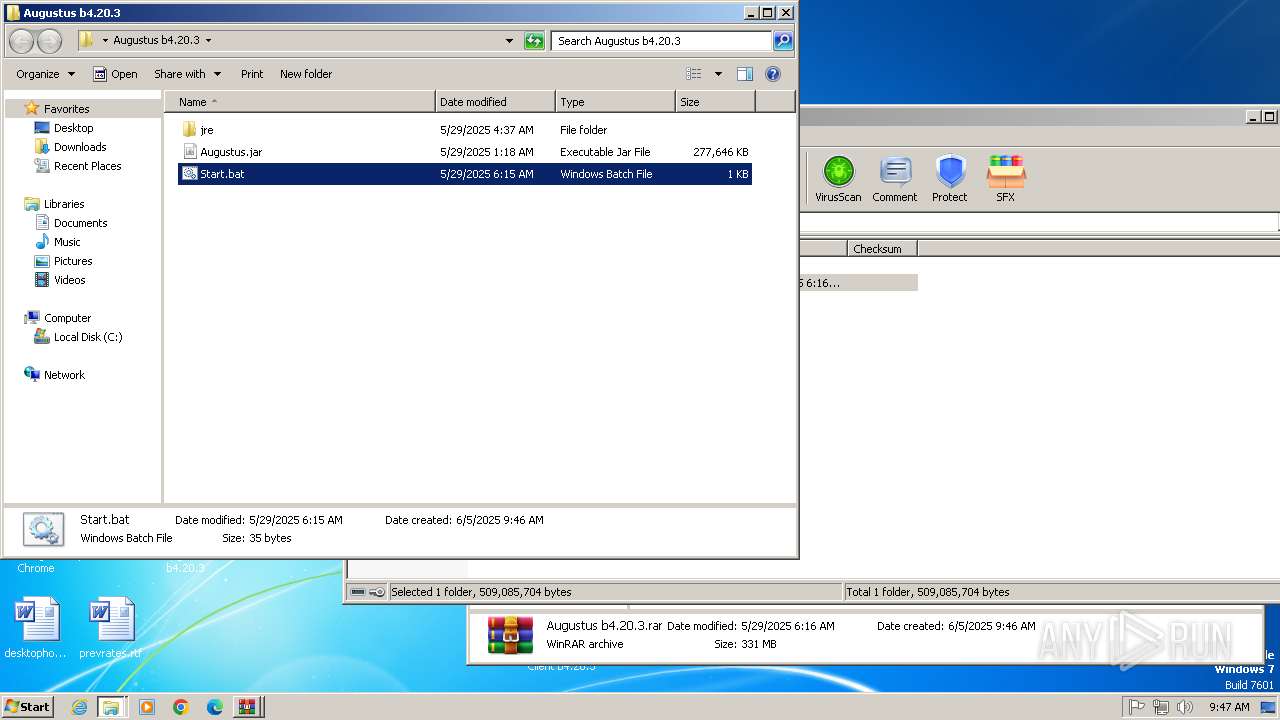
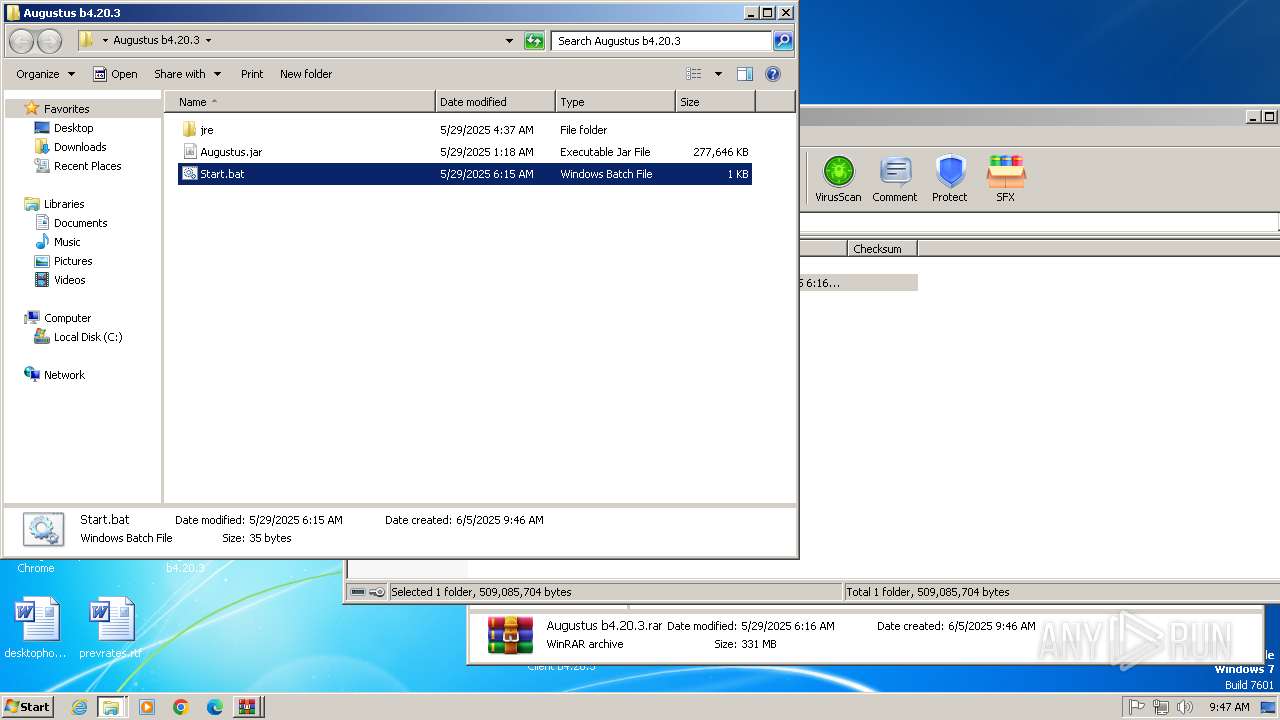
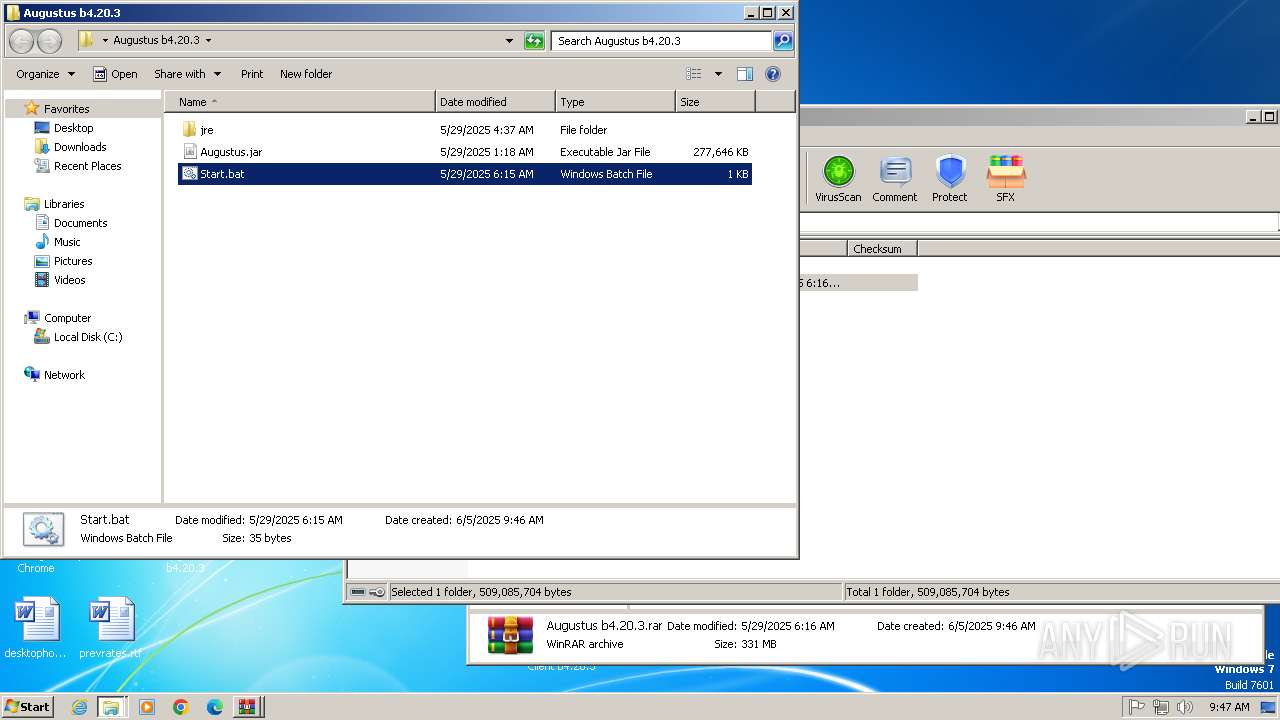
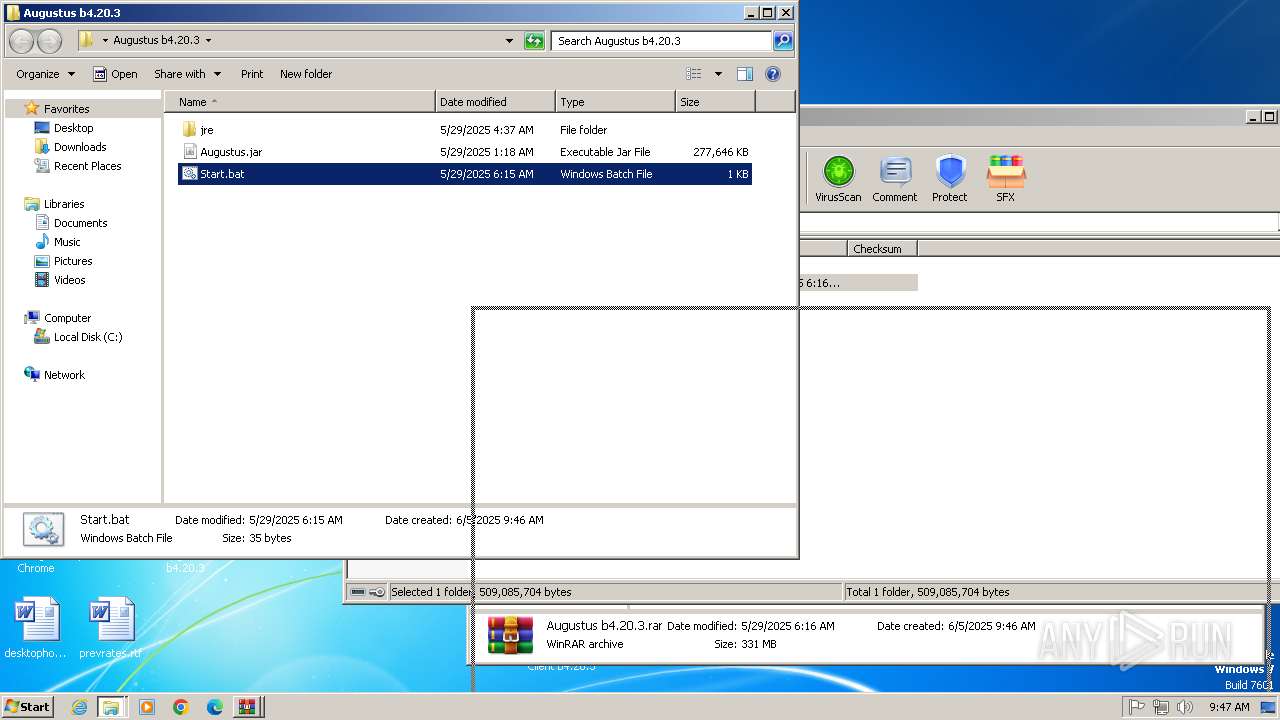
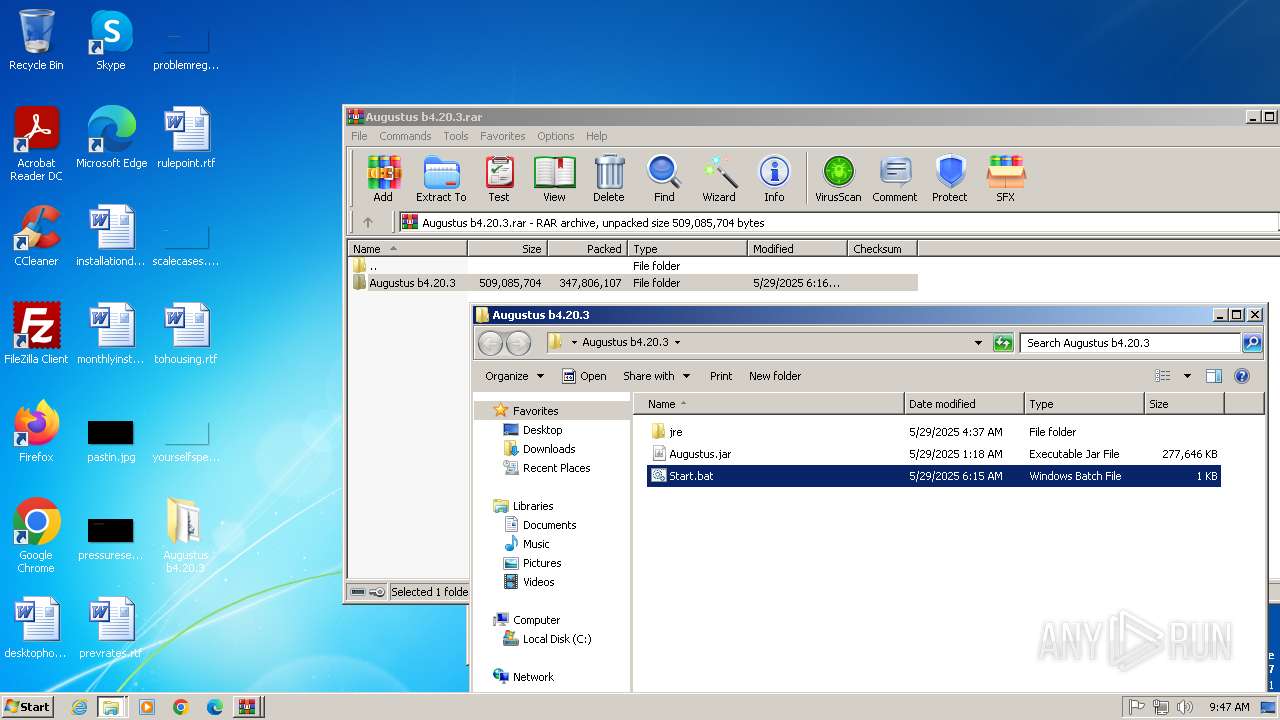
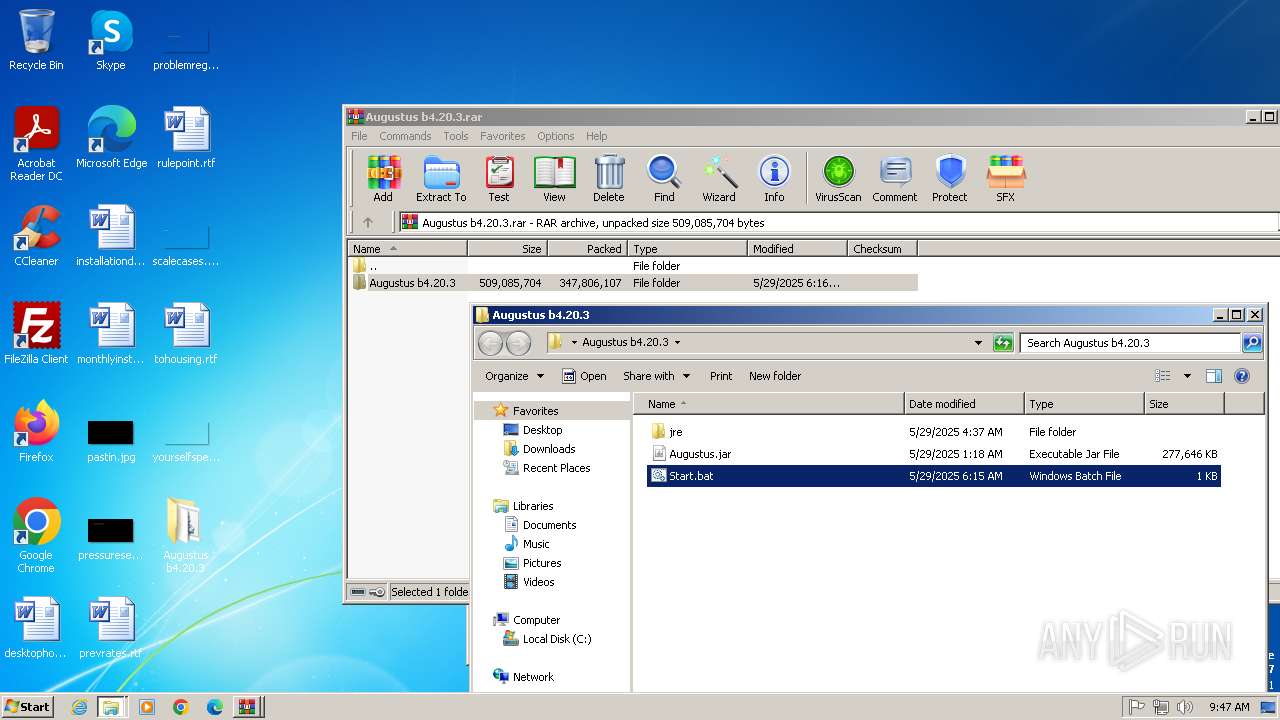
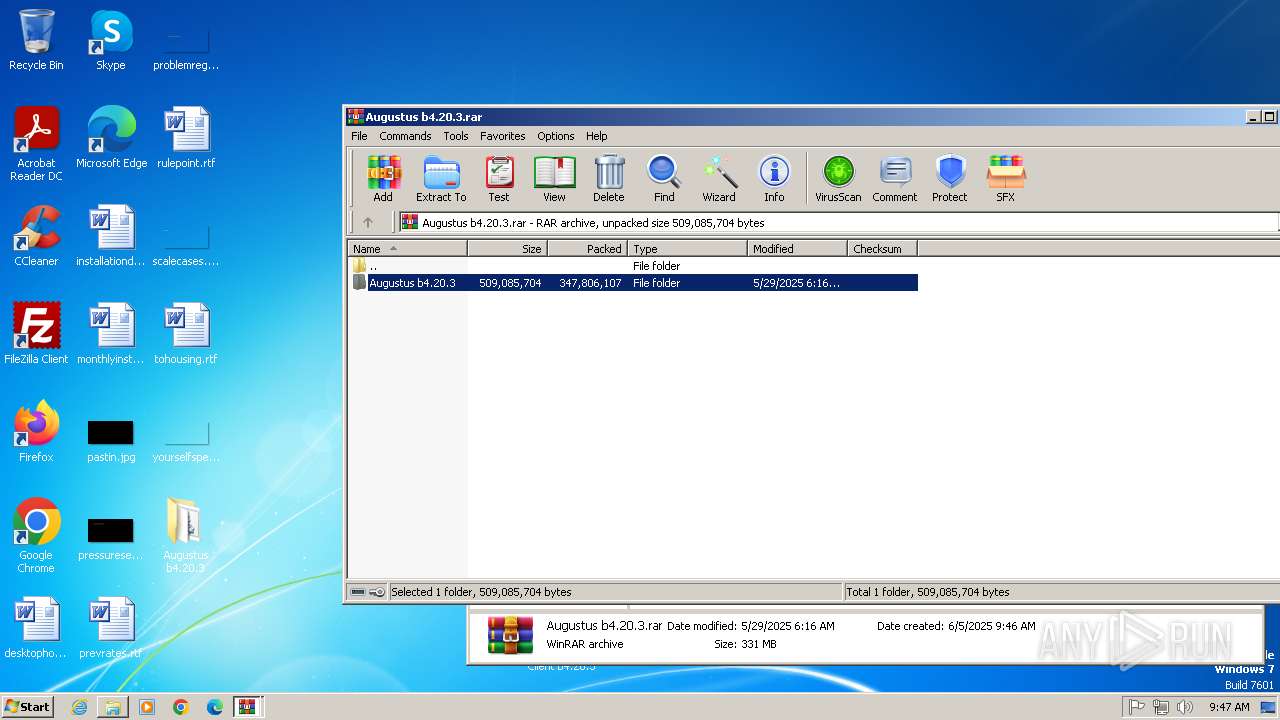
| 1764 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\Augustus Client b4.20.3\Augustus b4.20.3.rar" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
Total events
7 334
Read events
7 236
Write events
93
Delete events
5
Modification events
| (PID) Process: | (3900) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3900) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3900) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3900) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3900) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3900) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3900) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3900) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
| (PID) Process: | (3900) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
| (PID) Process: | (3900) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_enableddate |
Value: 0 | |||
Executable files
322
Suspicious files
80
Text files
238
Unknown types
41
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3900 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF19430a.TMP | — | |
MD5:— | SHA256:— | |||
| 3900 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3900 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 3900 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:9F941EA08DBDCA2EB3CFA1DBBBA6F5DC | SHA256:127F71DF0D2AD895D4F293E62284D85971AE047CA15F90B87BF6335898B0B655 | |||
| 3900 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Variations | binary | |
MD5:961E3604F228B0D10541EBF921500C86 | SHA256:F7B24F2EB3D5EB0550527490395D2F61C3D2FE74BB9CB345197DAD81B58B5FED | |||
| 3900 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF19430a.TMP | text | |
MD5:1C6BD9993E8ECB91342E78927D81DCA3 | SHA256:76BE6BB39D2B3287BCBBCF6465599F0CF66FE5B9F4F55D10ED38B0BCF1A4BEC3 | |||
| 3900 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF19431a.TMP | text | |
MD5:46DCF7DB72970F06A3B4803F7064C6E6 | SHA256:179243BCC118729AE487E1CADCF2C0976413903B97CF5B5DA985D0D60B60716A | |||
| 3900 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old | text | |
MD5:EBECE2BDCF7A0206932028EE2E294E94 | SHA256:A83229A1A2D897DB7C7AA22DE86ADC931DB0445F7400DE6D1AE00003711906A9 | |||
| 3900 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF1948d6.TMP | — | |
MD5:— | SHA256:— | |||
| 3900 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
13
TCP/UDP connections
62
DNS requests
38
Threats
32
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
860 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acvebl5hyowh6yyy3wmoaw5wbfpa_4.10.2830.100/oimompecagnajdejgnnjijobebaeigek_4.10.2830.100_win32_acmfn7n2mz6vs4wnlypsmq4uakaq.crx3 | unknown | — | — | whitelisted |
860 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acvebl5hyowh6yyy3wmoaw5wbfpa_4.10.2830.100/oimompecagnajdejgnnjijobebaeigek_4.10.2830.100_win32_acmfn7n2mz6vs4wnlypsmq4uakaq.crx3 | unknown | — | — | whitelisted |
860 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acvebl5hyowh6yyy3wmoaw5wbfpa_4.10.2830.100/oimompecagnajdejgnnjijobebaeigek_4.10.2830.100_win32_acmfn7n2mz6vs4wnlypsmq4uakaq.crx3 | unknown | — | — | whitelisted |
860 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acvebl5hyowh6yyy3wmoaw5wbfpa_4.10.2830.100/oimompecagnajdejgnnjijobebaeigek_4.10.2830.100_win32_acmfn7n2mz6vs4wnlypsmq4uakaq.crx3 | unknown | — | — | whitelisted |
860 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acvebl5hyowh6yyy3wmoaw5wbfpa_4.10.2830.100/oimompecagnajdejgnnjijobebaeigek_4.10.2830.100_win32_acmfn7n2mz6vs4wnlypsmq4uakaq.crx3 | unknown | — | — | whitelisted |
860 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acvebl5hyowh6yyy3wmoaw5wbfpa_4.10.2830.100/oimompecagnajdejgnnjijobebaeigek_4.10.2830.100_win32_acmfn7n2mz6vs4wnlypsmq4uakaq.crx3 | unknown | — | — | whitelisted |
860 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acvebl5hyowh6yyy3wmoaw5wbfpa_4.10.2830.100/oimompecagnajdejgnnjijobebaeigek_4.10.2830.100_win32_acmfn7n2mz6vs4wnlypsmq4uakaq.crx3 | unknown | — | — | whitelisted |
860 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acvebl5hyowh6yyy3wmoaw5wbfpa_4.10.2830.100/oimompecagnajdejgnnjijobebaeigek_4.10.2830.100_win32_acmfn7n2mz6vs4wnlypsmq4uakaq.crx3 | unknown | — | — | whitelisted |
860 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acvebl5hyowh6yyy3wmoaw5wbfpa_4.10.2830.100/oimompecagnajdejgnnjijobebaeigek_4.10.2830.100_win32_acmfn7n2mz6vs4wnlypsmq4uakaq.crx3 | unknown | — | — | whitelisted |
860 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acvebl5hyowh6yyy3wmoaw5wbfpa_4.10.2830.100/oimompecagnajdejgnnjijobebaeigek_4.10.2830.100_win32_acmfn7n2mz6vs4wnlypsmq4uakaq.crx3 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 224.0.0.252:5355 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
3900 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
2400 | chrome.exe | 31.216.144.5:443 | mega.nz | Datacenter Luxembourg S.A. | LU | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | whitelisted |
2400 | chrome.exe | 173.194.76.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
2400 | chrome.exe | 216.58.206.74:443 | content-autofill.googleapis.com | GOOGLE | US | whitelisted |
2400 | chrome.exe | 89.44.169.134:443 | eu.static.mega.co.nz | Datacenter Luxembourg S.A. | LU | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2400 | chrome.exe | 66.203.125.11:443 | g.api.mega.co.nz | Datacenter Luxembourg S.A. | LU | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
mega.nz |
| whitelisted |
accounts.google.com |
| whitelisted |
content-autofill.googleapis.com |
| whitelisted |
eu.static.mega.co.nz |
| whitelisted |
g.api.mega.co.nz |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
www.google.com |
| whitelisted |
gfs270n461.userstorage.mega.co.nz |
| unknown |
gfs206n461.userstorage.mega.co.nz |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2400 | chrome.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (mega .nz) |
2400 | chrome.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (mega .nz) |
2400 | chrome.exe | Misc activity | ET FILE_SHARING File Sharing Domain Observed in TLS SNI (mega .nz) |
2400 | chrome.exe | Misc activity | ET FILE_SHARING Observed DNS Query to Filesharing Service (mega .co .nz) |
2400 | chrome.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (mega .nz) |
2400 | chrome.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (mega .nz) |
2400 | chrome.exe | Misc activity | ET FILE_SHARING File Sharing Domain Observed in TLS SNI (mega .nz) |
2400 | chrome.exe | Misc activity | ET FILE_SHARING File Sharing Domain Observed in TLS SNI (mega .nz) |
2400 | chrome.exe | Misc activity | ET FILE_SHARING Observed DNS Query to Filesharing Service (mega .co .nz) |
2400 | chrome.exe | Misc activity | ET FILE_SHARING Observed DNS Query to Filesharing Service (mega .co .nz) |