| File name: | Özel Dosyalar.exe |
| Full analysis: | https://app.any.run/tasks/545f7300-bed8-47a4-b16c-59ff4bea71ab |
| Verdict: | Malicious activity |
| Analysis date: | August 27, 2018, 17:45:09 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed |
| MD5: | 3975D7F4543ED0EB25CD2E7932A99A1F |
| SHA1: | D6EA775D54CD944CC62760423396AFE6C9BDBF93 |
| SHA256: | A97A50B06946E7D8352360F1AE24973A446A5CACA508ADE38F8B5797982419DA |
| SSDEEP: | 1536:wZx8gcK8ossZDulaPnPuhkvJJth5SLnouy8uQkgB54vm:wZx8gJscuAnU+JYoutueXl |
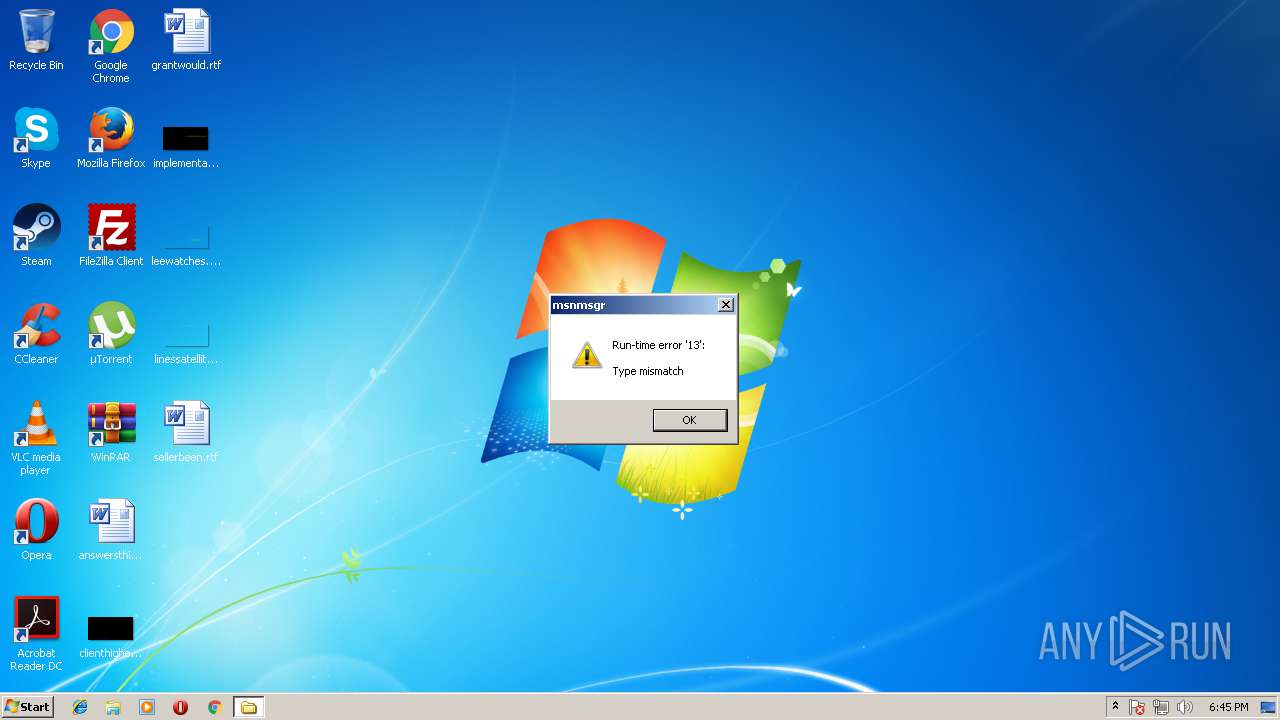
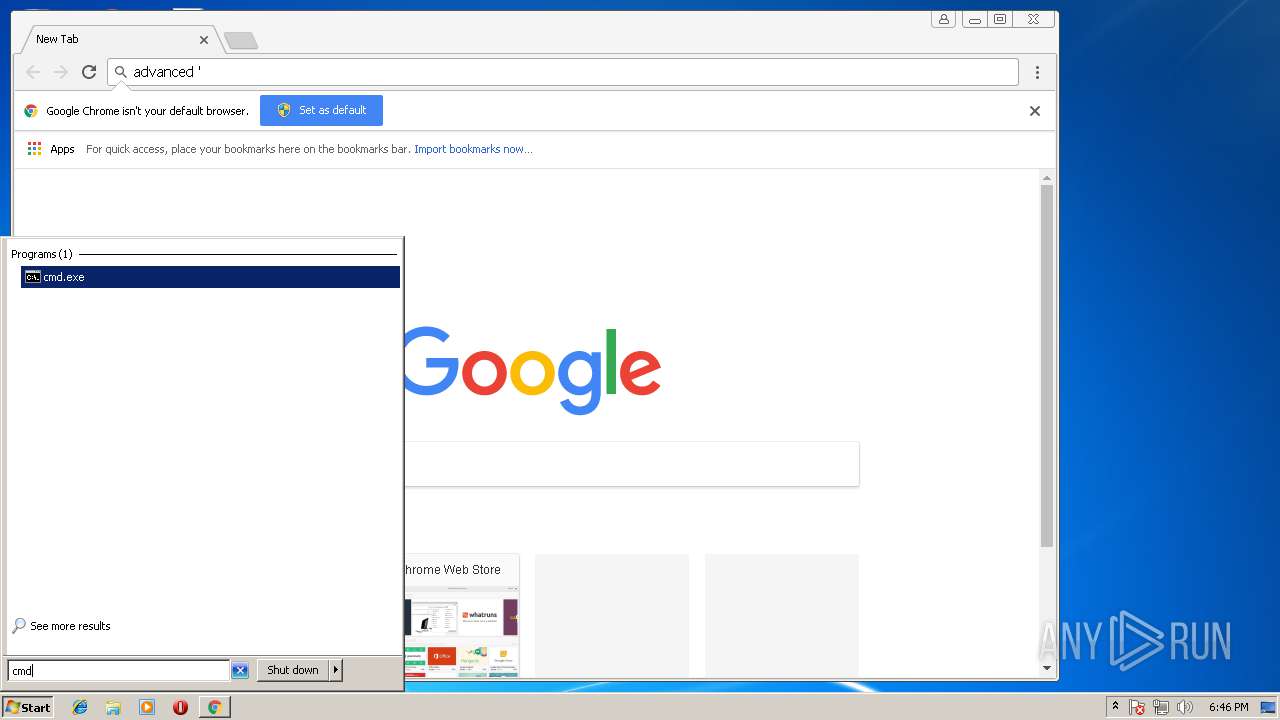
MALICIOUS
UAC/LUA settings modification
- Özel Dosyalar.exe (PID: 2440)
- MusaLLaT.exe (PID: 2076)
Changes the autorun value in the registry
- MusaLLaT.exe (PID: 2076)
SUSPICIOUS
Creates files in the user directory
- Özel Dosyalar.exe (PID: 2440)
- MusaLLaT.exe (PID: 2076)
Executable content was dropped or overwritten
- Özel Dosyalar.exe (PID: 2440)
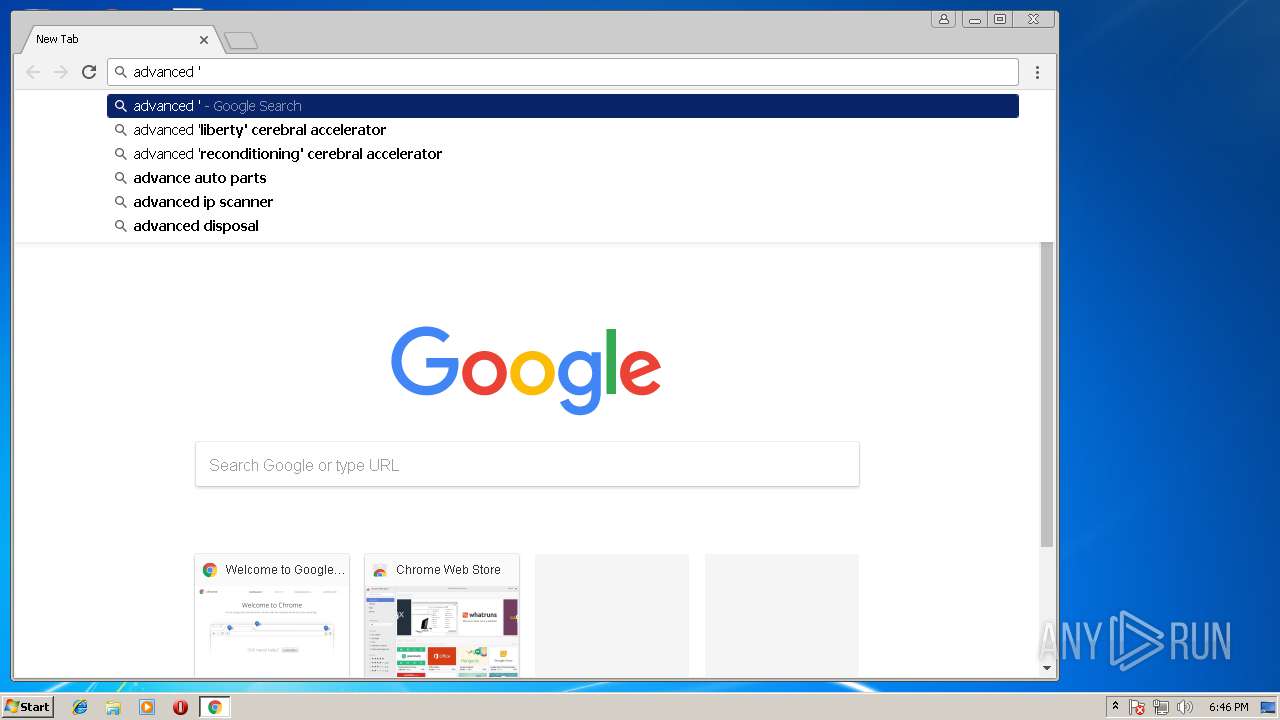
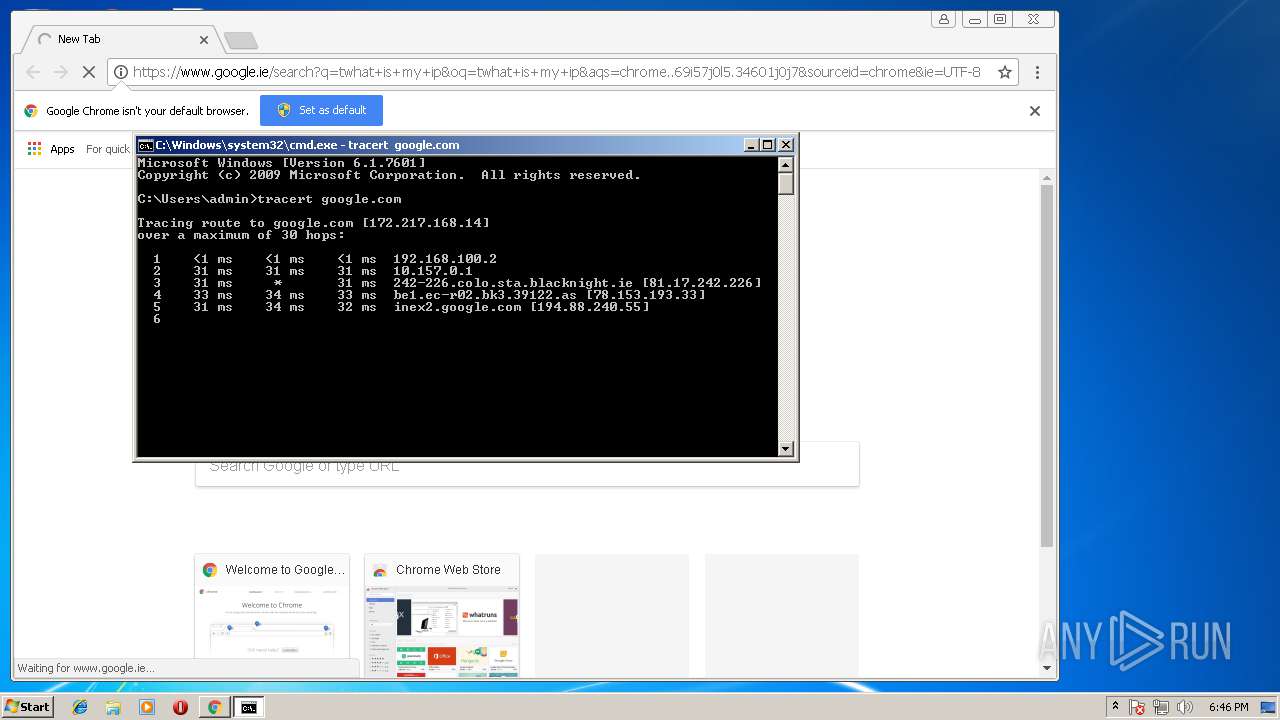
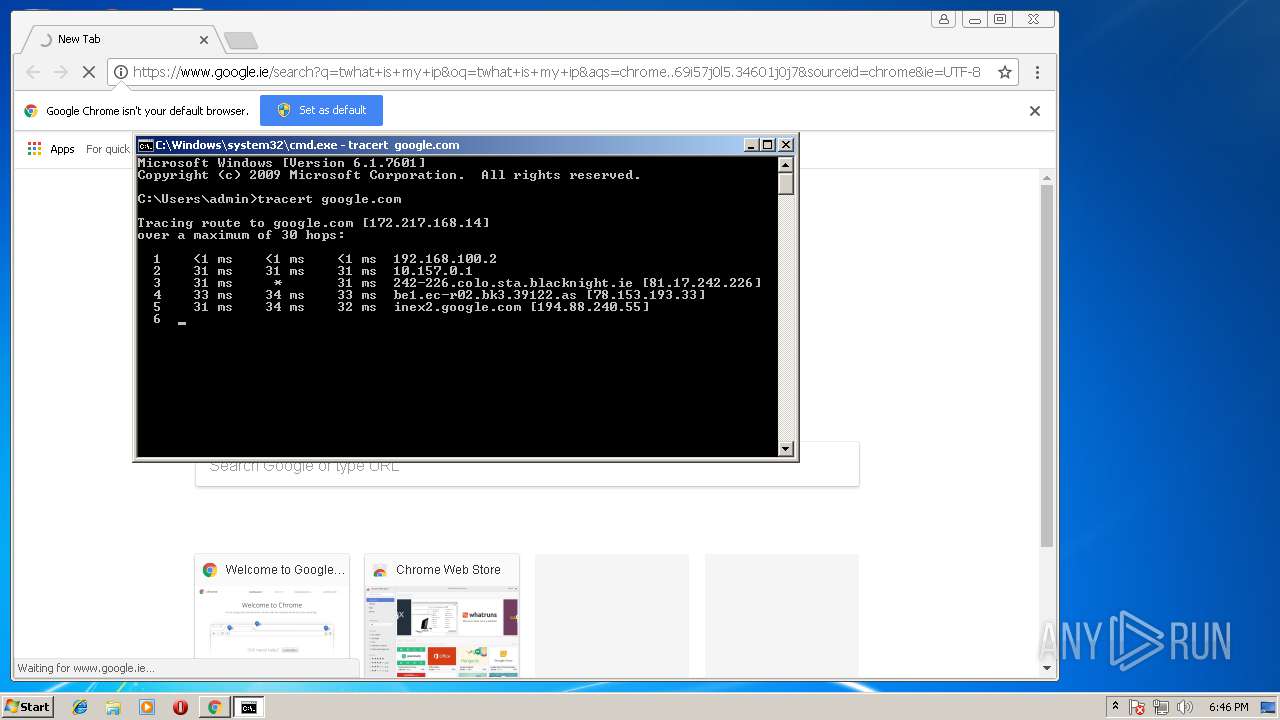
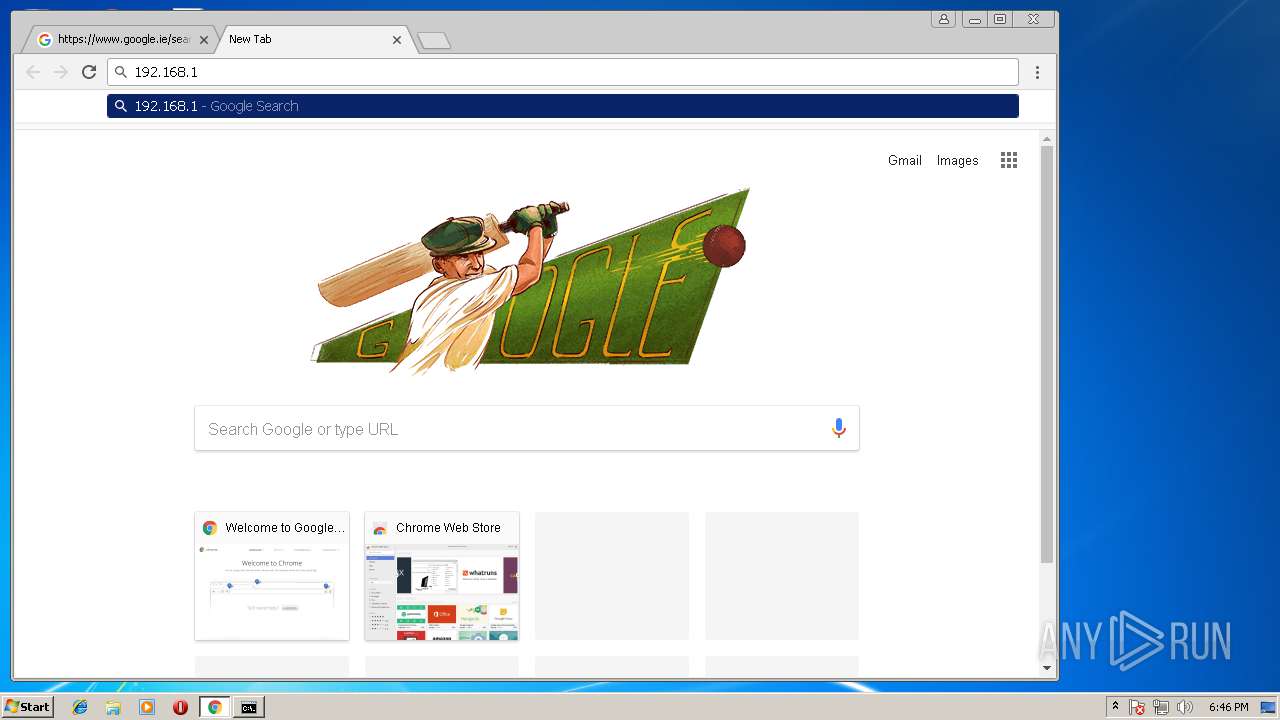
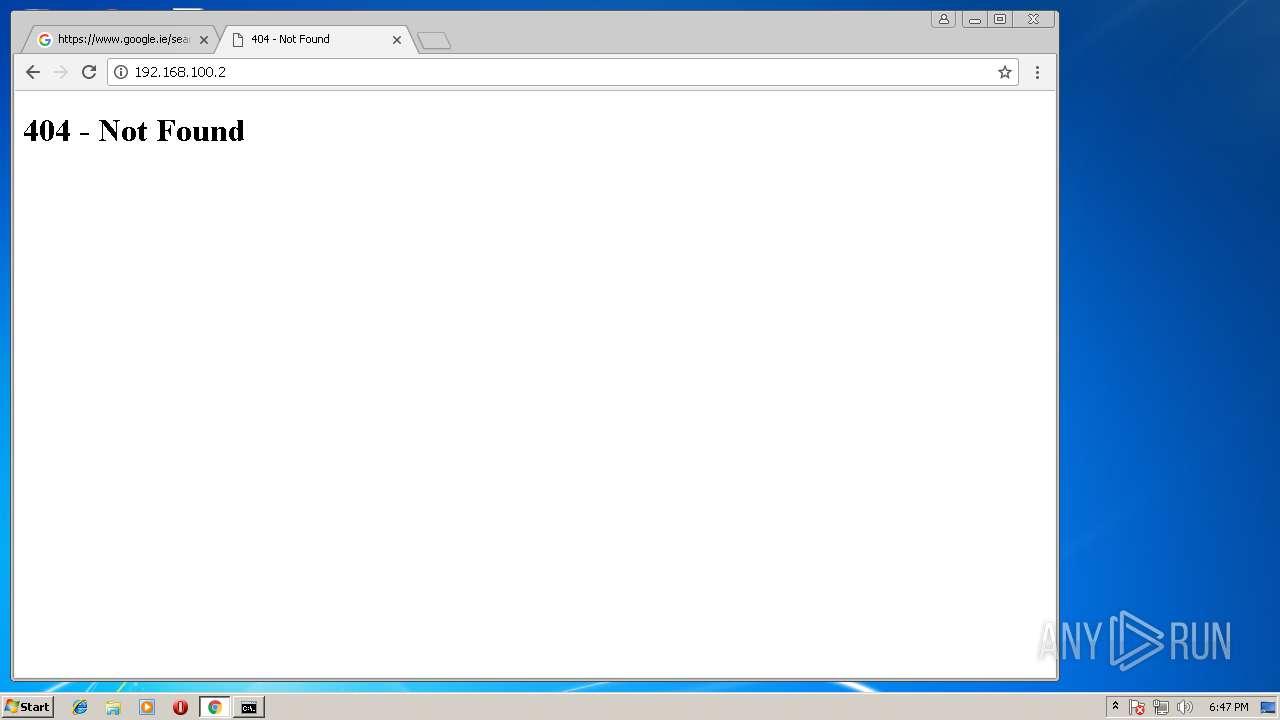
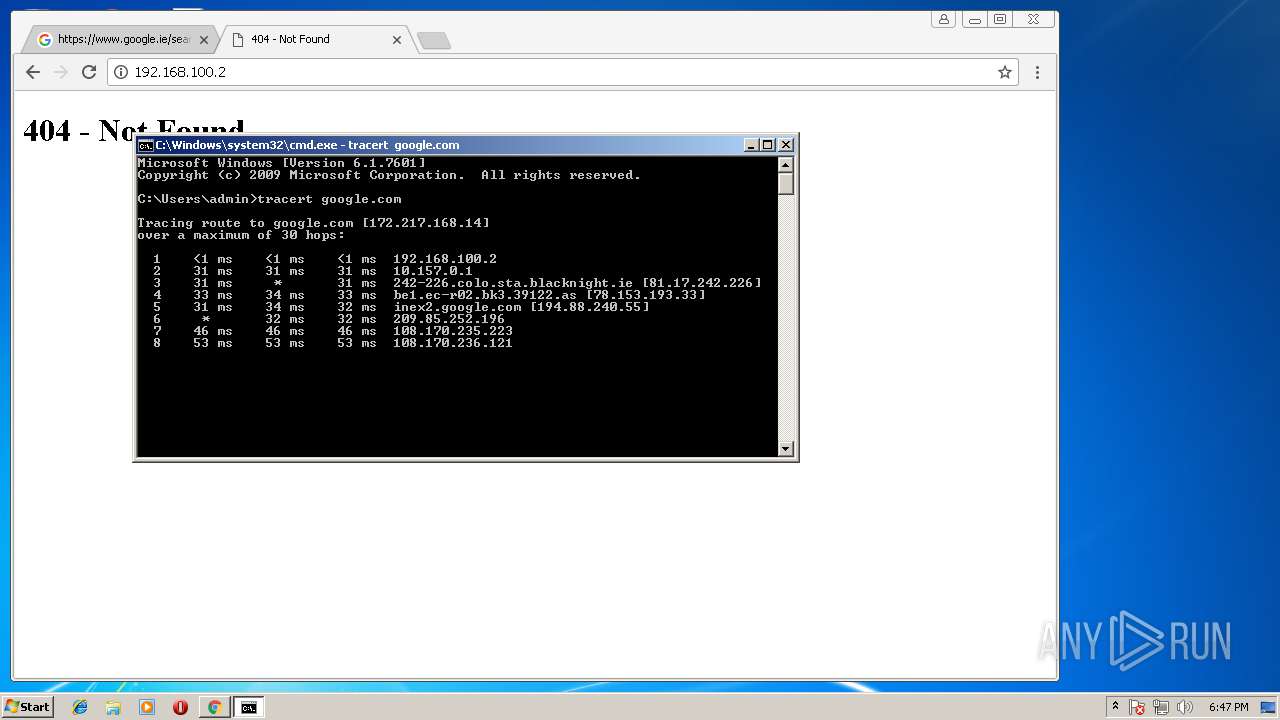
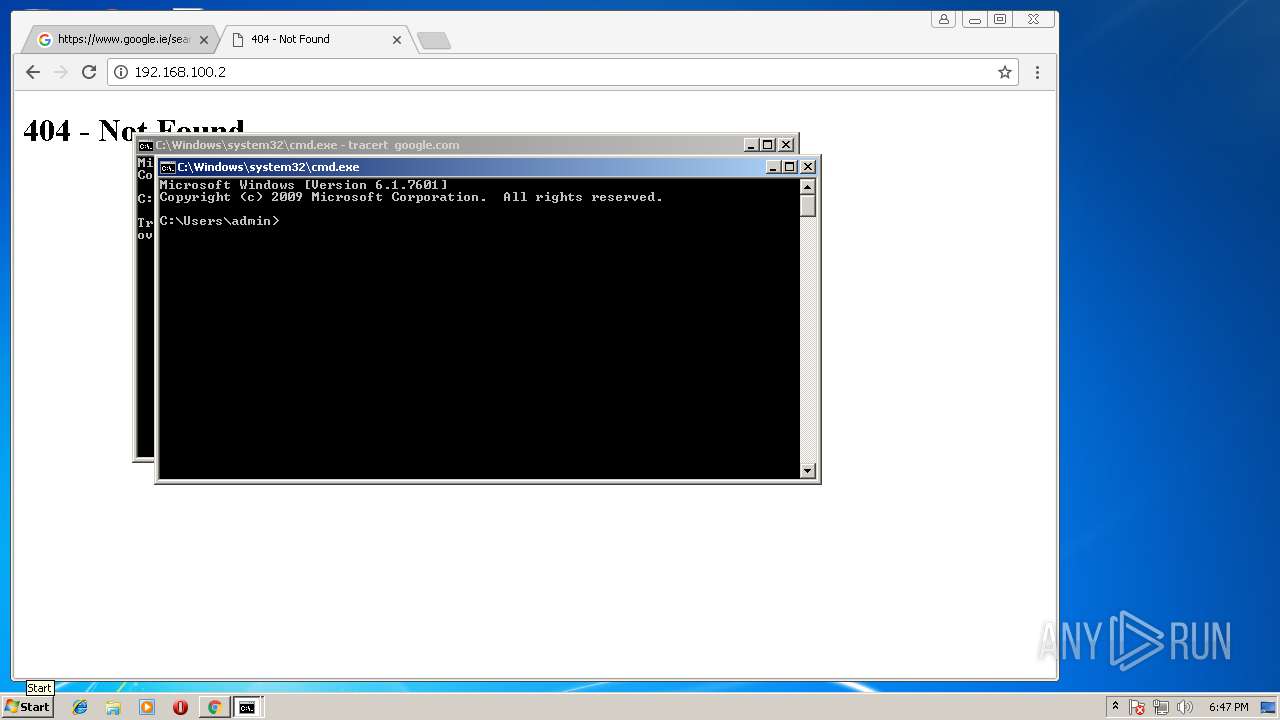
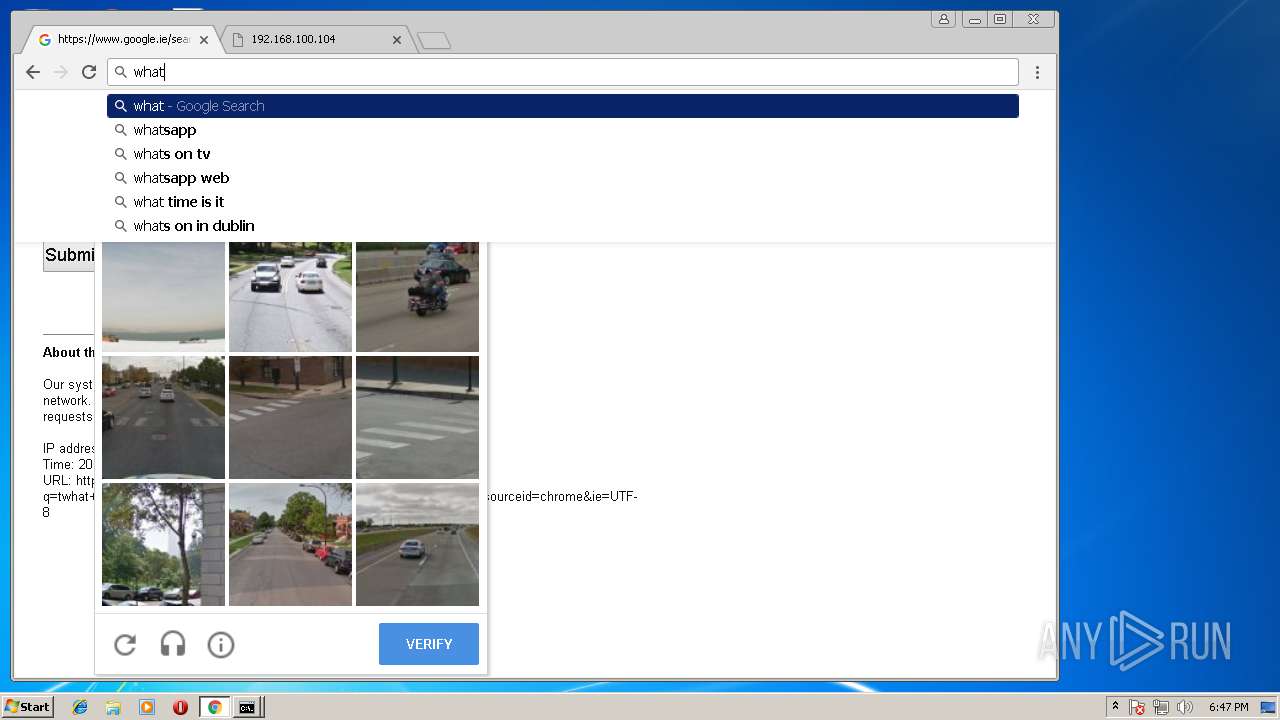
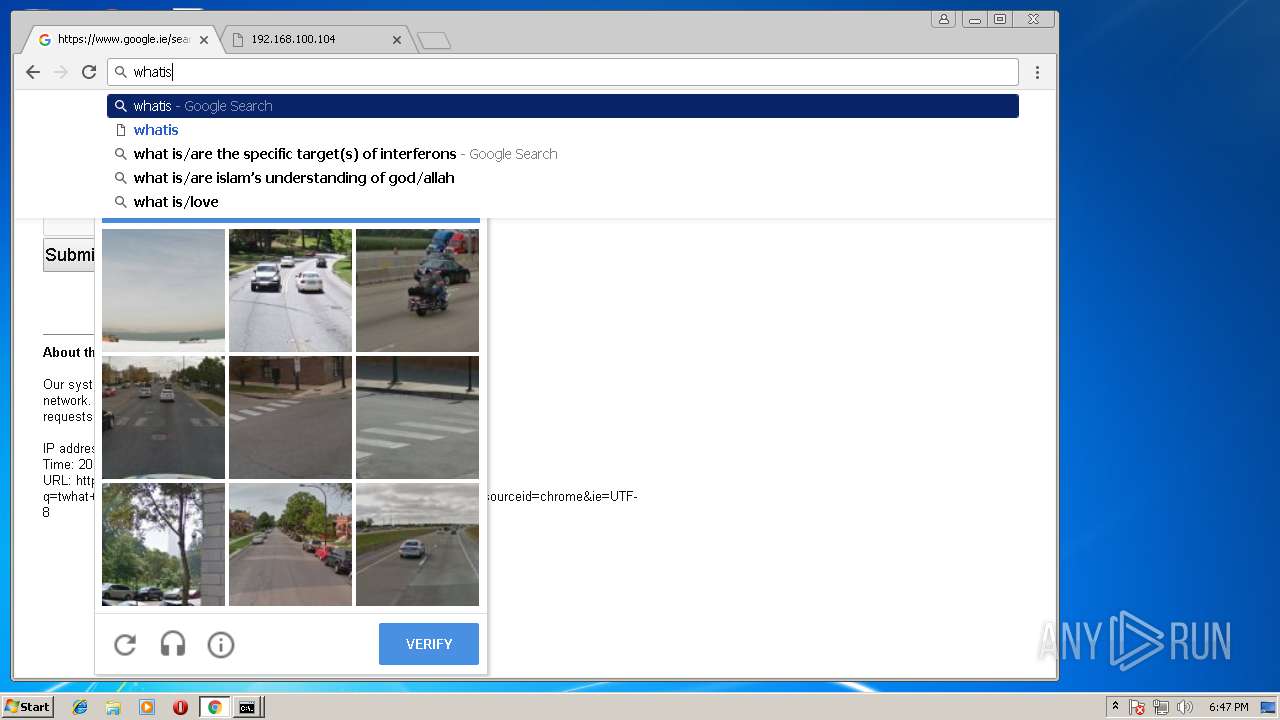
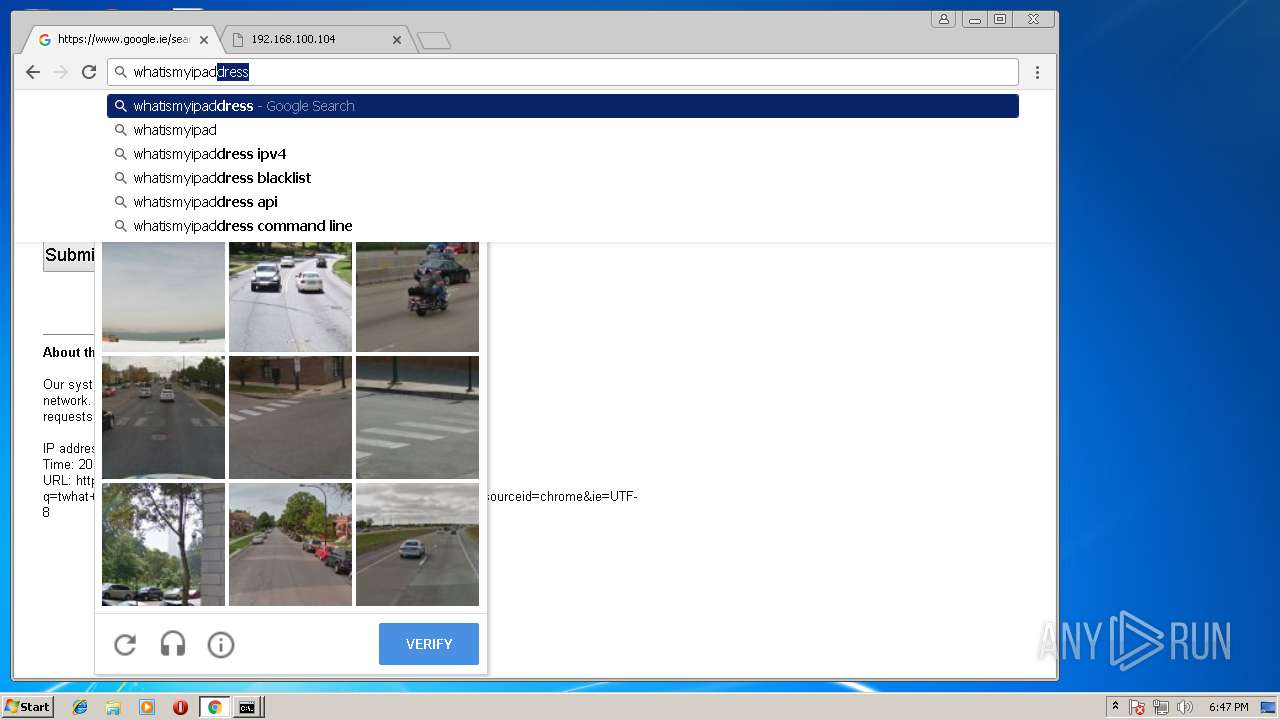
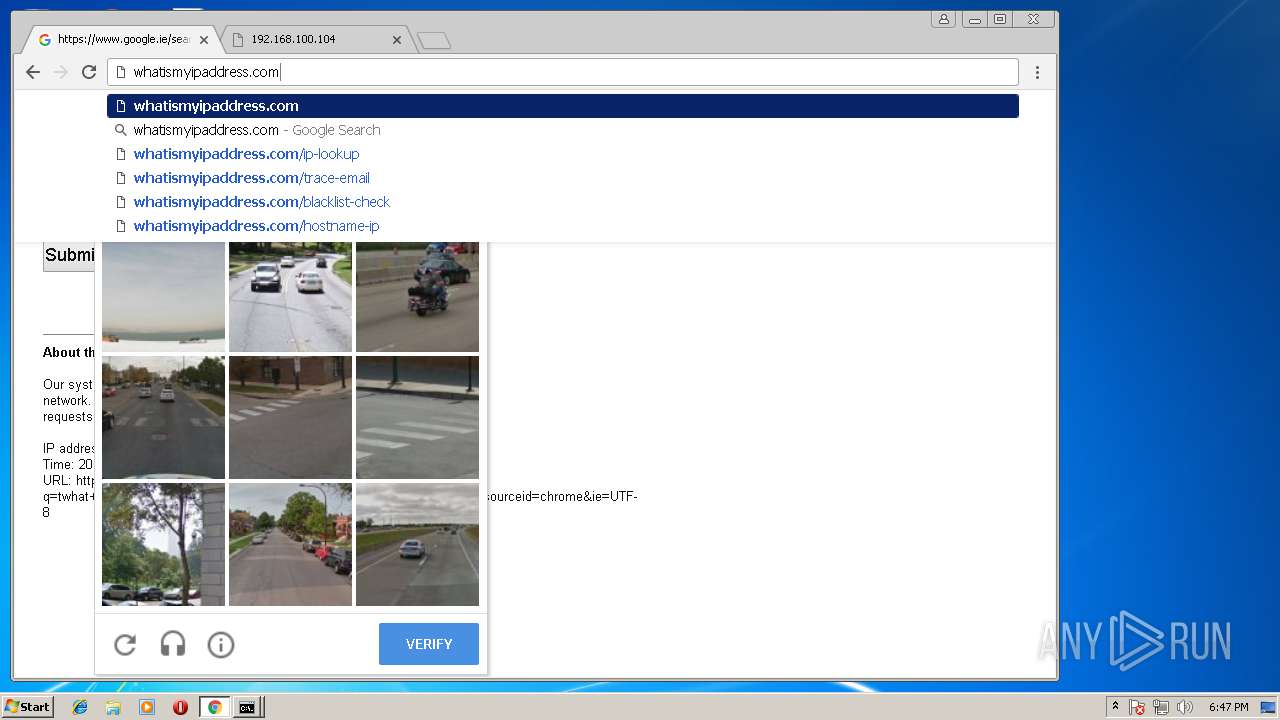
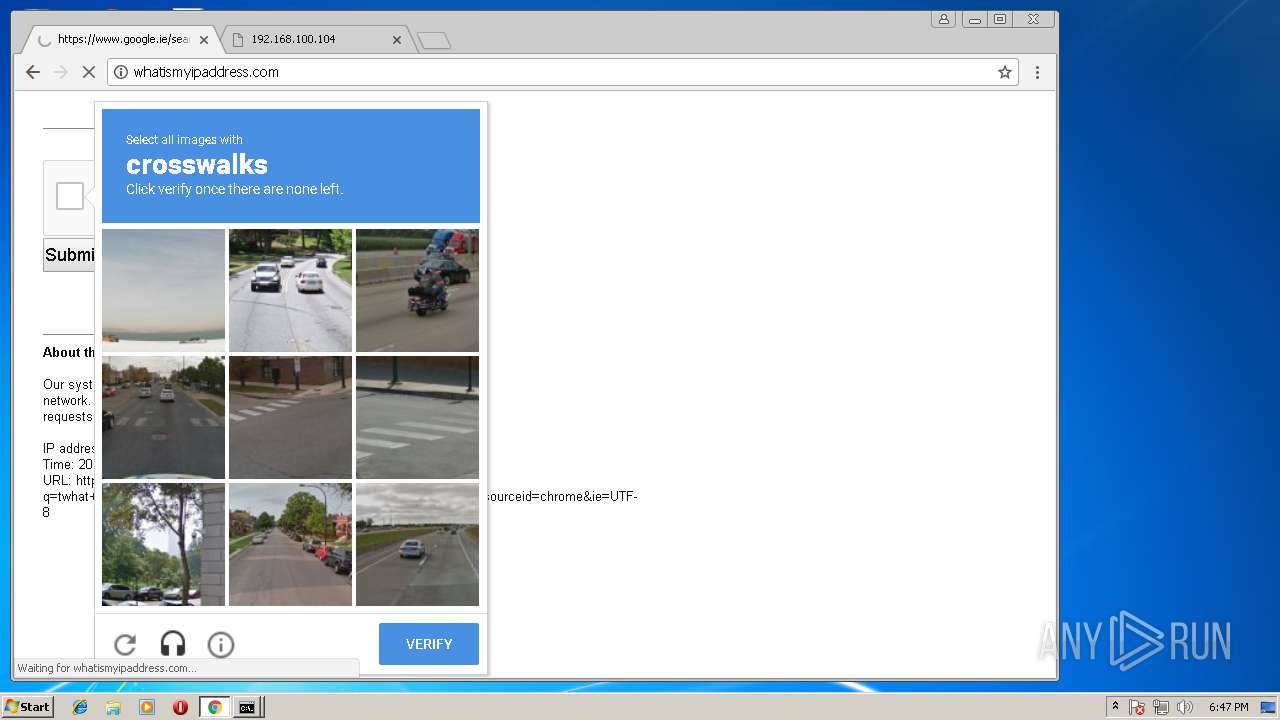
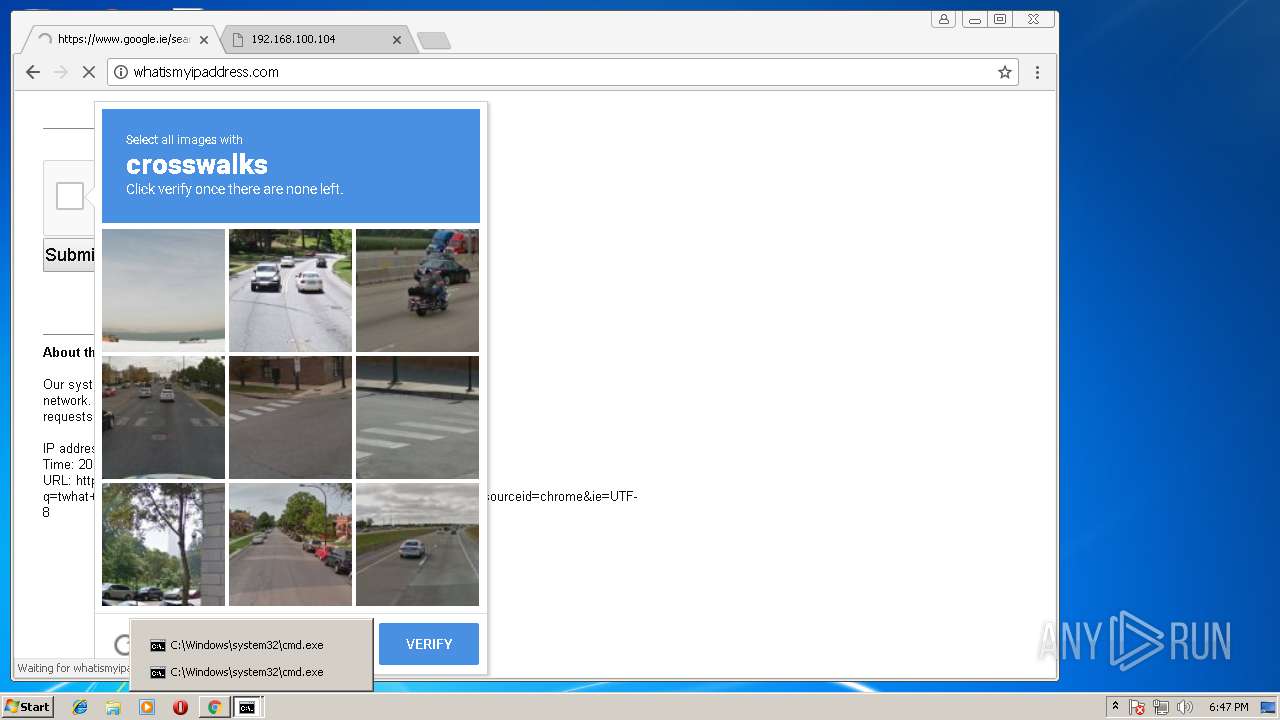
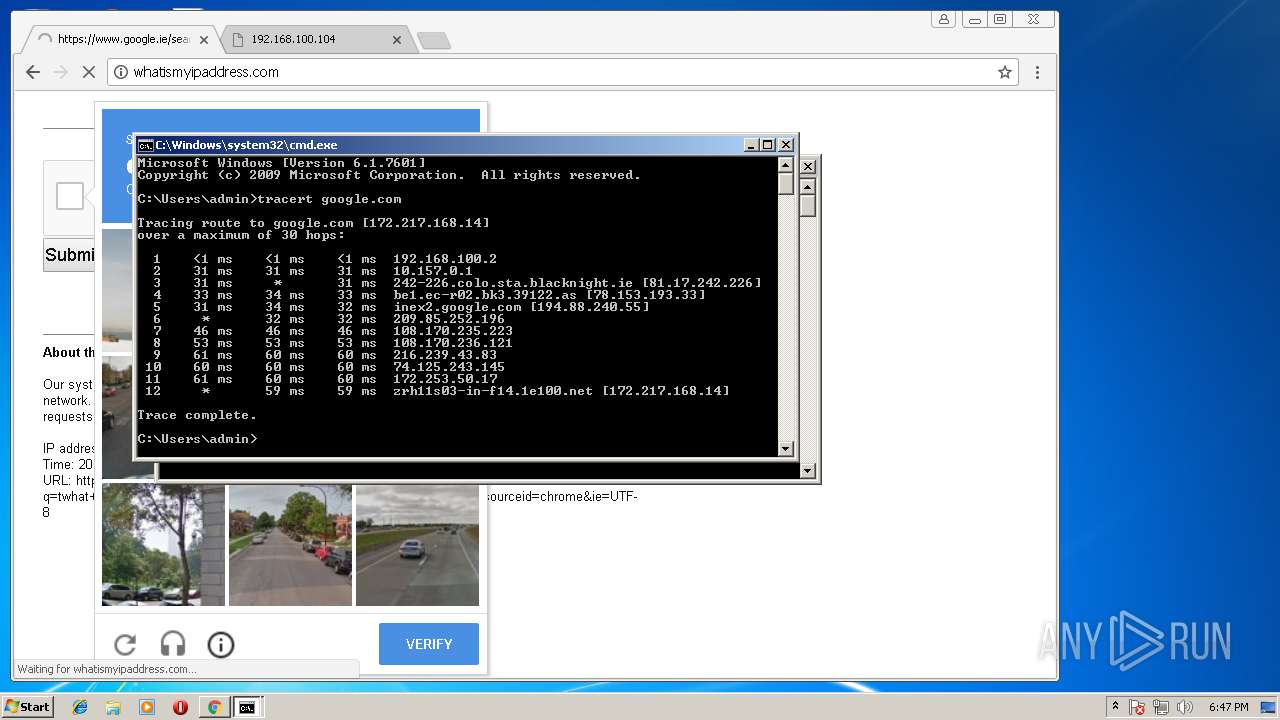
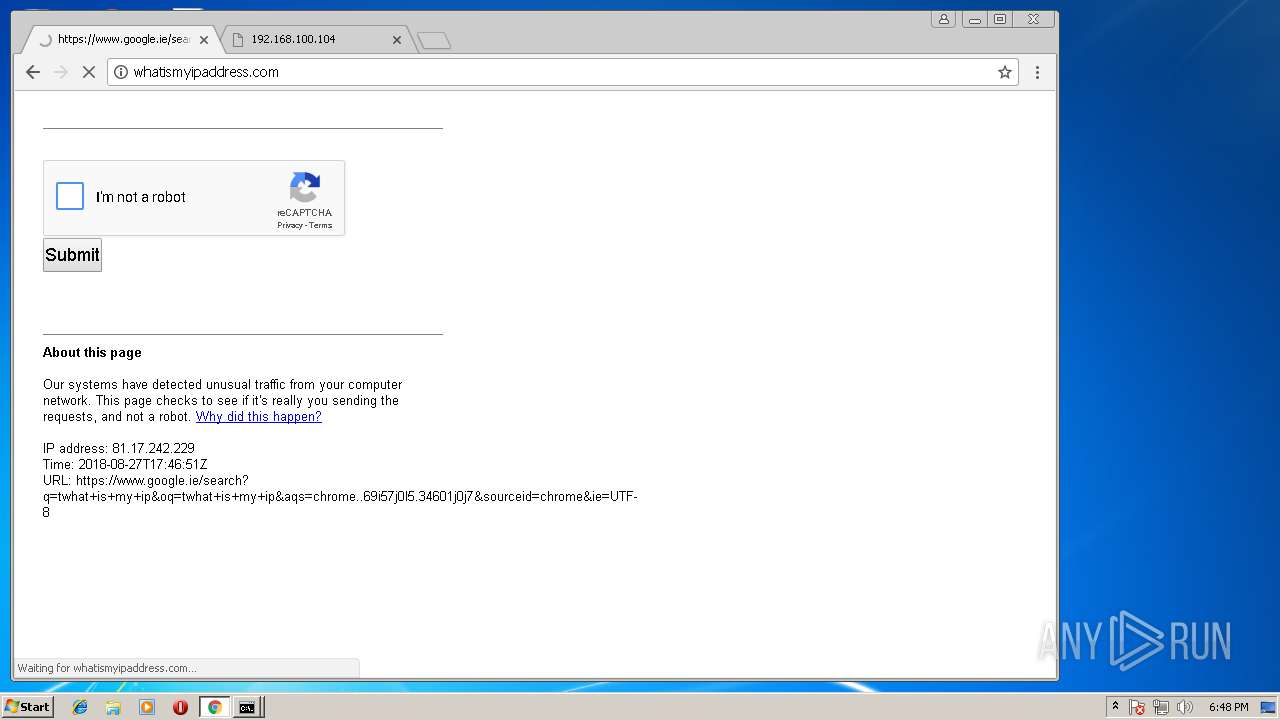
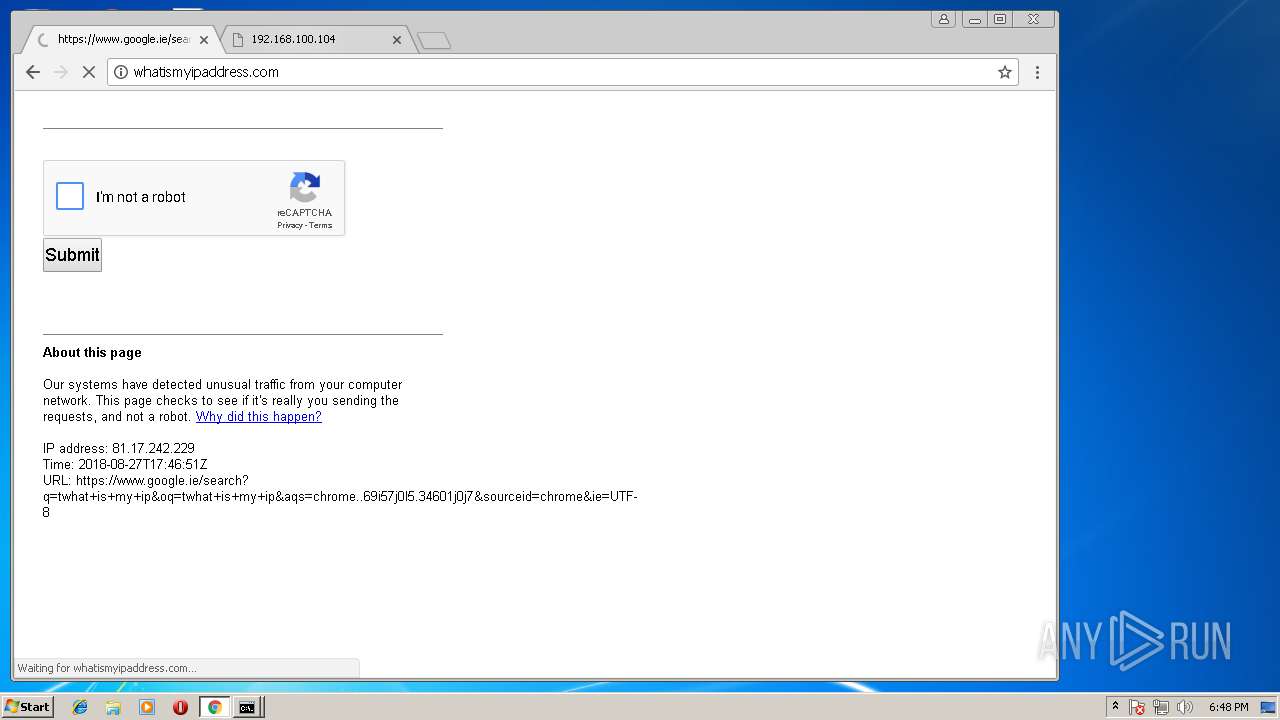
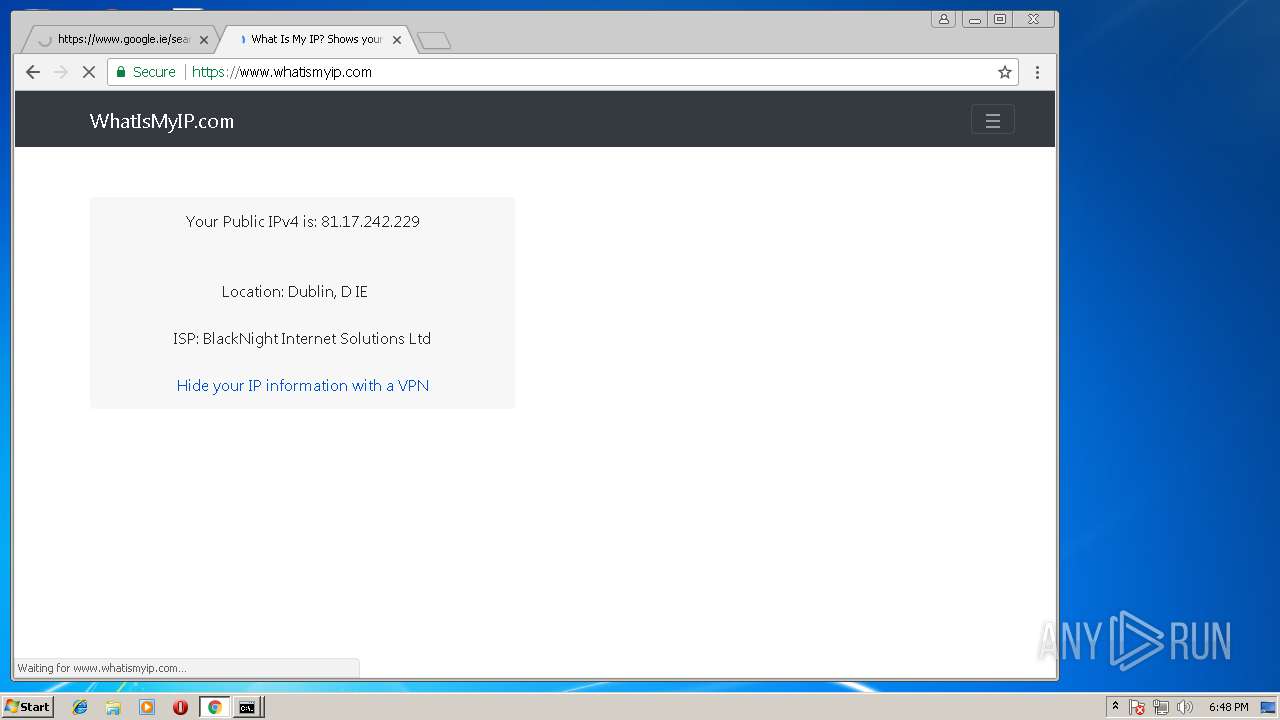
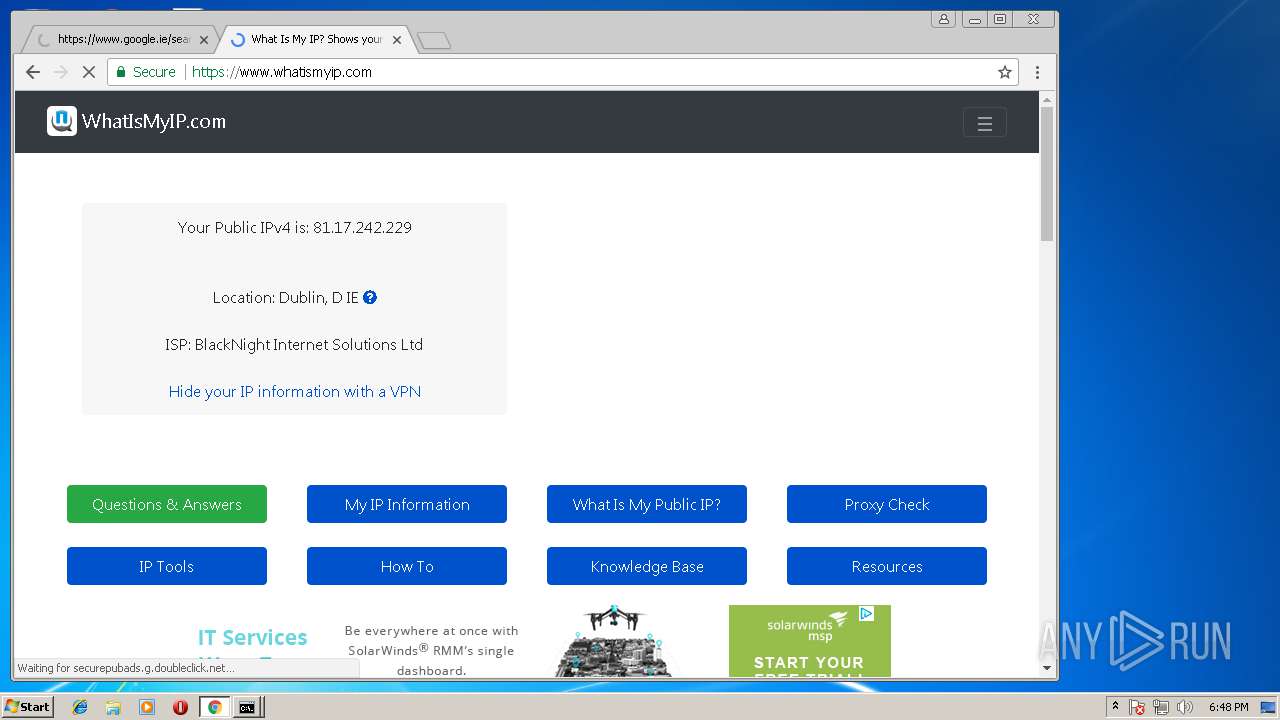
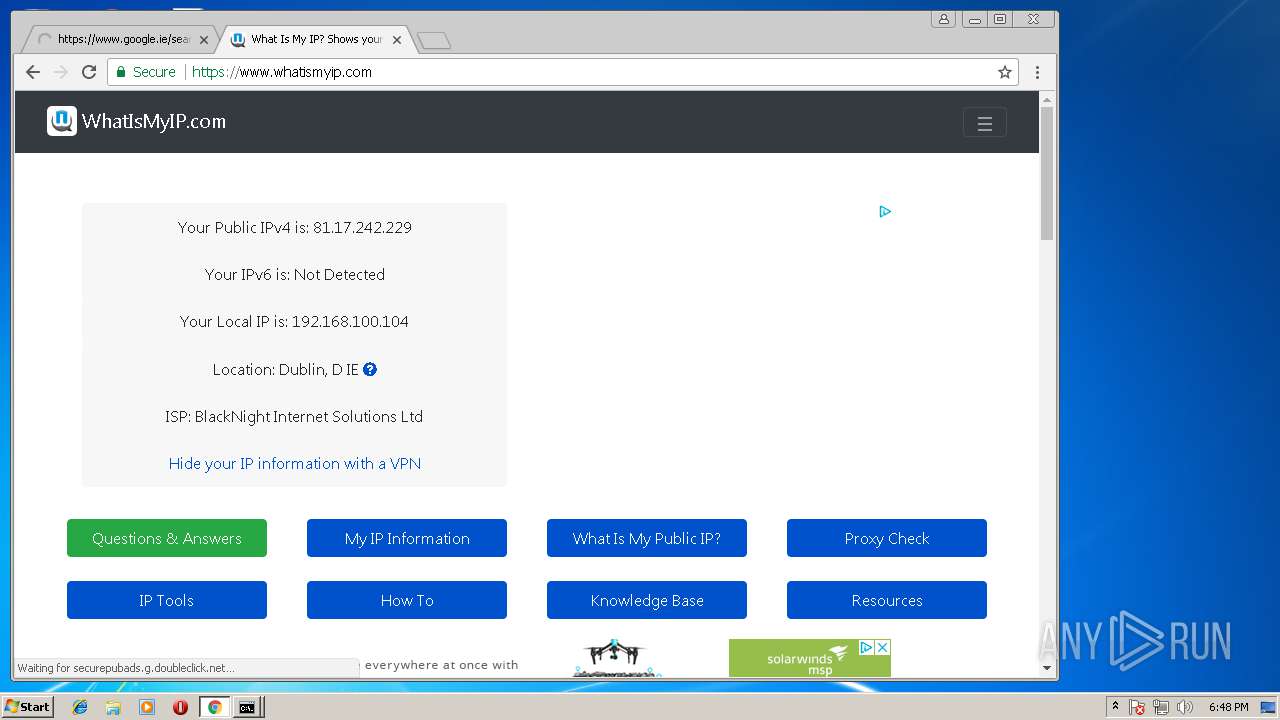
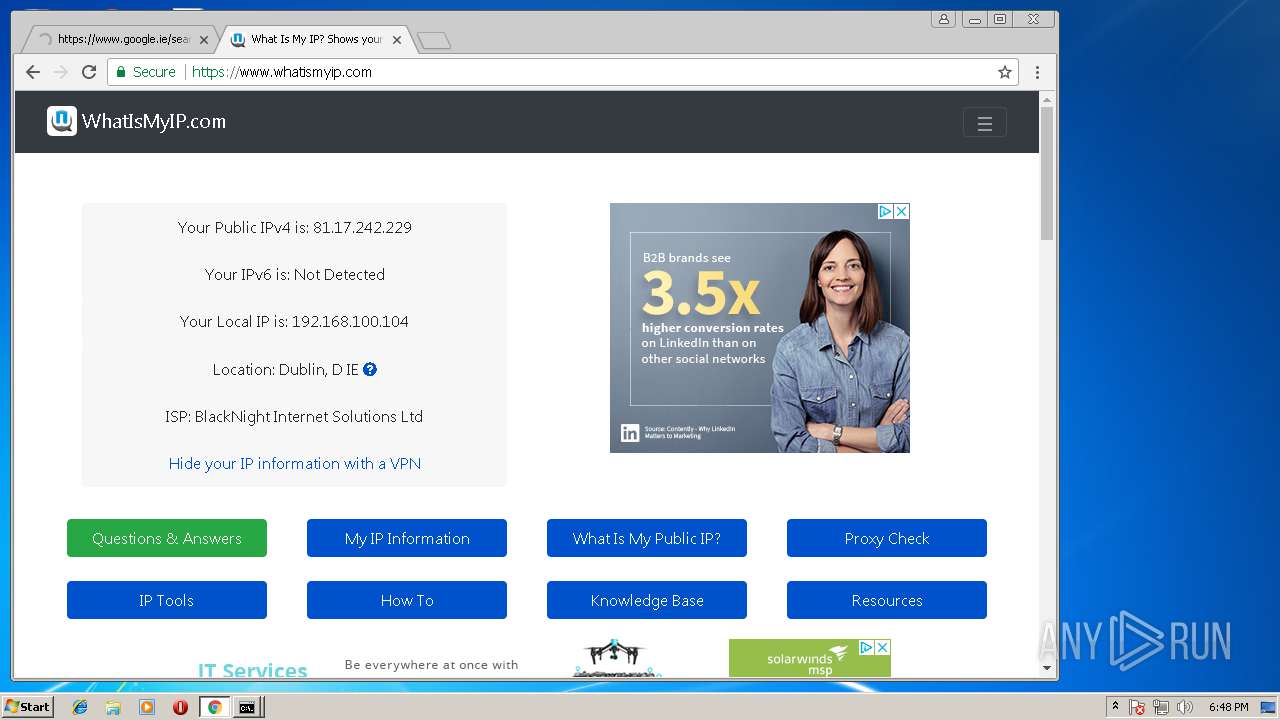
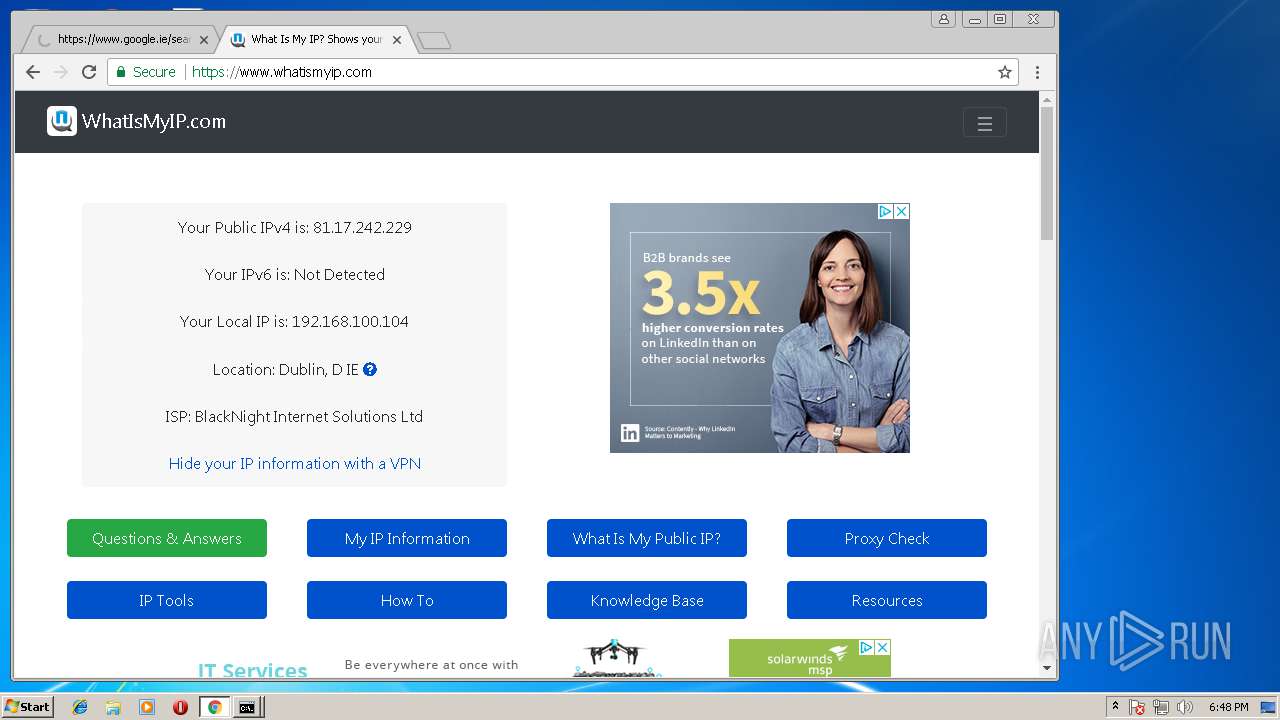
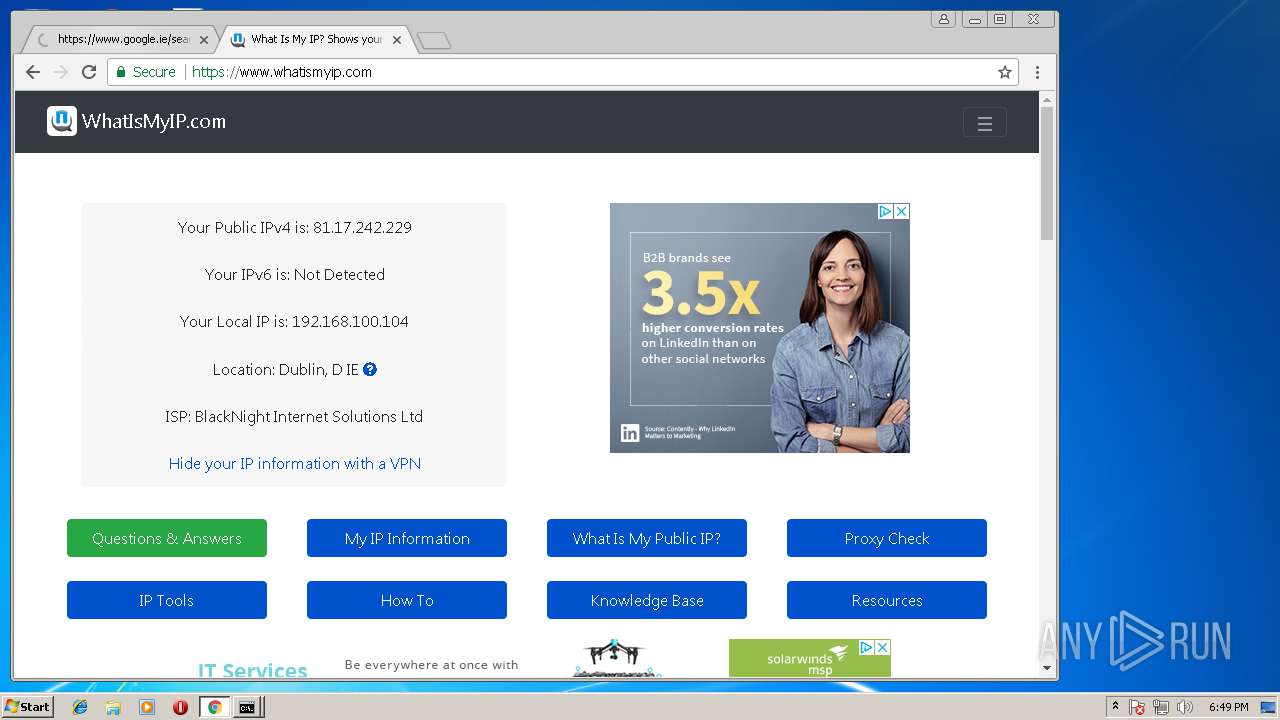
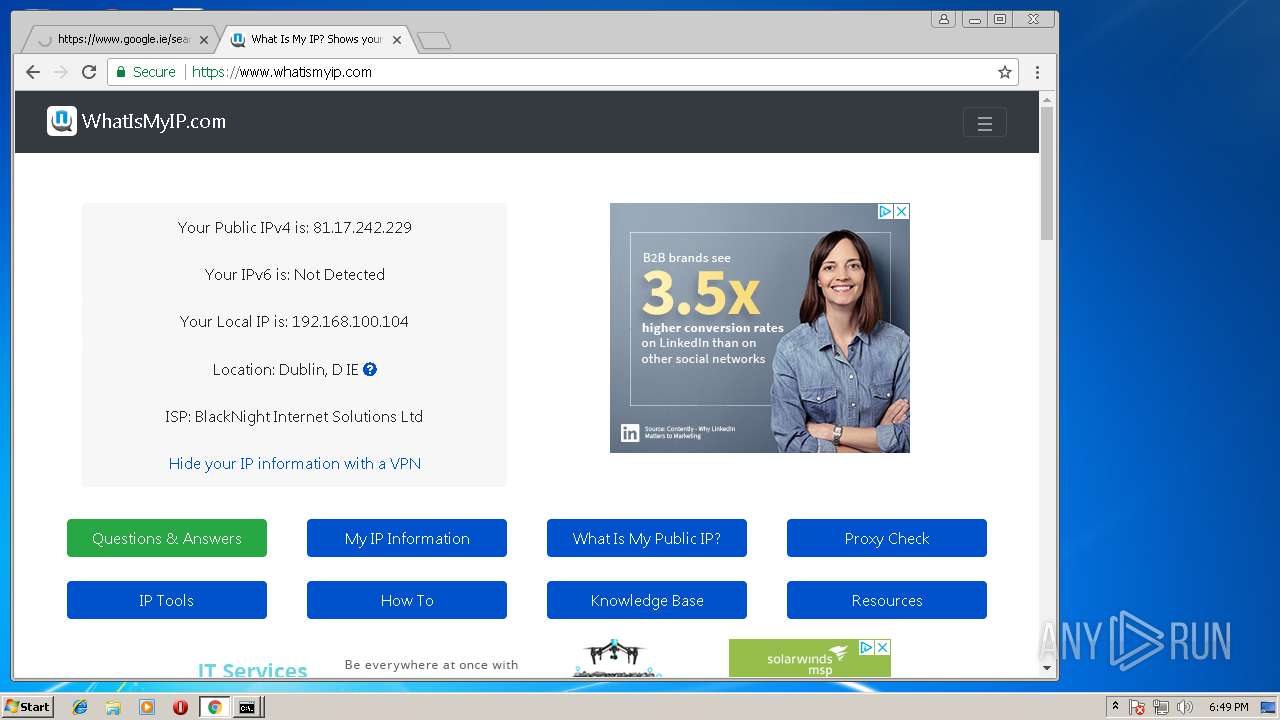
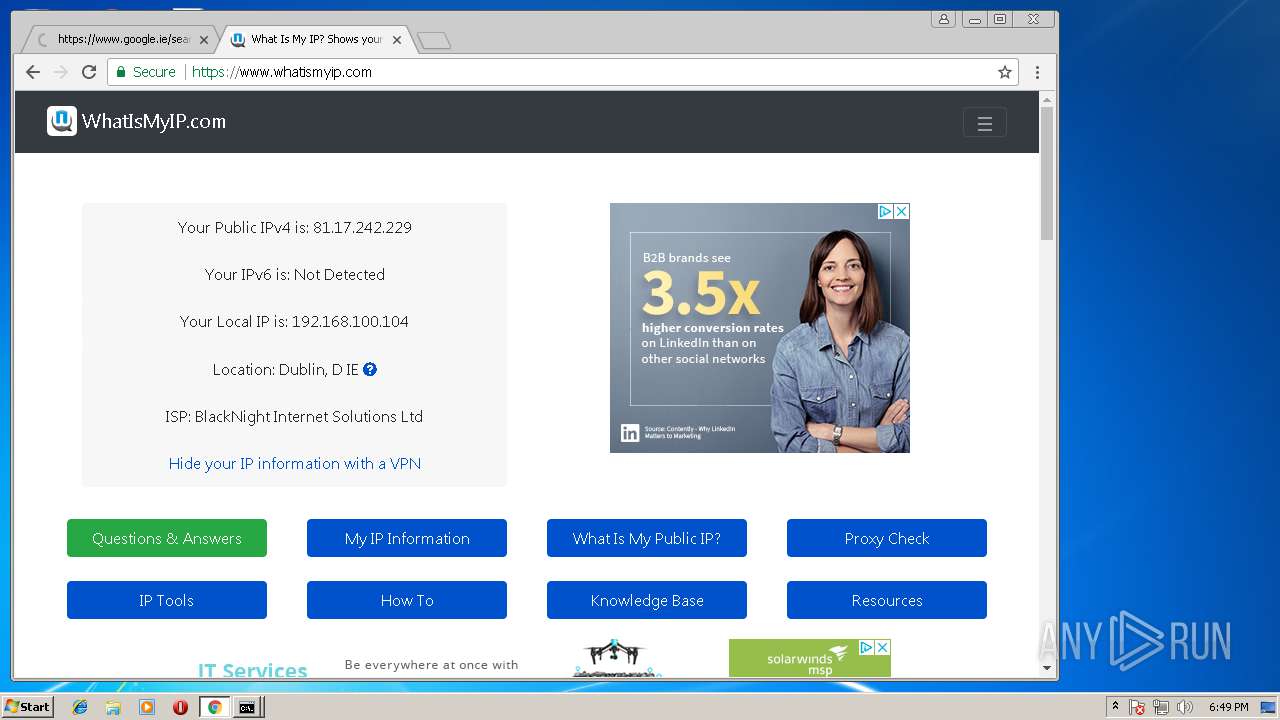
Checks for external IP
- chrome.exe (PID: 1504)
INFO
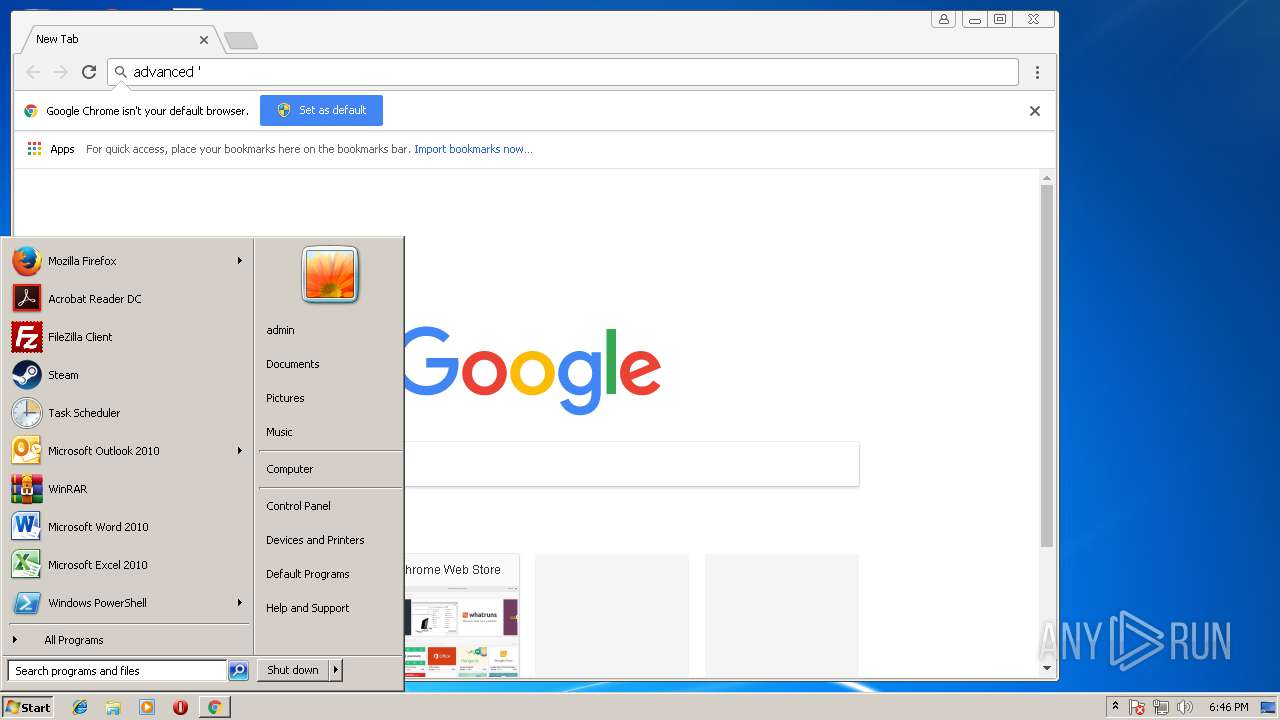
Application launched itself
- chrome.exe (PID: 1504)
Dropped object may contain URL's
- chrome.exe (PID: 1504)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (39.3) |
|---|---|---|
| .exe | | | Win32 EXE Yoda's Crypter (38.6) |
| .dll | | | Win32 Dynamic Link Library (generic) (9.5) |
| .exe | | | Win32 Executable (generic) (6.5) |
| .exe | | | Generic Win/DOS Executable (2.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2011:01:04 14:49:16+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 53248 |
| InitializedDataSize: | 81920 |
| UninitializedDataSize: | 434176 |
| EntryPoint: | 0x76580 |
| OSVersion: | 4 |
| ImageVersion: | 8.1 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 8.1.0.8 |
| ProductVersionNumber: | 8.1.0.8 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| ProductName: | z 3 r 0 _ x |
| FileVersion: | 8.01.0008 |
| ProductVersion: | 8.01.0008 |
| InternalName: | Dosya Klasörü |
| OriginalFileName: | Dosya Klasörü.exe |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 04-Jan-2011 13:49:16 |
| Detected languages: |
|
| ProductName: | z 3 r 0 _ x |
| FileVersion: | 8.01.0008 |
| ProductVersion: | 8.01.0008 |
| InternalName: | Dosya Klasörü |
| OriginalFilename: | Dosya Klasörü.exe |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000C8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 04-Jan-2011 13:49:16 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
UPX0 | 0x00001000 | 0x0006A000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
UPX1 | 0x0006B000 | 0x0000D000 | 0x0000C200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.97316 |
.rsrc | 0x00078000 | 0x00029000 | 0x00013C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.97945 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.30813 | 520 | Unicode (UTF 16LE) | English - United States | RT_VERSION |
30001 | 2.7552 | 1640 | Unicode (UTF 16LE) | UNKNOWN | RT_ICON |
30002 | 3.07781 | 744 | Unicode (UTF 16LE) | UNKNOWN | RT_ICON |
30003 | 3.31077 | 296 | Unicode (UTF 16LE) | UNKNOWN | RT_ICON |
30004 | 3.84352 | 3752 | Unicode (UTF 16LE) | UNKNOWN | RT_ICON |
30005 | 3.91649 | 2216 | Unicode (UTF 16LE) | UNKNOWN | RT_ICON |
30006 | 3.98653 | 1736 | Unicode (UTF 16LE) | UNKNOWN | RT_ICON |
30007 | 3.84672 | 1384 | Unicode (UTF 16LE) | UNKNOWN | RT_ICON |
30008 | 3.313 | 9640 | Unicode (UTF 16LE) | UNKNOWN | RT_ICON |
30009 | 3.78865 | 4264 | Unicode (UTF 16LE) | UNKNOWN | RT_ICON |
Imports
KERNEL32.DLL |
MSVBVM60.DLL |
Total processes
63
Monitored processes
29
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 348 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1760,267841884714280811,13333328326167706721,131072 --service-pipe-token=E7BE99EDAB36C41120AE6773EBF14E3F --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --enable-pinch --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --content-image-texture-target=0,0,3553;0,1,3553;0,2,3553;0,3,3553;0,4,3553;0,5,3553;0,6,3553;0,7,3553;0,8,3553;0,9,3553;0,10,3553;0,11,3553;0,12,3553;0,13,3553;0,14,3553;0,15,3553;0,16,3553;0,17,3553;1,0,3553;1,1,3553;1,2,3553;1,3,3553;1,4,3553;1,5,3553;1,6,3553;1,7,3553;1,8,3553;1,9,3553;1,10,3553;1,11,3553;1,12,3553;1,13,3553;1,14,3553;1,15,3553;1,16,3553;1,17,3553;2,0,3553;2,1,3553;2,2,3553;2,3,3553;2,4,3553;2,5,3553;2,6,3553;2,7,3553;2,8,3553;2,9,3553;2,10,3553;2,11,3553;2,12,3553;2,13,3553;2,14,3553;2,15,3553;2,16,3553;2,17,3553;3,0,3553;3,1,3553;3,2,3553;3,3,3553;3,4,3553;3,5,3553;3,6,3553;3,7,3553;3,8,3553;3,9,3553;3,10,3553;3,11,3553;3,12,3553;3,13,3553;3,14,3553;3,15,3553;3,16,3553;3,17,3553;4,0,3553;4,1,3553;4,2,3553;4,3,3553;4,4,3553;4,5,3553;4,6,3553;4,7,3553;4,8,3553;4,9,3553;4,10,3553;4,11,3553;4,12,3553;4,13,3553;4,14,3553;4,15,3553;4,16,3553;4,17,3553 --disable-accelerated-video-decode --disable-gpu-compositing --enable-gpu-async-worker-context --service-request-channel-token=E7BE99EDAB36C41120AE6773EBF14E3F --renderer-client-id=24 --mojo-platform-channel-handle=4248 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 61.0.3163.91 Modules
| |||||||||||||||
| 1504 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 61.0.3163.91 Modules
| |||||||||||||||
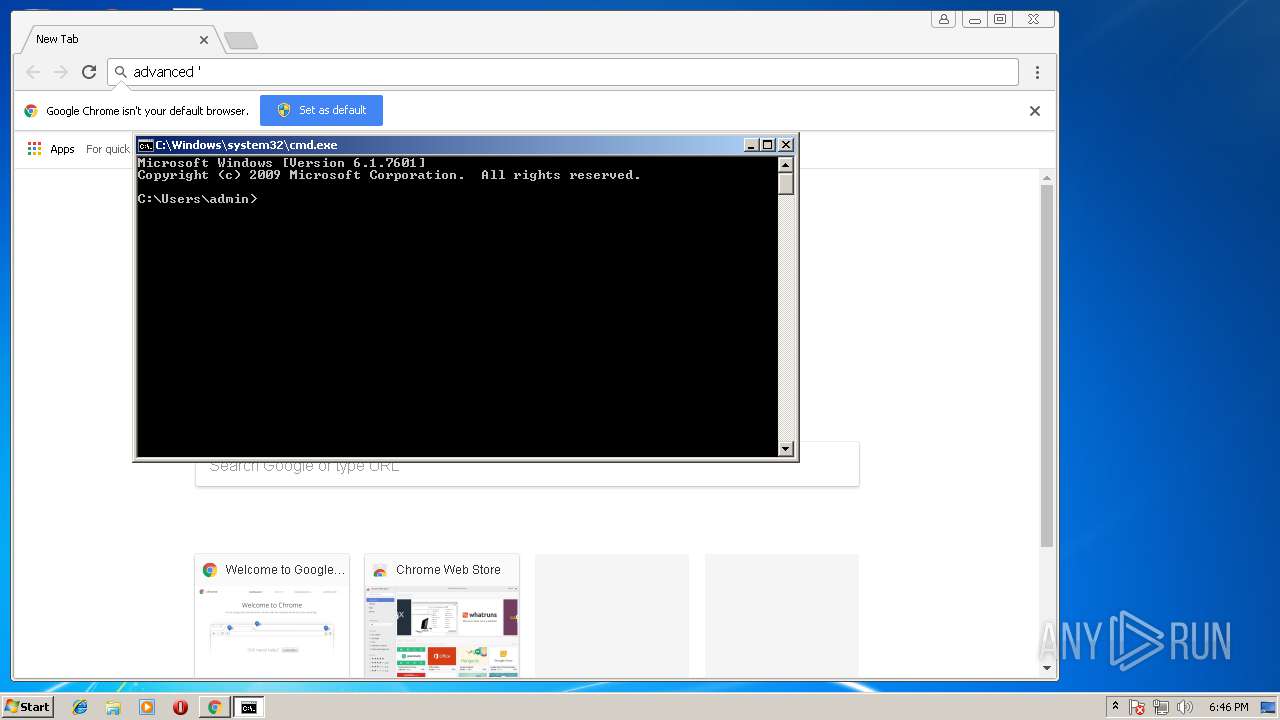
| 1888 | ipconfig | C:\Windows\system32\ipconfig.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: IP Configuration Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2076 | C:\Users\admin\AppData\Roaming\MusaLLaT.exe | C:\Users\admin\AppData\Roaming\MusaLLaT.exe | Özel Dosyalar.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 8.01.0008 Modules
| |||||||||||||||
| 2324 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1760,267841884714280811,13333328326167706721,131072 --service-pipe-token=B78CB2BD525F16D67E0266CD008410D4 --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --enable-pinch --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --content-image-texture-target=0,0,3553;0,1,3553;0,2,3553;0,3,3553;0,4,3553;0,5,3553;0,6,3553;0,7,3553;0,8,3553;0,9,3553;0,10,3553;0,11,3553;0,12,3553;0,13,3553;0,14,3553;0,15,3553;0,16,3553;0,17,3553;1,0,3553;1,1,3553;1,2,3553;1,3,3553;1,4,3553;1,5,3553;1,6,3553;1,7,3553;1,8,3553;1,9,3553;1,10,3553;1,11,3553;1,12,3553;1,13,3553;1,14,3553;1,15,3553;1,16,3553;1,17,3553;2,0,3553;2,1,3553;2,2,3553;2,3,3553;2,4,3553;2,5,3553;2,6,3553;2,7,3553;2,8,3553;2,9,3553;2,10,3553;2,11,3553;2,12,3553;2,13,3553;2,14,3553;2,15,3553;2,16,3553;2,17,3553;3,0,3553;3,1,3553;3,2,3553;3,3,3553;3,4,3553;3,5,3553;3,6,3553;3,7,3553;3,8,3553;3,9,3553;3,10,3553;3,11,3553;3,12,3553;3,13,3553;3,14,3553;3,15,3553;3,16,3553;3,17,3553;4,0,3553;4,1,3553;4,2,3553;4,3,3553;4,4,3553;4,5,3553;4,6,3553;4,7,3553;4,8,3553;4,9,3553;4,10,3553;4,11,3553;4,12,3553;4,13,3553;4,14,3553;4,15,3553;4,16,3553;4,17,3553 --disable-accelerated-video-decode --disable-gpu-compositing --enable-gpu-async-worker-context --service-request-channel-token=B78CB2BD525F16D67E0266CD008410D4 --renderer-client-id=6 --mojo-platform-channel-handle=3360 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 61.0.3163.91 Modules
| |||||||||||||||
| 2408 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1760,267841884714280811,13333328326167706721,131072 --lang=en-US --service-request-channel-token=B97FC0B86E6C3F654FBCD7EFBA817440 --mojo-platform-channel-handle=2952 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 61.0.3163.91 Modules
| |||||||||||||||
| 2440 | "C:\Users\admin\AppData\Local\Temp\Özel Dosyalar.exe" | C:\Users\admin\AppData\Local\Temp\Özel Dosyalar.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 8.01.0008 Modules
| |||||||||||||||
| 2484 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1760,267841884714280811,13333328326167706721,131072 --service-pipe-token=F7342CFE42E7F654F3B493A22A5B5490 --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --enable-pinch --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --content-image-texture-target=0,0,3553;0,1,3553;0,2,3553;0,3,3553;0,4,3553;0,5,3553;0,6,3553;0,7,3553;0,8,3553;0,9,3553;0,10,3553;0,11,3553;0,12,3553;0,13,3553;0,14,3553;0,15,3553;0,16,3553;0,17,3553;1,0,3553;1,1,3553;1,2,3553;1,3,3553;1,4,3553;1,5,3553;1,6,3553;1,7,3553;1,8,3553;1,9,3553;1,10,3553;1,11,3553;1,12,3553;1,13,3553;1,14,3553;1,15,3553;1,16,3553;1,17,3553;2,0,3553;2,1,3553;2,2,3553;2,3,3553;2,4,3553;2,5,3553;2,6,3553;2,7,3553;2,8,3553;2,9,3553;2,10,3553;2,11,3553;2,12,3553;2,13,3553;2,14,3553;2,15,3553;2,16,3553;2,17,3553;3,0,3553;3,1,3553;3,2,3553;3,3,3553;3,4,3553;3,5,3553;3,6,3553;3,7,3553;3,8,3553;3,9,3553;3,10,3553;3,11,3553;3,12,3553;3,13,3553;3,14,3553;3,15,3553;3,16,3553;3,17,3553;4,0,3553;4,1,3553;4,2,3553;4,3,3553;4,4,3553;4,5,3553;4,6,3553;4,7,3553;4,8,3553;4,9,3553;4,10,3553;4,11,3553;4,12,3553;4,13,3553;4,14,3553;4,15,3553;4,16,3553;4,17,3553 --disable-accelerated-video-decode --disable-gpu-compositing --enable-gpu-async-worker-context --service-request-channel-token=F7342CFE42E7F654F3B493A22A5B5490 --renderer-client-id=22 --mojo-platform-channel-handle=3624 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 61.0.3163.91 Modules
| |||||||||||||||
| 2492 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1760,267841884714280811,13333328326167706721,131072 --service-pipe-token=9AA734A51B76EF6EBCF223A2DDA8DD71 --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --enable-pinch --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --content-image-texture-target=0,0,3553;0,1,3553;0,2,3553;0,3,3553;0,4,3553;0,5,3553;0,6,3553;0,7,3553;0,8,3553;0,9,3553;0,10,3553;0,11,3553;0,12,3553;0,13,3553;0,14,3553;0,15,3553;0,16,3553;0,17,3553;1,0,3553;1,1,3553;1,2,3553;1,3,3553;1,4,3553;1,5,3553;1,6,3553;1,7,3553;1,8,3553;1,9,3553;1,10,3553;1,11,3553;1,12,3553;1,13,3553;1,14,3553;1,15,3553;1,16,3553;1,17,3553;2,0,3553;2,1,3553;2,2,3553;2,3,3553;2,4,3553;2,5,3553;2,6,3553;2,7,3553;2,8,3553;2,9,3553;2,10,3553;2,11,3553;2,12,3553;2,13,3553;2,14,3553;2,15,3553;2,16,3553;2,17,3553;3,0,3553;3,1,3553;3,2,3553;3,3,3553;3,4,3553;3,5,3553;3,6,3553;3,7,3553;3,8,3553;3,9,3553;3,10,3553;3,11,3553;3,12,3553;3,13,3553;3,14,3553;3,15,3553;3,16,3553;3,17,3553;4,0,3553;4,1,3553;4,2,3553;4,3,3553;4,4,3553;4,5,3553;4,6,3553;4,7,3553;4,8,3553;4,9,3553;4,10,3553;4,11,3553;4,12,3553;4,13,3553;4,14,3553;4,15,3553;4,16,3553;4,17,3553 --disable-accelerated-video-decode --disable-gpu-compositing --enable-gpu-async-worker-context --service-request-channel-token=9AA734A51B76EF6EBCF223A2DDA8DD71 --renderer-client-id=9 --mojo-platform-channel-handle=3564 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 61.0.3163.91 Modules
| |||||||||||||||
| 2500 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1760,267841884714280811,13333328326167706721,131072 --lang=en-US --service-request-channel-token=9F5F41CA5955E5687A0120FAA4D1B64E --mojo-platform-channel-handle=1984 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 61.0.3163.91 Modules
| |||||||||||||||
Total events
605
Read events
471
Write events
124
Delete events
10
Modification events
| (PID) Process: | (2440) Özel Dosyalar.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Security Center |
| Operation: | write | Name: | UACDisableNotify |
Value: 0 | |||
| (PID) Process: | (2440) Özel Dosyalar.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | EnableLUA |
Value: 0 | |||
| (PID) Process: | (2076) MusaLLaT.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Security Center |
| Operation: | write | Name: | UACDisableNotify |
Value: 0 | |||
| (PID) Process: | (2076) MusaLLaT.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | EnableLUA |
Value: 0 | |||
| (PID) Process: | (2076) MusaLLaT.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | MusaLLaT |
Value: C:\Users\admin\AppData\Roaming\MusaLLaT.exe | |||
| (PID) Process: | (4008) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 1504-13179865564167000 |
Value: 259 | |||
| (PID) Process: | (1504) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1504) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1504) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1504) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
Executable files
1
Suspicious files
91
Text files
92
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2440 | Özel Dosyalar.exe | C:\Users\admin\AppData\Local\Temp\~DFD09E474D9E779373.TMP | — | |
MD5:— | SHA256:— | |||
| 2076 | MusaLLaT.exe | C:\Users\admin\AppData\Local\Temp\~DF8D28422818B4BF8D.TMP | — | |
MD5:— | SHA256:— | |||
| 1504 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000008.dbtmp | — | |
MD5:— | SHA256:— | |||
| 1504 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\abb192f4-5a9f-467b-ba25-af842ab7c5d2.tmp | — | |
MD5:— | SHA256:— | |||
| 1504 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\CacheStorage\e6622492fa163609ddd4212f54512baa07929ed3\0b424357-803d-4002-a471-5e43f4cbfdf1\index-dir\temp-index | — | |
MD5:— | SHA256:— | |||
| 2076 | MusaLLaT.exe | C:\Users\admin\AppData\Roaming\Declare.ini | text | |
MD5:— | SHA256:— | |||
| 1504 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\CacheStorage\e6622492fa163609ddd4212f54512baa07929ed3\0b424357-803d-4002-a471-5e43f4cbfdf1\index-dir\the-real-index | binary | |
MD5:— | SHA256:— | |||
| 1504 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1504 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old~RF4cd281.TMP | text | |
MD5:— | SHA256:— | |||
| 1504 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\CacheStorage\e6622492fa163609ddd4212f54512baa07929ed3\0b424357-803d-4002-a471-5e43f4cbfdf1\index-dir\the-real-index~RF4cd223.TMP | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
57
DNS requests
34
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
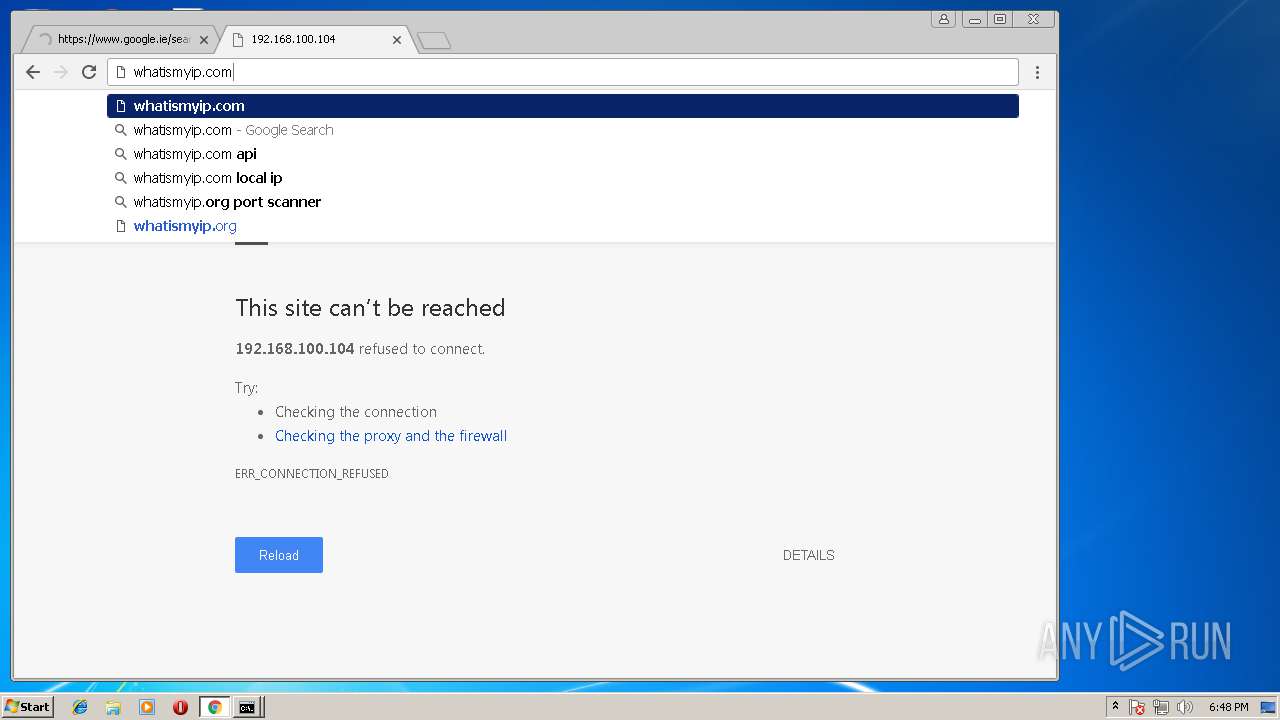
1504 | chrome.exe | GET | — | 104.16.17.96:80 | http://whatismyipaddress.com/ | US | — | — | shared |
1504 | chrome.exe | GET | 200 | 216.58.215.238:80 | http://clients1.google.com/tools/pso/ping?as=chrome&brand=GCEA&pid=&hl=en&events=C1F,C1I,C2I,C7I,C1S,C7S&rep=2&rlz=C1:,C2:,C7:&id=4E3014F88A1776A95D57E2AE3211A742FF35E455C4BA364784 | US | text | 140 b | whitelisted |
1504 | chrome.exe | GET | 301 | 104.27.193.92:80 | http://whatismyip.com/ | US | html | 171 b | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1504 | chrome.exe | 216.58.215.227:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
1504 | chrome.exe | 216.58.215.238:443 | apis.google.com | Google Inc. | US | whitelisted |
1504 | chrome.exe | 172.217.18.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
1504 | chrome.exe | 172.217.168.10:443 | translate.googleapis.com | Google Inc. | US | whitelisted |
1504 | chrome.exe | 216.58.207.36:443 | www.google.com | Google Inc. | US | whitelisted |
1504 | chrome.exe | 172.217.168.3:443 | www.google.ie | Google Inc. | US | whitelisted |
— | — | 10.157.0.1:137 | — | — | — | unknown |
— | — | 172.253.50.17:137 | — | Google Inc. | US | whitelisted |
1504 | chrome.exe | 104.16.17.96:80 | whatismyipaddress.com | Cloudflare Inc | US | shared |
1504 | chrome.exe | 104.27.193.92:80 | whatismyip.com | Cloudflare Inc | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ssl.gstatic.com |
| whitelisted |
www.google.de |
| whitelisted |
apis.google.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
translate.googleapis.com |
| whitelisted |
www.google.com |
| malicious |
www.google.ie |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
clients4.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1504 | chrome.exe | Attempted Information Leak | ET POLICY IP Check Domain (whatismyip in HTTP Host) |
1 ETPRO signatures available at the full report