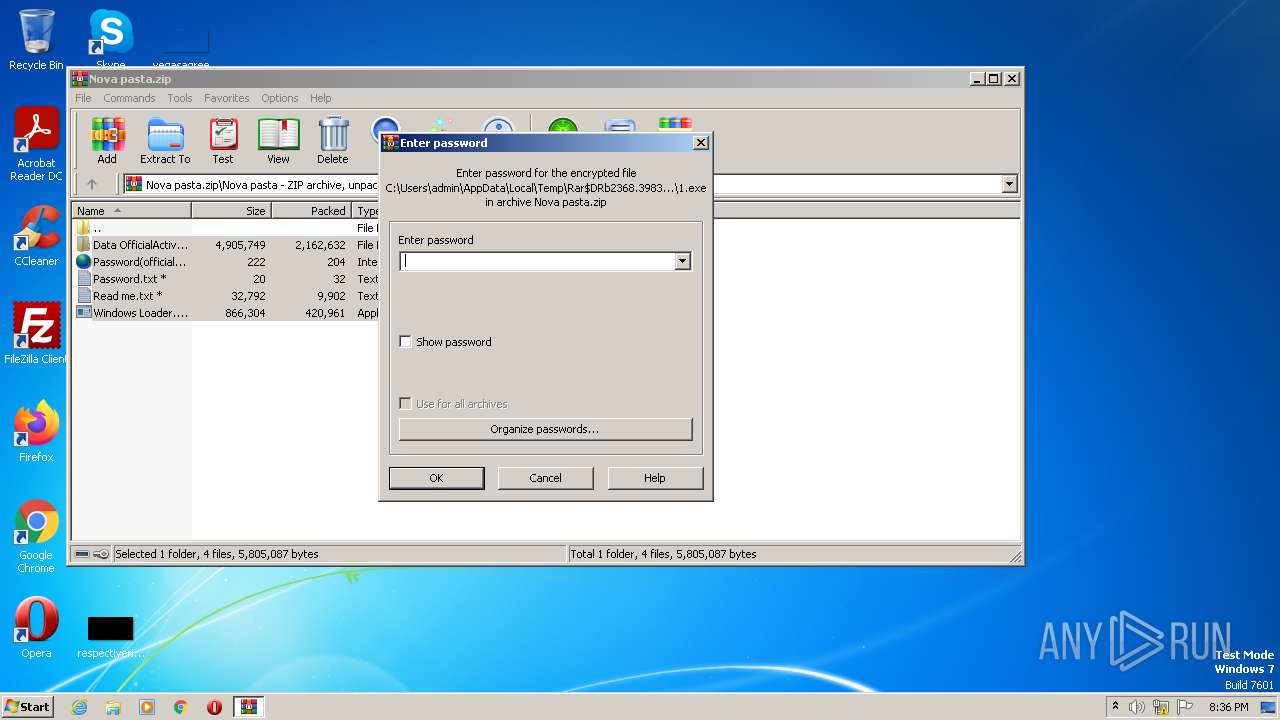
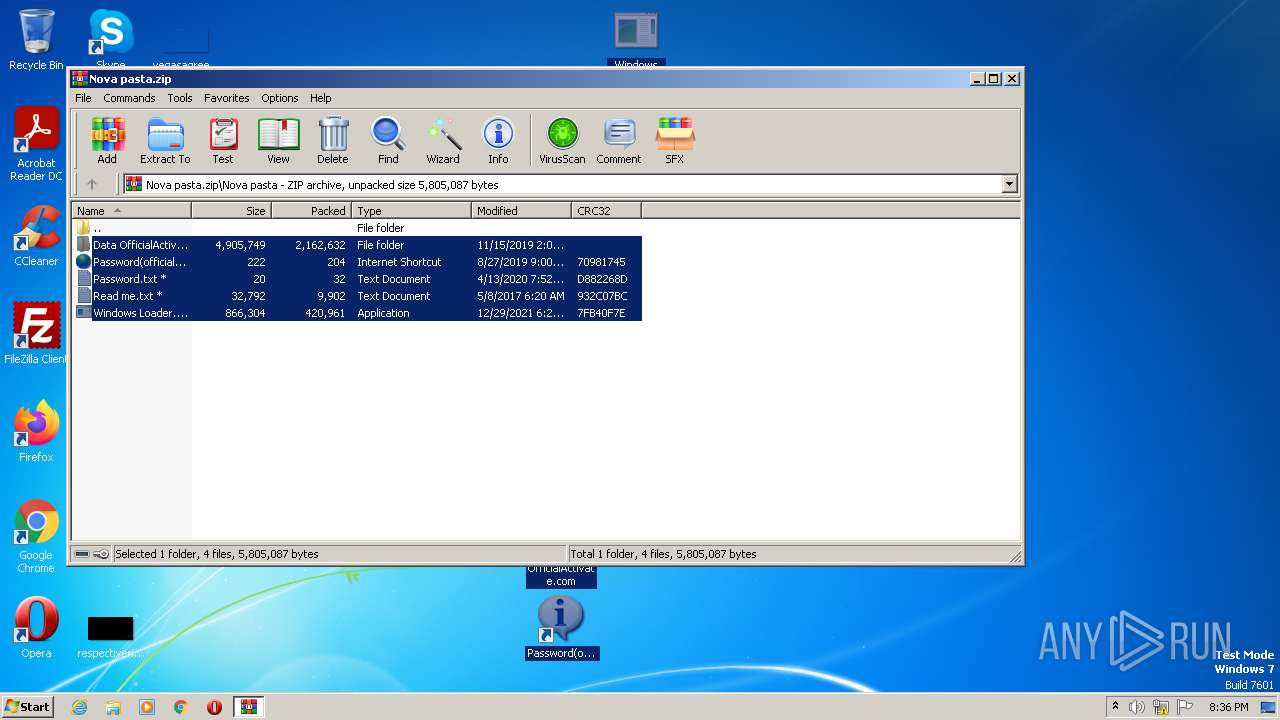
| File name: | Nova pasta.zip |
| Full analysis: | https://app.any.run/tasks/33623ca7-6517-4c25-b6a6-441a37db34f4 |
| Verdict: | Malicious activity |
| Analysis date: | March 12, 2023, 20:36:40 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 692EF82947F1BEBCB0C0440C138638A4 |
| SHA1: | 8846859A1A80791D3614972F9DB315806F45C742 |
| SHA256: | A9734BBD8221F40763B4E37270F6E0CED94D63A6FD193C5912143619D543D954 |
| SSDEEP: | 49152:P5hY5m12tJdSmxUnb3fbZs+1C2wOtS3LqtDiOhvTWJt/NaF+zFfHoHIHoHtV:P5Ym125Sm+zfbZsPxuPZTuaF+yHIOV |
MALICIOUS
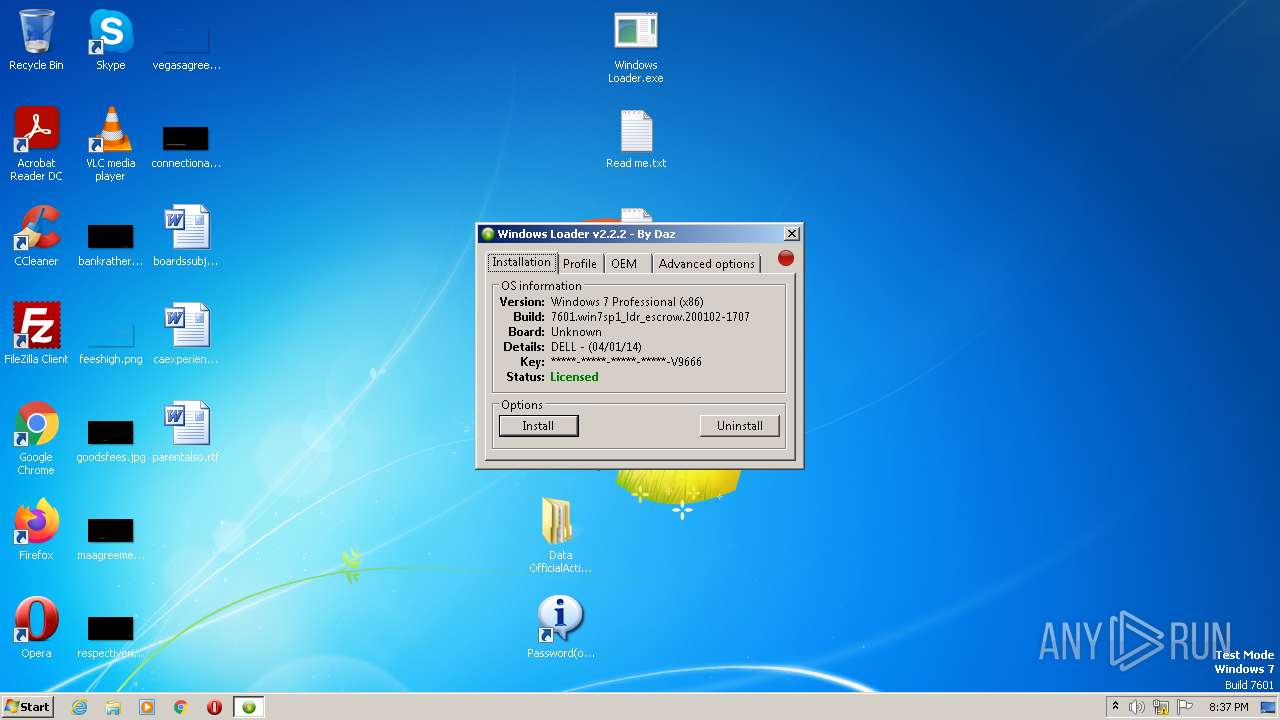
Application was dropped or rewritten from another process
- msw.exe (PID: 1624)
- Windows Loader.exe (PID: 1504)
- 1.exe (PID: 2624)
- 1.exe (PID: 3340)
- msw.exe (PID: 2348)
- Windows Loader.exe (PID: 1900)
- 1.exe (PID: 2800)
Create files in the Startup directory
- Windows Loader.exe (PID: 1900)
Drops the executable file immediately after the start
- Windows Loader.exe (PID: 1900)
SUSPICIOUS
Reads the Internet Settings
- Windows Loader.exe (PID: 1504)
- Windows Loader.exe (PID: 1900)
Executable content was dropped or overwritten
- Windows Loader.exe (PID: 1900)
Reads the BIOS version
- 1.exe (PID: 3340)
Starts CMD.EXE for commands execution
- 1.exe (PID: 3340)
- cmd.exe (PID: 3428)
- cmd.exe (PID: 3744)
Application launched itself
- cmd.exe (PID: 3428)
- cmd.exe (PID: 3744)
Uses ICACLS.EXE to modify access control lists
- cmd.exe (PID: 4052)
- cmd.exe (PID: 852)
Executes scripts
- cmd.exe (PID: 948)
- cmd.exe (PID: 1640)
Reads security settings of Internet Explorer
- cscript.exe (PID: 3556)
- cscript.exe (PID: 3160)
INFO
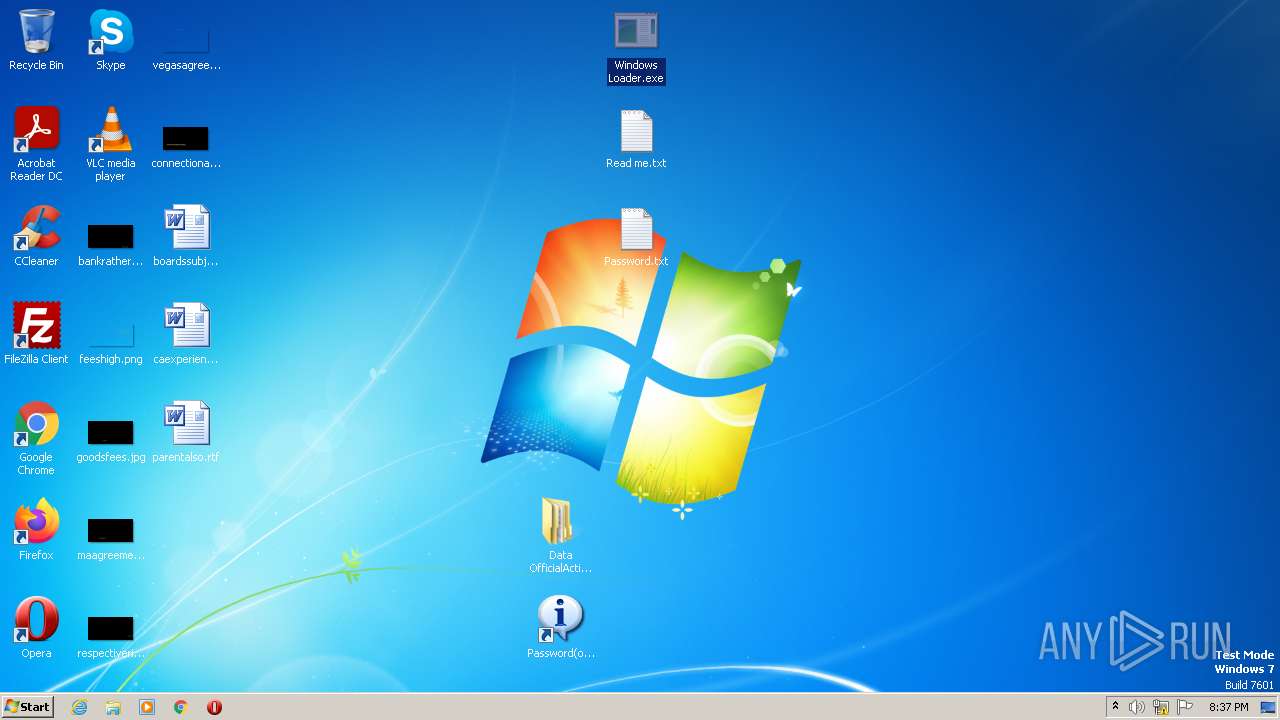
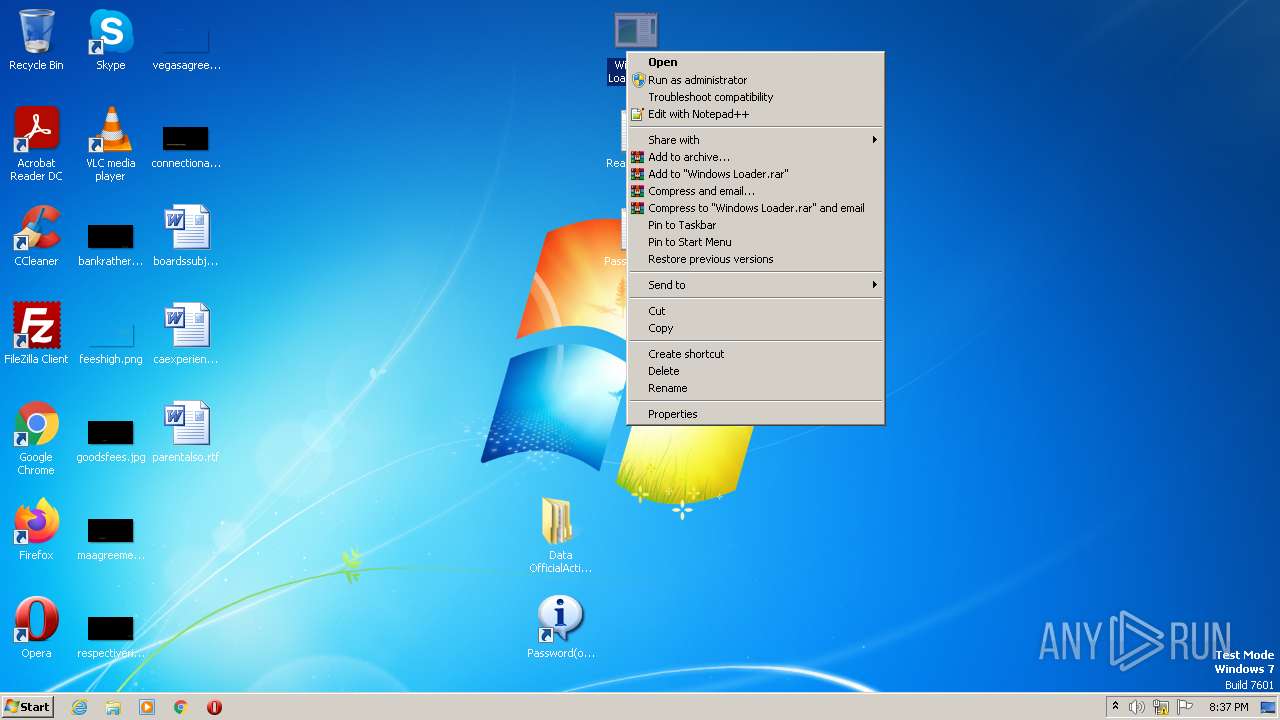
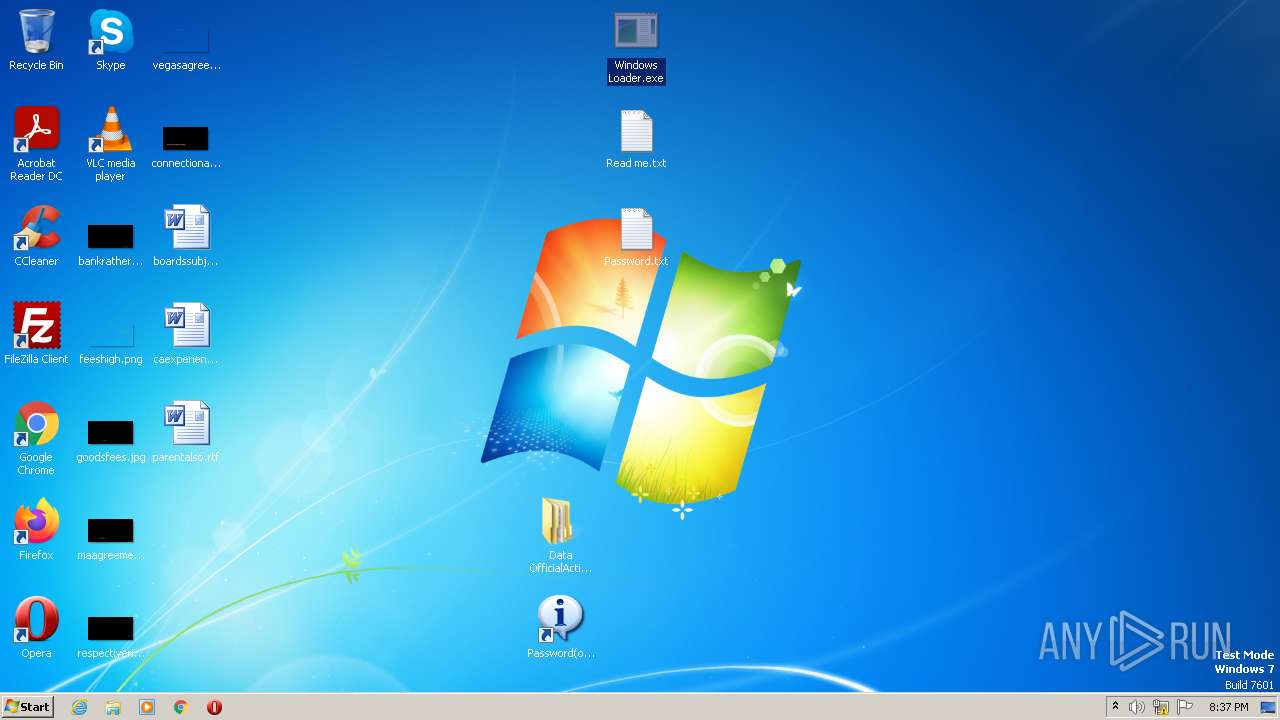
Manual execution by a user
- Windows Loader.exe (PID: 1504)
- Windows Loader.exe (PID: 1900)
Checks supported languages
- Windows Loader.exe (PID: 1504)
- msw.exe (PID: 1624)
- 1.exe (PID: 3340)
- Windows Loader.exe (PID: 1900)
- 1.exe (PID: 2800)
- msw.exe (PID: 2348)
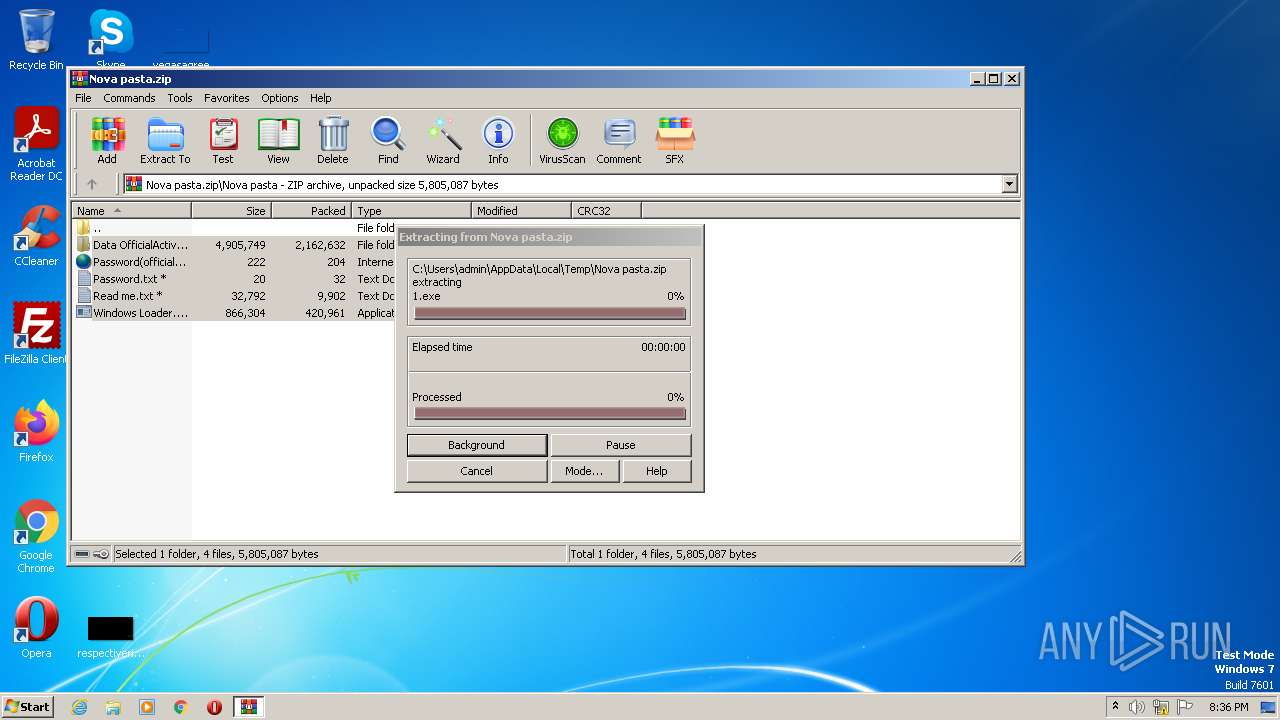
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2368)
Drops the executable file immediately after the start
- WinRAR.exe (PID: 2368)
Reads mouse settings
- Windows Loader.exe (PID: 1504)
- msw.exe (PID: 1624)
- Windows Loader.exe (PID: 1900)
- msw.exe (PID: 2348)
The process checks LSA protection
- Windows Loader.exe (PID: 1504)
- 1.exe (PID: 3340)
- msw.exe (PID: 1624)
- Windows Loader.exe (PID: 1900)
- 1.exe (PID: 2800)
- cscript.exe (PID: 3160)
- msw.exe (PID: 2348)
- cscript.exe (PID: 3556)
Reads the computer name
- Windows Loader.exe (PID: 1504)
- 1.exe (PID: 3340)
- msw.exe (PID: 1624)
- Windows Loader.exe (PID: 1900)
- msw.exe (PID: 2348)
Reads the machine GUID from the registry
- 1.exe (PID: 3340)
Creates files in the program directory
- Windows Loader.exe (PID: 1900)
Reads Environment values
- 1.exe (PID: 3340)
Reads product name
- 1.exe (PID: 3340)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
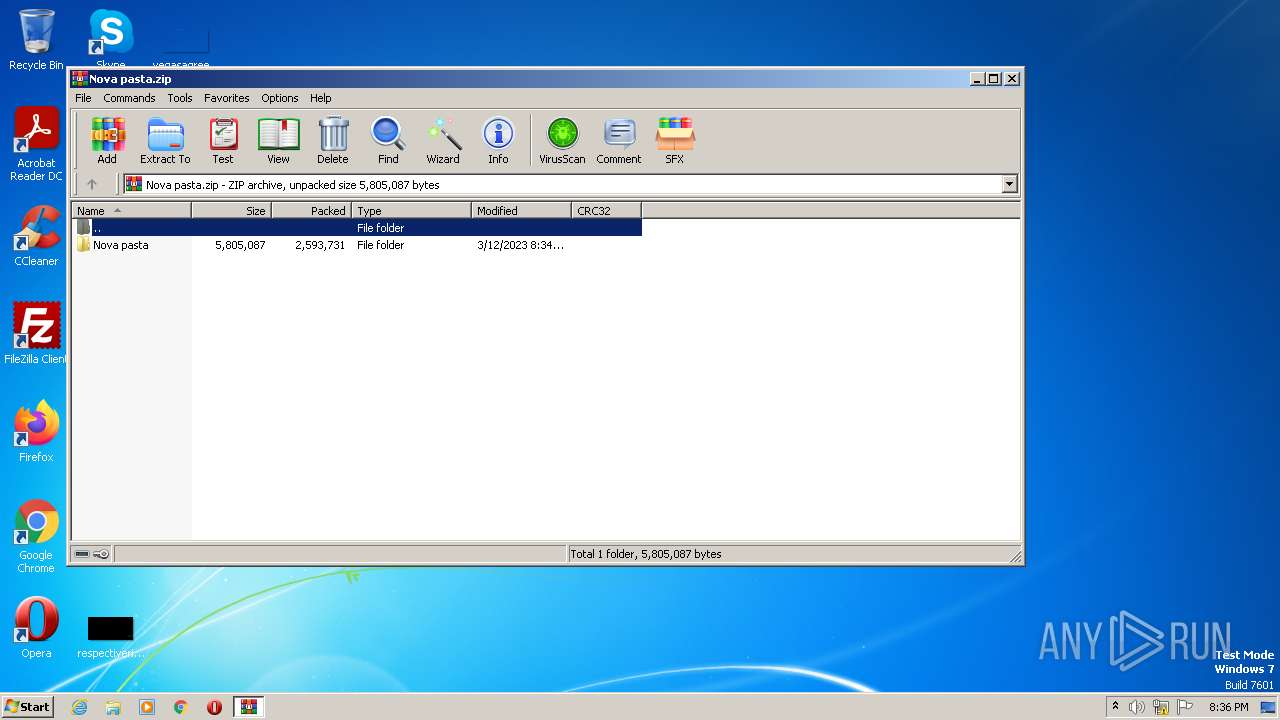
| ZipFileName: | Nova pasta/ |
|---|---|
| ZipUncompressedSize: | - |
| ZipCompressedSize: | - |
| ZipCRC: | 0x00000000 |
| ZipModifyDate: | 2023:03:12 17:34:28 |
| ZipCompression: | None |
| ZipBitFlag: | - |
| ZipRequiredVersion: | 20 |
Total processes
74
Monitored processes
22
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 588 | icacls C:\ldrscan\bootwin /grant *S-1-1-0:(F) | C:\Windows\System32\icacls.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Exit code: 2 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 852 | cmd.exe /A /C "icacls C:\ldrscan\bootwin /grant *S-1-1-0:(F)" | C:\Windows\System32\cmd.exe | — | 1.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 2 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 948 | cmd.exe /A /C "C:\Windows\System32\cscript.exe //nologo C:\Windows\System32\slmgr.vbs -ilc "C:\Dell.XRM-MS"" | C:\Windows\System32\cmd.exe | — | 1.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
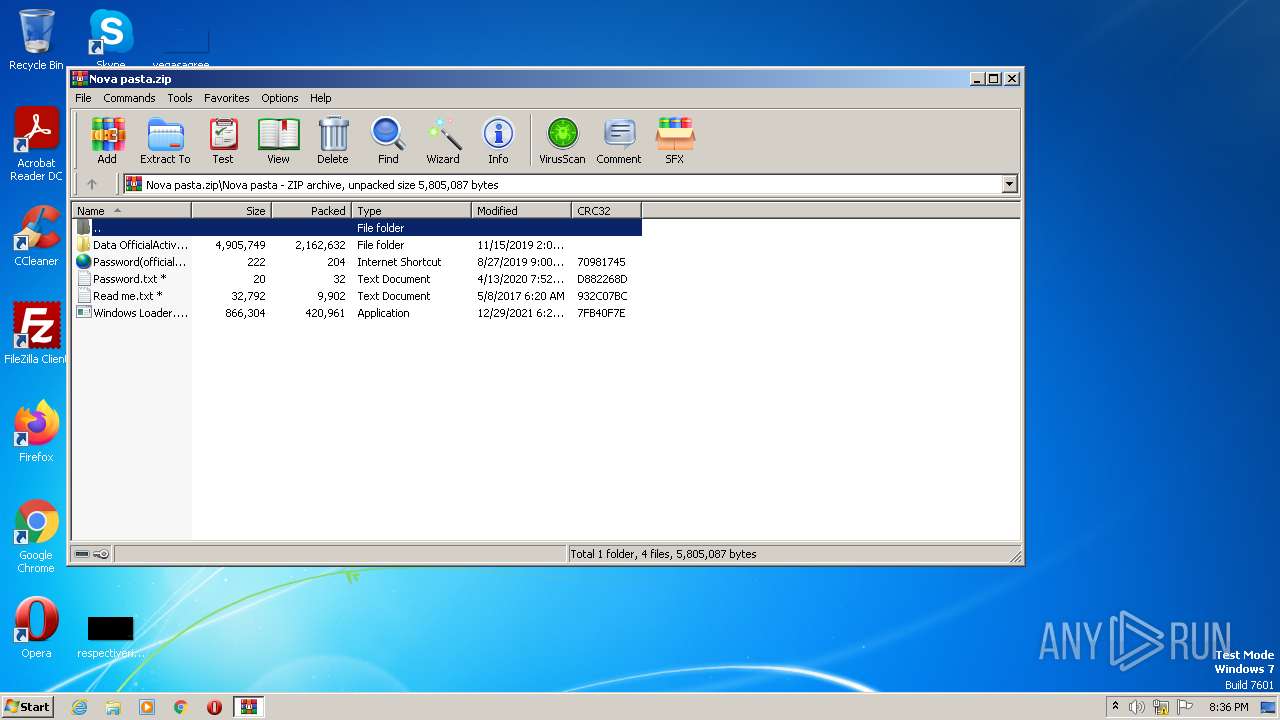
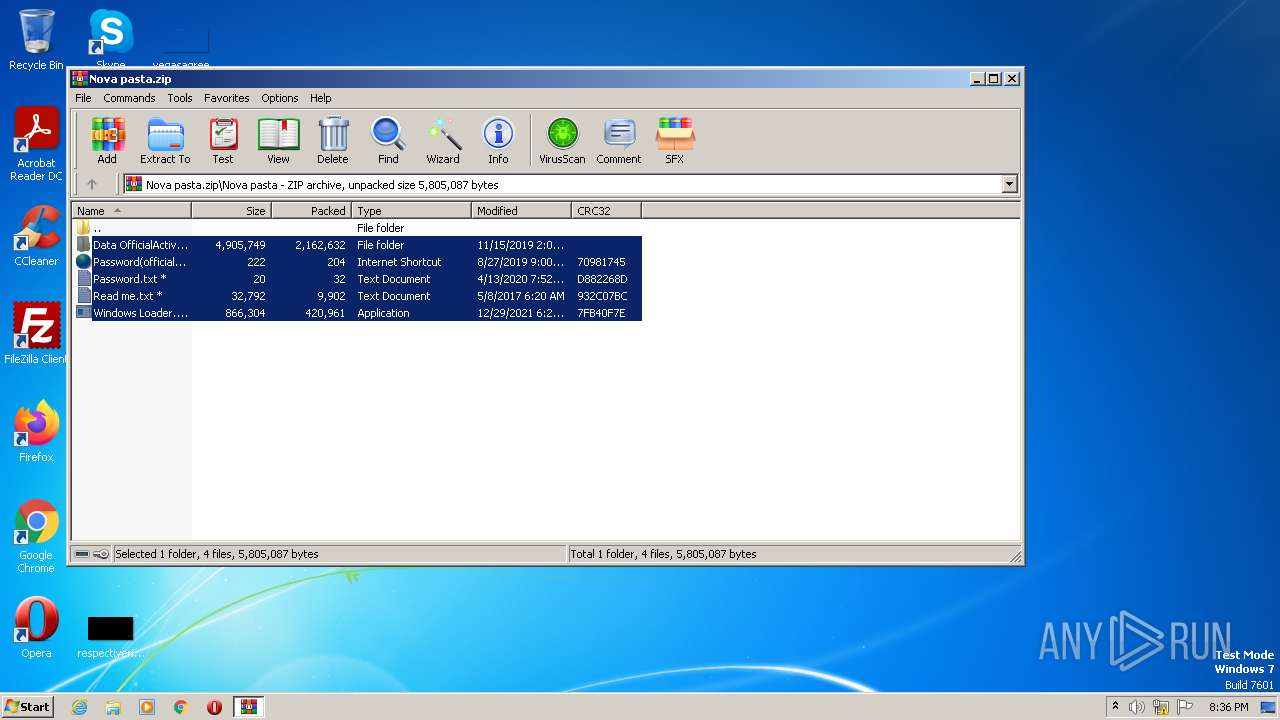
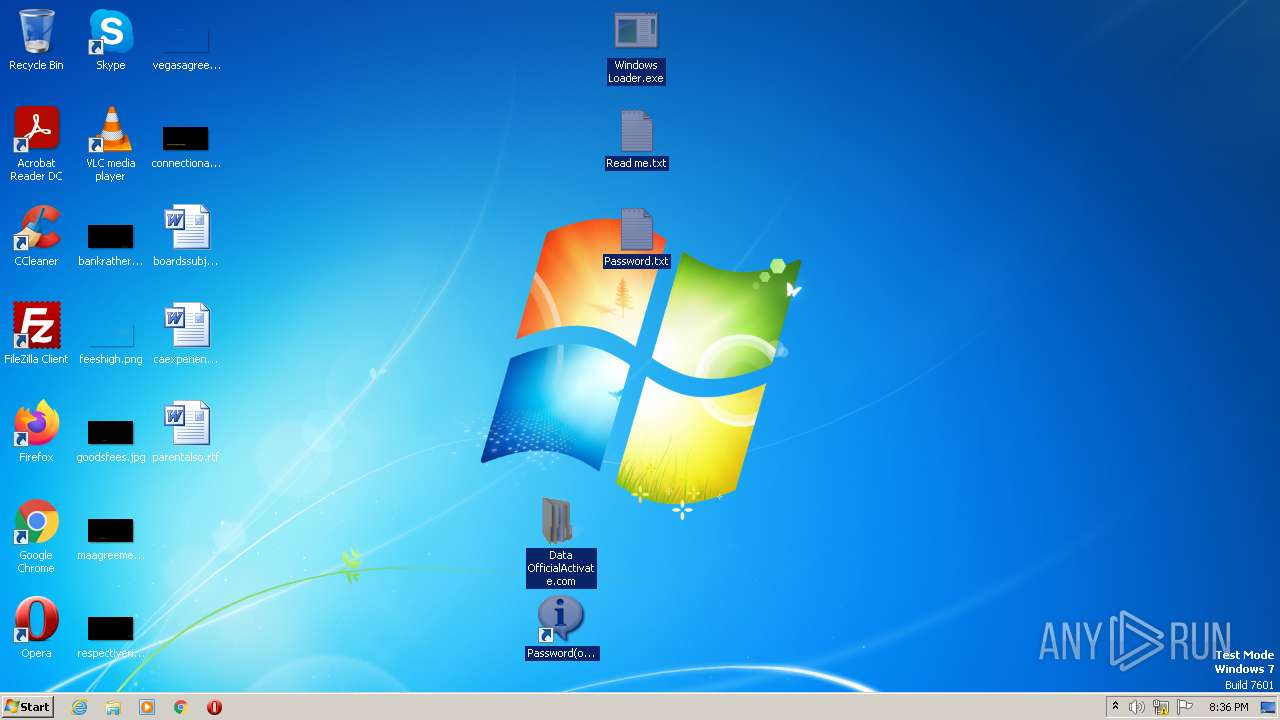
| 1504 | "C:\Users\admin\Desktop\Windows Loader.exe" | C:\Users\admin\Desktop\Windows Loader.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1624 | "Data OfficialActivate.com\0\1\2\3\4\5\6\7\8\9\msw.exe" | C:\Users\admin\Desktop\Data OfficialActivate.com\0\1\2\3\4\5\6\7\8\9\msw.exe | — | Windows Loader.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1640 | cmd.exe /A /C "C:\Windows\System32\cscript.exe //nologo C:\Windows\System32\slmgr.vbs -ipk 32KD2-K9CTF-M3DJT-4J3WC-733WD" | C:\Windows\System32\cmd.exe | — | 1.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1900 | "C:\Users\admin\Desktop\Windows Loader.exe" | C:\Users\admin\Desktop\Windows Loader.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2348 | "Data OfficialActivate.com\0\1\2\3\4\5\6\7\8\9\msw.exe" | C:\Users\admin\Desktop\Data OfficialActivate.com\0\1\2\3\4\5\6\7\8\9\msw.exe | — | Windows Loader.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2368 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Nova pasta.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 2408 | icacls C:\ldrscan\bootwin /grant *S-1-1-0:(F) | C:\Windows\System32\icacls.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Exit code: 2 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
5 256
Read events
5 182
Write events
74
Delete events
0
Modification events
| (PID) Process: | (2368) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16D\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2368) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (2368) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (2368) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\phacker.zip | |||
| (PID) Process: | (2368) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2368) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2368) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2368) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2368) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF42000000420000000204000037020000 | |||
| (PID) Process: | (2368) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\General |
| Operation: | write | Name: | LastFolder |
Value: C:\Users\admin\Desktop | |||
Executable files
8
Suspicious files
0
Text files
10
Unknown types
10
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1624 | msw.exe | C:\Users\admin\Desktop\Google Chrome.lnk | lnk | |
MD5:— | SHA256:— | |||
| 2368 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2368.39836\Nova pasta\Data OfficialActivate.com\0\1\2\3\4\5\6\7\8\9\Keys.ini | text | |
MD5:3BA4950BCF43B1C7B714A1D93B57EA86 | SHA256:1384C5FD758A1BD8C9372594503E22D71B0877D332886A1B7D50CB86C4A0A13C | |||
| 2368 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2368.39836\Nova pasta\Data OfficialActivate.com\0\1\2\3\4\5\6\7\8\9\1.exe | executable | |
MD5:323C0FD51071400B51EEDB1BE90A8188 | SHA256:2F2ABA1E074F5F4BAA08B524875461889F8F04D4FFC43972AC212E286022AB94 | |||
| 2368 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2368.39836\Nova pasta\Password.txt | text | |
MD5:AB6633DDE80796679B0270984F69557F | SHA256:— | |||
| 2368 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2368.39836\Nova pasta\Read me.txt | text | |
MD5:3E83D11DCD0D1DC8B6CF531353CF9E81 | SHA256:B5FCBF4B91C436640AAB0E8106F942CD47080BF799A22D747B5CF898BD13475C | |||
| 2368 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2368.39836\Nova pasta\Password(officialactivate.com).URL | text | |
MD5:B8BCED623AA5C52C7B437CDA646B4E1B | SHA256:7B7EA523C21C52DD432ADE4934F37CB643B212269CEEFC557772777D0C2A4FCE | |||
| 2348 | msw.exe | C:\Users\admin\Desktop\Firefox.lnk | lnk | |
MD5:— | SHA256:— | |||
| 1624 | msw.exe | C:\Users\admin\Desktop\Firefox.lnk | lnk | |
MD5:— | SHA256:— | |||
| 2348 | msw.exe | C:\Users\admin\Desktop\Google Chrome.lnk | lnk | |
MD5:— | SHA256:— | |||
| 2368 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2368.39836\Nova pasta\Data OfficialActivate.com\0\1\2\3\4\5\6\7\8\9\msw.exe | executable | |
MD5:B907101C213D3C0F02A0C00038446DCA | SHA256:FEFC84AC3C1A6A2F9B5062EA1580301D2ED1729DB519F203EA3AE0C2ECDC85E8 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report