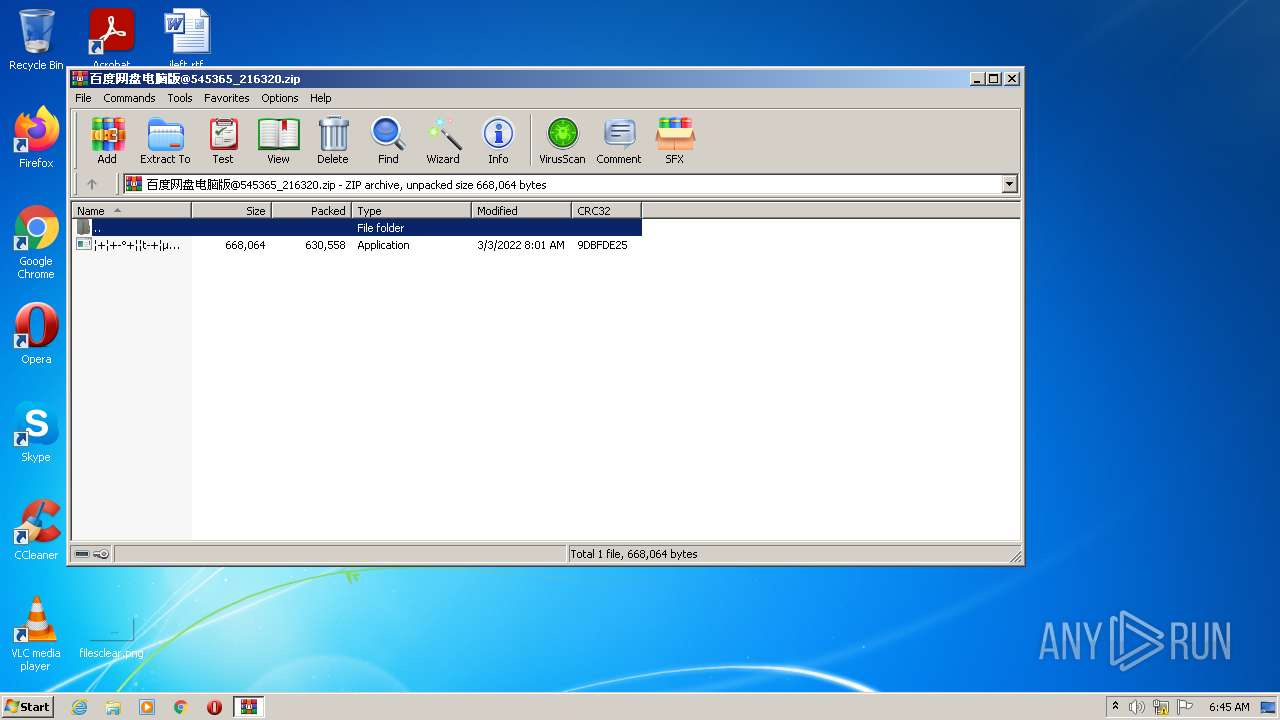
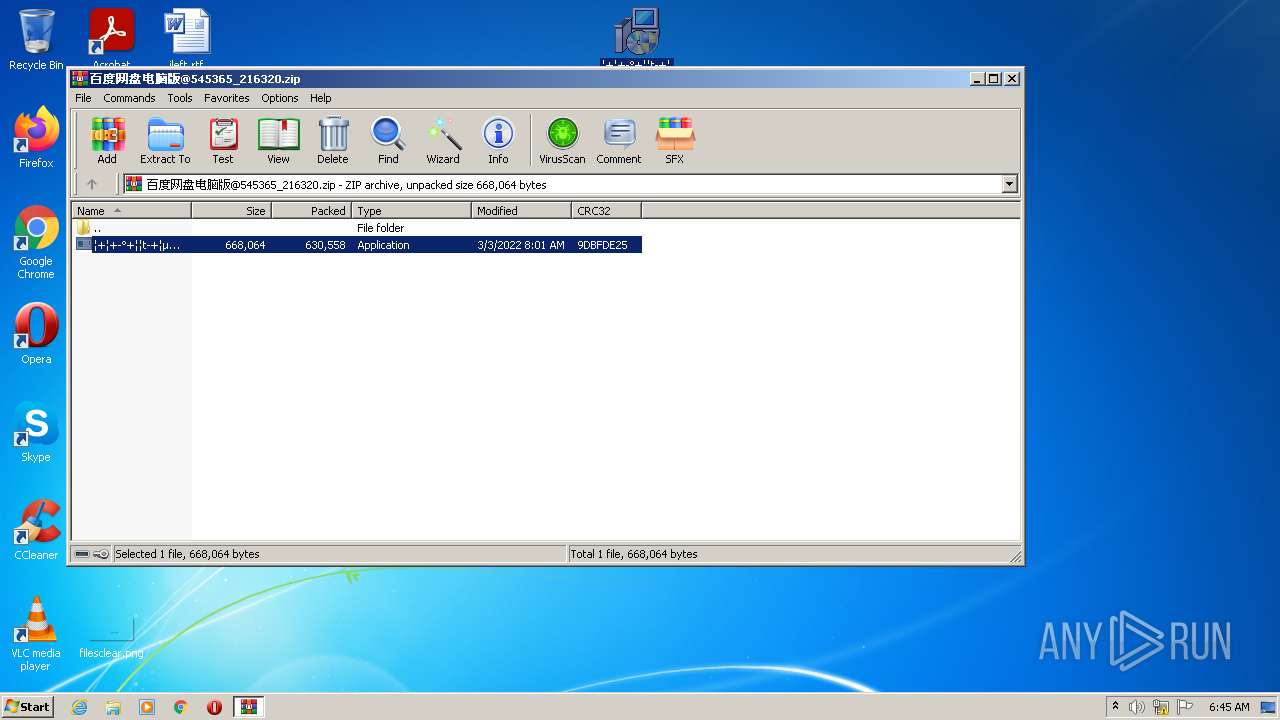
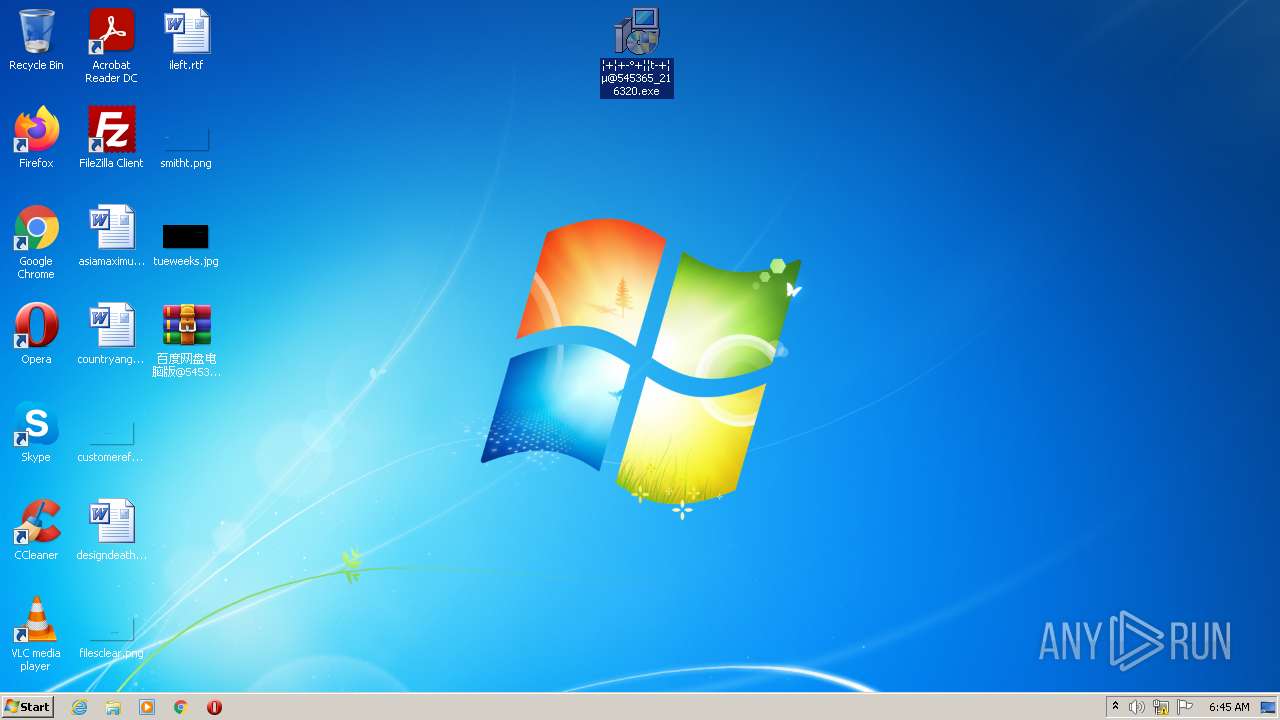
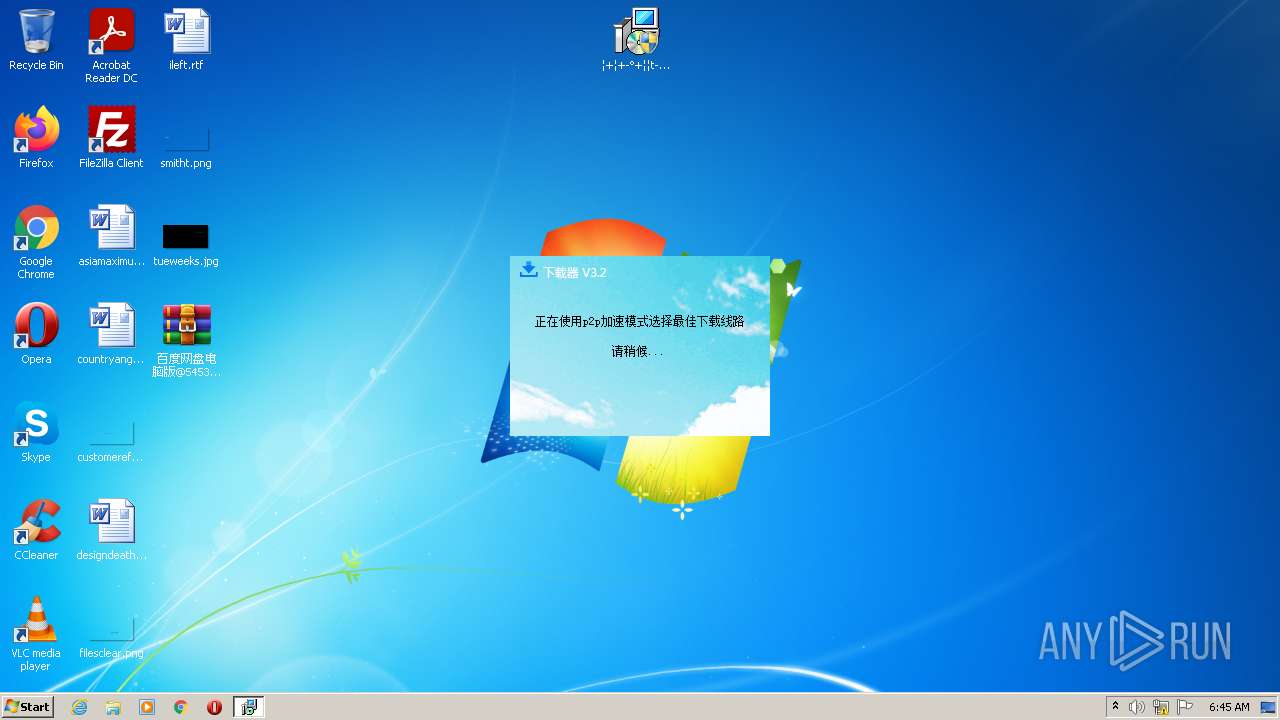
| File name: | 百度网盘电脑版@545365_216320.zip |
| Full analysis: | https://app.any.run/tasks/44b660c7-4569-47bb-8e39-0fc2aecded8d |
| Verdict: | Malicious activity |
| Analysis date: | March 10, 2022, 06:45:13 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 7311BAED4A50DF16056B09CB8DB4508D |
| SHA1: | 272D05F082900F2F8E8219A012537596AFF5CA17 |
| SHA256: | A968C5B75663EDFBF646975B4AEF520986472C026C482A15DB7C2E72633F4CDA |
| SSDEEP: | 12288:0AgKzOuuMaDWFfbMa5bsRFYEQPWf74xoufXTUlQfuMLiVKUv:9Ru2xMaEFYhwcxoKpHc |
MALICIOUS
Application was dropped or rewritten from another process
- �+�+-�+��t-+��@545365_216320.exe (PID: 2248)
Steals credentials from Web Browsers
- �+�+-�+��t-+��@545365_216320.exe (PID: 2248)
Actions looks like stealing of personal data
- �+�+-�+��t-+��@545365_216320.exe (PID: 2248)
SUSPICIOUS
Checks supported languages
- �+�+-�+��t-+��@545365_216320.exe (PID: 2248)
- WinRAR.exe (PID: 3536)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3536)
Reads the computer name
- �+�+-�+��t-+��@545365_216320.exe (PID: 2248)
- WinRAR.exe (PID: 3536)
Creates files in the user directory
- �+�+-�+��t-+��@545365_216320.exe (PID: 2248)
Reads Microsoft Outlook installation path
- �+�+-�+��t-+��@545365_216320.exe (PID: 2248)
Reads internet explorer settings
- �+�+-�+��t-+��@545365_216320.exe (PID: 2248)
INFO
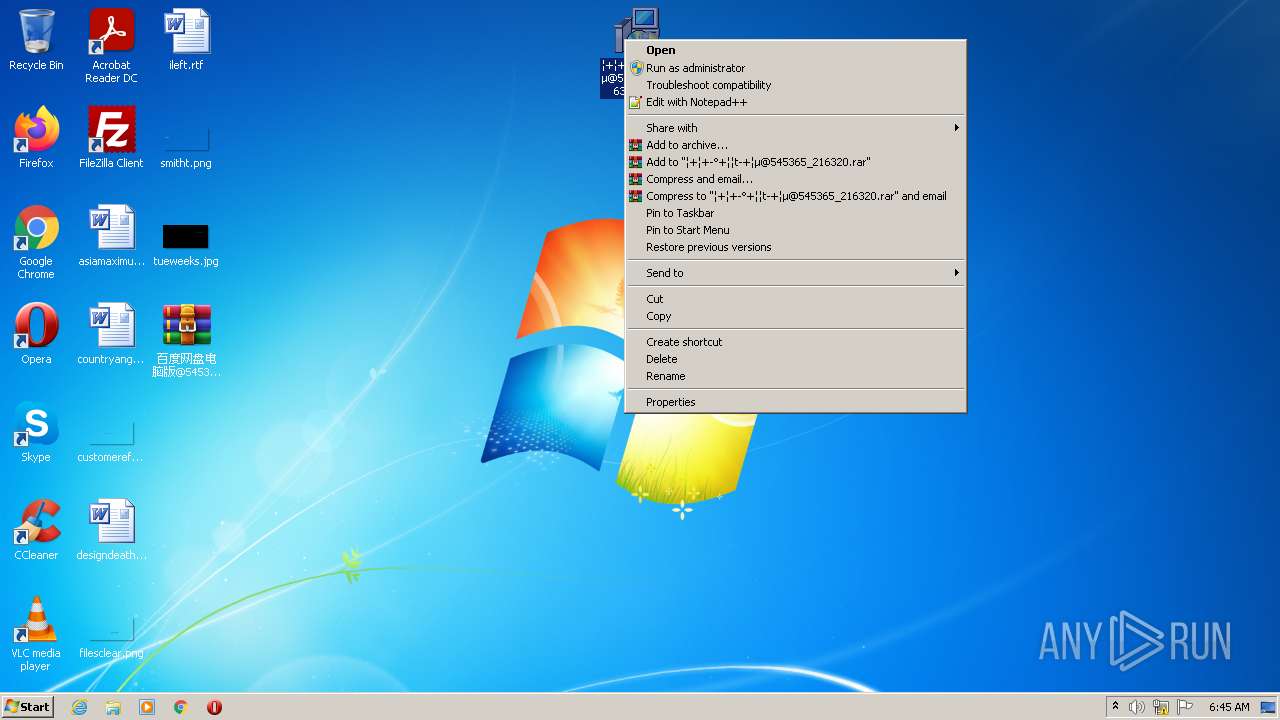
Manual execution by user
- �+�+-�+��t-+��@545365_216320.exe (PID: 2248)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipFileName: | ?ٶ????̵???@545365_216320.exe |
|---|---|
| ZipUncompressedSize: | 668064 |
| ZipCompressedSize: | 630558 |
| ZipCRC: | 0x9dbfde25 |
| ZipModifyDate: | 2022:03:03 16:01:28 |
| ZipCompression: | Deflated |
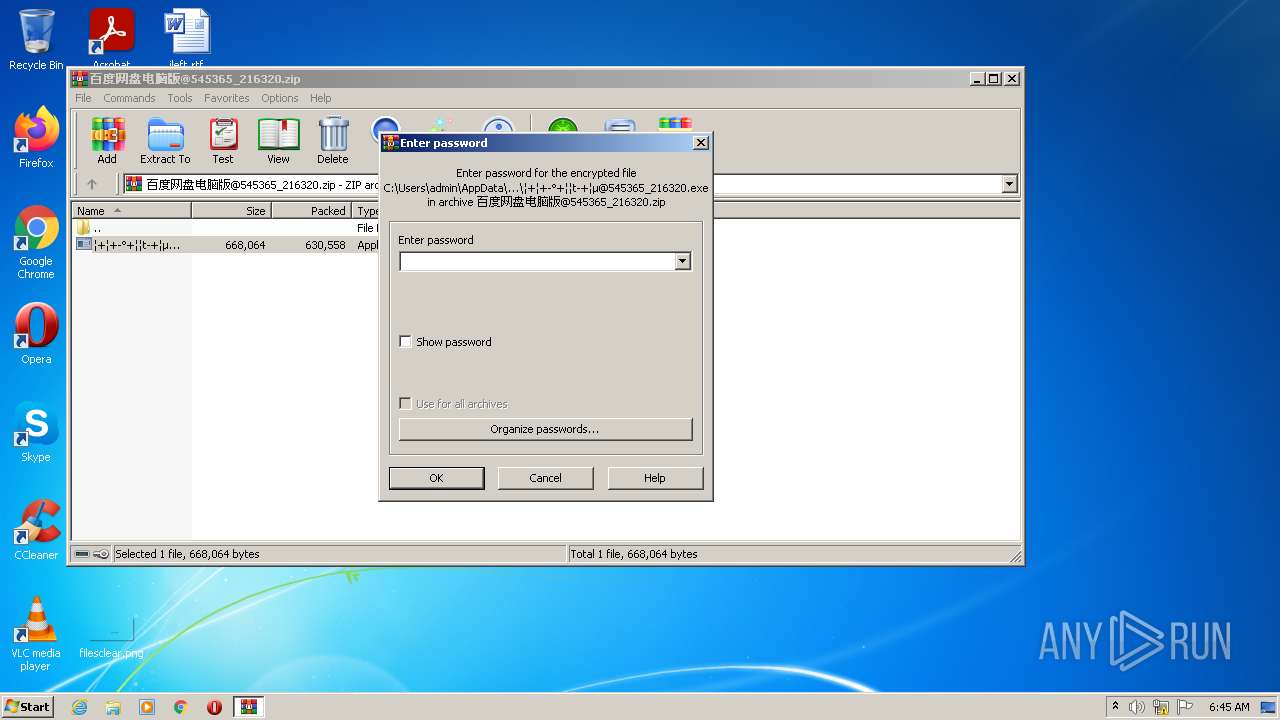
| ZipBitFlag: | 0x0001 |
| ZipRequiredVersion: | 20 |
Total processes
40
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2248 | "C:\Users\admin\Desktop\�+�+-�+��t-+��@545365_216320.exe" | C:\Users\admin\Desktop\�+�+-�+��t-+��@545365_216320.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: HIGH Description: _ Exit code: 0 Version: 6.0.0.1111 Modules
| |||||||||||||||
| 3536 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\???????@545365_216320.zip" | C:\Program Files\WinRAR\WinRAR.exe | Explorer.EXE | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
Total events
1 318
Read events
1 278
Write events
40
Delete events
0
Modification events
| (PID) Process: | (3536) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3536) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3536) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3536) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (3536) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (3536) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\???????@545365_216320.zip | |||
| (PID) Process: | (3536) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3536) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3536) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3536) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
1
Suspicious files
0
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2248 | �+�+-�+��t-+��@545365_216320.exe | C:\Users\admin\AppData\Roaming\GlobalMgr.db | text | |
MD5:— | SHA256:— | |||
| 3536 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb3536.37863\�+�+-�+��t-+��@545365_216320.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
10
DNS requests
2
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2248 | �+�+-�+��t-+��@545365_216320.exe | POST | — | 47.103.45.17:80 | http://w.nanweng.cn/qy/gl | CN | — | — | malicious |
2248 | �+�+-�+��t-+��@545365_216320.exe | POST | — | 47.103.45.17:80 | http://w.nanweng.cn/qy/png | CN | — | — | malicious |
2248 | �+�+-�+��t-+��@545365_216320.exe | POST | — | 47.103.45.17:80 | http://w.nanweng.cn/qy/gl | CN | — | — | malicious |
2248 | �+�+-�+��t-+��@545365_216320.exe | POST | — | 47.103.45.17:80 | http://w.nanweng.cn/qy/gl | CN | — | — | malicious |
2248 | �+�+-�+��t-+��@545365_216320.exe | POST | — | 47.103.45.17:80 | http://w.nanweng.cn/qy/gl | CN | — | — | malicious |
2248 | �+�+-�+��t-+��@545365_216320.exe | POST | — | 47.103.45.17:80 | http://w.nanweng.cn/qy/png | CN | — | — | malicious |
2248 | �+�+-�+��t-+��@545365_216320.exe | POST | — | 47.103.45.17:80 | http://w.nanweng.cn/qy/png | CN | — | — | malicious |
2248 | �+�+-�+��t-+��@545365_216320.exe | POST | — | 47.103.45.17:80 | http://w.nanweng.cn/qy/png | CN | — | — | malicious |
2248 | �+�+-�+��t-+��@545365_216320.exe | POST | — | 47.103.45.17:80 | http://w.nanweng.cn/qy/gl | CN | — | — | malicious |
2248 | �+�+-�+��t-+��@545365_216320.exe | POST | — | 47.103.45.17:80 | http://w.nanweng.cn/qy/png | CN | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2248 | �+�+-�+��t-+��@545365_216320.exe | 47.103.45.17:80 | w.nanweng.cn | Hangzhou Alibaba Advertising Co.,Ltd. | CN | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
w.nanweng.cn |
| malicious |