| File name: | Keygen Start.exe |
| Full analysis: | https://app.any.run/tasks/5df3ad9f-ba92-4d51-b838-f7b2958abecb |
| Verdict: | Malicious activity |
| Analysis date: | August 08, 2020, 22:32:54 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 34EE30044BFFDE645511B6E3D06AD8B4 |
| SHA1: | AA237F26EAFA53EFAAB2F58516275FD128A60DF8 |
| SHA256: | A95DC316190C7CD3D27F91986DCCE9BCDCEA6CC6BFE747EB5A3844415C67F235 |
| SSDEEP: | 768:zPaZozmd52vT9u4vgojwKJC3IgfenhS0aBT59/+DaOC0fTq9zhVbfbmdP/kyoW:ziZozmd5sT9u4vmKx4enhfQT543fTaCx |
MALICIOUS
Changes the autorun value in the registry
- Keygen Start.exe (PID: 2852)
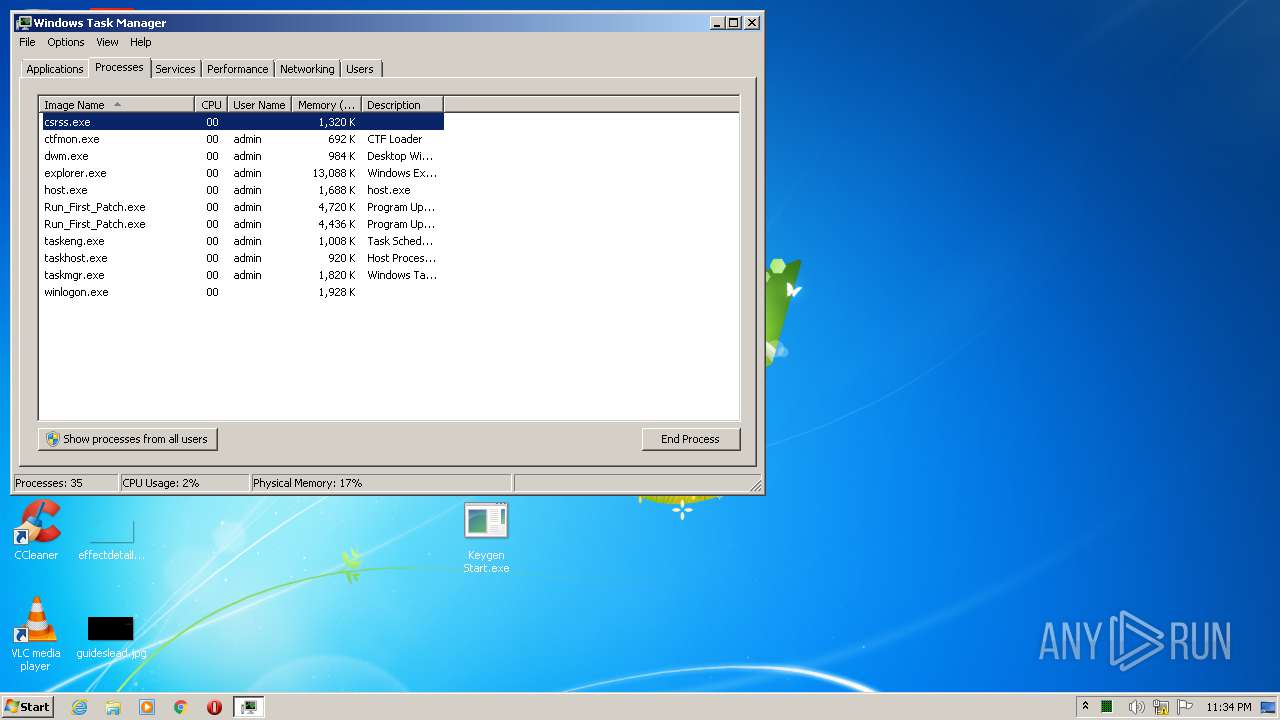
Uses Task Scheduler to run other applications
- cmd.exe (PID: 1840)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 3232)
SUSPICIOUS
Executable content was dropped or overwritten
- Keygen Start.exe (PID: 2852)
Creates files in the user directory
- Keygen Start.exe (PID: 2852)
Starts CMD.EXE for commands execution
- Keygen Start.exe (PID: 2852)
Starts itself from another location
- Keygen Start.exe (PID: 2852)
Executed via Task Scheduler
- Run_First_Patch.exe (PID: 4164)
INFO
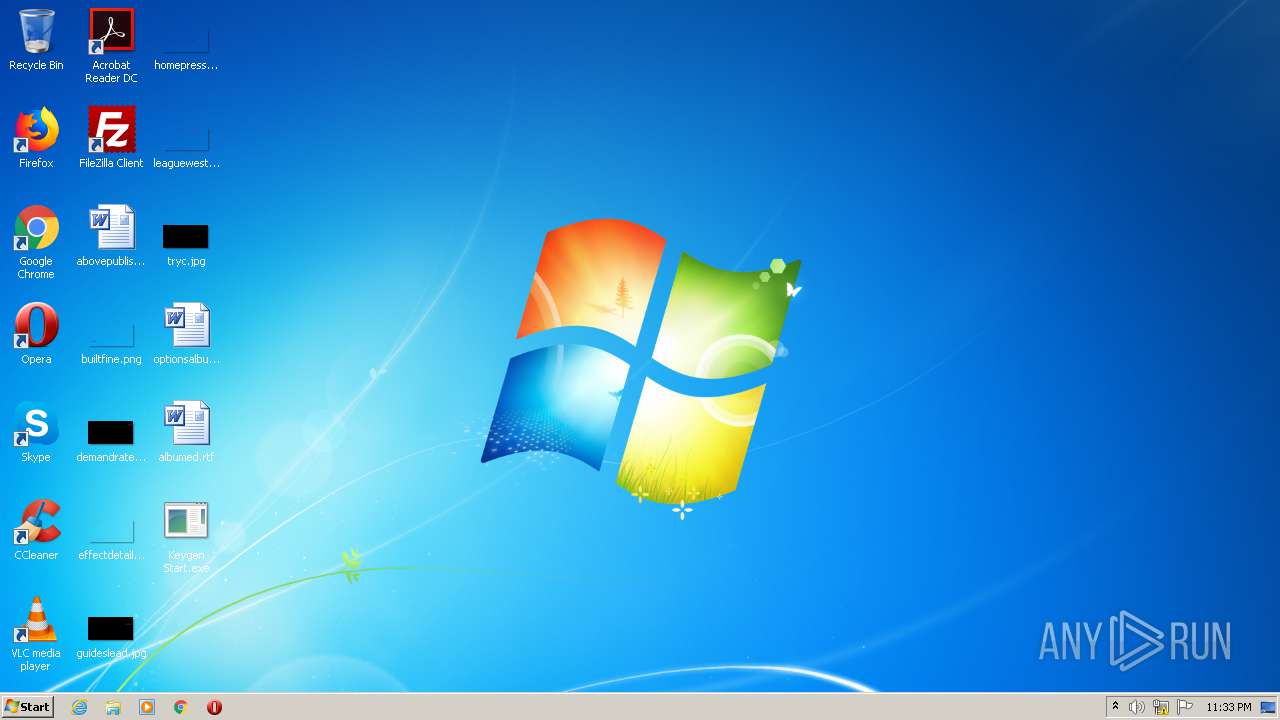
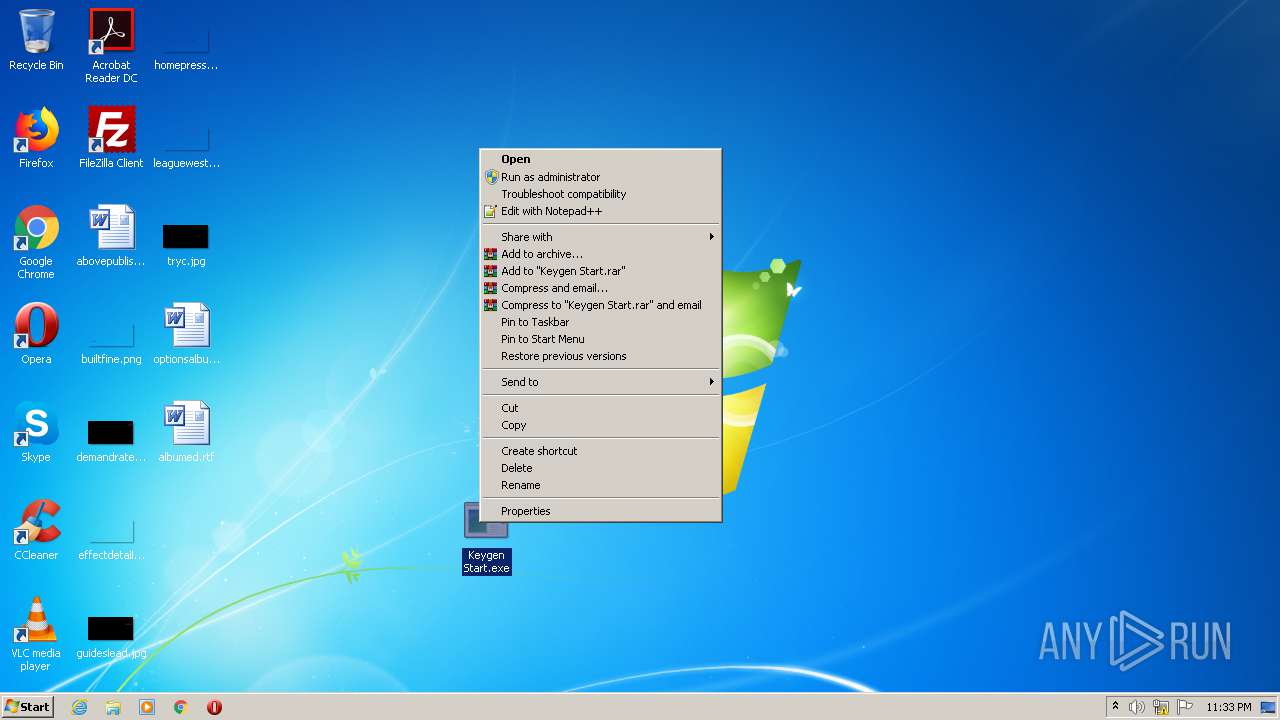
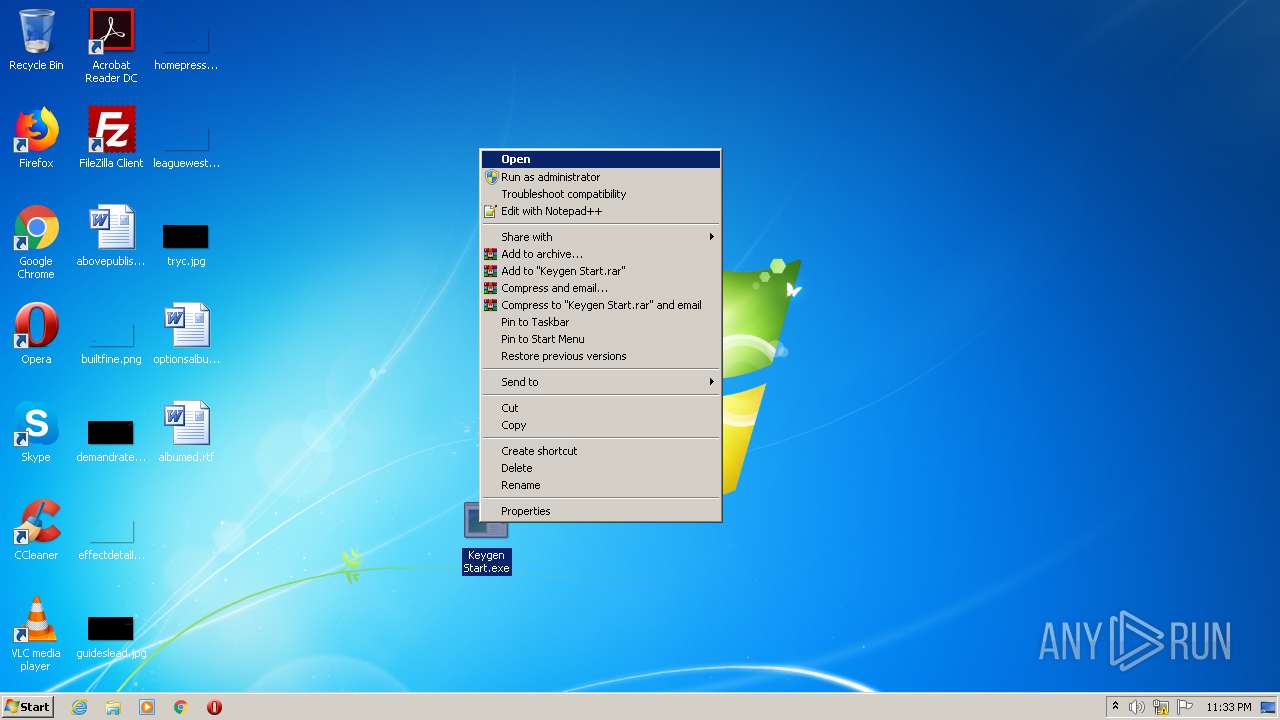
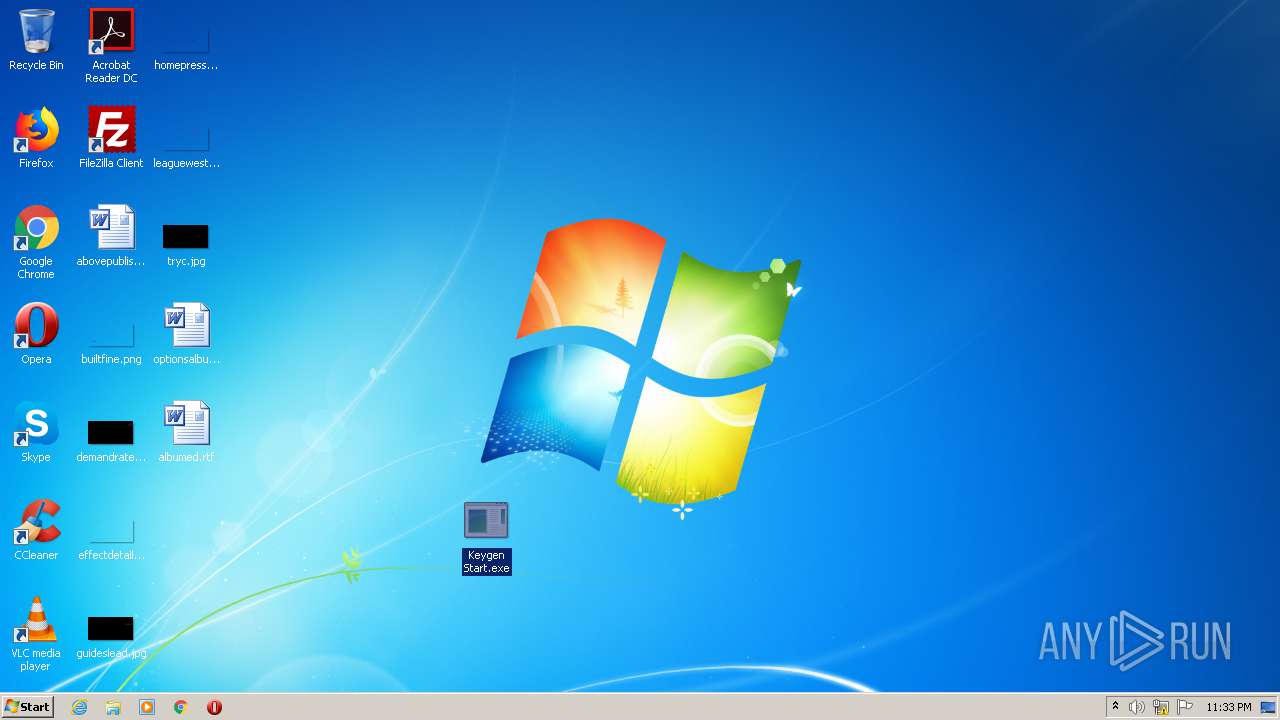
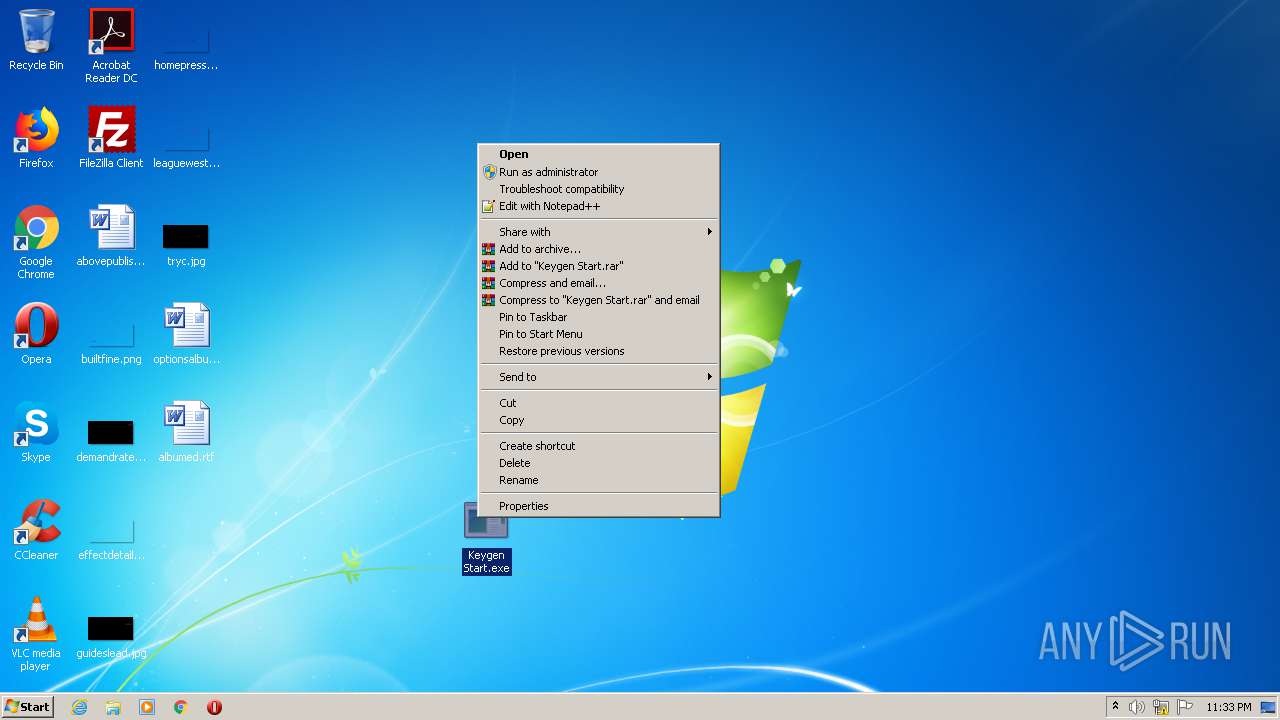
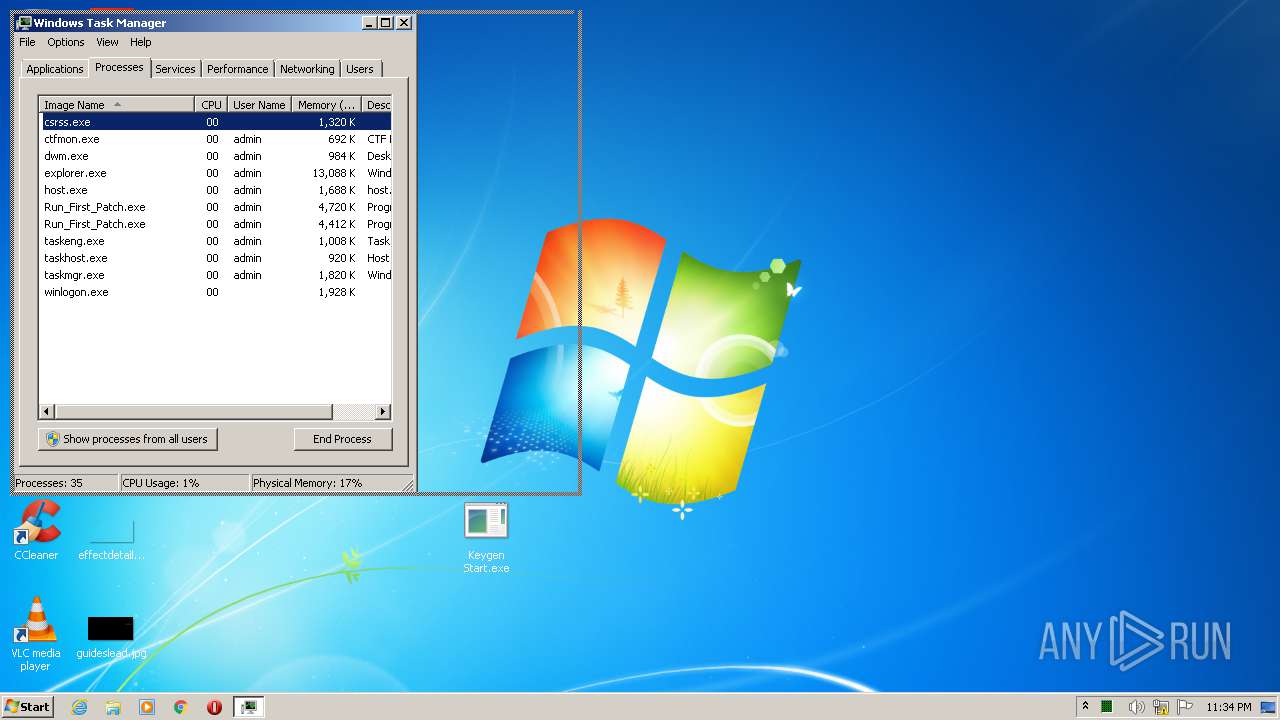
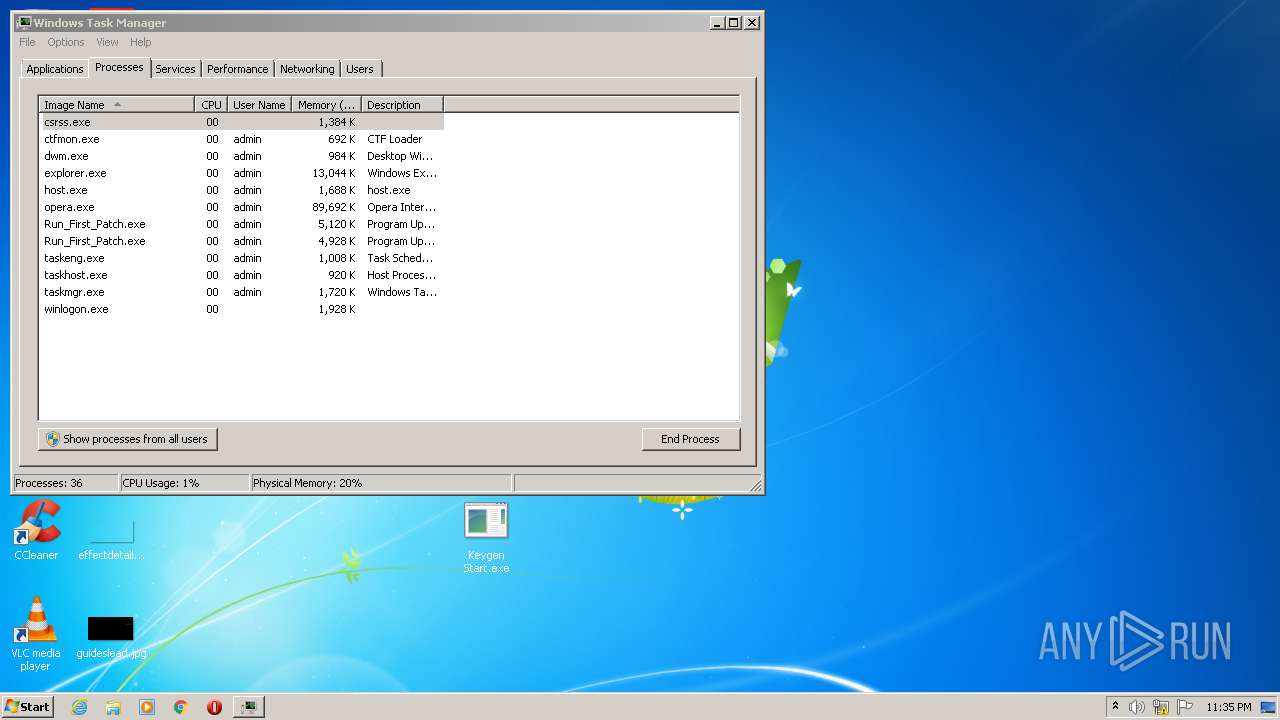
Manual execution by user
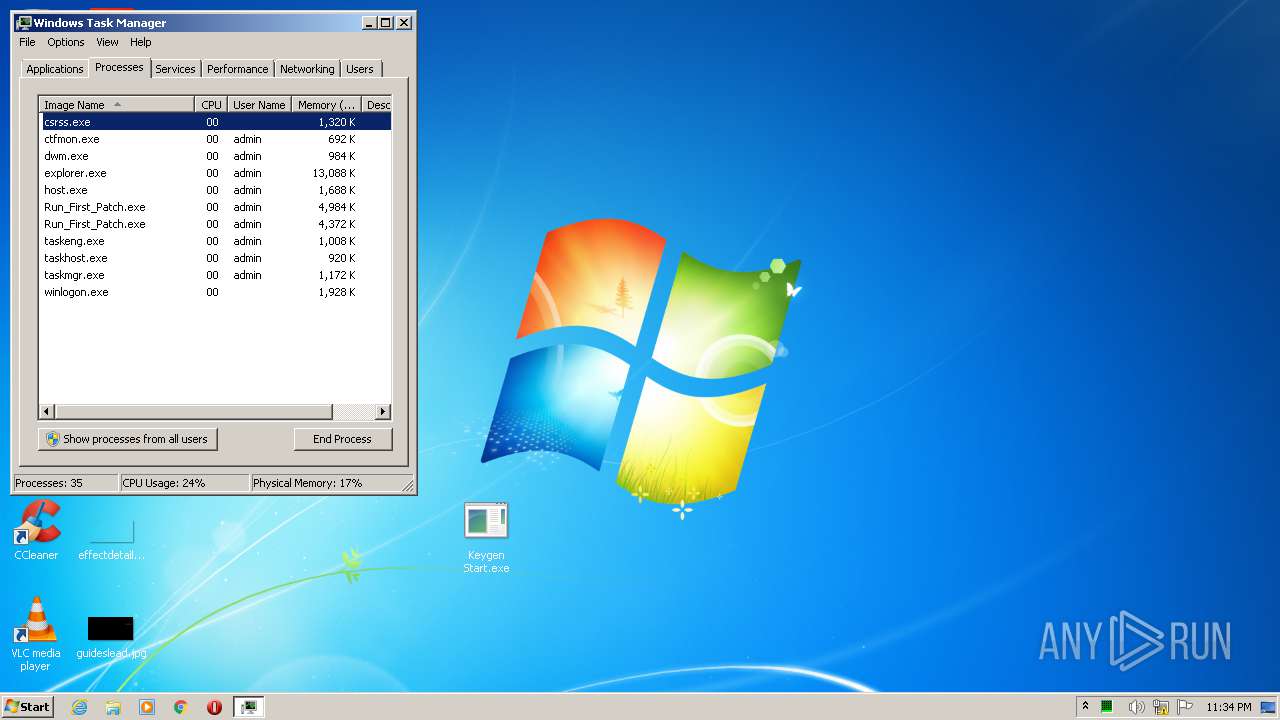
- taskmgr.exe (PID: 6352)
- Keygen Start.exe (PID: 3660)
- Keygen Start.exe (PID: 3236)
- Keygen Start.exe (PID: 2480)
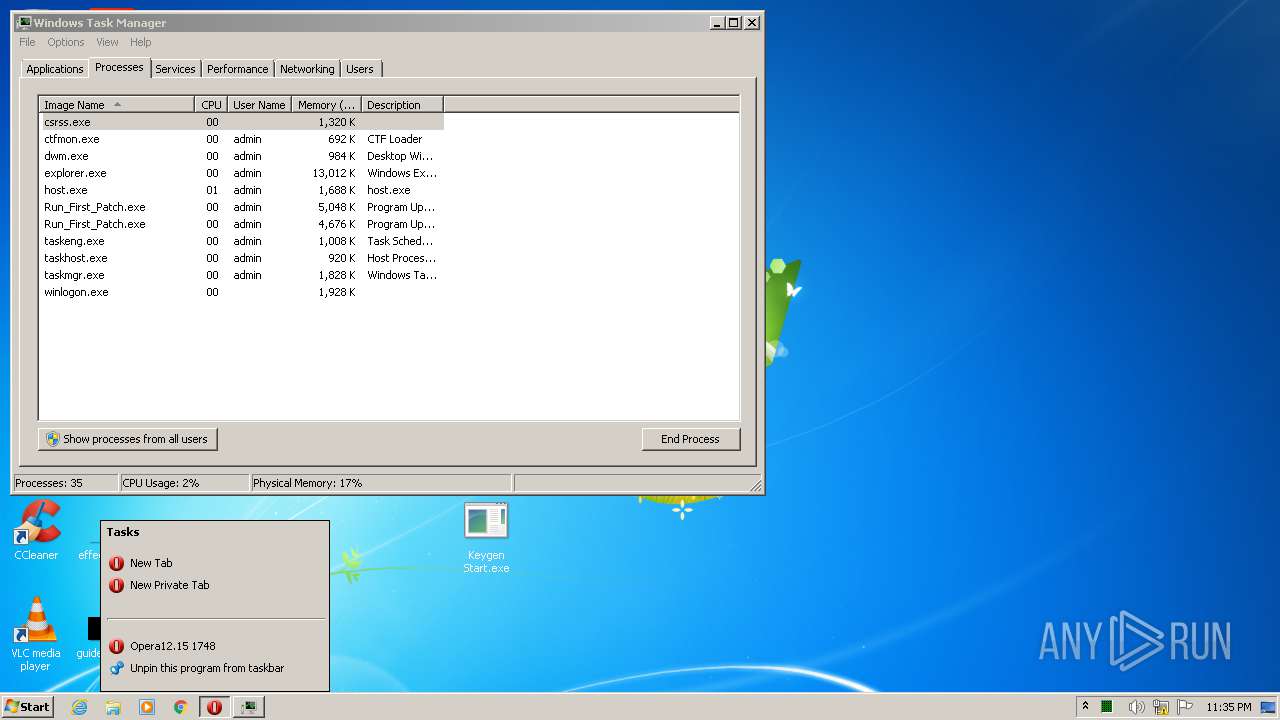
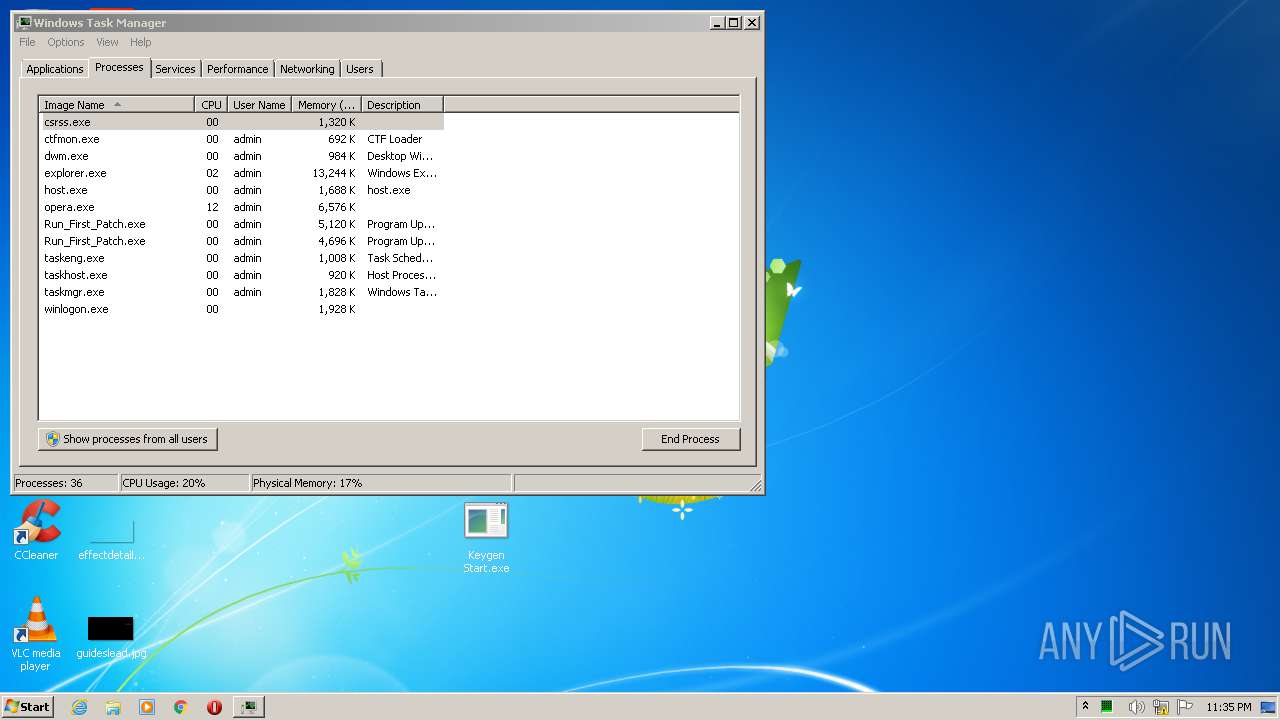
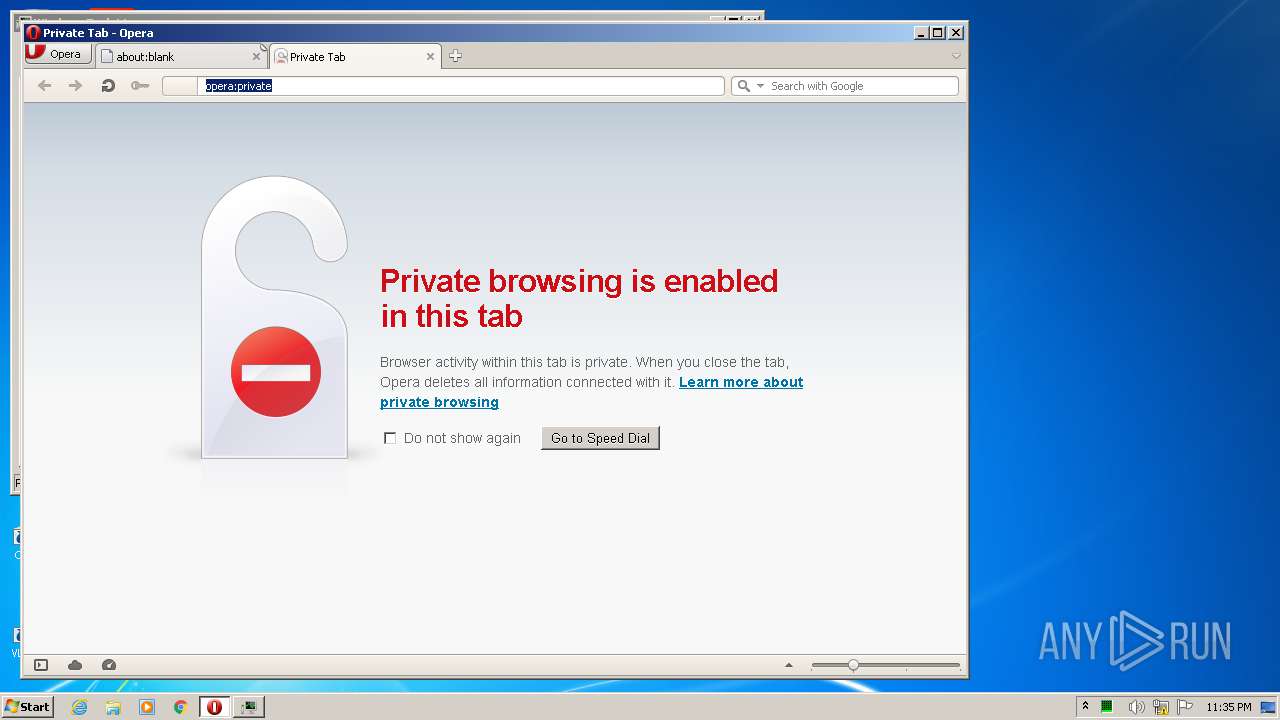
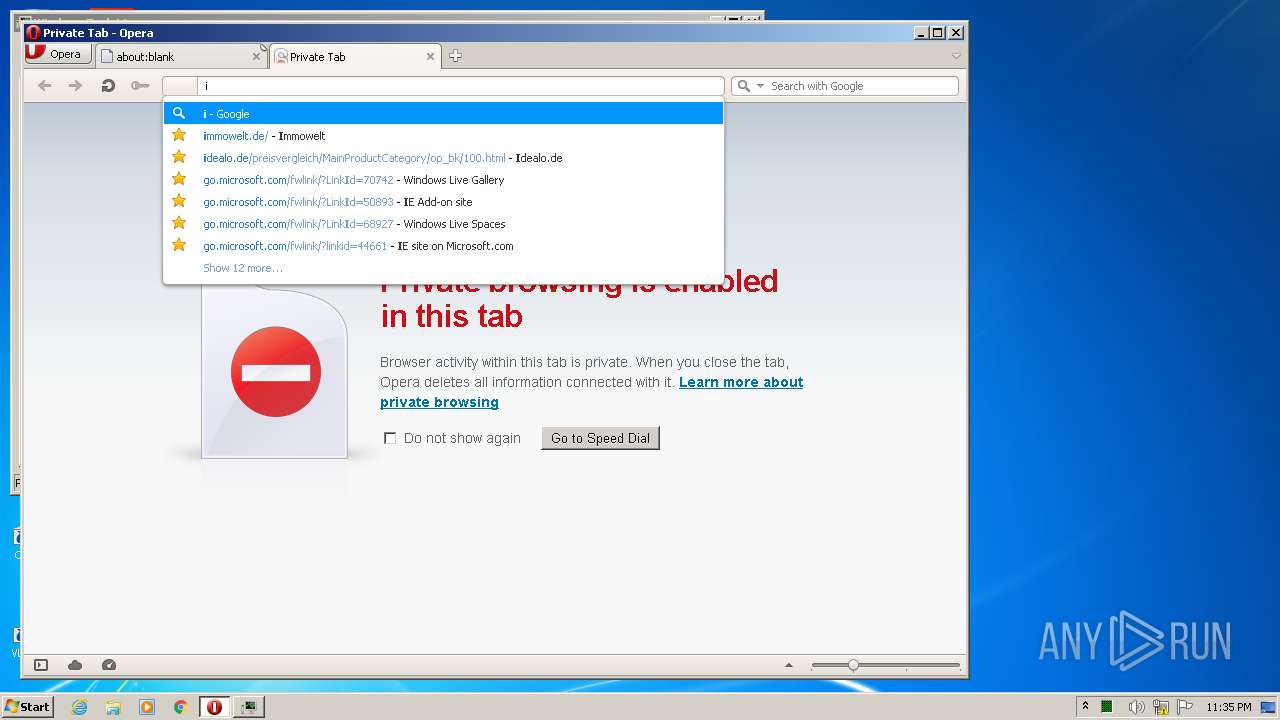
- opera.exe (PID: 8460)
Creates files in the user directory
- opera.exe (PID: 8460)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (82.9) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (7.4) |
| .exe | | | Win32 Executable (generic) (5.1) |
| .exe | | | Generic Win/DOS Executable (2.2) |
| .exe | | | DOS Executable Generic (2.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:05:01 23:28:19+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 11 |
| CodeSize: | 38912 |
| InitializedDataSize: | 2048 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xb7ee |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.1.0.0 |
| ProductVersionNumber: | 1.1.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | Update |
| CompanyName: | Github |
| FileDescription: | Program Update |
| FileVersion: | 1.1.0.0 |
| InternalName: | RunFirstPatch.exe |
| LegalCopyright: | Copyright © GitHub 2013-2015 |
| OriginalFileName: | RunFirstPatch.exe |
| ProductName: | Update |
| ProductVersion: | 1.1.0.0 |
| AssemblyVersion: | 1.1.0.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 01-May-2020 21:28:19 |
| Comments: | Update |
| CompanyName: | Github |
| FileDescription: | Program Update |
| FileVersion: | 1.1.0.0 |
| InternalName: | RunFirstPatch.exe |
| LegalCopyright: | Copyright © GitHub 2013-2015 |
| OriginalFilename: | RunFirstPatch.exe |
| ProductName: | Update |
| ProductVersion: | 1.1.0.0 |
| Assembly Version: | 1.1.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 01-May-2020 21:28:19 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x000097F4 | 0x00009800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 4.9689 |
.rsrc | 0x0000C000 | 0x000005C8 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.14835 |
.reloc | 0x0000E000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.0815394 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.00112 | 490 | UNKNOWN | UNKNOWN | RT_MANIFEST |
Imports
mscoree.dll |
Total processes
50
Monitored processes
10
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1208 | "C:\Users\admin\AppData\Roaming\Cortana\Run_First_Patch.exe" | C:\Users\admin\AppData\Roaming\Cortana\Run_First_Patch.exe | — | Keygen Start.exe | |||||||||||
User: admin Company: Github Integrity Level: MEDIUM Description: Program Update Exit code: 0 Version: 1.1.0.0 Modules
| |||||||||||||||
| 1840 | "C:\Windows\System32\cmd.exe" /c schtasks.exe /create /tn "Updater" /tr "C:\Users\admin\AppData\Roaming\Cortana\Run_First_Patch.exe" /SC MINUTE /mo 1 | C:\Windows\System32\cmd.exe | — | Keygen Start.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2480 | "C:\Users\admin\Desktop\Keygen Start.exe" | C:\Users\admin\Desktop\Keygen Start.exe | explorer.exe | ||||||||||||
User: admin Company: Github Integrity Level: HIGH Description: Program Update Exit code: 0 Version: 1.1.0.0 Modules
| |||||||||||||||
| 2852 | "C:\Users\admin\Desktop\Keygen Start.exe" | C:\Users\admin\Desktop\Keygen Start.exe | explorer.exe | ||||||||||||
User: admin Company: Github Integrity Level: MEDIUM Description: Program Update Exit code: 0 Version: 1.1.0.0 Modules
| |||||||||||||||
| 3232 | schtasks.exe /create /tn "Updater" /tr "C:\Users\admin\AppData\Roaming\Cortana\Run_First_Patch.exe" /SC MINUTE /mo 1 | C:\Windows\system32\schtasks.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3236 | "C:\Users\admin\Desktop\Keygen Start.exe" | C:\Users\admin\Desktop\Keygen Start.exe | — | explorer.exe | |||||||||||
User: admin Company: Github Integrity Level: MEDIUM Description: Program Update Exit code: 0 Version: 1.1.0.0 Modules
| |||||||||||||||
| 3660 | "C:\Users\admin\Desktop\Keygen Start.exe" | C:\Users\admin\Desktop\Keygen Start.exe | — | explorer.exe | |||||||||||
User: admin Company: Github Integrity Level: MEDIUM Description: Program Update Exit code: 0 Version: 1.1.0.0 Modules
| |||||||||||||||
| 4164 | C:\Users\admin\AppData\Roaming\Cortana\Run_First_Patch.exe | C:\Users\admin\AppData\Roaming\Cortana\Run_First_Patch.exe | — | taskeng.exe | |||||||||||
User: admin Company: Github Integrity Level: MEDIUM Description: Program Update Exit code: 0 Version: 1.1.0.0 Modules
| |||||||||||||||
| 6352 | "C:\Windows\system32\taskmgr.exe" /4 | C:\Windows\system32\taskmgr.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Task Manager Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 8460 | "C:\Program Files\Opera\opera.exe" -newprivatetab | C:\Program Files\Opera\opera.exe | explorer.exe | ||||||||||||
User: admin Company: Opera Software Integrity Level: MEDIUM Description: Opera Internet Browser Exit code: 0 Version: 1748 Modules
| |||||||||||||||
Total events
858
Read events
709
Write events
149
Delete events
0
Modification events
| (PID) Process: | (2852) Keygen Start.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | Cortana Updater |
Value: C:\Users\admin\AppData\Roaming\Cortana\Run_First_Patch.exe | |||
| (PID) Process: | (2852) Keygen Start.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2852) Keygen Start.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2852) Keygen Start.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Keygen Start_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2852) Keygen Start.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Keygen Start_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2852) Keygen Start.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Keygen Start_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2852) Keygen Start.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Keygen Start_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2852) Keygen Start.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Keygen Start_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (2852) Keygen Start.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Keygen Start_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (2852) Keygen Start.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Keygen Start_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
Executable files
1
Suspicious files
48
Text files
11
Unknown types
12
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 8460 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\sessions\oprA472.tmp | — | |
MD5:— | SHA256:— | |||
| 8460 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\oprA473.tmp | — | |
MD5:— | SHA256:— | |||
| 8460 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\oprA4B3.tmp | — | |
MD5:— | SHA256:— | |||
| 8460 | opera.exe | C:\Users\admin\AppData\Local\Opera\Opera\cache\sesn\opr00001.tmp | — | |
MD5:— | SHA256:— | |||
| 8460 | opera.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\EDP2YKP5E07E62V9JZ7V.temp | — | |
MD5:— | SHA256:— | |||
| 8460 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\oprE372.tmp | — | |
MD5:— | SHA256:— | |||
| 8460 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\operaprefs.ini | text | |
MD5:— | SHA256:— | |||
| 2852 | Keygen Start.exe | C:\Users\admin\AppData\Roaming\Cortana\Run_First_Patch.exe | executable | |
MD5:— | SHA256:— | |||
| 8460 | opera.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\2YKFEIFNH4Y38CVO4WFW.temp | — | |
MD5:— | SHA256:— | |||
| 8460 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\sessions\autosave.win | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
22
TCP/UDP connections
74
DNS requests
38
Threats
16
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
8460 | opera.exe | GET | 200 | 2.16.186.11:80 | http://ocsp.int-x3.letsencrypt.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBR%2B5mrncpqz%2FPiiIGRsFqEtYHEIXQQUqEpqYwR93brm0Tm3pkVl7%2FOo7KECEgObfHHgHlsa0R7fVL2Sj72S7g%3D%3D | unknown | der | 527 b | whitelisted |
8460 | opera.exe | GET | 200 | 93.184.220.29:80 | http://crl4.digicert.com/DigiCertHighAssuranceEVRootCA.crl | US | der | 592 b | whitelisted |
8460 | opera.exe | GET | 200 | 172.217.18.3:80 | http://ocsp.pki.goog/gts1o1core/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEHd7gOri6w9kCAAAAABNncw%3D | US | der | 471 b | whitelisted |
8460 | opera.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.sectigo.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBQh80WaEMqmyEvaHjlisSfVM4p8SAQUF9nWJSdn%2BTHCSUPZMDZEjGypT%2BsCEQDEaJCNDIKa86QoNjLIdlay | US | der | 472 b | whitelisted |
8460 | opera.exe | GET | 200 | 172.217.18.3:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQD%2F%2B1AZzq8MRwIAAAAAc8vb | US | der | 472 b | whitelisted |
8460 | opera.exe | GET | 200 | 192.35.177.64:80 | http://crl.identrust.com/DSTROOTCAX3CRL.crl | US | der | 994 b | whitelisted |
8460 | opera.exe | GET | 200 | 172.217.18.3:80 | http://ocsp.pki.goog/gts1o1core/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEHOAWRr6KWpJCAAAAABNnhs%3D | US | der | 471 b | whitelisted |
8460 | opera.exe | GET | 200 | 172.217.18.3:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQCiXMxMjl1fvwIAAAAAc8tg | US | der | 472 b | whitelisted |
8460 | opera.exe | GET | 200 | 151.139.128.14:80 | http://crl.usertrust.com/USERTrustRSACertificationAuthority.crl | US | der | 922 b | whitelisted |
8460 | opera.exe | GET | 200 | 93.184.220.29:80 | http://crl3.digicert.com/DigiCertGlobalRootCA.crl | US | der | 631 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
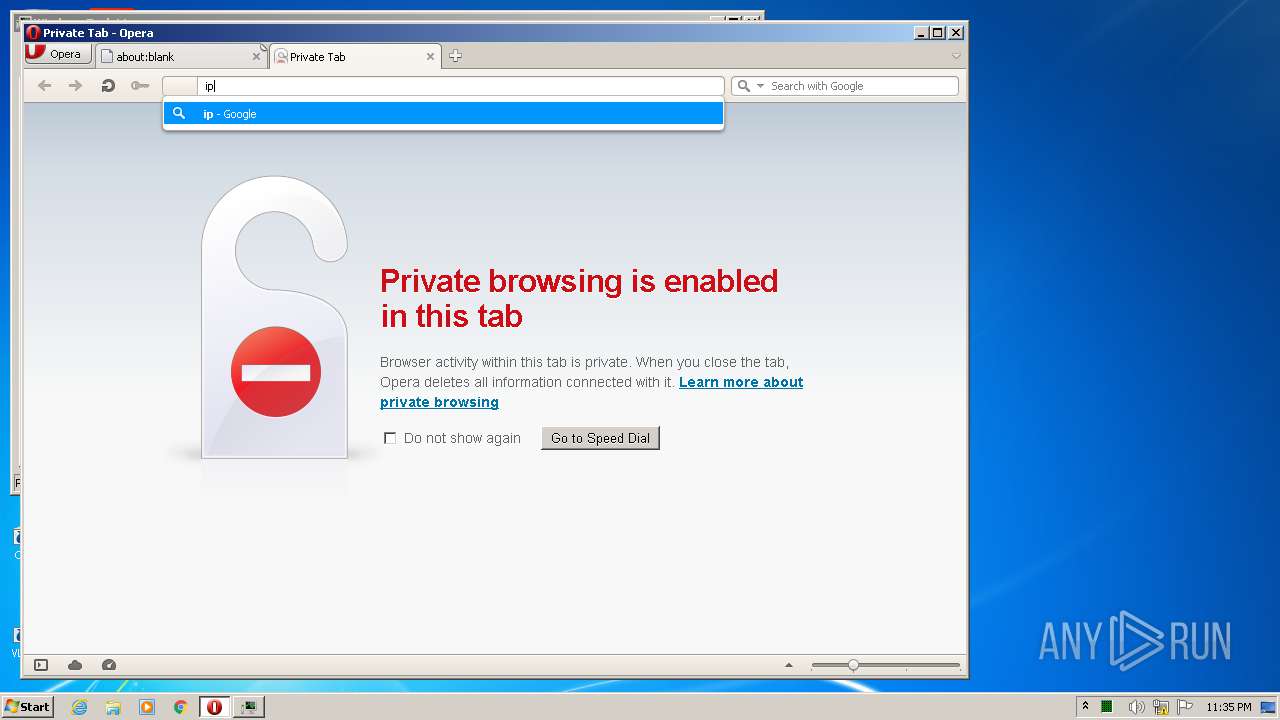
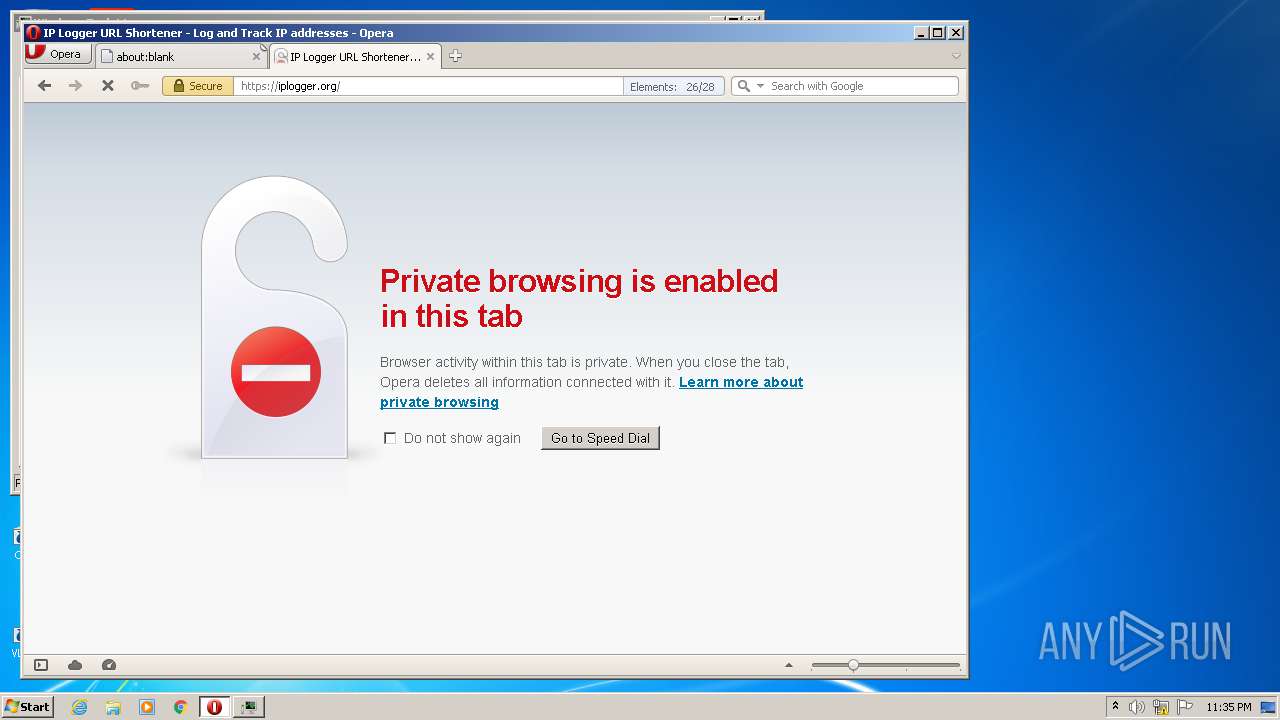
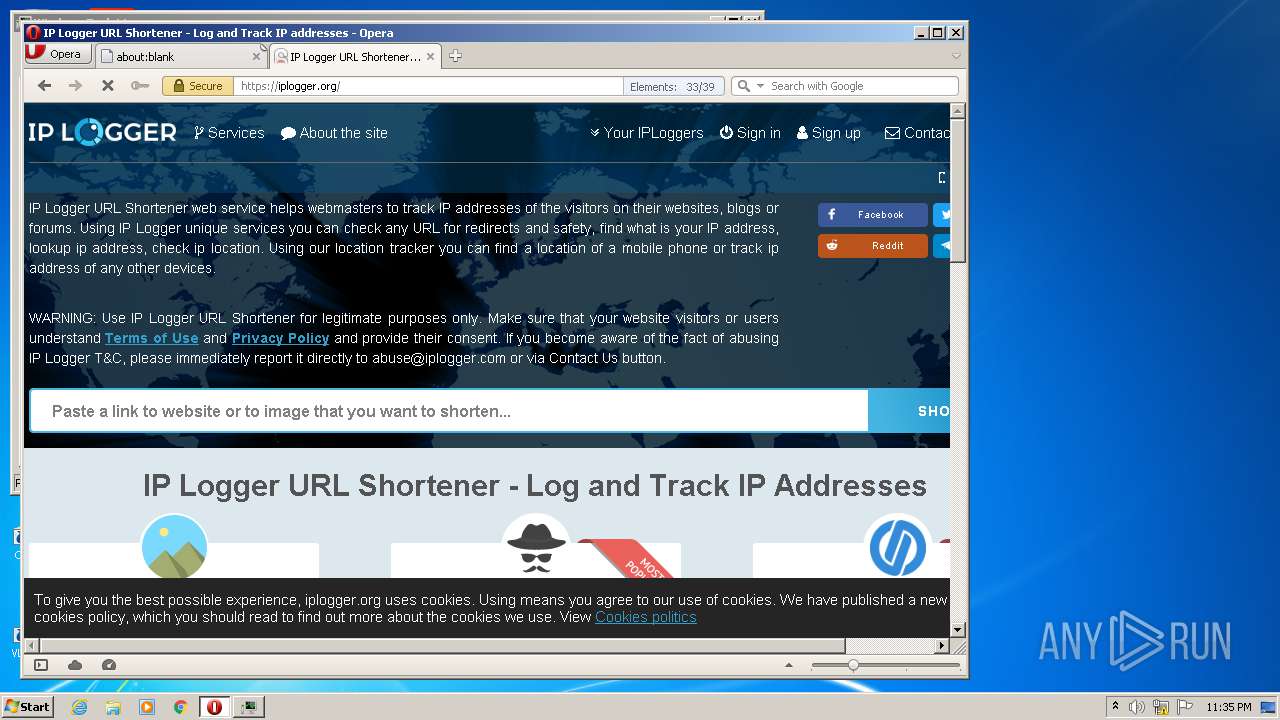
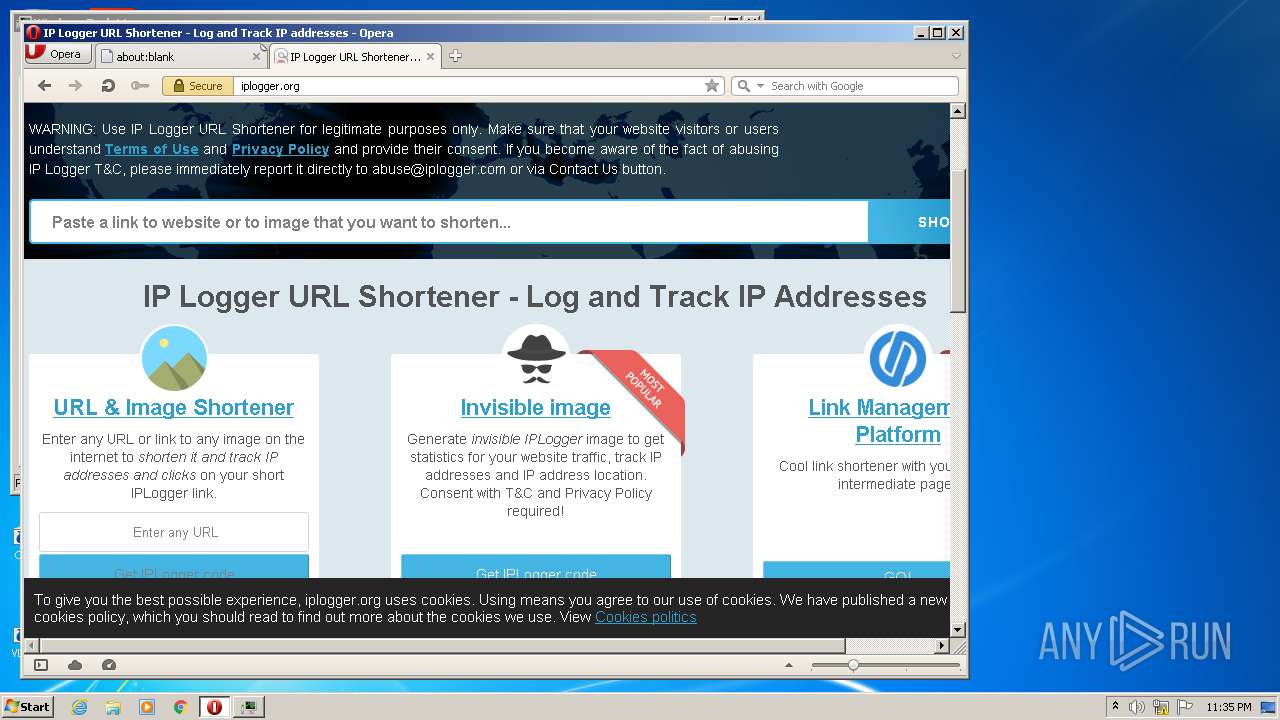
2852 | Keygen Start.exe | 88.99.66.31:443 | iplogger.org | Hetzner Online GmbH | DE | malicious |
8460 | opera.exe | 185.26.182.94:443 | certs.opera.com | Opera Software AS | — | whitelisted |
8460 | opera.exe | 88.99.66.31:80 | iplogger.org | Hetzner Online GmbH | DE | malicious |
8460 | opera.exe | 93.184.220.29:80 | crl4.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
8460 | opera.exe | 185.26.182.94:80 | certs.opera.com | Opera Software AS | — | whitelisted |
8460 | opera.exe | 88.99.66.31:443 | iplogger.org | Hetzner Online GmbH | DE | malicious |
8460 | opera.exe | 192.35.177.64:80 | crl.identrust.com | IdenTrust | US | malicious |
8460 | opera.exe | 2.16.186.11:80 | ocsp.int-x3.letsencrypt.org | Akamai International B.V. | — | whitelisted |
8460 | opera.exe | 216.58.205.234:443 | ajax.googleapis.com | Google Inc. | US | whitelisted |
8460 | opera.exe | 172.217.16.130:443 | pagead2.googlesyndication.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
iplogger.org |
| shared |
certs.opera.com |
| whitelisted |
crl4.digicert.com |
| whitelisted |
sitecheck2.opera.com |
| whitelisted |
crl.identrust.com |
| whitelisted |
ocsp.int-x3.letsencrypt.org |
| whitelisted |
ajax.googleapis.com |
| whitelisted |
m.servedby-buysellads.com |
| whitelisted |
pagead2.googlesyndication.com |
| whitelisted |
unpkg.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2852 | Keygen Start.exe | Potential Corporate Privacy Violation | POLICY [PTsecurity] IP Check Domain SSL certificate |
2852 | Keygen Start.exe | Potential Corporate Privacy Violation | POLICY [PTsecurity] IP Check Domain SSL certificate |
8460 | opera.exe | Potential Corporate Privacy Violation | POLICY [PTsecurity] IP Check Domain SSL certificate |
8460 | opera.exe | Potential Corporate Privacy Violation | POLICY [PTsecurity] IP Check Domain SSL certificate |
8460 | opera.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
8460 | opera.exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |
10 ETPRO signatures available at the full report