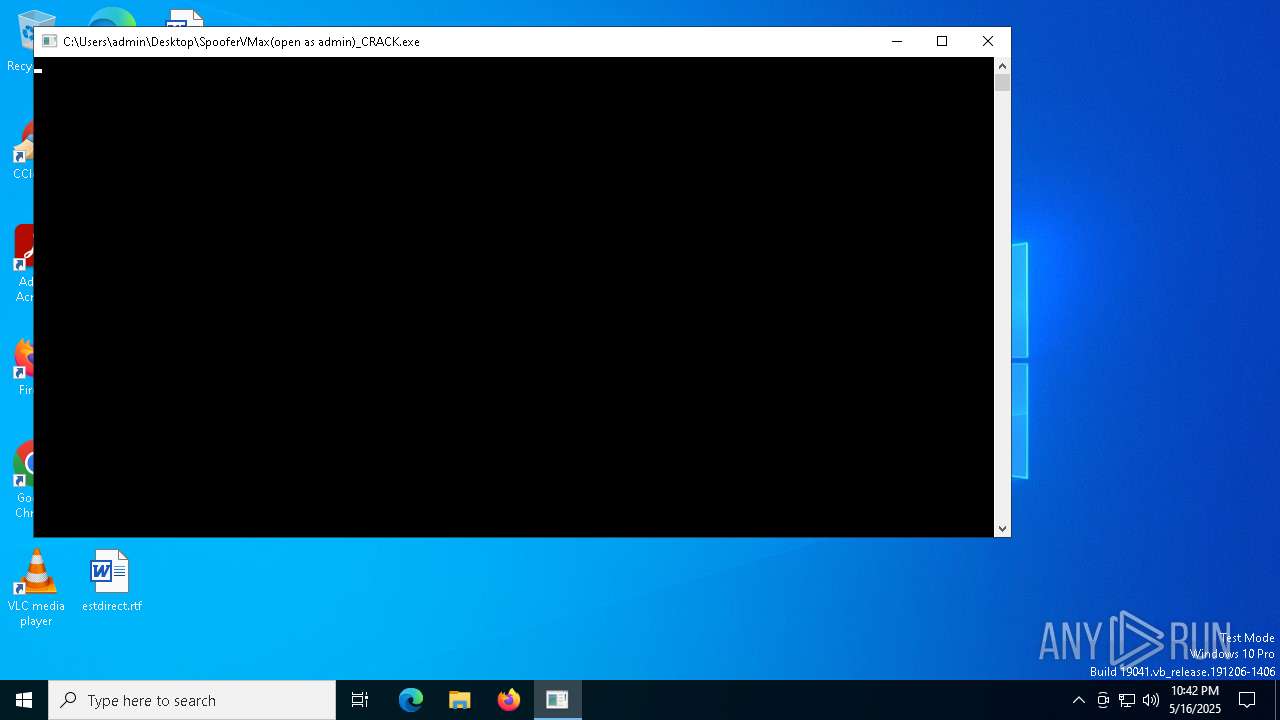
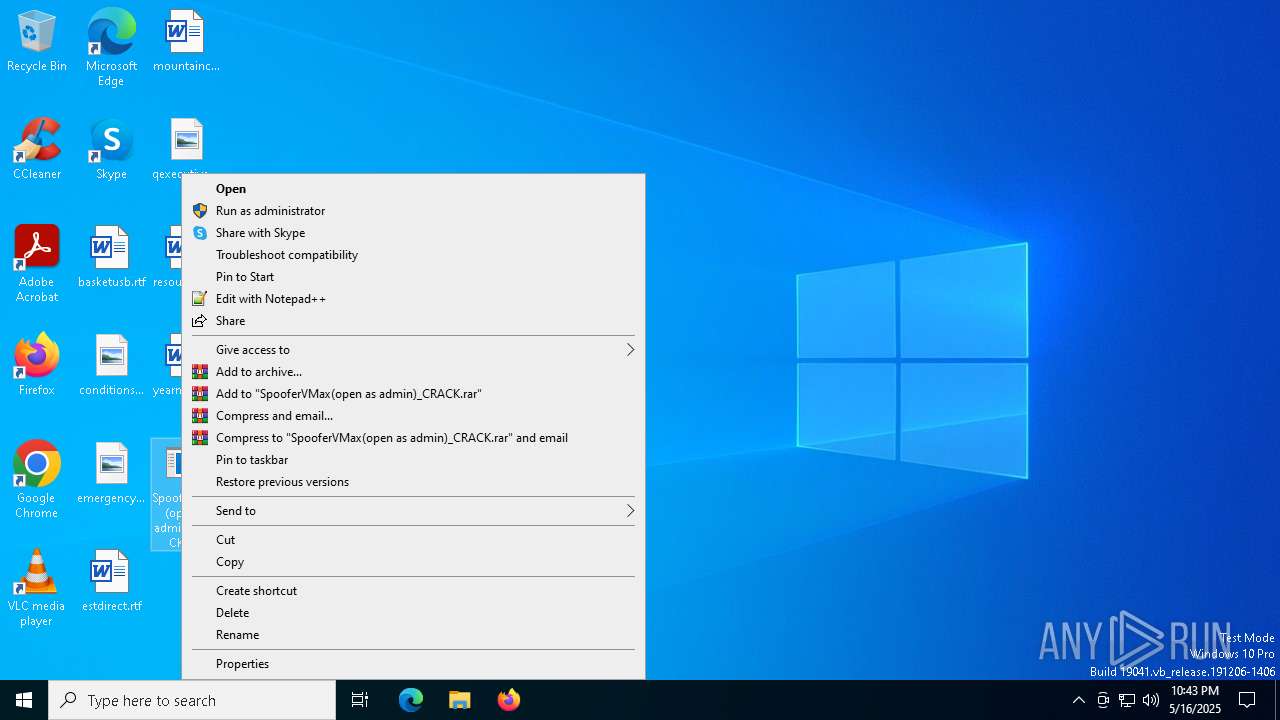
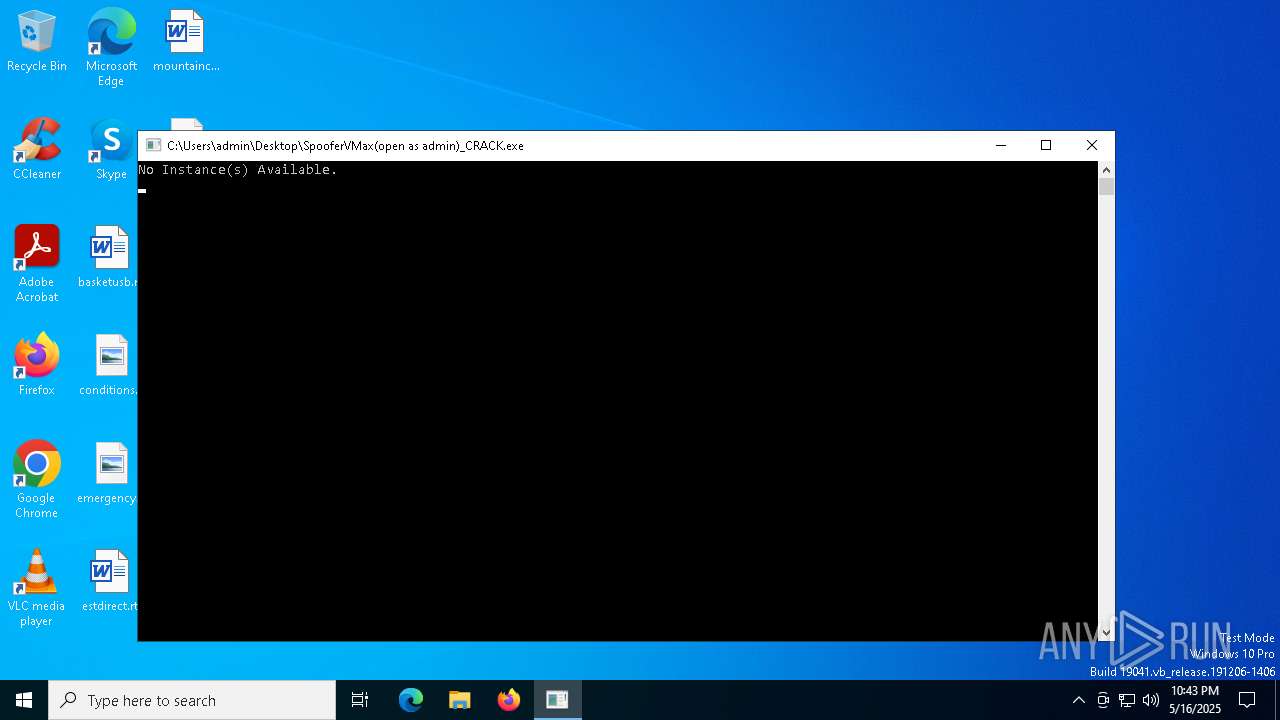
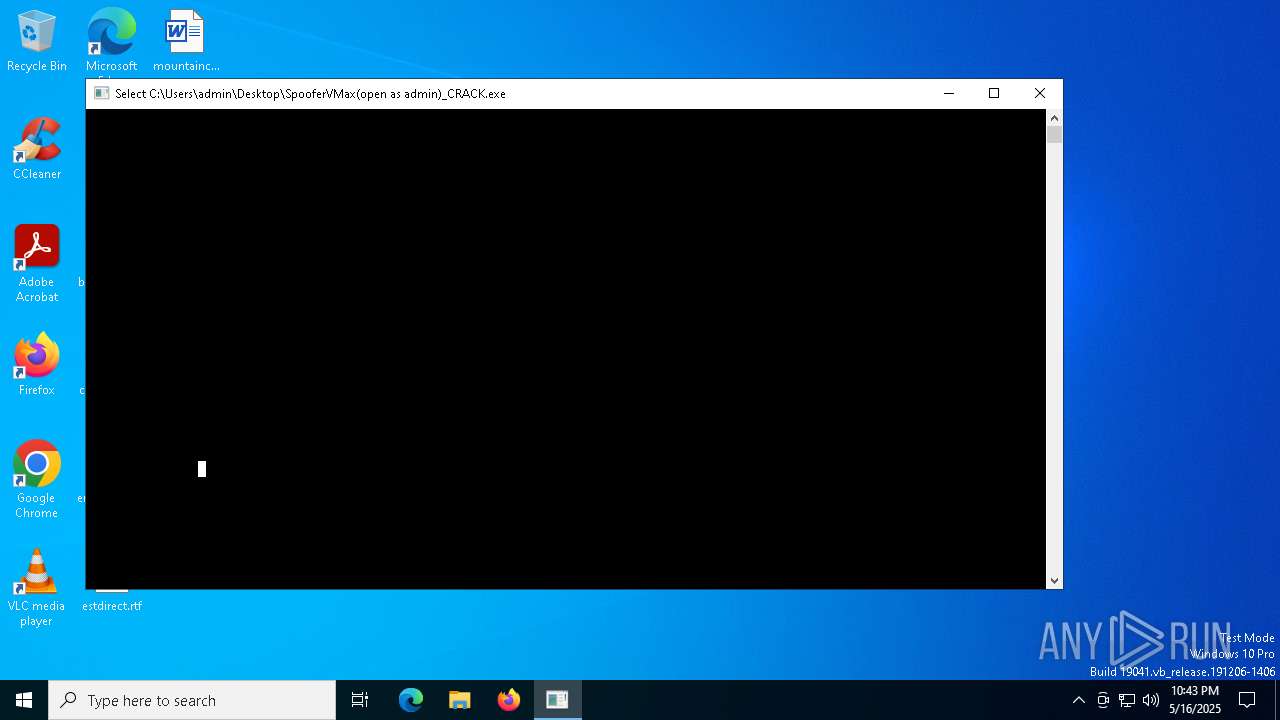
| File name: | SpooferVMax(open as admin)_CRACK.exe |
| Full analysis: | https://app.any.run/tasks/7a36005f-f2b0-479e-9217-11e828aa1f55 |
| Verdict: | Malicious activity |
| Analysis date: | May 16, 2025, 22:42:53 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (console) x86-64, for MS Windows, 6 sections |
| MD5: | 406482283A5FACBED225529D5099FA68 |
| SHA1: | 096FE20697593B1ABDD4156D7B19059E28C22444 |
| SHA256: | A9564B62F481AA802D5E28DFA6299B540F11A44781AA349831A9D5E56FC54712 |
| SSDEEP: | 24576:8AAd9d5PmiEWT563RO3eBqVkW++FfnjEIUuUCUD2N1U1U5UpA1s:8xmiEG563ROuBqmW++tY81s |
MALICIOUS
No malicious indicators.SUSPICIOUS
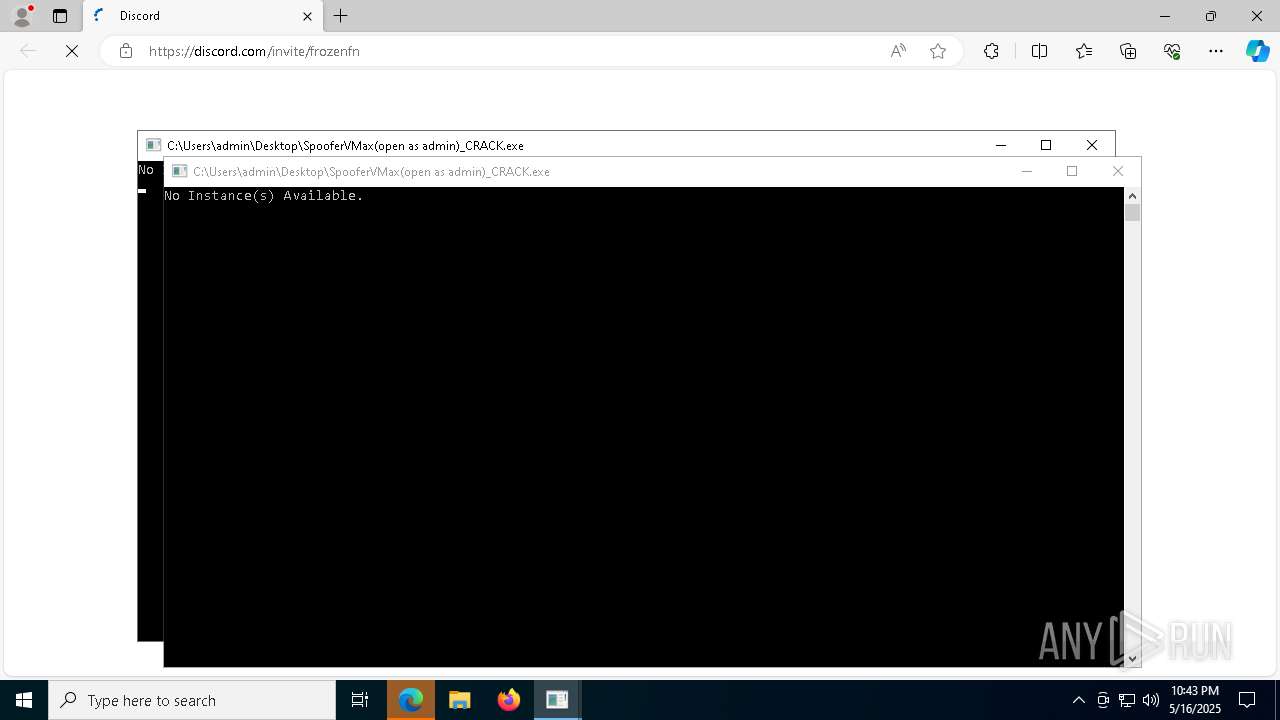
Uses WMIC.EXE to obtain data on the base board management (motherboard or system board)
- cmd.exe (PID: 2384)
- cmd.exe (PID: 7572)
- cmd.exe (PID: 1276)
- cmd.exe (PID: 7964)
- cmd.exe (PID: 6404)
- cmd.exe (PID: 7424)
Starts CMD.EXE for commands execution
- SpooferVMax(open as admin)_CRACK.exe (PID: 6108)
- SpooferVMax(open as admin)_CRACK.exe (PID: 7432)
- SpooferVMax(open as admin)_CRACK.exe (PID: 4980)
- SpooferVMax(open as admin)_CRACK.exe (PID: 7996)
- SpooferVMax(open as admin)_CRACK.exe (PID: 7012)
- SpooferVMax(open as admin)_CRACK.exe (PID: 7928)
Reads security settings of Internet Explorer
- SpooferVMax(open as admin)_CRACK.exe (PID: 6108)
- SpooferVMax(open as admin)_CRACK.exe (PID: 7432)
- SpooferVMax(open as admin)_CRACK.exe (PID: 4980)
- SpooferVMax(open as admin)_CRACK.exe (PID: 7996)
- SpooferVMax(open as admin)_CRACK.exe (PID: 7012)
- SpooferVMax(open as admin)_CRACK.exe (PID: 7928)
Uses WMIC.EXE to obtain Windows Installer data
- cmd.exe (PID: 7800)
- cmd.exe (PID: 7292)
- cmd.exe (PID: 5384)
- cmd.exe (PID: 6800)
- cmd.exe (PID: 7556)
Accesses product unique identifier via WMI (SCRIPT)
- WMIC.exe (PID: 7620)
- WMIC.exe (PID: 7320)
- WMIC.exe (PID: 6676)
- WMIC.exe (PID: 516)
- WMIC.exe (PID: 7880)
INFO
Checks supported languages
- SpooferVMax(open as admin)_CRACK.exe (PID: 6108)
- SpooferVMax(open as admin)_CRACK.exe (PID: 7432)
- identity_helper.exe (PID: 7224)
- identity_helper.exe (PID: 7604)
- SpooferVMax(open as admin)_CRACK.exe (PID: 7996)
- identity_helper.exe (PID: 7752)
- SpooferVMax(open as admin)_CRACK.exe (PID: 4980)
- SpooferVMax(open as admin)_CRACK.exe (PID: 7012)
- SpooferVMax(open as admin)_CRACK.exe (PID: 7928)
Reads security settings of Internet Explorer
- WMIC.exe (PID: 5256)
- WMIC.exe (PID: 7680)
- WMIC.exe (PID: 7620)
- WMIC.exe (PID: 7392)
- WMIC.exe (PID: 7320)
- WMIC.exe (PID: 736)
- WMIC.exe (PID: 6676)
- WMIC.exe (PID: 5728)
- WMIC.exe (PID: 8120)
- WMIC.exe (PID: 7880)
- WMIC.exe (PID: 516)
Creates files in the program directory
- SpooferVMax(open as admin)_CRACK.exe (PID: 6108)
Reads the computer name
- SpooferVMax(open as admin)_CRACK.exe (PID: 6108)
- SpooferVMax(open as admin)_CRACK.exe (PID: 7432)
- identity_helper.exe (PID: 7224)
- identity_helper.exe (PID: 7604)
- identity_helper.exe (PID: 7752)
- SpooferVMax(open as admin)_CRACK.exe (PID: 4980)
- SpooferVMax(open as admin)_CRACK.exe (PID: 7996)
- SpooferVMax(open as admin)_CRACK.exe (PID: 7012)
- SpooferVMax(open as admin)_CRACK.exe (PID: 7928)
Manual execution by a user
- SpooferVMax(open as admin)_CRACK.exe (PID: 7432)
- SpooferVMax(open as admin)_CRACK.exe (PID: 7996)
- SpooferVMax(open as admin)_CRACK.exe (PID: 4980)
- SpooferVMax(open as admin)_CRACK.exe (PID: 7928)
- SpooferVMax(open as admin)_CRACK.exe (PID: 7012)
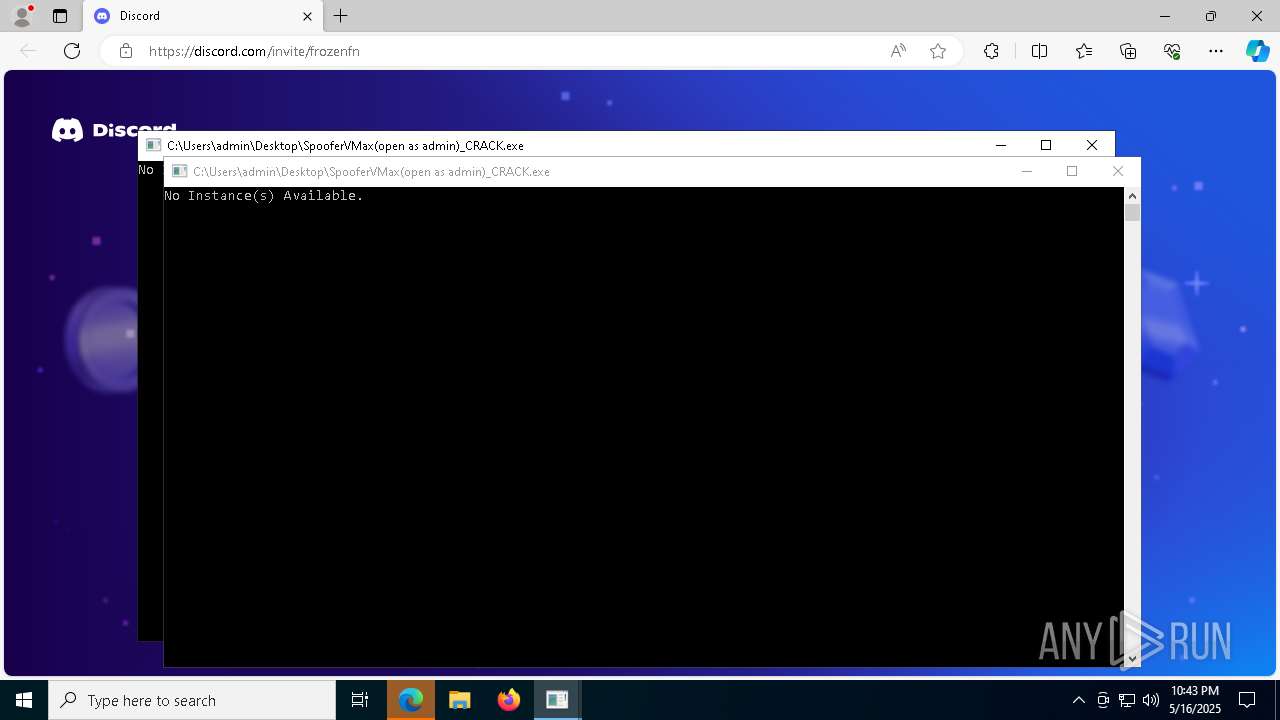
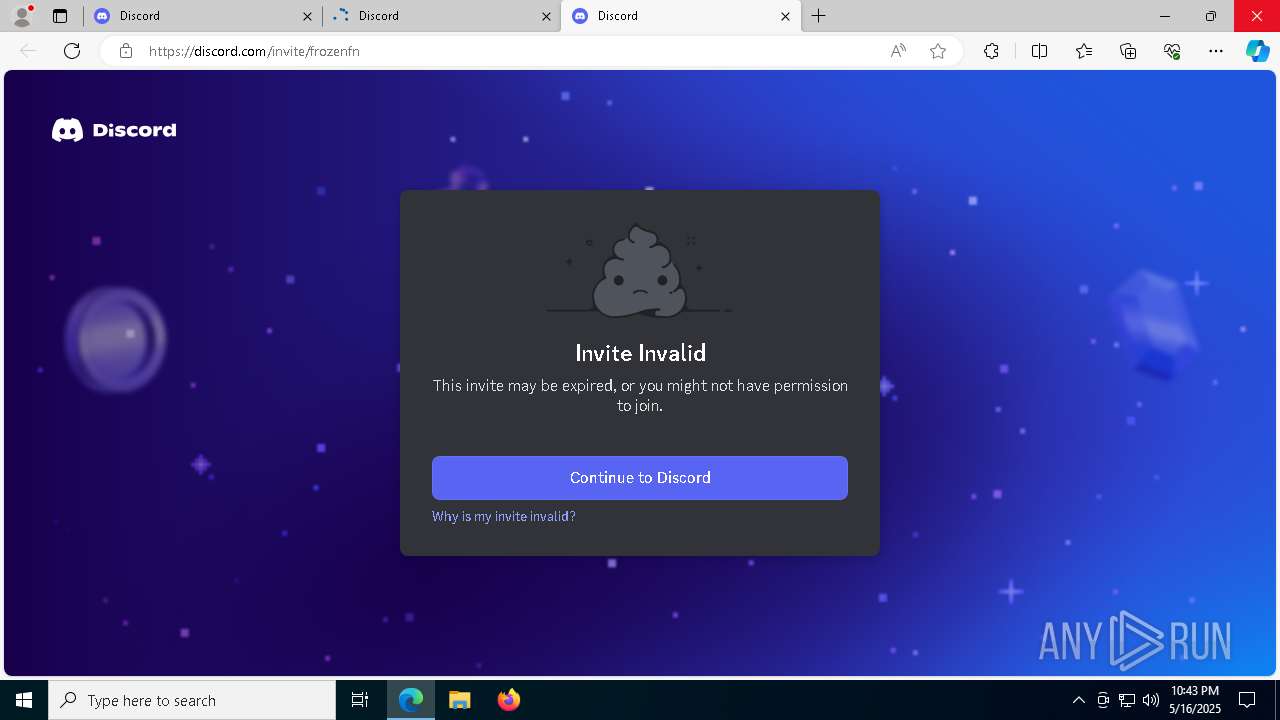
Attempting to use instant messaging service
- msedge.exe (PID: 7808)
- msedge.exe (PID: 8176)
- msedge.exe (PID: 5400)
- msedge.exe (PID: 7952)
Application launched itself
- msedge.exe (PID: 7480)
- msedge.exe (PID: 8128)
- msedge.exe (PID: 8112)
- msedge.exe (PID: 4488)
Gets the hash of the file via CERTUTIL.EXE
- certutil.exe (PID: 8000)
- certutil.exe (PID: 8100)
- certutil.exe (PID: 6028)
- certutil.exe (PID: 1056)
- certutil.exe (PID: 3332)
Reads Environment values
- identity_helper.exe (PID: 7224)
- identity_helper.exe (PID: 7604)
- identity_helper.exe (PID: 7752)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2024:07:01 15:35:56+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.4 |
| CodeSize: | 568832 |
| InitializedDataSize: | 169984 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x8741c |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows command line |
Total processes
280
Monitored processes
150
Malicious processes
0
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 516 | wmic csproduct get uuid | C:\Windows\System32\wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: WMI Commandline Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 668 | C:\WINDOWS\system32\cmd.exe /c certutil -hashfile "C:\Users\admin\Desktop\SpooferVMax(open as admin)_CRACK.exe" MD5 | find /i /v "md5" | find /i /v "certutil" | C:\Windows\System32\cmd.exe | — | SpooferVMax(open as admin)_CRACK.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 736 | wmic baseboard get serialnumber | C:\Windows\System32\wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: WMI Commandline Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 864 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=3704 --field-trial-handle=2420,i,10938996564821951780,10443302760277209678,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 864 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6732 --field-trial-handle=2324,i,7675637728526107052,3693385550186448405,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1040 | find /i /v "certutil" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (grep) Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1056 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=14 --mojo-platform-channel-handle=4228 --field-trial-handle=2476,i,9500446582915188717,7478864536760454494,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1056 | certutil -hashfile "C:\Users\admin\Desktop\SpooferVMax(open as admin)_CRACK.exe" MD5 | C:\Windows\System32\certutil.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: CertUtil.exe Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1072 | find /i /v "certutil" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (grep) Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1096 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=2696 --field-trial-handle=2476,i,9500446582915188717,7478864536760454494,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
16 044
Read events
15 959
Write events
85
Delete events
0
Modification events
| (PID) Process: | (6108) SpooferVMax(open as admin)_CRACK.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (6108) SpooferVMax(open as admin)_CRACK.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (6108) SpooferVMax(open as admin)_CRACK.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (7480) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\459440 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {F5C72954-73F8-47A5-BF38-A7D49B921D3C} | |||
| (PID) Process: | (7480) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 1 | |||
| (PID) Process: | (7480) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | MicrosoftEdgeAutoLaunch_29EBC4579851B72EE312C449CF839B1A |
Value: "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --no-startup-window --win-session-start | |||
| (PID) Process: | (8128) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (8128) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (8128) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (8128) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
Executable files
22
Suspicious files
302
Text files
114
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7480 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10bcd9.TMP | — | |
MD5:— | SHA256:— | |||
| 7480 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10bcd9.TMP | — | |
MD5:— | SHA256:— | |||
| 7480 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7480 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7480 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10bce9.TMP | — | |
MD5:— | SHA256:— | |||
| 7480 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10bce9.TMP | — | |
MD5:— | SHA256:— | |||
| 7480 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7480 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7480 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10bce9.TMP | — | |
MD5:— | SHA256:— | |||
| 7480 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
73
DNS requests
83
Threats
51
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.180:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
756 | lsass.exe | GET | 200 | 69.192.161.44:80 | http://x1.c.lencr.org/ | unknown | — | — | whitelisted |
7444 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7444 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.48.23.180:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6108 | SpooferVMax(open as admin)_CRACK.exe | 172.67.72.57:443 | keyauth.win | CLOUDFLARENET | US | malicious |
756 | lsass.exe | 69.192.161.44:80 | x1.c.lencr.org | AKAMAI-AS | DE | whitelisted |
— | — | 162.159.128.233:443 | discord.com | — | — | whitelisted |
— | — | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 239.255.255.250:1900 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
keyauth.win |
| malicious |
x1.c.lencr.org |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
discord.gg |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
8176 | msedge.exe | Potentially Bad Traffic | ET INFO KeyAuth Open-source Authentication System Domain in DNS Lookup (keyauth .win) |
6108 | SpooferVMax(open as admin)_CRACK.exe | Potentially Bad Traffic | ET INFO KeyAuth Open-source Authentication System Domain (keyauth .win) in TLS SNI |
8176 | msedge.exe | Misc activity | ET INFO Observed Discord Domain in DNS Lookup (discord .com) |
7808 | msedge.exe | Misc activity | ET INFO Observed Discord Domain (discord .com in TLS SNI) |
8176 | msedge.exe | Misc activity | ET INFO Discord Chat Service Domain in DNS Lookup (discord .com) |
7808 | msedge.exe | Misc activity | ET INFO Observed Discord Service Domain (discord .com) in TLS SNI |
8176 | msedge.exe | Misc activity | ET INFO Observed Discord Domain in DNS Lookup (discord .com) |
8176 | msedge.exe | Misc activity | ET INFO Discord Chat Service Domain in DNS Lookup (discord .com) |
7808 | msedge.exe | Misc activity | ET INFO Observed Discord Domain in DNS Lookup (discord .com) |
7808 | msedge.exe | Misc activity | ET INFO Observed Discord Domain (discord .com in TLS SNI) |