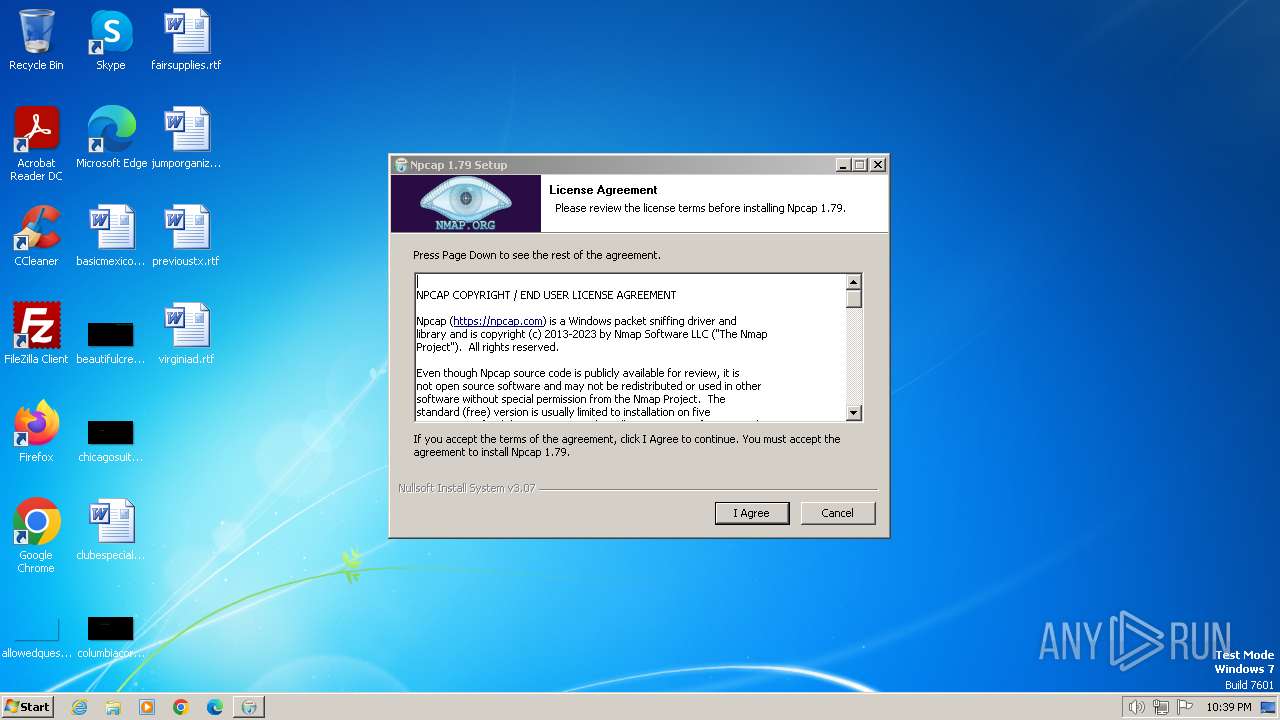
| File name: | npcap-1.79.exe |
| Full analysis: | https://app.any.run/tasks/890c5c97-6cef-4ab9-8de0-7f71d4b8ee38 |
| Verdict: | Malicious activity |
| Analysis date: | June 21, 2024, 21:38:48 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | A4D7E47DF742F62080BF845D606045B4 |
| SHA1: | 723743DC9FA4A190452A7FFC971ADFAAC91606FA |
| SHA256: | A95577EBBC67FC45B319E2EF3A55F4E9B211FE82ED4CB9D8BE6B1A9E2425CE53 |
| SSDEEP: | 49152:D6RKhVd9S1OsrcrMPSqfAQ4HgmY8mMiXZDeEN7sWv3Xu9uJRdSKpt6qUI2fqEFNI:D6YhsoIPSNvY8mMicEN7sGO9cRb6qxGu |
MALICIOUS
Drops the executable file immediately after the start
- npcap-1.79.exe (PID: 2752)
- NPFInstall.exe (PID: 2992)
- drvinst.exe (PID: 1104)
Creates a writable file in the system directory
- npcap-1.79.exe (PID: 2752)
- drvinst.exe (PID: 1104)
- NPFInstall.exe (PID: 2992)
Run PowerShell with an invisible window
- powershell.exe (PID: 3092)
- powershell.exe (PID: 2544)
- powershell.exe (PID: 2588)
- powershell.exe (PID: 2124)
- powershell.exe (PID: 3208)
Uses Task Scheduler to run other applications
- nsD897.tmp (PID: 940)
SUSPICIOUS
Malware-specific behavior (creating "System.dll" in Temp)
- npcap-1.79.exe (PID: 2752)
The process creates files with name similar to system file names
- npcap-1.79.exe (PID: 2752)
Executable content was dropped or overwritten
- npcap-1.79.exe (PID: 2752)
- NPFInstall.exe (PID: 2992)
- drvinst.exe (PID: 1104)
Starts application with an unusual extension
- npcap-1.79.exe (PID: 2752)
Starts CMD.EXE for commands execution
- nsF636.tmp (PID: 2960)
Uses WMIC.EXE to obtain quick Fix Engineering (patches) data
- cmd.exe (PID: 540)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 540)
Reads the Internet Settings
- WMIC.exe (PID: 3144)
Drops a system driver (possible attempt to evade defenses)
- npcap-1.79.exe (PID: 2752)
- drvinst.exe (PID: 1104)
- NPFInstall.exe (PID: 2992)
Creates a software uninstall entry
- npcap-1.79.exe (PID: 2752)
The process hide an interactive prompt from the user
- ns46AA.tmp (PID: 964)
- ns5021.tmp (PID: 656)
- ns59C9.tmp (PID: 2000)
- ns6207.tmp (PID: 2756)
- nsCD99.tmp (PID: 3428)
Starts POWERSHELL.EXE for commands execution
- ns46AA.tmp (PID: 964)
- ns5021.tmp (PID: 656)
- ns59C9.tmp (PID: 2000)
- ns6207.tmp (PID: 2756)
- nsCD99.tmp (PID: 3428)
The process bypasses the loading of PowerShell profile settings
- ns46AA.tmp (PID: 964)
- ns5021.tmp (PID: 656)
- ns59C9.tmp (PID: 2000)
- ns6207.tmp (PID: 2756)
- nsCD99.tmp (PID: 3428)
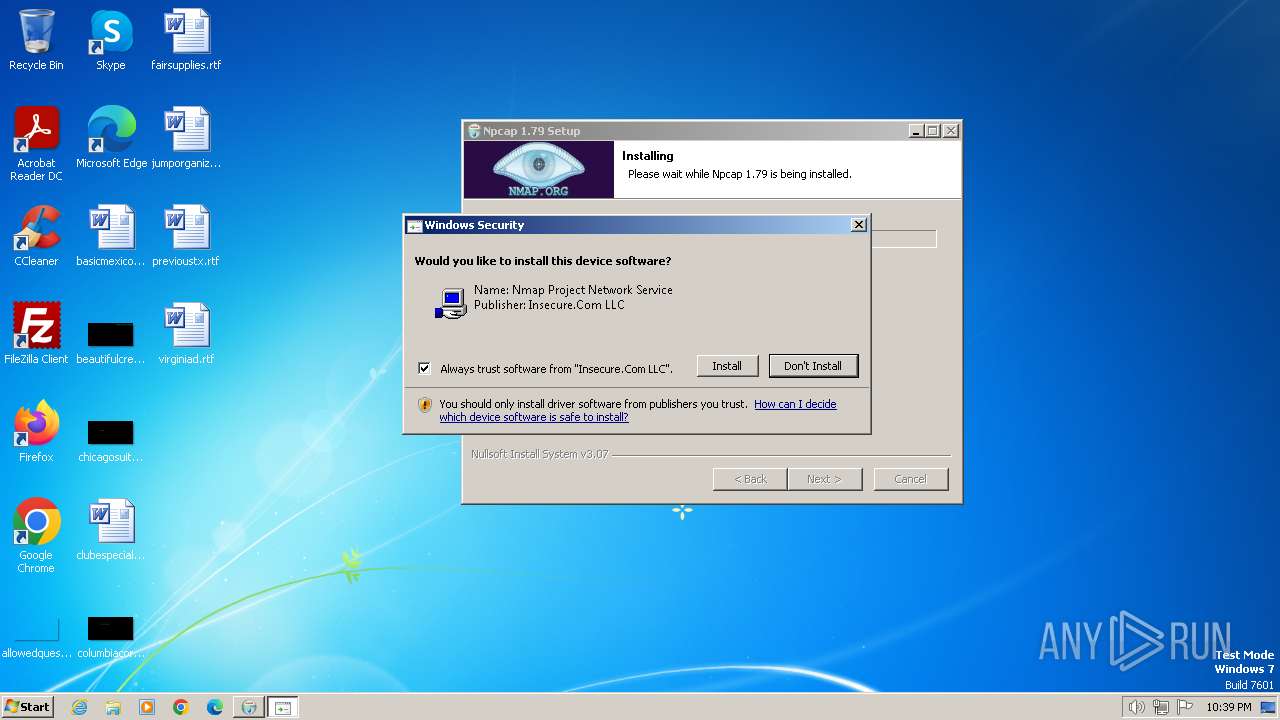
Adds/modifies Windows certificates
- certutil.exe (PID: 2312)
Creates files in the driver directory
- drvinst.exe (PID: 1104)
- NPFInstall.exe (PID: 2992)
Checks Windows Trust Settings
- drvinst.exe (PID: 1104)
- NPFInstall.exe (PID: 2992)
Reads security settings of Internet Explorer
- NPFInstall.exe (PID: 2992)
Reads settings of System Certificates
- rundll32.exe (PID: 3004)
- NPFInstall.exe (PID: 2992)
Executes as Windows Service
- VSSVC.exe (PID: 2456)
Creates or modifies Windows services
- npcap-1.79.exe (PID: 2752)
INFO
Create files in a temporary directory
- npcap-1.79.exe (PID: 2752)
- NPFInstall.exe (PID: 2992)
Checks supported languages
- npcap-1.79.exe (PID: 2752)
- nsF636.tmp (PID: 2960)
- ns4206.tmp (PID: 3856)
- NPFInstall.exe (PID: 3072)
- ns46AA.tmp (PID: 964)
- ns58DD.tmp (PID: 3324)
- ns59C9.tmp (PID: 2000)
- ns5021.tmp (PID: 656)
- ns57E2.tmp (PID: 3512)
- ns6AF3.tmp (PID: 3800)
- ns6207.tmp (PID: 2756)
- ns696B.tmp (PID: 1284)
- ns69F8.tmp (PID: 2884)
- ns6D57.tmp (PID: 2964)
- ns6BEE.tmp (PID: 3824)
- NPFInstall.exe (PID: 3888)
- NPFInstall.exe (PID: 1392)
- NPFInstall.exe (PID: 2992)
- ns6E42.tmp (PID: 2704)
- drvinst.exe (PID: 1104)
- nsCD99.tmp (PID: 3428)
- nsD897.tmp (PID: 940)
Creates files in the program directory
- npcap-1.79.exe (PID: 2752)
- NPFInstall.exe (PID: 3072)
Reads the computer name
- npcap-1.79.exe (PID: 2752)
- NPFInstall.exe (PID: 3072)
- NPFInstall.exe (PID: 1392)
- NPFInstall.exe (PID: 2992)
- drvinst.exe (PID: 1104)
Reads Environment values
- npcap-1.79.exe (PID: 2752)
Reads the machine GUID from the registry
- NPFInstall.exe (PID: 2992)
- drvinst.exe (PID: 1104)
Reads security settings of Internet Explorer
- rundll32.exe (PID: 3004)
Reads the software policy settings
- drvinst.exe (PID: 1104)
- rundll32.exe (PID: 3004)
- NPFInstall.exe (PID: 2992)
Adds/modifies Windows certificates
- drvinst.exe (PID: 1104)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2021:07:24 22:40:31+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 28160 |
| InitializedDataSize: | 152576 |
| UninitializedDataSize: | 2048 |
| EntryPoint: | 0x3a59 |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 5.1.79.117 |
| ProductVersionNumber: | 5.1.79.117 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| FileDescription: | Npcap 1.79 installer |
| FileVersion: | 1.79 |
| LegalCopyright: | Copyright (c) 2023, Insecure.Com LLC. All rights reserved. |
| ProductName: | Npcap |
| ProductVersion: | 1.79 |
Total processes
102
Monitored processes
42
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 400 | C:\Windows\System32\findstr.exe "^KB4474419" | C:\Windows\System32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (QGREP) Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 540 | cmd /Q /C "%SYSTEMROOT%\System32\wbem\wmic.exe qfe get hotfixid | %SYSTEMROOT%\System32\findstr.exe "^KB4474419"" | C:\Windows\System32\cmd.exe | — | nsF636.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 656 | "C:\Users\admin\AppData\Local\Temp\nsaF5D8.tmp\ns5021.tmp" powershell.exe -NoProfile -WindowStyle Hidden -NonInteractive -Command "If (Get-ChildItem Cert:\LocalMachine\Root\0563b8630d62d75abbc8ab1e4bdfb5a899b24d43){certutil.exe -verifystore 'Root' '0563b8630d62d75abbc8ab1e4bdfb5a899b24d43';If($LASTEXITCODE -ne 0){Remove-Item Cert:\LocalMachine\Root\0563b8630d62d75abbc8ab1e4bdfb5a899b24d43}}" | C:\Users\admin\AppData\Local\Temp\nsaF5D8.tmp\ns5021.tmp | — | npcap-1.79.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 940 | "C:\Users\admin\AppData\Local\Temp\nsaF5D8.tmp\nsD897.tmp" SCHTASKS.EXE /Create /F /RU SYSTEM /SC ONSTART /TN npcapwatchdog /TR "'C:\Program Files\Npcap\CheckStatus.bat'" /NP | C:\Users\admin\AppData\Local\Temp\nsaF5D8.tmp\nsD897.tmp | — | npcap-1.79.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 952 | "C:\Windows\system32\certutil.exe" -verifystore Root 5fb7ee0633e259dbad0c4c9ae6d38f1a61c7dc25 | C:\Windows\System32\certutil.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: CertUtil.exe Exit code: 2148073489 Version: 6.1.7601.18151 (win7sp1_gdr.130512-1533) Modules
| |||||||||||||||
| 964 | "C:\Users\admin\AppData\Local\Temp\nsaF5D8.tmp\ns46AA.tmp" powershell.exe -NoProfile -WindowStyle Hidden -NonInteractive -Command "Get-ChildItem Cert:\LocalMachine\Root | Where-Object {$_.Thumbprint -eq '0563b8630d62d75abbc8ab1e4bdfb5a899b24d43'} | Sort-Object -Descending -Property FriendlyName | Select-Object -Skip 1 | Remove-Item" | C:\Users\admin\AppData\Local\Temp\nsaF5D8.tmp\ns46AA.tmp | — | npcap-1.79.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1104 | DrvInst.exe "4" "0" "C:\Users\admin\AppData\Local\Temp\{45ae0cc7-1d09-7b44-98d9-285322697362}\NPCAP.inf" "0" "605306be3" "000002C0" "WinSta0\Default" "000004E0" "208" "C:\Program Files\Npcap" | C:\Windows\System32\drvinst.exe | svchost.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1284 | "C:\Users\admin\AppData\Local\Temp\nsaF5D8.tmp\ns696B.tmp" certutil.exe -verifystore "Root" "5fb7ee0633e259dbad0c4c9ae6d38f1a61c7dc25" | C:\Users\admin\AppData\Local\Temp\nsaF5D8.tmp\ns696B.tmp | — | npcap-1.79.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 2148073489 Modules
| |||||||||||||||
| 1392 | "C:\Program Files\Npcap\NPFInstall.exe" -n -iw | C:\Program Files\Npcap\NPFInstall.exe | — | ns6D57.tmp | |||||||||||
User: admin Company: Insecure.Com LLC. Integrity Level: HIGH Description: A LWF & WFP driver installation tool Exit code: 0 Version: 1.79 Modules
| |||||||||||||||
| 1568 | certutil.exe -addstore -f "Root" "C:\Users\admin\AppData\Local\Temp\nsaF5D8.tmp\5fb7ee0633e259dbad0c4c9ae6d38f1a61c7dc25.sst" | C:\Windows\System32\certutil.exe | — | ns69F8.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: CertUtil.exe Exit code: 2148086027 Version: 6.1.7601.18151 (win7sp1_gdr.130512-1533) Modules
| |||||||||||||||
Total events
42 243
Read events
41 804
Write events
419
Delete events
20
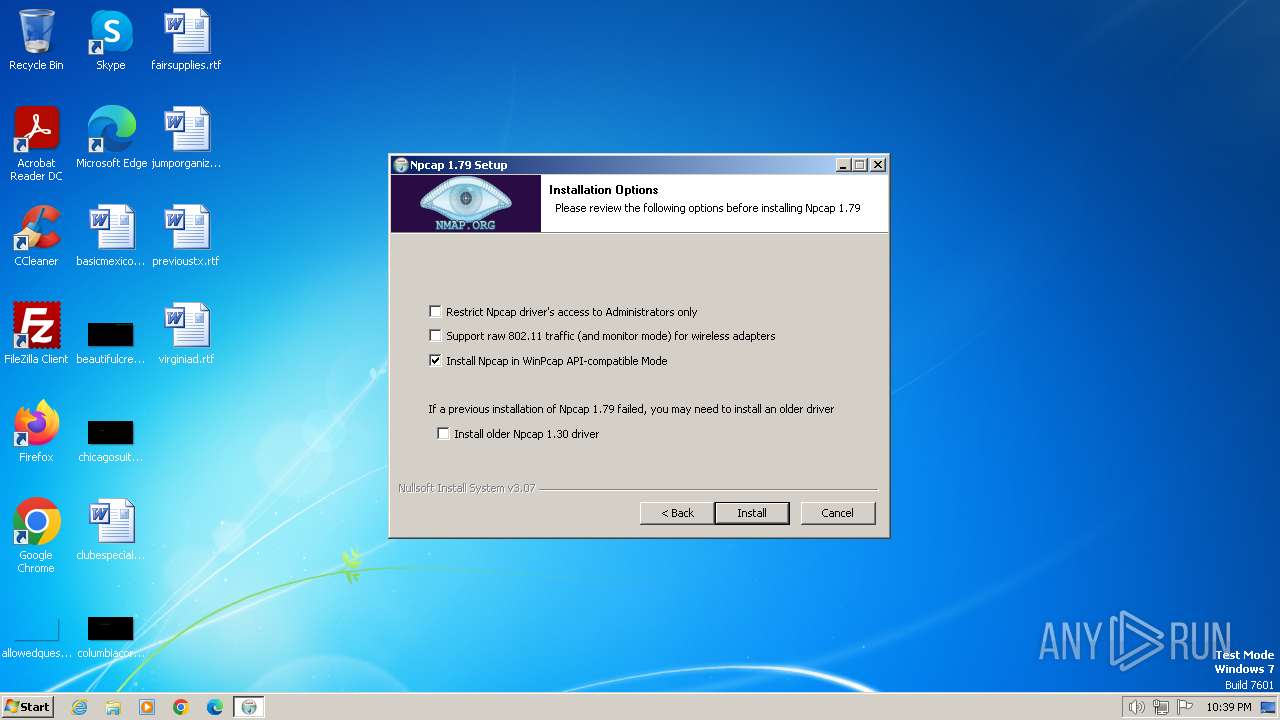
Modification events
| (PID) Process: | (2752) npcap-1.79.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Npcap |
| Operation: | write | Name: | AdminOnly |
Value: 0 | |||
| (PID) Process: | (2752) npcap-1.79.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Npcap |
| Operation: | write | Name: | WinPcapCompatible |
Value: 1 | |||
| (PID) Process: | (2752) npcap-1.79.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\NpcapInst |
| Operation: | write | Name: | UninstallString |
Value: "C:\Program Files\Npcap\uninstall.exe" | |||
| (PID) Process: | (2752) npcap-1.79.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\NpcapInst |
| Operation: | write | Name: | QuietUninstallString |
Value: "C:\Program Files\Npcap\uninstall.exe" /S | |||
| (PID) Process: | (2752) npcap-1.79.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\NpcapInst |
| Operation: | write | Name: | DisplayIcon |
Value: C:\Program Files\Npcap\uninstall.exe | |||
| (PID) Process: | (2752) npcap-1.79.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\NpcapInst |
| Operation: | write | Name: | UninstallPath |
Value: C:\Program Files\Npcap | |||
| (PID) Process: | (3092) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (4016) certutil.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2544) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\AuthRoot\Certificates\0563B8630D62D75ABBC8AB1E4BDFB5A899B24D43 |
| Operation: | delete value | Name: | File |
Value: | |||
| (PID) Process: | (2544) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\AuthRoot\Certificates\0563B8630D62D75ABBC8AB1E4BDFB5A899B24D43 |
| Operation: | delete key | Name: | (default) |
Value: | |||
Executable files
38
Suspicious files
38
Text files
11
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2752 | npcap-1.79.exe | C:\Users\admin\AppData\Local\Temp\nsaF5D8.tmp\ns4206.tmp | executable | |
MD5:F9E61A25016DCB49867477C1E71A704E | SHA256:274E53DC8C5DDC273A6F5683B71B882EF8917029E2EAF6C8DBEE0C62D999225D | |||
| 2752 | npcap-1.79.exe | C:\Users\admin\AppData\Local\Temp\nsaF5D8.tmp\nsF636.tmp | executable | |
MD5:F9E61A25016DCB49867477C1E71A704E | SHA256:274E53DC8C5DDC273A6F5683B71B882EF8917029E2EAF6C8DBEE0C62D999225D | |||
| 2752 | npcap-1.79.exe | C:\Users\admin\AppData\Local\Temp\nsaF5D8.tmp\nsExec.dll | executable | |
MD5:F9E61A25016DCB49867477C1E71A704E | SHA256:274E53DC8C5DDC273A6F5683B71B882EF8917029E2EAF6C8DBEE0C62D999225D | |||
| 2752 | npcap-1.79.exe | C:\Users\admin\AppData\Local\Temp\nsaF5D8.tmp\InstallOptions.dll | executable | |
MD5:170C17AC80215D0A377B42557252AE10 | SHA256:61EA114D9D0CD1E884535095AA3527A6C28DF55A4ECEE733C8C398F50B84CC3D | |||
| 2752 | npcap-1.79.exe | C:\Program Files\Npcap\DiagReport.bat | text | |
MD5:B82606A6AFB3777D62E35E8D9850FAED | SHA256:0843361F05255E3970ED955171C20003238756C57137FEF9AC19D29FBD49F9F6 | |||
| 2752 | npcap-1.79.exe | C:\Users\admin\AppData\Local\Temp\nsaF5D8.tmp\NPFInstall.exe | executable | |
MD5:23AF43847B2C8529EC7171D4A378E001 | SHA256:5B1A62010BC7F9A58721D067919D6CEDB0E8E414261E729E202E79334A791492 | |||
| 2752 | npcap-1.79.exe | C:\Program Files\Npcap\FixInstall.bat | text | |
MD5:3DCB581D39D9349A906368B77A4CEDFA | SHA256:C6158E40BDFD88E892EE6C4DA3A16A037EDF2CC77DC008CBD8FBEB44C643DDDA | |||
| 2752 | npcap-1.79.exe | C:\Program Files\Npcap\LICENSE | text | |
MD5:964BCA11041A5C595BA098D459C056DC | SHA256:CF7CD1D5F8E0713A7F86DA0BB5339A5ABBEAF9FE0FD0838401FBC58D1FCCC3C1 | |||
| 2752 | npcap-1.79.exe | C:\Users\admin\AppData\Local\Temp\nsaF5D8.tmp\options.ini | text | |
MD5:13A70D1FB5473932B6BECACCE3256EB8 | SHA256:6FB874CA5489CE28232F3451467A3E39047ECED5670830F813E5DEFA6A80D8F7 | |||
| 2752 | npcap-1.79.exe | C:\Users\admin\AppData\Local\Temp\nsaF5D8.tmp\final.ini | text | |
MD5:5FAA58B0398F6C4442D5CFBC616B4531 | SHA256:4AF865B65FDBA7BB5C874F3D67BFDCE7EEAD2459A572E0681A6C067568AF4902 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
11
DNS requests
6
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1372 | svchost.exe | GET | 304 | 95.101.54.121:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?33775f6043c93e33 | unknown | — | — | unknown |
1060 | svchost.exe | GET | 304 | 95.101.54.128:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?8f69642324cc87bd | unknown | — | — | unknown |
1372 | svchost.exe | GET | 200 | 2.16.164.72:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | unknown |
1372 | svchost.exe | GET | 200 | 23.211.9.92:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1060 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
1372 | svchost.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1372 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
1372 | svchost.exe | 95.101.54.121:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
1372 | svchost.exe | 2.16.164.72:80 | crl.microsoft.com | Akamai International B.V. | NL | unknown |
1372 | svchost.exe | 23.211.9.92:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
1060 | svchost.exe | 95.101.54.128:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
dns.msftncsi.com |
| shared |
settings-win.data.microsoft.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |