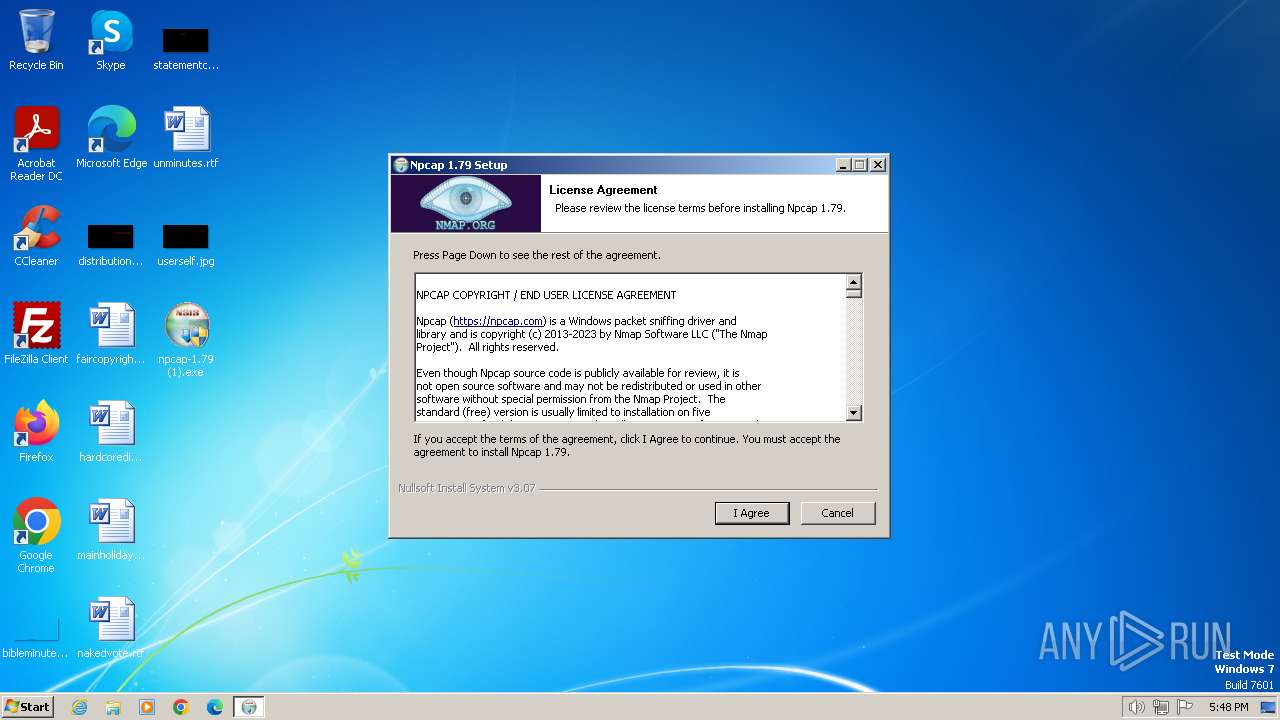
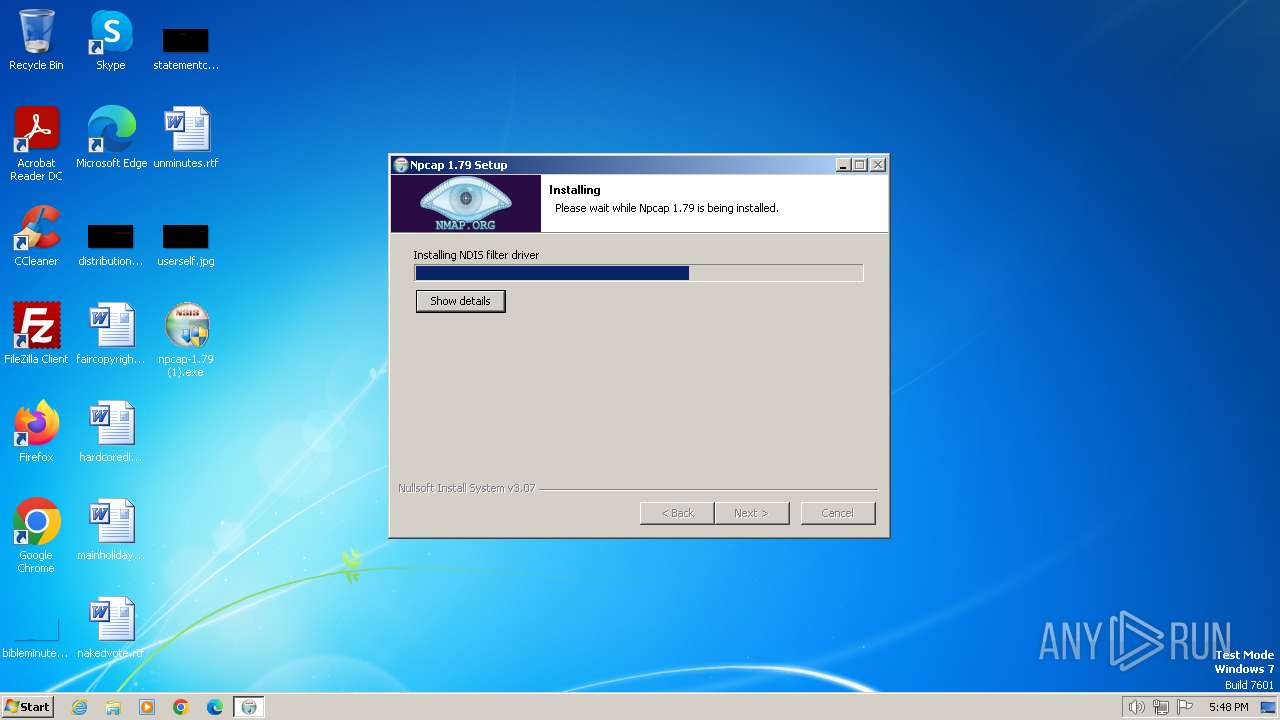
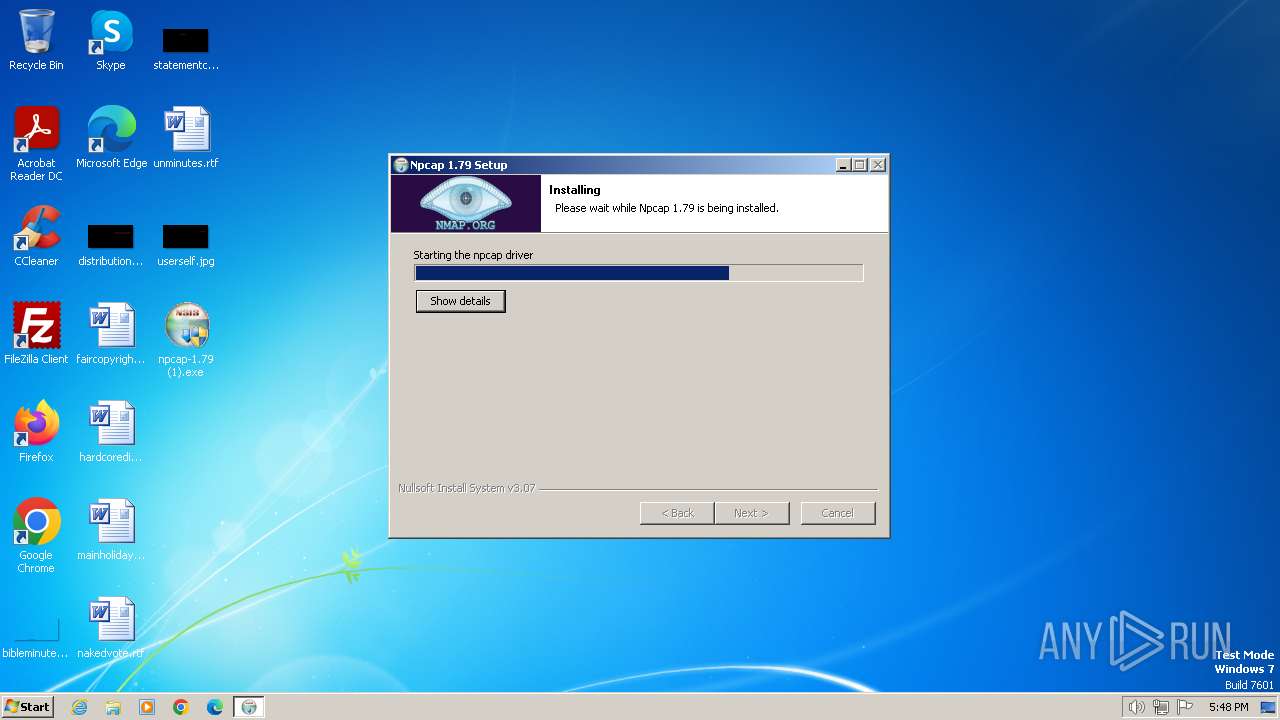
| File name: | npcap-1.79 (1).exe |
| Full analysis: | https://app.any.run/tasks/5bd5d095-0304-4528-aae6-3a9d8b74d0b4 |
| Verdict: | Malicious activity |
| Analysis date: | April 07, 2024, 16:47:47 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | A4D7E47DF742F62080BF845D606045B4 |
| SHA1: | 723743DC9FA4A190452A7FFC971ADFAAC91606FA |
| SHA256: | A95577EBBC67FC45B319E2EF3A55F4E9B211FE82ED4CB9D8BE6B1A9E2425CE53 |
| SSDEEP: | 49152:D6RKhVd9S1OsrcrMPSqfAQ4HgmY8mMiXZDeEN7sWv3Xu9uJRdSKpt6qUI2fqEFNI:D6YhsoIPSNvY8mMicEN7sGO9cRb6qxGu |
MALICIOUS
Drops the executable file immediately after the start
- npcap-1.79 (1).exe (PID: 2672)
- NPFInstall.exe (PID: 2032)
- drvinst.exe (PID: 3596)
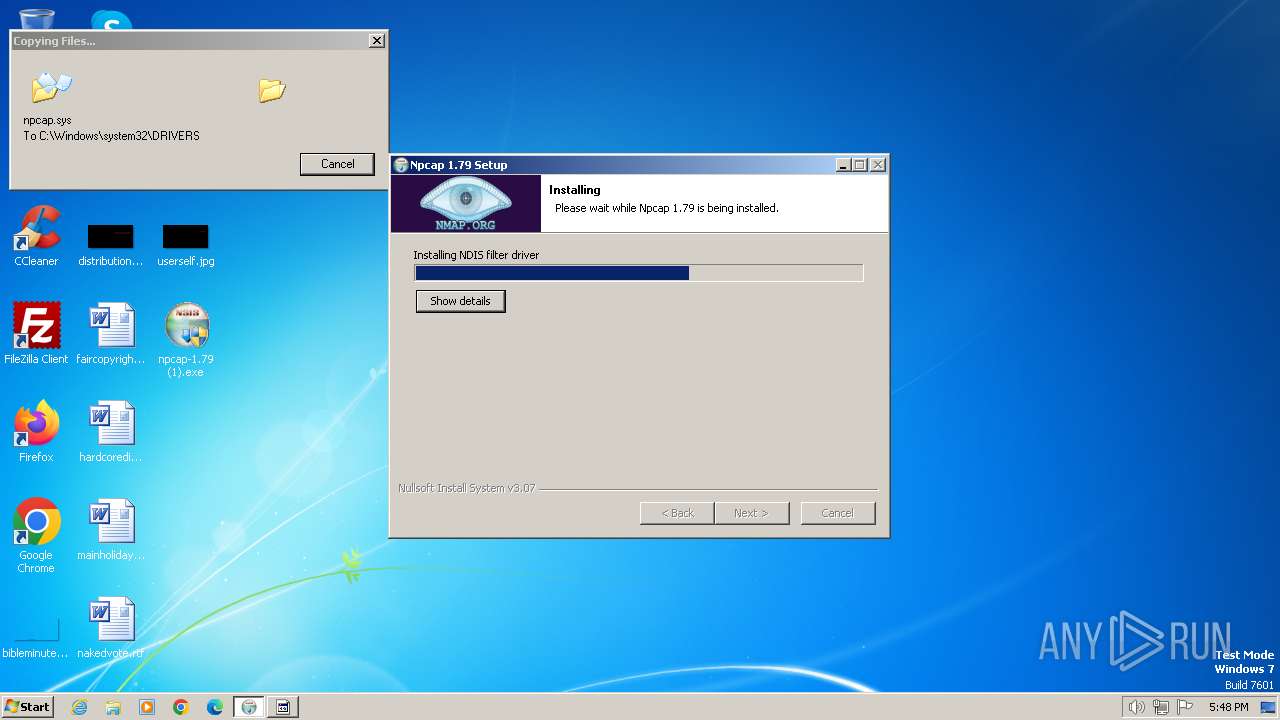
Creates a writable file in the system directory
- npcap-1.79 (1).exe (PID: 2672)
- drvinst.exe (PID: 3596)
- NPFInstall.exe (PID: 2032)
Run PowerShell with an invisible window
- powershell.exe (PID: 2780)
- powershell.exe (PID: 3088)
- powershell.exe (PID: 2584)
- powershell.exe (PID: 116)
- powershell.exe (PID: 3292)
SUSPICIOUS
The process creates files with name similar to system file names
- npcap-1.79 (1).exe (PID: 2672)
Malware-specific behavior (creating "System.dll" in Temp)
- npcap-1.79 (1).exe (PID: 2672)
Reads the Internet Settings
- WMIC.exe (PID: 3164)
Creates a software uninstall entry
- npcap-1.79 (1).exe (PID: 2672)
The process bypasses the loading of PowerShell profile settings
- ns58BF.tmp (PID: 2788)
- ns5E5D.tmp (PID: 2384)
- ns63EE.tmp (PID: 2376)
- ns68B2.tmp (PID: 2616)
- nsE914.tmp (PID: 1836)
Starts POWERSHELL.EXE for commands execution
- ns58BF.tmp (PID: 2788)
- ns63EE.tmp (PID: 2376)
- ns5E5D.tmp (PID: 2384)
- ns68B2.tmp (PID: 2616)
- nsE914.tmp (PID: 1836)
The process hide an interactive prompt from the user
- ns58BF.tmp (PID: 2788)
- ns5E5D.tmp (PID: 2384)
- ns63EE.tmp (PID: 2376)
- ns68B2.tmp (PID: 2616)
- nsE914.tmp (PID: 1836)
Starts CMD.EXE for commands execution
- ns2326.tmp (PID: 1348)
Uses WMIC.EXE to obtain quick Fix Engineering (patches) data
- cmd.exe (PID: 696)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 696)
Starts application with an unusual extension
- npcap-1.79 (1).exe (PID: 2672)
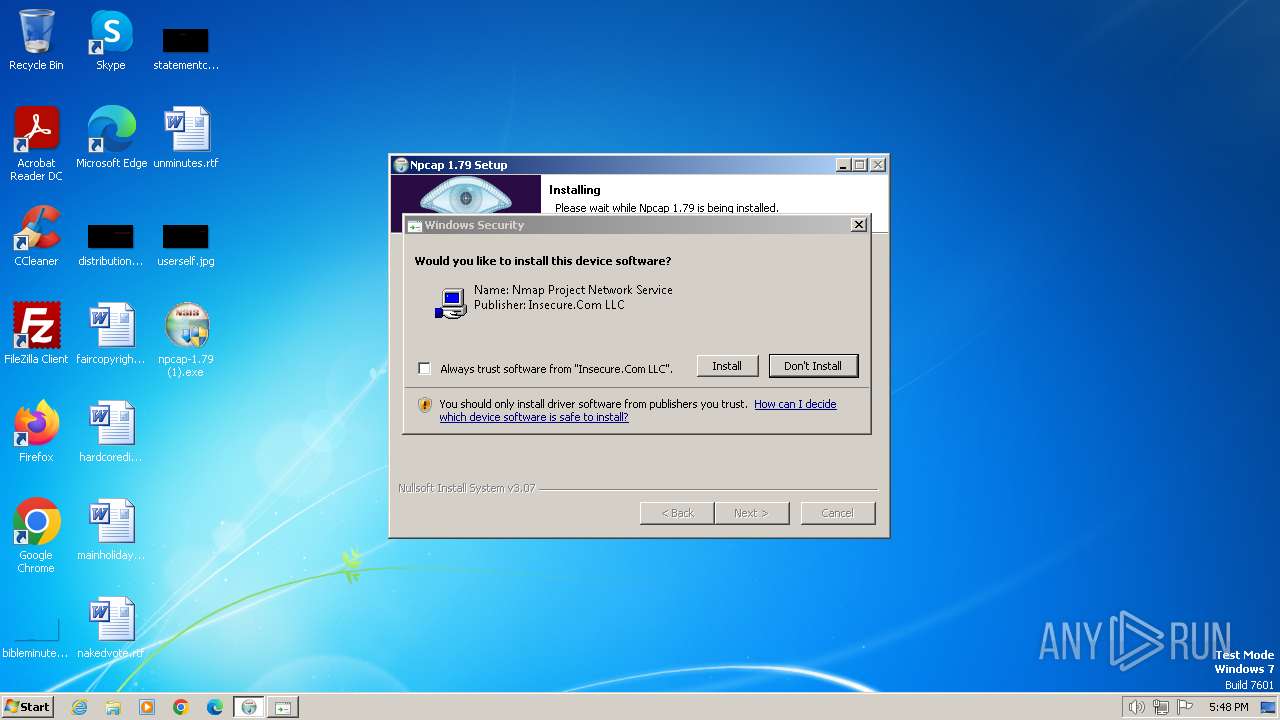
Checks Windows Trust Settings
- drvinst.exe (PID: 3596)
- NPFInstall.exe (PID: 2032)
Creates files in the driver directory
- drvinst.exe (PID: 3596)
- NPFInstall.exe (PID: 2032)
Reads settings of System Certificates
- rundll32.exe (PID: 3644)
- NPFInstall.exe (PID: 2032)
Creates or modifies Windows services
- npcap-1.79 (1).exe (PID: 2672)
Executes as Windows Service
- VSSVC.exe (PID: 2980)
Reads security settings of Internet Explorer
- NPFInstall.exe (PID: 2032)
Adds/modifies Windows certificates
- certutil.exe (PID: 1028)
INFO
Checks supported languages
- npcap-1.79 (1).exe (PID: 2672)
- NPFInstall.exe (PID: 2388)
- ns566C.tmp (PID: 1340)
- ns58BF.tmp (PID: 2788)
- ns6311.tmp (PID: 1404)
- ns5E5D.tmp (PID: 2384)
- ns6380.tmp (PID: 1840)
- ns6CF9.tmp (PID: 572)
- ns63EE.tmp (PID: 2376)
- ns2326.tmp (PID: 1348)
- NPFInstall.exe (PID: 3084)
- ns68B2.tmp (PID: 2616)
- NPFInstall.exe (PID: 2032)
- ns6DF5.tmp (PID: 2740)
- ns6F4E.tmp (PID: 3012)
- drvinst.exe (PID: 3596)
- ns6FBD.tmp (PID: 2764)
- nsE914.tmp (PID: 1836)
- nsEE55.tmp (PID: 2148)
- NPFInstall.exe (PID: 2768)
- ns6E73.tmp (PID: 1732)
- ns6D77.tmp (PID: 3988)
Reads the computer name
- npcap-1.79 (1).exe (PID: 2672)
- NPFInstall.exe (PID: 2388)
- NPFInstall.exe (PID: 2768)
- NPFInstall.exe (PID: 2032)
- drvinst.exe (PID: 3596)
Create files in a temporary directory
- npcap-1.79 (1).exe (PID: 2672)
- NPFInstall.exe (PID: 2032)
Creates files in the program directory
- npcap-1.79 (1).exe (PID: 2672)
- NPFInstall.exe (PID: 2388)
Reads Environment values
- npcap-1.79 (1).exe (PID: 2672)
Reads the machine GUID from the registry
- drvinst.exe (PID: 3596)
- NPFInstall.exe (PID: 2032)
Reads the software policy settings
- rundll32.exe (PID: 3644)
- drvinst.exe (PID: 3596)
- NPFInstall.exe (PID: 2032)
Reads security settings of Internet Explorer
- rundll32.exe (PID: 3644)
Adds/modifies Windows certificates
- drvinst.exe (PID: 3596)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2021:07:24 22:40:31+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 28160 |
| InitializedDataSize: | 152576 |
| UninitializedDataSize: | 2048 |
| EntryPoint: | 0x3a59 |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 5.1.79.117 |
| ProductVersionNumber: | 5.1.79.117 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| FileDescription: | Npcap 1.79 installer |
| FileVersion: | 1.79 |
| LegalCopyright: | Copyright (c) 2023, Insecure.Com LLC. All rights reserved. |
| ProductName: | Npcap |
| ProductVersion: | 1.79 |
Total processes
102
Monitored processes
42
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 116 | powershell.exe -NoProfile -WindowStyle Hidden -NonInteractive -Command "Microsoft.PowerShell.Management\Start-Service -Name npcap -PassThru | Microsoft.PowerShell.Management\Stop-Service -PassThru | Microsoft.PowerShell.Management\Start-Service" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | nsE914.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 572 | "C:\Users\admin\AppData\Local\Temp\nso2306.tmp\ns6CF9.tmp" certutil.exe -verifystore "Root" "5fb7ee0633e259dbad0c4c9ae6d38f1a61c7dc25" | C:\Users\admin\AppData\Local\Temp\nso2306.tmp\ns6CF9.tmp | — | npcap-1.79 (1).exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 2148073489 Modules
| |||||||||||||||
| 584 | certutil.exe -verifystore "Root" "5fb7ee0633e259dbad0c4c9ae6d38f1a61c7dc25" | C:\Windows\System32\certutil.exe | — | ns6CF9.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: CertUtil.exe Exit code: 2148073489 Version: 6.1.7601.18151 (win7sp1_gdr.130512-1533) Modules
| |||||||||||||||
| 696 | cmd /Q /C "%SYSTEMROOT%\System32\wbem\wmic.exe qfe get hotfixid | %SYSTEMROOT%\System32\findstr.exe "^KB4474419"" | C:\Windows\System32\cmd.exe | — | ns2326.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1028 | certutil.exe -addstore -f "TrustedPublisher" "C:\Users\admin\AppData\Local\Temp\nso2306.tmp\signing.p7b" | C:\Windows\System32\certutil.exe | — | ns6DF5.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: CertUtil.exe Exit code: 0 Version: 6.1.7601.18151 (win7sp1_gdr.130512-1533) Modules
| |||||||||||||||
| 1232 | "C:\Windows\system32\certutil.exe" -verifystore Root 0563b8630d62d75abbc8ab1e4bdfb5a899b24d43 | C:\Windows\System32\certutil.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: CertUtil.exe Exit code: 2148073489 Version: 6.1.7601.18151 (win7sp1_gdr.130512-1533) Modules
| |||||||||||||||
| 1340 | "C:\Users\admin\AppData\Local\Temp\nso2306.tmp\ns566C.tmp" "C:\Users\admin\AppData\Local\Temp\nso2306.tmp\NPFInstall.exe" -n -check_dll | C:\Users\admin\AppData\Local\Temp\nso2306.tmp\ns566C.tmp | — | npcap-1.79 (1).exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1348 | "C:\Users\admin\AppData\Local\Temp\nso2306.tmp\ns2326.tmp" cmd /Q /C "%SYSTEMROOT%\System32\wbem\wmic.exe qfe get hotfixid | %SYSTEMROOT%\System32\findstr.exe "^KB4474419"" | C:\Users\admin\AppData\Local\Temp\nso2306.tmp\ns2326.tmp | — | npcap-1.79 (1).exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1404 | "C:\Users\admin\AppData\Local\Temp\nso2306.tmp\ns6311.tmp" certutil.exe -verifystore "Root" "0563b8630d62d75abbc8ab1e4bdfb5a899b24d43" | C:\Users\admin\AppData\Local\Temp\nso2306.tmp\ns6311.tmp | — | npcap-1.79 (1).exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 2148073489 Modules
| |||||||||||||||
| 1696 | "C:\Users\admin\Desktop\npcap-1.79 (1).exe" | C:\Users\admin\Desktop\npcap-1.79 (1).exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Npcap 1.79 installer Exit code: 3221226540 Version: 1.79 Modules
| |||||||||||||||
Total events
40 360
Read events
39 924
Write events
417
Delete events
19
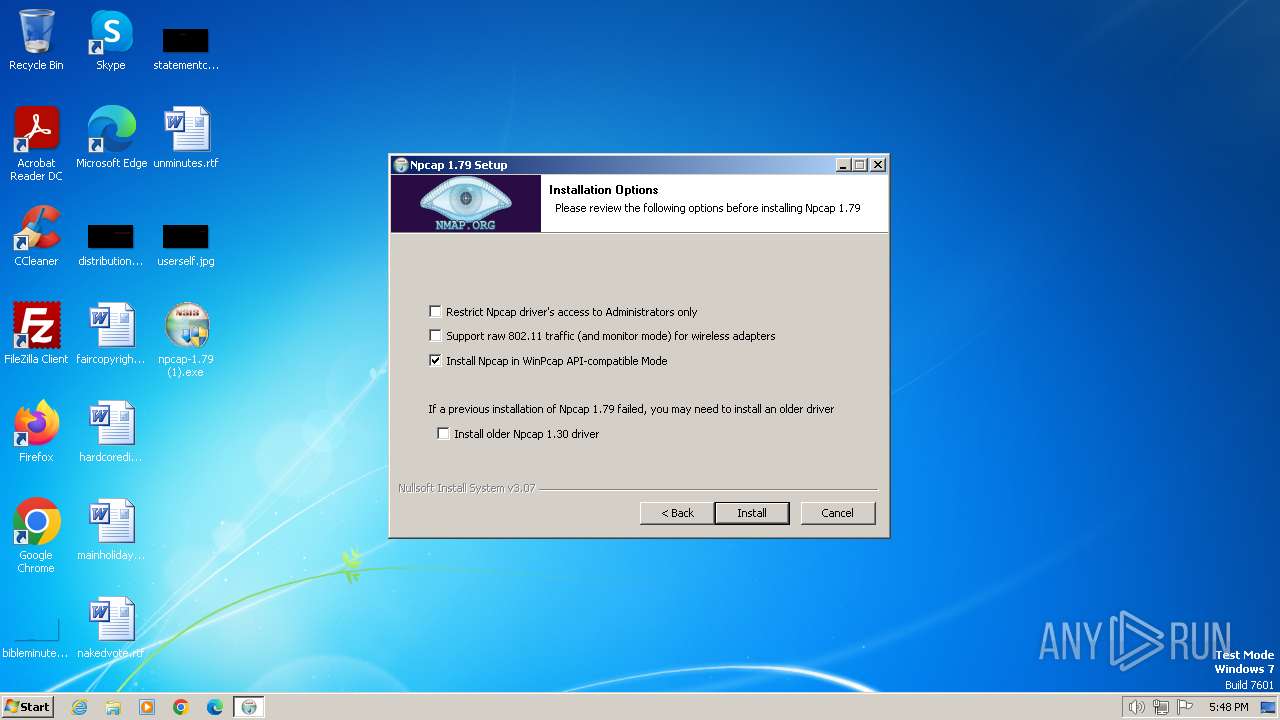
Modification events
| (PID) Process: | (2672) npcap-1.79 (1).exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Npcap |
| Operation: | write | Name: | AdminOnly |
Value: 0 | |||
| (PID) Process: | (2672) npcap-1.79 (1).exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Npcap |
| Operation: | write | Name: | WinPcapCompatible |
Value: 1 | |||
| (PID) Process: | (2672) npcap-1.79 (1).exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\NpcapInst |
| Operation: | write | Name: | UninstallString |
Value: "C:\Program Files\Npcap\uninstall.exe" | |||
| (PID) Process: | (2672) npcap-1.79 (1).exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\NpcapInst |
| Operation: | write | Name: | QuietUninstallString |
Value: "C:\Program Files\Npcap\uninstall.exe" /S | |||
| (PID) Process: | (2672) npcap-1.79 (1).exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\NpcapInst |
| Operation: | write | Name: | DisplayIcon |
Value: C:\Program Files\Npcap\uninstall.exe | |||
| (PID) Process: | (2672) npcap-1.79 (1).exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\NpcapInst |
| Operation: | write | Name: | UninstallPath |
Value: C:\Program Files\Npcap | |||
| (PID) Process: | (2780) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1232) certutil.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3088) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\AuthRoot\Certificates\0563B8630D62D75ABBC8AB1E4BDFB5A899B24D43 |
| Operation: | delete value | Name: | File |
Value: | |||
| (PID) Process: | (3088) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\AuthRoot\Certificates\0563B8630D62D75ABBC8AB1E4BDFB5A899B24D43 |
| Operation: | delete key | Name: | (default) |
Value: | |||
Executable files
39
Suspicious files
11
Text files
10
Unknown types
27
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2672 | npcap-1.79 (1).exe | C:\Users\admin\AppData\Local\Temp\nso2306.tmp\System.dll | executable | |
MD5:— | SHA256:— | |||
| 2672 | npcap-1.79 (1).exe | C:\Users\admin\AppData\Local\Temp\nso2306.tmp\options.ini | text | |
MD5:— | SHA256:— | |||
| 2672 | npcap-1.79 (1).exe | C:\Users\admin\AppData\Local\Temp\nso2306.tmp\InstallOptions.dll | executable | |
MD5:— | SHA256:— | |||
| 2672 | npcap-1.79 (1).exe | C:\Users\admin\AppData\Local\Temp\nso2306.tmp\final.ini | text | |
MD5:— | SHA256:— | |||
| 2672 | npcap-1.79 (1).exe | C:\Users\admin\AppData\Local\Temp\nso2306.tmp\nsExec.dll | executable | |
MD5:— | SHA256:— | |||
| 2672 | npcap-1.79 (1).exe | C:\Users\admin\AppData\Local\Temp\nso2306.tmp\ns2326.tmp | executable | |
MD5:— | SHA256:— | |||
| 2672 | npcap-1.79 (1).exe | C:\Users\admin\AppData\Local\Temp\nso2306.tmp\modern-header.bmp | image | |
MD5:— | SHA256:— | |||
| 2672 | npcap-1.79 (1).exe | C:\Users\admin\AppData\Local\Temp\nso2306.tmp\NPFInstall.exe | executable | |
MD5:— | SHA256:— | |||
| 2672 | npcap-1.79 (1).exe | C:\Users\admin\AppData\Local\Temp\nso2306.tmp\ns566C.tmp | executable | |
MD5:— | SHA256:— | |||
| 2388 | NPFInstall.exe | C:\Program Files\Npcap\NPFInstall.log | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
6
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | unknown |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |