| File name: | Client.exe |
| Full analysis: | https://app.any.run/tasks/a4bed7a4-4f05-4cb6-9861-56eba23bc45f |
| Verdict: | Malicious activity |
| Threats: | DCrat, also known as Dark Crystal RAT, is a remote access trojan (RAT), which was first introduced in 2018. It is a modular malware that can be customized to perform different tasks. For instance, it can steal passwords, crypto wallet information, hijack Telegram and Steam accounts, and more. Attackers may use a variety of methods to distribute DCrat, but phishing email campaigns are the most common. |
| Analysis date: | April 29, 2025, 10:47:28 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows, 3 sections |
| MD5: | 0275C9F573C320290911DB65ABF35713 |
| SHA1: | 441E6788588E8085AF196073AA71E3DB91789835 |
| SHA256: | A949310E56814119F7FEFB5079EA19BDD05934C0F3EB45655CB2351993332B08 |
| SSDEEP: | 6144:xPmZ6HtqL7cI07ZkZReCRB6D1ZbnBTlsv:x+Z6NqHcIqZkZReKB6DV2v |
MALICIOUS
SHEETRAT mutex has been found
- Client.exe (PID: 4448)
Uses Task Scheduler to autorun other applications
- cmd.exe (PID: 6564)
Uses Task Scheduler to run other applications
- cmd.exe (PID: 2644)
- cmd.exe (PID: 6644)
- cmd.exe (PID: 1312)
- cmd.exe (PID: 4528)
- cmd.exe (PID: 6268)
- cmd.exe (PID: 4112)
- cmd.exe (PID: 920)
- cmd.exe (PID: 4844)
- cmd.exe (PID: 1164)
- cmd.exe (PID: 7144)
- cmd.exe (PID: 6456)
- cmd.exe (PID: 6644)
- cmd.exe (PID: 1628)
- cmd.exe (PID: 5588)
- cmd.exe (PID: 232)
- cmd.exe (PID: 6068)
- cmd.exe (PID: 3828)
- cmd.exe (PID: 3028)
- cmd.exe (PID: 6980)
- cmd.exe (PID: 1100)
- cmd.exe (PID: 2796)
- cmd.exe (PID: 3552)
- cmd.exe (PID: 2960)
- cmd.exe (PID: 1300)
- cmd.exe (PID: 5080)
- cmd.exe (PID: 6176)
- cmd.exe (PID: 7224)
- cmd.exe (PID: 6620)
- cmd.exe (PID: 7352)
- cmd.exe (PID: 7472)
- cmd.exe (PID: 7712)
- cmd.exe (PID: 7800)
- cmd.exe (PID: 7632)
- cmd.exe (PID: 7972)
- cmd.exe (PID: 8056)
- cmd.exe (PID: 8148)
- cmd.exe (PID: 7188)
- cmd.exe (PID: 7884)
- cmd.exe (PID: 7272)
Changes the login/logoff helper path in the registry
- Client.exe (PID: 4448)
Changes the AppInit_DLLs value (autorun option)
- Client.exe (PID: 4448)
Changes the autorun value in the registry
- Client.exe (PID: 4448)
- CCleaner64.exe (PID: 1748)
Connects to the CnC server
- Client.exe (PID: 4448)
PURELOGS has been detected (SURICATA)
- Client.exe (PID: 4448)
DARKCRYSTAL has been detected (SURICATA)
- Client.exe (PID: 4448)
SHEETRAT has been detected (SURICATA)
- Client.exe (PID: 4448)
SUSPICIOUS
Reads security settings of Internet Explorer
- Client.exe (PID: 5964)
- CCleaner64.exe (PID: 660)
- CCleaner64.exe (PID: 732)
- CCleaner64.exe (PID: 1748)
Reads the date of Windows installation
- Client.exe (PID: 5964)
- CCleaner64.exe (PID: 660)
- CCleaner64.exe (PID: 732)
Application launched itself
- Client.exe (PID: 5964)
- CCleaner64.exe (PID: 660)
- CCleaner64.exe (PID: 732)
Likely accesses (executes) a file from the Public directory
- cmd.exe (PID: 6564)
- schtasks.exe (PID: 6476)
- cmd.exe (PID: 2644)
- schtasks.exe (PID: 1324)
- cmd.exe (PID: 6644)
- schtasks.exe (PID: 6388)
- schtasks.exe (PID: 6456)
- cmd.exe (PID: 1312)
- xdwdMicrosoft Security Essentials.exe (PID: 5408)
- xdwdMicrosoft Security Essentials.exe (PID: 5756)
- xdwdRainmeter.exe (PID: 6248)
- xdwdRainmeter.exe (PID: 5124)
- schtasks.exe (PID: 6136)
- cmd.exe (PID: 4528)
- schtasks.exe (PID: 6944)
- cmd.exe (PID: 6268)
- cmd.exe (PID: 4112)
- cmd.exe (PID: 920)
- schtasks.exe (PID: 3364)
- schtasks.exe (PID: 6644)
- cmd.exe (PID: 1164)
- schtasks.exe (PID: 1132)
- cmd.exe (PID: 4844)
- schtasks.exe (PID: 5384)
- cmd.exe (PID: 7144)
- schtasks.exe (PID: 976)
- cmd.exe (PID: 6456)
- schtasks.exe (PID: 1164)
- schtasks.exe (PID: 4892)
- cmd.exe (PID: 1628)
- cmd.exe (PID: 5588)
- schtasks.exe (PID: 6244)
- cmd.exe (PID: 6644)
- schtasks.exe (PID: 976)
- cmd.exe (PID: 6068)
- schtasks.exe (PID: 2776)
- cmd.exe (PID: 232)
- schtasks.exe (PID: 2908)
- cmd.exe (PID: 3028)
- schtasks.exe (PID: 4996)
- cmd.exe (PID: 6980)
- schtasks.exe (PID: 1376)
- cmd.exe (PID: 1100)
- schtasks.exe (PID: 4000)
- cmd.exe (PID: 2796)
- cmd.exe (PID: 3828)
- schtasks.exe (PID: 1280)
- schtasks.exe (PID: 6620)
- cmd.exe (PID: 3552)
- cmd.exe (PID: 2960)
- schtasks.exe (PID: 6080)
- cmd.exe (PID: 1300)
- schtasks.exe (PID: 5512)
- schtasks.exe (PID: 6512)
- cmd.exe (PID: 5080)
- schtasks.exe (PID: 2780)
- cmd.exe (PID: 6176)
- schtasks.exe (PID: 2960)
- cmd.exe (PID: 6620)
- schtasks.exe (PID: 7104)
- cmd.exe (PID: 7352)
- cmd.exe (PID: 7224)
- schtasks.exe (PID: 7276)
- schtasks.exe (PID: 7400)
- schtasks.exe (PID: 7564)
- cmd.exe (PID: 7632)
- schtasks.exe (PID: 7760)
- schtasks.exe (PID: 7684)
- cmd.exe (PID: 7712)
- cmd.exe (PID: 7800)
- schtasks.exe (PID: 7848)
- cmd.exe (PID: 7884)
- cmd.exe (PID: 7472)
- cmd.exe (PID: 7972)
- schtasks.exe (PID: 8024)
- schtasks.exe (PID: 8108)
- cmd.exe (PID: 8148)
- schtasks.exe (PID: 6972)
- cmd.exe (PID: 7188)
- schtasks.exe (PID: 7248)
- schtasks.exe (PID: 6468)
- cmd.exe (PID: 7272)
- schtasks.exe (PID: 7932)
- cmd.exe (PID: 8056)
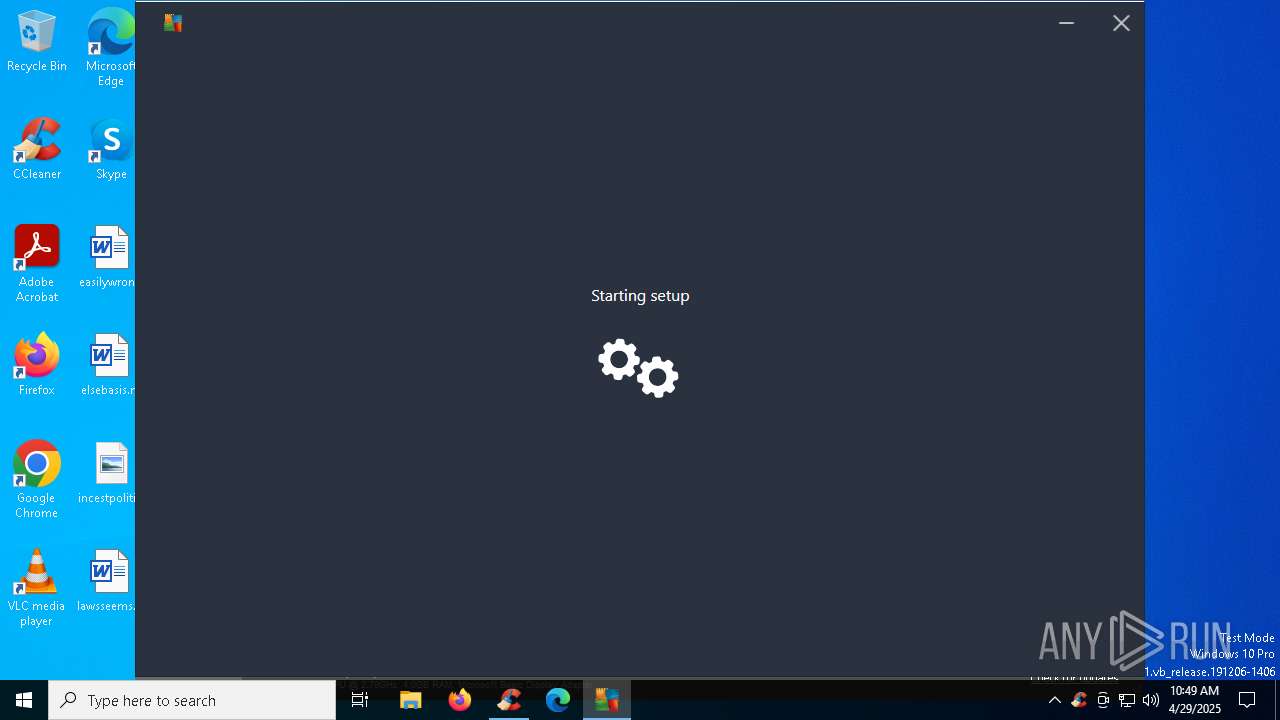
Executable content was dropped or overwritten
- Client.exe (PID: 4448)
- CCleaner64.exe (PID: 732)
- CCleaner64.exe (PID: 1748)
- Microstub.exe (PID: 5124)
- avg_antivirus_free_online_setup.exe (PID: 6392)
- icarus.exe (PID: 4268)
- icarus.exe (PID: 6896)
Starts CMD.EXE for commands execution
- Client.exe (PID: 4448)
- xdwdMicrosoft Security Essentials.exe (PID: 5408)
- xdwdMicrosoft Security Essentials.exe (PID: 5756)
- xdwdRainmeter.exe (PID: 6248)
- xdwdRainmeter.exe (PID: 5124)
Potential Corporate Privacy Violation
- svchost.exe (PID: 2196)
Connects to unusual port
- Client.exe (PID: 4448)
Executes as Windows Service
- WmiApSrv.exe (PID: 5084)
The process checks if it is being run in the virtual environment
- Client.exe (PID: 4448)
Contacting a server suspected of hosting an CnC
- Client.exe (PID: 4448)
Reads Internet Explorer settings
- CCleaner64.exe (PID: 732)
- CCleaner64.exe (PID: 1748)
Checks for external IP
- CCleaner64.exe (PID: 732)
- svchost.exe (PID: 2196)
- Microstub.exe (PID: 5124)
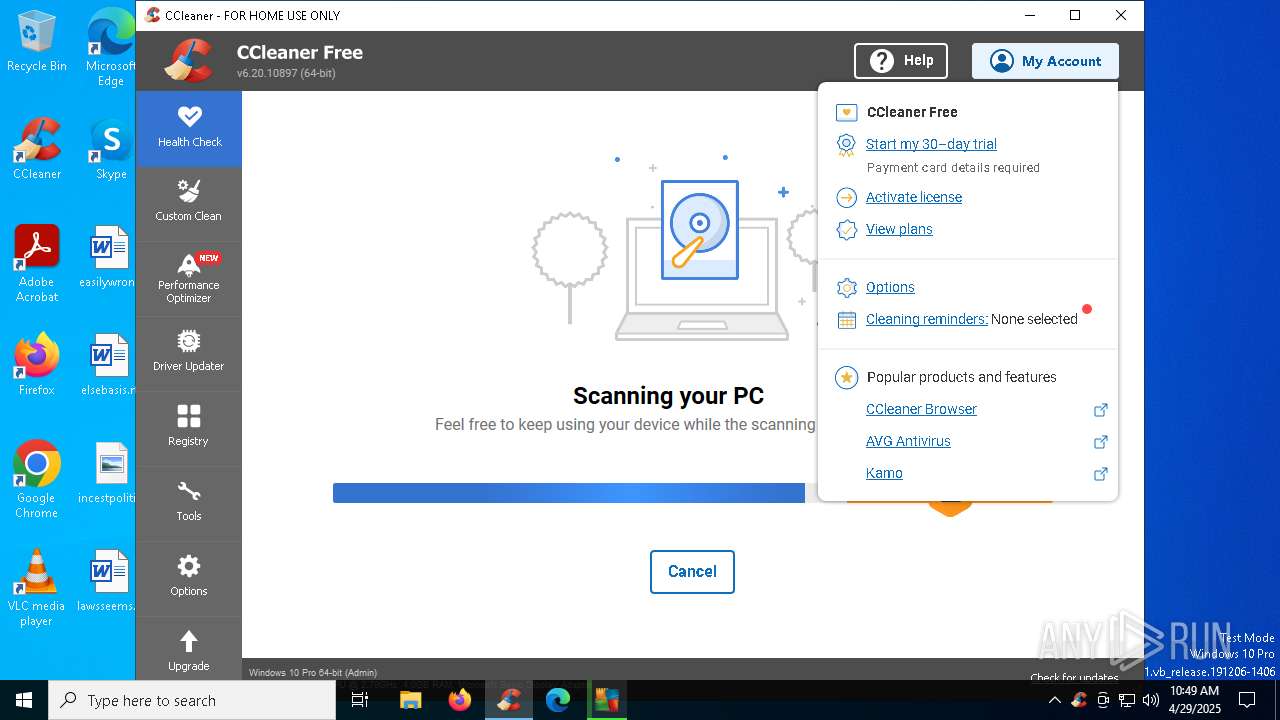
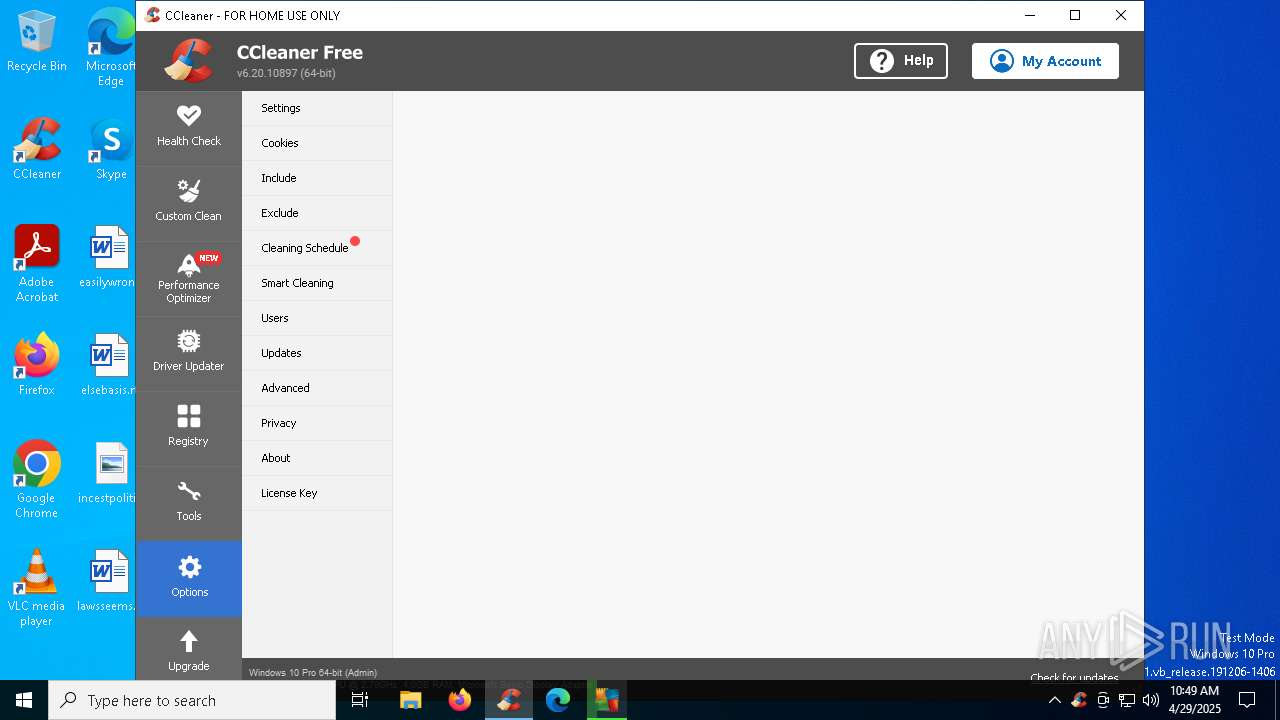
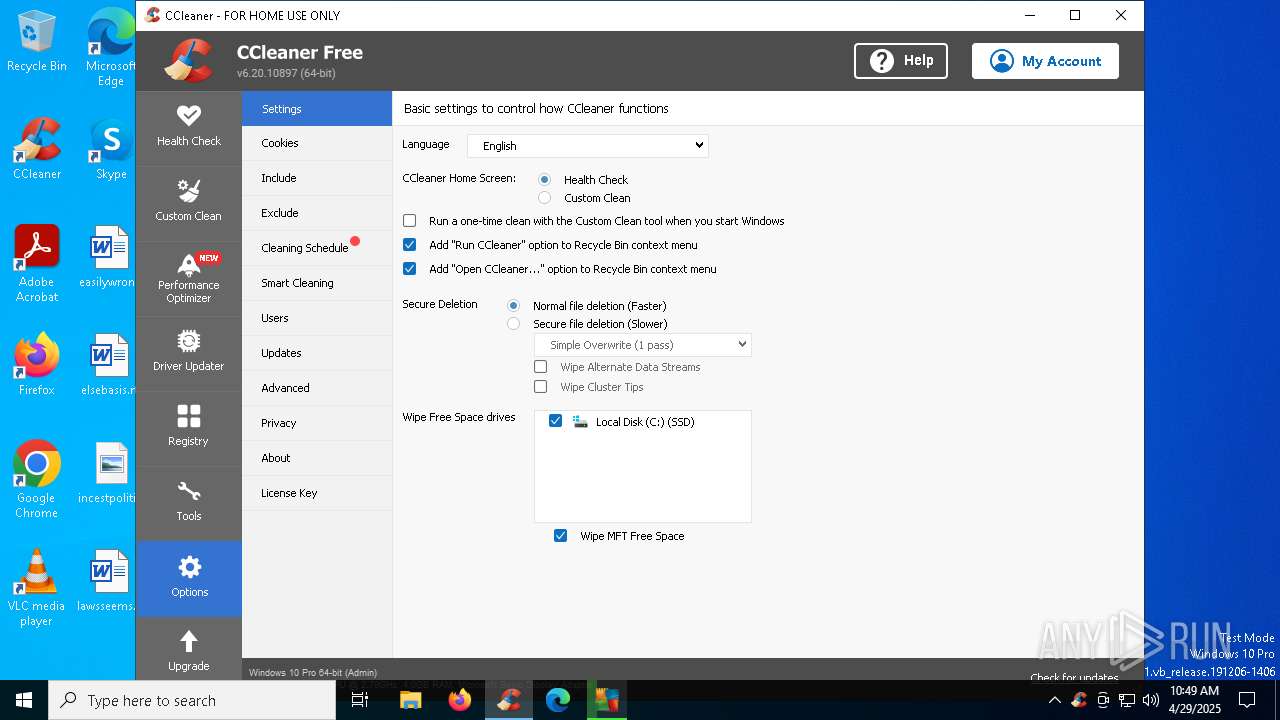
Searches for installed software
- CCleaner64.exe (PID: 732)
- CCleaner64.exe (PID: 1748)
- CCleaner64.exe (PID: 6068)
The process executes via Task Scheduler
- CCleaner.exe (PID: 2596)
The process verifies whether the antivirus software is installed
- CCleaner64.exe (PID: 1748)
- CCleaner64.exe (PID: 732)
Starts application from unusual location
- CCleaner64.exe (PID: 732)
Starts itself from another location
- icarus.exe (PID: 4268)
Query current time using 'w32tm.exe'
- CCleaner64.exe (PID: 732)
Process drops legitimate windows executable
- icarus.exe (PID: 6896)
INFO
Checks supported languages
- Client.exe (PID: 5964)
- Client.exe (PID: 4448)
- xdwdMicrosoft Security Essentials.exe (PID: 5408)
- xdwdRainmeter.exe (PID: 5124)
- xdwdRainmeter.exe (PID: 6248)
- xdwdMicrosoft Security Essentials.exe (PID: 5756)
- CCleaner64.exe (PID: 660)
- CCleaner64.exe (PID: 732)
- CCleaner64.exe (PID: 1748)
- CCleaner64.exe (PID: 4560)
- CCleaner.exe (PID: 2596)
- CCleaner64.exe (PID: 6068)
- Microstub.exe (PID: 5124)
- avg_antivirus_free_online_setup.exe (PID: 6392)
Reads the machine GUID from the registry
- Client.exe (PID: 5964)
- Client.exe (PID: 4448)
- CCleaner64.exe (PID: 1748)
- CCleaner64.exe (PID: 732)
- CCleaner64.exe (PID: 6068)
- Microstub.exe (PID: 5124)
- avg_antivirus_free_online_setup.exe (PID: 6392)
Reads the computer name
- Client.exe (PID: 5964)
- Client.exe (PID: 4448)
- xdwdMicrosoft Security Essentials.exe (PID: 5408)
- xdwdMicrosoft Security Essentials.exe (PID: 5756)
- xdwdRainmeter.exe (PID: 6248)
- xdwdRainmeter.exe (PID: 5124)
- CCleaner64.exe (PID: 660)
- CCleaner64.exe (PID: 732)
- CCleaner64.exe (PID: 1748)
- CCleaner64.exe (PID: 4560)
- CCleaner.exe (PID: 2596)
- CCleaner64.exe (PID: 6068)
- Microstub.exe (PID: 5124)
- avg_antivirus_free_online_setup.exe (PID: 6392)
Process checks computer location settings
- Client.exe (PID: 5964)
- CCleaner64.exe (PID: 660)
- CCleaner64.exe (PID: 732)
Auto-launch of the file from Task Scheduler
- cmd.exe (PID: 2644)
- cmd.exe (PID: 6644)
- cmd.exe (PID: 1312)
- cmd.exe (PID: 4528)
- cmd.exe (PID: 6268)
- cmd.exe (PID: 4112)
- cmd.exe (PID: 920)
- cmd.exe (PID: 1164)
- cmd.exe (PID: 4844)
- cmd.exe (PID: 7144)
- cmd.exe (PID: 6456)
- cmd.exe (PID: 1628)
- cmd.exe (PID: 6644)
- cmd.exe (PID: 5588)
- cmd.exe (PID: 232)
- cmd.exe (PID: 6068)
- cmd.exe (PID: 3828)
- cmd.exe (PID: 3028)
- cmd.exe (PID: 6980)
- cmd.exe (PID: 1100)
- cmd.exe (PID: 2796)
- cmd.exe (PID: 3552)
- cmd.exe (PID: 2960)
- cmd.exe (PID: 1300)
- cmd.exe (PID: 5080)
- cmd.exe (PID: 6176)
- cmd.exe (PID: 6620)
- cmd.exe (PID: 7224)
- cmd.exe (PID: 7472)
- cmd.exe (PID: 7632)
- cmd.exe (PID: 7712)
- cmd.exe (PID: 7800)
- cmd.exe (PID: 7352)
- cmd.exe (PID: 7884)
- cmd.exe (PID: 7972)
- cmd.exe (PID: 8056)
- cmd.exe (PID: 8148)
- cmd.exe (PID: 7188)
- cmd.exe (PID: 7272)
Auto-launch of the file from Registry key
- Client.exe (PID: 4448)
- CCleaner64.exe (PID: 1748)
Manual execution by a user
- xdwdMicrosoft Security Essentials.exe (PID: 5408)
- xdwdRainmeter.exe (PID: 6248)
- xdwdRainmeter.exe (PID: 5124)
- xdwdMicrosoft Security Essentials.exe (PID: 5756)
- CCleaner64.exe (PID: 660)
- CCleaner64.exe (PID: 4560)
Reads the time zone
- Client.exe (PID: 4448)
Reads CPU info
- Client.exe (PID: 4448)
- CCleaner64.exe (PID: 732)
- CCleaner64.exe (PID: 1748)
- CCleaner64.exe (PID: 6068)
Reads Environment values
- CCleaner64.exe (PID: 660)
- CCleaner64.exe (PID: 732)
- CCleaner64.exe (PID: 1748)
- CCleaner64.exe (PID: 4560)
- CCleaner.exe (PID: 2596)
- CCleaner64.exe (PID: 6068)
Creates files in the program directory
- CCleaner64.exe (PID: 732)
- CCleaner64.exe (PID: 1748)
- avg_antivirus_free_online_setup.exe (PID: 6392)
Reads product name
- CCleaner64.exe (PID: 732)
- CCleaner64.exe (PID: 1748)
Reads the software policy settings
- CCleaner64.exe (PID: 732)
- CCleaner64.exe (PID: 1748)
- CCleaner64.exe (PID: 6068)
- Microstub.exe (PID: 5124)
- avg_antivirus_free_online_setup.exe (PID: 6392)
The sample compiled with english language support
- CCleaner64.exe (PID: 732)
- CCleaner64.exe (PID: 1748)
- Microstub.exe (PID: 5124)
- avg_antivirus_free_online_setup.exe (PID: 6392)
- icarus.exe (PID: 4268)
- icarus.exe (PID: 6896)
Checks proxy server information
- CCleaner64.exe (PID: 732)
- avg_antivirus_free_online_setup.exe (PID: 6392)
Creates files or folders in the user directory
- CCleaner64.exe (PID: 732)
Create files in a temporary directory
- CCleaner64.exe (PID: 732)
- avg_antivirus_free_online_setup.exe (PID: 6392)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (72.2) |
|---|---|---|
| .scr | | | Windows screen saver (12.9) |
| .dll | | | Win32 Dynamic Link Library (generic) (6.4) |
| .exe | | | Win32 Executable (generic) (4.4) |
| .exe | | | Generic Win/DOS Executable (1.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2100:10:13 03:20:15+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32 |
| LinkerVersion: | 48 |
| CodeSize: | 299008 |
| InitializedDataSize: | 2560 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x4adfe |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 199.299.7.262 |
| ProductVersionNumber: | 197.98.173.35 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | VLC Media Player |
| FileDescription: | Bitdefender Antivirus |
| FileVersion: | 199.299.7.262 |
| InternalName: | Microsoft Word Host.exe |
| LegalCopyright: | Microsoft Edge Host |
| LegalTrademarks: | Adobe Photoshop |
| OriginalFileName: | Microsoft Word Host.exe |
| ProductName: | FileZilla Upgrade |
| ProductVersion: | 197.98.173.35 |
| AssemblyVersion: | 197.98.173.35 |
Total processes
285
Monitored processes
157
Malicious processes
6
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 232 | "CMD" /c SchTaSKs /create /f /sc minute /mo -1 /tn "MATLAB" /tr "C:\Users\Public\Documents\xdwdMicrosoft Security Essentials.exe" /RL HIGHEST & exit | C:\Windows\System32\cmd.exe | — | Client.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 2147500037 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 616 | scHTaSks /Run /I /TN "HandBrake" | C:\Windows\System32\schtasks.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 660 | "CMD" /c scHTaSks /Run /I /TN "HandBrake" | C:\Windows\System32\cmd.exe | — | xdwdMicrosoft Security Essentials.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 660 | "C:\Program Files\CCleaner\CCleaner64.exe" | C:\Program Files\CCleaner\CCleaner64.exe | — | explorer.exe | |||||||||||
User: admin Company: Piriform Software Ltd Integrity Level: MEDIUM Description: CCleaner Exit code: 0 Version: 6.20.0.10897 Modules
| |||||||||||||||
| 684 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 732 | "C:\Program Files\CCleaner\CCleaner64.exe" /uac | C:\Program Files\CCleaner\CCleaner64.exe | CCleaner64.exe | ||||||||||||
User: admin Company: Piriform Software Ltd Integrity Level: HIGH Description: CCleaner Version: 6.20.0.10897 Modules
| |||||||||||||||
| 920 | "CMD" /c SchTaSKs /create /f /sc minute /mo -1 /tn "MATLAB" /tr "C:\Users\Public\Documents\xdwdMicrosoft Security Essentials.exe" /RL HIGHEST & exit | C:\Windows\System32\cmd.exe | — | Client.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 2147500037 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 920 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 976 | SchTaSKs /create /f /sc minute /mo -1 /tn "MATLAB" /tr "C:\Users\Public\Documents\xdwdMicrosoft Security Essentials.exe" /RL HIGHEST | C:\Windows\System32\schtasks.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Scheduler Configuration Tool Exit code: 2147500037 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 976 | SchTaSKs /create /f /sc minute /mo -1 /tn "MATLAB" /tr "C:\Users\Public\Documents\xdwdMicrosoft Security Essentials.exe" /RL HIGHEST | C:\Windows\System32\schtasks.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Scheduler Configuration Tool Exit code: 2147500037 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
49 881
Read events
49 652
Write events
155
Delete events
74
Modification events
| (PID) Process: | (5964) Client.exe | Key: | HKEY_CURRENT_USER\SOFTWARE |
| Operation: | write | Name: | hwid |
Value: MUFFQ0EyRTVDODhDMzgzNkJFQkZBM0M= | |||
| (PID) Process: | (4448) Client.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Windows |
| Operation: | write | Name: | AppInit_DLLs |
Value: C:\WINDOWS\xdwd.dll | |||
| (PID) Process: | (4448) Client.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Windows |
| Operation: | write | Name: | LoadAppInit_DLLs |
Value: 1 | |||
| (PID) Process: | (4448) Client.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Windows |
| Operation: | write | Name: | RequireSignedAppInit_DLLs |
Value: 0 | |||
| (PID) Process: | (4448) Client.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon |
| Operation: | write | Name: | Userinit |
Value: C:\Windows\System32\userinit.exe,C:\Users\Public\Documents\xdwdMicrosoft Security Essentials.exe | |||
| (PID) Process: | (4448) Client.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | xdwdfghfghfg |
Value: C:\Users\Public\Pictures\xdwdRainmeter.exe | |||
| (PID) Process: | (4448) Client.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\.NET Memory Cache 4.0\Linkage |
| Operation: | write | Name: | Export |
Value: .NET Memory Cache 4.0 | |||
| (PID) Process: | (4448) Client.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\MSDTC Bridge 3.0.0.0\Linkage |
| Operation: | write | Name: | Export |
Value: MSDTC Bridge 3.0.0.0 | |||
| (PID) Process: | (4448) Client.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\MSDTC Bridge 4.0.0.0\Linkage |
| Operation: | write | Name: | Export |
Value: MSDTC Bridge 4.0.0.0 | |||
| (PID) Process: | (4448) Client.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\ServiceModelEndpoint 3.0.0.0\Linkage |
| Operation: | write | Name: | Export |
Value: ServiceModelEndpoint 3.0.0.0 | |||
Executable files
55
Suspicious files
90
Text files
50
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4448 | Client.exe | C:\Users\Public\Pictures\xdwdRainmeter.exe | executable | |
MD5:0275C9F573C320290911DB65ABF35713 | SHA256:A949310E56814119F7FEFB5079EA19BDD05934C0F3EB45655CB2351993332B08 | |||
| 4448 | Client.exe | C:\Users\Public\Documents\xdwdMicrosoft Security Essentials.exe | executable | |
MD5:0275C9F573C320290911DB65ABF35713 | SHA256:A949310E56814119F7FEFB5079EA19BDD05934C0F3EB45655CB2351993332B08 | |||
| 732 | CCleaner64.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\RR3E01RZ\icon-avg-av-v1[1].png | image | |
MD5:E47CB251409215C966FC25515A827A2F | SHA256:98F68BFE513BF5E0543AF912DED861AC906EFA7692B310FD013E60BCBDBB8A73 | |||
| 732 | CCleaner64.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\AH8CR9J5\35NQZ9AJ.txt | text | |
MD5:A8D158D95D0E6853CEDAB255DD9D74F4 | SHA256:E361847BBA5BA5957BB258FB85C981AC10973310218490AF73514E42EBEE42C9 | |||
| 732 | CCleaner64.exe | C:\Program Files\CCleaner\gcapi_1745923717732.dll | executable | |
MD5:F17F96322F8741FE86699963A1812897 | SHA256:8B6CE3A640E2D6F36B0001BE2A1ABB765AE51E62C314A15911E75138CBB544BB | |||
| 732 | CCleaner64.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\ccc0fa1b9f86f7b3.customDestinations-ms | binary | |
MD5:CAD56C32A230D042BD8D77CE6F29E30C | SHA256:6D2BABFD3D913FB7E4B52D2CF98476BCE87F820C7061B3297C8EEEA085FD8C3A | |||
| 732 | CCleaner64.exe | — | ||
MD5:— | SHA256:— | |||
| 4448 | Client.exe | C:\Windows\xdwd.dll | executable | |
MD5:16E5A492C9C6AE34C59683BE9C51FA31 | SHA256:35C8D022E1D917F1AABDCEAE98097CCC072161B302F84C768CA63E4B32AC2B66 | |||
| 732 | CCleaner64.exe | C:\Program Files\CCleaner\gcapi_dll.dll | executable | |
MD5:F17F96322F8741FE86699963A1812897 | SHA256:8B6CE3A640E2D6F36B0001BE2A1ABB765AE51E62C314A15911E75138CBB544BB | |||
| 732 | CCleaner64.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\ccc0fa1b9f86f7b3.customDestinations-ms~RF11c7f0.TMP | binary | |
MD5:715D03F2C851242AE02F082C92170337 | SHA256:52F9047E9A072554A68045FD0215B8484C2D6D758FEE82543FBAA7C7F7D163D9 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
197
TCP/UDP connections
121
DNS requests
55
Threats
54
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 304 | 52.149.20.212:443 | https://slscr.update.microsoft.com/SLS/%7B522D76A4-93E1-47F8-B8CE-07C937AD1A1E%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | unknown | — | — | unknown |
— | — | GET | 200 | 52.149.20.212:443 | https://slscr.update.microsoft.com/SLS/%7B522D76A4-93E1-47F8-B8CE-07C937AD1A1E%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | unknown | — | — | unknown |
5576 | SIHClient.exe | GET | 200 | 2.16.164.99:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5576 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.1.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 13.95.31.18:443 | https://fe3cr.delivery.mp.microsoft.com/clientwebservice/ping | unknown | — | — | unknown |
5576 | SIHClient.exe | GET | 200 | 2.16.164.99:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut_2010-06-23.crl | unknown | — | — | whitelisted |
5576 | SIHClient.exe | GET | 200 | 2.16.164.99:80 | http://crl.microsoft.com/pki/crl/products/MicTimStaPCA_2010-07-01.crl | unknown | — | — | whitelisted |
— | — | POST | 400 | 20.190.160.14:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | unknown | text | 203 b | whitelisted |
— | — | POST | 400 | 20.190.160.131:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | unknown | text | 203 b | whitelisted |
— | — | POST | 400 | 40.126.32.76:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | unknown | text | 203 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 40.126.32.134:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
— | — | 20.190.160.20:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 20.190.160.20:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3216 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
2112 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2104 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
login.live.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
Hikitariko-60039.portmap.host |
| malicious |
6.tcp.eu.ngrok.io |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Potential Corporate Privacy Violation | ET INFO DNS Query to a Reverse Proxy Service Observed |
2196 | svchost.exe | Misc activity | ET INFO DNS Query for Port Mapping/Tunneling Service Domain (.portmap .host) |
2196 | svchost.exe | Misc activity | ET INFO DNS Query to a *.ngrok domain (ngrok.io) |
4448 | Client.exe | A Network Trojan was detected | ET MALWARE PureLogs Backdoor Client GZIP C2 Traffic |
4448 | Client.exe | A Network Trojan was detected | ET MALWARE PureLogs Backdoor Client GZIP C2 Traffic |
4448 | Client.exe | A Network Trojan was detected | ET MALWARE DcRAT/Sheet RAT CnC Checkin Using MessagePack |
4448 | Client.exe | A Network Trojan was detected | ET MALWARE PureLogs Backdoor Client GZIP C2 Traffic |
4448 | Client.exe | A Network Trojan was detected | ET MALWARE PureLogs Backdoor Client GZIP C2 Traffic |
4448 | Client.exe | A Network Trojan was detected | ET MALWARE PureLogs Backdoor Client GZIP C2 Traffic |
4448 | Client.exe | A Network Trojan was detected | ET MALWARE PureLogs Backdoor Server GZIP C2 Traffic |