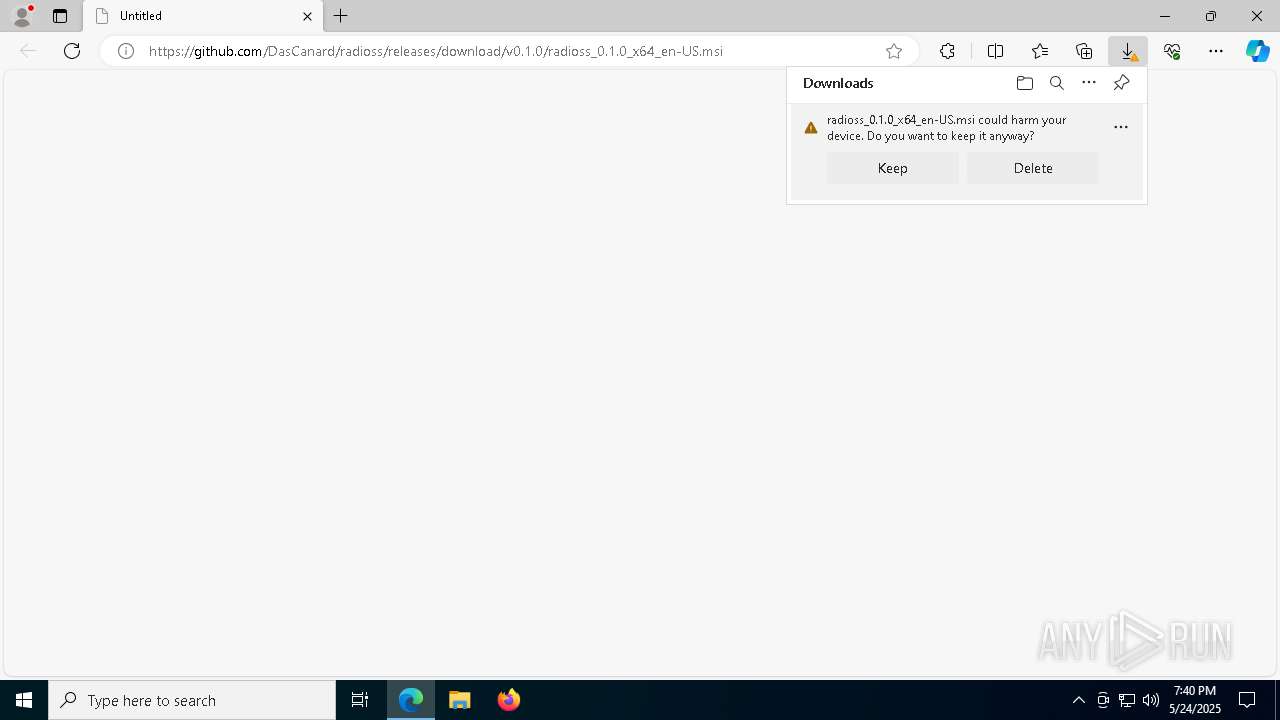
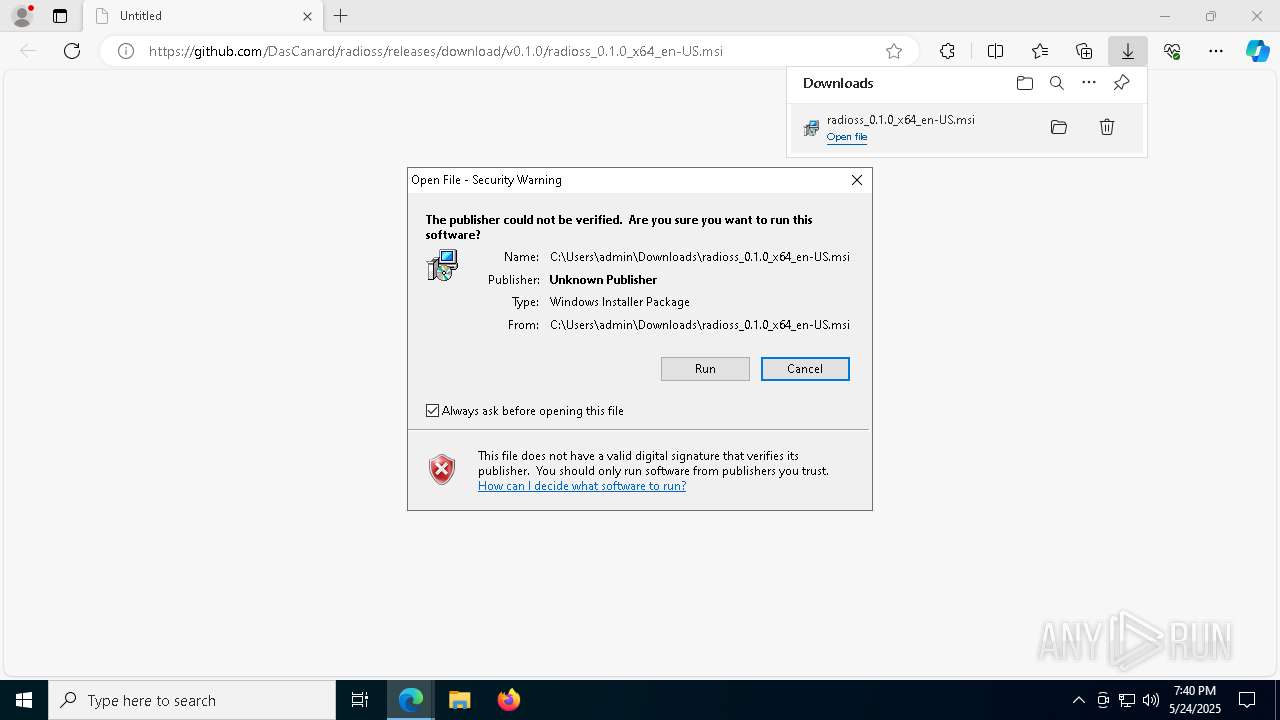
| URL: | https://github.com/DasCanard/radioss/releases/download/v0.1.0/radioss_0.1.0_x64_en-US.msi |
| Full analysis: | https://app.any.run/tasks/5452bea6-35e2-4665-9563-bb5e9ccb85c1 |
| Verdict: | Malicious activity |
| Analysis date: | May 24, 2025, 19:40:12 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MD5: | 5678F0F2AC29144B2FBA7FF3ABD74C31 |
| SHA1: | 8741B97B62FCAB32DDF4CA85122786F8D84111D1 |
| SHA256: | A93D82CF500FAE857D7C31D9AD17D382E7F6F0A70B7422E44B42F7368DA5732B |
| SSDEEP: | 3:N8tEdHXsJArkCeLK736AhsrM:2u9XSMQ+j6AhsY |
MALICIOUS
Run PowerShell with an invisible window
- powershell.exe (PID: 2908)
SUSPICIOUS
The process bypasses the loading of PowerShell profile settings
- msiexec.exe (PID: 1312)
Downloads file from URI via Powershell
- powershell.exe (PID: 2908)
Executes as Windows Service
- VSSVC.exe (PID: 1348)
Manipulates environment variables
- powershell.exe (PID: 2908)
Starts POWERSHELL.EXE for commands execution
- msiexec.exe (PID: 1312)
Starts process via Powershell
- powershell.exe (PID: 2908)
Executable content was dropped or overwritten
- powershell.exe (PID: 2908)
- MicrosoftEdgeWebview2Setup.exe (PID: 8292)
- MicrosoftEdgeUpdate.exe (PID: 8468)
- MicrosoftEdge_X64_136.0.3240.92.exe (PID: 9076)
Starts a Microsoft application from unusual location
- MicrosoftEdgeWebview2Setup.exe (PID: 8292)
- MicrosoftEdgeUpdate.exe (PID: 8468)
Process drops legitimate windows executable
- MicrosoftEdgeWebview2Setup.exe (PID: 8292)
- MicrosoftEdgeUpdate.exe (PID: 8468)
- MicrosoftEdge_X64_136.0.3240.92.exe (PID: 9076)
Starts itself from another location
- MicrosoftEdgeUpdate.exe (PID: 8468)
Application launched itself
- setup.exe (PID: 9100)
INFO
Reads Microsoft Office registry keys
- msedge.exe (PID: 780)
Executable content was dropped or overwritten
- msiexec.exe (PID: 7584)
- msiexec.exe (PID: 1312)
Checks supported languages
- msiexec.exe (PID: 1312)
- identity_helper.exe (PID: 7748)
- msiexec.exe (PID: 7588)
Manages system restore points
- SrTasks.exe (PID: 4404)
Reads the computer name
- msiexec.exe (PID: 1312)
- msiexec.exe (PID: 7588)
- identity_helper.exe (PID: 7748)
Reads Environment values
- identity_helper.exe (PID: 7748)
Application launched itself
- msedge.exe (PID: 780)
The sample compiled with english language support
- MicrosoftEdgeWebview2Setup.exe (PID: 8292)
- MicrosoftEdgeUpdate.exe (PID: 8468)
- MicrosoftEdge_X64_136.0.3240.92.exe (PID: 9076)
The executable file from the user directory is run by the Powershell process
- MicrosoftEdgeWebview2Setup.exe (PID: 8292)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
186
Monitored processes
50
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 632 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | SrTasks.exe |
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) | ||||
| 780 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" "https://github.com/DasCanard/radioss/releases/download/v0.1.0/radioss_0.1.0_x64_en-US.msi" | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | explorer.exe | |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 | ||||
| 1168 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6976 --field-trial-handle=2440,i,11474636097686671777,8707031954304186490,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe |
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 | ||||
| 1312 | C:\WINDOWS\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | services.exe | |
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Version: 5.0.19041.1 (WinBuild.160101.0800) | ||||
| 1348 | C:\WINDOWS\system32\vssvc.exe | C:\Windows\System32\VSSVC.exe | — | services.exe |
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Version: 10.0.19041.1 (WinBuild.160101.0800) | ||||
| 2552 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4936 --field-trial-handle=2440,i,11474636097686671777,8707031954304186490,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe |
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 | ||||
| 2908 | powershell.exe -NoProfile -windowstyle hidden try { [Net.ServicePointManager]::SecurityProtocol = [Net.SecurityProtocolType]::Tls12 } catch {}; Invoke-WebRequest -Uri "https://go.microsoft.com/fwlink/p/?LinkId=2124703" -OutFile "$env:TEMP\MicrosoftEdgeWebview2Setup.exe" ; Start-Process -FilePath "$env:TEMP\MicrosoftEdgeWebview2Setup.exe" -ArgumentList ('/silent', '/install') -Wait | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | msiexec.exe | |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Version: 10.0.19041.1 (WinBuild.160101.0800) | ||||
| 4112 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=122.0.6261.70 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 "--annotation=prod=Microsoft Edge" --annotation=ver=122.0.2365.59 --initial-client-data=0x300,0x304,0x308,0x2f8,0x320,0x7ffc89dd5fd8,0x7ffc89dd5fe4,0x7ffc89dd5ff0 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 | ||||
| 4404 | C:\WINDOWS\system32\srtasks.exe ExecuteScopeRestorePoint /WaitForRestorePoint:11 | C:\Windows\System32\SrTasks.exe | — | msiexec.exe |
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Windows System Protection background tasks. Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) | ||||
| 4724 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --no-appcompat-clear --gpu-preferences=WAAAAAAAAADgAAAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAAAEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=2428 --field-trial-handle=2440,i,11474636097686671777,8707031954304186490,262144 --variations-seed-version /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe |
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 | ||||
Total events
0
Read events
0
Write events
0
Delete events
0
Modification events
Executable files
211
Suspicious files
69
Text files
35
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 780 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10a7cb.TMP | — | |
MD5:— | SHA256:— | |||
| 780 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 780 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10a7cb.TMP | — | |
MD5:— | SHA256:— | |||
| 780 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 780 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10a7da.TMP | — | |
MD5:— | SHA256:— | |||
| 780 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 780 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10a819.TMP | — | |
MD5:— | SHA256:— | |||
| 780 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 780 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10a838.TMP | — | |
MD5:— | SHA256:— | |||
| 780 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
50
DNS requests
42
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.16.168.114:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
8816 | svchost.exe | HEAD | 200 | 208.89.74.17:80 | http://msedge.f.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/3e2fb3dd-6316-4a11-801b-c8c0d21312e9?P1=1748720448&P2=404&P3=2&P4=ln6mCQeNpP2kXzYzHphUyH8jMZDut4JHP4O3aAIt7uprqnsP3j5b6gGZb0sLncTgpRRZnBwyJBmRUB2TgCD87Q%3d%3d | unknown | — | — | whitelisted |
4892 | SIHClient.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
8816 | svchost.exe | GET | 200 | 208.89.74.17:80 | http://msedge.f.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/3e2fb3dd-6316-4a11-801b-c8c0d21312e9?P1=1748720448&P2=404&P3=2&P4=ln6mCQeNpP2kXzYzHphUyH8jMZDut4JHP4O3aAIt7uprqnsP3j5b6gGZb0sLncTgpRRZnBwyJBmRUB2TgCD87Q%3d%3d | unknown | — | — | whitelisted |
4892 | SIHClient.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5796 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5048 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.16.168.114:80 | crl.microsoft.com | Akamai International B.V. | RU | whitelisted |
5496 | MoUsoCoreWorker.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
780 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
6416 | msedge.exe | 140.82.121.3:443 | github.com | GITHUB | US | whitelisted |
6416 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
github.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
objects.githubusercontent.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
8816 | svchost.exe | Misc activity | ET INFO Packed Executable Download |