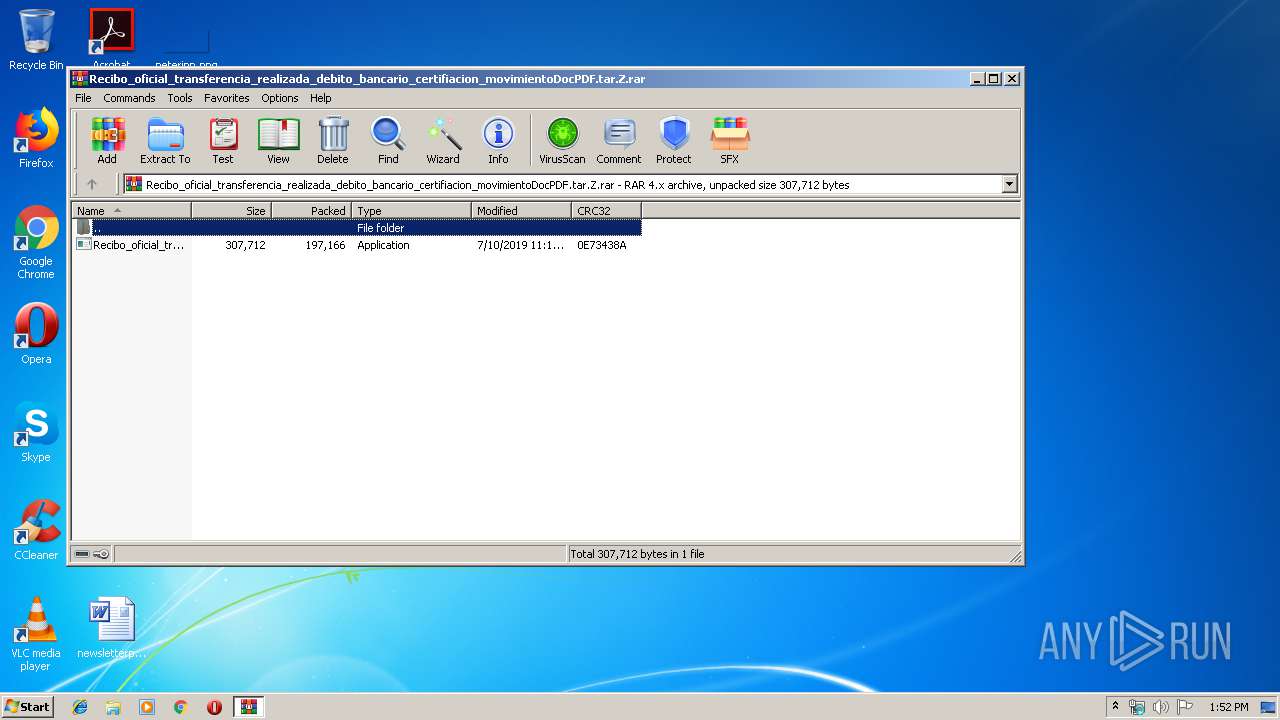
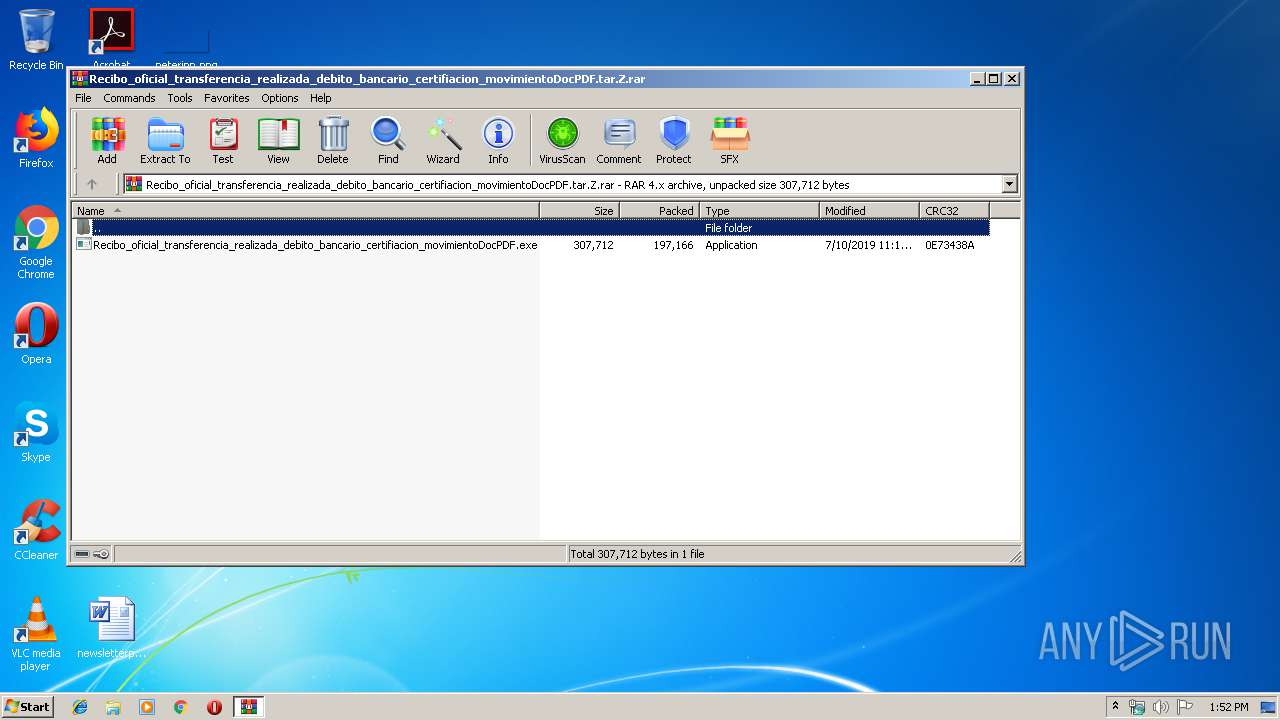
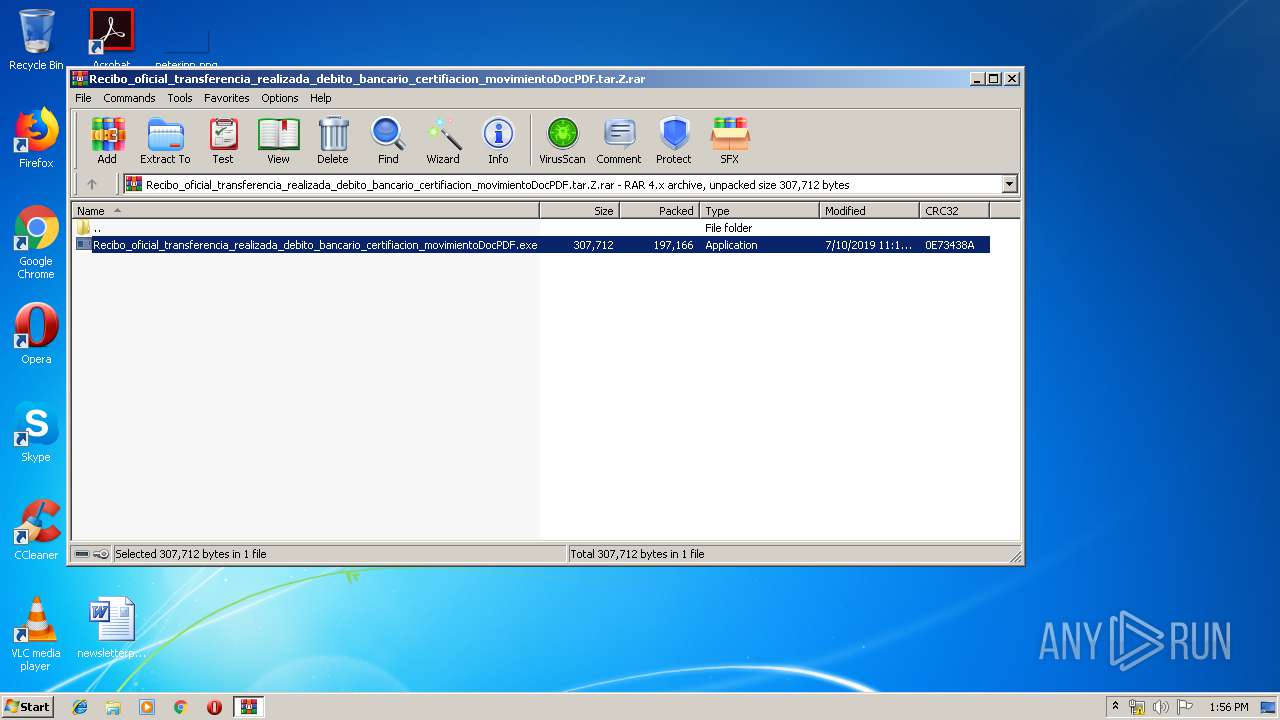
| File name: | Recibo_oficial_transferencia_realizada_debito_bancario_certifiacion_movimientoDocPDF.tar.Z |
| Full analysis: | https://app.any.run/tasks/a162a0ea-bd33-42f4-925e-64225c894bba |
| Verdict: | Malicious activity |
| Analysis date: | July 11, 2019, 12:51:44 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v4, os: Win32 |
| MD5: | 6FAFF4F73309C2C67811B3A0ECDF57EF |
| SHA1: | C922D23C26C2078858BF499BDC574F89786E6EC3 |
| SHA256: | A93523980BDF19A7E66CA009A6AD8940A2F6D55A02CCAECC1772147A8FFA289C |
| SSDEEP: | 3072:l/ty0Ssd6mRHH7VwN6EahKtSs5nzOQDHPwyLPyeP7J6n+5rROXIOLqnCIxNxeVHF:l/tQKEZ5EsxqIIoycnXXZxNqF |
MALICIOUS
Application was dropped or rewritten from another process
- Recibo_oficial_transferencia_realizada_debito_bancario_certifiacion_movimientoDocPDF.exe (PID: 3776)
Writes to a start menu file
- cscript.exe (PID: 3648)
SUSPICIOUS
Creates files in the user directory
- cscript.exe (PID: 3648)
Executable content was dropped or overwritten
- Recibo_oficial_transferencia_realizada_debito_bancario_certifiacion_movimientoDocPDF.exe (PID: 3776)
- WinRAR.exe (PID: 2892)
Executes scripts
- Recibo_oficial_transferencia_realizada_debito_bancario_certifiacion_movimientoDocPDF.exe (PID: 3776)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v-4.x) (58.3) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (41.6) |
EXIF
ZIP
| CompressedSize: | 197280 |
|---|---|
| UncompressedSize: | 307712 |
| OperatingSystem: | Win32 |
| ModifyDate: | 2019:07:10 23:14:04 |
| PackingMethod: | Normal |
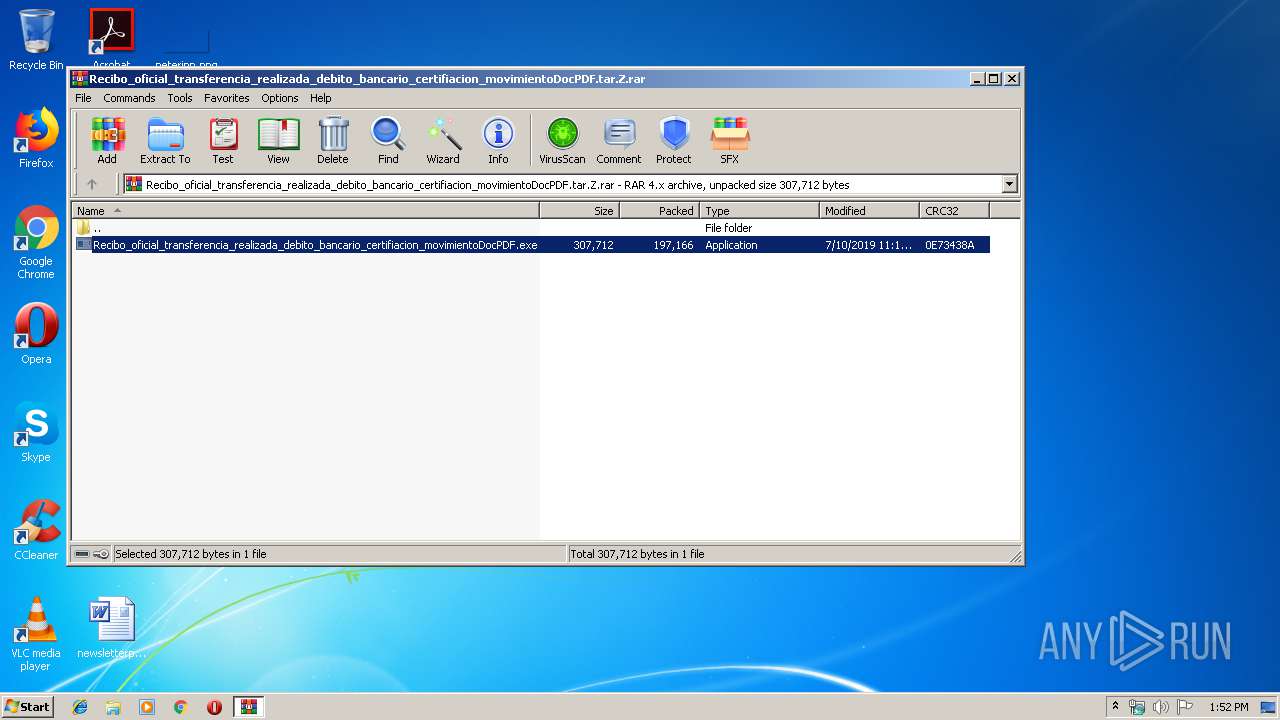
| ArchivedFileName: | Recibo_oficial_transferencia_realizada_debito_bancario_certifiacion_movimientoDocPDF.exe |
Total processes
40
Monitored processes
4
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2892 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Recibo_oficial_transferencia_realizada_debito_bancario_certifiacion_movimientoDocPDF.tar.Z.rar" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2972 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\RegAsm.exe" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\RegAsm.exe | Recibo_oficial_transferencia_realizada_debito_bancario_certifiacion_movimientoDocPDF.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Assembly Registration Utility Exit code: 0 Version: 2.0.50727.5420 (Win7SP1.050727-5400) Modules
| |||||||||||||||
| 3648 | "C:\Windows\System32\cscript.exe" //B //Nologo C:\Users\admin\startupname.vbs | C:\Windows\System32\cscript.exe | Recibo_oficial_transferencia_realizada_debito_bancario_certifiacion_movimientoDocPDF.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Console Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 3776 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa2892.6111\Recibo_oficial_transferencia_realizada_debito_bancario_certifiacion_movimientoDocPDF.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa2892.6111\Recibo_oficial_transferencia_realizada_debito_bancario_certifiacion_movimientoDocPDF.exe | WinRAR.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
910
Read events
875
Write events
35
Delete events
0
Modification events
| (PID) Process: | (2892) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2892) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2892) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\70\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2892) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Recibo_oficial_transferencia_realizada_debito_bancario_certifiacion_movimientoDocPDF.tar.Z.rar | |||
| (PID) Process: | (2892) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2892) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2892) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2892) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2892) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2892) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
2
Suspicious files
0
Text files
1
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2892 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2892.6111\Recibo_oficial_transferencia_realizada_debito_bancario_certifiacion_movimientoDocPDF.exe | executable | |
MD5:— | SHA256:— | |||
| 3776 | Recibo_oficial_transferencia_realizada_debito_bancario_certifiacion_movimientoDocPDF.exe | C:\Users\admin\startupname.vbs | text | |
MD5:— | SHA256:— | |||
| 3648 | cscript.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\startupname.Lnk | lnk | |
MD5:— | SHA256:— | |||
| 3776 | Recibo_oficial_transferencia_realizada_debito_bancario_certifiacion_movimientoDocPDF.exe | C:\Users\admin\Chrome.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
11
DNS requests
5
Threats
5
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2972 | RegAsm.exe | 186.82.242.6:2093 | dominoduck2064.duckdns.org | Telmex Colombia S.A. | CO | malicious |
— | — | 186.82.242.6:2093 | dominoduck2064.duckdns.org | Telmex Colombia S.A. | CO | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
dominoduck2064.duckdns.org |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1044 | svchost.exe | Misc activity | ET INFO DYNAMIC_DNS Query to *.duckdns. Domain |
1044 | svchost.exe | Misc activity | ET INFO DYNAMIC_DNS Query to *.duckdns. Domain |
1044 | svchost.exe | Misc activity | ET INFO DYNAMIC_DNS Query to *.duckdns. Domain |
1044 | svchost.exe | Misc activity | ET INFO DYNAMIC_DNS Query to *.duckdns. Domain |
1044 | svchost.exe | Misc activity | ET INFO DYNAMIC_DNS Query to *.duckdns. Domain |