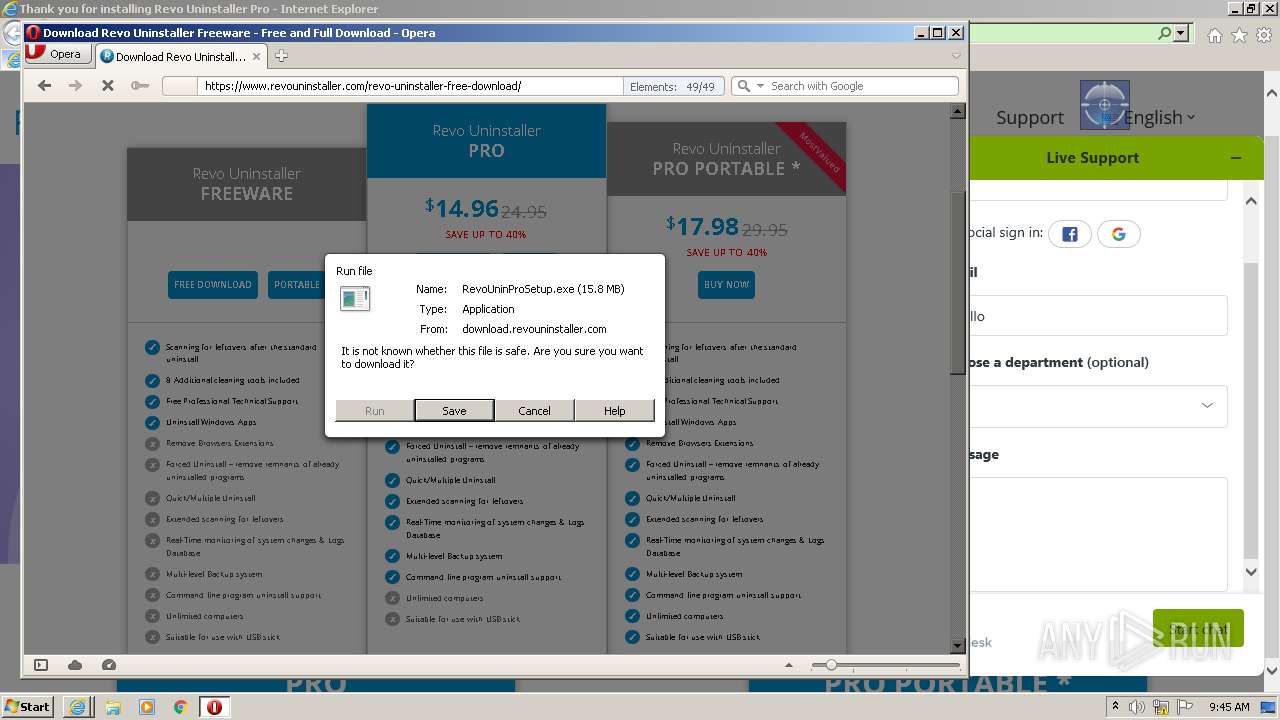
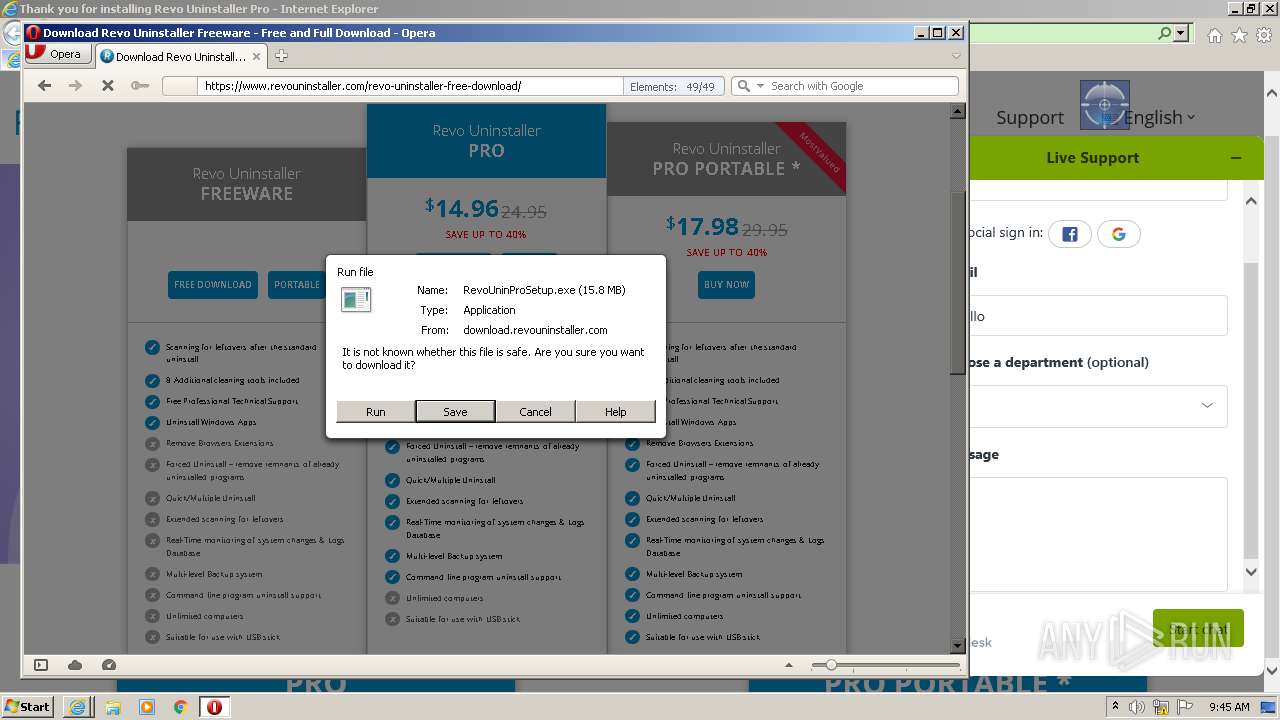
| File name: | RevoUninProSetup (2).exe |
| Full analysis: | https://app.any.run/tasks/1dcd8c1d-6857-4ee4-8bc3-15f5a7f3ba09 |
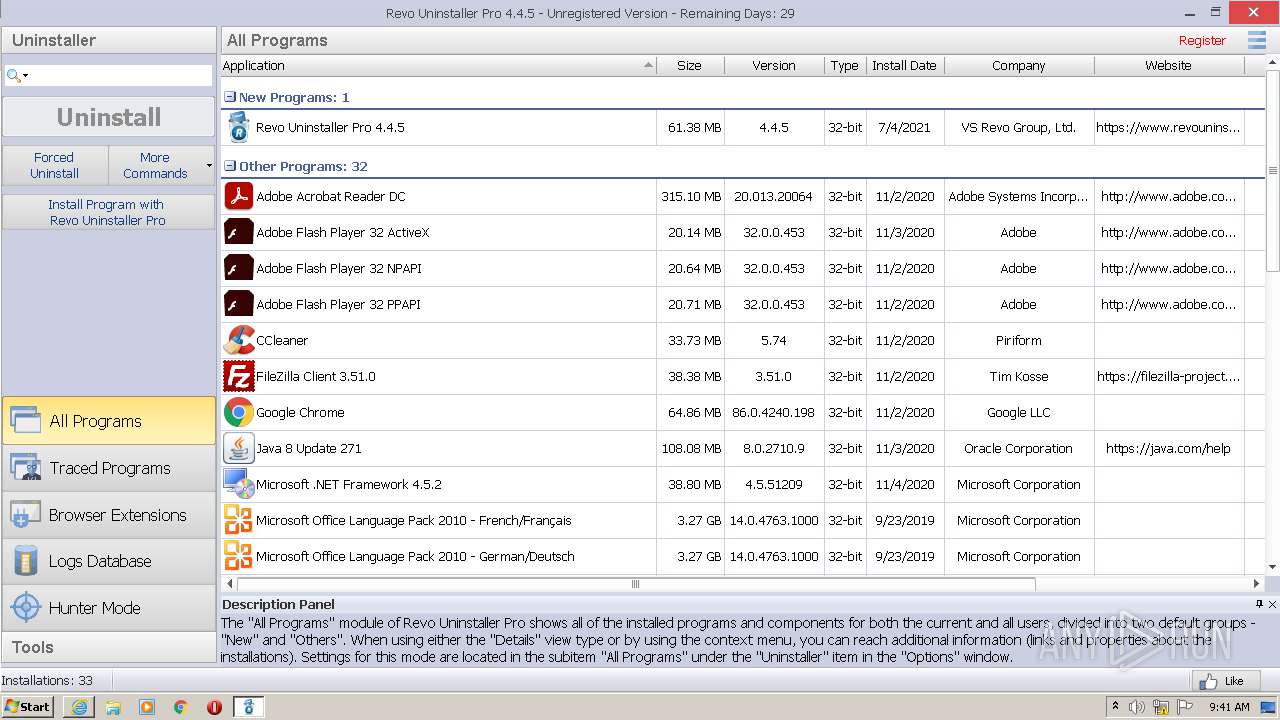
| Verdict: | Malicious activity |
| Threats: | Stealers are a group of malicious software that are intended for gaining unauthorized access to users’ information and transferring it to the attacker. The stealer malware category includes various types of programs that focus on their particular kind of data, including files, passwords, and cryptocurrency. Stealers are capable of spying on their targets by recording their keystrokes and taking screenshots. This type of malware is primarily distributed as part of phishing campaigns. |
| Analysis date: | July 04, 2021, 08:40:28 |
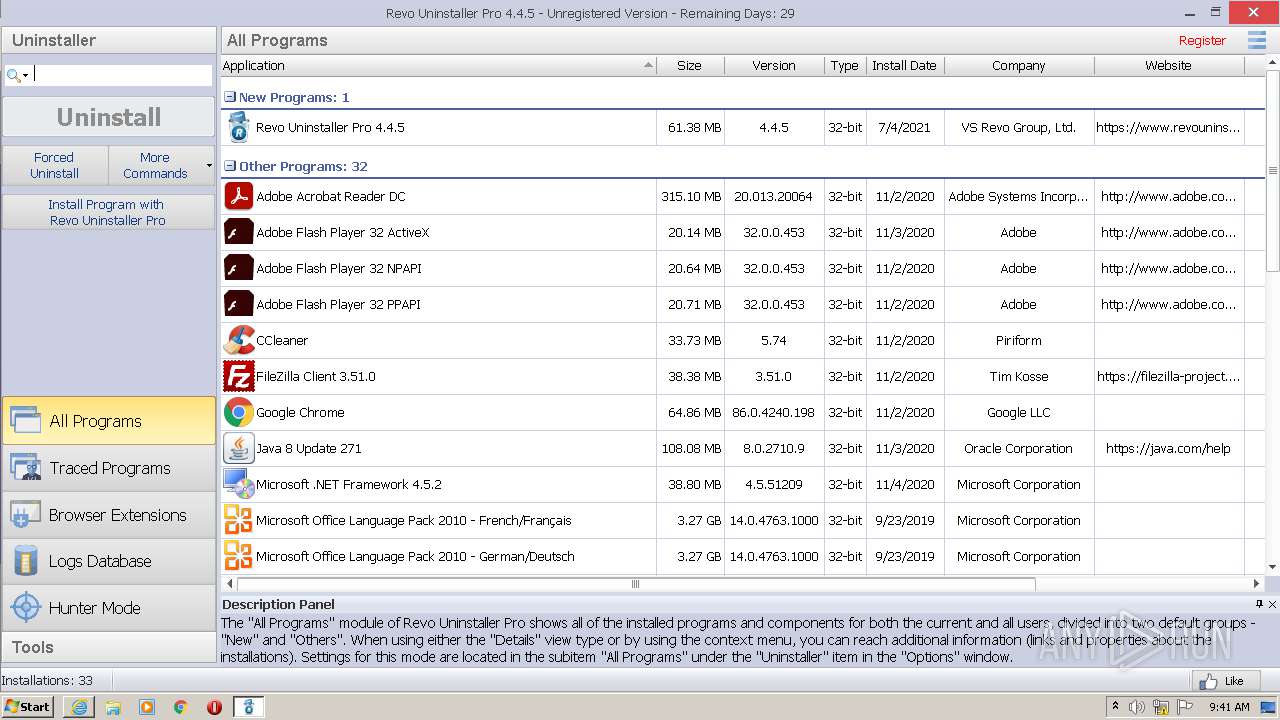
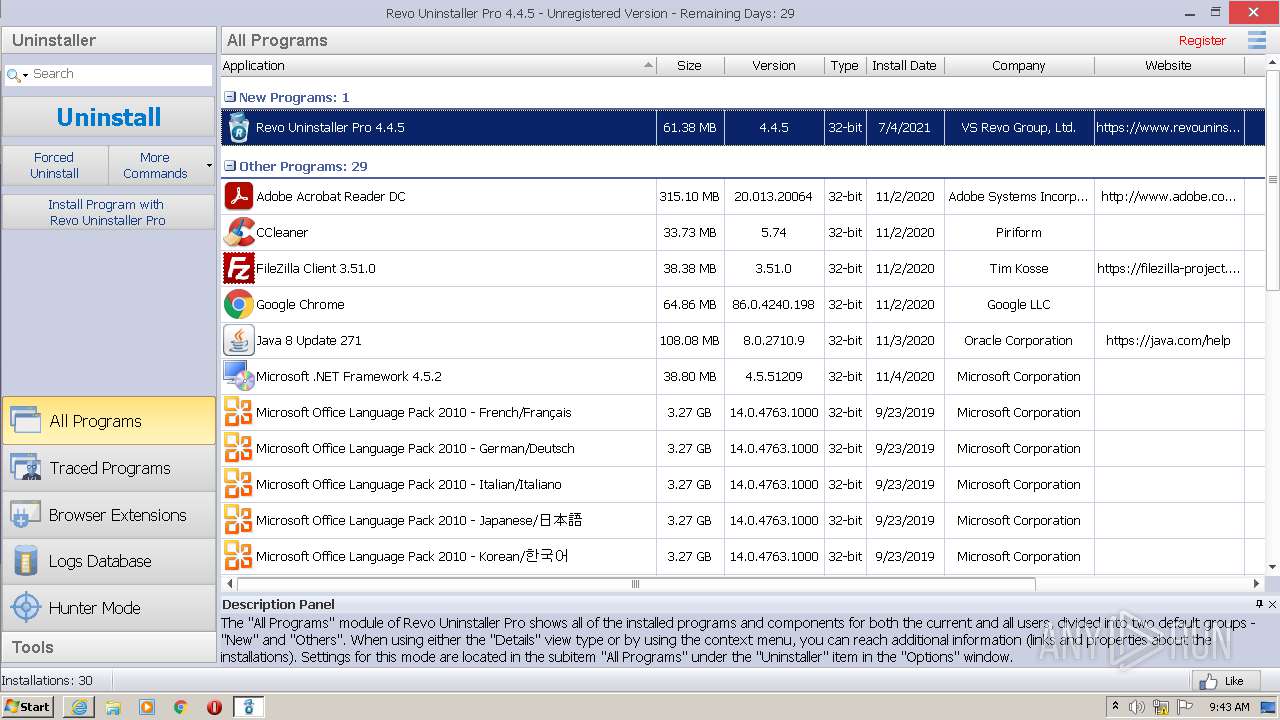
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | B2C9918C0DCC1A7CA7A944D6702CB446 |
| SHA1: | B78D08191B15081ED600424AC9B7728B68376A72 |
| SHA256: | A92D1E8924861659D24BCDBCAC87921797B2A78EC25962C5CB1AA2052F2D71E9 |
| SSDEEP: | 393216:HB72DLS00YXV7AU6zZBcvc6X2bR4/imqVbO7l6Umec0IU:HJELSeVkjzZBEc6Eq6/Mcx |
MALICIOUS
Drops executable file immediately after starts
- RevoUninProSetup (2).exe (PID: 2936)
- RevoUninProSetup (2).exe (PID: 4068)
- rundll32.exe (PID: 360)
Registers / Runs the DLL via REGSVR32.EXE
- RevoUninProSetup (2).tmp (PID: 2260)
Changes the autorun value in the registry
- rundll32.exe (PID: 360)
Loads dropped or rewritten executable
- regsvr32.exe (PID: 1548)
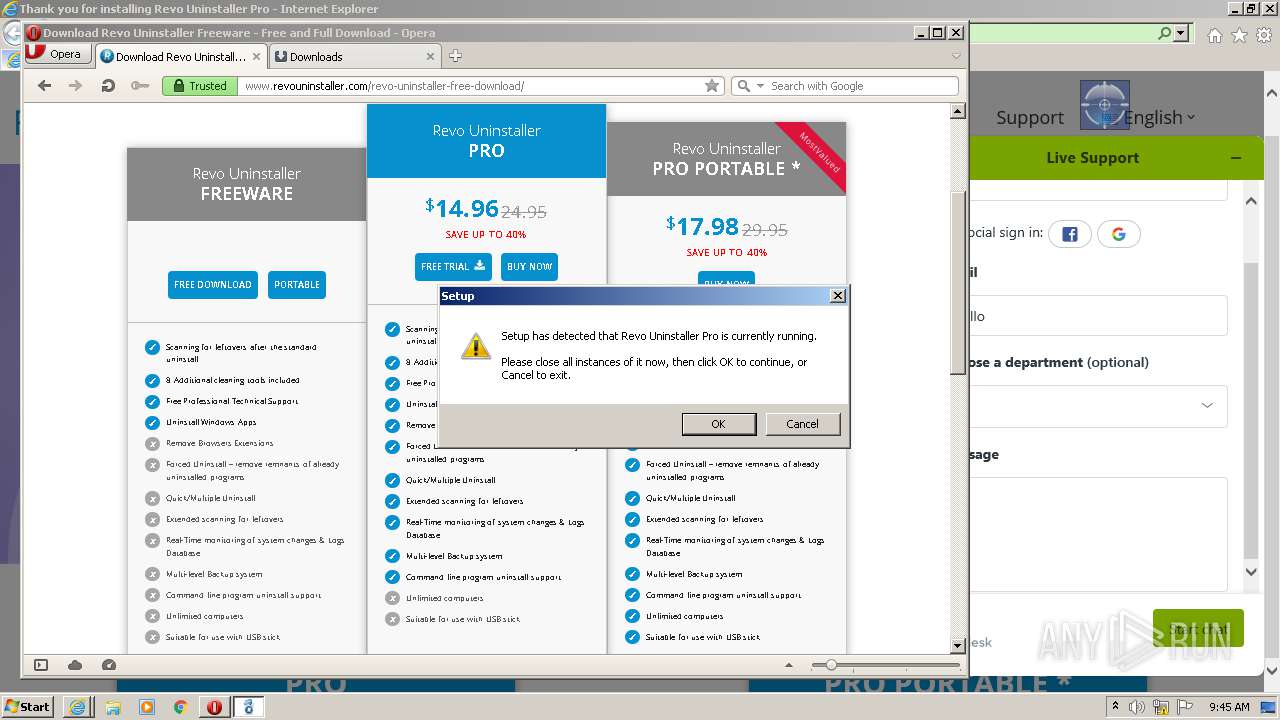
Application was dropped or rewritten from another process
- ruplp.exe (PID: 3404)
- RevoUninPro.exe (PID: 1248)
- RevoUninPro.exe (PID: 2928)
- ruplp.exe (PID: 3260)
Stealing of credential data
- RevoUninPro.exe (PID: 2928)
SUSPICIOUS
Executable content was dropped or overwritten
- RevoUninProSetup (2).exe (PID: 2936)
- RevoUninProSetup (2).exe (PID: 4068)
- RevoUninProSetup (2).tmp (PID: 2260)
- rundll32.exe (PID: 360)
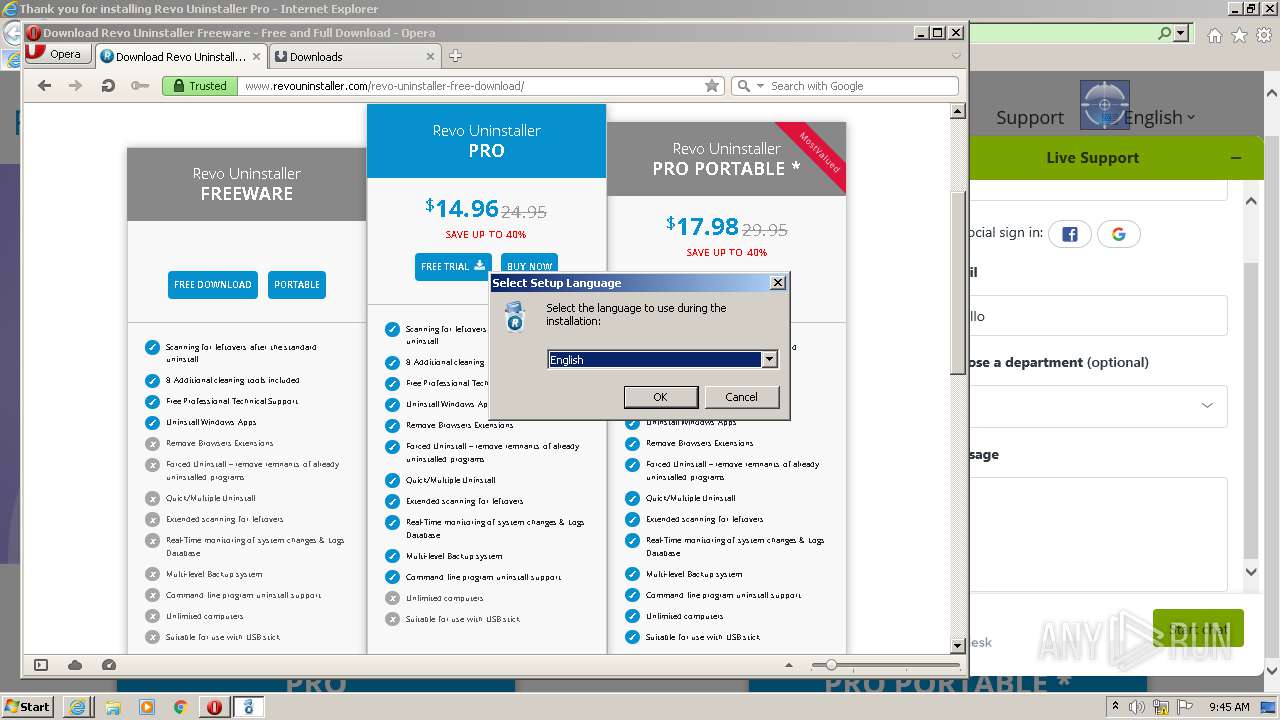
Checks supported languages
- RevoUninProSetup (2).tmp (PID: 2984)
- RevoUninProSetup (2).exe (PID: 2936)
- RevoUninProSetup (2).exe (PID: 4068)
- RevoUninProSetup (2).tmp (PID: 2260)
- ruplp.exe (PID: 3404)
- ruplp.exe (PID: 3260)
- RevoUninPro.exe (PID: 1248)
- RevoUninPro.exe (PID: 2928)
Reads the computer name
- RevoUninProSetup (2).tmp (PID: 2984)
- RevoUninProSetup (2).tmp (PID: 2260)
- RevoUninPro.exe (PID: 1248)
- RevoUninPro.exe (PID: 2928)
- ruplp.exe (PID: 3404)
- ruplp.exe (PID: 3260)
Reads Windows owner or organization settings
- RevoUninProSetup (2).tmp (PID: 2260)
Reads the Windows organization settings
- RevoUninProSetup (2).tmp (PID: 2260)
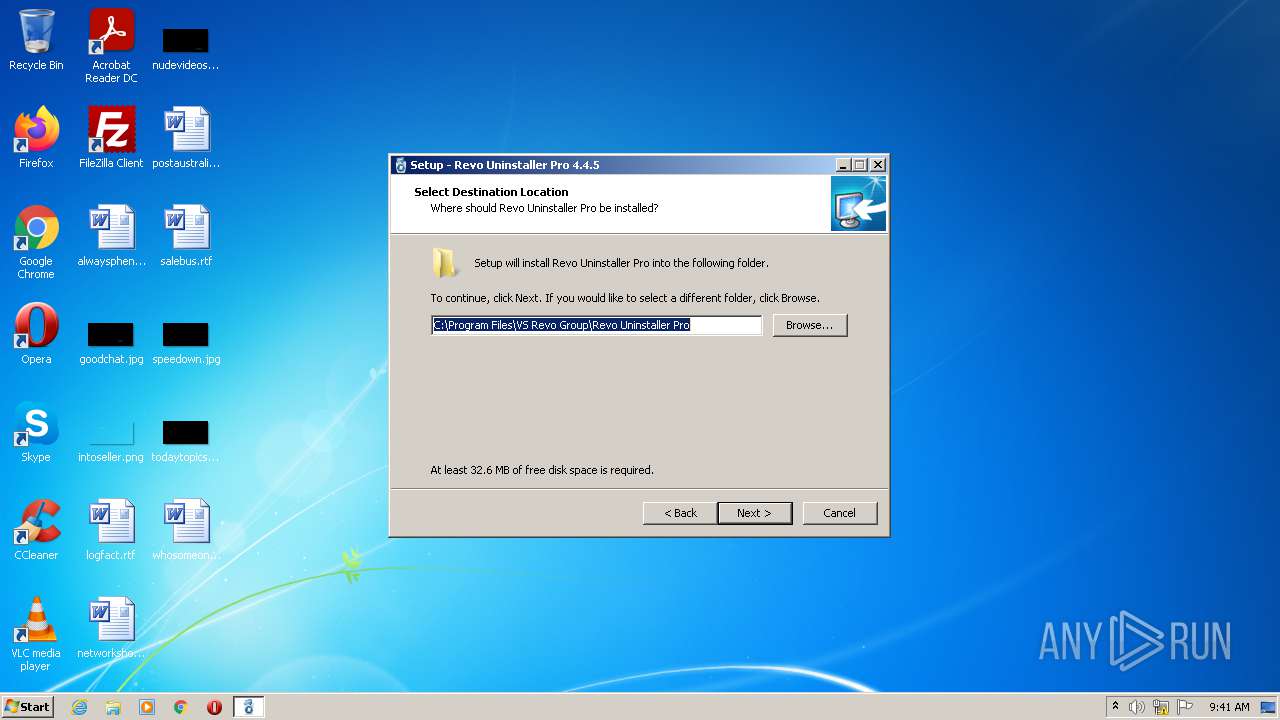
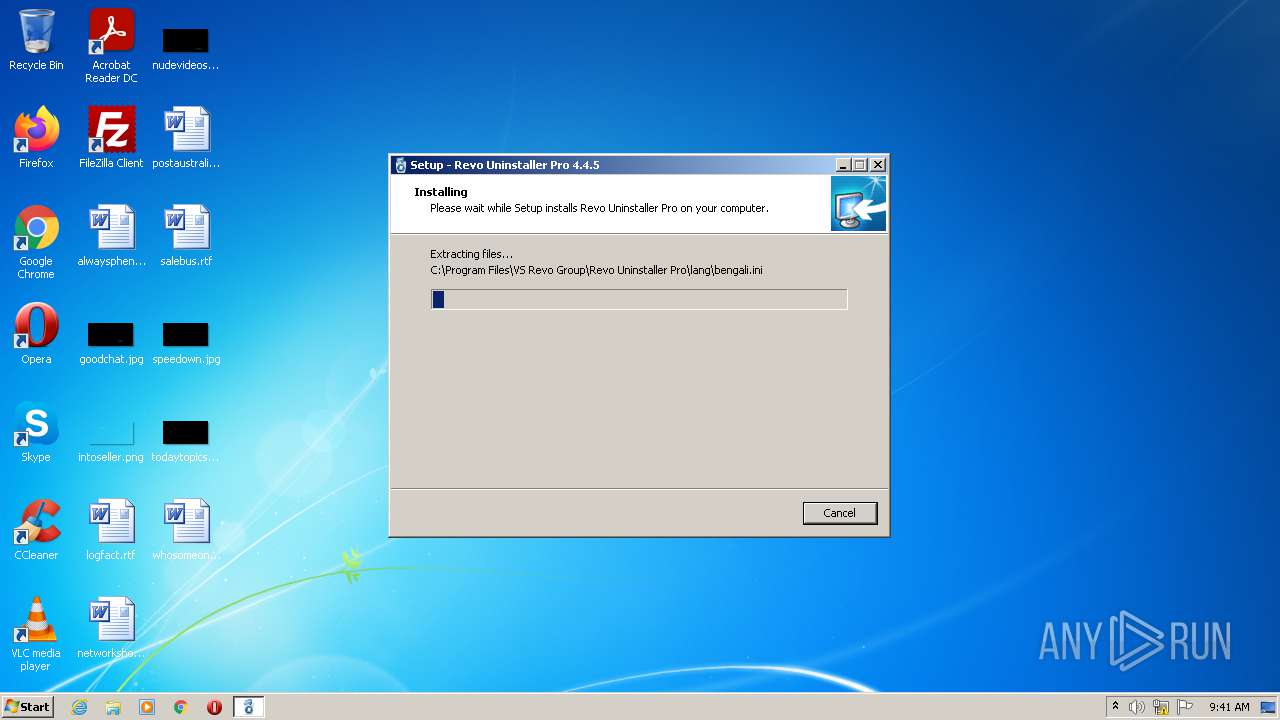
Creates a directory in Program Files
- RevoUninProSetup (2).tmp (PID: 2260)
Drops a file with too old compile date
- RevoUninProSetup (2).tmp (PID: 2260)
Drops a file that was compiled in debug mode
- RevoUninProSetup (2).tmp (PID: 2260)
- rundll32.exe (PID: 360)
Creates files in the user directory
- RevoUninProSetup (2).tmp (PID: 2260)
Changes default file association
- RevoUninProSetup (2).tmp (PID: 2260)
Creates/Modifies COM task schedule object
- regsvr32.exe (PID: 1548)
Uses RUNDLL32.EXE to load library
- RevoUninProSetup (2).tmp (PID: 2260)
Creates files in the Windows directory
- rundll32.exe (PID: 360)
Creates files in the driver directory
- rundll32.exe (PID: 360)
Removes files from Windows directory
- rundll32.exe (PID: 360)
Reads the time zone
- runonce.exe (PID: 2064)
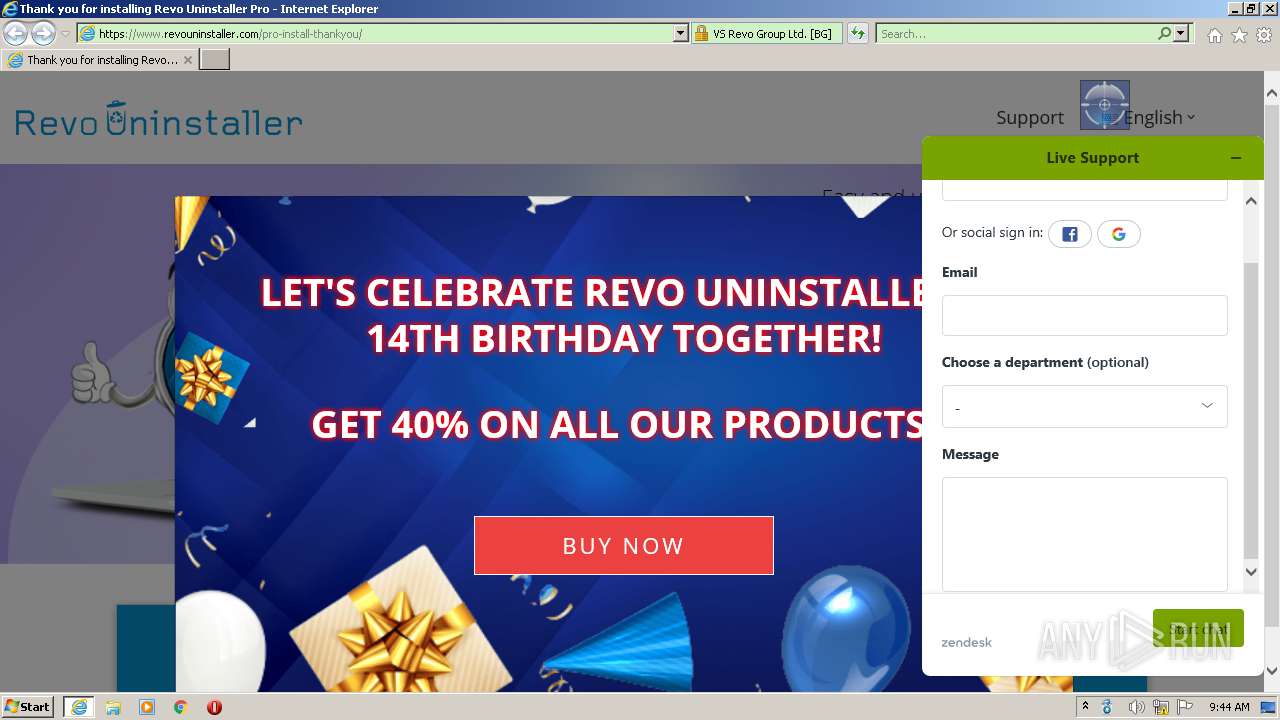
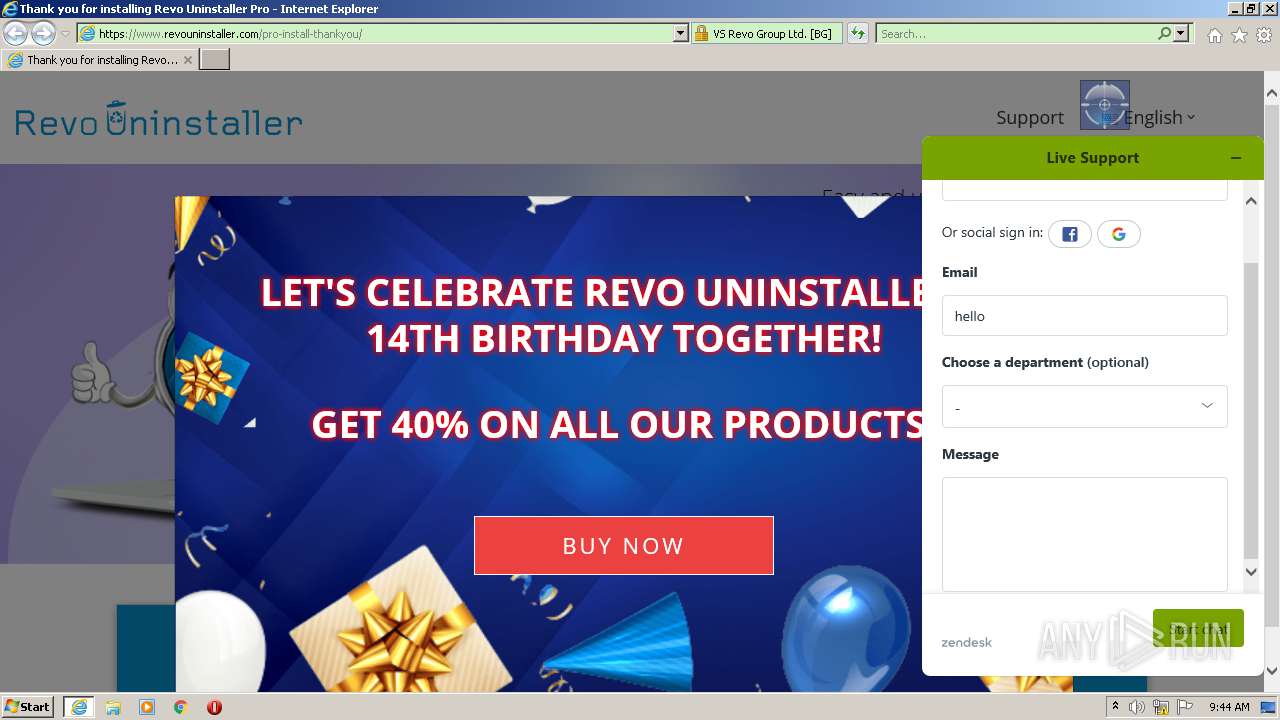
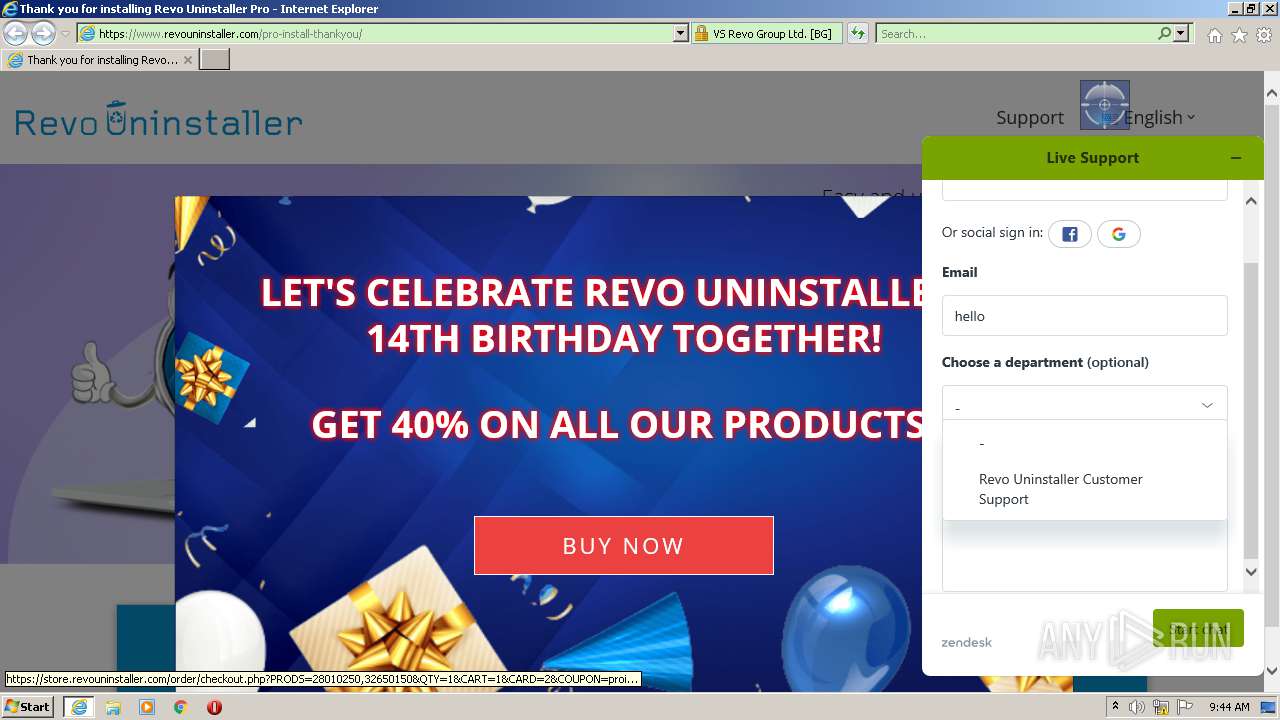
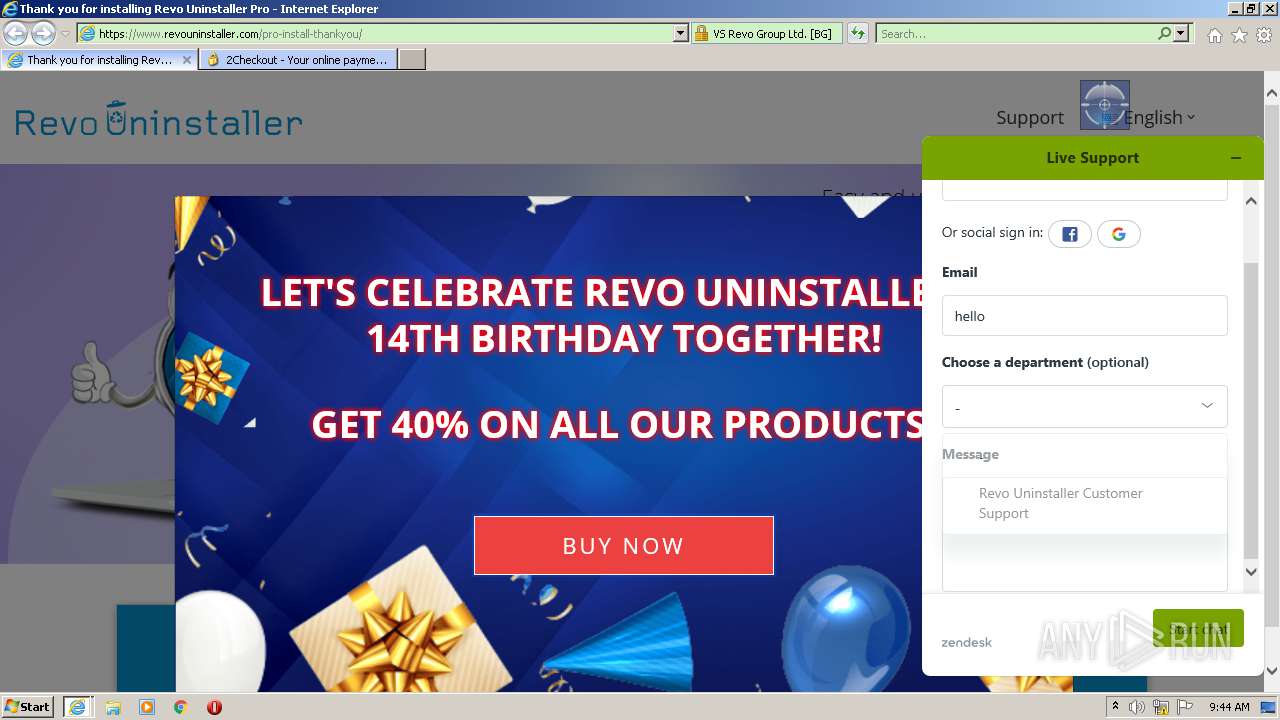
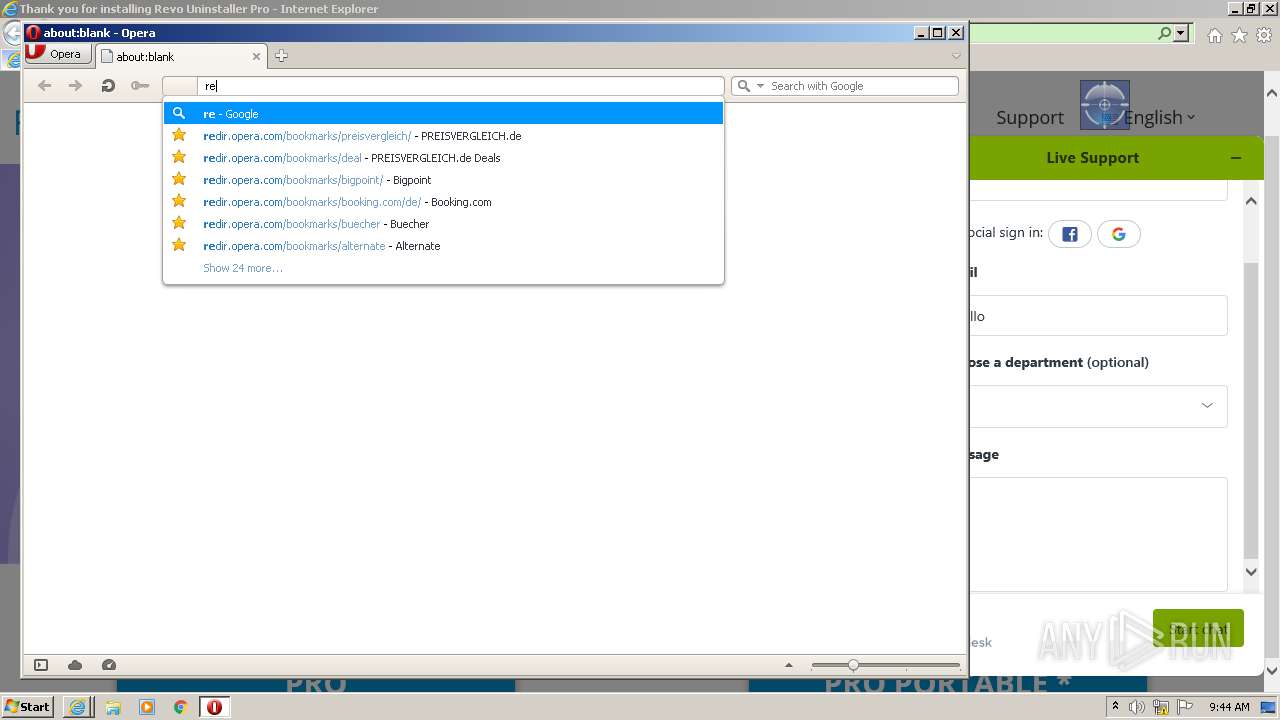
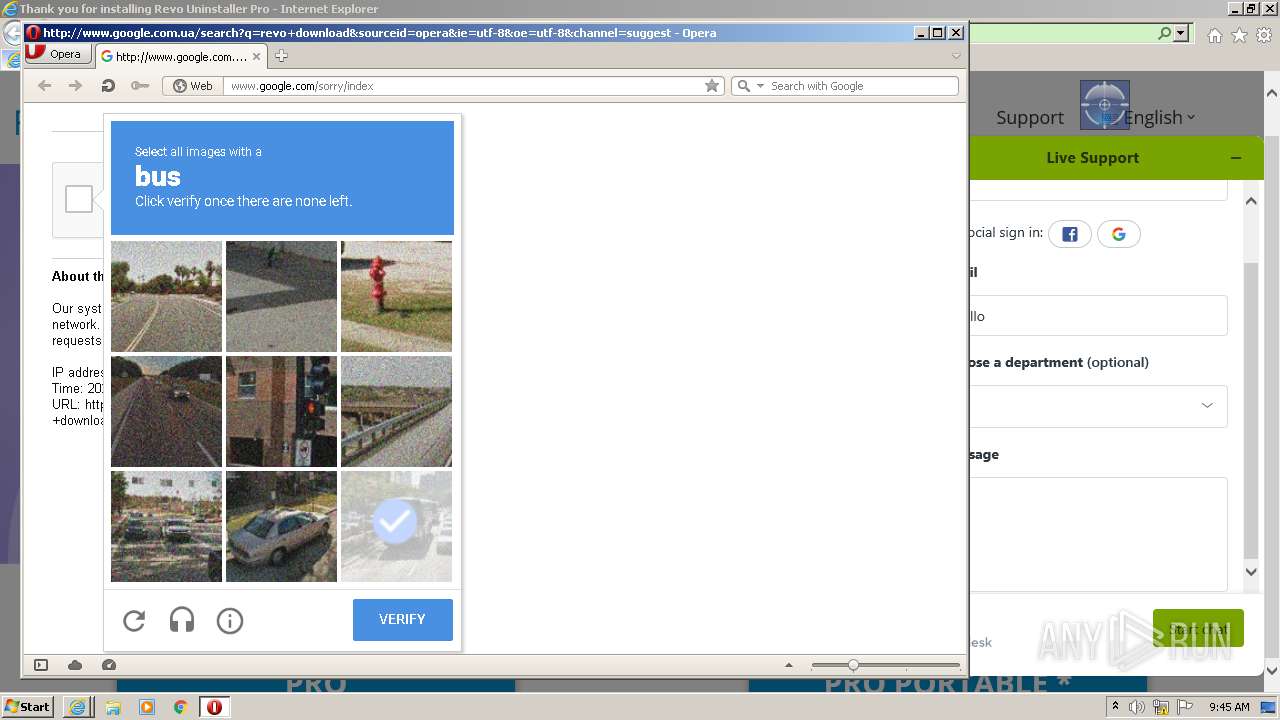
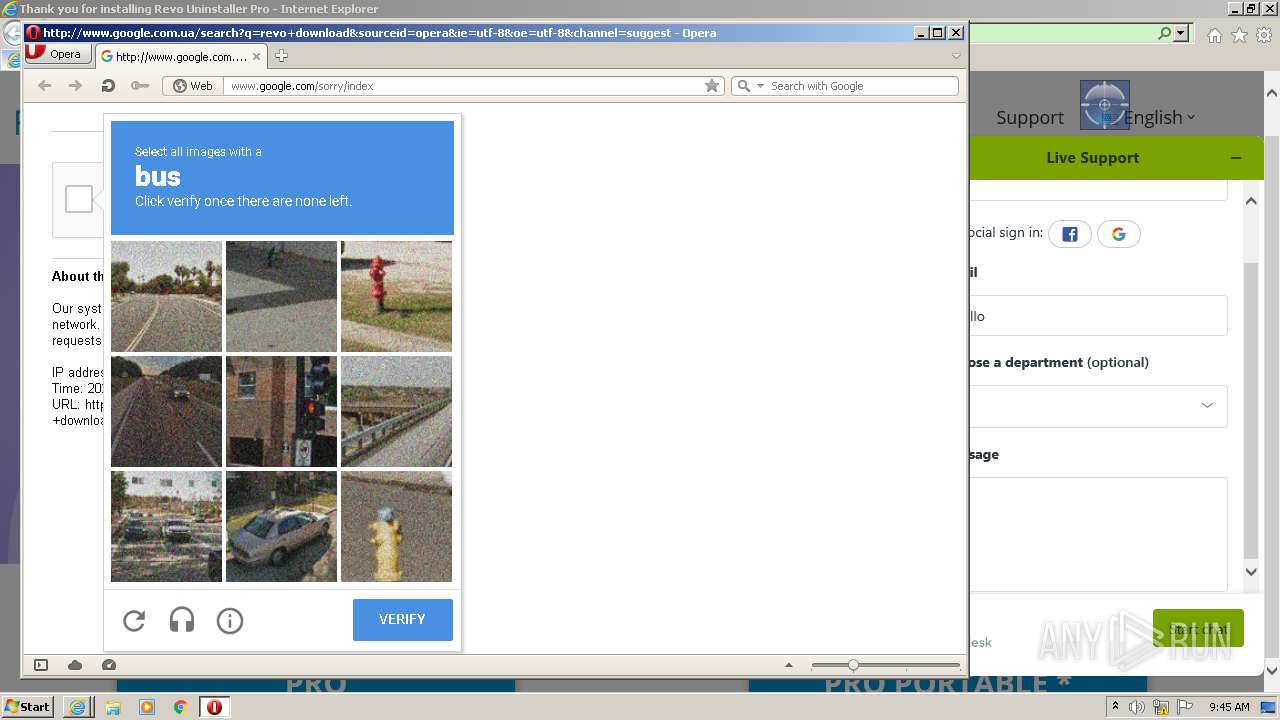
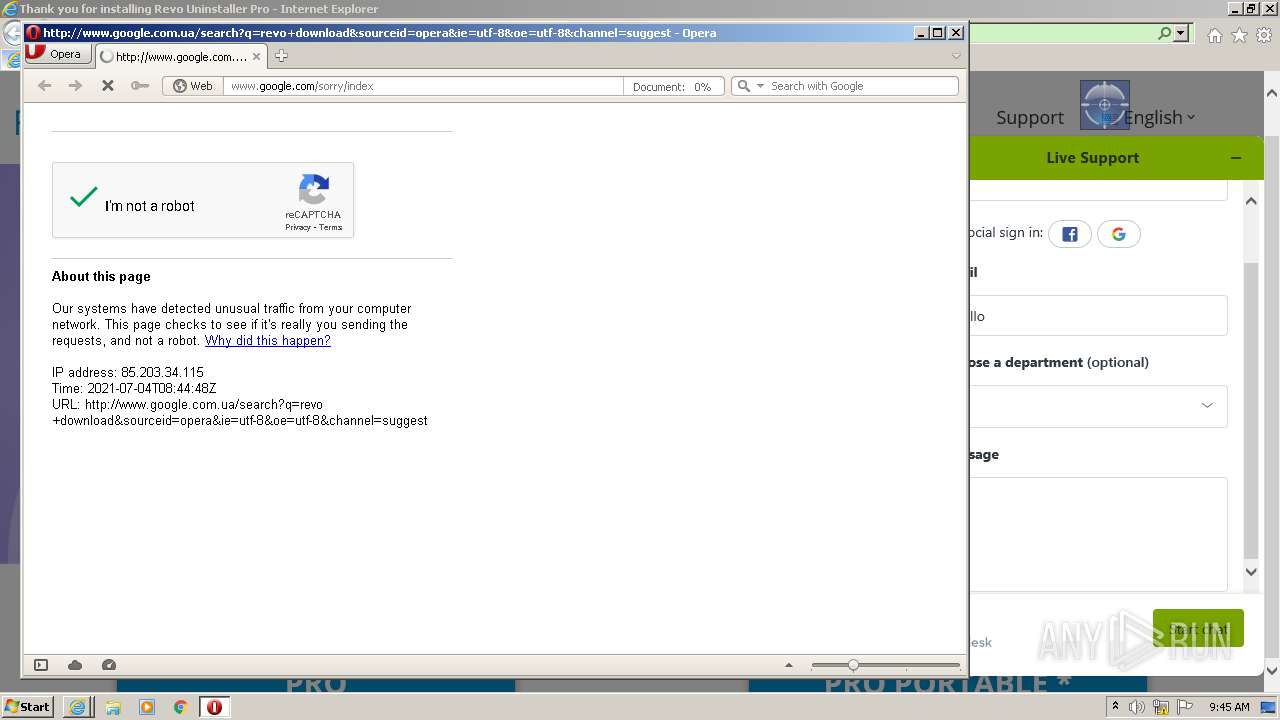
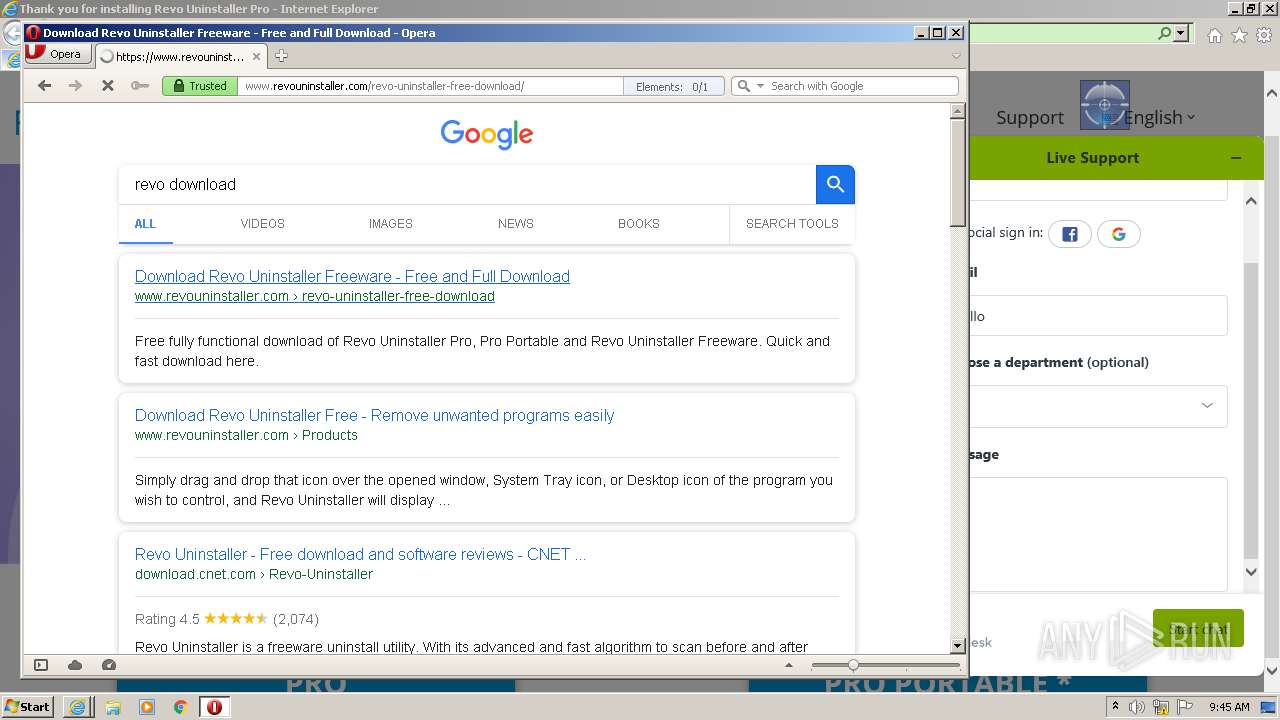
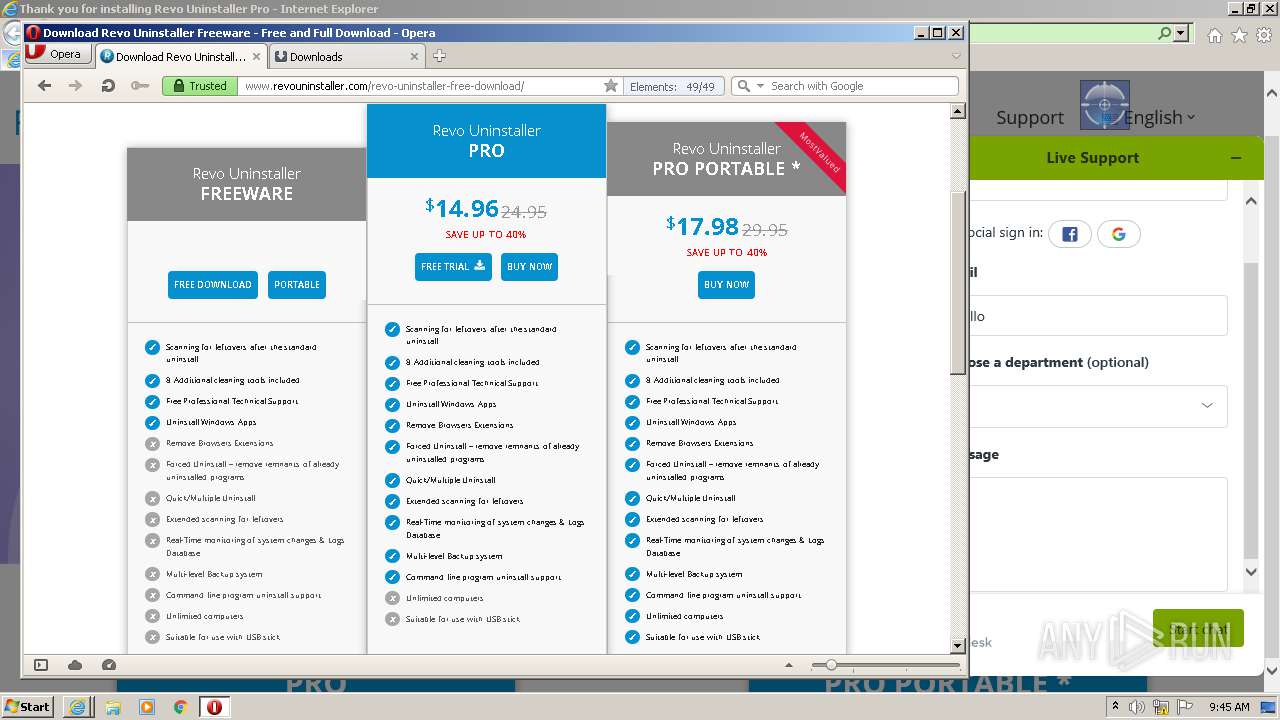
Starts Internet Explorer
- RevoUninProSetup (2).tmp (PID: 2260)
Executed via COM
- ruplp.exe (PID: 3260)
- DllHost.exe (PID: 1348)
Reads Environment values
- ruplp.exe (PID: 3260)
- vssvc.exe (PID: 3096)
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 3496)
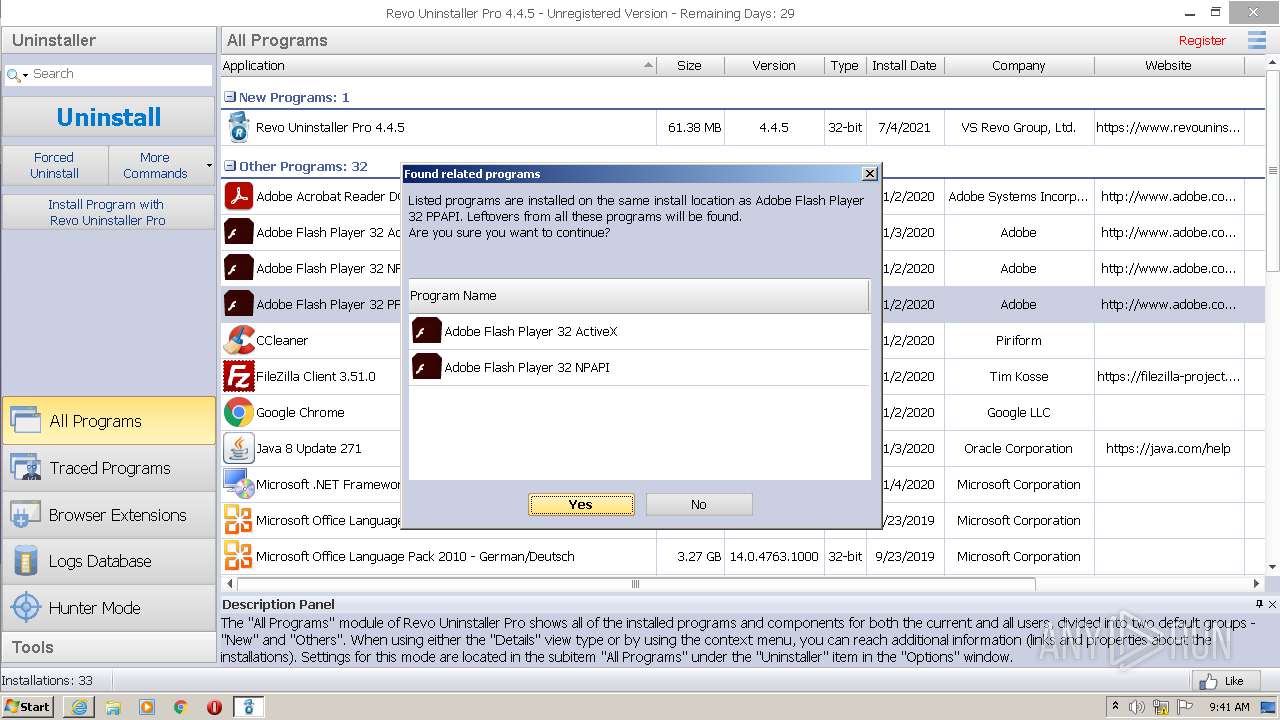
Searches for installed software
- DllHost.exe (PID: 1348)
- RevoUninPro.exe (PID: 2928)
- RevoUninPro.exe (PID: 1248)
Executed as Windows Service
- vssvc.exe (PID: 3096)
INFO
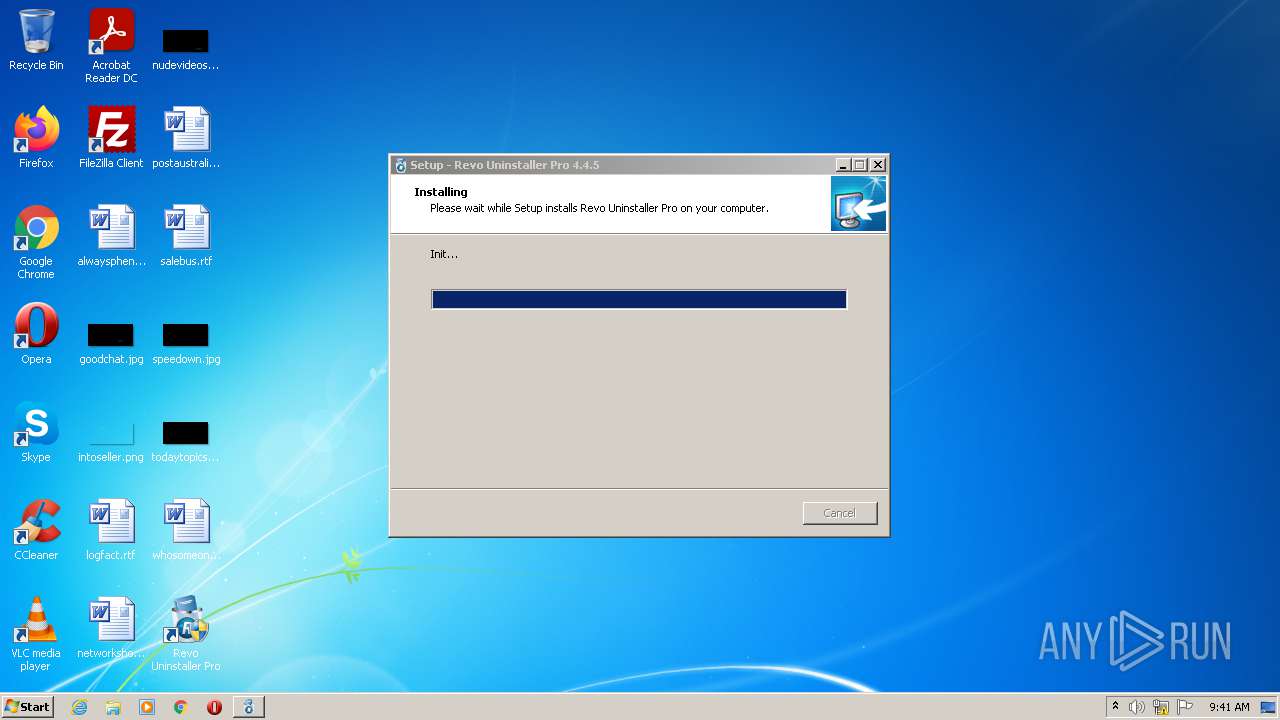
Application was dropped or rewritten from another process
- RevoUninProSetup (2).tmp (PID: 2984)
- RevoUninProSetup (2).tmp (PID: 2260)
Creates files in the program directory
- RevoUninProSetup (2).tmp (PID: 2260)
Checks supported languages
- regsvr32.exe (PID: 1548)
- rundll32.exe (PID: 360)
- runonce.exe (PID: 2064)
- grpconv.exe (PID: 3104)
- iexplore.exe (PID: 4032)
- iexplore.exe (PID: 3496)
- vssvc.exe (PID: 3096)
- DllHost.exe (PID: 1348)
Reads CPU info
- runonce.exe (PID: 2064)
Creates a software uninstall entry
- RevoUninProSetup (2).tmp (PID: 2260)
Reads the computer name
- rundll32.exe (PID: 360)
- runonce.exe (PID: 2064)
- iexplore.exe (PID: 3496)
- iexplore.exe (PID: 4032)
- vssvc.exe (PID: 3096)
- DllHost.exe (PID: 1348)
Application launched itself
- iexplore.exe (PID: 4032)
Changes internet zones settings
- iexplore.exe (PID: 4032)
Reads settings of System Certificates
- iexplore.exe (PID: 3496)
- iexplore.exe (PID: 4032)
Checks Windows Trust Settings
- iexplore.exe (PID: 3496)
- iexplore.exe (PID: 4032)
Reads internet explorer settings
- iexplore.exe (PID: 3496)
Changes settings of System certificates
- iexplore.exe (PID: 3496)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3496)
Creates files in the user directory
- iexplore.exe (PID: 3496)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Delphi generic (57.2) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (18.2) |
| .exe | | | Win16/32 Executable Delphi generic (8.3) |
| .exe | | | Generic Win/DOS Executable (8) |
| .exe | | | DOS Executable Generic (8) |
EXIF
EXE
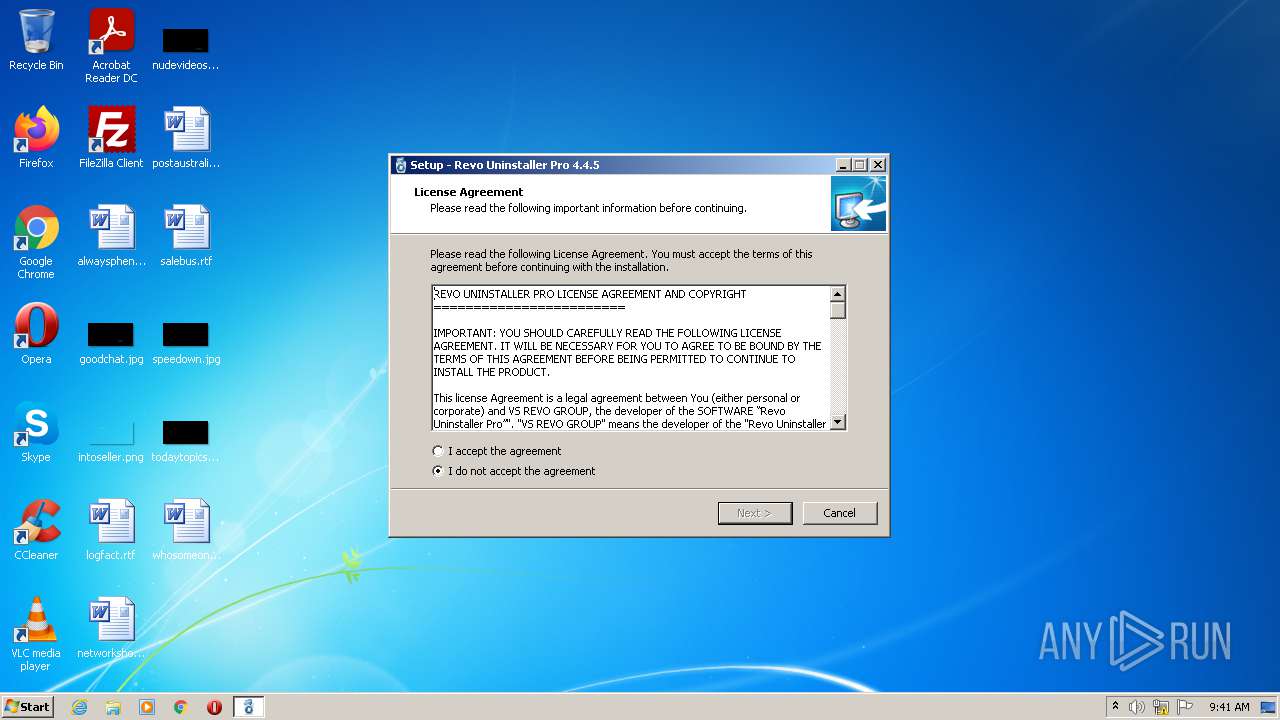
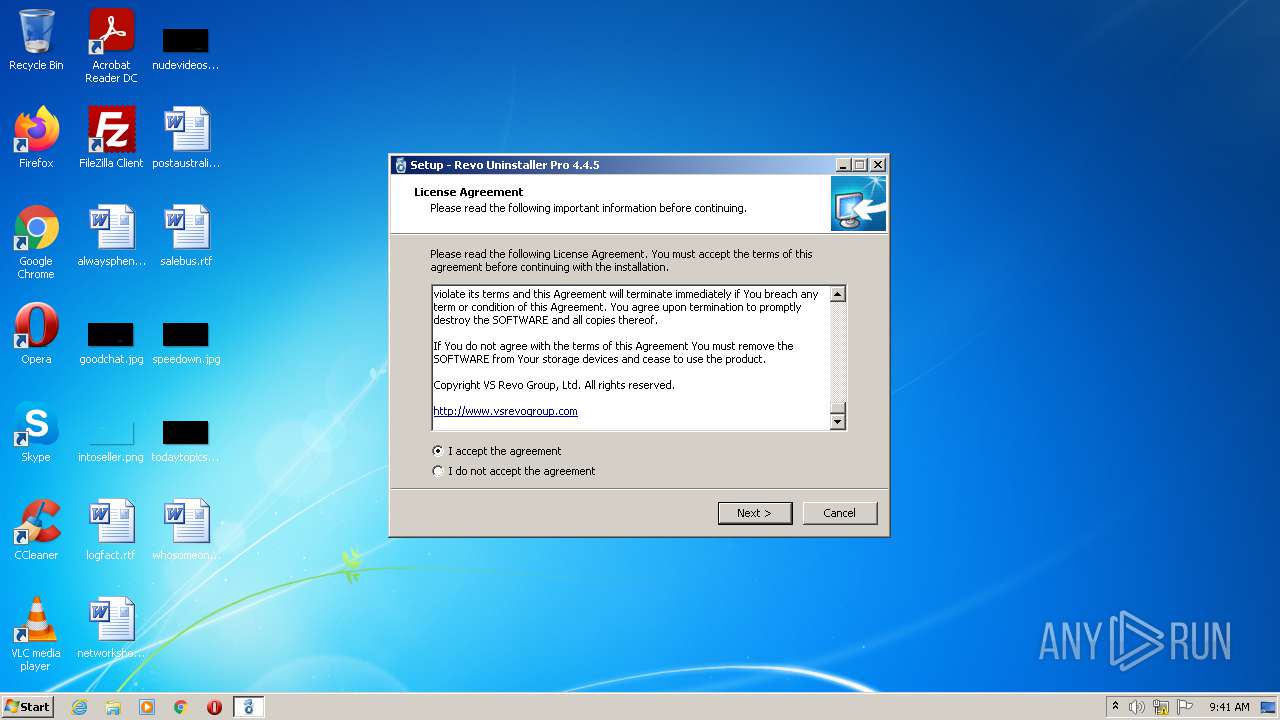
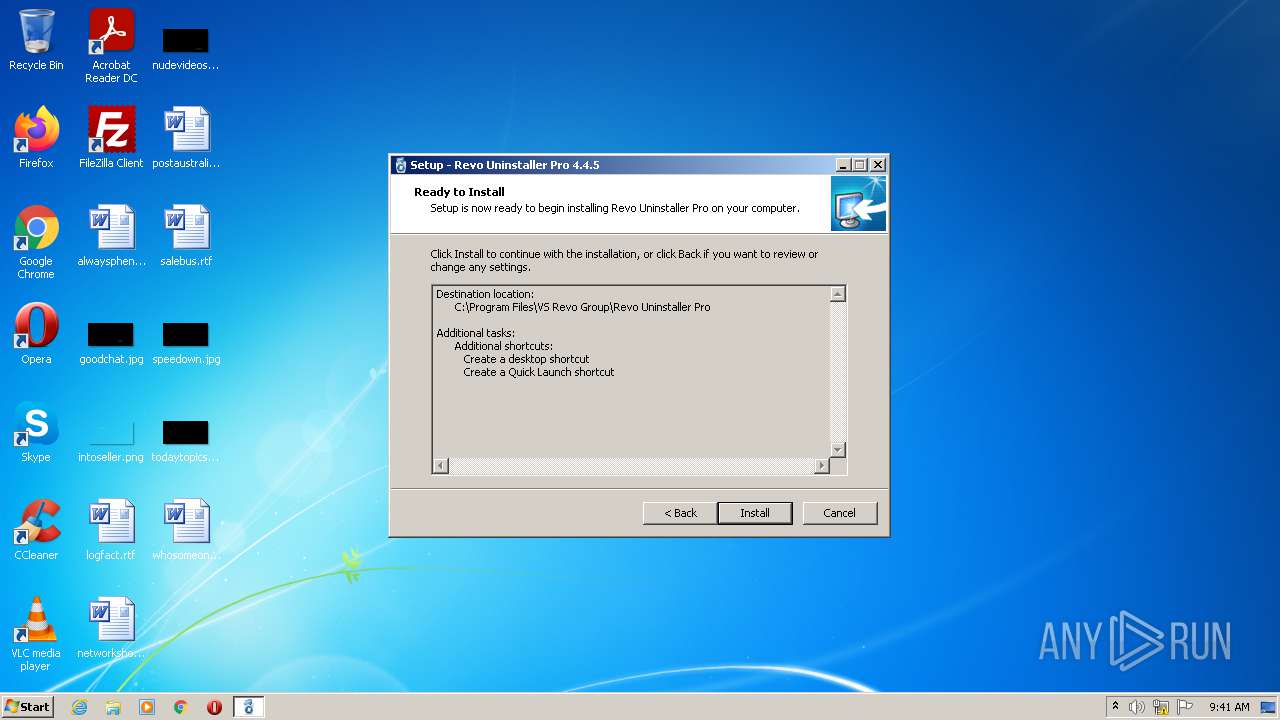
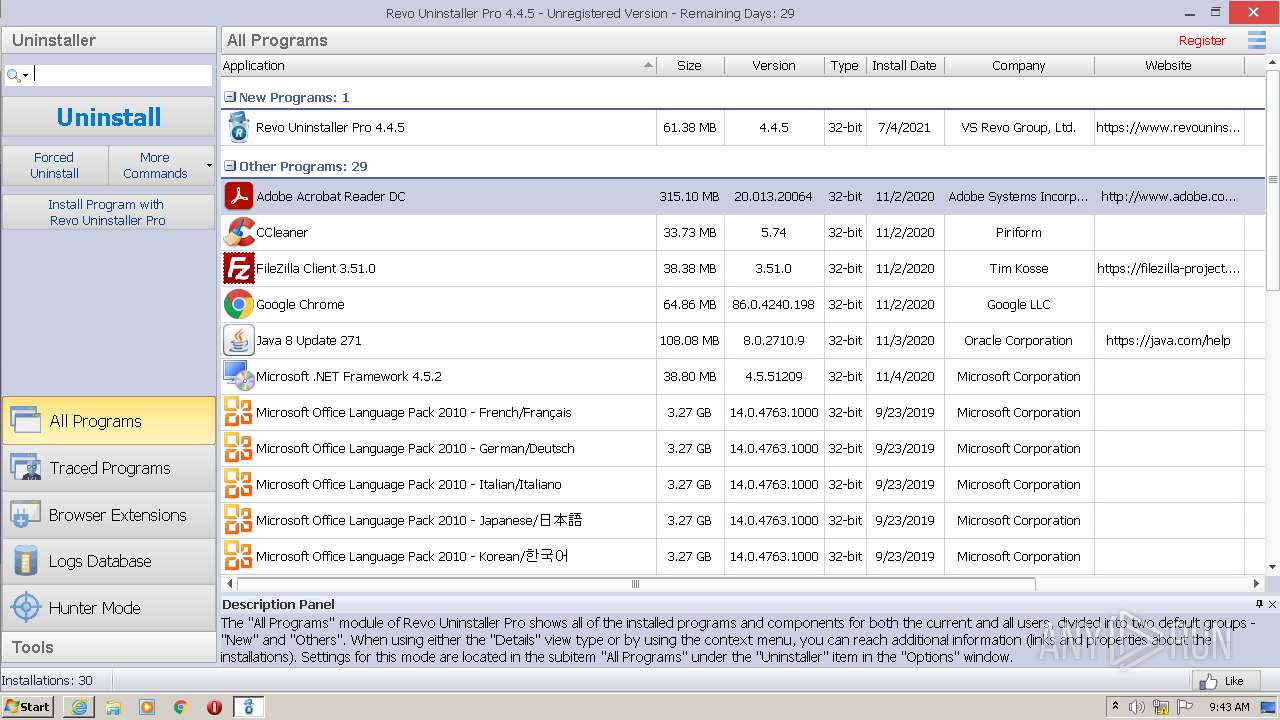
| ProductVersion: | 4.4.5 |
|---|---|
| ProductName: | Revo Uninstaller Pro |
| LegalCopyright: | VS Revo Group, Ltd. |
| FileVersion: | 4.4.5.0 |
| FileDescription: | Revo Uninstaller Pro |
| CompanyName: | VS Revo Group |
| Comments: | This installation was built with Inno Setup. |
| CharacterSet: | Unicode |
| LanguageCode: | Neutral |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 4.4.5.0 |
| FileVersionNumber: | 4.4.5.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 5 |
| ImageVersion: | 6 |
| OSVersion: | 5 |
| EntryPoint: | 0x1181c |
| UninitializedDataSize: | - |
| InitializedDataSize: | 121344 |
| CodeSize: | 66560 |
| LinkerVersion: | 2.25 |
| PEType: | PE32 |
| TimeStamp: | 2018:06:14 15:27:46+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 14-Jun-2018 13:27:46 |
| Detected languages: |
|
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | VS Revo Group |
| FileDescription: | Revo Uninstaller Pro |
| FileVersion: | 4.4.5.0 |
| LegalCopyright: | VS Revo Group, Ltd. |
| ProductName: | Revo Uninstaller Pro |
| ProductVersion: | 4.4.5 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 14-Jun-2018 13:27:46 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000F25C | 0x0000F400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.37588 |
.itext | 0x00011000 | 0x00000FA4 | 0x00001000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.77877 |
.data | 0x00012000 | 0x00000C8C | 0x00000E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.30283 |
.bss | 0x00013000 | 0x000056BC | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x00019000 | 0x00000E04 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.59781 |
.tls | 0x0001A000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x0001B000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.204488 |
.rsrc | 0x0001C000 | 0x0001B894 | 0x0001BA00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.13876 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.13965 | 1580 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 4.41967 | 16936 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 4.75966 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 4.62521 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 5.10263 | 2440 | Latin 1 / Western European | English - United States | RT_ICON |
6 | 4.83132 | 1128 | Latin 1 / Western European | English - United States | RT_ICON |
4091 | 2.56031 | 104 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4092 | 3.25287 | 212 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4093 | 3.26919 | 164 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4094 | 3.33268 | 684 | Latin 1 / Western European | UNKNOWN | RT_STRING |
Imports
advapi32.dll |
comctl32.dll |
kernel32.dll |
oleaut32.dll |
user32.dll |
Total processes
58
Monitored processes
17
Malicious processes
6
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 360 | "rundll32.exe " SETUPAPI.DLL,InstallHinfSection DefaultInstall 132 C:\Program Files\VS Revo Group\Revo Uninstaller Pro\revoflt.inf | C:\Windows\system32\rundll32.exe | RevoUninProSetup (2).tmp | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1248 | "C:\Program Files\VS Revo Group\Revo Uninstaller Pro\RevoUninPro.exe" /bc | C:\Program Files\VS Revo Group\Revo Uninstaller Pro\RevoUninPro.exe | — | RevoUninProSetup (2).tmp | |||||||||||
User: admin Company: VS Revo Group Integrity Level: HIGH Description: Revo Uninstaller Pro Exit code: 0 Version: 4.4.5.0 Modules
| |||||||||||||||
| 1348 | C:\Windows\system32\DllHost.exe /Processid:{F32D97DF-E3E5-4CB9-9E3E-0EB5B4E49801} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1548 | "C:\Windows\system32\regsvr32.exe" /s "C:\Program Files\VS Revo Group\Revo Uninstaller Pro\RUExt.dll" | C:\Windows\system32\regsvr32.exe | — | RevoUninProSetup (2).tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2064 | "C:\Windows\system32\runonce.exe" -r | C:\Windows\system32\runonce.exe | — | rundll32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Run Once Wrapper Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
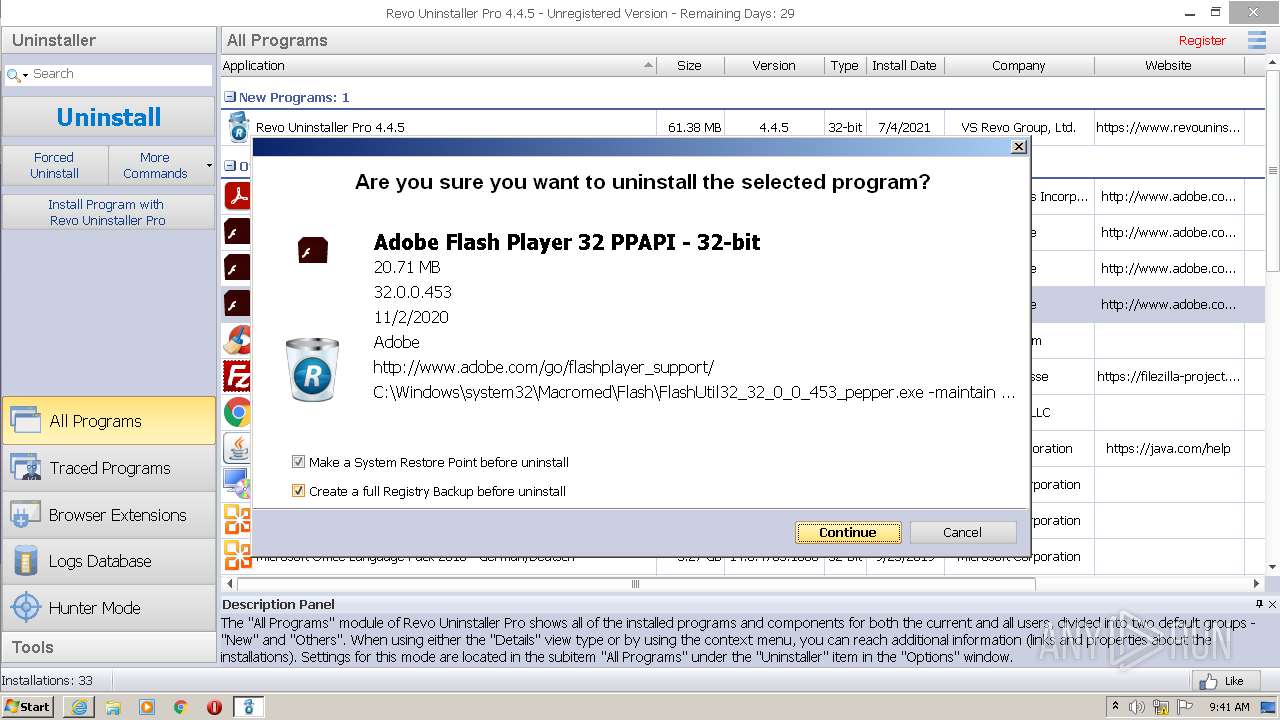
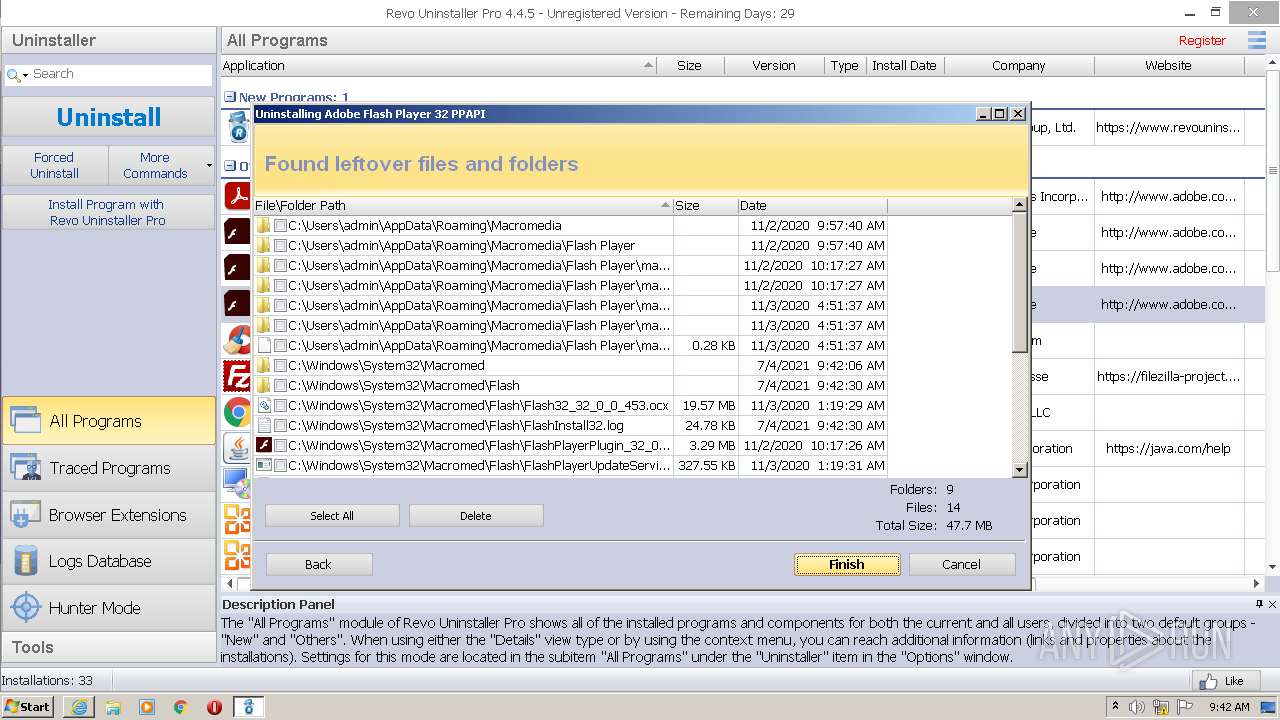
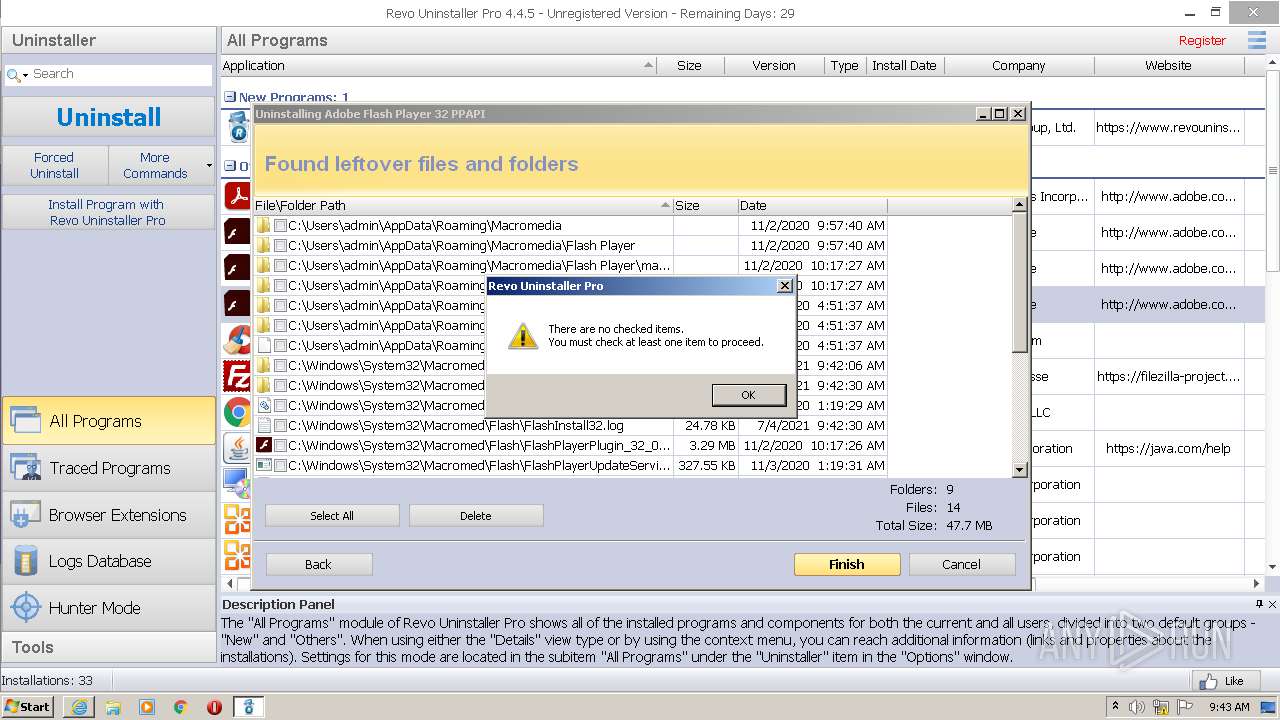
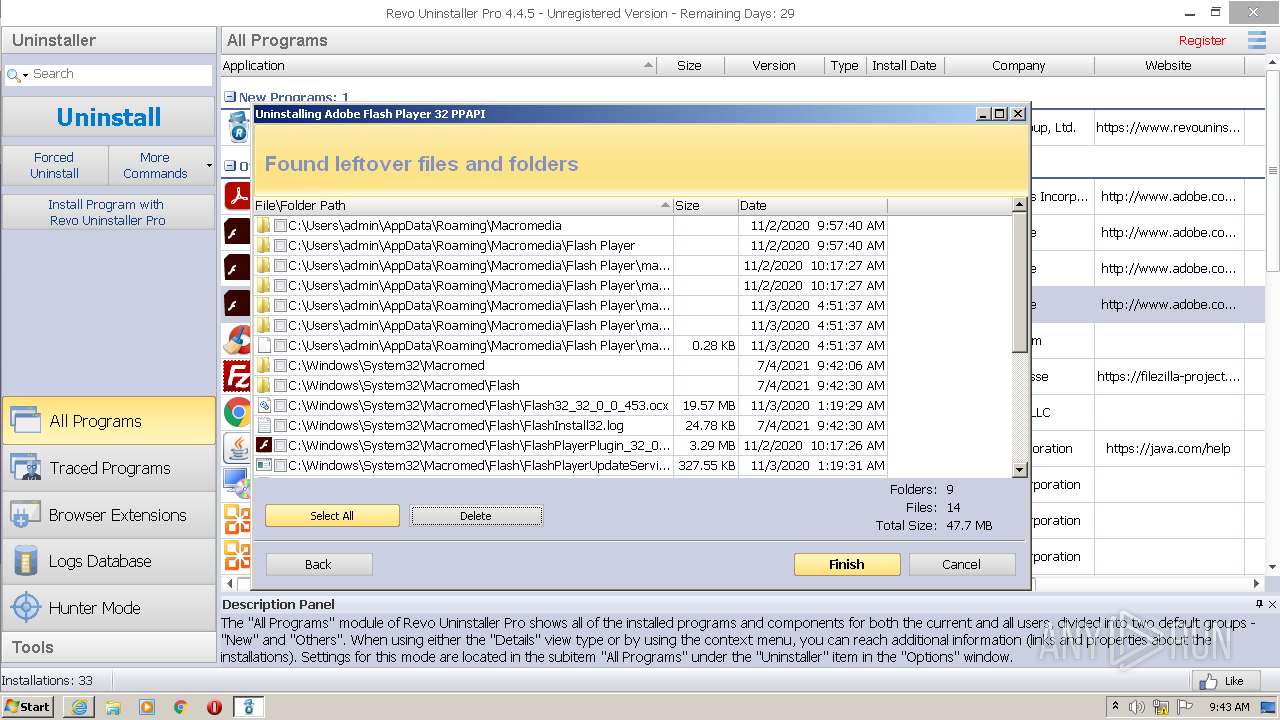
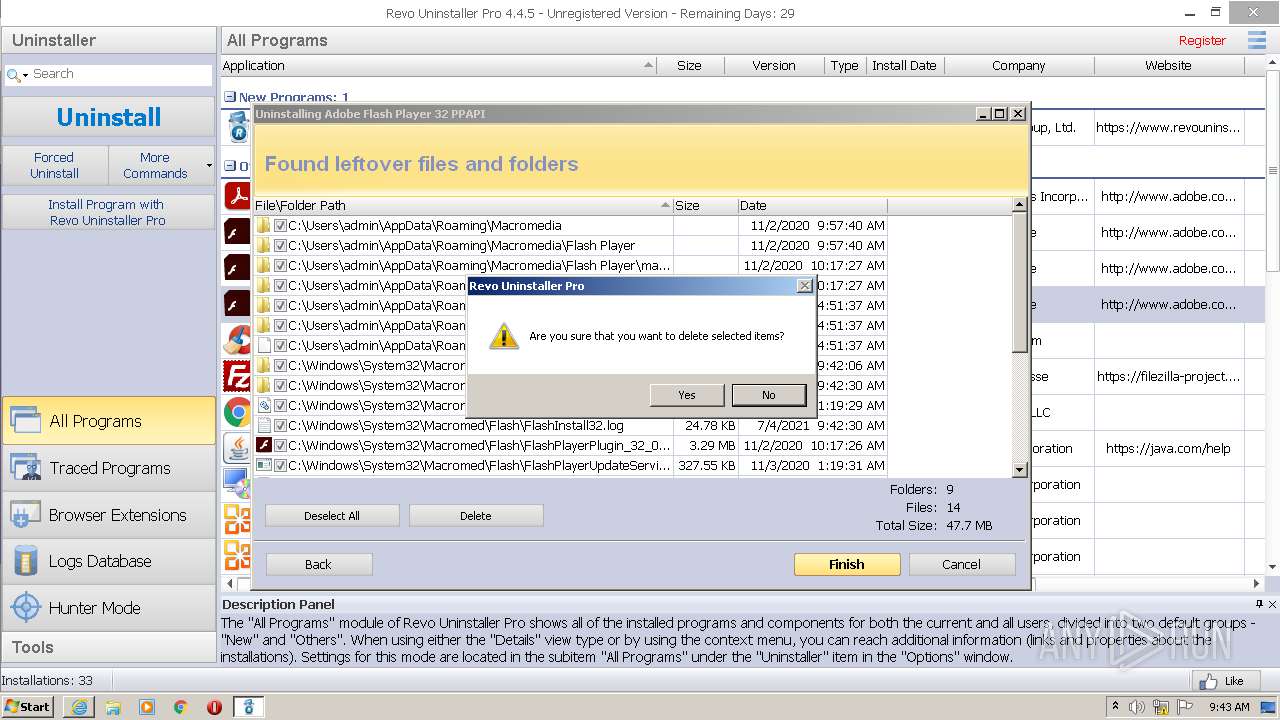
| 2124 | C:\Windows\system32\Macromed\Flash\FlashUtil32_32_0_0_453_pepper.exe -maintain pepperplugin | C:\Windows\system32\Macromed\Flash\FlashUtil32_32_0_0_453_pepper.exe | RevoUninPro.exe | ||||||||||||
User: admin Company: Adobe Integrity Level: HIGH Description: Adobe� Flash� Player Installer/Uninstaller 32.0 r0 Exit code: 0 Version: 32,0,0,453 Modules
| |||||||||||||||
| 2260 | "C:\Users\admin\AppData\Local\Temp\is-RCDUT.tmp\RevoUninProSetup (2).tmp" /SL5="$2013E,15950528,188928,C:\Users\admin\AppData\Local\Temp\RevoUninProSetup (2).exe" /SPAWNWND=$1013C /NOTIFYWND=$20138 | C:\Users\admin\AppData\Local\Temp\is-RCDUT.tmp\RevoUninProSetup (2).tmp | RevoUninProSetup (2).exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 2928 | "C:\Program Files\VS Revo Group\Revo Uninstaller Pro\RevoUninPro.exe" | C:\Program Files\VS Revo Group\Revo Uninstaller Pro\RevoUninPro.exe | RevoUninProSetup (2).tmp | ||||||||||||
User: admin Company: VS Revo Group Integrity Level: HIGH Description: Revo Uninstaller Pro Exit code: 0 Version: 4.4.5.0 Modules
| |||||||||||||||
| 2936 | "C:\Users\admin\AppData\Local\Temp\RevoUninProSetup (2).exe" | C:\Users\admin\AppData\Local\Temp\RevoUninProSetup (2).exe | Explorer.EXE | ||||||||||||
User: admin Company: VS Revo Group Integrity Level: MEDIUM Description: Revo Uninstaller Pro Exit code: 0 Version: 4.4.5.0 Modules
| |||||||||||||||
| 2984 | "C:\Users\admin\AppData\Local\Temp\is-KMCTR.tmp\RevoUninProSetup (2).tmp" /SL5="$20138,15950528,188928,C:\Users\admin\AppData\Local\Temp\RevoUninProSetup (2).exe" | C:\Users\admin\AppData\Local\Temp\is-KMCTR.tmp\RevoUninProSetup (2).tmp | — | RevoUninProSetup (2).exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
Total events
33 343
Read events
32 699
Write events
634
Delete events
10
Modification events
| (PID) Process: | (2260) RevoUninProSetup (2).tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{FB562550-BBE6-4298-861A-5C0A6562C272} |
| Operation: | write | Name: | (default) |
Value: Revo Uninstaller Pro | |||
| (PID) Process: | (2260) RevoUninProSetup (2).tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{FB562550-BBE6-4298-861A-5C0A6562C272} |
| Operation: | write | Name: | InfoTip |
Value: Uninstall, Remove Programs, Clear Web Browsers Tracks, Control Automatically Started Applications | |||
| (PID) Process: | (2260) RevoUninProSetup (2).tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{FB562550-BBE6-4298-861A-5C0A6562C272} |
| Operation: | write | Name: | {305CA226-D286-468e-B848-2B2E8E697B74} 2 |
Value: 8 | |||
| (PID) Process: | (2260) RevoUninProSetup (2).tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{FB562550-BBE6-4298-861A-5C0A6562C272}\DefaultIcon |
| Operation: | write | Name: | (default) |
Value: C:\Program Files\VS Revo Group\Revo Uninstaller Pro\RevoUninPro.exe,0 | |||
| (PID) Process: | (2260) RevoUninProSetup (2).tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{FB562550-BBE6-4298-861A-5C0A6562C272}\Shell\Open\command |
| Operation: | write | Name: | (default) |
Value: C:\Program Files\VS Revo Group\Revo Uninstaller Pro\RevoUninPro.exe | |||
| (PID) Process: | (2260) RevoUninProSetup (2).tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{FB562550-BBE6-4298-861A-5C0A6562C272}\ShellFolder |
| Operation: | write | Name: | Attributes |
Value: 48 | |||
| (PID) Process: | (2260) RevoUninProSetup (2).tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\ControlPanel\NameSpace\{FB562550-BBE6-4298-861A-5C0A6562C272} |
| Operation: | write | Name: | (default) |
Value: Revo Uninstaller Pro | |||
| (PID) Process: | (2260) RevoUninProSetup (2).tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\App Paths\RevoUninPro.exe |
| Operation: | write | Name: | (default) |
Value: C:\Program Files\VS Revo Group\Revo Uninstaller Pro\RevoUninPro.exe | |||
| (PID) Process: | (2260) RevoUninProSetup (2).tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\.ruel |
| Operation: | write | Name: | (default) |
Value: RevoUninstallerPro.ruel | |||
| (PID) Process: | (2260) RevoUninProSetup (2).tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\RevoUninstallerPro.ruel\DefaultIcon |
| Operation: | write | Name: | (default) |
Value: C:\Program Files\VS Revo Group\Revo Uninstaller Pro\RevoUninPro.exe,0 | |||
Executable files
18
Suspicious files
38
Text files
154
Unknown types
50
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2260 | RevoUninProSetup (2).tmp | C:\Program Files\VS Revo Group\Revo Uninstaller Pro\lang\armenian.ini | text | |
MD5:22C302D515747DF778989919124FBDA2 | SHA256:A74A42D62FD6E52E082E318548597E4F05F448C80BA49B91B5166C80F75B6D49 | |||
| 4068 | RevoUninProSetup (2).exe | C:\Users\admin\AppData\Local\Temp\is-RCDUT.tmp\RevoUninProSetup (2).tmp | executable | |
MD5:D0BF64E27284709966A4E2EFEF3233EF | SHA256:2019350B1451F4653D27C33B1C034155CE81534F318CD2E3591DD2EE73C77F09 | |||
| 2260 | RevoUninProSetup (2).tmp | C:\Program Files\VS Revo Group\Revo Uninstaller Pro\lang\is-SB799.tmp | text | |
MD5:22C302D515747DF778989919124FBDA2 | SHA256:A74A42D62FD6E52E082E318548597E4F05F448C80BA49B91B5166C80F75B6D49 | |||
| 2260 | RevoUninProSetup (2).tmp | C:\Program Files\VS Revo Group\Revo Uninstaller Pro\lang\albanian.ini | text | |
MD5:7D61A847C3B5EE3A9A9410669D2297CC | SHA256:73FF519307077241A90D45F65260639EB6DF590990139A8D1312170F781B4CAA | |||
| 2260 | RevoUninProSetup (2).tmp | C:\Program Files\VS Revo Group\Revo Uninstaller Pro\lang\is-TQHQI.tmp | text | |
MD5:F16B36E63303619EE98621BBF623968B | SHA256:68E4ECDD6CFD97DCADF55CF90531BD8A09142DB8CF8E62DFE20DD133759B9127 | |||
| 2260 | RevoUninProSetup (2).tmp | C:\Program Files\VS Revo Group\Revo Uninstaller Pro\lang\is-80036.tmp | text | |
MD5:BDD599204771F0B07232DDF28413B408 | SHA256:B93B48B4296A701CA43D6F32370C5885BF08FA8446BDDD5C8DB6252CA9E3C79D | |||
| 2260 | RevoUninProSetup (2).tmp | C:\Program Files\VS Revo Group\Revo Uninstaller Pro\lang\is-DCVD2.tmp | text | |
MD5:5D7940A52B9653AB25C4FD2F15D0CC7C | SHA256:2D773FBC4D2C194A260964E76D2ECF28C89C29C6BD30632BF774F7DDBEB57FEC | |||
| 2260 | RevoUninProSetup (2).tmp | C:\Program Files\VS Revo Group\Revo Uninstaller Pro\lang\arabic.ini | text | |
MD5:F16B36E63303619EE98621BBF623968B | SHA256:68E4ECDD6CFD97DCADF55CF90531BD8A09142DB8CF8E62DFE20DD133759B9127 | |||
| 2260 | RevoUninProSetup (2).tmp | C:\Program Files\VS Revo Group\Revo Uninstaller Pro\lang\bengali.ini | text | |
MD5:BDD599204771F0B07232DDF28413B408 | SHA256:B93B48B4296A701CA43D6F32370C5885BF08FA8446BDDD5C8DB6252CA9E3C79D | |||
| 2260 | RevoUninProSetup (2).tmp | C:\Program Files\VS Revo Group\Revo Uninstaller Pro\lang\bulgarian.ini | text | |
MD5:F93C2D2FFC30165B83201E19E1721655 | SHA256:CE3FBCA0C918C911EC62D7F724638D92A5CEFE440B669901E18B74DA81404593 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
73
TCP/UDP connections
214
DNS requests
84
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3496 | iexplore.exe | GET | — | 13.32.23.215:80 | http://o.ss2.us//MEowSDBGMEQwQjAJBgUrDgMCGgUABBSLwZ6EW5gdYc9UaSEaaLjjETNtkAQUv1%2B30c7dH4b0W1Ws3NcQwg6piOcCCQCnDkpMNIK3fw%3D%3D | US | — | — | whitelisted |
3496 | iexplore.exe | GET | — | 142.250.186.163:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQDri3X7Vj%2BUVwoAAAAA4FIL | US | — | — | whitelisted |
3496 | iexplore.exe | GET | 200 | 142.250.186.163:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | US | der | 1.41 Kb | whitelisted |
3496 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRJ9L2KGL92BpjF3kAtaDtxauTmhgQUPdNQpdagre7zSmAKZdMh1Pj41g8CEALos1hjj%2BuM4esEEgtyqA8%3D | US | der | 471 b | whitelisted |
3496 | iexplore.exe | GET | 200 | 104.18.20.226:80 | http://ocsp.globalsign.com/ca/gsatlasr3dvtlsca2020/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQT6XbZiiF%2BR%2FUEno7LSD4H4YmN6gQUQm1XLU8fJnd0pidk9oD6j0ho%2FnwCEAF6Y%2F3B9WD5TqnTJ4MIyeE%3D | US | der | 1.42 Kb | whitelisted |
3496 | iexplore.exe | GET | 200 | 142.250.186.163:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
3496 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEBblhnjgcJQ5S9%2FbTvymO98%3D | US | der | 471 b | whitelisted |
3496 | iexplore.exe | GET | 200 | 142.250.186.163:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | US | der | 724 b | whitelisted |
3496 | iexplore.exe | GET | 200 | 142.250.186.163:80 | http://ocsp.pki.goog/gts1o1core/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEEv1fo69oyETBQAAAACH6kw%3D | US | der | 471 b | whitelisted |
3496 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 1.47 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3496 | iexplore.exe | 142.250.186.163:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
3496 | iexplore.exe | 104.18.21.226:80 | ocsp2.globalsign.com | Cloudflare Inc | US | shared |
3496 | iexplore.exe | 2.16.186.25:80 | ctldl.windowsupdate.com | Akamai International B.V. | — | whitelisted |
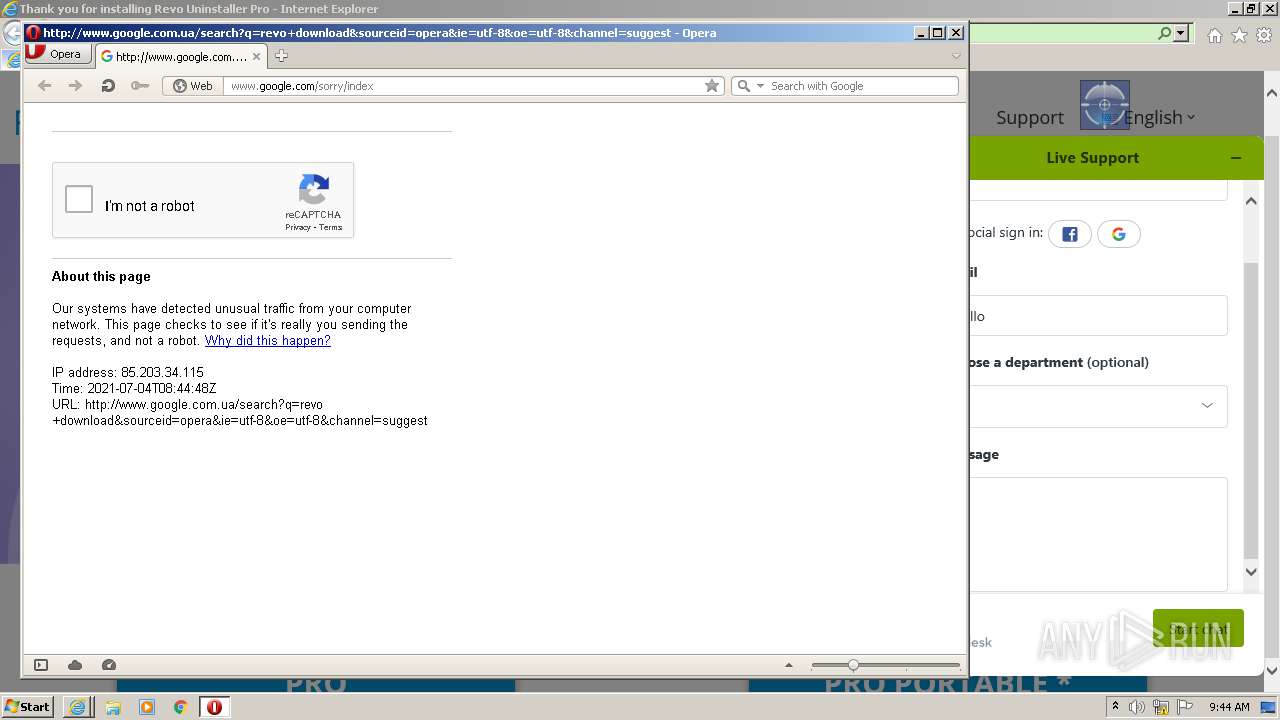
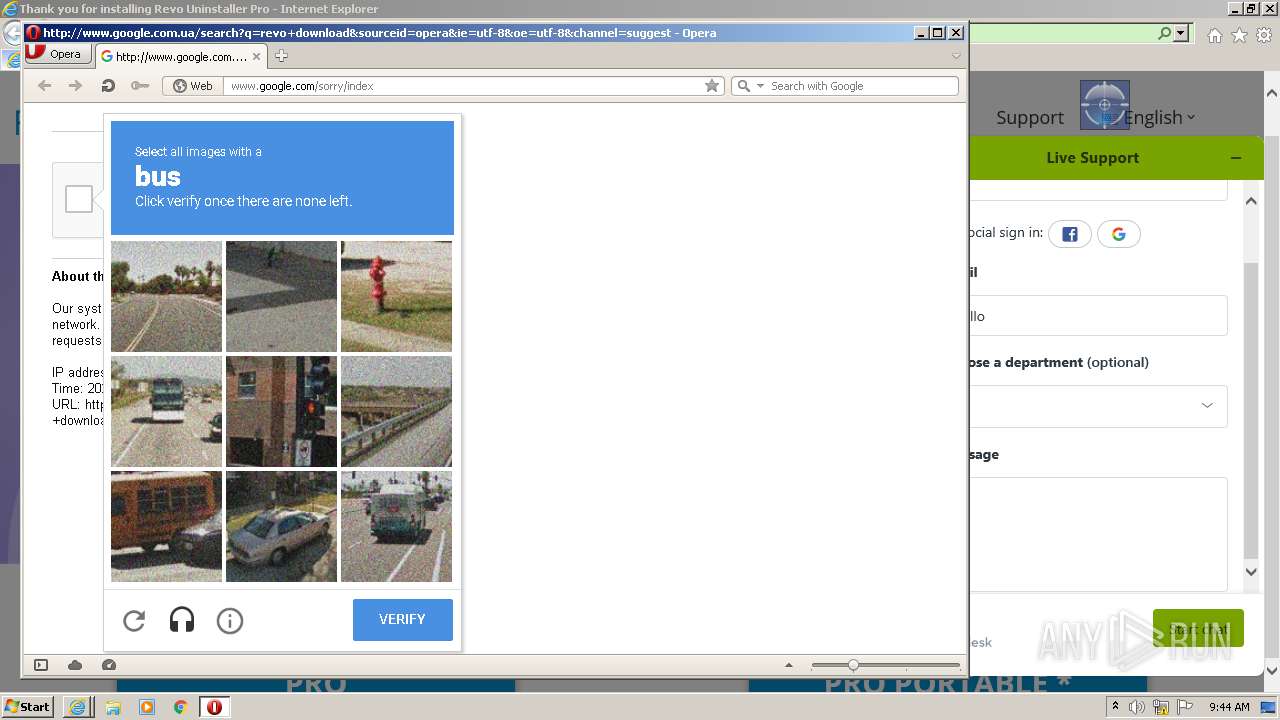
3496 | iexplore.exe | 146.20.152.114:443 | www.revouninstaller.com | Rackspace Ltd. | US | suspicious |
3496 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3496 | iexplore.exe | 142.250.74.202:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3496 | iexplore.exe | 104.18.11.207:443 | stackpath.bootstrapcdn.com | Cloudflare Inc | US | suspicious |
3496 | iexplore.exe | 104.18.70.113:443 | static.zdassets.com | Cloudflare Inc | US | shared |
3496 | iexplore.exe | 2.18.233.88:443 | f057a20f961f56a72089-b74530d2d26278124f446233f95622ef.ssl.cf1.rackcdn.com | Akamai International B.V. | — | whitelisted |
3496 | iexplore.exe | 172.217.23.99:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.revouninstaller.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
stackpath.bootstrapcdn.com |
| whitelisted |
static.zdassets.com |
| whitelisted |
ajax.googleapis.com |
| whitelisted |
cdn.jsdelivr.net |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
— | — | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |
— | — | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
— | — | Potentially Bad Traffic | ET INFO TLS Handshake Failure |