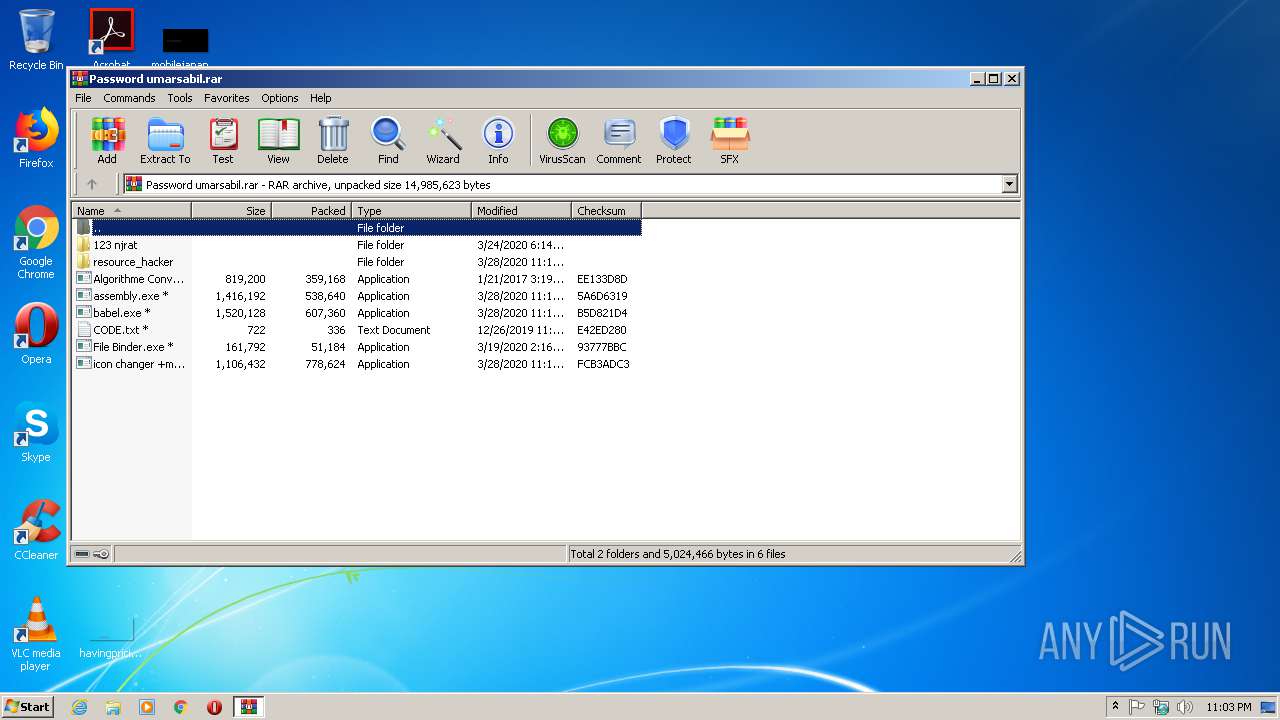
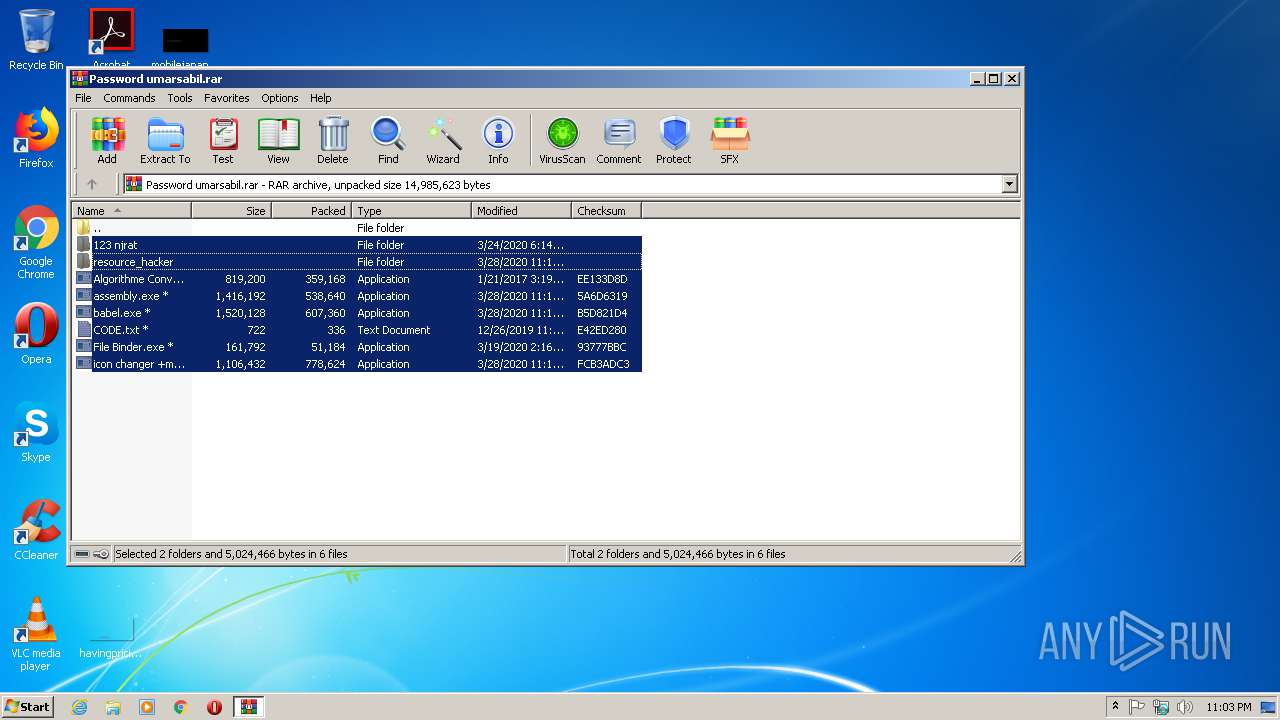
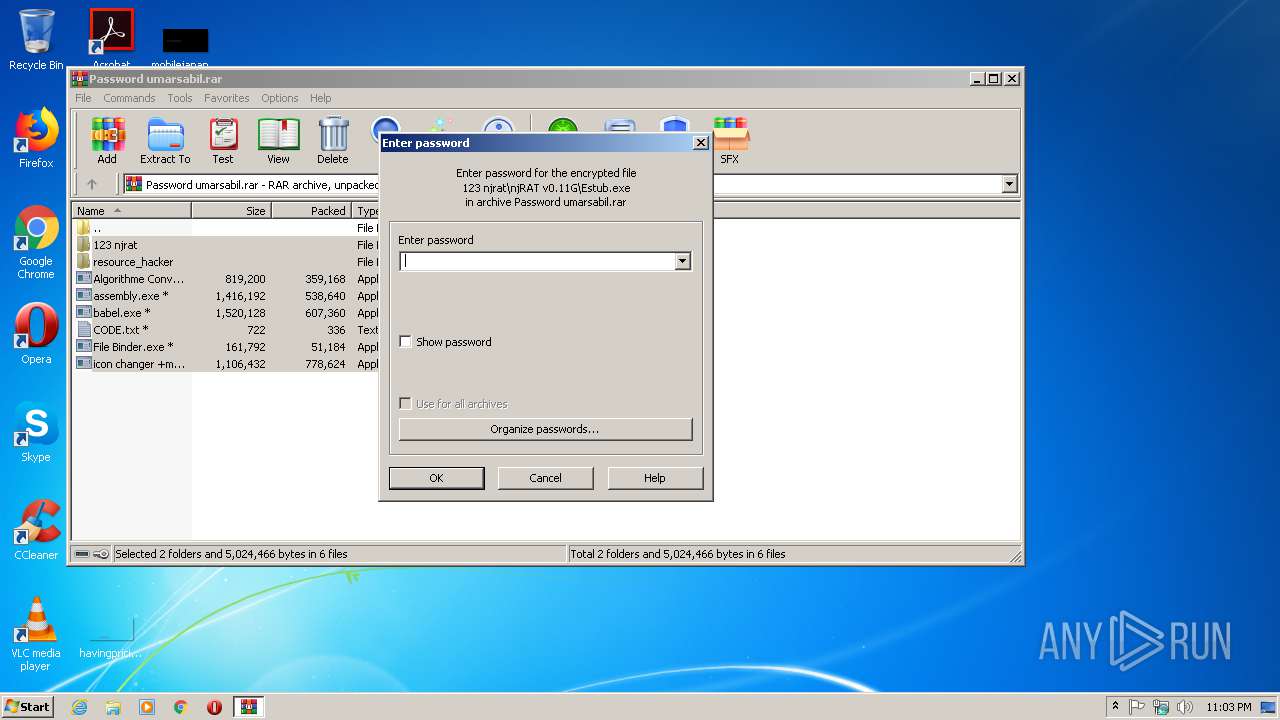
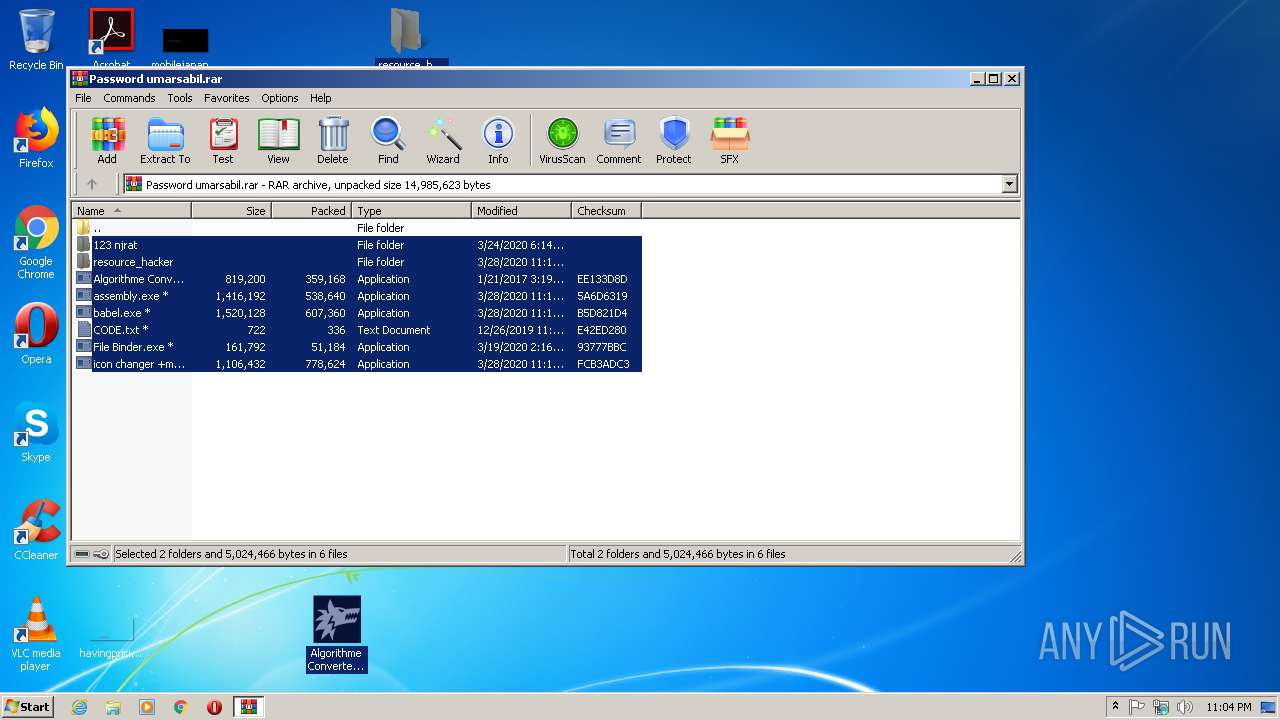
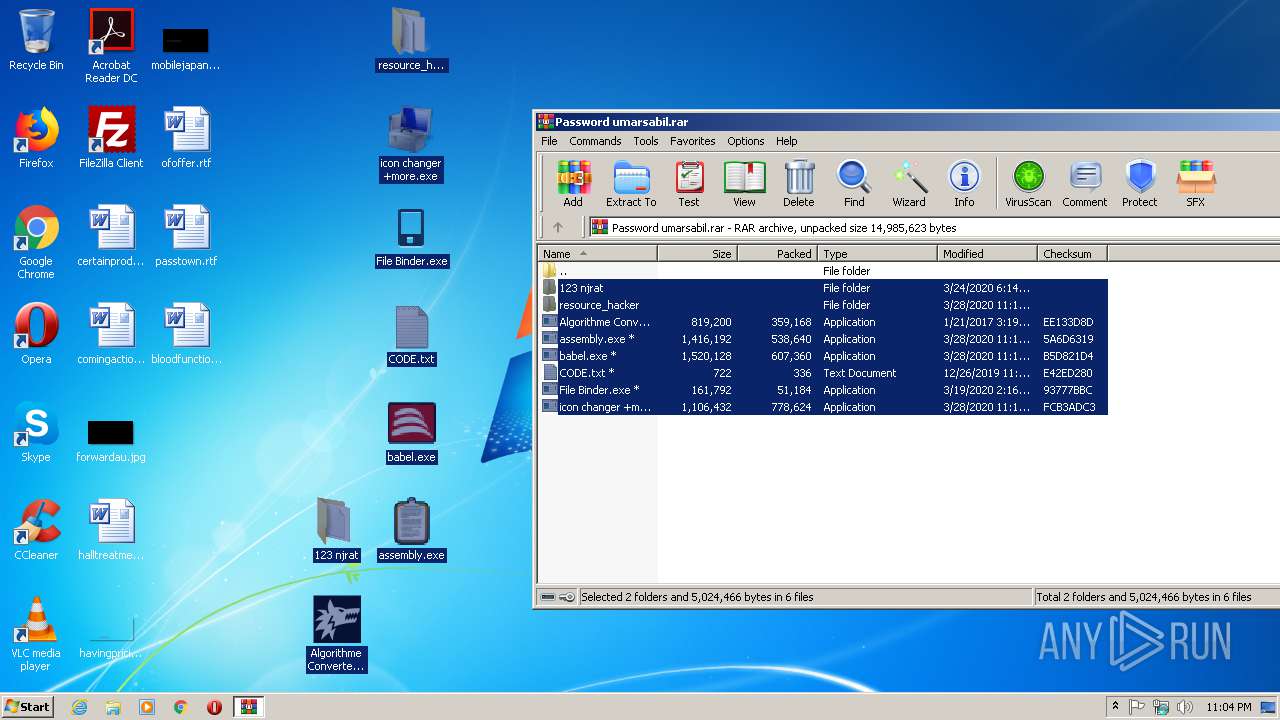
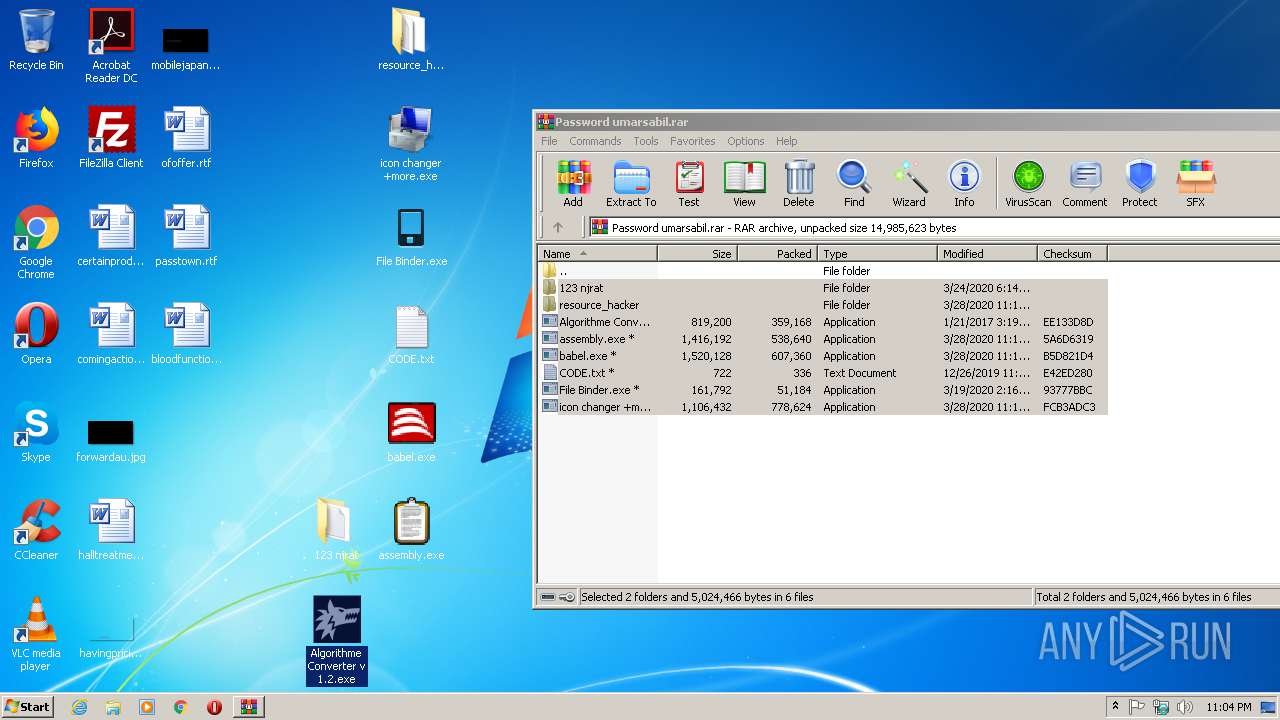
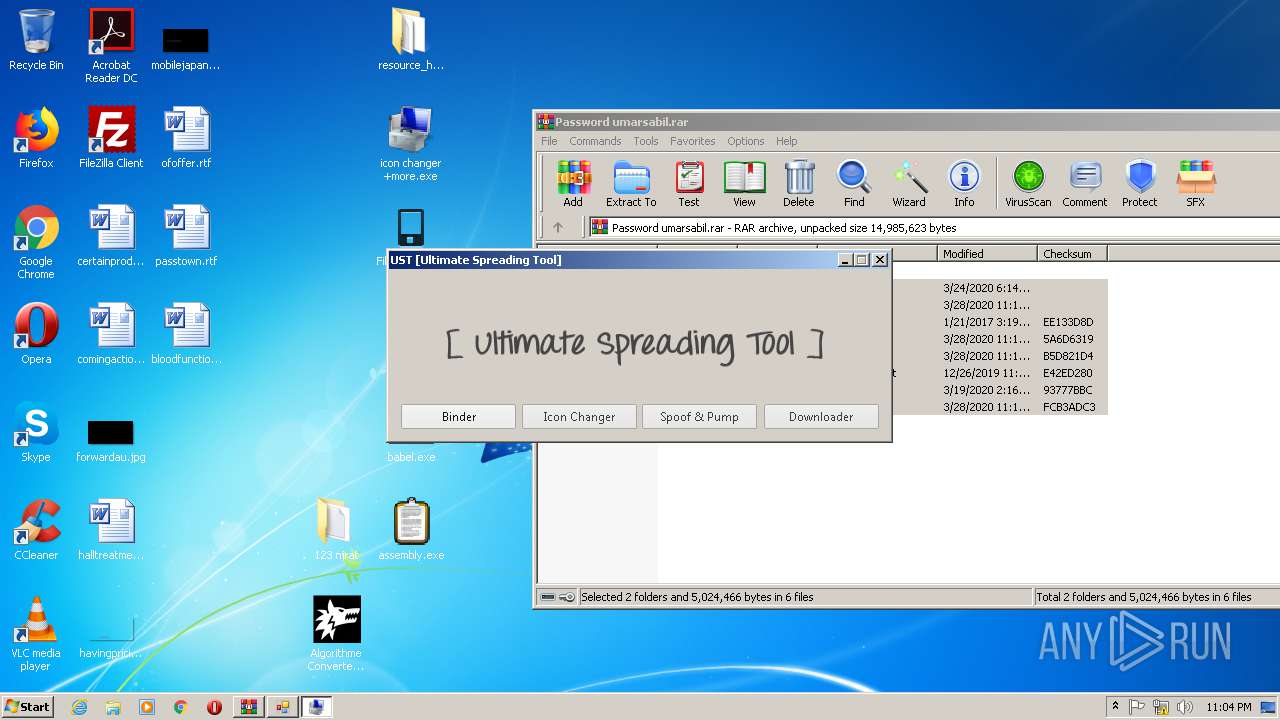
| File name: | Password umarsabil.rar |
| Full analysis: | https://app.any.run/tasks/12b20384-52fe-4fe3-81ad-beb5ac27a475 |
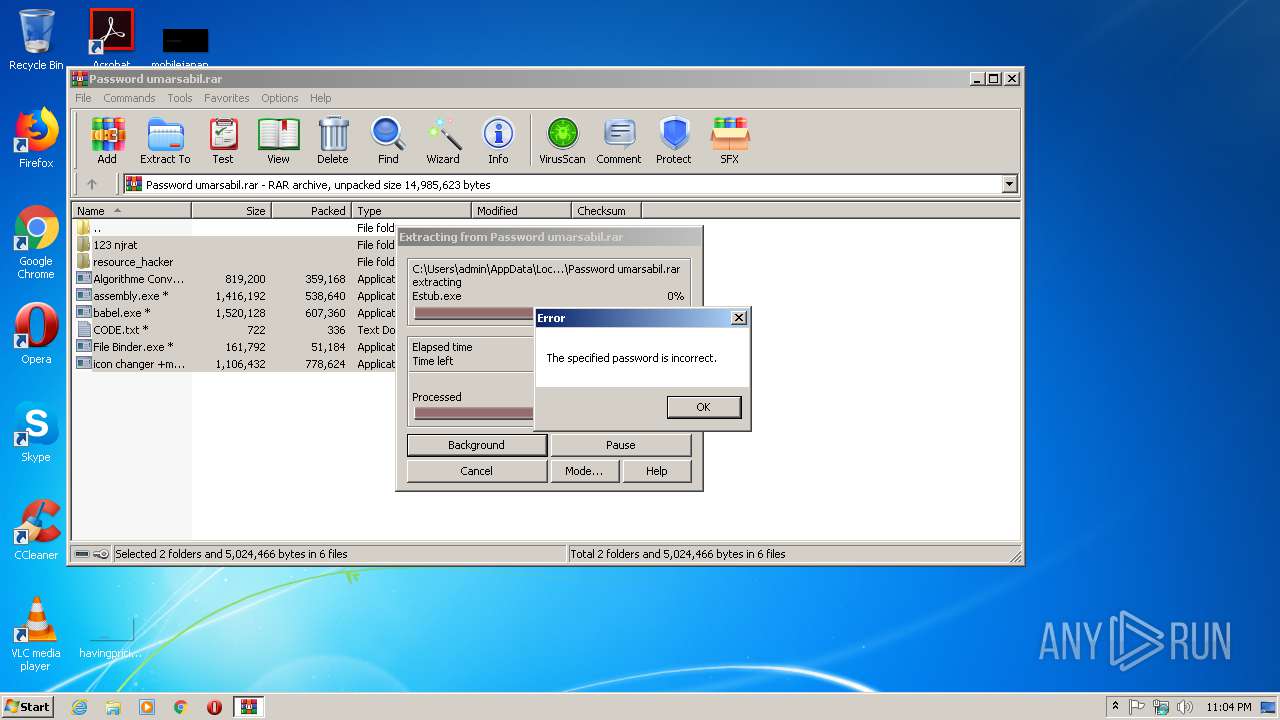
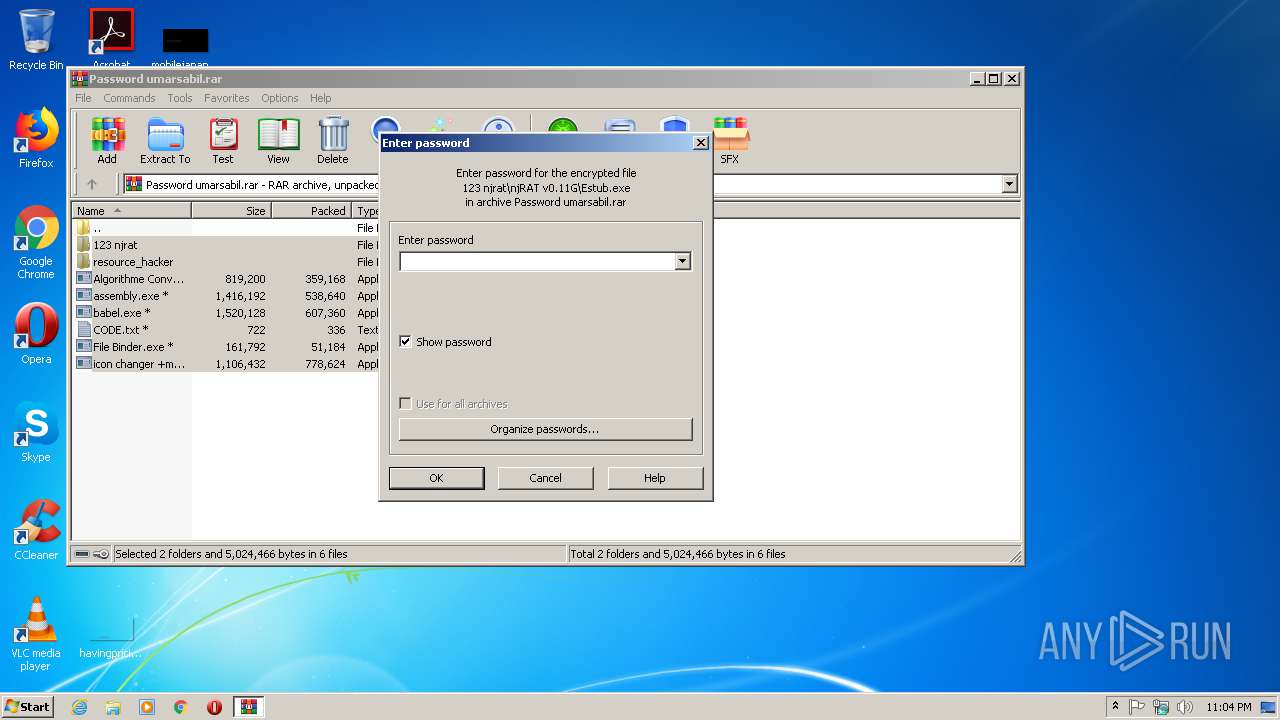
| Verdict: | Malicious activity |
| Analysis date: | May 29, 2020, 22:03:14 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 55EA32062368EFDF5CD4B2340E44746F |
| SHA1: | C3BCFDA1EB82737D09027CC0606C983B3C419DC2 |
| SHA256: | A92B2D2F63D35823F84B786C8B16D487A7C9657E3C91D8CB97310AA61A596C9B |
| SSDEEP: | 196608:ZZpxc0Cg5lLkp0LqgIbmIPlRFBuu3DudPrQ:ZJc026qgIxPjFBuNs |
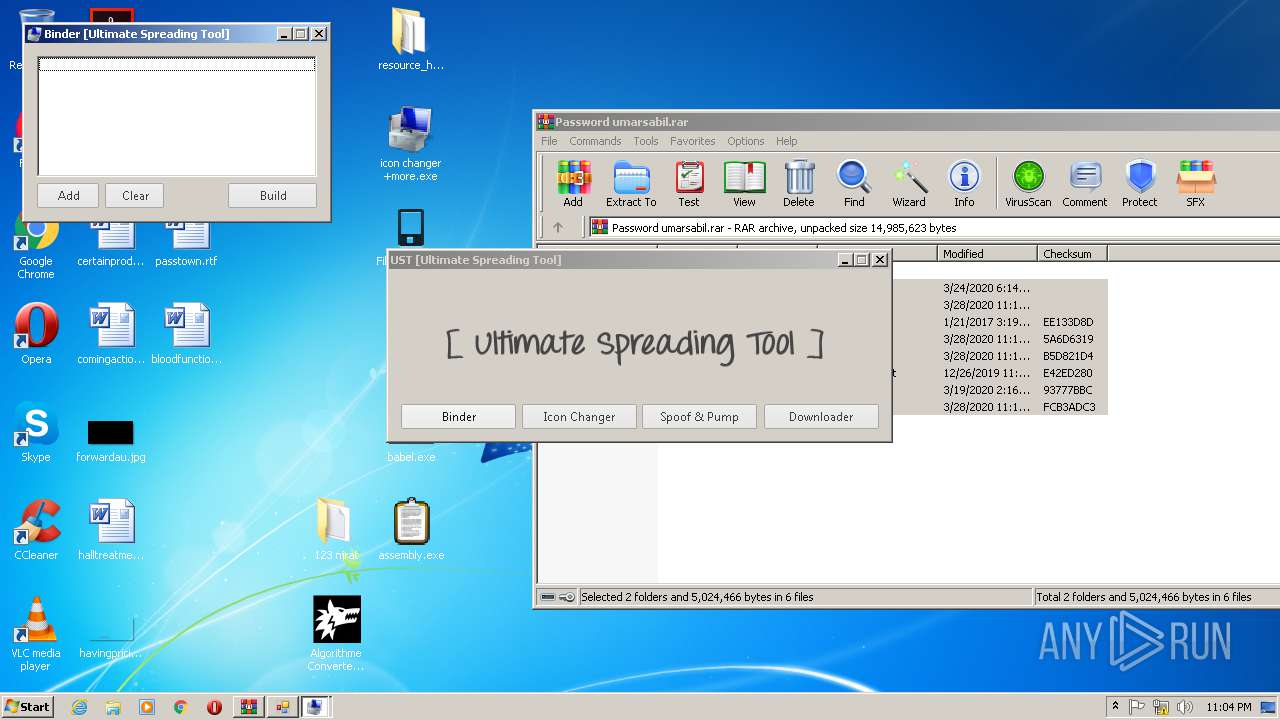
MALICIOUS
Application was dropped or rewritten from another process
- babel.exe (PID: 1272)
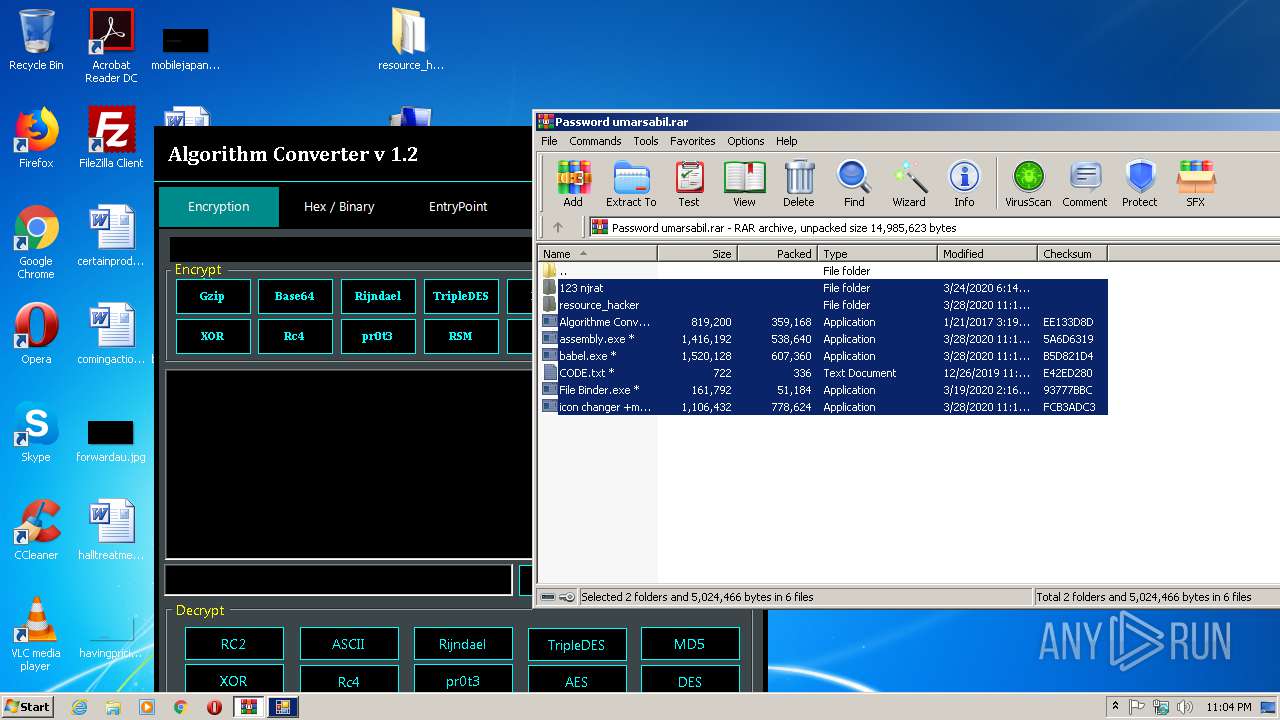
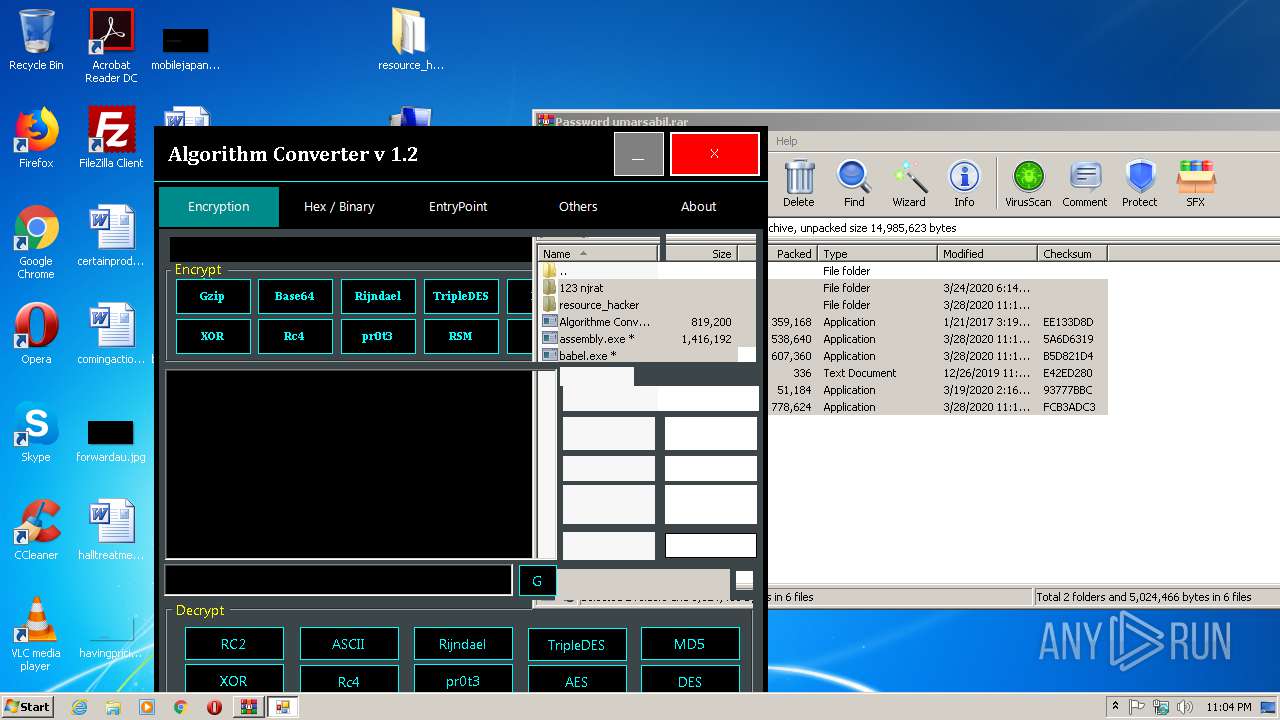
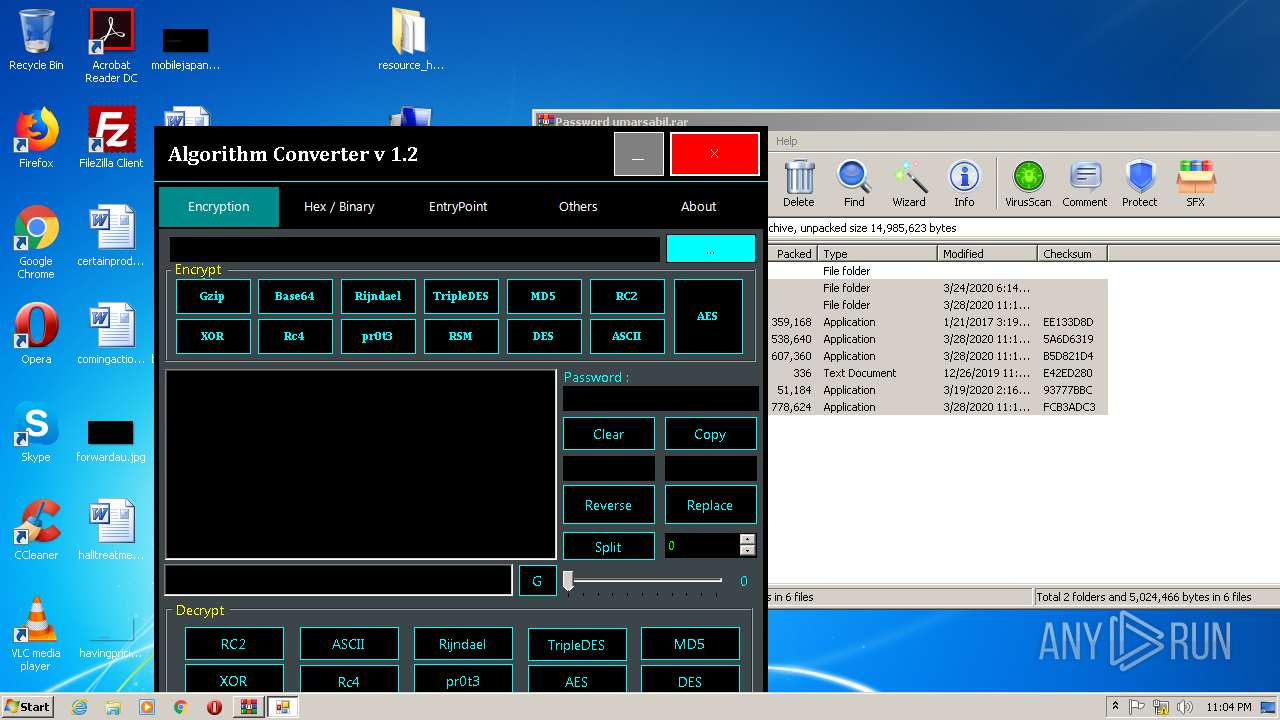
- Algorithme Converter v 1.2.exe (PID: 1532)
- babel.exe (PID: 4024)
- icon changer +more.exe (PID: 624)
- babel.exe (PID: 3652)
- icon changer +more.exe (PID: 4016)
- babel.exe (PID: 1928)
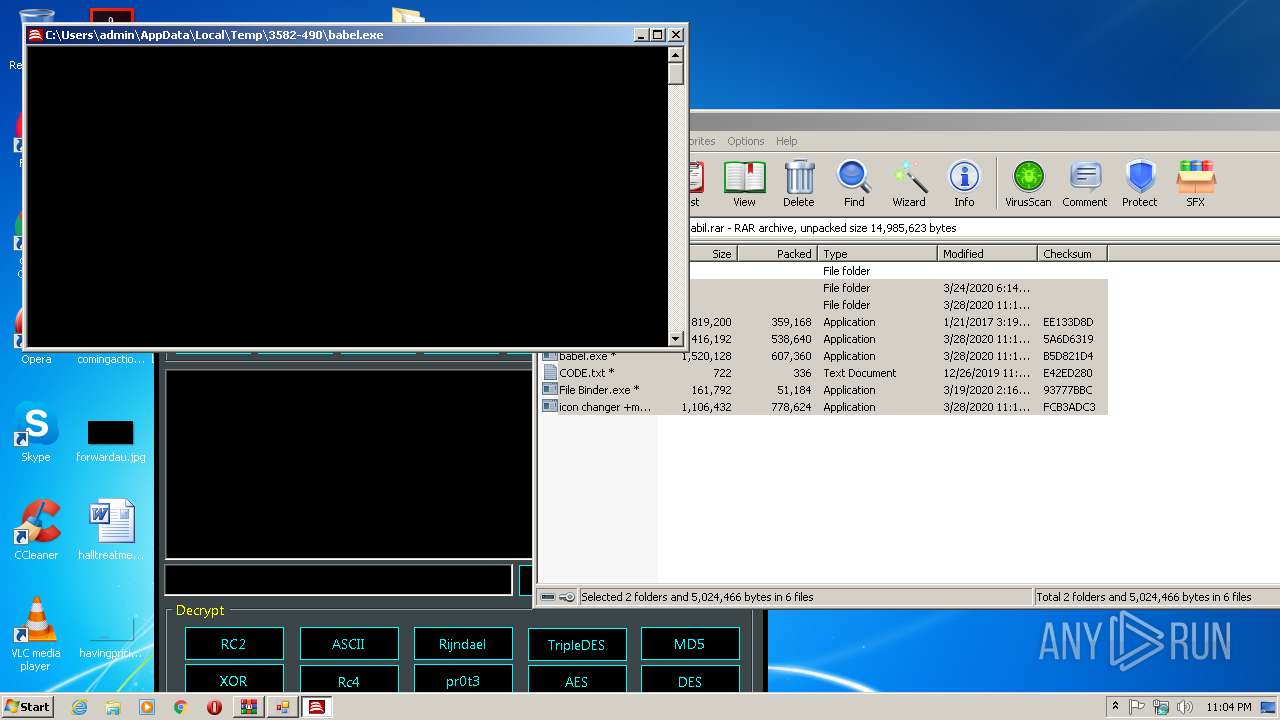
Starts Visual C# compiler
- babel.exe (PID: 4024)
- babel.exe (PID: 1928)
Actions looks like stealing of personal data
- babel.exe (PID: 1272)
SUSPICIOUS
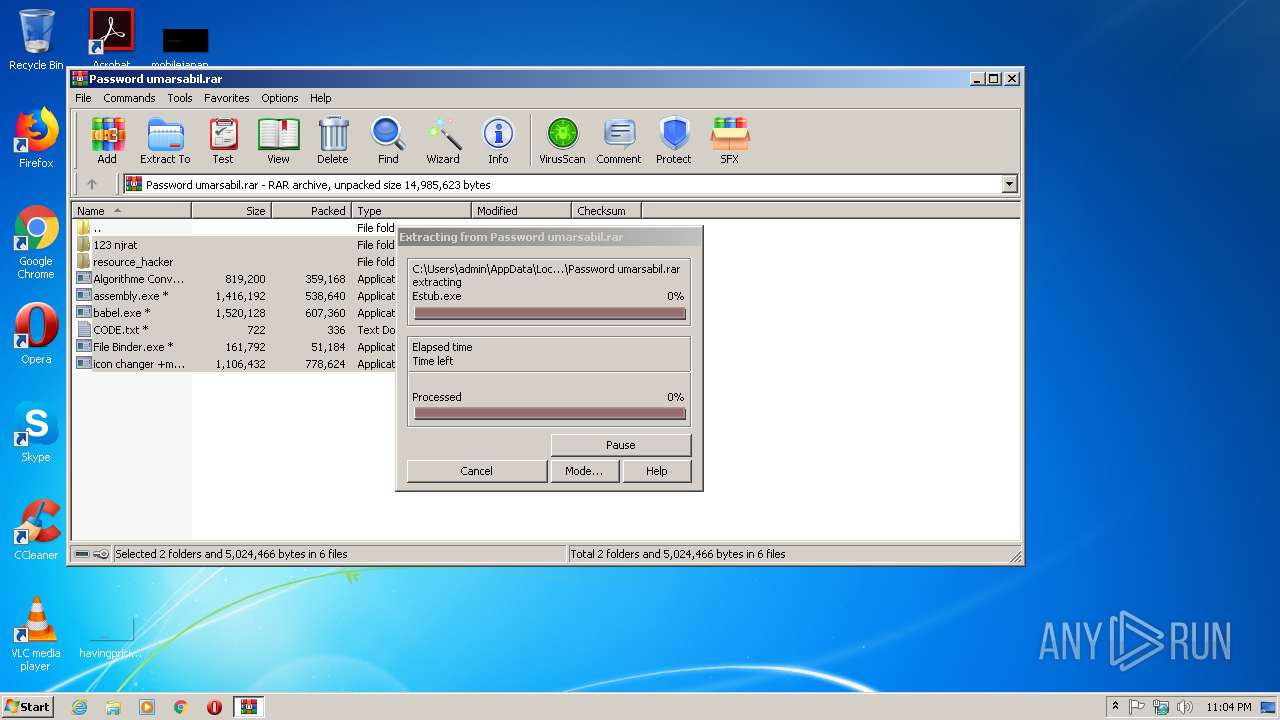
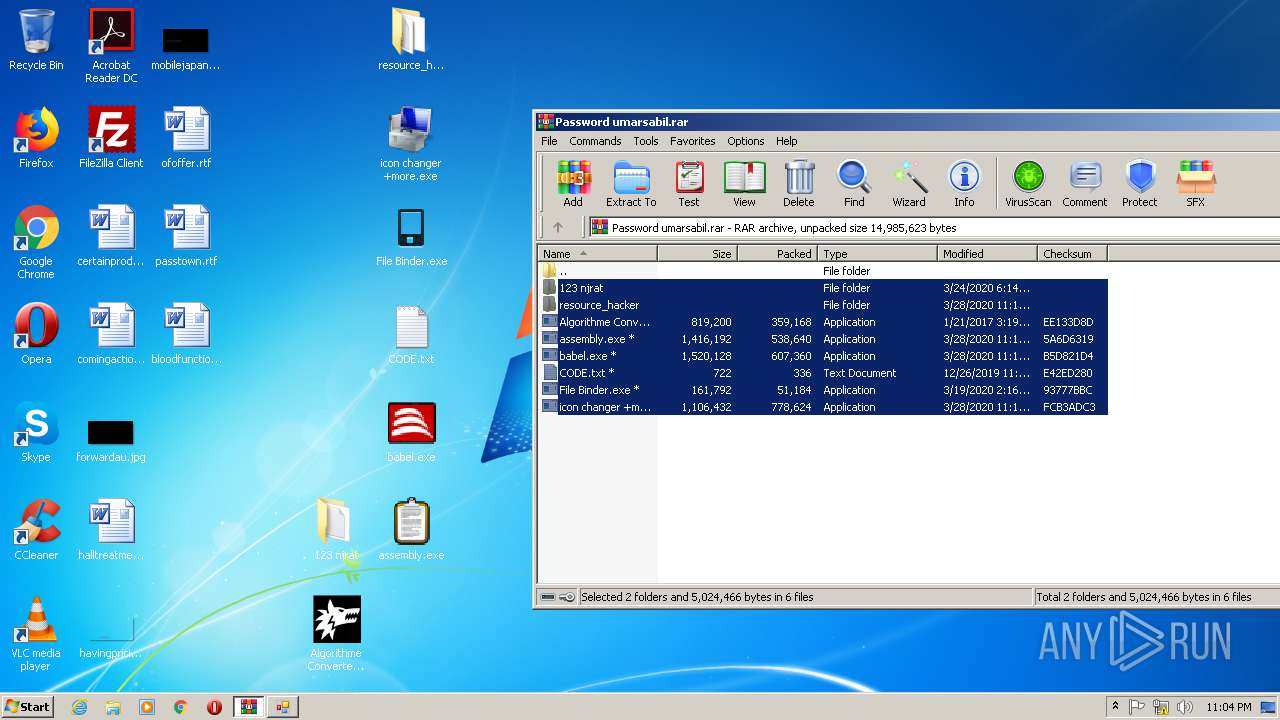
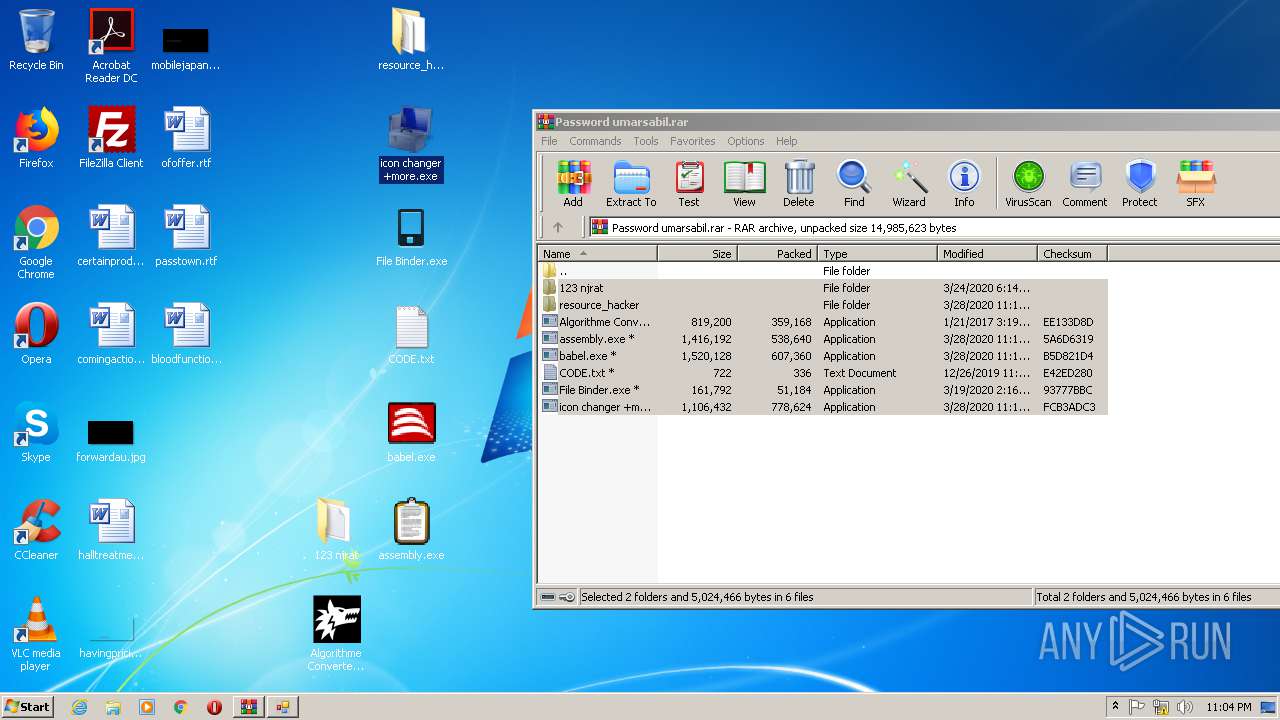
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2296)
- babel.exe (PID: 1272)
- icon changer +more.exe (PID: 624)
- babel.exe (PID: 3652)
Writes to a desktop.ini file (may be used to cloak folders)
- WinRAR.exe (PID: 2296)
INFO
Manual execution by user
- Algorithme Converter v 1.2.exe (PID: 1532)
- babel.exe (PID: 1272)
- icon changer +more.exe (PID: 624)
- babel.exe (PID: 3652)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
48
Monitored processes
12
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 464 | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RES21FA.tmp" "c:\Users\admin\AppData\Local\Temp\CSC21F9.tmp" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 8.00.50727.4940 (Win7SP1.050727-5400) Modules
| |||||||||||||||
| 624 | "C:\Users\admin\Desktop\icon changer +more.exe" | C:\Users\admin\Desktop\icon changer +more.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1272 | "C:\Users\admin\Desktop\babel.exe" | C:\Users\admin\Desktop\babel.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1532 | "C:\Users\admin\Desktop\Algorithme Converter v 1.2.exe" | C:\Users\admin\Desktop\Algorithme Converter v 1.2.exe | — | explorer.exe | |||||||||||
User: admin Company: Algorithme Converter v 1.2 Integrity Level: MEDIUM Description: Algorithme Converter v 1.2 Exit code: 0 Version: 1.2.0.0 Modules
| |||||||||||||||
| 1928 | "C:\Users\admin\AppData\Local\Temp\3582-490\babel.exe" | C:\Users\admin\AppData\Local\Temp\3582-490\babel.exe | — | babel.exe | |||||||||||
User: admin Company: Alberto Ferrazzoli Integrity Level: MEDIUM Description: babel.exe Exit code: 1 Version: 4.0.0.0 Modules
| |||||||||||||||
| 2204 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\mxiaqaca.cmdline" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe | — | babel.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual C# Command Line Compiler Exit code: 0 Version: 8.0.50727.4927 (NetFXspW7.050727-4900) Modules
| |||||||||||||||
| 2296 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Password umarsabil.rar" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3256 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\jprrozla.cmdline" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe | — | babel.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual C# Command Line Compiler Exit code: 0 Version: 8.0.50727.4927 (NetFXspW7.050727-4900) Modules
| |||||||||||||||
| 3652 | "C:\Users\admin\Desktop\babel.exe" | C:\Users\admin\Desktop\babel.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3988 | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RES3E0E.tmp" "c:\Users\admin\AppData\Local\Temp\CSC3E0D.tmp" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 8.00.50727.4940 (Win7SP1.050727-5400) Modules
| |||||||||||||||
Total events
1 454
Read events
1 429
Write events
25
Delete events
0
Modification events
| (PID) Process: | (2296) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2296) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2296) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2296) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12F\52C64B7E |
| Operation: | write | Name: | @C:\Windows\system32\NetworkExplorer.dll,-1 |
Value: Network | |||
| (PID) Process: | (2296) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Password umarsabil.rar | |||
| (PID) Process: | (2296) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2296) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2296) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2296) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2296) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12F\52C64B7E |
| Operation: | write | Name: | @C:\Windows\system32\notepad.exe,-469 |
Value: Text Document | |||
Executable files
5
Suspicious files
1
Text files
3
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2296 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2296.15324\123 njrat\njRAT v0.11G\Mono.Cecil.dll | — | |
MD5:— | SHA256:— | |||
| 2296 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2296.15324\123 njrat\njRAT v0.11G\njRAT v0.11G.exe | — | |
MD5:— | SHA256:— | |||
| 2296 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2296.15324\123 njrat\njRAT v0.11G\nj_users\DELL-PC_DELL_52013E44\PASS.txt | — | |
MD5:— | SHA256:— | |||
| 2296 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2296.15324\123 njrat\njRAT v0.11G\Plugin\cam.dll | — | |
MD5:— | SHA256:— | |||
| 2296 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2296.15324\123 njrat\njRAT v0.11G\Plugin\ch.dll | — | |
MD5:— | SHA256:— | |||
| 2296 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2296.15324\123 njrat\njRAT v0.11G\Plugin\inf.dll | — | |
MD5:— | SHA256:— | |||
| 2296 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2296.15324\123 njrat\njRAT v0.11G\Plugin\mic.dll | — | |
MD5:— | SHA256:— | |||
| 2296 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2296.15324\123 njrat\njRAT v0.11G\Plugin\plg.dll | — | |
MD5:— | SHA256:— | |||
| 2296 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2296.15324\123 njrat\njRAT v0.11G\Plugin\Pt.dll | — | |
MD5:— | SHA256:— | |||
| 2296 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2296.15324\123 njrat\njRAT v0.11G\Plugin\pw.dll | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report